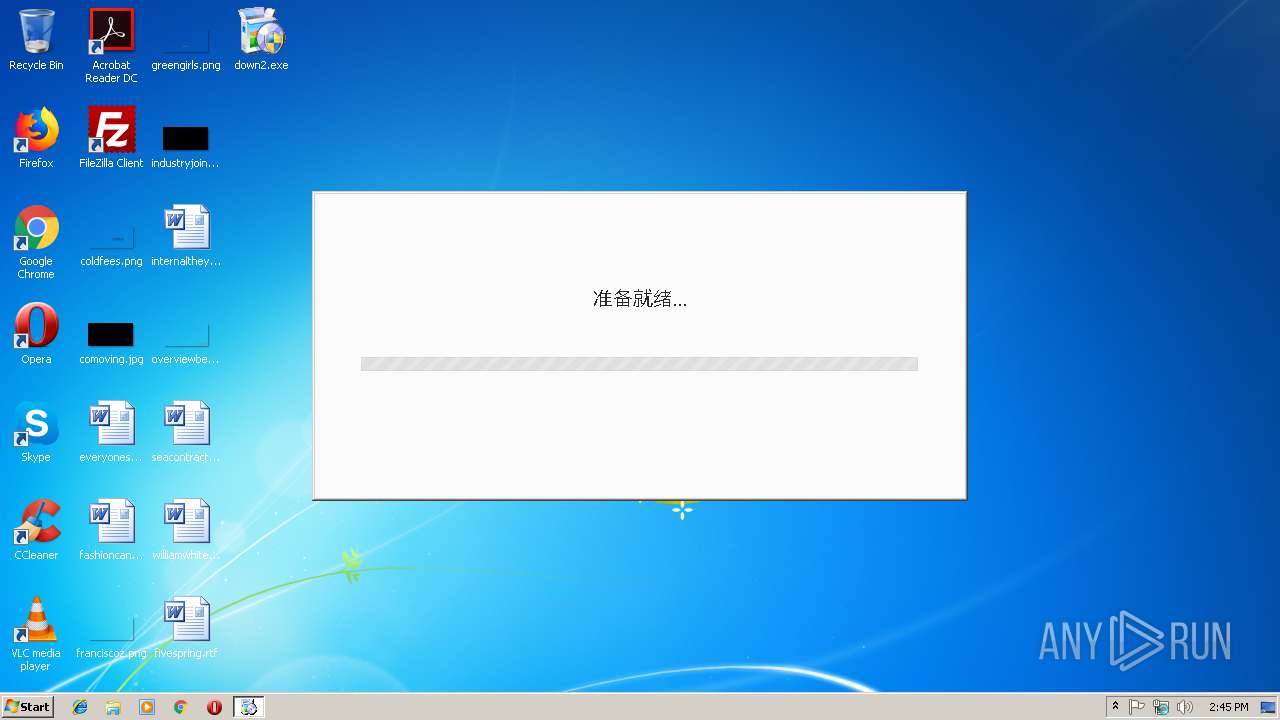
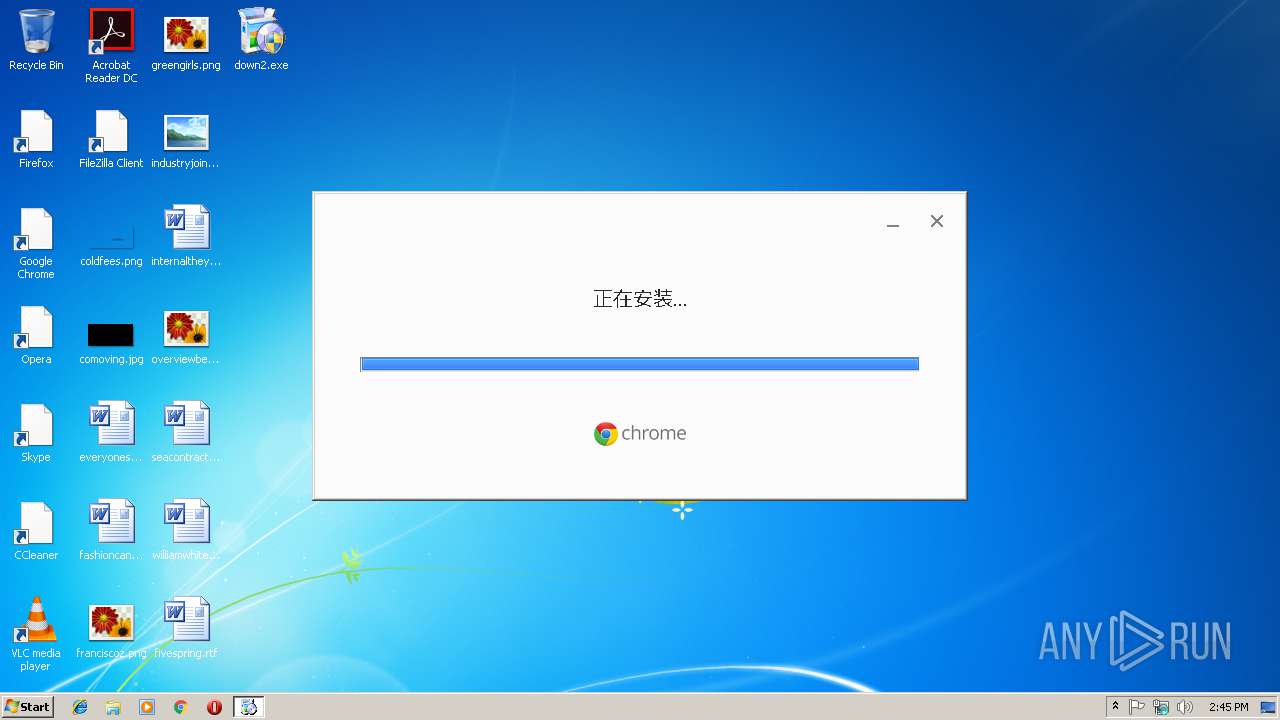
| File name: | down2.exe |
| Full analysis: | https://app.any.run/tasks/7e768fd9-2583-49e0-aba2-958bad755af4 |
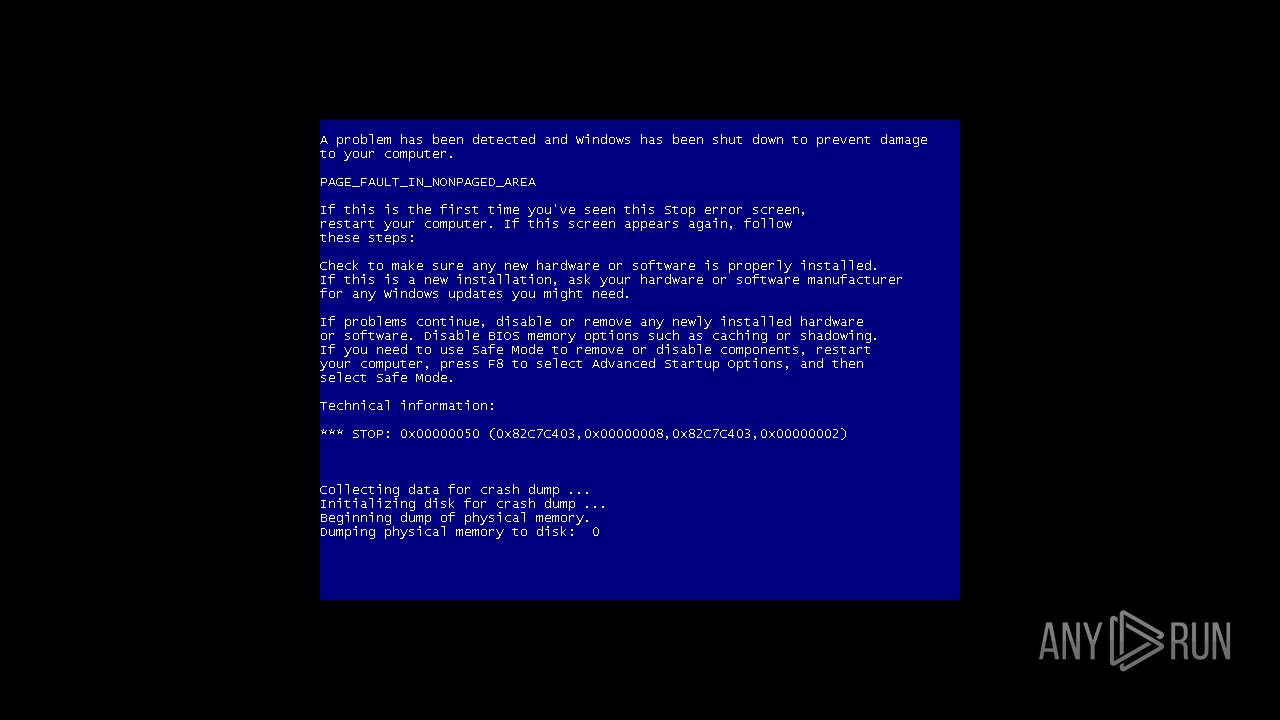
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 14:45:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6070309FC85000309E813AFB25584457 |
| SHA1: | 010F7A317F1AABC76DF83B4E3AB955EC4A1D9512 |
| SHA256: | 1A3CDE3C6FFB2792A922AE3CBFFC700FAFCCD0B7CDCE648860ECFD1F3C89D003 |
| SSDEEP: | 49152:DmvTYbAy39JR3HrSdbAy2nwUn59s0hyEygUUDjfR7VBlB8bcXPOdwrBqiGMUk4jI:YTyAOFLUT6T59sTd8R7VBHZKyBqRjzg |
MALICIOUS
Application was dropped or rewritten from another process
- ChromeSetup.exe (PID: 3908)
- GoogleUpdate.exe (PID: 3988)
- GoogleUpdate.exe (PID: 2856)
- GoogleUpdate.exe (PID: 2236)
- GoogleUpdate.exe (PID: 2652)
- GoogleUpdate.exe (PID: 2860)
- GoogleUpdate.exe (PID: 3056)
- setup.exe (PID: 2768)
- setup.exe (PID: 3524)
- GoogleCrashHandler.exe (PID: 3044)
- GoogleUpdateOnDemand.exe (PID: 2304)
- GoogleUpdate.exe (PID: 2052)
- GoogleUpdate.exe (PID: 3320)
Loads the Task Scheduler COM API
- GoogleUpdate.exe (PID: 2856)
Loads dropped or rewritten executable
- GoogleUpdate.exe (PID: 2856)
- GoogleUpdate.exe (PID: 2236)
- GoogleUpdate.exe (PID: 3988)
- GoogleUpdate.exe (PID: 2860)
- GoogleUpdate.exe (PID: 2652)
- GoogleUpdate.exe (PID: 3056)
- GoogleUpdate.exe (PID: 2052)
Uses SVCHOST.EXE for hidden code execution
- down2.exe (PID: 2640)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 2652)
Changes the autorun value in the registry
- setup.exe (PID: 2768)
SUSPICIOUS
Executable content was dropped or overwritten
- ChromeSetup.exe (PID: 3908)
- down2.exe (PID: 2640)
- GoogleUpdate.exe (PID: 2856)
- svchost.exe (PID: 3368)
- 71.0.3578.98_chrome_installer.exe (PID: 1144)
- setup.exe (PID: 2768)
Low-level read access rights to disk partition
- down2.exe (PID: 2640)
Creates COM task schedule object
- GoogleUpdate.exe (PID: 2236)
- GoogleUpdate.exe (PID: 2856)
Disables SEHOP
- GoogleUpdate.exe (PID: 2856)
Starts itself from another location
- GoogleUpdate.exe (PID: 2856)
Creates files in the program directory
- ChromeSetup.exe (PID: 3908)
- GoogleUpdate.exe (PID: 2856)
- GoogleUpdate.exe (PID: 3056)
- setup.exe (PID: 2768)
Creates files in the Windows directory
- svchost.exe (PID: 3368)
- GoogleUpdate.exe (PID: 3056)
- setup.exe (PID: 3524)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 2652)
Creates files in the driver directory
- svchost.exe (PID: 3368)
Modifies the open verb of a shell class
- setup.exe (PID: 2768)
Removes files from Windows directory
- setup.exe (PID: 2768)
Creates a software uninstall entry
- setup.exe (PID: 2768)
Application launched itself
- GoogleUpdate.exe (PID: 3056)
INFO
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 2768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:07 10:44:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 548864 |
| InitializedDataSize: | 2129920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.33.23 |
| ProductVersionNumber: | 1.3.33.23 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.3.33.23 |
| FileDescription: | Google Update Setup |
| ProductName: | Google Update |
| ProductVersion: | 1.3.33.23 |
| LegalCopyright: | Copyright 2007-2010 Google Inc. |
| Comments: | Google Update |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jan-2019 09:44:24 |
| Detected languages: |
|
| FileVersion: | 1.3.33.23 |
| FileDescription: | Google Update Setup |
| ProductName: | Google Update |
| ProductVersion: | 1.3.33.23 |
| LegalCopyright: | Copyright 2007-2010 Google Inc. |
| Comments: | Google Update |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 07-Jan-2019 09:44:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00275000 | 0x0002B000 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98994 | |
.rsrc | 0x002A0000 | 0x00008000 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.60535 |
.data0 | 0x002A8000 | 0x00061000 | 0x00029E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.76254 |
.adata | 0x00309000 | 0x00001000 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 3.76602 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.13669 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.91985 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.83772 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.68656 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.50268 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
127 | 1.95915 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 2.62987 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
51
Monitored processes
17
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files\Google\Update\Install\{1CA7861E-FBB4-471B-B552-7E843B109E84}\71.0.3578.98_chrome_installer.exe" --verbose-logging --do-not-launch-chrome --system-level /installerdata="C:\Windows\TEMP\gui47C6.tmp" | C:\Program Files\Google\Update\Install\{1CA7861E-FBB4-471B-B552-7E843B109E84}\71.0.3578.98_chrome_installer.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 71.0.3578.98 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4zMy4yMyIgc2hlbGxfdmVyc2lvbj0iMS4zLjMzLjIzIiBpc21hY2hpbmU9IjEiIHNlc3Npb25pZD0iezNDQ0JFNDNFLTA2QTEtNEI0RS1COTA2LUU4QzM5RkI0NkJENX0iIHVzZXJpZD0iezA0RTY2QkE2LTkzOUQtNEI4MS04NjY0LUIzRDU4REVERDA2Rn0iIGluc3RhbGxzb3VyY2U9InRhZ2dlZG1pIiByZXF1ZXN0aWQ9Ins1MUJDNzVBNy05RTI0LTQ3M0UtOTlFNi1EMjYyMjE5RTJENjN9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IHBoeXNtZW1vcnk9IjMiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjYuMS43NjAxLjAiIHNwPSJTZXJ2aWNlIFBhY2sgMSIgYXJjaD0ieDg2Ii8-PGFwcCBhcHBpZD0iezhBNjlEMzQ1LUQ1NjQtNDYzQy1BRkYxLUE2OUQ5RTUzMEY5Nn0iIHZlcnNpb249IiIgbmV4dHZlcnNpb249IjcxLjAuMzU3OC45OCIgYXA9Ing2NC1zdGFibGUtc3RhdHNkZWZfMSIgbGFuZz0iemgtQ04iIGJyYW5kPSIiIGNsaWVudD0iIiBpbnN0YWxsYWdlPSIxMzUiIGluc3RhbGxkYXRlPSI0MjU2IiBpaWQ9IntEQjU2NjM5RC00MEFCLTc5MTItMkY5RC1CRTQyNzVCNjAyNTR9IiBjb2hvcnQ9IjE6Z3UvaTE5OiIgY29ob3J0bmFtZT0iU3RhYmxlIEluc3RhbGxzIE9ubHkiPjxldmVudCBldmVudHR5cGU9IjkiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiLz48ZXZlbnQgZXZlbnR0eXBlPSI1IiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIi8-PGV2ZW50IGV2ZW50dHlwZT0iMSIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgZG93bmxvYWRlcj0iYml0cyIgdXJsPSJodHRwOi8vcmVkaXJlY3Rvci5ndnQxLmNvbS9lZGdlZGwvcmVsZWFzZTIvY2hyb21lL0VwNnBiakYweGxRXzcxLjAuMzU3OC45OC83MS4wLjM1NzguOThfY2hyb21lX2luc3RhbGxlci5leGUiIGRvd25sb2FkZWQ9IjUzNDA4NDk2IiB0b3RhbD0iNTM0MDg0OTYiIGRvd25sb2FkX3RpbWVfbXM9IjEzMjE5Ii8-PGV2ZW50IGV2ZW50dHlwZT0iMSIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIvPjxldmVudCBldmVudHR5cGU9IjYiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiLz48ZXZlbnQgZXZlbnR0eXBlPSIyIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBzb3VyY2VfdXJsX2luZGV4PSIwIiB1cGRhdGVfY2hlY2tfdGltZV9tcz0iMzE1NiIgZG93bmxvYWRfdGltZV9tcz0iMTM4NDQiIGRvd25sb2FkZWQ9IjUzNDA4NDk2IiB0b3RhbD0iNTM0MDg0OTYiIGluc3RhbGxfdGltZV9tcz0iOTE3MiIvPjxkYXRhIG5hbWU9Imluc3RhbGwiIGluZGV4PSJlbXB0eSIvPjwvYXBwPjwvcmVxdWVzdD4 | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /regserver | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Update\1.3.33.23\GoogleUpdateOnDemand.exe" -Embedding | C:\Program Files\Google\Update\1.3.33.23\GoogleUpdateOnDemand.exe | — | svchost.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Update Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2640 | "C:\Users\admin\Desktop\down2.exe" | C:\Users\admin\Desktop\down2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Google Update Setup Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4zMy4yMyIgc2hlbGxfdmVyc2lvbj0iMS4zLjMzLjIzIiBpc21hY2hpbmU9IjEiIHNlc3Npb25pZD0iezNDQ0JFNDNFLTA2QTEtNEI0RS1COTA2LUU4QzM5RkI0NkJENX0iIHVzZXJpZD0iezA0RTY2QkE2LTkzOUQtNEI4MS04NjY0LUIzRDU4REVERDA2Rn0iIGluc3RhbGxzb3VyY2U9InRhZ2dlZG1pIiByZXF1ZXN0aWQ9IntDQ0YzQjEzMC04NkQyLTRERjQtQTgyQS1FMDQ5QUREQ0ZBODV9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IHBoeXNtZW1vcnk9IjMiIHNzZT0iMSIgc3NlMj0iMSIgc3NlMz0iMSIgc3NzZTM9IjEiIHNzZTQxPSIxIiBzc2U0Mj0iMSIgYXZ4PSIxIi8-PG9zIHBsYXRmb3JtPSJ3aW4iIHZlcnNpb249IjYuMS43NjAxLjAiIHNwPSJTZXJ2aWNlIFBhY2sgMSIgYXJjaD0ieDg2Ii8-PGFwcCBhcHBpZD0iezQzMEZENEQwLUI3MjktNEY2MS1BQTM0LTkxNTI2NDgxNzk5RH0iIHZlcnNpb249IjEuMy4zMy4xNyIgbmV4dHZlcnNpb249IjEuMy4zMy4yMyIgbGFuZz0iemgtQ04iIGJyYW5kPSIiIGNsaWVudD0iIiBpaWQ9IntEQjU2NjM5RC00MEFCLTc5MTItMkY5RC1CRTQyNzVCNjAyNTR9Ij48ZXZlbnQgZXZlbnR0eXBlPSIyIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBpbnN0YWxsX3RpbWVfbXM9IjE2MjUiLz48L2FwcD48L3JlcXVlc3Q- | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\CR_F8170.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\CR_F8170.tmp\CHROME.PACKED.7Z" --verbose-logging --do-not-launch-chrome --system-level /installerdata="C:\Windows\TEMP\gui47C6.tmp" | C:\Users\admin\AppData\Local\Temp\CR_F8170.tmp\setup.exe | 71.0.3578.98_chrome_installer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 71.0.3578.98 Modules
| |||||||||||||||
| 2856 | "C:\Program Files\GUMF503.tmp\GoogleUpdate.exe" /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={DB56639D-40AB-7912-2F9D-BE4275B60254}&lang=zh-CN&browser=4&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x64-stable-statsdef_1&installdataindex=empty" | C:\Program Files\GUMF503.tmp\GoogleUpdate.exe | ChromeSetup.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /handoff "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={DB56639D-40AB-7912-2F9D-BE4275B60254}&lang=zh-CN&browser=4&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x64-stable-statsdef_1&installdataindex=empty" /installsource taggedmi /sessionid "{3CCBE43E-06A1-4B4E-B906-E8C39FB46BD5}" | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Google\Update\1.3.33.23\GoogleCrashHandler.exe" | C:\Program Files\Google\Update\1.3.33.23\GoogleCrashHandler.exe | — | GoogleUpdate.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Crash Handler Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
Total events
1 973
Read events
468
Write events
1 365
Delete events
140
Modification events
| (PID) Process: | (2640) down2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.key |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2640) down2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.key |
| Operation: | write | Name: | |
Value: regfile | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 1 | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | delete value | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\GoogleUpdate.exe.old20f764 | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update |
| Operation: | write | Name: | path |
Value: C:\Program Files\Google\Update\GoogleUpdate.exe | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update |
| Operation: | write | Name: | UninstallCmdLine |
Value: "C:\Program Files\Google\Update\GoogleUpdate.exe" /uninstall | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\Clients\{430FD4D0-B729-4F61-AA34-91526481799D} |
| Operation: | write | Name: | pv |
Value: 1.3.33.23 | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\Clients\{430FD4D0-B729-4F61-AA34-91526481799D} |
| Operation: | write | Name: | name |
Value: Google 更新 | |||
| (PID) Process: | (2856) GoogleUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientState\{430FD4D0-B729-4F61-AA34-91526481799D} |
| Operation: | write | Name: | pv |
Value: 1.3.33.23 | |||
Executable files
159
Suspicious files
5
Text files
18
Unknown types
66
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | down2.exe | C:\Users\admin\AppData\Local\Temp\ChromeSetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\GoogleUpdateComRegisterShell64.exe | executable | |
MD5:E093DC3362DBCECB4FA27C9CACE64D0A | SHA256:30AE722349C3A700CE31927DE27E50463DB60DD3A9980EE81E0839D5F5F89267 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\goopdate.dll | executable | |
MD5:DFDC0F7FB807FAD35308E83D95EB68A6 | SHA256:39E018EBE1FAEB76D2E7E6E67354BEDA587F801D197D32938EE39BD130485CE2 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\psmachine.dll | executable | |
MD5:55390B3DEE47126A70E09C7729966A32 | SHA256:66F2C5DE9DDDE1C2DD3671F8CE141073B74608E37067F3E787DEDBA4C59DC087 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\GoogleCrashHandler64.exe | executable | |
MD5:32D5589FB273DCE6422F56E4DB2DE367 | SHA256:9CBD0395E540E2DCFC5681FF4CBA2BA4CEAD845FEFC4F78C443258570D0CC031 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\psmachine_64.dll | executable | |
MD5:A5B17D12719EA1FF72B5E46F8D4385D9 | SHA256:9BE1477BE27FC3DE1617694F4C5DB1118842275772E3D77A479BCBEFFD9CF328 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\psuser.dll | executable | |
MD5:E83F92CFB6876FB3DEFB3825E4FA9C87 | SHA256:25C850421D0E8A6AE4531AE28857BABE295A719FFF9FE1E0ECC843ED0DEAE219 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\goopdateres_am.dll | executable | |
MD5:27F6BBD61941D43925F88562139C6F65 | SHA256:35A6E99723B99ED65D780479FB289BFD31CC1E306350C088062C2462CE578A84 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\goopdateres_ar.dll | executable | |
MD5:C58D00CF808BE896AD5072E1E5F2F526 | SHA256:EC64A0509AA00B27D678CEDDCE8CE799A9250687C3ADE647E5A8F7D82DAF95A9 | |||
| 3908 | ChromeSetup.exe | C:\Program Files\GUMF503.tmp\goopdateres_bn.dll | executable | |
MD5:CB0ED6FA92CBC86BF87ECCED719A6A24 | SHA256:F33F1EFD4896D752B2336ACE53AA3D5F359ADFEDE35DE92D440B23130892213C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3368 | svchost.exe | GET | — | 222.187.232.56:80 | http://www.taolea.top/tongji.php?os=6.1.7601&userid=hcc888&mac=5254004A04AF&ver=&xiezai=0&wb=&az=2&uid= | CN | — | — | suspicious |
— | — | HEAD | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome/Ep6pbjF0xlQ_71.0.3578.98/71.0.3578.98_chrome_installer.exe | US | — | — | whitelisted |
2640 | down2.exe | POST | 200 | 69.30.242.179:80 | http://69.30.242.179/img/logxz.txt | US | text | 6 b | suspicious |
— | — | GET | 200 | 173.194.150.219:80 | http://r5---sn-5goeen7r.gvt1.com/edgedl/release2/chrome/Ep6pbjF0xlQ_71.0.3578.98/71.0.3578.98_chrome_installer.exe?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1547131408&mv=m&pl=24&shardbypass=yes | US | executable | 50.9 Mb | whitelisted |
— | — | HEAD | 200 | 173.194.150.219:80 | http://r5---sn-5goeen7r.gvt1.com/edgedl/release2/chrome/Ep6pbjF0xlQ_71.0.3578.98/71.0.3578.98_chrome_installer.exe?cms_redirect=yes&mip=82.102.22.104&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1547131408&mv=m&pl=24&shardbypass=yes | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | svchost.exe | 222.187.232.56:80 | www.taolea.top | No.31,Jin-rong Street | CN | suspicious |
2652 | GoogleUpdate.exe | 172.217.16.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3056 | GoogleUpdate.exe | 172.217.16.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2640 | down2.exe | 69.30.242.179:80 | — | WholeSale Internet, Inc. | US | suspicious |
— | — | 173.194.150.219:80 | r5---sn-5goeen7r.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.taolea.top |
| suspicious |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-5goeen7r.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |