| File name: | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader |
| Full analysis: | https://app.any.run/tasks/fd79b8d3-8b00-4613-8899-98b526f88ad7 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2025, 12:30:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 21A3A583237A7BA6A2E7973267D8A95E |
| SHA1: | 8CE73C3B98749DE88ECC1A894606D7CC67967549 |
| SHA256: | 1A1F83CD65F8670AD894D709EF422BAD58E038C4145B54B692462D5327019887 |
| SSDEEP: | 98304:ogl96U4Eu0YjXhCk5cC3qgJeLrDuOXRdAqNWjAXg123zEfVw0/2QUO3hvgHWhhsi:F3Mr/ |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Connects to the CnC server
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Process drops legitimate windows executable
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Checks Windows Trust Settings
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads security settings of Internet Explorer
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads Internet Explorer settings
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads Microsoft Outlook installation path
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Contacting a server suspected of hosting an CnC
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
INFO
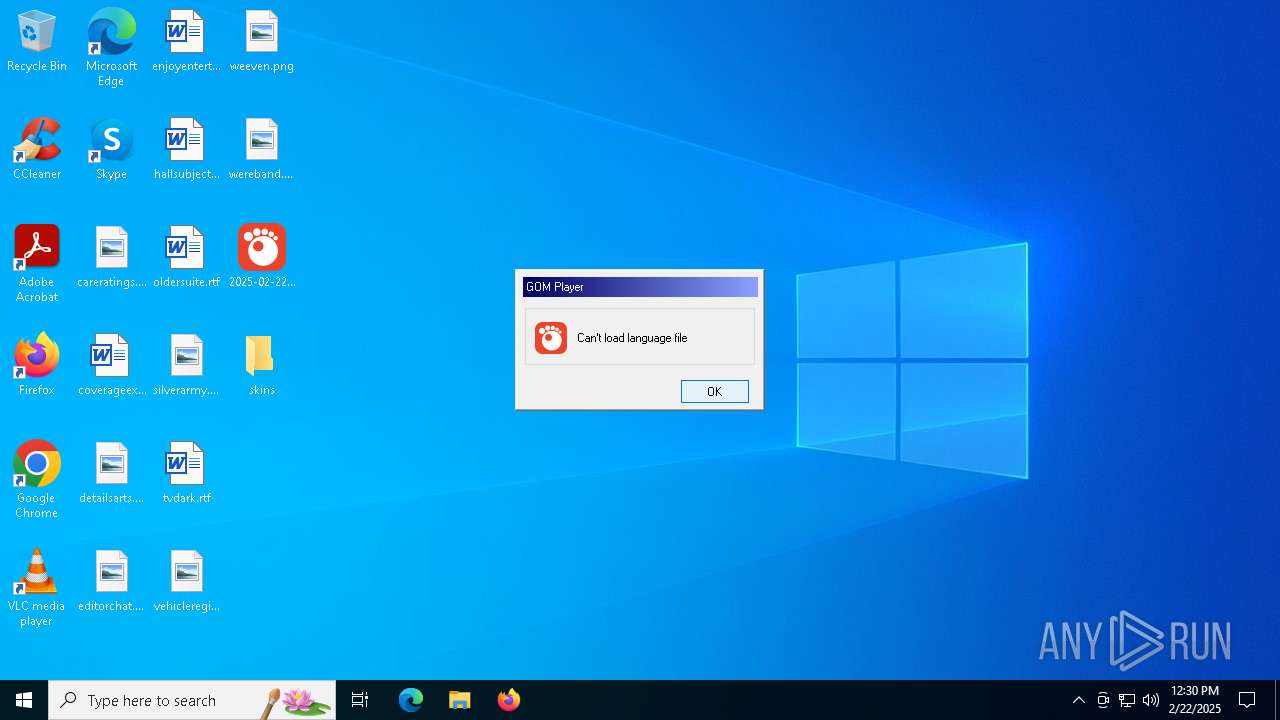
The sample compiled with korean language support
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Checks supported languages
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Failed to create an executable file in Windows directory
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads the computer name
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
The sample compiled with english language support
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Create files in a temporary directory
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads the machine GUID from the registry
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Checks proxy server information
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Creates files or folders in the user directory
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Reads the software policy settings
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Creates files in the program directory
- 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:01:20 00:44:19+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 7917568 |
| InitializedDataSize: | 7259136 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x64147b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.105.5375 |
| ProductVersionNumber: | 2.3.105.5375 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | GOM & Company |
| FileDescription: | GOM Player |
| FileVersion: | 2, 3, 105, 5375 |
| InternalName: | GOM |
| LegalCopyright: | Copyright 2003 GOM & Company All Rights Reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | GOM.EXE |
| PrivateBuild: | - |
| ProductName: | GOM Player |
| ProductVersion: | 2, 3, 105, 5375 |
| SpecialBuild: | - |
Total processes
121
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2084 | "C:\Users\admin\Desktop\2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe" | C:\Users\admin\Desktop\2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | explorer.exe | ||||||||||||
User: admin Company: GOM & Company Integrity Level: MEDIUM Description: GOM Player Exit code: 0 Version: 2, 3, 105, 5375 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 043
Read events
4 128
Write events
854
Delete events
61
Modification events
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION |
| Operation: | write | Name: | smver |
Value: 3 | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION |
| Operation: | write | Name: | mode |
Value: 3 | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION\FILTER_BLACKLIST |
| Operation: | write | Name: | 011_sFriendlyName |
Value: FFDSHOW Audio Decoder | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION\FILTER_BLACKLIST |
| Operation: | write | Name: | 011_clsid |
Value: {52AF62CF-7099-4674-B52E-AFC3B464A419} | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION\FILTER_BLACKLIST |
| Operation: | write | Name: | 011_bActive |
Value: 1 | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION\FILTER_BLACKLIST |
| Operation: | write | Name: | 011_bUnused |
Value: 0 | |||
| (PID) Process: | (2084) 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GRETECH\GOMPLAYER\OPTION\FILTER_BLACKLIST |
| Operation: | write | Name: | 020_sFriendlyName |
Value: MainConcept (Adobe2) AAC Decoder | |||
Executable files
2
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll.000 | text | |
MD5:1130C911BF5DB4B8F7CF9B6F4B457623 | SHA256:EBA08CC8182F379392A97F542B350EA0DBBE5E4009472F35AF20E3D857EAFDF1 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:4FDEA5C6C2D18A4E29D335E69C1BEADD | SHA256:E1ACA66D27C7D39C82DBC39A3B99D7E4D733421B2DE6BE6B28DE8690681D777F | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:1BFC0DB680F106D3431AC13601943E8C | SHA256:277661CB93FB6BCA410E95B5940F1765A736102A81DCD3A403184E86FA8B2346 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:BEF8DB9A226F8B8C51AC794A40435181 | SHA256:B3A3AF5D018027CBC0FAC2B06555A1DF10AB4BAF533A1BF5B17425C4F446C0F1 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\Roaming\GRETECH\GOMPlayer\RecentURL.asx | text | |
MD5:44781ECE18DF4A32C818CDAE41AF12EE | SHA256:23A6A277C7DD6A2235AB9FD8EBC5AD31BCADF25FCBE1D6FC07BCD675E49850D9 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\Local\Temp\conres.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:FBEDC7AED124DE6590E1FB97B8432508 | SHA256:C7AC6CC42FDFE3CA23ACBACC143DED2C8B354917BC06B3D8FC8231A2C9A5ED61 | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_CBECBD5B884BB75B183807EECD99D9AD | binary | |
MD5:71AEE6246348AA096F76FD9B1A4C98D1 | SHA256:81888CFEF449145A97D416087654EE153C80C412AE2B7C89D8F81B8518D202DE | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_CBECBD5B884BB75B183807EECD99D9AD | binary | |
MD5:C8AAA37A645FF15EE0E8BE703ECAA384 | SHA256:DF89E1D871F86AC452910465D51D5B2FD3CCDBC4692BDEB5173EF9B184CAB7BA | |||
| 2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | C:\Users\admin\AppData\Local\Temp\A1D26E2\6CB7280824.tmp | executable | |
MD5:9CBC4A8F3FF94DD0C7EAB7C6A46E57CC | SHA256:0AC363452FBCE3DCBAB61B7488B73801EAEC004AB01B4F34406B65DF608CE2EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
21
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4912 | RUXIMICS.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | GET | 403 | 45.79.19.196:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | GET | 404 | 44.197.149.37:80 | http://log.gomlab.com/player/playing?usmid=GOMPLAYER_READ_FAIL&build=&appver=2.3.105.5375&bit=32bit&os=windows1064bit&lang=eng&skin=users&launching=producticon&browser=msedge&settingmode=3&vrsetting=8 | unknown | — | — | unknown |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | GET | 403 | 45.79.19.196:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAsItdjkZt4h6uHSonYxKRY%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4912 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1684 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4912 | RUXIMICS.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1684 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
5isohu.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.aieov.com |
| malicious |
log.gomlab.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
2084 | 2025-02-22_21a3a583237a7ba6a2e7973267d8a95e_bkransomware_floxif_hijackloader.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |