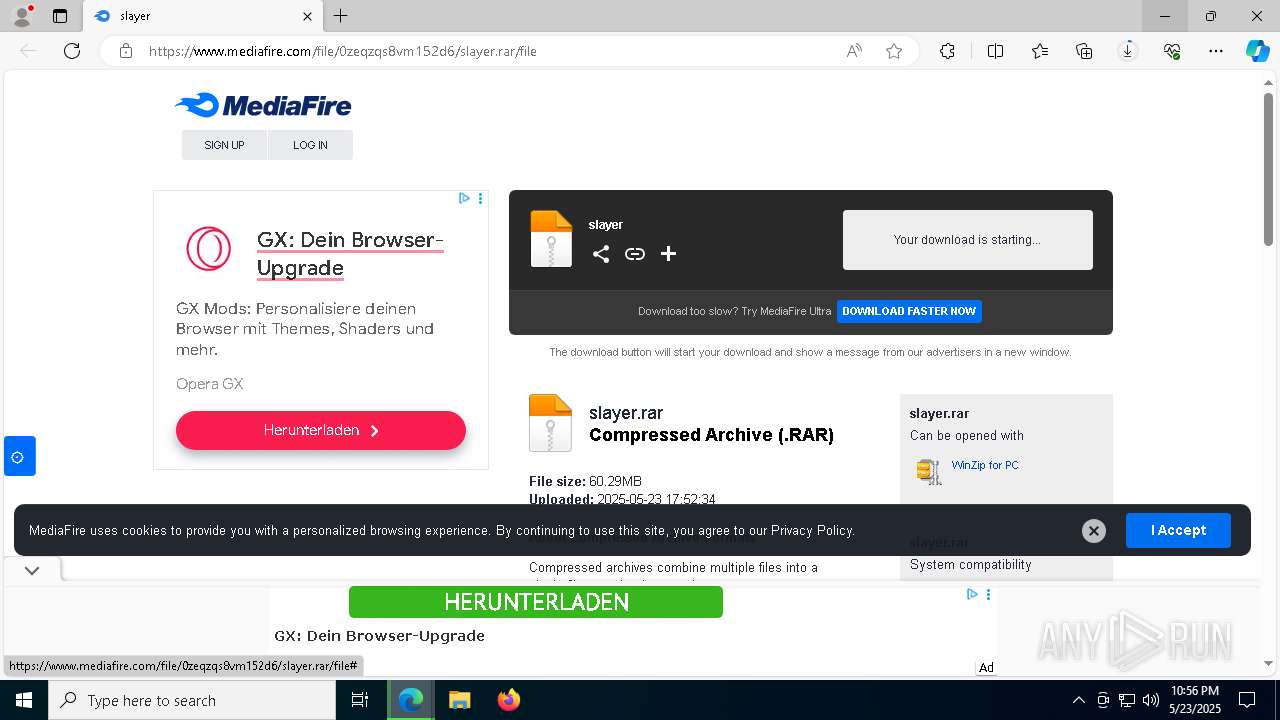
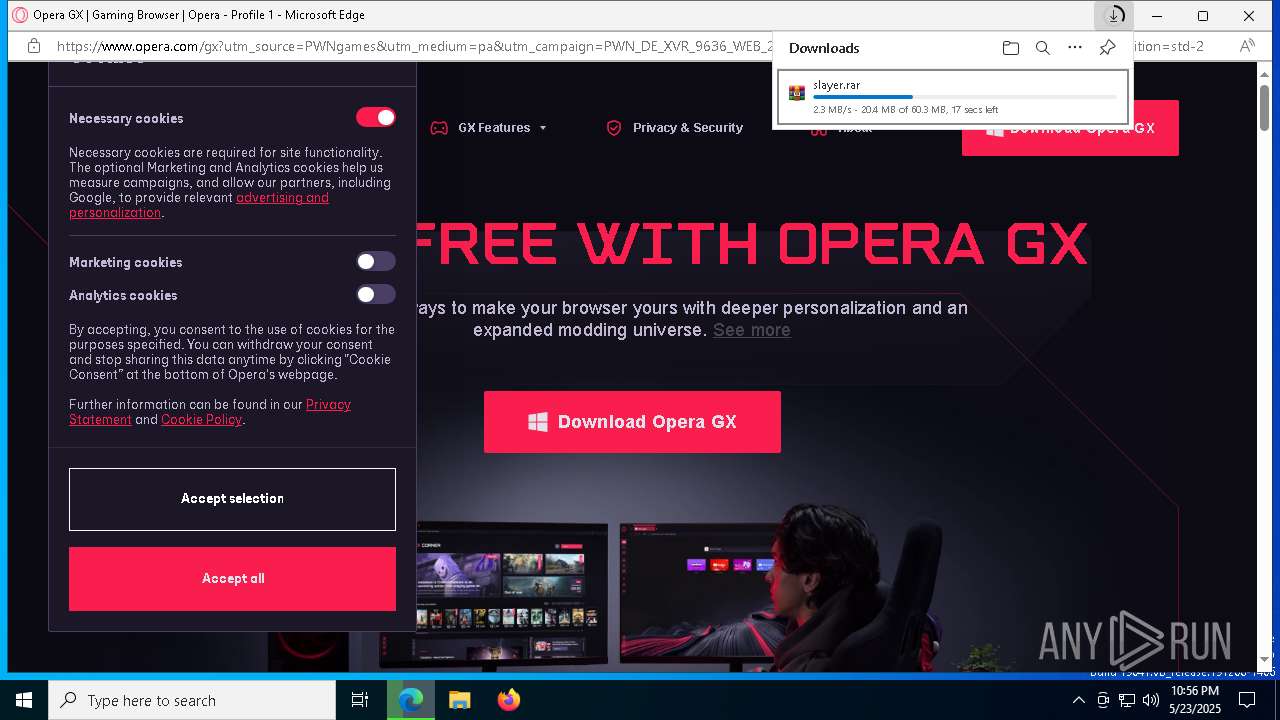
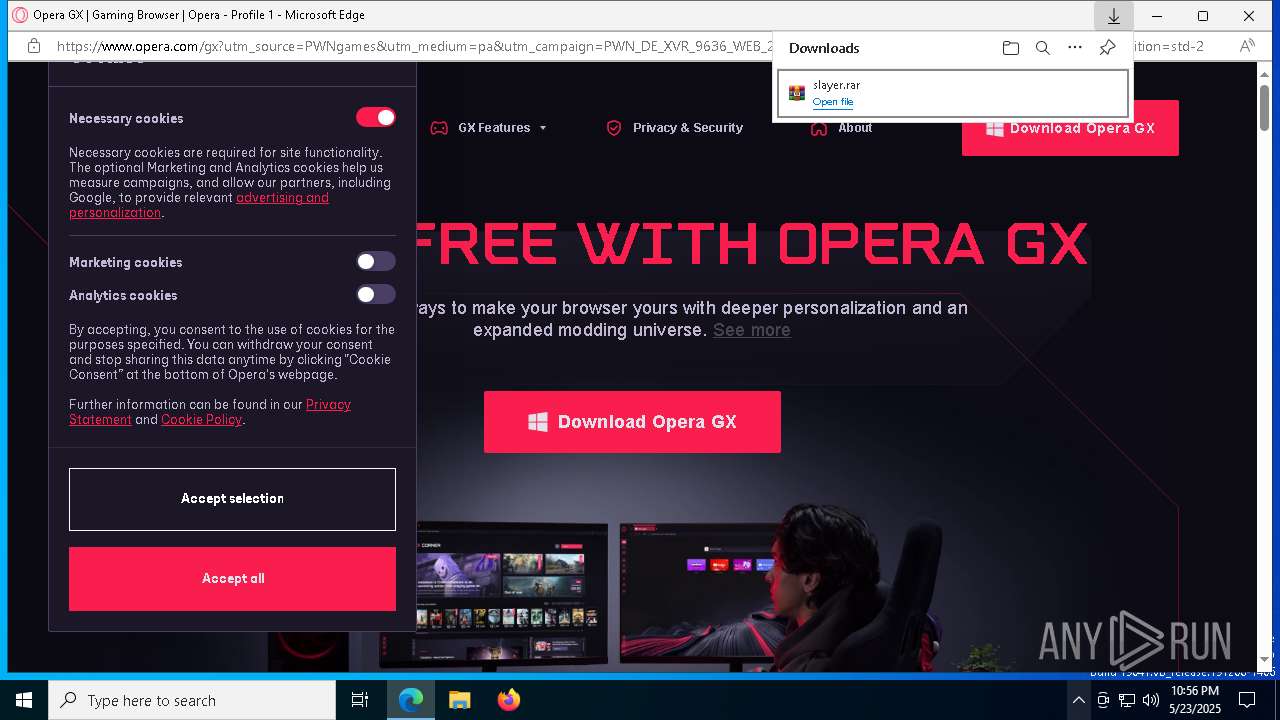
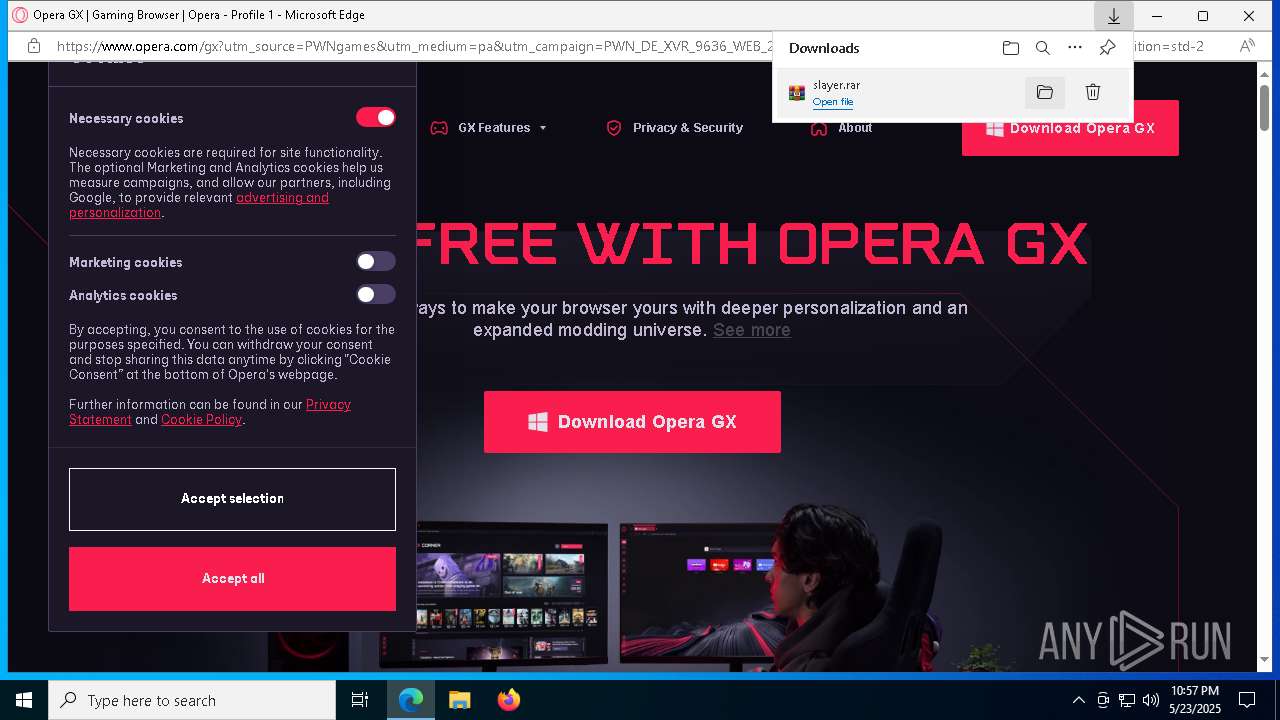
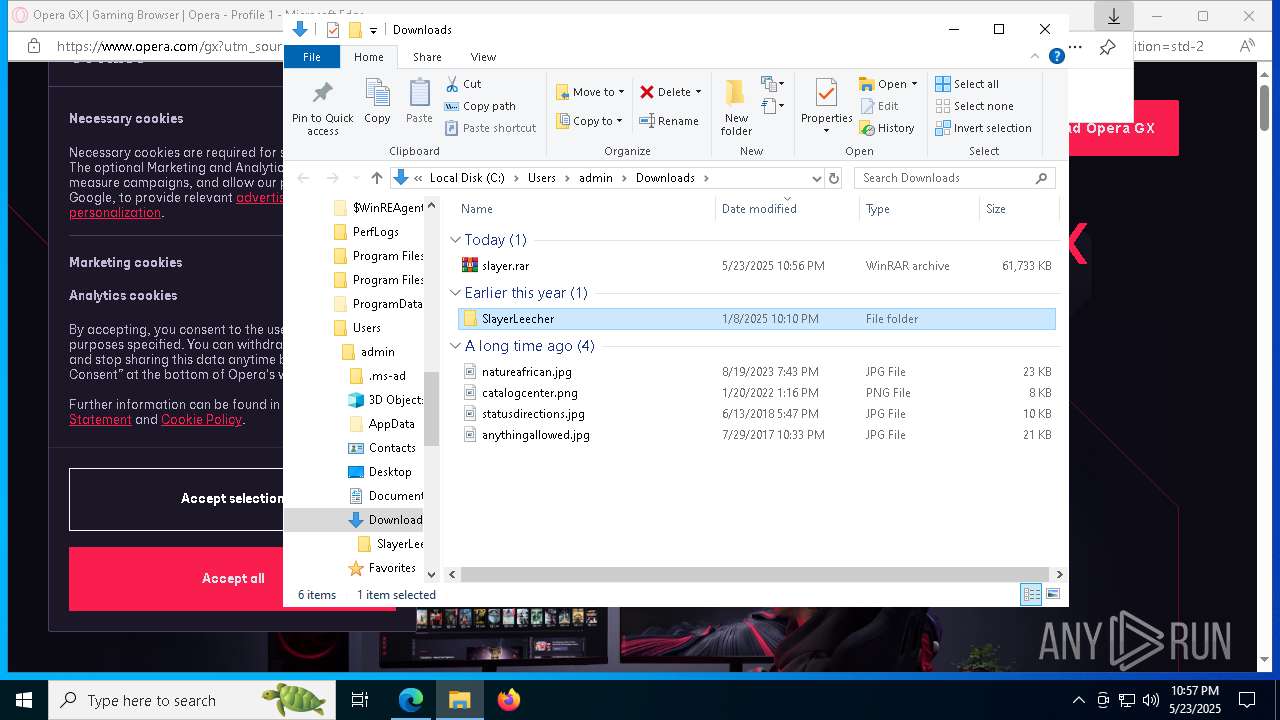
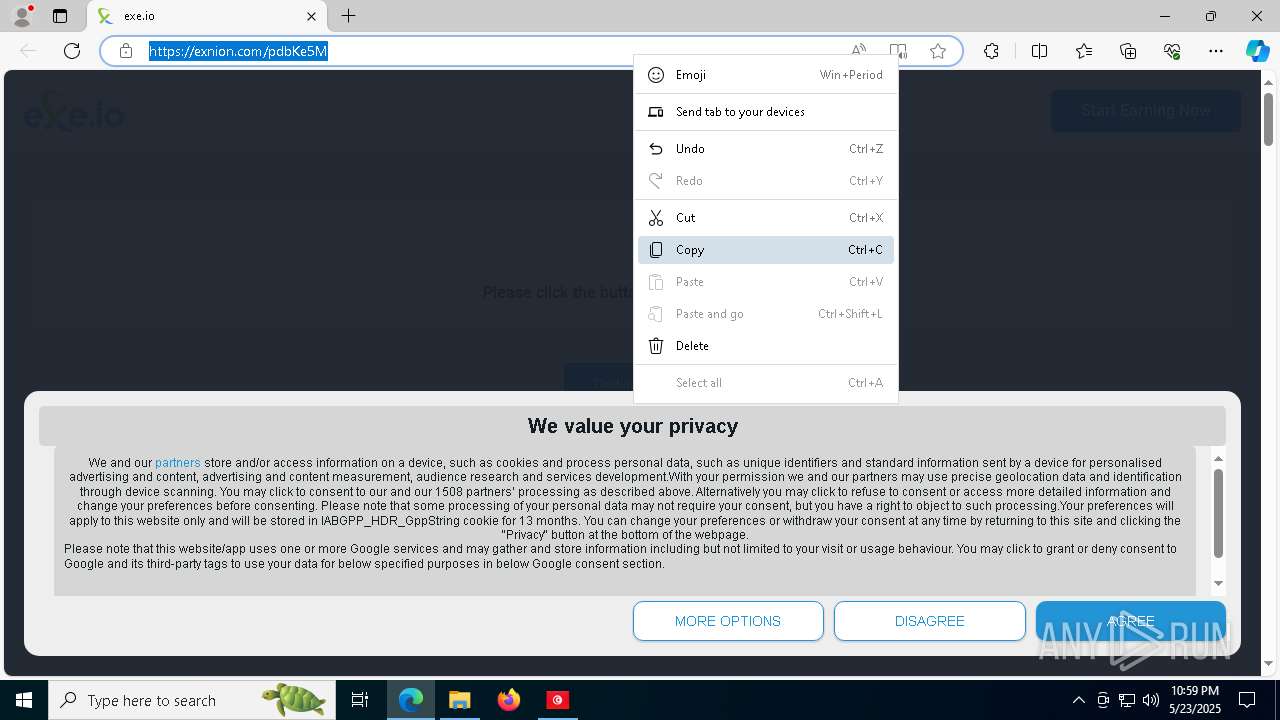
| URL: | https://www.mediafire.com/file/0zeqzqs8vm152d6/slayer.rar/file |
| Full analysis: | https://app.any.run/tasks/27ee35db-3f17-4db0-ac57-b99943466ac1 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 22:56:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ECE2C2B6CD3D1CA8C77F80C757DD8C06 |
| SHA1: | 95FCBC1AA745E141960965228D29C421F5CA1299 |
| SHA256: | 19D072D78304A3E604DF952BA2FBCCF650AA29CA503043663B347756FF02212C |
| SSDEEP: | 3:N8DSLw3eGUoVJfP0RGW4UPA:2OLw3eGxJH0RB4aA |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3308)
- cmd.exe (PID: 5588)
- version.exe (PID: 4180)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 1704)
Run PowerShell with an invisible window
- powershell.exe (PID: 9272)
- powershell.exe (PID: 9252)
- powershell.exe (PID: 9344)
- powershell.exe (PID: 9324)
- powershell.exe (PID: 9464)
- powershell.exe (PID: 9612)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 9396)
Changes Windows Defender settings
- cmd.exe (PID: 3308)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 7388)
Known privilege escalation attack
- dllhost.exe (PID: 3272)
SUSPICIOUS
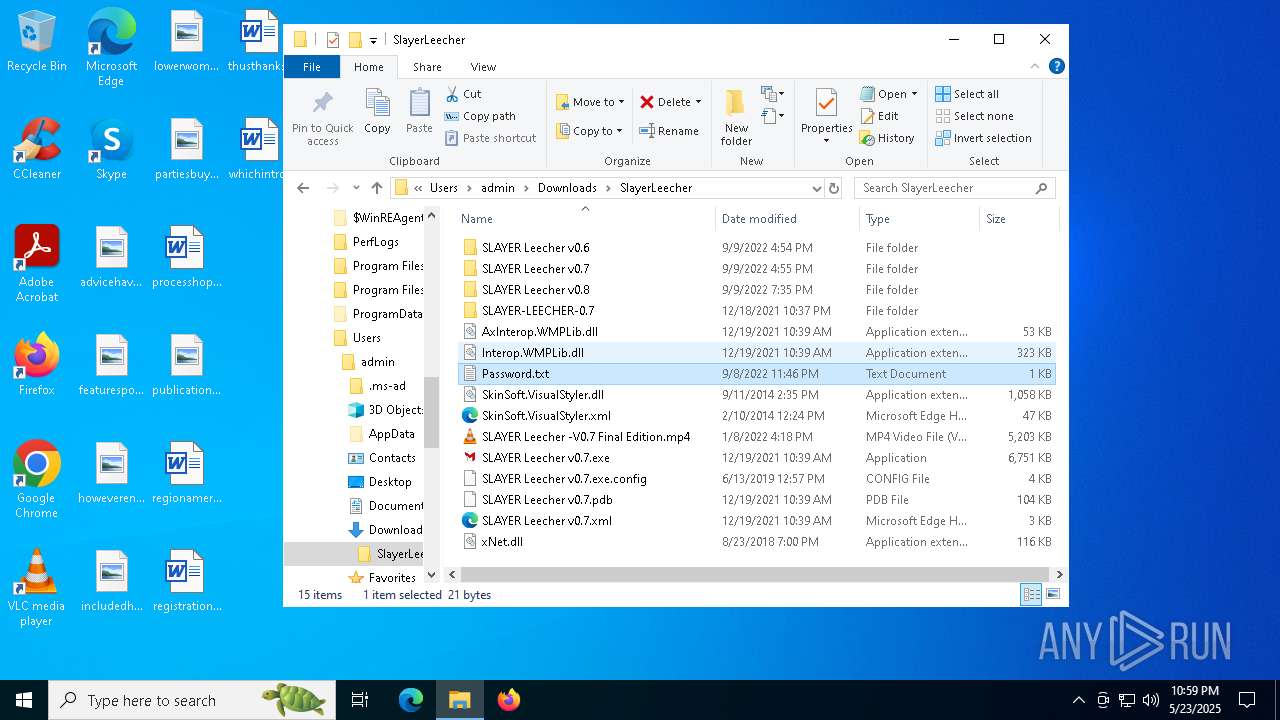
Process drops legitimate windows executable
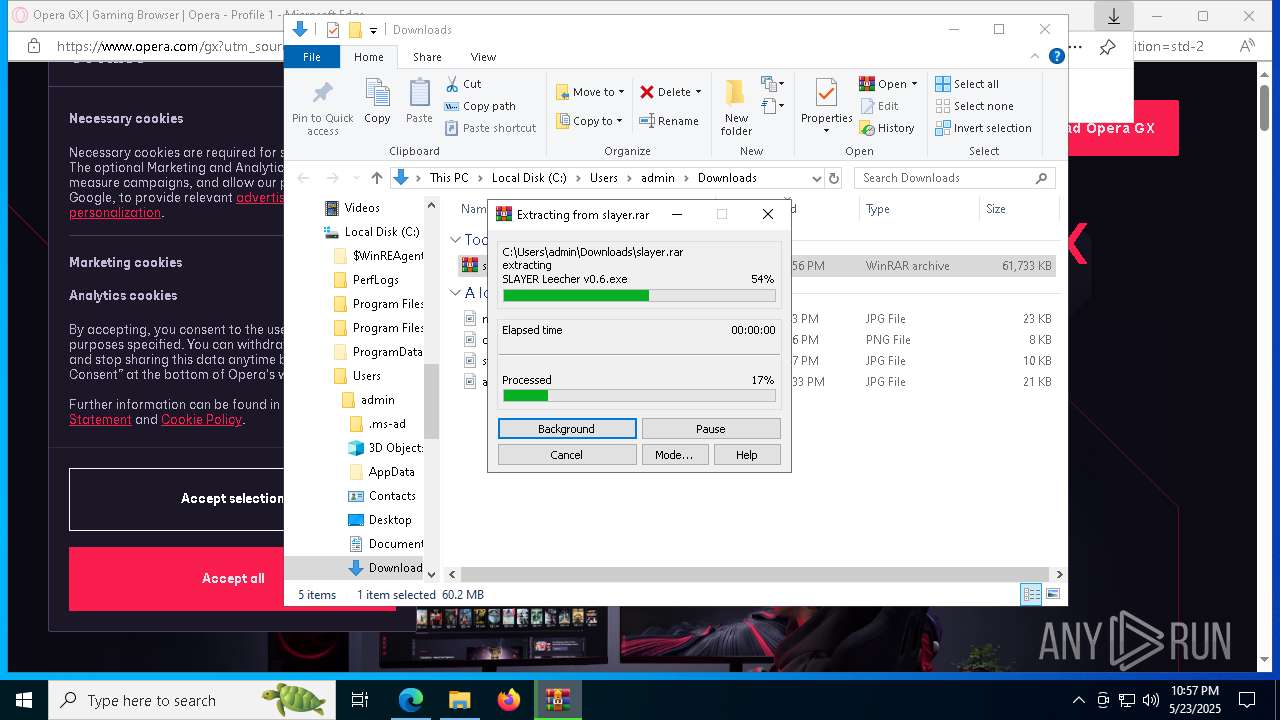
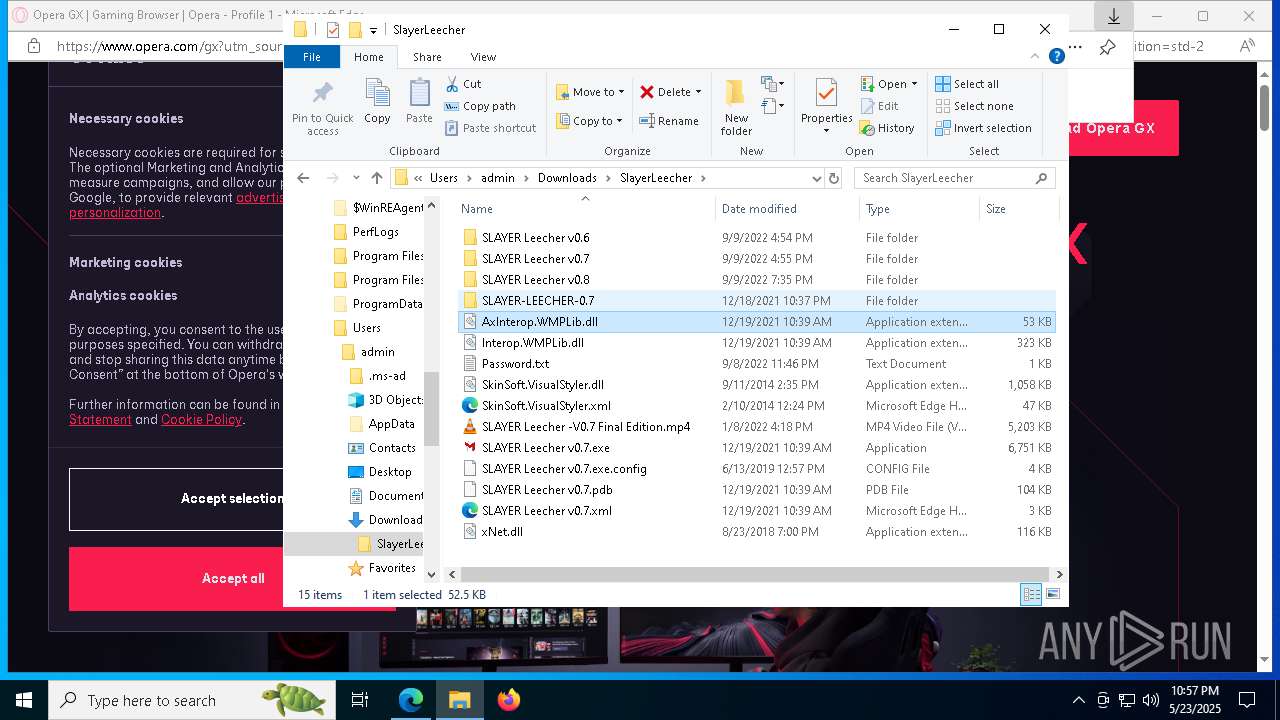
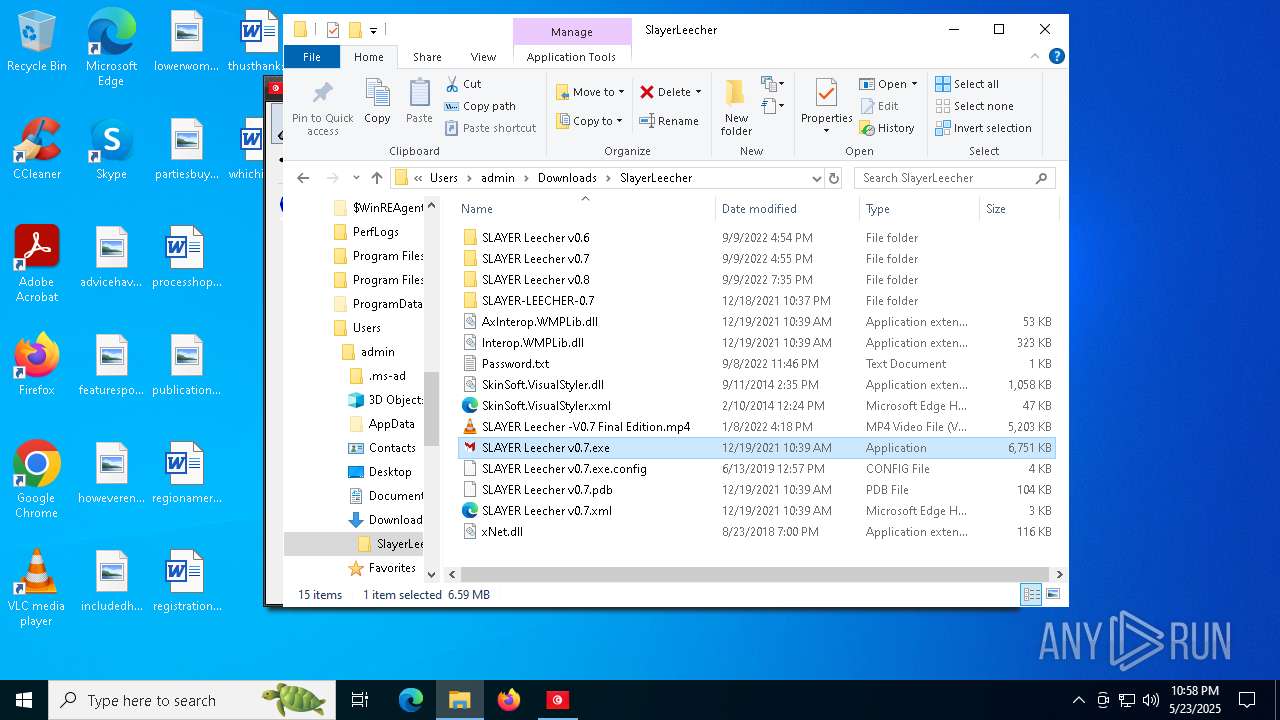
- WinRAR.exe (PID: 1196)
- Setup.exe (PID: 7416)
- svchost.exe (PID: 7304)
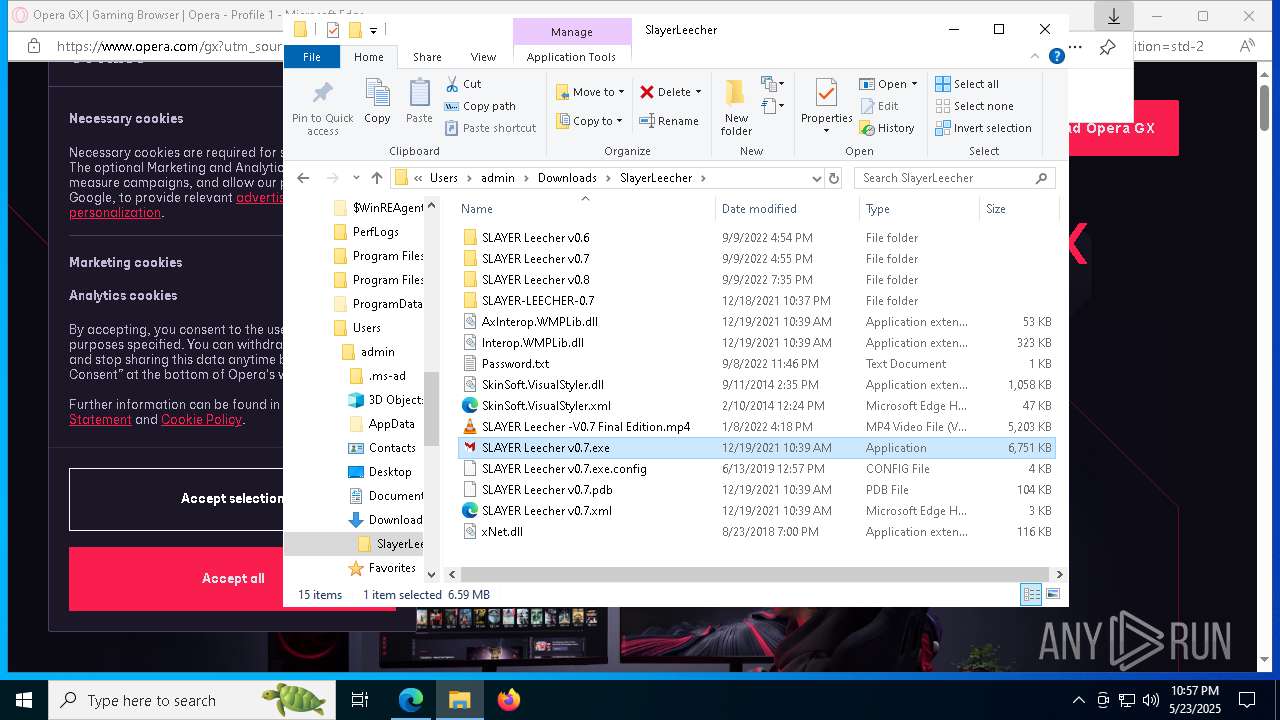
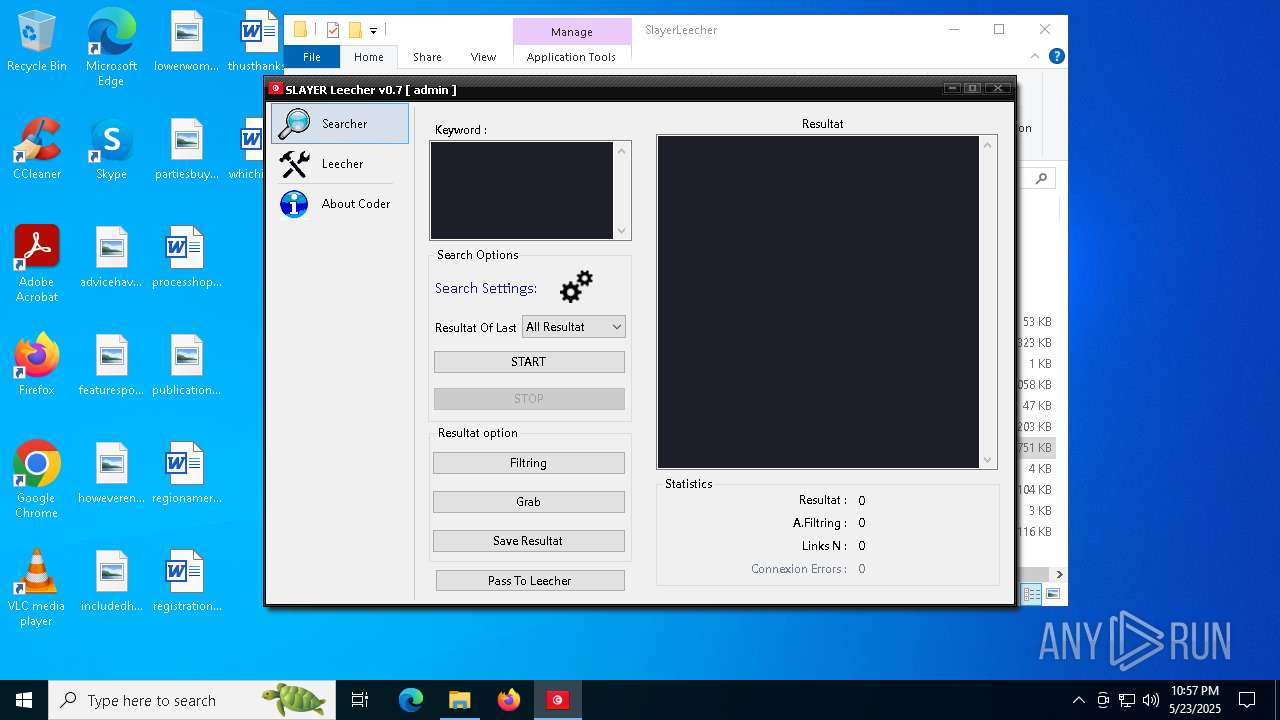
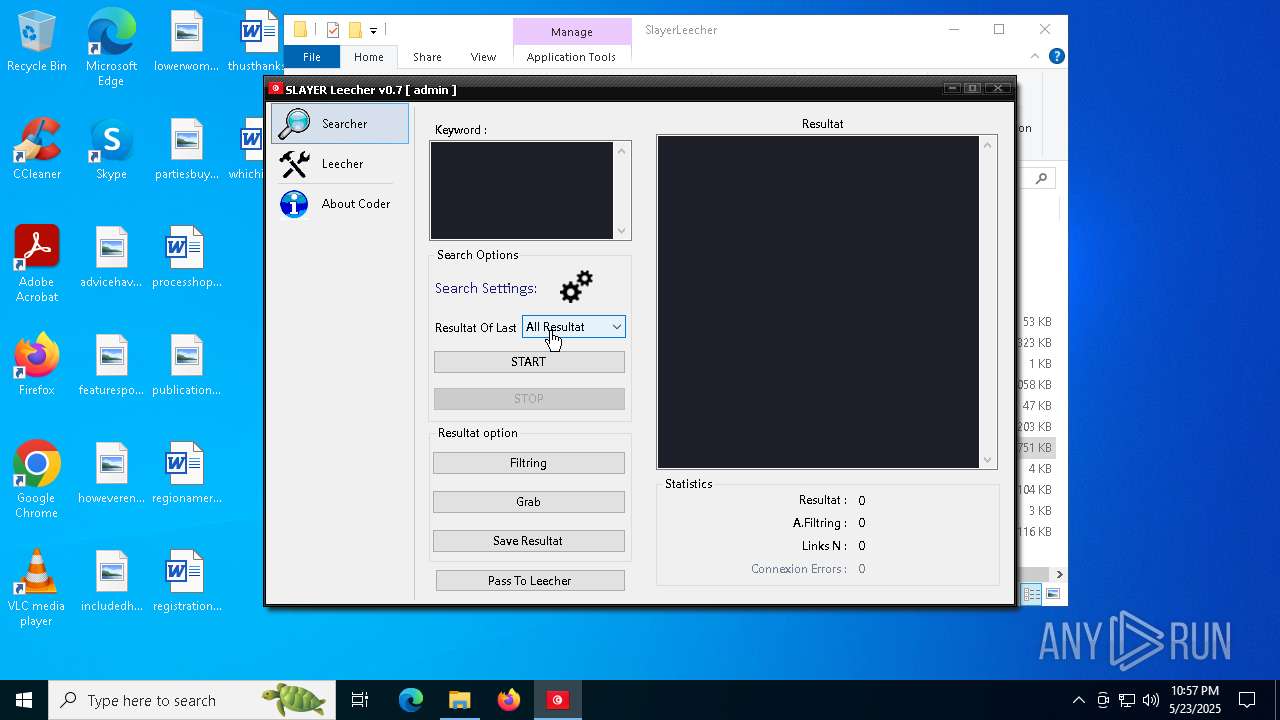
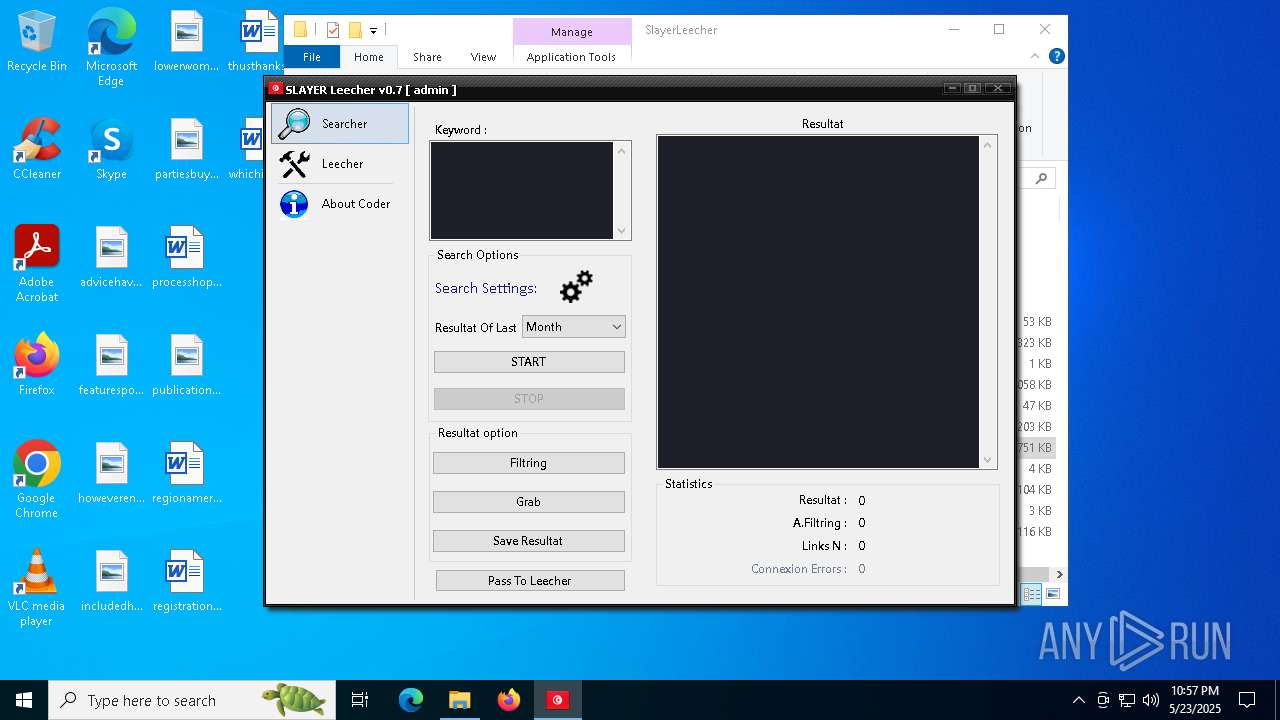
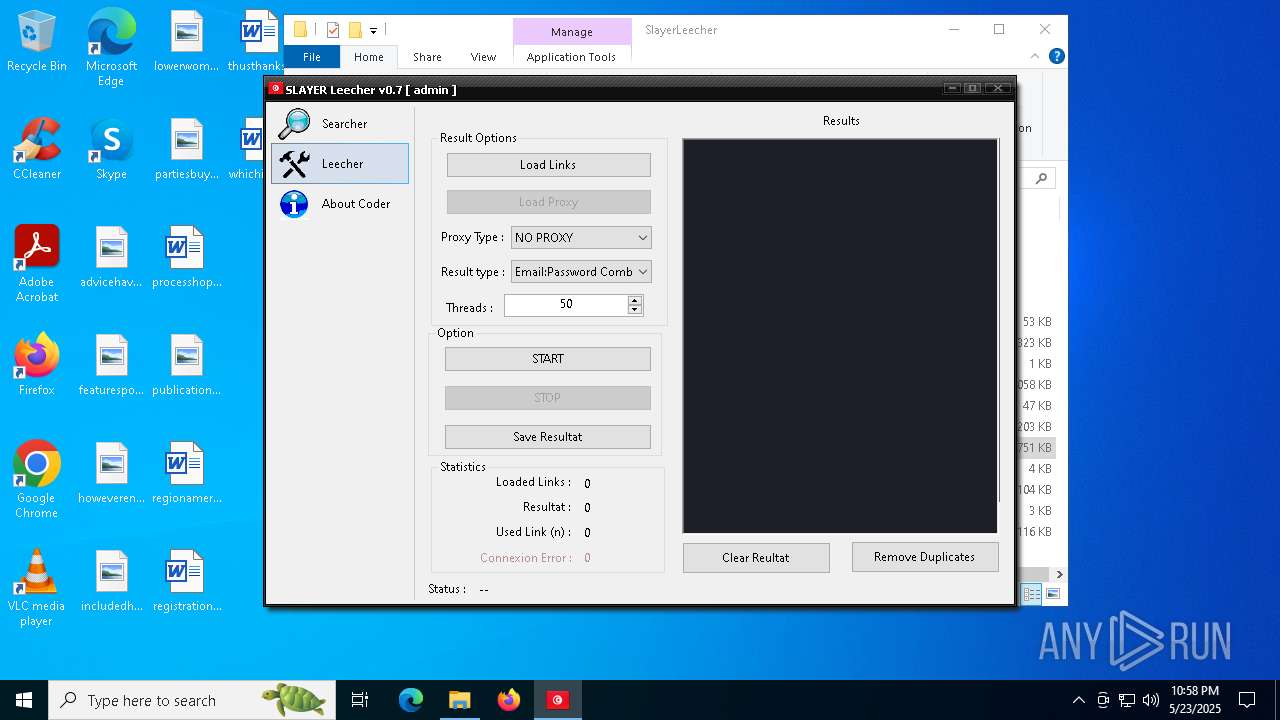
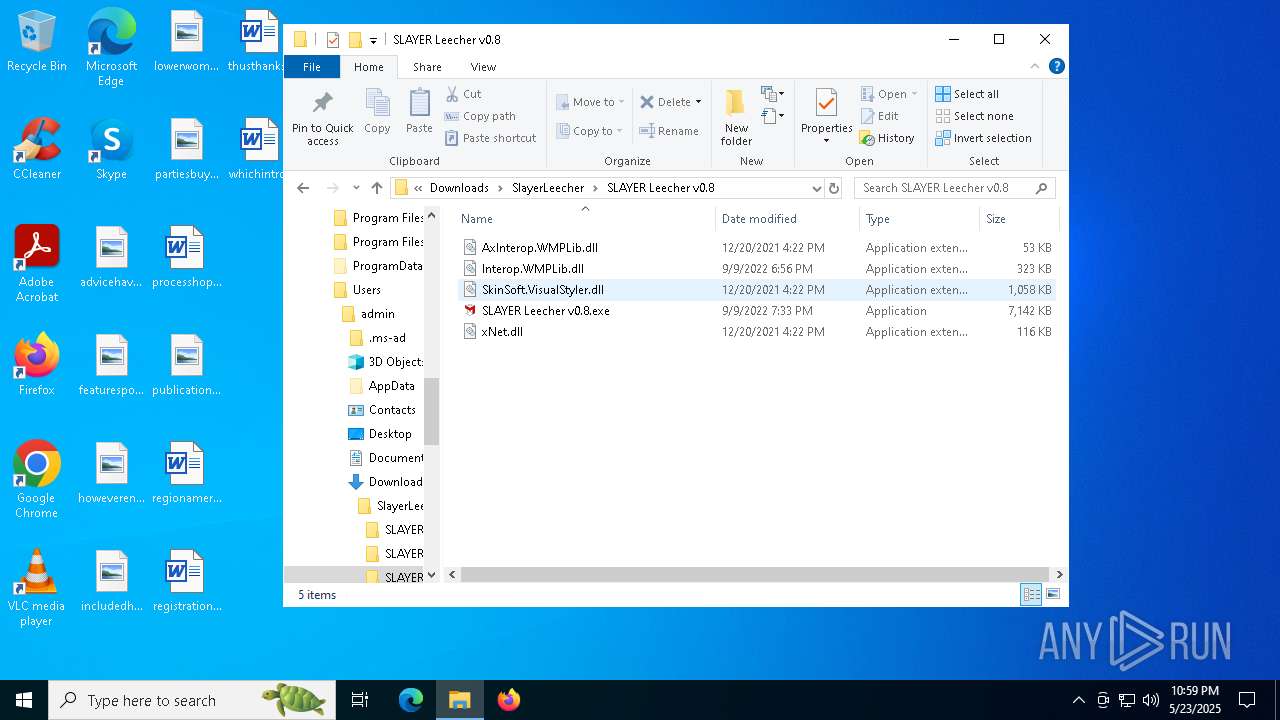
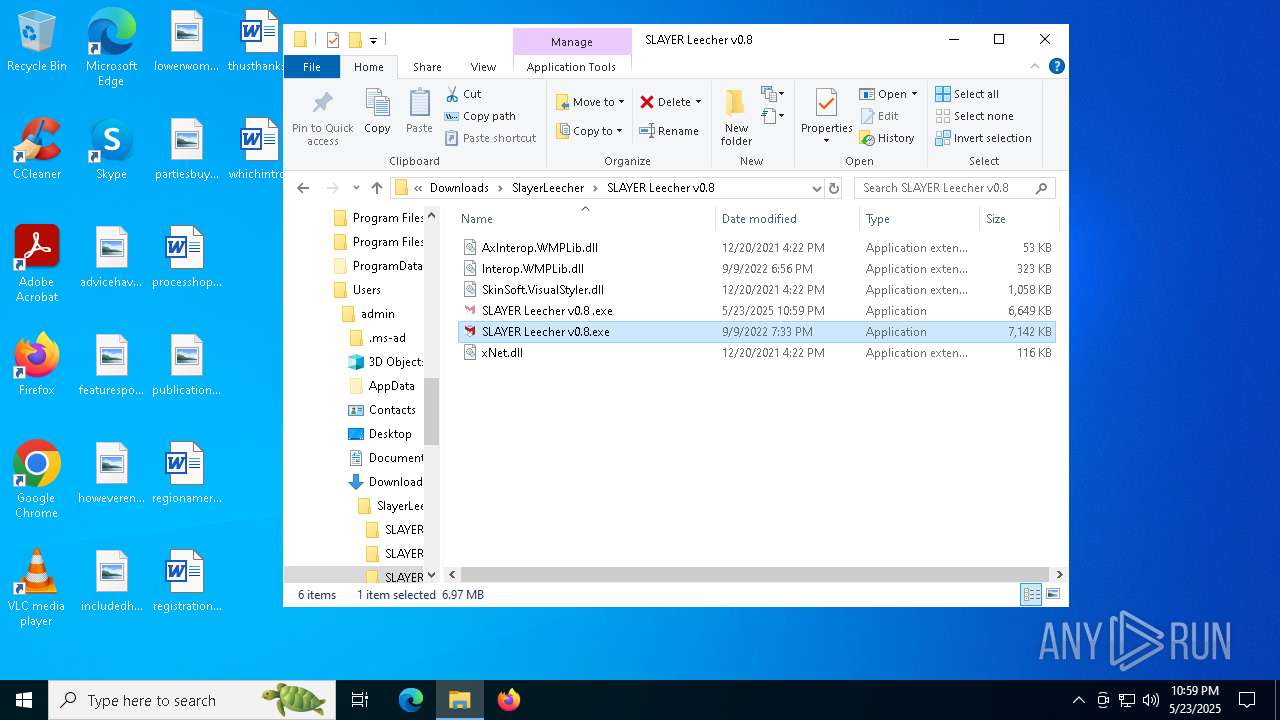
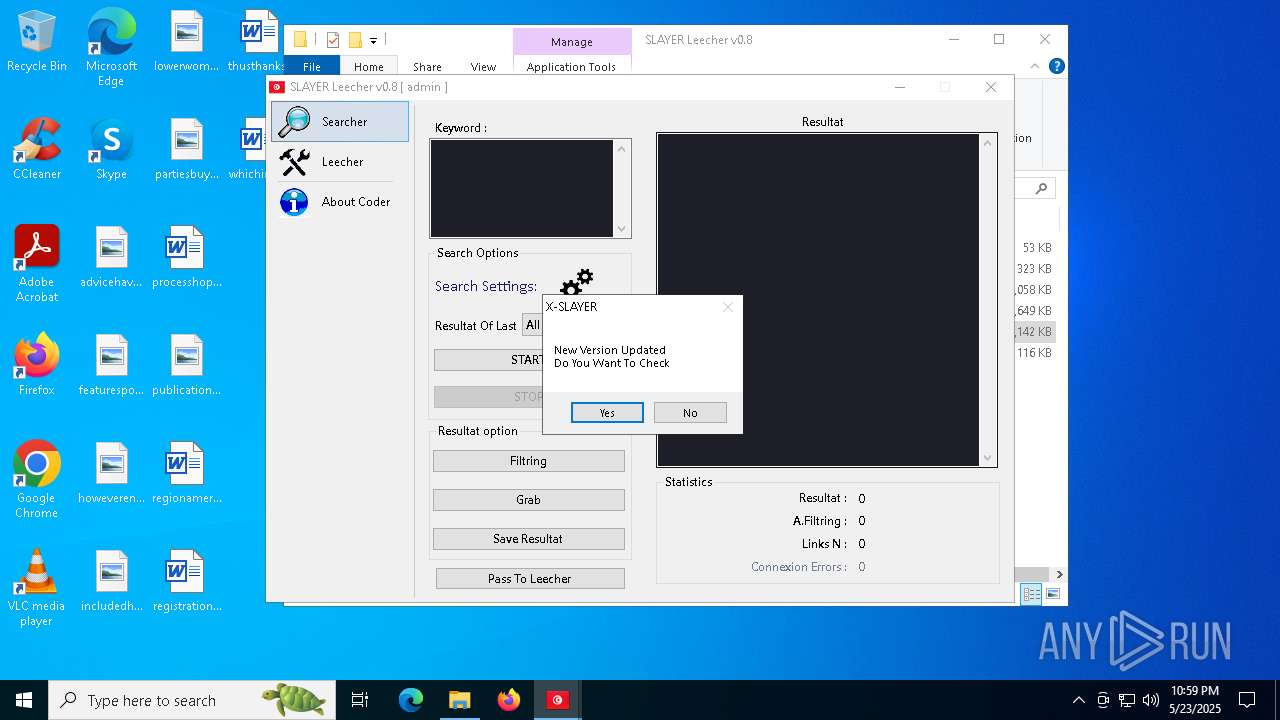
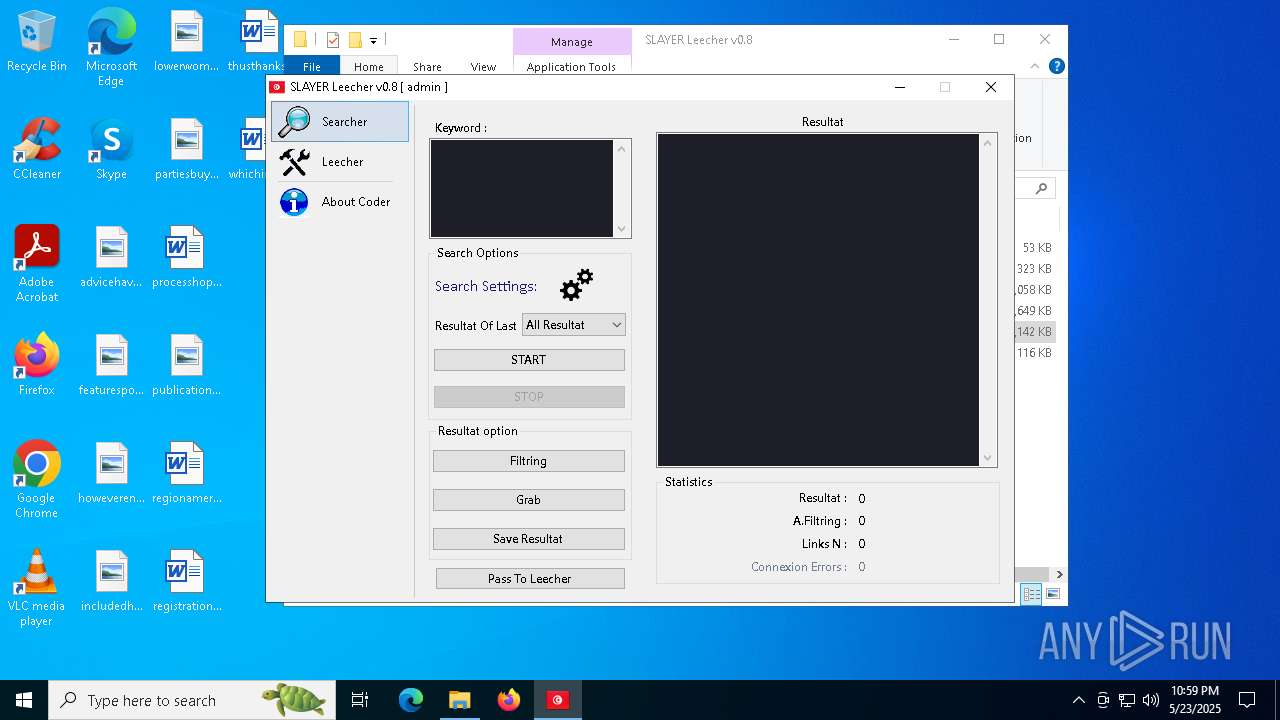
- SLAYER Leecher v0.8.exe (PID: 7508)
- explorer.exe (PID: 9072)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 1196)
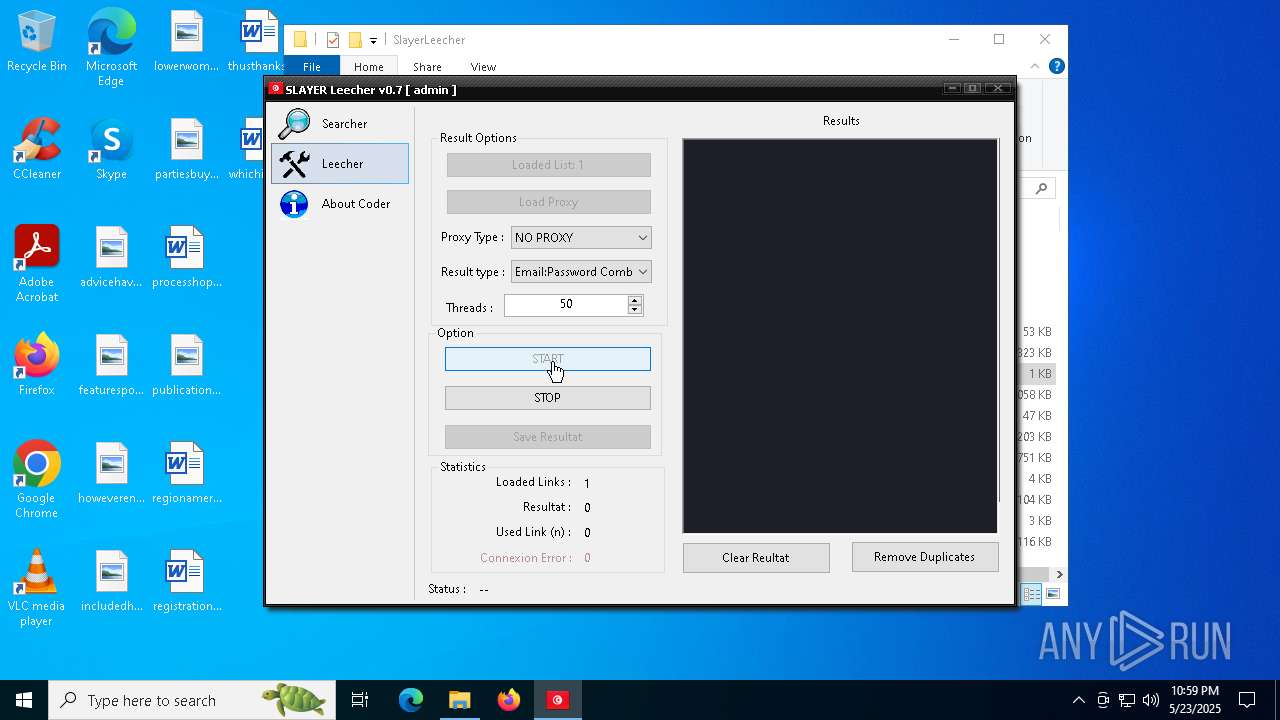
Executes application which crashes
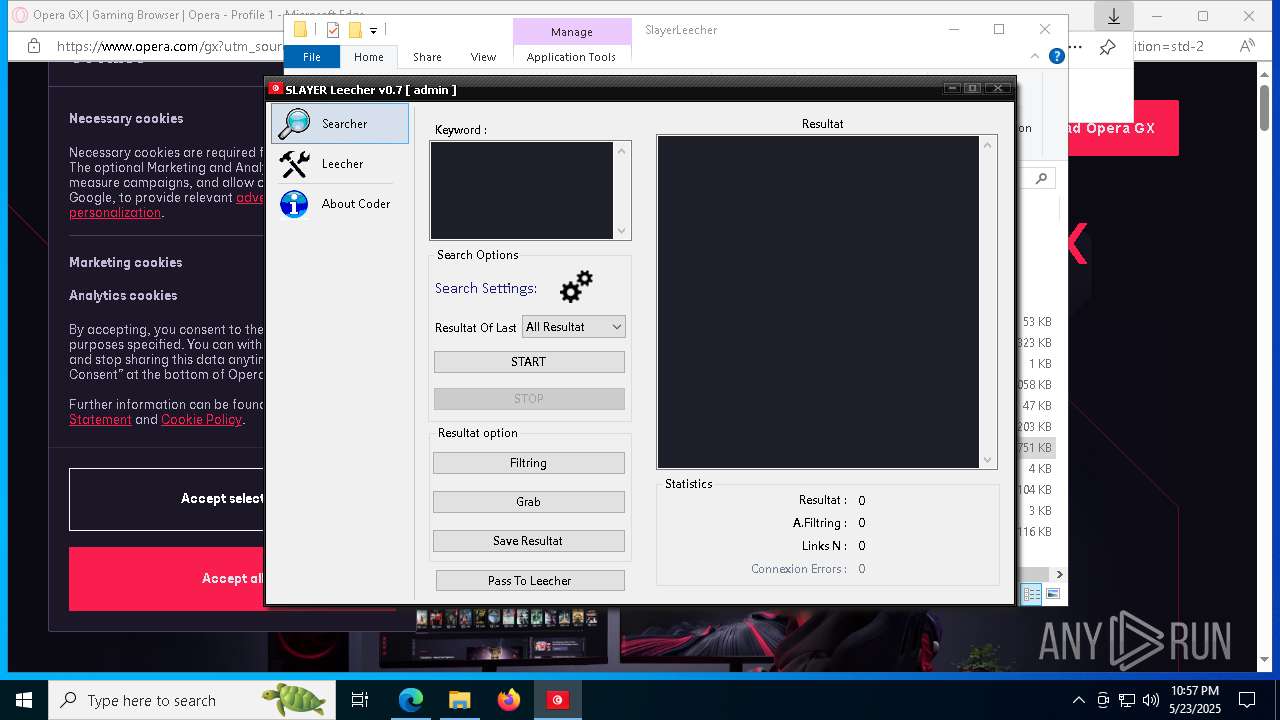
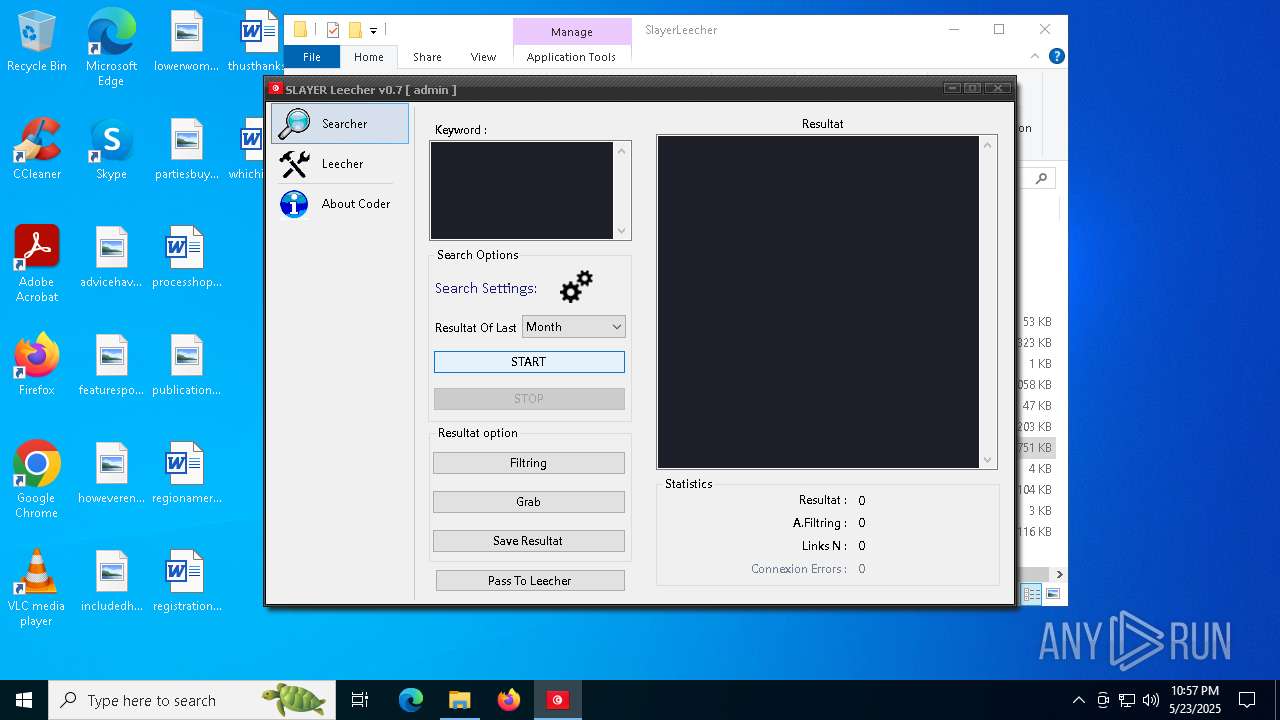
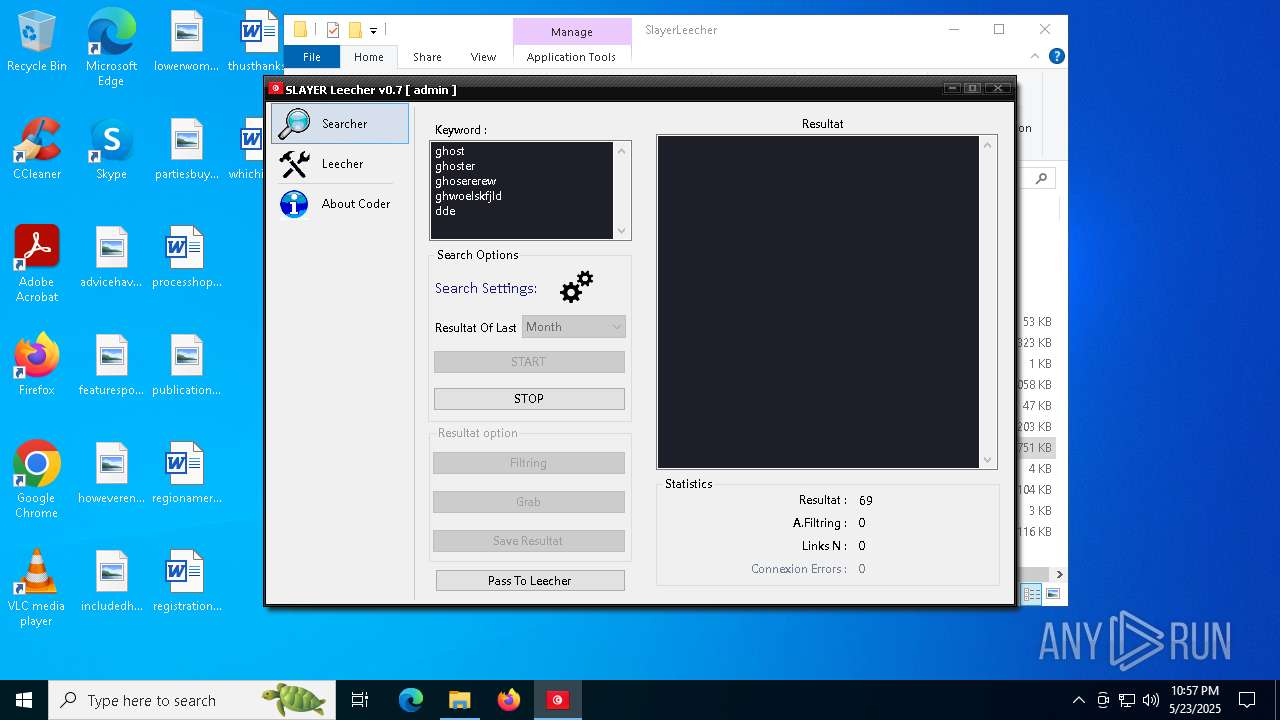
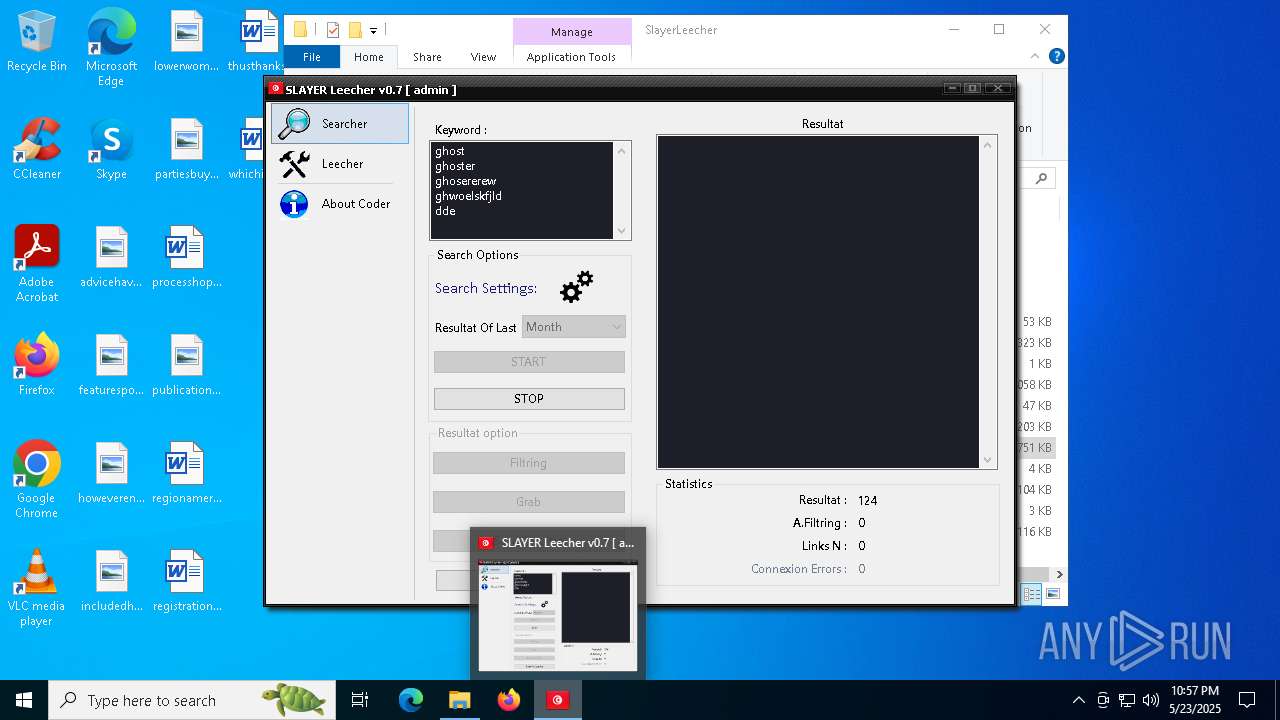
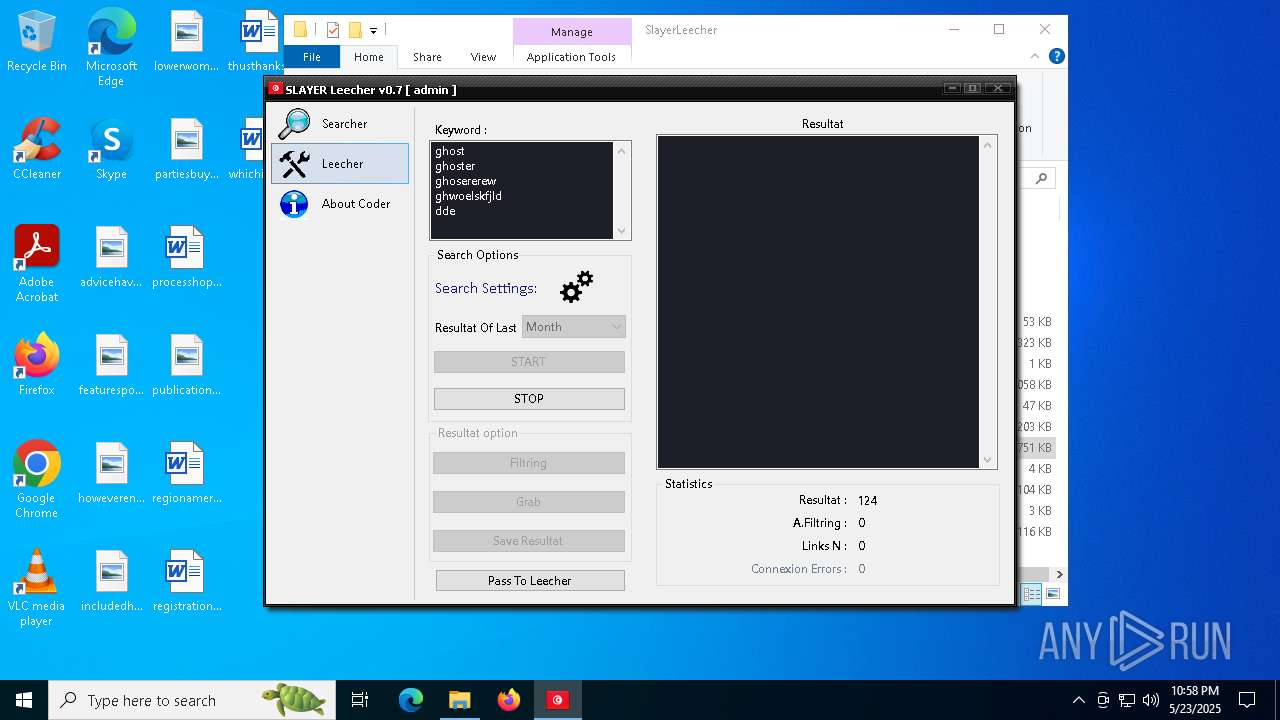
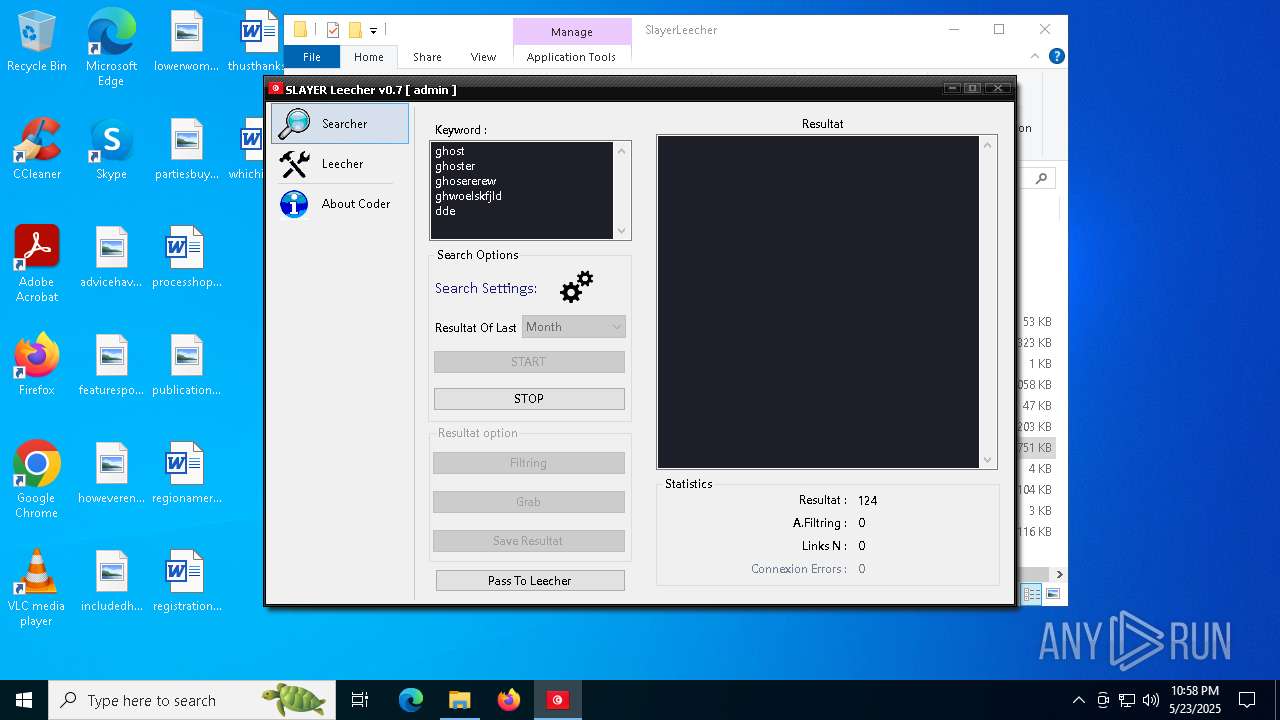
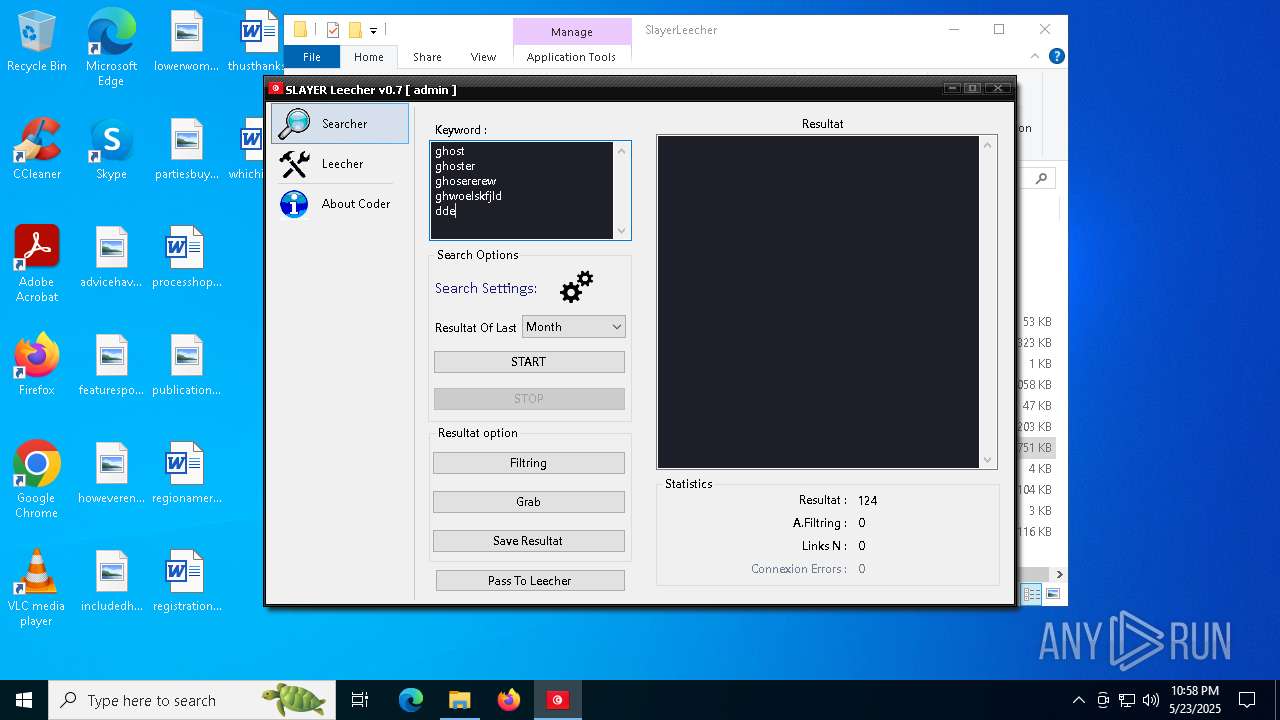
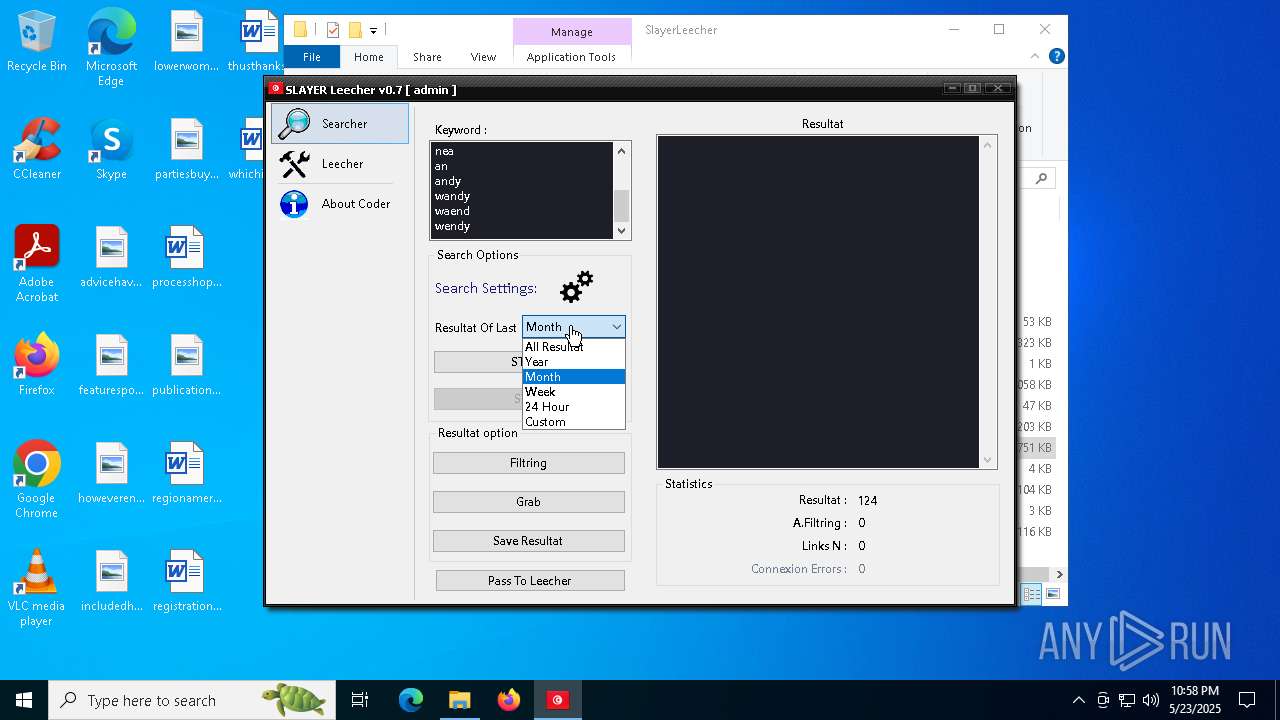
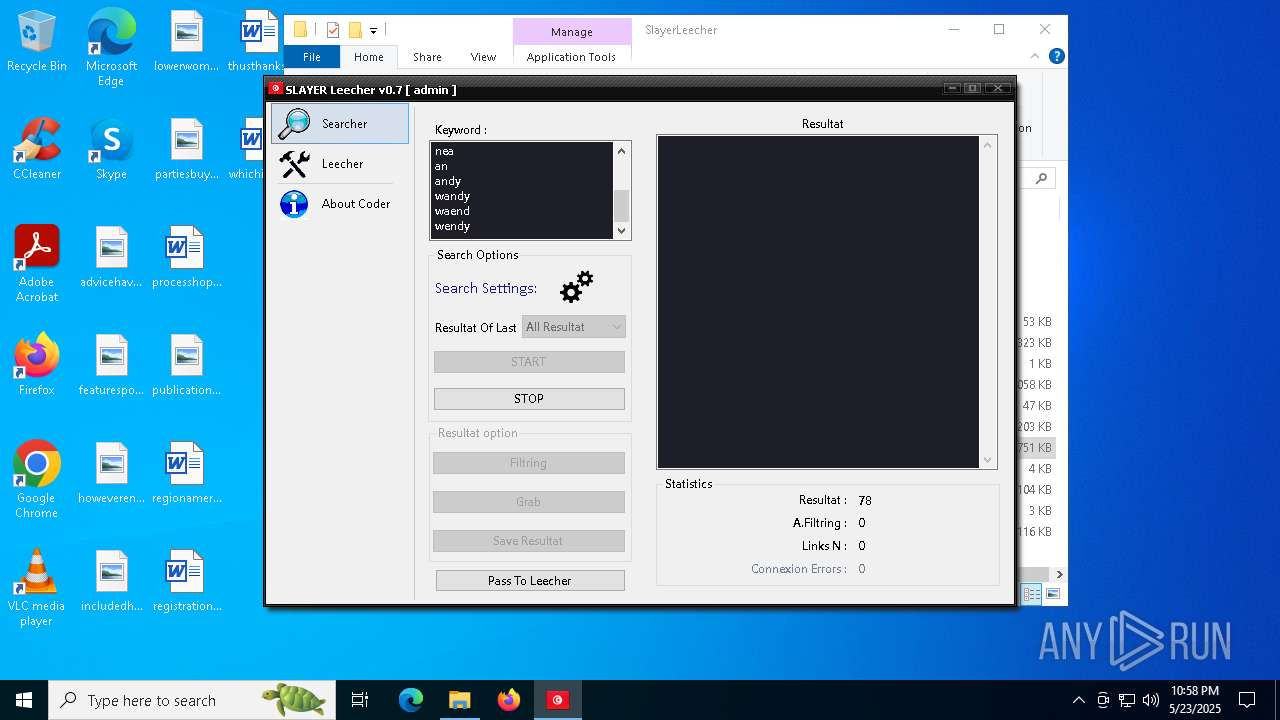
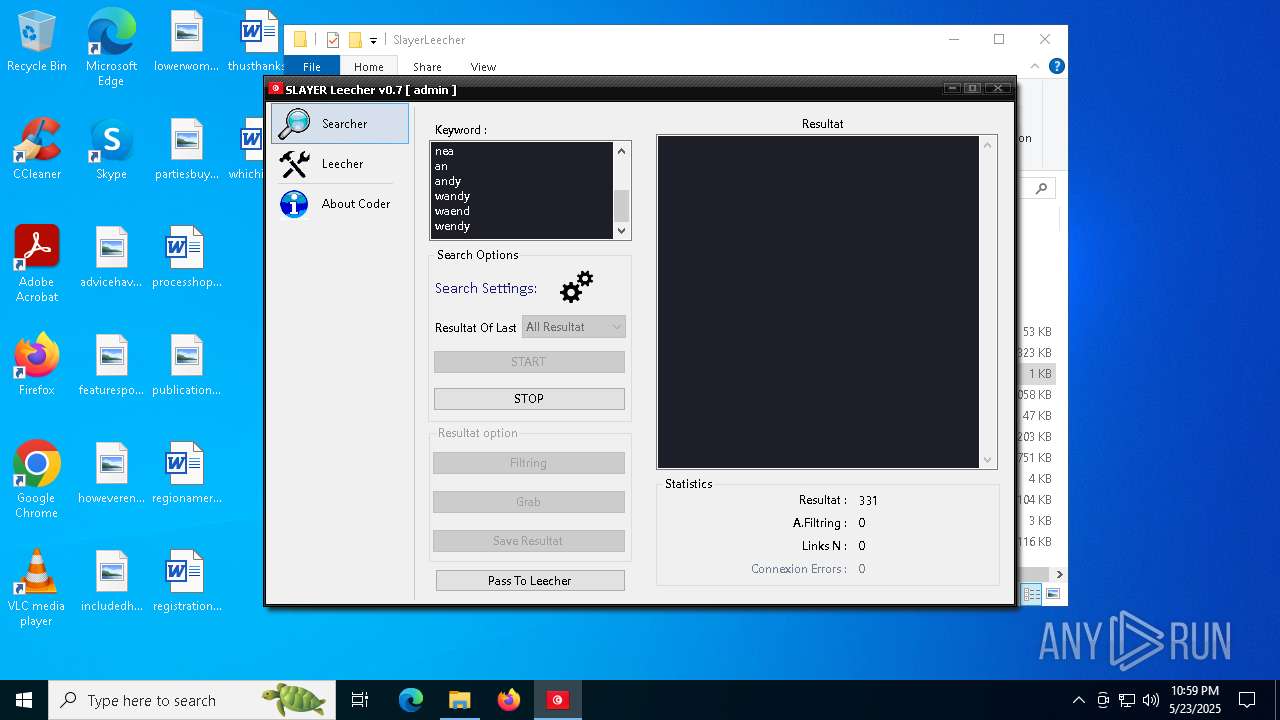
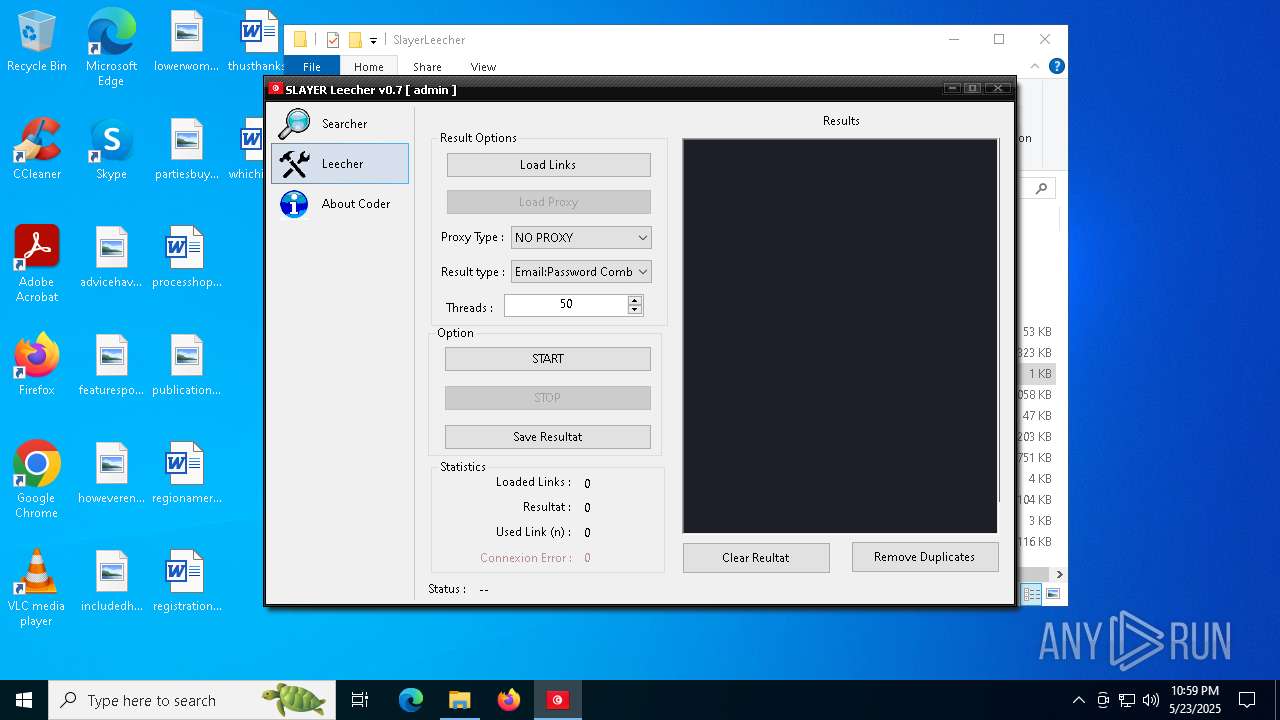
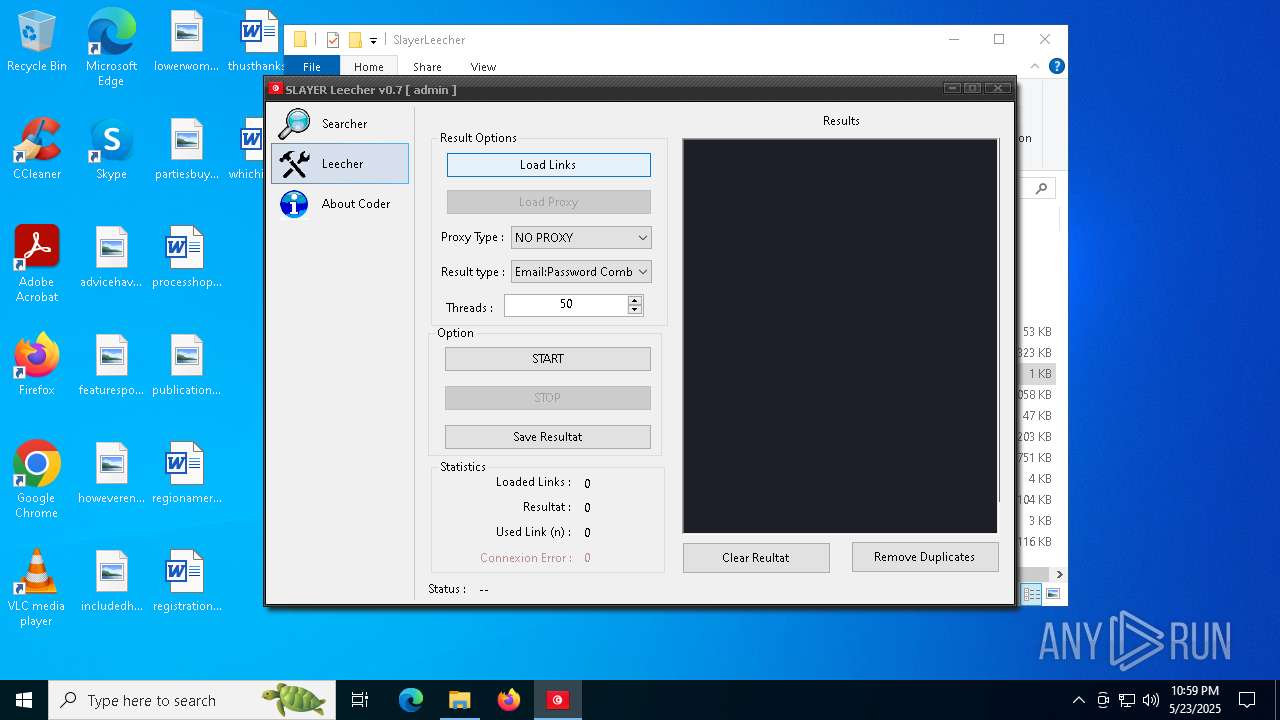
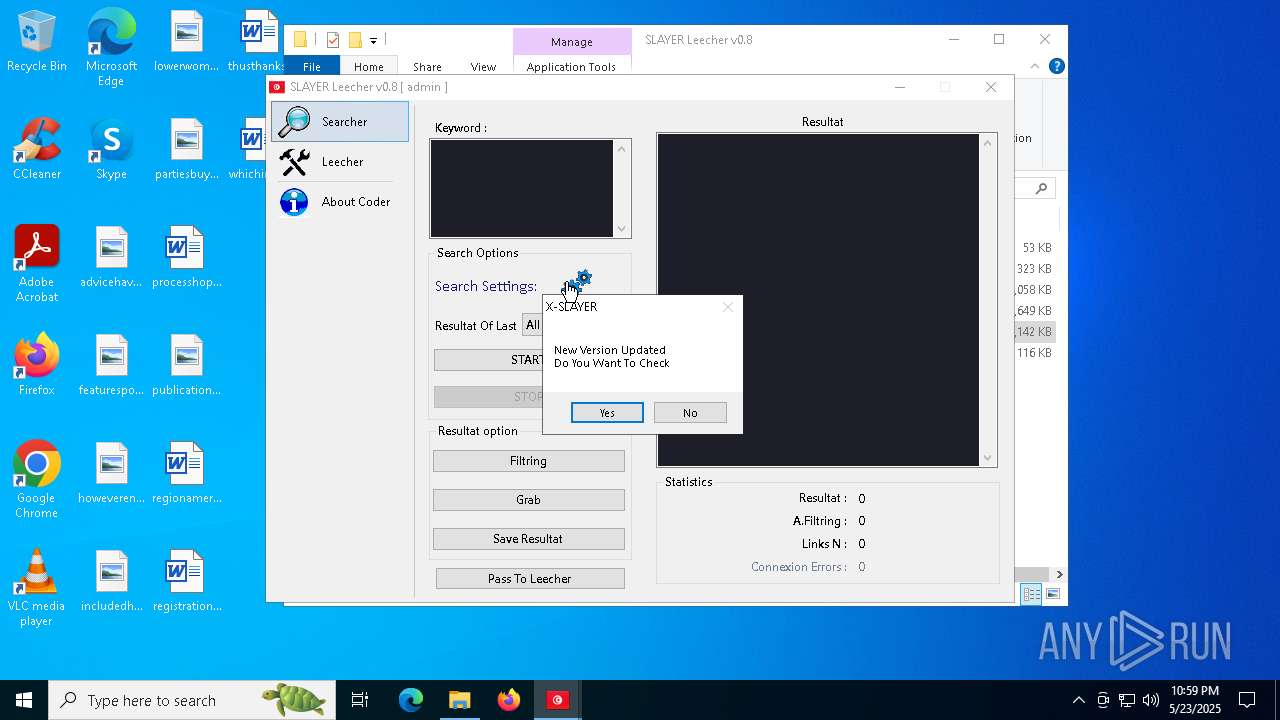
- SLAYER Leecher v0.7.exe (PID: 672)
Executable content was dropped or overwritten
- SLAYER Leecher v0.7.exe (PID: 672)
- Setup.exe (PID: 7416)
- SLAYER Leecher v0.8.exe (PID: 7508)
- svchost.exe (PID: 7304)
- explorer.exe (PID: 9072)
There is functionality for taking screenshot (YARA)
- SLAYER Leecher v0.7.exe (PID: 672)
Starts a Microsoft application from unusual location
- Setup.exe (PID: 7416)
- Setup.exe (PID: 9184)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- explorer.exe (PID: 9072)
Starts CMD.EXE for commands execution
- version.exe (PID: 4180)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5588)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 1704)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5588)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 3308)
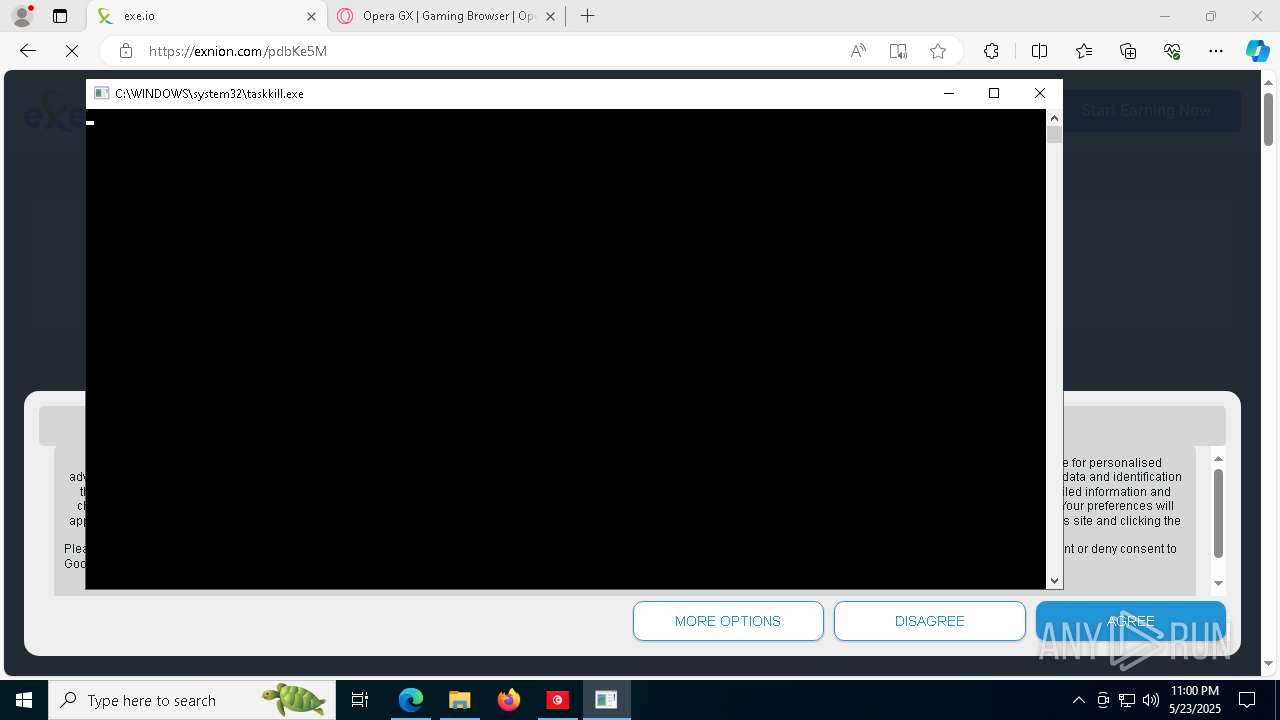
Uses TASKKILL.EXE to kill process
- dllhost.exe (PID: 3272)
Starts itself from another location
- explorer.exe (PID: 9072)
Uses NETSH.EXE to add a firewall rule or allowed programs
- explorer.exe (PID: 10332)
Connects to unusual port
- explorer.exe (PID: 10332)
INFO
Reads the computer name
- identity_helper.exe (PID: 8612)
Application launched itself
- msedge.exe (PID: 2692)
- msedge.exe (PID: 7128)
Checks supported languages
- identity_helper.exe (PID: 8612)
Reads the software policy settings
- slui.exe (PID: 7740)
The sample compiled with english language support
- SLAYER Leecher v0.7.exe (PID: 672)
- msedge.exe (PID: 5176)
- svchost.exe (PID: 7304)
- explorer.exe (PID: 9072)
Executable content was dropped or overwritten
- msedge.exe (PID: 5176)
- WinRAR.exe (PID: 1196)
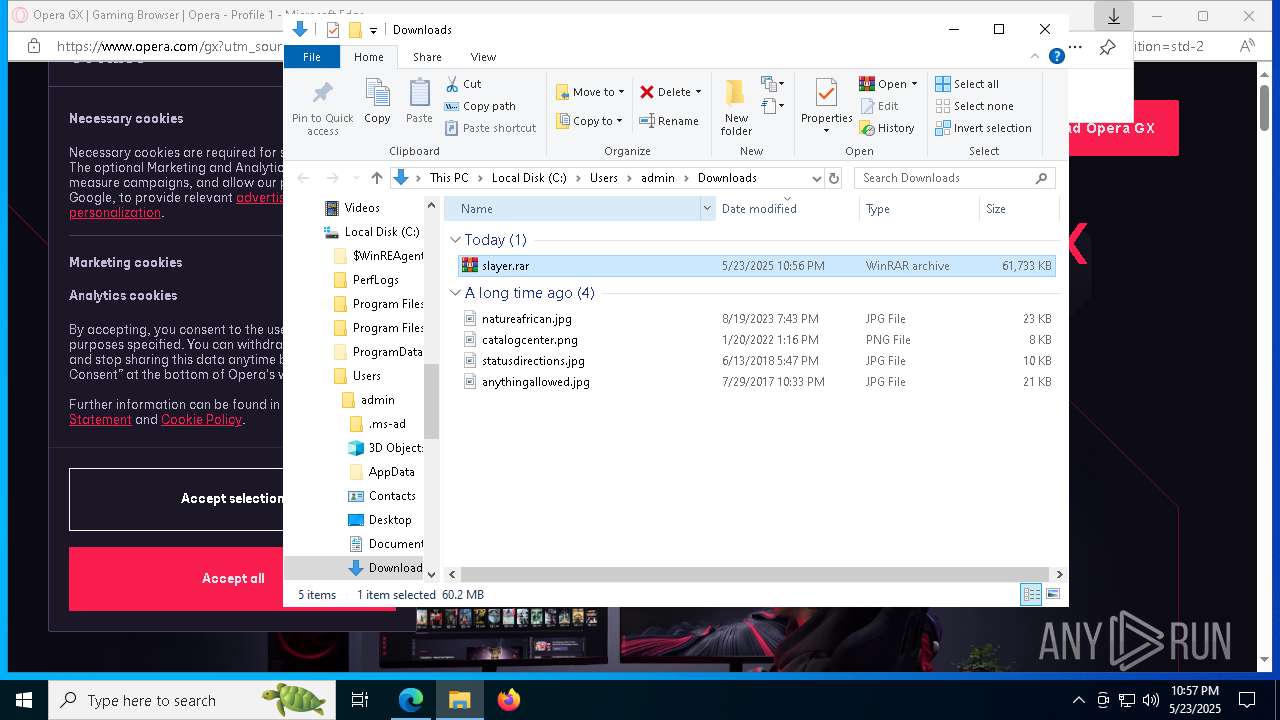
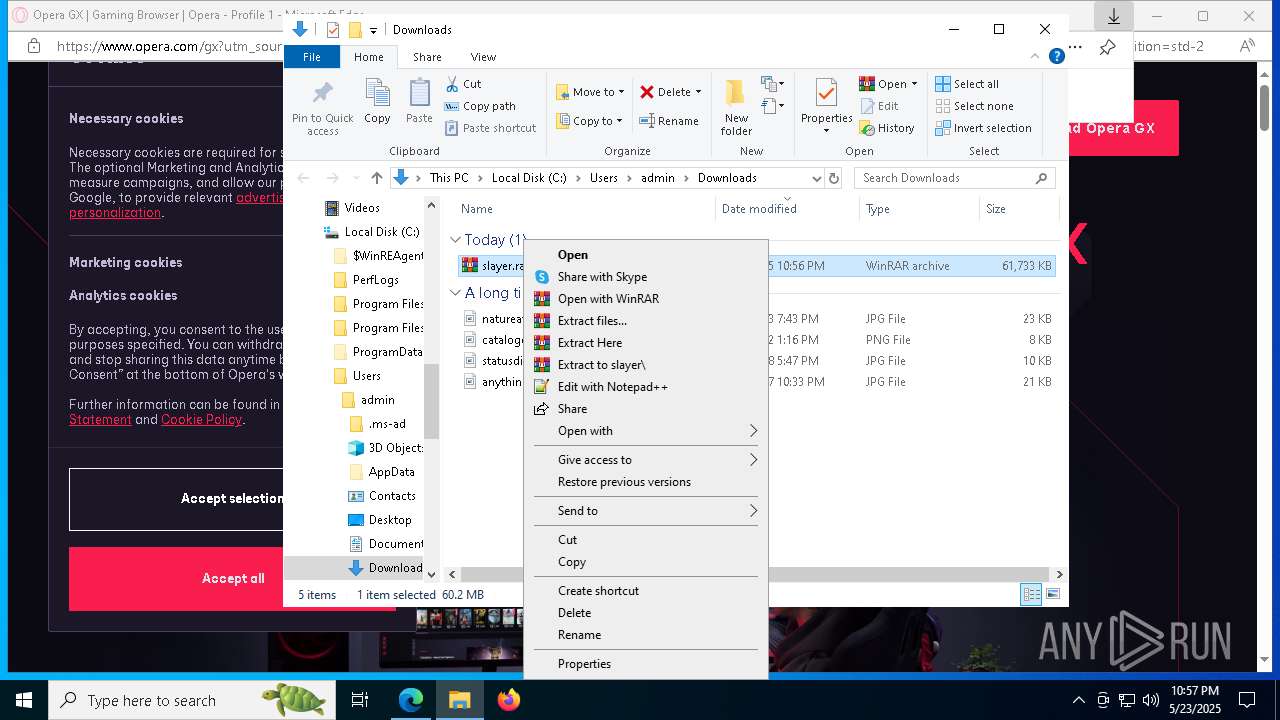
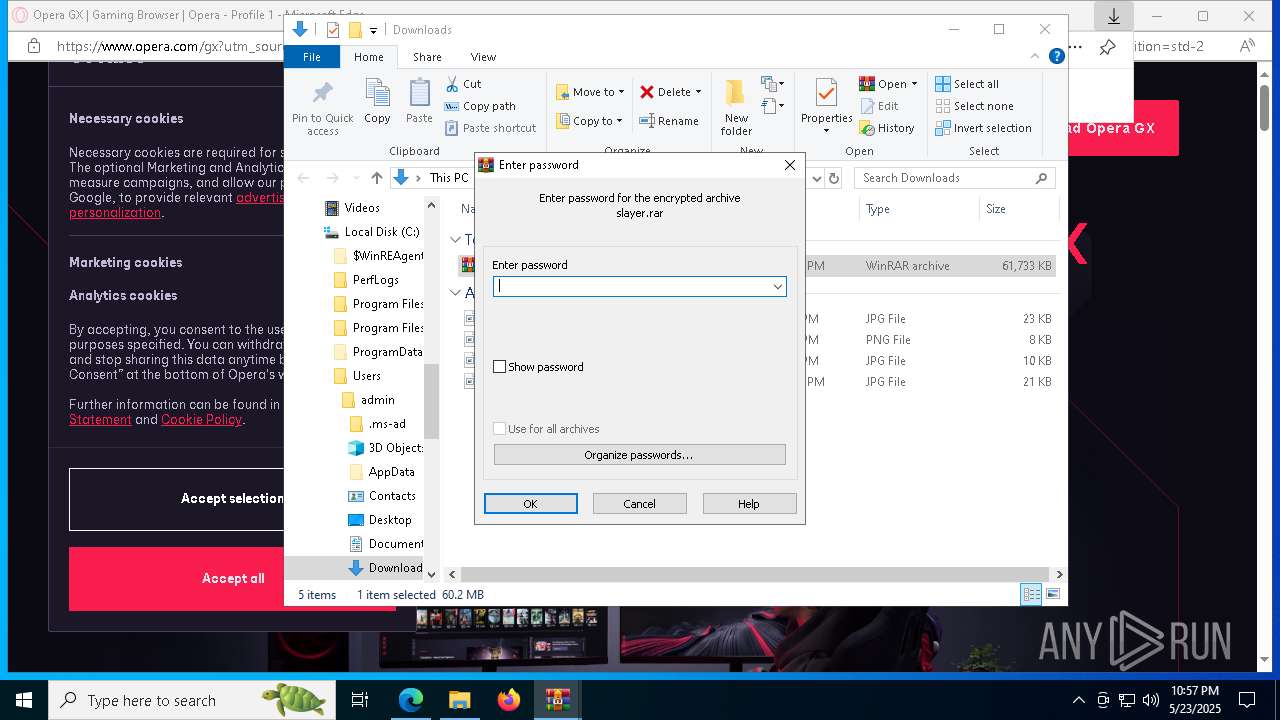
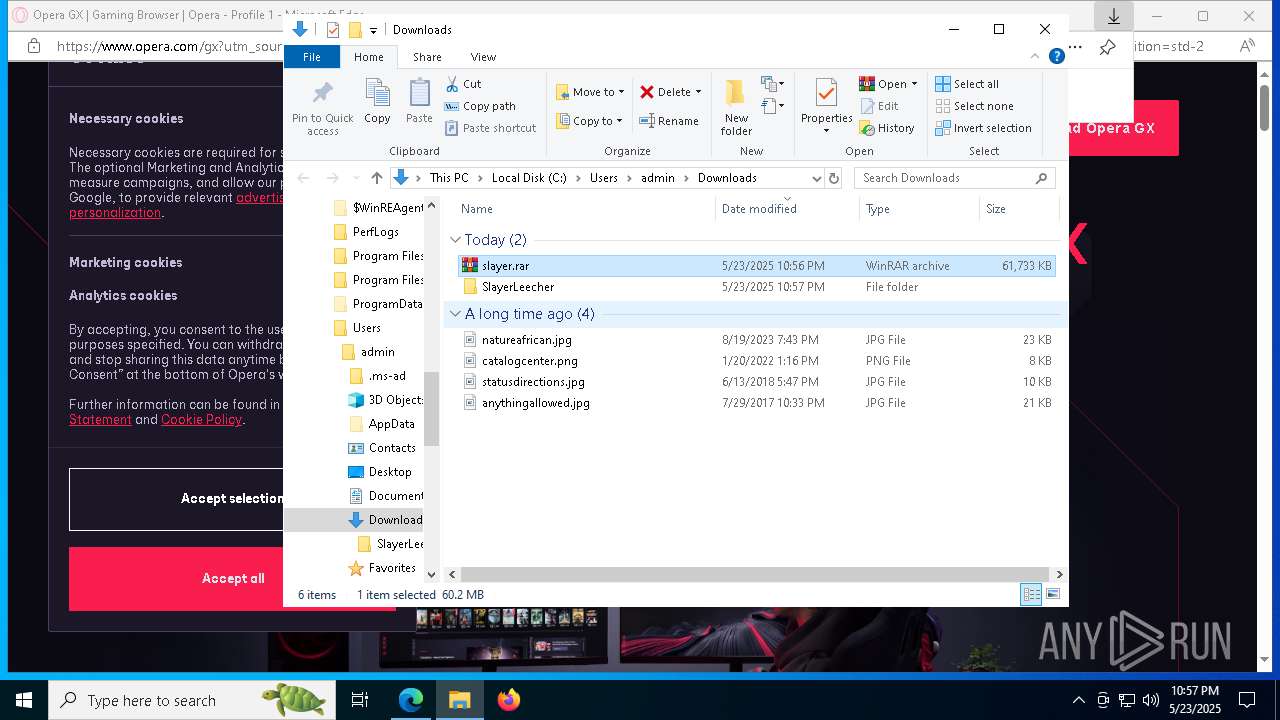
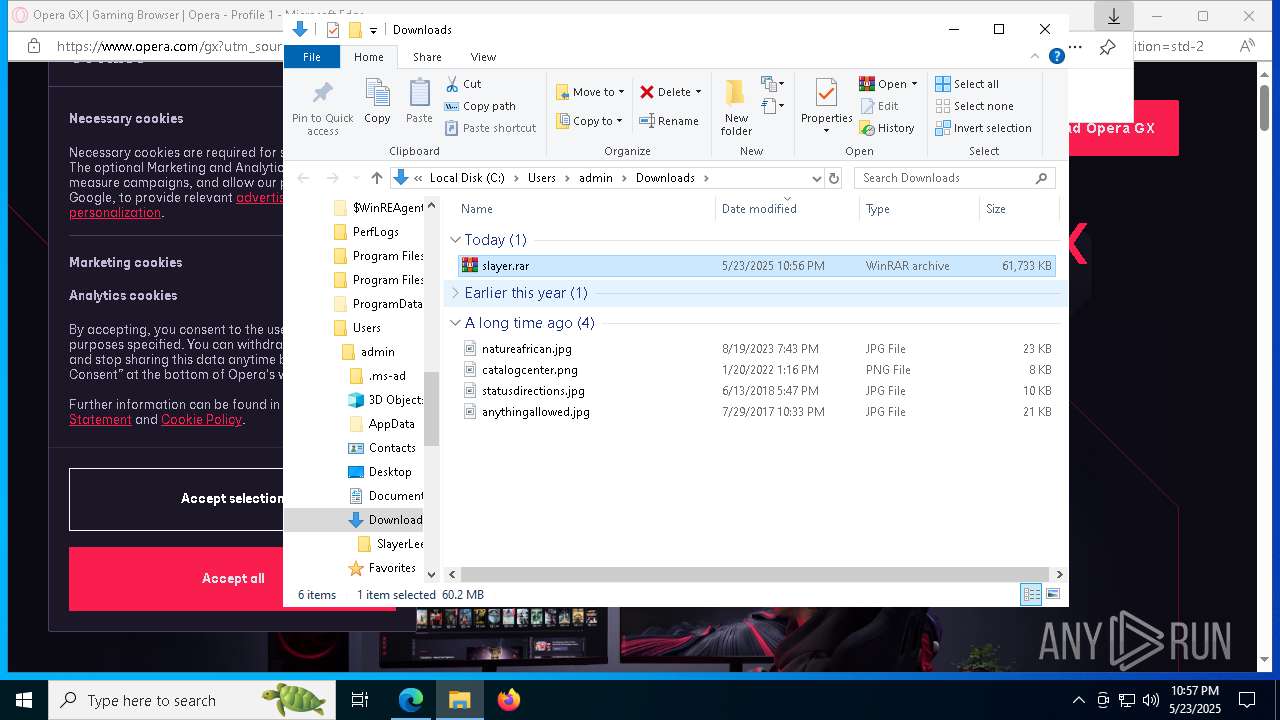
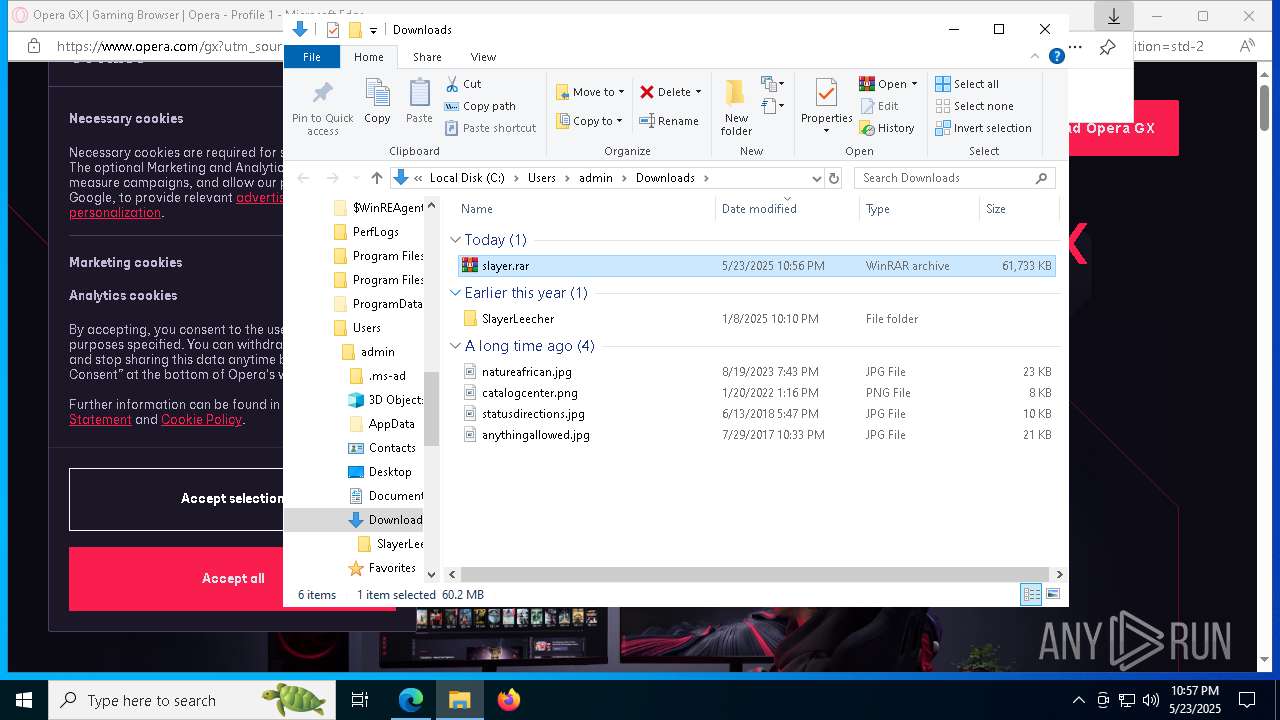
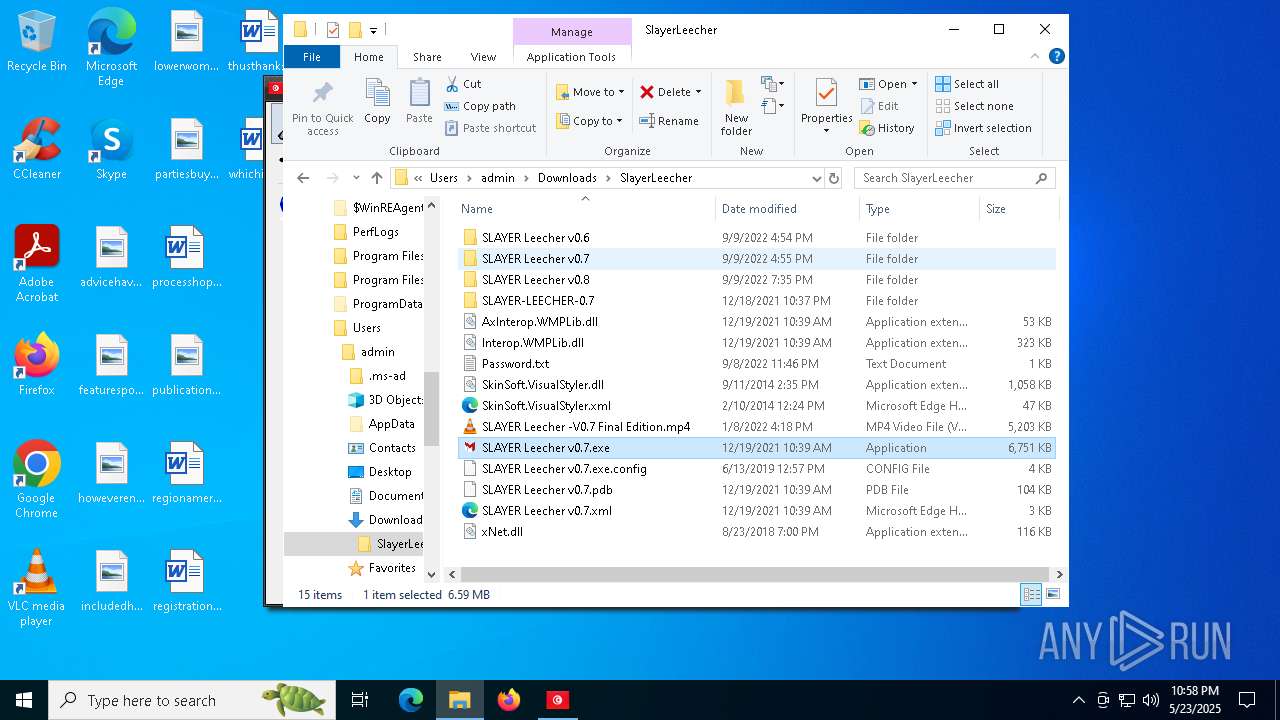
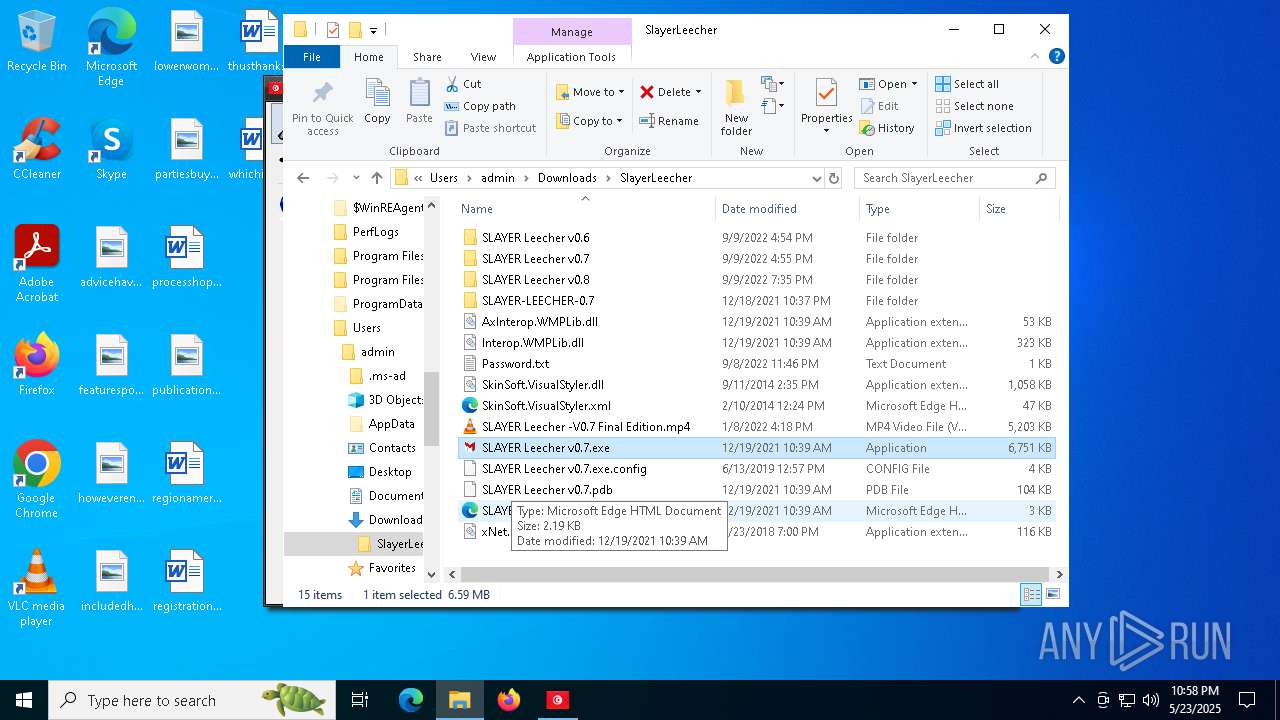
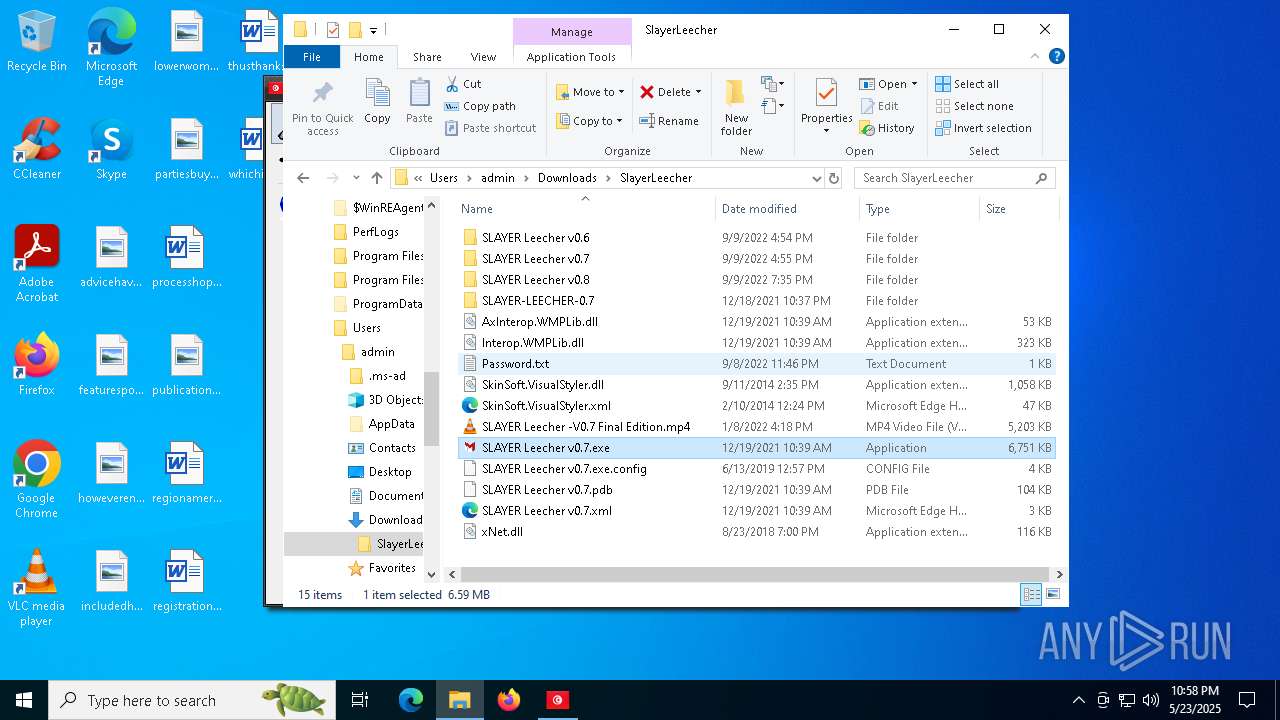
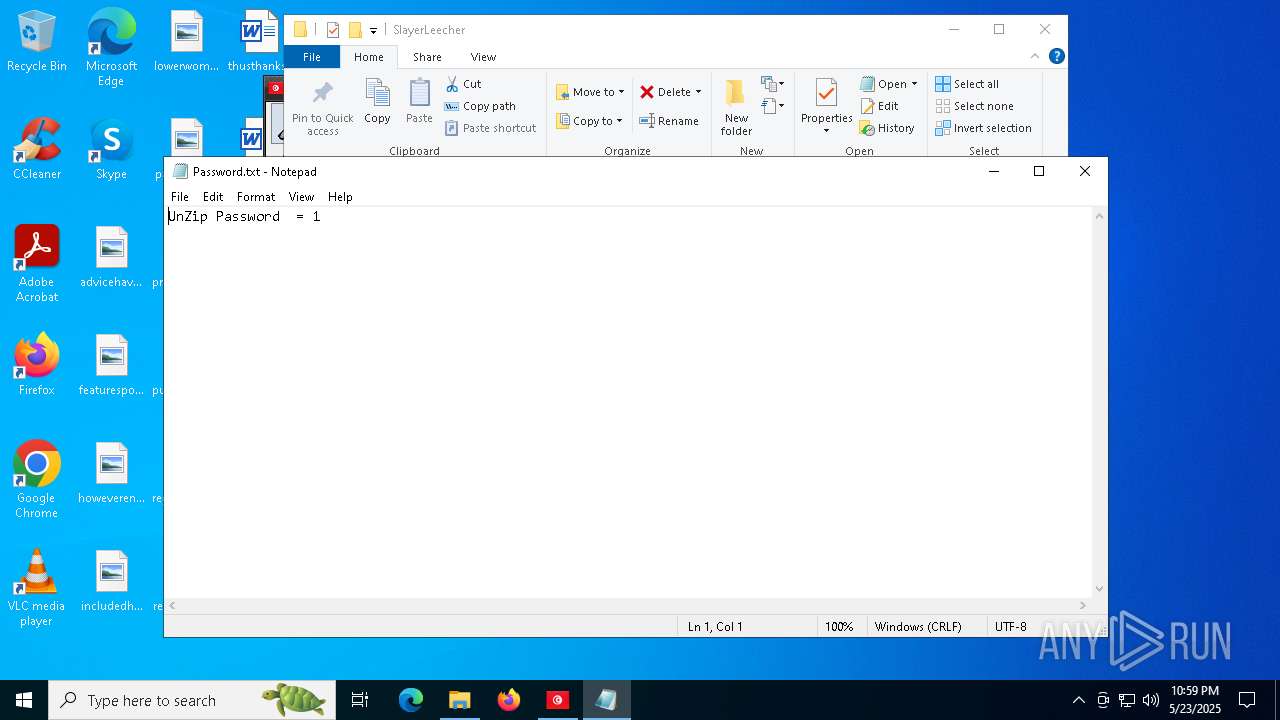
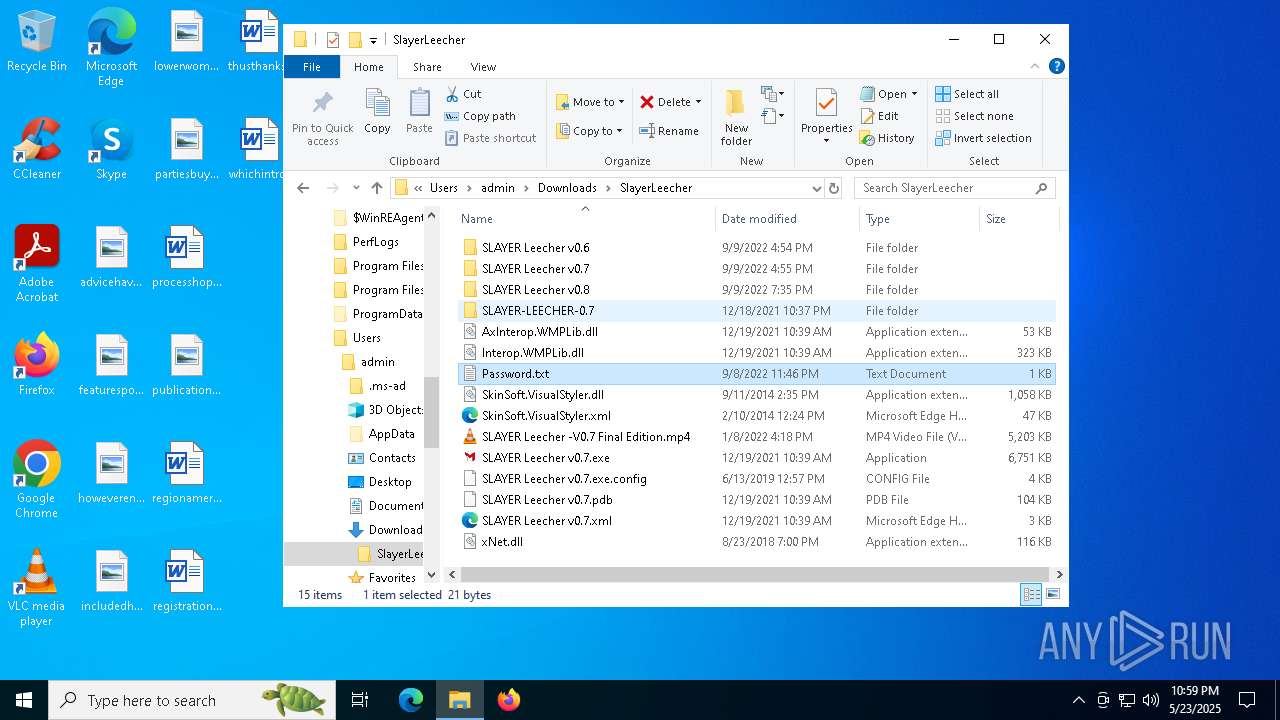
Manual execution by a user
- notepad.exe (PID: 496)
- SLAYER Leecher v0.8.exe (PID: 7508)
- WinRAR.exe (PID: 1196)
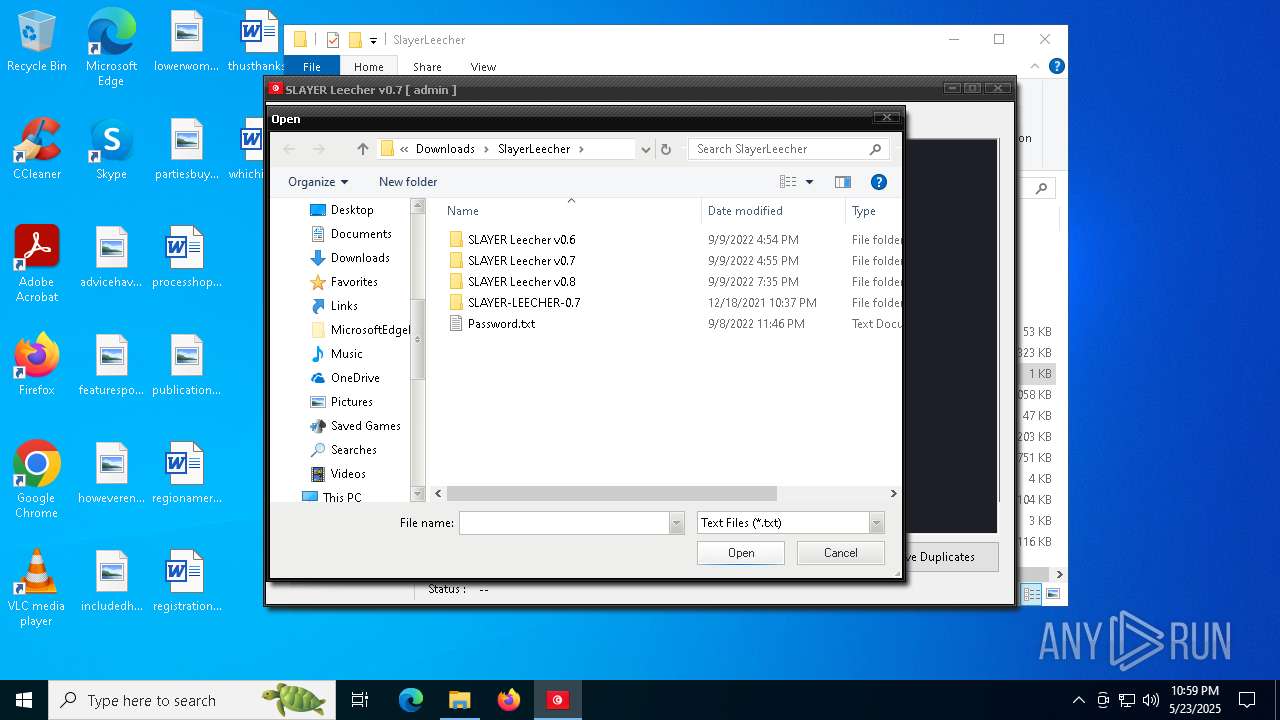
- SLAYER Leecher v0.7.exe (PID: 672)
Reads Environment values
- identity_helper.exe (PID: 8612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
340
Monitored processes
199
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6344 --field-trial-handle=2556,i,8082645456708475551,1131536458986311585,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
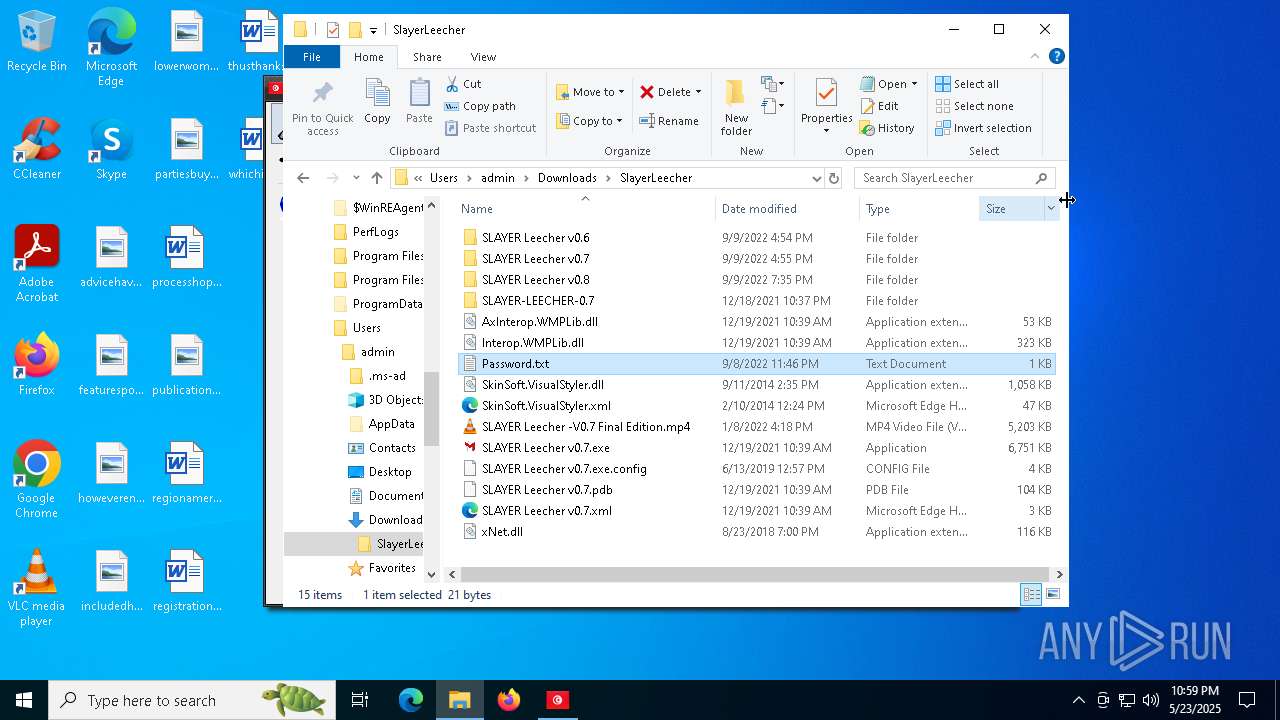
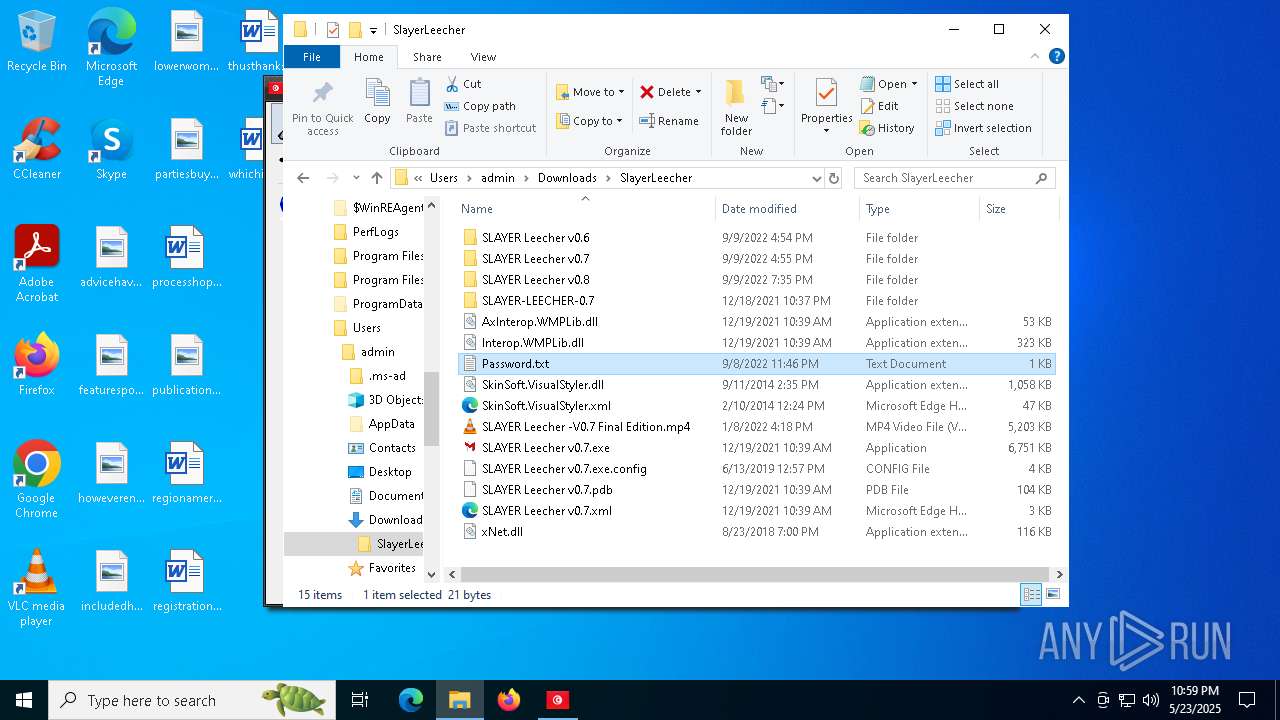
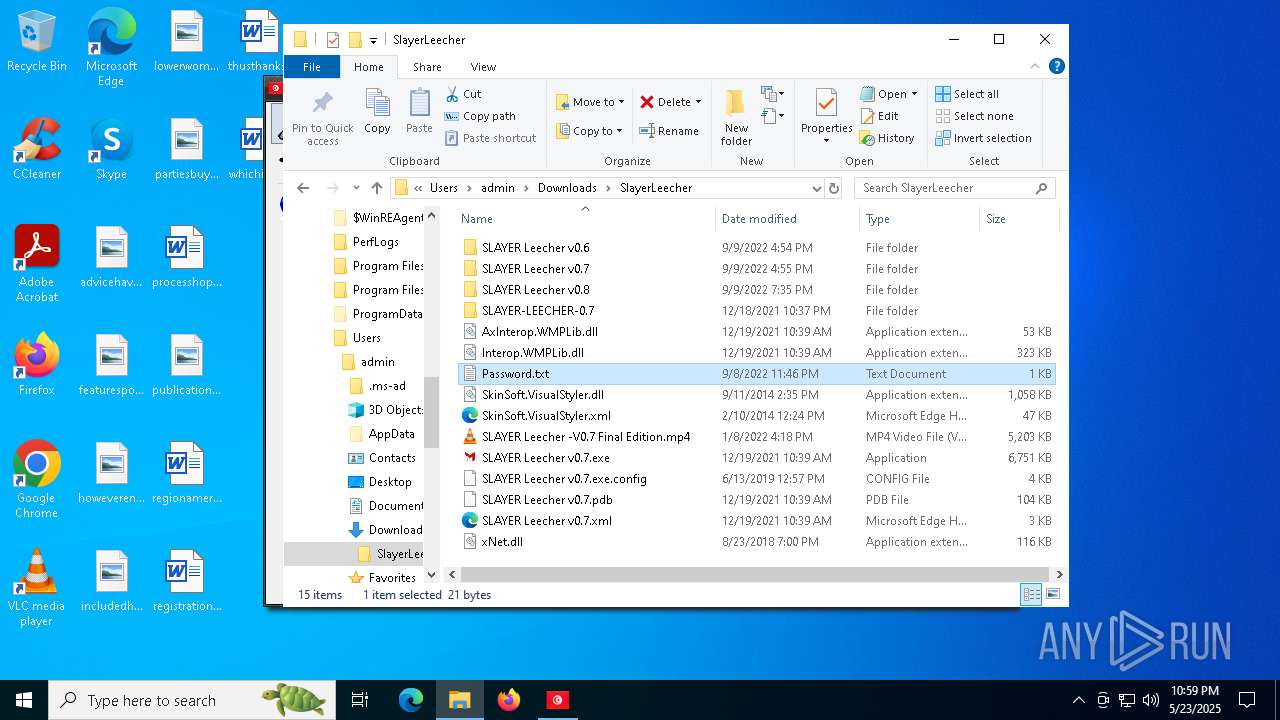
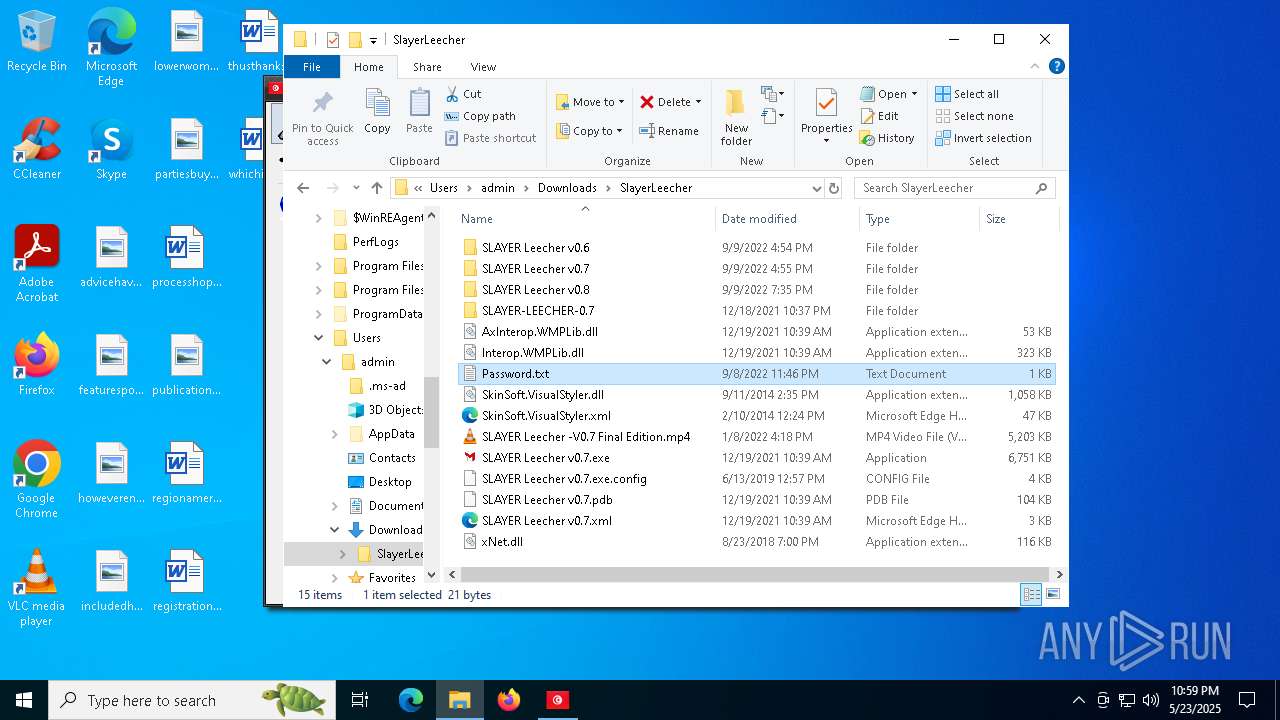
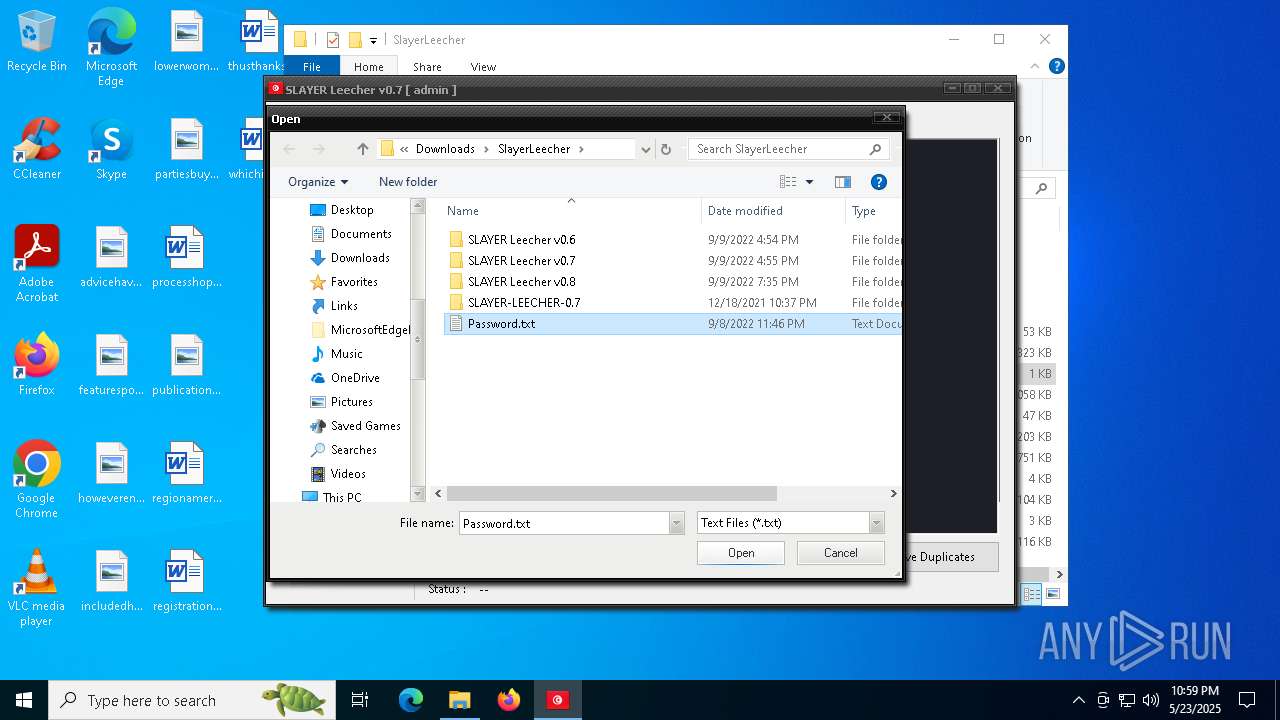
| 496 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\SlayerLeecher\Password.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
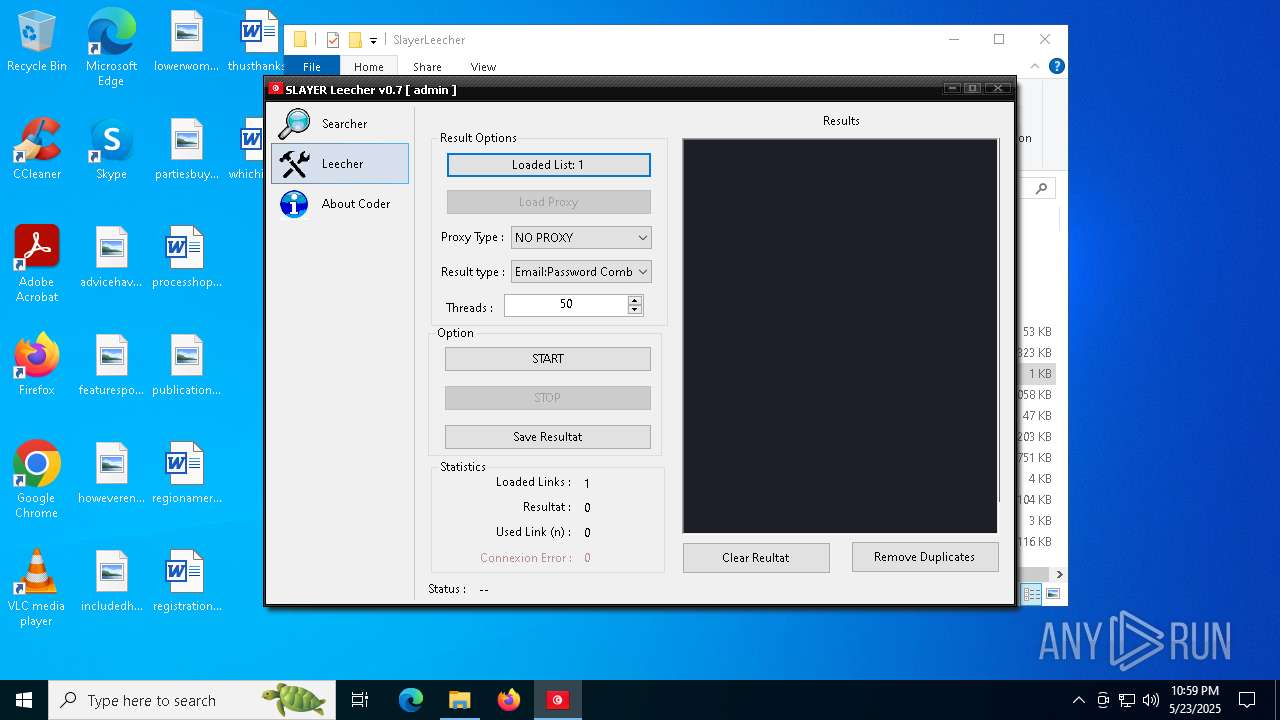
| 672 | "C:\Users\admin\Downloads\SlayerLeecher\SLAYER Leecher v0.7.exe" | C:\Users\admin\Downloads\SlayerLeecher\SLAYER Leecher v0.7.exe | explorer.exe | ||||||||||||
User: admin Company: Iheb Briki Integrity Level: MEDIUM Description: SLAYER Leecher Exit code: 3762504530 Version: 0.4.1 Modules
| |||||||||||||||
| 800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --mojo-platform-channel-handle=8416 --field-trial-handle=2556,i,8082645456708475551,1131536458986311585,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=5932 --field-trial-handle=2556,i,8082645456708475551,1131536458986311585,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --mojo-platform-channel-handle=6360 --field-trial-handle=2352,i,16032814996060392508,12171735719761972655,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
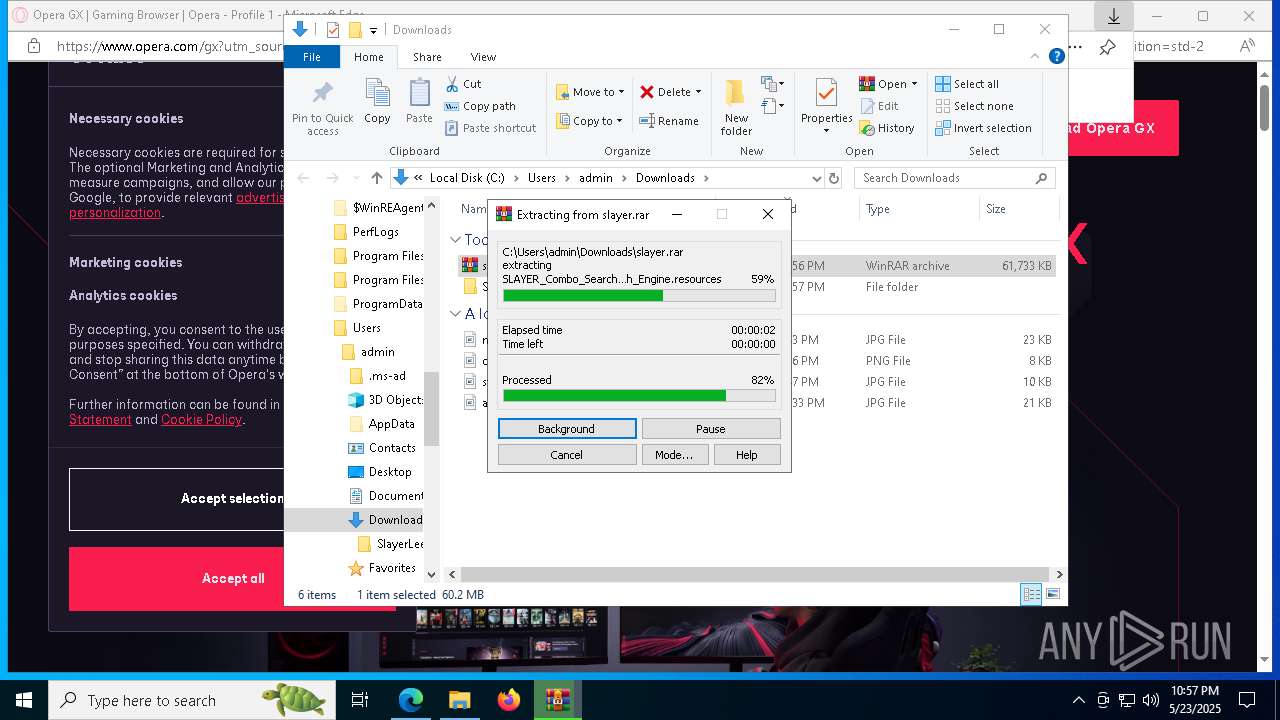
| 1196 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\slayer.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5384 --field-trial-handle=2556,i,8082645456708475551,1131536458986311585,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
72 370
Read events
72 129
Write events
238
Delete events
3
Modification events
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EAC270C96B942F00 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E15E78C96B942F00 | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B19A3CFA-C8BA-4967-ACD2-54C10A1BF41A} | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {56382216-3F02-4E05-9D21-1A18B1BEF787} | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FF9F8DD6-E492-40C2-AB45-BFAA4E003948} | |||
| (PID) Process: | (2692) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1CB4708D-B392-455D-8C10-24D5EB8C4E55} | |||
Executable files
80
Suspicious files
966
Text files
282
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b42f.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b42f.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b40f.TMP | — | |
MD5:— | SHA256:— | |||
| 2692 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
734
DNS requests
910
Threats
34
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7560 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748302751&P2=404&P3=2&P4=cda0Idw4VZkZ12ovaoyQqq28Bmtap5xdNvwCzVAyVJzFR9WbJo2m7P5VaHnTjLRnI0SxFVj1YRBREp1MbQA5pQ%3d%3d | unknown | — | — | whitelisted |
7560 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748302751&P2=404&P3=2&P4=cda0Idw4VZkZ12ovaoyQqq28Bmtap5xdNvwCzVAyVJzFR9WbJo2m7P5VaHnTjLRnI0SxFVj1YRBREp1MbQA5pQ%3d%3d | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7560 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748302751&P2=404&P3=2&P4=cda0Idw4VZkZ12ovaoyQqq28Bmtap5xdNvwCzVAyVJzFR9WbJo2m7P5VaHnTjLRnI0SxFVj1YRBREp1MbQA5pQ%3d%3d | unknown | — | — | whitelisted |
7560 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748302753&P2=404&P3=2&P4=KmXaSH1RpXQXjxwkd%2f8OU8C2gEgEaWakbgXMOD%2bThP32CFt1mjkg30yCW%2bCN%2bymI2a2jXDofd6eWu46l6bLErg%3d%3d | unknown | — | — | whitelisted |
7560 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748302753&P2=404&P3=2&P4=KmXaSH1RpXQXjxwkd%2f8OU8C2gEgEaWakbgXMOD%2bThP32CFt1mjkg30yCW%2bCN%2bymI2a2jXDofd6eWu46l6bLErg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5796 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7288 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2692 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7288 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | — | — | whitelisted |
7288 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7288 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7288 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7288 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7288 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7288 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |