| URL: | Https://docs.google.com/uc?export=download&id=1NdXGlf5wqGzd9ZsE-q6ZVEBlBpdf77Tj |
| Full analysis: | https://app.any.run/tasks/6322ba90-d376-46bd-bbe2-4bd99dcbc7e2 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 17:06:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FB2FE8874EFCA12893A62FF5C0F5C1F0 |
| SHA1: | A57880E69D1AD298408D96B53B72D22CFEA121BA |
| SHA256: | 1A210FC0496331773FA6CE4C1398E7F0C96C18FC25365A8B98BB562B568EC5A0 |
| SSDEEP: | 3:nnBP3u2NAaBrC2rBMceg9/zkYCP:nBm2BB+2r3/HCP |
MALICIOUS
Application was dropped or rewritten from another process
- D.exe (PID: 872)
- D.exe (PID: 3444)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 2320)
- cmd.exe (PID: 2888)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 3064)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 2676)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 3892)
Executes PowerShell scripts
- cmd.exe (PID: 3136)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 3956)
Known privilege escalation attack
- DllHost.exe (PID: 2088)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 3444)
SUSPICIOUS
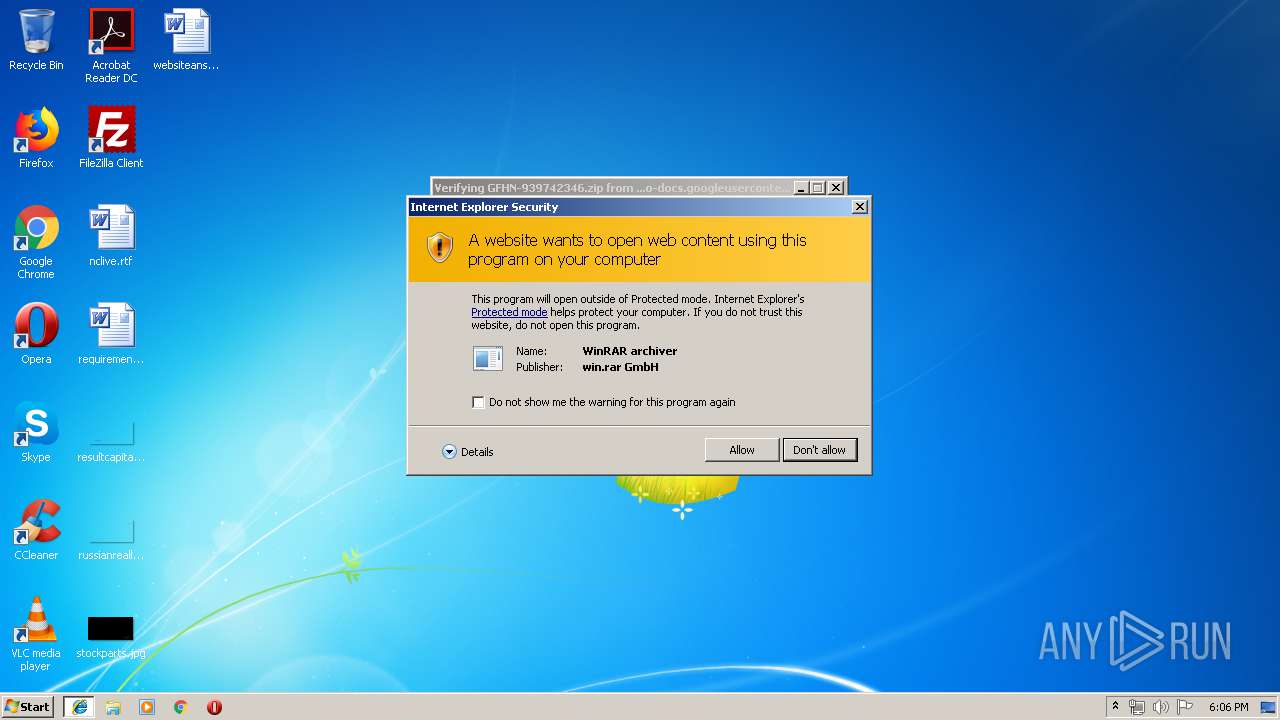
Starts CMD.EXE for commands execution
- D.exe (PID: 872)
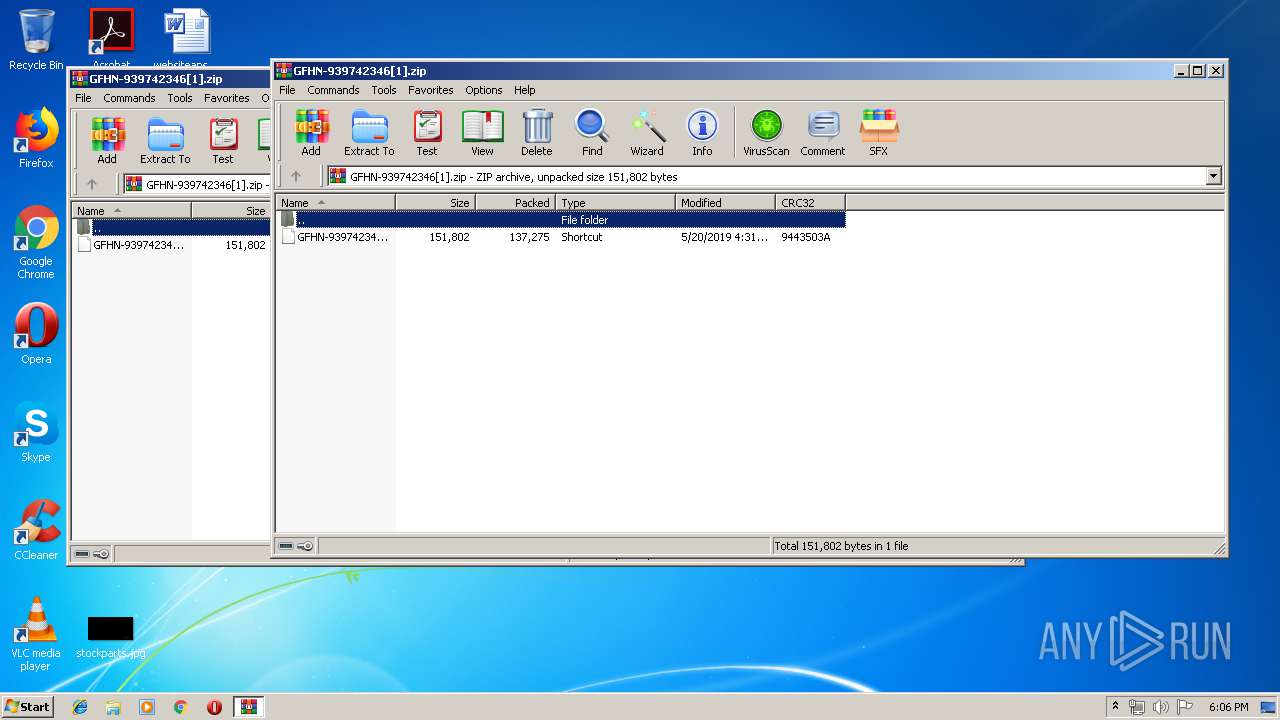
- WinRAR.exe (PID: 3460)
- D.exe (PID: 3444)
Executable content was dropped or overwritten
- powershell.exe (PID: 3432)
Creates files in the user directory
- powershell.exe (PID: 3432)
- powershell.exe (PID: 3436)
- powershell.exe (PID: 1704)
- powershell.exe (PID: 3884)
- powershell.exe (PID: 2780)
Executes PowerShell scripts
- cmd.exe (PID: 2352)
- cmd.exe (PID: 2304)
Executed via COM
- DllHost.exe (PID: 2088)
INFO
Changes internet zones settings
- iexplore.exe (PID: 868)
Application launched itself
- iexplore.exe (PID: 868)
Reads settings of System Certificates
- iexplore.exe (PID: 868)
- powershell.exe (PID: 3432)
Adds / modifies Windows certificates
- iexplore.exe (PID: 868)
Changes settings of System certificates
- iexplore.exe (PID: 868)
Reads Internet Cache Settings
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 868)
Creates files in the user directory
- iexplore.exe (PID: 3412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
33
Malicious processes
8
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | C:\Users\admin\AppData\Local\Temp/d | C:\Users\admin\AppData\Local\Temp\D.exe | — | cmd.exe | |||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
| 948 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | sc stop WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 643
Read events
2 234
Write events
403
Delete events
6
Modification events
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9BF1D92D-7B21-11E9-A370-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (868) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050001001400110006001E004503 | |||
Executable files
1
Suspicious files
14
Text files
10
Unknown types
6
Dropped files
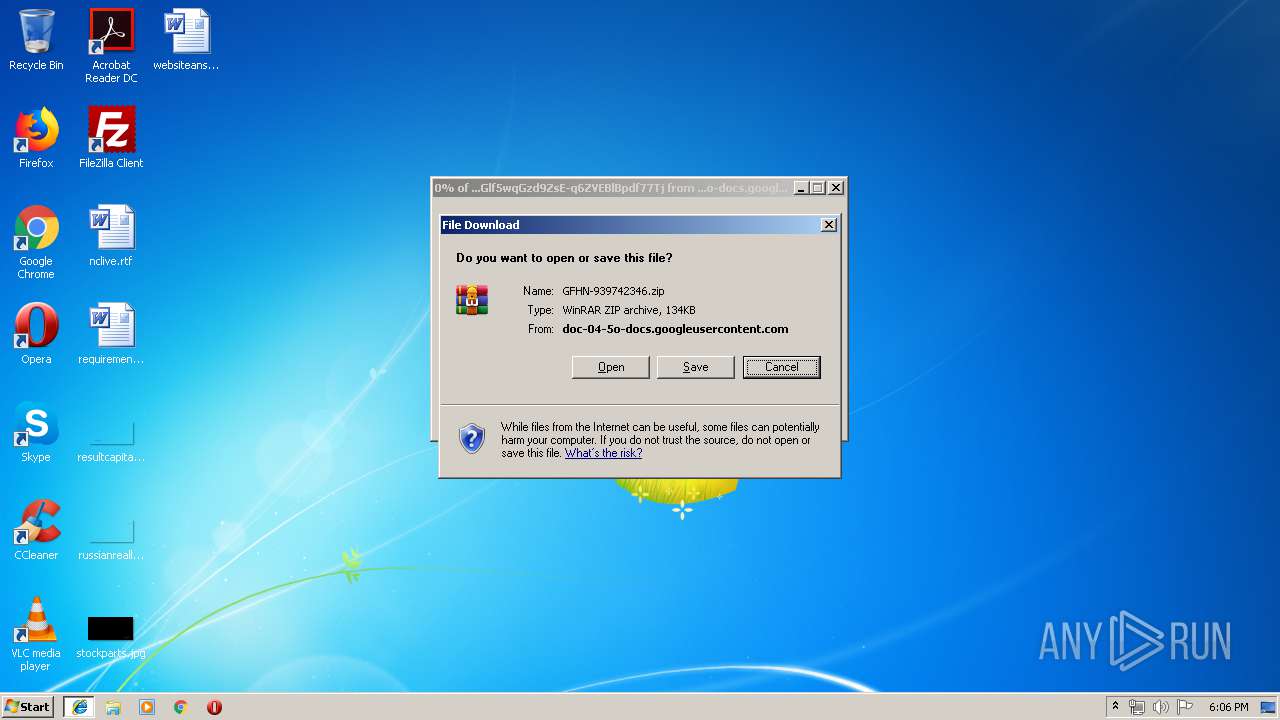
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 868 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF79BB1EEA9C3616F2.TMP | — | |
MD5:— | SHA256:— | |||
| 868 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAAAC0902A63D8231.TMP | — | |
MD5:— | SHA256:— | |||
| 868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{9BF1D92D-7B21-11E9-A370-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3432 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZMN8XTN9VDWYTFGNVBYF.temp | — | |
MD5:— | SHA256:— | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
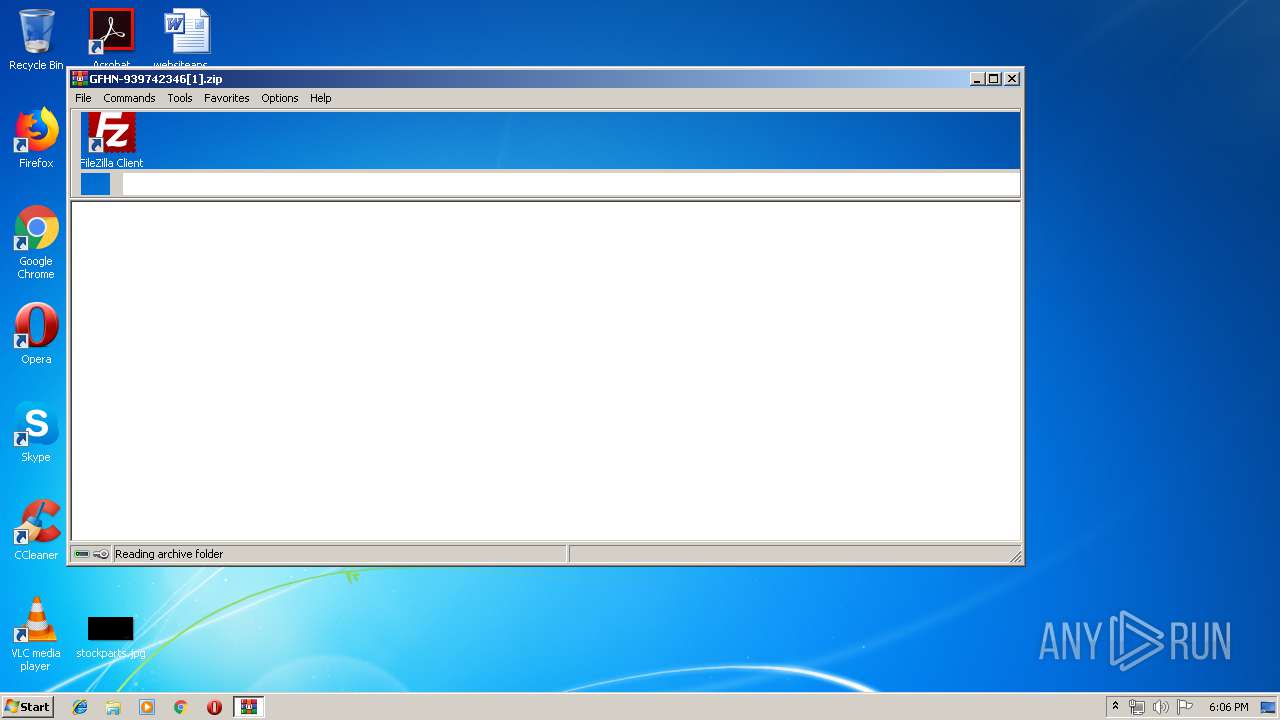
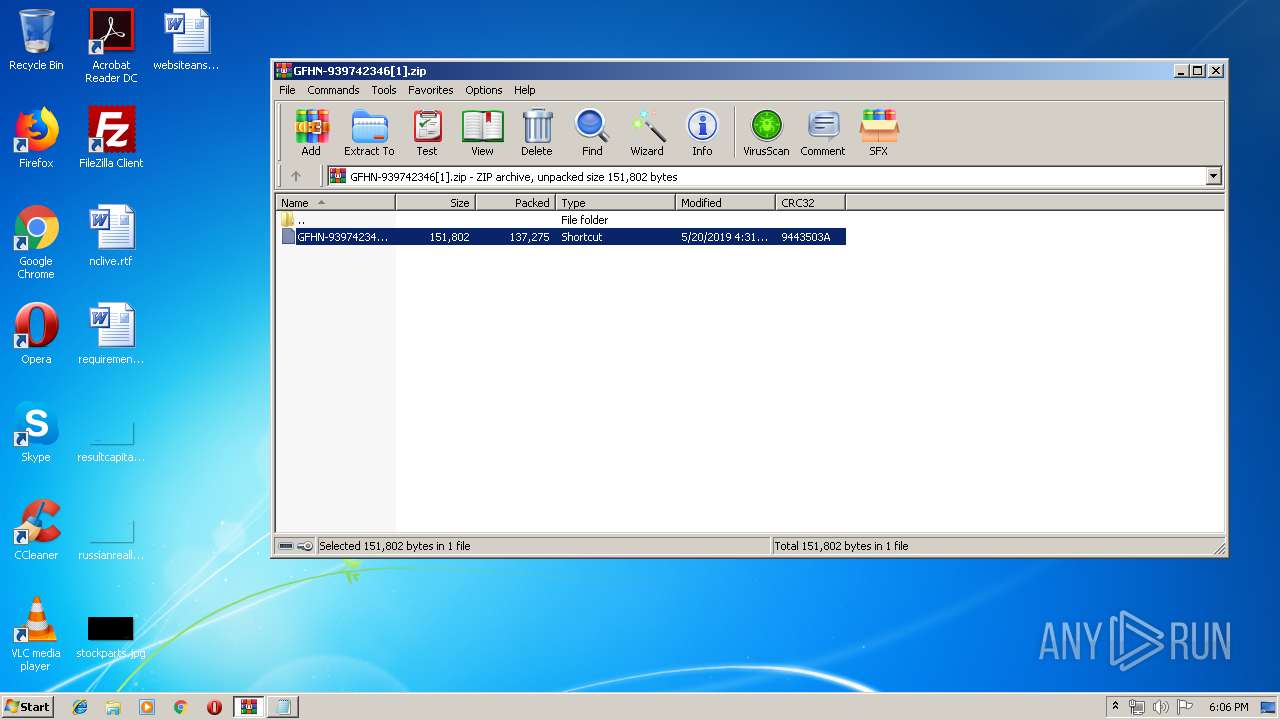
| 3412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\41AVX78V\GFHN-939742346[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 3436 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SLEWTS9KXTQGIAWWZ4S8.temp | — | |
MD5:— | SHA256:— | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
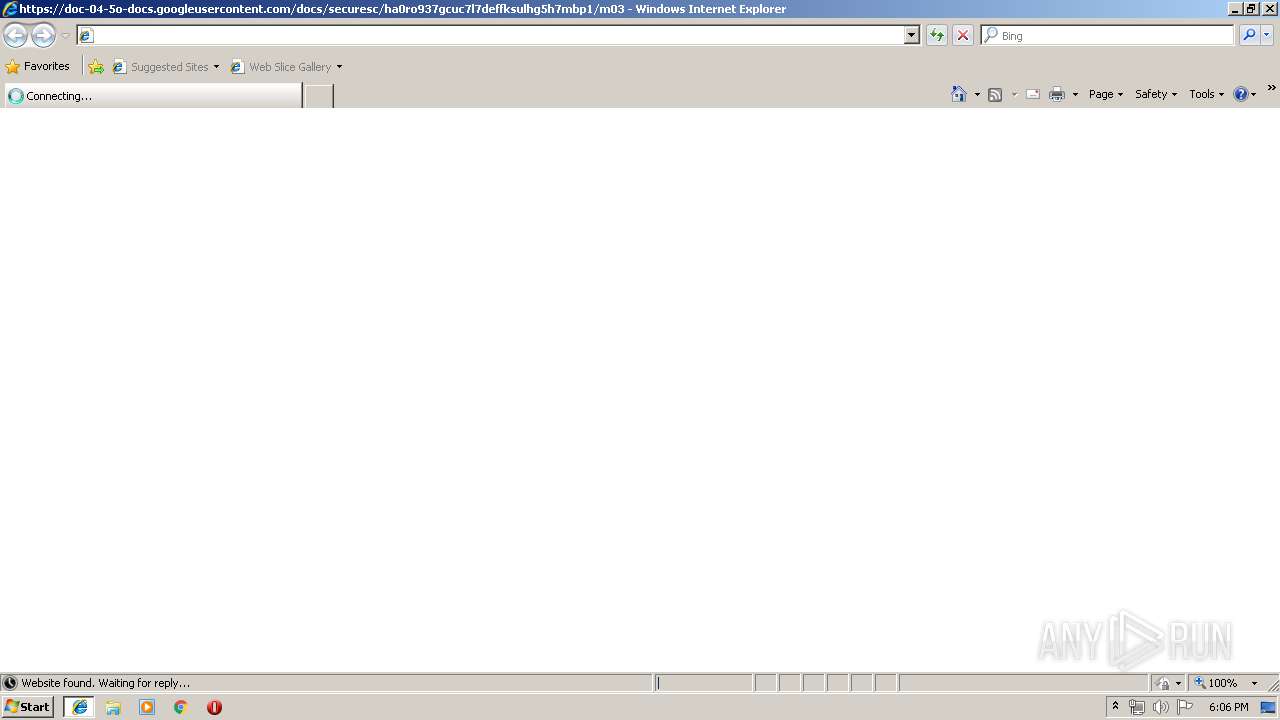
868 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3412 | iexplore.exe | 172.217.22.33:443 | doc-04-5o-docs.googleusercontent.com | Google Inc. | US | whitelisted |
3432 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
3412 | iexplore.exe | 216.58.207.78:443 | docs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
docs.google.com |
| shared |
doc-04-5o-docs.googleusercontent.com |
| shared |
www.braintrainersuk.com |
| malicious |