| File name: | flvpn.php |
| Full analysis: | https://app.any.run/tasks/f410ce8c-0ca0-47d5-afac-356eb9c97c3e |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 22:35:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 02C2DF39C828BF051A5697CE4DECE67F |
| SHA1: | 2C5CA293BB5C29C72F7CDAB9AA154A48DAAD4ECE |
| SHA256: | 1A096F26514F116DA0BAA88639A22BEA1BB957486E4508A4CB090DD1912B8B97 |
| SSDEEP: | 98304:xstLFgbNkWwcsZofJYbgnE9o2zW+Sg62JCTB6XS+sBWtKDWgwHopp+LHEpIqKQ:xstKNEyfagE+GW3g62JsI8oKaopckz |
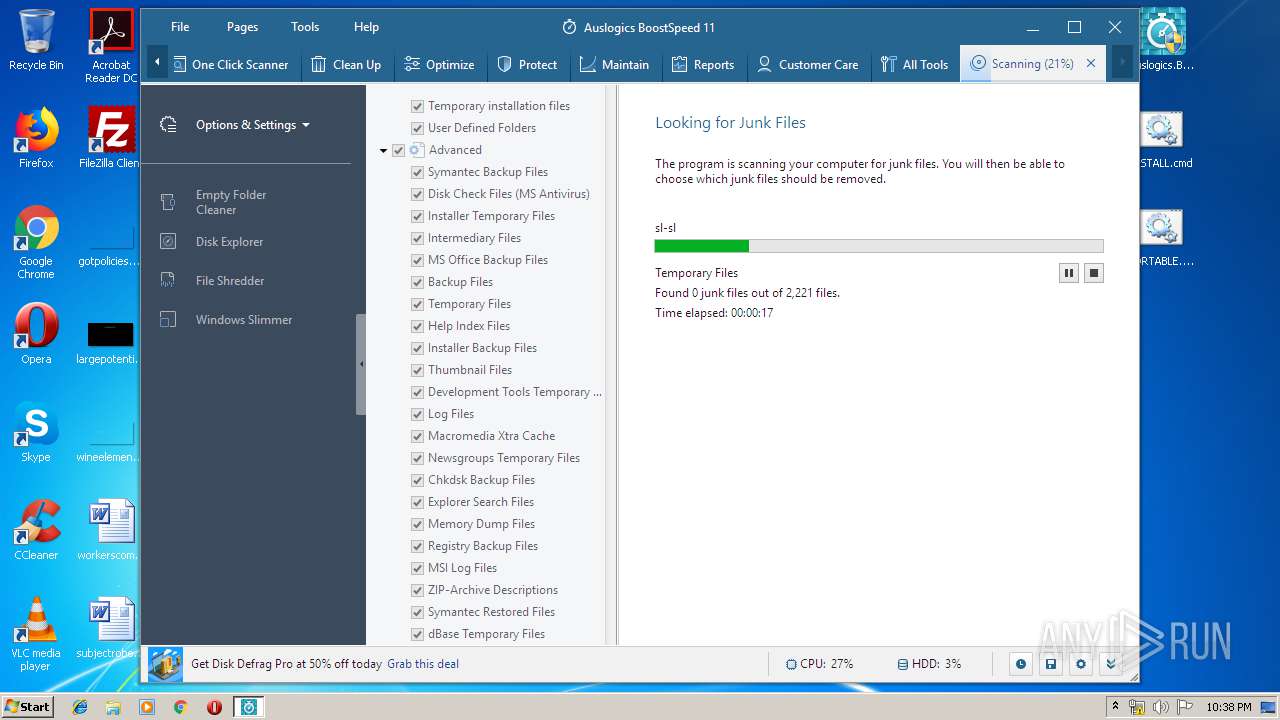
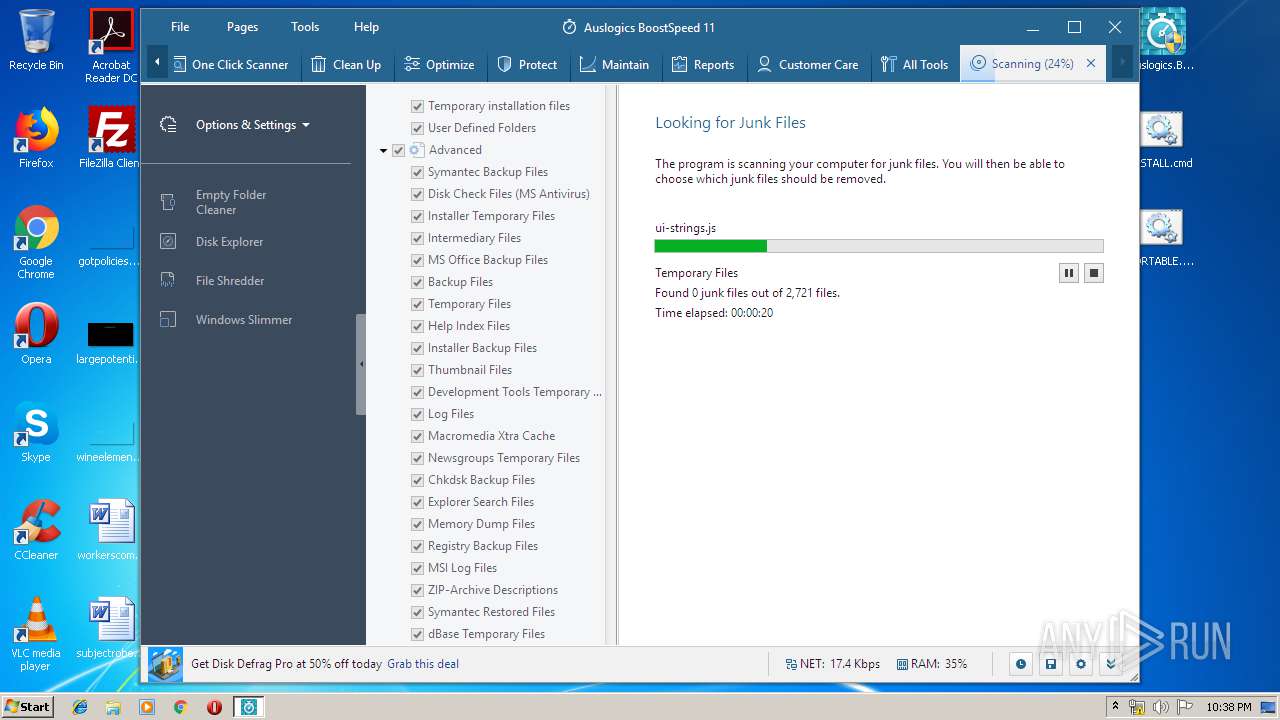
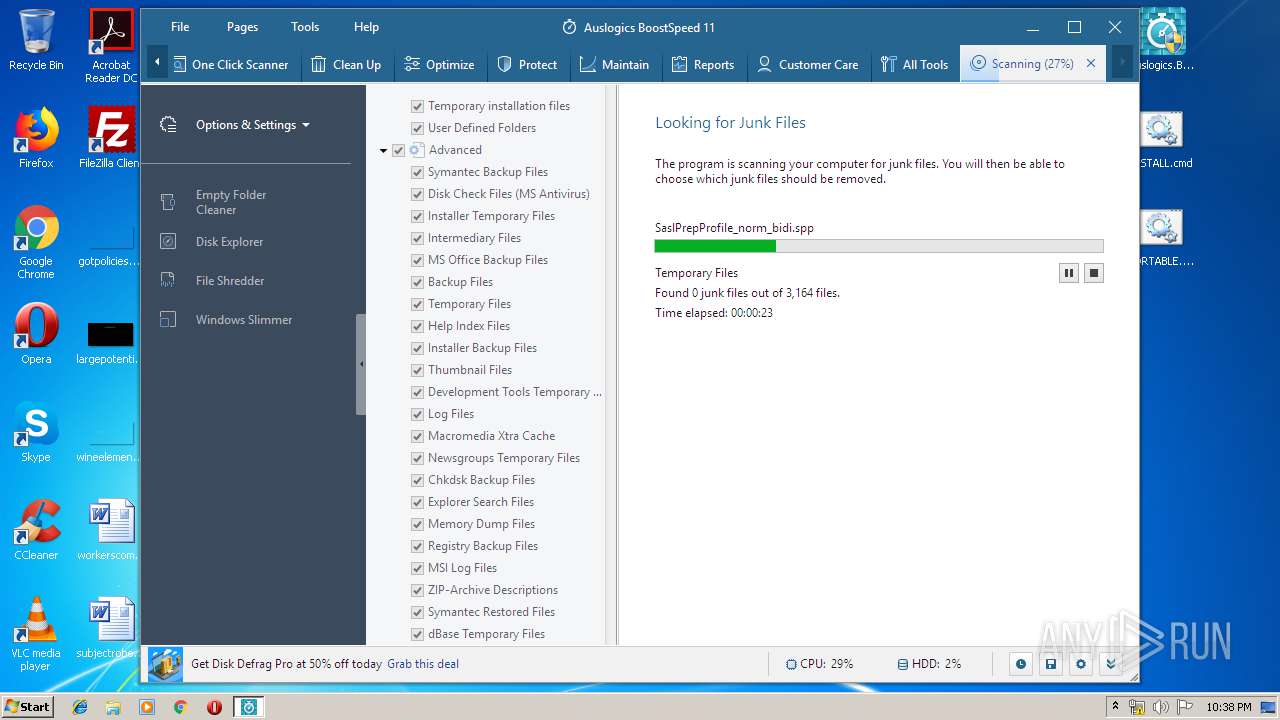
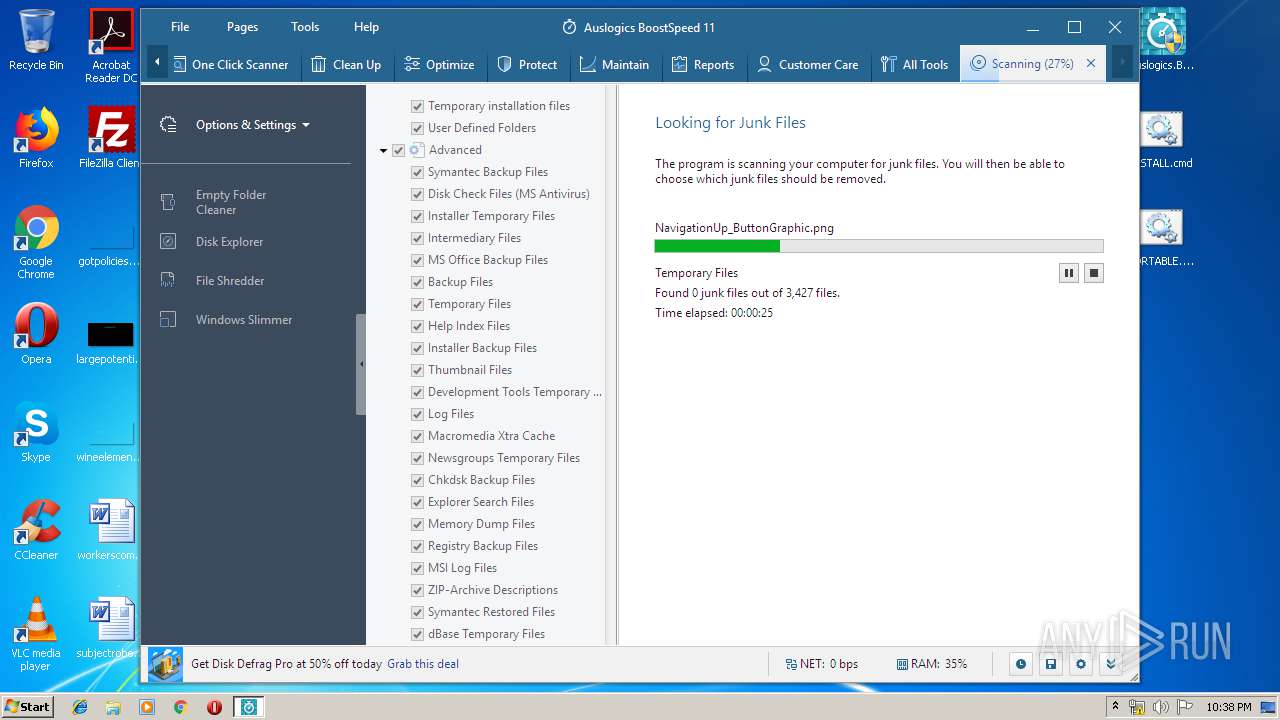
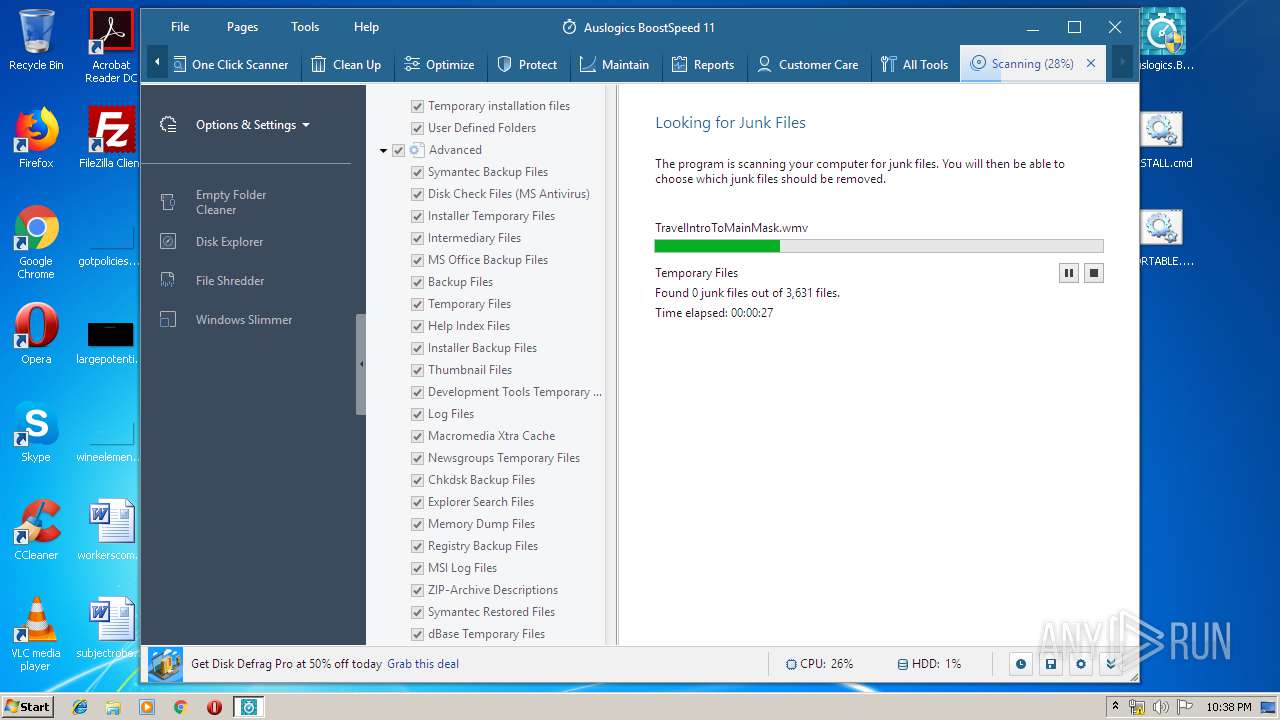
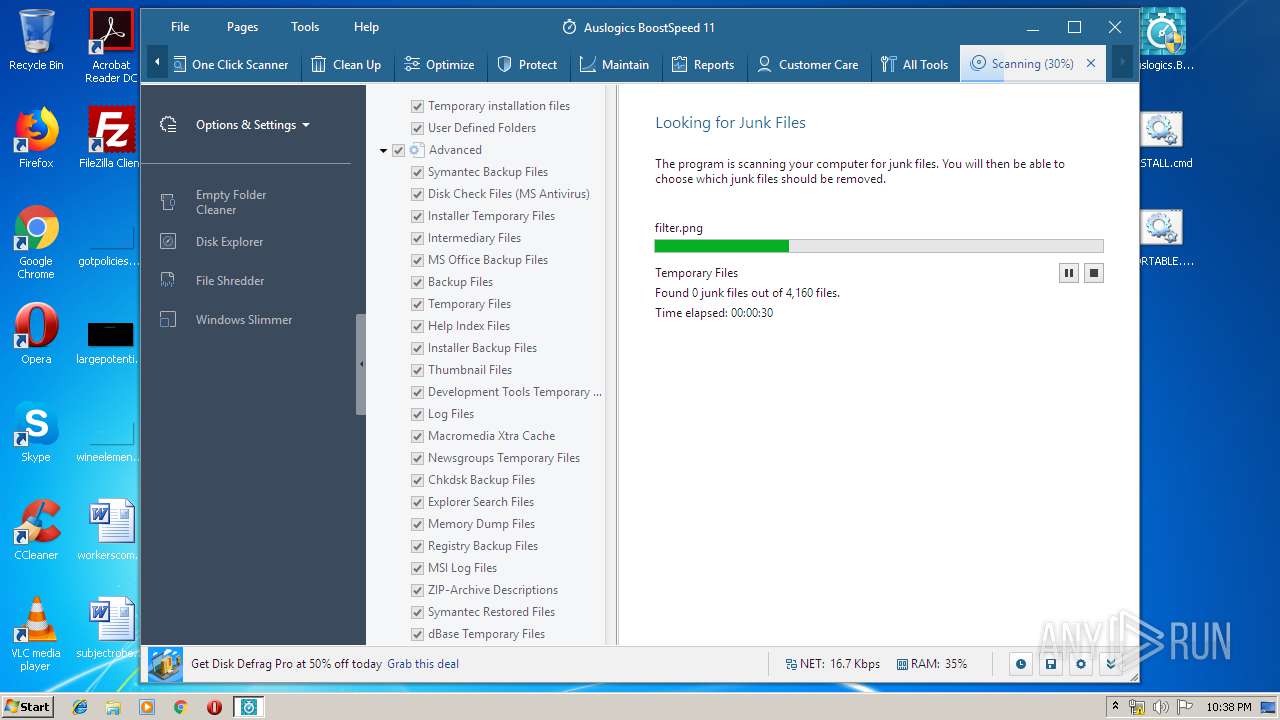
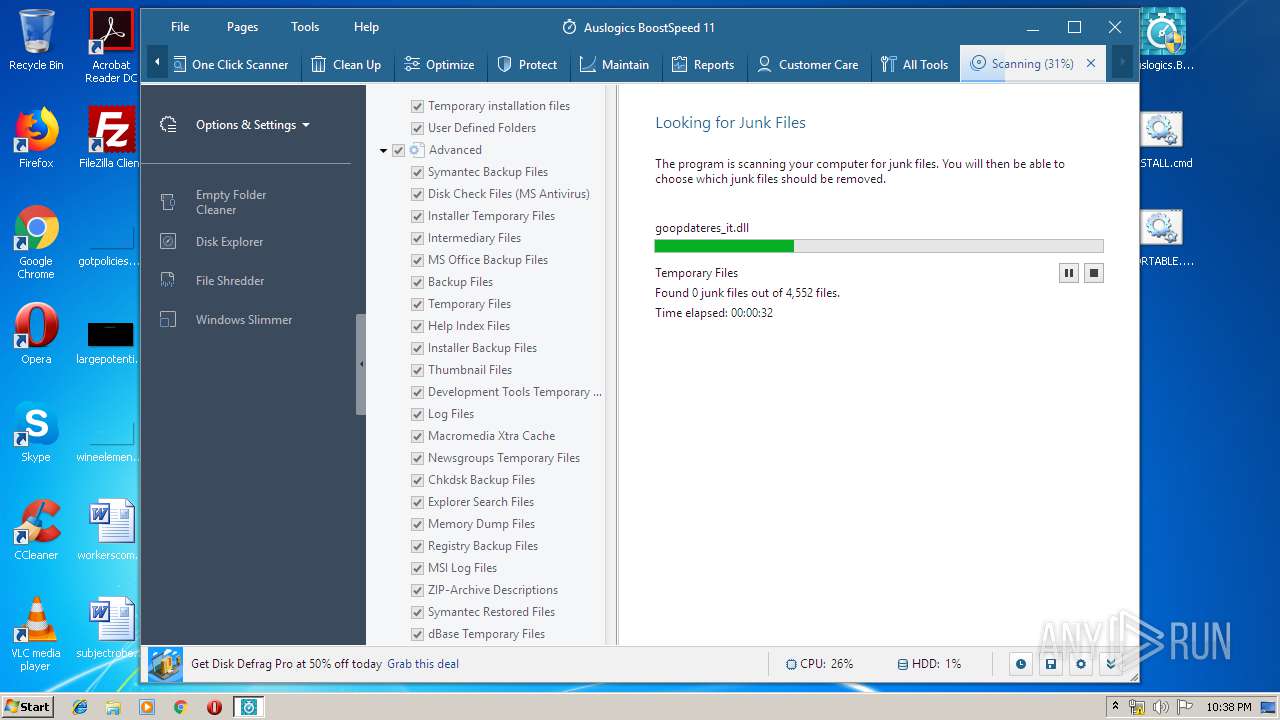
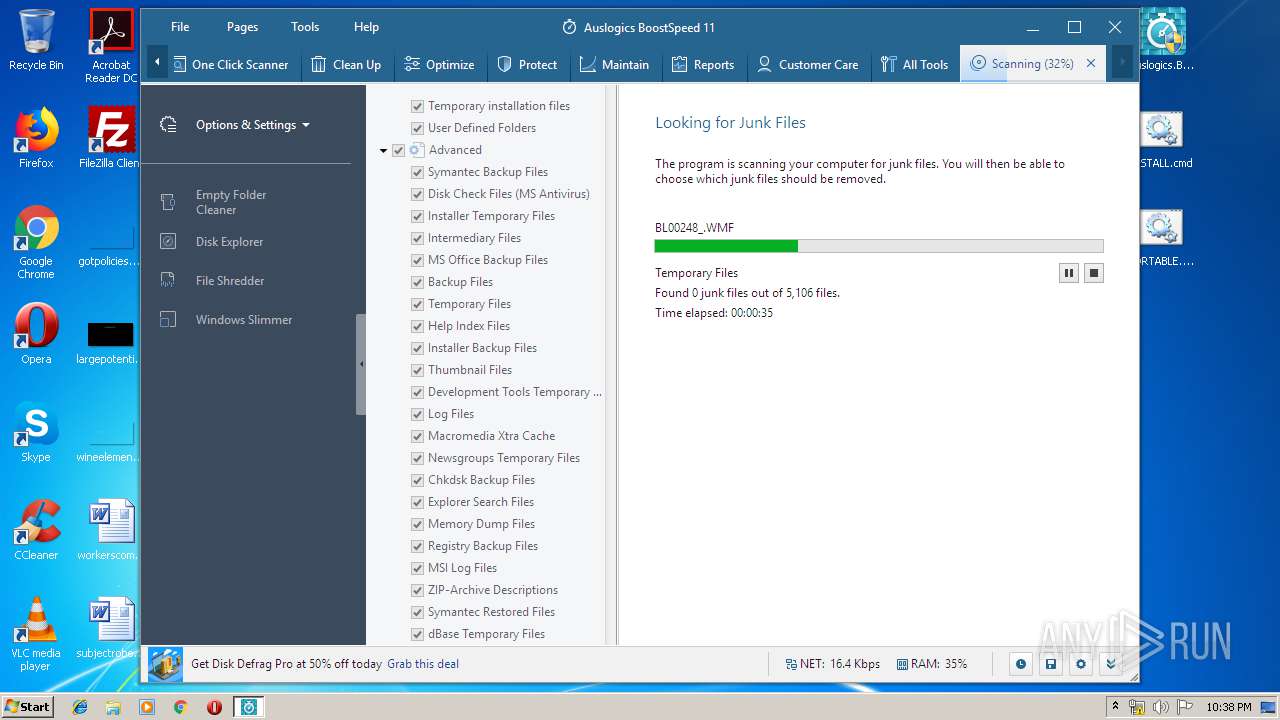
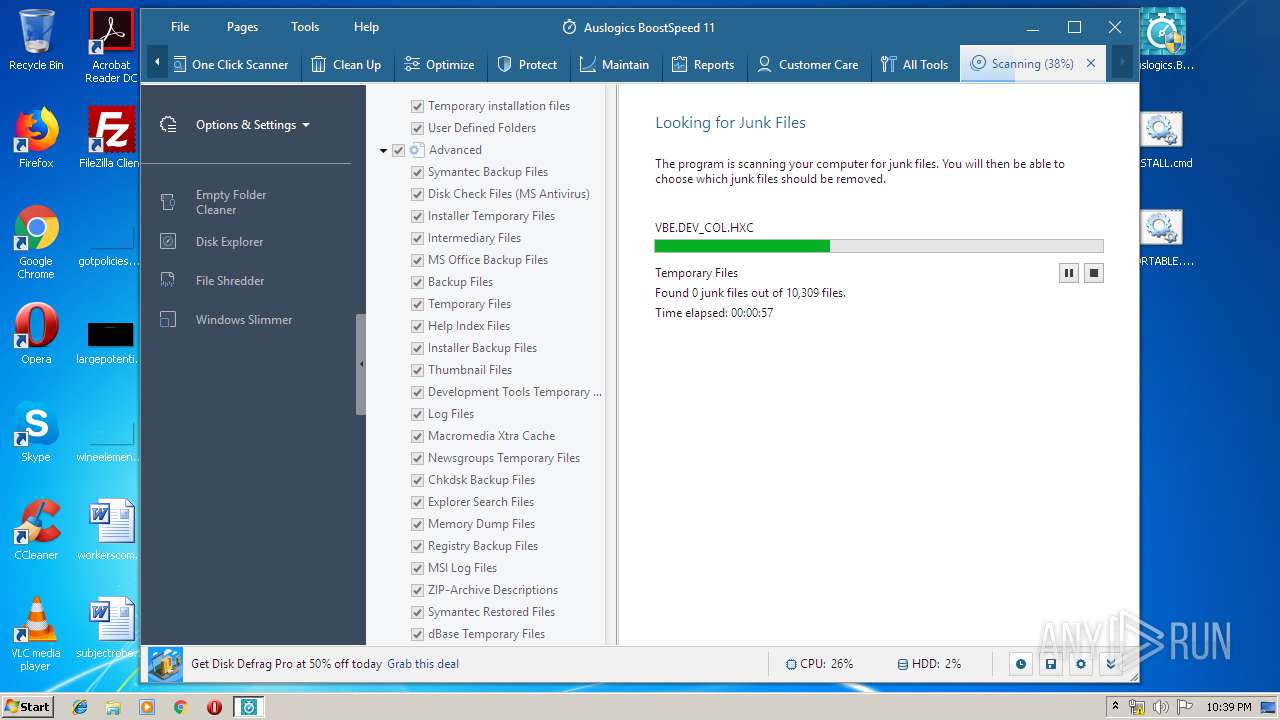
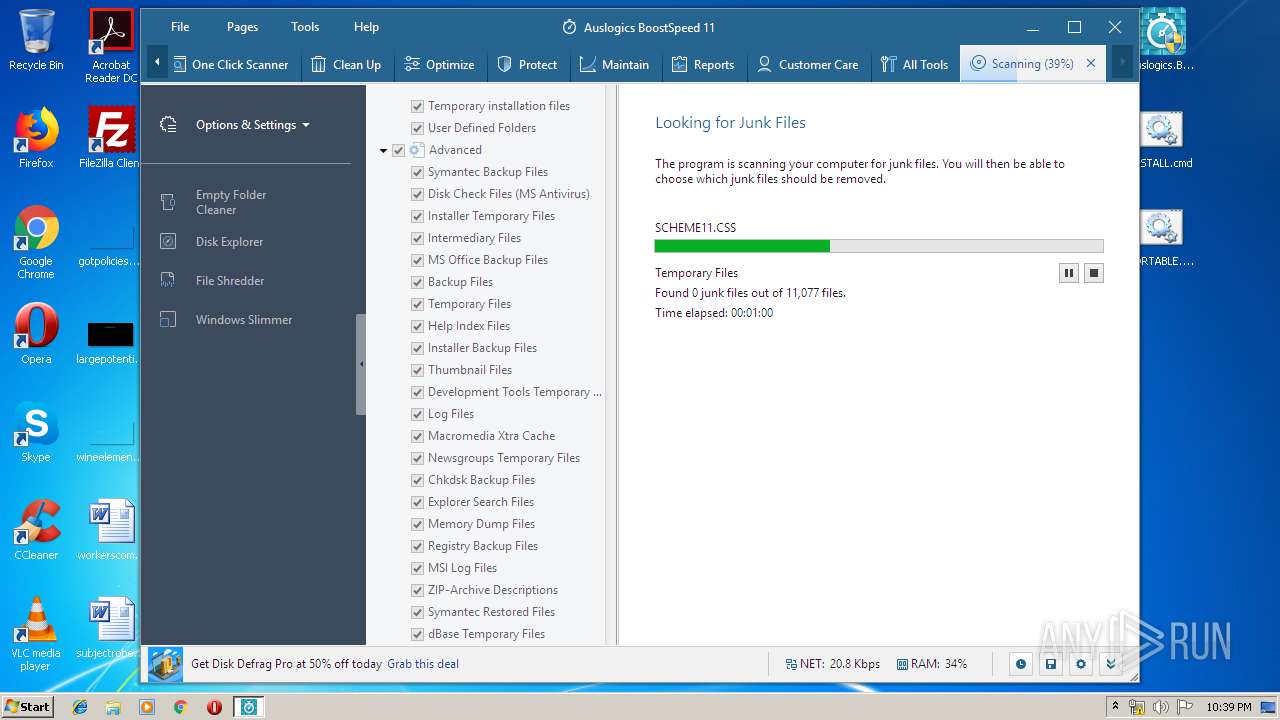
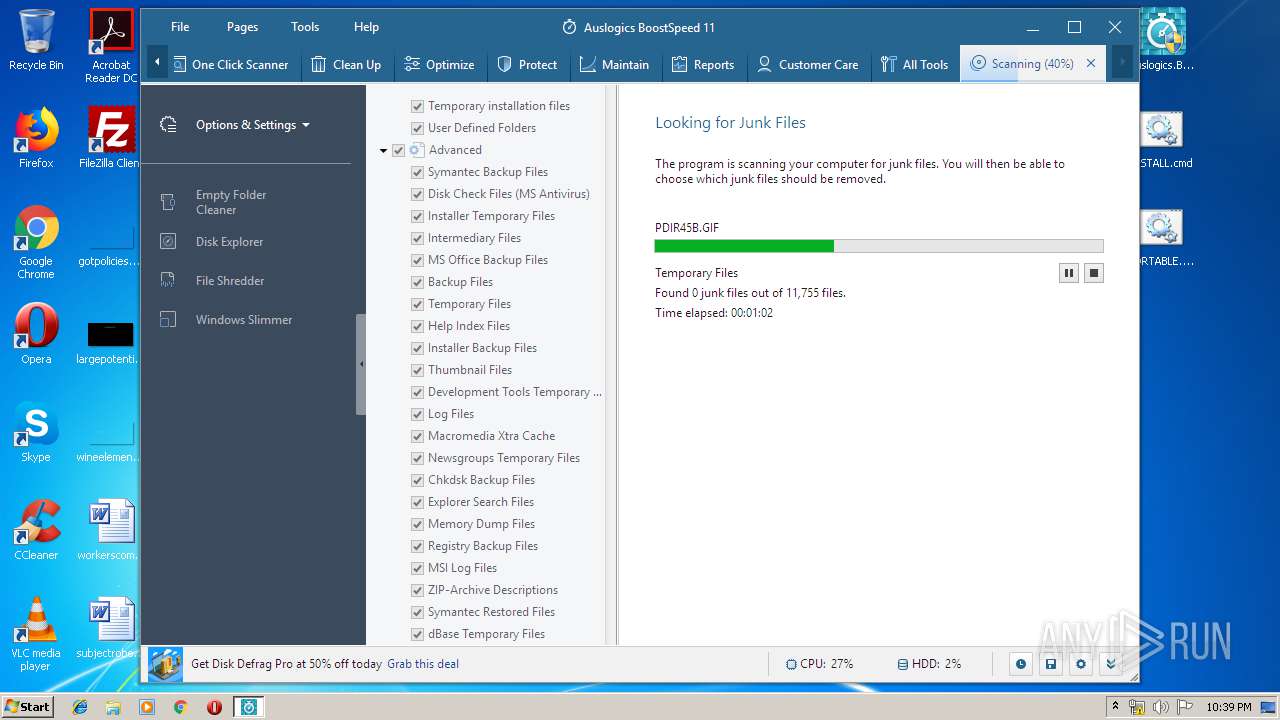
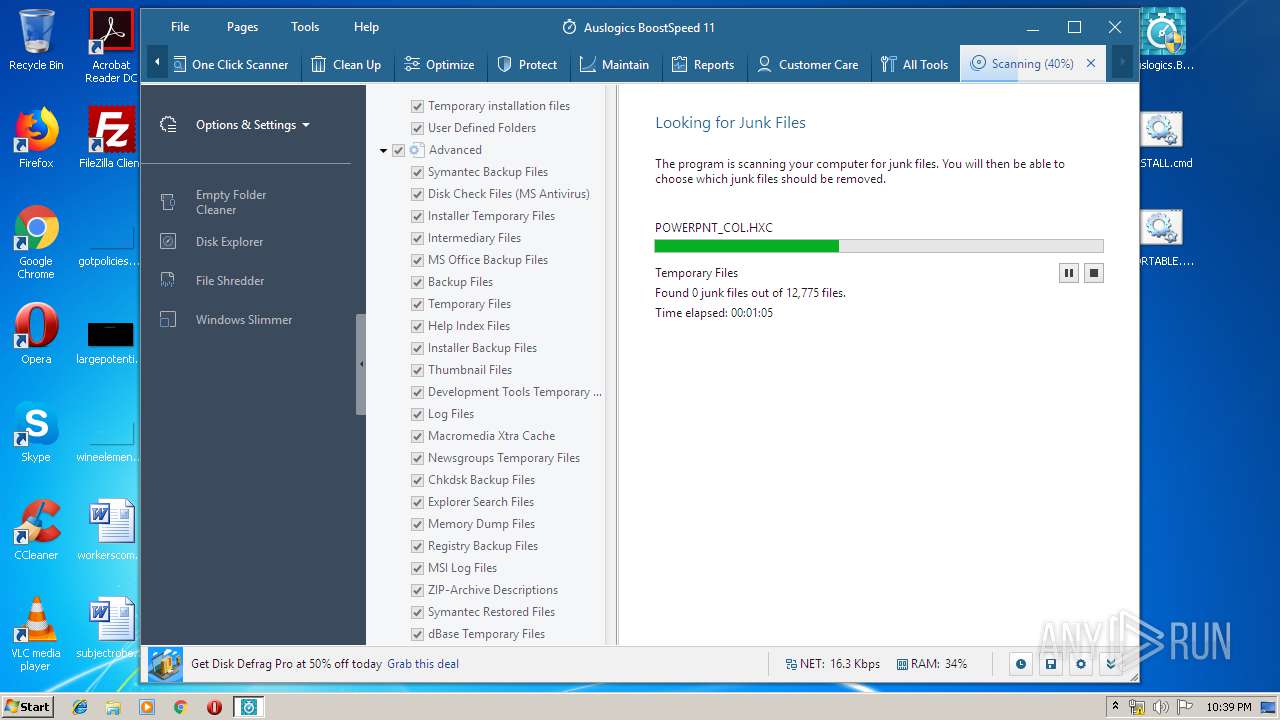
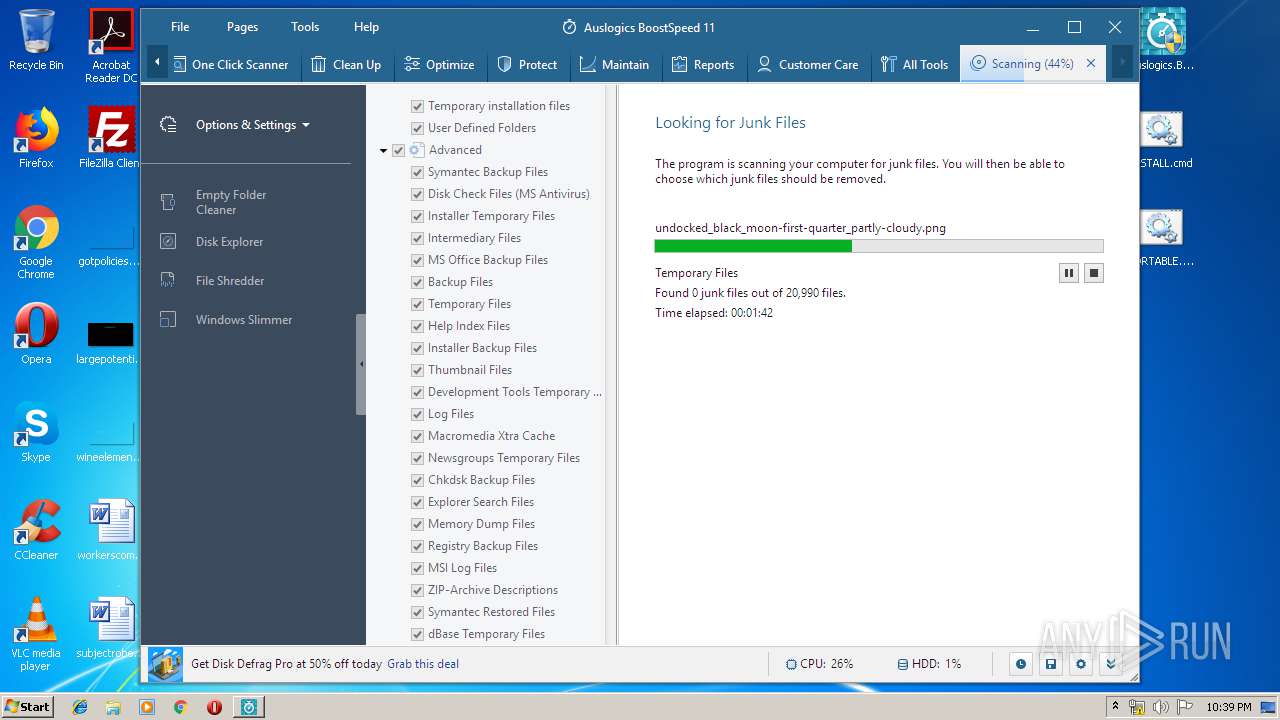
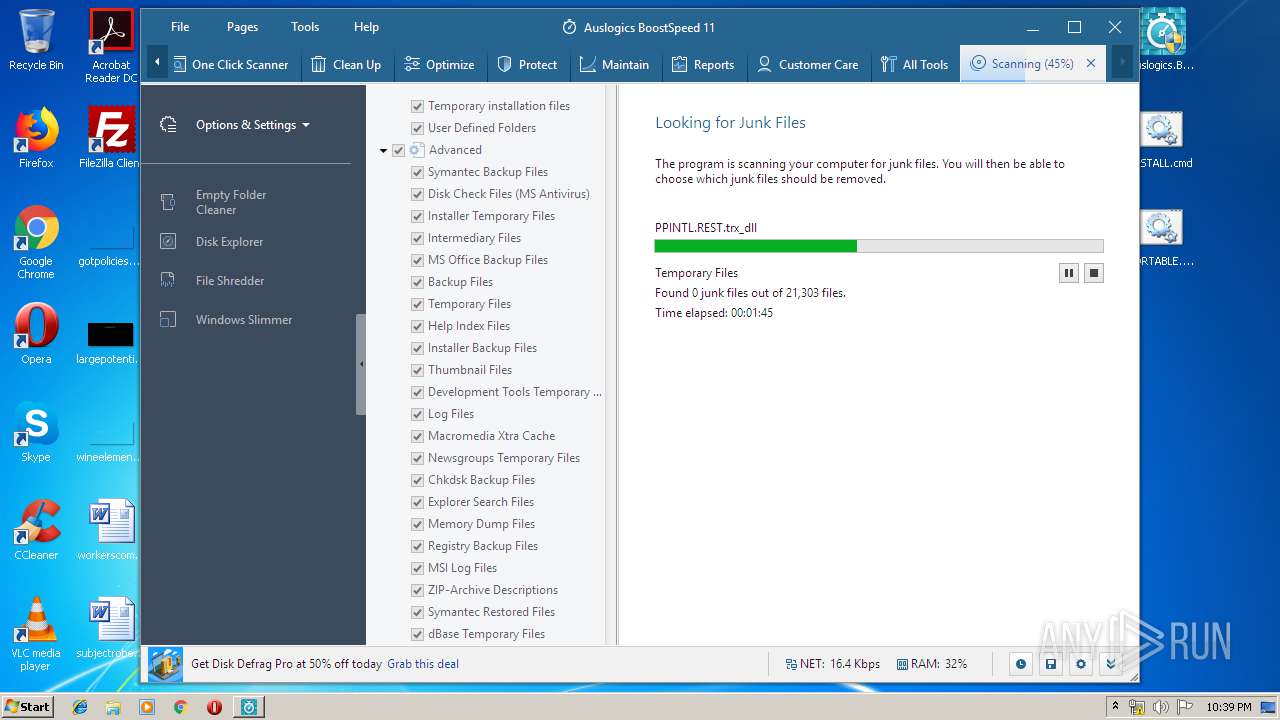
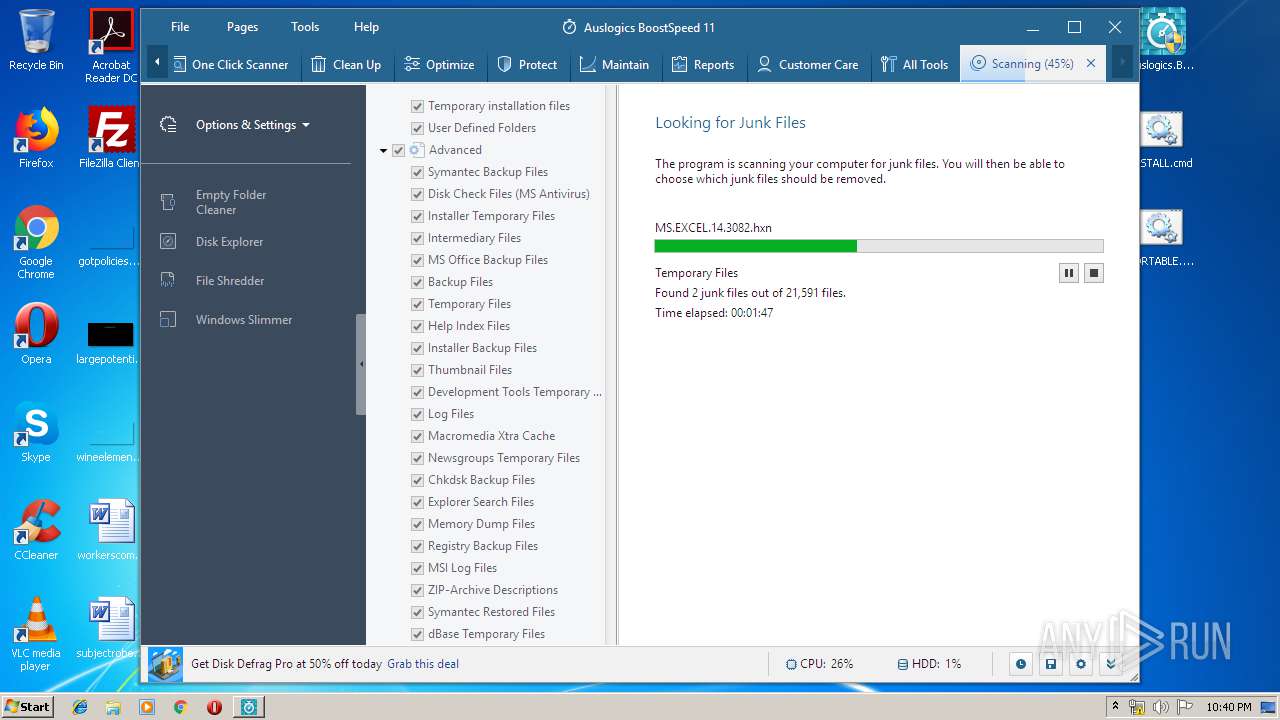
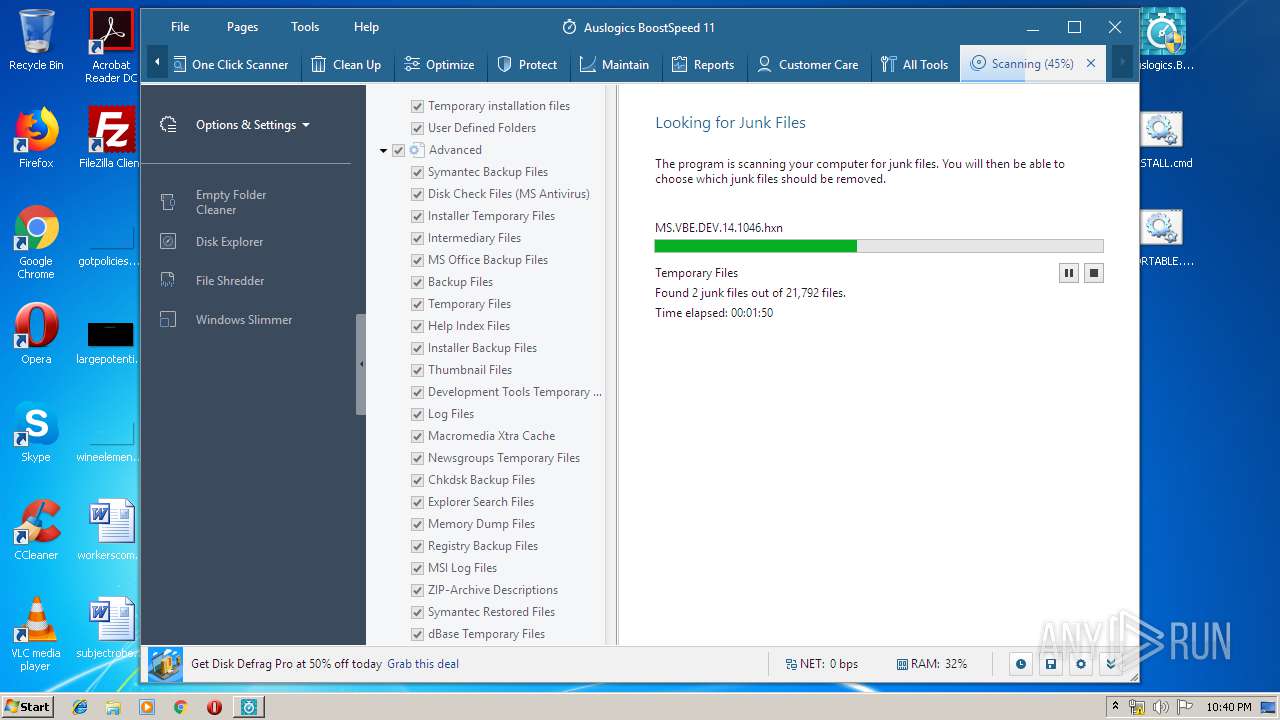
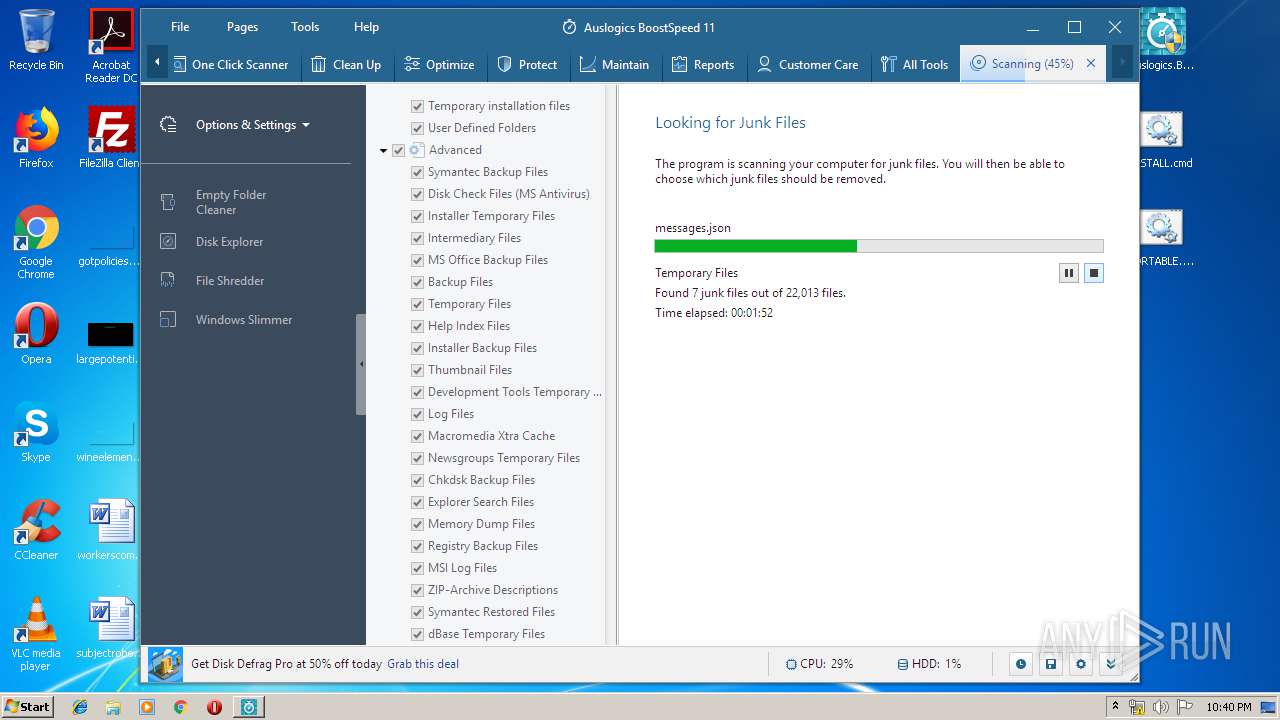
MALICIOUS
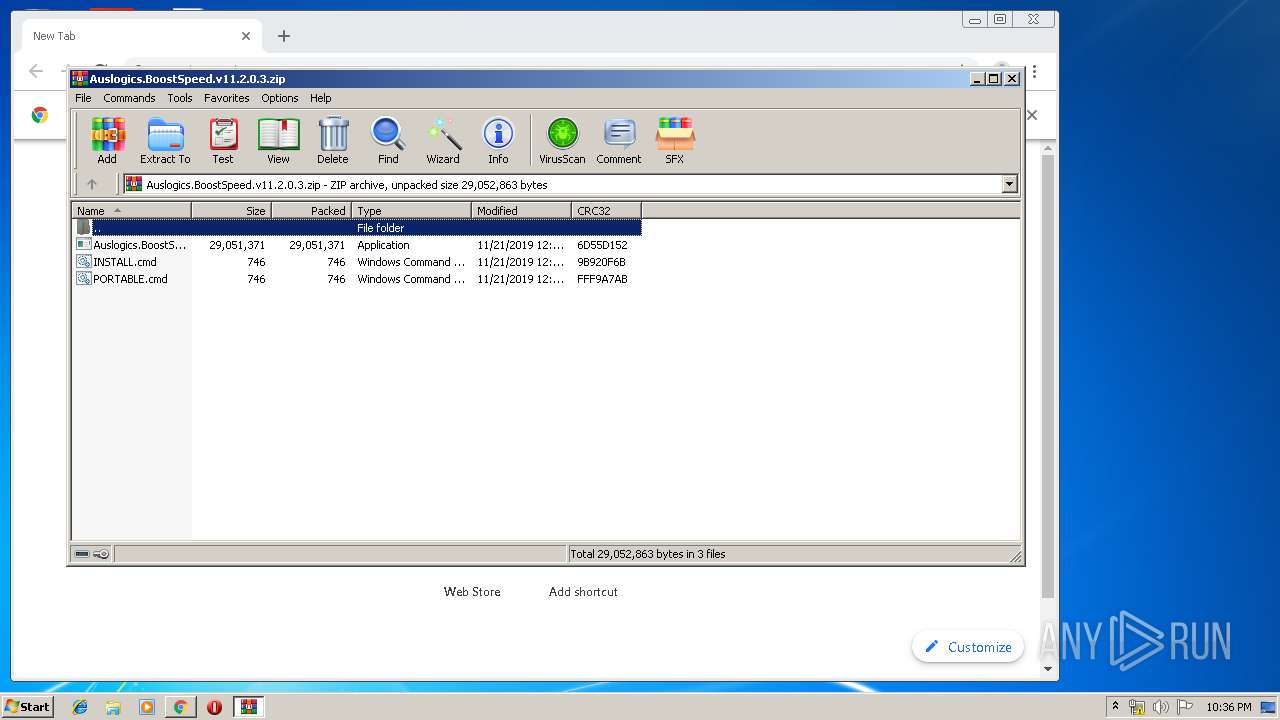
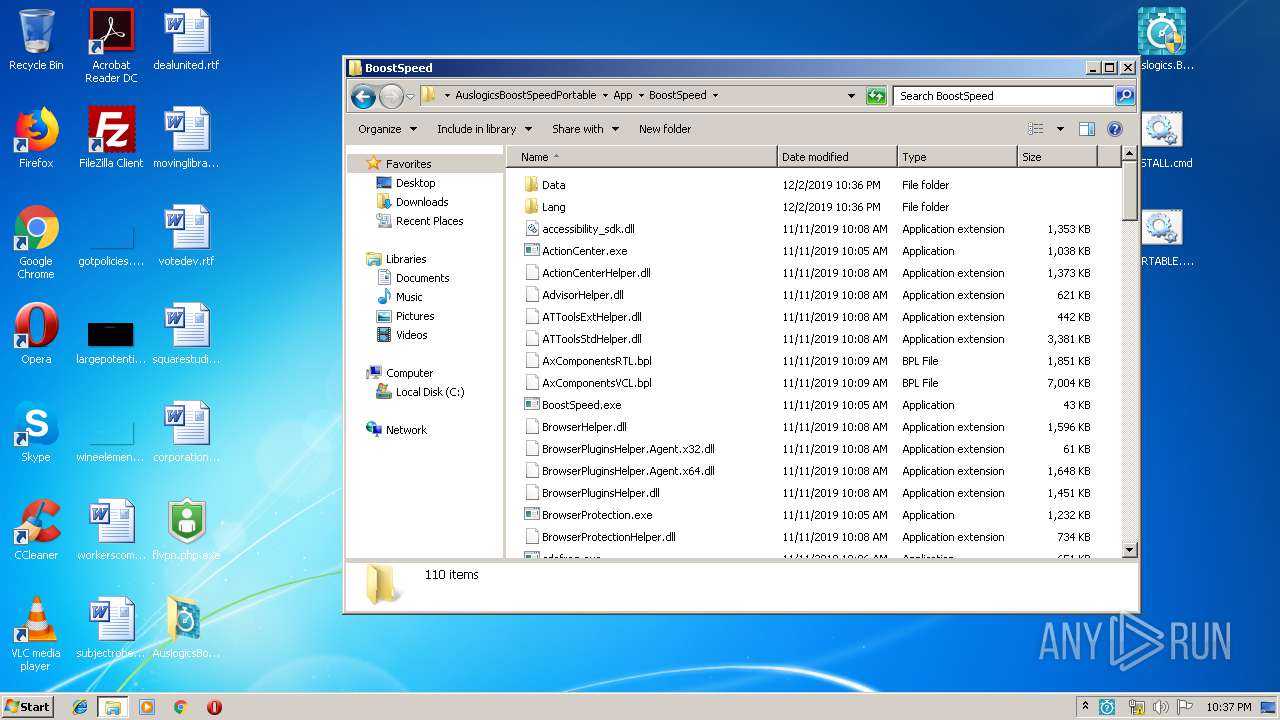
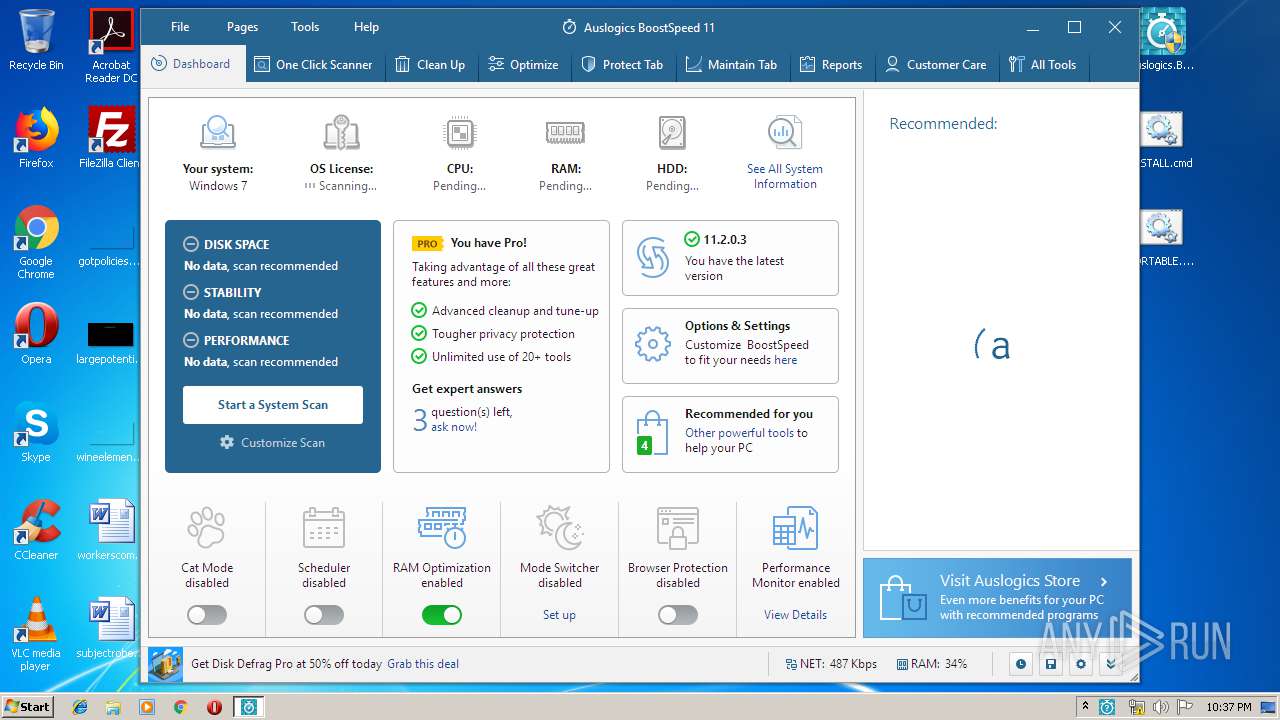
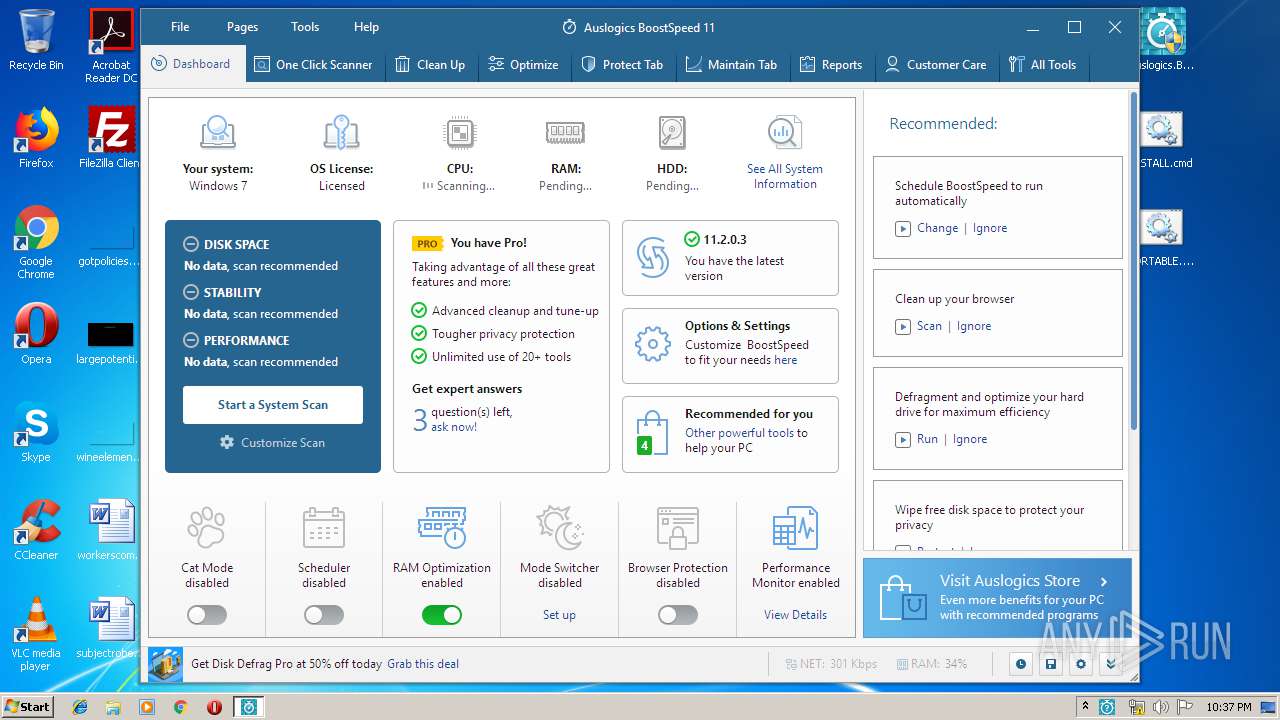
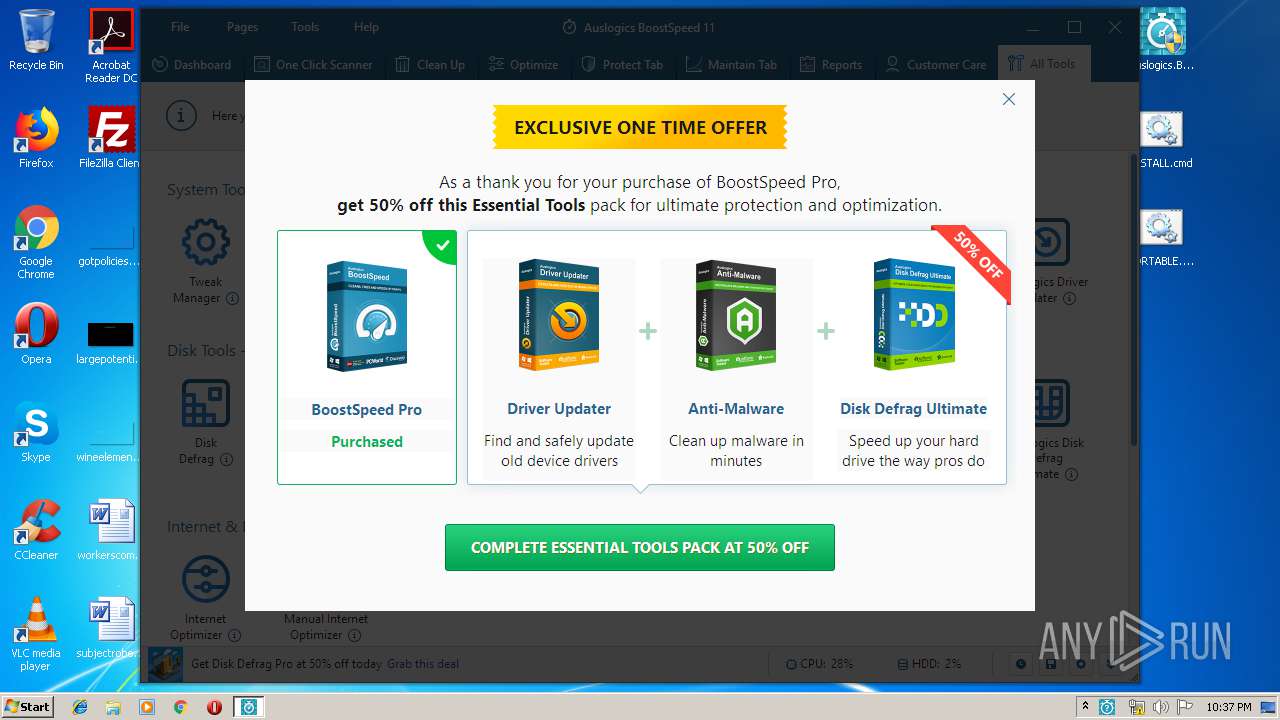
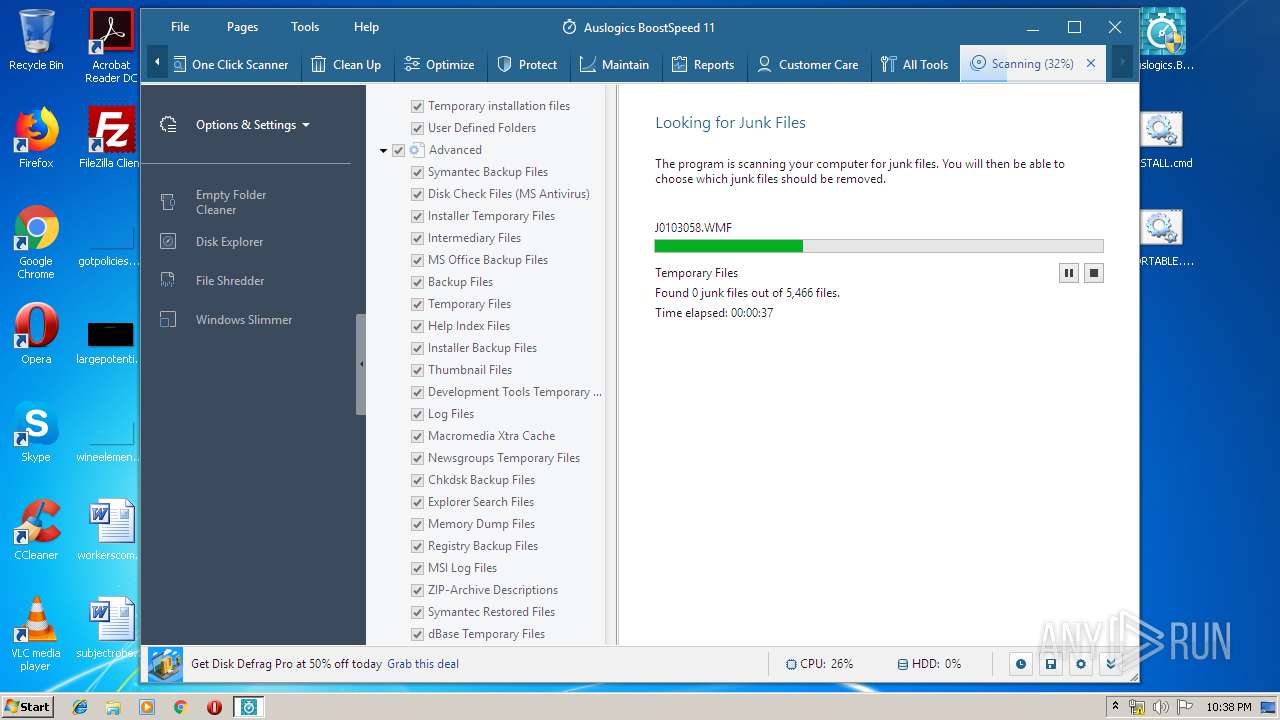
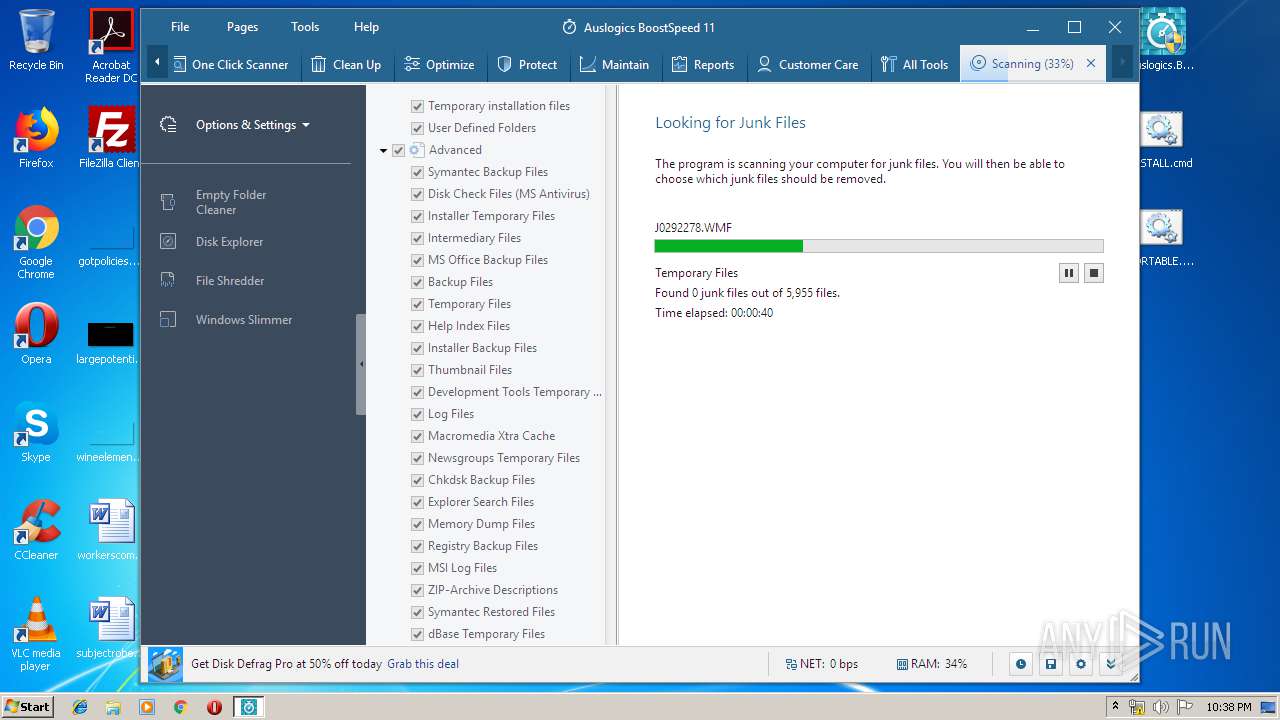
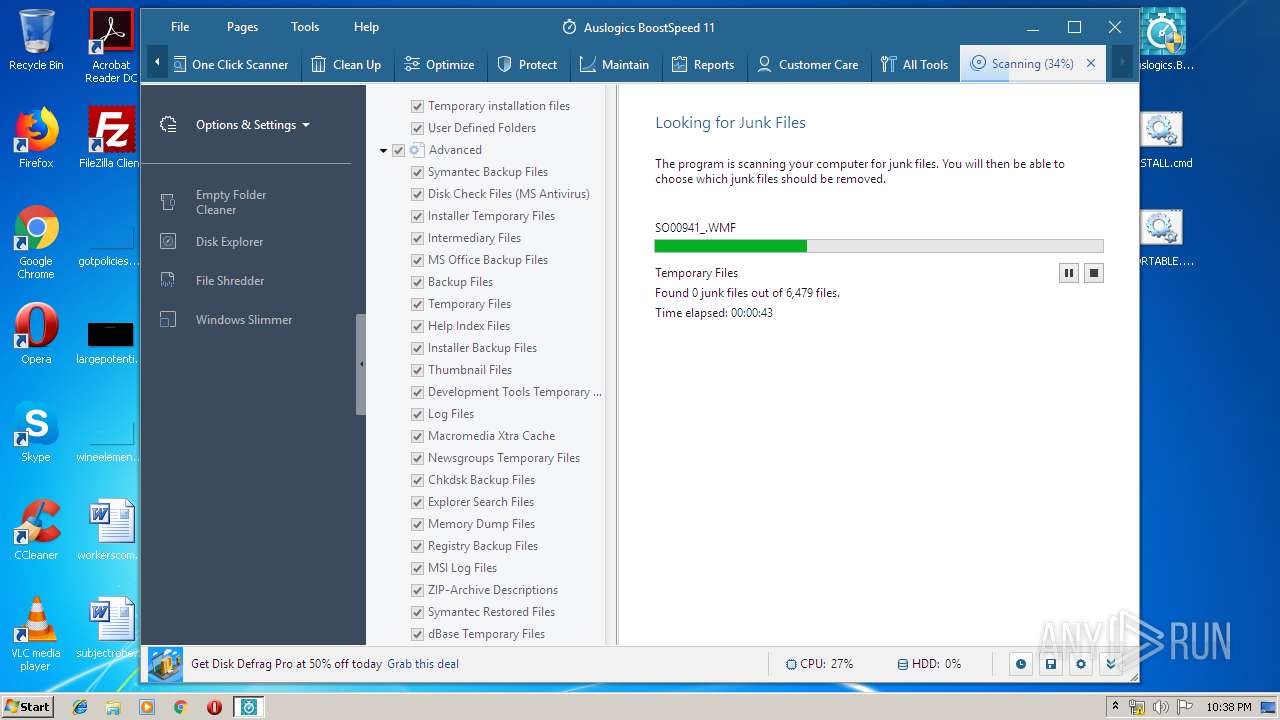
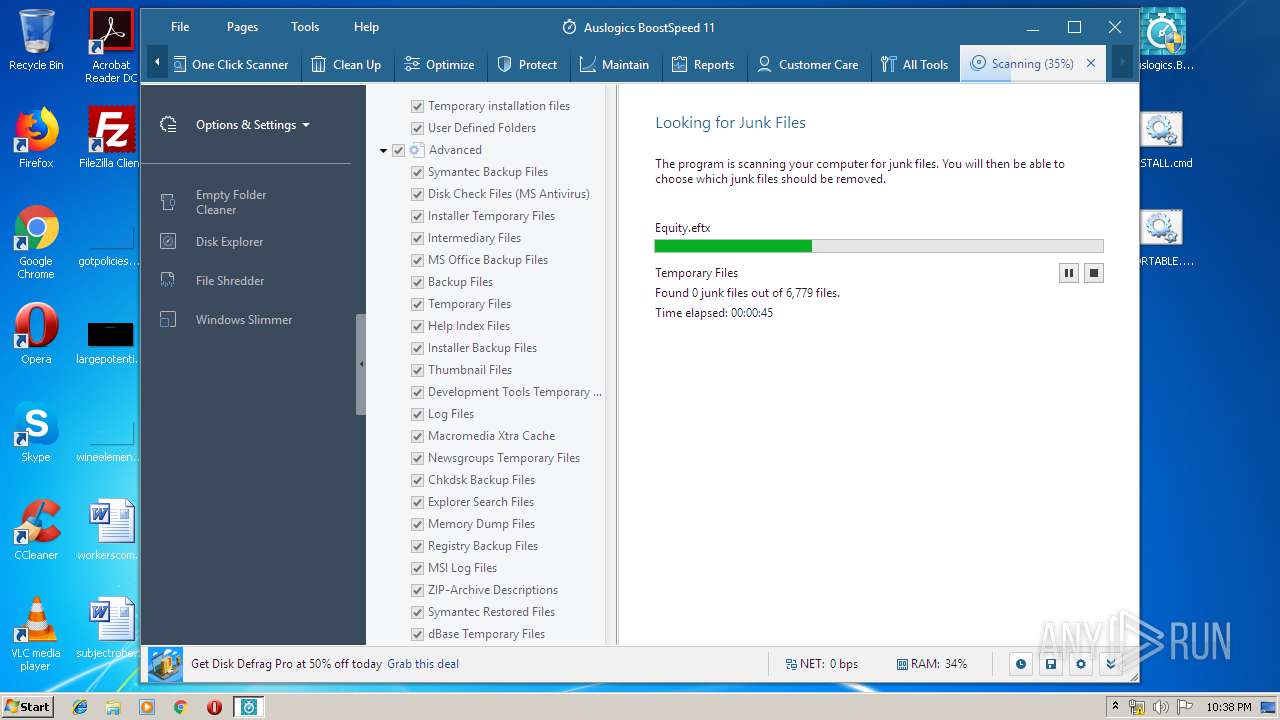
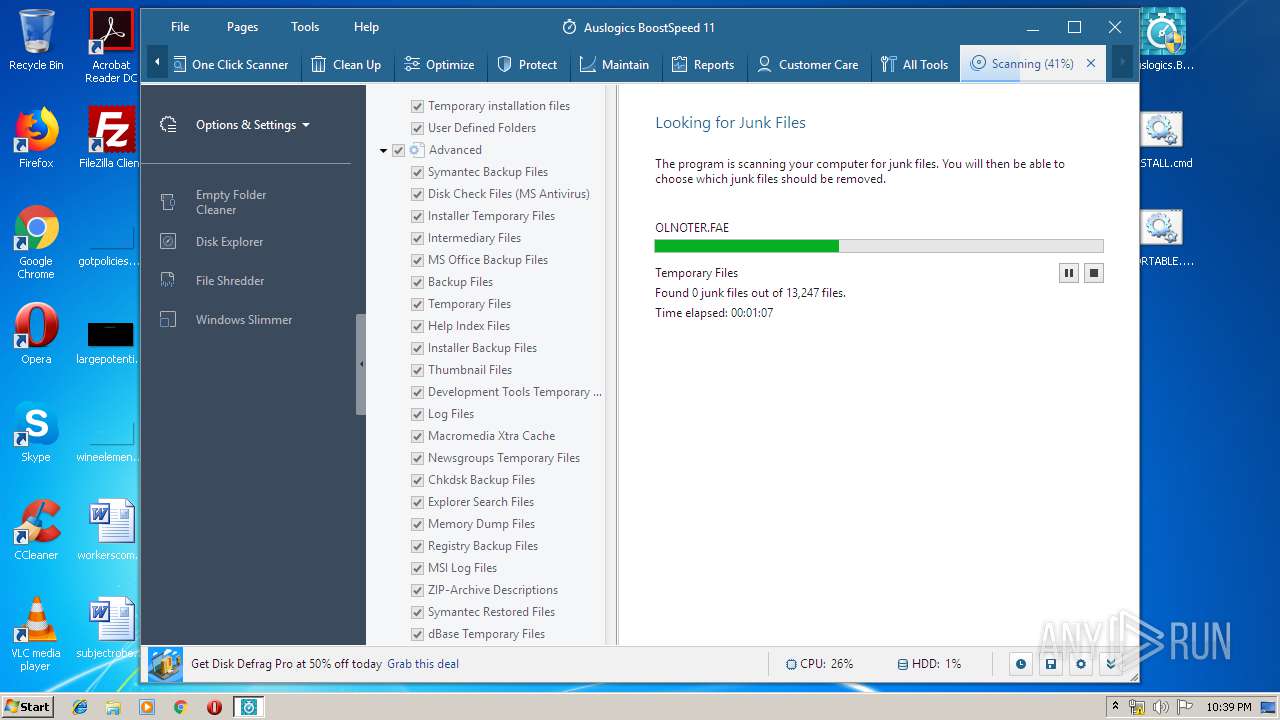
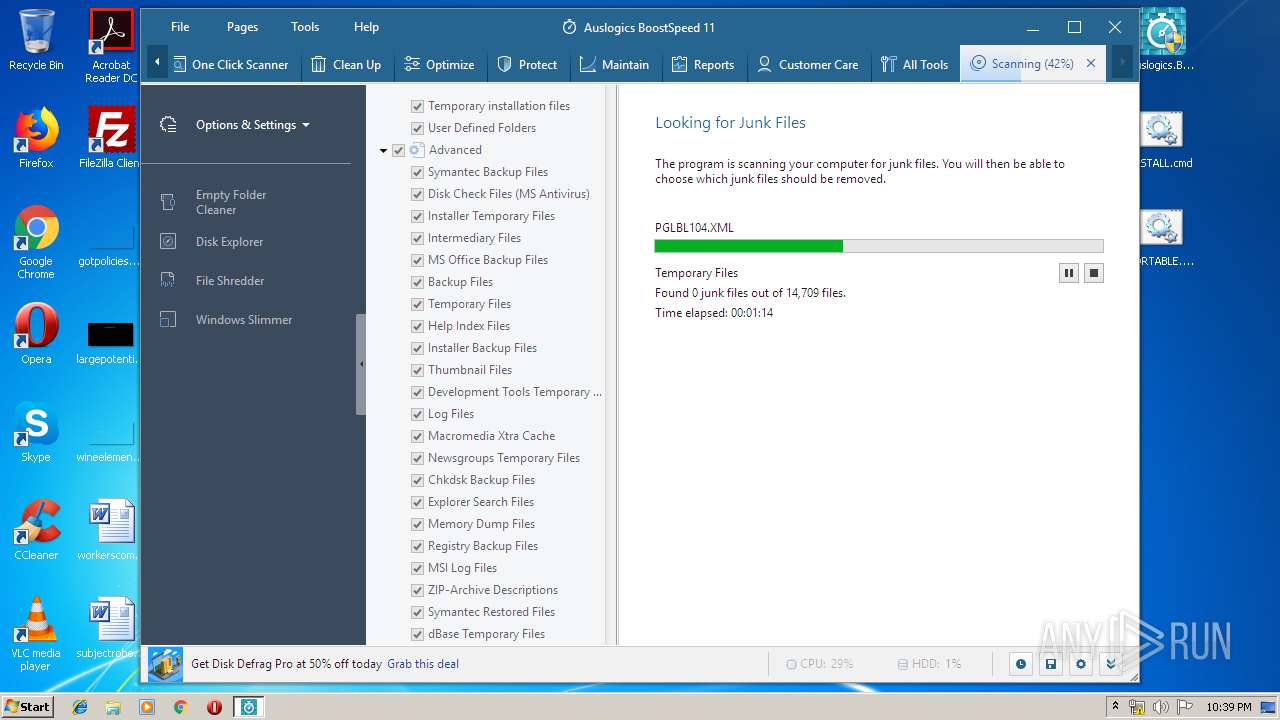
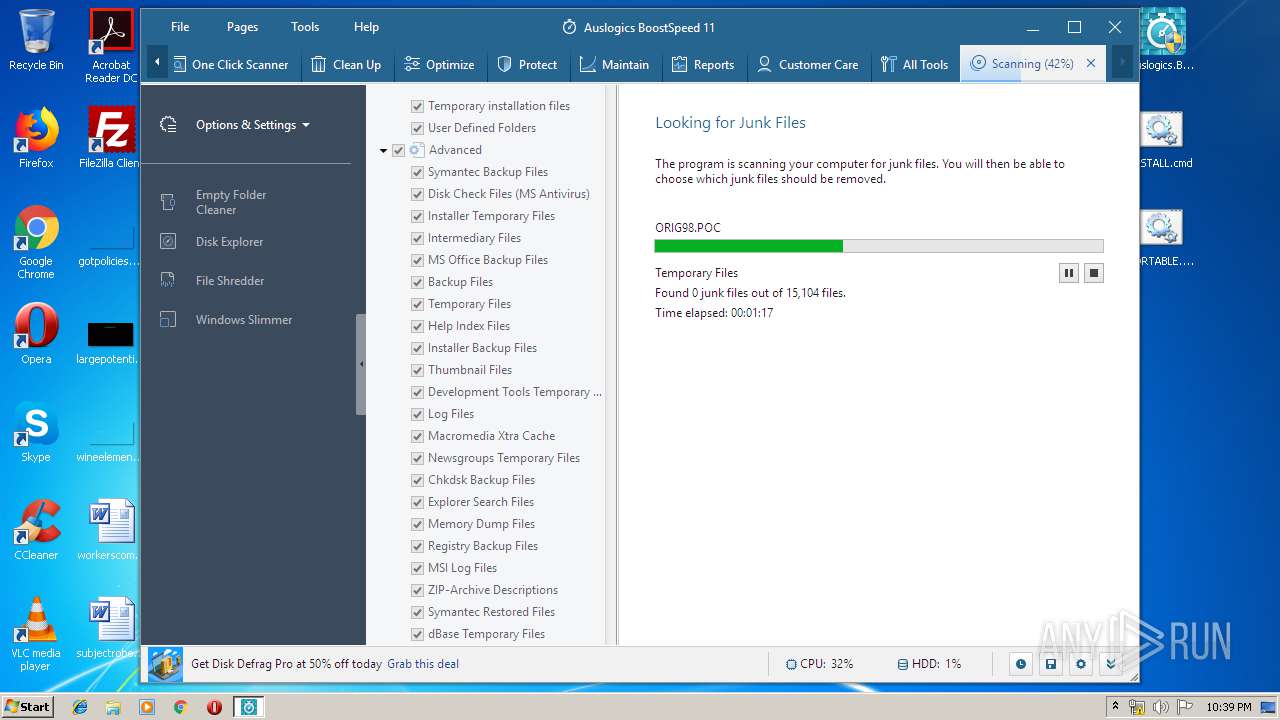
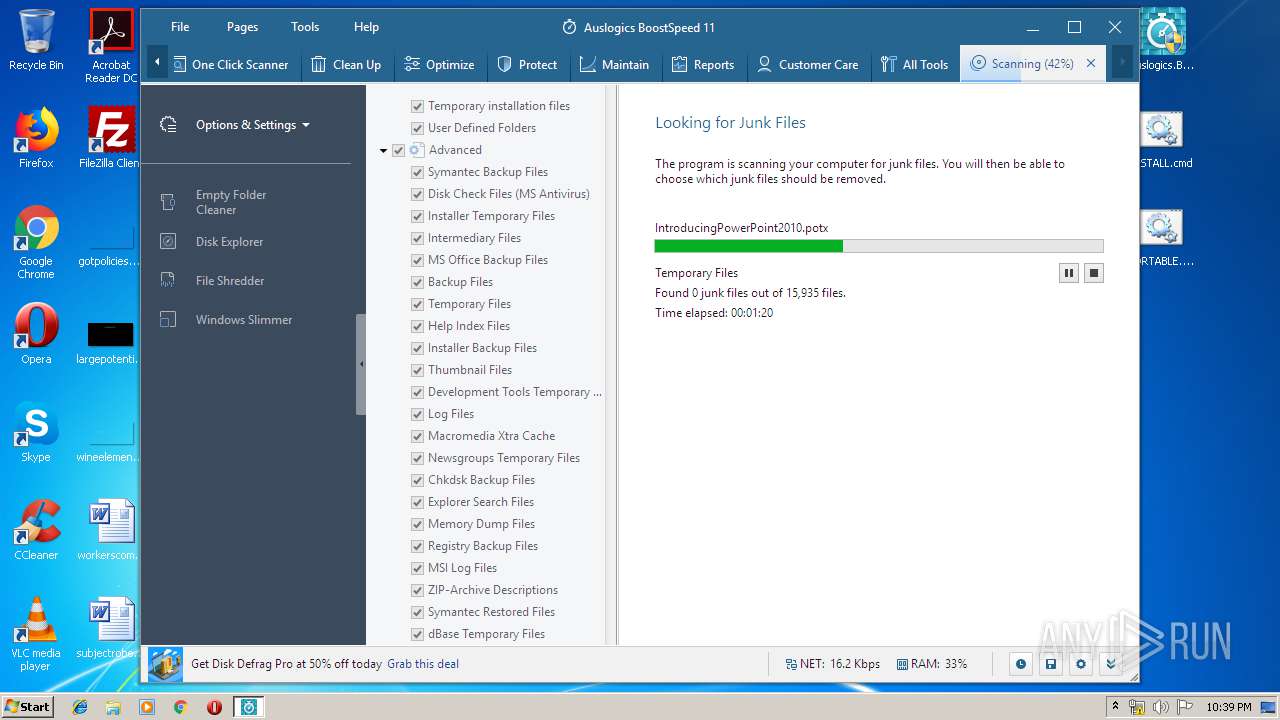
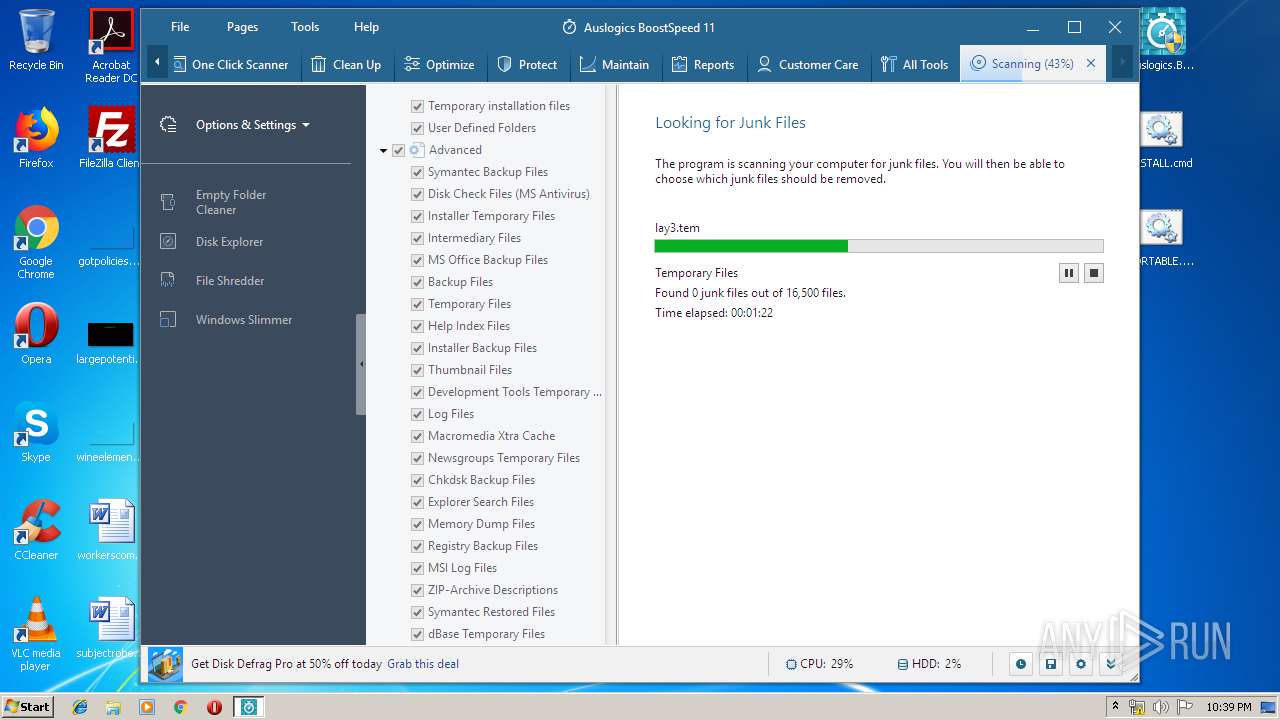
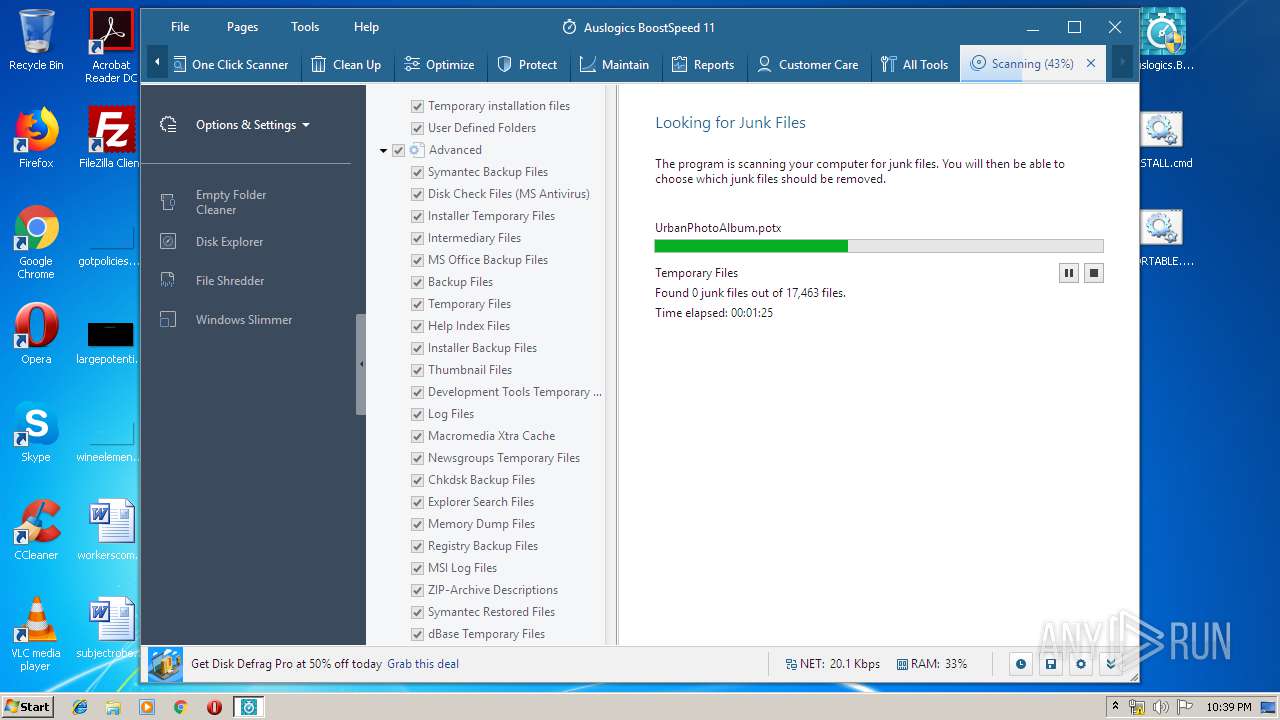
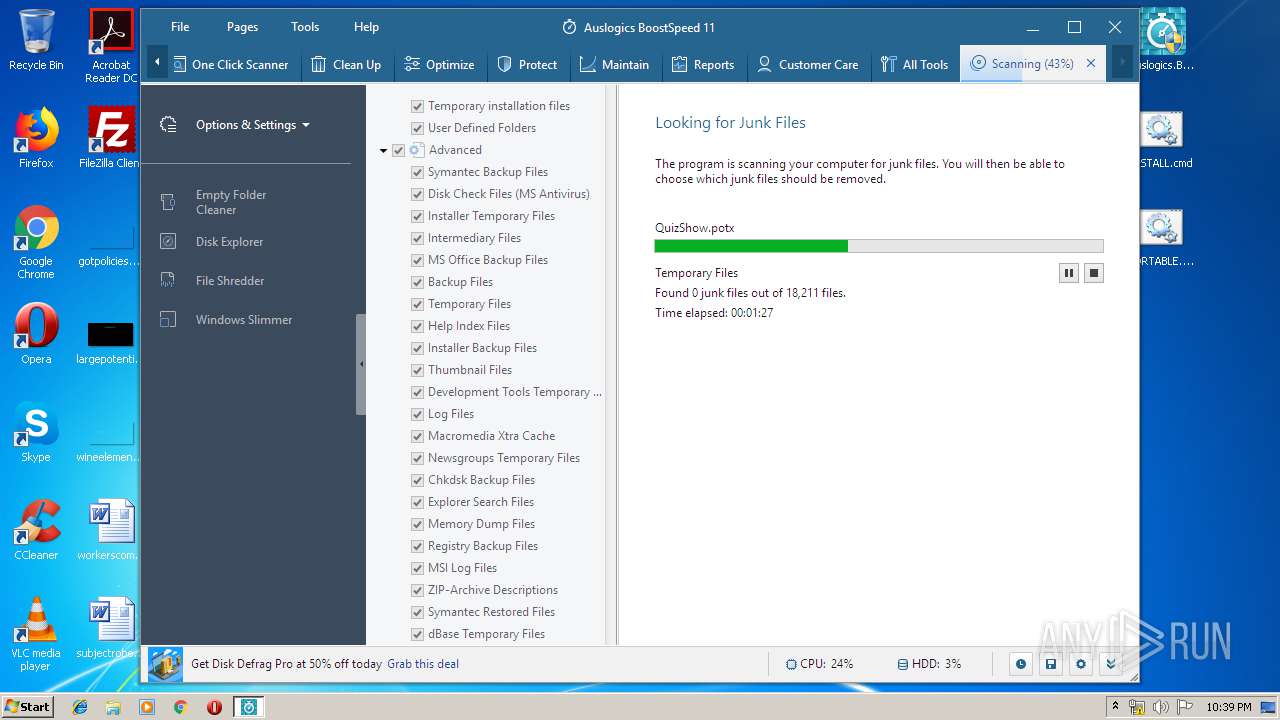
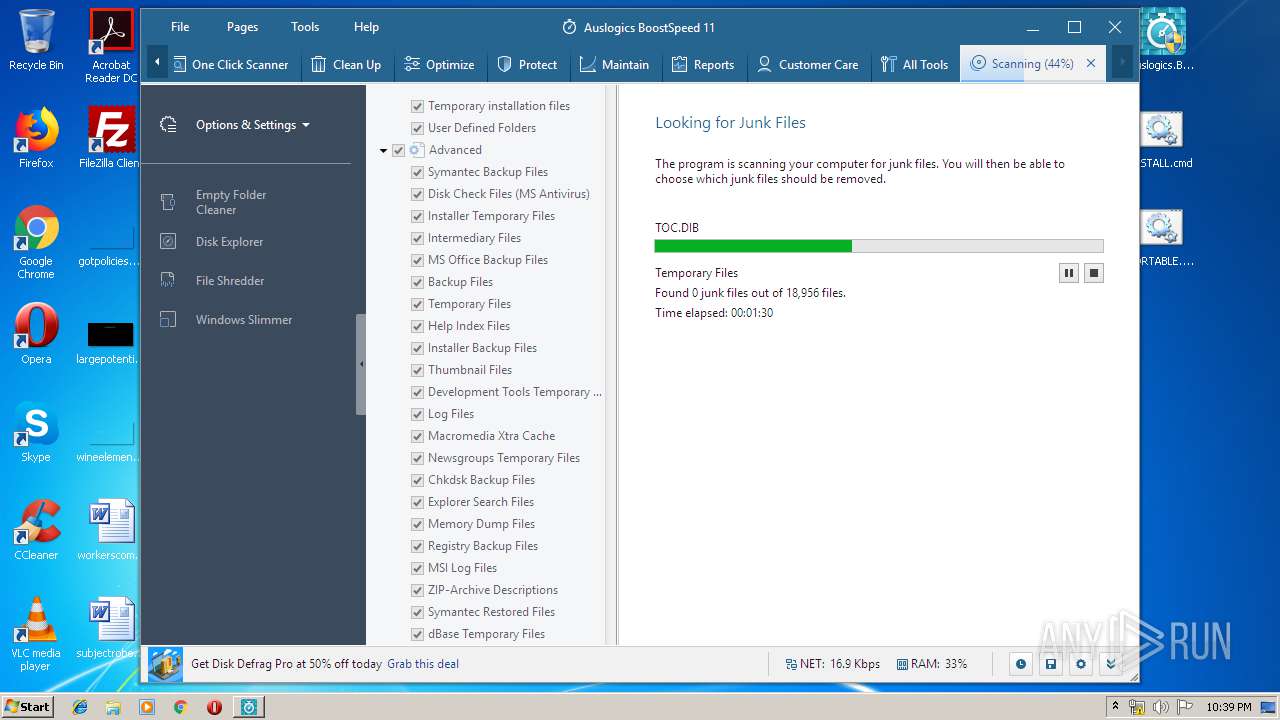
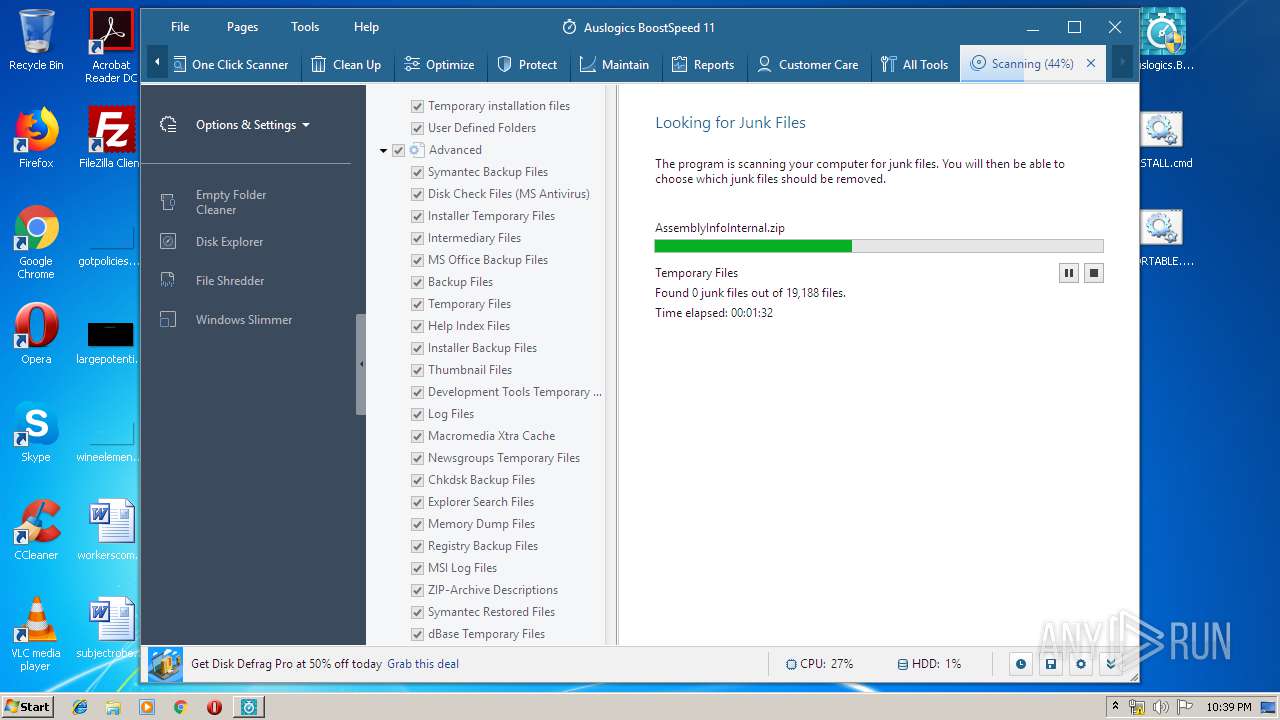
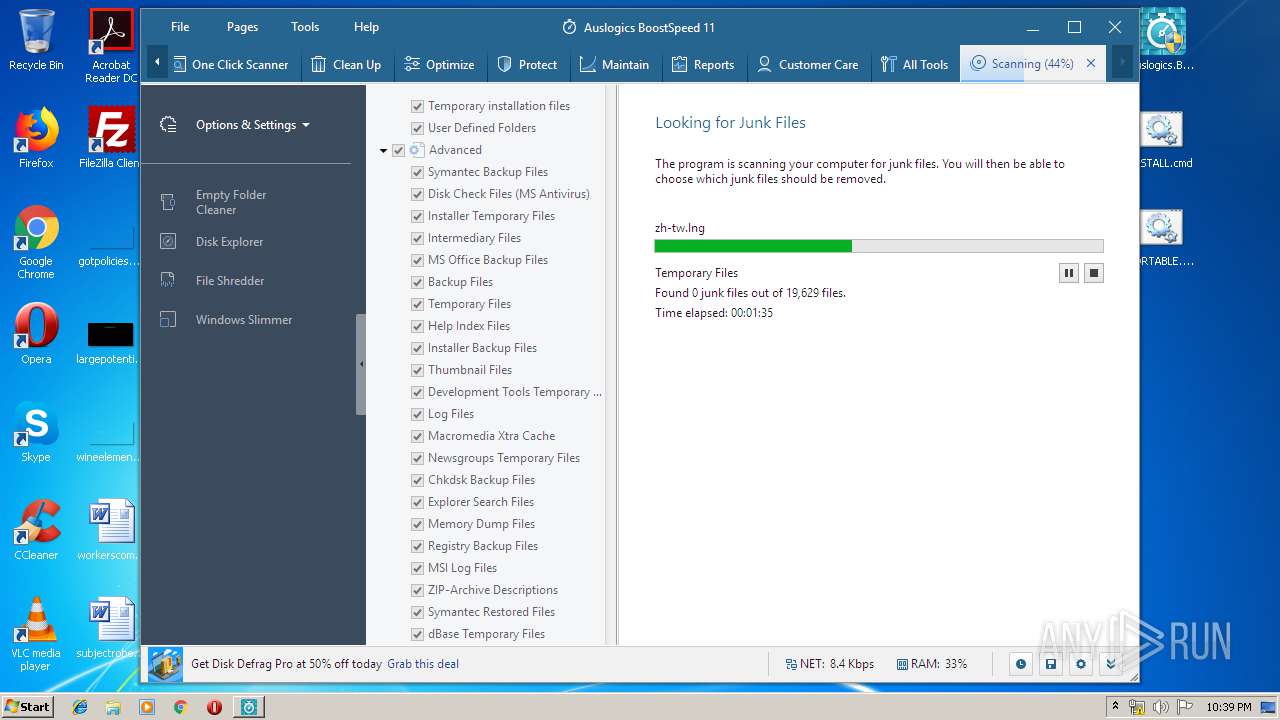
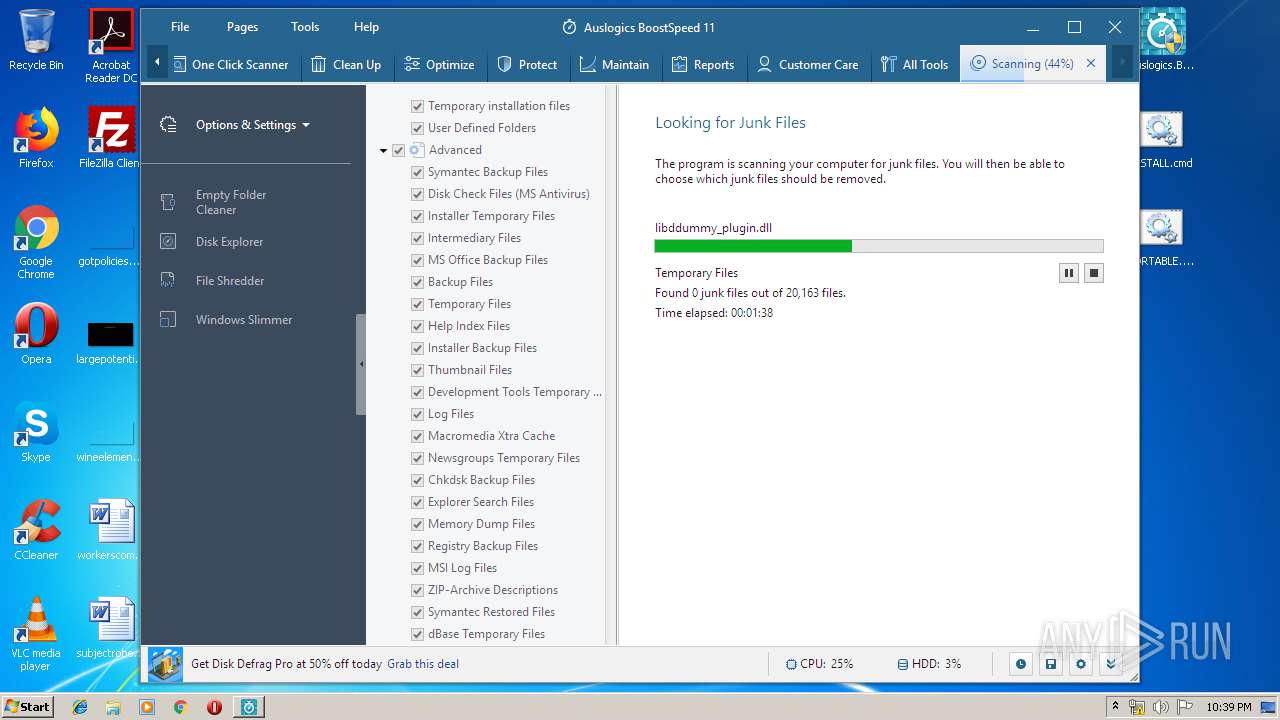
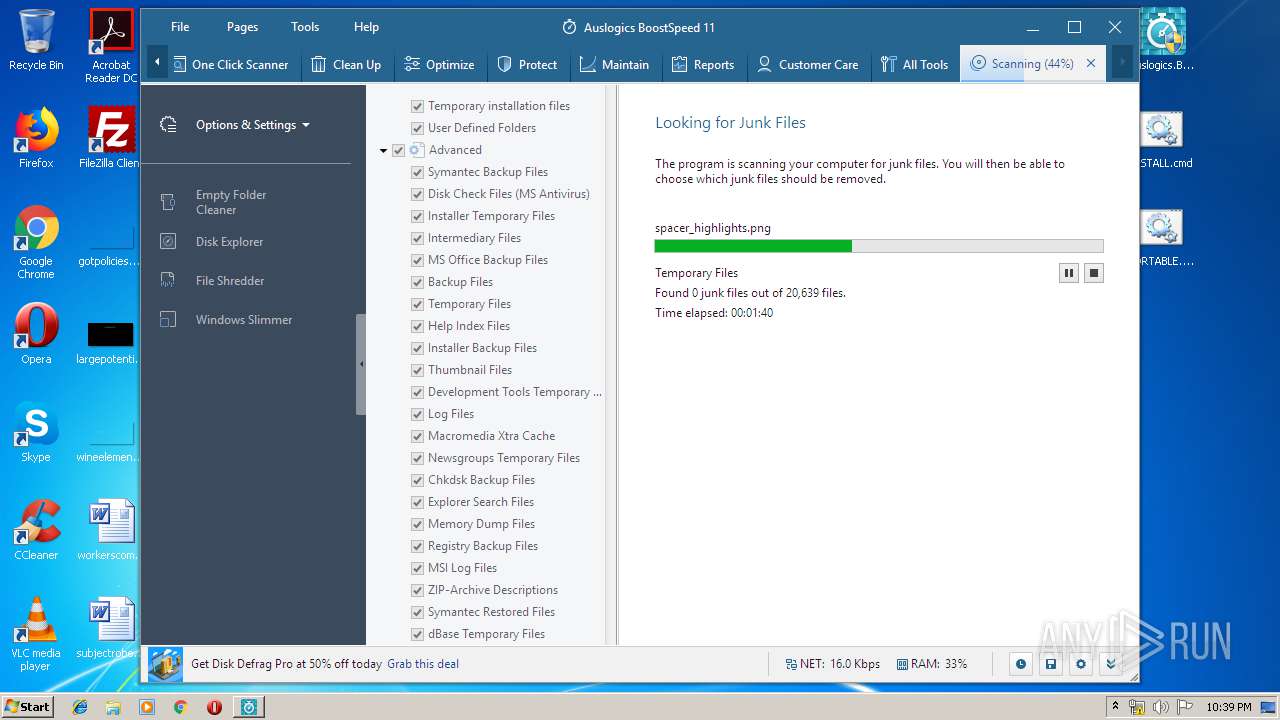
Loads dropped or rewritten executable
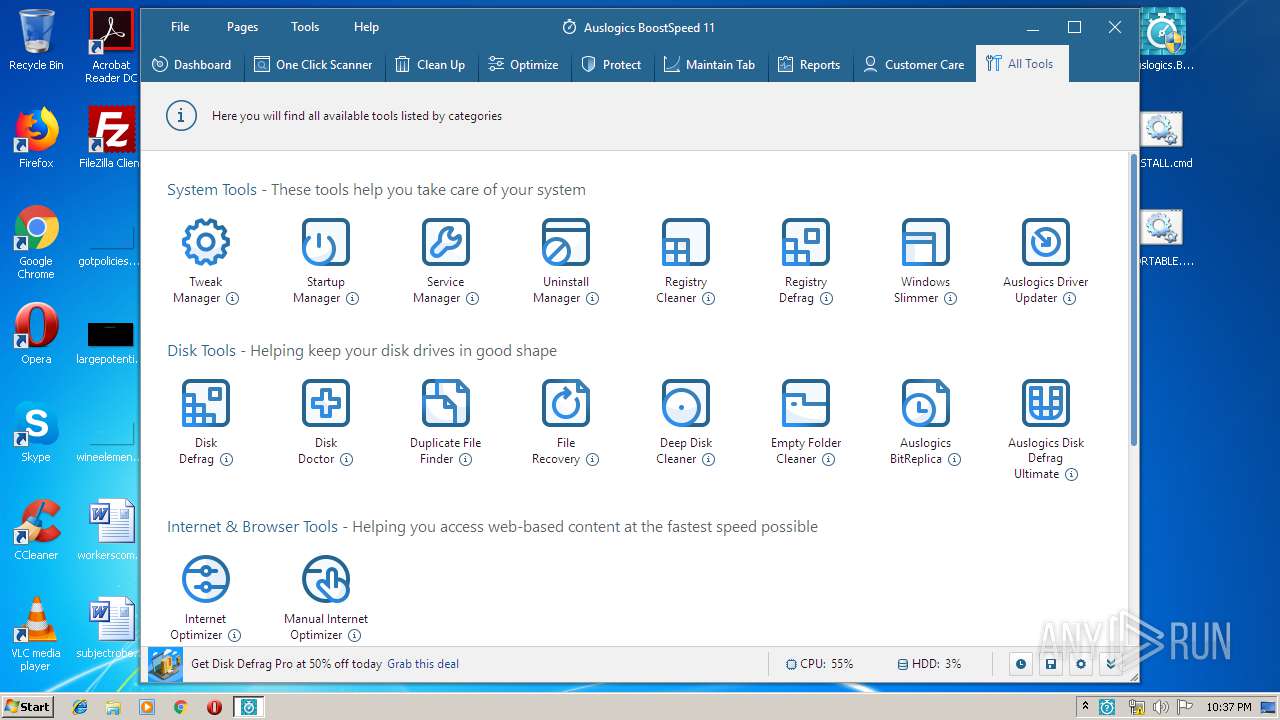
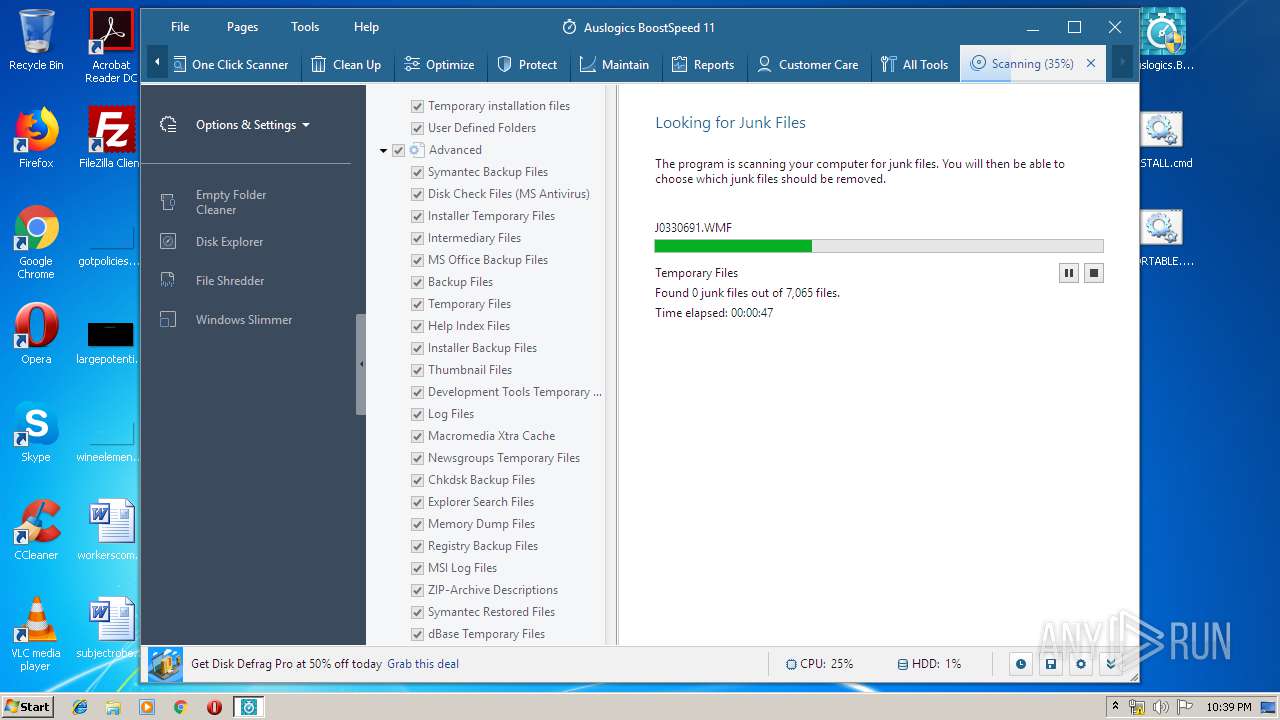
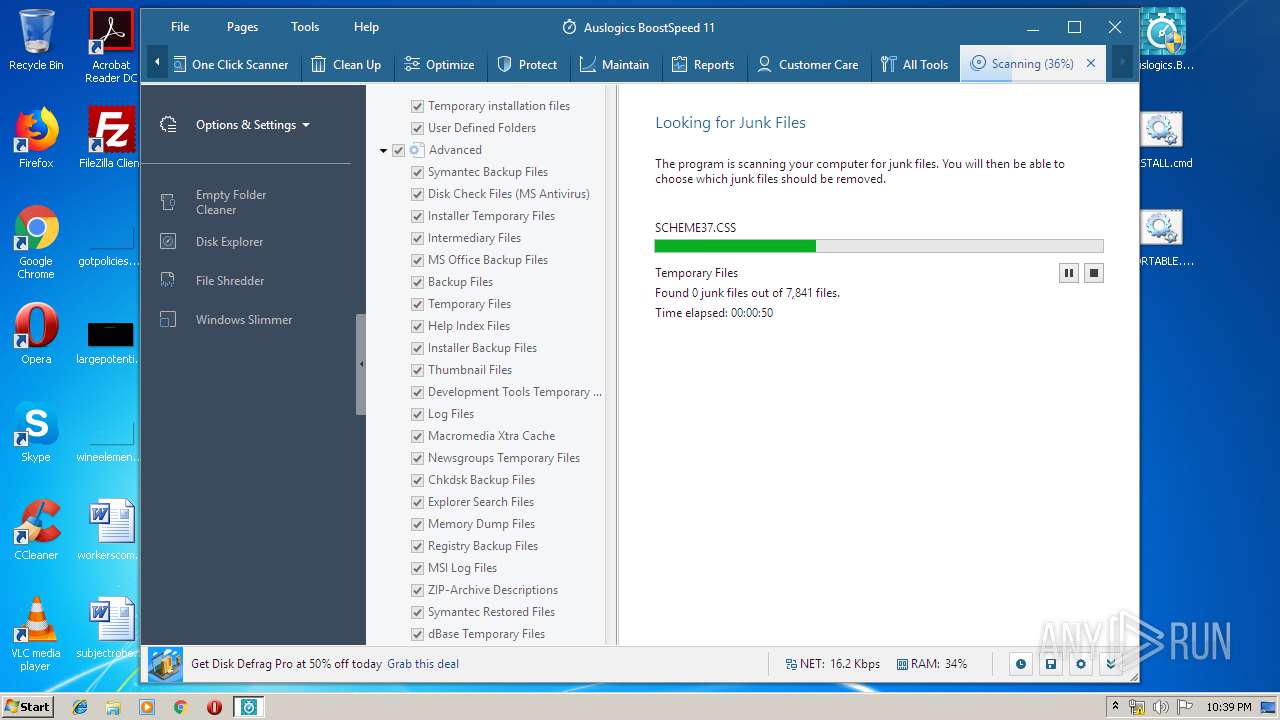
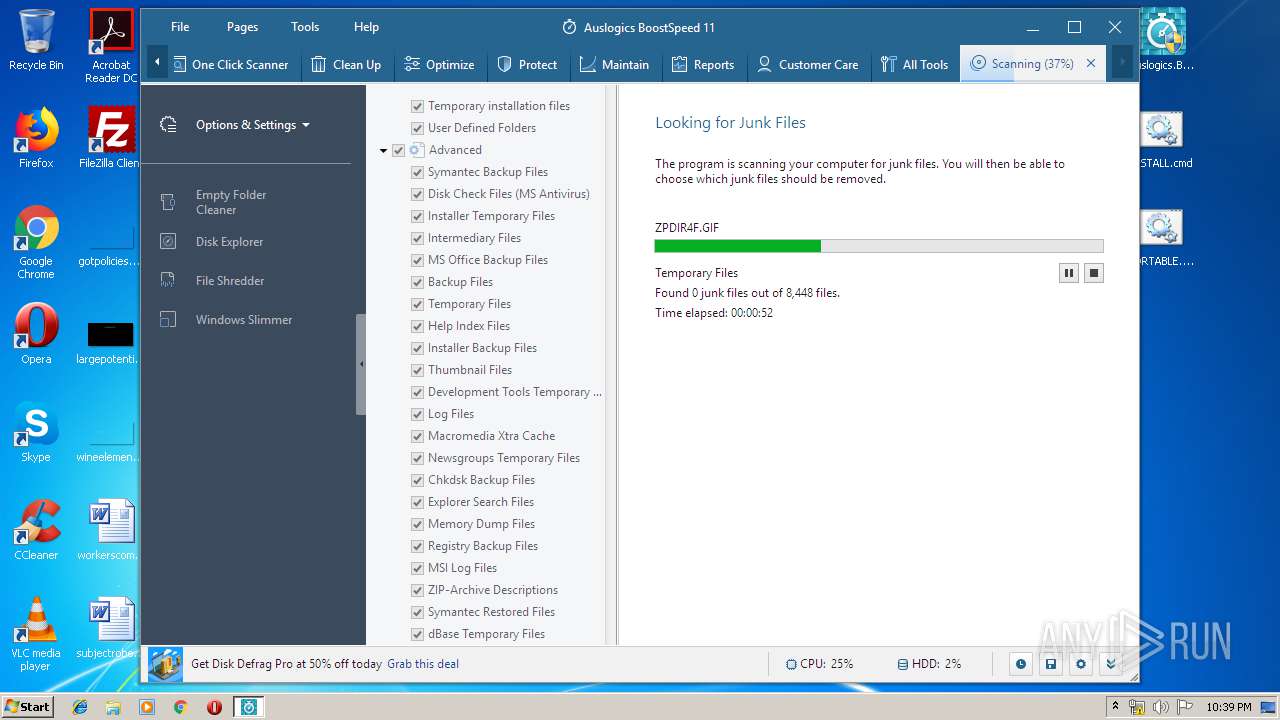
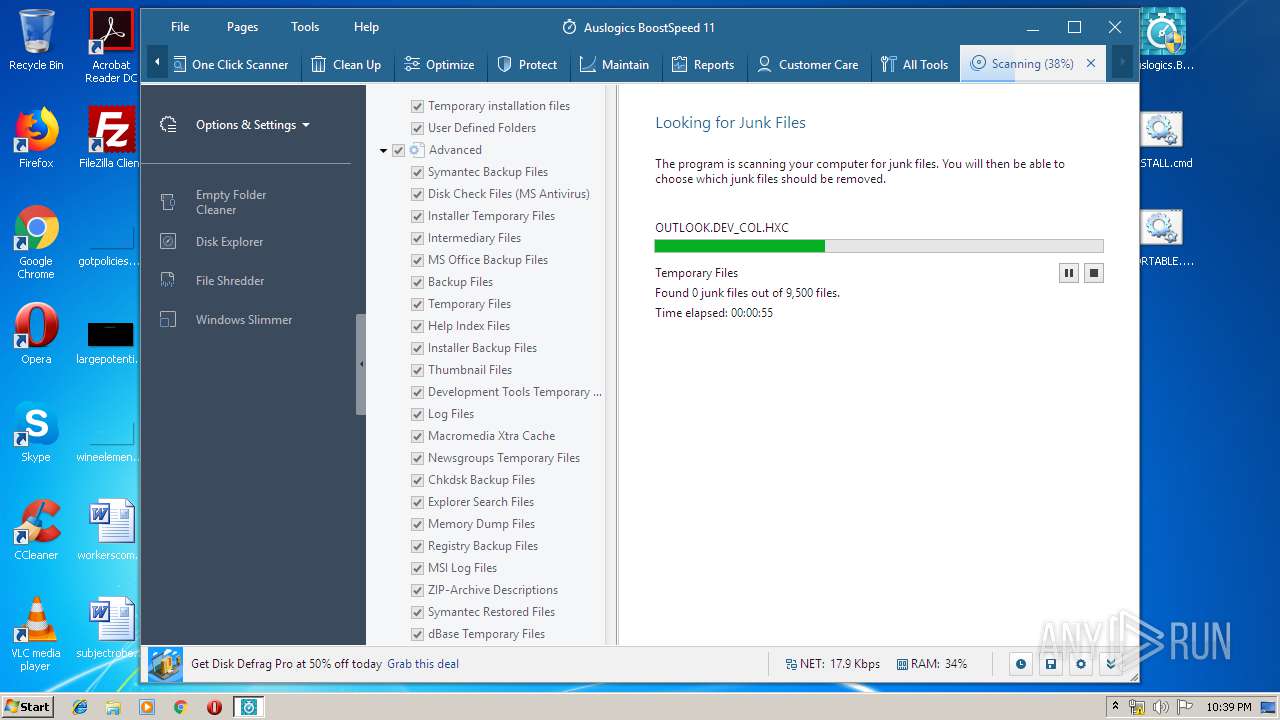
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
- Integrator.exe (PID: 2712)
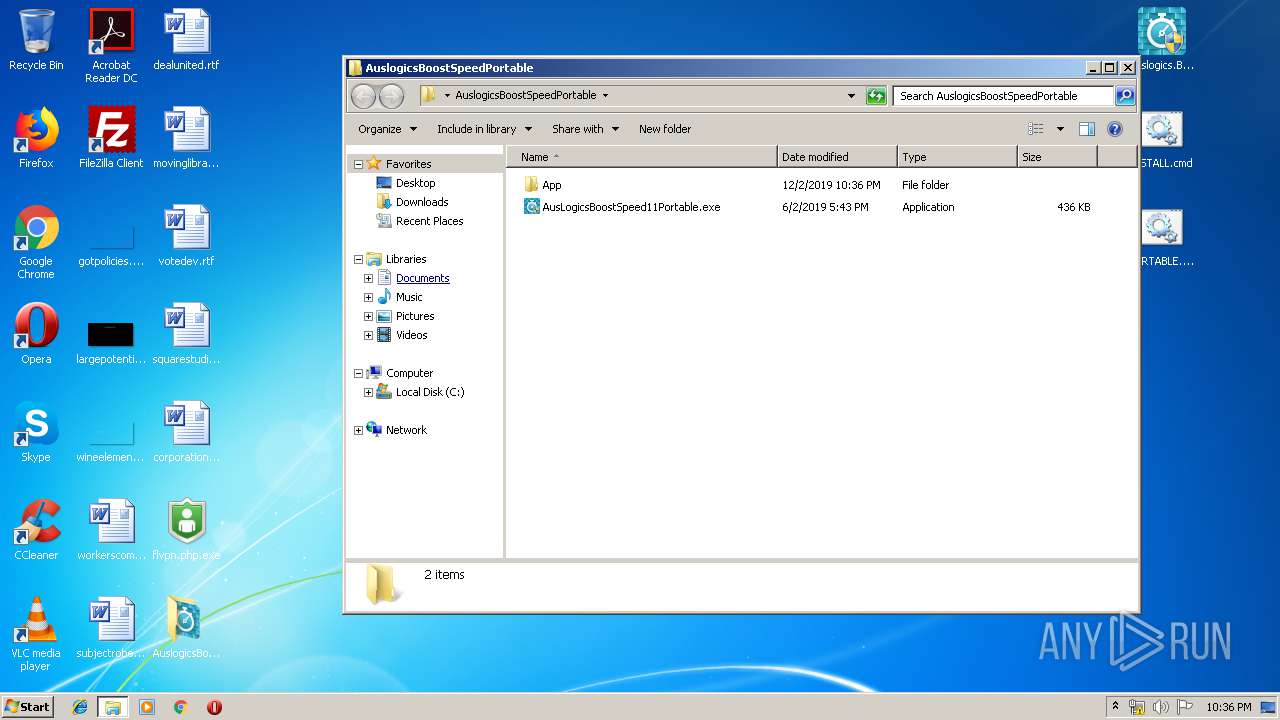
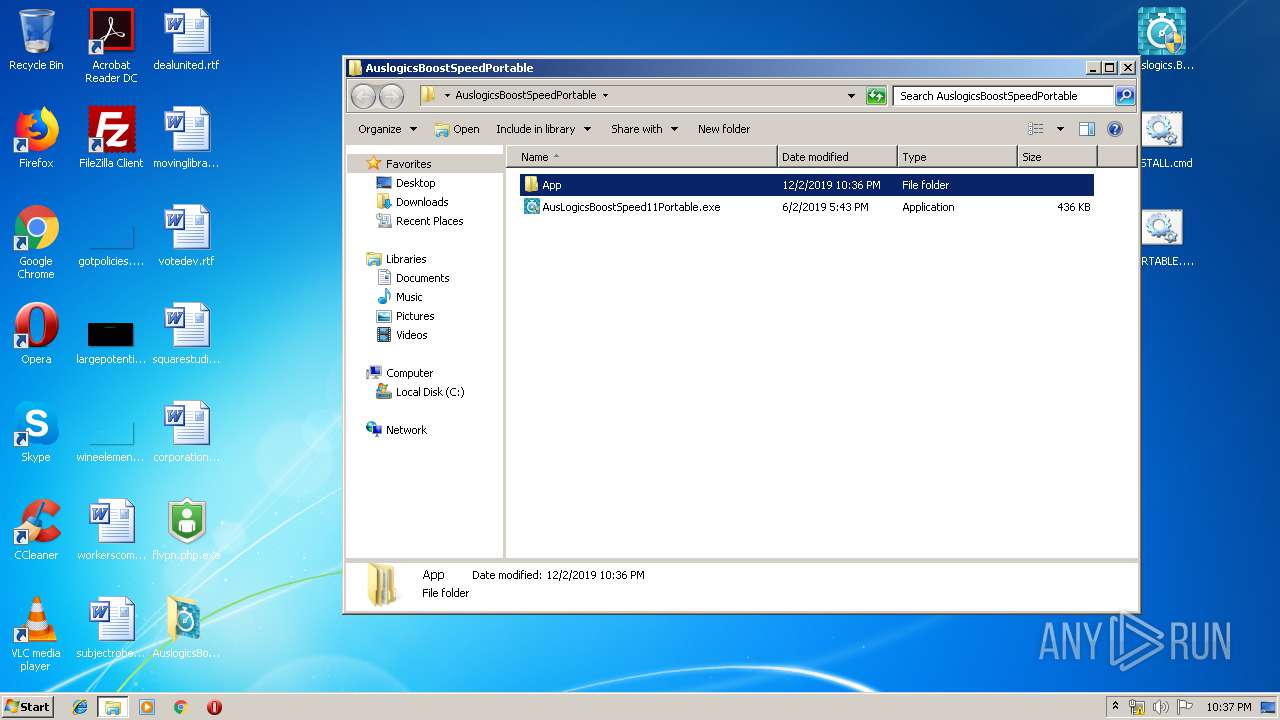
- AusLogicsBoostSpeed11Portable.exe (PID: 2128)
- taboneclickscanner.exe (PID: 2996)
- SearchProtocolHost.exe (PID: 3604)
- taboptimize.exe (PID: 3948)
- tabprotect.exe (PID: 2352)
- tabmaintain.exe (PID: 3996)
- tabreports.exe (PID: 3892)
- tabcarecenter.exe (PID: 1316)
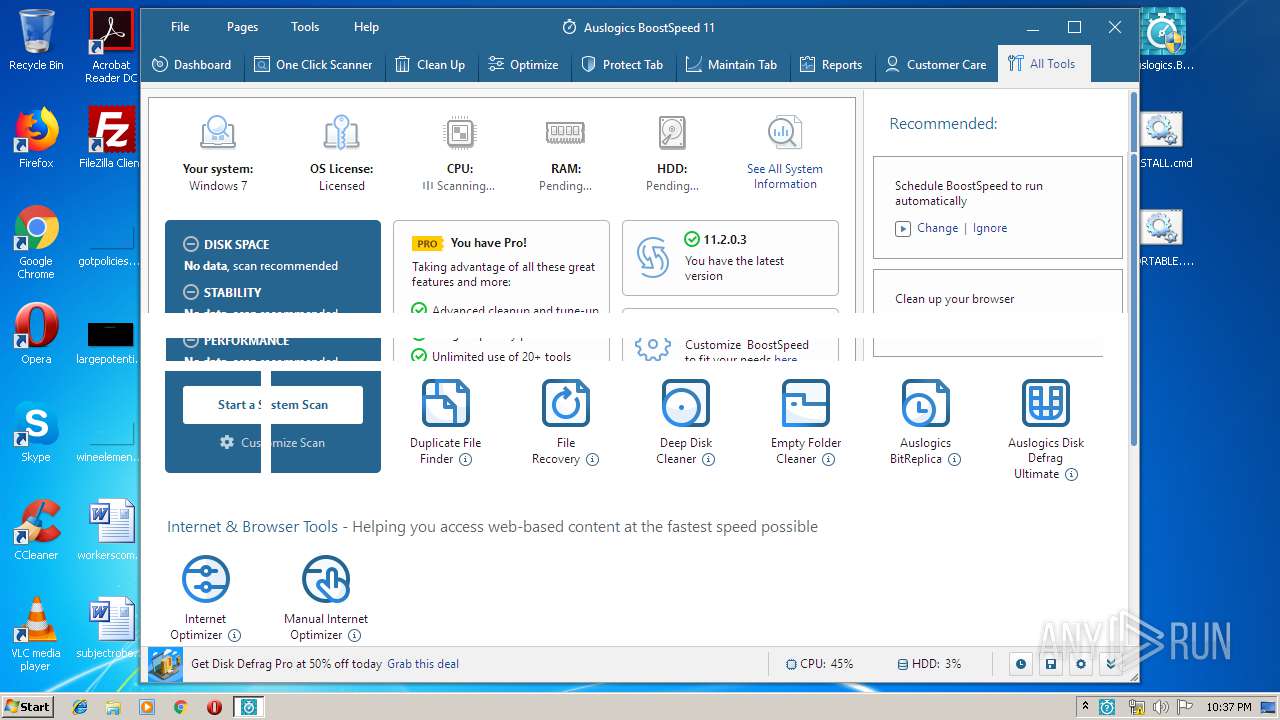
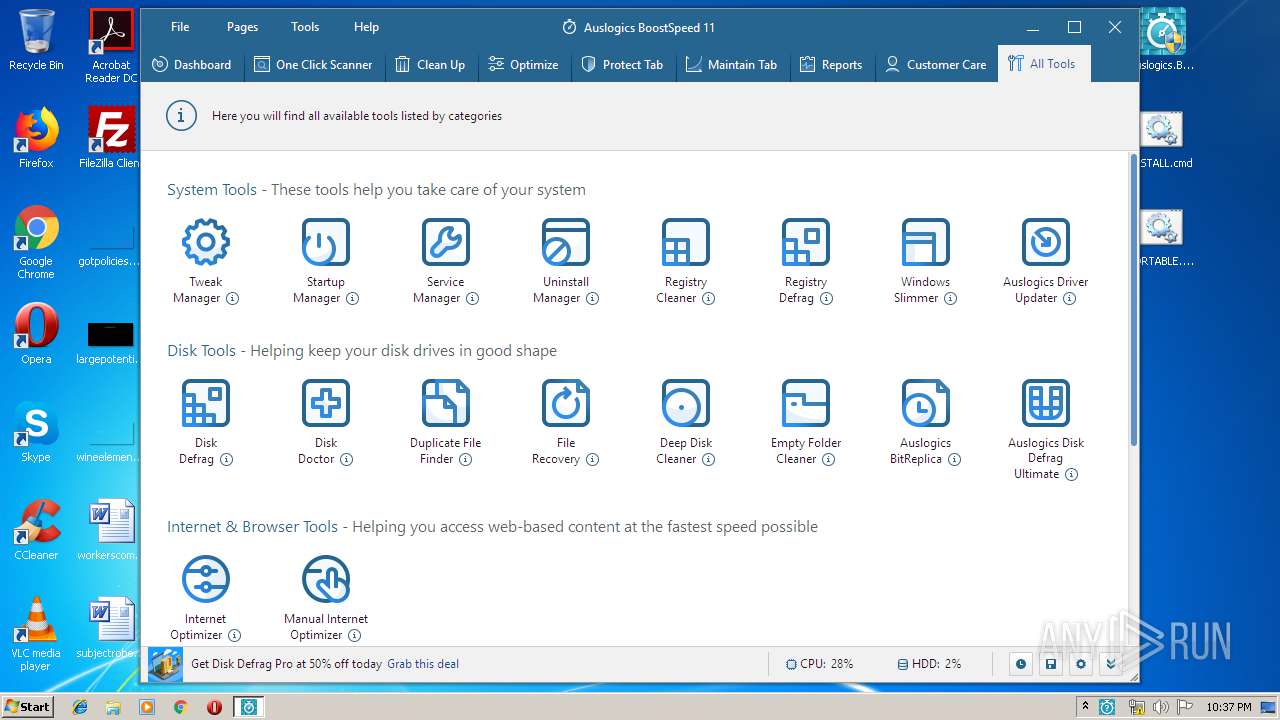
- taballtools.exe (PID: 1764)
- tabcleanup.exe (PID: 1904)
- explorer.exe (PID: 352)
- DllHost.exe (PID: 3856)
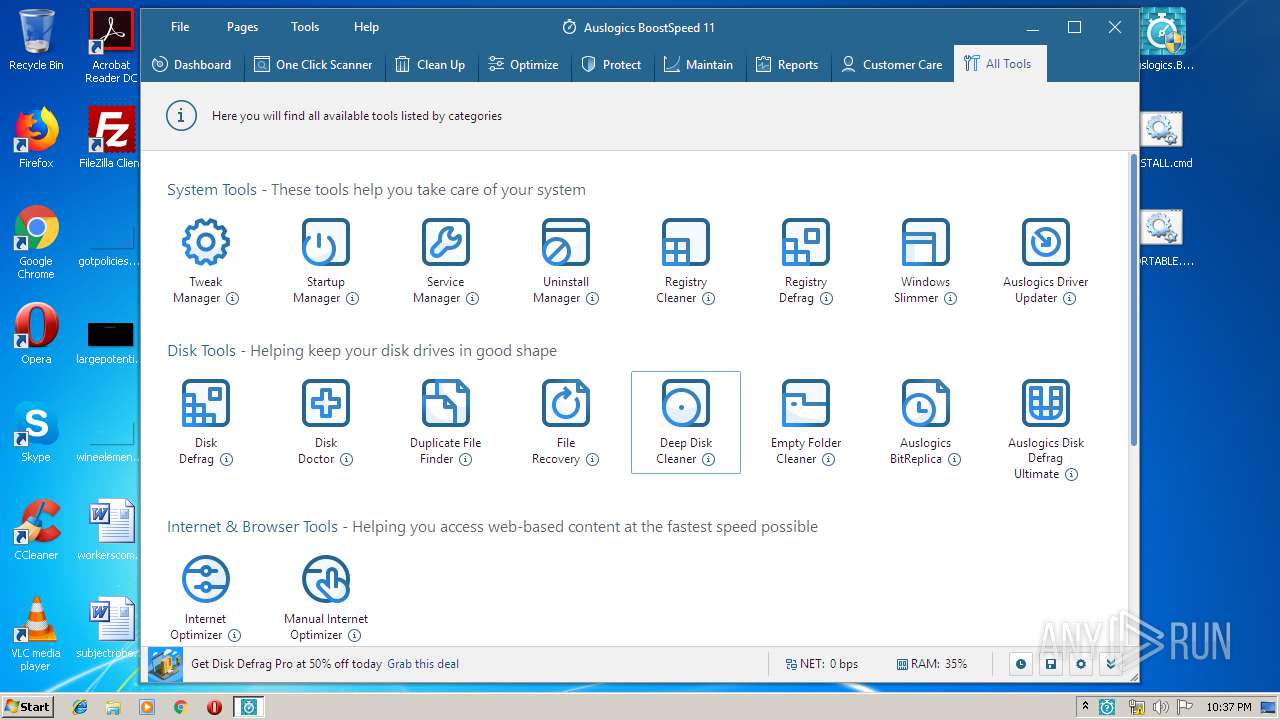
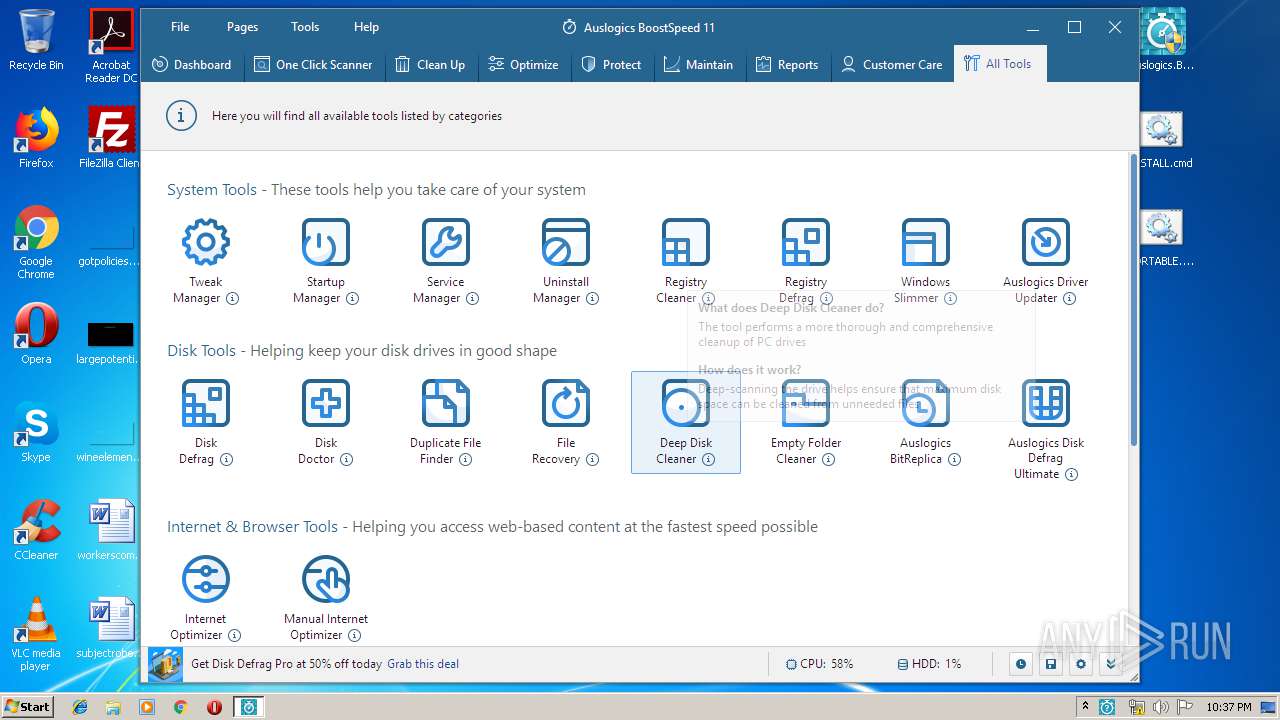
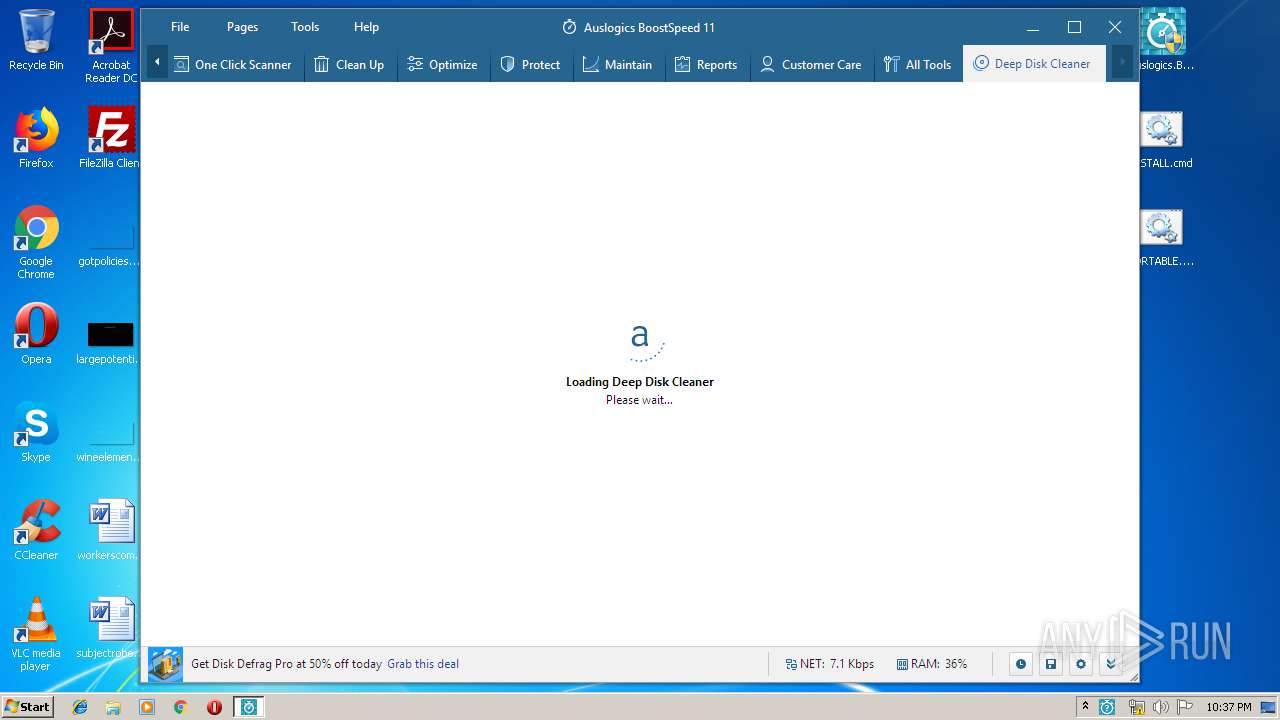
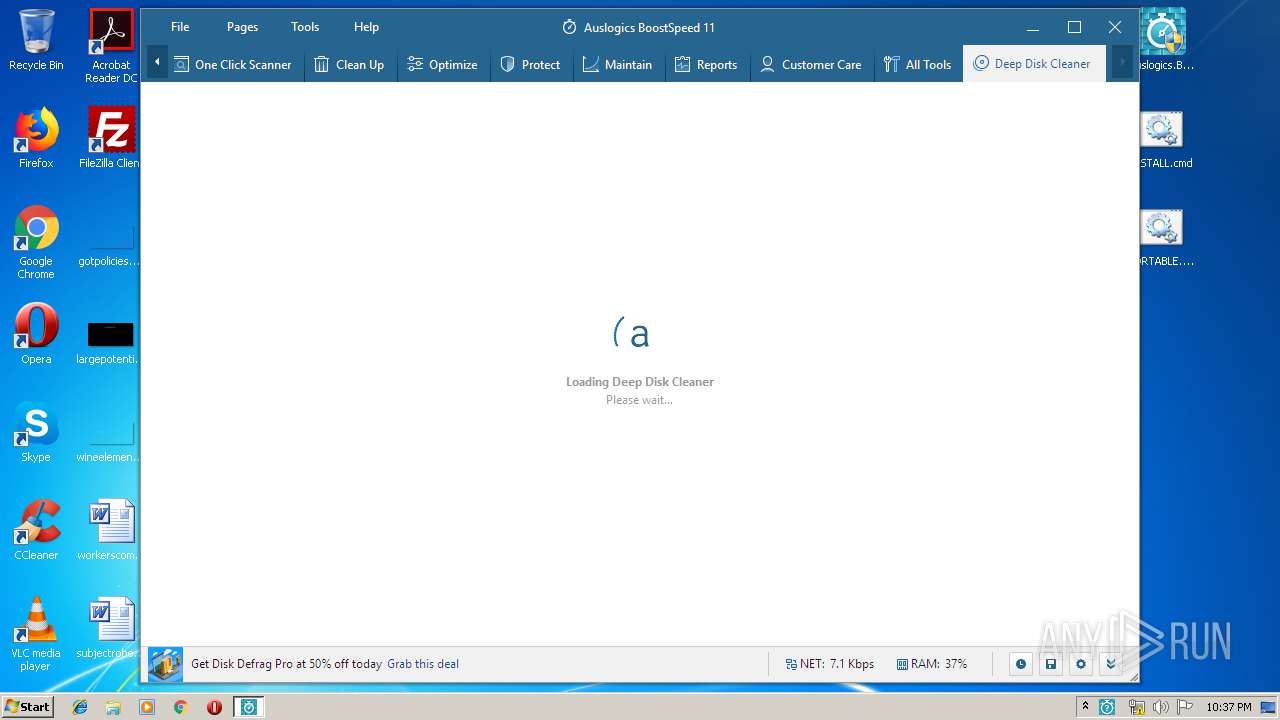
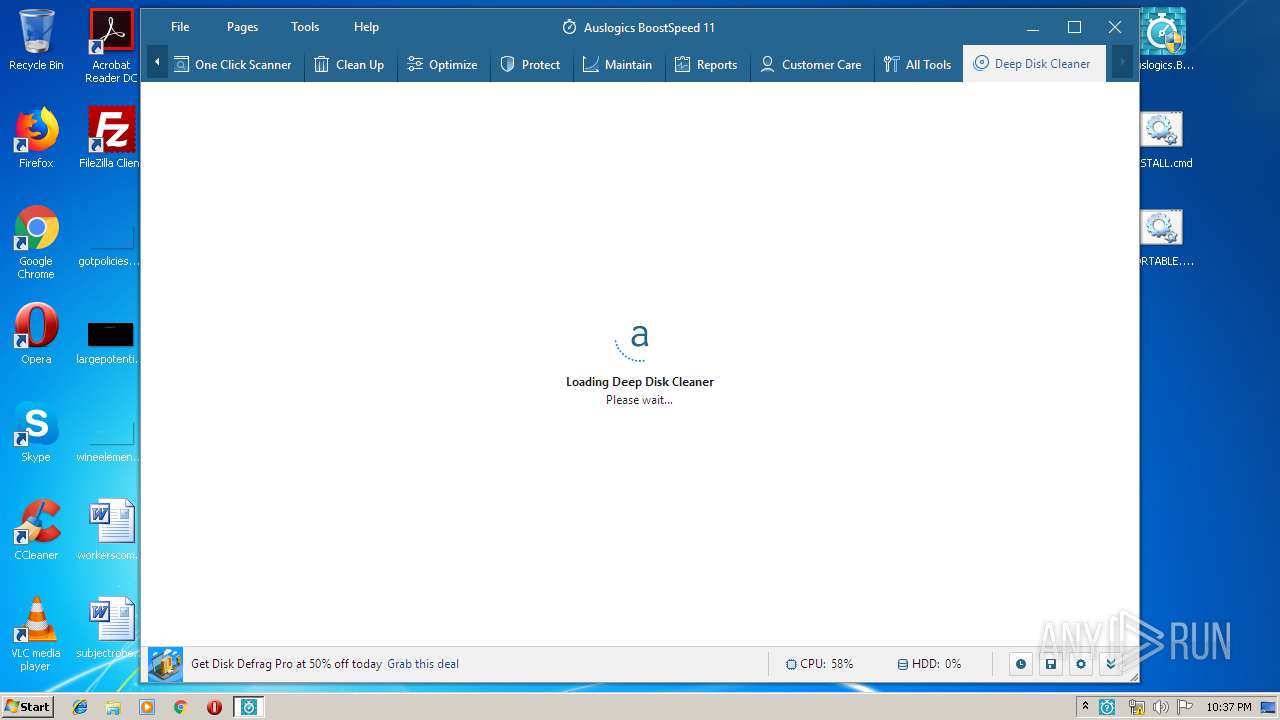
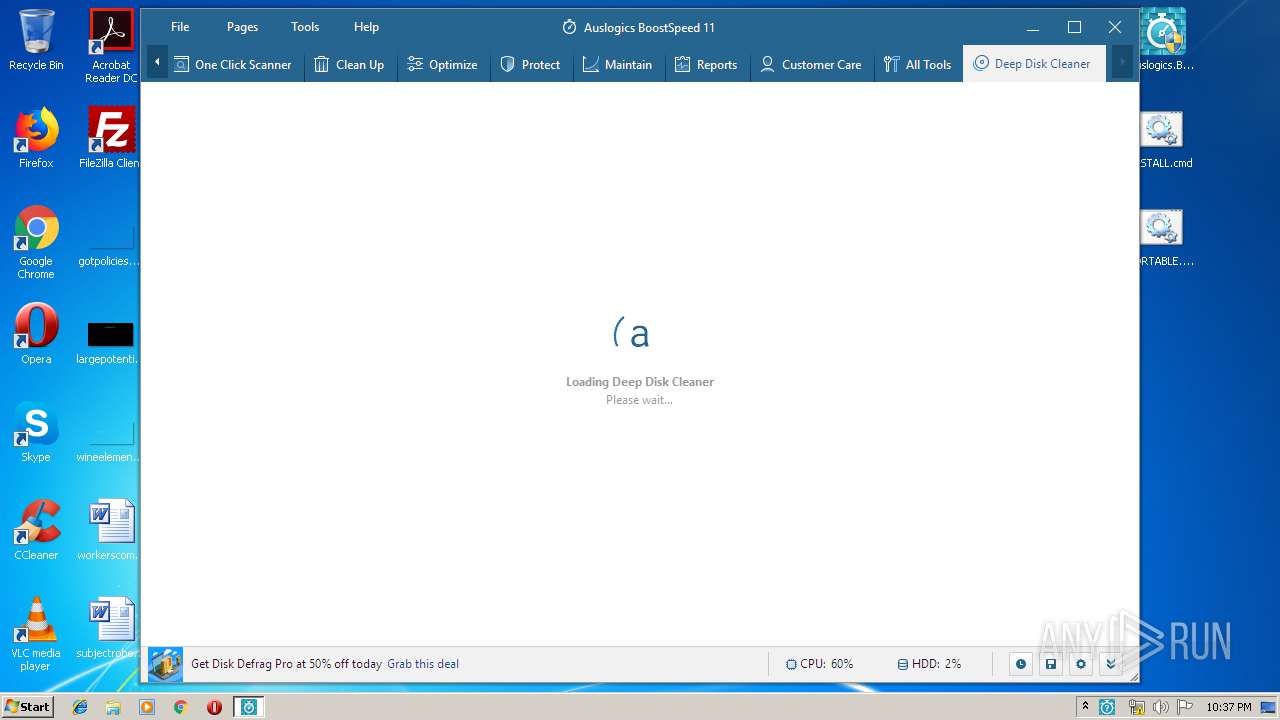
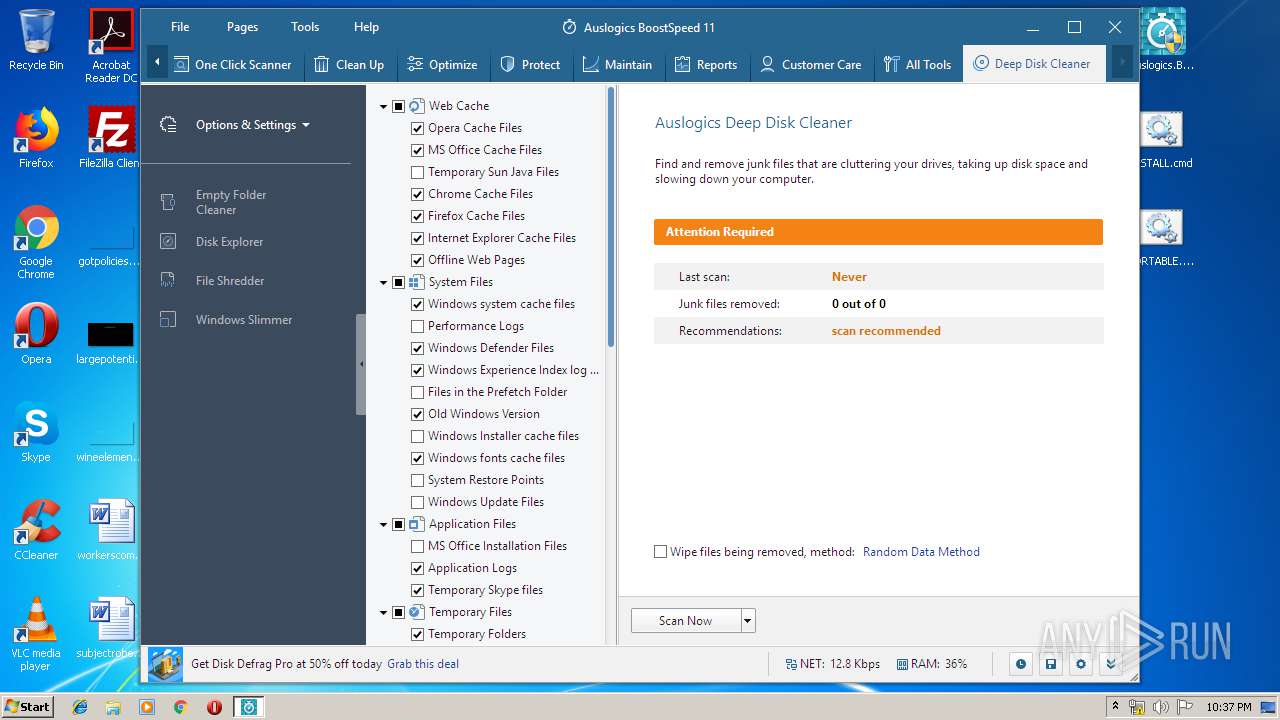
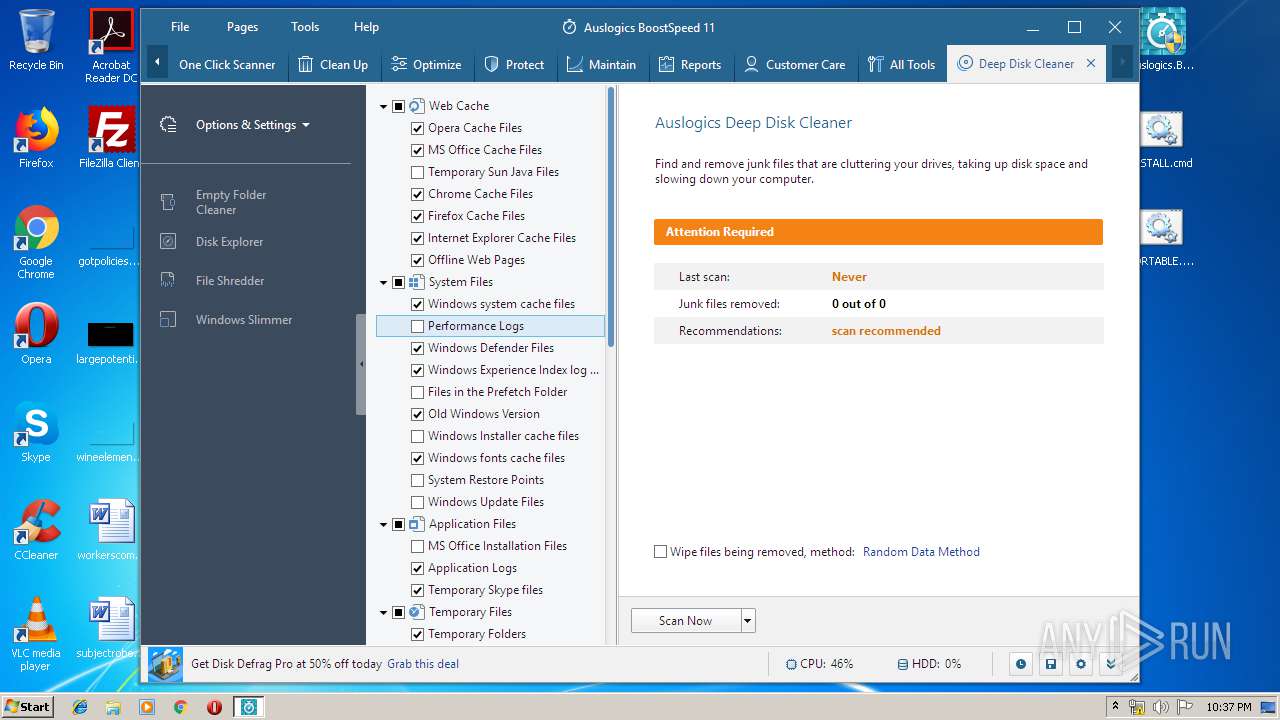
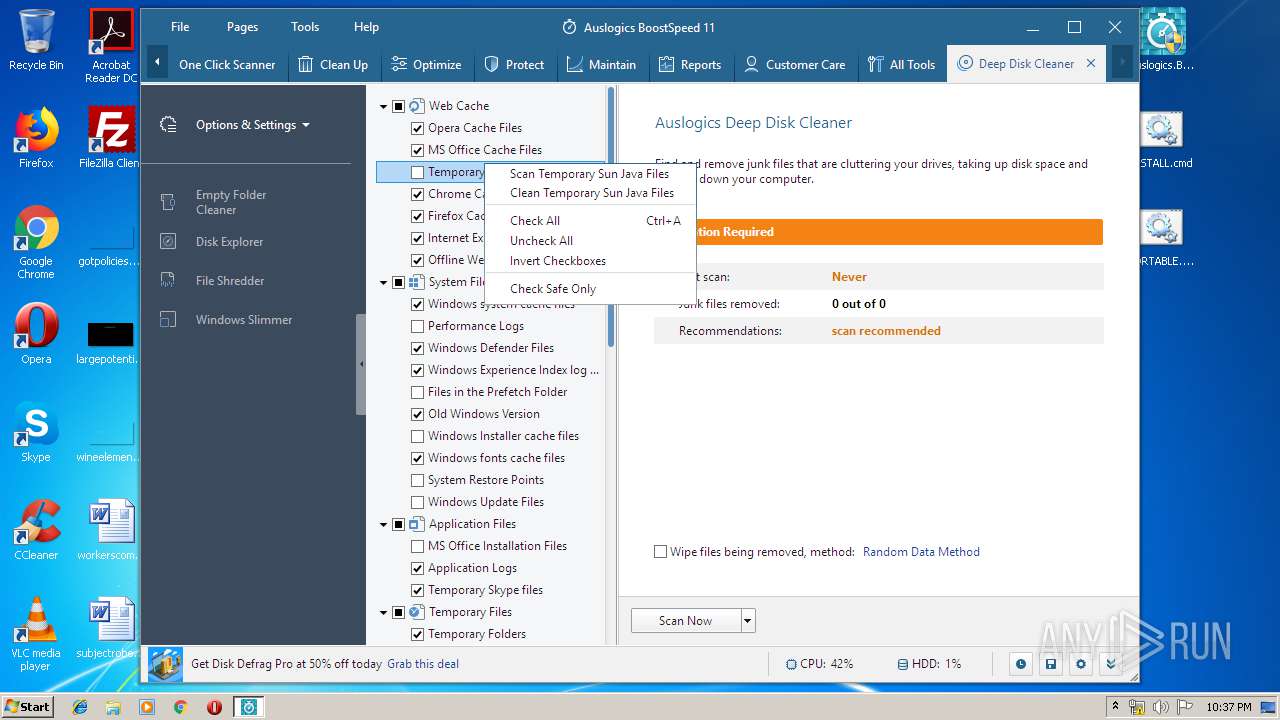
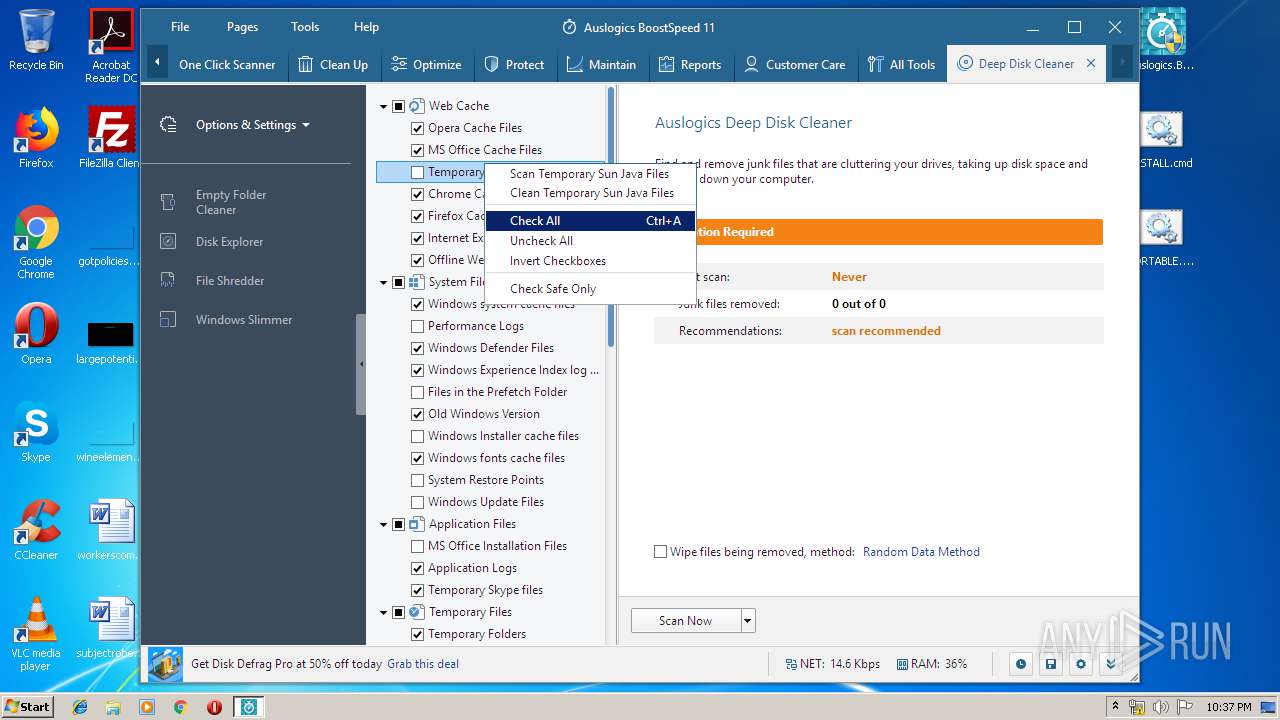
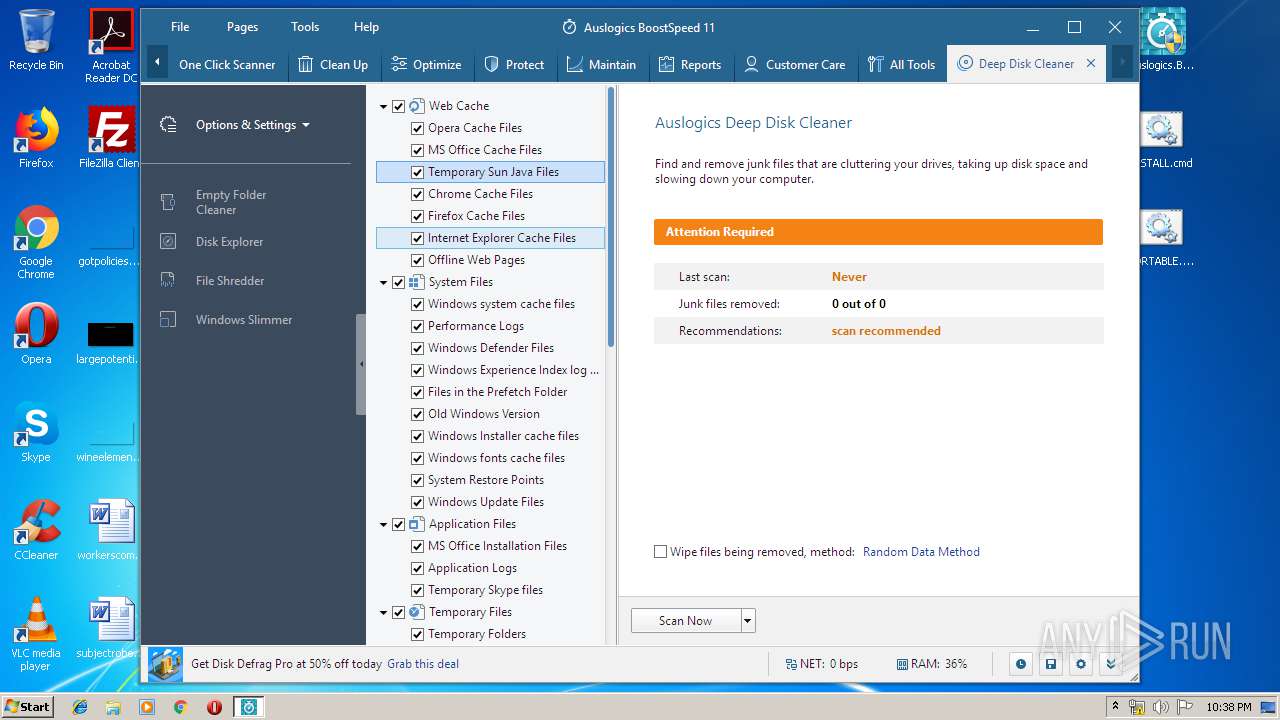
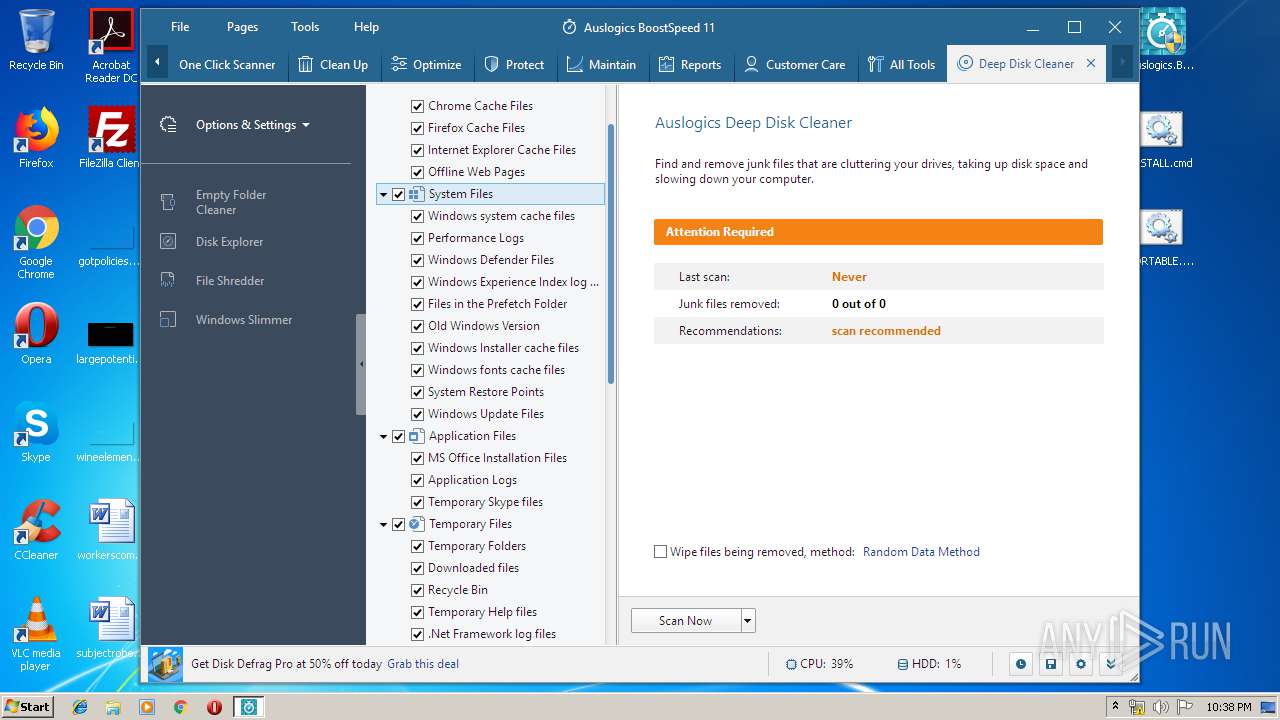
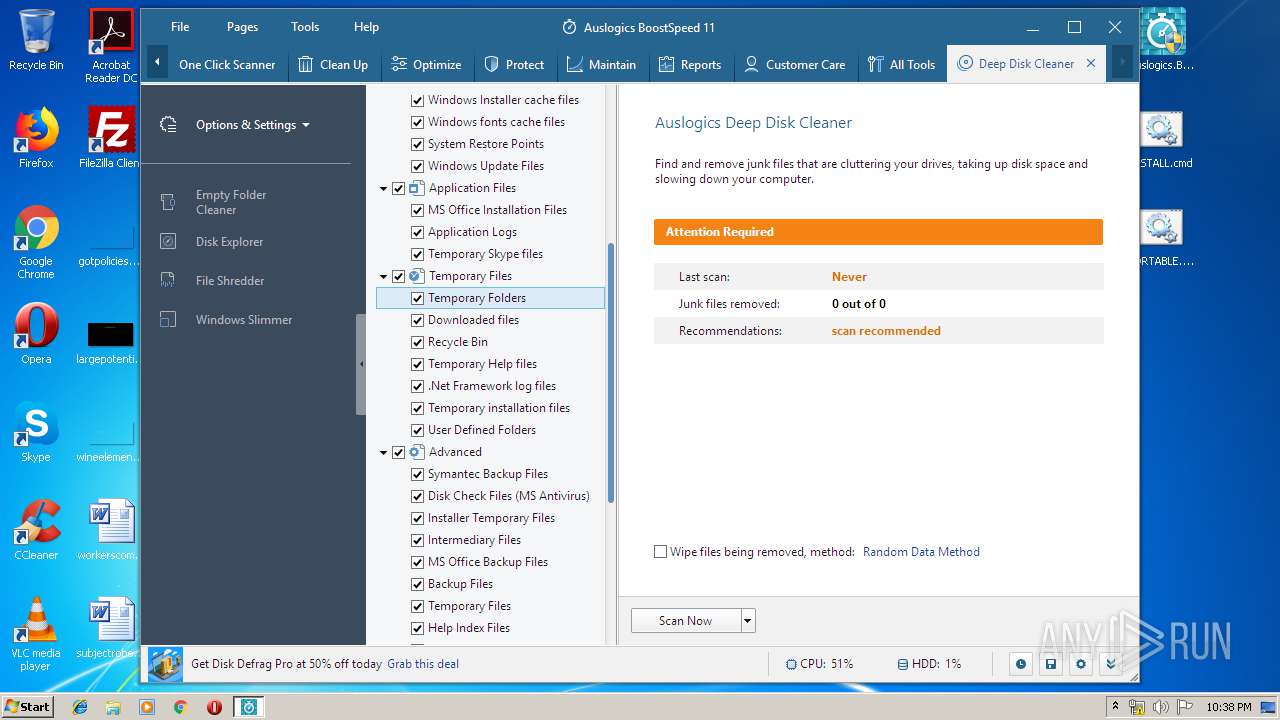
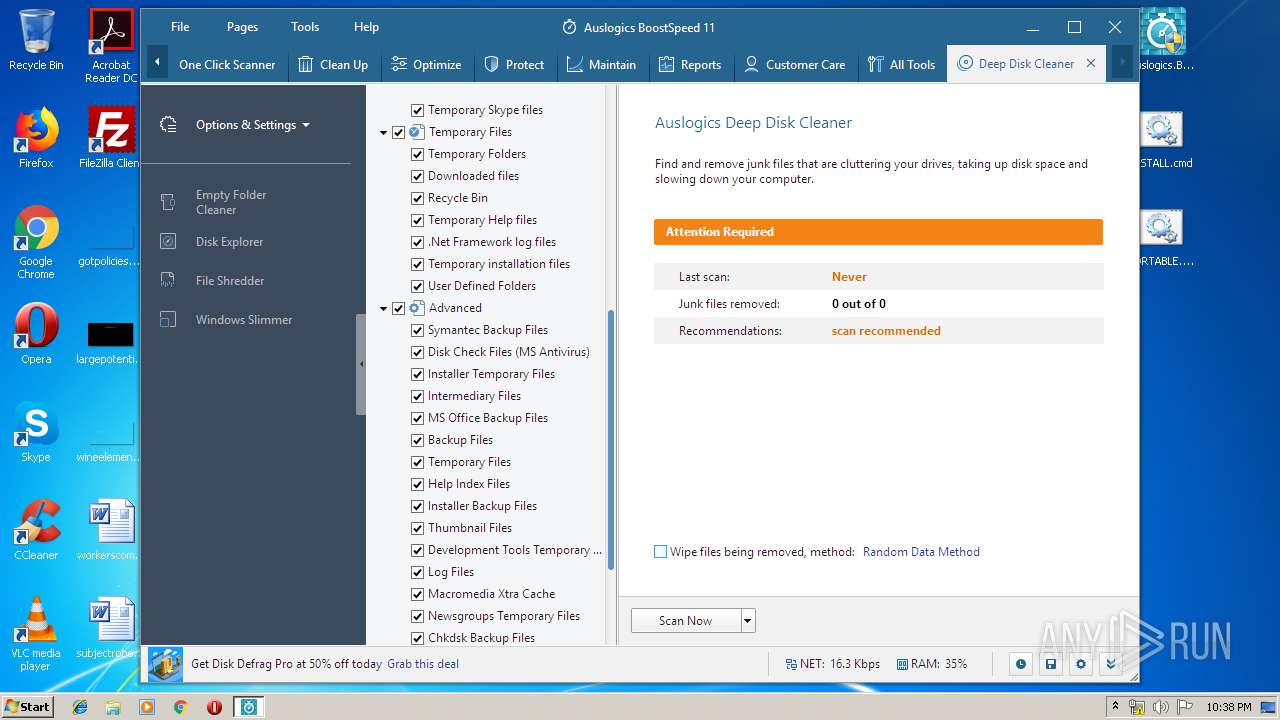
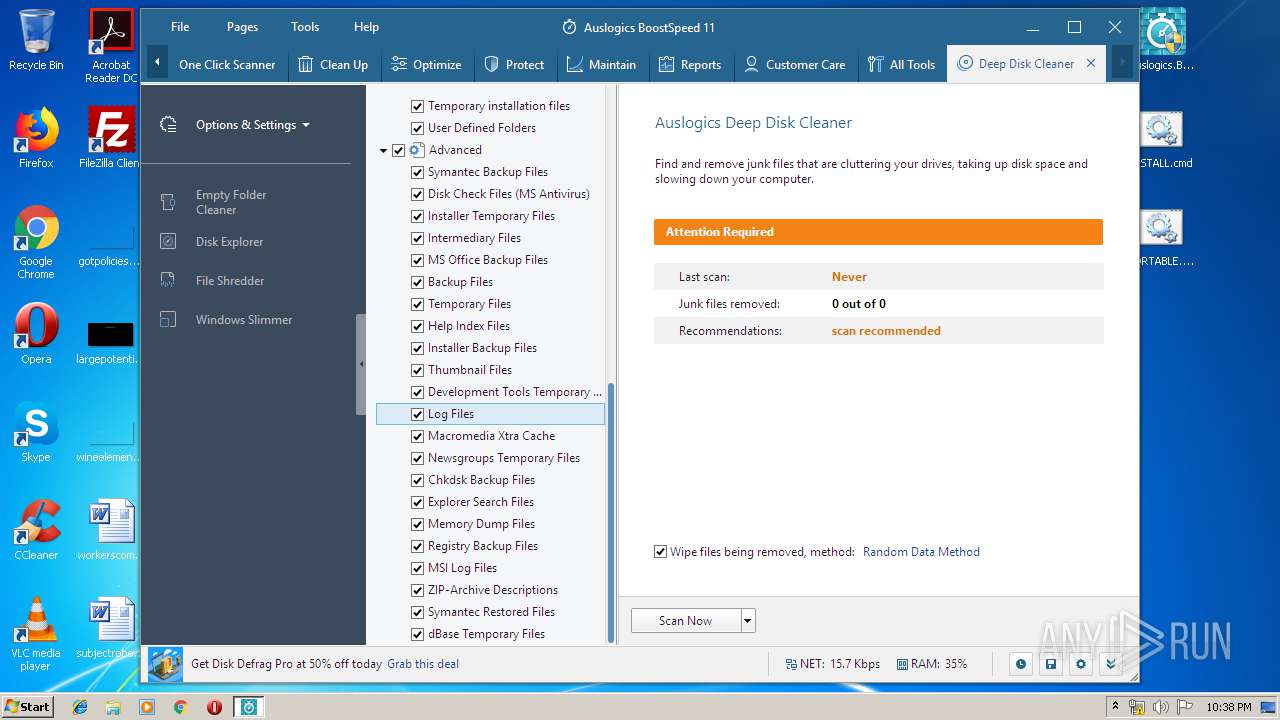
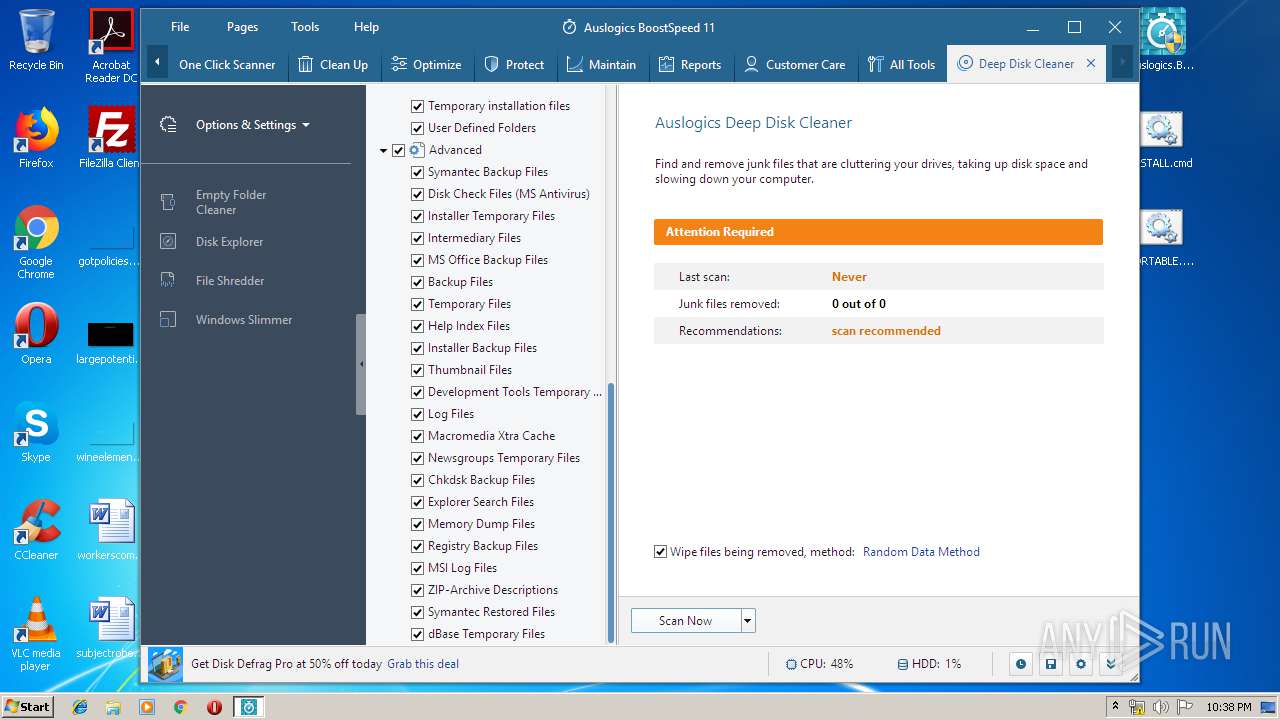
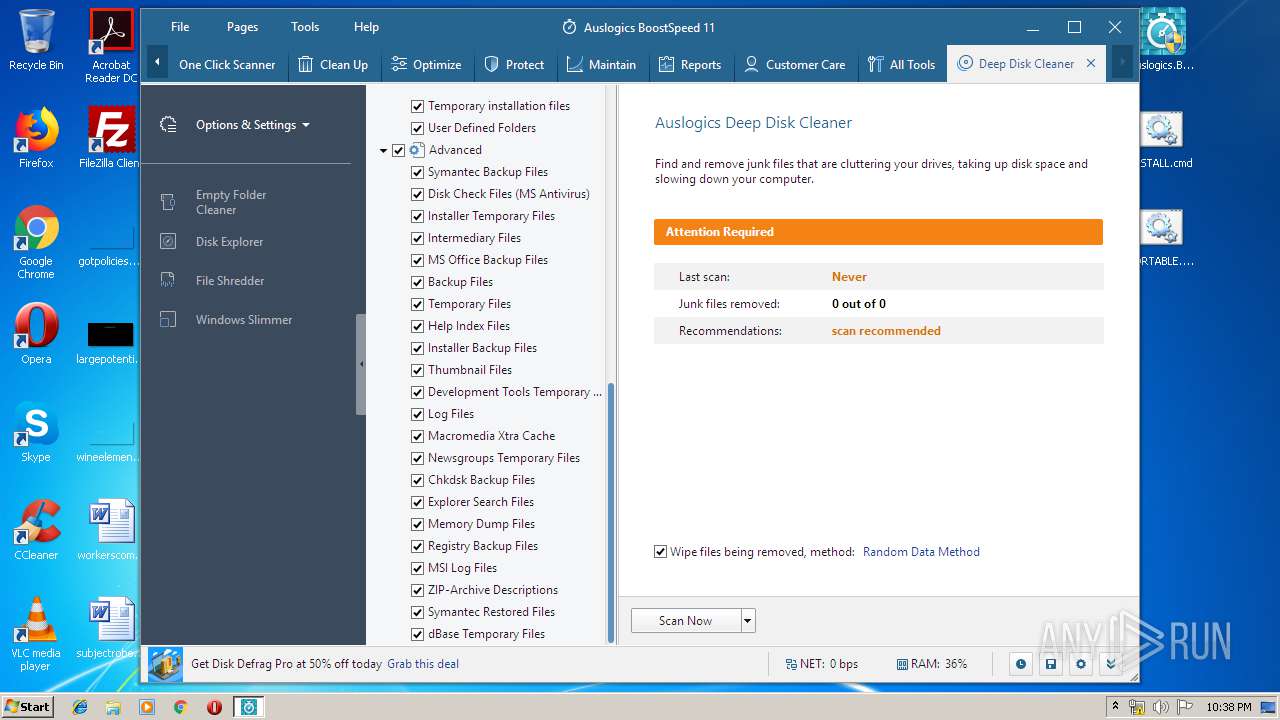
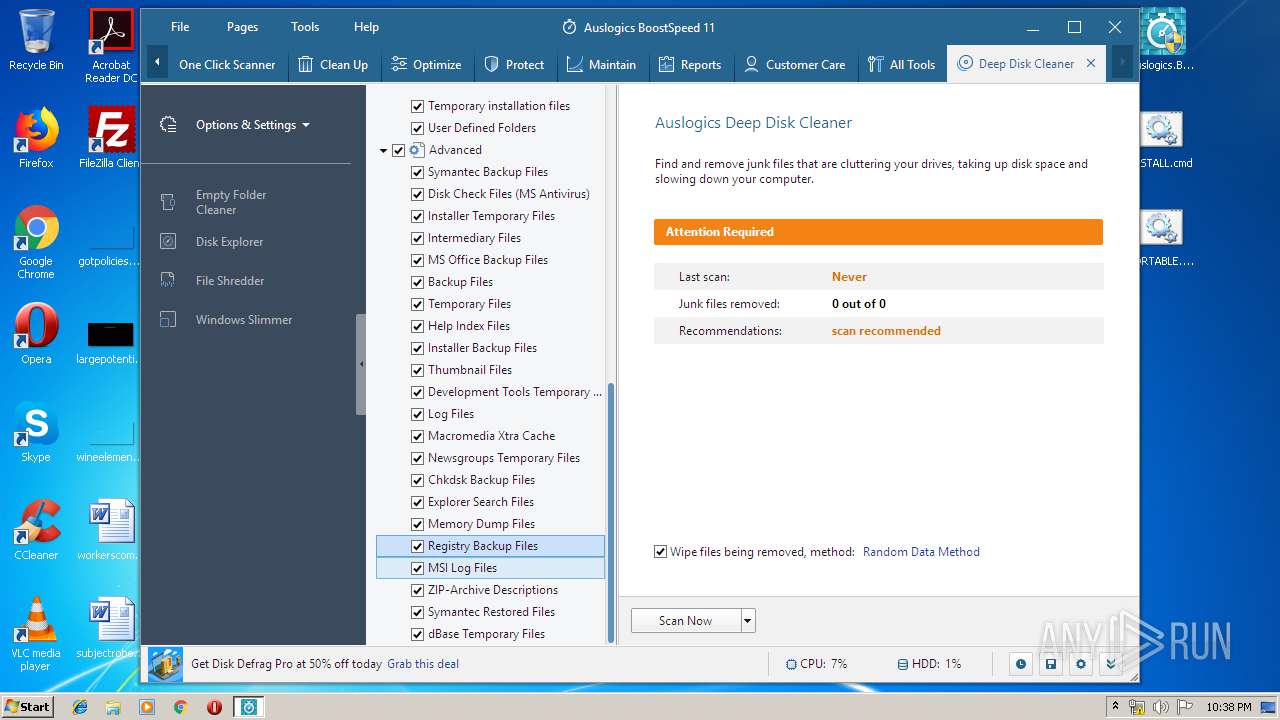
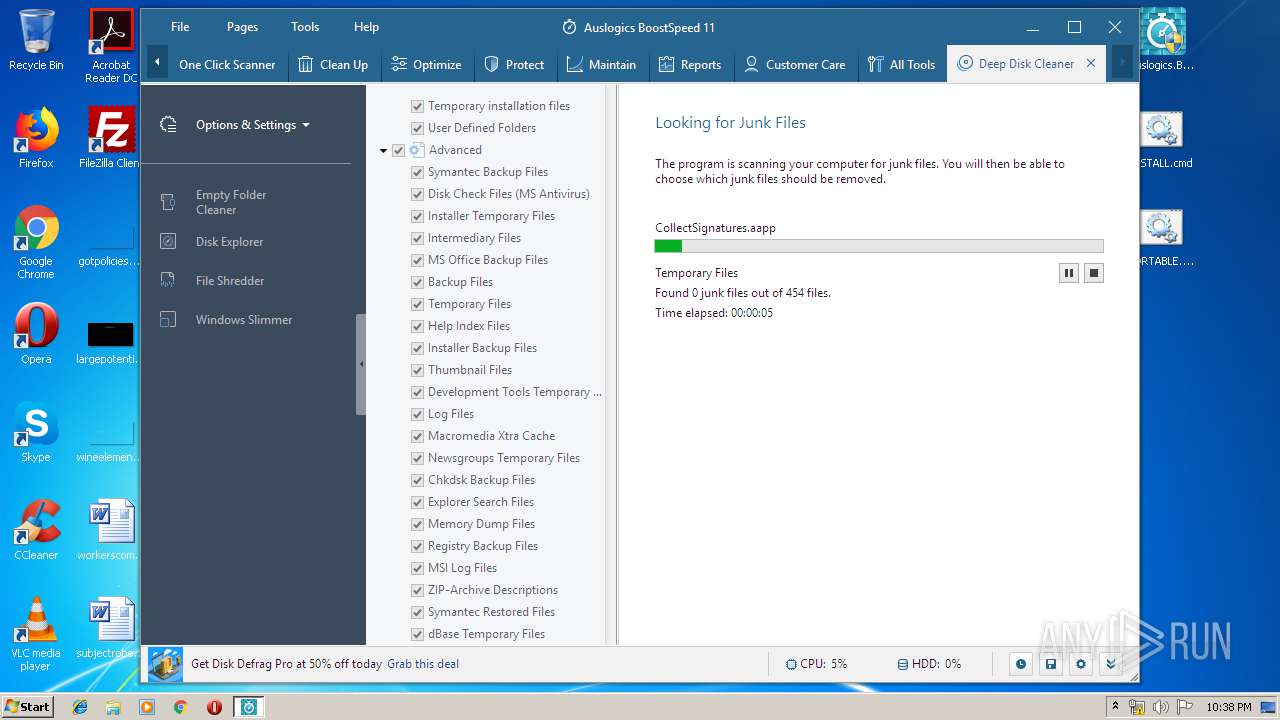
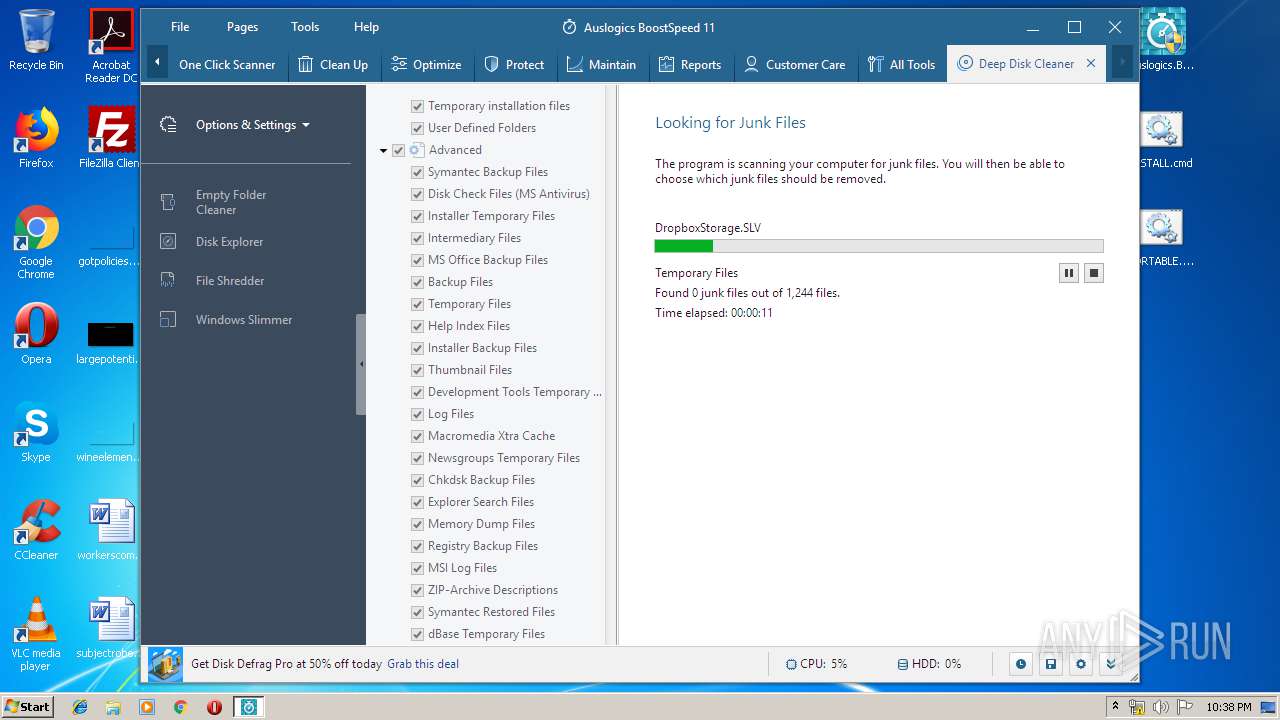
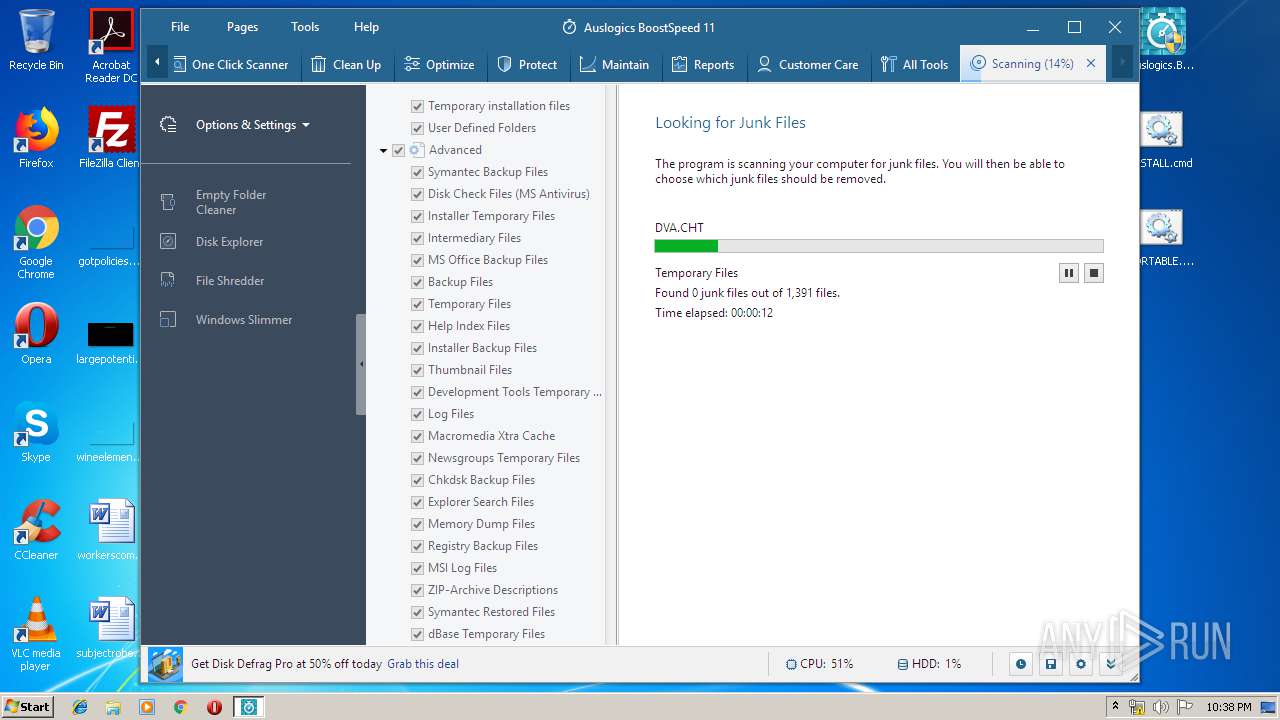
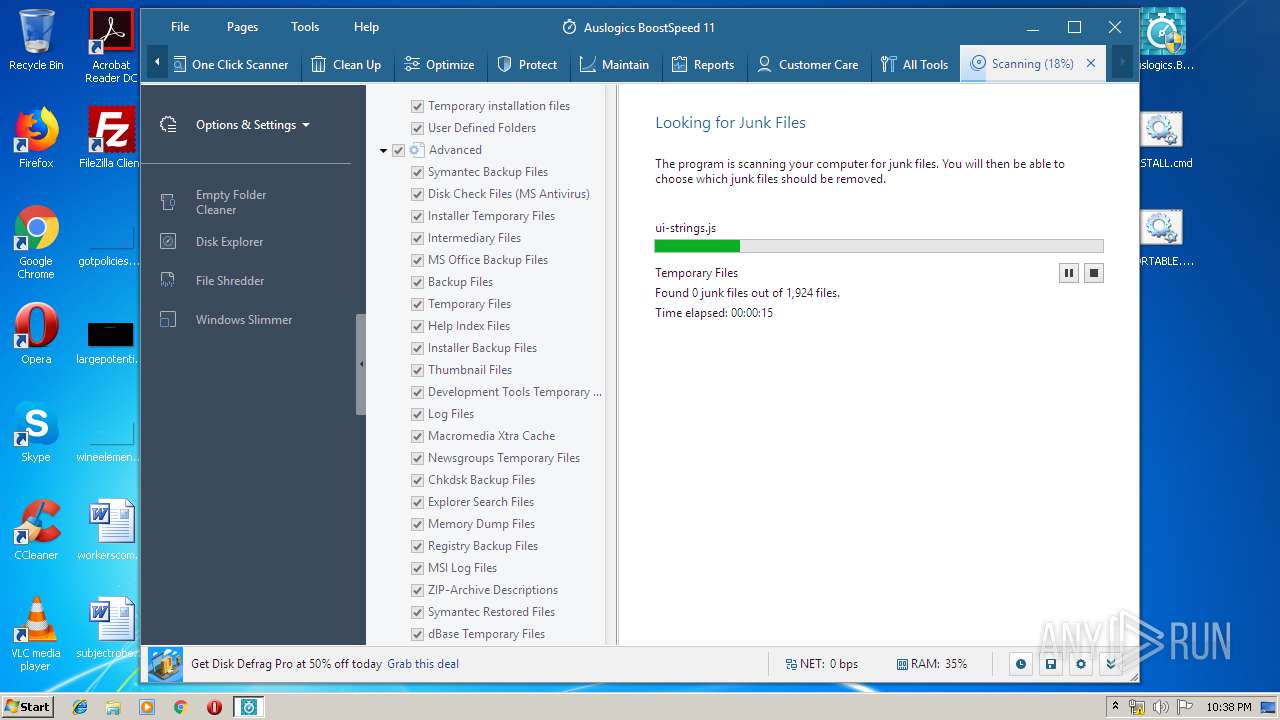
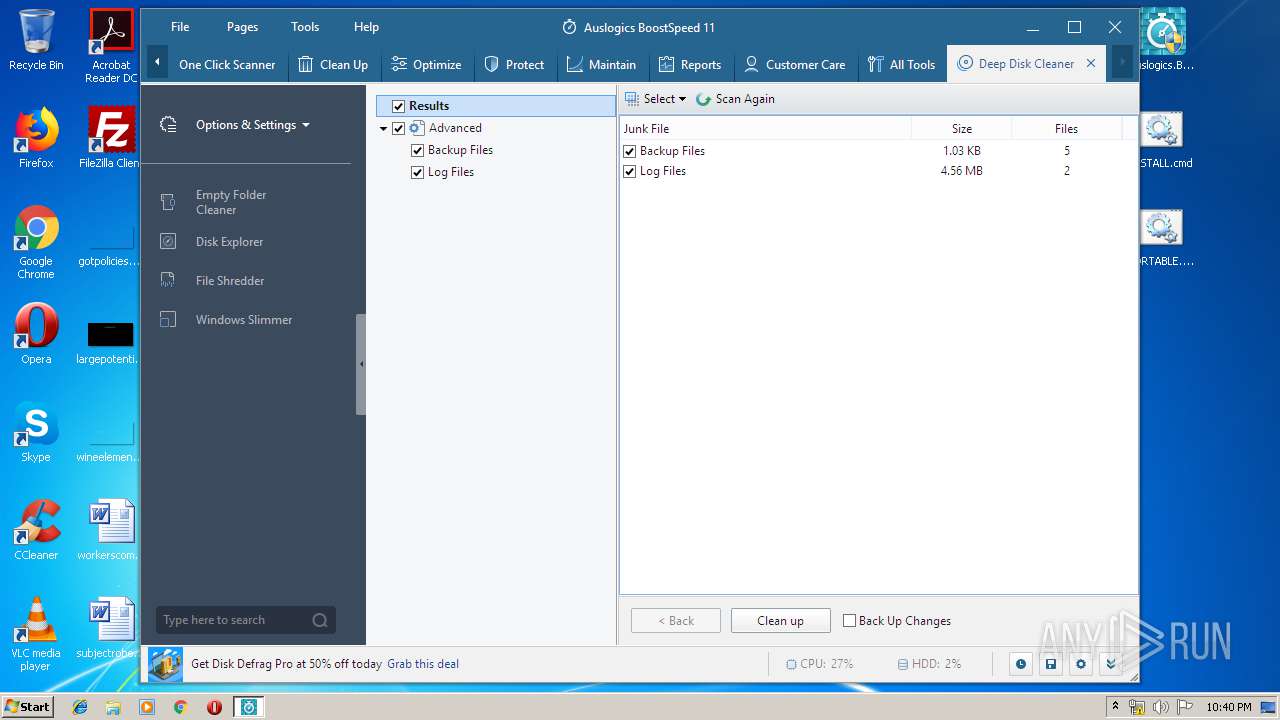
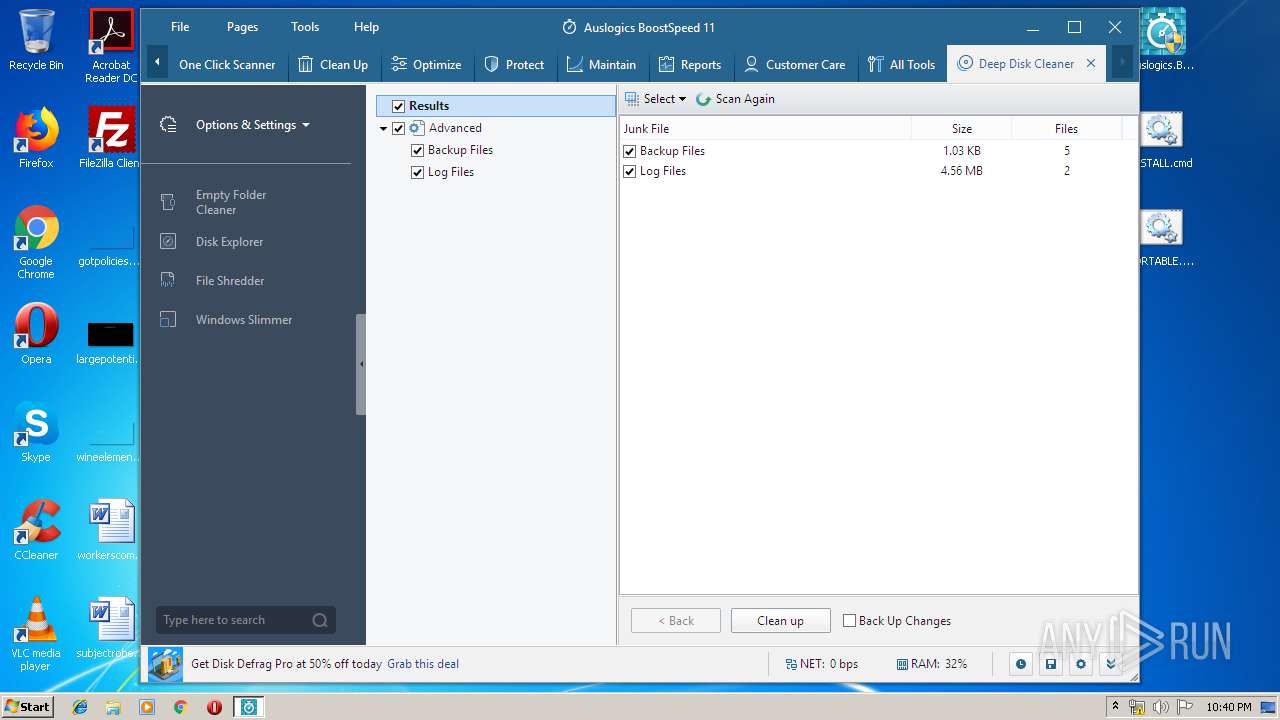
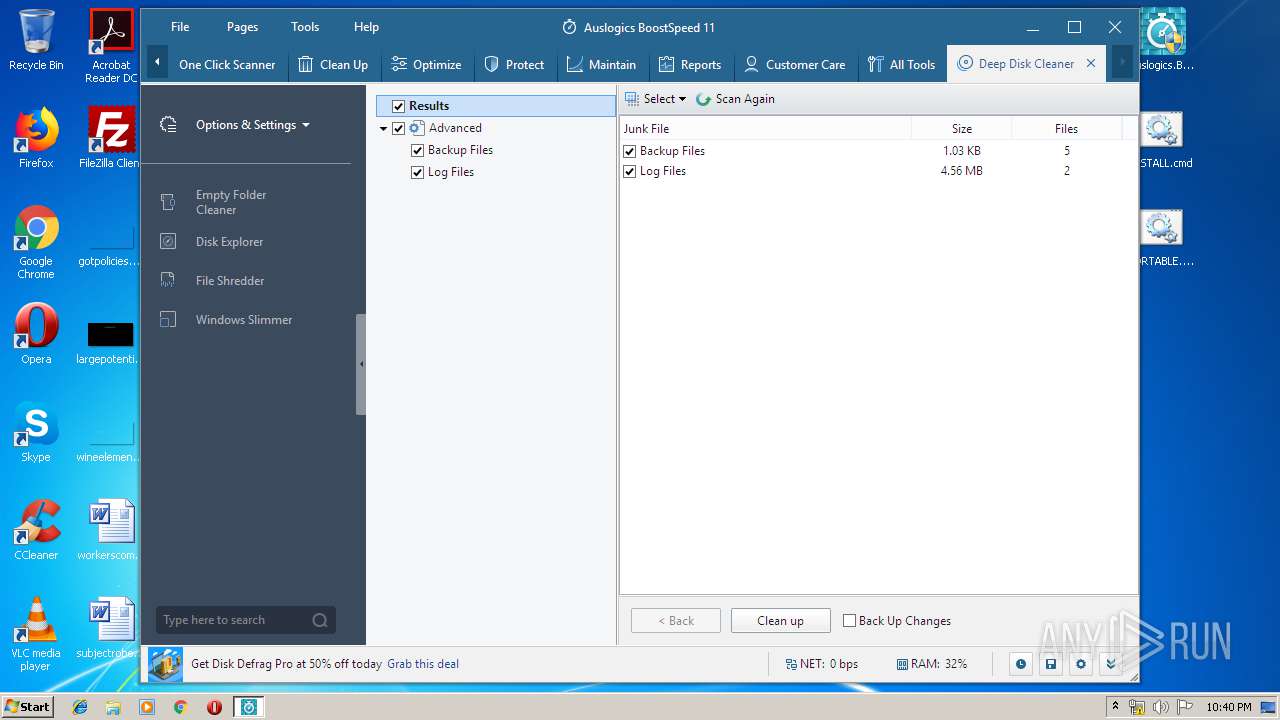
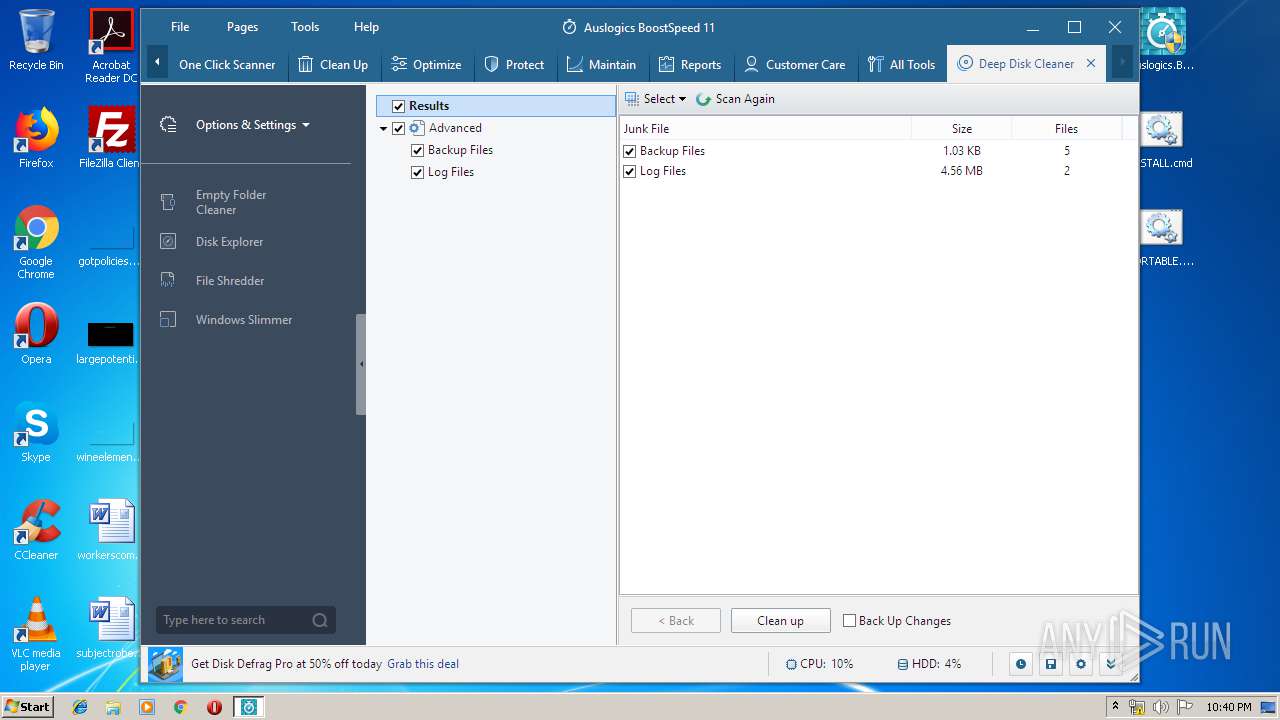
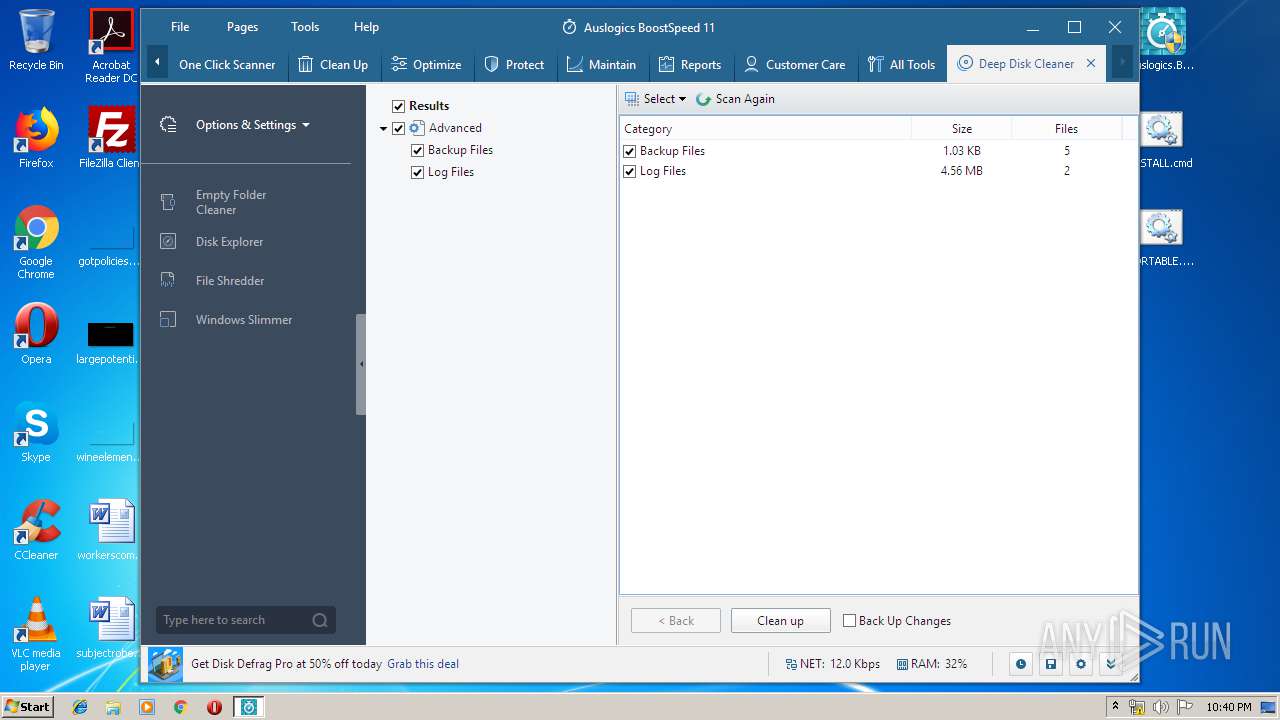
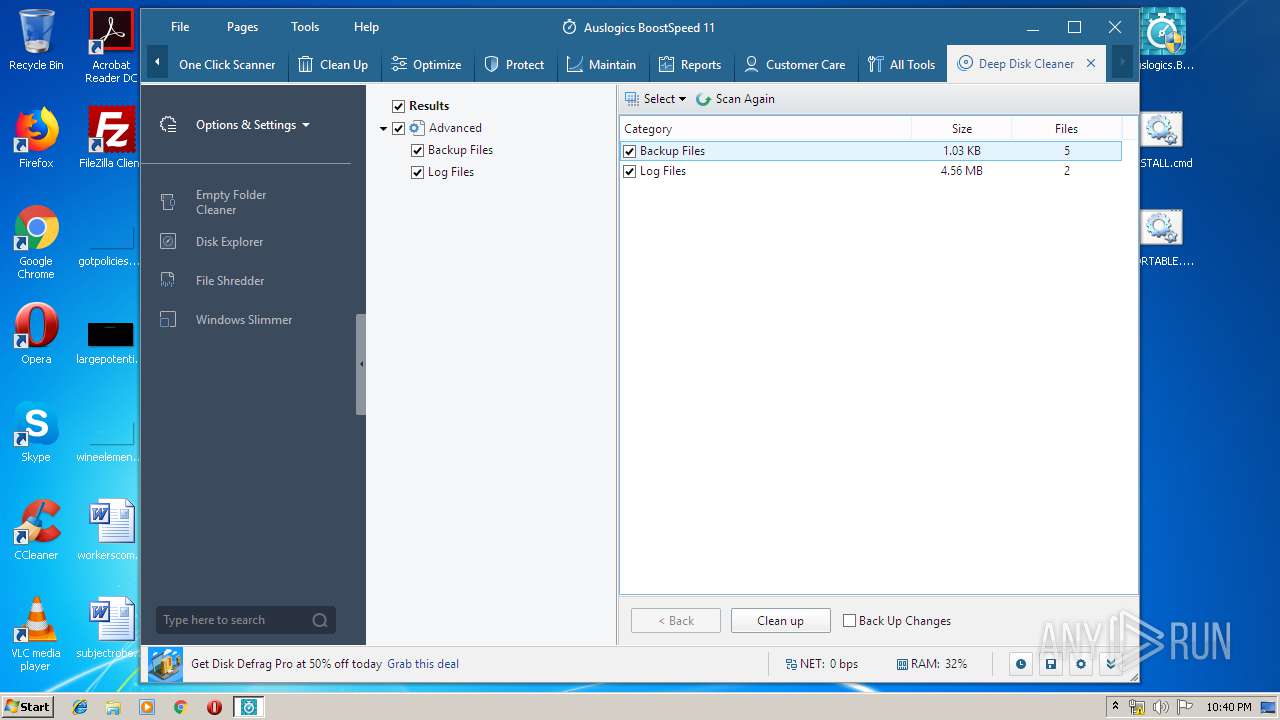
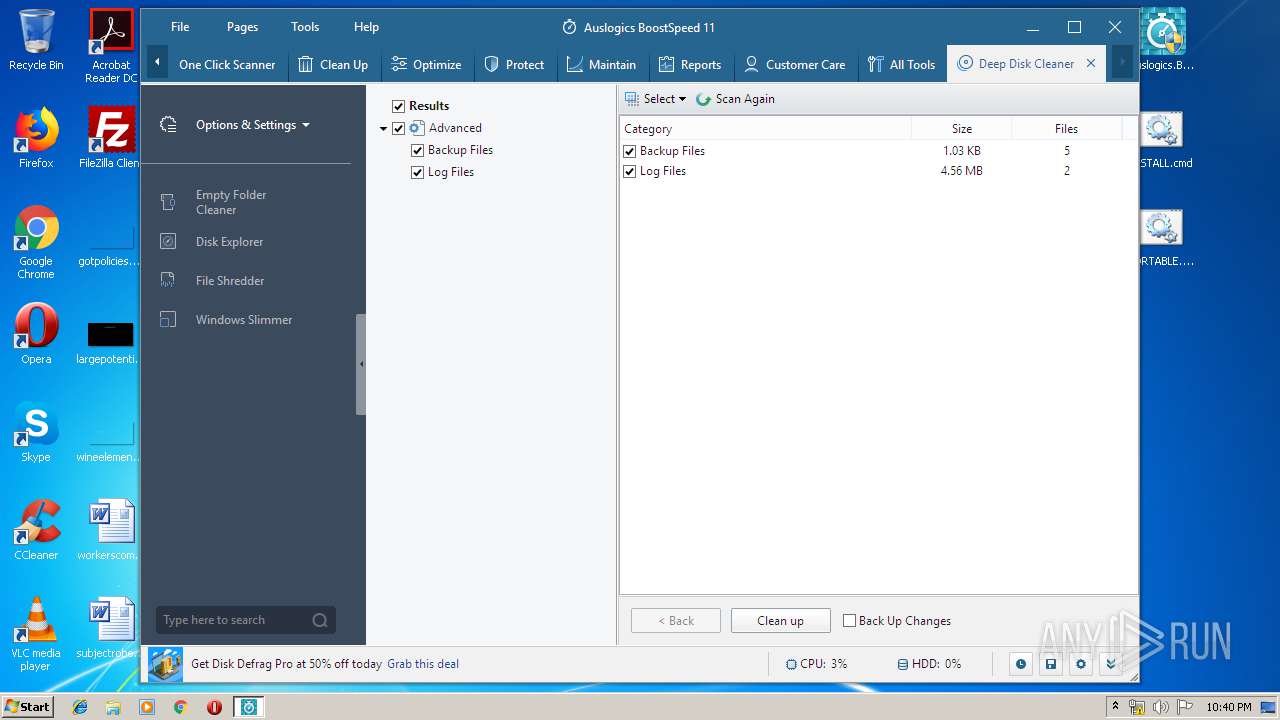
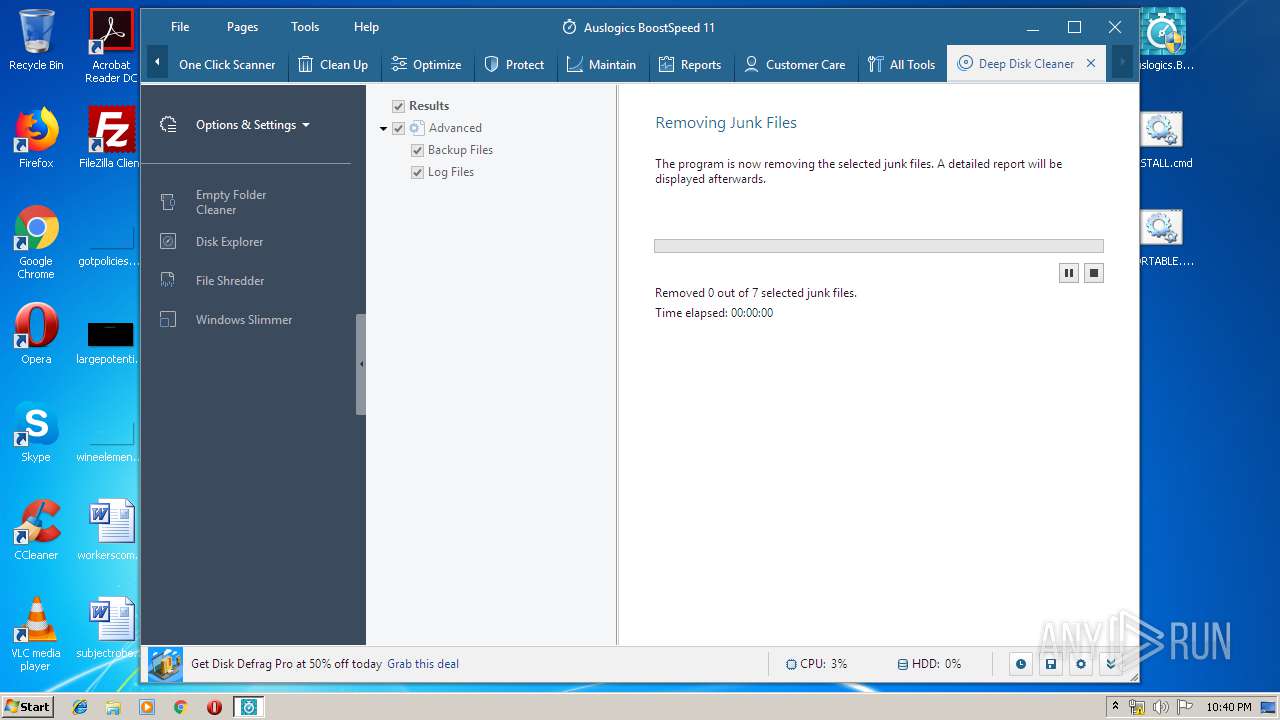
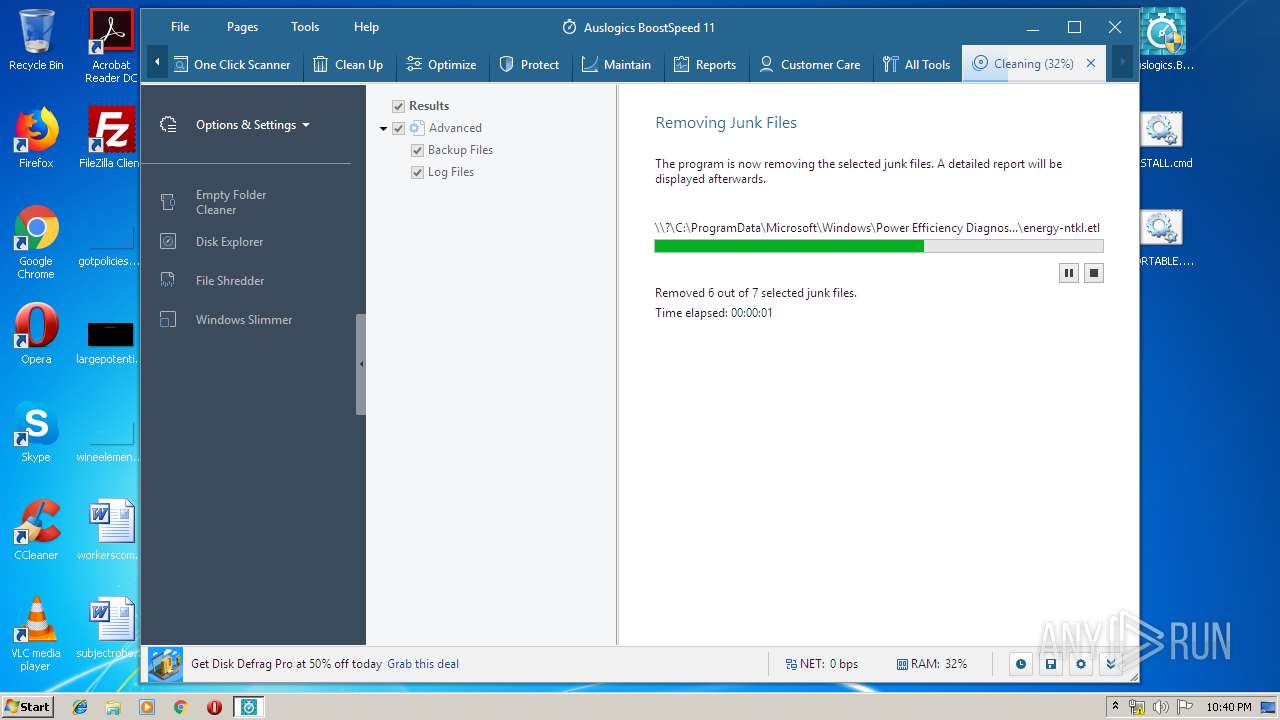
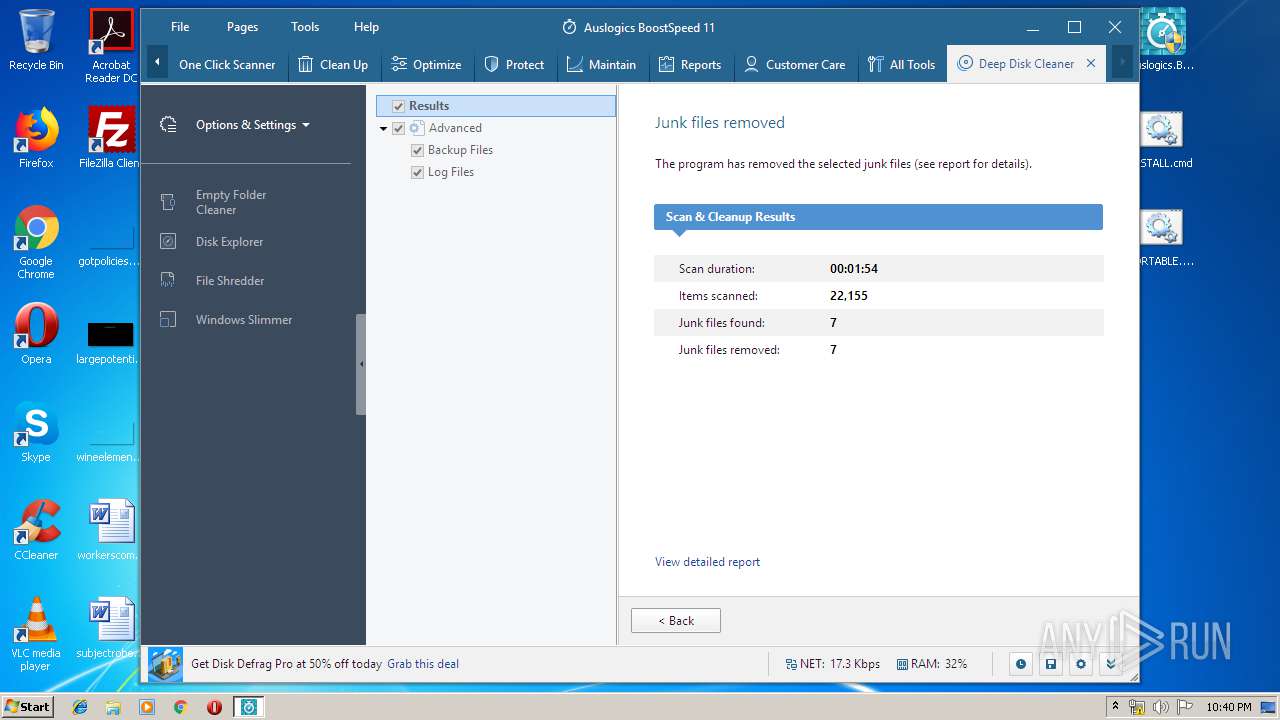
- DeepDiskCleaner.exe (PID: 2956)
- DeepDiskCleaner.exe (PID: 3576)
- tabdashboard.exe (PID: 3104)
Application was dropped or rewritten from another process
- nsF789.tmp (PID: 2504)
- AusLogicsBoostSpeed11Portable.exe (PID: 4092)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 2060)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 3804)
- AusLogicsBoostSpeed11Portable.exe (PID: 2128)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
- Integrator.exe (PID: 2712)
- nsF47A.tmp (PID: 2992)
- taballtools.exe (PID: 1764)
- tabcarecenter.exe (PID: 1316)
- tabmaintain.exe (PID: 3996)
- tabdashboard.exe (PID: 3104)
- tabcleanup.exe (PID: 1904)
- taboneclickscanner.exe (PID: 2996)
- taboptimize.exe (PID: 3948)
- tabprotect.exe (PID: 2352)
- tabreports.exe (PID: 3892)
- DeepDiskCleaner.exe (PID: 3576)
- DeepDiskCleaner.exe (PID: 2956)
Changes settings of System certificates
- Integrator.exe (PID: 2712)
Loads the Task Scheduler COM API
- Integrator.exe (PID: 2712)
- tabdashboard.exe (PID: 3104)
- taboptimize.exe (PID: 3948)
Actions looks like stealing of personal data
- tabprotect.exe (PID: 2352)
SUSPICIOUS
Executable content was dropped or overwritten
- flvpn.php.exe (PID: 3012)
- flvpn.php.exe (PID: 776)
- AusLogicsBoostSpeed11Portable.exe (PID: 2128)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
Reads the Windows organization settings
- flvpn.php.tmp (PID: 2700)
Starts SC.EXE for service management
- flvpn.php.tmp (PID: 2700)
Uses TASKKILL.EXE to kill process
- flvpn.php.tmp (PID: 2700)
Reads Windows owner or organization settings
- flvpn.php.tmp (PID: 2700)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3956)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
- Integrator.exe (PID: 2712)
Creates files in the user directory
- explorer.exe (PID: 352)
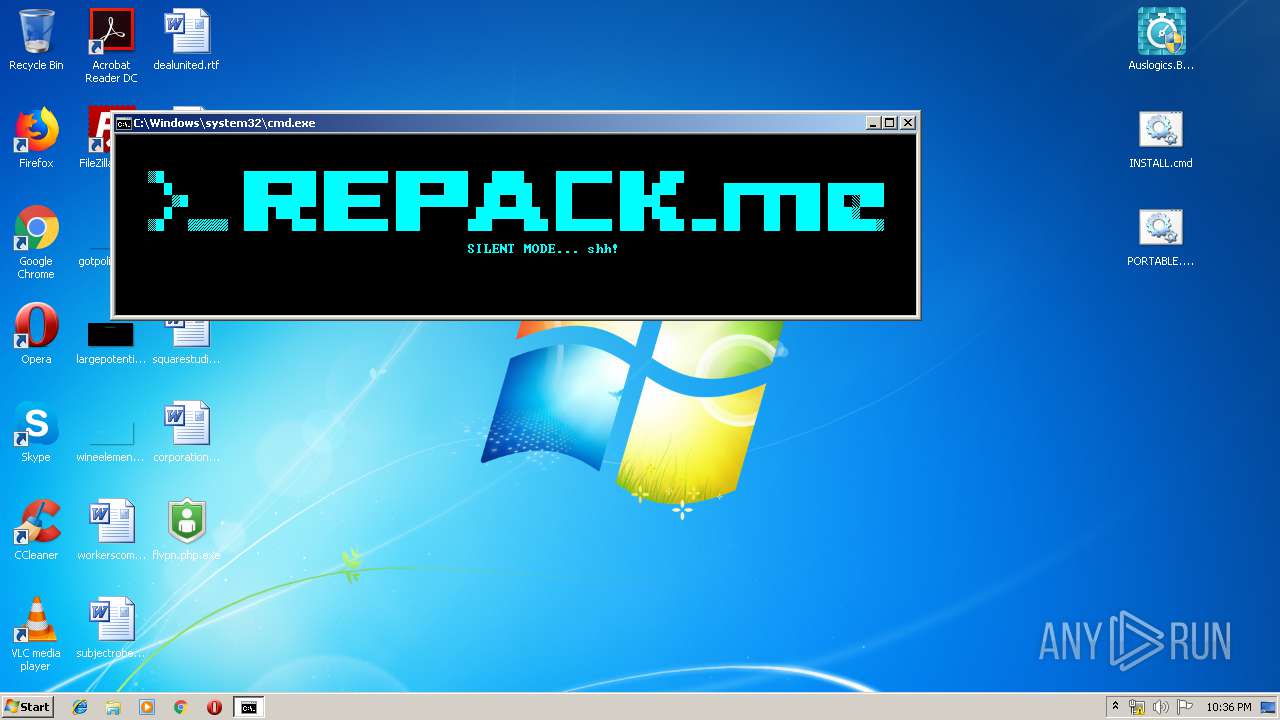
Starts CMD.EXE for commands execution
- explorer.exe (PID: 352)
Starts application with an unusual extension
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
Uses NETSH.EXE for network configuration
- nsF47A.tmp (PID: 2992)
Reads the machine GUID from the registry
- Integrator.exe (PID: 2712)
- tabcleanup.exe (PID: 1904)
- tabdashboard.exe (PID: 3104)
- taboneclickscanner.exe (PID: 2996)
- tabreports.exe (PID: 3892)
- taballtools.exe (PID: 1764)
- taboptimize.exe (PID: 3948)
- tabprotect.exe (PID: 2352)
- tabcarecenter.exe (PID: 1316)
- tabmaintain.exe (PID: 3996)
- DeepDiskCleaner.exe (PID: 2956)
- DeepDiskCleaner.exe (PID: 3576)
Reads Windows Product ID
- Integrator.exe (PID: 2712)
- tabdashboard.exe (PID: 3104)
- tabcleanup.exe (PID: 1904)
- taboneclickscanner.exe (PID: 2996)
- taballtools.exe (PID: 1764)
- tabreports.exe (PID: 3892)
- tabmaintain.exe (PID: 3996)
- tabcarecenter.exe (PID: 1316)
- taboptimize.exe (PID: 3948)
- tabprotect.exe (PID: 2352)
- DeepDiskCleaner.exe (PID: 2956)
- DeepDiskCleaner.exe (PID: 3576)
Reads the BIOS version
- Integrator.exe (PID: 2712)
- taboptimize.exe (PID: 3948)
- tabmaintain.exe (PID: 3996)
- tabcarecenter.exe (PID: 1316)
- DeepDiskCleaner.exe (PID: 2956)
- tabdashboard.exe (PID: 3104)
- tabprotect.exe (PID: 2352)
Adds / modifies Windows certificates
- Integrator.exe (PID: 2712)
Low-level read access rights to disk partition
- Integrator.exe (PID: 2712)
- tabcleanup.exe (PID: 1904)
- taboptimize.exe (PID: 3948)
- tabmaintain.exe (PID: 3996)
- tabdashboard.exe (PID: 3104)
- DeepDiskCleaner.exe (PID: 2956)
Executed via COM
- DllHost.exe (PID: 3856)
Creates files in the program directory
- Integrator.exe (PID: 2712)
- taboptimize.exe (PID: 3948)
- tabcarecenter.exe (PID: 1316)
- tabprotect.exe (PID: 2352)
- DeepDiskCleaner.exe (PID: 2956)
Searches for installed software
- taboptimize.exe (PID: 3948)
- tabmaintain.exe (PID: 3996)
- DeepDiskCleaner.exe (PID: 2956)
- taboneclickscanner.exe (PID: 2996)
- Integrator.exe (PID: 2712)
Creates COM task schedule object
- AusLogicsBoostSpeed11Portable.exe (PID: 2128)
INFO
Application was dropped or rewritten from another process
- flvpn.php.tmp (PID: 2700)
- flvpn.php.tmp (PID: 1532)
Application launched itself
- chrome.exe (PID: 3956)
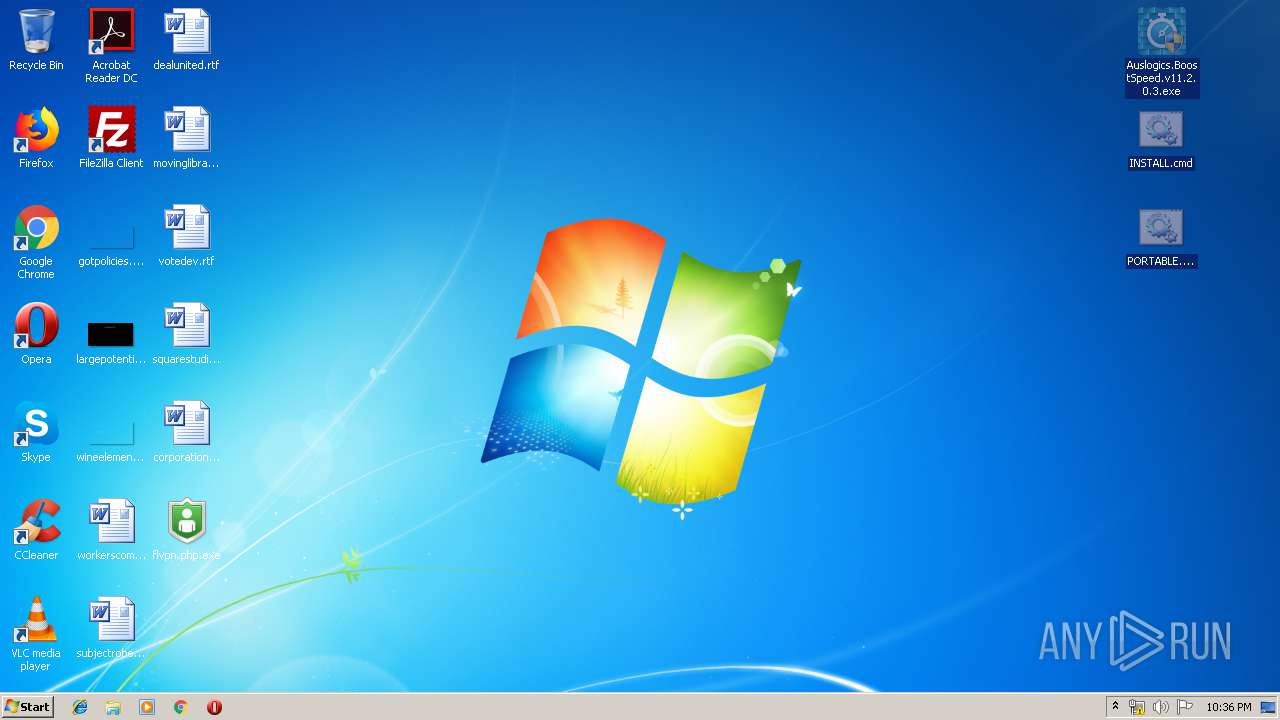
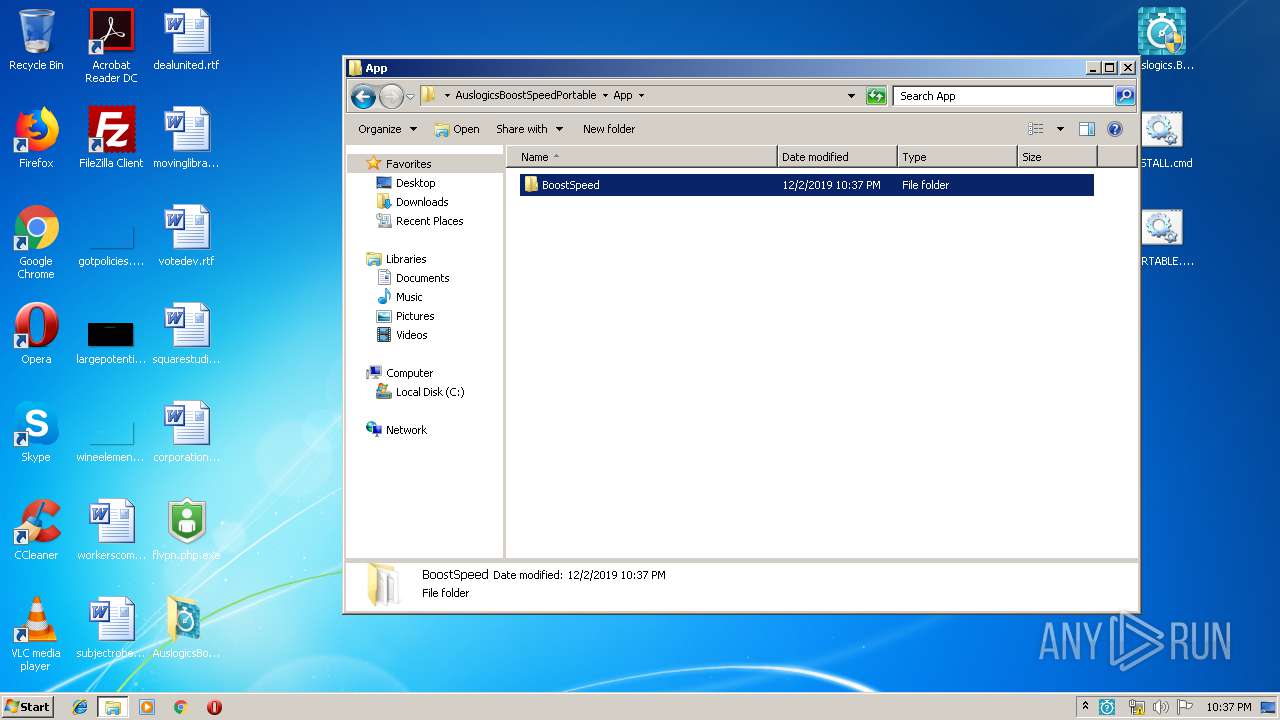
Manual execution by user
- chrome.exe (PID: 3956)
- cmd.exe (PID: 3840)
- AusLogicsBoostSpeed11Portable.exe (PID: 4092)
- AusLogicsBoostSpeed11Portable.exe (PID: 2128)
Reads the hosts file
- chrome.exe (PID: 2612)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
- chrome.exe (PID: 3956)
Reads settings of System Certificates
- chrome.exe (PID: 2612)
Reads Internet Cache Settings
- chrome.exe (PID: 3956)
Dropped object may contain Bitcoin addresses
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1560)
Reads Microsoft Office registry keys
- taboneclickscanner.exe (PID: 2996)
- taboptimize.exe (PID: 3948)
- tabmaintain.exe (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 165888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
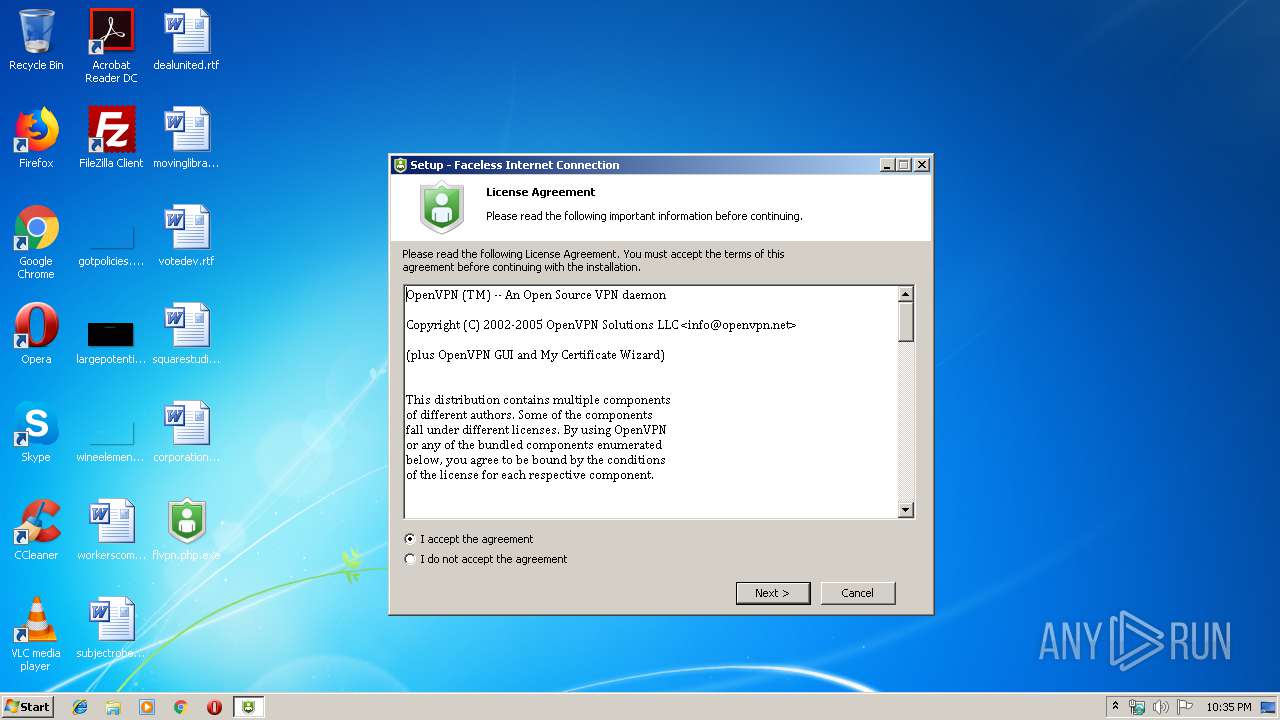
| FileDescription: | Faceless Internet Connection Setup |
| FileVersion: | |
| LegalCopyright: | Copyright © 2011 Faceless LLC |
| ProductName: | Faceless Internet Connection |
| ProductVersion: | 1.3.22 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Faceless Internet Connection Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright © 2011 Faceless LLC |
| ProductName: | Faceless Internet Connection |
| ProductVersion: | 1.3.22 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00026710 | 0x00026800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37826 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.72995 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.6841 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.89864 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.77322 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.92887 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.86345 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
123
Monitored processes
66
Malicious processes
17
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13658470690555012529,6061913510911400173,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4183196260130228338 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\Desktop\flvpn.php.exe" /SPAWNWND=$2019A /NOTIFYWND=$40138 | C:\Users\admin\Desktop\flvpn.php.exe | flvpn.php.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Faceless Internet Connection Setup Exit code: 2 Version: Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13658470690555012529,6061913510911400173,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7862292795661446361 --mojo-platform-channel-handle=3516 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3908 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,13658470690555012529,6061913510911400173,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11101008404732464503 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Users\admin\Desktop\AuslogicsBoostSpeedPortable\App\BoostSpeed\tabcarecenter.exe" | C:\Users\admin\Desktop\AuslogicsBoostSpeedPortable\App\BoostSpeed\tabcarecenter.exe | Integrator.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Care Center Exit code: 0 Version: 11.2.0.3 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,13658470690555012529,6061913510911400173,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4351833047056255605 --mojo-platform-channel-handle=4428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1416 | "C:\Windows\System32\sc.exe" stop Faceless | C:\Windows\System32\sc.exe | — | flvpn.php.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ed2a9d0,0x6ed2a9e0,0x6ed2a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
20 875
Read events
19 932
Write events
850
Delete events
93
Modification events
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 8C0A00006A2981CD60A9D501 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 86507EFCF50826AA3B7EC6054BDACCFD4C2D1E998522B2F7C036447231FFAB45 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 86507EFCF50826AA3B7EC6054BDACCFD4C2D1E998522B2F7C036447231FFAB45 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 8C0A00006A2981CD60A9D501 | |||
| (PID) Process: | (2700) flvpn.php.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 0000000001000000010000001C180000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF70ACACD760A9D50100000000 | |||
Executable files
111
Suspicious files
54
Text files
285
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\194a1dcd-840d-4e26-a01a-8a47ea4d0756.tmp | — | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3a1061.TMP | text | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3a1090.TMP | text | |
MD5:— | SHA256:— | |||
| 3956 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
38
DNS requests
29
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2712 | Integrator.exe | HEAD | 200 | 45.33.8.241:80 | http://ads.auslogics.com/uploads/50af3d5413855c55b7843c2659c42f65.png | US | — | — | whitelisted |
— | — | GET | 200 | 13.35.254.76:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2612 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
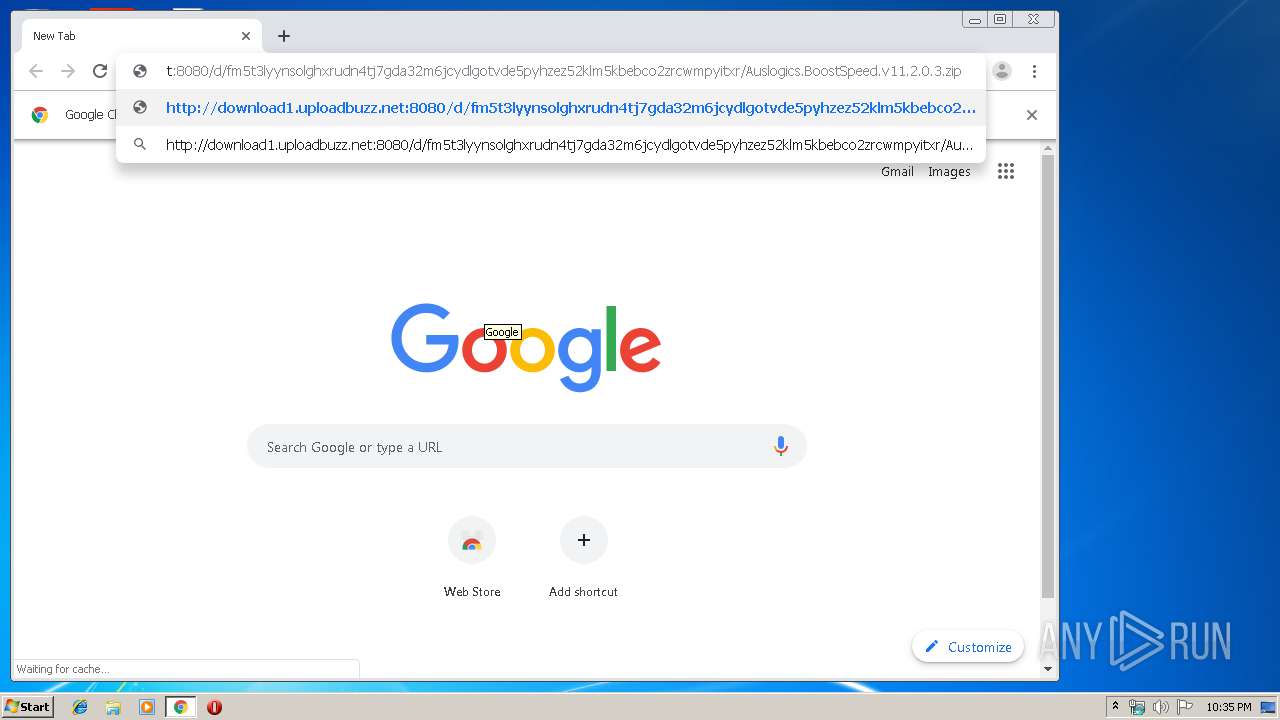
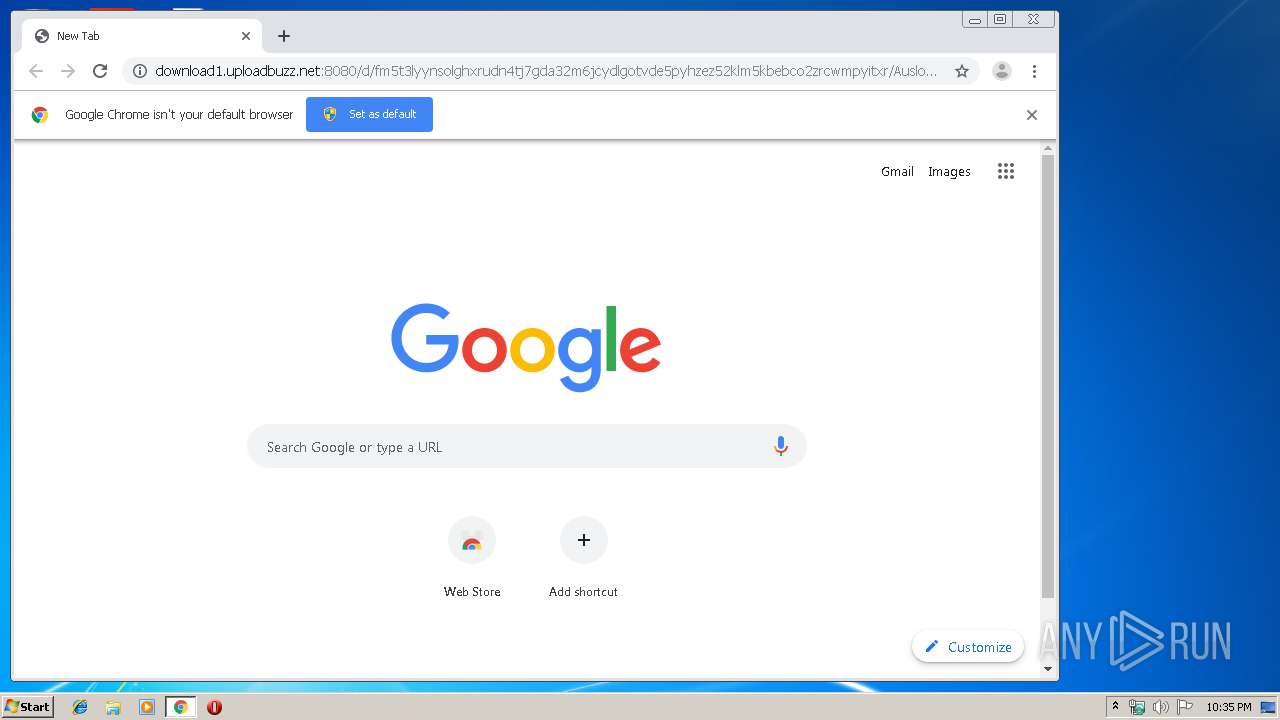
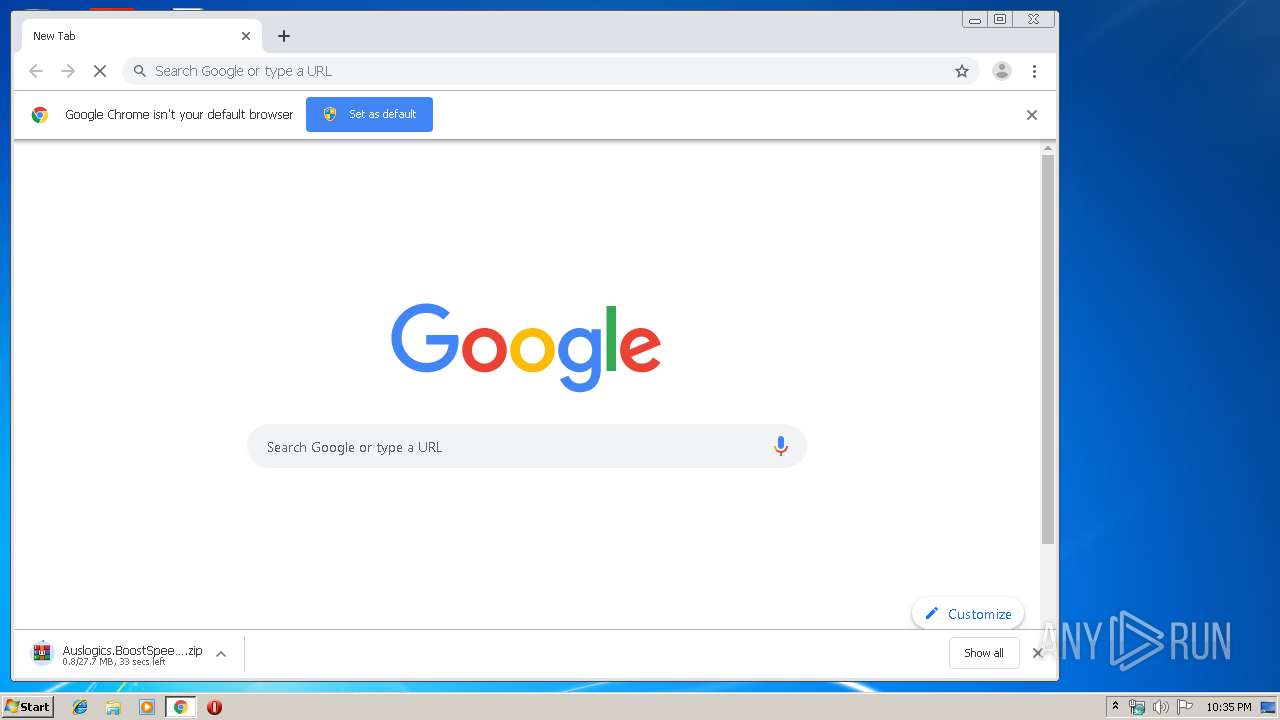
2612 | chrome.exe | GET | 200 | 5.79.69.194:8080 | http://download1.uploadbuzz.net:8080/d/fm5t3lyynsolghxrudn4tj7gda32m6jcydlgotvde5pyhzez52klm5kbebco2zrcwmpyitxr/Auslogics.BoostSpeed.v11.2.0.3.zip | NL | compressed | 27.7 Mb | unknown |
2612 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
— | — | GET | 200 | 13.35.254.226:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
— | — | GET | 200 | 143.204.208.145:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA4vBMJJxPg6SKCVbxEbKkA%3D | US | der | 471 b | whitelisted |
2612 | chrome.exe | GET | 200 | 173.194.7.57:80 | http://r3---sn-p5qlsnsr.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.94&mm=28&mn=sn-p5qlsnsr&ms=nvh&mt=1575326119&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2612 | chrome.exe | GET | 200 | 74.125.155.199:80 | http://r1---sn-p5qs7n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.94&mm=28&mn=sn-p5qs7n7z&ms=nvh&mt=1575326060&mv=m&mvi=0&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
— | — | GET | 200 | 143.204.208.228:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2612 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2612 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.22.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 74.125.155.199:80 | r1---sn-p5qs7n7z.gvt1.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
5 ETPRO signatures available at the full report