| File name: | Internet360Ini.dll |
| Full analysis: | https://app.any.run/tasks/011206a9-d048-4817-956f-965f8c25d667 |
| Verdict: | Malicious activity |
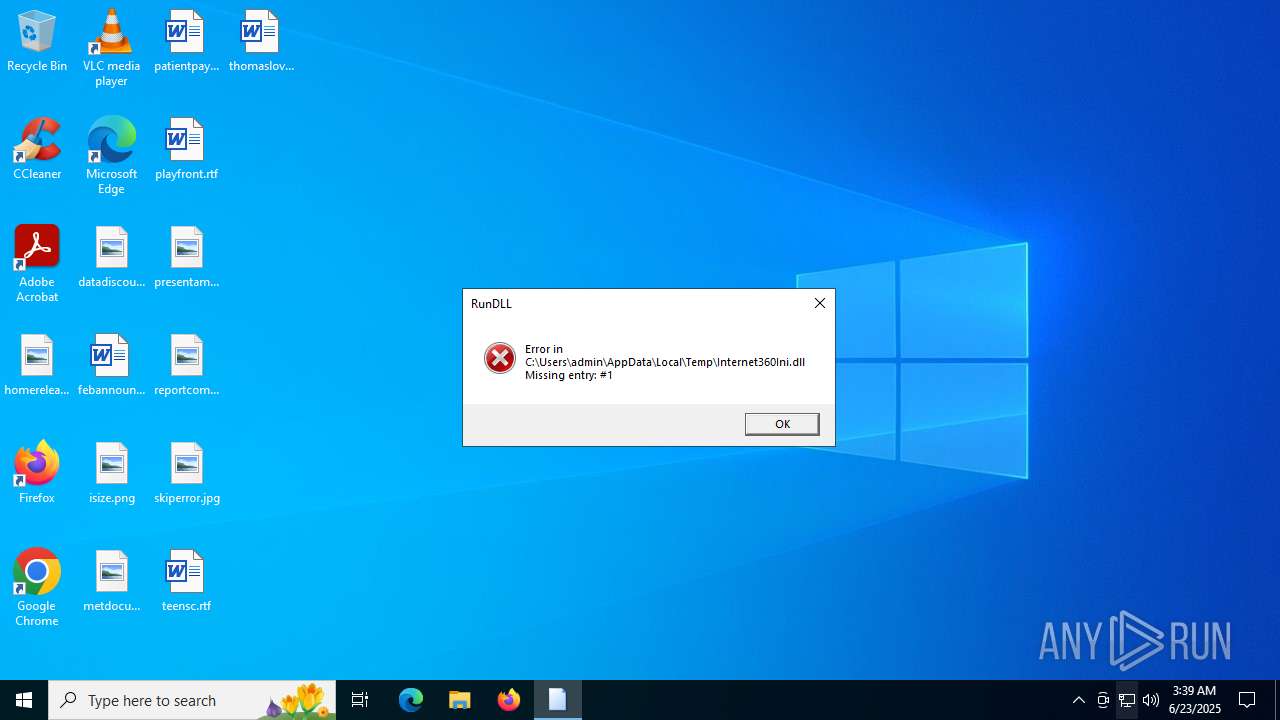
| Analysis date: | June 23, 2025, 03:38:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | B5553A4D3B8130ECCC58260CD3C63E94 |
| SHA1: | D2098F74F560D903F547957163644473BE39F7EC |
| SHA256: | 1A45F3A6EB916A84762370CE7DECFA5F42393D06C9E30FB56BD84BFAD67A12B1 |
| SSDEEP: | 98304:IwBMD4y+r59B3g84TY0DgDrTdbrZmaJvGpxUDZhpnZmu4aHNIesxVXL0MxJ+19t9:gm |
MALICIOUS
XORed URL has been found (YARA)
- rundll32.exe (PID: 6640)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- rundll32.exe (PID: 6640)
The process verifies whether the antivirus software is installed
- rundll32.exe (PID: 6640)
INFO
Create files in a temporary directory
- rundll32.exe (PID: 6640)
The sample compiled with chinese language support
- rundll32.exe (PID: 6640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6640) rundll32.exe
Decrypted-URLs (82)http://cacerts.digicert.com/DigiCertAssuredIDRootCA.crt0E
http://cacerts.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crt0
http://cacerts.digicert.com/DigiCertTrustedRootG4.crt0C
http://chp.f.360.cn/wdcquery
http://cp.uidf.f.360.cn/wpeinfo
http://crl.globalsign.com/ca/gstsacasha384g4.crl0
http://crl.globalsign.com/codesigningrootr45.crl0U
http://crl.globalsign.com/gs/gstimestampingg2.crl0T
http://crl.globalsign.com/gs/gstimestampingsha2g2.crl0
http://crl.globalsign.com/gsgccr45evcodesignca2020.crl0
http://crl.globalsign.com/root-r6.crl0G
http://crl.globalsign.net/root-r3.crl0
http://crl.globalsign.net/root.crl0
http://crl.thawte.com/ThawteTimestampingCA.crl0
http://crl.verisign.com/pca3-g5.crl04
http://crl3.digicert.com/DigiCertAssuredIDRootCA.crl0
http://crl3.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crl0
http://crl3.digicert.com/DigiCertTrustedRootG4.crl0
http://dl.360safe.com/gf/%u.cab
http://dl.360safe.com/gf/def.cab
http://down.360safe.com/setup.exe
http://down.360safe.com/setupbeta.exe
http://hao.360.cn/?ln=360ini
http://logo.verisign.com/vslogo.gif04
http://my.360.com
http://my.360safe.com
http://ocsp.digicert.com0A
http://ocsp.digicert.com0C
http://ocsp.digicert.com0X
http://ocsp.globalsign.com/ca/gstsacasha384g40C
http://ocsp.globalsign.com/codesigningrootr450F
http://ocsp.globalsign.com/gsgccr45evcodesignca20200U
http://ocsp.thawte.com0
http://ocsp.verisign.com0
http://ocsp2.globalsign.com/gstimestampingsha2g20
http://ocsp2.globalsign.com/rootr606
http://pinst.360.cn/360safebeta/safebeta_home.cab
http://pinst.360.cn/360sd/360sd_min.cab
http://s.360.cn/hips/update/inst.htm?m=%s&v=%s&s=%d&r=%d&d=%s&oav=%d
http://s.360.cn/safe/install.html?mid=%s&
http://s.360.cn/safe/setupsperr.htm?mid=%s
http://s1.symcb.com/pca3-g5.crl0
http://s2.symcb.com0
http://sd.360.cn
http://sd.360.cn/downloadbeta.html
http://secure.globalsign.com/cacert/codesigningrootr45.crt0A
http://secure.globalsign.com/cacert/gsgccr45evcodesignca2020.crt0?
http://secure.globalsign.com/cacert/gstimestampingg2.crt0
http://secure.globalsign.com/cacert/gstimestampingsha2g2.crt0
http://secure.globalsign.com/cacert/gstsacasha384g4.crt0
http://sf.symcb.com/sf.crl0a
http://sf.symcb.com/sf.crl0f
http://sf.symcb.com/sf.crt0
http://sfdl.360safe.com/inst_gf_popup.exe
http://sfdl.360safe.com/inst_gf_popup_ev.exe
http://sfdl.360safe.com/inst_js_popup.exe
http://sfdl.360safe.com/inst_js_popup_ev.exe
http://stat.sd.360.cn/setupfail.htm?pid=%s&case=%d
http://sv.symcb.com/sv.crl0a
http://sv.symcb.com/sv.crl0f
http://sv.symcb.com/sv.crt0
http://ts-aia.ws.symantec.com/tss-ca-g2.cer0
http://ts-crl.ws.symantec.com/tss-ca-g2.crl0
http://ts-crl.ws.symantec.com/tss-ca-g2.crl0(
http://ts-ocsp.ws.symantec.com07
http://www.2345.com/?pic360
http://www.360.cn
http://www.360.cn/killer/360compkill.html
http://www.360.cn/userexperienceimprovement.html
http://www.360.cn/xukexieyi.html#shadu
http://www.360safe.com
http://www.symauth.com/cps0(
http://www.symauth.com/rpa00
https://d.symcb.com/cps0%
https://d.symcb.com/rpa0
https://hao.360.cn/
https://www.globalsign.com/repository/0
https://www.globalsign.com/repository/03
https://www.globalsign.com/repository/06
https://www.verisign.com/cps0*
https://www.verisign.com/rpa
https://www.verisign.com/rpa0
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:29 02:32:09+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 882176 |
| InitializedDataSize: | 3628544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x859ff |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.1311 |
| ProductVersionNumber: | 2.0.0.1311 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 2, 0, 0, 1311 |
| OriginalFileName: | 360ini.dll |
| ProductVersion: | 2, 0, 0, 1311 |
Total processes
138
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "C:\WINDOWS\SysWOW64\rundll32.exe" C:\Users\admin\AppData\Local\Temp\Internet360Ini.dll, #1 | C:\Windows\SysWOW64\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
xor-url(PID) Process(6640) rundll32.exe Decrypted-URLs (82)http://cacerts.digicert.com/DigiCertAssuredIDRootCA.crt0E http://cacerts.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crt0 http://cacerts.digicert.com/DigiCertTrustedRootG4.crt0C http://chp.f.360.cn/wdcquery http://cp.uidf.f.360.cn/wpeinfo http://crl.globalsign.com/ca/gstsacasha384g4.crl0 http://crl.globalsign.com/codesigningrootr45.crl0U http://crl.globalsign.com/gs/gstimestampingg2.crl0T http://crl.globalsign.com/gs/gstimestampingsha2g2.crl0 http://crl.globalsign.com/gsgccr45evcodesignca2020.crl0 http://crl.globalsign.com/root-r6.crl0G http://crl.globalsign.net/root-r3.crl0 http://crl.globalsign.net/root.crl0 http://crl.thawte.com/ThawteTimestampingCA.crl0 http://crl.verisign.com/pca3-g5.crl04 http://crl3.digicert.com/DigiCertAssuredIDRootCA.crl0 http://crl3.digicert.com/DigiCertTrustedG4RSA4096SHA256TimeStampingCA.crl0 http://crl3.digicert.com/DigiCertTrustedRootG4.crl0 http://dl.360safe.com/gf/%u.cab http://dl.360safe.com/gf/def.cab http://down.360safe.com/setup.exe http://down.360safe.com/setupbeta.exe http://hao.360.cn/?ln=360ini http://logo.verisign.com/vslogo.gif04 http://my.360.com http://my.360safe.com http://ocsp.digicert.com0A http://ocsp.digicert.com0C http://ocsp.digicert.com0X http://ocsp.globalsign.com/ca/gstsacasha384g40C http://ocsp.globalsign.com/codesigningrootr450F http://ocsp.globalsign.com/gsgccr45evcodesignca20200U http://ocsp.thawte.com0 http://ocsp.verisign.com0 http://ocsp2.globalsign.com/gstimestampingsha2g20 http://ocsp2.globalsign.com/rootr606 http://pinst.360.cn/360safebeta/safebeta_home.cab http://pinst.360.cn/360sd/360sd_min.cab http://s.360.cn/hips/update/inst.htm?m=%s&v=%s&s=%d&r=%d&d=%s&oav=%d http://s.360.cn/safe/install.html?mid=%s& http://s.360.cn/safe/setupsperr.htm?mid=%s http://s1.symcb.com/pca3-g5.crl0 http://s2.symcb.com0 http://sd.360.cn http://sd.360.cn/downloadbeta.html http://secure.globalsign.com/cacert/codesigningrootr45.crt0A http://secure.globalsign.com/cacert/gsgccr45evcodesignca2020.crt0? http://secure.globalsign.com/cacert/gstimestampingg2.crt0 http://secure.globalsign.com/cacert/gstimestampingsha2g2.crt0 http://secure.globalsign.com/cacert/gstsacasha384g4.crt0 http://sf.symcb.com/sf.crl0a http://sf.symcb.com/sf.crl0f http://sf.symcb.com/sf.crt0 http://sfdl.360safe.com/inst_gf_popup.exe http://sfdl.360safe.com/inst_gf_popup_ev.exe http://sfdl.360safe.com/inst_js_popup.exe http://sfdl.360safe.com/inst_js_popup_ev.exe http://stat.sd.360.cn/setupfail.htm?pid=%s&case=%d http://sv.symcb.com/sv.crl0a http://sv.symcb.com/sv.crl0f http://sv.symcb.com/sv.crt0 http://ts-aia.ws.symantec.com/tss-ca-g2.cer0 http://ts-crl.ws.symantec.com/tss-ca-g2.crl0 http://ts-crl.ws.symantec.com/tss-ca-g2.crl0( http://ts-ocsp.ws.symantec.com07 http://www.2345.com/?pic360 http://www.360.cn http://www.360.cn/killer/360compkill.html http://www.360.cn/userexperienceimprovement.html http://www.360.cn/xukexieyi.html#shadu http://www.360safe.com http://www.symauth.com/cps0( http://www.symauth.com/rpa00 https://d.symcb.com/cps0% https://d.symcb.com/rpa0 https://hao.360.cn/ https://www.globalsign.com/repository/0 https://www.globalsign.com/repository/03 https://www.globalsign.com/repository/06 https://www.verisign.com/cps0* https://www.verisign.com/rpa https://www.verisign.com/rpa0 | |||||||||||||||
Total events
792
Read events
792
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
40
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{B2EC757F-A3FE-47c5-BE2C-D21A6FF3116F}.tmp | binary | |
MD5:5F71BC59239BF0A44A51EA83938BF665 | SHA256:A61D3EEBDA474232E5671C19767712EBC6A95A22CD48D6CAE9C1ED71E14E0333 | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{573F230F-21B3-408c-9225-F35980A8B225}.tmp | binary | |
MD5:986BC962DB01E3095B2CA3D3A7C75F0B | SHA256:E658175C8DF1CF62B0EA4A72A57641EB2DB8E78C7BEEF3BB13C707A6350ACECF | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{4B57941B-D63C-4fcb-AD98-ADE437621B6F}.tmp | binary | |
MD5:167211F20709EAEA30634D70E2E7E4E7 | SHA256:BC4F37EE9E4E48D9CA9BF5D7E1AD1D328533700FA41DBBBBA71ED0EF52AEC05C | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{6C054229-FF0B-4565-BD5B-EAA72F05809B}.tmp | binary | |
MD5:7A46290111B0EC1394F2EEE89B414634 | SHA256:7C058211F96982E8998FB05E96A694826D476B439B39617B1F3B1FBB4CC37827 | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{CCEE56E9-743D-49c8-8FC5-6ABE31299F9A}.tmp | binary | |
MD5:311525913479B93B4B134E7686BFD915 | SHA256:7D9A6DEAAEA72064F852A56A6AE397765B8DBE2C305EA93474C94C352BB681EE | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{EF3E26AD-ACE9-419d-8F90-86CCE10AD7DC}.tmp | binary | |
MD5:FBD30370AE8916EB2DC4B20CA90900C4 | SHA256:8422813143CF4ED76E8D13696BCAAC9005F0FE0BF60968940AE6C2BBE228DB85 | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{0E4EC65C-06C6-4435-A023-0819C354D9EF}.tmp | binary | |
MD5:C2D09A9BB844DB442E60383A1FB80F6F | SHA256:61EE3ADAE0A30F834B292DF983F0AB1C37073F56B30484C4495C016DBFE9554B | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{ECA84820-1E6E-4db2-A0F2-49CD00F7E0AC}.tmp | binary | |
MD5:24F190D59C043D97F76CC491C2C60FA0 | SHA256:C6AB0E3B99E6C58586A739D0C6134516964712B19C394110AB95592745945592 | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{4F30F805-A5F4-4280-8C29-5AEEFD3F605B}\jXoVlNyVdPzQjAbG.tmp | binary | |
MD5:9DDE4D9D99002D0BA83029E835AECCA8 | SHA256:C977746C33D273A482B02036F83F29FD5811AEECC301CD46F50C37955BD25E98 | |||
| 6640 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\{43830E44-914B-4dfb-81F2-F1E04A140E59}.tmp | binary | |
MD5:201AC30A1999E58386A76F36724071CA | SHA256:1CE7A8347D729F460899BC6396CD777CF794DB6FC900D33051619331144DC5E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
29
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6640 | rundll32.exe | GET | 200 | 171.8.167.90:80 | http://s.360.cn/hips/update/inst.htm?m=c3375a2e510ecaee01a0a4820a727e6e&m2=eeeeeeee77e256d0cc4755a6dd1f6ad7651f60d32b83&v=2001311&s=700&r=0&d=99990001 | CN | — | — | whitelisted |
6640 | rundll32.exe | GET | 200 | 171.8.167.90:80 | http://s.360.cn/hips/update/inst.htm?m=c3375a2e510ecaee01a0a4820a727e6e&m2=eeeeeeee77e256d0cc4755a6dd1f6ad7651f60d32b83&v=2001311&s=705&r=0&d=99990001 | CN | — | — | whitelisted |
6640 | rundll32.exe | GET | 200 | 171.8.167.90:80 | http://s.360.cn/hips/update/inst.htm?m=c3375a2e510ecaee01a0a4820a727e6e&m2=eeeeeeee77e256d0cc4755a6dd1f6ad7651f60d32b83&v=2001311&s=3000&r=0&d=0 | CN | — | — | whitelisted |
6640 | rundll32.exe | GET | 200 | 180.163.247.35:80 | http://grow.safe.360.cn/conf/item/info?m2=eeeeeeee77e256d0cc4755a6dd1f6ad7651f60d32b83&mid=c3375a2e510ecaee01a0a4820a727e6e&position=360ini&q=%6b%50%77%56%76%48%63%62%56%6f%46%77%70%32%4f%35%70%67%7a%71%77%69%72%78%51%31%53%62%36%36%7a%75%74%44%32%63%37%6e%71%63%53%55%69%79%4c%50%55%6a%42%72%74%52%35%63%7a%6a%72%61%65%70%41%37%6d%69%5a%34%37%51%67%43%78%66%58%2f%79%72%73%4f%6c%62%78%49%42%6a%43%48%4d%34%37%78%78%56%46%4f%32%4a%41%50%4b%51%69%47%6d%38%42%6f%32%49%4c%38%66%67%6a%58%56%4f%70%5a%4b%2b%6d%52%38%49%32%44%53%49%45%4b%6a%55%37%37%65%71%36%79%70%64%53%77%55%42%50%4f%42%6a%4c%76%47%53%39%6d%4b%57%46%35%39%56%78%4a%42%6f%6c%44%36%35%66%67%63%3d&rand=116970×tamp=1750649934&ver=10.0.19041.3636&sign=faedcaa32f6824c826fe532e98803790 | CN | binary | 27.4 Kb | whitelisted |
6640 | rundll32.exe | GET | 200 | 171.8.167.90:80 | http://s.360.cn/hips/update/inst.htm?m=c3375a2e510ecaee01a0a4820a727e6e&m2=eeeeeeee77e256d0cc4755a6dd1f6ad7651f60d32b83&v=2001311&s=3001&r=0&d=0 | CN | — | — | whitelisted |
3576 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5504 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
5504 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5244 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6640 | rundll32.exe | 171.8.167.90:80 | s.360.cn | Luoyang, Henan Province, P.R.China. | CN | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6640 | rundll32.exe | 180.163.247.35:80 | grow.safe.360.cn | China Telecom Group | CN | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3576 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3576 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
s.360.cn |
| whitelisted |
grow.safe.360.cn |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |