| File name: | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe |
| Full analysis: | https://app.any.run/tasks/403bdfed-fdaa-4244-a7f9-720d15b19460 |
| Verdict: | Malicious activity |
| Analysis date: | May 03, 2018, 16:09:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1BD6C9E8E3A11F03A22017CF246DCD16 |
| SHA1: | 7F279497422E034302F7E7E416036F184D5EDDCC |
| SHA256: | 1A3112662B7BFC1620D03C8B3A62F862A316404EB1A04E057AB839DDDF75162C |
| SSDEEP: | 6144:+bUTp1uEA7Z9V+KM+/87wBeat1RAAx94DqoJVAepXPRSDJikrHLAPS7EQRMuOBf/:+IeEQZKA87wBe2Rf4DqokedPRSDskrHQ |
MALICIOUS
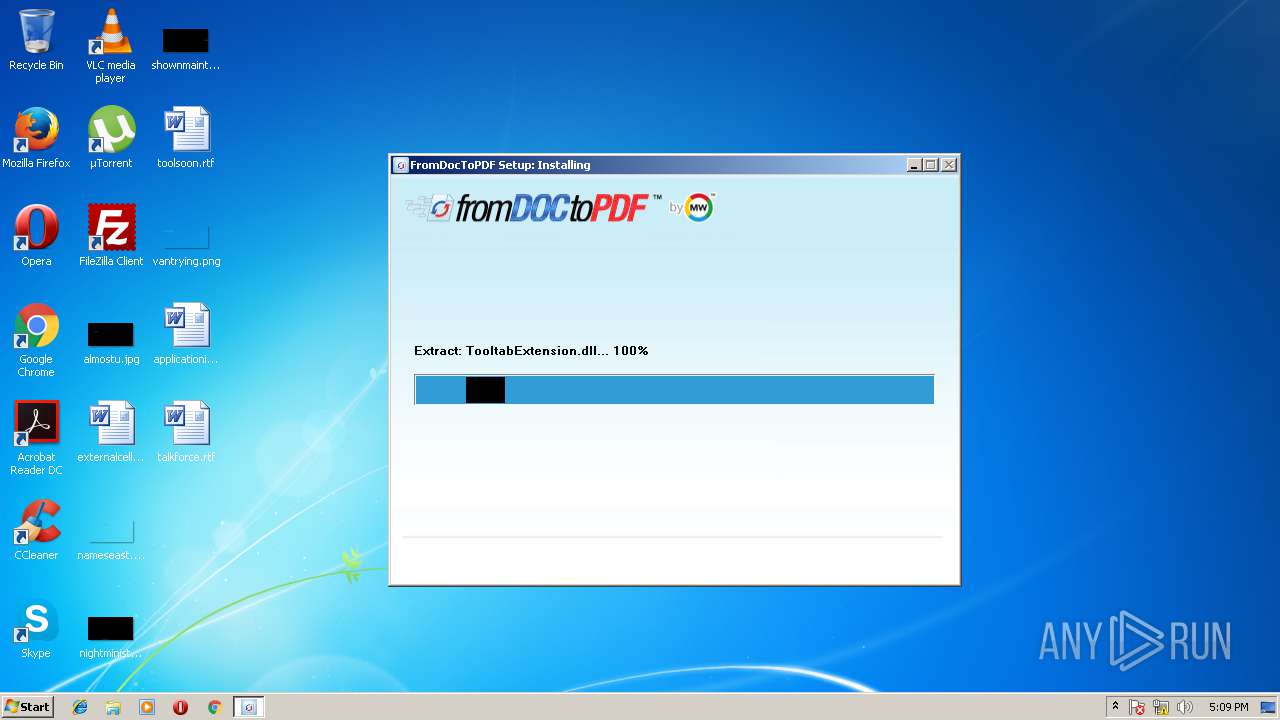
Application loaded dropped or rewritten executable
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
SUSPICIOUS
Creates a software uninstall entry
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
Creates files in the user directory
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 3760)
Reads Internet Cache Settings
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
INFO
Dropped object may contain URL's
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 1588)
- iexplore.exe (PID: 3844)
Loads rich edit control libraries
- FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe (PID: 284)
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 3760)
Reads Internet Cache Settings
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 3844)
Creates files in the user directory
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 1588)
- iexplore.exe (PID: 3844)
Changes internet zones settings
- iexplore.exe (PID: 1588)
Application launched itself
- iexplore.exe (PID: 1588)
Reads internet explorer settings
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 2828)
- iexplore.exe (PID: 3844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.1000 |
| ProductVersionNumber: | 2.7.1.1000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
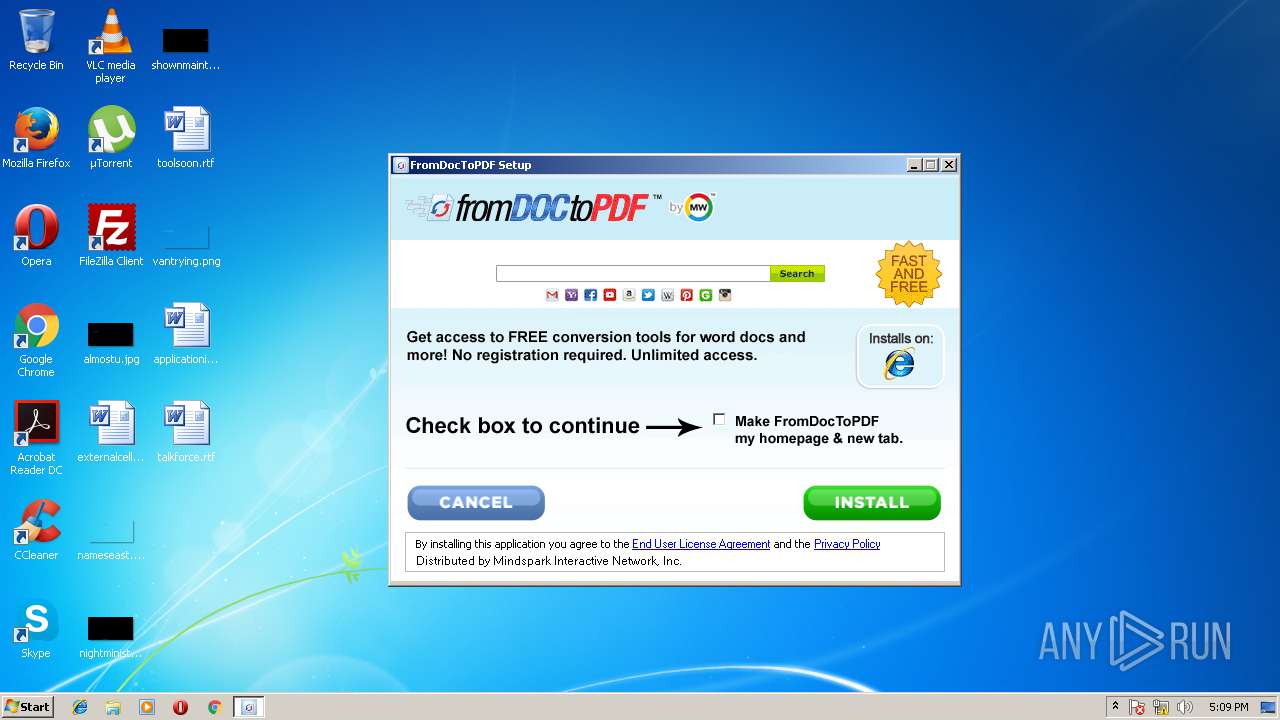
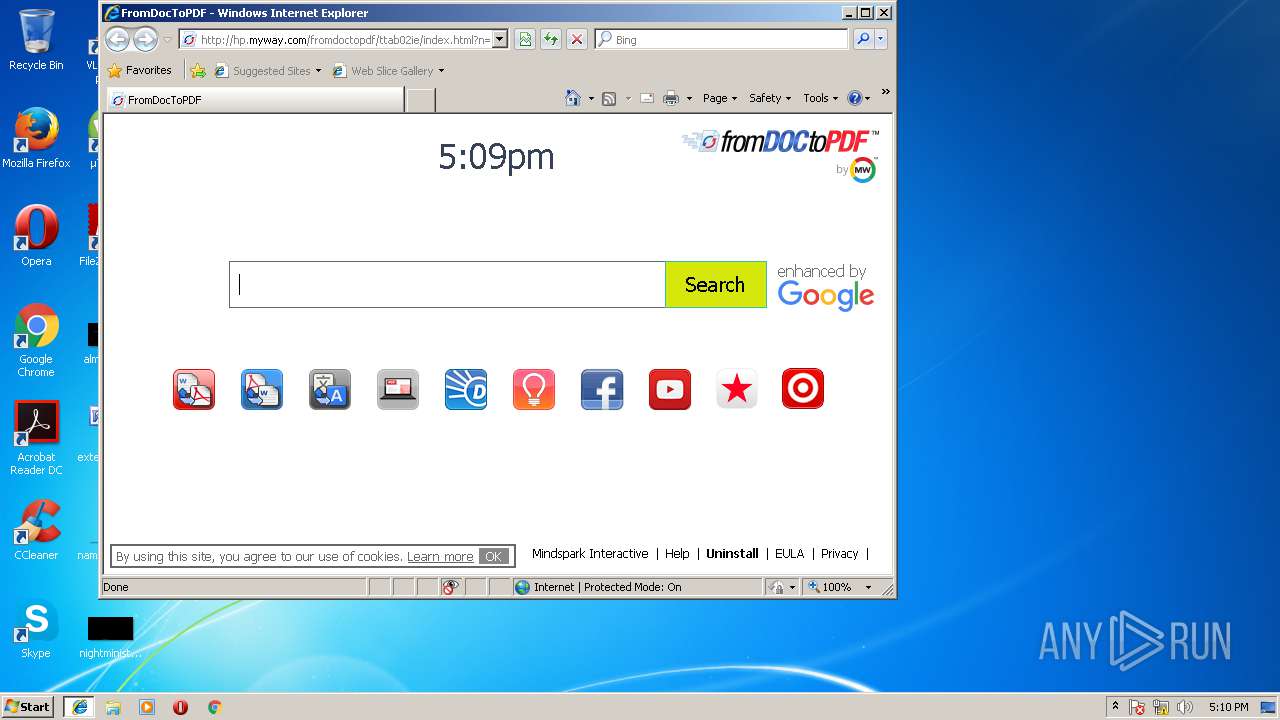
| Comments: | http://www.mindspark.com/ |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | FromDocToPDF Setup |
| FileVersion: | 2.7.1.1000 |
| InternalName: | FromDocToPDF |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | FromDocToPDF |
| ProductVersion: | 2.7.1.1000 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:44 |
| Detected languages: |
|
| Comments: | http://www.mindspark.com/ |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | FromDocToPDF Setup |
| FileVersion: | 2.7.1.1000 |
| InternalName: | FromDocToPDF |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | FromDocToPDF |
| ProductVersion: | 2.7.1.1000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000606C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45707 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94596 |
.data | 0x0000A000 | 0x0002AF98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79535 |
.ndata | 0x00035000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x00003440 | 0x00003600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.02798 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31253 | 1118 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
37
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Users\admin\AppData\Local\Temp\FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe" | C:\Users\admin\AppData\Local\Temp\FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: FromDocToPDF Setup Exit code: 0 Version: 2.7.1.1000 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1588 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1588 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
| 3844 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1588 CREDAT:203010 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 337
Read events
1 141
Write events
194
Delete events
2
Modification events
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (284) FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\FromDocToPDF_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
23
Text files
110
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\CabCED2.tmp | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\TarCED3.tmp | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\CabCEF3.tmp | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\TarCEF4.tmp | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\CabCFE0.tmp | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\Local\Temp\TarCFE1.tmp | — | |
MD5:— | SHA256:— | |||
| 1588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HB72KPVE\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 284 | FromDocToPDF.9065da2d0b6c406094a64dbbe3242676.exe.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
86
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 74.113.233.192:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-16&errorType=nsisError&errorDetails=9065da2d0b6c406094a64dbbe3242676&platform=vicinio&anxv=2.7.1.1000&anxd=2017-09-13&coid=9065da2d0b6c406094a64dbbe3242676&refPartner=^Y6^mni000^ttab02&refSub=&anxl=en-US&anxr=-2017021195&refCobrand=Y6&refCampaign=mni000&refTrack=ttab02&refCountry= | US | — | — | whitelisted |
— | — | GET | 204 | 74.113.233.192:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=InstallerInvoked&platform=vicinio&anxv=2.7.1.1000&anxd=2017-09-13&coid=9065da2d0b6c406094a64dbbe3242676&refPartner=^Y6^xpt873^TTAB02^pr&refSub=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE&anxl=en-US&anxr=-2093208097&refCobrand=Y6&refCampaign=xpt873&refTrack=TTAB02&refCountry=pr | US | — | — | whitelisted |
— | — | GET | 204 | 74.113.233.192:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-17&errorType=nsisError&errorDetails=http%3A%2F%2Fdownload%2Efromdoctopdf%2Ecom%2Finstall_pixels%2Ejhtml%3Fpartner%3D%5EY6%5Expt873%5ETTAB02%5Epr%26sub_id%3DEAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE%26coId%3D9065da2d0b6c406094a64dbbe3242676%26tbGuid%3D9F5F35FC-F38F-455C-8789-874EEB85382F%26source%3Dmsni&platform=vicinio&anxv=2.7.1.1000&anxd=2017-09-13&coid=9065da2d0b6c406094a64dbbe3242676&refPartner=^Y6^xpt873^TTAB02^pr&refSub=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE&anxl=en-US&anxr=2071889810&refCobrand=Y6&refCampaign=xpt873&refTrack=TTAB02&refCountry=pr | US | — | — | whitelisted |
— | — | GET | 204 | 74.113.233.192:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-23&errorType=nsisError&errorDetails=http%3A%2F%2Fdownload%2Efromdoctopdf%2Ecom%2Fconfig_event%2Ejhtml%3Fanxuu%3D3A03354F-0B7A-4186-99F7-FDF385616FD0%26anxa%3DCAPOne%26anxv%3D%26anxd%3D%26anxsn%3Ddfprdsndlbfe74%2Edf%2Ejabodo%2Ecom%26anxu%3Dhttp%3A%2F%2Fdownload%2Efromdoctopdf%2Ecom%2Findex%2Ejhtml%26anxl%3Den%26anxlv%3DThu%2520May%252003%252011%3A42%3A57%2520EDT%25202018%26anxrp%26anxrk%3D%26anxrm%3D%26anxrc%3D%26anxrs%3D%26anxsq%3D%26anxt%3D9F5F35FC-F38F-455C-8789-874EEB85382F%26anxp%3D%255EY6%255Expt873%255ETTAB02%255Epr%26anxi%26anxtv%26fParameter%3D000000b0%26coid%3D9065da2d0b6c406094a64dbbe3242676%26anxe%3DToolbarConfig%26anxr%3D1333631676%26anxsi%3DEAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE&platform=vicinio&anxv=2.7.1.1000&anxd=2017-09-13&coid=9065da2d0b6c406094a64dbbe3242676&refPartner=^Y6^xpt873^TTAB02^pr&refSub=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE&anxl=en-US&anxr=2052862270&refCobrand=Y6&ref | US | — | — | whitelisted |
— | — | GET | 204 | 74.113.233.187:80 | http://anx.tb.ask.com/anx.gif?anxuu=3A03354F-0B7A-4186-99F7-FDF385616FD0&anxa=CAPOne&anxv=&anxd=&anxsn=dfprdsndlbfe74.df.jabodo.com&anxu=http://download.fromdoctopdf.com/index.jhtml&anxl=en&anxlv=Thu%20May%2003%2011:42:57%20EDT%202018&anxrp&anxrk=&anxrm=&anxrc=&anxrs=&anxsq=&anxt=9F5F35FC-F38F-455C-8789-874EEB85382F&anxp=%5EY6%5Expt873%5ETTAB02%5Epr&anxi&anxtv&fParameter=000000b0&coid=9065da2d0b6c406094a64dbbe3242676&anxe=ToolbarConfig&anxr=1333631676&anxsi=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE | US | — | — | whitelisted |
— | — | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.4 Kb | whitelisted |
— | — | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
— | — | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNV5Yn2BTHKH3rQdMEVxo5OsA%3D%3D | unknown | der | 527 b | whitelisted |
— | — | GET | 200 | 74.113.235.138:80 | http://download.fromdoctopdf.com/install_pixels.jhtml?partner=^Y6^xpt873^TTAB02^pr&sub_id=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE&coId=9065da2d0b6c406094a64dbbe3242676&tbGuid=9F5F35FC-F38F-455C-8789-874EEB85382F&source=msni | IE | html | 11.9 Kb | whitelisted |
— | — | GET | 200 | 74.113.235.138:80 | http://download.fromdoctopdf.com/config_event.jhtml?anxuu=3A03354F-0B7A-4186-99F7-FDF385616FD0&anxa=CAPOne&anxv=&anxd=&anxsn=dfprdsndlbfe74.df.jabodo.com&anxu=http://download.fromdoctopdf.com/index.jhtml&anxl=en&anxlv=Thu%20May%2003%2011:42:57%20EDT%202018&anxrp&anxrk=&anxrm=&anxrc=&anxrs=&anxsq=&anxt=9F5F35FC-F38F-455C-8789-874EEB85382F&anxp=%5EY6%5Expt873%5ETTAB02%5Epr&anxi&anxtv&fParameter=000000b0&coid=9065da2d0b6c406094a64dbbe3242676&anxe=ToolbarConfig&anxr=1333631676&anxsi=EAIaIQobChMI7tH_4fDp2gIVDwuGCh2qxwi1EAEYASAAEgLY2_D_BwE | IE | html | 596 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.22.98:80 | www.googleadservices.com | Google Inc. | US | whitelisted |
— | — | 74.113.233.192:80 | anx.mindspark.com | Mindspark Interactive Network, Inc. | US | suspicious |
— | — | 74.113.235.138:443 | dp.tb.ask.com | Mindspark Interactive Network, Inc. | IE | malicious |
— | — | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
— | — | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 74.113.235.138:80 | dp.tb.ask.com | Mindspark Interactive Network, Inc. | IE | malicious |
— | — | 216.58.205.226:80 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 185.31.128.128:80 | a.rfihub.com | Rocket Fuel Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
hp.myway.com |
| whitelisted |
www.bing.com |
| whitelisted |
download.fromdoctopdf.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |