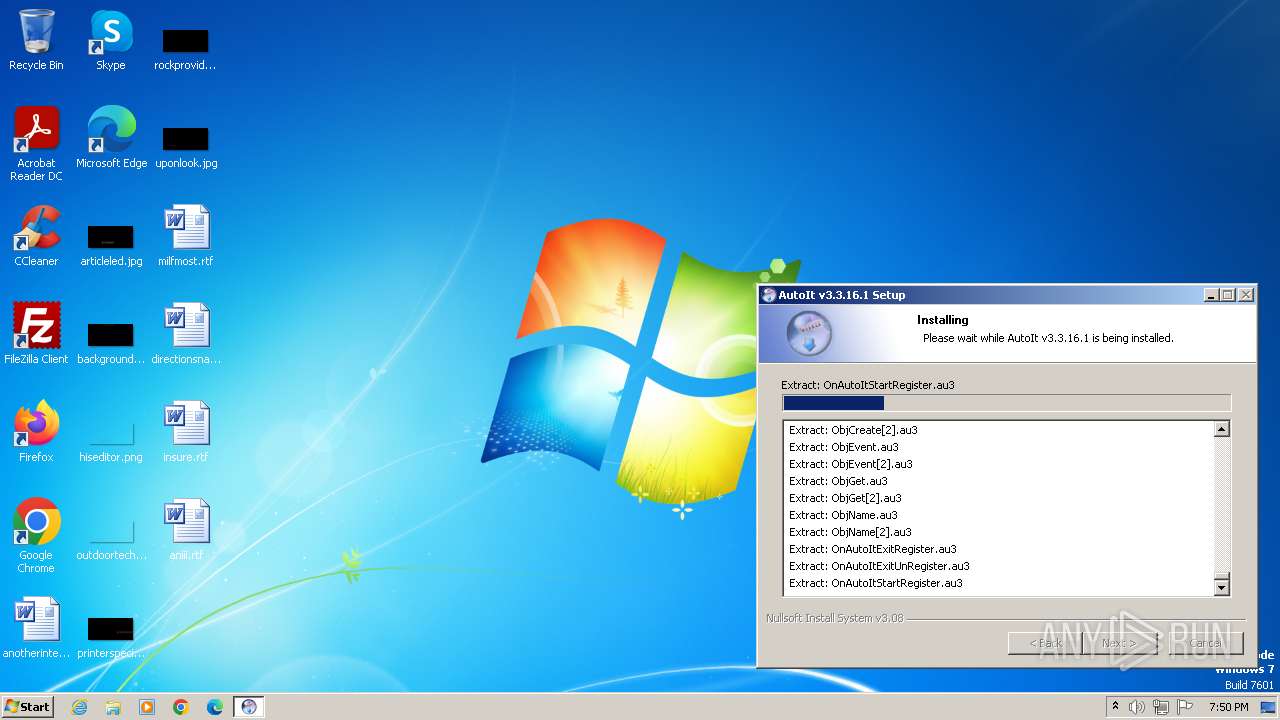
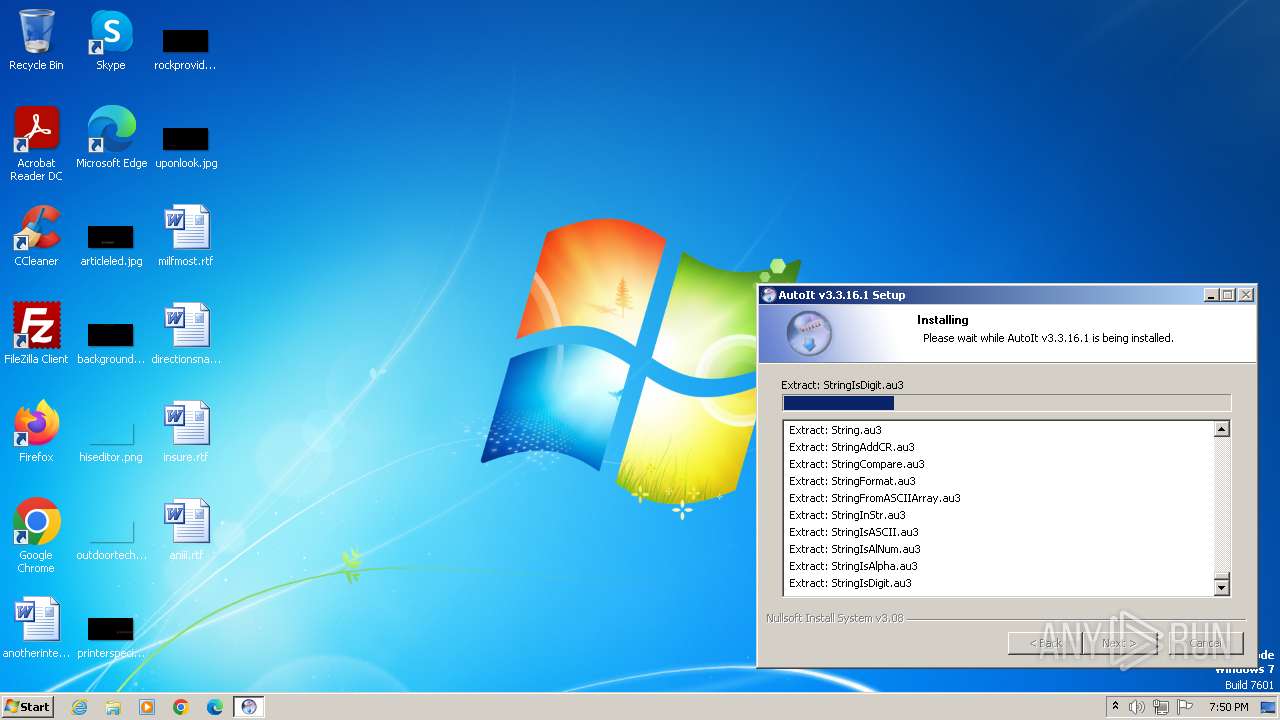
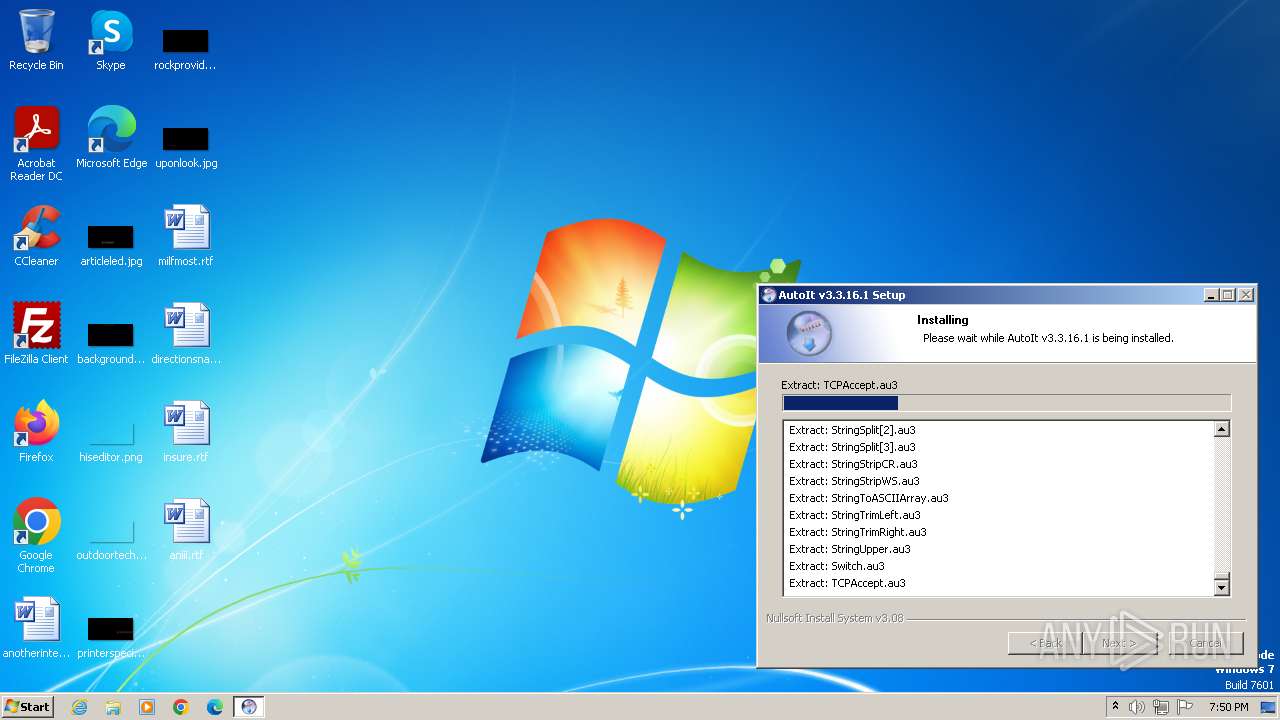
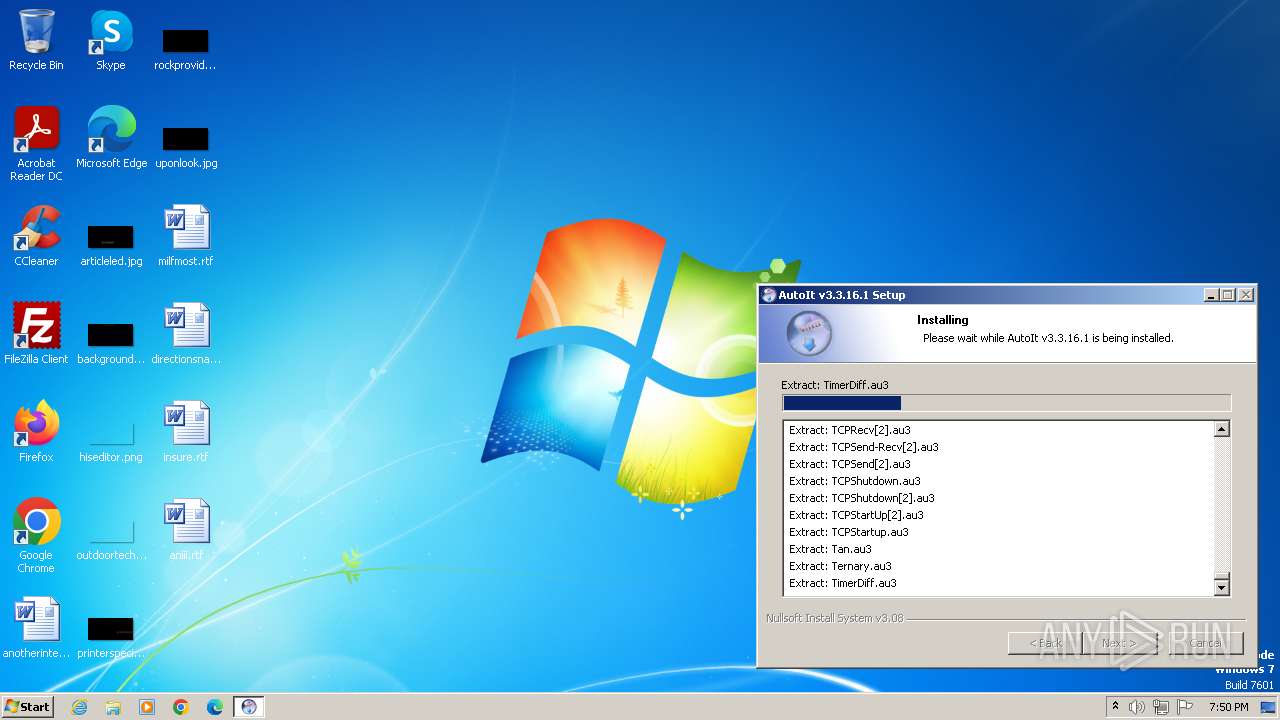
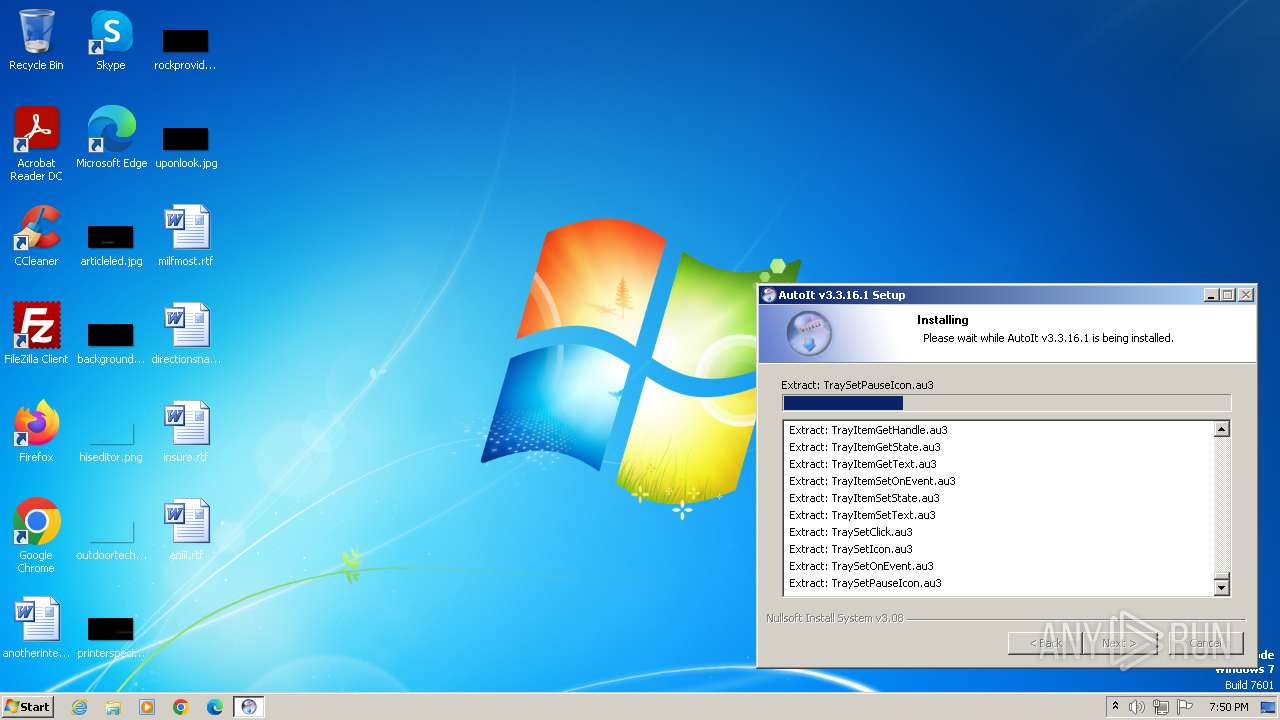
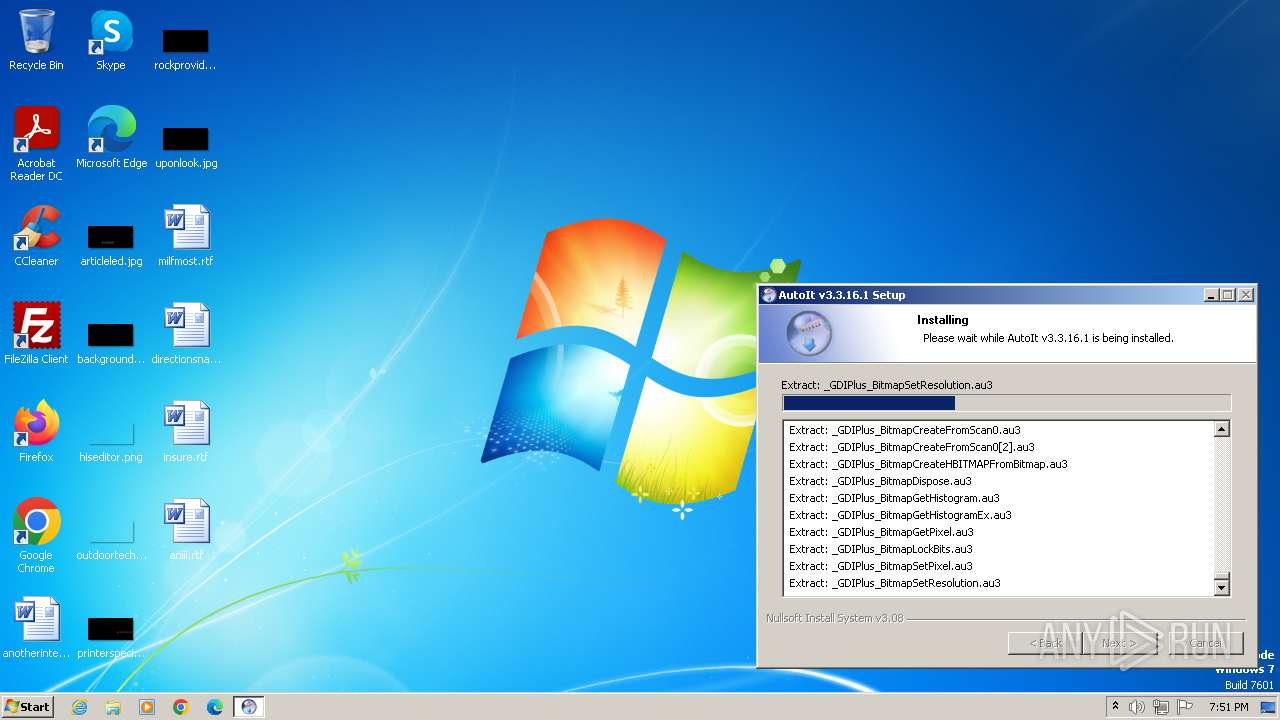
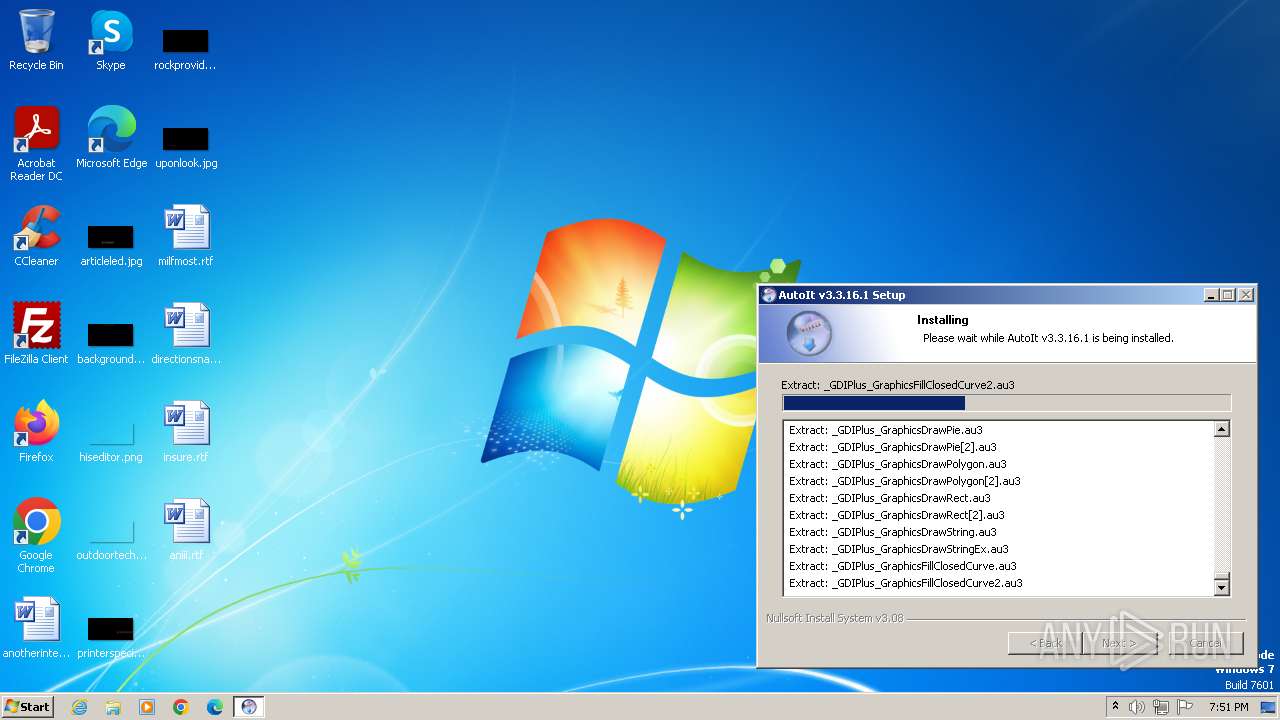
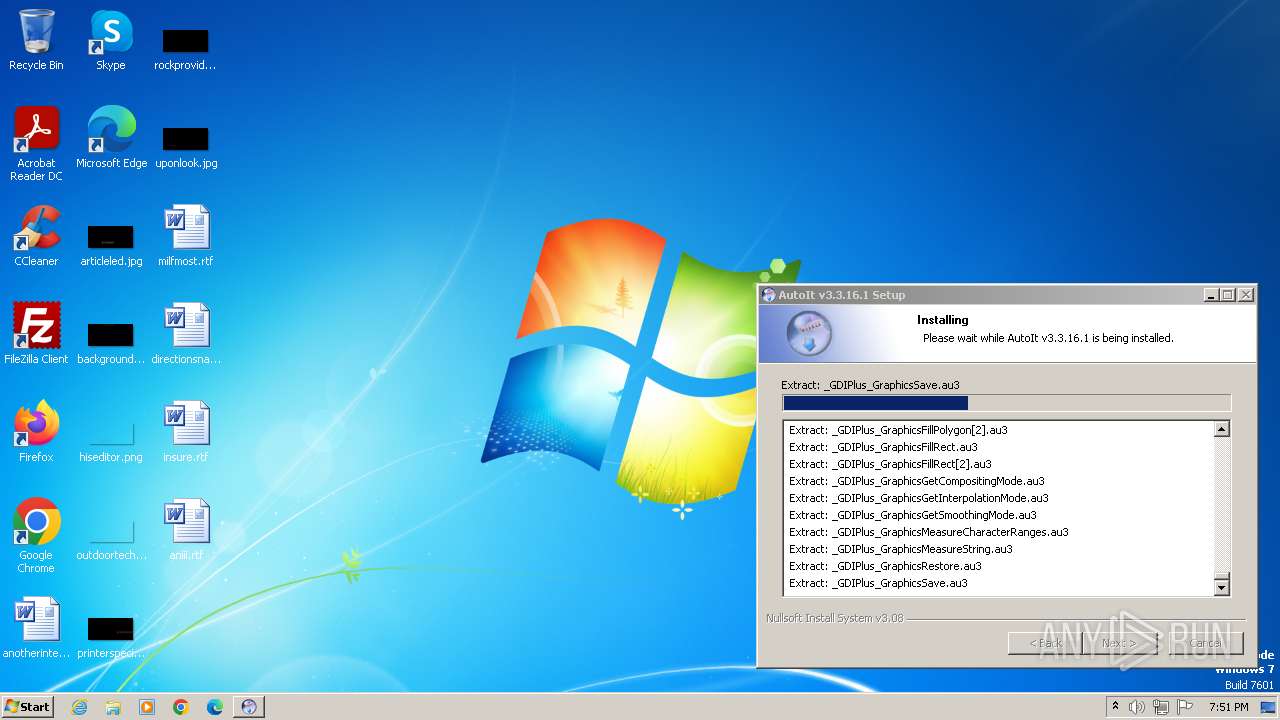
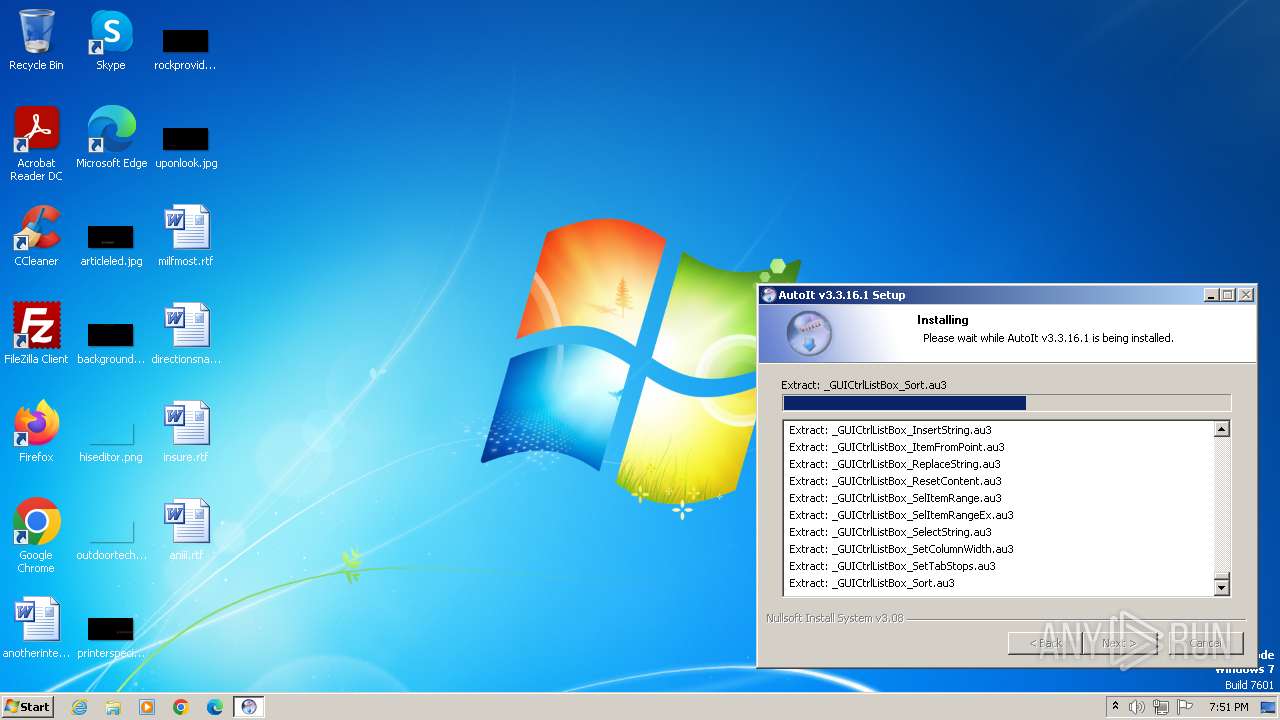
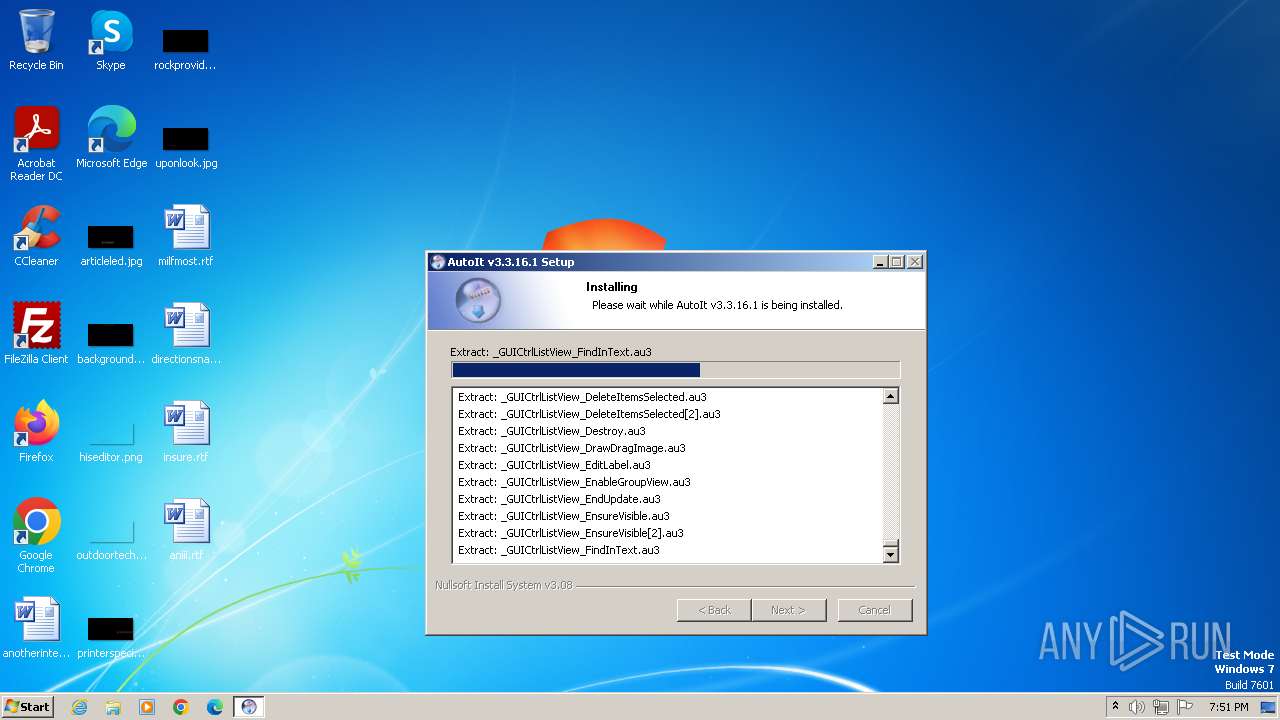
| File name: | autoit-v3-setup.exe |
| Full analysis: | https://app.any.run/tasks/e31e6139-ee1d-41b3-984b-dfc99780b410 |
| Verdict: | Malicious activity |
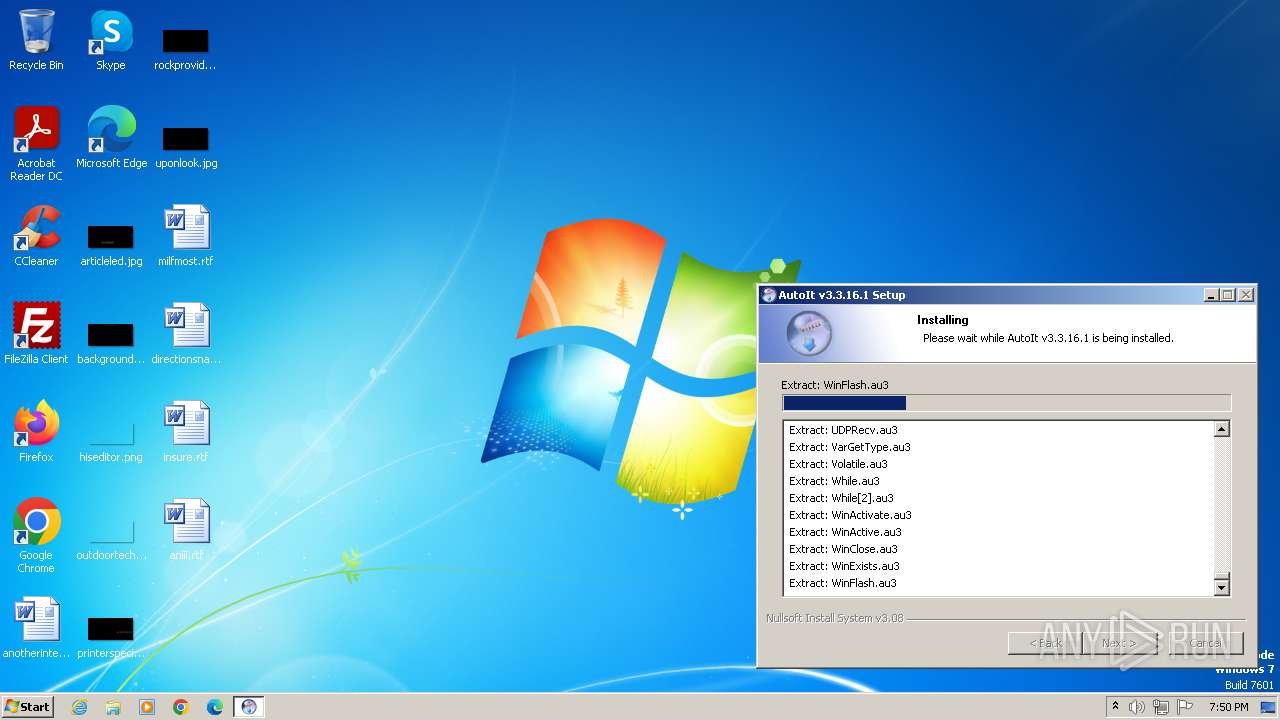
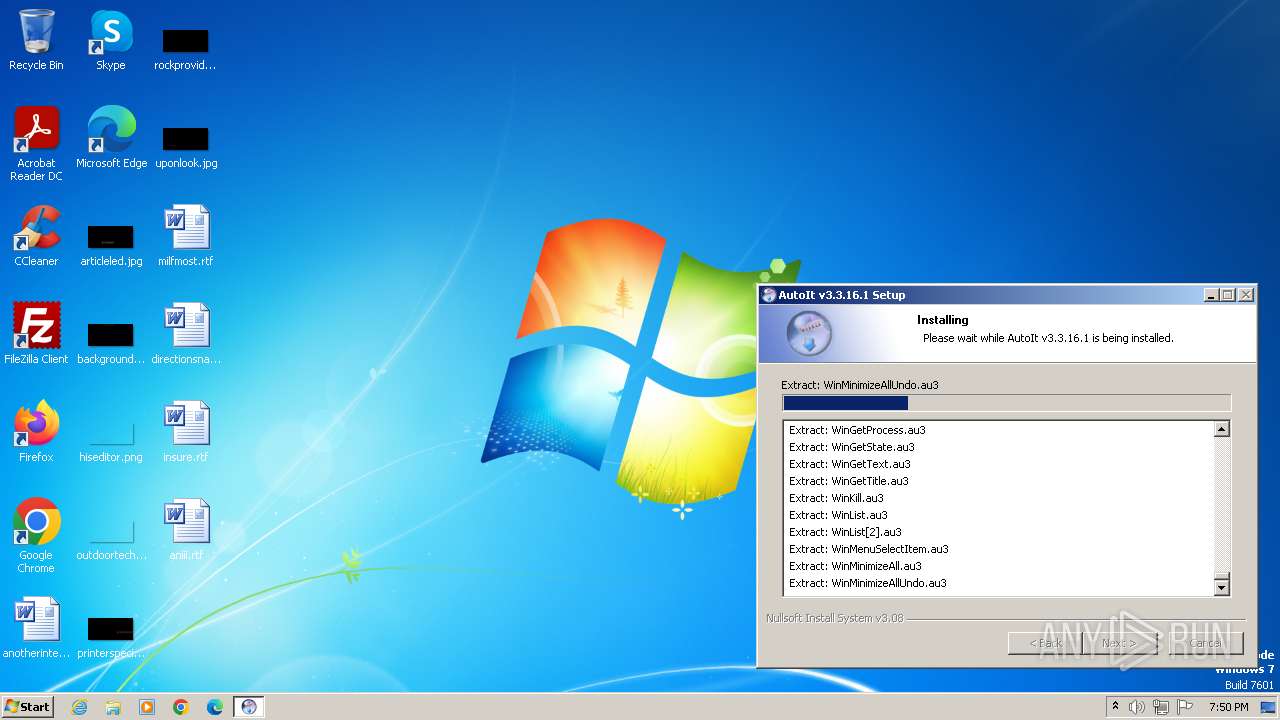
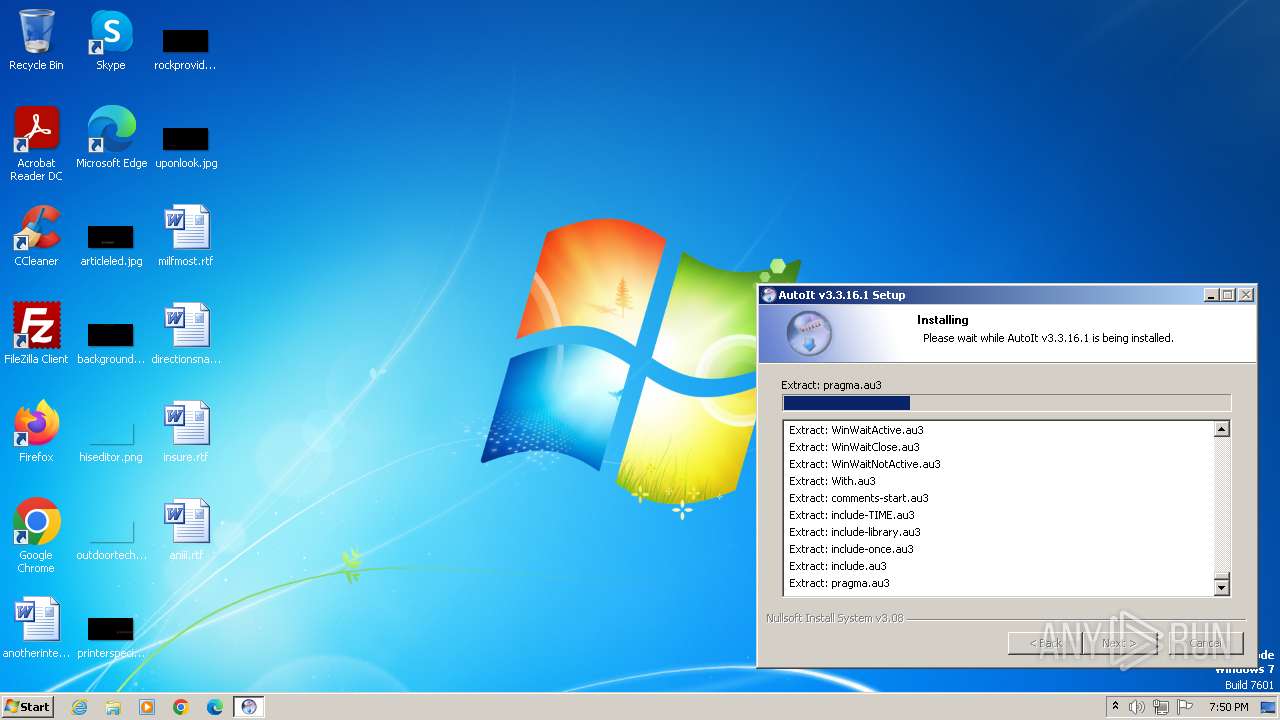
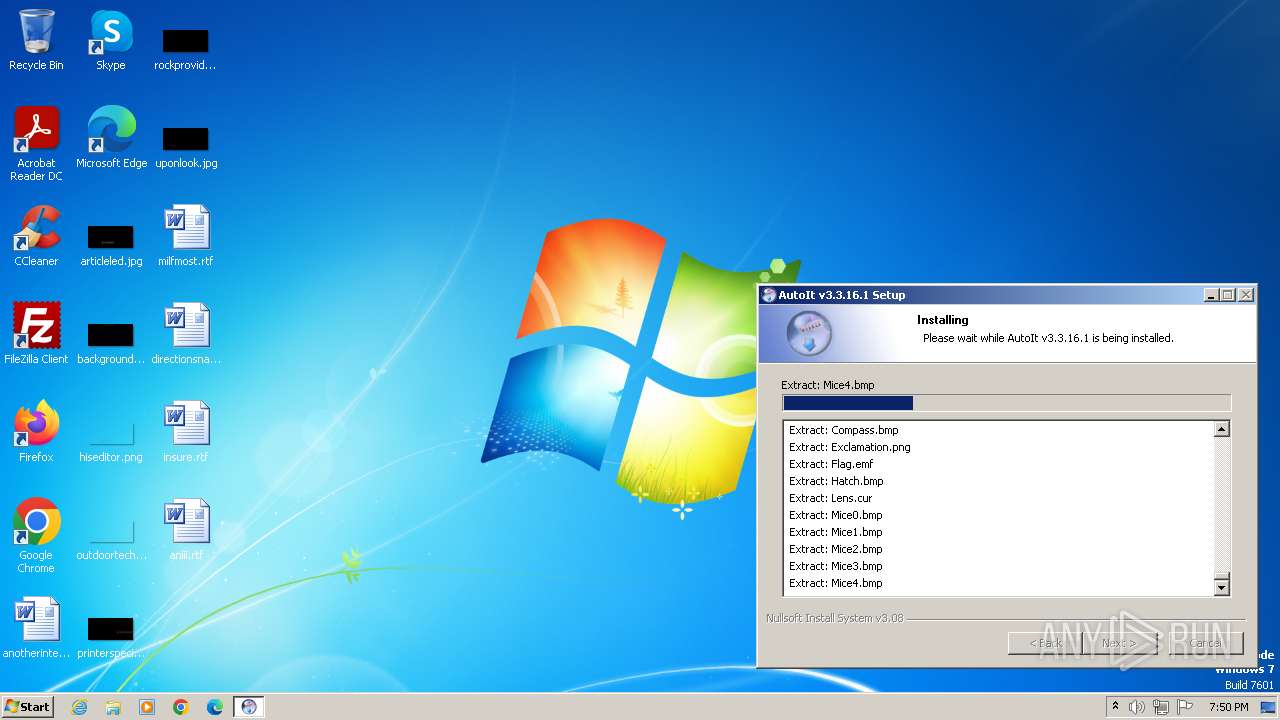
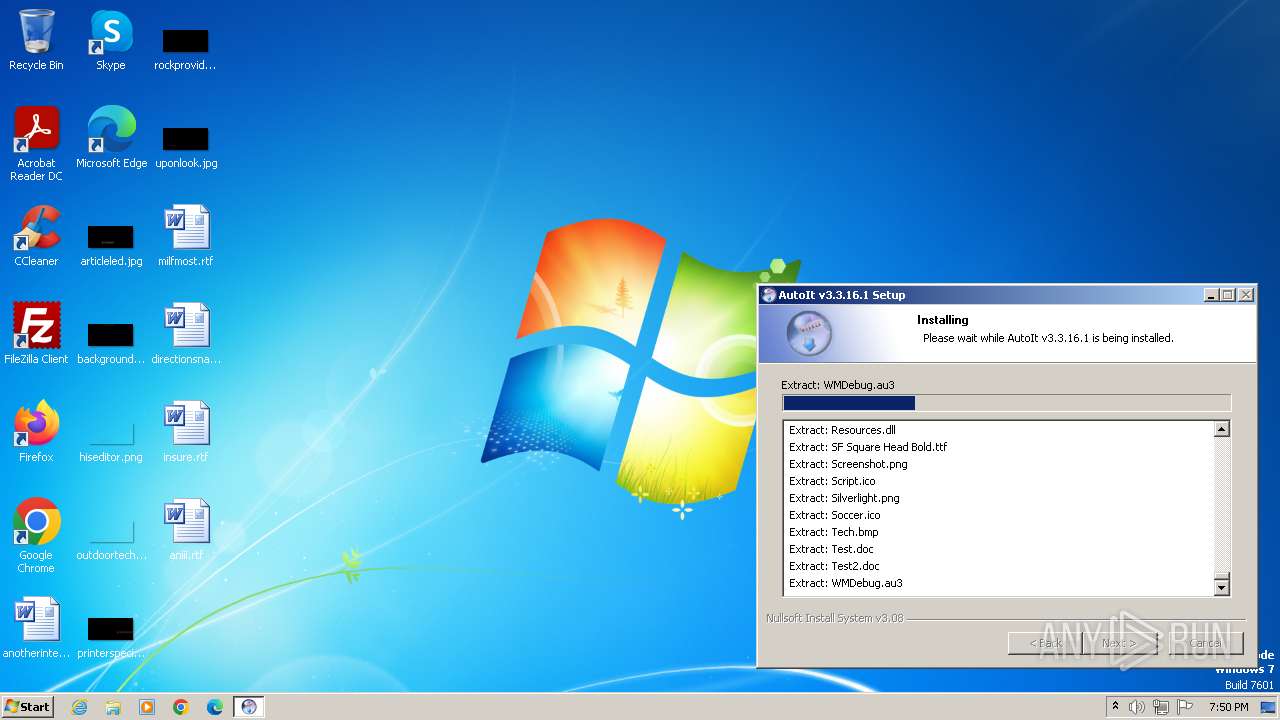
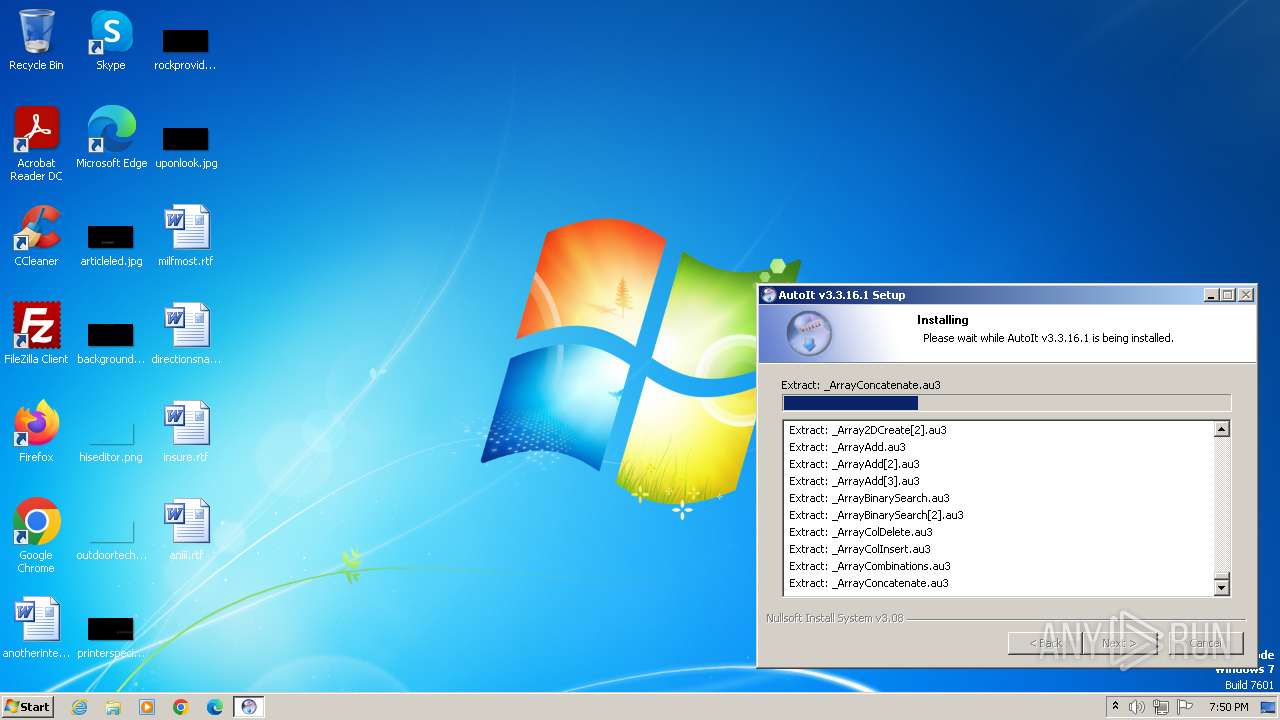
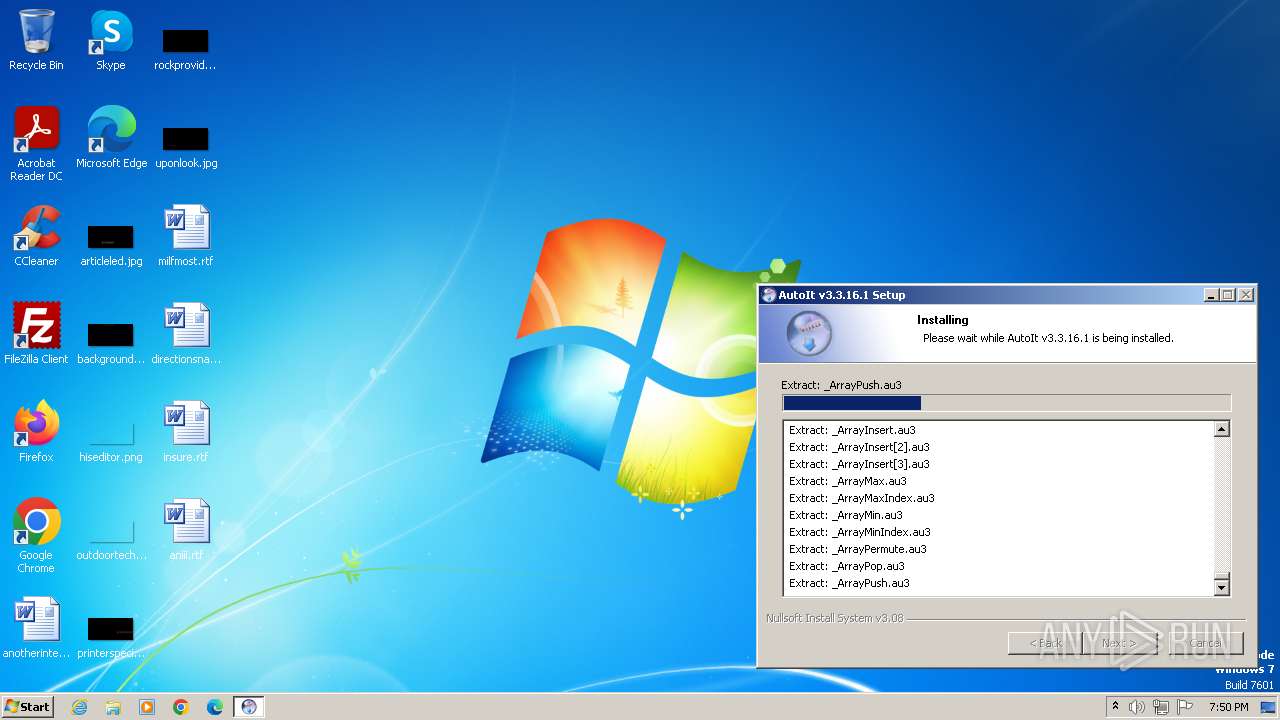
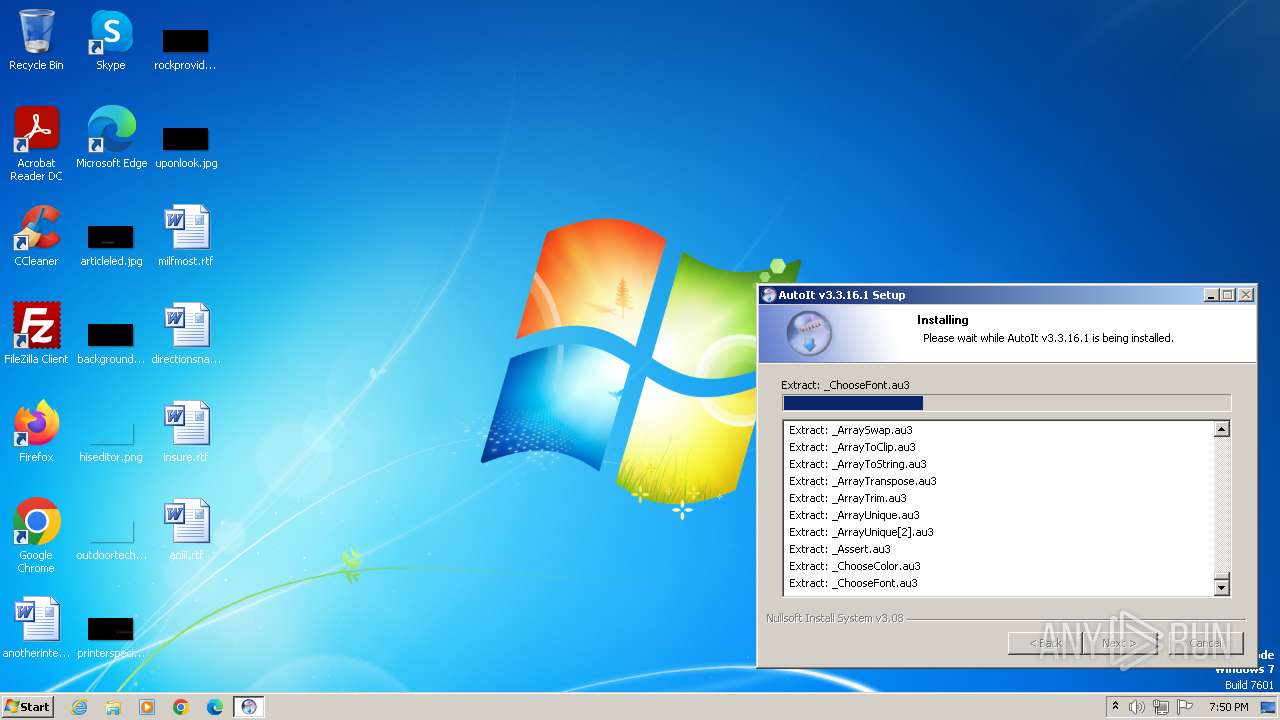
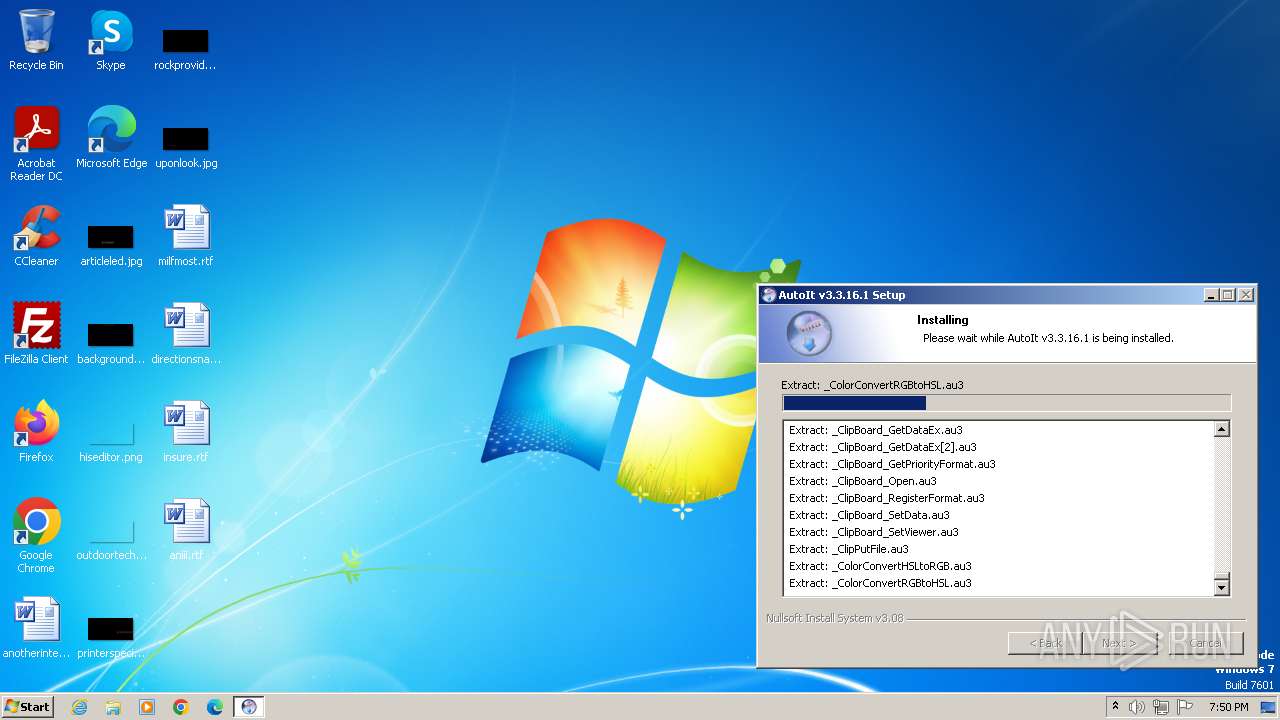
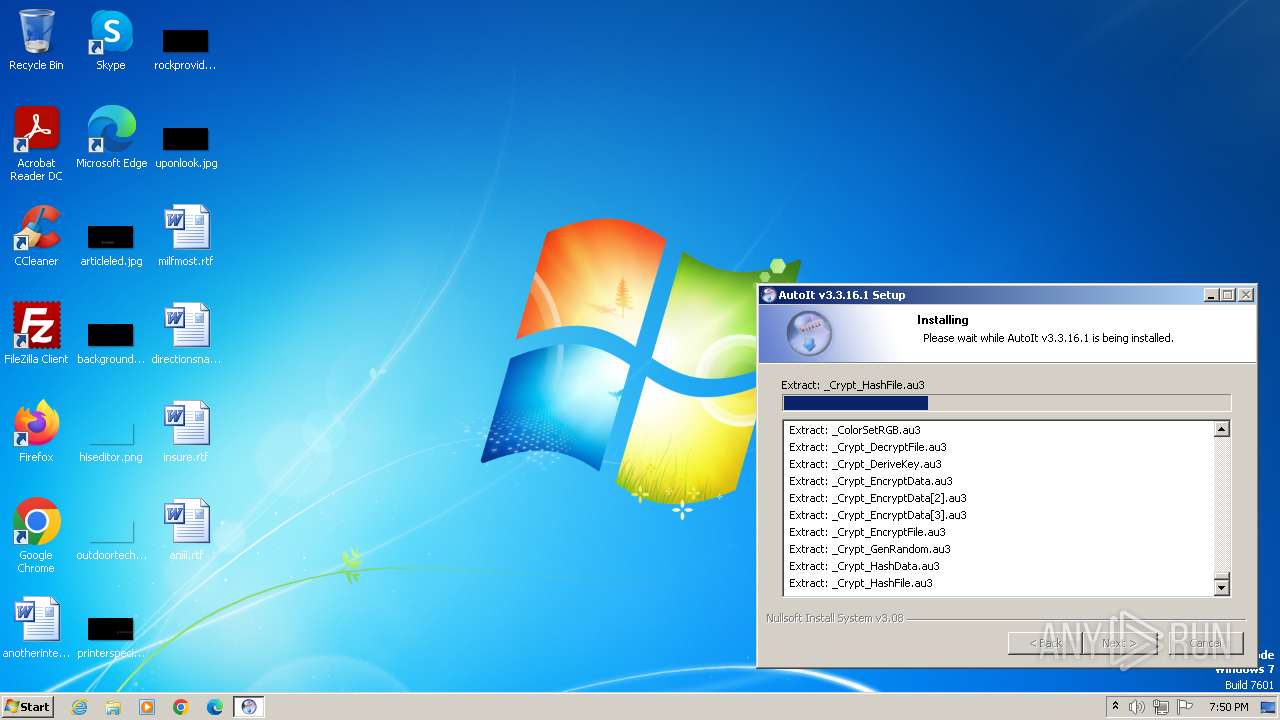
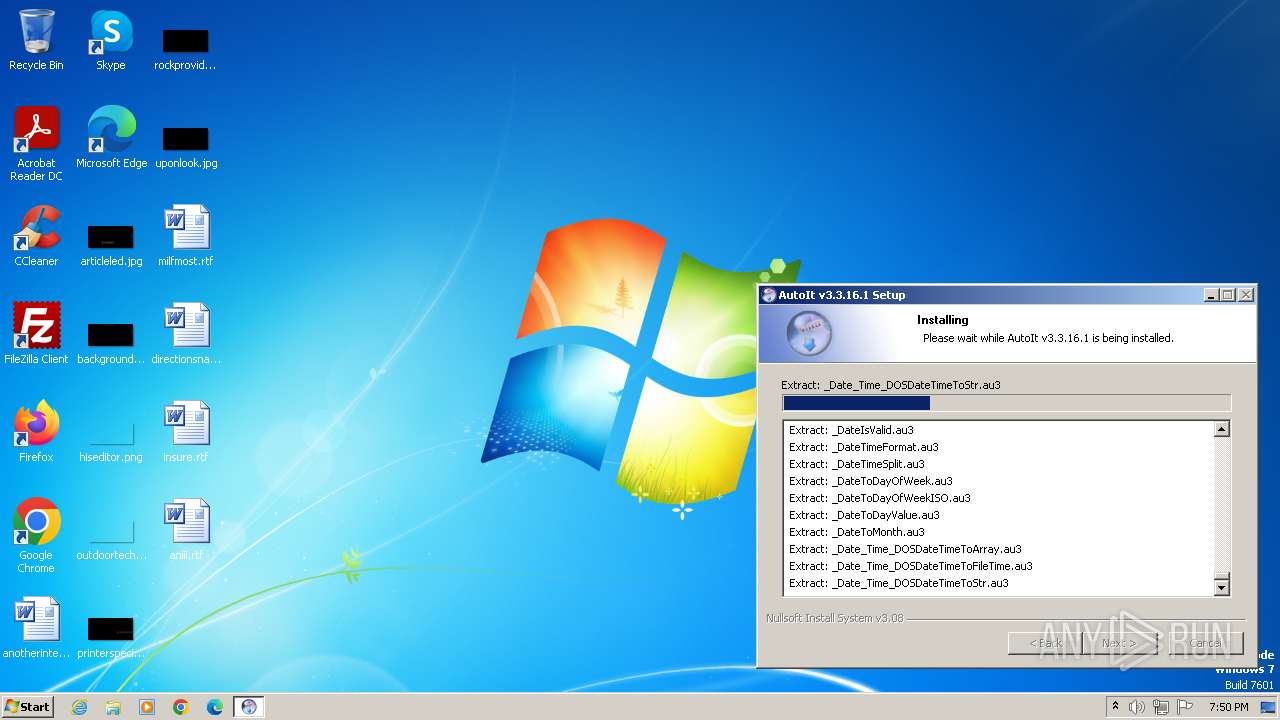
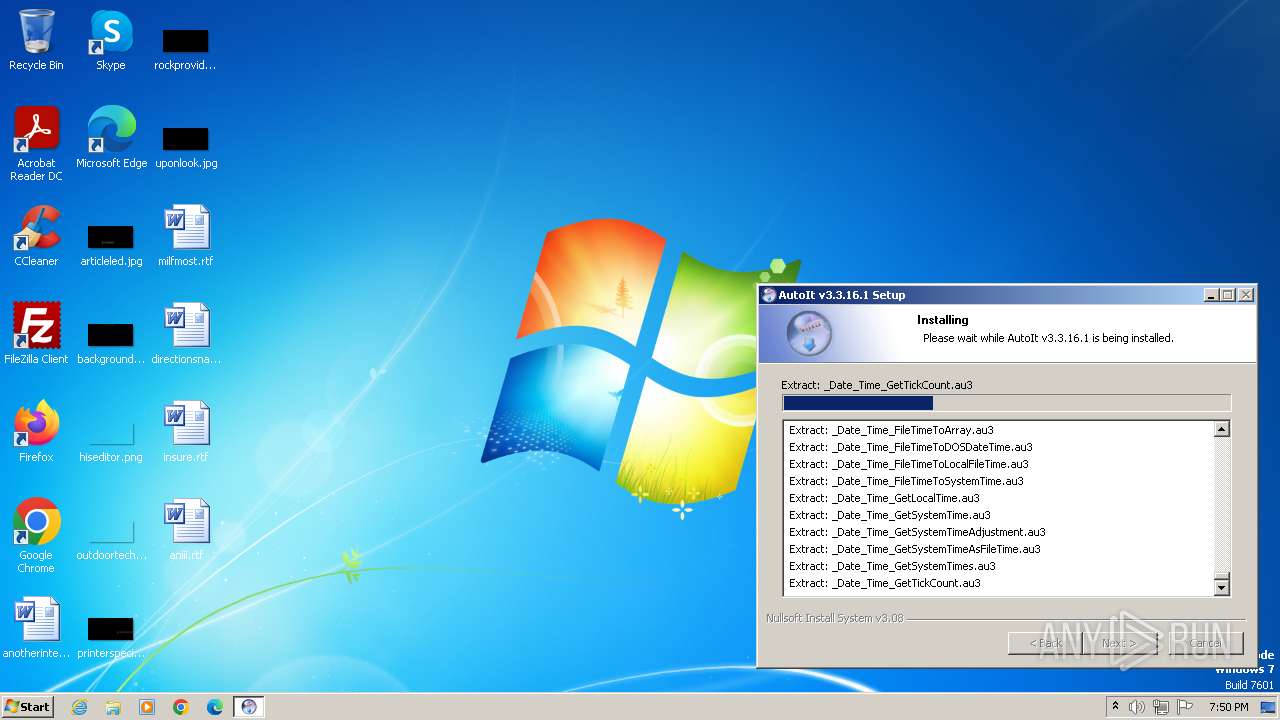
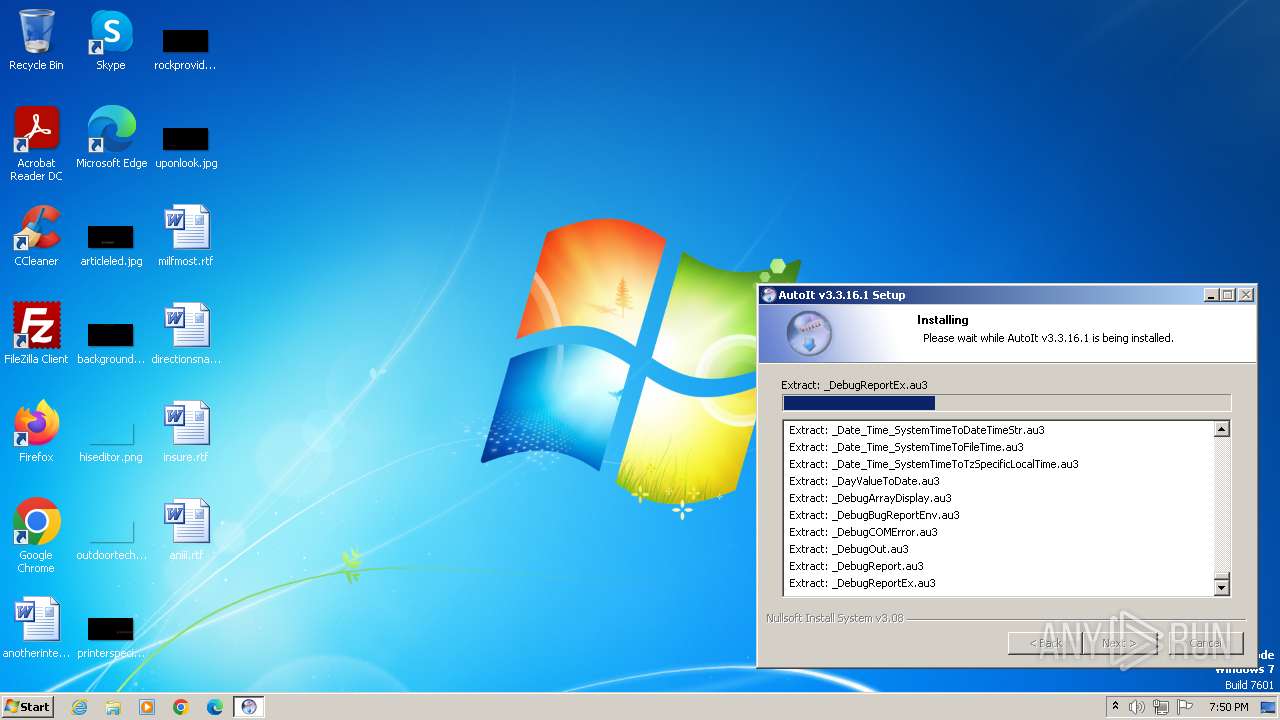
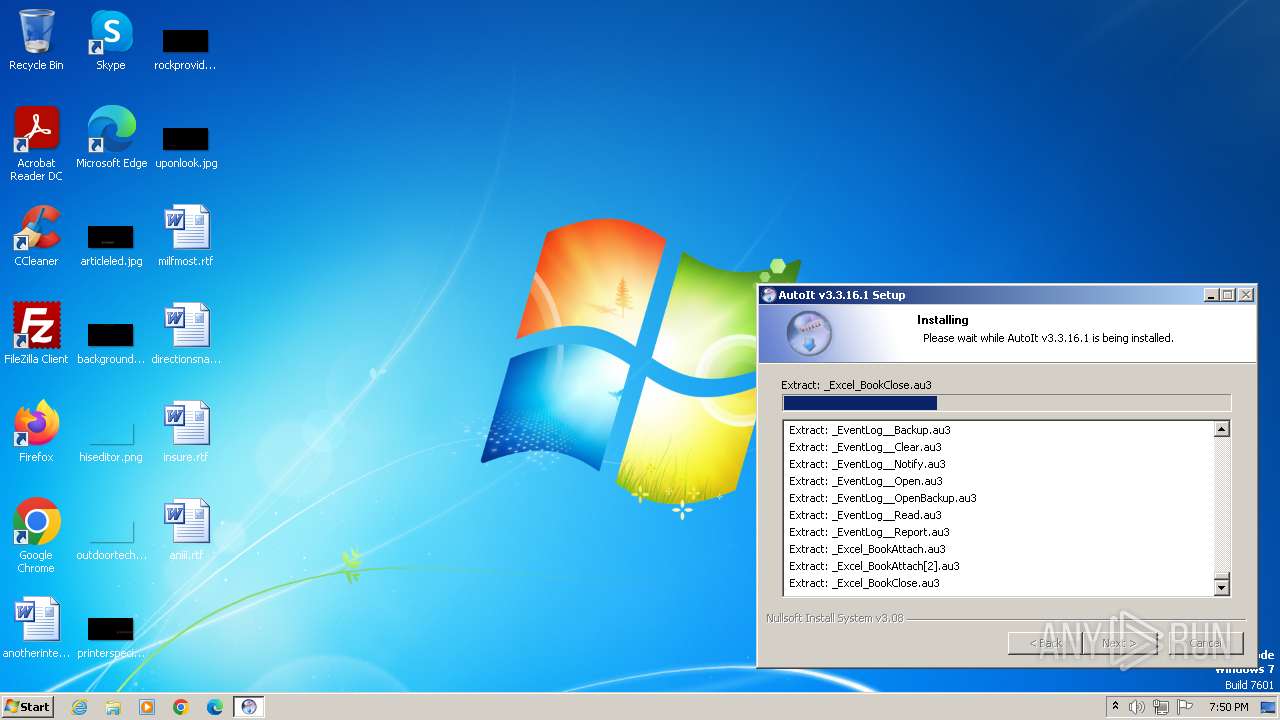
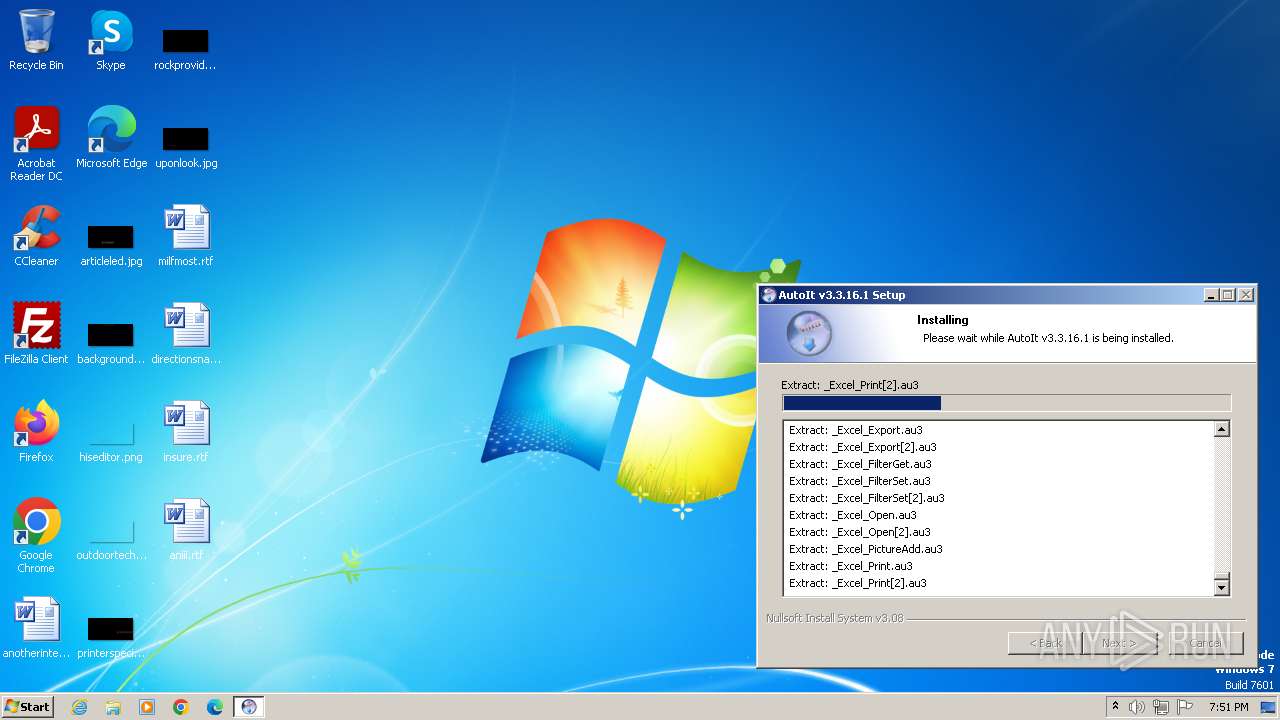
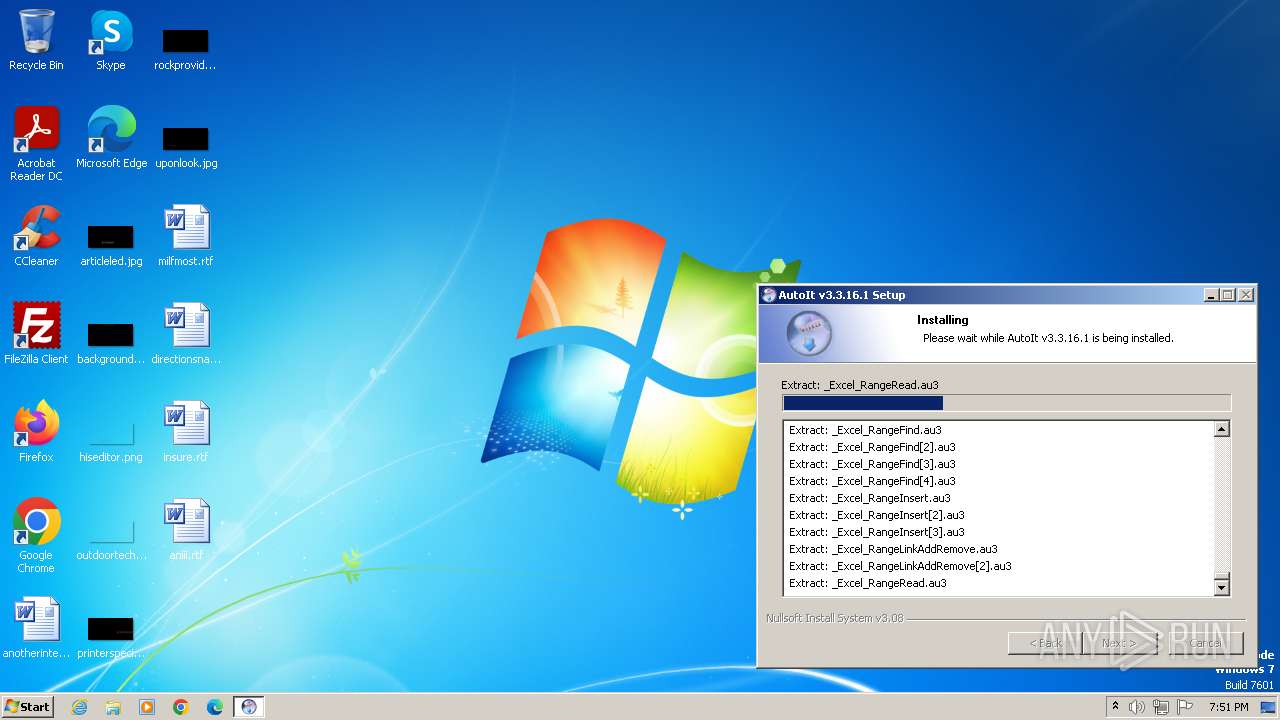
| Analysis date: | November 15, 2023, 19:50:03 |
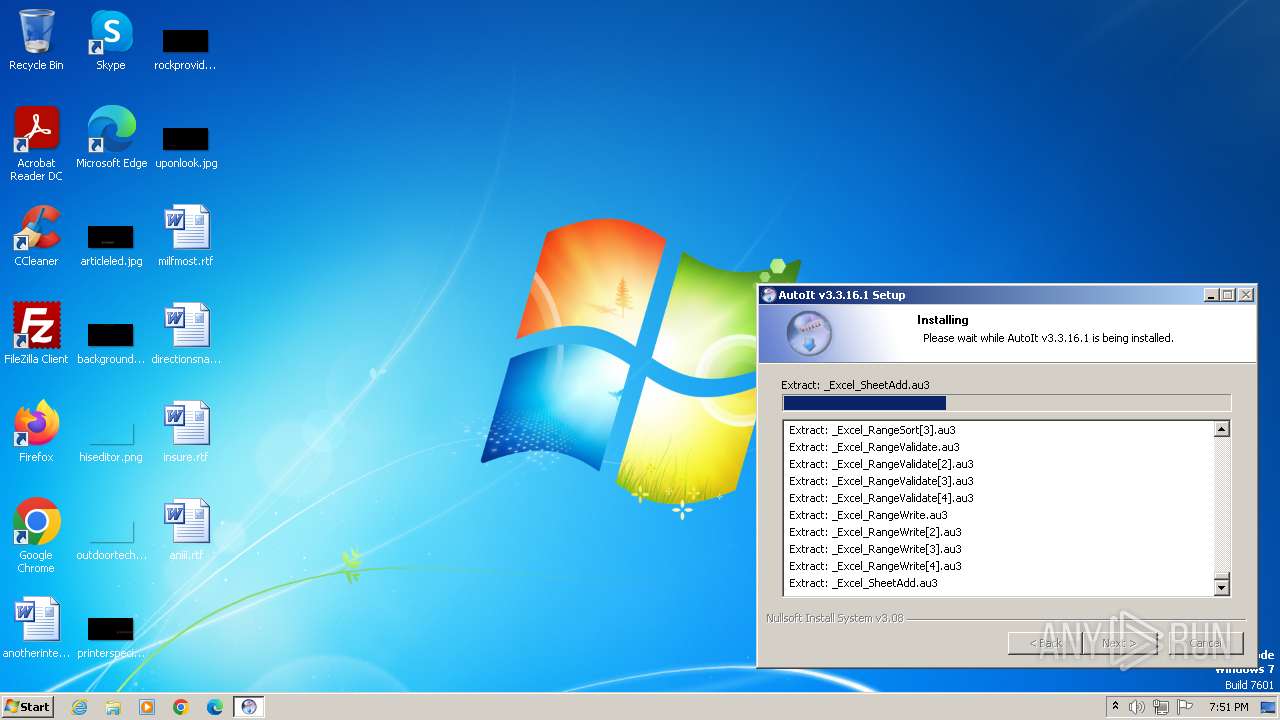
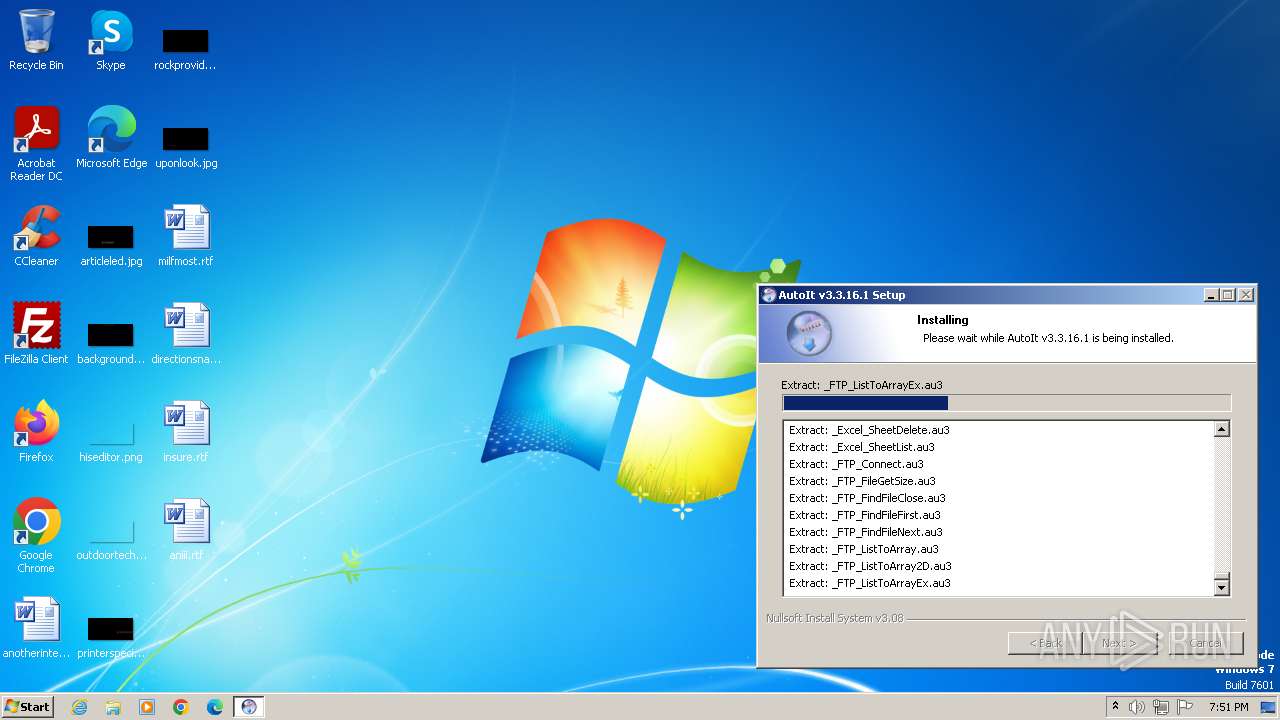
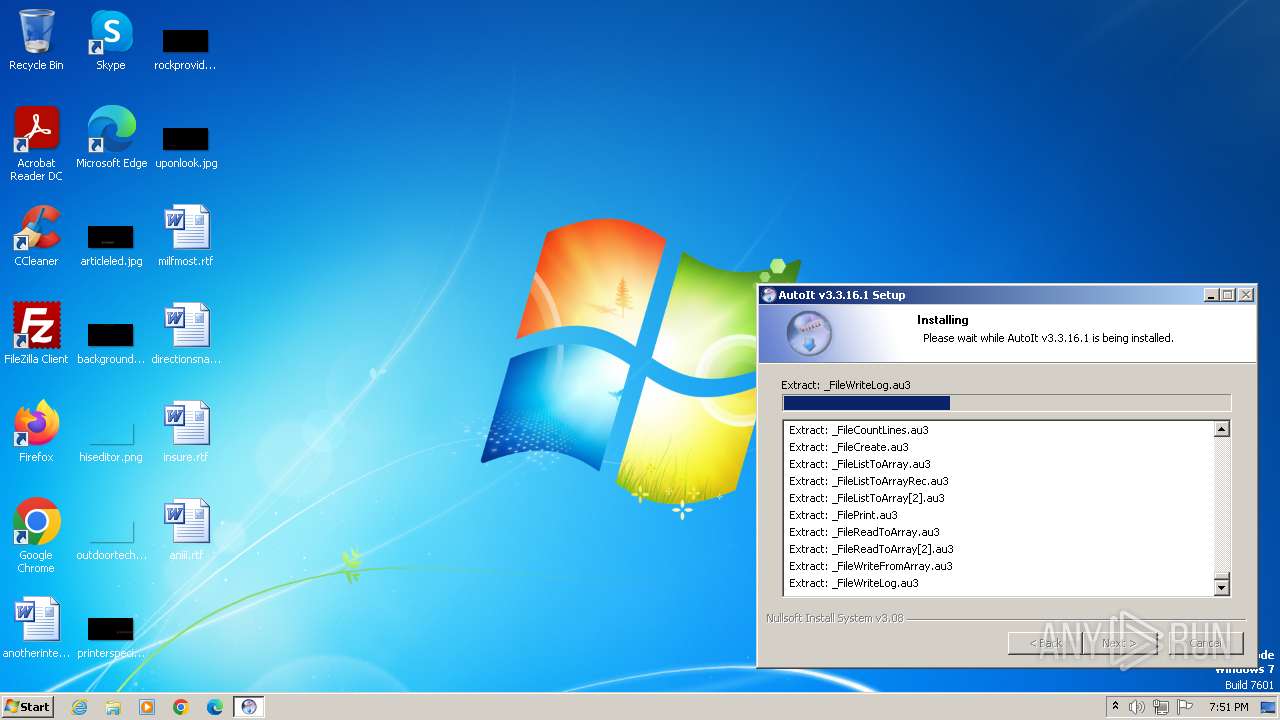
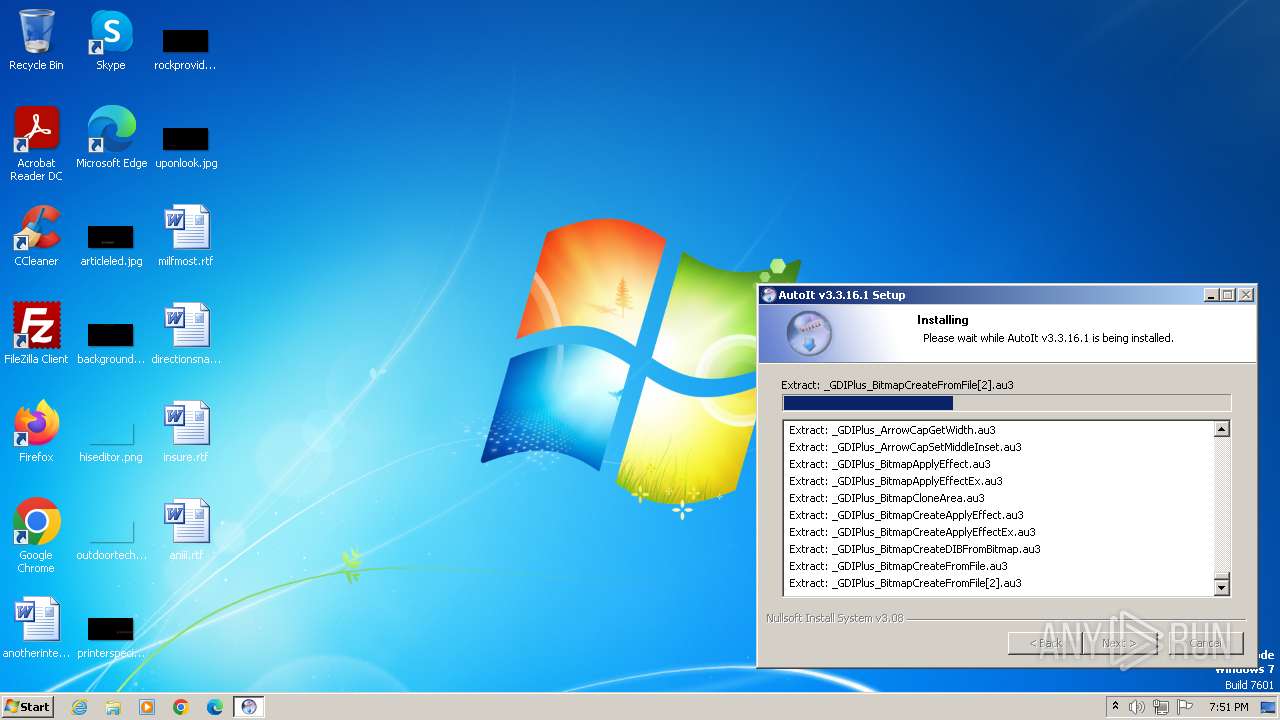
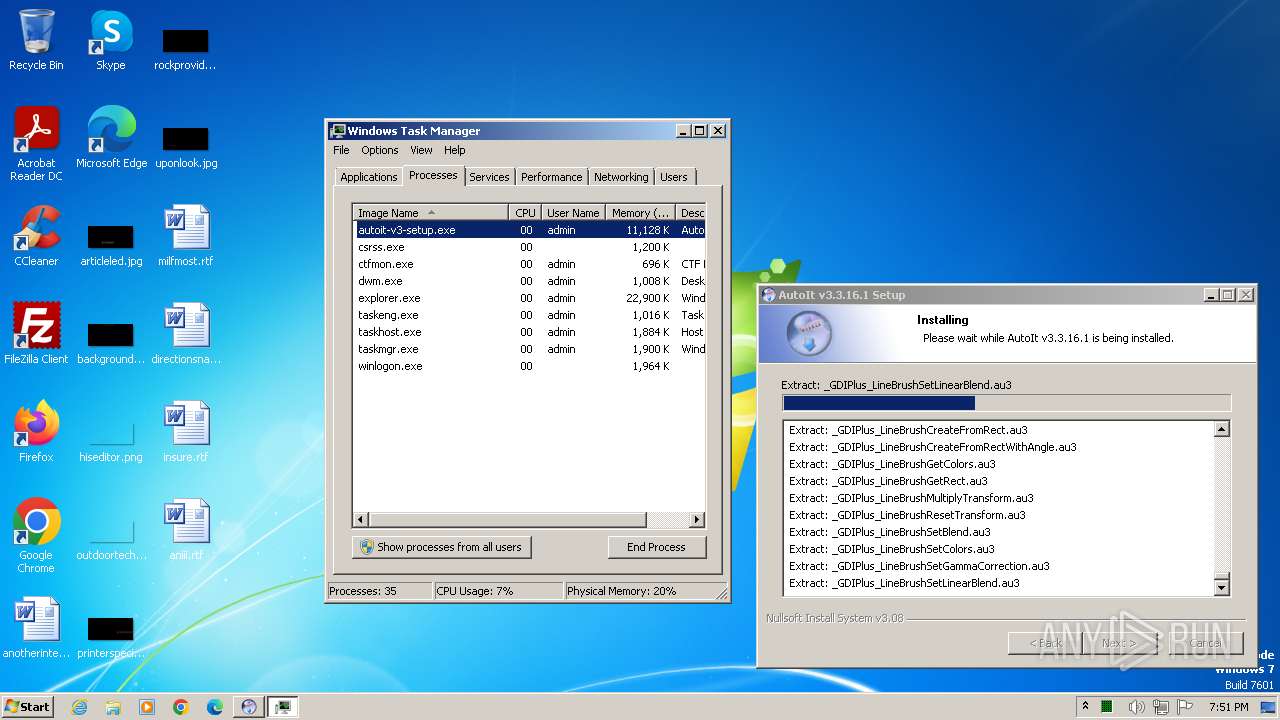
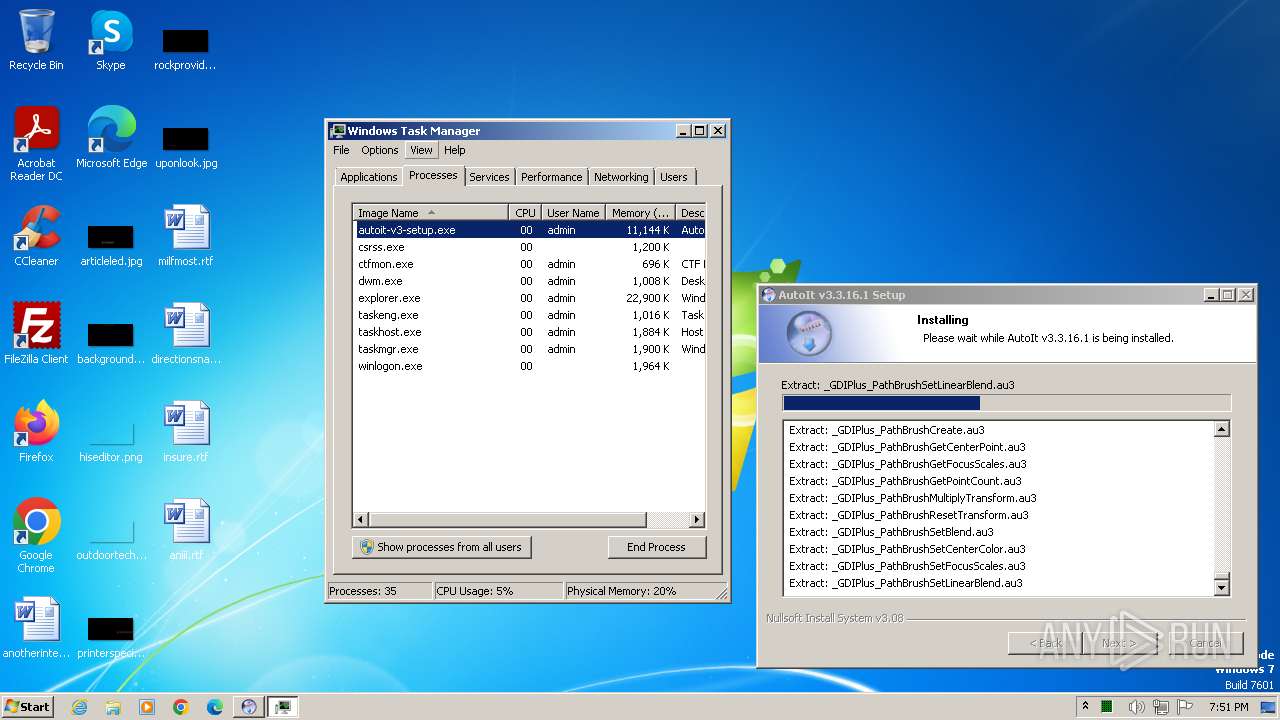
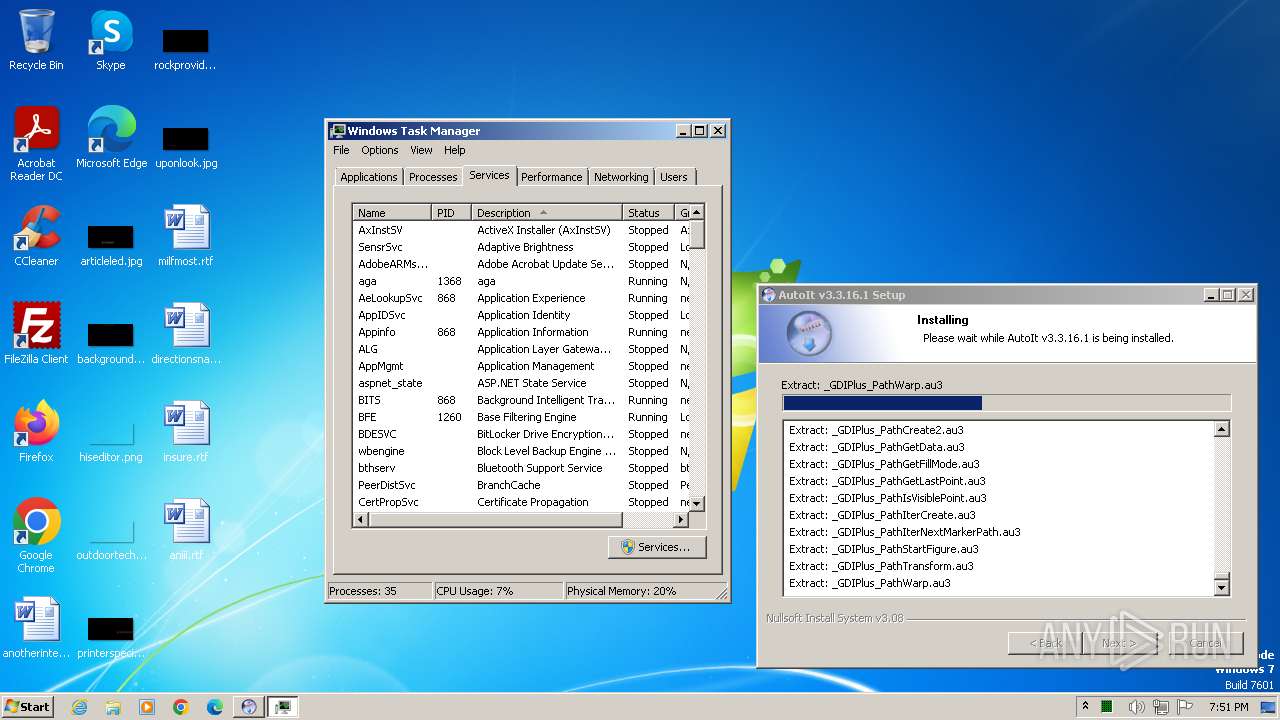
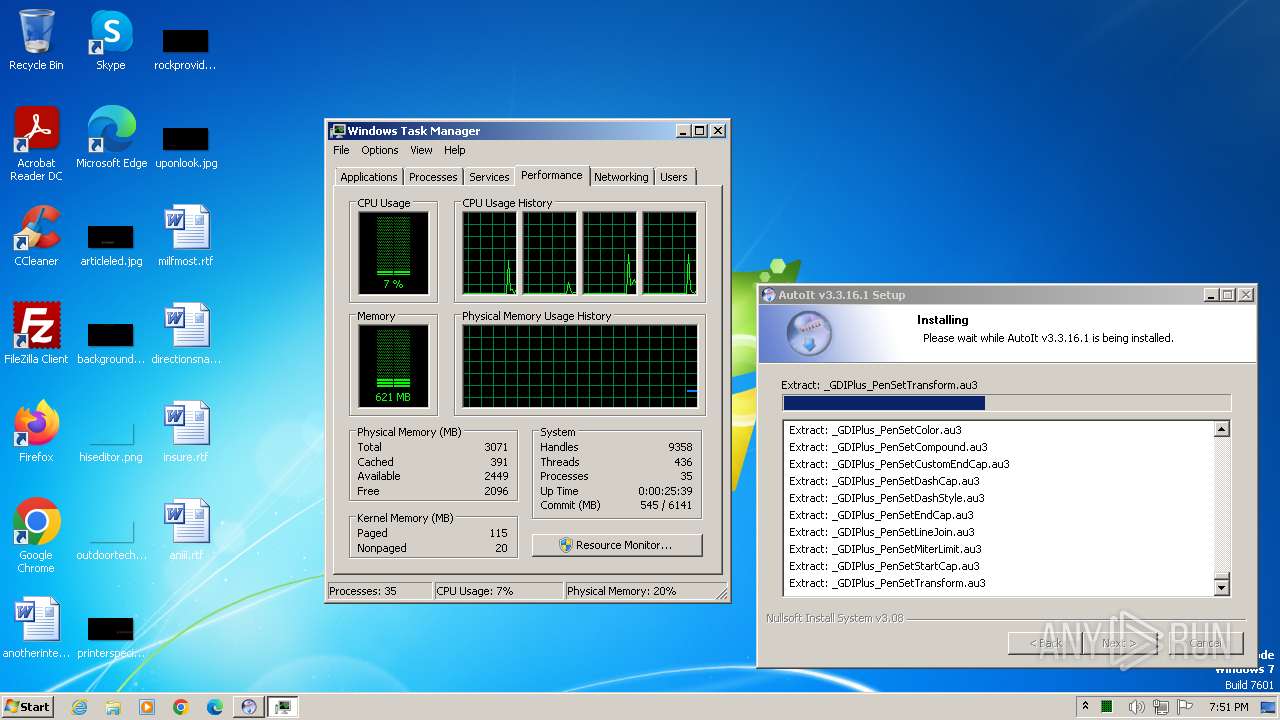
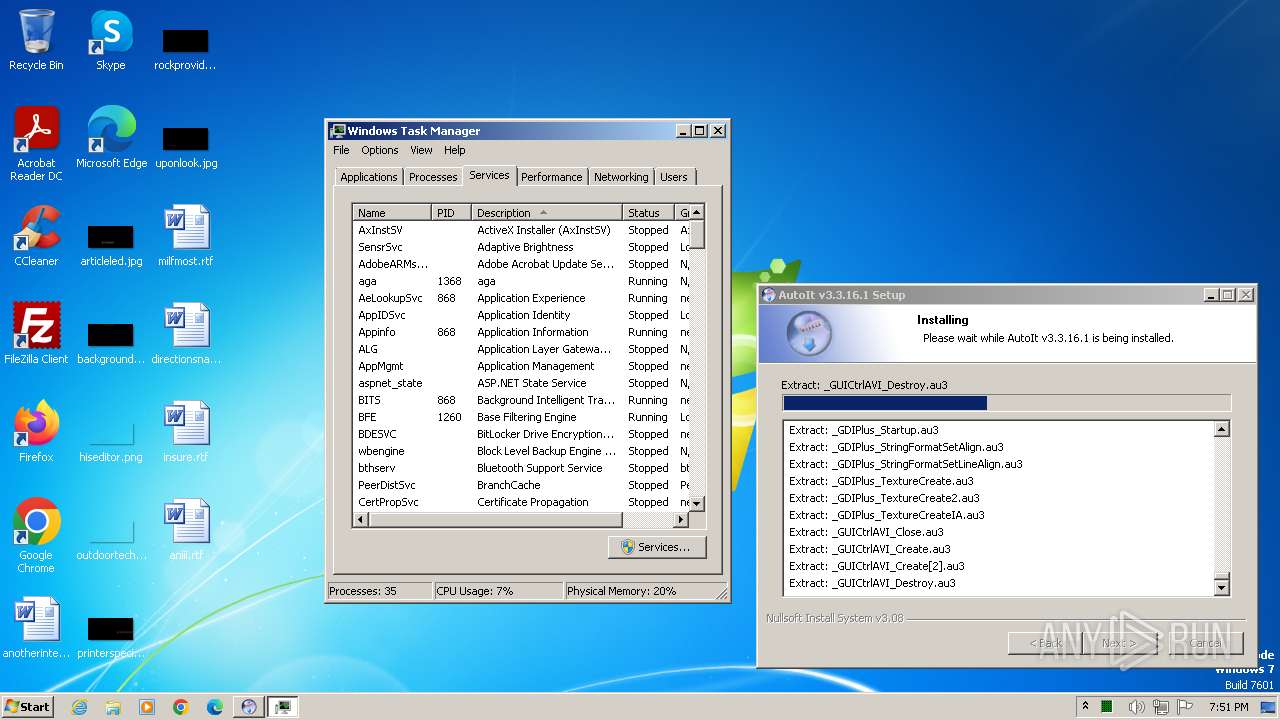
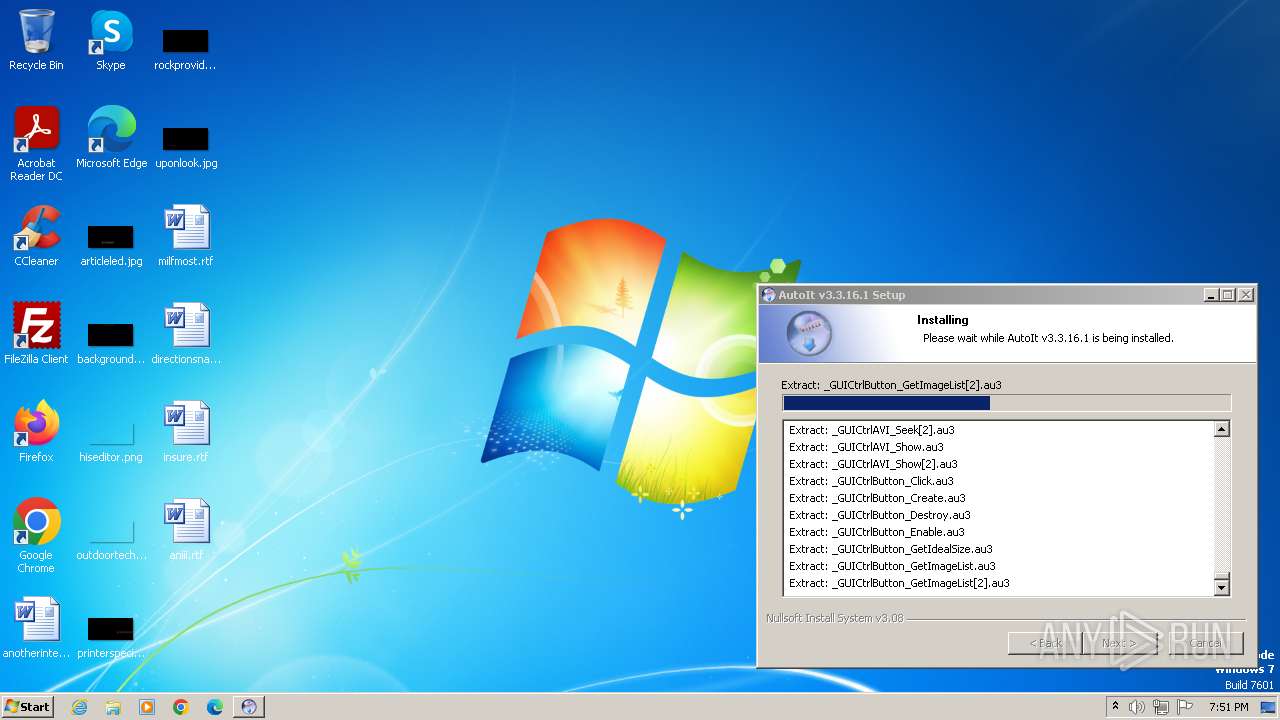
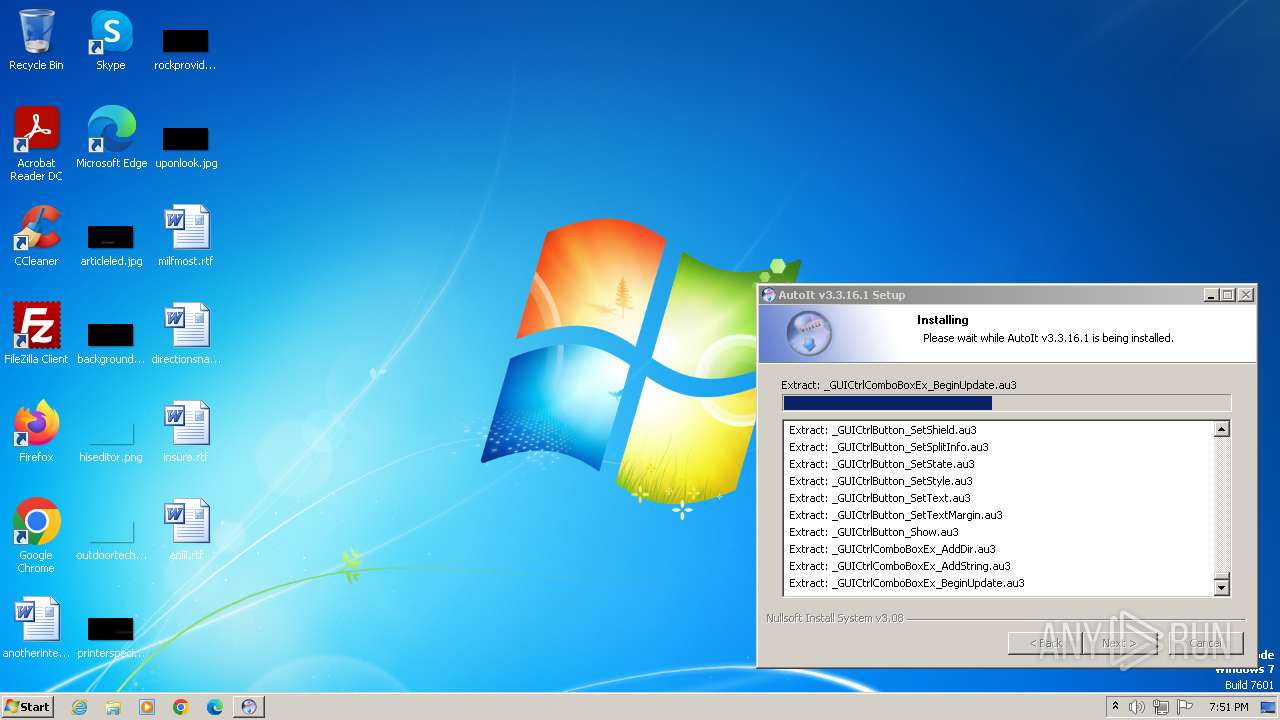
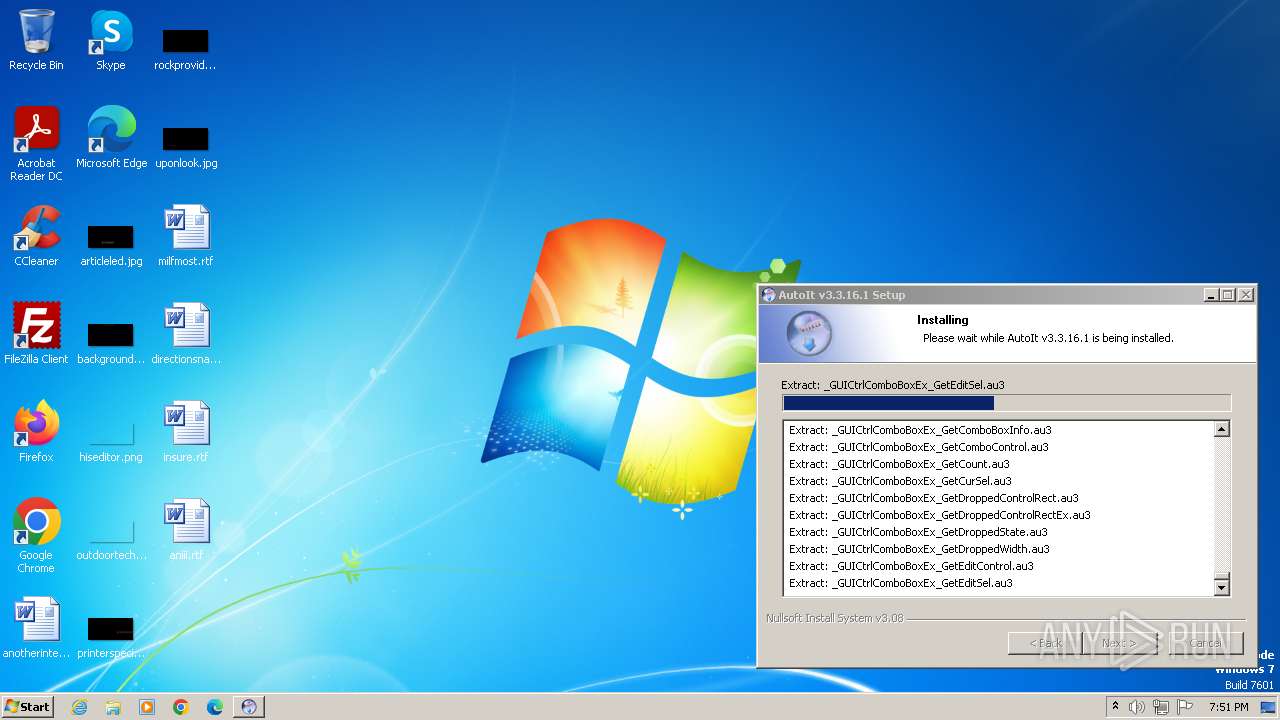
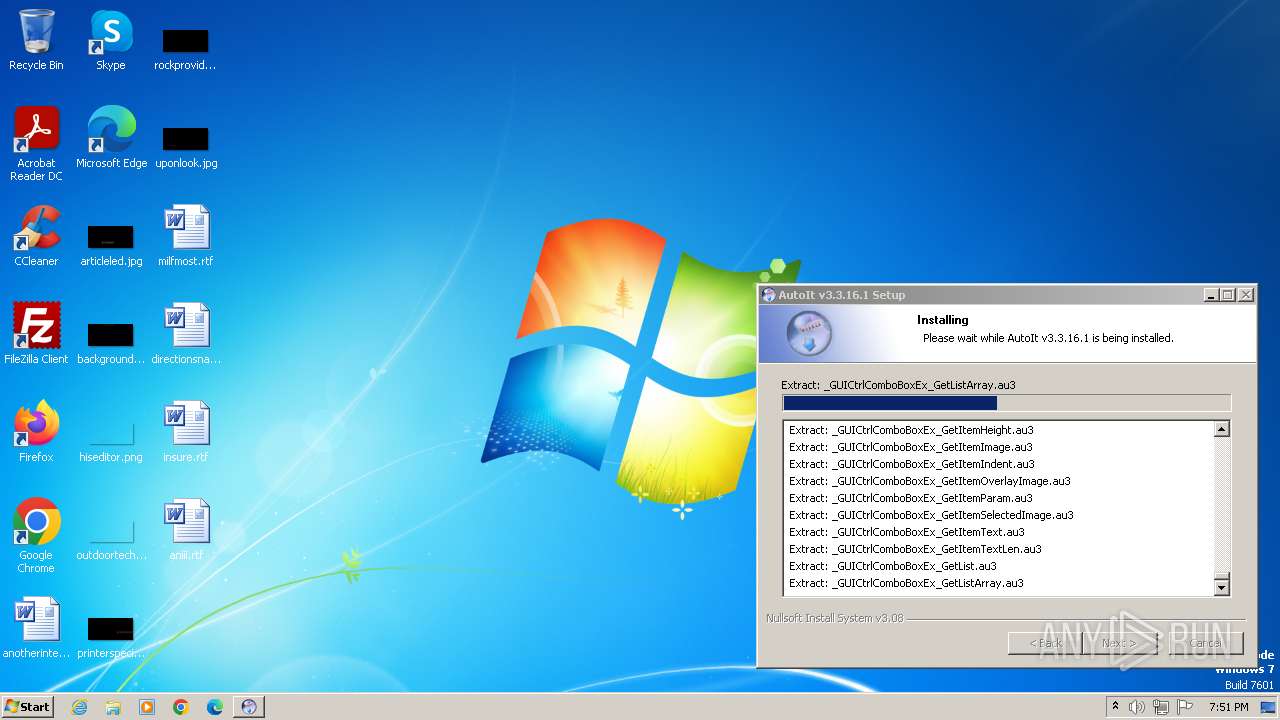
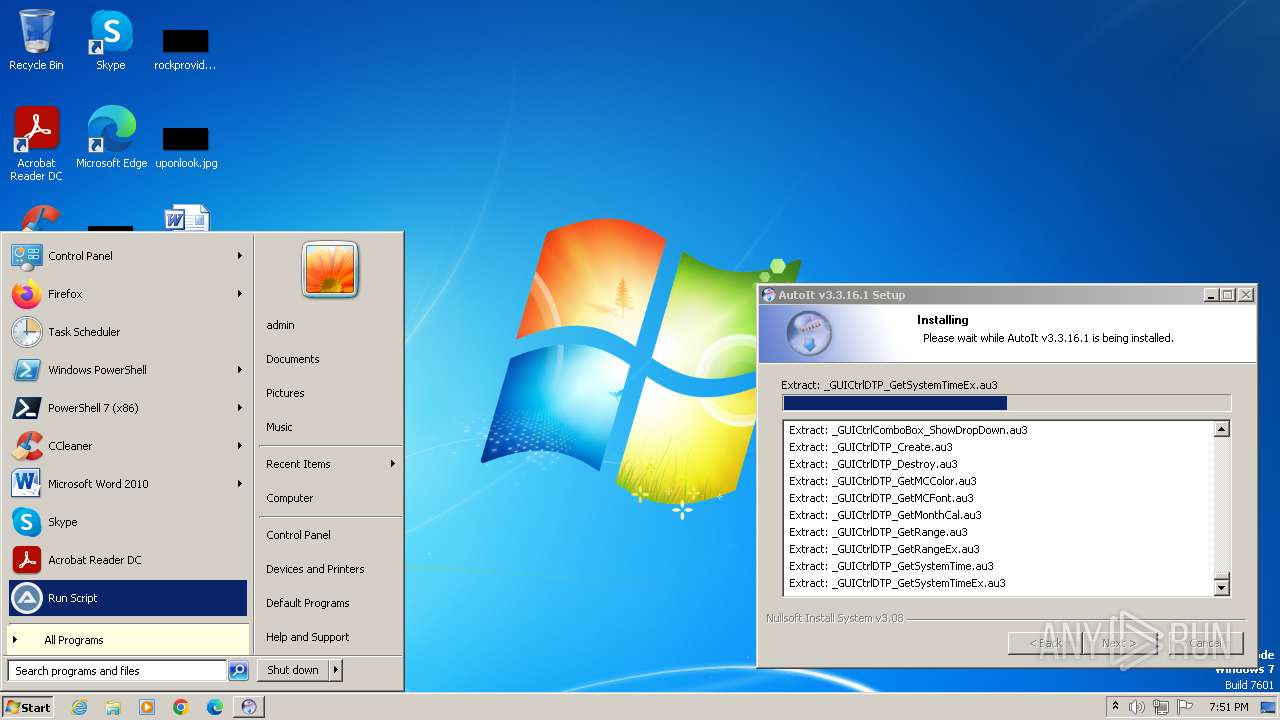
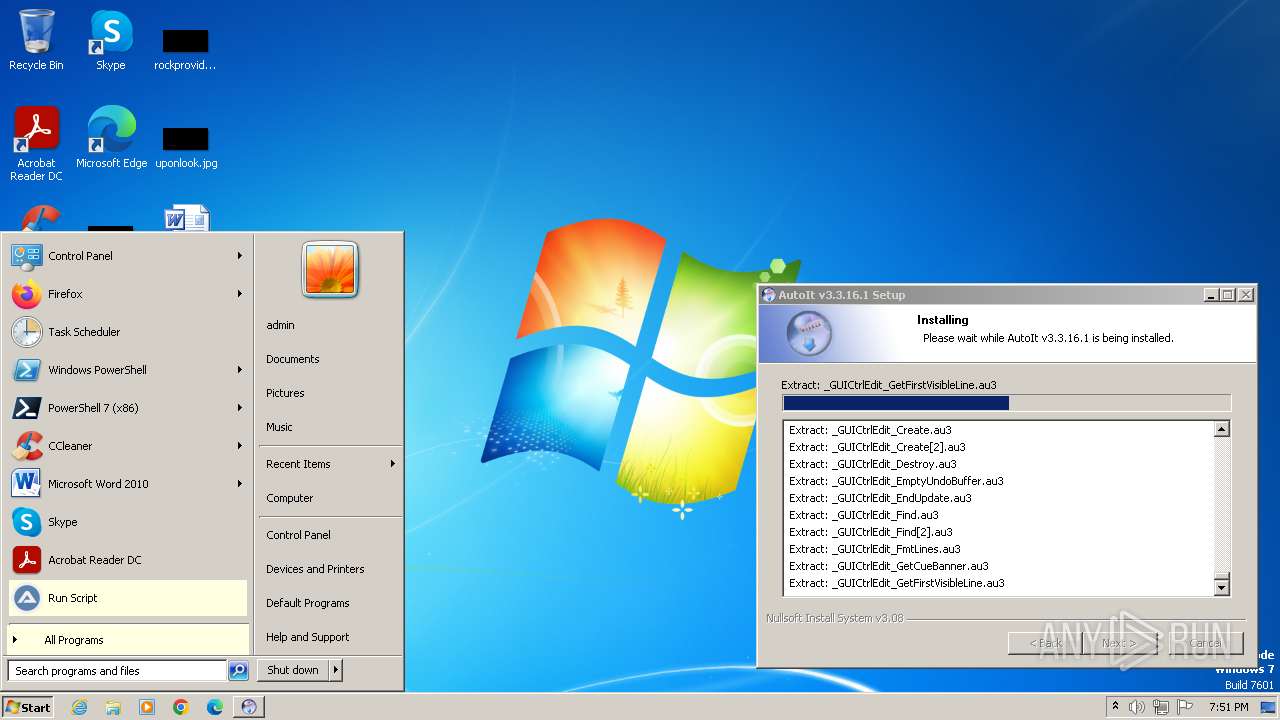
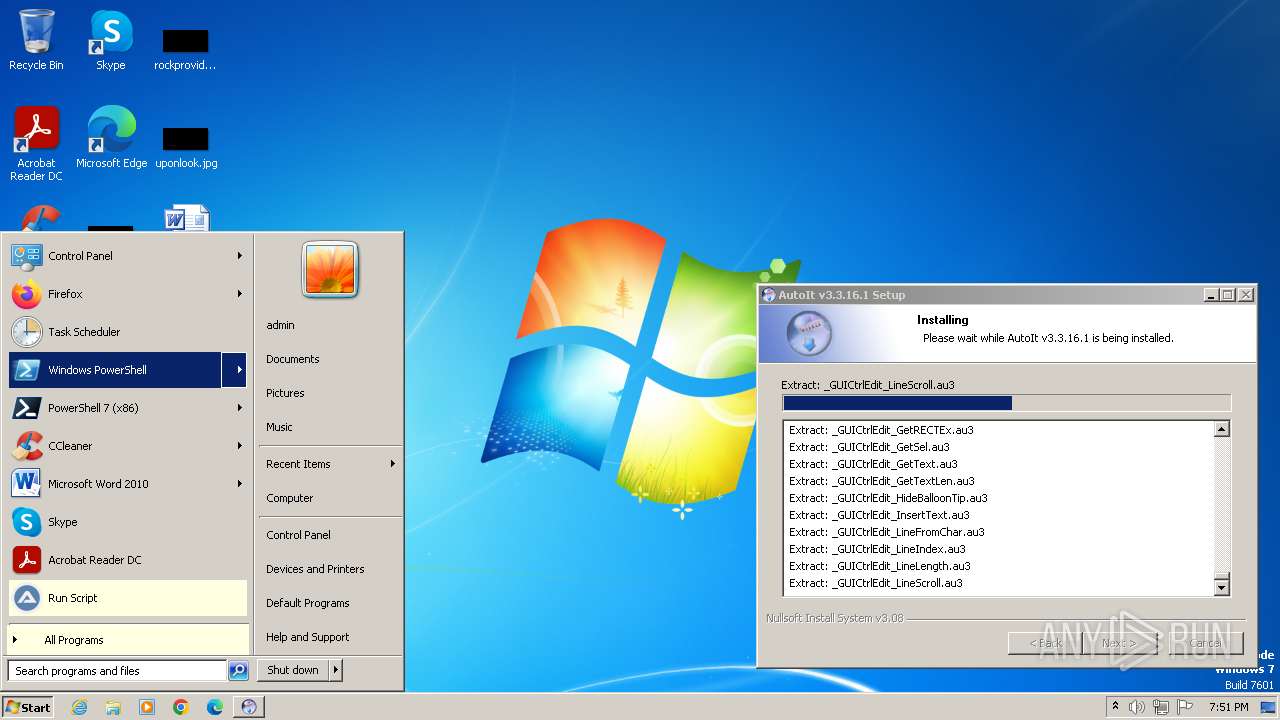
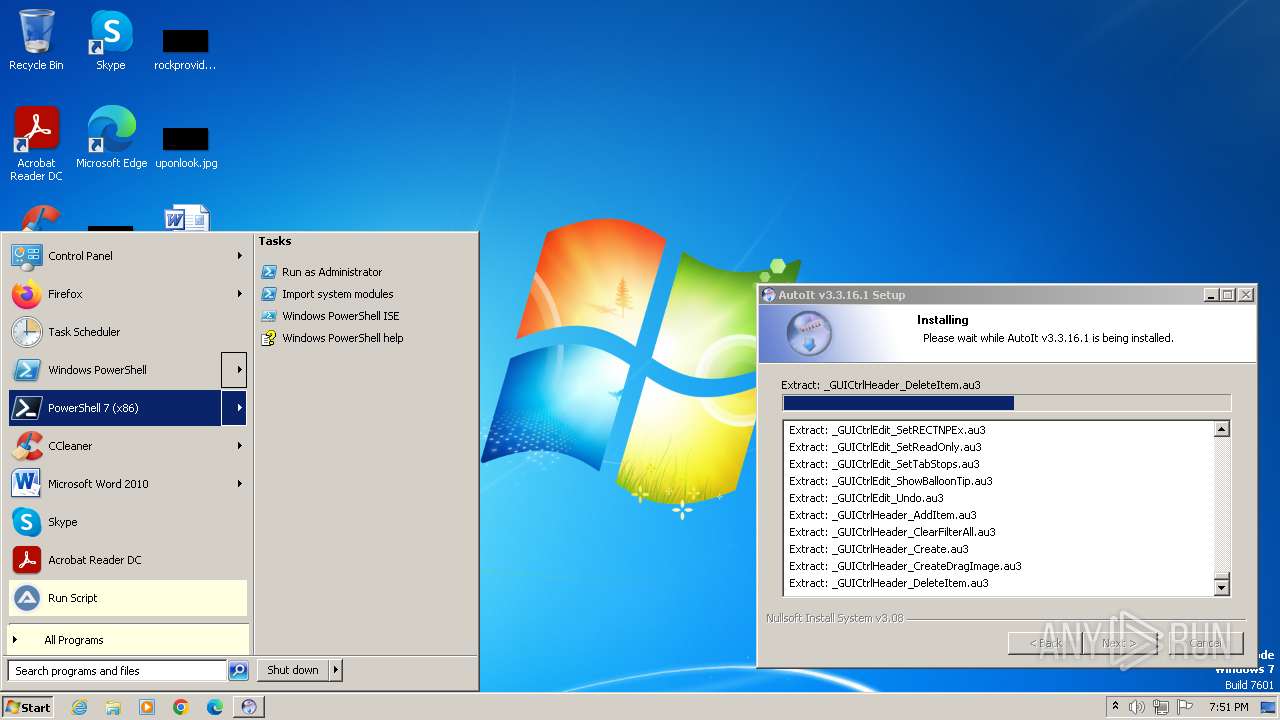
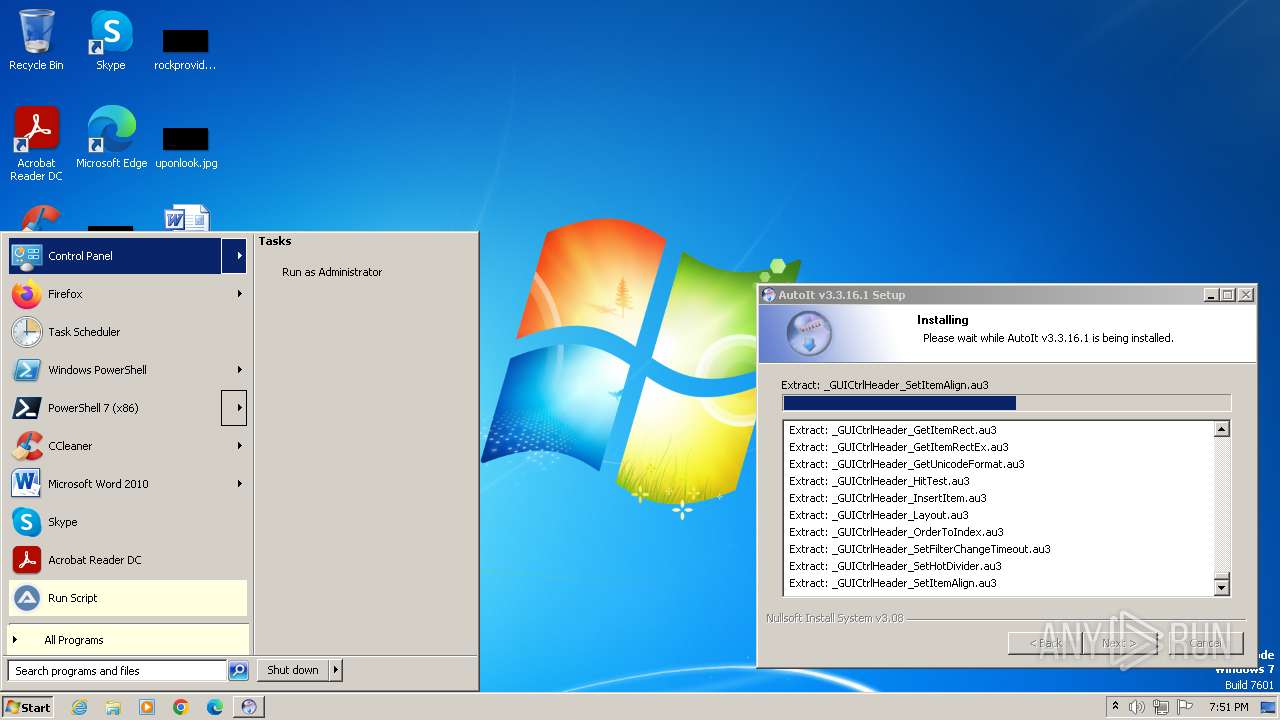
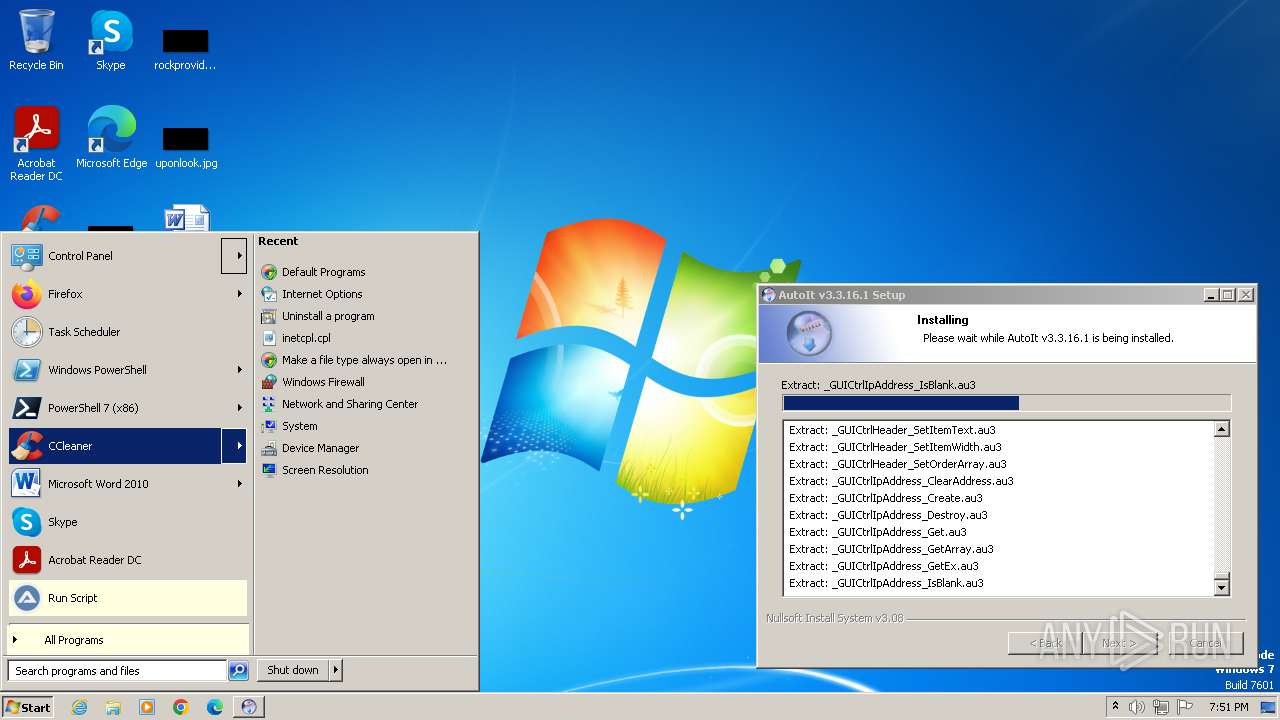
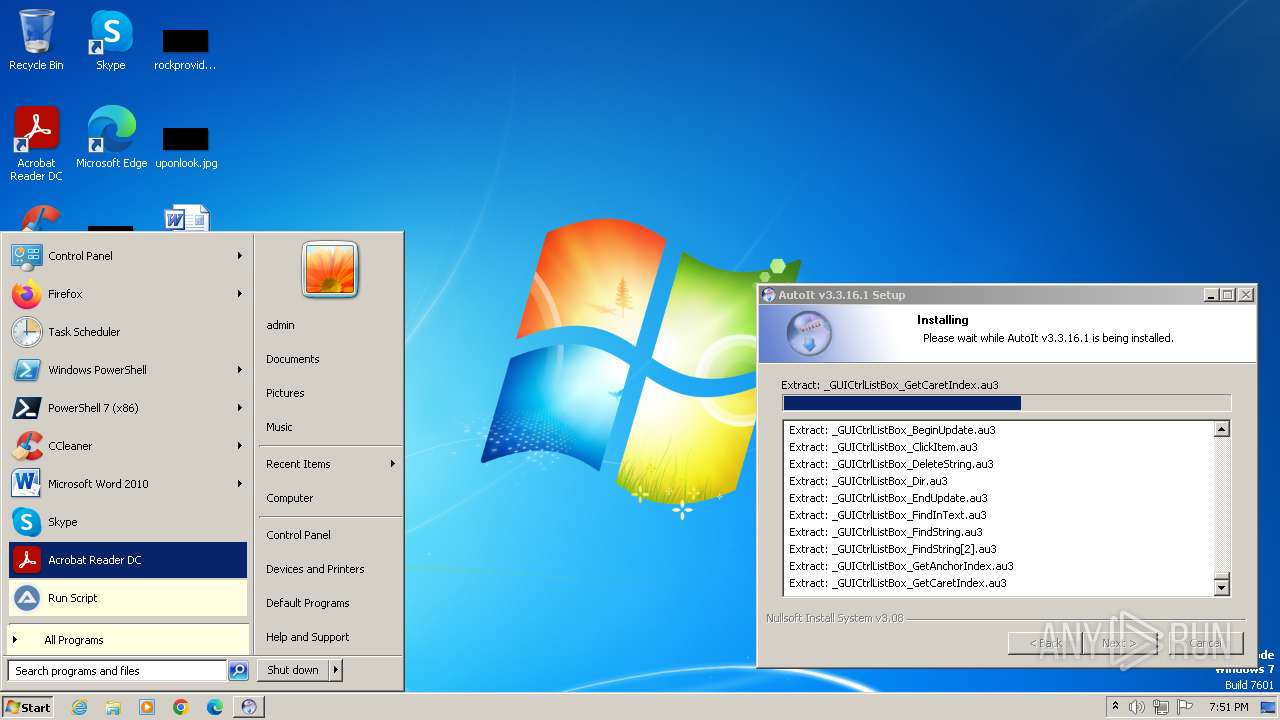
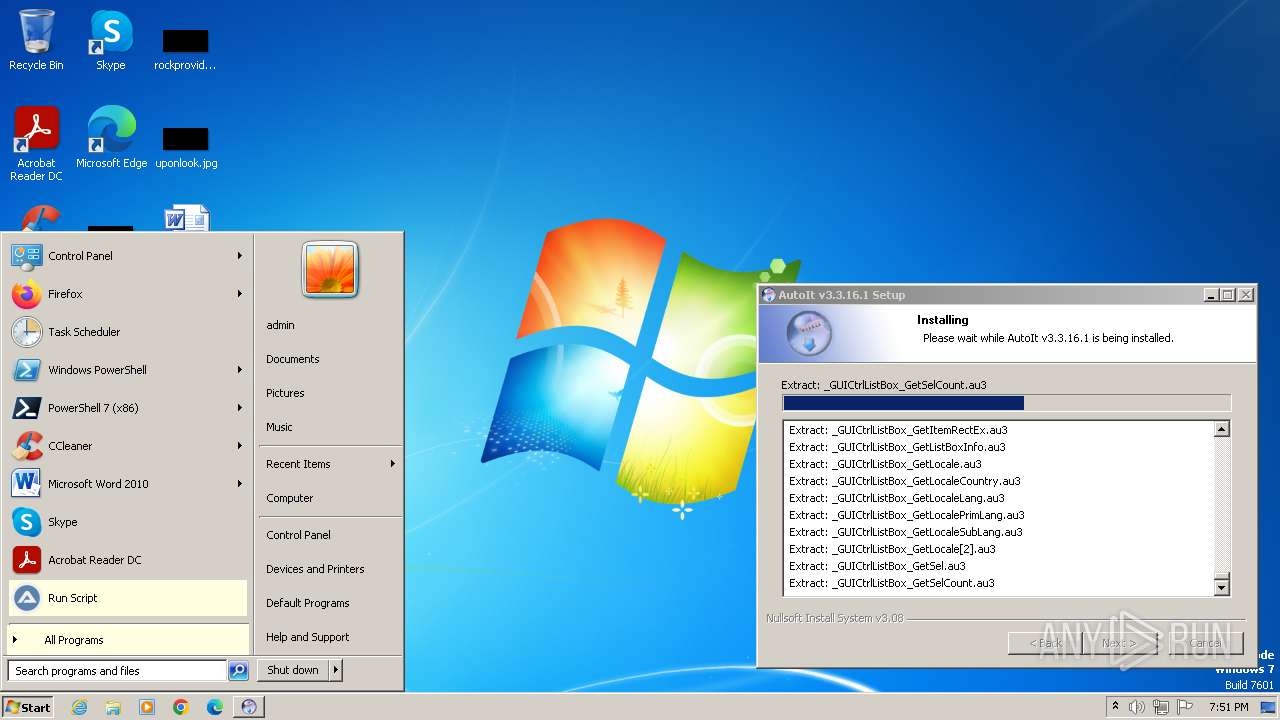
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
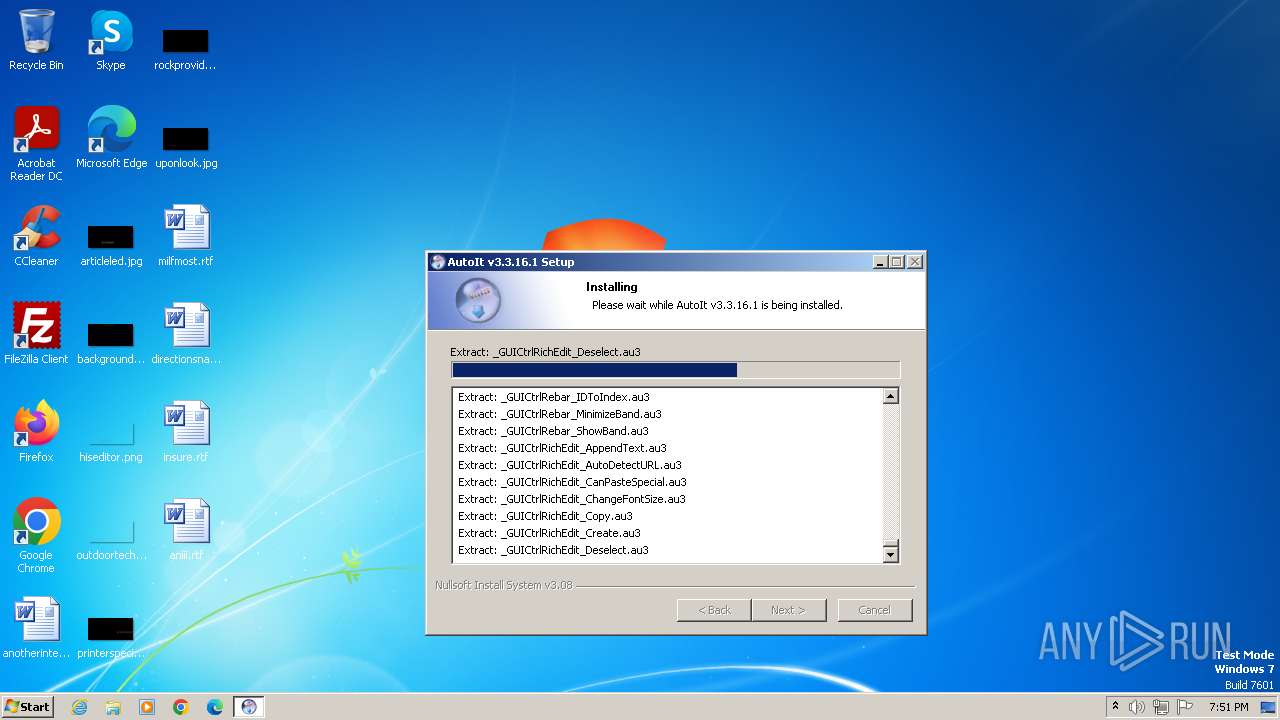
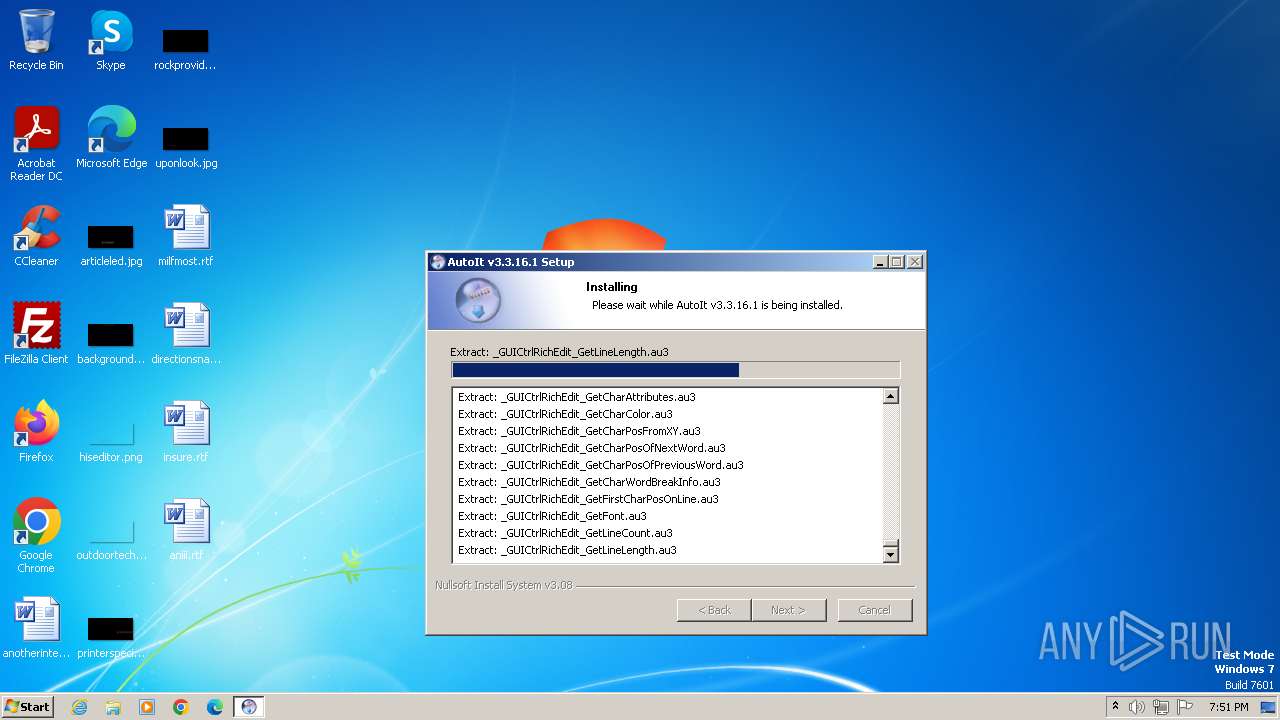
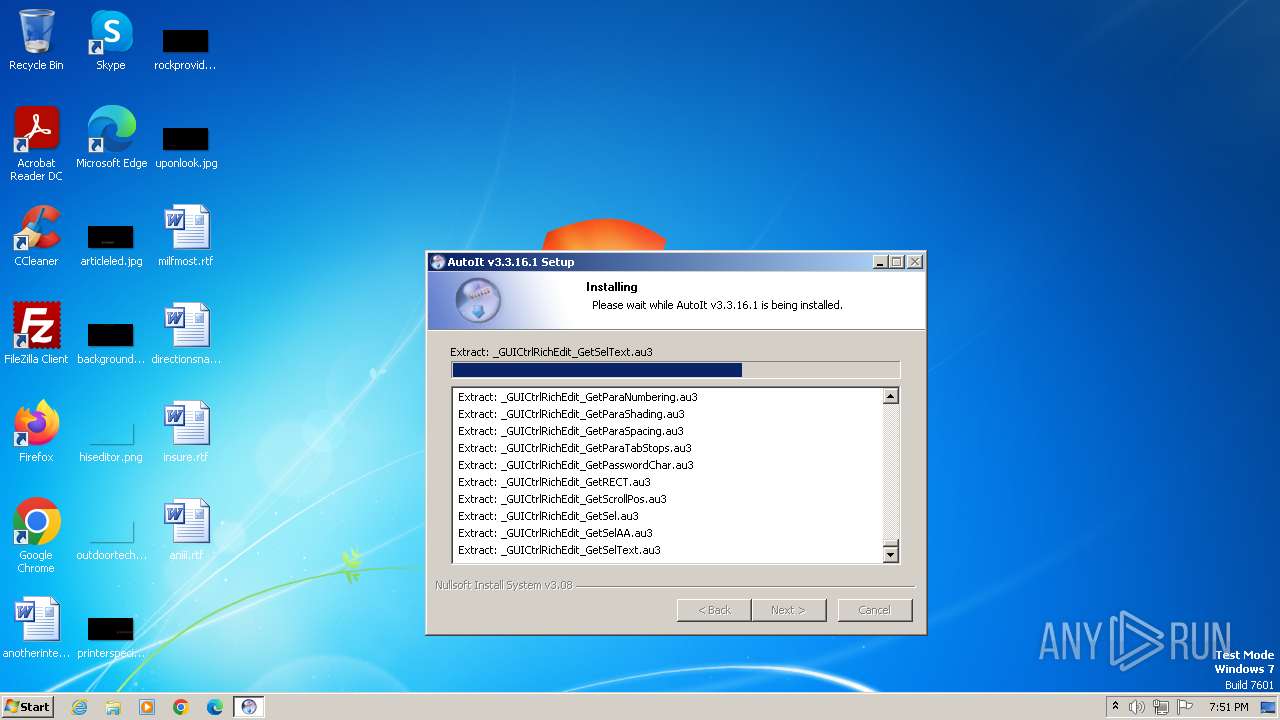
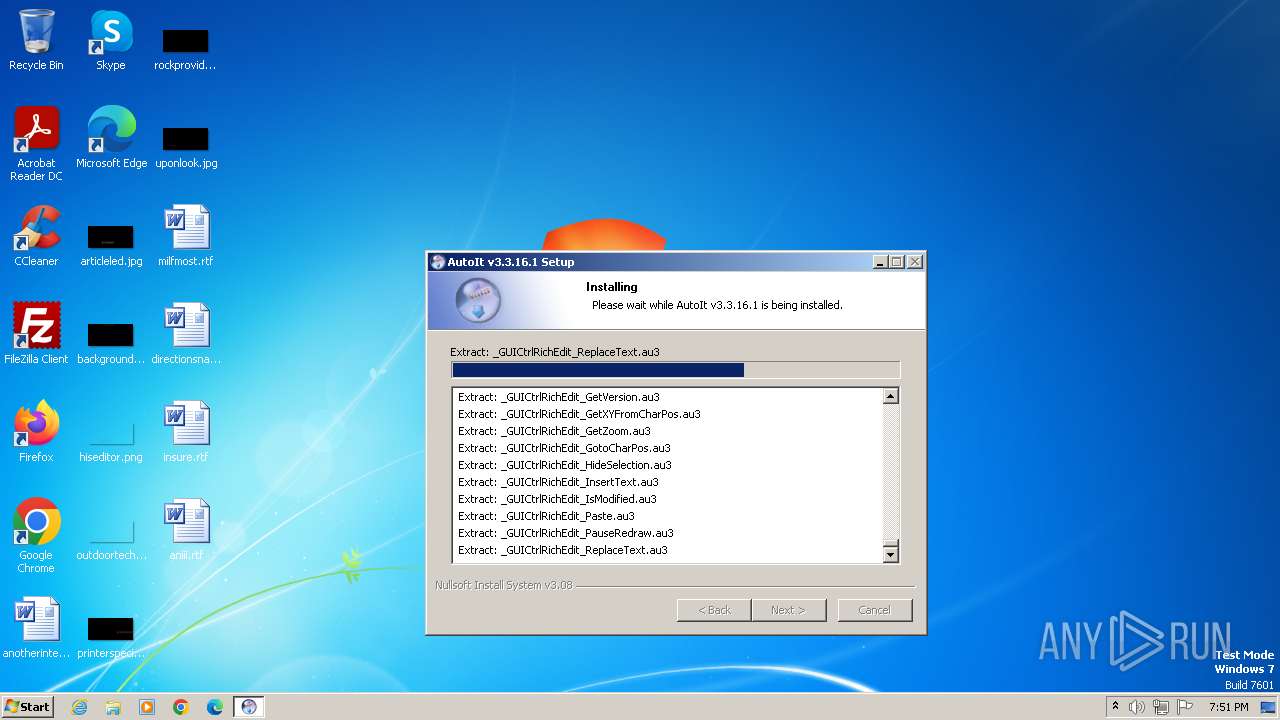
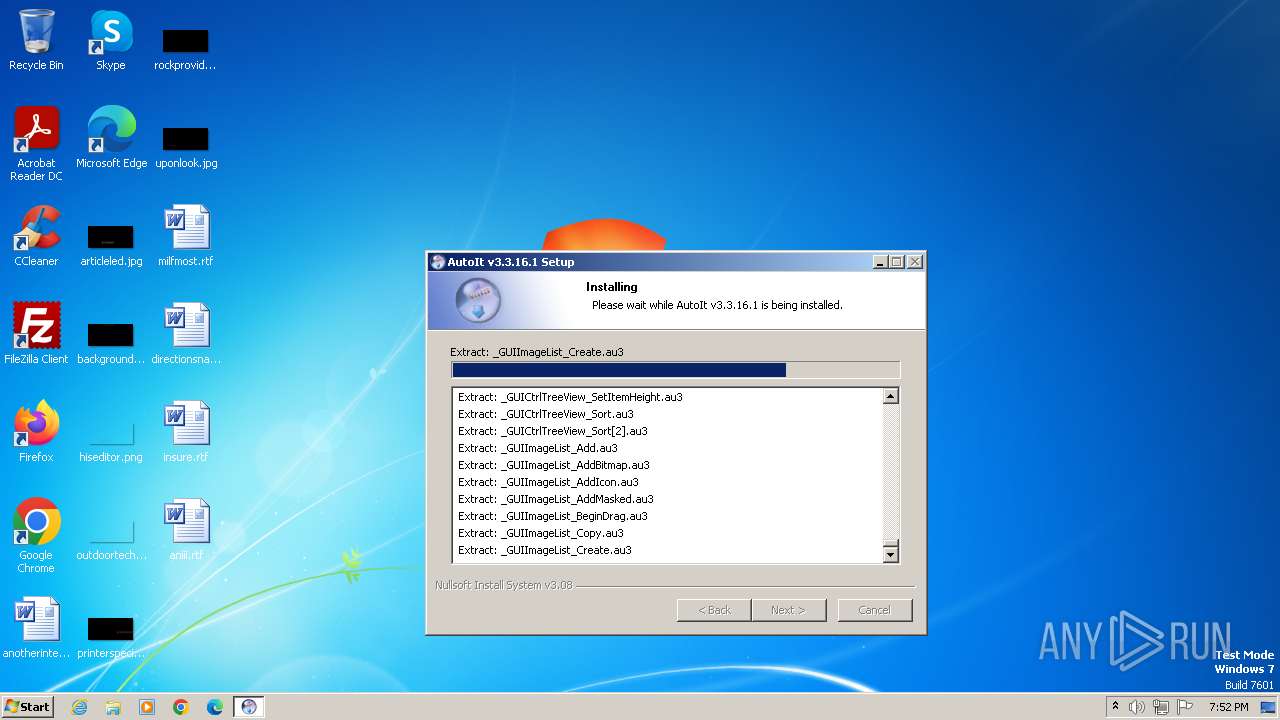
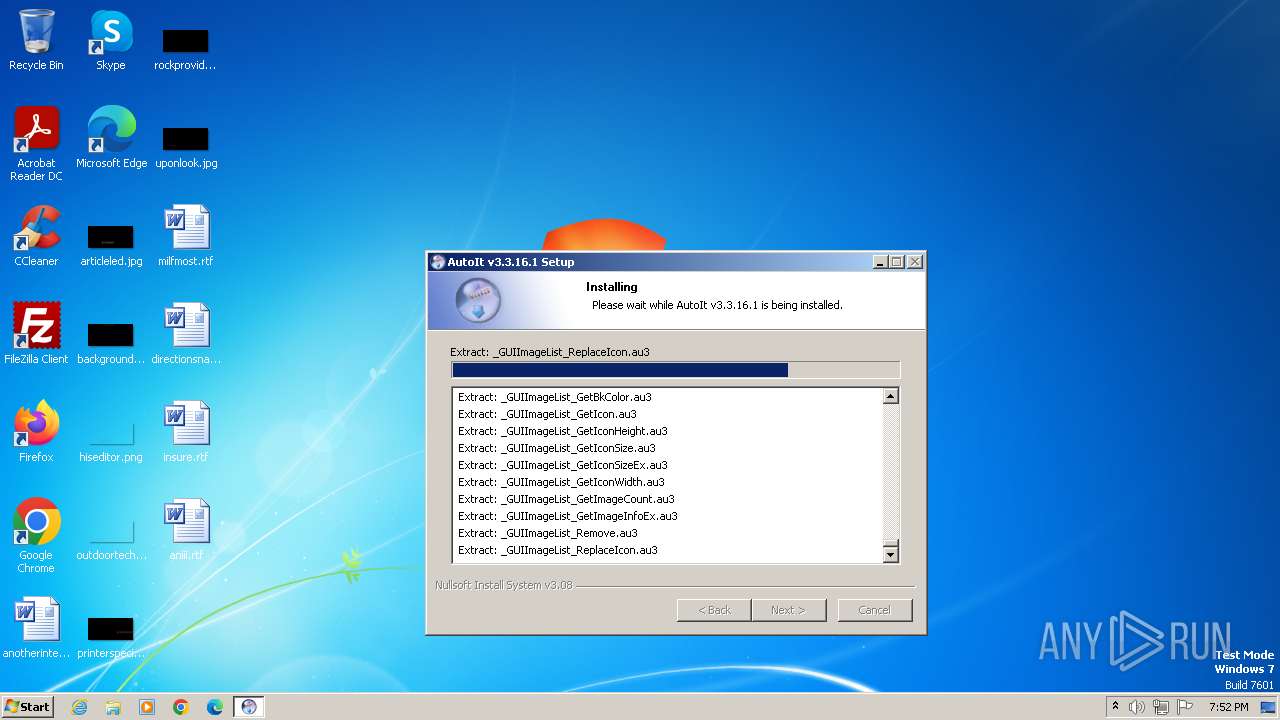
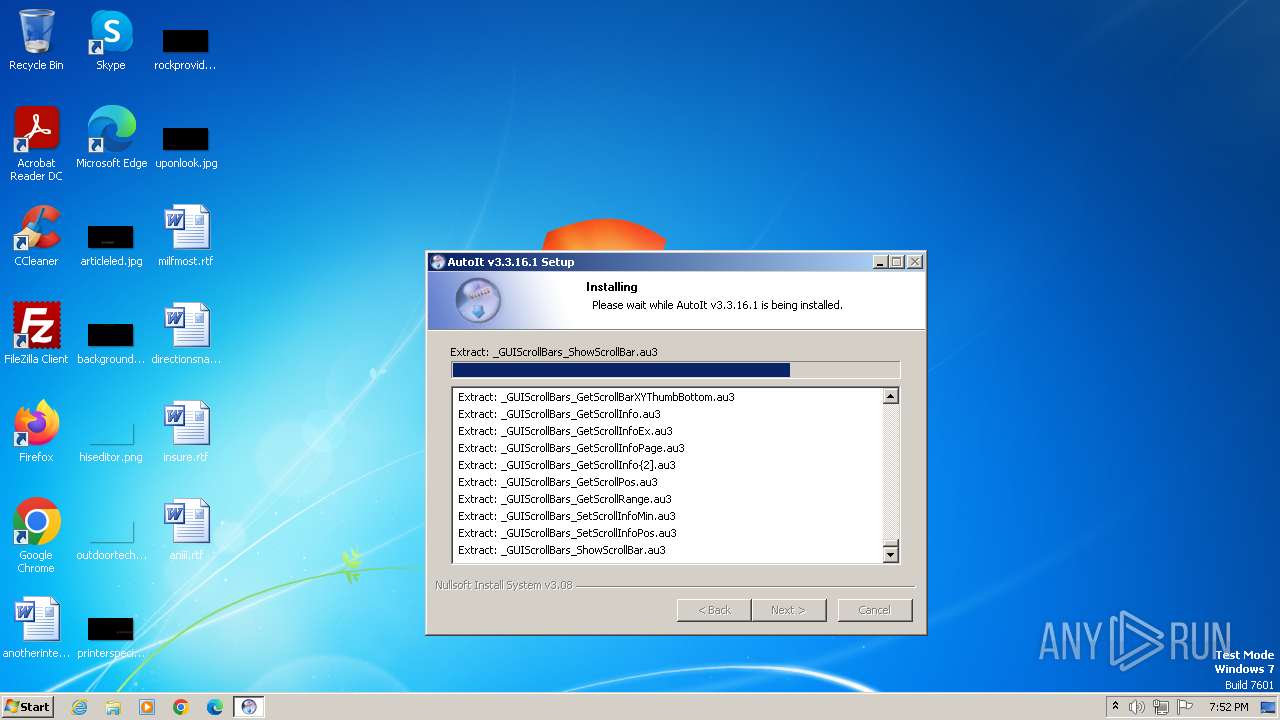
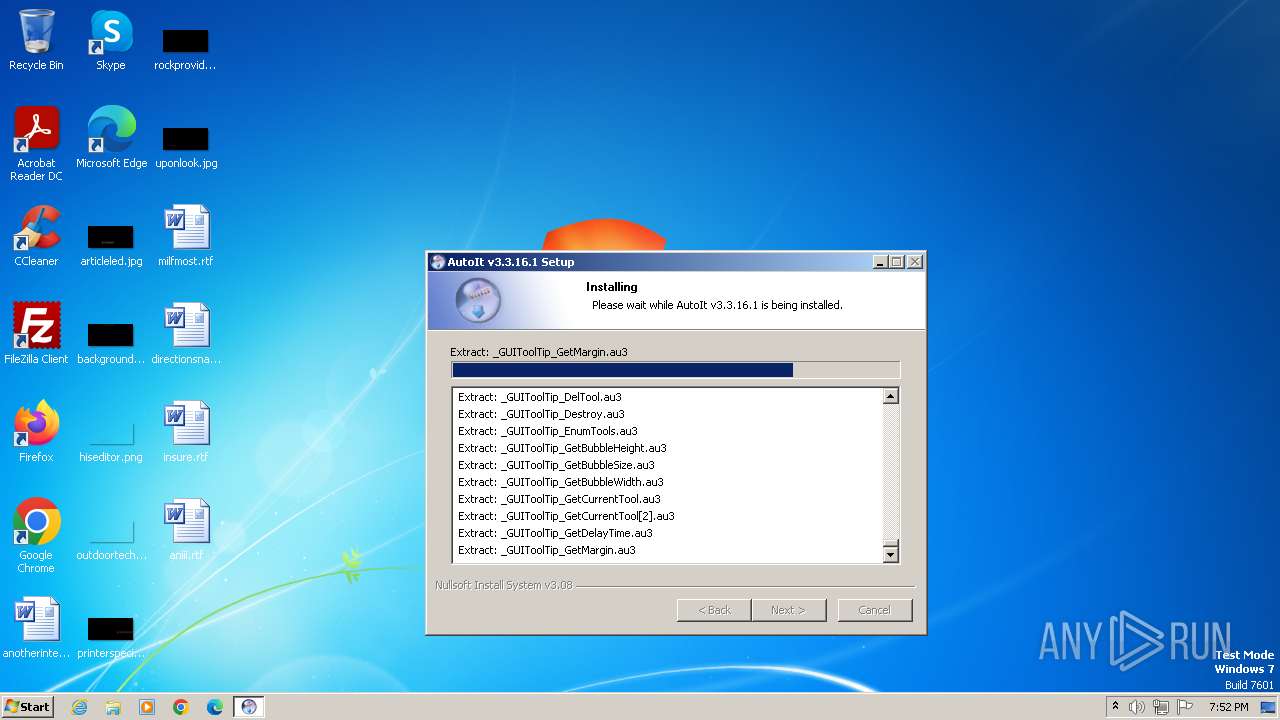
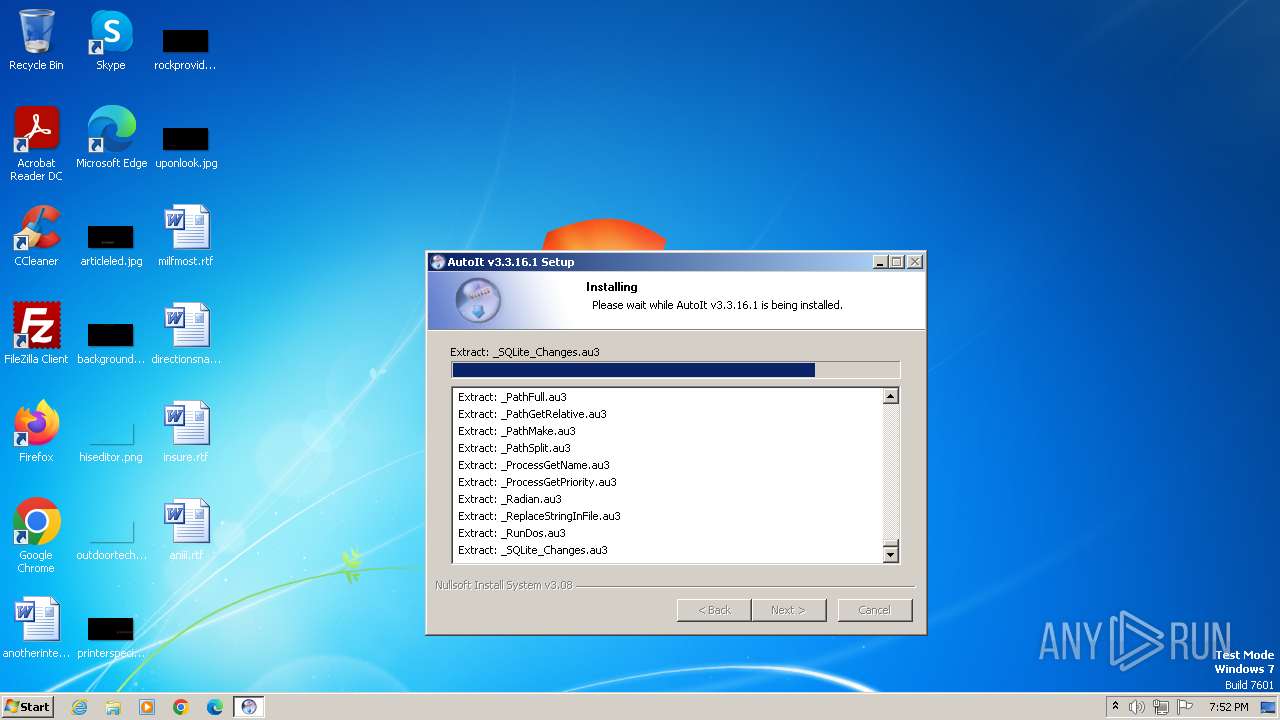
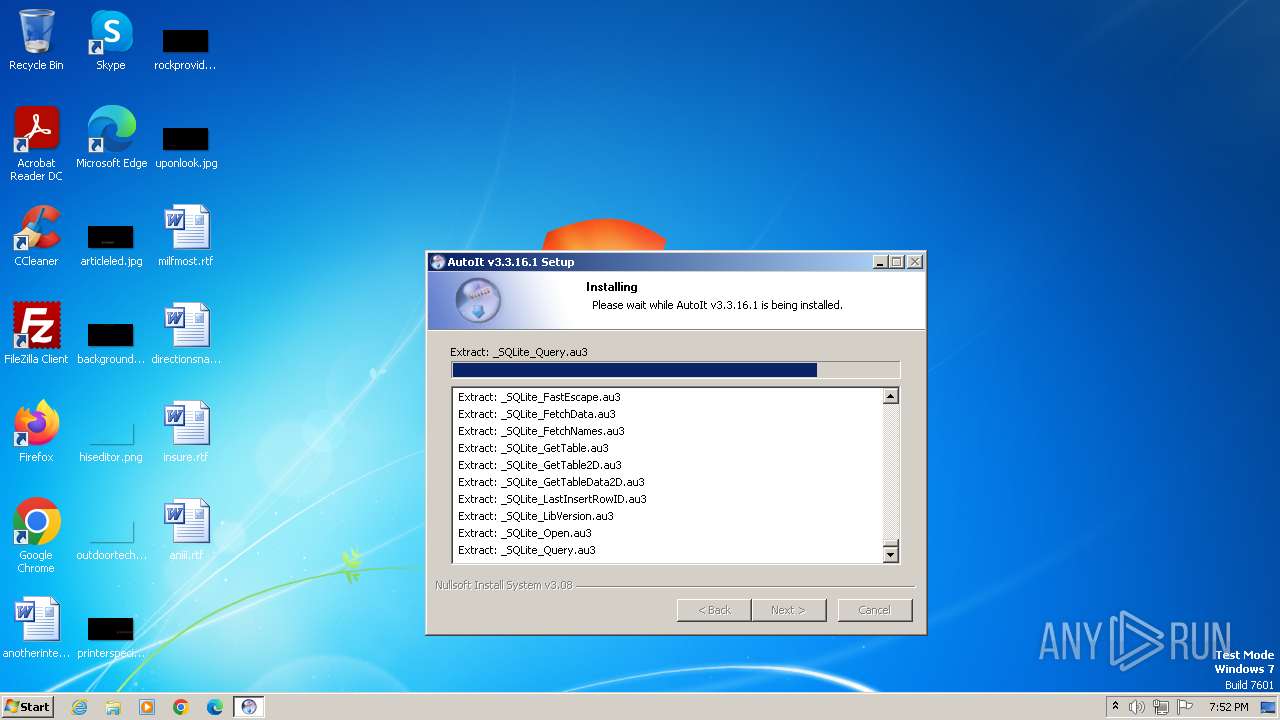
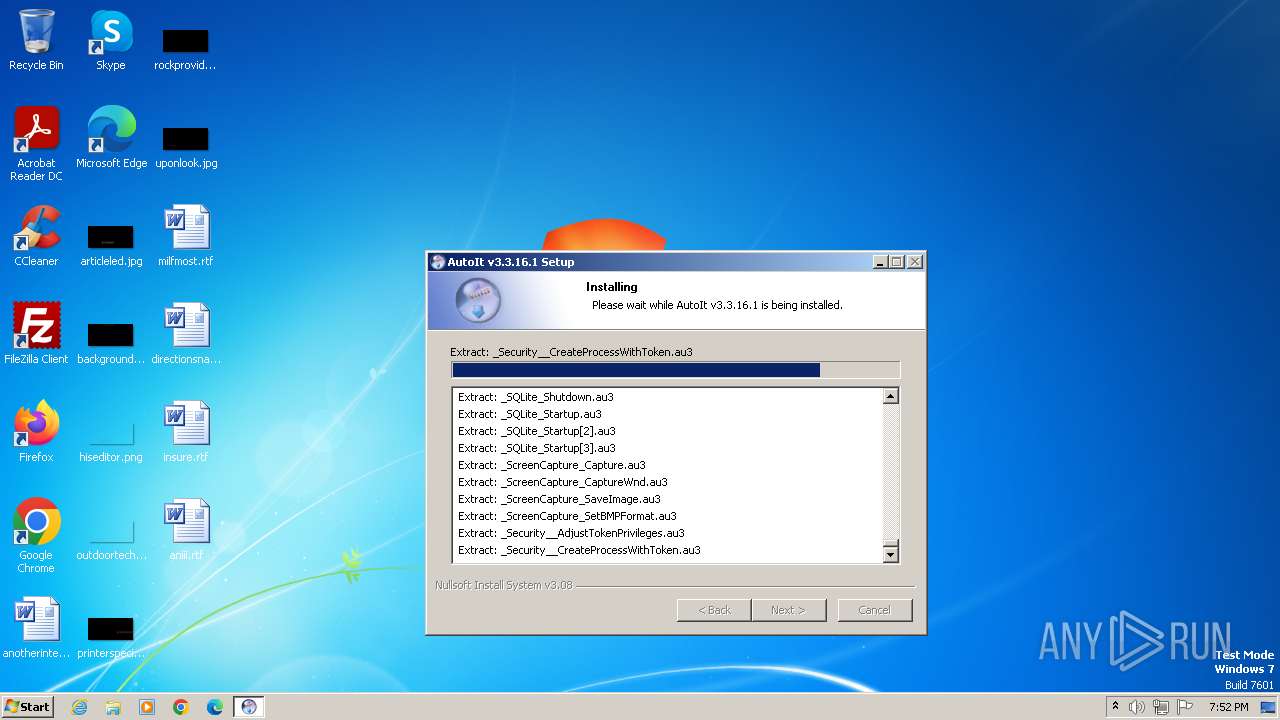
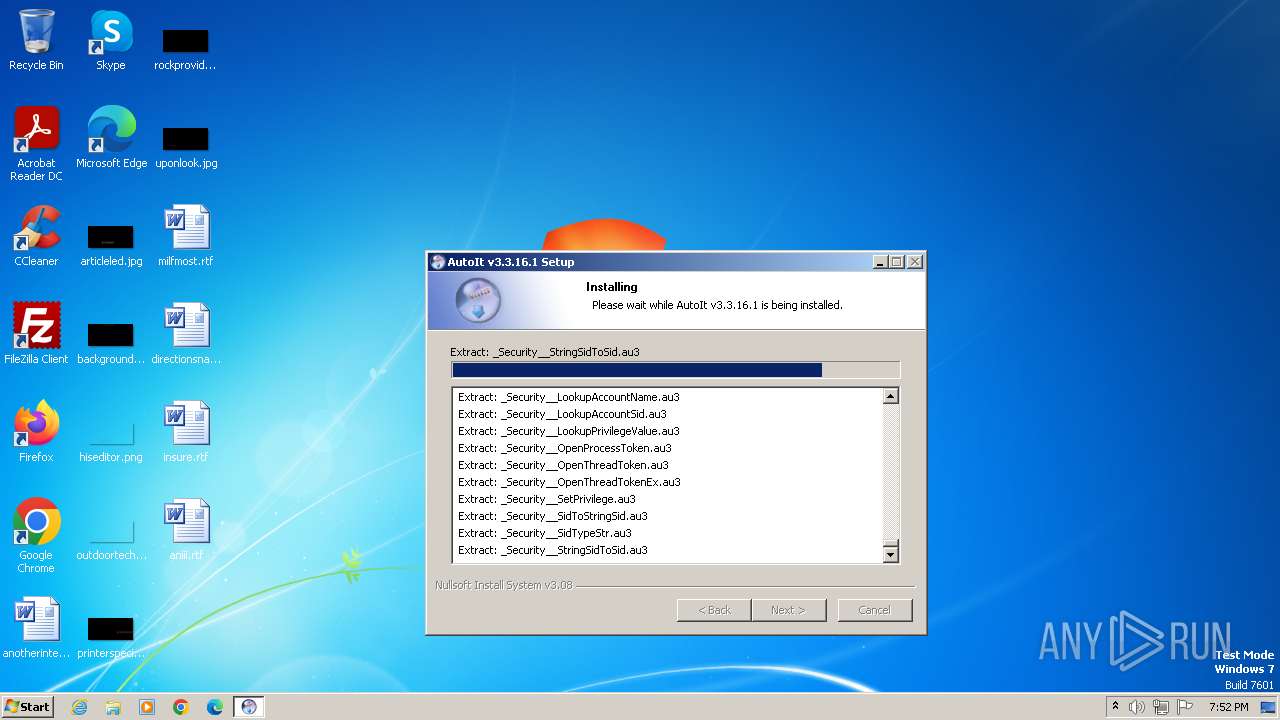
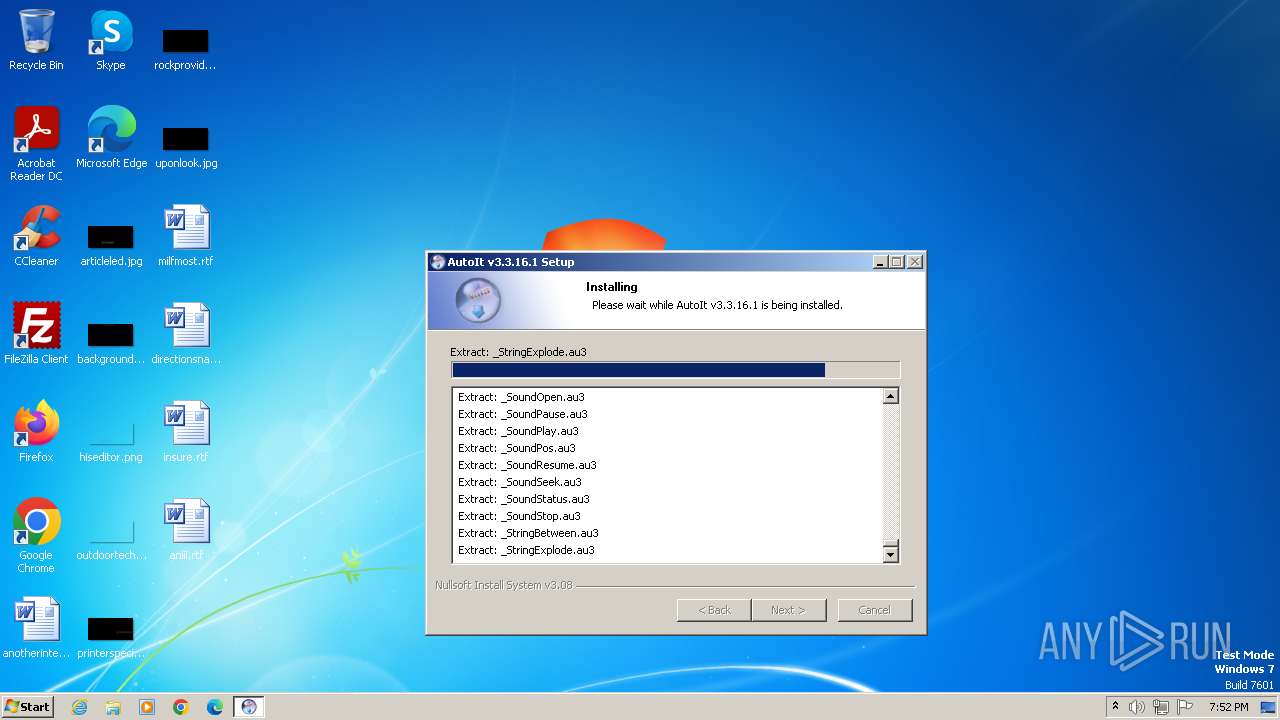
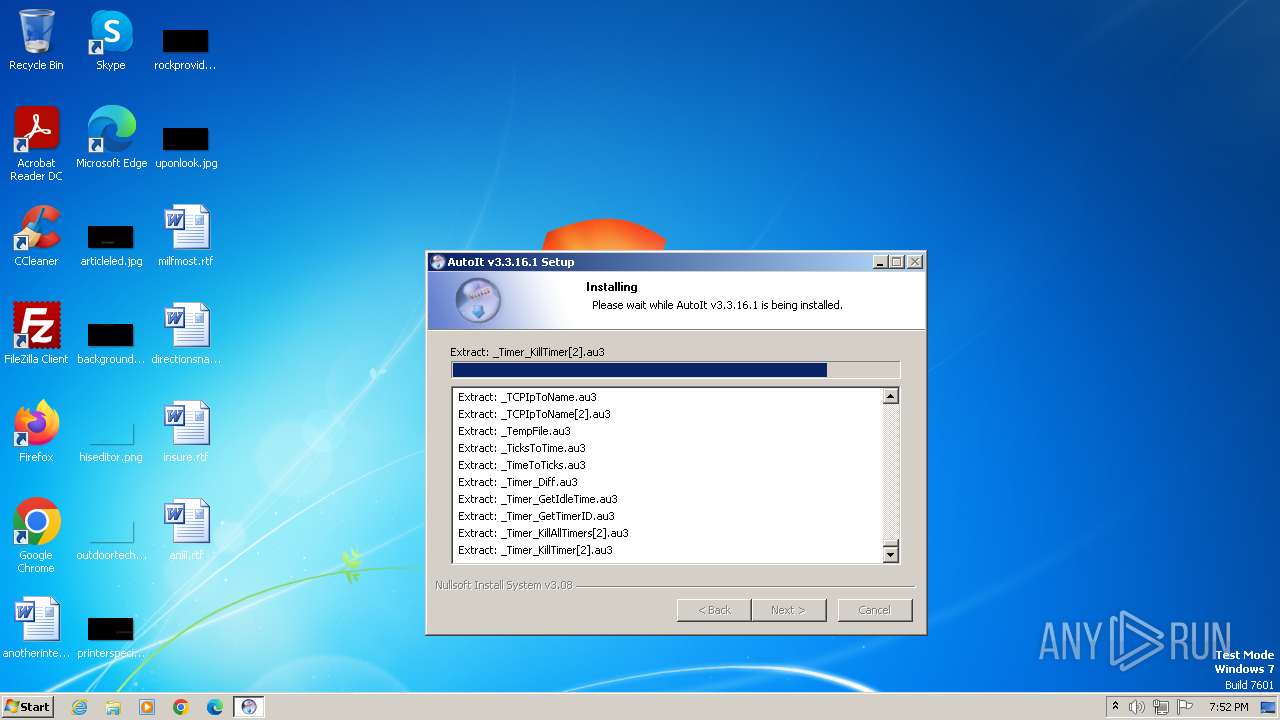
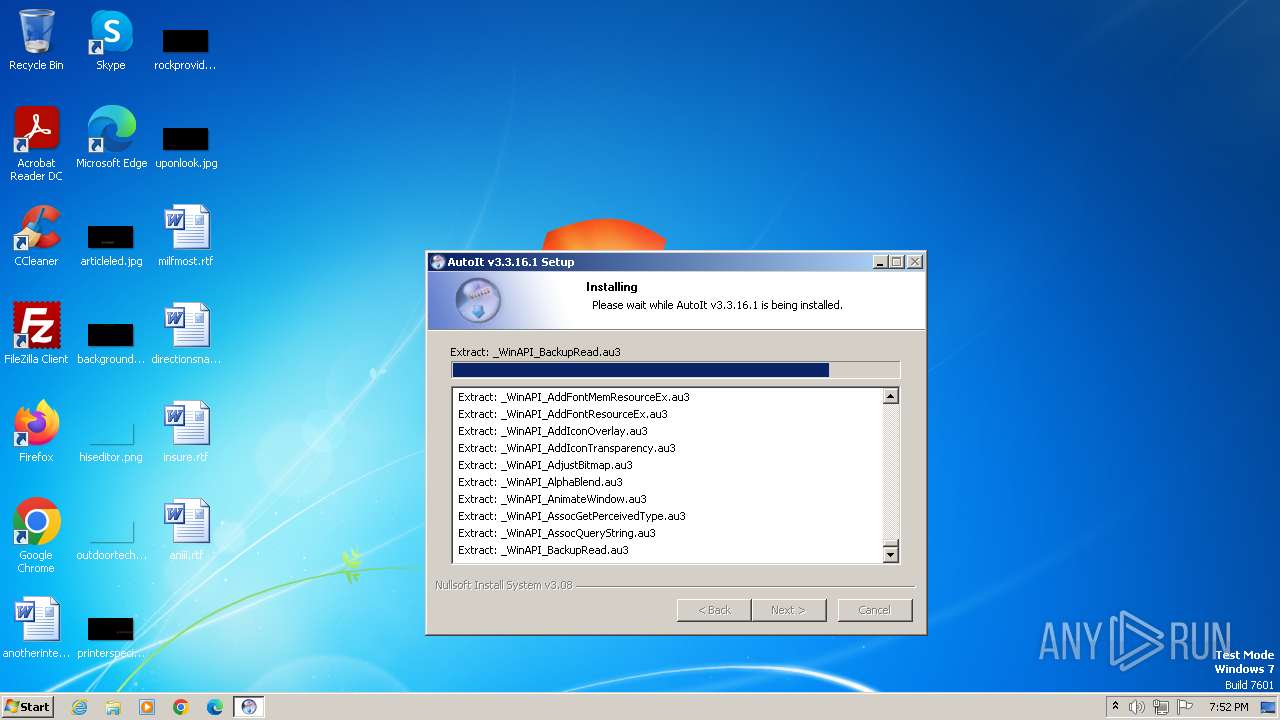
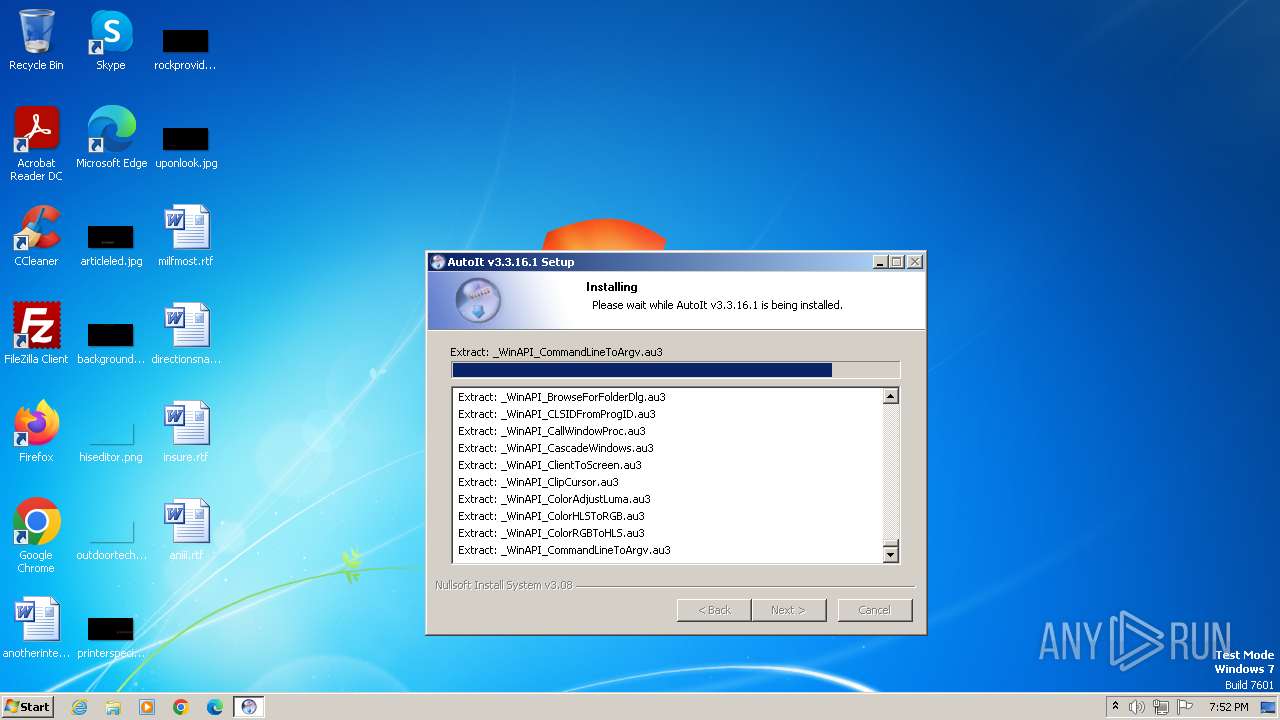
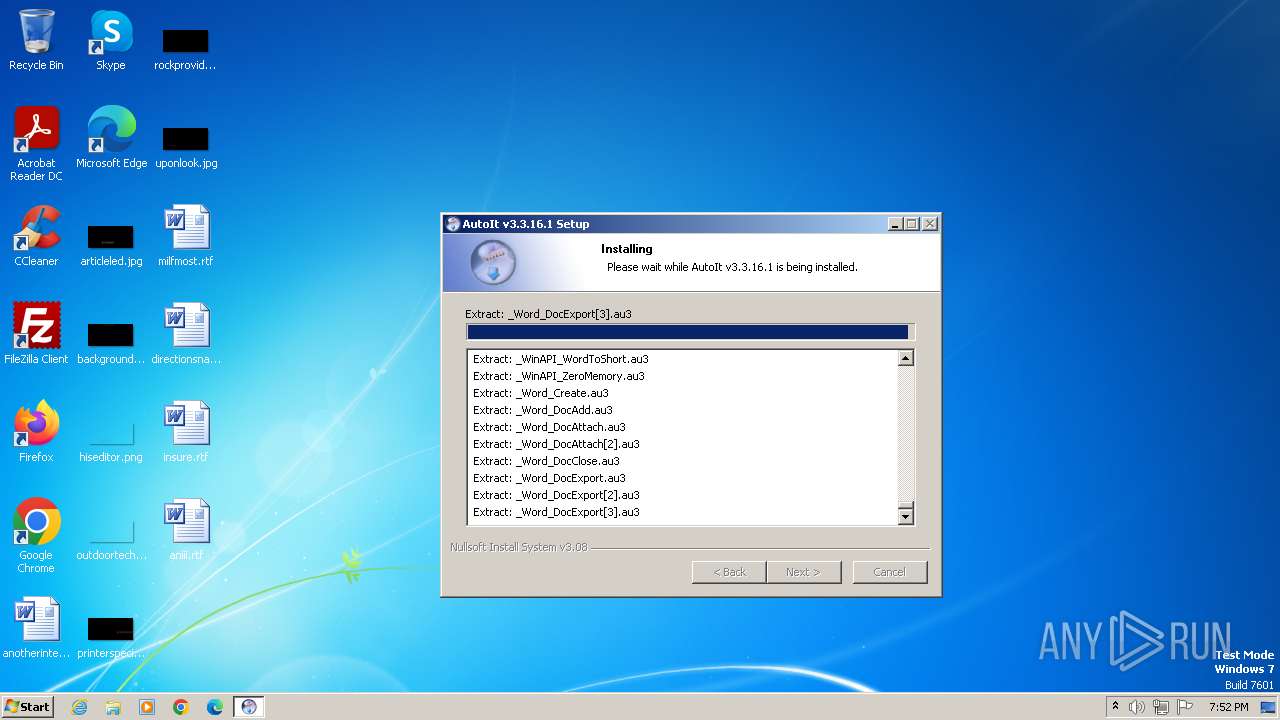
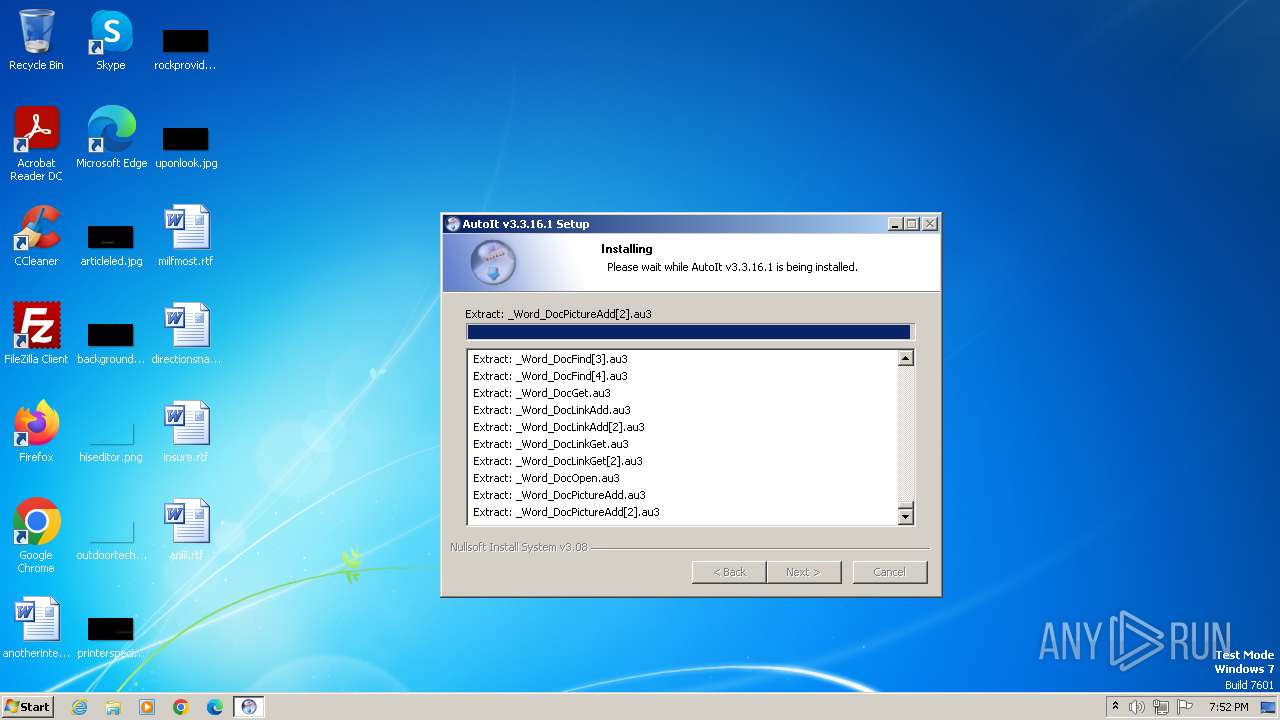
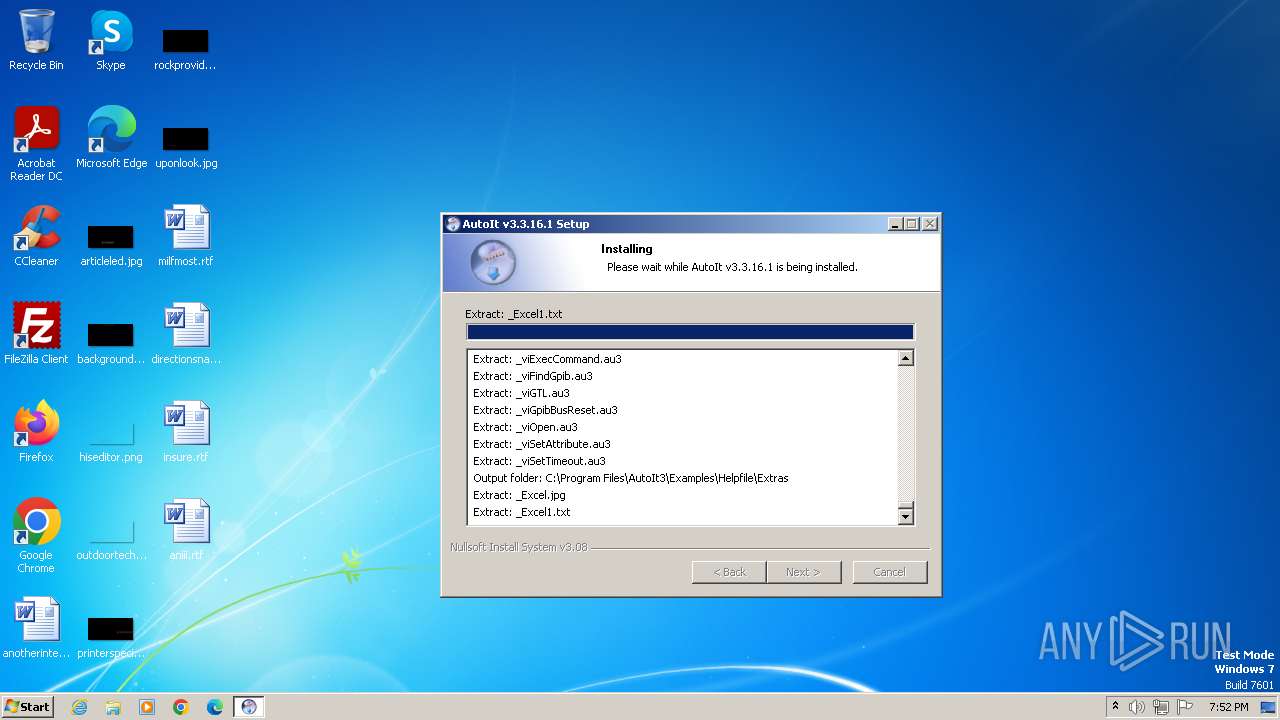
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A65B5DF1A846FB0BB7AD4B2DA19BBBCD |
| SHA1: | B93C659C6F9ECA5CDAEA8E552C0466CAC3EA61D6 |
| SHA256: | 19F91EE8A2ACF408D69BE07E1C4A99992213E565B9C8BB6D5C52F59F79707DA3 |
| SSDEEP: | 393216:TDaWWhLNL186VkPwBOf74ycQf2TftfJBYT6IL/owfe:TDaWWdNxpg2icfRC7L/xm |
MALICIOUS
Drops the executable file immediately after the start
- autoit-v3-setup.exe (PID: 3608)
SUSPICIOUS
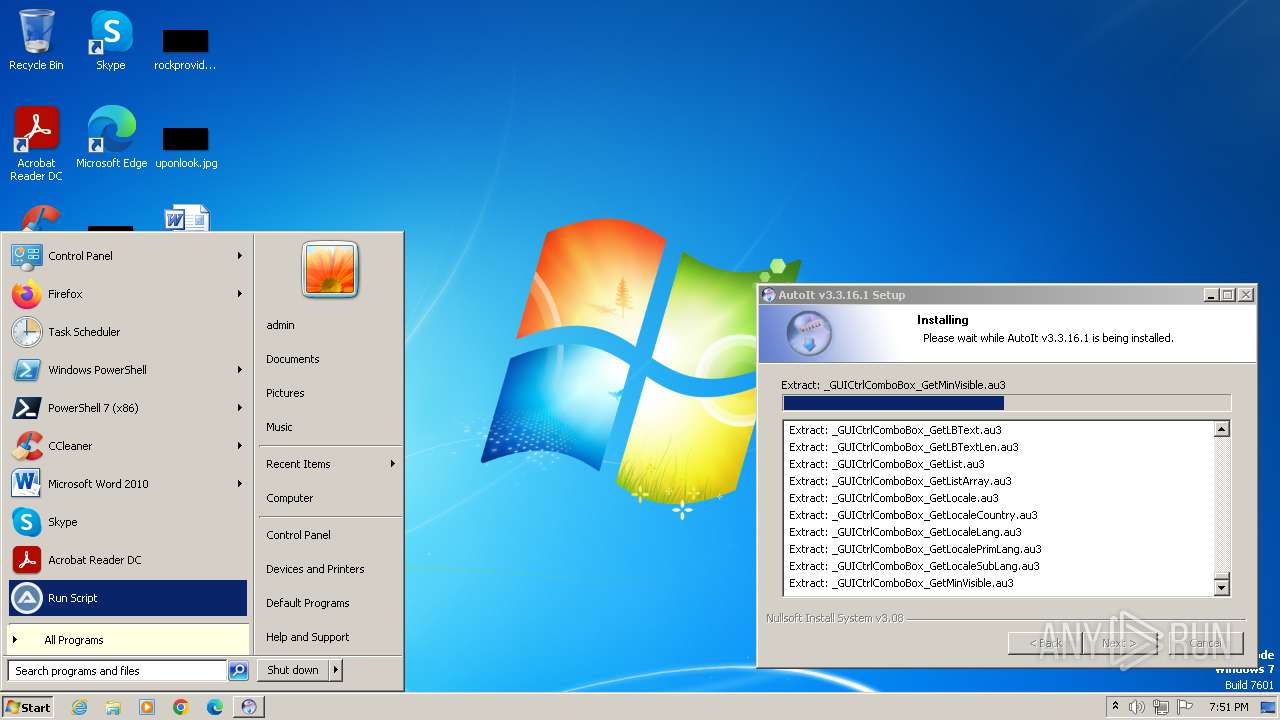
Malware-specific behavior (creating "System.dll" in Temp)
- autoit-v3-setup.exe (PID: 3608)
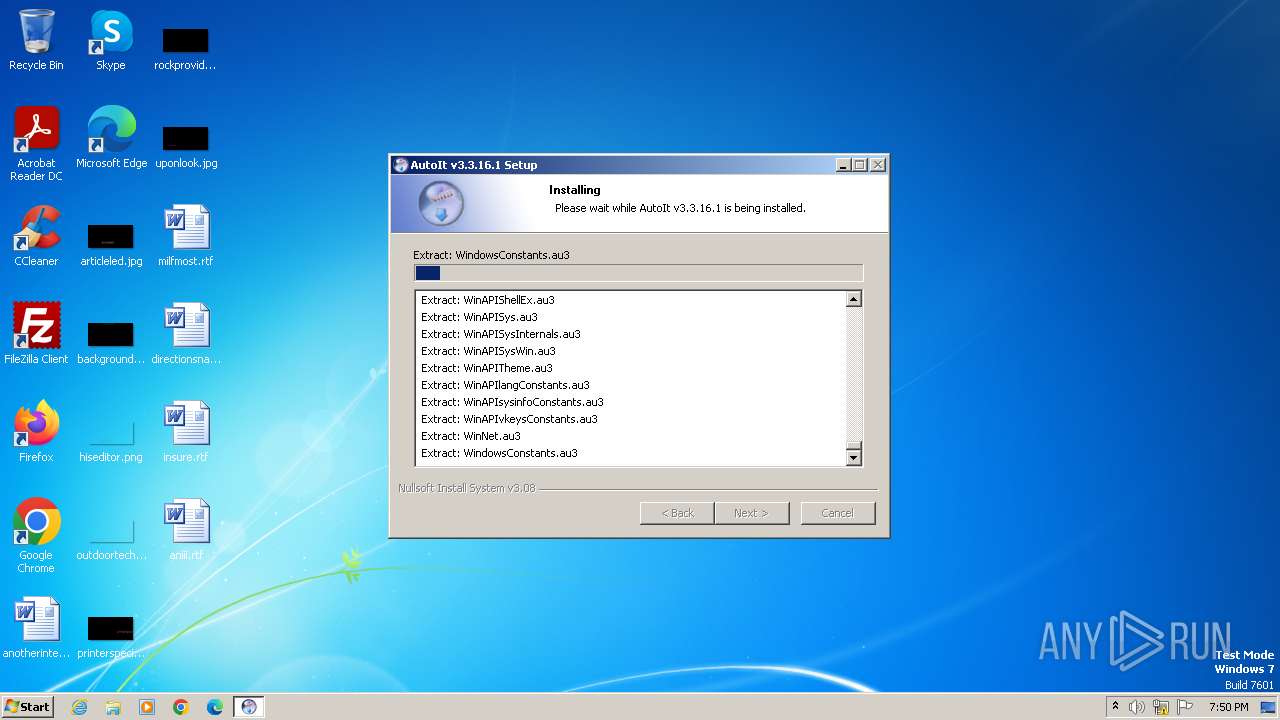
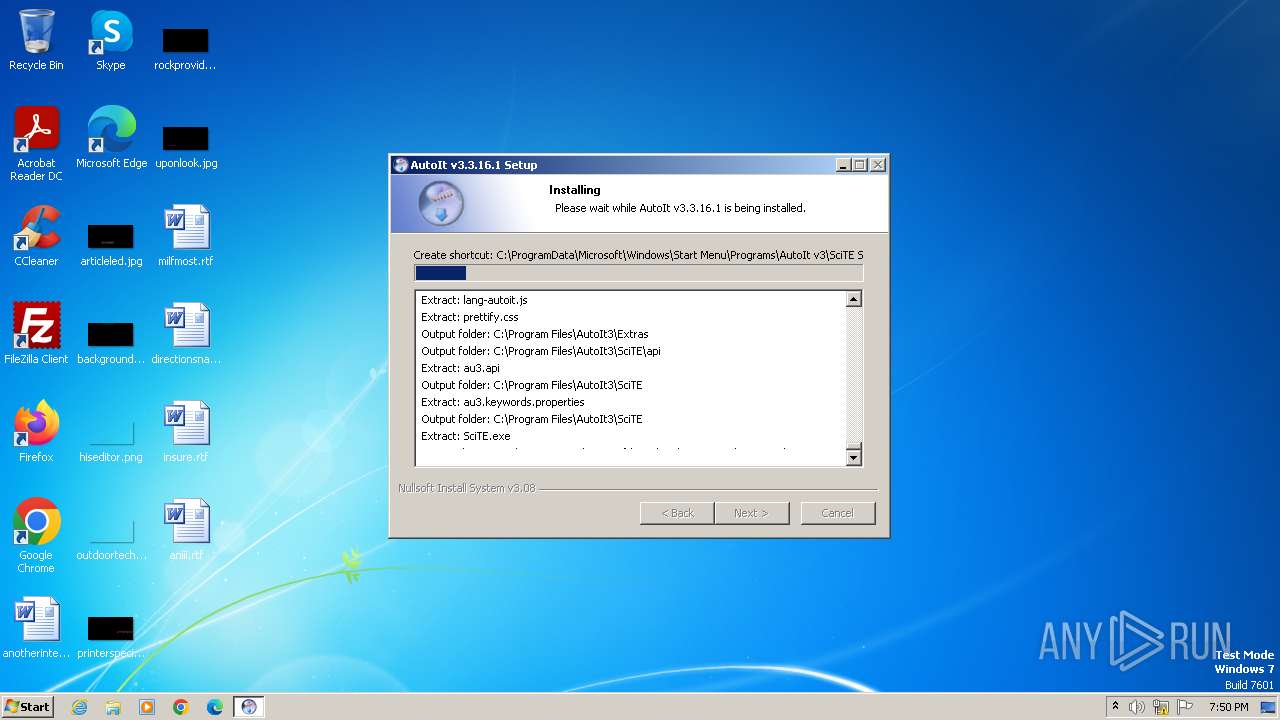
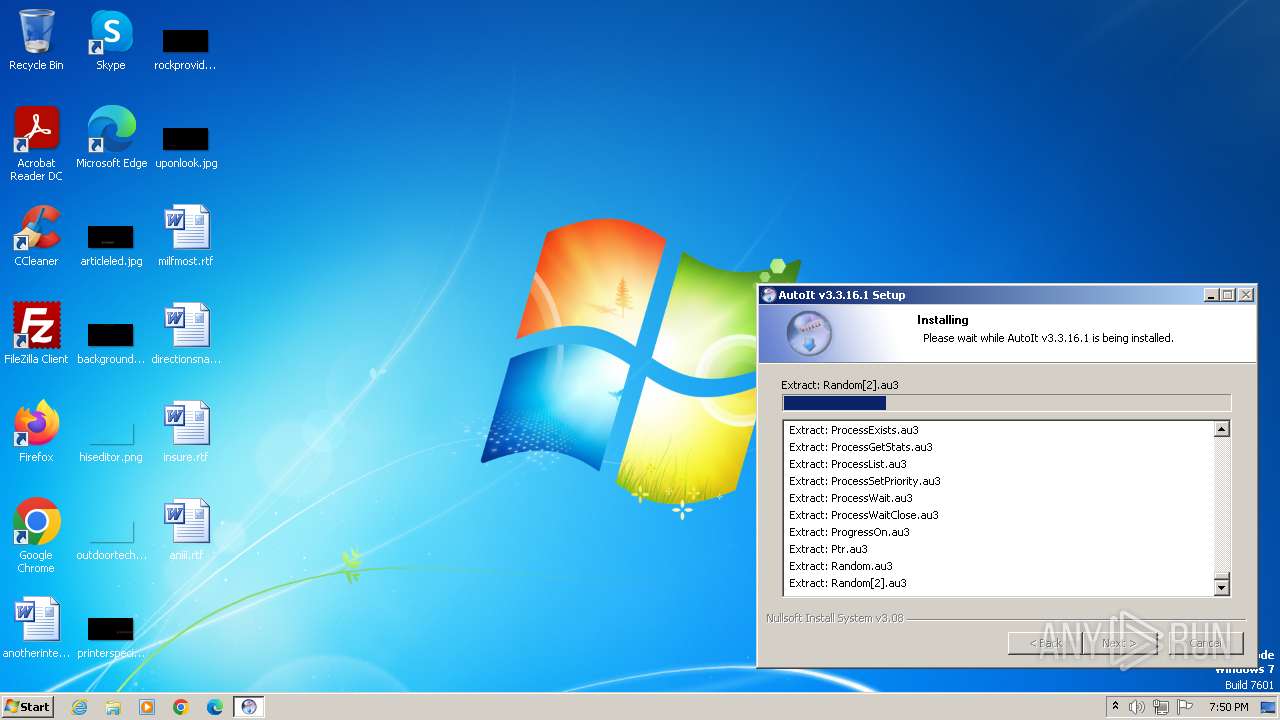
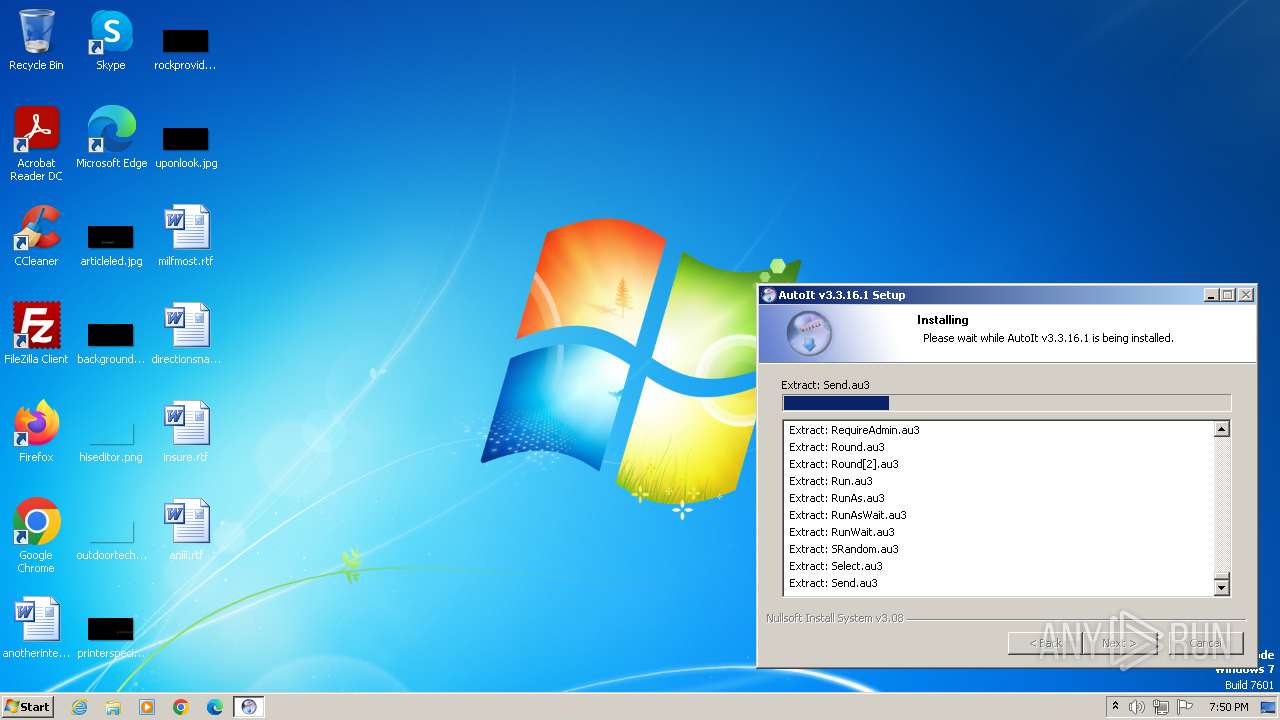
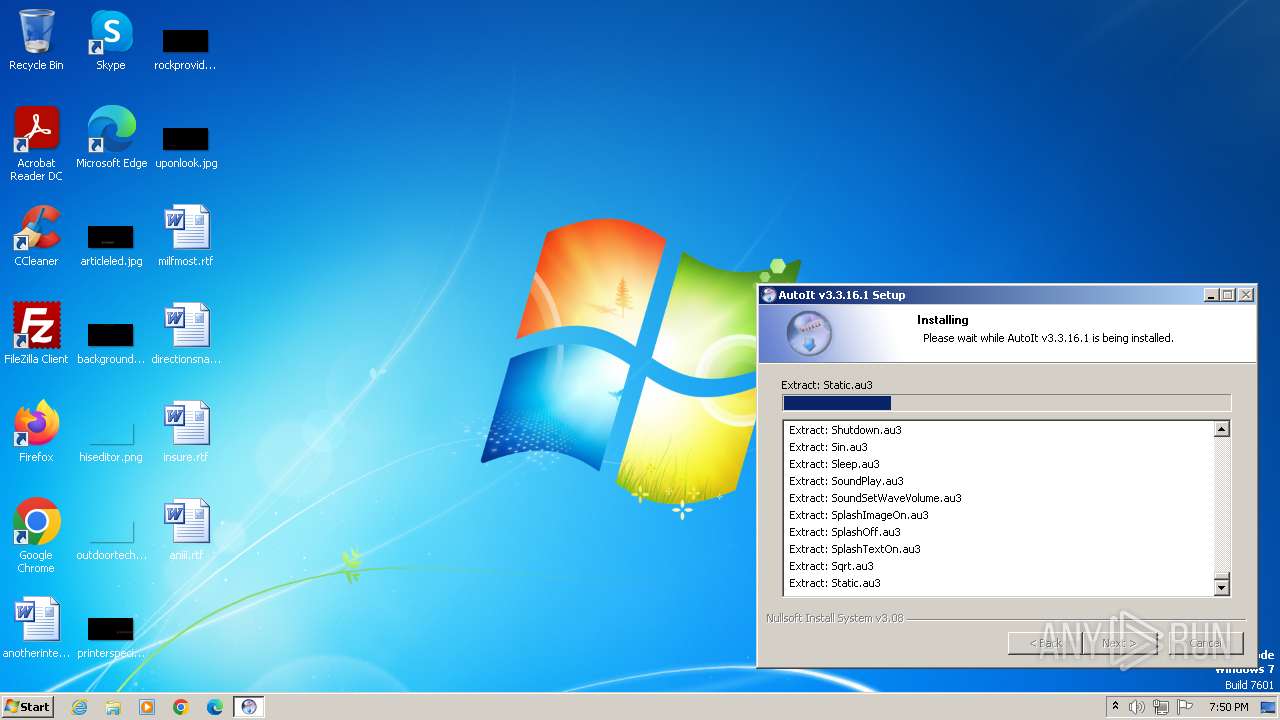
Drops the AutoIt3 executable file
- autoit-v3-setup.exe (PID: 3608)
The process creates files with name similar to system file names
- autoit-v3-setup.exe (PID: 3608)
Reads the Internet Settings
- hh.exe (PID: 4004)
Reads Microsoft Outlook installation path
- hh.exe (PID: 4004)
Reads Internet Explorer settings
- hh.exe (PID: 4004)
INFO
Checks supported languages
- autoit-v3-setup.exe (PID: 3608)
- wmpnscfg.exe (PID: 3680)
- AutoIt3.exe (PID: 3592)
Reads the computer name
- autoit-v3-setup.exe (PID: 3608)
- wmpnscfg.exe (PID: 3680)
- AutoIt3.exe (PID: 3592)
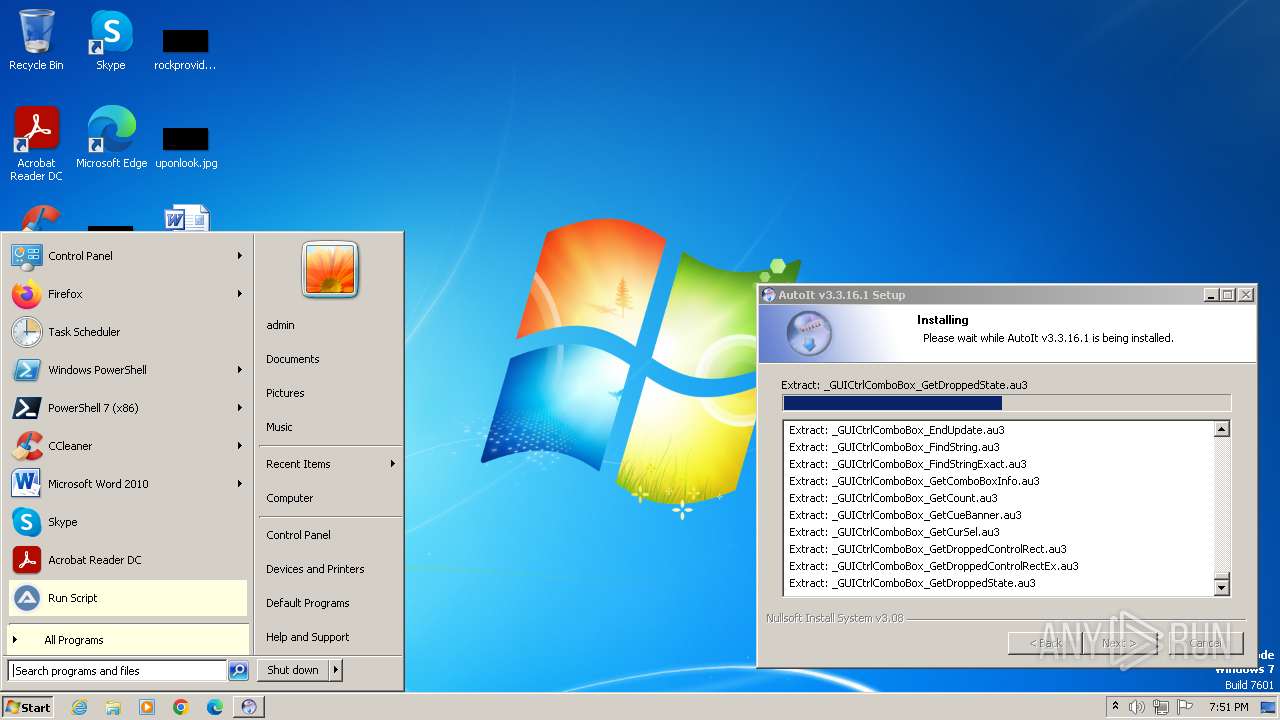
Create files in a temporary directory
- autoit-v3-setup.exe (PID: 3608)
- hh.exe (PID: 4004)
Creates files in the program directory
- autoit-v3-setup.exe (PID: 3608)
- hh.exe (PID: 4004)
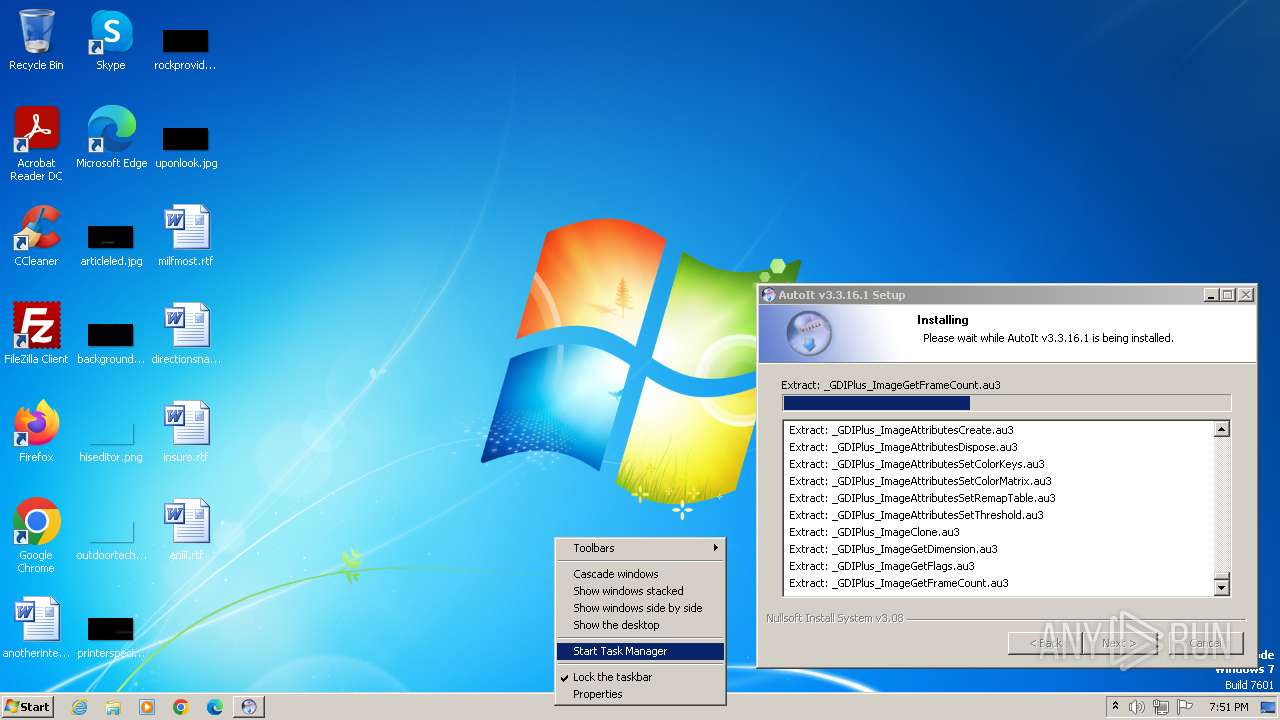
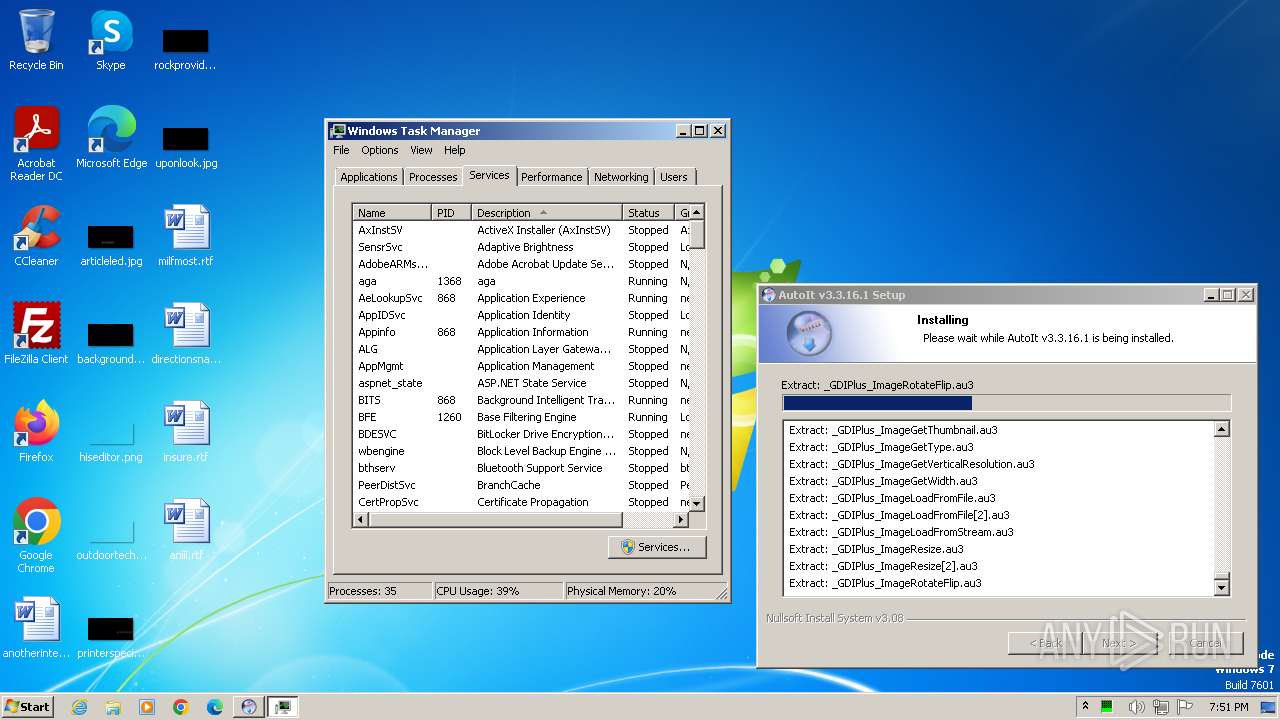
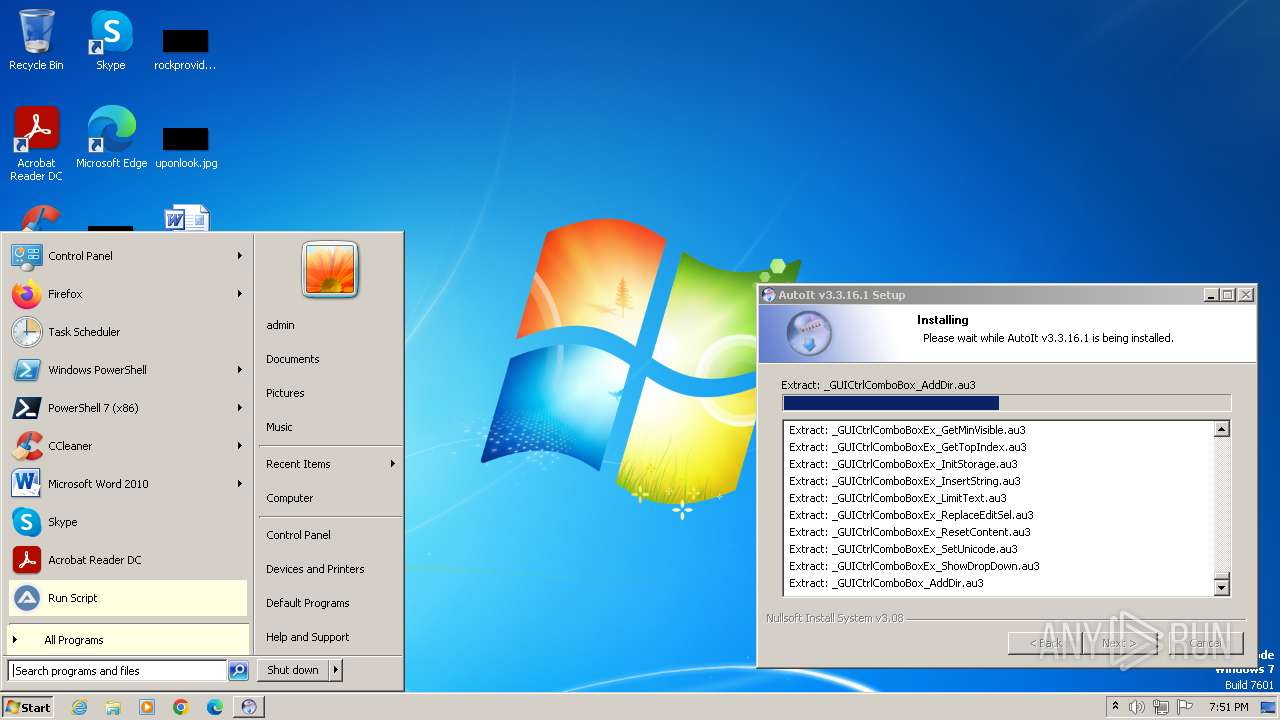
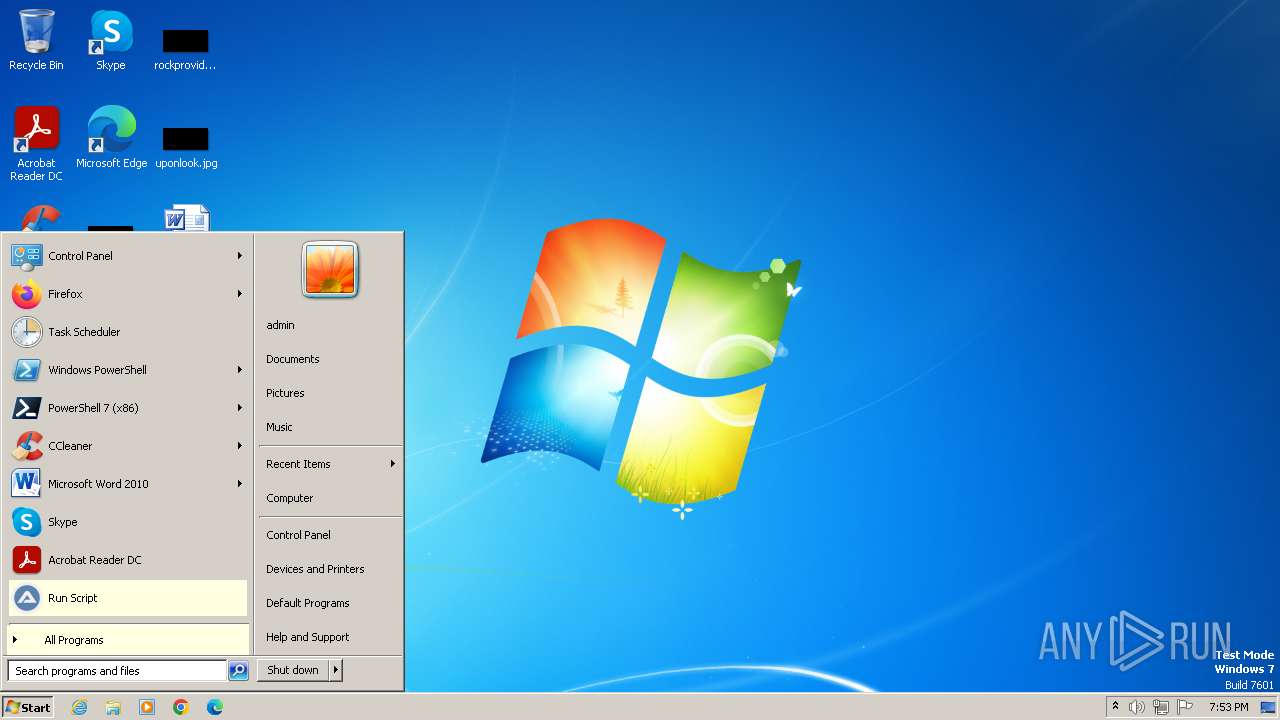
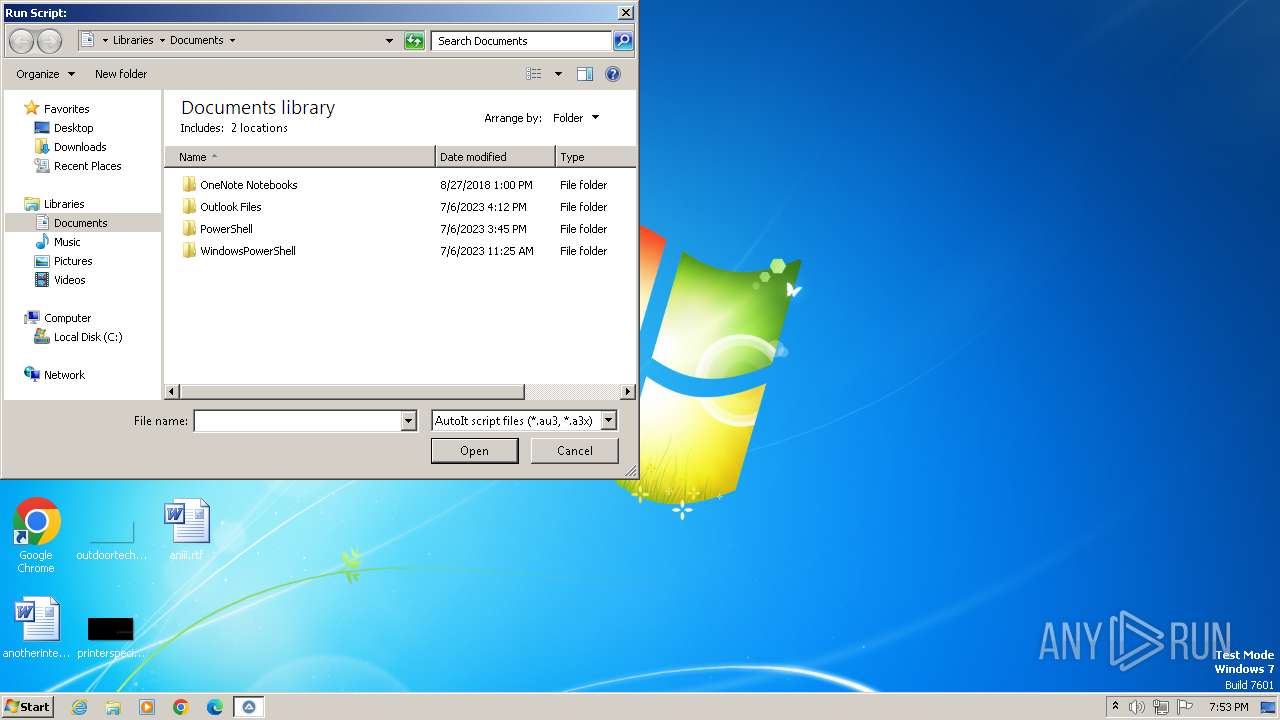
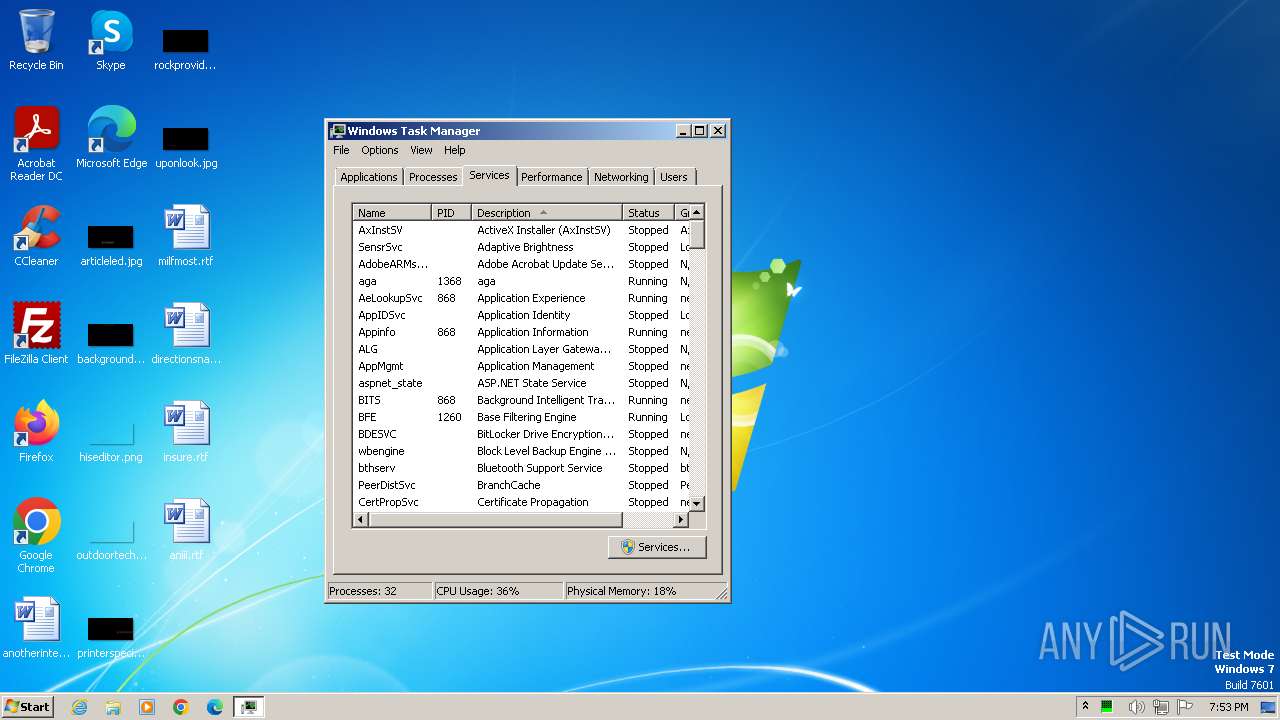
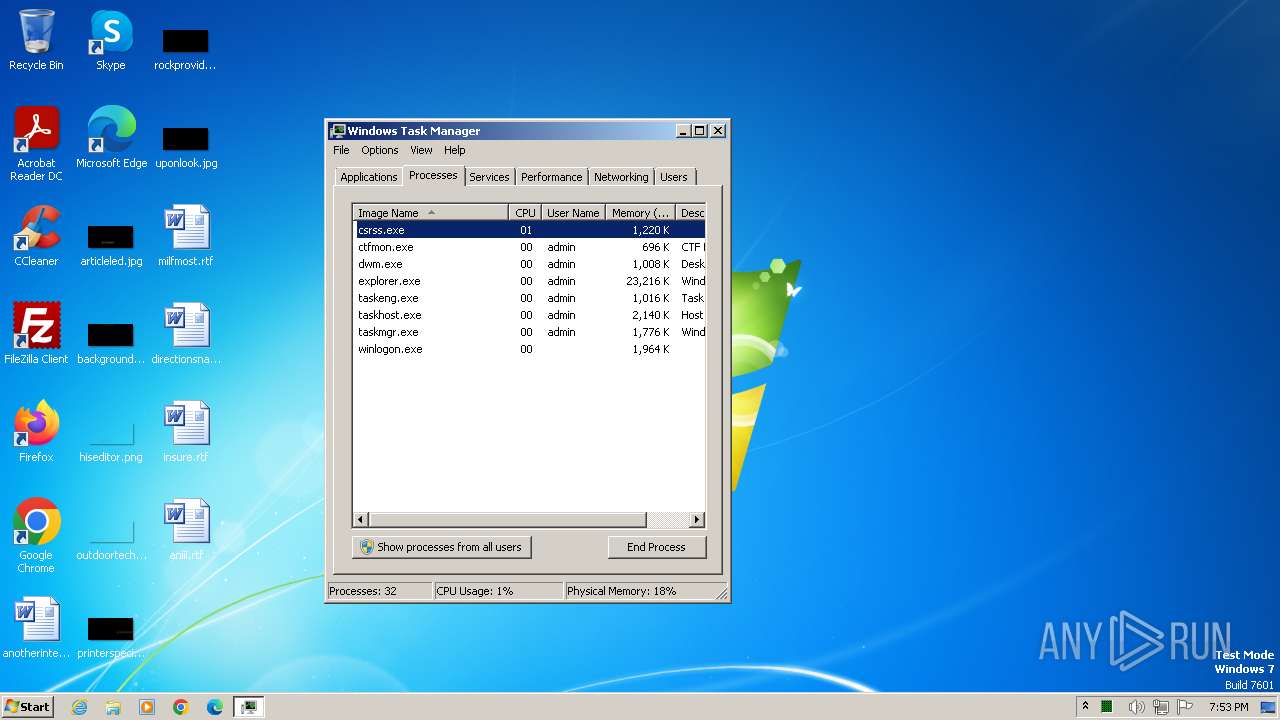
Manual execution by a user
- wmpnscfg.exe (PID: 3680)
- taskmgr.exe (PID: 3776)
- taskmgr.exe (PID: 2196)
- AutoIt3.exe (PID: 3592)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3680)
- hh.exe (PID: 4004)
- AutoIt3.exe (PID: 3592)
Checks proxy server information
- hh.exe (PID: 4004)
Creates files or folders in the user directory
- hh.exe (PID: 4004)
Reads mouse settings
- AutoIt3.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 23:56:47+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
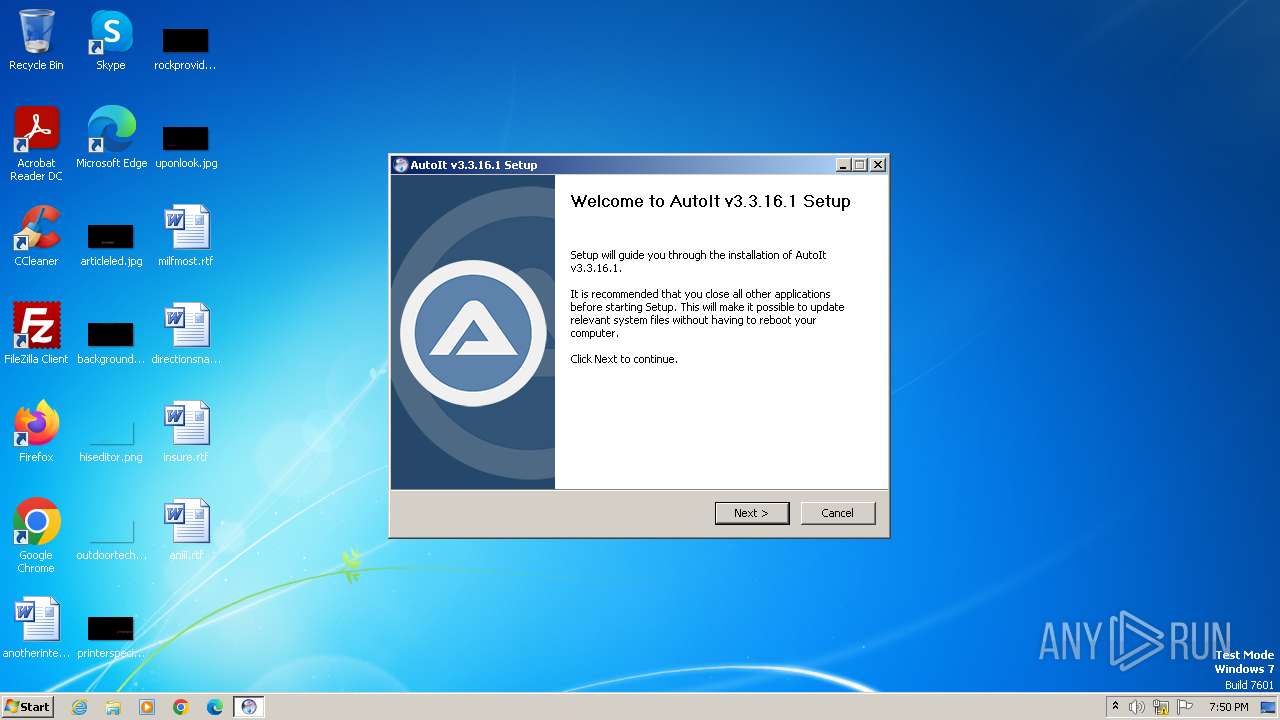
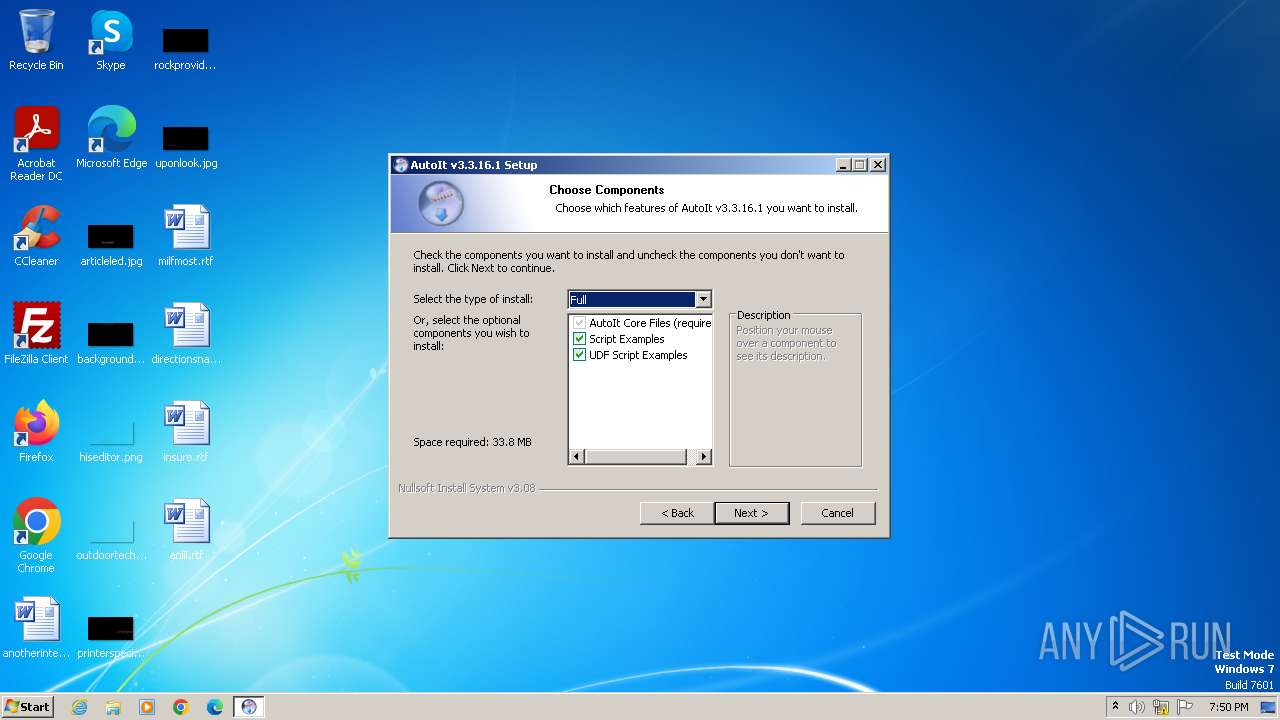
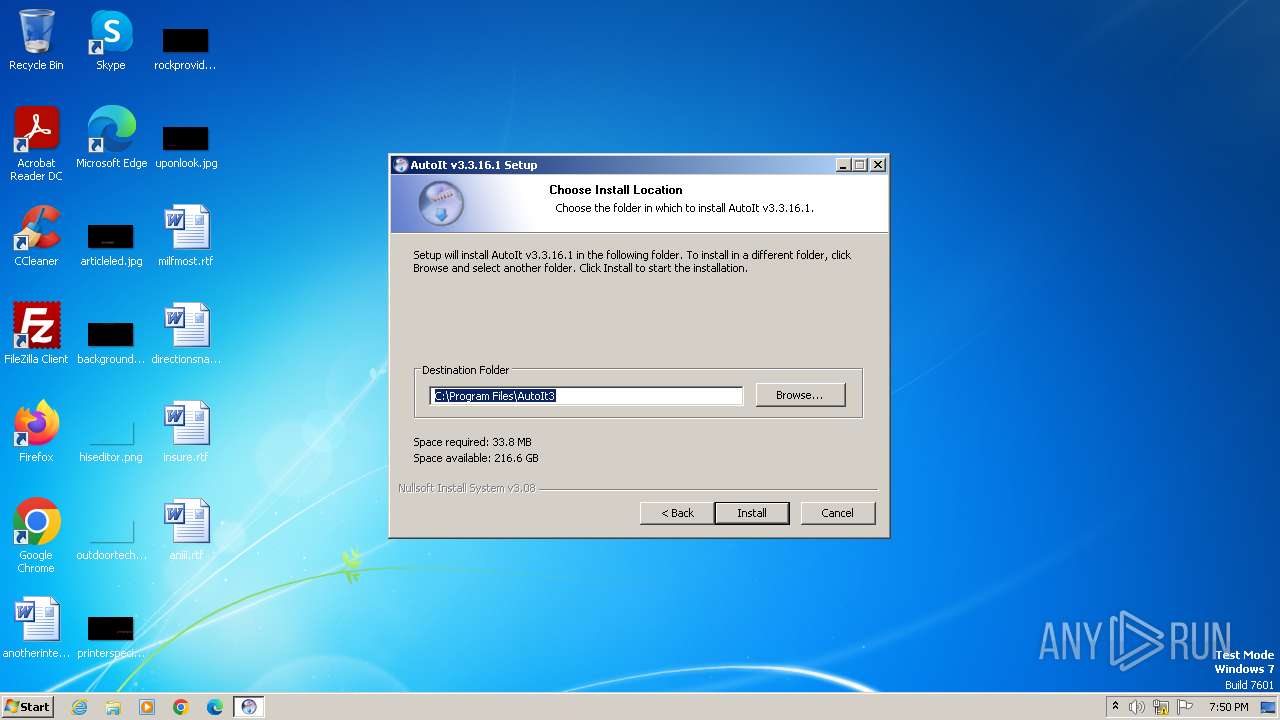
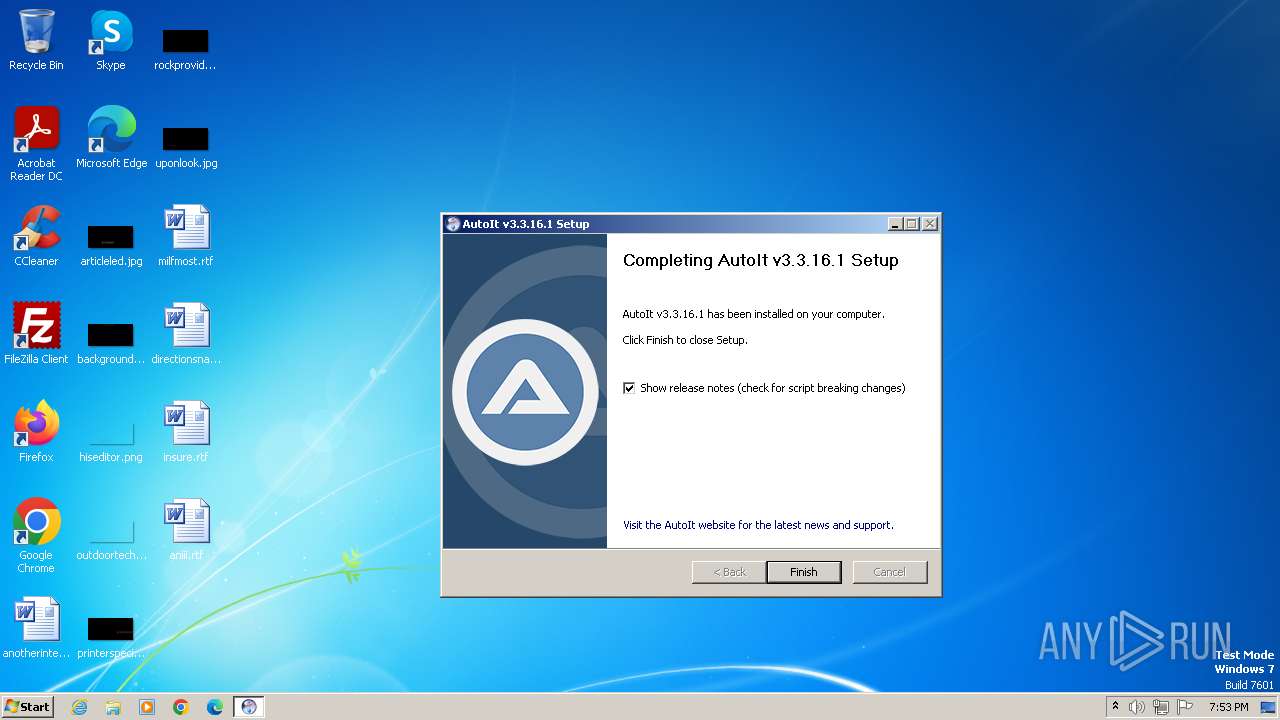
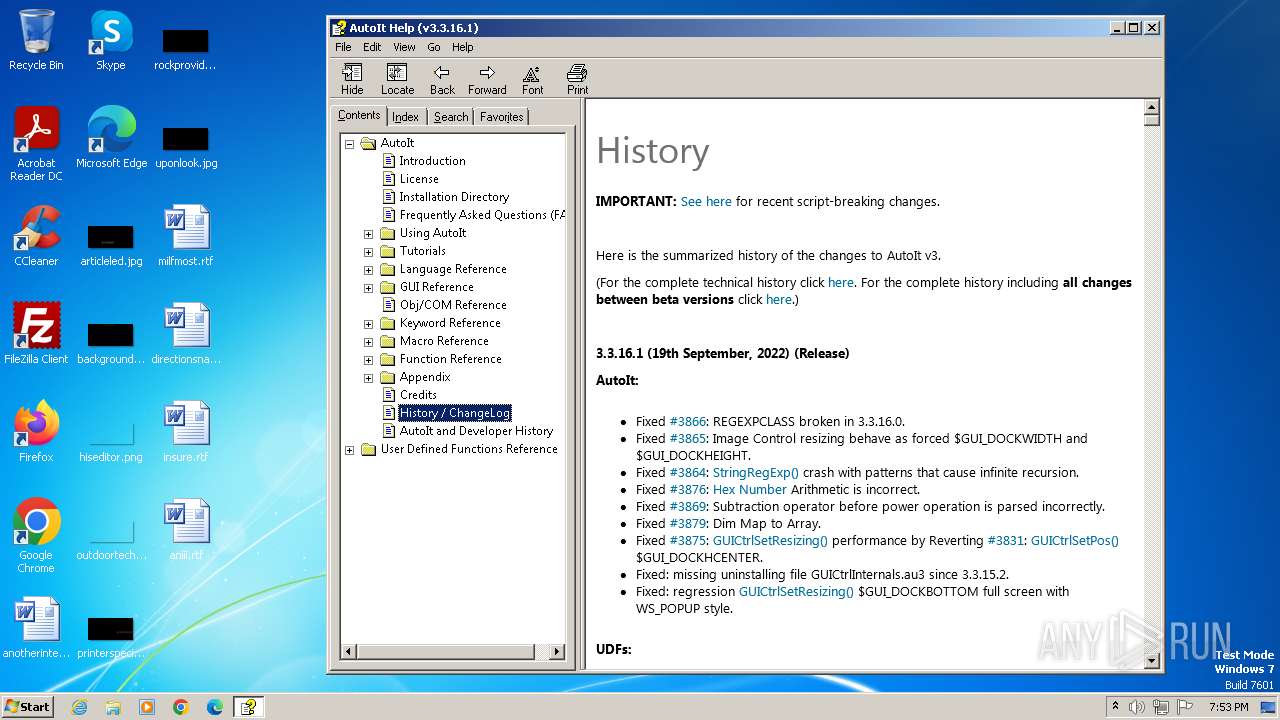
| FileVersionNumber: | 3.3.16.1 |
| ProductVersionNumber: | 3.3.16.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
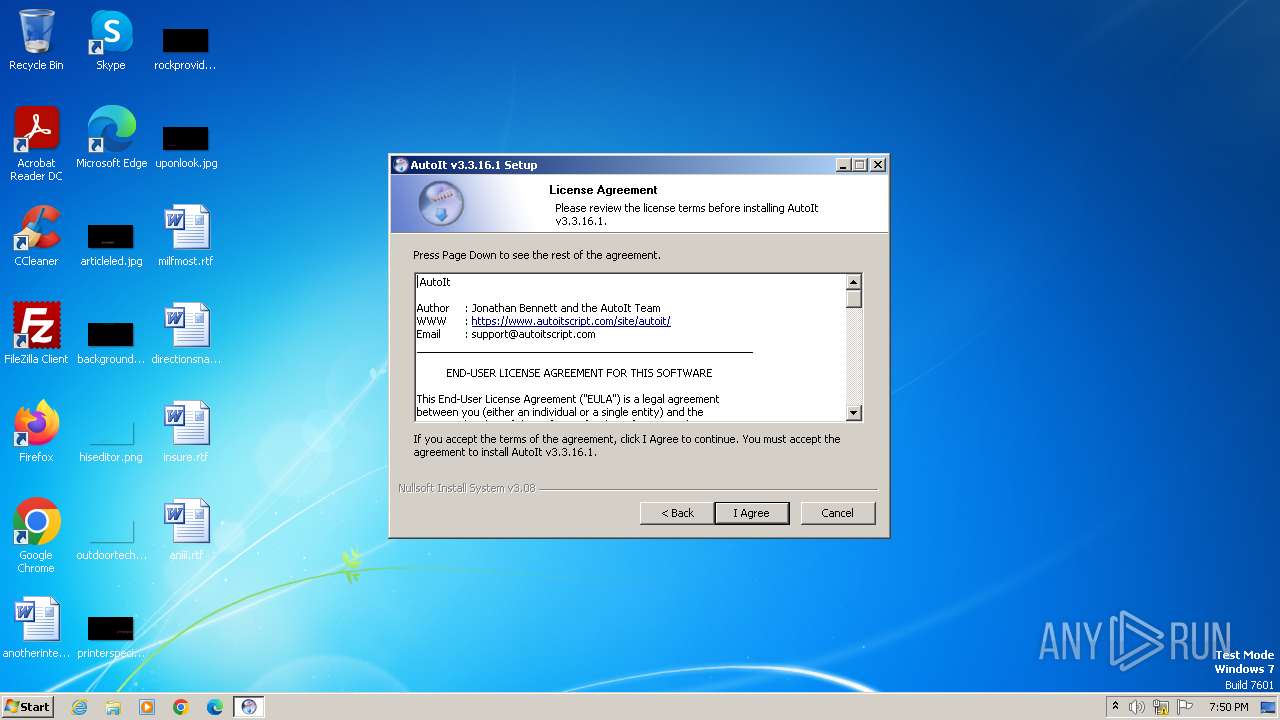
| CompanyName: | AutoIt Team |
| FileDescription: | AutoIt v3 Setup |
| FileVersion: | 3.3.16.1 |
| LegalCopyright: | @ 1999-2021 Jonathan Bennett & AutoIt Team |
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Setup Exit code: 3221226540 Version: 3.3.16.1 Modules
| |||||||||||||||
| 3592 | "C:\Program Files\AutoIt3\AutoIt3.exe" | C:\Program Files\AutoIt3\AutoIt3.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 1 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 3608 | "C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\autoit-v3-setup.exe | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Setup Exit code: 0 Version: 3.3.16.1 Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4004 | "C:\Windows\hh.exe" -mapid 1000 "C:\Program Files\AutoIt3\AutoIt.chm" | C:\Windows\hh.exe | — | autoit-v3-setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 849
Read events
6 807
Write events
38
Delete events
4
Modification events
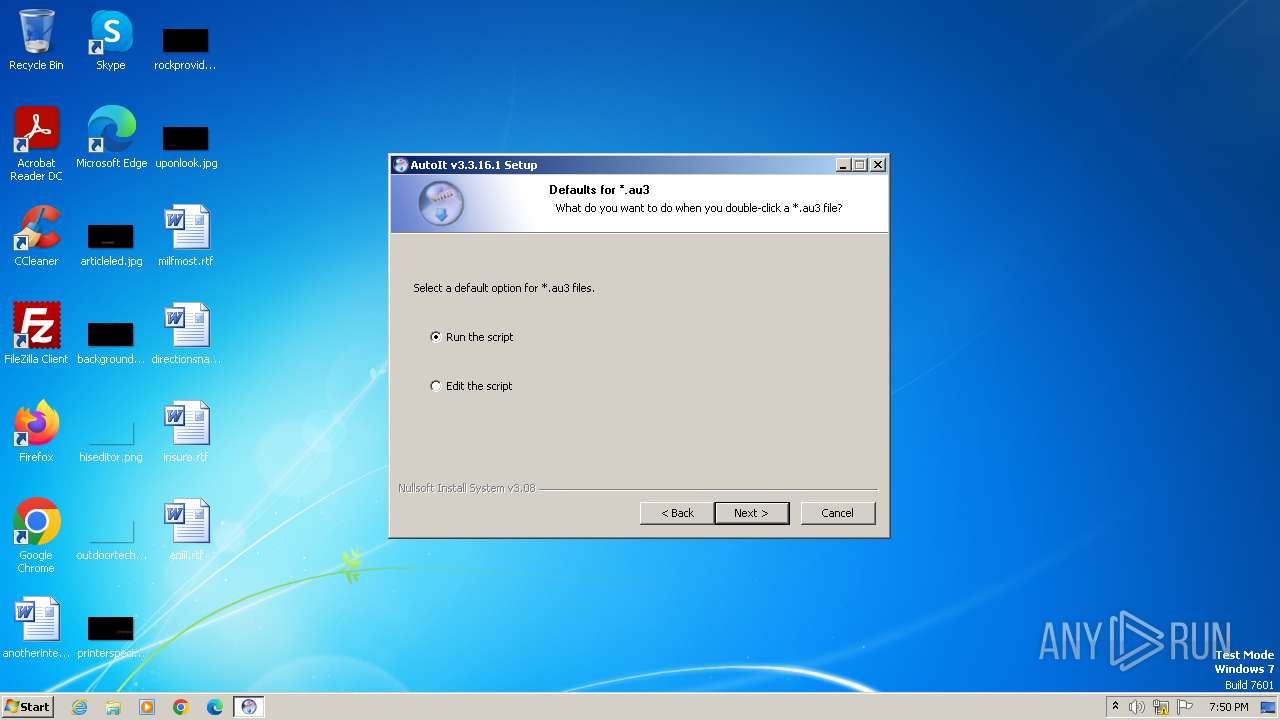
| (PID) Process: | (3608) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 115 | |||
| (PID) Process: | (3608) autoit-v3-setup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager\Environment |
| Operation: | write | Name: | PSModulePath |
Value: %SystemRoot%\system32\WindowsPowerShell\v1.0\Modules\ | |||
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{BAFD5861-CF0D-4B88-AAB7-181CF2966D7E}\{2BB51435-DBE2-4FD5-B569-D9713A803F5B} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{BAFD5861-CF0D-4B88-AAB7-181CF2966D7E} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3680) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{2E2F7D1A-E7F4-4F6A-BC81-196768759206} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3776) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (3776) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004401000076000000DC0200005C0200000200000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF02000000FFFFFFFF4F00000028000000970000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (4004) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4004) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4004) hh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
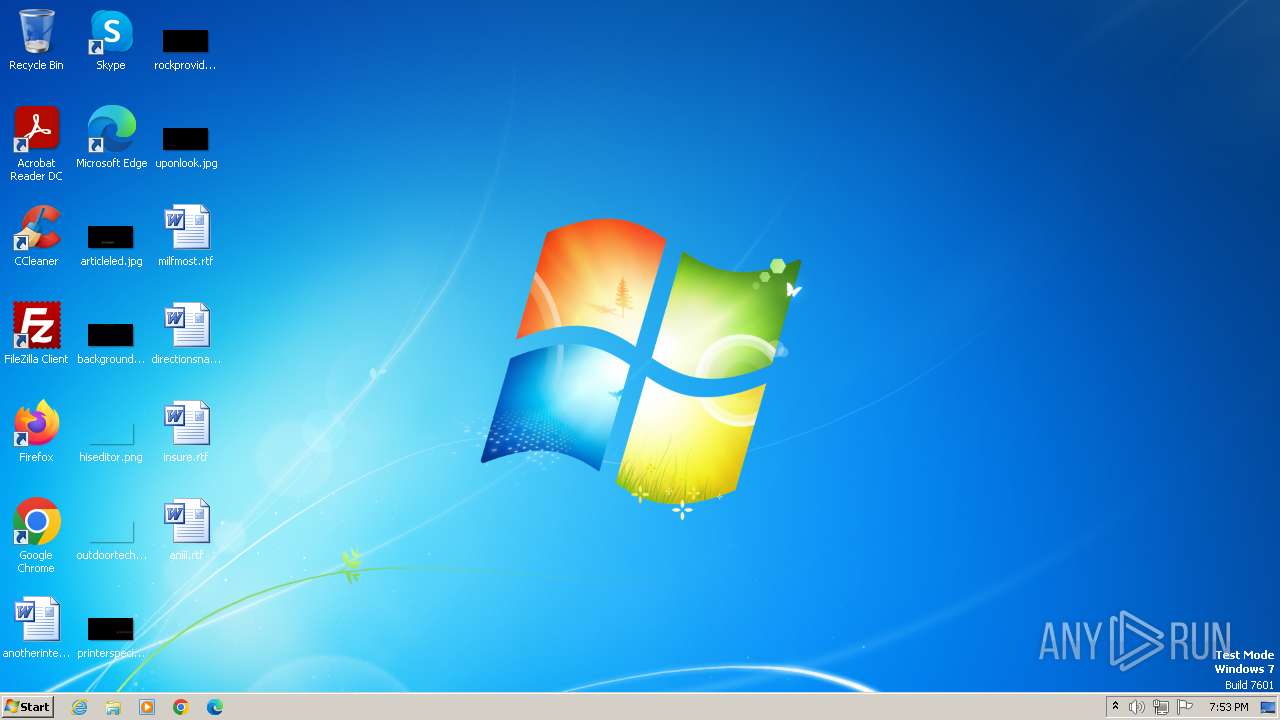
Executable files
24
Suspicious files
42
Text files
2 830
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt.chm | — | |
MD5:— | SHA256:— | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\ioPreviousVersion.ini | text | |
MD5:8C032D104411DA01E43D8E8B9AD88EB4 | SHA256:659CAD01FE631A96E0856C44D4114E12AC0E5402F863C2B1213A87D375C26F59 | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\ioDefaultOpen.ini | text | |
MD5:8C032D104411DA01E43D8E8B9AD88EB4 | SHA256:659CAD01FE631A96E0856C44D4114E12AC0E5402F863C2B1213A87D375C26F59 | |||
| 3608 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\Au3Info_x64.exe | executable | |
MD5:3026C30FFE9201A5B6164A64988E55FC | SHA256:3DDD9BAAD088D3ABEA6AC26C19E957AAE9CB9E47101CDEC8115188ED0092B7E0 | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\modern-wizard.bmp | image | |
MD5:6930F12EAC110EF91B3F05EBF1BD461D | SHA256:5DDC4D595B497247847B29E9E60AA496E0F13B220D80FAA3241CFC6F44CE570D | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\modern-header.bmp | image | |
MD5:940C56737BF9BB69CE7A31C623D4E87A | SHA256:766A893FE962AEFD27C574CB05F25CF895D3FC70A00DB5A6FA73D573F571AEFC | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\UserInfo.dll | executable | |
MD5:2F69AFA9D17A5245EC9B5BB03D56F63C | SHA256:E54989D2B83E7282D0BEC56B098635146AAB5D5A283F1F89486816851EF885A0 | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\ioX64Options.ini | text | |
MD5:B7DAECFA83B6DB257578441991630153 | SHA256:244F61A89801AB52A66E7579C16D92A6A60E063F8F972F601FF0EE2BC73AE0B2 | |||
| 3608 | autoit-v3-setup.exe | C:\Users\admin\AppData\Local\Temp\nsn7EDB.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 3608 | autoit-v3-setup.exe | C:\Program Files\AutoIt3\AutoIt v3 Website.url | text | |
MD5:7B6871AD1DE81E0201386EEB8A71498F | SHA256:A8697C79934FF08407412D2C0C0492217709841638F1FD7FC6D8A68C105EED0B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | — | Akamai International B.V. | NL | unknown |
868 | svchost.exe | 88.221.124.138:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |
dns.msftncsi.com |
| shared |