| File name: | ch44.ps1 |
| Full analysis: | https://app.any.run/tasks/ae7003c4-1a21-4fd1-a733-029bc083d47d |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2021, 11:07:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/plain |
| File info: | UTF-8 Unicode (with BOM) text, with very long lines, with no line terminators |
| MD5: | 8FD4A2515402107BB836D97FDA8F43DE |
| SHA1: | 62F17B7B8E2DE5709C97A8CC0FD87A66861668DE |
| SHA256: | 1A255F9DA1756D65B3CA710061A484BE2B8181C96561D298C3082A17A6783303 |
| SSDEEP: | 768:KcOZrOxLo3jgplYD2j9P/VsZ3kxP5gG8WU9KUYRiPFocJhw1cH6dRcWkiYD:KcOZrOo3jgplUeP/VsZ3URgGjU9l5FoE |
MALICIOUS
No malicious indicators.SUSPICIOUS
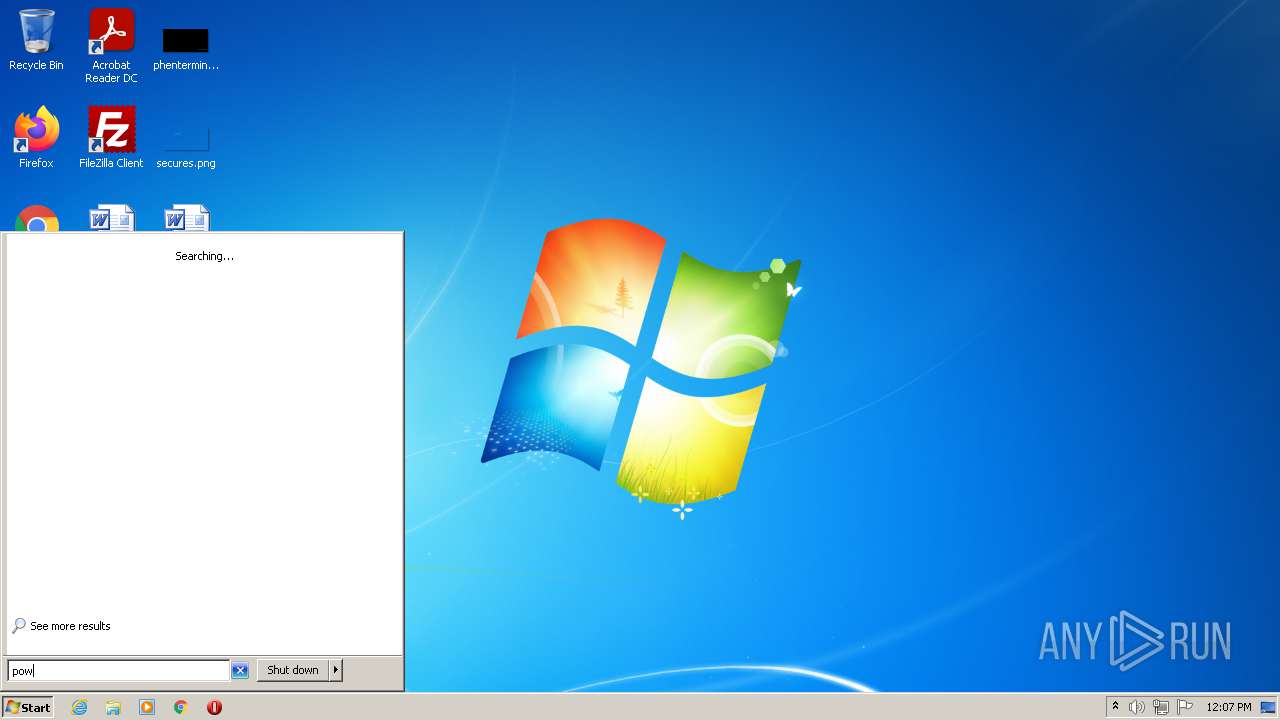
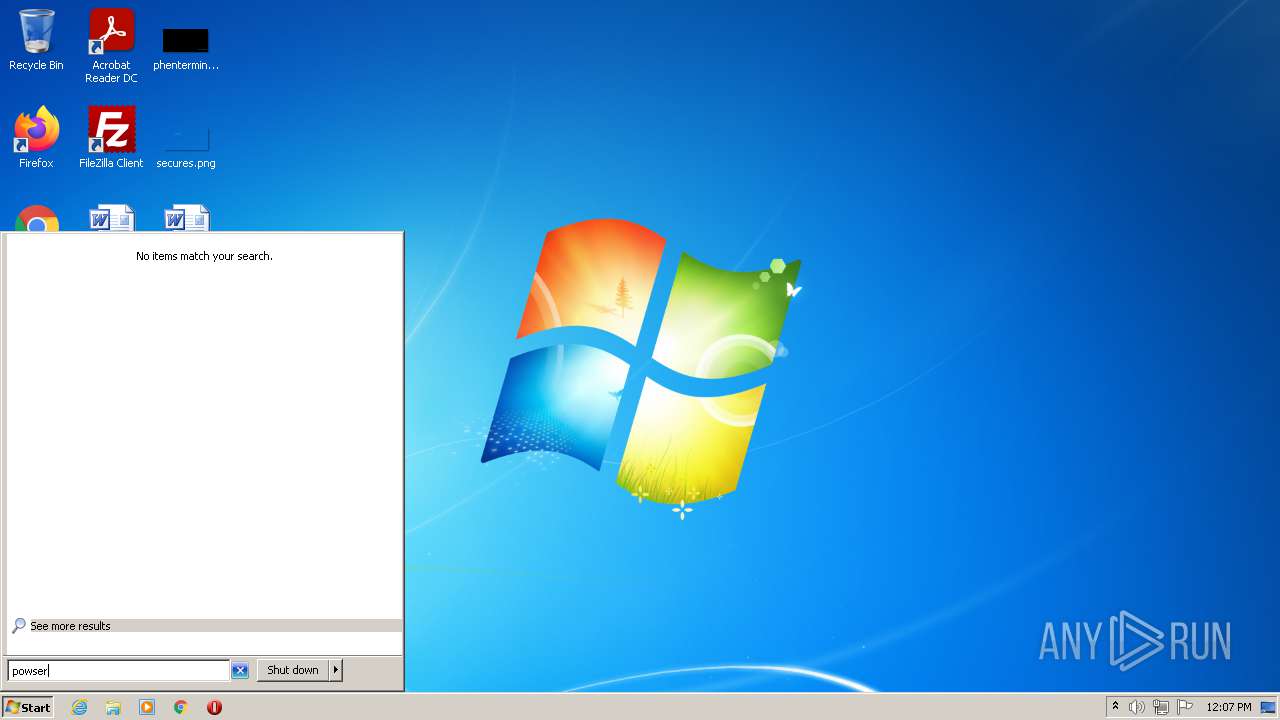
Checks supported languages
- powershell.exe (PID: 3732)
- powershell.exe (PID: 2064)
Reads the date of Windows installation
- powershell.exe (PID: 2064)
- powershell.exe (PID: 3732)
Reads the computer name
- powershell.exe (PID: 2064)
- powershell.exe (PID: 3732)
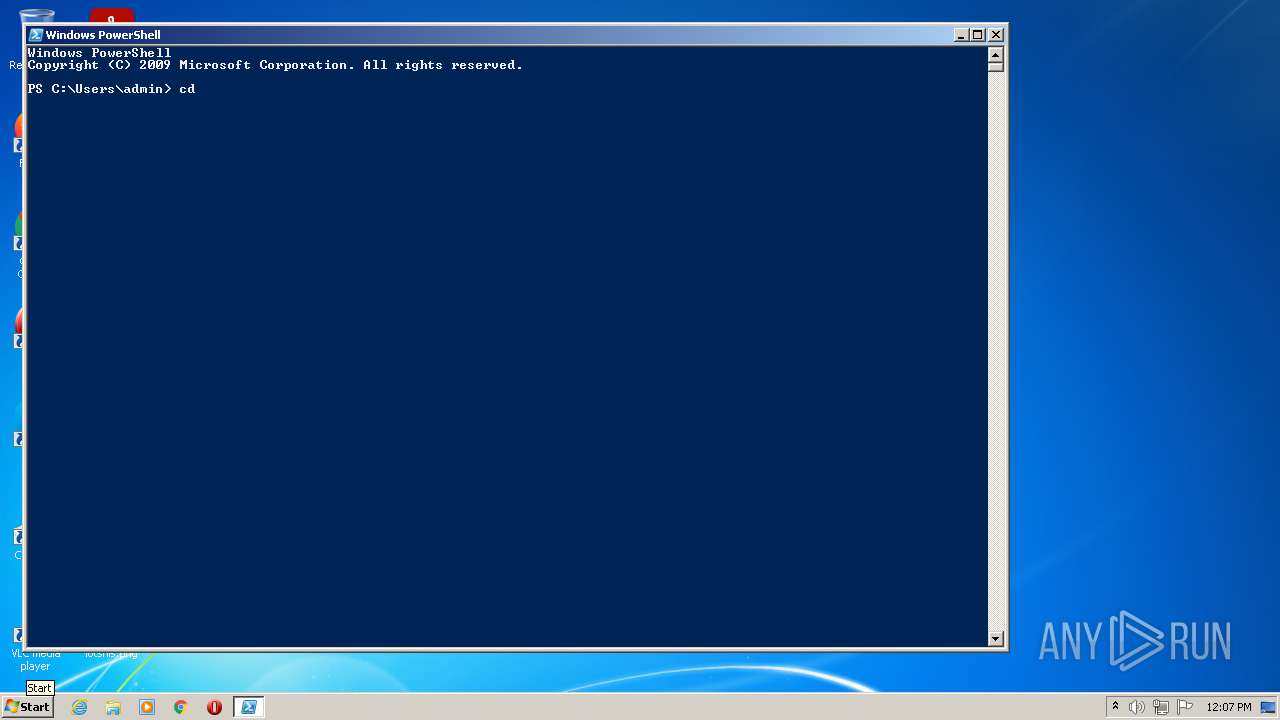
PowerShell script executed
- powershell.exe (PID: 2064)
- powershell.exe (PID: 3732)
Creates files in the user directory
- powershell.exe (PID: 3732)
- powershell.exe (PID: 2064)
INFO
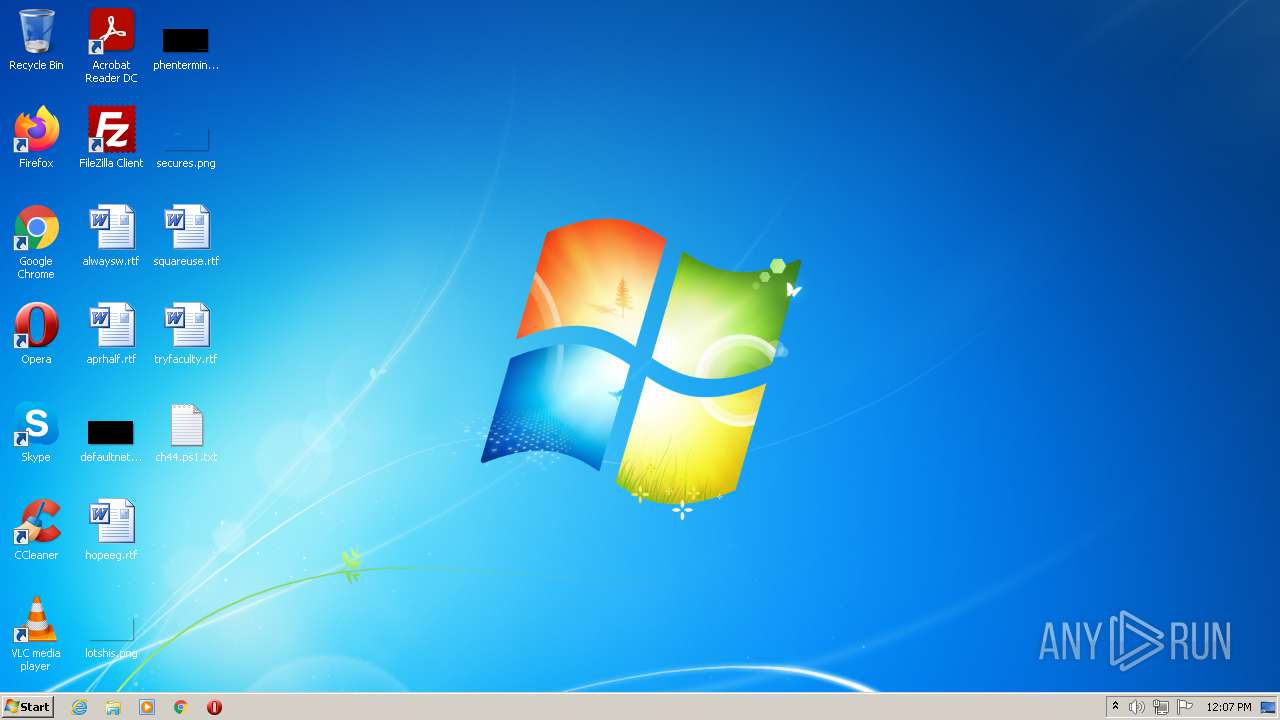
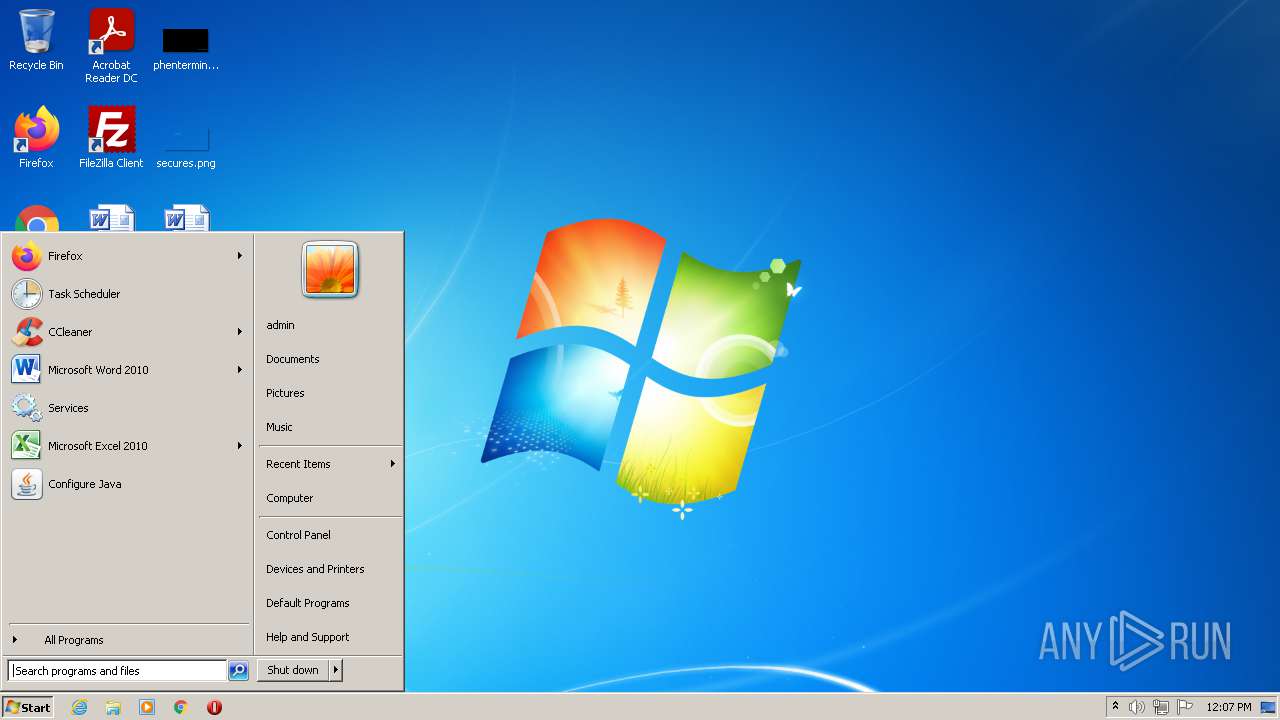
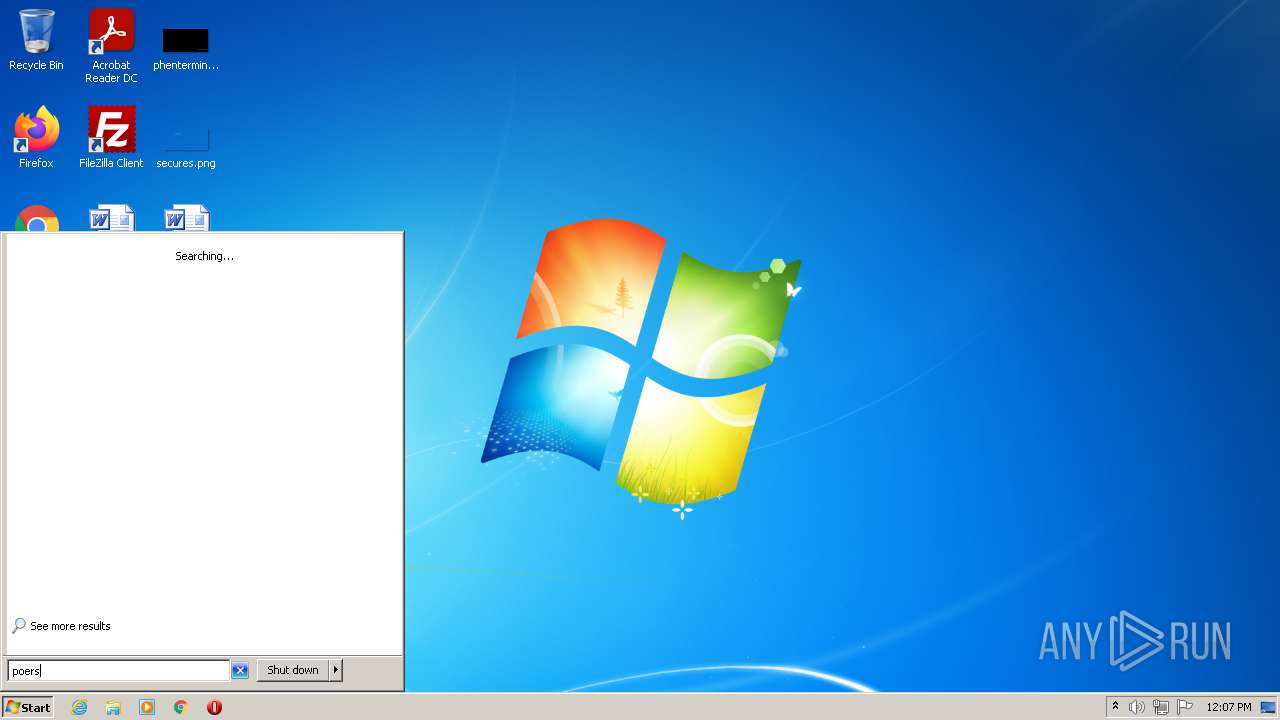
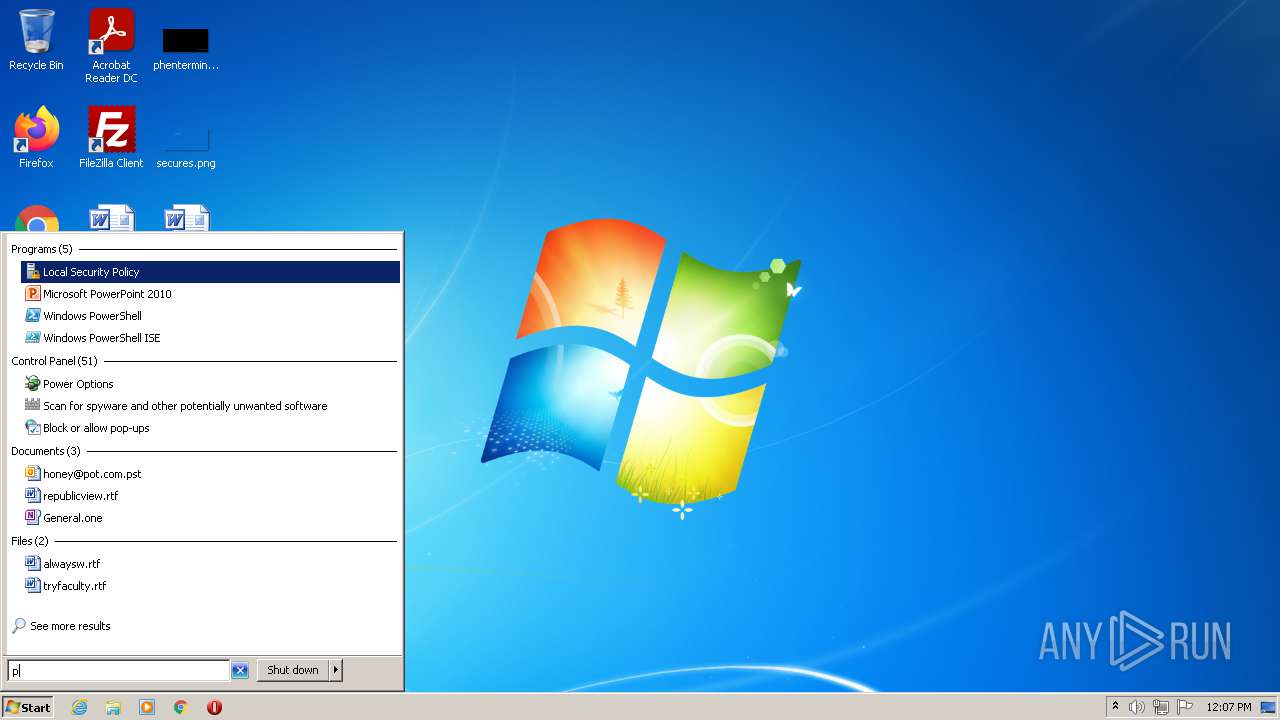
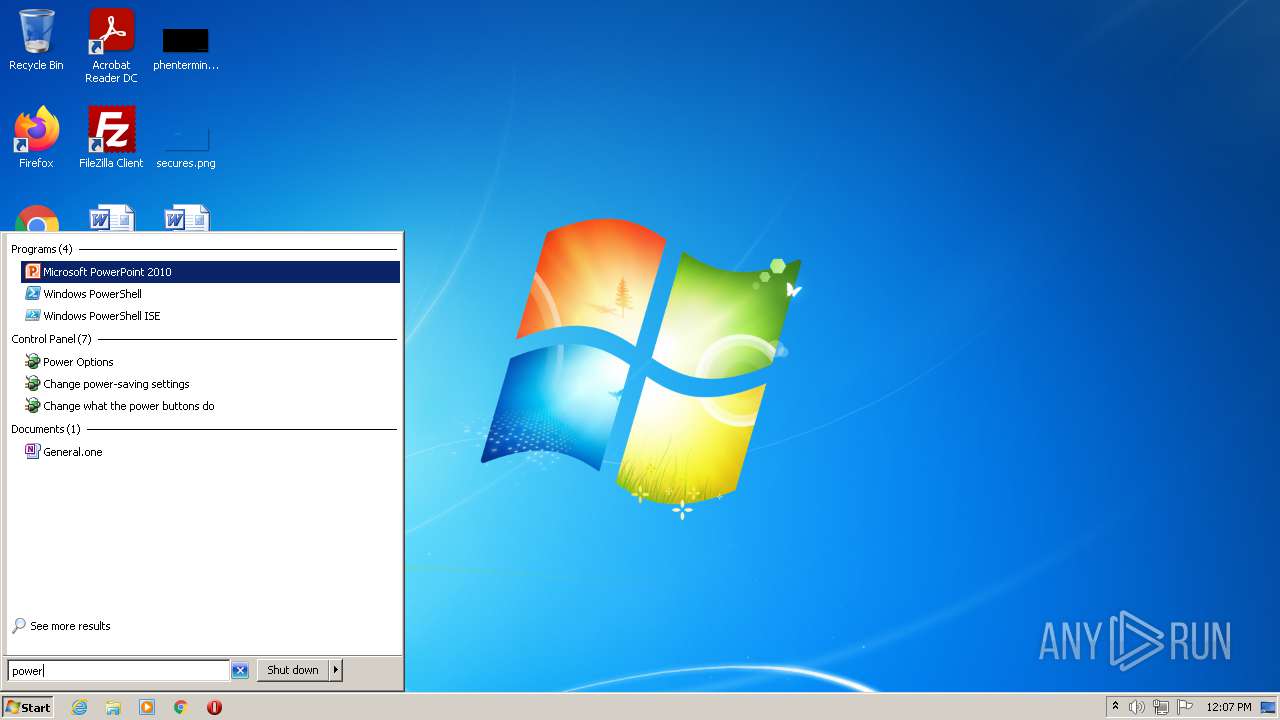
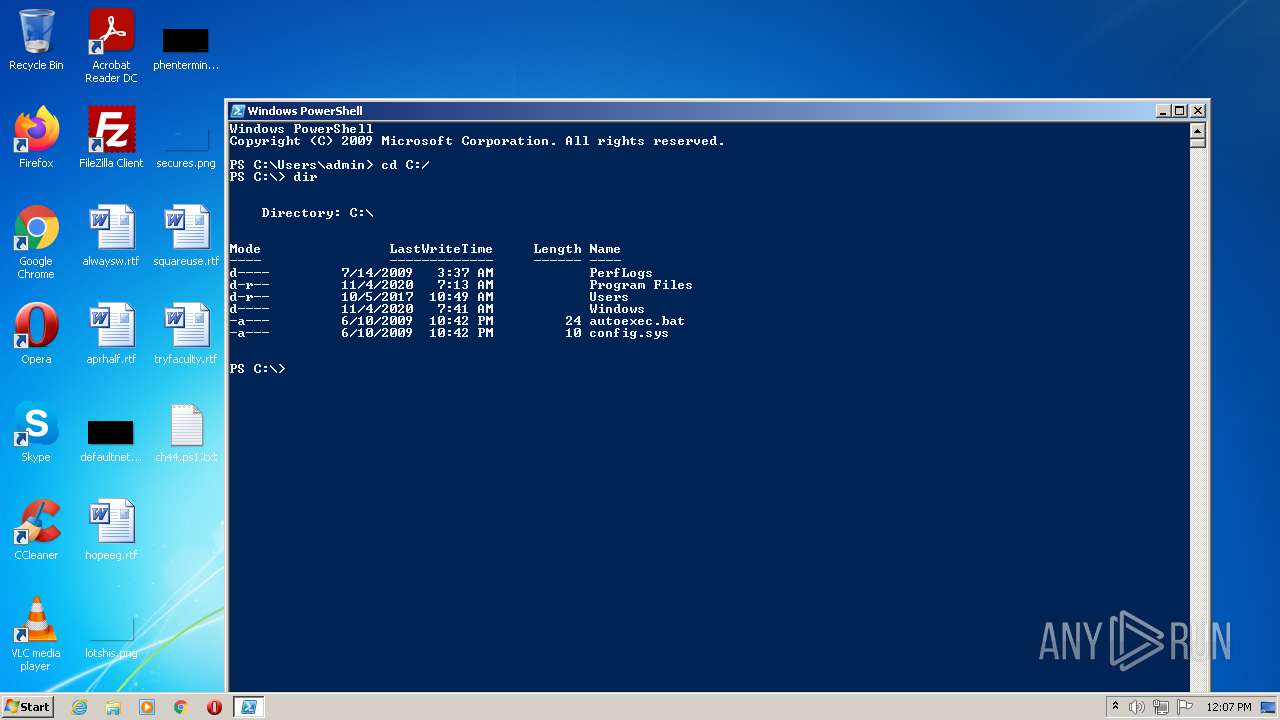
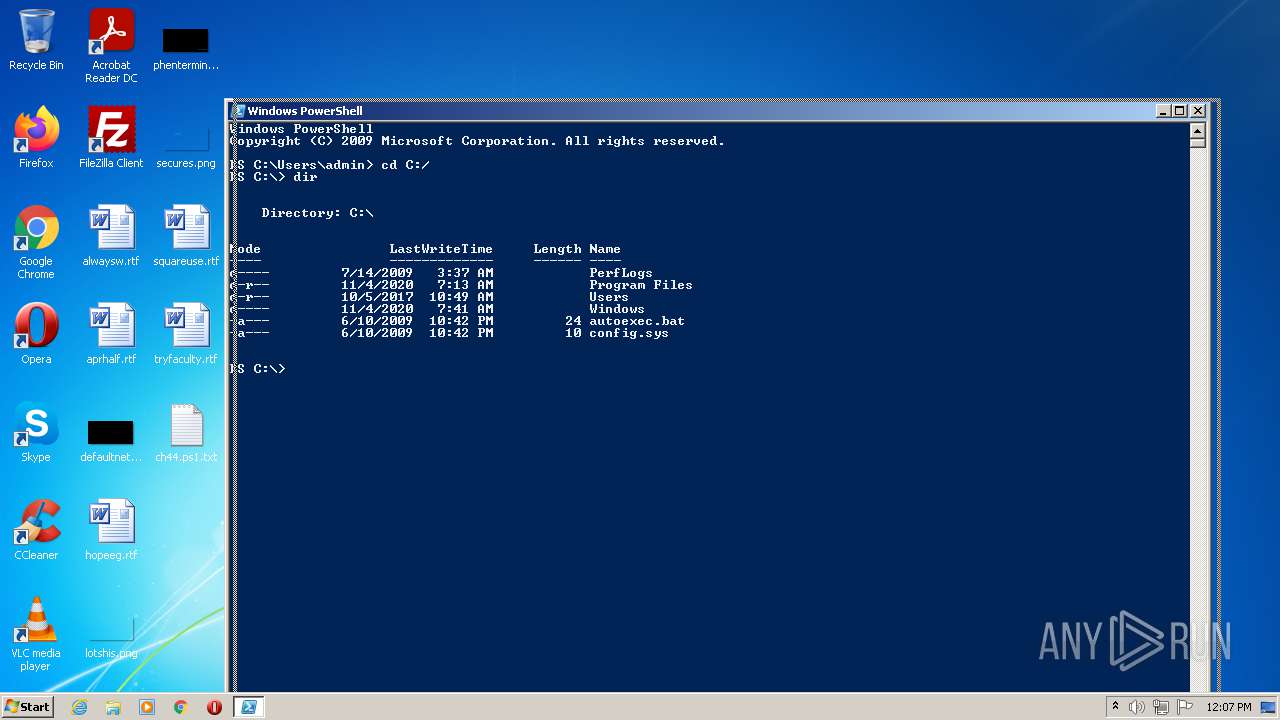
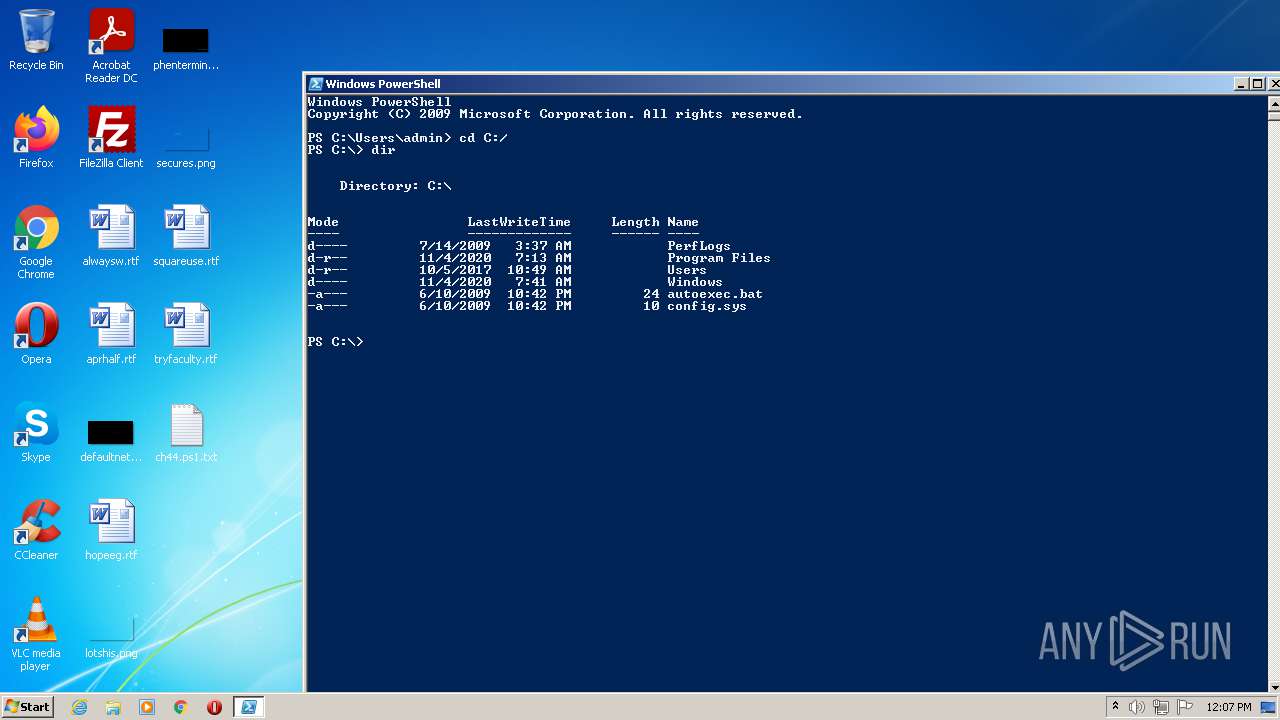
Manual execution by user
- powershell.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" ch44.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3732 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 861
Read events
1 754
Write events
107
Delete events
0
Modification events
| (PID) Process: | (2064) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3732) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19749a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF193714.TMP | binary | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9L23QQ6KW8YXSLYKBOR4.temp | binary | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3GQL4WM2Z3WAN7H1NLYE.temp | binary | |
MD5:— | SHA256:— | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report