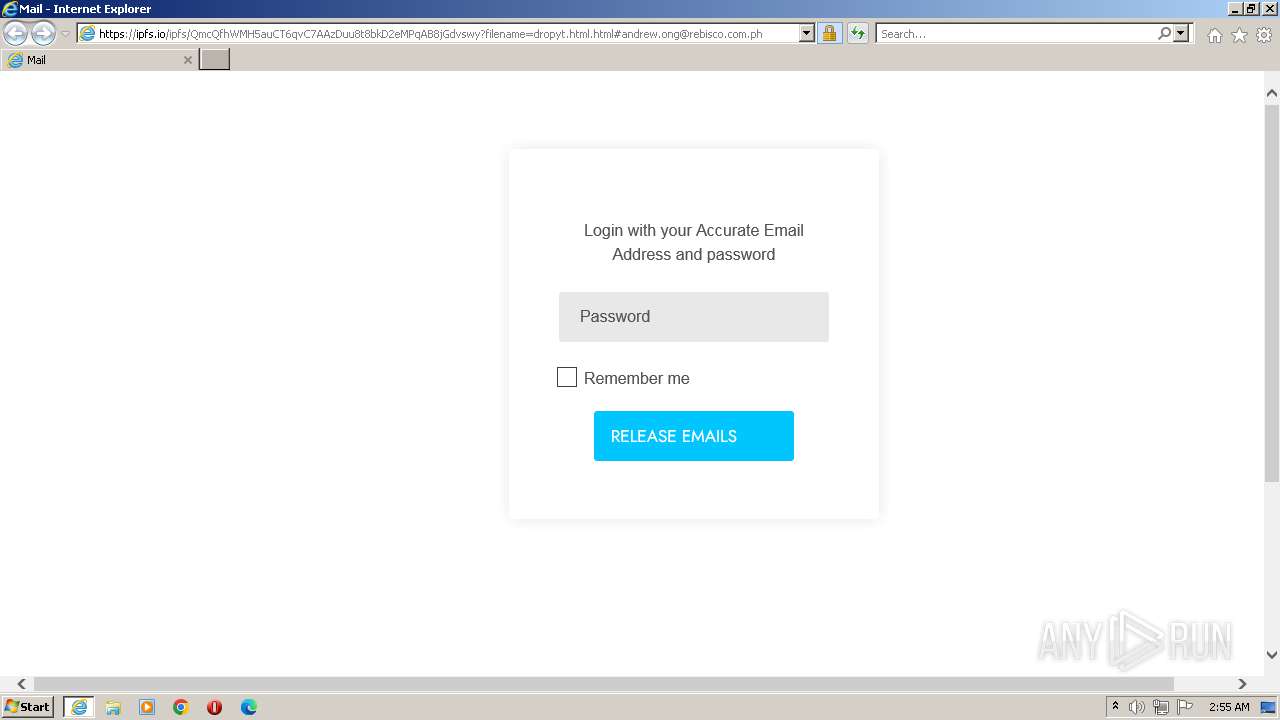
| URL: | https://ipfs.io/ipfs/QmcQfhWMH5auCT6qvC7AAzDuu8t8bkD2eMPqAB8jGdvswy?filename=dropyt.html.html#andrew.ong@rebisco.com.ph |
| Full analysis: | https://app.any.run/tasks/269b63be-5b91-42f4-a6f7-b683a04fb208 |
| Verdict: | Malicious activity |
| Analysis date: | September 20, 2023, 01:55:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B2256AF115FBE67A453388307CD96286 |
| SHA1: | 8CBE43B9F22478ED3EC61B718281C35071BF7A99 |
| SHA256: | 19EF698D2A92F151790E74C0A52D06E67FA440C58B9E2D6EA9876A671EA9E1EF |
| SSDEEP: | 3:N8/KIX7QGFkJFRHOQJkndKaAsgwh0GEtKUi4TLn:2/3LQxRHON+GEtE4TLn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ipfs.io/ipfs/QmcQfhWMH5auCT6qvC7AAzDuu8t8bkD2eMPqAB8jGdvswy?filename=dropyt.html.html#andrew.ong@rebisco.com.ph" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2220 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 041
Read events
13 970
Write events
69
Delete events
2
Modification events
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA04F.tmp | cat | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B3FDE6E144B6249D1223DE772944F43C | SHA256:CCD916E91362C9AF0E0624BF6E46B5411791479054E29DEB56B2B397CC9825DE | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\bootstrap.min[1].css | text | |
MD5:450FC463B8B1A349DF717056FBB3E078 | SHA256:2C0F3DCFE93D7E380C290FE4AB838ED8CADFF1596D62697F5444BE460D1F876D | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:86F862172FEFB0F21DED7150C4934B30 | SHA256:429E05474EE0C41798EC24AD31BEEB8D03F8A5507AF287C86CC712F016D3F25F | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA04E.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dropyt.html[1].html | html | |
MD5:296FF0489E1B9CA5403E907103A56A40 | SHA256:8A4C7E0D4403C5EB3B16992226C3931F06F99051C2CEEC373C0881C256160E8D | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:9615DC4673A55052DE405358FB3D69C4 | SHA256:3031742B024211E76B092BB33D71FE52E89B1C14157494D9B1BBD25C0265C43A | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:24BE8A92460B5B7A555B1DA559296958 | SHA256:77A3CFE6B7EB676AF438D5DE88C7EFCB6ABCC494E0B65DA90201969E6D79B2A3 | |||
| 2372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
51
DNS requests
21
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?49361a3f17fc7612 | unknown | compressed | 4.66 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | der | 717 b | unknown |
2372 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?99509caa2b0d3cd9 | unknown | compressed | 4.66 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?de7631ecb9c6cb08 | unknown | compressed | 61.6 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?84ad23b6f0f61de4 | unknown | compressed | 61.6 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | der | 471 b | unknown |
2372 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | der | 1.47 Kb | unknown |
2372 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGtoBrErbly1Eg67e808s0k%3D | unknown | der | 471 b | unknown |
2372 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | der | 1.41 Kb | unknown |
2220 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | unknown | der | 1.47 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2372 | iexplore.exe | 209.94.90.1:443 | ipfs.io | PROTOCOL | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2372 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
2372 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
2372 | iexplore.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
2372 | iexplore.exe | 104.16.87.20:443 | cdn.jsdelivr.net | CLOUDFLARENET | — | shared |
2372 | iexplore.exe | 142.250.187.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2372 | iexplore.exe | 185.15.59.240:443 | upload.wikimedia.org | WIKIMEDIA | US | unknown |
2372 | iexplore.exe | 151.101.194.137:443 | code.jquery.com | FASTLY | US | unknown |
2372 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipfs.io |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET INFO Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
2372 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |
2372 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |
2220 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |
2220 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |