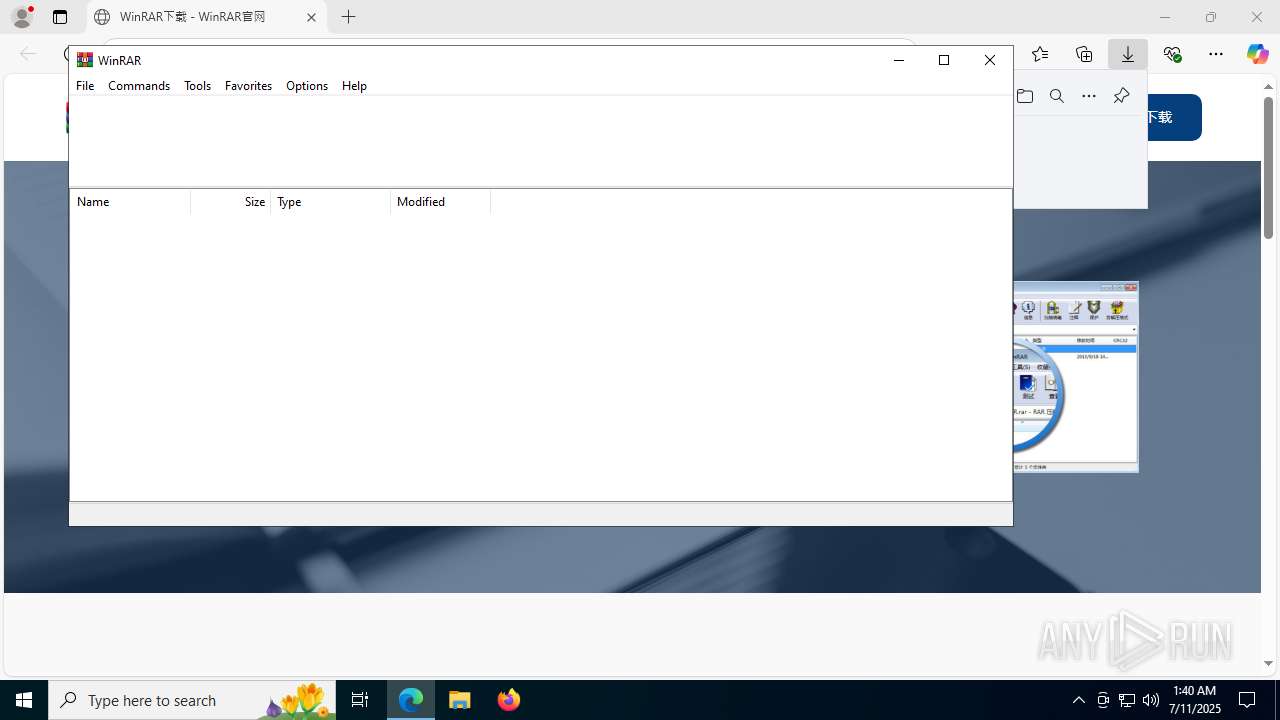
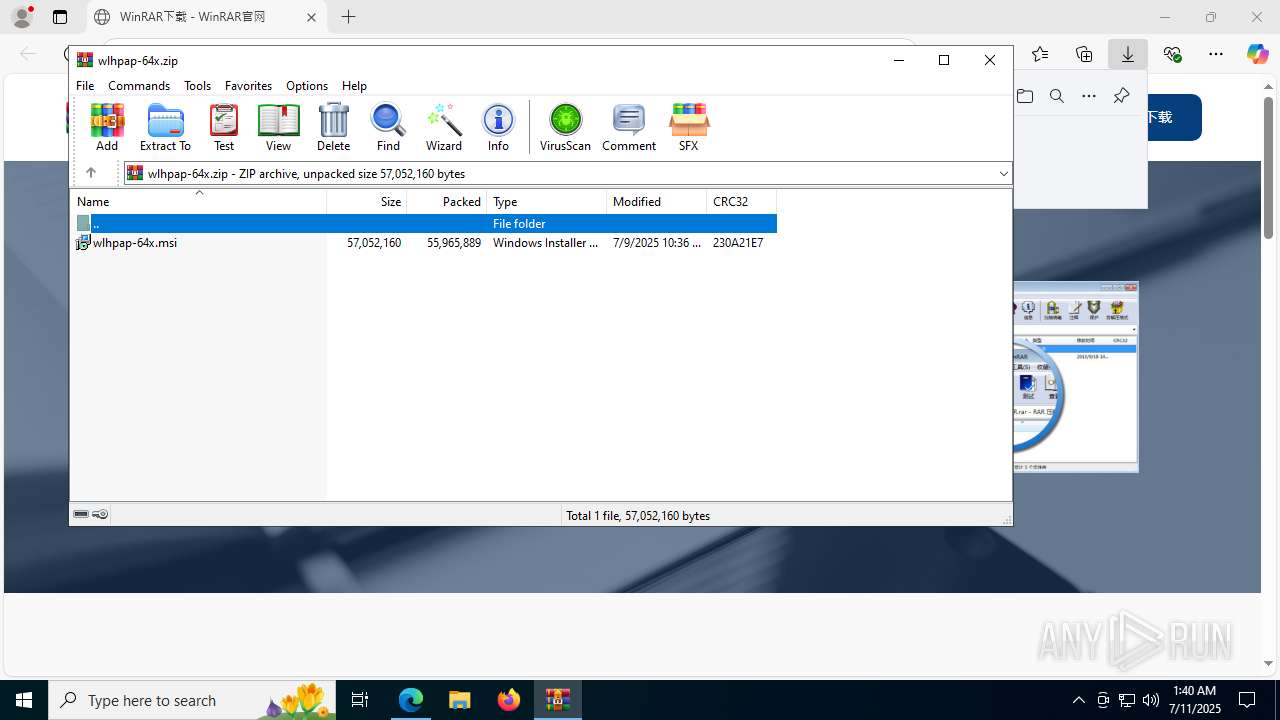
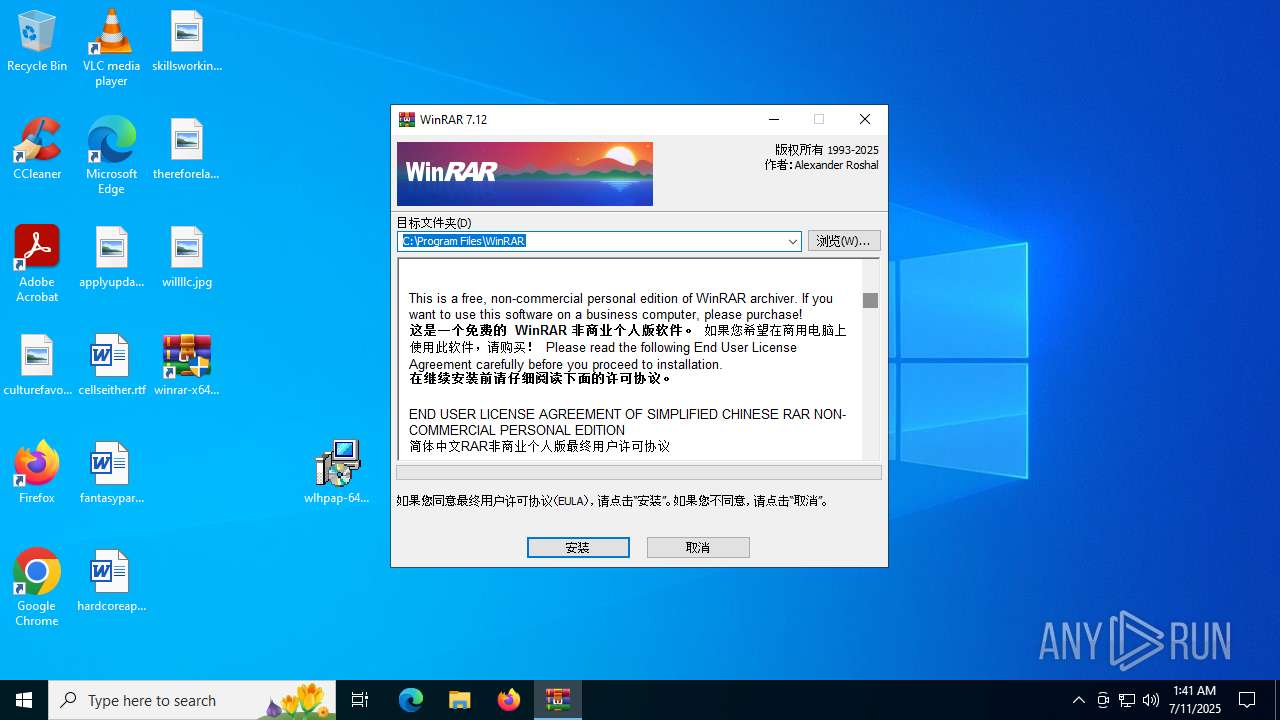
| URL: | https://www.cn-winrar.com/ |
| Full analysis: | https://app.any.run/tasks/6ef43f5e-a3a4-420a-b259-6bf62e785ab1 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2025, 01:38:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
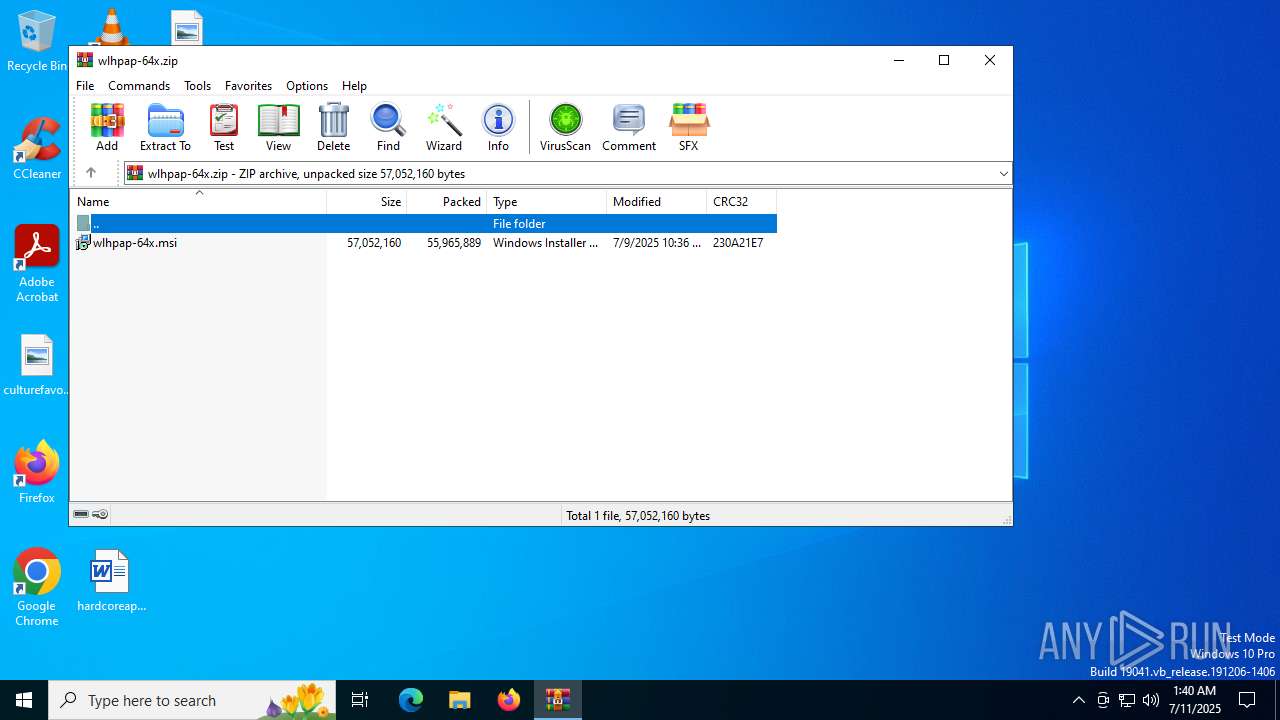
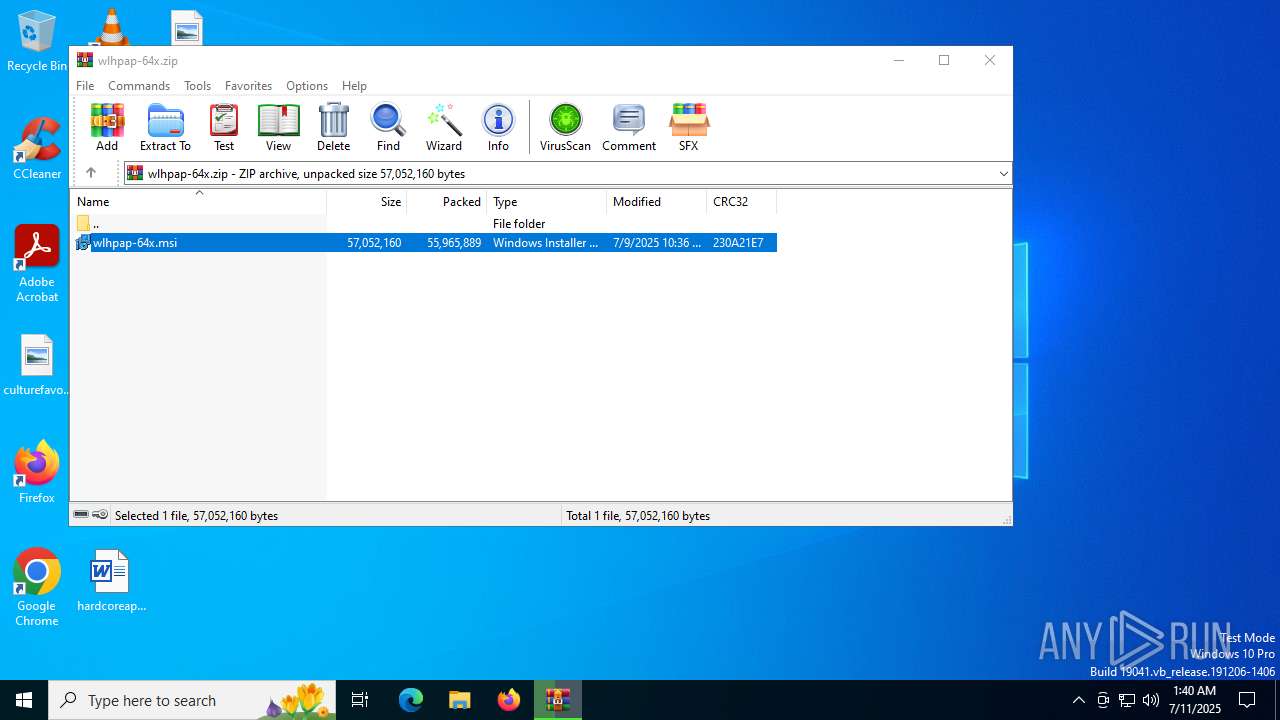
| MD5: | 955A3A1917A167D45E4829A1668F71A9 |
| SHA1: | C372BB52794C0DA1AC4A54CE9B53B43B18A5BAB9 |
| SHA256: | 19E30B7EB9A1388C38A62320F5D681ECECBB5A8A90CD59FC5FB22F88DE958AA4 |
| SSDEEP: | 3:N8DSLNat:2OLg |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- OptionalFeatures.exe (PID: 3876)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2200)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7812)
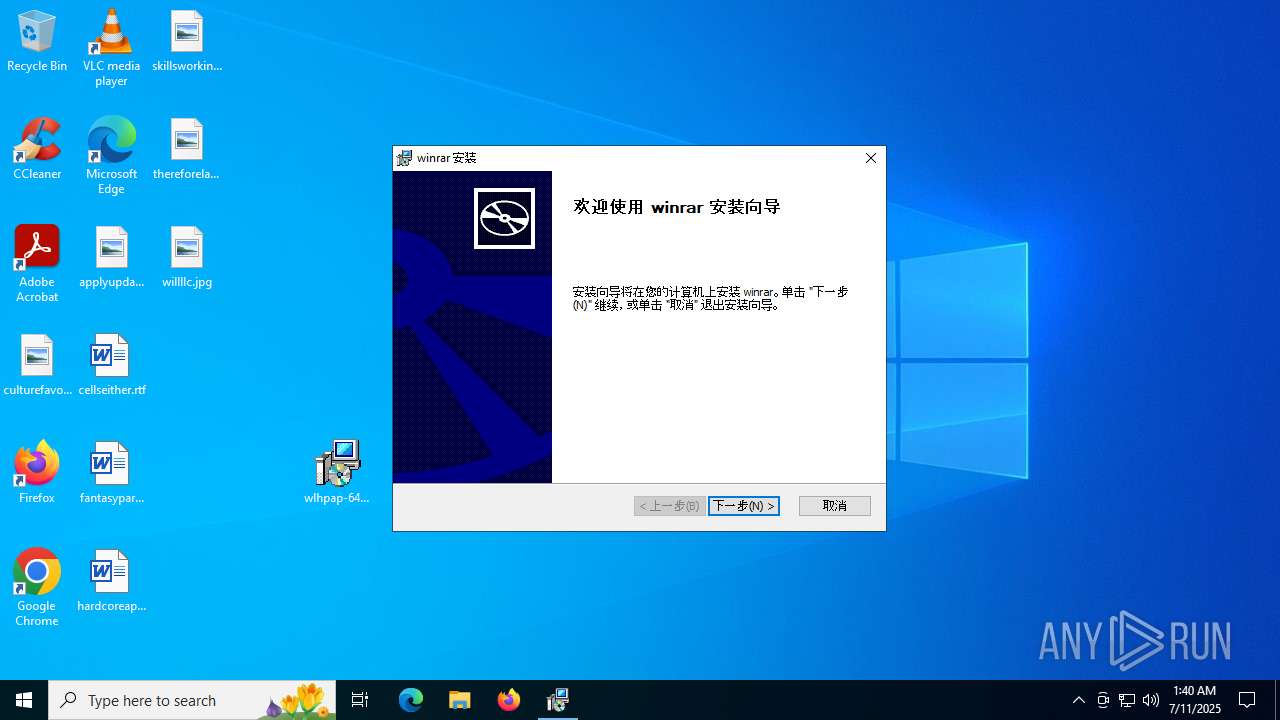
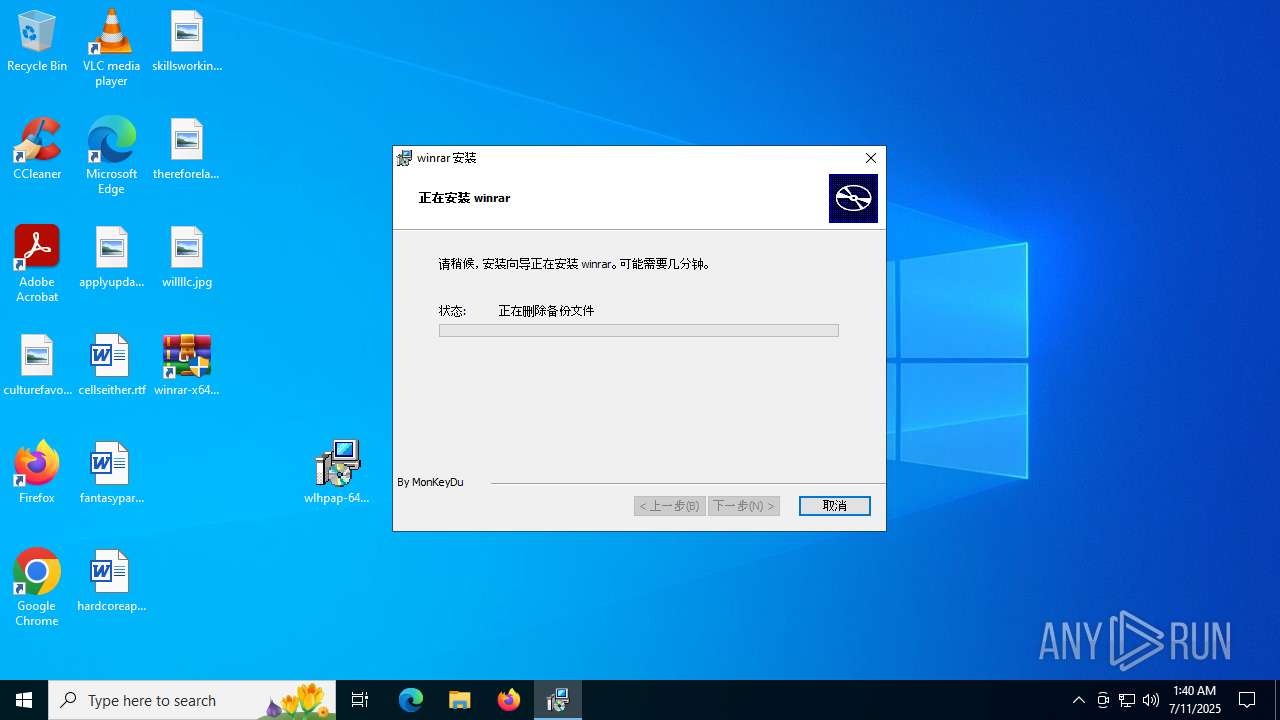
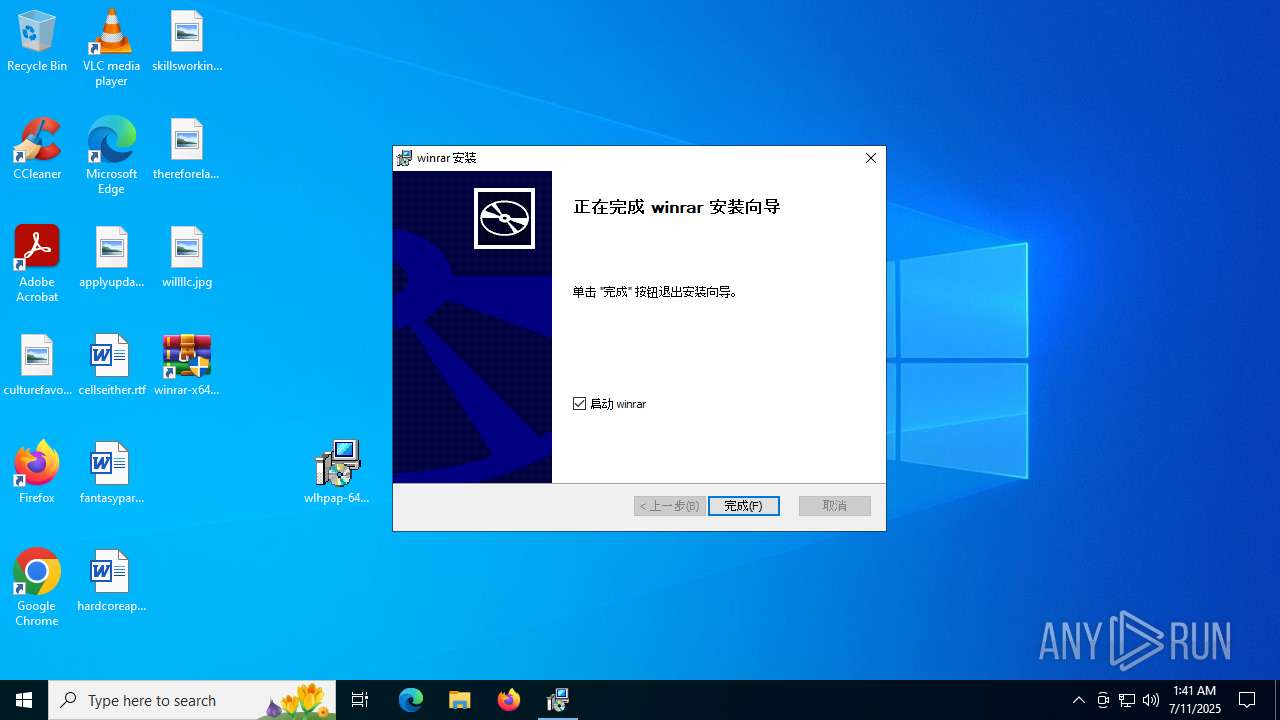
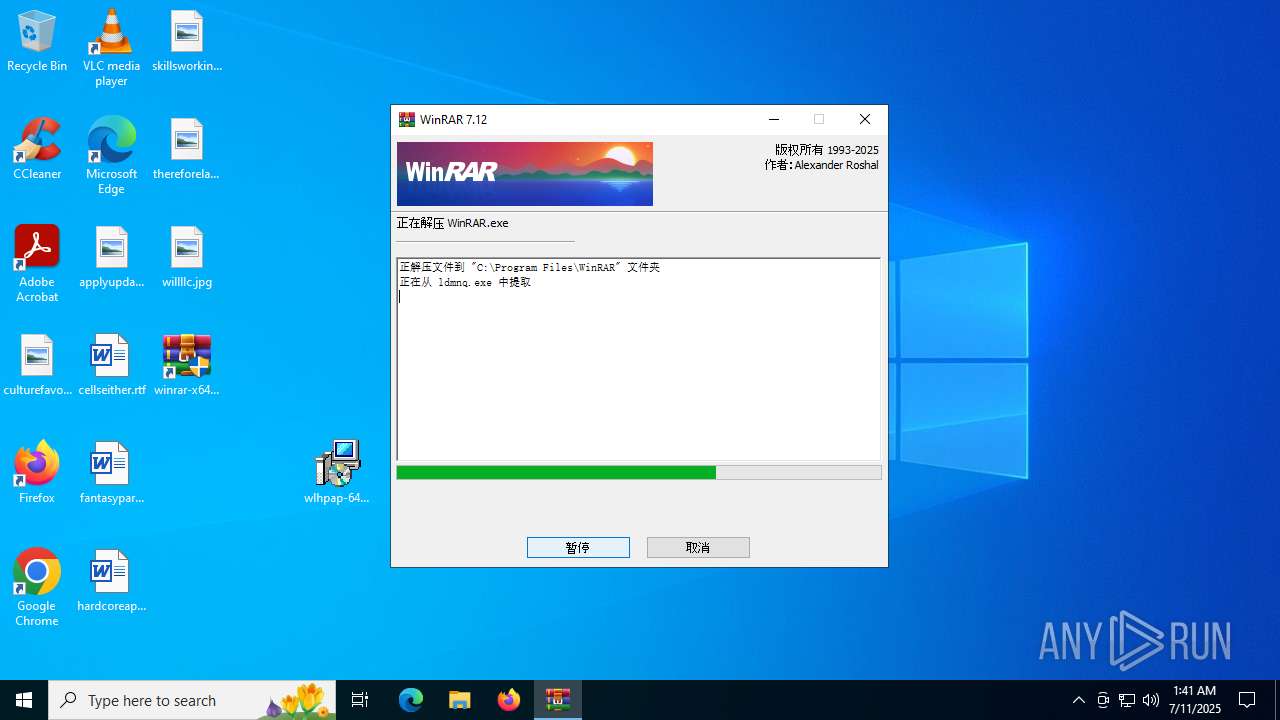
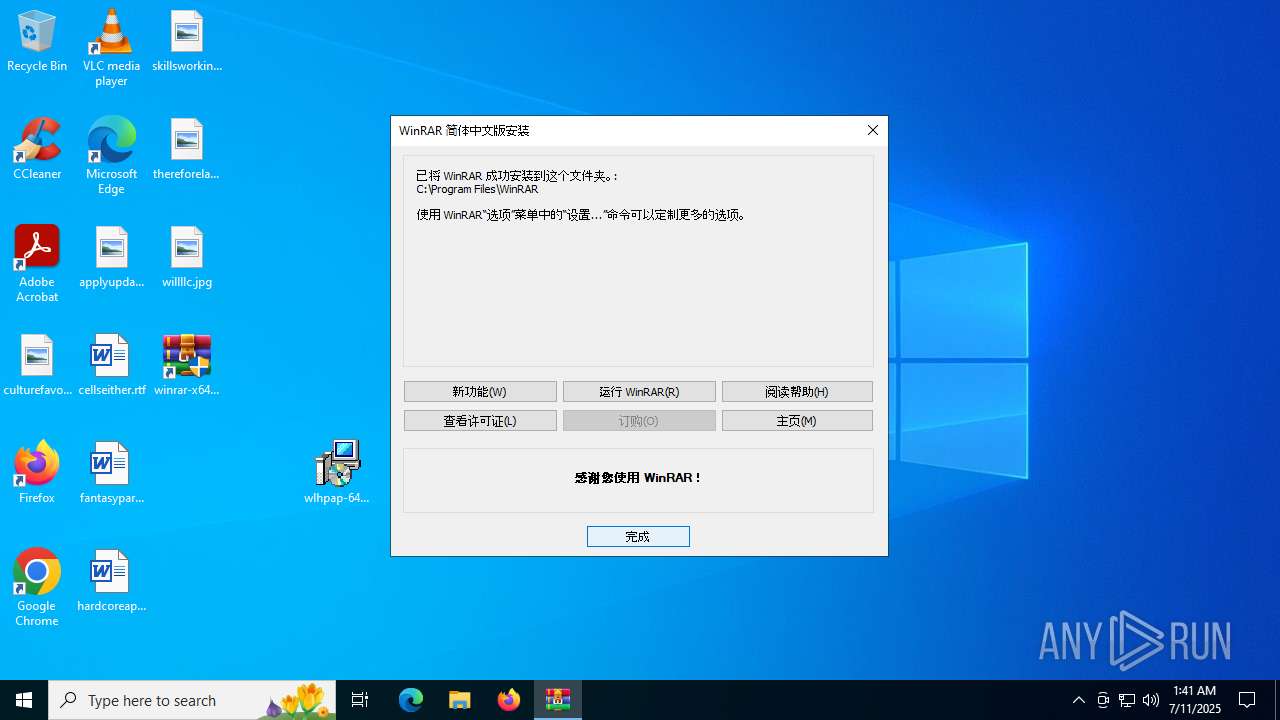
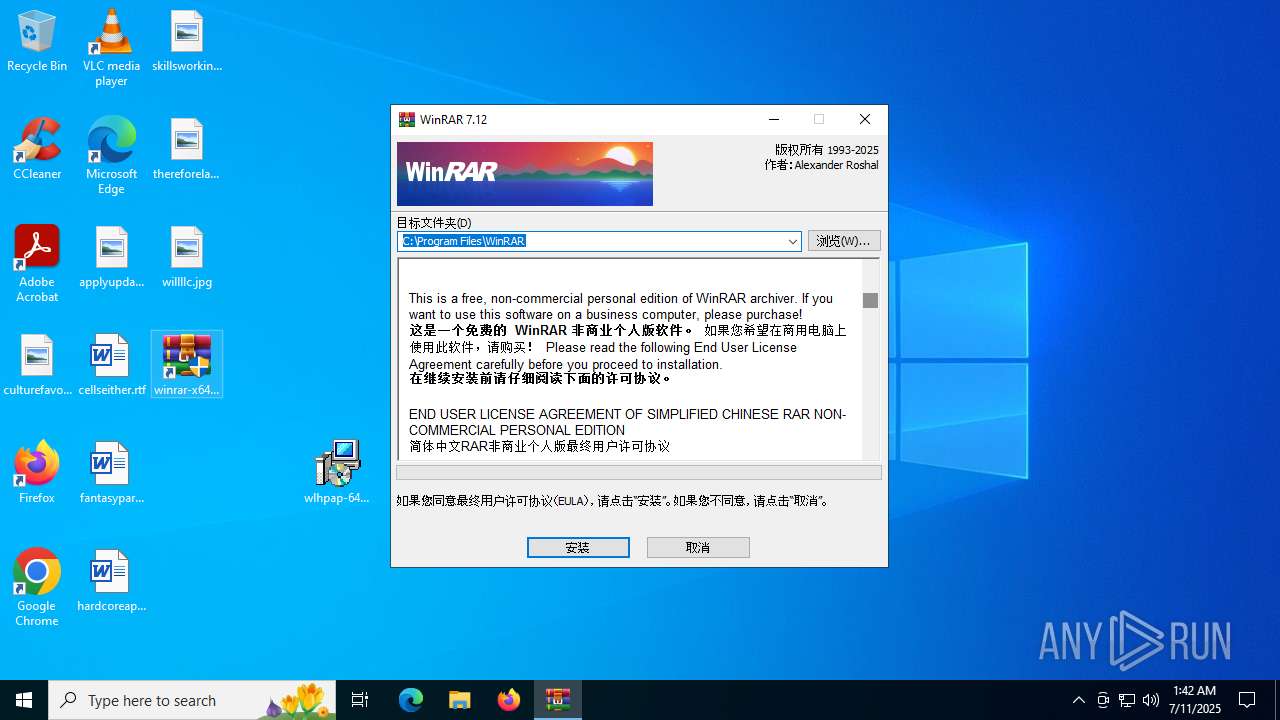
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 7812)
- ldmnq.exe (PID: 2220)
Executes as Windows Service
- VSSVC.exe (PID: 7972)
- regsvr32.exe (PID: 5744)
Reads the BIOS version
- msiexec.exe (PID: 3608)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4816)
- ldmnq.exe (PID: 2220)
- msiexec.exe (PID: 3608)
- ldmnq.exe (PID: 888)
Reads Microsoft Outlook installation path
- ldmnq.exe (PID: 2220)
- ldmnq.exe (PID: 888)
Application launched itself
- msiexec.exe (PID: 7812)
Reads Internet Explorer settings
- ldmnq.exe (PID: 2220)
- ldmnq.exe (PID: 888)
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 3852)
Reads the date of Windows installation
- ldmnq.exe (PID: 2220)
Executable content was dropped or overwritten
- ldmnq.exe (PID: 2220)
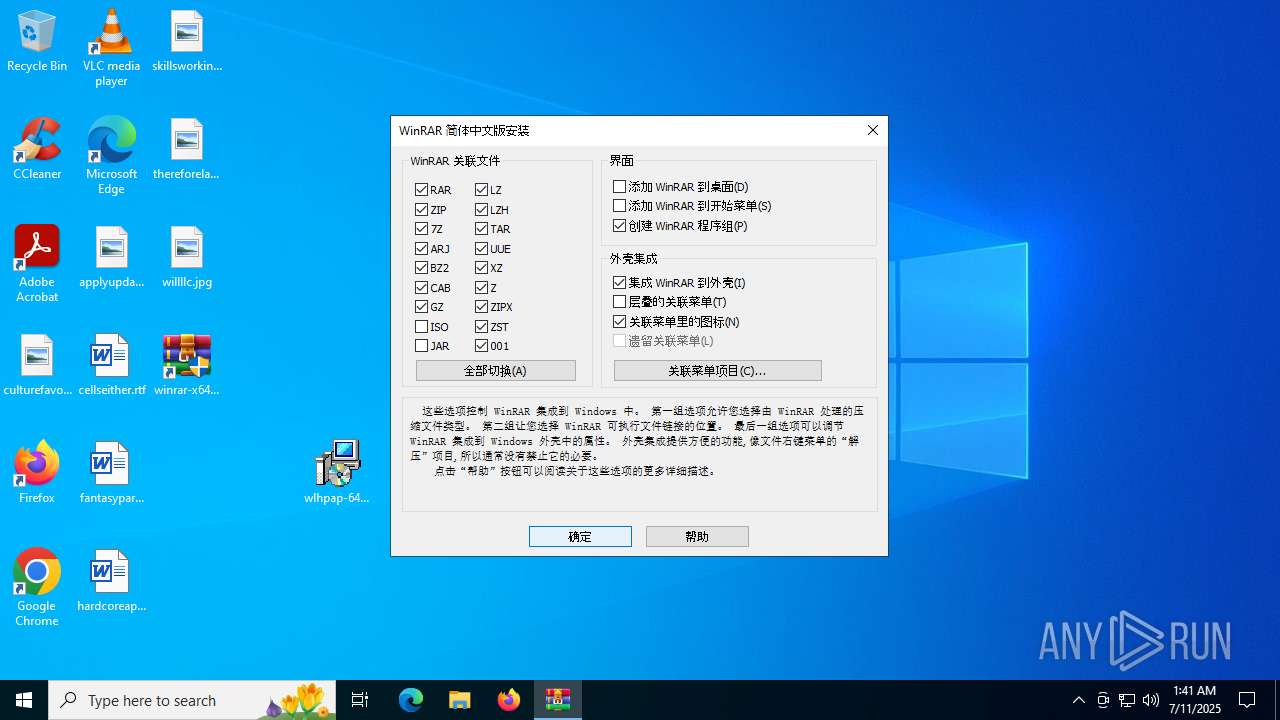
Creates a software uninstall entry
- Uninstall.exe (PID: 3852)
Contacting a server suspected of hosting an CnC
- sihost.exe (PID: 4180)
Searches for installed software
- Uninstall.exe (PID: 3852)
Connects to unusual port
- sihost.exe (PID: 4180)
INFO
Reads the computer name
- identity_helper.exe (PID: 7500)
- identity_helper.exe (PID: 7280)
- msiexec.exe (PID: 7812)
- msiexec.exe (PID: 4816)
- msiexec.exe (PID: 6812)
- ldmnq.exe (PID: 2220)
- msiexec.exe (PID: 3608)
- Uninstall.exe (PID: 3852)
- ldmnq.exe (PID: 888)
Application launched itself
- msedge.exe (PID: 6188)
- msedge.exe (PID: 6776)
Checks supported languages
- identity_helper.exe (PID: 7500)
- identity_helper.exe (PID: 7280)
- msiexec.exe (PID: 7812)
- msiexec.exe (PID: 6812)
- msiexec.exe (PID: 4816)
- ldmnq.exe (PID: 2220)
- msiexec.exe (PID: 3608)
- Uninstall.exe (PID: 3852)
- ldmnq.exe (PID: 888)
Reads Environment values
- identity_helper.exe (PID: 7500)
- identity_helper.exe (PID: 7280)
- msiexec.exe (PID: 6812)
- msiexec.exe (PID: 4816)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6188)
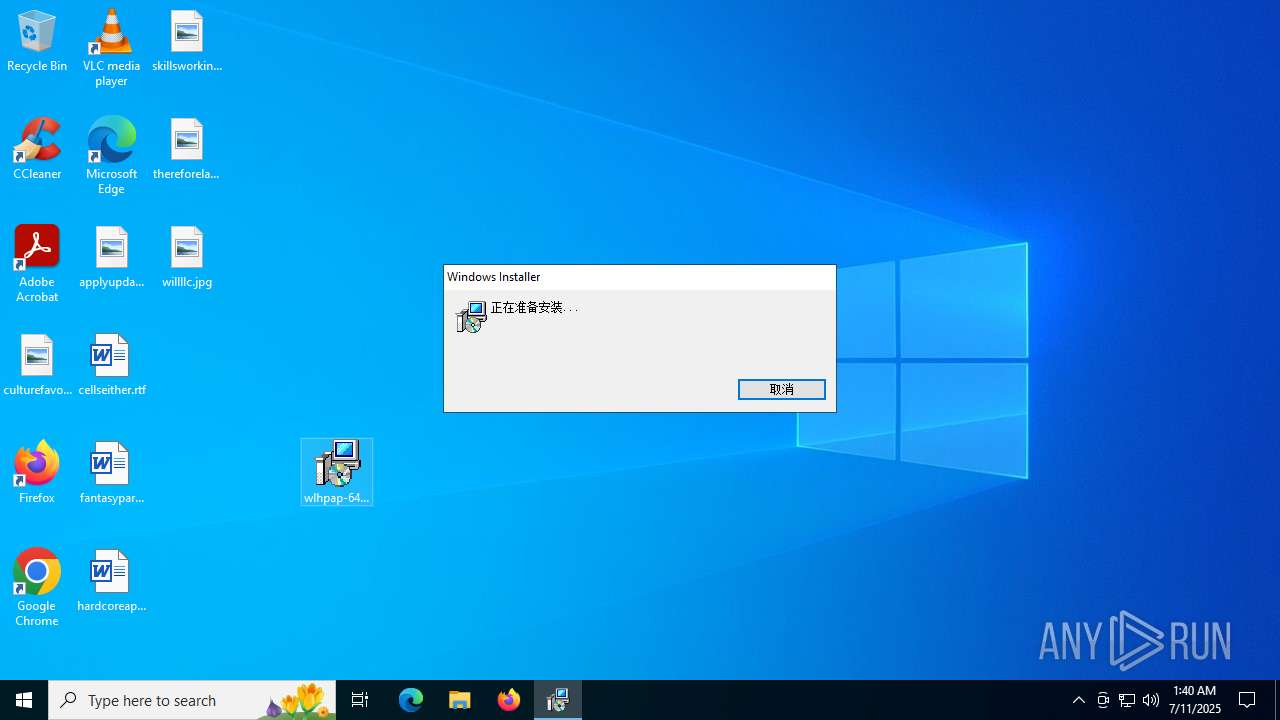
Manual execution by a user
- msiexec.exe (PID: 7300)
- ldmnq.exe (PID: 7884)
- ldmnq.exe (PID: 888)
Manages system restore points
- SrTasks.exe (PID: 3480)
The sample compiled with english language support
- msiexec.exe (PID: 7300)
- msiexec.exe (PID: 7812)
- ldmnq.exe (PID: 2220)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7300)
- msiexec.exe (PID: 7812)
Checks proxy server information
- slui.exe (PID: 7692)
- ldmnq.exe (PID: 2220)
- msiexec.exe (PID: 3608)
- ldmnq.exe (PID: 888)
- slui.exe (PID: 868)
Reads the software policy settings
- slui.exe (PID: 7692)
- msiexec.exe (PID: 3608)
- slui.exe (PID: 7324)
- slui.exe (PID: 868)
The sample compiled with chinese language support
- msiexec.exe (PID: 7812)
Creates files or folders in the user directory
- msiexec.exe (PID: 3608)
- Uninstall.exe (PID: 3852)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3608)
Process checks computer location settings
- msiexec.exe (PID: 4816)
- ldmnq.exe (PID: 2220)
Creates files in the program directory
- ldmnq.exe (PID: 2220)
- Uninstall.exe (PID: 3852)
- sihost.exe (PID: 4180)
The sample compiled with german language support
- ldmnq.exe (PID: 2220)
Themida protector has been detected
- regsvr32.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
290
Monitored processes
72
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\winrar\winrar\ldmnq.exe" | C:\Program Files (x86)\winrar\winrar\ldmnq.exe | explorer.exe | ||||||||||||
User: admin Company: 全球发行商 win.rar GmbH Integrity Level: HIGH Description: WinRAR Exit code: 255 Version: 7.12.0 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7100,i,8990981623879196958,18305119538104187526,262144 --variations-seed-version --mojo-platform-channel-handle=7184 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5116,i,14473482391149411463,15504438932125473837,262144 --variations-seed-version --mojo-platform-channel-handle=4684 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc4451f208,0x7ffc4451f214,0x7ffc4451f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | C:\WINDOWS\system32\migwiz\mighost.exe | C:\Windows\System32\migwiz\mighost.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Migration Plugins host program Exit code: 0 Version: 10.0.19041.3693 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4448,i,14473482391149411463,15504438932125473837,262144 --variations-seed-version --mojo-platform-channel-handle=5360 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4680,i,14473482391149411463,15504438932125473837,262144 --variations-seed-version --mojo-platform-channel-handle=4748 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 167
Read events
24 753
Write events
370
Delete events
44
Modification events
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3884) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F5EAD0A733982F00 | |||
Executable files
29
Suspicious files
201
Text files
121
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176b9b.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176baa.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176baa.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176bd9.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176be9.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
111
DNS requests
93
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2764 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3956 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CdX31Q1ENZnlkSTZSVVCeQGQQ5S7g6nGkWvk9MqY2mI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8048 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5424 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752361306&P2=404&P3=2&P4=c2%2bVhPWdjxM3X14zElZD31uNrTJDbgWPfUSmC72TDXB8Sq9KcTxETsD5YIL7gmi9batcfsezZTCjtFVuzPyXOQ%3d%3d | unknown | — | — | whitelisted |
8048 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5424 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752361306&P2=404&P3=2&P4=c2%2bVhPWdjxM3X14zElZD31uNrTJDbgWPfUSmC72TDXB8Sq9KcTxETsD5YIL7gmi9batcfsezZTCjtFVuzPyXOQ%3d%3d | unknown | — | — | whitelisted |
5424 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752361306&P2=404&P3=2&P4=c2%2bVhPWdjxM3X14zElZD31uNrTJDbgWPfUSmC72TDXB8Sq9KcTxETsD5YIL7gmi9batcfsezZTCjtFVuzPyXOQ%3d%3d | unknown | — | — | whitelisted |
5424 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1752357709&P2=404&P3=2&P4=Qk0EhoCbeYXRdpk8N3f%2fqYk%2bNydXZ%2brNmzuUTj%2bjs1SNDb588Imz%2bE%2bHburtnSSk6A%2bIkIMnWVKoKz%2fz5XL7ig%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3956 | msedge.exe | 156.226.172.158:443 | www.cn-winrar.com | Sun Network Hong Kong Limited - HongKong Backbone | SC | unknown |
3956 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.cn-winrar.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
3956 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
3956 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
3956 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
3956 | msedge.exe | Misc activity | ET INFO Observed Alibaba Cloud CDN Domain (aliyuncs .com in TLS SNI) |
3956 | msedge.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2200 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain (mlcrosoft) |
4180 | sihost.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Gh0stRAT.Gen Server Response (SweetSpecter) |
Process | Message |
|---|---|
TiWorker.exe | Failed to locate Mobile Store key, so we're not running on a mobile device. [HRESULT = 0x80070002 - ERROR_FILE_NOT_FOUND] |