| File name: | xray-68-1152.jar |
| Full analysis: | https://app.any.run/tasks/6a432c09-77c9-46b5-b449-56a0c8320eeb |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 11:54:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 3AA399398F1680806ABD824020054467 |
| SHA1: | 719D762B3D040117EF58DDFA5EC609F9FCA31332 |
| SHA256: | 1A0DF1D65144EC6B2896ECE1320DADFD026D701284B2C9701735BD5713890812 |
| SSDEEP: | 6144:eFmxs7LcwAaiAnJZLMcnZ/XyzCZw2XN2tGh4p0Ht:eAYdAVAnJZLFXyzCS2PhVHt |
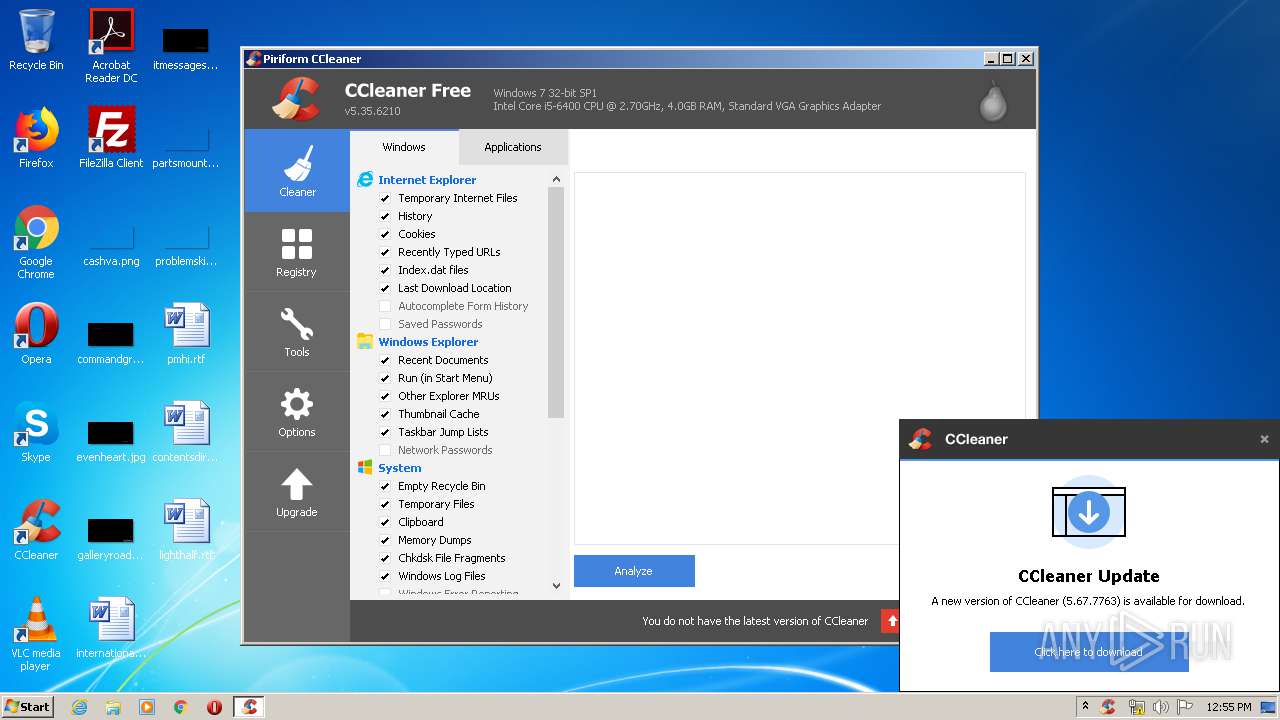
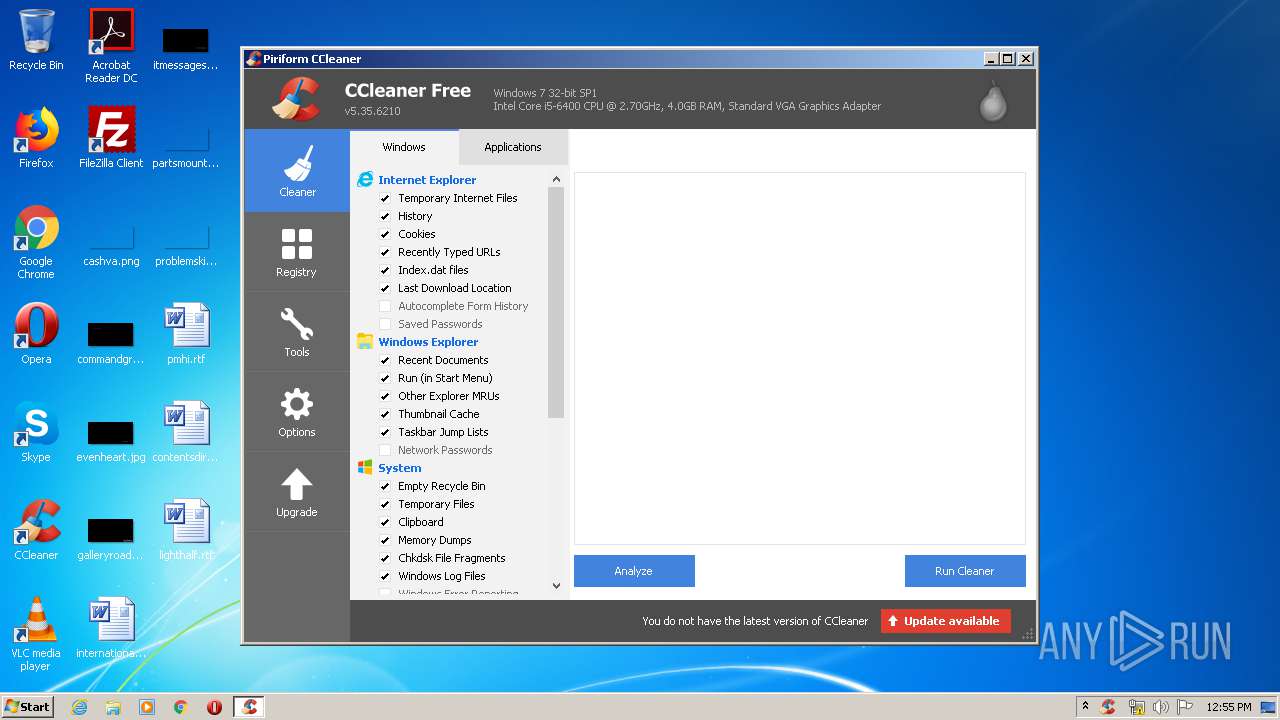
MALICIOUS
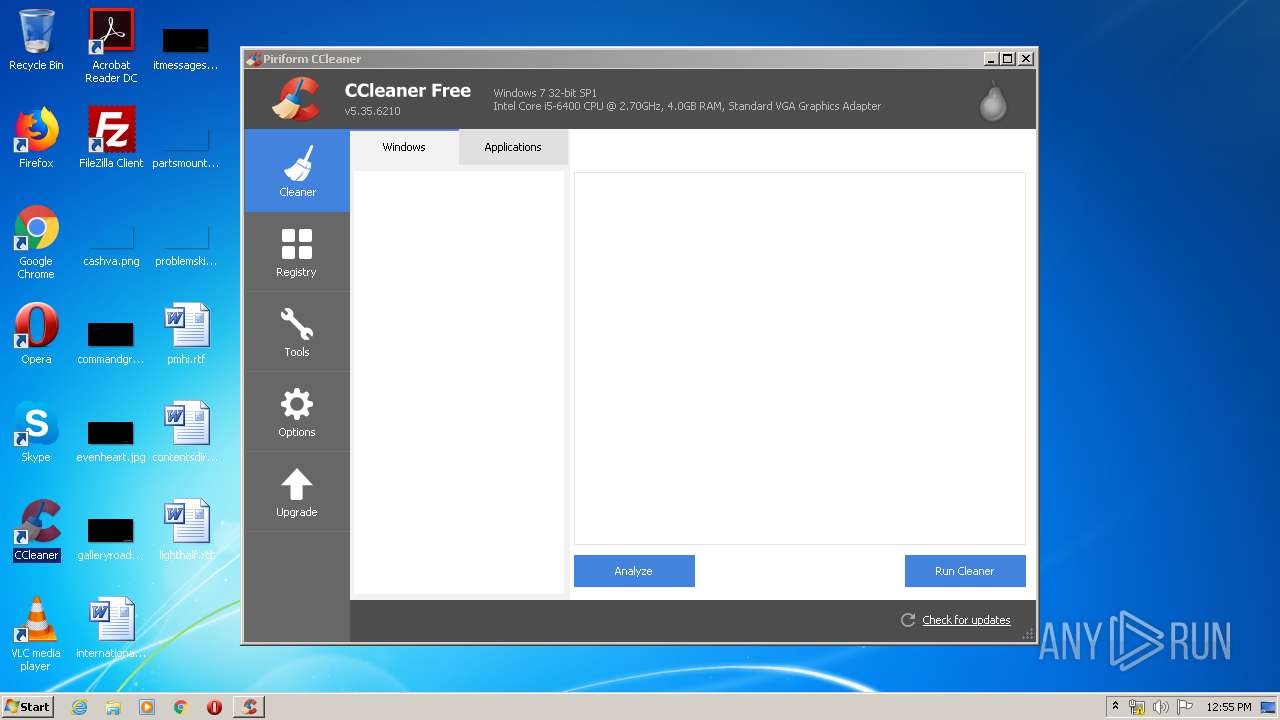
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 588)
- CCleaner.exe (PID: 2232)
Changes the autorun value in the registry
- CCleaner.exe (PID: 2232)
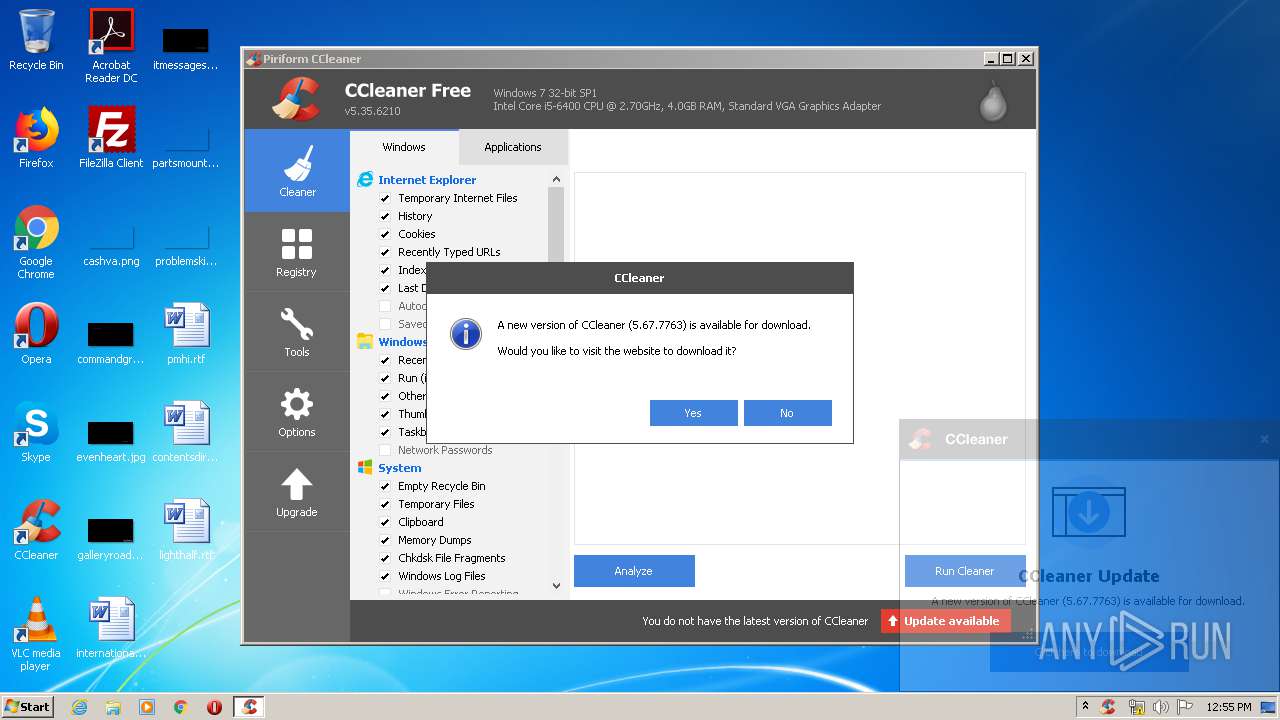
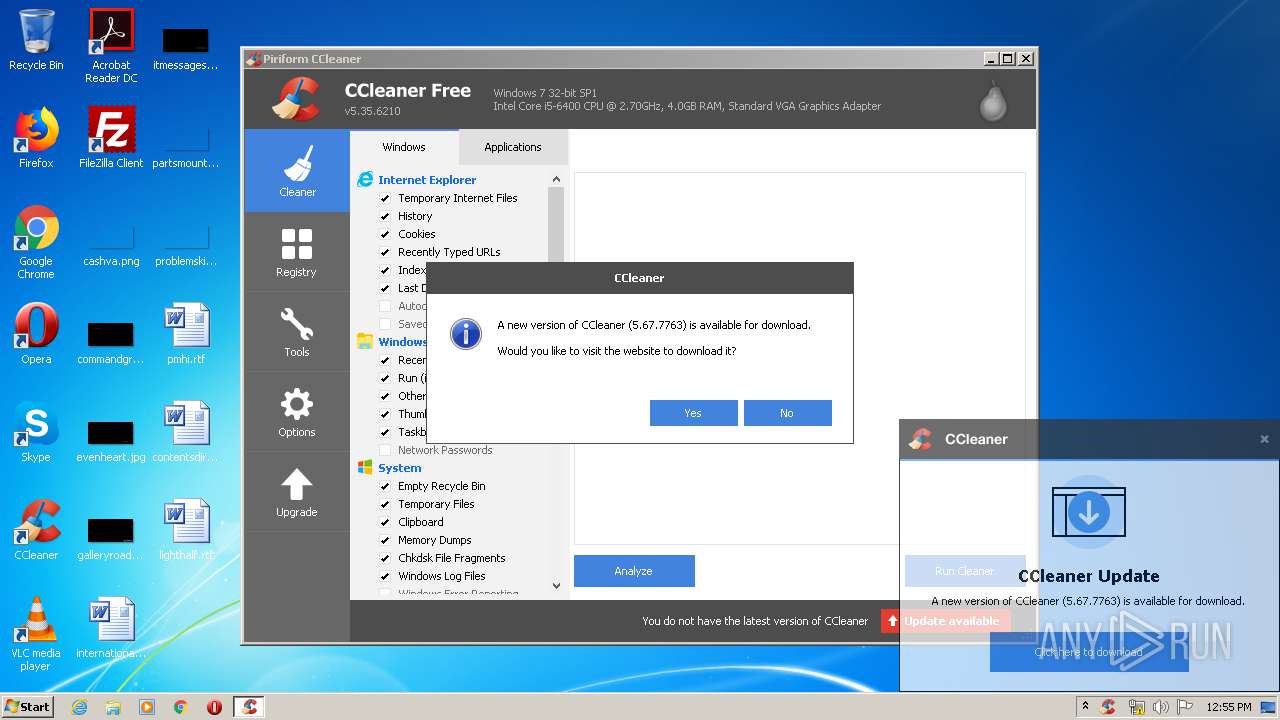
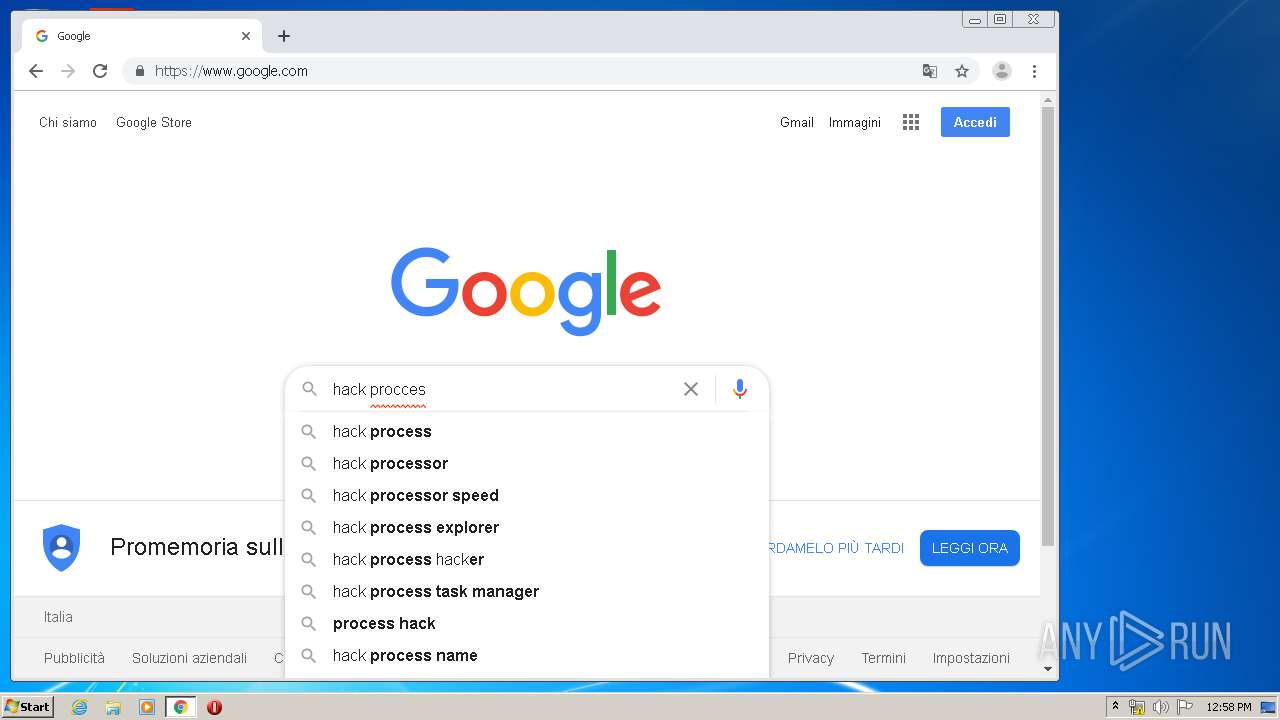
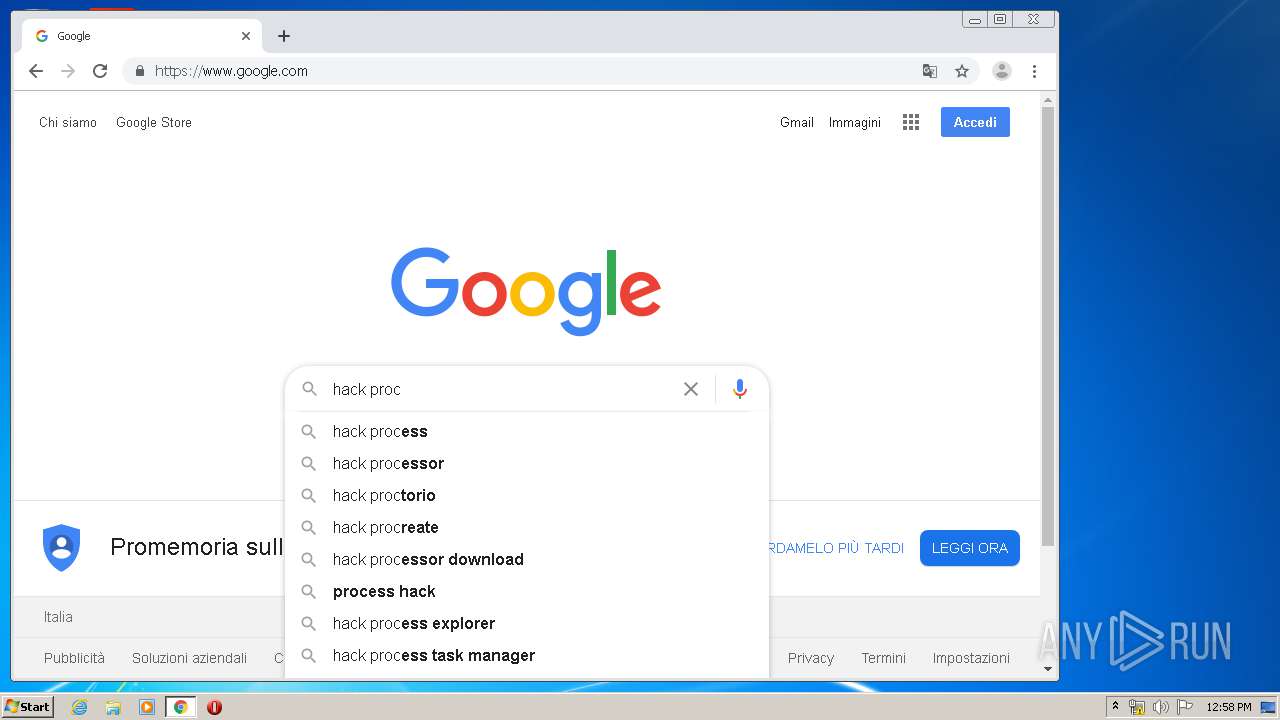
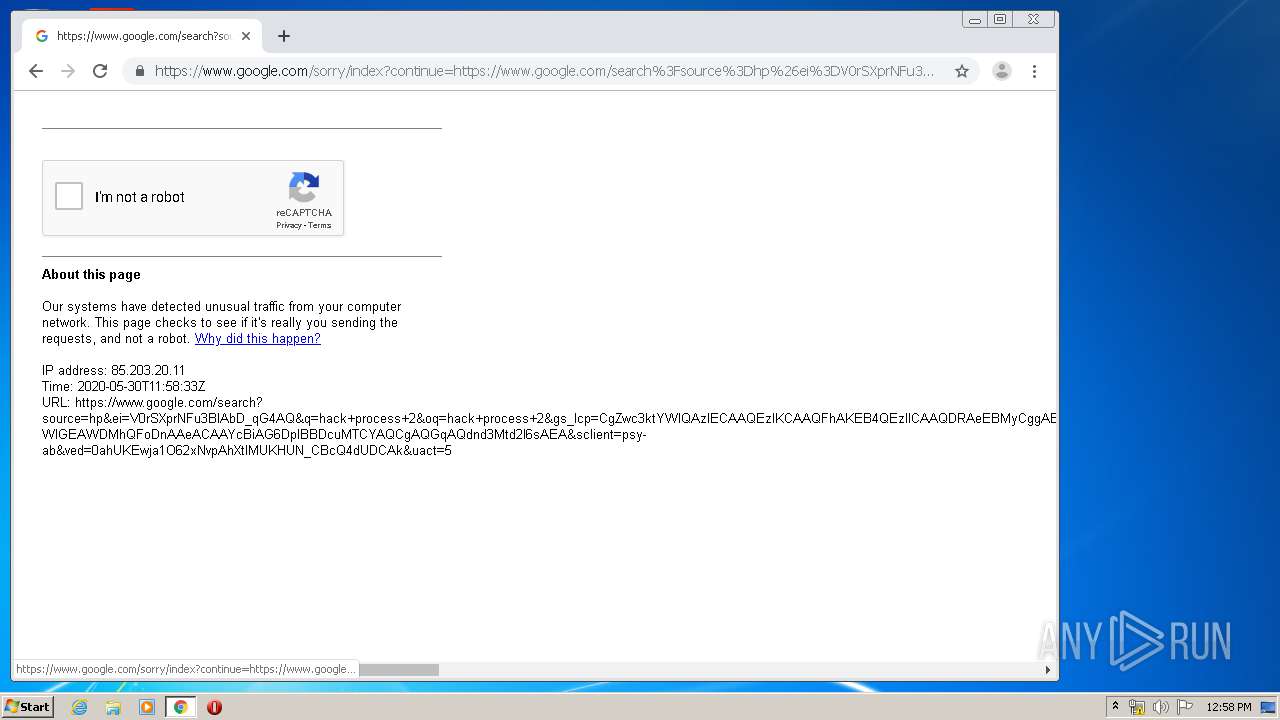
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2368)
- CCleaner.exe (PID: 2232)
Changes settings of System certificates
- CCleaner.exe (PID: 2368)
SUSPICIOUS
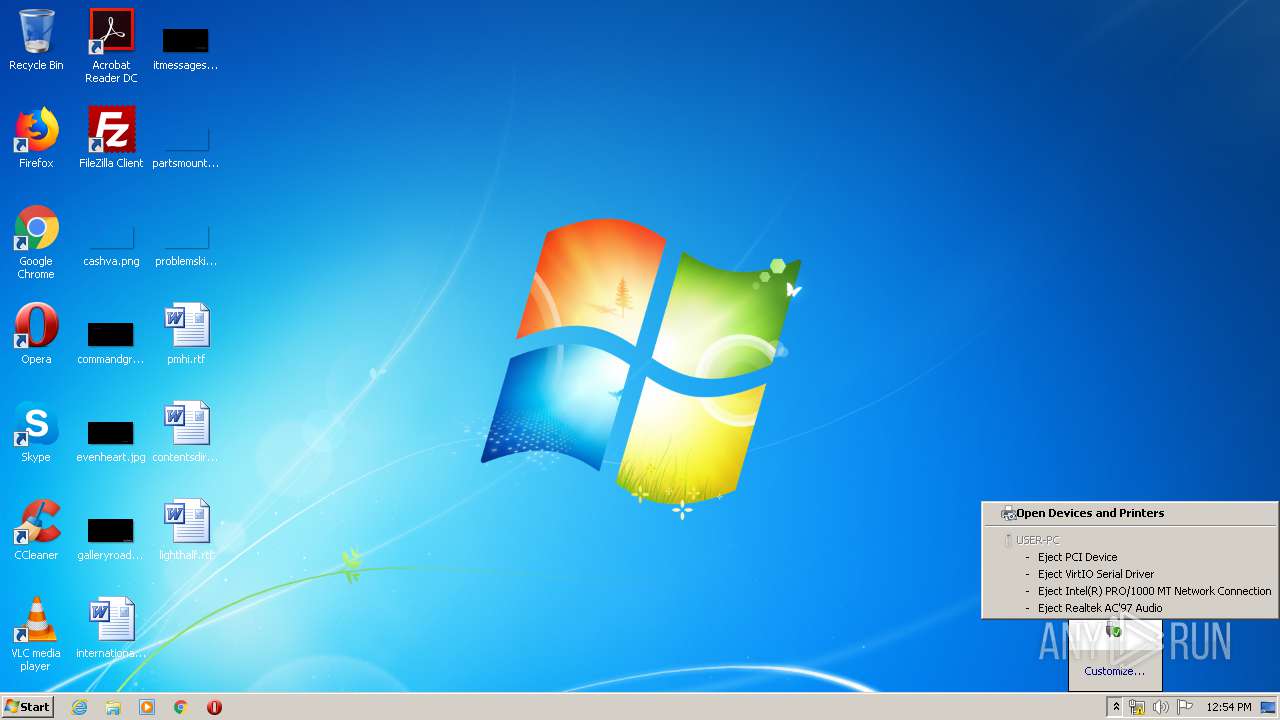
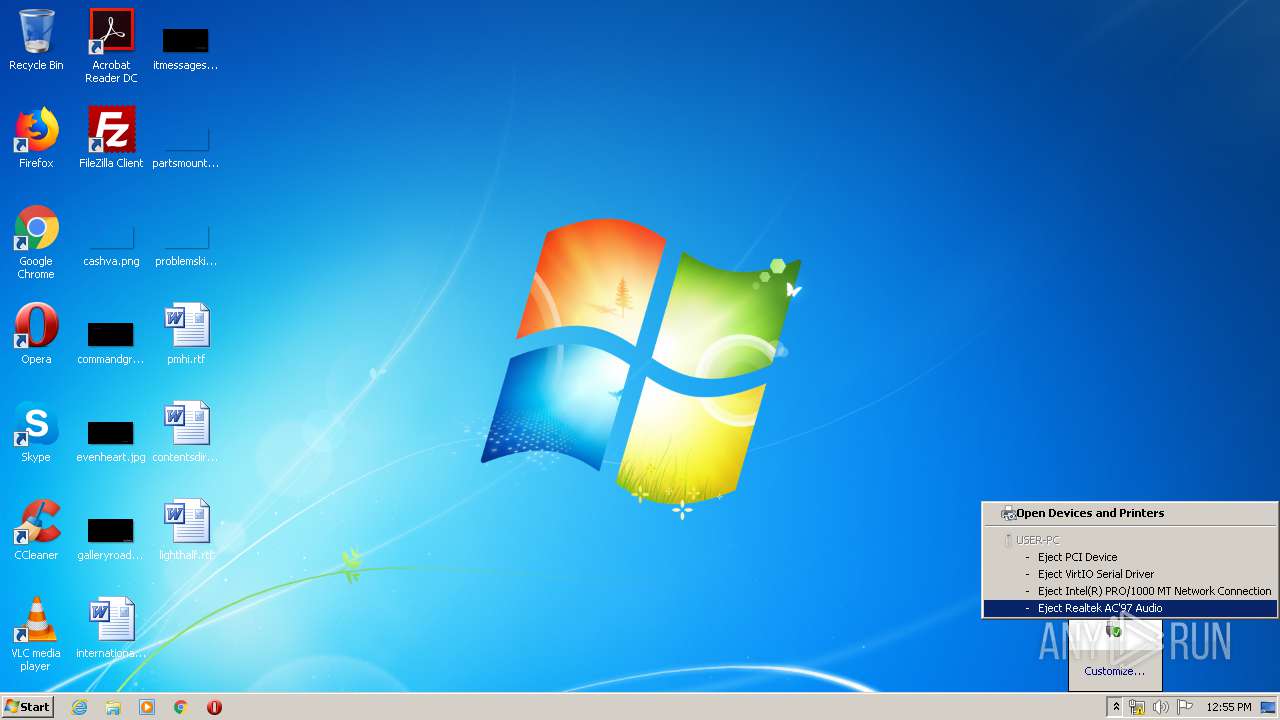
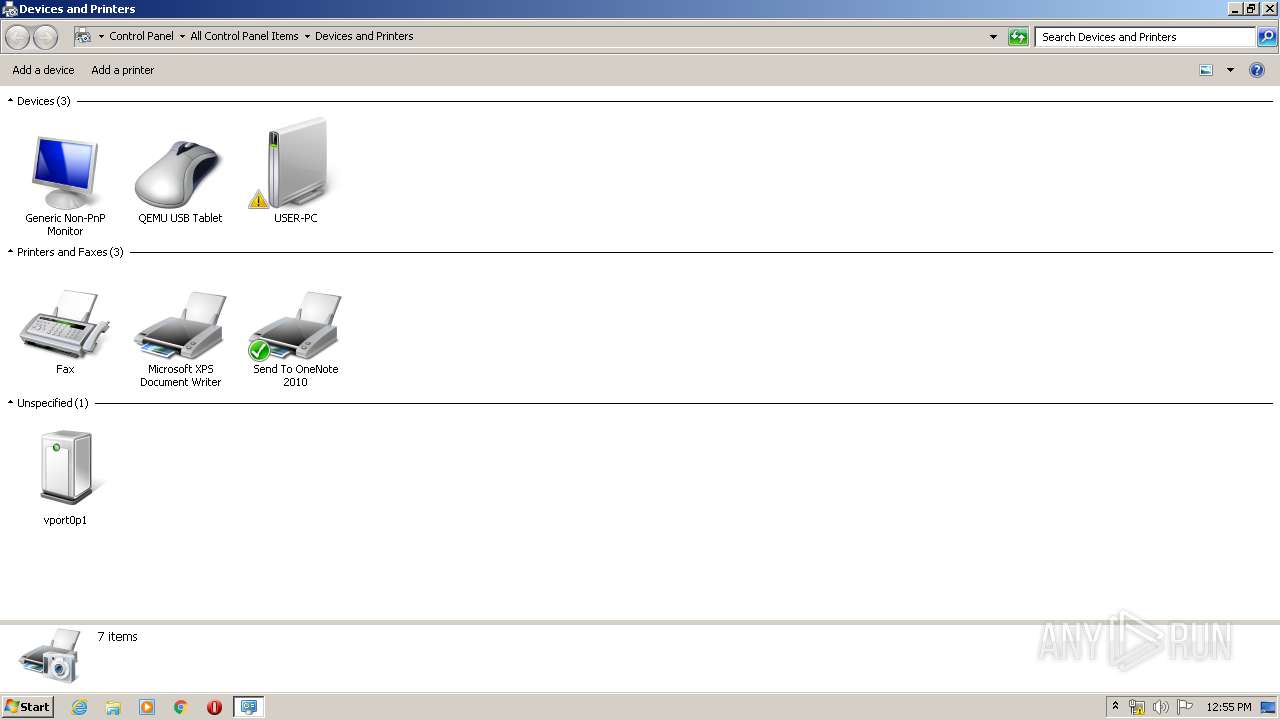
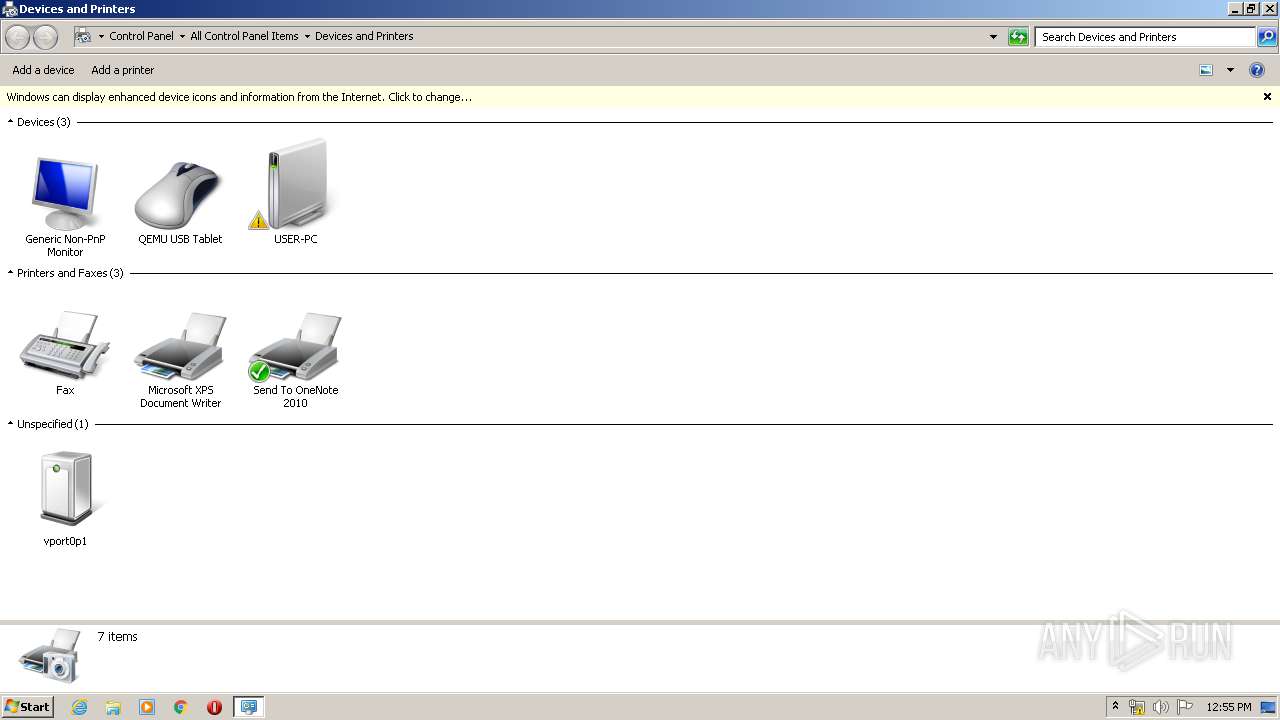
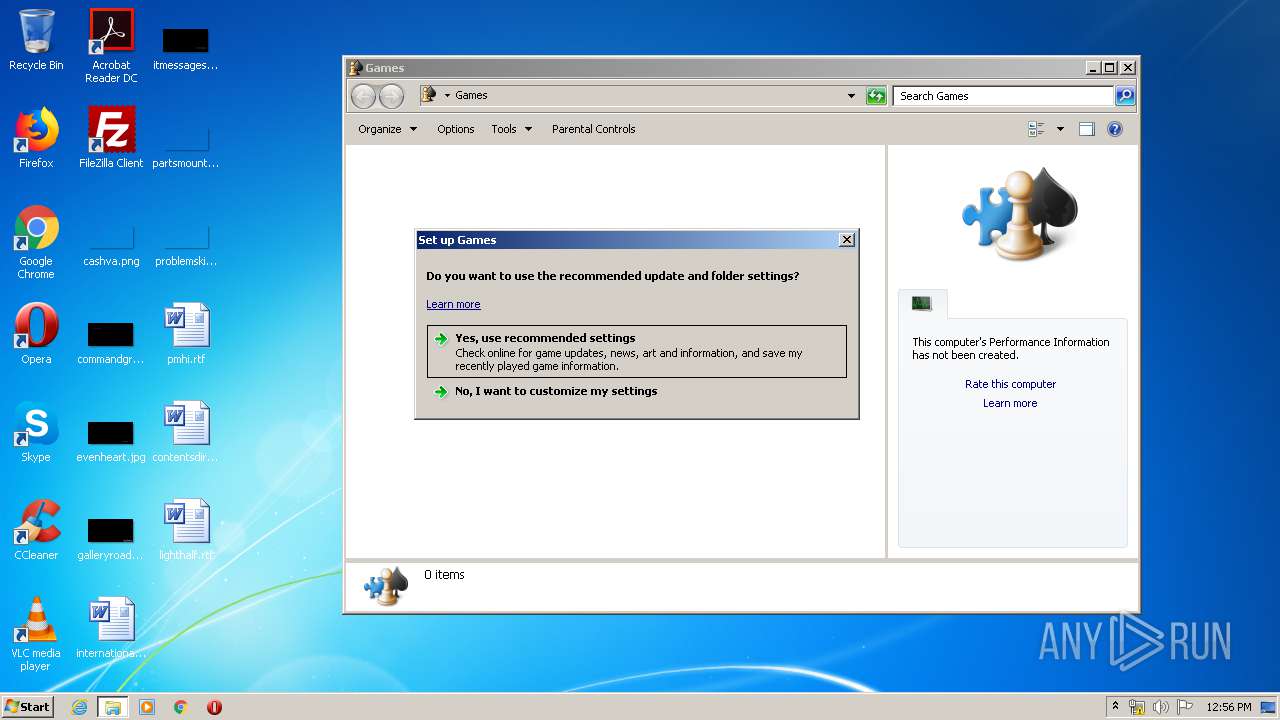
Executed via COM
- DeviceDisplayObjectProvider.exe (PID: 2408)
- DeviceDisplayObjectProvider.exe (PID: 4036)
Executed via Task Scheduler
- CCleaner.exe (PID: 2368)
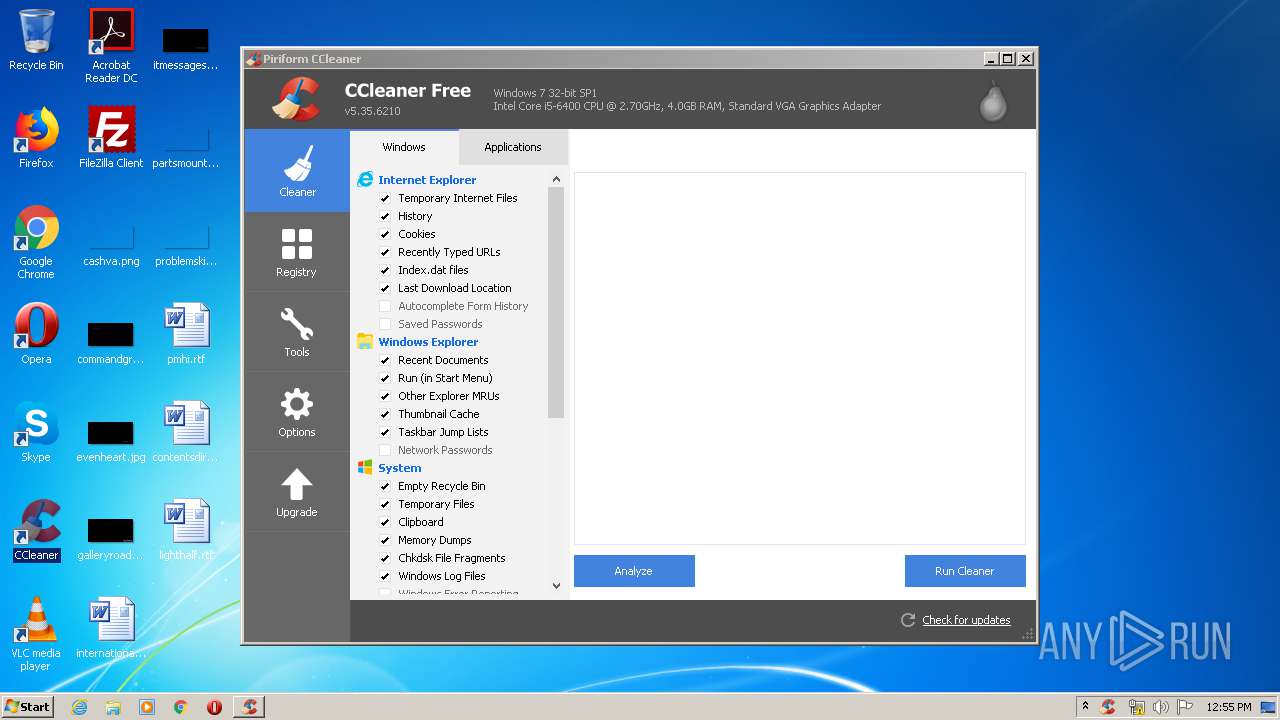
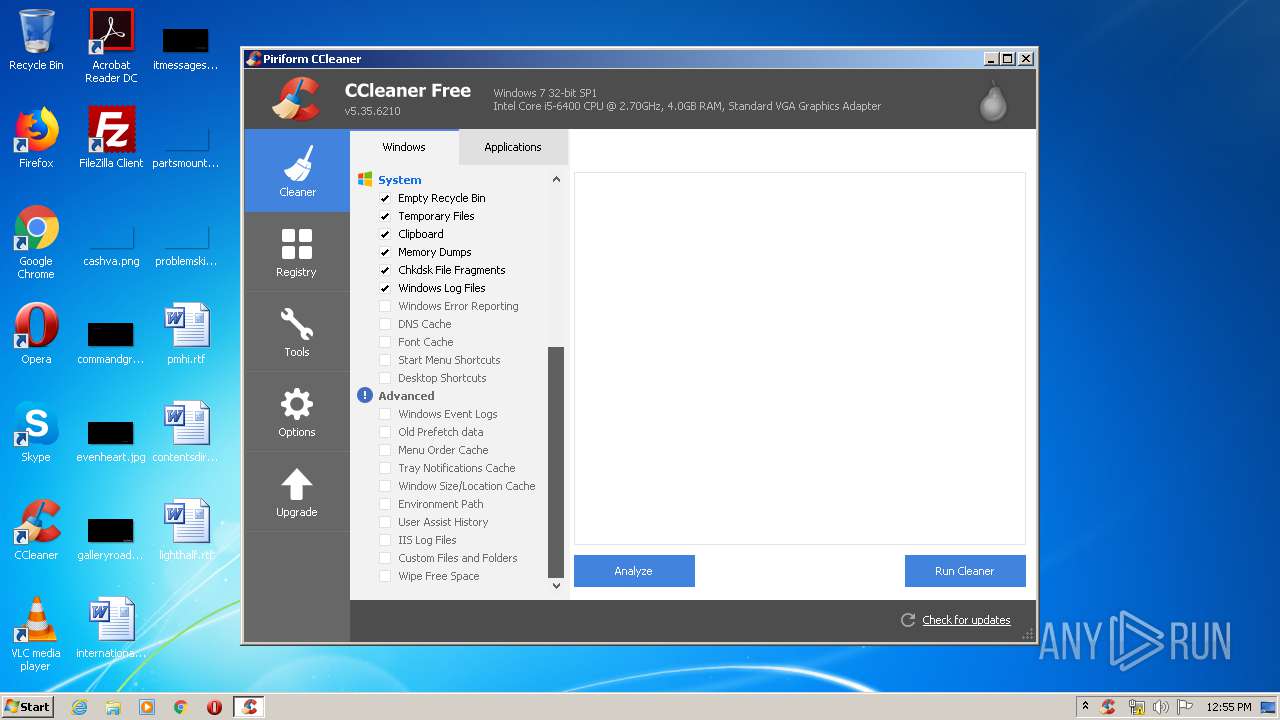
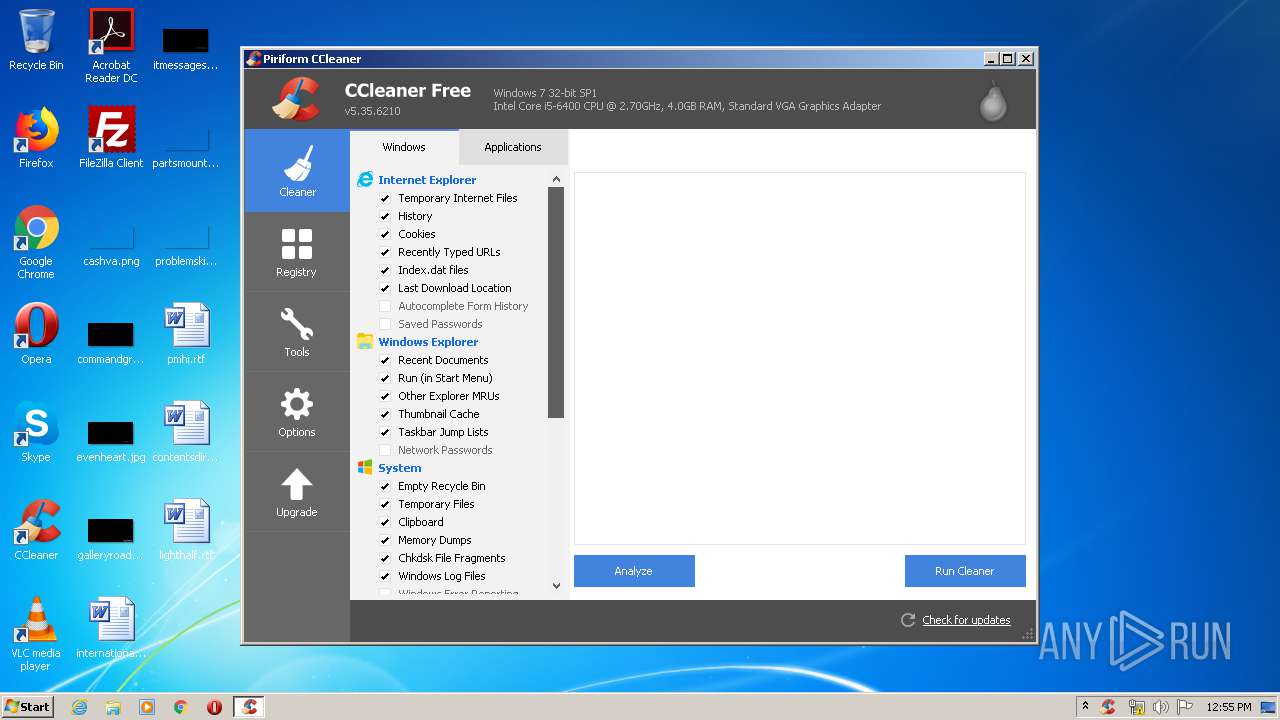
Reads internet explorer settings
- CCleaner.exe (PID: 2368)
- CCleaner.exe (PID: 2232)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2368)
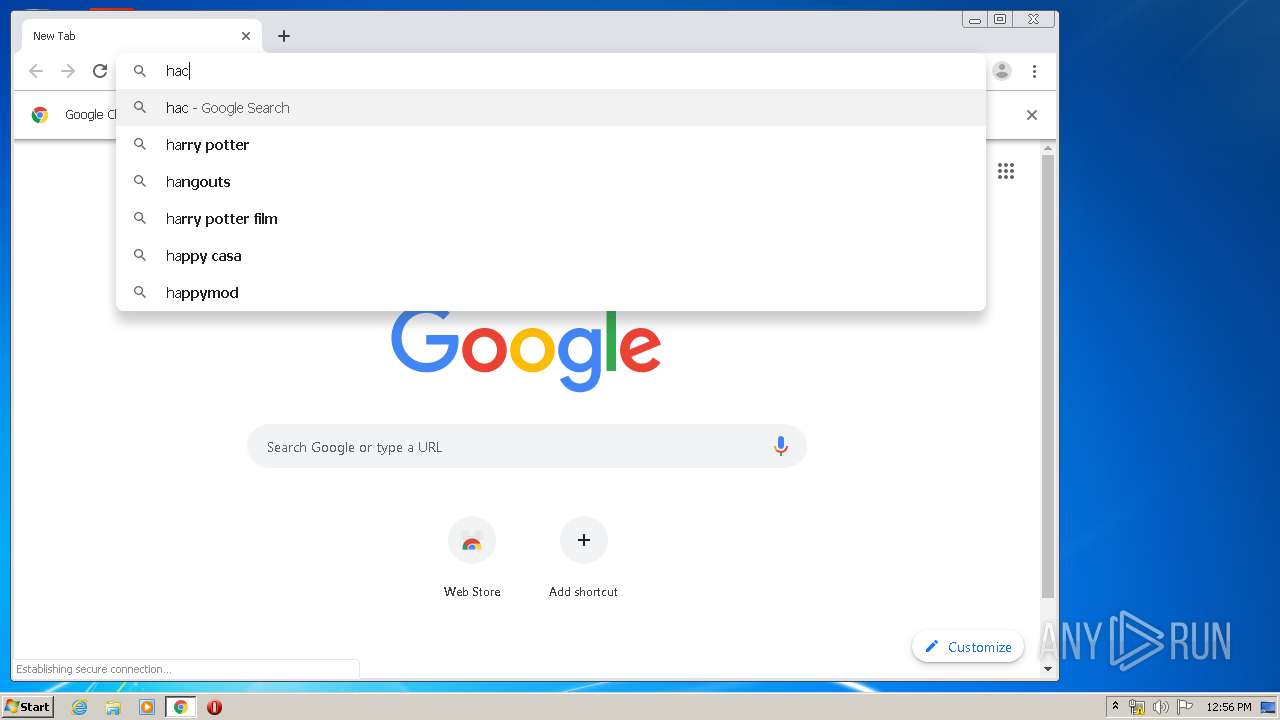
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2368)
Application launched itself
- CCleaner.exe (PID: 2368)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2368)
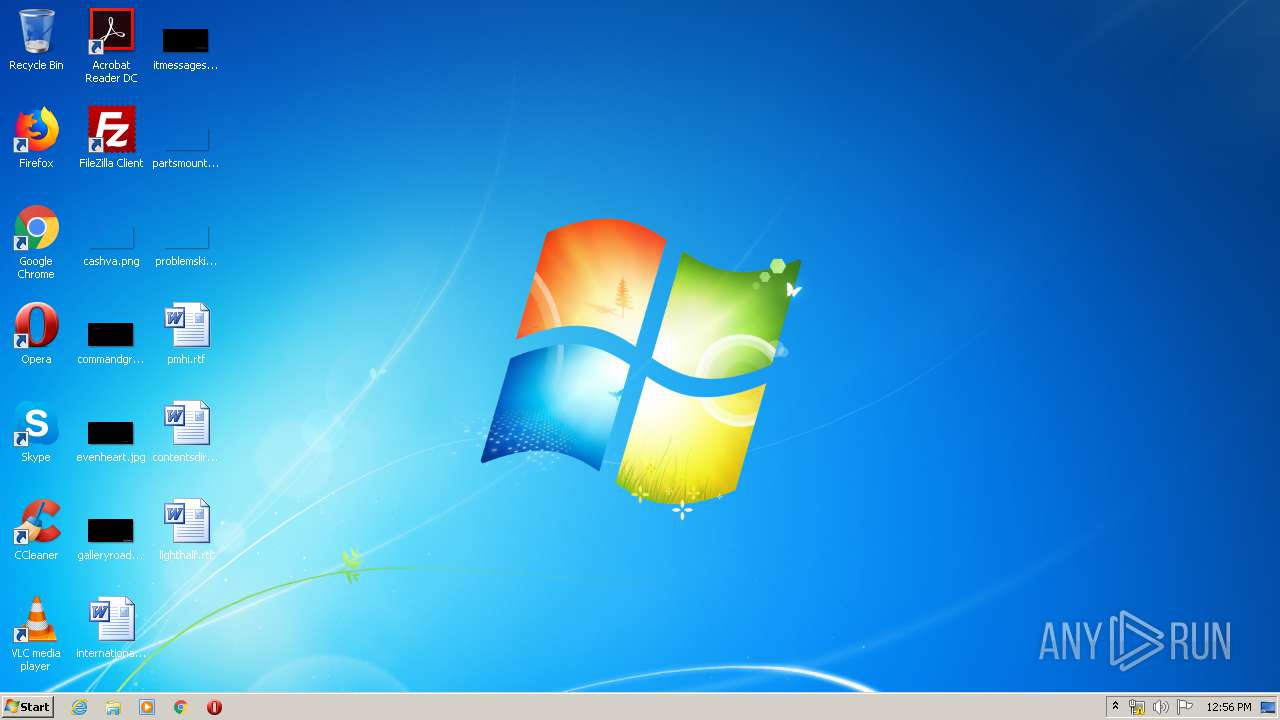
Creates files in the user directory
- CCleaner.exe (PID: 2368)
Reads Internet Cache Settings
- CCleaner.exe (PID: 2368)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3456)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 2368)
INFO
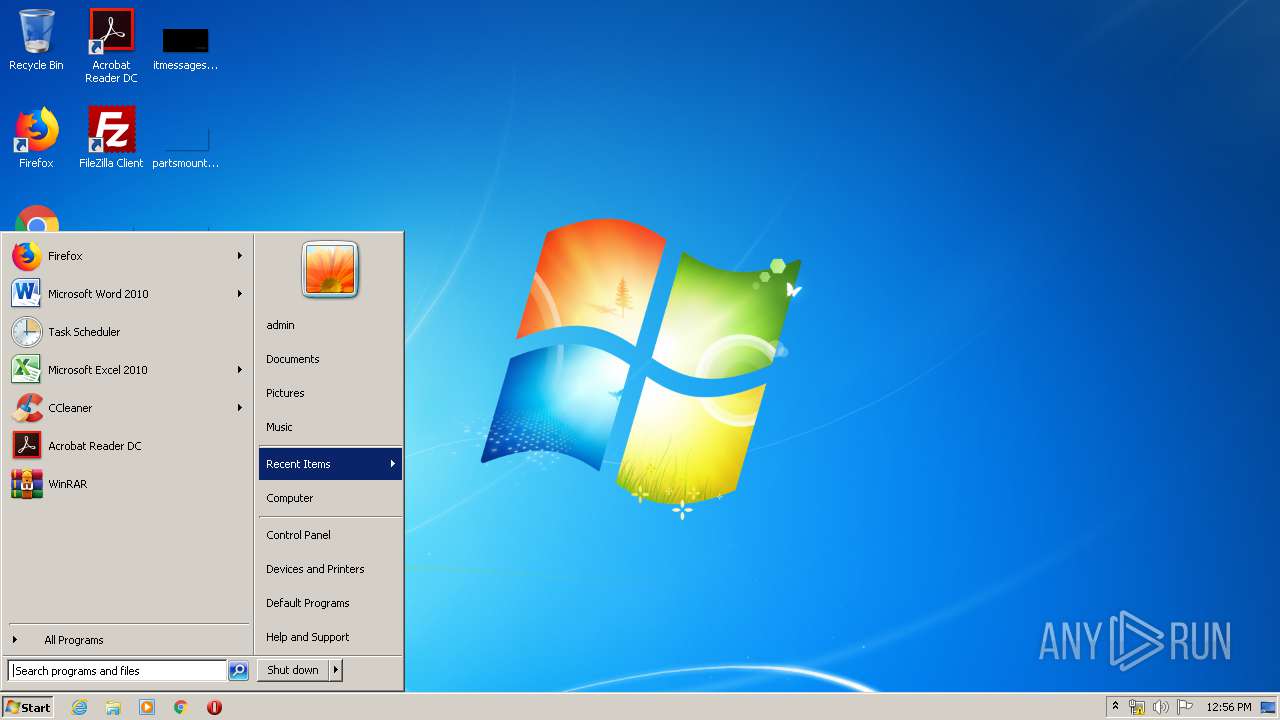
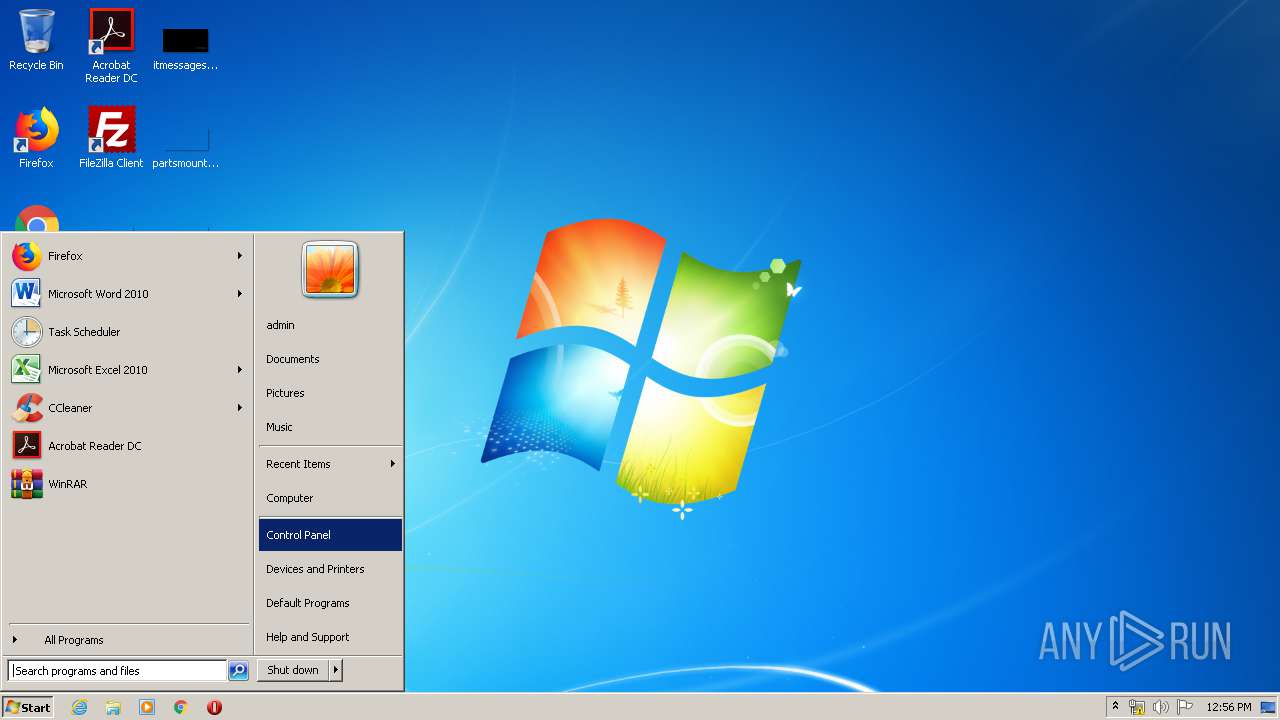
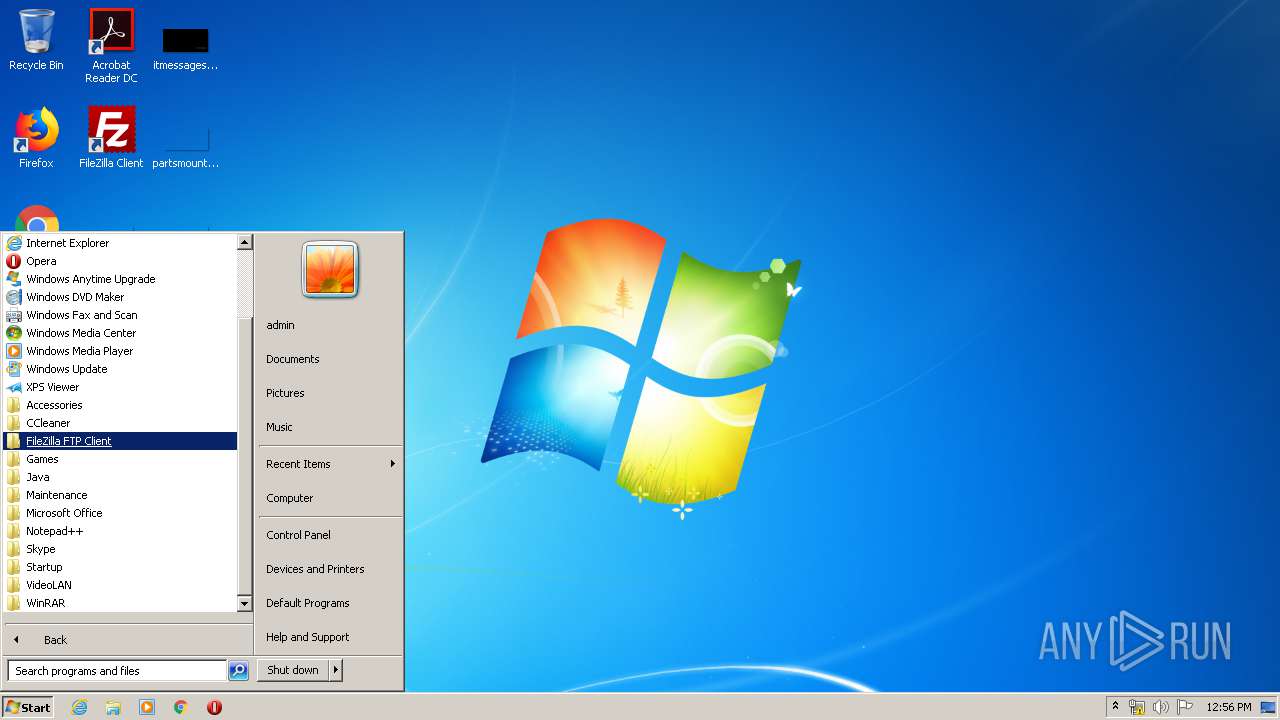
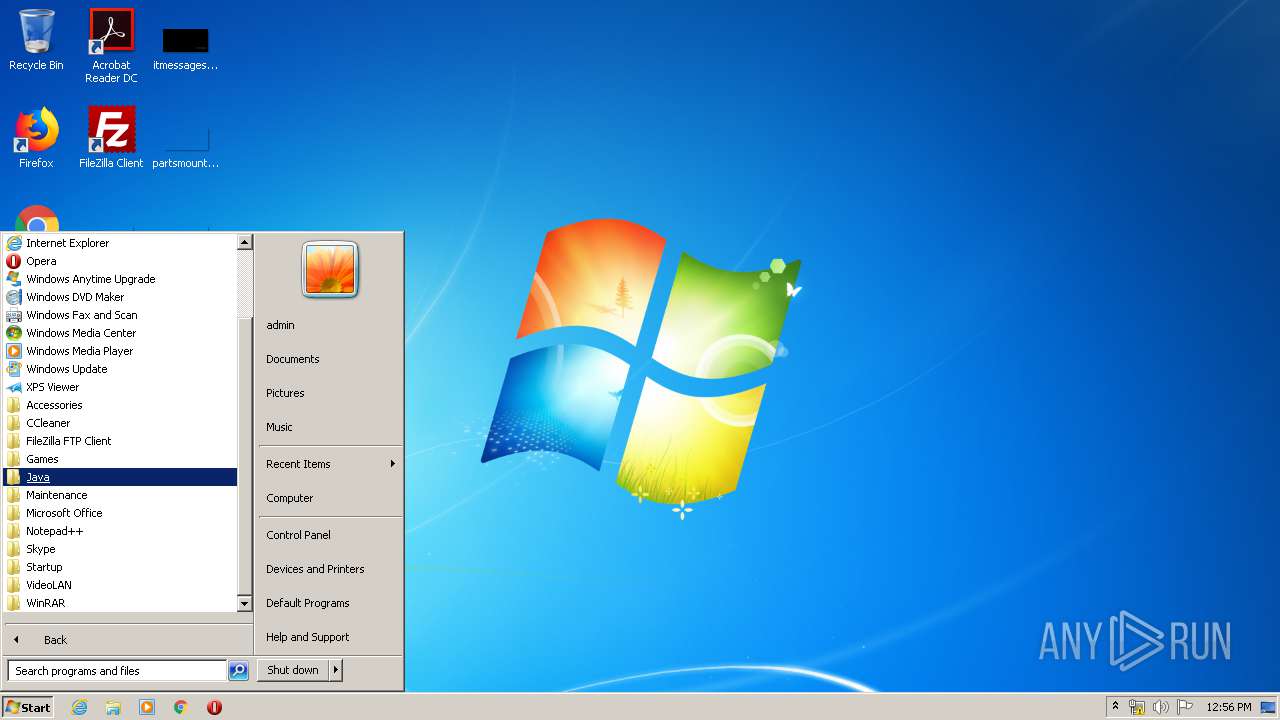
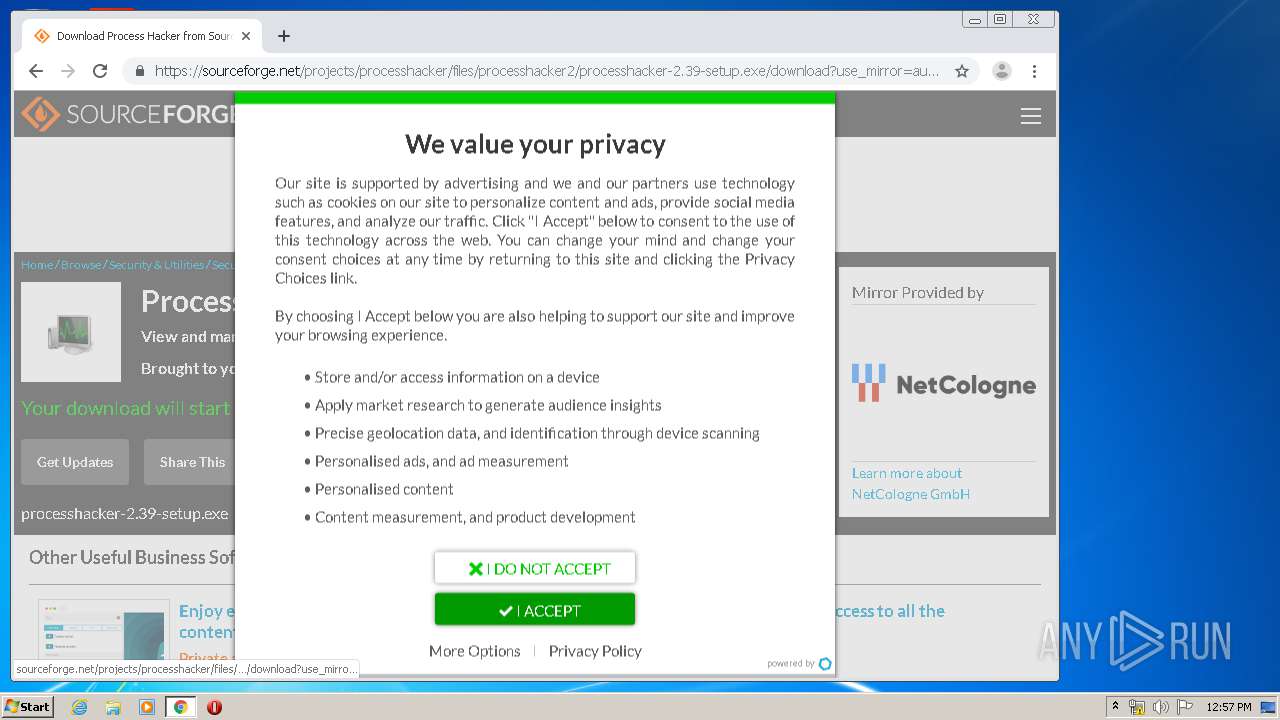
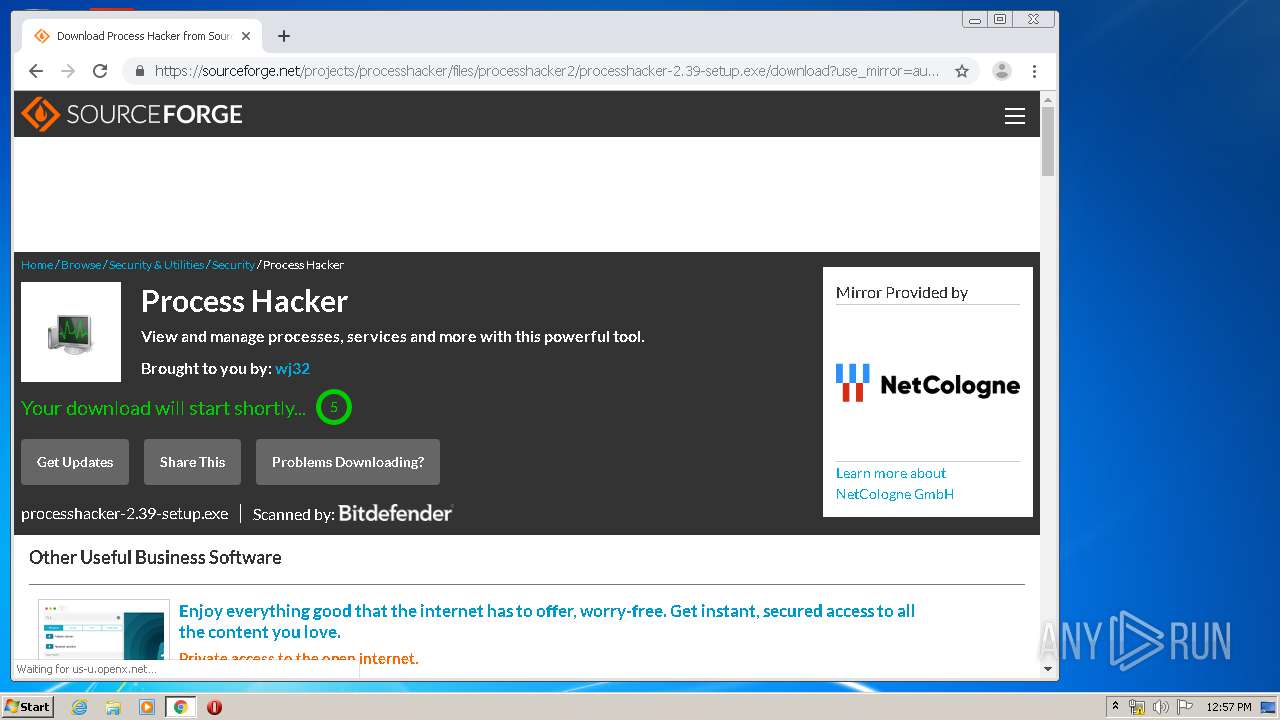
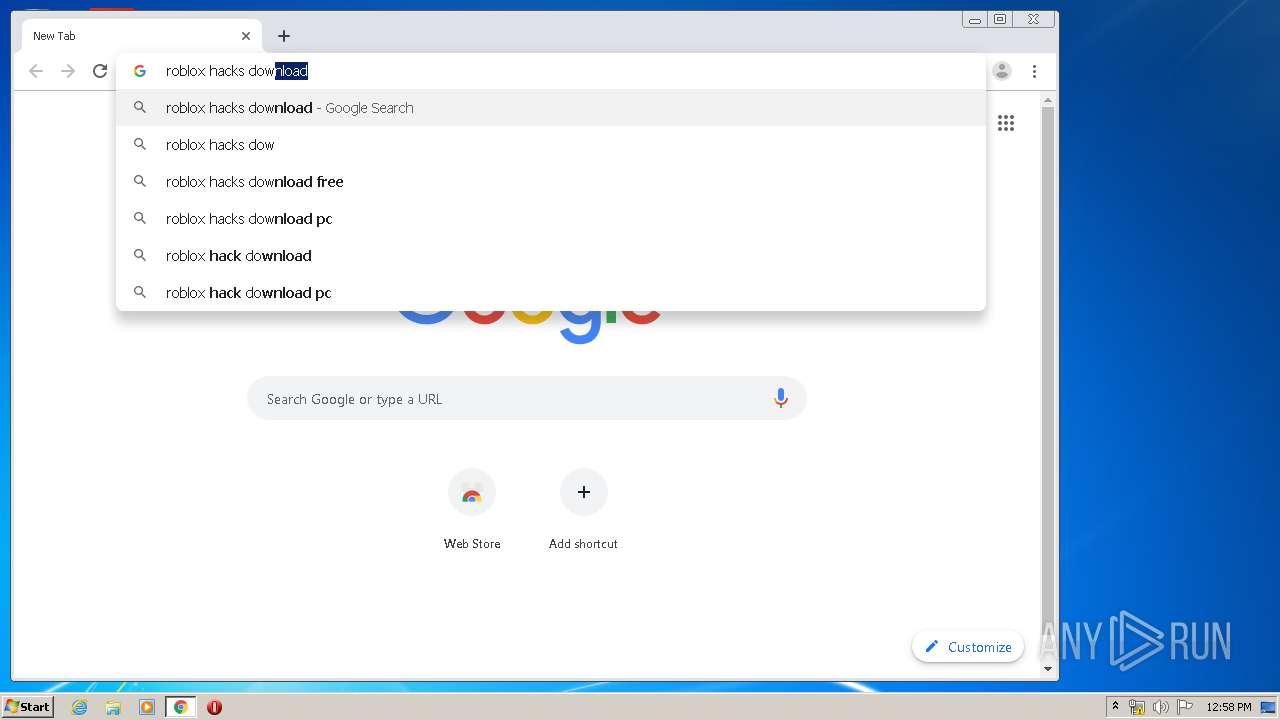
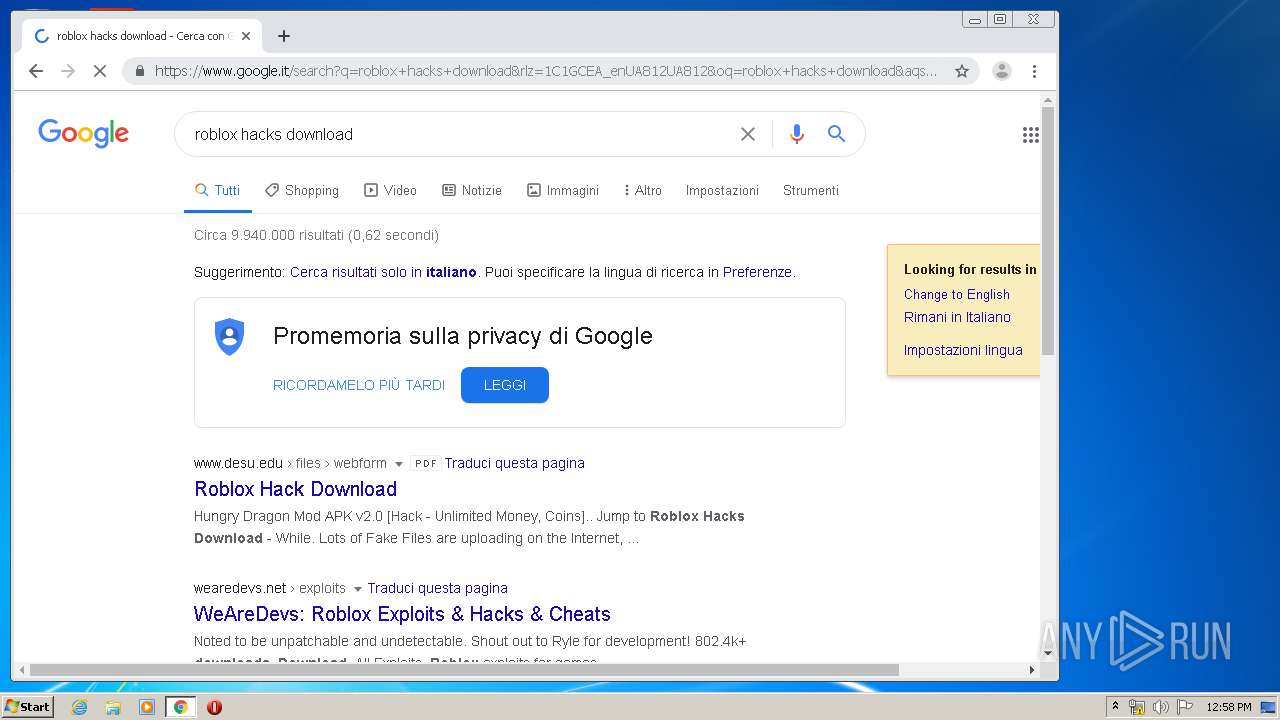
Manual execution by user
- CCleaner.exe (PID: 588)
- AcroRd32.exe (PID: 2652)
- chrome.exe (PID: 3456)
Reads the hosts file
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2636)
Application launched itself
- chrome.exe (PID: 3456)
Reads settings of System Certificates
- chrome.exe (PID: 2636)
- CCleaner.exe (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:21 21:42:21 |
| ZipCRC: | 0x0803bf86 |
| ZipCompressedSize: | 148 |
| ZipUncompressedSize: | 223 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
99
Monitored processes
58
Malicious processes
2
Suspicious processes
0
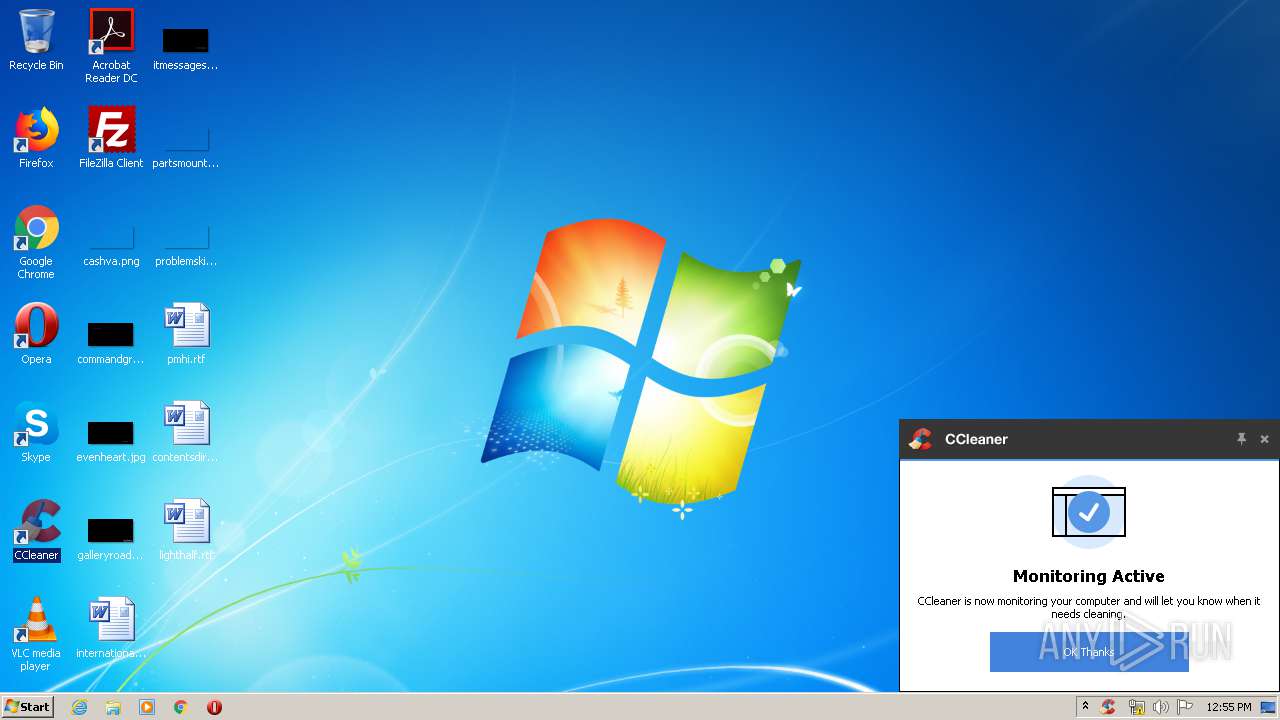
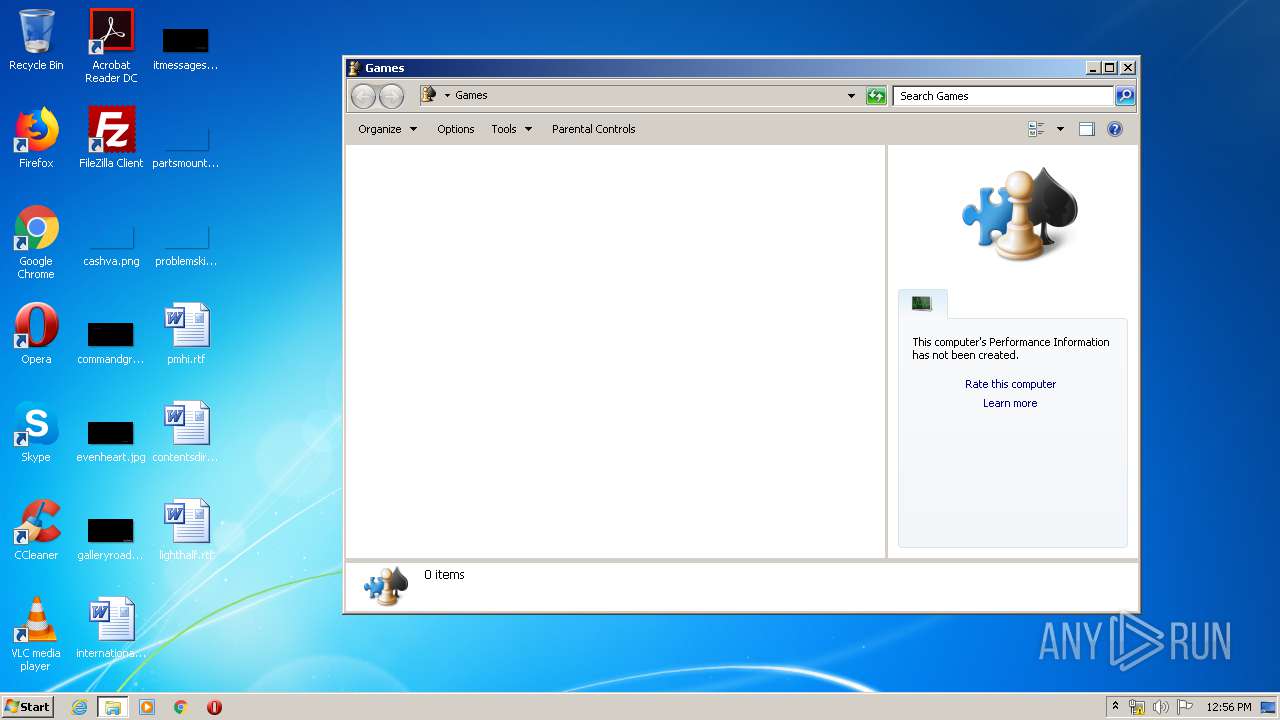
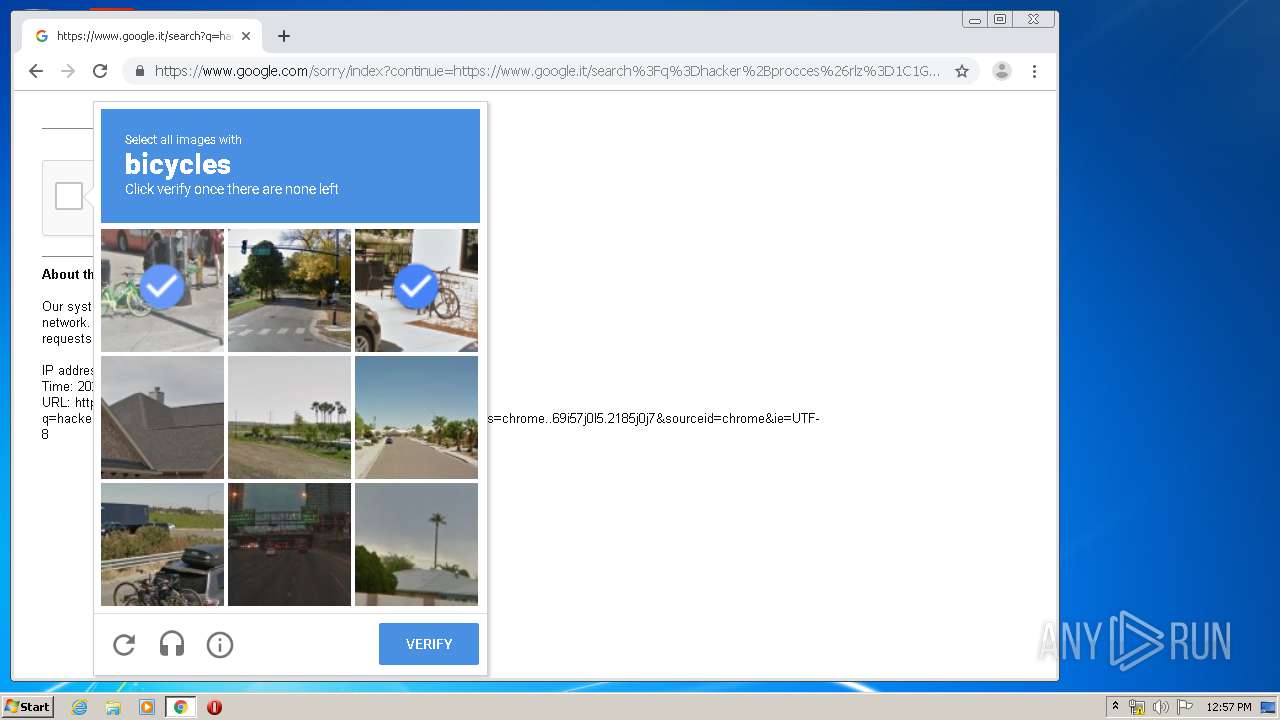
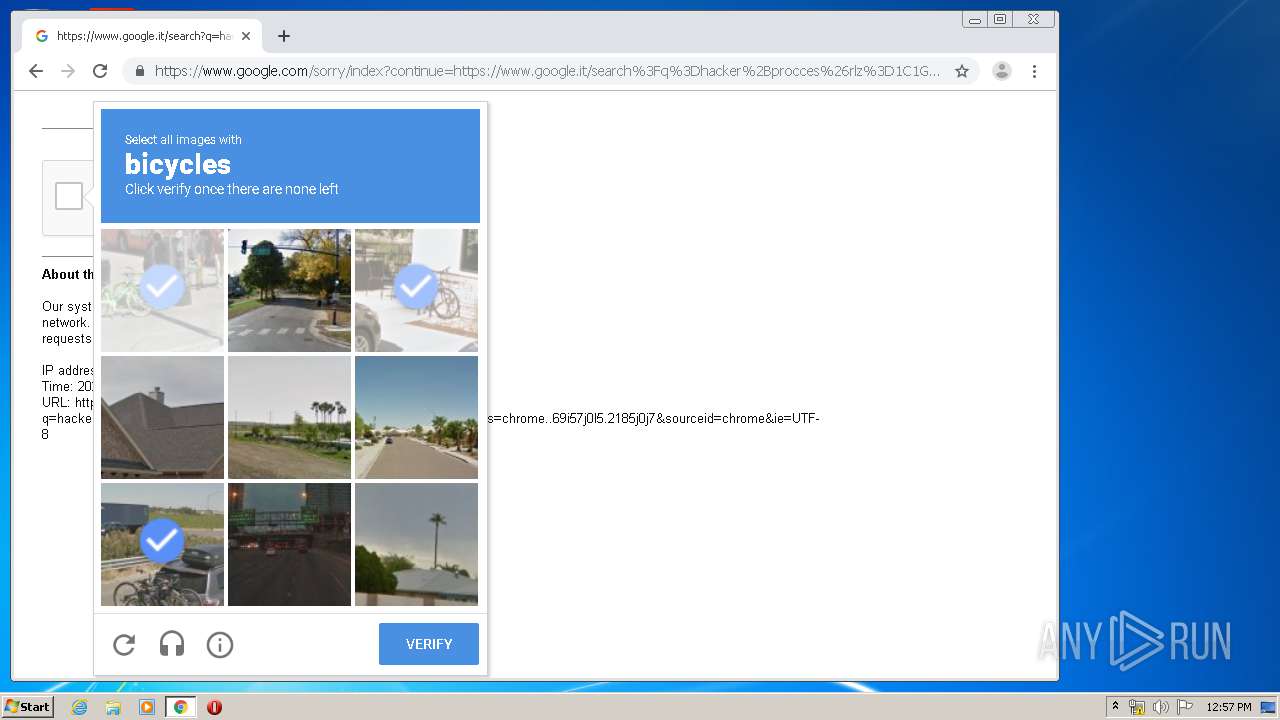
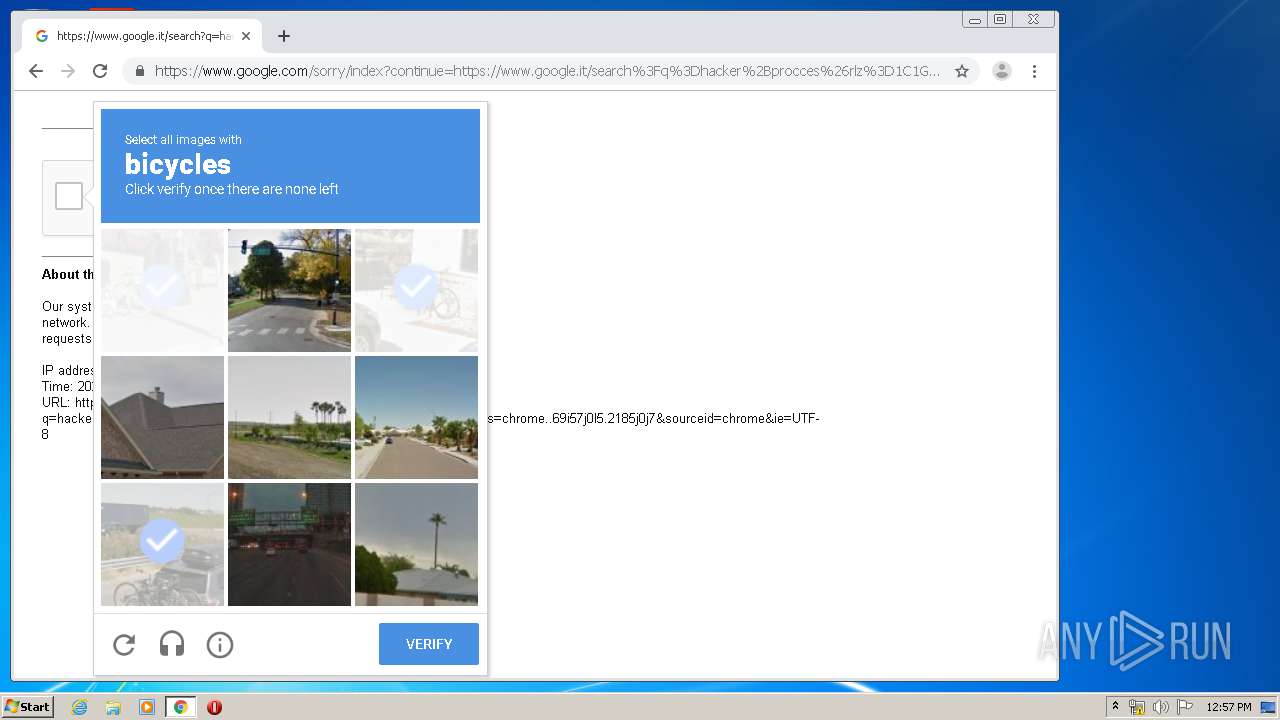
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11638146982378844349 --mojo-platform-channel-handle=3832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14072143103533855743 --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14431167724337101732 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=884585686718255013 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8193777255498253520 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5680416646062452301 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5779128699932194704 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8774317044065931970,2814348974849802562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=596894250574098456 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 474
Read events
1 472
Write events
1 996
Delete events
6
Modification events
| (PID) Process: | (1764) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | WipeFreeSpaceDrives |
Value: C:\ | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2232) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | Monitoring |
Value: 1 | |||
| (PID) Process: | (2232) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CCleaner Monitoring |
Value: "C:\Program Files\CCleaner\CCleaner.exe" /MONITOR | |||
| (PID) Process: | (2232) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | SystemMonitoring |
Value: 1 | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | CookiesToSave |
Value: *.piriform.com | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | RunICS |
Value: 0 | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | delete value | Name: | AutoICS |
Value: 1 | |||
| (PID) Process: | (2368) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
154
Text files
264
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
| 2408 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\OLDCACHE.000 | — | |
MD5:— | SHA256:— | |||
| 4036 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
| 4036 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\OLDCACHE.000 | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\tmp.edb | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\webappsstore.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9JS7281SYZ07P98E5LM2.temp | — | |
MD5:— | SHA256:— | |||
| 2368 | CCleaner.exe | C:\Users\admin\AppData\Local\Temp\Cab5272.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
127
DNS requests
89
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2368 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
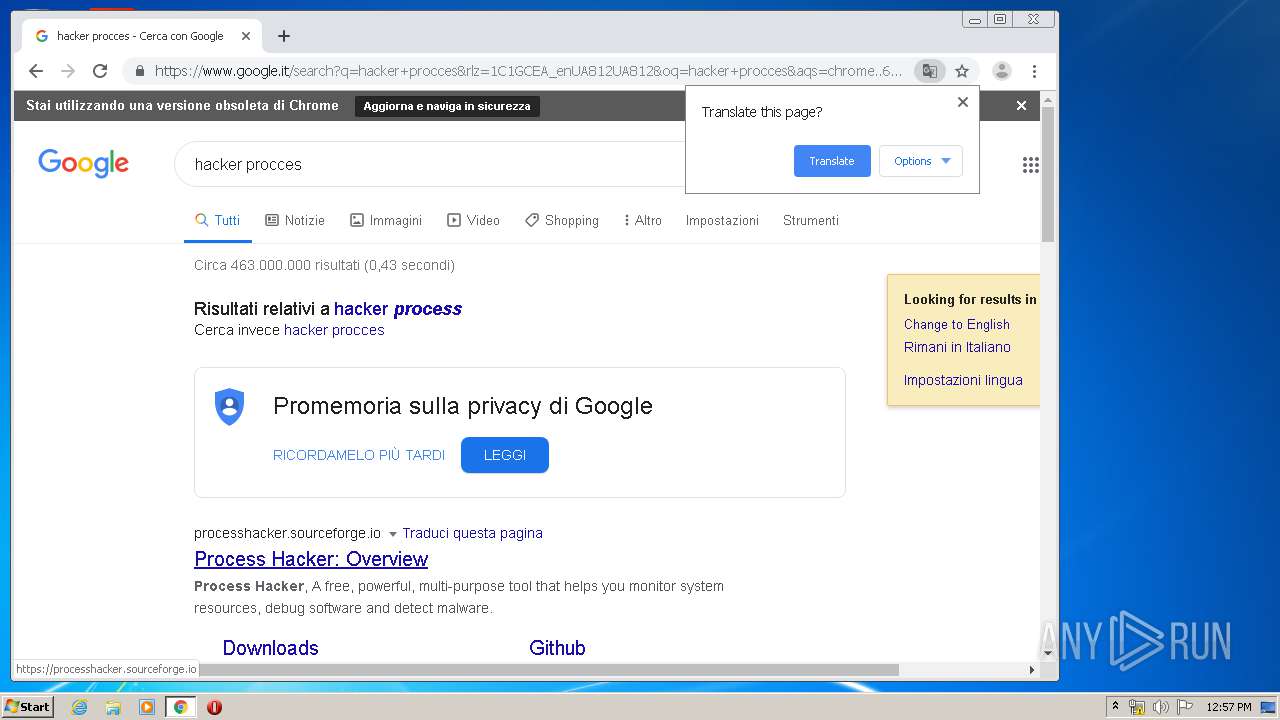
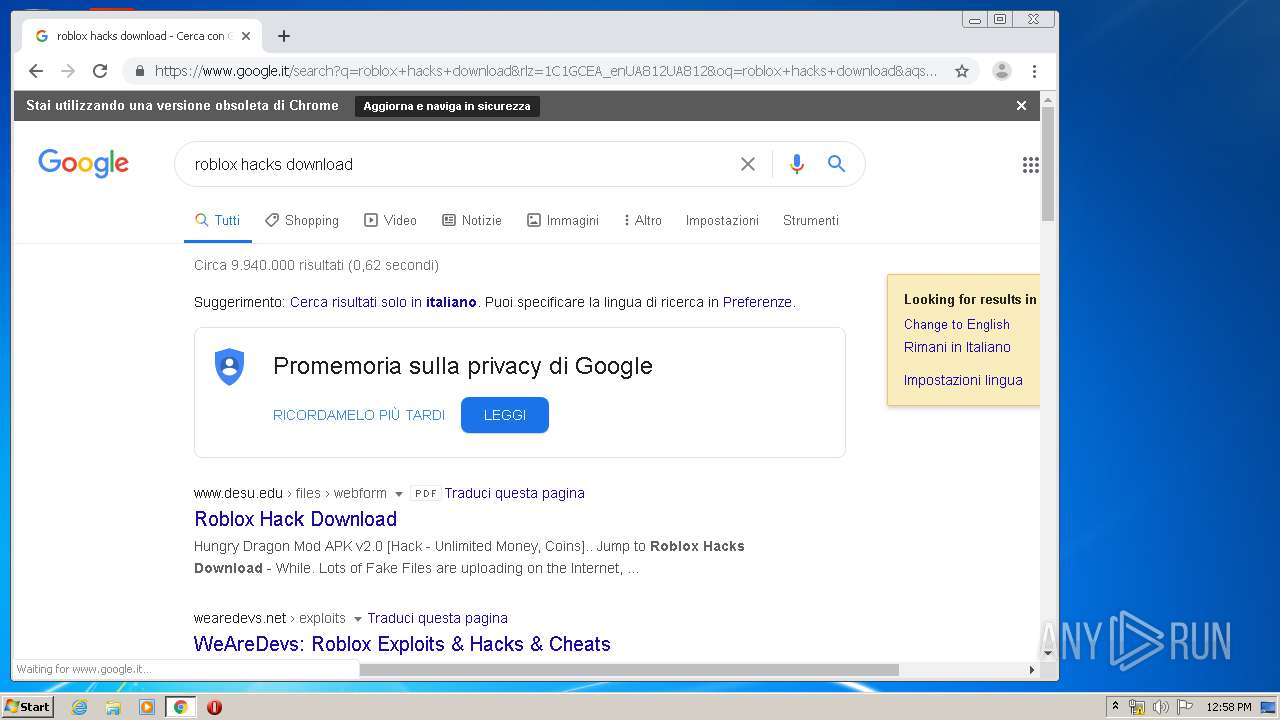
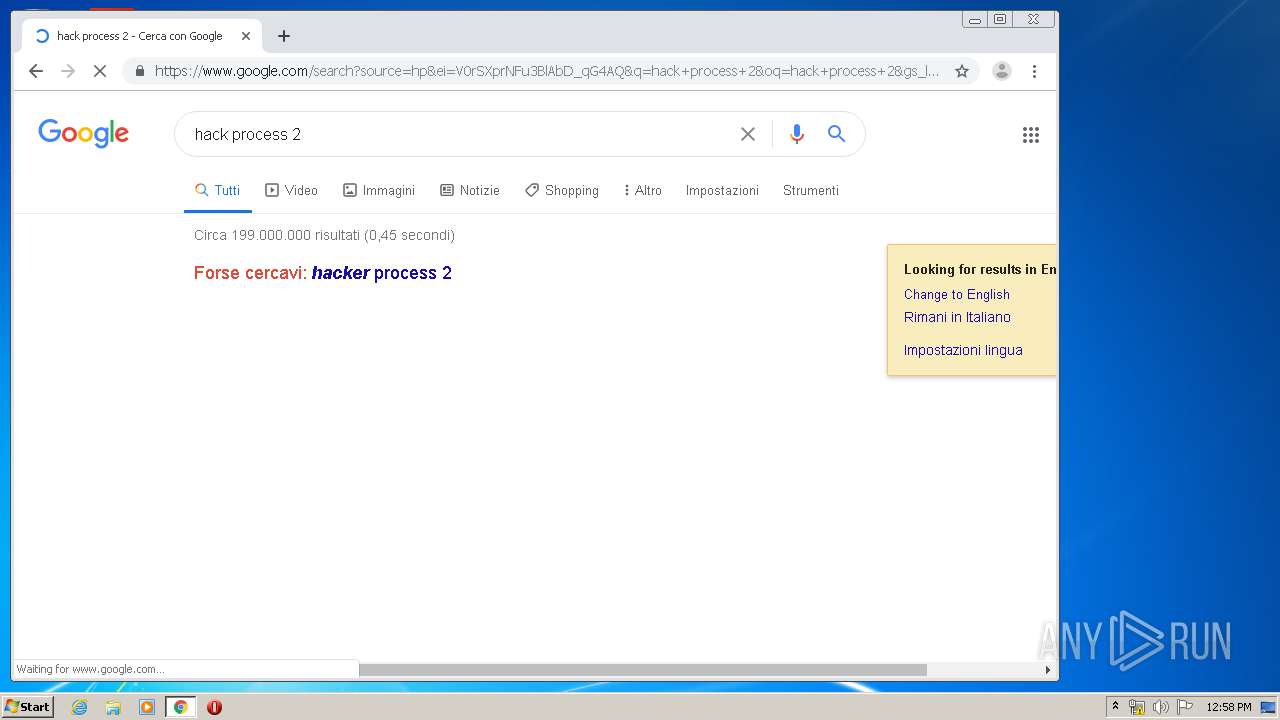
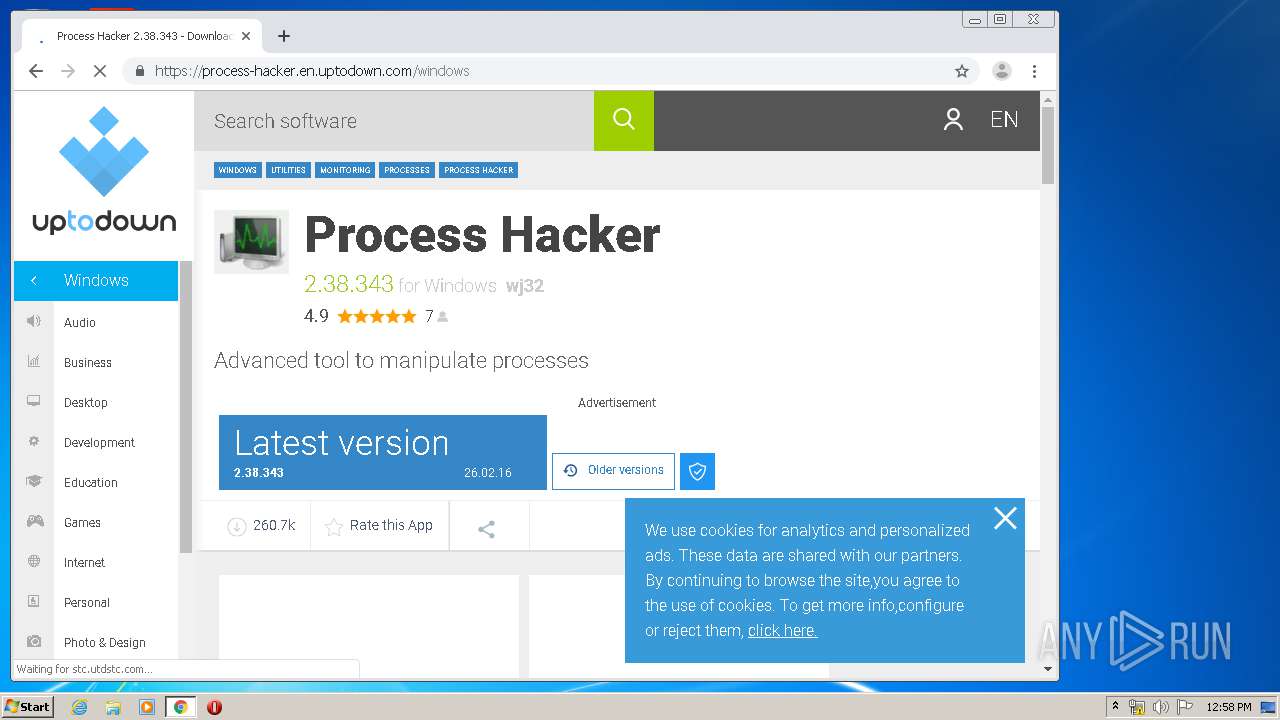
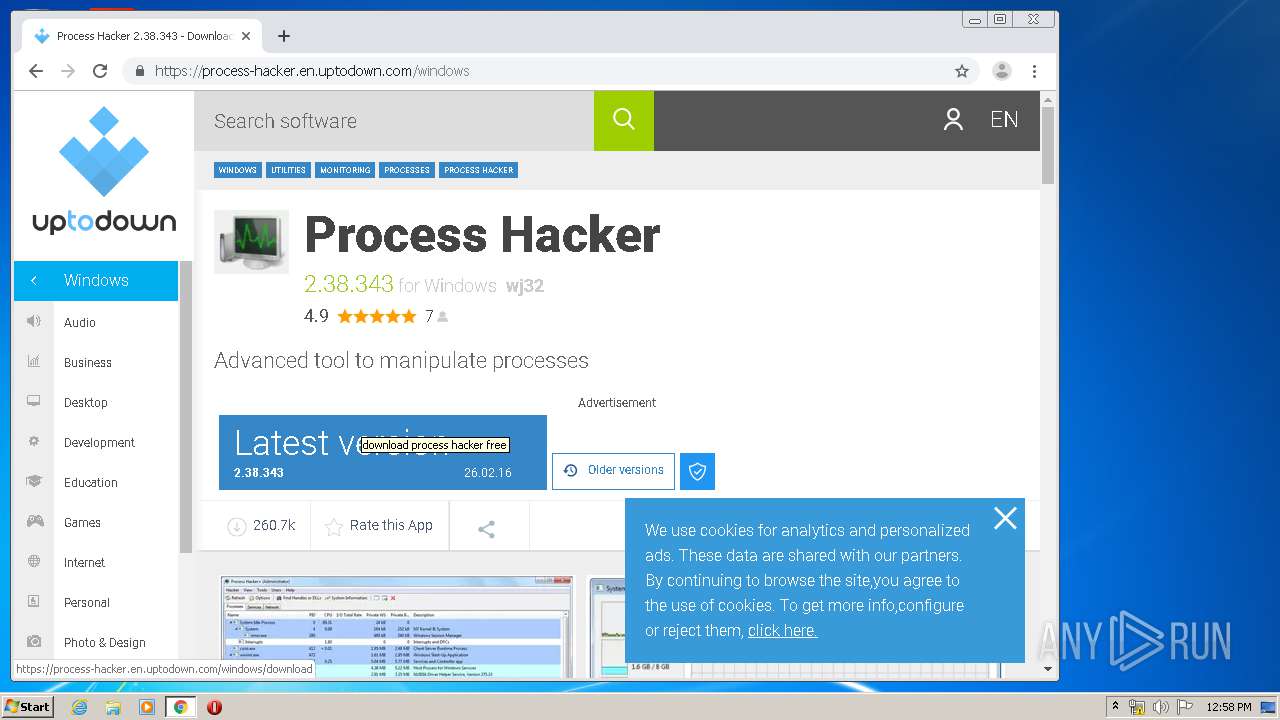
2636 | chrome.exe | GET | 302 | 5.149.248.70:80 | http://eseclist.com/synthesizer/hysterical?impacted=pericarditis/ZG93bmxvYWR8Yng4TXpOM2JUTTFmSHd4TlRnMk1URTBNek13Zkh3eU16STNmSHdvUlU1SFNVNUZLU0JFY25Wd1lXd2dXMFpwYkdVZ1ZYQnNiMkZrWFE.livers=Um9ibG94IEhhY2sgRG93bmxvYWQUm9=oregonians | NL | — | — | malicious |
2636 | chrome.exe | GET | 301 | 172.227.120.75:80 | http://img.utdstc.com/avatar/defaultavatar.png:xs | US | — | — | whitelisted |
2636 | chrome.exe | GET | 301 | 172.227.120.75:80 | http://img.utdstc.com/avatar/avatar-2925134-6df.jpg:xs | US | — | — | whitelisted |
2636 | chrome.exe | GET | 301 | 172.227.120.75:80 | http://img.utdstc.com/avatar/avatar-3485909-b2c.jpg:xs | US | — | — | whitelisted |
2636 | chrome.exe | GET | 301 | 172.227.120.75:80 | http://img.utdstc.com/avatar/avatar-2985353-d4a.jpg:xs | US | — | — | whitelisted |
2368 | CCleaner.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
2636 | chrome.exe | GET | 200 | 2.21.78.252:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
2368 | CCleaner.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2636 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2636 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
2368 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
2368 | CCleaner.exe | 151.101.2.202:443 | www.ccleaner.com | Fastly | US | suspicious |
2368 | CCleaner.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
2368 | CCleaner.exe | 151.101.2.109:443 | license.piriform.com | Fastly | US | suspicious |
2368 | CCleaner.exe | 151.101.2.109:80 | license.piriform.com | Fastly | US | suspicious |
2636 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.piriform.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
license.piriform.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |