| File name: | psiphon3.exe |
| Full analysis: | https://app.any.run/tasks/47de1fd1-c517-4211-8db1-fb13120db70c |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2025, 21:37:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | 571A5BCF956C66EC785A191B4816367D |
| SHA1: | 728BB195FC49EC14D259B6934617CEABC2EE567D |
| SHA256: | 19EB6685DC45C426865297FD2130976F55E0E9E5A3687EA692D0C3047CD370E6 |
| SSDEEP: | 98304:LnW9gjQiYWWyKWv35T3dZ02xoYEf9wEF7Sa8nWpWX/ipuPy0EcM8i2wCKtC029uu:SKX6x6hYgYD1I+n8go2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- psiphon3.exe (PID: 2356)
Reads security settings of Internet Explorer
- psiphon3.exe (PID: 2356)
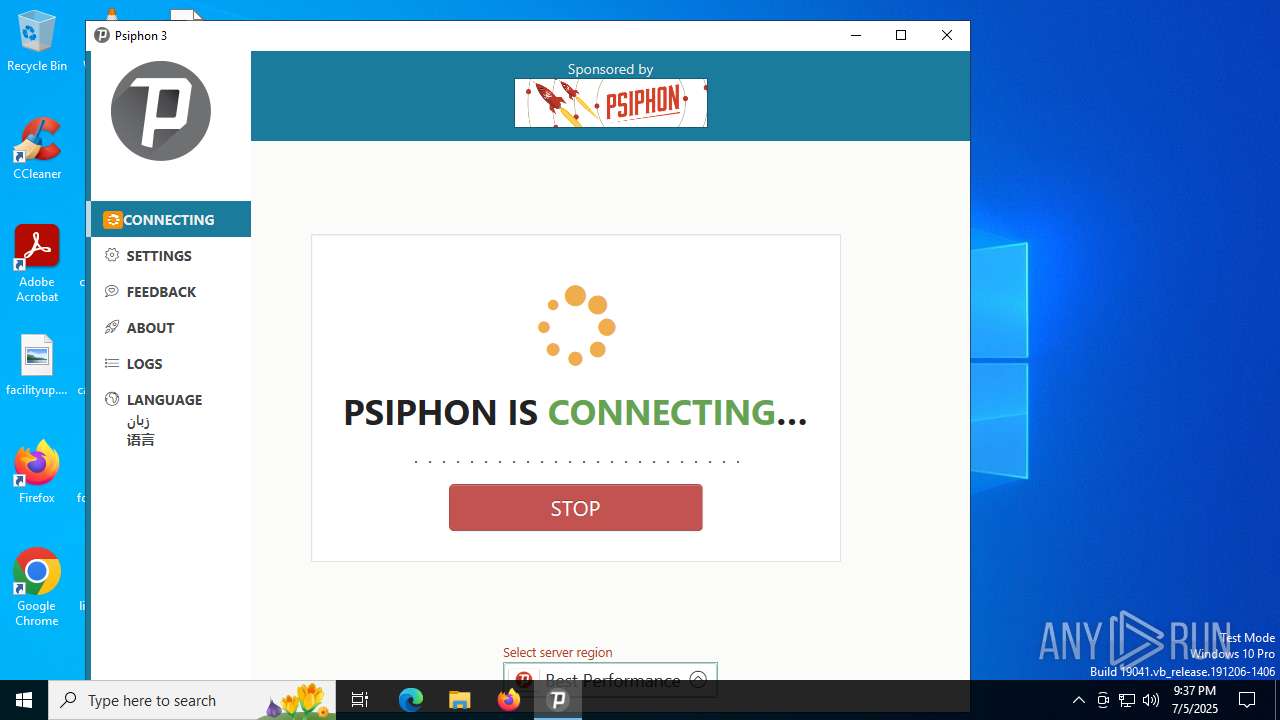
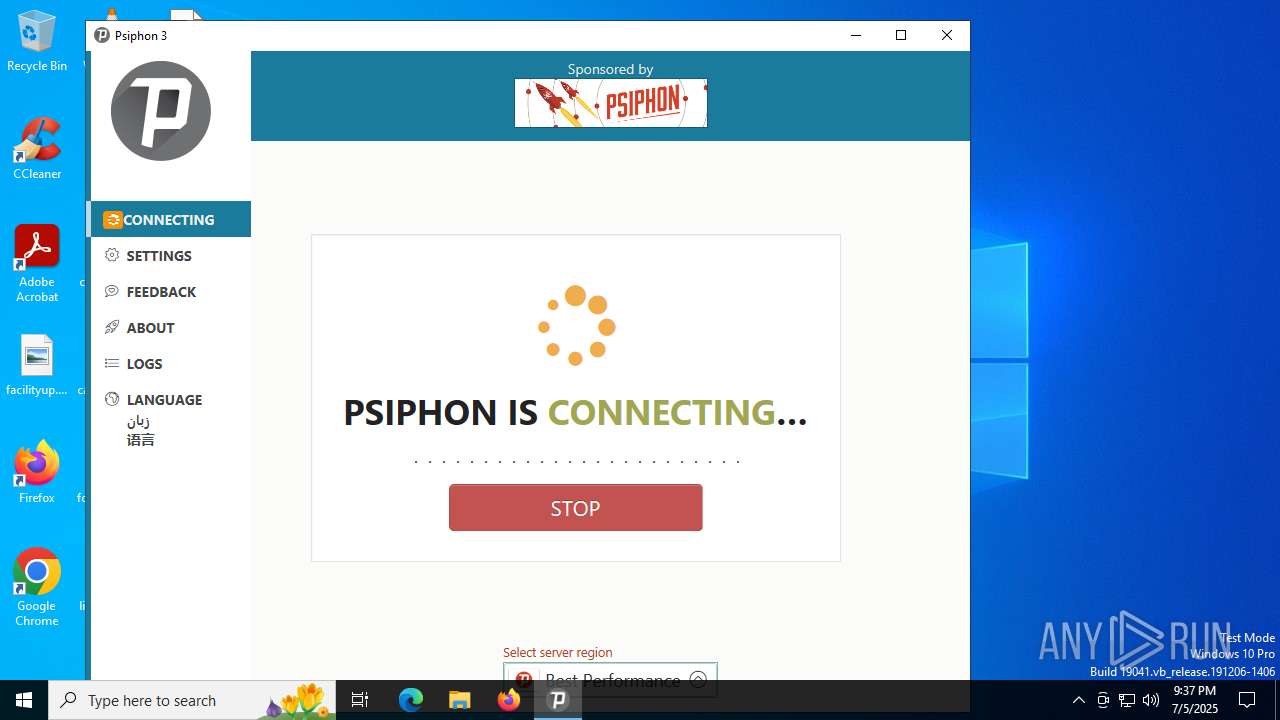
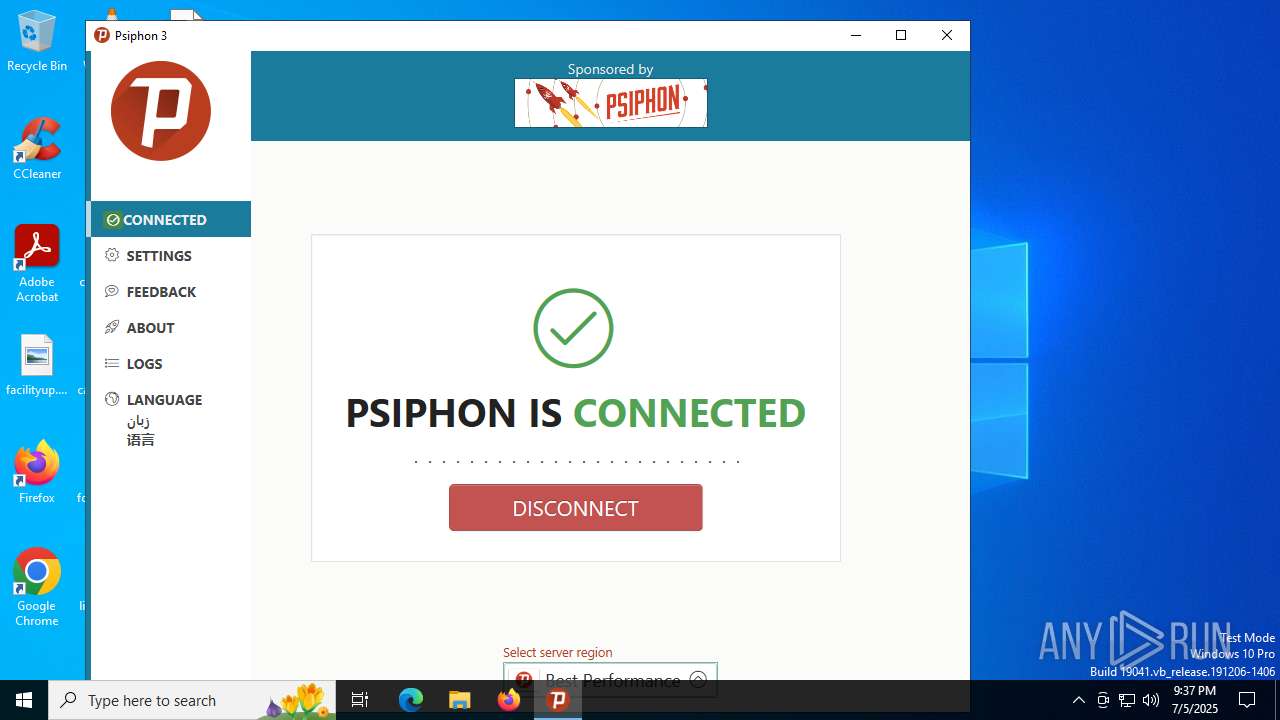
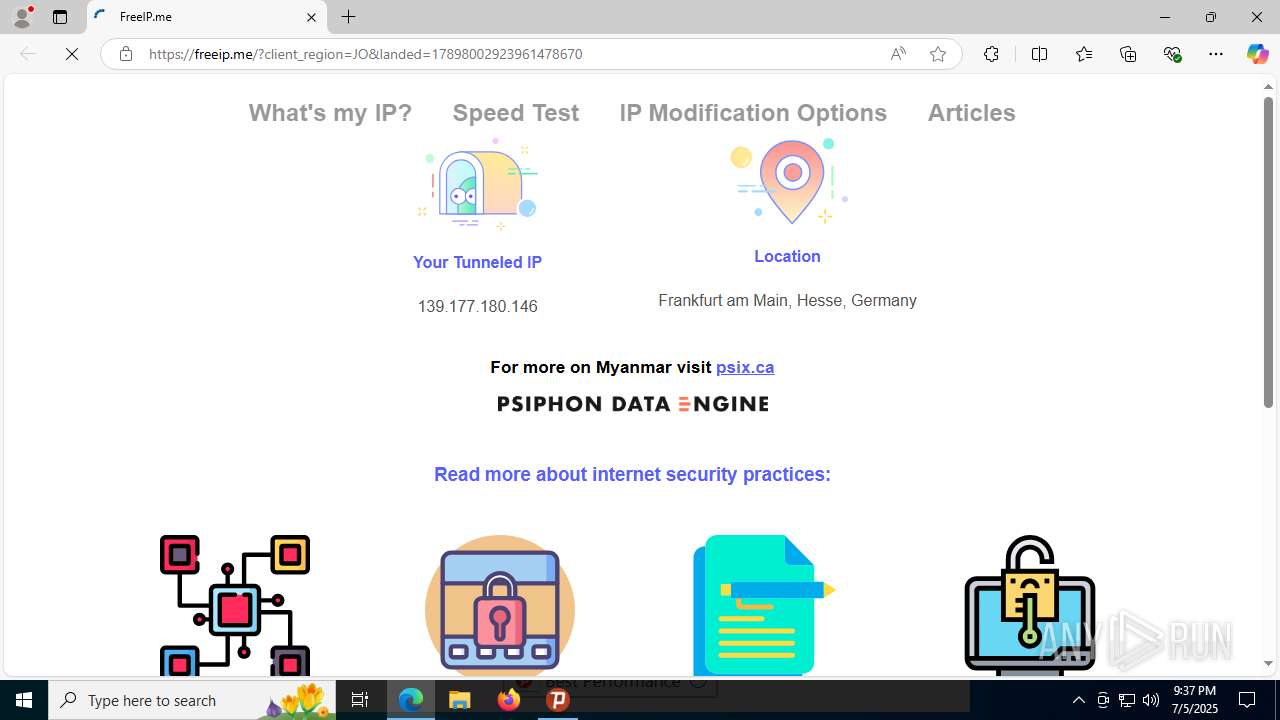
Psiphon VPN has been detected
- psiphon3.exe (PID: 2356)
Executable content was dropped or overwritten
- psiphon3.exe (PID: 2356)
Reads Internet Explorer settings
- psiphon3.exe (PID: 2356)
Connects to unusual port
- psiphon-tunnel-core.exe (PID: 4572)
Connects to SSH
- psiphon-tunnel-core.exe (PID: 4572)
There is functionality for taking screenshot (YARA)
- psiphon3.exe (PID: 2356)
Connects to the server without a host name
- psiphon-tunnel-core.exe (PID: 4572)
Psiphon VPN server synchronization mutex
- psiphon3.exe (PID: 2356)
INFO
Reads the computer name
- psiphon3.exe (PID: 2356)
- psiphon-tunnel-core.exe (PID: 4572)
- identity_helper.exe (PID: 7428)
Checks supported languages
- psiphon3.exe (PID: 2356)
- psiphon-tunnel-core.exe (PID: 4572)
- identity_helper.exe (PID: 7428)
Disables trace logs
- psiphon3.exe (PID: 2356)
Creates files or folders in the user directory
- psiphon3.exe (PID: 2356)
- psiphon-tunnel-core.exe (PID: 4572)
Create files in a temporary directory
- psiphon3.exe (PID: 2356)
Checks proxy server information
- psiphon3.exe (PID: 2356)
- slui.exe (PID: 7900)
Detects GO elliptic curve encryption (YARA)
- psiphon3.exe (PID: 2356)
- psiphon-tunnel-core.exe (PID: 4572)
Application based on Golang
- psiphon3.exe (PID: 2356)
- psiphon-tunnel-core.exe (PID: 4572)
UPX packer has been detected
- psiphon3.exe (PID: 2356)
Application launched itself
- msedge.exe (PID: 4684)
- msedge.exe (PID: 1156)
Reads the software policy settings
- slui.exe (PID: 7900)
- psiphon3.exe (PID: 2356)
Reads Environment values
- identity_helper.exe (PID: 7428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (40) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (26) |
| .exe | | | Win32 EXE Yoda's Crypter (25.6) |
| .exe | | | Win32 Executable (generic) (4.3) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:25 14:09:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 10305536 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 20840448 |
| EntryPoint: | 0x1db2490 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
161
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2692,i,17889959471652366791,11884440529737306163,262144 --variations-seed-version --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
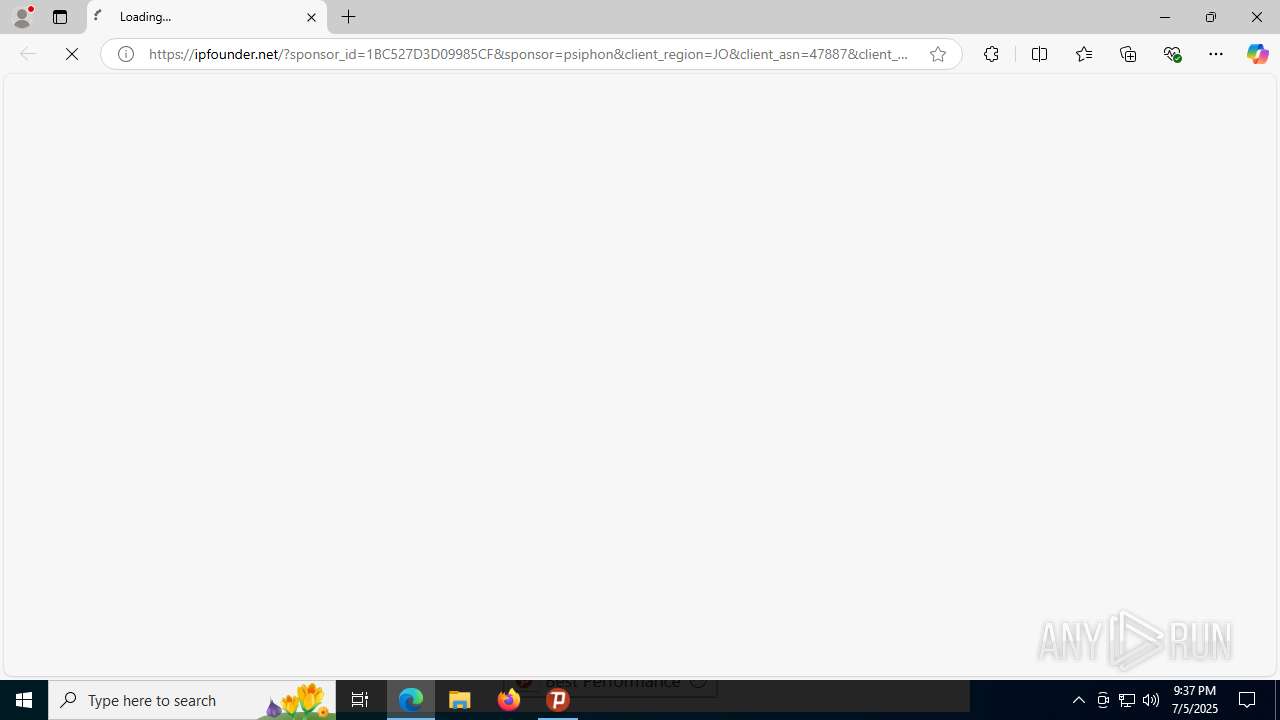
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument https://ipfounder.net/?sponsor_id=1BC527D3D09985CF&sponsor=psiphon&client_region=JO&client_asn=47887&client_platform=windows&secret=580EfjEI29xL3hoyU6dgP4vSEVxdcGI7JDFkxgjds7PHulSEF0wmORpvzbqxyTwYtpowsY4xMFnfWEnTghe6l8jiV9K5QSZoir2i6fDeKJD6EhL6DkoYTEMu2EE9YJvy3LdCUZ7ncdVC6ipgWx06wznvDLbY1ajfcfRGCpfsQJei2q6tb0GSFh1QK3x3qXKwyjmNPc5J&psireason=connect&psicash=eyJtZXRhZGF0YSI6eyJjbGllbnRfcmVnaW9uIjoiSk8iLCJjbGllbnRfdmVyc2lvbiI6IjE4NiIsInByb3BhZ2F0aW9uX2NoYW5uZWxfaWQiOiI5MkFBQ0M1QkFCRTA5NDRDIiwic3BvbnNvcl9pZCI6IjFCQzUyN0QzRDA5OTg1Q0YiLCJ1c2VyX2FnZW50IjoiUHNpcGhvbi1Qc2lDYXNoLVdpbmRvd3MiLCJ2IjoxfSwidGltZXN0YW1wIjoiMjAyNS0wNy0wNVQyMTozNzoyOC4zMTBaIiwidG9rZW5zIjpudWxsLCJ2IjoxfQ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2280,i,17889959471652366791,11884440529737306163,262144 --variations-seed-version --mojo-platform-channel-handle=2268 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\Desktop\psiphon3.exe" | C:\Users\admin\Desktop\psiphon3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3584 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4268,i,17889959471652366791,11884440529737306163,262144 --variations-seed-version --mojo-platform-channel-handle=4224 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3596,i,17889959471652366791,11884440529737306163,262144 --variations-seed-version --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4572 | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe --config "C:\Users\admin\AppData\Local\Psiphon3\psiphon.config" --serverList "C:\Users\admin\AppData\Local\Psiphon3\server_list.dat" | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | psiphon3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://ipfounder.net/?sponsor_id=1BC527D3D09985CF&sponsor=psiphon&client_region=JO&client_asn=47887&client_platform=windows&secret=580EfjEI29xL3hoyU6dgP4vSEVxdcGI7JDFkxgjds7PHulSEF0wmORpvzbqxyTwYtpowsY4xMFnfWEnTghe6l8jiV9K5QSZoir2i6fDeKJD6EhL6DkoYTEMu2EE9YJvy3LdCUZ7ncdVC6ipgWx06wznvDLbY1ajfcfRGCpfsQJei2q6tb0GSFh1QK3x3qXKwyjmNPc5J&psireason=connect&psicash=eyJtZXRhZGF0YSI6eyJjbGllbnRfcmVnaW9uIjoiSk8iLCJjbGllbnRfdmVyc2lvbiI6IjE4NiIsInByb3BhZ2F0aW9uX2NoYW5uZWxfaWQiOiI5MkFBQ0M1QkFCRTA5NDRDIiwic3BvbnNvcl9pZCI6IjFCQzUyN0QzRDA5OTg1Q0YiLCJ1c2VyX2FnZW50IjoiUHNpcGhvbi1Qc2lDYXNoLVdpbmRvd3MiLCJ2IjoxfSwidGltZXN0YW1wIjoiMjAyNS0wNy0wNVQyMTozNzoyOC4zMTBaIiwidG9rZW5zIjpudWxsLCJ2IjoxfQ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | psiphon3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2180,i,17889959471652366791,11884440529737306163,262144 --variations-seed-version --mojo-platform-channel-handle=2432 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc44e0f208,0x7ffc44e0f214,0x7ffc44e0f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
7 304
Read events
7 266
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2356) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
7
Suspicious files
236
Text files
75
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2356 | psiphon3.exe | C:\Users\admin\AppData\Local\Psiphon3\psicash\psicashdatastore.prod.2.temp | binary | |
MD5:5AD5CC4D26869082EFD29C436B57384A | SHA256:C5C24F7CA1C946FA4DFD44407409C8E11EC6E41F0E1C7C45BF8381B42AFB31F1 | |||
| 2356 | psiphon3.exe | C:\Users\admin\AppData\Local\Psiphon3\psicash\psicashdatastore.prod.temp | binary | |
MD5:5AD5CC4D26869082EFD29C436B57384A | SHA256:C5C24F7CA1C946FA4DFD44407409C8E11EC6E41F0E1C7C45BF8381B42AFB31F1 | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF179981.TMP | — | |
MD5:— | SHA256:— | |||
| 2356 | psiphon3.exe | C:\Users\admin\AppData\Local\Temp\dat659F.tmp | binary | |
MD5:79CE7E9887A670AB6A18EAF59CAB7FA7 | SHA256:24F0C91CD083494F5475C9DDE62F4477EA9FAE06DF25C398949781FF879FCD83 | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF179990.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF179990.TMP | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2356 | psiphon3.exe | C:\Users\admin\AppData\Local\Psiphon3\psicash\psicashdatastore.prod | binary | |
MD5:5AD5CC4D26869082EFD29C436B57384A | SHA256:C5C24F7CA1C946FA4DFD44407409C8E11EC6E41F0E1C7C45BF8381B42AFB31F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
42
DNS requests
7
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 104.18.168.46:443 | https://docasion-rookie-sectrogram.psiphon3.net/ | unknown | — | — | unknown |
— | — | POST | 200 | 104.18.168.46:443 | https://docasion-rookie-sectrogram.psiphon3.net/ | unknown | binary | 78 b | unknown |
4572 | psiphon-tunnel-core.exe | POST | 200 | 154.17.253.225:80 | http://154.17.253.225/ | unknown | — | — | unknown |
4572 | psiphon-tunnel-core.exe | POST | 200 | 154.17.253.225:80 | http://154.17.253.225/ | unknown | — | — | unknown |
4572 | psiphon-tunnel-core.exe | POST | 200 | 154.17.253.225:80 | http://154.17.253.225/ | unknown | — | — | unknown |
4572 | psiphon-tunnel-core.exe | POST | 200 | 154.17.253.225:80 | http://154.17.253.225/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2432 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6024 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
4572 | psiphon-tunnel-core.exe | Potentially Bad Traffic | ET INFO Psiphon VPN Related Activity (POST) |
4572 | psiphon-tunnel-core.exe | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
4572 | psiphon-tunnel-core.exe | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
4572 | psiphon-tunnel-core.exe | Potentially Bad Traffic | ET INFO Psiphon VPN Related Activity (POST) |
Process | Message |
|---|---|
psiphon3.exe | 2025-07-05T21:37:19.071Z: |
psiphon3.exe | Client Version: 186 |
psiphon3.exe | |
psiphon3.exe | 2025-07-05T21:37:19.105Z: |
psiphon3.exe | |
psiphon3.exe | Psiphon Tunnel connecting... |
psiphon3.exe | {"data":{"data":{"message":"RemoteServerListURLs overridden by AdditionalParameters"},"noticeType":"Info","timestamp":"2025-07-05T21:37:22.520Z"},"msg":"CoreNotice","timestamp!!timestamp":"2025-07-05T21:37:22.624Z"}
|
psiphon3.exe | {"data":{"data":{"message":"ObfuscatedServerListRootURLs overridden by AdditionalParameters"},"noticeType":"Info","timestamp":"2025-07-05T21:37:22.520Z"},"msg":"CoreNotice","timestamp!!timestamp":"2025-07-05T21:37:22.624Z"}
|
psiphon3.exe | |
psiphon3.exe | |