| File name: | cleaner-util.exe |
| Full analysis: | https://app.any.run/tasks/20161b4f-3f23-44e4-b12a-b0830e05d6ae |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 14:44:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 73E9796DDBB46CD8682849DAFFC10D40 |
| SHA1: | 83F518C22B9B98B29069B97F1056F8965B3C9FB7 |
| SHA256: | 1A3017C9B446CDA28B40594A806F383667ACC5102341687F64626D72478CC937 |
| SSDEEP: | 98304:CpFvk6dxzivdTflBzuLhtWsw2lCLioT4PU7MqT4PU7MIW0vIFOF8N/YhGW1NCYV8:SFWdlBzu/RN/IGINChRaPGbRfrqNKx |
MALICIOUS
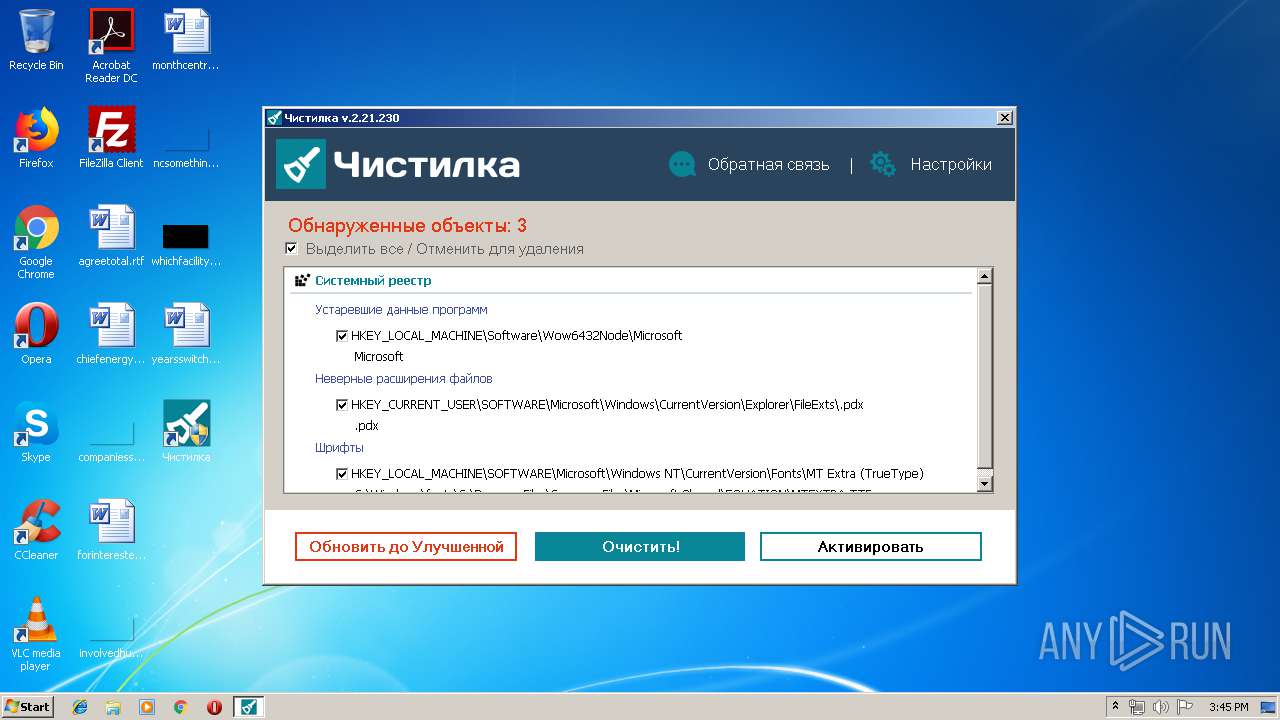
Changes settings of System certificates
- cleaner-util.exe (PID: 1244)
Loads the Task Scheduler COM API
- cleaner-util.exe (PID: 1244)
Loads dropped or rewritten executable
- cleaner-util.exe (PID: 1244)
Disables Windows Defender
- cleaner-util.exe (PID: 1244)
Changes Windows auto-update feature
- cleaner-util.exe (PID: 1244)
SUSPICIOUS
Adds / modifies Windows certificates
- cleaner-util.exe (PID: 1244)
Low-level read access rights to disk partition
- cleaner-util.exe (PID: 1244)
Creates files in the Windows directory
- cleaner-util.exe (PID: 1244)
Creates files in the program directory
- cleaner-util.exe (PID: 1244)
Creates a software uninstall entry
- cleaner-util.exe (PID: 1244)
Reads internet explorer settings
- cleaner-util.exe (PID: 1244)
Executable content was dropped or overwritten
- cleaner-util.exe (PID: 1244)
Reads the cookies of Google Chrome
- cleaner-util.exe (PID: 1244)
Reads the cookies of Mozilla Firefox
- cleaner-util.exe (PID: 1244)
Creates files in the user directory
- cleaner-util.exe (PID: 1244)
Reads Internet Cache Settings
- cleaner-util.exe (PID: 1244)
Reads Microsoft Outlook installation path
- cleaner-util.exe (PID: 1244)
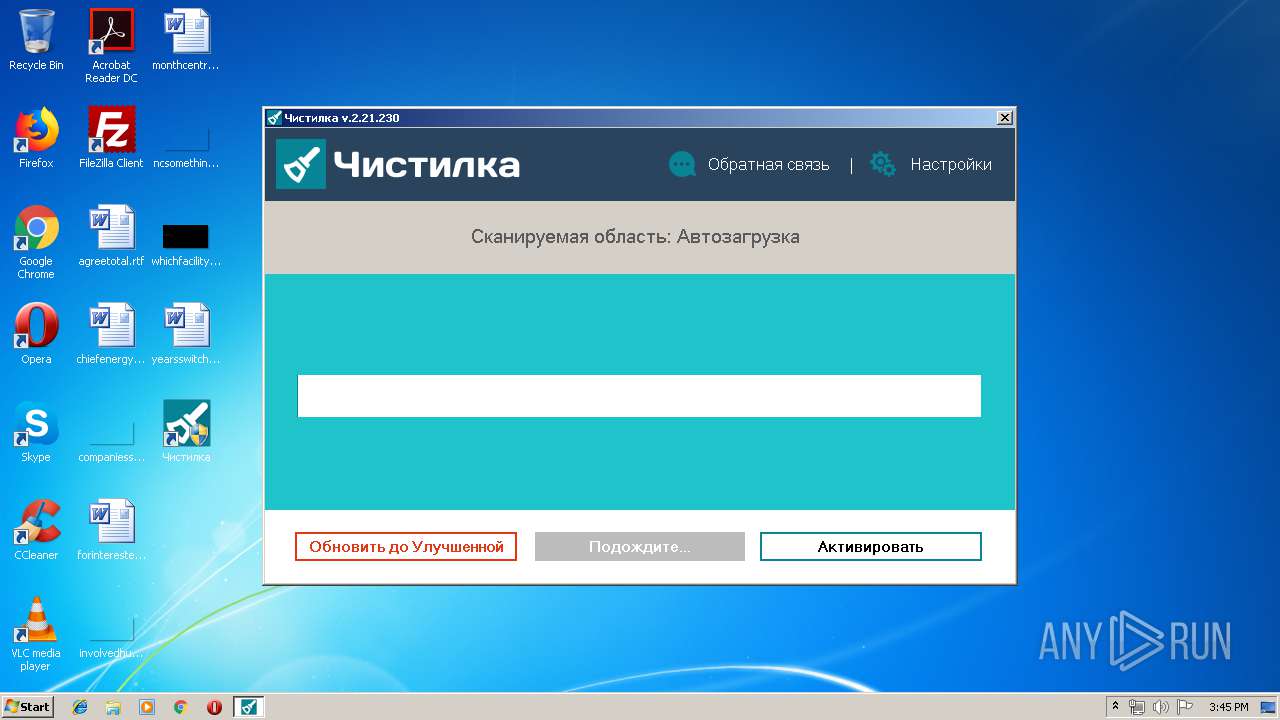
Searches for installed software
- cleaner-util.exe (PID: 1244)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:13 16:14:22+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 2609152 |
| InitializedDataSize: | 8143872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ac14b |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
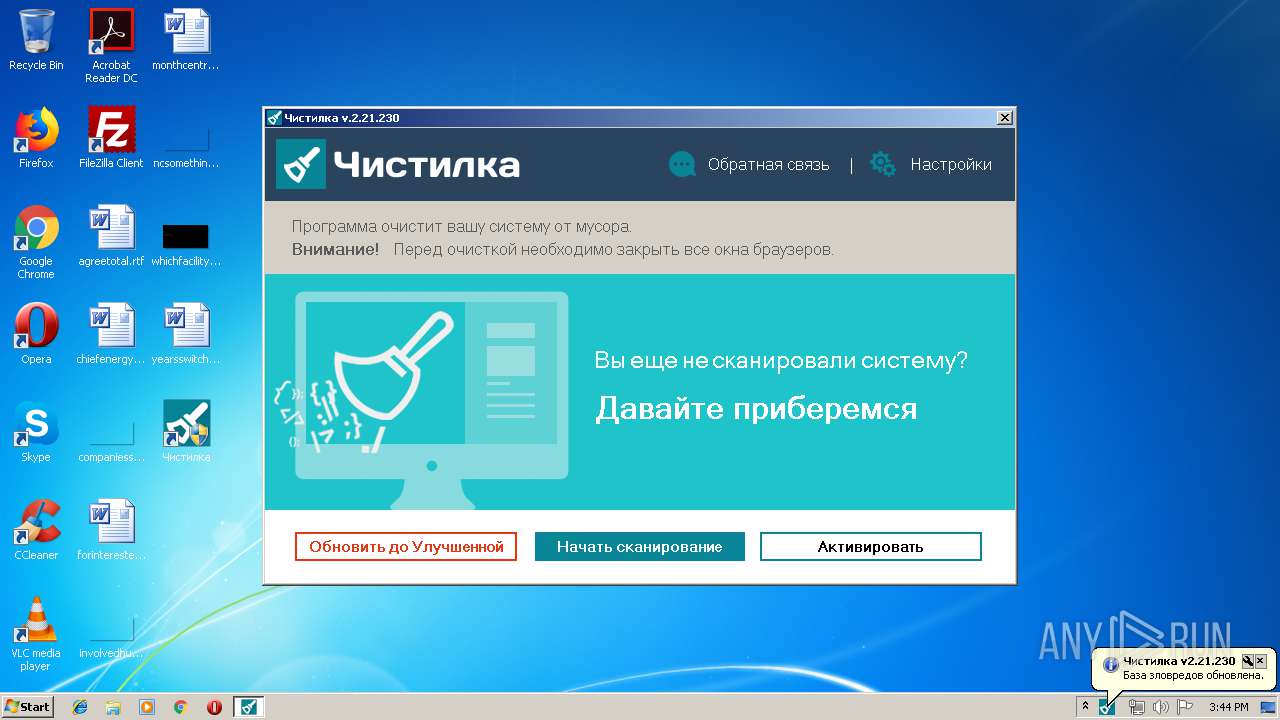
| FileVersionNumber: | 2.21.230.0 |
| ProductVersionNumber: | 2.21.230.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
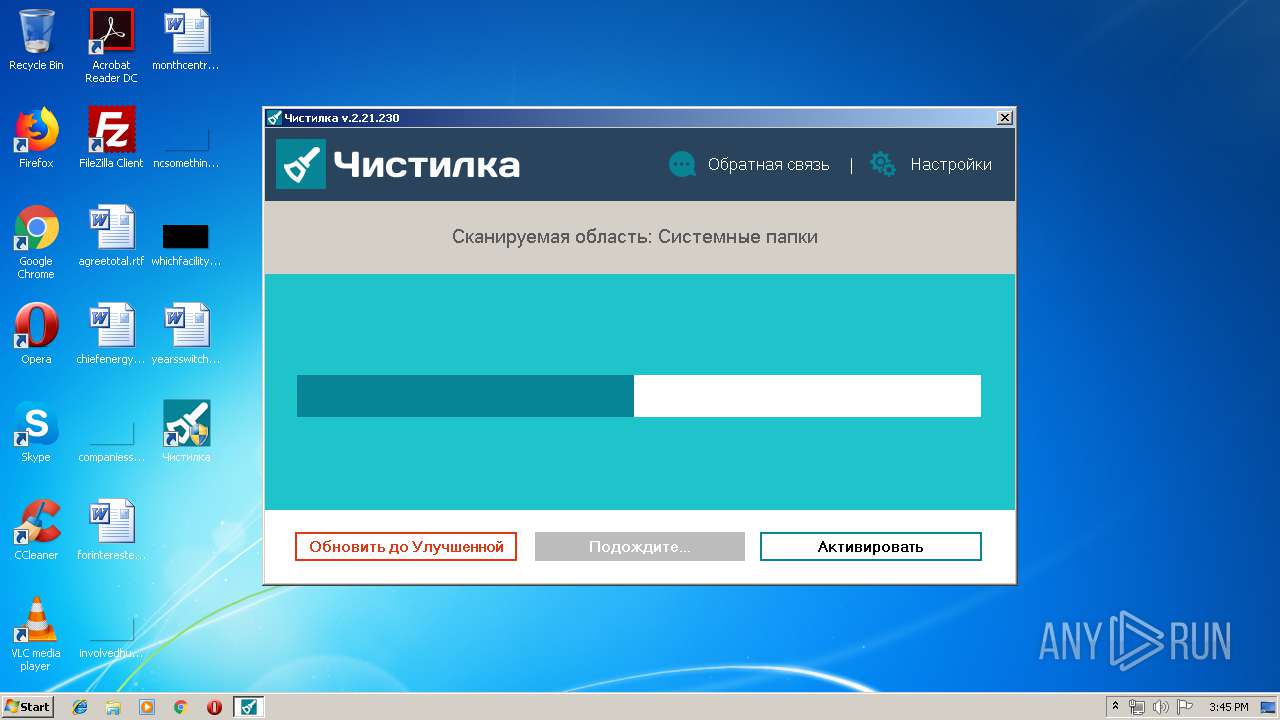
| FileDescription: | Программное обеспечение для содержания компьютера в чистоте. |
| FileVersion: | 2.21.230 |
| InternalName: | Чистилка.exe |
| LegalCopyright: | - |
| LegalTrademarks1: | - |
| LegalTrademarks2: | - |
| OriginalFileName: | Чистилка.exe |
| ProductName: | Чистилка |
| ProductVersion: | 2.21.230 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Aug-2019 14:14:22 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | Программное обеспечение для содержания компьютера в чистоте. |
| FileVersion: | 2.21.230 |
| InternalName: | Чистилка.exe |
| LegalCopyright: | - |
| LegalTrademarks1: | - |
| LegalTrademarks2: | - |
| OriginalFilename: | Чистилка.exe |
| ProductName: | Чистилка |
| ProductVersion: | 2.21.230 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000138 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Aug-2019 14:14:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0027CFD3 | 0x0027D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63074 |
.rdata | 0x0027E000 | 0x001CE390 | 0x001CE400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.24469 |
.data | 0x0044D000 | 0x000190C4 | 0x00013E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.47096 |
.rsrc | 0x00467000 | 0x005C0788 | 0x005C0800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.78766 |
.reloc | 0x00A28000 | 0x0002184C | 0x00021A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59693 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39289 | 1431 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.86832 | 67624 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 4.07244 | 16936 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 4.12089 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 4.62272 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
6 | 5.04001 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
9 | 3.16517 | 120 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 2.51883 | 72 | Latin 1 / Western European | Russian - Russia | RT_STRING |
12 | 2.69688 | 74 | Latin 1 / Western European | Russian - Russia | RT_STRING |
70 | 3.50833 | 234 | Latin 1 / Western European | Russian - Russia | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
RPCRT4.dll |
SHELL32.dll |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Users\admin\AppData\Local\Temp\cleaner-util.exe" | C:\Users\admin\AppData\Local\Temp\cleaner-util.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3340 | "C:\Users\admin\AppData\Local\Temp\cleaner-util.exe" | C:\Users\admin\AppData\Local\Temp\cleaner-util.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 138
Read events
974
Write events
145
Delete events
19
Modification events
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\chst |
| Operation: | write | Name: | uid |
Value: fe5f2943-2e14-412b-bfe7-eaecd221612a-a18e5c95eab57f110e4ba9b3eca4eda773c326c0 | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\chst |
| Operation: | write | Name: | prt |
Value: | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\chst |
| Operation: | write | Name: | hwid |
Value: 048ea7dadfda4e2e7e4c5da96a4934a6d6c67b7a | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\chst |
| Operation: | write | Name: | v |
Value: 2.21.230 | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\33E4E80807204C2B6182A3A14B591ACD25B5F0DB |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000033E4E80807204C2B6182A3A14B591ACD25B5F0DB1400000001000000140000008D8C5EC454AD8AE177E99BF99B05E1B8018D61E1040000000100000010000000ADAB5C4DF031FB9299F71ADA7E18F6130F00000001000000300000008B612B2190A95B28B866B9BE5D0B95F368C17534AB1DA61A42DFB32766F9AE2908FE6BFD1669BE140EDDAF0D33E95235190000000100000010000000FC741B3B78CFB31E075744FE5D0EEB96180000000100000010000000EA6089055218053DD01E37E1D806EEDF20000000010000001706000030820613308203FBA00302010202107D5B5126B476BA11DB74160BBC530DA7300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3138313130323030303030305A170D3330313233313233353935395A30818F310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F726431183016060355040A130F5365637469676F204C696D69746564313730350603550403132E5365637469676F2052534120446F6D61696E2056616C69646174696F6E205365637572652053657276657220434130820122300D06092A864886F70D01010105000382010F003082010A0282010100D67333D6D73C20D000D21745B8D63E07A23FC741EE3230C9B06CFDF49FCB12980F2D3F8D4D010C820F177F622EE9B84879FB16834EADD7322593B707BFB9503FA94CC3402AE939FFD981CA1F163241DA8026B9237A87201EE3FF209A3C95446F8775069040B4329316091008233ED2DD870F6F5D51146A0A69C54F017269CFD3934C6D04A0A31B827EB19AB9EDC59EC537789F9A0834FB562E58C4090E06645BBC37DCF19F2868A856B092A35C9FBB8898081B241DAB3085AEAFB02E9E7A9DC1C0421CE202F0EAE04AD2EF900EB4C14016F06F85424A64F7A430A0FEBF2EA3275A8E8B58B8ADC319178463ED6F56FD83CB6034C474BEE69DDBE1E4E5CA0C5F150203010001A382016E3082016A301F0603551D230418301680145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB301D0603551D0E041604148D8C5EC454AD8AE177E99BF99B05E1B8018D61E1300E0603551D0F0101FF04040302018630120603551D130101FF040830060101FF020100301D0603551D250416301406082B0601050507030106082B06010505070302301B0603551D200414301230060604551D20003008060667810C01020130500603551D1F044930473045A043A041863F687474703A2F2F63726C2E7573657274727573742E636F6D2F55534552547275737452534143657274696669636174696F6E417574686F726974792E63726C307606082B06010505070101046A3068303F06082B060105050730028633687474703A2F2F6372742E7573657274727573742E636F6D2F555345525472757374525341416464547275737443412E637274302506082B060105050730018619687474703A2F2F6F6373702E7573657274727573742E636F6D300D06092A864886F70D01010C0500038202010032BF61BD0E48C34FC7BA474DF89C781901DC131D806FFCC370B4529A31339A5752FB319E6BA4EF54AA898D401768F811107CD2CAB1F15586C7EEB3369186F63951BF46BF0FA0BAB4F77E49C42A36179EE468397AAF944E566FB27B3BBF0A86BDCDC5771C03B838B1A21F5F7EDB8ADC4648B6680ACFB2B5B4E234E467A93866095ED2B8FC9D283A174027C2724E29FD213C7CCF13FB962CC53144FD13EDD59BA96968777CEEE1FFA4F93638085339A284349C19F3BE0EACD52437EB23A878D0D3E7EF924764623922EFC6F711BE2285C6664424268E10328DC893AE079E833E2FD9F9F5468E63BEC1E6B4DCA6CD21A8860A95D92E85261AFDFCB1B657426D95D133F6391406824138F58F58DC805BA4D57D9578FDA79BFFFDC5A869AB26E7A7A405875BA9B7B8A3200B97A94585DDB38BE589378E290DFC0617F638400E42E41206FB7BF3C6116862DFE398F413D8154F8BB169D91060BC642AEA31B7E4B5A33A149B26E30B7BFD028EB699C138975936F6A874A286B65EEBC664EACFA0A3F96E9EBA2D11B6869808582DC9AC2564F25E75B438C1AE7F5A4683EA51CAB6F19911356BA56A7BC600B0E7F8BE64B2ADC8C2F1ACE351EAA493E079C8E18140C90A5BE1123CC1602AE397C08942CA94CF46981269BB98D0C2D30D724B476EE593C43228638743E4B0323E0AD34BBF239B1429412B9A041F932DF1C739483CAD5A127F | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\CA\Certificates\EAB040689A0D805B5D6FD654FC168CFF00B78BE3 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000EAB040689A0D805B5D6FD654FC168CFF00B78BE31400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB040000000100000010000000DB78CBD190952735D940BC80AC2432C00F0000000100000030000000435FE6564241D6B3828352EF9BE443D511C21F0AFB325C4038A5820F00D87774A8EF2193DDAAE065B2572FAF2BF0EE63190000000100000010000000EA6089055218053DD01E37E1D806EEDF18000000010000001000000045ED9BBC5E43D3B9ECD63C060DB78E5C20000000010000007B050000308205773082045FA003020102021013EA28705BF4ECED0C36630980614336300D06092A864886F70D01010C0500306F310B300906035504061302534531143012060355040A130B416464547275737420414231263024060355040B131D41646454727573742045787465726E616C20545450204E6574776F726B312230200603550403131941646454727573742045787465726E616C20434120526F6F74301E170D3030303533303130343833385A170D3230303533303130343833385A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A381F43081F1301F0603551D23041830168014ADBD987A34B426F7FAC42654EF03BDE024CB541A301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF30110603551D20040A300830060604551D200030440603551D1F043D303B3039A037A0358633687474703A2F2F63726C2E7573657274727573742E636F6D2F416464547275737445787465726E616C4341526F6F742E63726C303506082B0601050507010104293027302506082B060105050730018619687474703A2F2F6F6373702E7573657274727573742E636F6D300D06092A864886F70D01010C050003820101009365F63783950F5EC3821C1FD677E73C8AC0AA09F0E90B26F1E0C26A75A1C779C9B95260C829120EF0AD03D609C476DFE5A68195A746DA8257A99592C5B68F03226C3377C17B32176E07CE5A14413A05241BF614063BA825240EBBCC2A75DDB970413F7CD0633621071F46FF60A491E167BCDE1F7E1914C9636791EA67076BB48F8BC06E437DC3A1806CB21EBC53857DDC90A1A4BC2DEF4672573505BFBB46BB6E6D3799B6FF239291C66E40F88F2956EA5FD55F1453ACF04F61EAF722CCA7560BE2B8341F26D97B1905683FBA3CD43806A2D3E68F0EE3B4716D4042C584B440952BF465A04879F61D8163969D4F75E0F87CE48EA9D1F2AD8AB38CC721CDC2EF | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\DAC9024F54D8F6DF94935FB1732638CA6AD77C13 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000410352DC0FF7501B16F0028EBA6F45C50F00000001000000140000005BCAA1C2780F0BCB5A90770451D96F38963F012D090000000100000042000000304006082B0601050507030406082B0601050507030106082B0601050507030206082B06010505070308060A2B0601040182370A0304060A2B0601040182370A030C6200000001000000200000000687260331A72403D909F105E69BCF0D32E1BD2493FFC6D9206D11BCD67707390B000000010000001E000000440053005400200052006F006F0074002000430041002000580033000000140000000100000014000000C4A7B1A47B2C71FADBE14B9075FFC415608589101D00000001000000100000004558D512EECB27464920897DE7B66053030000000100000014000000DAC9024F54D8F6DF94935FB1732638CA6AD77C131900000001000000100000006CF252FEC3E8F20996DE5D4DD9AEF42420000000010000004E0300003082034A30820232A003020102021044AFB080D6A327BA893039862EF8406B300D06092A864886F70D0101050500303F31243022060355040A131B4469676974616C205369676E617475726520547275737420436F2E311730150603550403130E44535420526F6F74204341205833301E170D3030303933303231313231395A170D3231303933303134303131355A303F31243022060355040A131B4469676974616C205369676E617475726520547275737420436F2E311730150603550403130E44535420526F6F7420434120583330820122300D06092A864886F70D01010105000382010F003082010A0282010100DFAFE99750088357B4CC6265F69082ECC7D32C6B30CA5BECD9C37DC740C118148BE0E83376492AE33F214993AC4E0EAF3E48CB65EEFCD3210F65D22AD9328F8CE5F777B0127BB595C089A3A9BAED732E7A0C063283A27E8A1430CD11A0E12A38B9790A31FD50BD8065DFB7516383C8E28861EA4B6181EC526BB9A2E24B1A289F48A39E0CDA098E3E172E1EDD20DF5BC62A8AAB2EBD70ADC50B1A25907472C57B6AAB34D63089FFE568137B540BC8D6AEEC5A9C921E3D64B38CC6DFBFC94170EC1672D526EC38553943D0FCFD185C40F197EBD59A9B8D1DBADA25B9C6D8DFC115023AABDA6EF13E2EF55C089C3CD68369E4109B192AB62957E3E53D9B9FF0025D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E04160414C4A7B1A47B2C71FADBE14B9075FFC41560858910300D06092A864886F70D01010505000382010100A31A2C9B17005CA91EEE2866373ABF83C73F4BC309A095205DE3D95944D23E0D3EBD8A4BA0741FCE10829C741A1D7E981ADDCB134BB32044E491E9CCFC7DA5DB6AE5FEE6FDE04EDDB7003AB57049AFF2E5EB02F1D1028B19CB943A5E48C4181E58195F1E025AF00CF1B1ADA9DC59868B6EE991F586CAFAB96633AA595BCEE2A7167347CB2BCC99B03748CFE3564BF5CF0F0C723287C6F044BB53726D43F526489A5267B758ABFE67767178DB0DA256141339243185A2A8025A3047E1DD5007BC02099000EB6463609B16BC88C912E6D27D918BF93D328D65B4E97CB15776EAC5B62839BF15651CC8F677966A0A8D770BD8910B048E07DB29B60AEE9D82353510 | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Proxima Nova Semibold (TrueType) |
Value: pns.ttf | |||
| (PID) Process: | (1244) cleaner-util.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Чистилка |
| Operation: | write | Name: | Publisher |
Value: Чистилка | |||
Executable files
2
Suspicious files
6
Text files
25
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cookies-journal | — | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\30D802E0E248FEE17AAF4A62594CC75A | binary | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E0968A1E3A40D2582E7FD463BAEB59CD | binary | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E0968A1E3A40D2582E7FD463BAEB59CD | der | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cookies | sqlite | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\Users\Public\Desktop\Чистилка.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Чистилка\Чистилка Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\ProgramData\Чистилка\settings.json | binary | |
MD5:— | SHA256:— | |||
| 1244 | cleaner-util.exe | C:\ProgramData\Чистилка\Чистилка.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
18
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1244 | cleaner-util.exe | GET | 301 | 62.109.11.221:80 | http://chistilka.com/ | RU | html | 332 b | unknown |
1244 | cleaner-util.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
1244 | cleaner-util.exe | GET | 200 | 140.82.35.84:80 | http://140.82.35.84/?hwid=6aab97bbec0aedef4de3d798737c0c8b1249f454&lastError=configError&parter=&uid=fe5f2943-2e14-412b-bfe7-eaecd221612a-a18e5c95eab57f110e4ba9b3eca4eda773c326c0&version=2.21.230 | US | text | 139 b | malicious |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
1244 | cleaner-util.exe | GET | 200 | 140.82.35.84:80 | http://140.82.35.84/?hwid=6aab97bbec0aedef4de3d798737c0c8b1249f454&lastError=configError&parter=&uid=fe5f2943-2e14-412b-bfe7-eaecd221612a-a18e5c95eab57f110e4ba9b3eca4eda773c326c0&version=2.21.230 | US | text | 139 b | malicious |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
1244 | cleaner-util.exe | POST | 200 | 54.213.214.53:80 | http://api.amplitude.com/httpapi | US | text | 7 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1244 | cleaner-util.exe | 54.213.214.53:80 | api.amplitude.com | Amazon.com, Inc. | US | unknown |
1244 | cleaner-util.exe | 62.109.11.221:80 | chistilka.com | JSC ISPsystem | RU | unknown |
1244 | cleaner-util.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
1244 | cleaner-util.exe | 62.109.11.221:443 | chistilka.com | JSC ISPsystem | RU | unknown |
1244 | cleaner-util.exe | 172.217.22.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
1244 | cleaner-util.exe | 62.109.13.130:443 | chistilka.ru | JSC ISPsystem | RU | malicious |
1244 | cleaner-util.exe | 54.37.81.78:443 | stat2.chistilka.com | OVH SAS | FR | malicious |
1244 | cleaner-util.exe | 5.135.140.26:443 | update.chistilka.com | OVH SAS | FR | suspicious |
1244 | cleaner-util.exe | 140.82.35.84:80 | — | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chistilka.com |
| unknown |
api.amplitude.com |
| whitelisted |
crt.sectigo.com |
| whitelisted |
crt.usertrust.com |
| whitelisted |
stat2.chistilka.com |
| malicious |
www.google-analytics.com |
| whitelisted |
chistilka.ru |
| malicious |
update.chistilka.com |
| suspicious |
pay.chistilka.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
cleaner-util.exe | [2019-08-13 15:44:46] M Log.cpp:110 Logging to C:\ProgramData\????????\logs\TKiller-2-2019-08-13-15-44-46.log
|
cleaner-util.exe | [2019-08-13 15:44:46] M main.cpp:17 App started, version 2.21.230, build type 'UTIL', pid 1244, command line '"C:\Users\admin\AppData\Local\Temp\cleaner-util.exe" '
|
cleaner-util.exe | [2019-08-13 15:44:46] M SystemInfo.cpp:60 OS: Windows 7 (6.1-32)
|
cleaner-util.exe | [2019-08-13 15:44:46] M RegistryDataStorage.cpp:14 Creating data storage for SID: S-1-5-21-1302019708-1500728564-335382590-1000
|
cleaner-util.exe | [2019-08-13 15:44:46] M Registry.cpp:93 REGF S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\chst
|
cleaner-util.exe | [2019-08-13 15:44:46] M Registry.cpp:93 REGF S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\chst_installer
|
cleaner-util.exe | [2019-08-13 15:44:46] M PersistentData.cpp:38 generateUid()
|
cleaner-util.exe | [2019-08-13 15:44:46] M PersistentData.cpp:59 generateUid(), uid fe5f2943-2e14-412b-bfe7-eaecd221612a-a18e5c95eab57f110e4ba9b3eca4eda773c326c0
|
cleaner-util.exe | [2019-08-13 15:44:46] E EmbeddedSettings.cpp:196 Failed to find blob begin pattern
|
cleaner-util.exe | [2019-08-13 15:44:46] M Registry.cpp:93 REGF S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\chst_installer
|