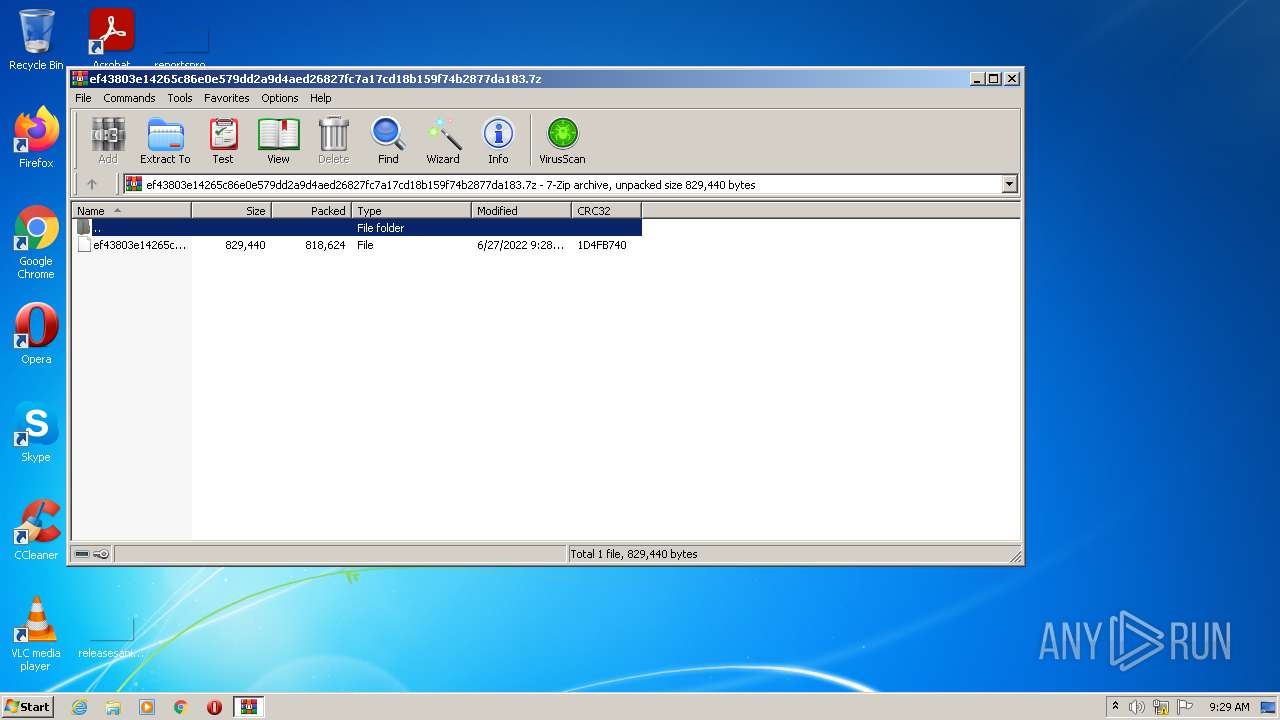
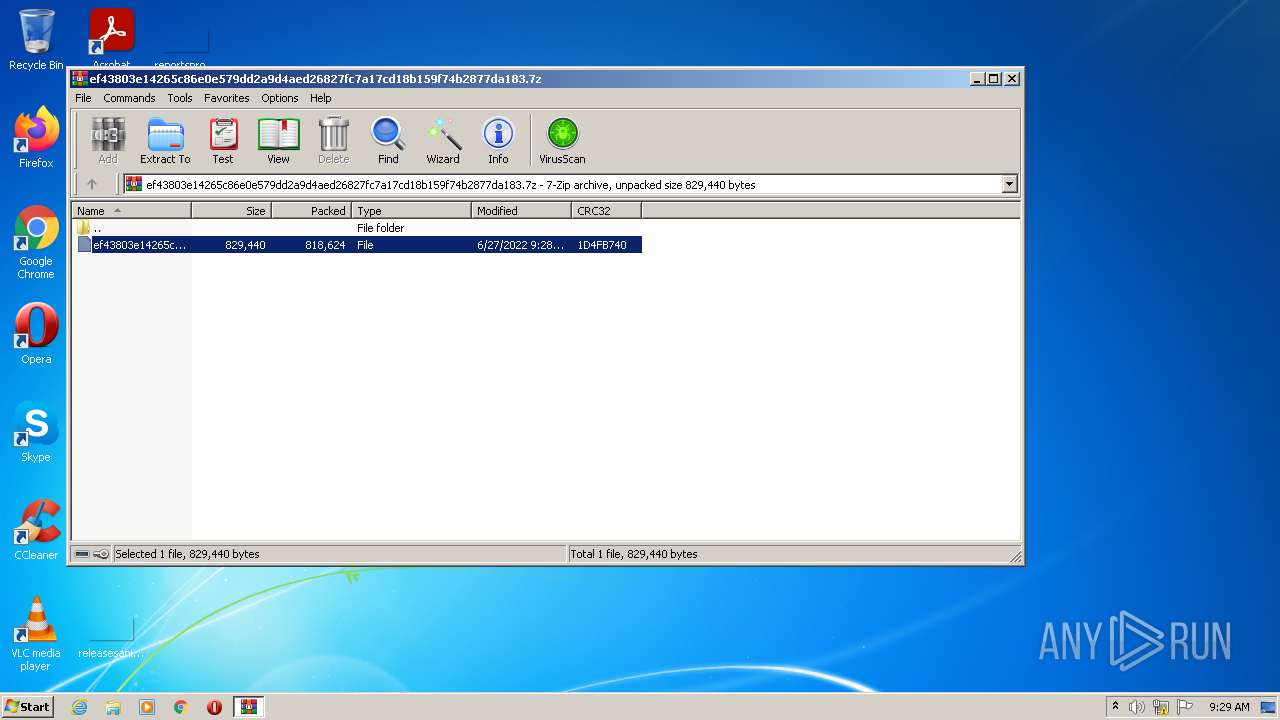
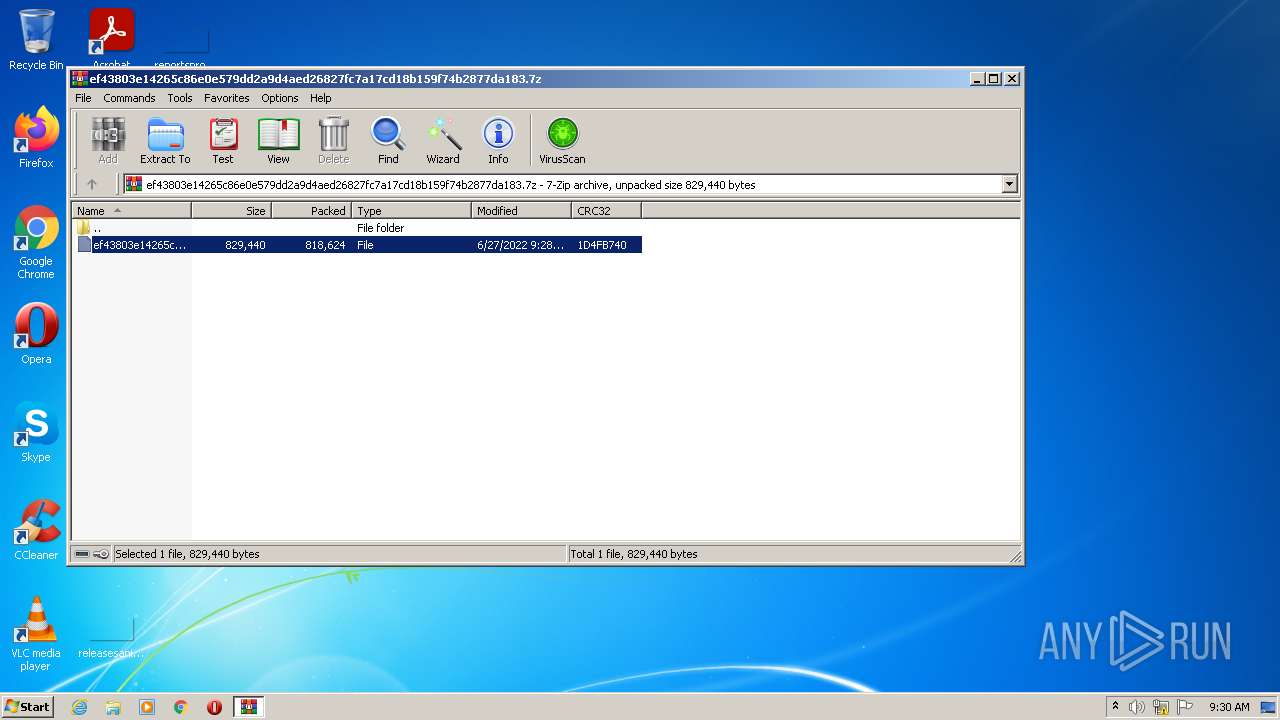
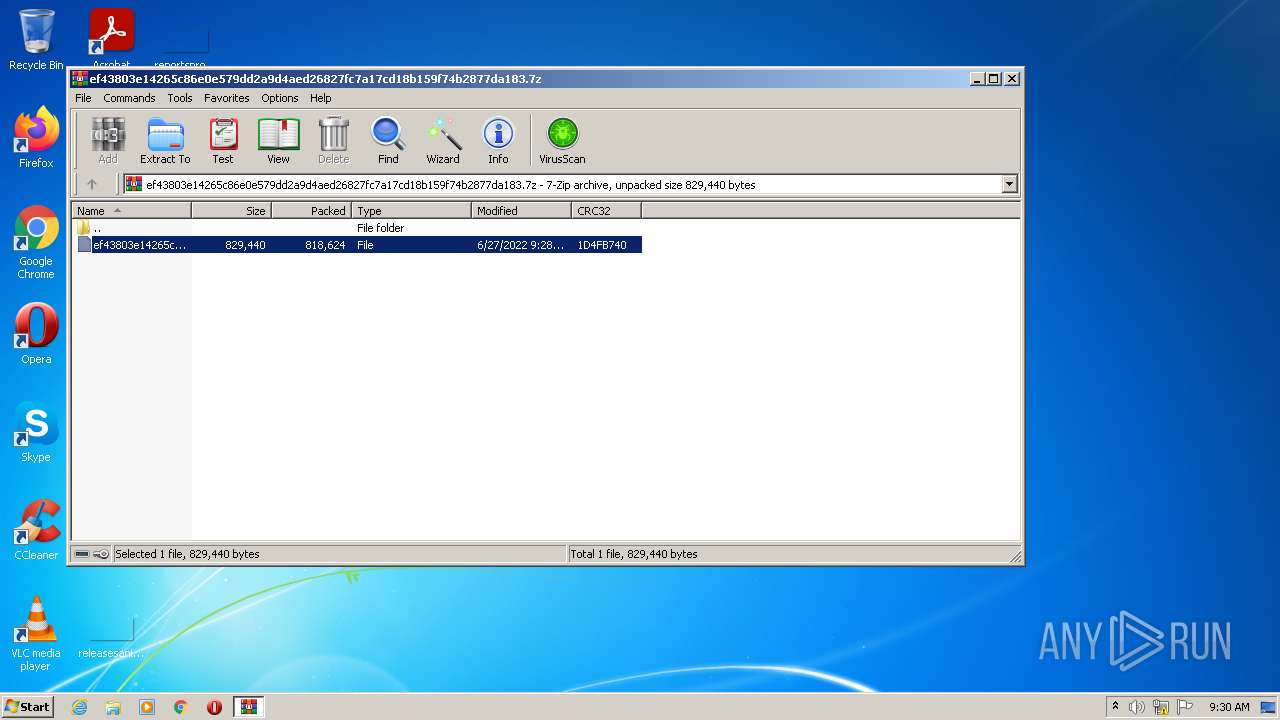
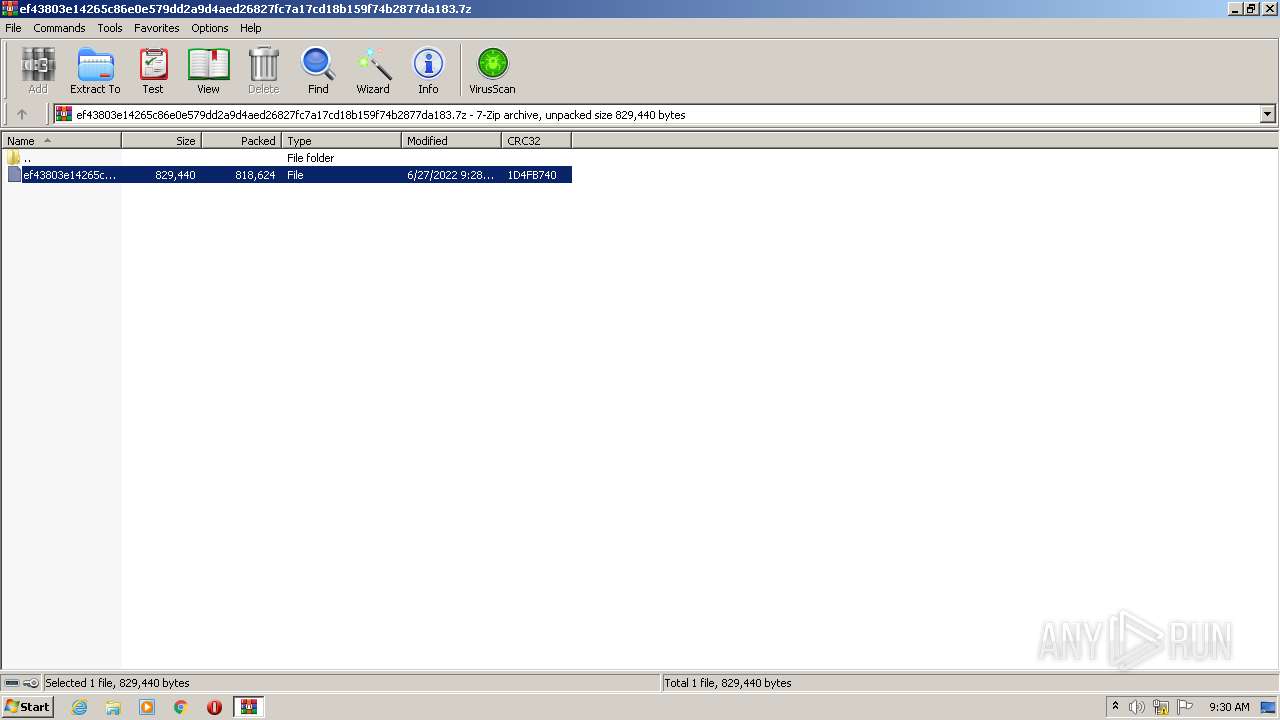
| File name: | ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183.7z |
| Full analysis: | https://app.any.run/tasks/a110cacd-aa1f-4b12-94d8-8ae0ddbc902f |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 08:29:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 6497176027838A757EBC9B747301090A |
| SHA1: | C68FE8EE1F48856A1434195C73D1BC981826B331 |
| SHA256: | 1A0252A83A7CBBC4A07F1066075132FC952BA6791396A9C8757E56E8CC6C24AA |
| SSDEEP: | 24576:D5ZiJTWbSL5vs//5nprgdP/VQpHRy4sPNS9Z:DLbSNvw/5pWnCH8Yj |
MALICIOUS
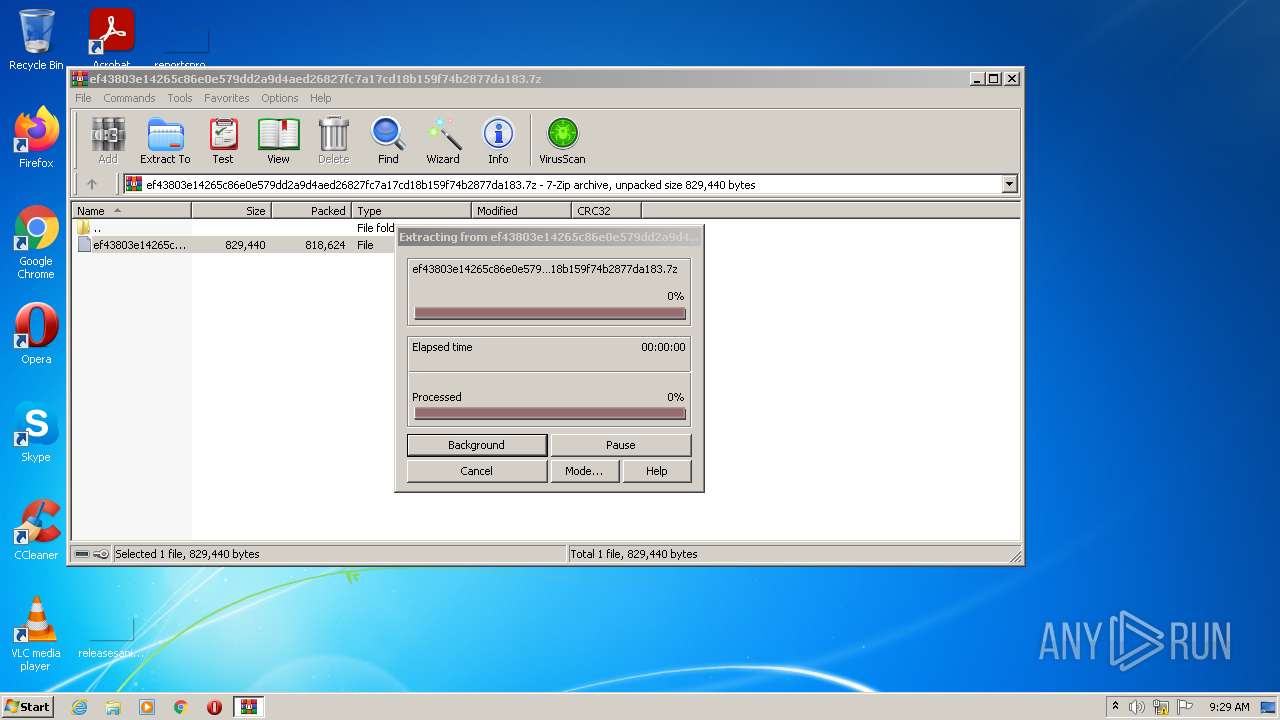
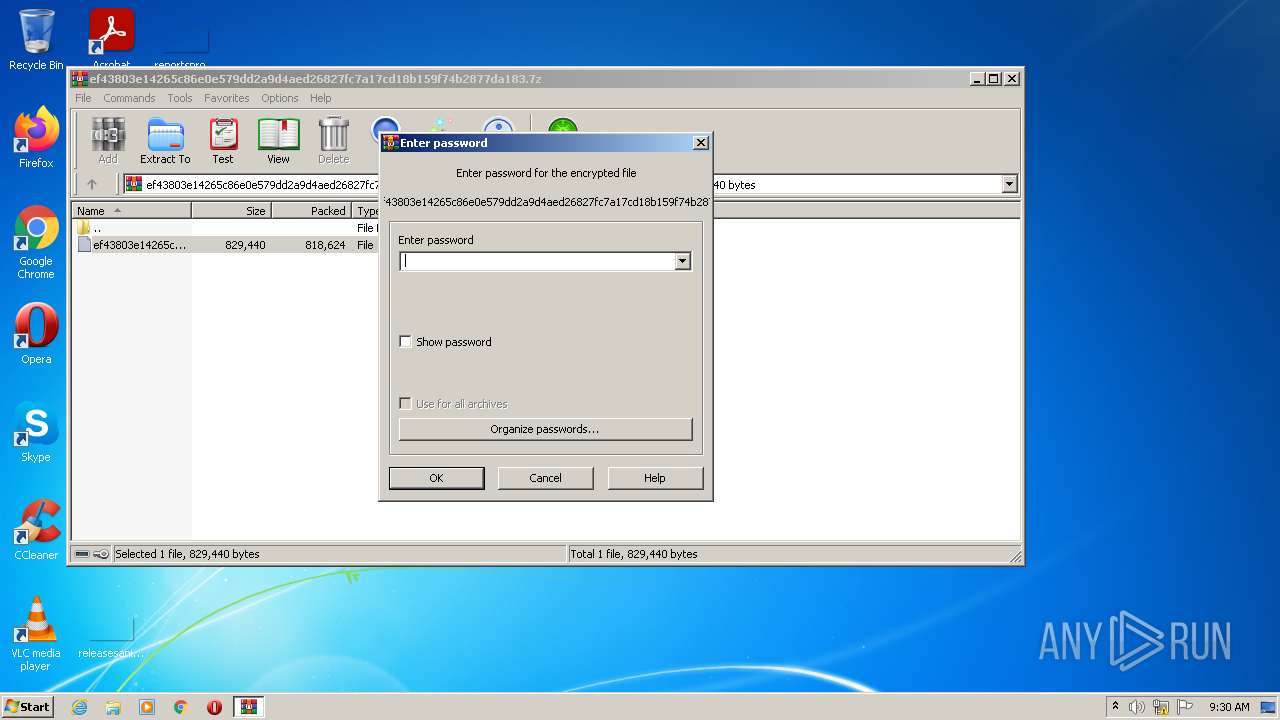
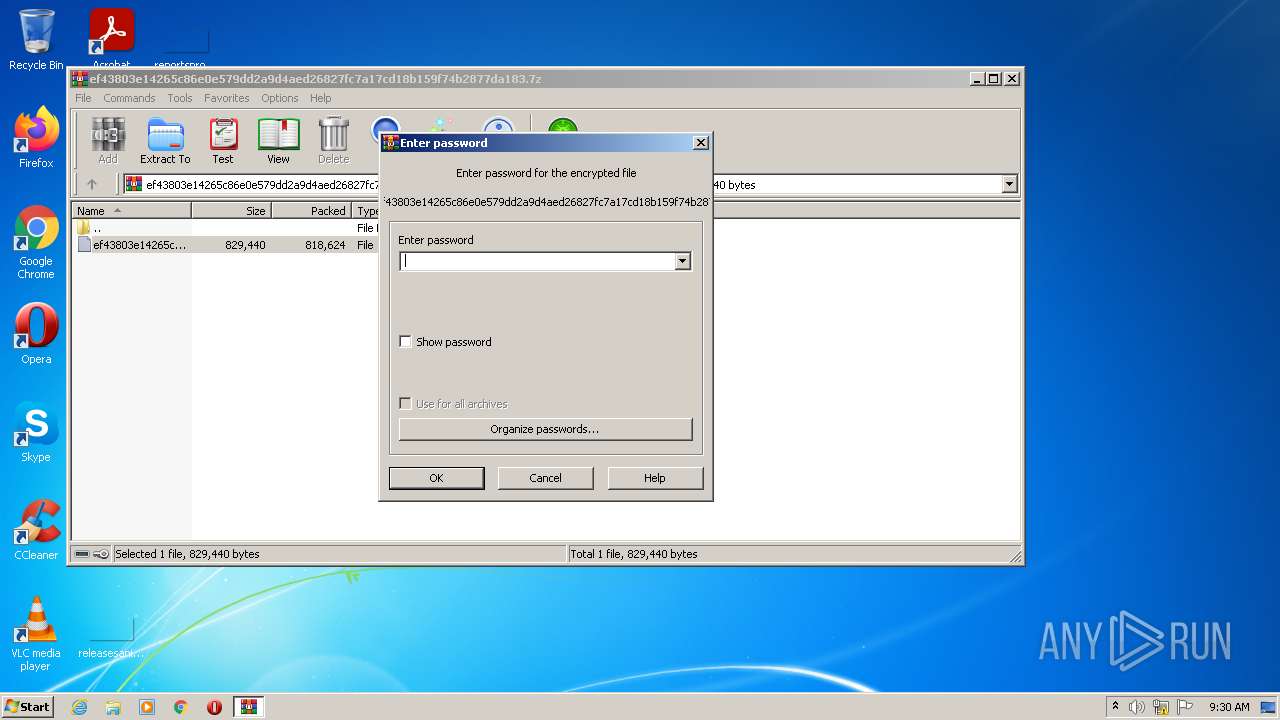
Drops executable file immediately after starts
- WinRAR.exe (PID: 2936)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2936)
- cmd.exe (PID: 2820)
Reads the computer name
- WinRAR.exe (PID: 2936)
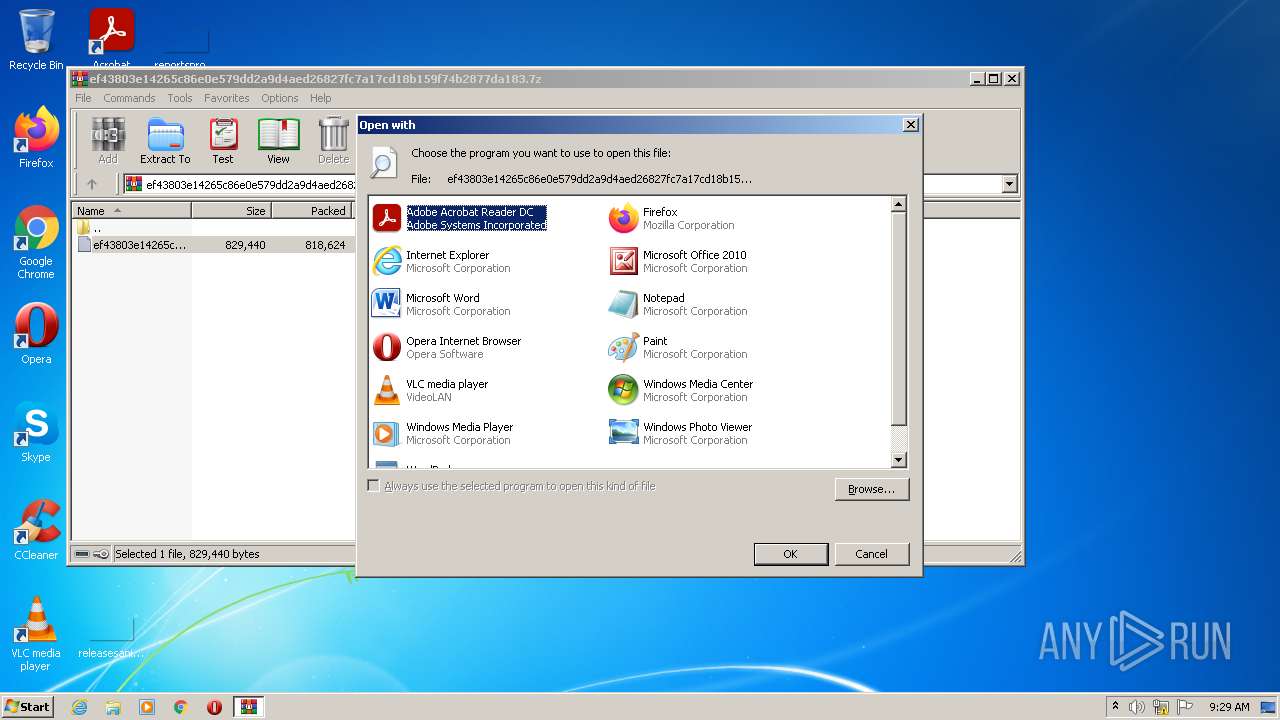
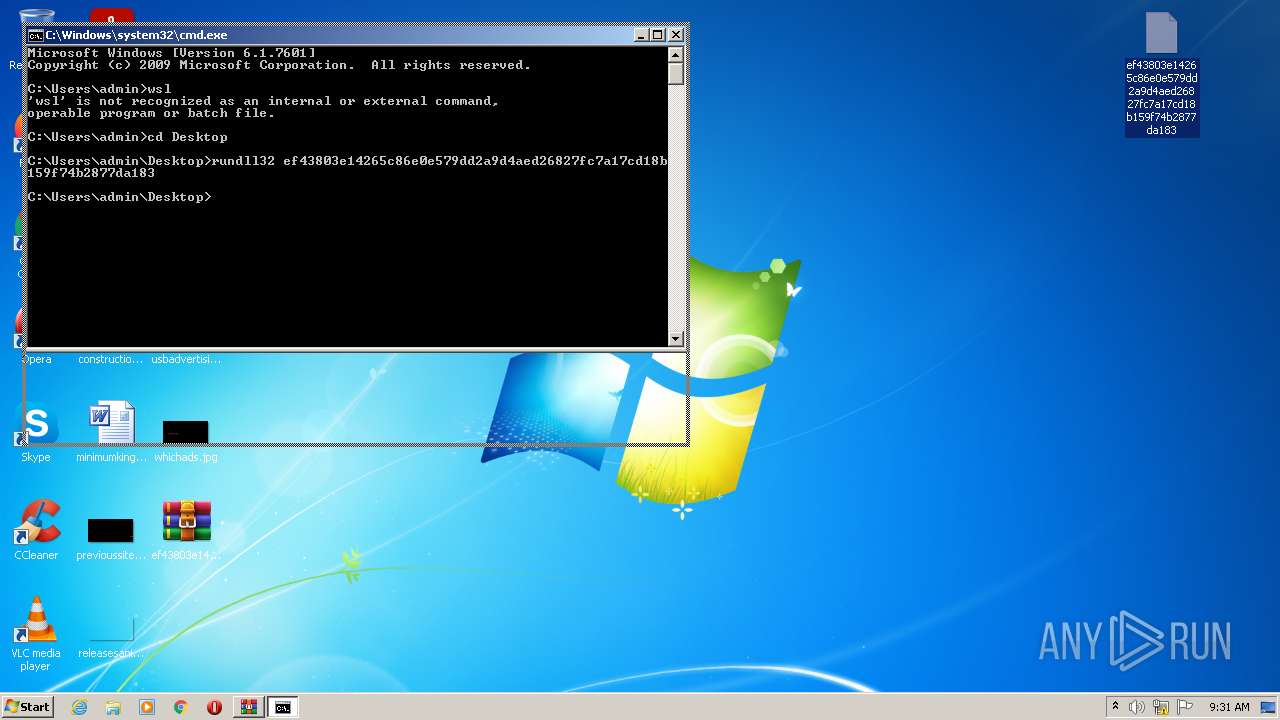
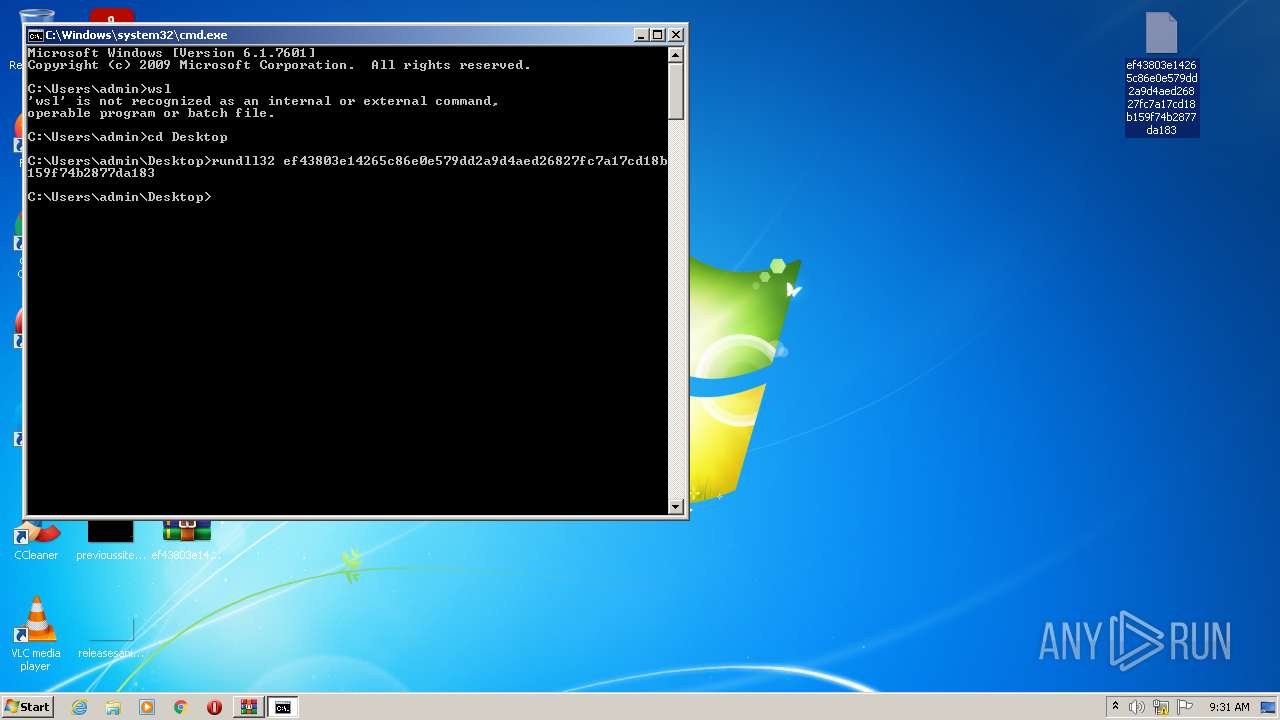
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2936)
- cmd.exe (PID: 2820)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2936)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2936)
INFO
Checks supported languages
- rundll32.exe (PID: 1776)
- rundll32.exe (PID: 2976)
Reads the computer name
- rundll32.exe (PID: 1776)
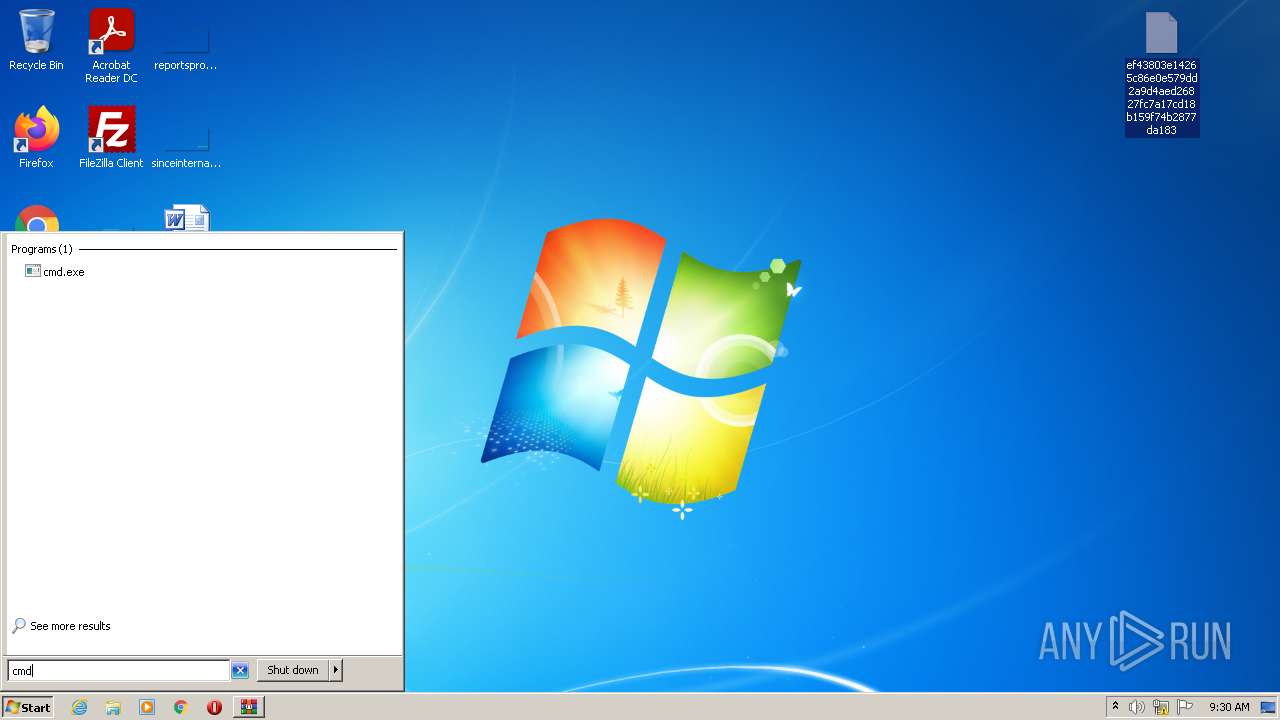
Manual execution by user
- cmd.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
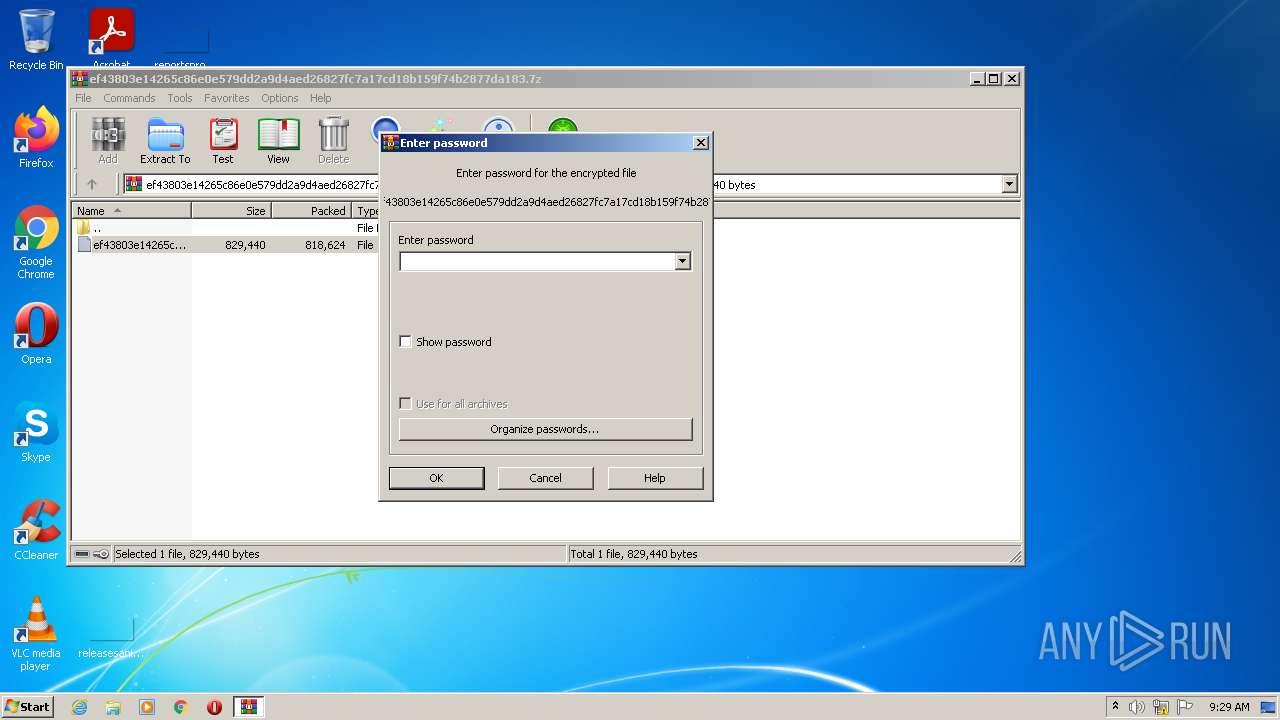
| 1776 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb2936.24396\ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
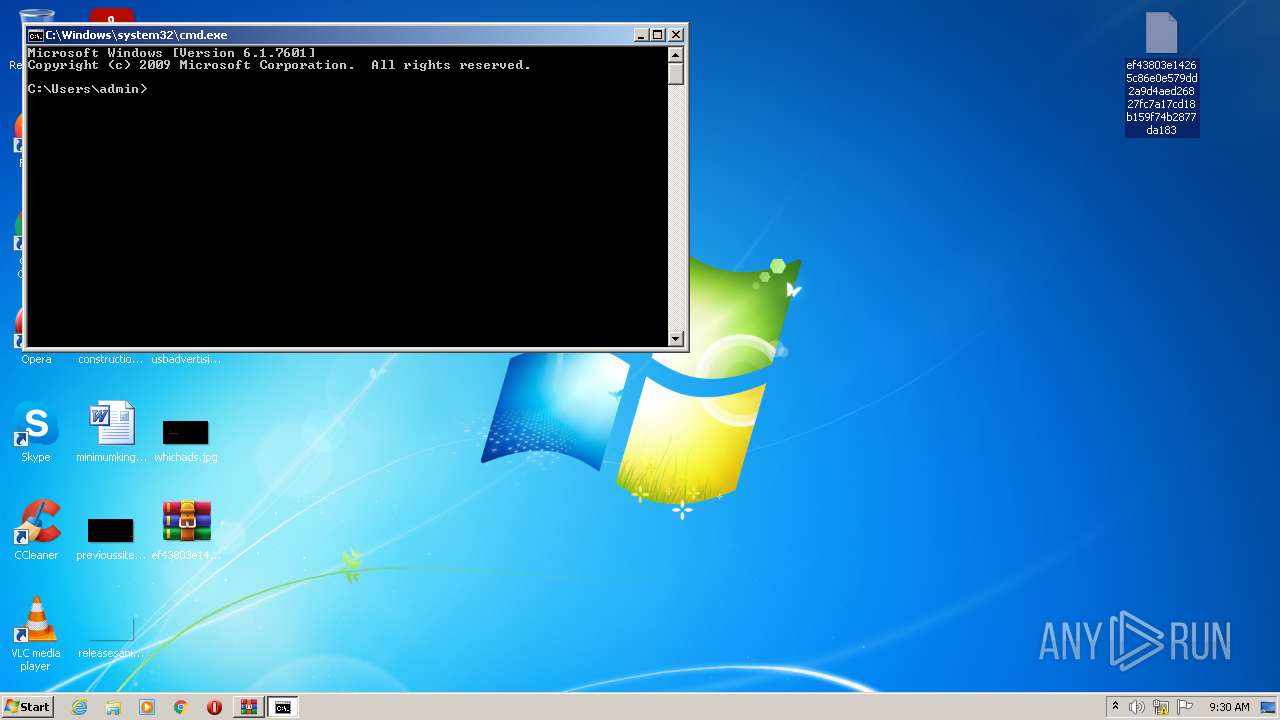
| 2820 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183.7z" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2976 | rundll32 ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 250
Read events
1 217
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183.7z | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2936.24396\ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183 | executable | |
MD5:— | SHA256:— | |||
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2936.27288\ef43803e14265c86e0e579dd2a9d4aed26827fc7a17cd18b159f74b2877da183 | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report