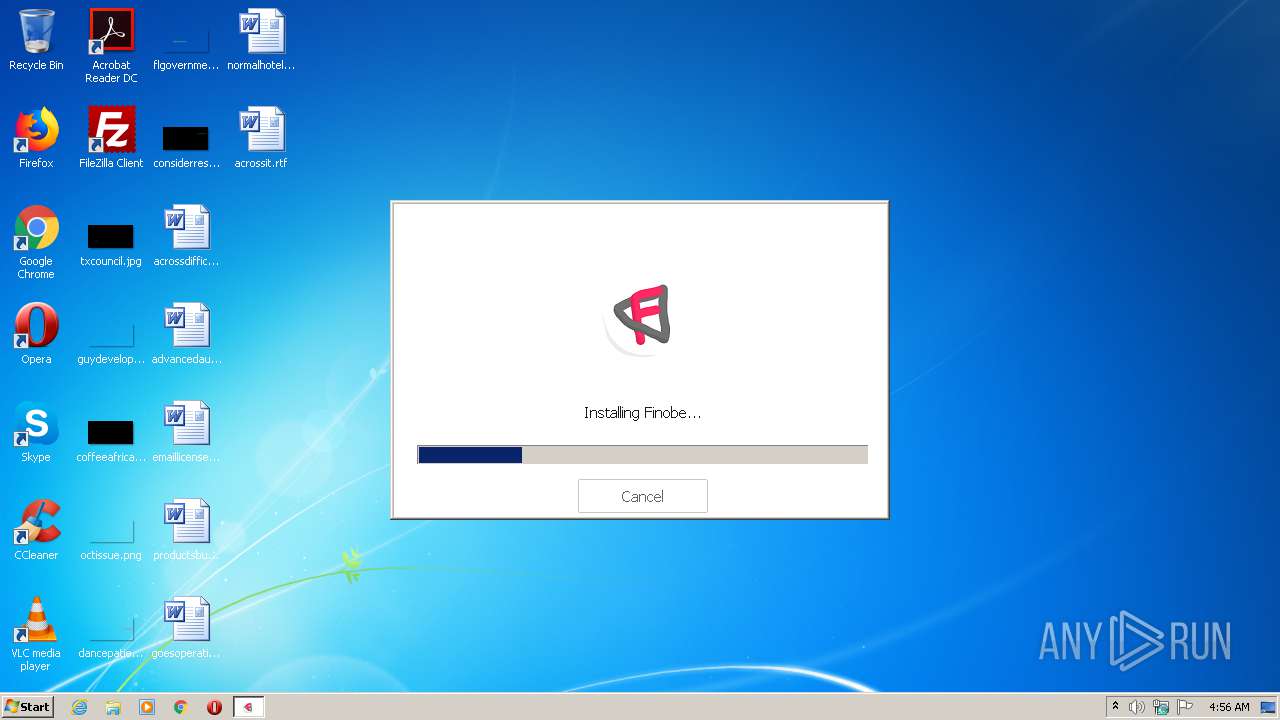
| File name: | BootstrapperFinobe.exe |
| Full analysis: | https://app.any.run/tasks/0d0d6e2f-47b1-4989-b10c-7d20f6df8158 |
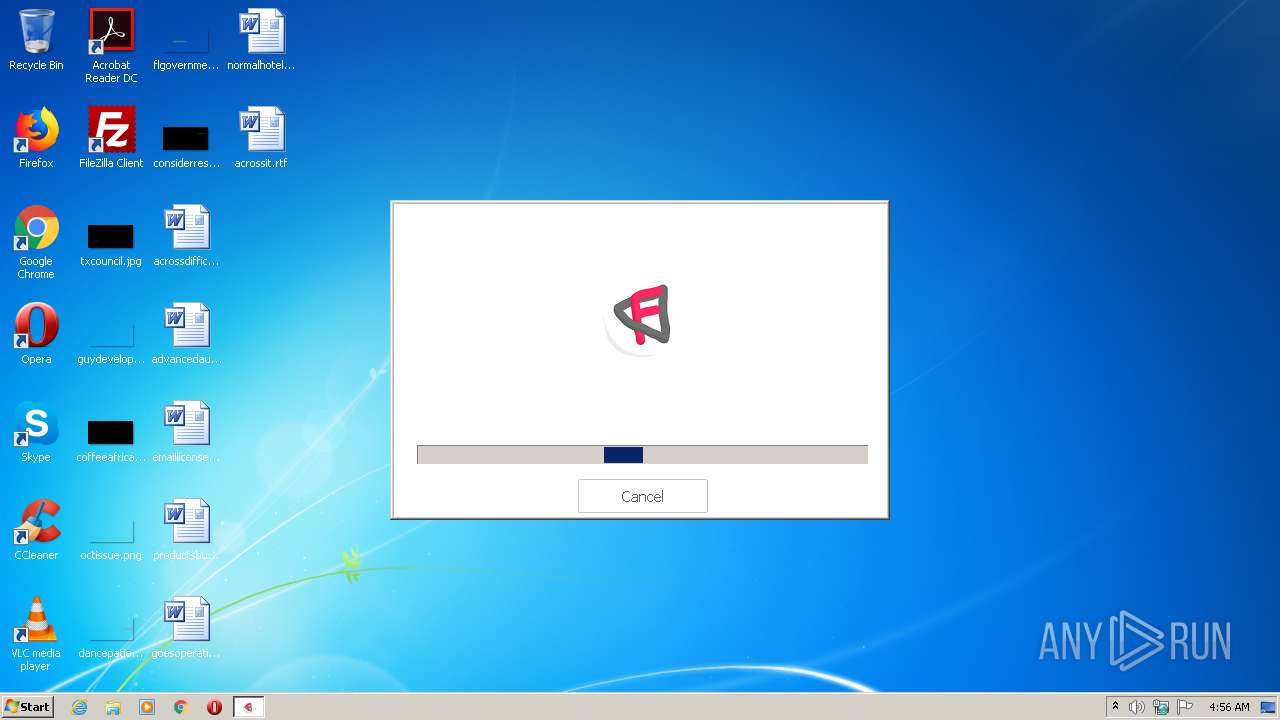
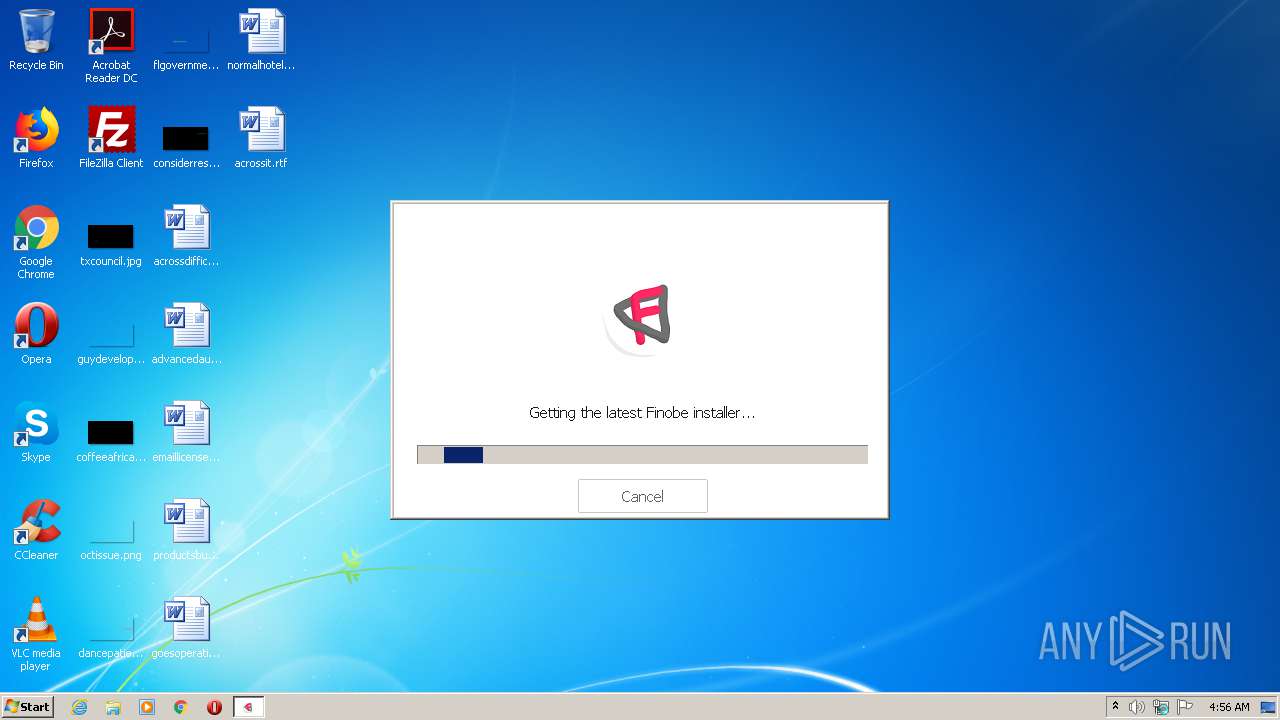
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 03:55:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C0B092FB6F0C796E20AD2DB65CA8206F |
| SHA1: | EE0E06817AC6C71C5951288BDB95CD755EFEC43F |
| SHA256: | 1A3C813C6760886A8ED1472BF86FC7E8A09F92DD95EE3C7E84BD11F6F43DA0AE |
| SSDEEP: | 49152:JAfLaF/Gaoe42UXJXphJHe3MfJo1cWE1/s/dkcrp3kTufOk4XUI8UrDh:/dGCfU5XfJH8MfJBWE1/s1kcrp3Ok4XJ |
MALICIOUS
Application was dropped or rewritten from another process
- RBX-052D5F4E.tmp (PID: 2864)
SUSPICIOUS
Starts application with an unusual extension
- BootstrapperFinobe.exe (PID: 2988)
Reads Internet Cache Settings
- BootstrapperFinobe.exe (PID: 2988)
- RBX-052D5F4E.tmp (PID: 2864)
Executable content was dropped or overwritten
- BootstrapperFinobe.exe (PID: 2988)
- RBX-052D5F4E.tmp (PID: 2864)
Creates files in the user directory
- BootstrapperFinobe.exe (PID: 2988)
- RBX-052D5F4E.tmp (PID: 2864)
INFO
Reads the hosts file
- chrome.exe (PID: 2404)
- chrome.exe (PID: 2512)
Manual execution by user
- chrome.exe (PID: 2404)
Application launched itself
- chrome.exe (PID: 2404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:20 23:47:18+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1750528 |
| InitializedDataSize: | 1040896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16f46b |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.105 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Finobe |
| FileDescription: | Finobe |
| FileVersion: | 1.0.0.105 |
| LegalCopyright: | (C) 2018 Finobe |
| ProductName: | Finobe Bootstrapper |
| ProductVersion: | 1.0.0.0 |
| ConfigurationName: | Release |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Feb-2019 22:47:18 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Finobe |
| FileDescription: | Finobe |
| FileVersion: | 1.0.0.105 |
| LegalCopyright: | (C) 2018 Finobe |
| ProductName: | Finobe Bootstrapper |
| ProductVersion: | 1.0.0.0 |
| ConfigurationName: | Release |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 20-Feb-2019 22:47:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001AB599 | 0x001AB600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5747 |
.rdata | 0x001AD000 | 0x0006B428 | 0x0006B600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2472 |
.data | 0x00219000 | 0x0000DA50 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.83575 |
.gfids | 0x00227000 | 0x00019FE8 | 0x0001A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24525 |
.giats | 0x00241000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.155178 |
.tls | 0x00242000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00243000 | 0x0004F304 | 0x0004F400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.69553 |
.reloc | 0x00293000 | 0x000220D8 | 0x00022200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.51252 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.79908 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
3 | 3.30928 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.1503 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.7351 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.95737 | 24372 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.37372 | 96 | Latin 1 / Western European | English - United States | RT_STRING |
130 | 3.12274 | 254 | Latin 1 / Western European | English - United States | RT_DIALOG |
131 | 2 | 8 | Latin 1 / Western European | English - United States | RT_ACCELERATOR |
157 | 2.27496 | 17290 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
PSAPI.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
?StartGame@SharedLauncher@@YAJAAV?$simple_logger@_W@@PA_W11ABU_GUID@@_N131W4LaunchMode@1@@Z | 1 | 0x000142E0 |
Total processes
47
Monitored processes
13
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10508733794987469509 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11548941004535342867 --mojo-platform-channel-handle=3504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4988853548630610674 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7769035236633169305 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2412 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\AppData\Local\Temp\RBX-052D5F4E.tmp" | C:\Users\admin\AppData\Local\Temp\RBX-052D5F4E.tmp | BootstrapperFinobe.exe | ||||||||||||
User: admin Company: Finobe Integrity Level: MEDIUM Description: Finobe Exit code: 0 Version: 1.1.0.79 Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Local\Temp\BootstrapperFinobe.exe" | C:\Users\admin\AppData\Local\Temp\BootstrapperFinobe.exe | explorer.exe | ||||||||||||
User: admin Company: Finobe Integrity Level: MEDIUM Description: Finobe Exit code: 0 Version: 1.0.0.105 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3241107580162641168 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1056,4586159893275633482,17591086839513595664,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6942082326722051391 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
317
Read events
241
Write events
73
Delete events
3
Modification events
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Finobe_Penelope |
| Operation: | write | Name: | CPath |
Value: C:\Users\admin\AppData\LocalLow\rbxcsettings.rbx | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2988) BootstrapperFinobe.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2864) RBX-052D5F4E.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
11
Suspicious files
5
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Local\Temp\Cab73EC.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Local\Temp\Tar73ED.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5VVG2959.txt | — | |
MD5:— | SHA256:— | |||
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\8XWNWLIF.txt | — | |
MD5:— | SHA256:— | |||
| 2864 | RBX-052D5F4E.tmp | C:\Users\admin\AppData\Local\Temp\Cab8AA1.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | RBX-052D5F4E.tmp | C:\Users\admin\AppData\Local\Temp\Tar8AA2.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | RBX-052D5F4E.tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\EO739WQY.txt | — | |
MD5:— | SHA256:— | |||
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\versionQTStudio[1] | text | |
MD5:— | SHA256:— | |||
| 2864 | RBX-052D5F4E.tmp | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\version-96610f8a17d139d5-Libraries[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 2988 | BootstrapperFinobe.exe | C:\Users\admin\AppData\Local\Temp\RBX-052D5F4E.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
13
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | BootstrapperFinobe.exe | 104.24.117.15:443 | finobe.com | Cloudflare Inc | US | shared |
2988 | BootstrapperFinobe.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2988 | BootstrapperFinobe.exe | 104.24.116.15:443 | finobe.com | Cloudflare Inc | US | shared |
2864 | RBX-052D5F4E.tmp | 104.24.116.15:443 | finobe.com | Cloudflare Inc | US | shared |
2864 | RBX-052D5F4E.tmp | 104.24.117.15:443 | finobe.com | Cloudflare Inc | US | shared |
2512 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
finobe.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
prod1-setup.finobe.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |