| URL: | https://f74.workupload.com/download/S2F9ARfsjg3 |
| Full analysis: | https://app.any.run/tasks/ba59f0db-5429-4d49-8703-ad0ed90f85e1 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2025, 13:17:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 650630FA841DC3D0F0A8E3E2B6486A62 |
| SHA1: | 8A859A61D676074E8FE98AF063C279CE2185A1B2 |
| SHA256: | 19C61AD6593752F7CD92D5E819D2CFA6A01A4FC2EBB05189DD13746E28AB89C1 |
| SSDEEP: | 3:N8gRmKP2ZBLbd:2ggoYBt |
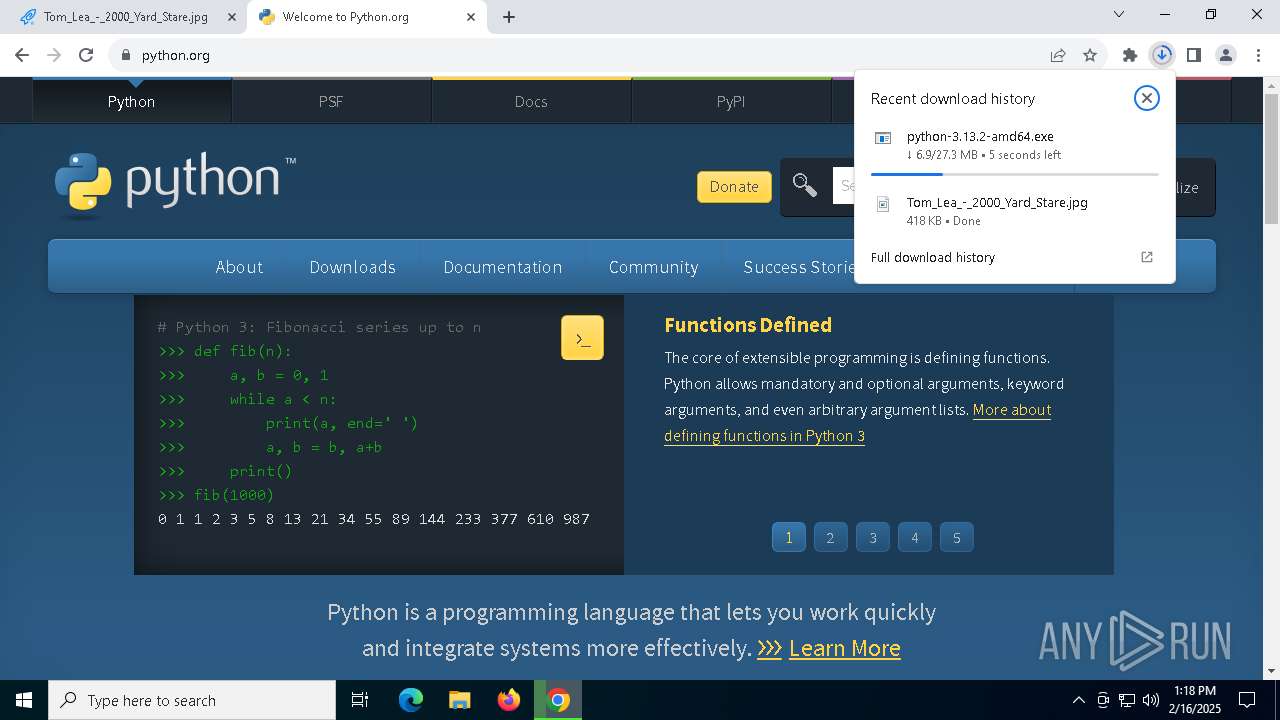
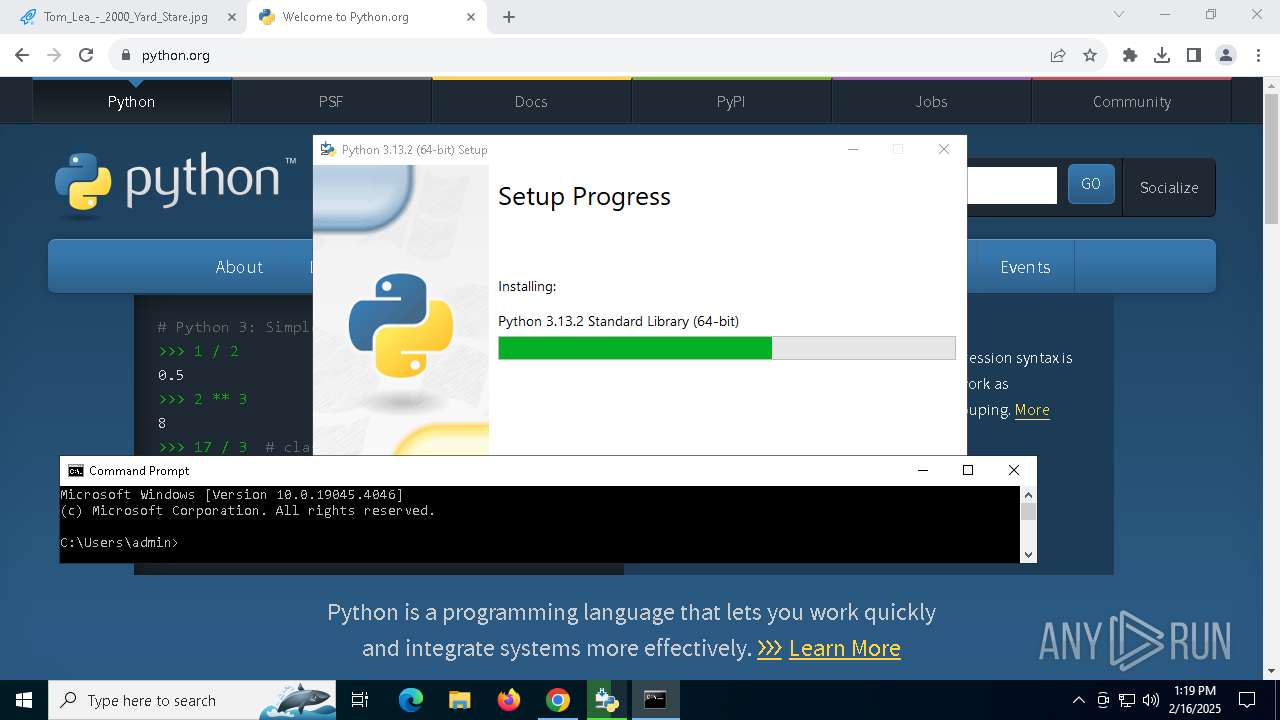
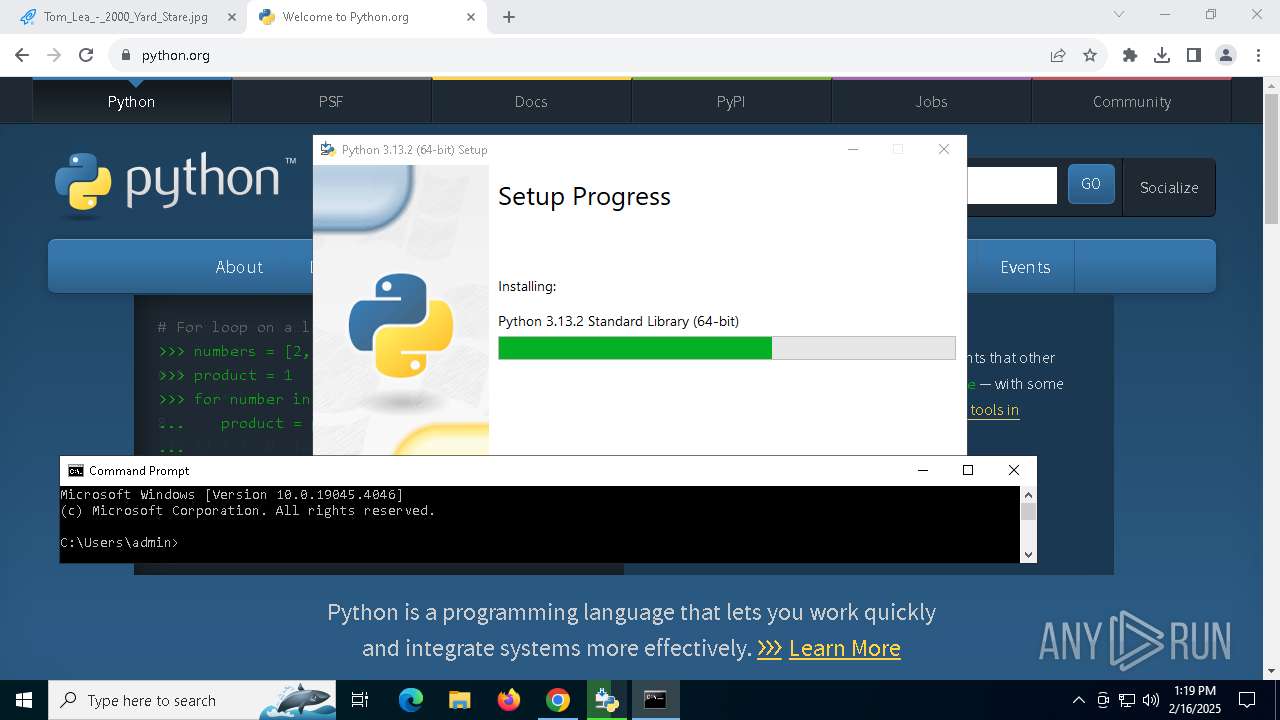
MALICIOUS
Changes the autorun value in the registry
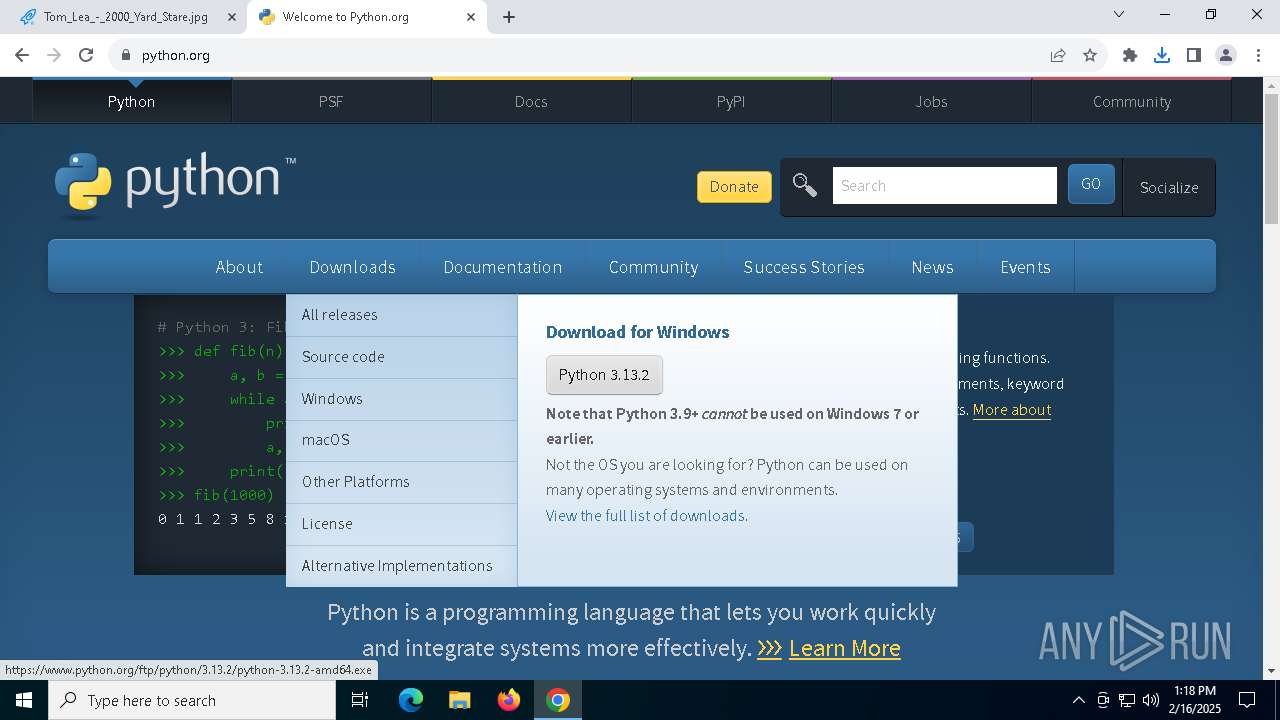
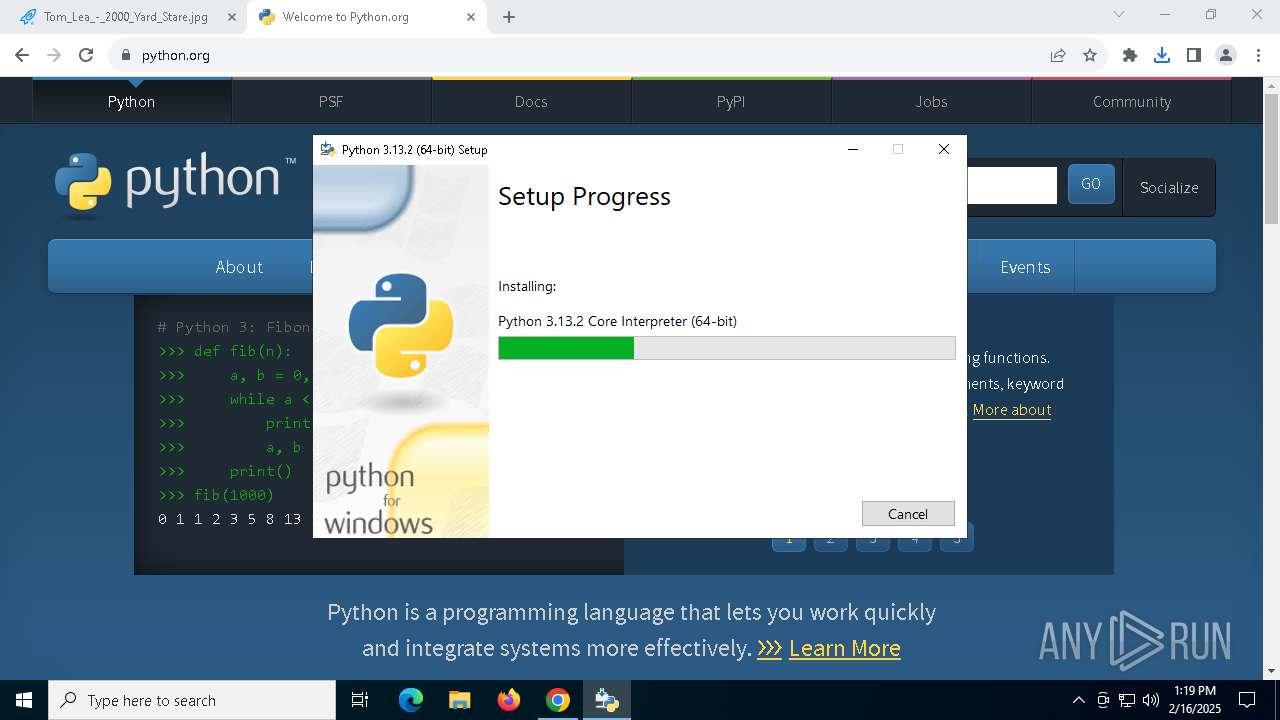
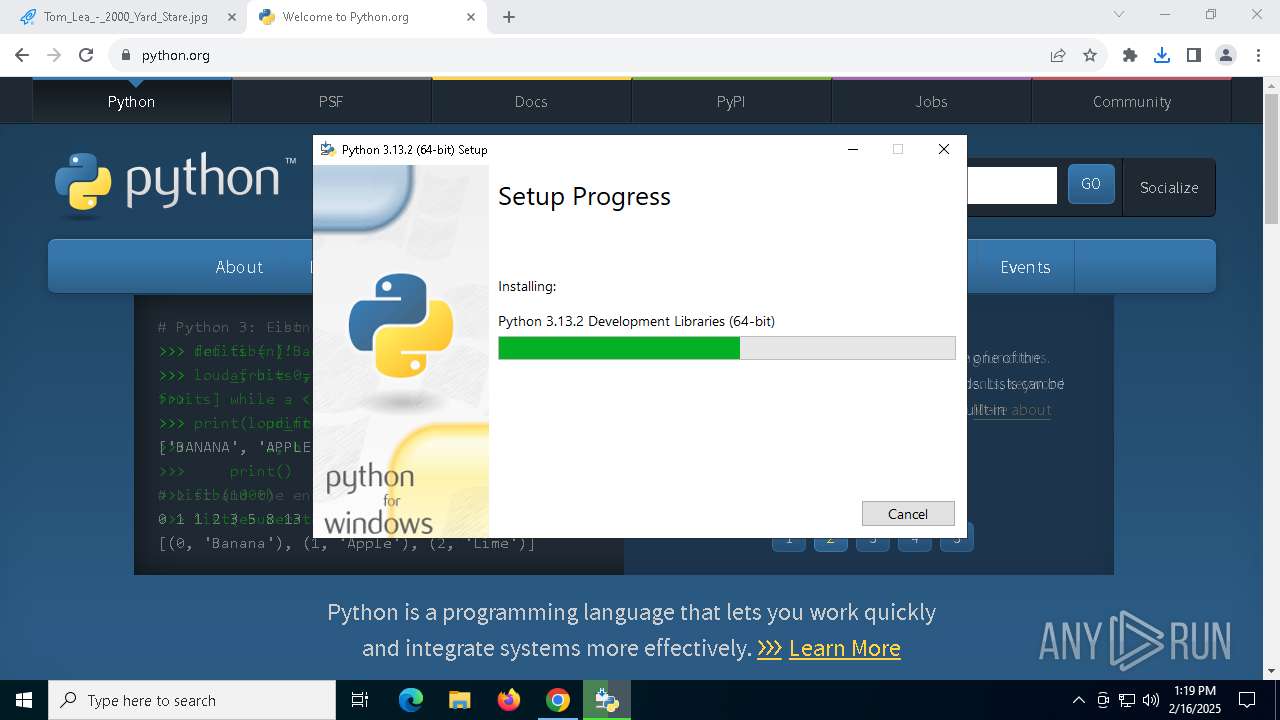
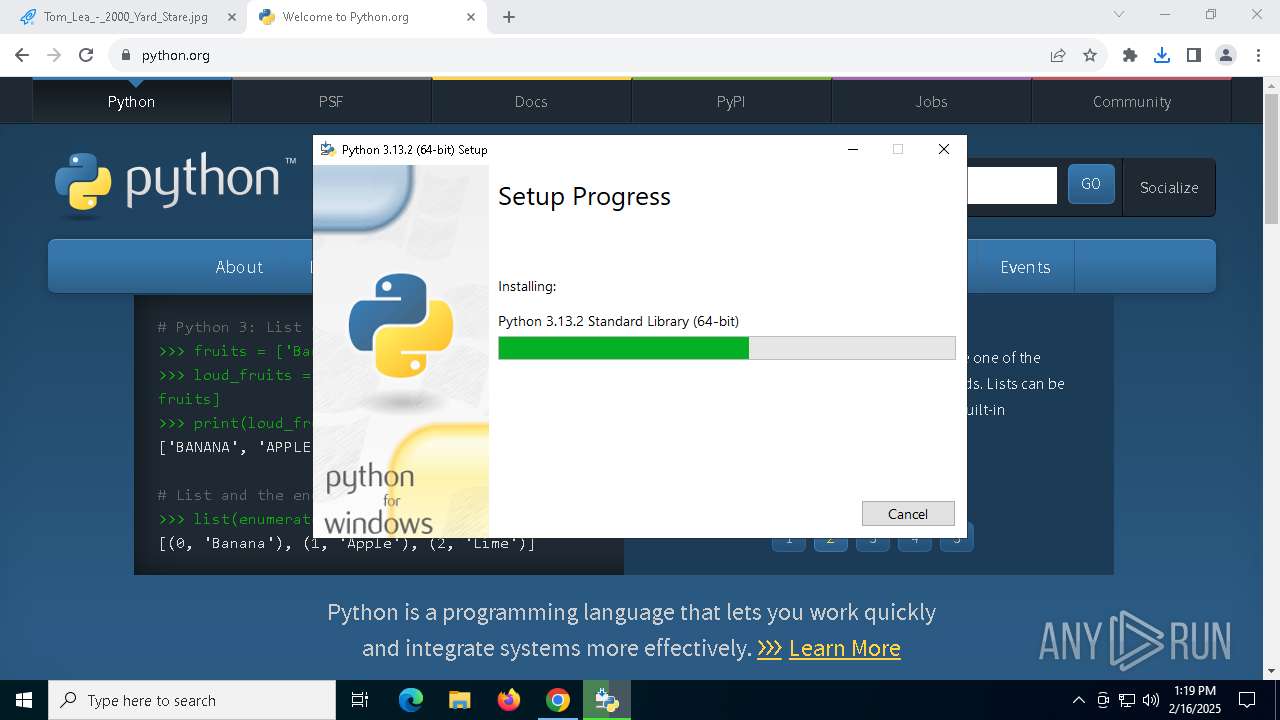
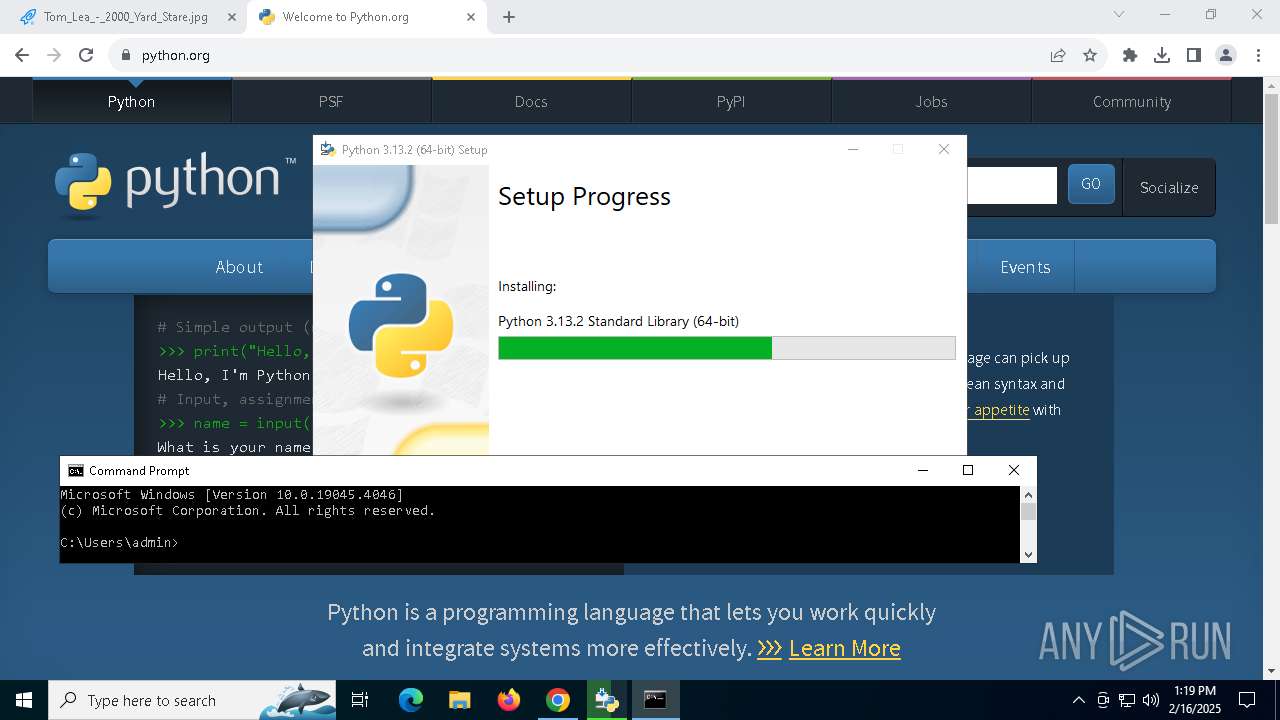
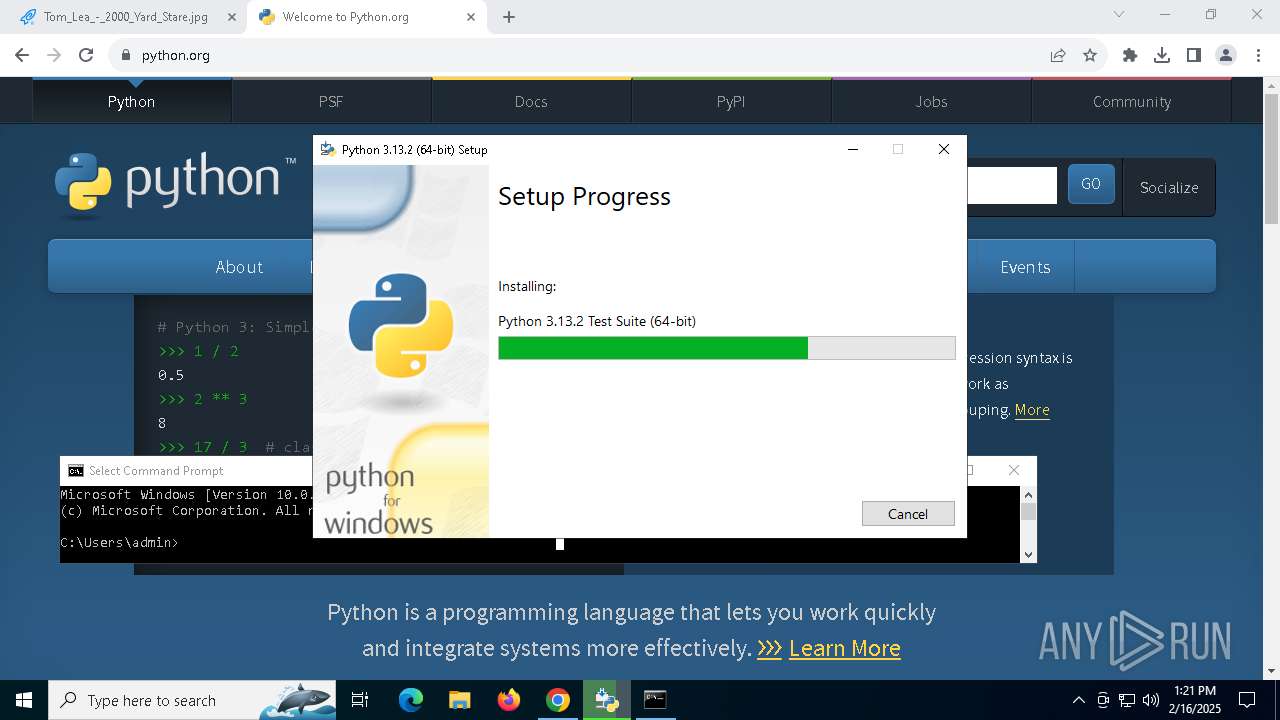
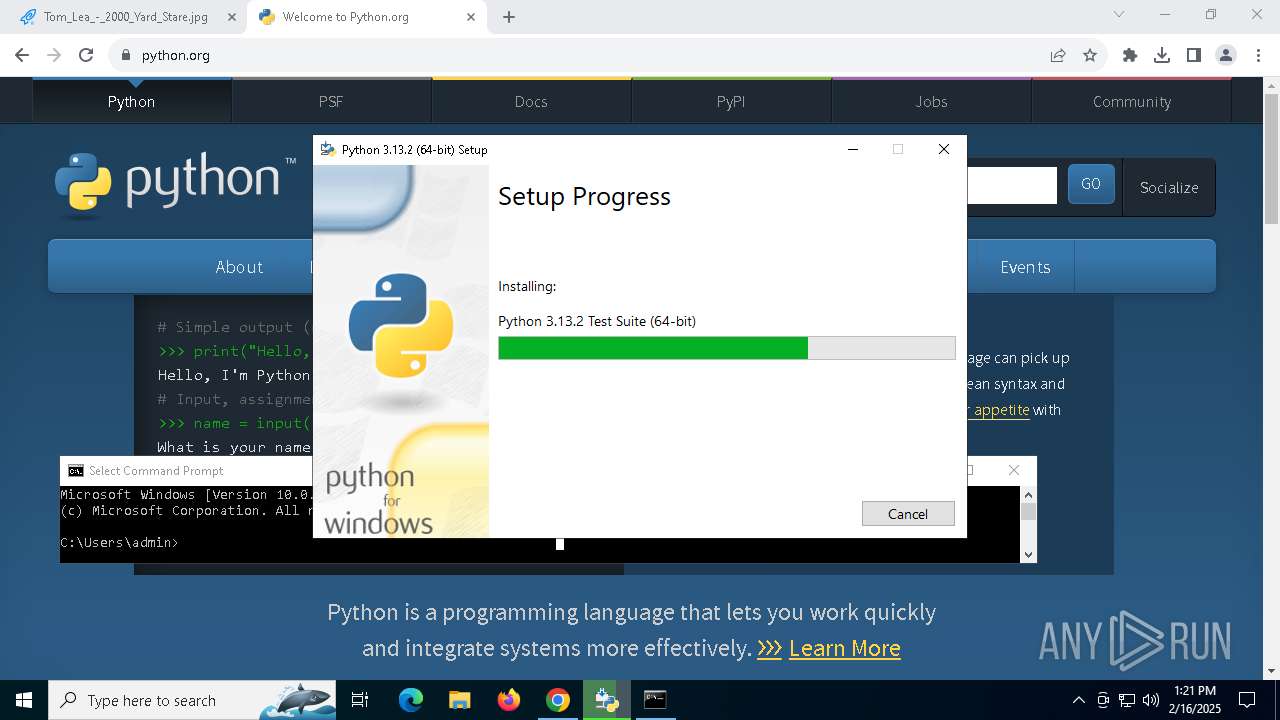
- python-3.13.2-amd64.exe (PID: 5888)
SUSPICIOUS
Executable content was dropped or overwritten
- python-3.13.2-amd64.exe (PID: 1540)
- python-3.13.2-amd64.exe (PID: 5888)
Creates a software uninstall entry
- python-3.13.2-amd64.exe (PID: 5888)
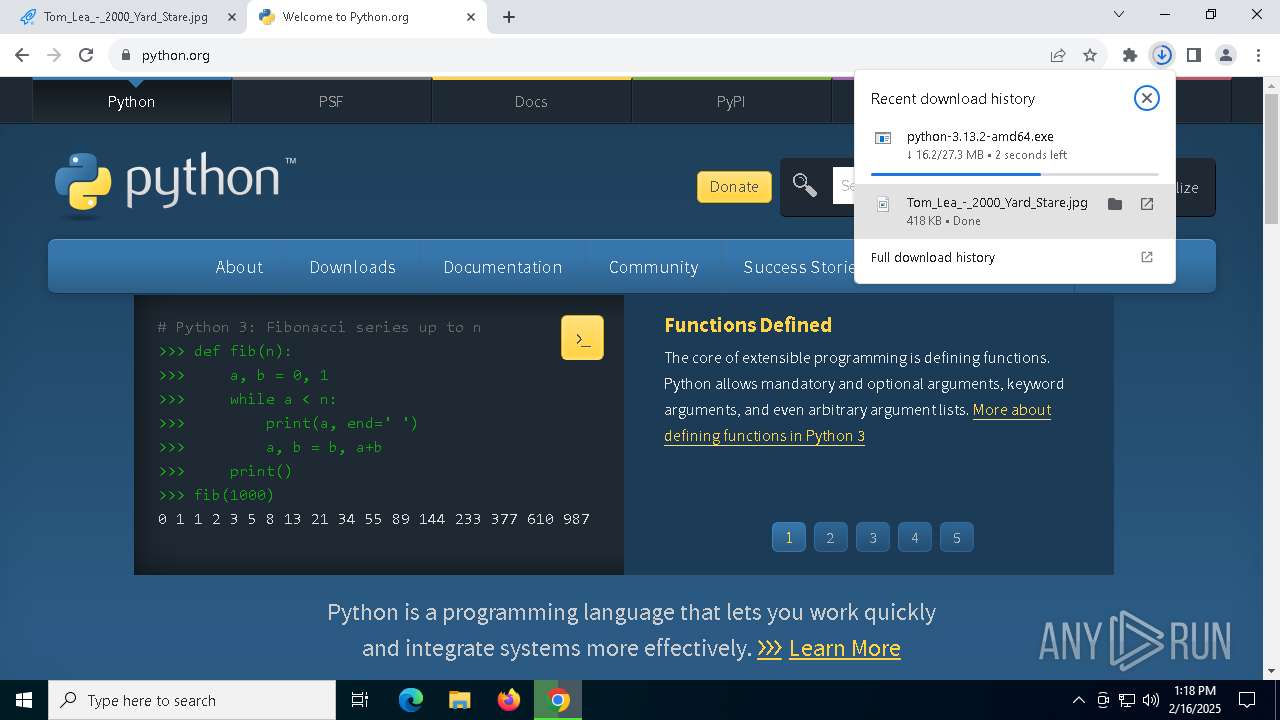
The process drops C-runtime libraries
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Searches for installed software
- python-3.13.2-amd64.exe (PID: 5888)
Checks Windows Trust Settings
- msiexec.exe (PID: 2144)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2144)
Process drops legitimate windows executable
- msiexec.exe (PID: 2144)
- python-3.13.2-amd64.exe (PID: 5888)
Process drops python dynamic module
- msiexec.exe (PID: 2144)
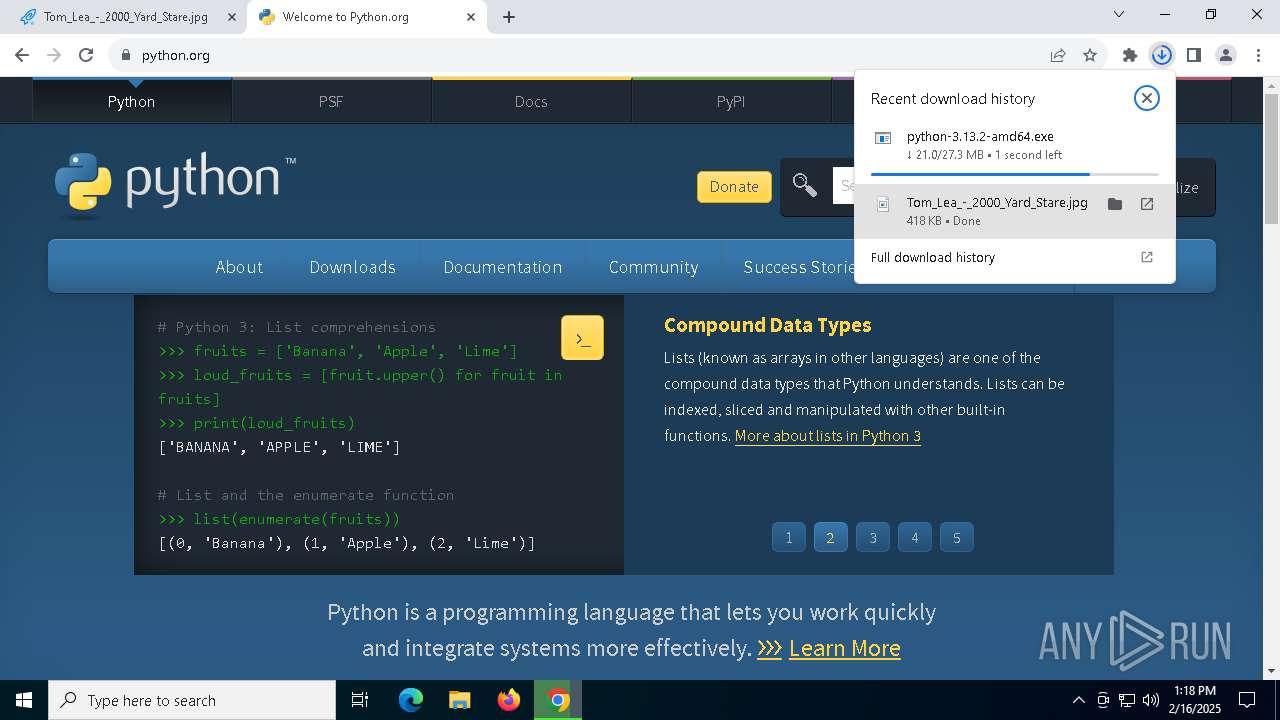
INFO
Application launched itself
- chrome.exe (PID: 6324)
Executable content was dropped or overwritten
- chrome.exe (PID: 6324)
- msiexec.exe (PID: 2144)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2392)
The sample compiled with english language support
- chrome.exe (PID: 6324)
- python-3.13.2-amd64.exe (PID: 1540)
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2392)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6324)
Checks supported languages
- python-3.13.2-amd64.exe (PID: 1540)
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Create files in a temporary directory
- python-3.13.2-amd64.exe (PID: 1540)
- python-3.13.2-amd64.exe (PID: 5888)
Creates files or folders in the user directory
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Reads the computer name
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Reads the machine GUID from the registry
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Mutex for Python MSI log
- python-3.13.2-amd64.exe (PID: 5888)
- msiexec.exe (PID: 2144)
Reads the software policy settings
- msiexec.exe (PID: 2144)
Creates a software uninstall entry
- msiexec.exe (PID: 2144)
Manual execution by a user
- cmd.exe (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
29
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4428 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
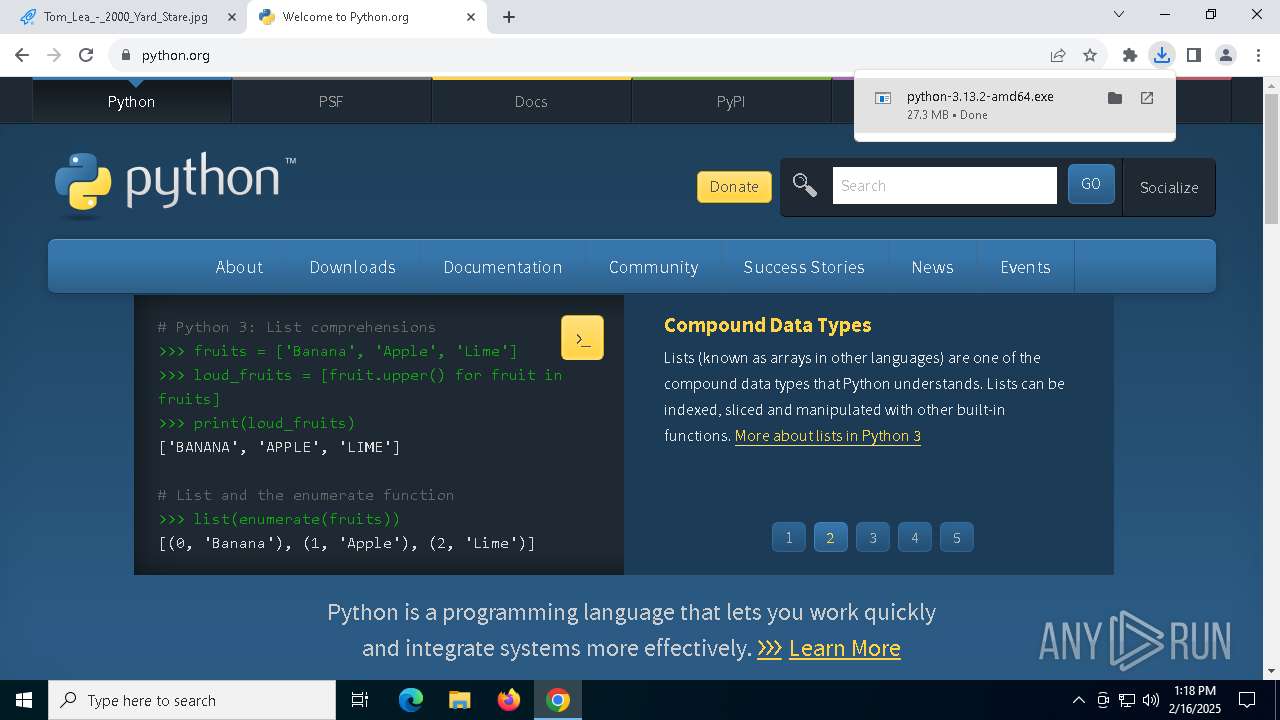
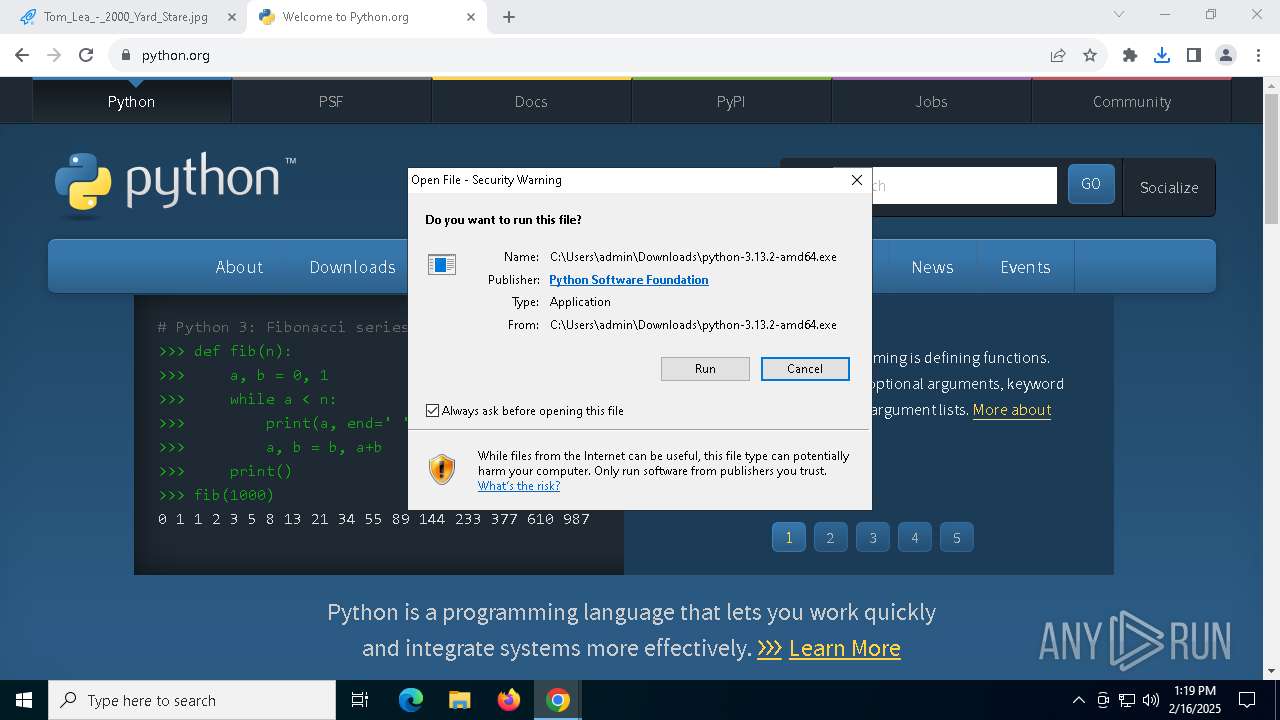
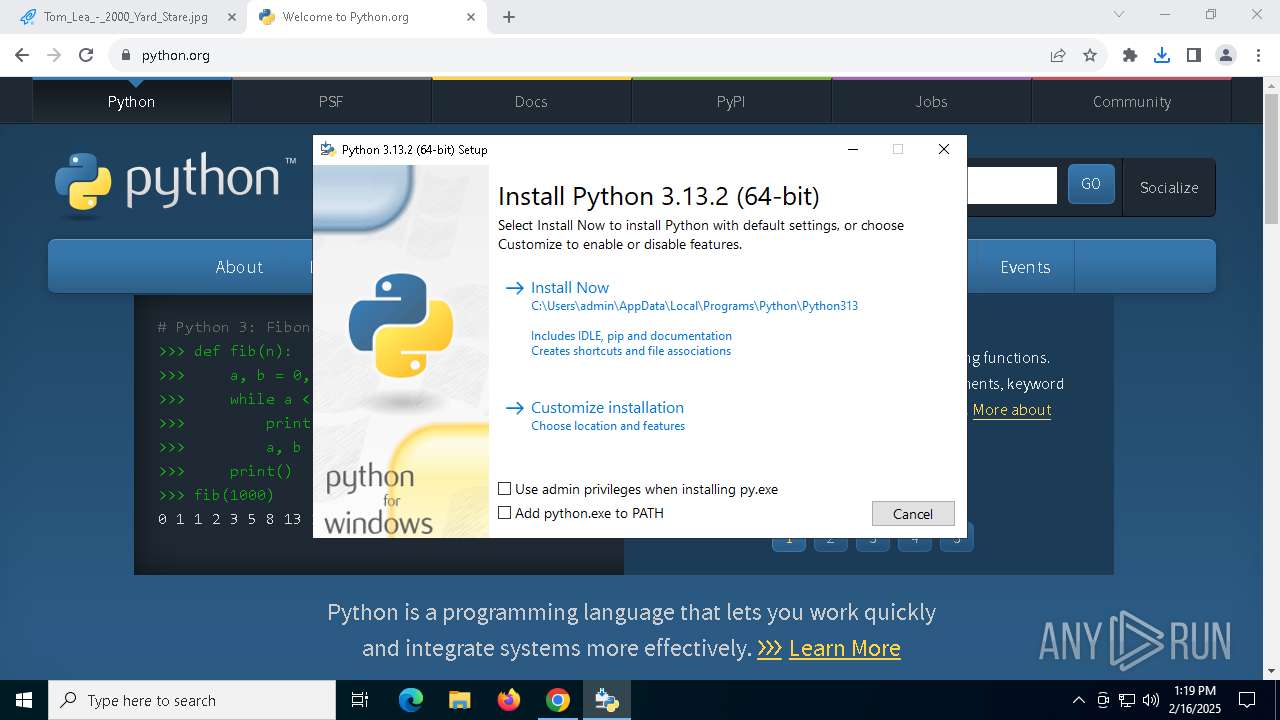
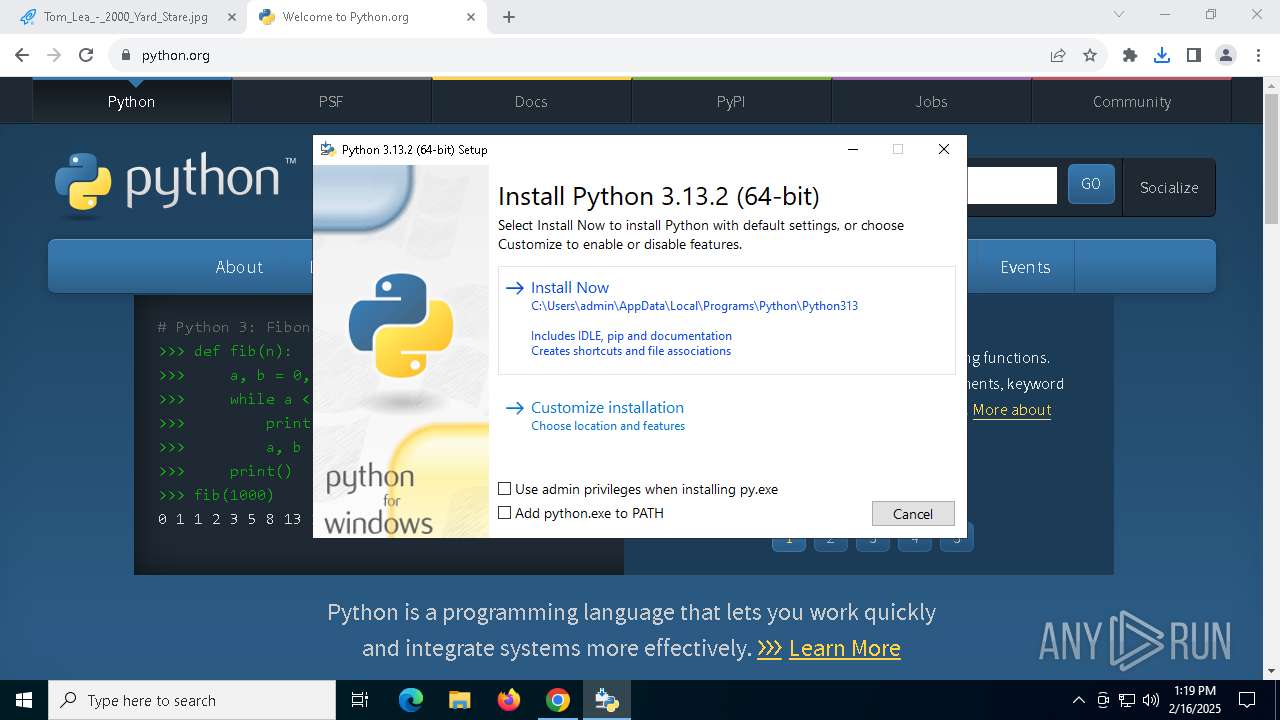
| 1540 | "C:\Users\admin\Downloads\python-3.13.2-amd64.exe" | C:\Users\admin\Downloads\python-3.13.2-amd64.exe | chrome.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.2 (64-bit) Version: 3.13.2150.0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6428 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2144 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4748 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5264 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5648 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5940 --field-trial-handle=1916,i,4649237089545553189,10663479715978093449,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3288 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
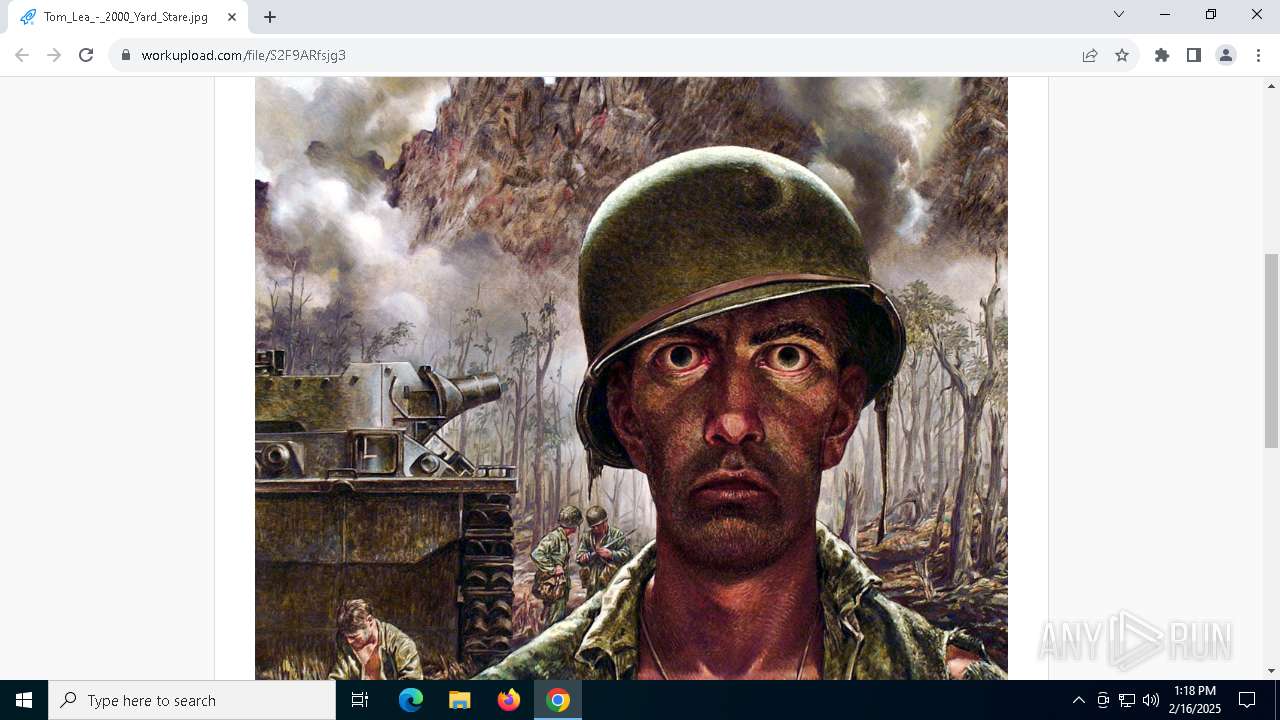
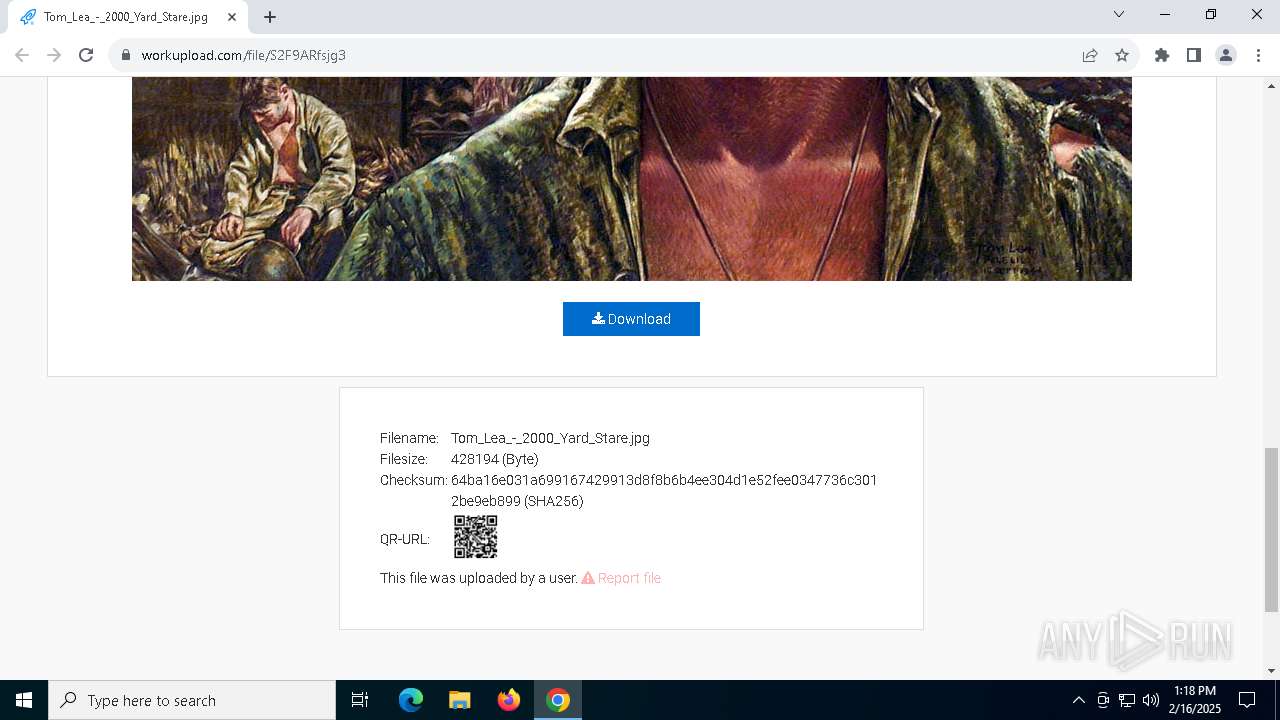
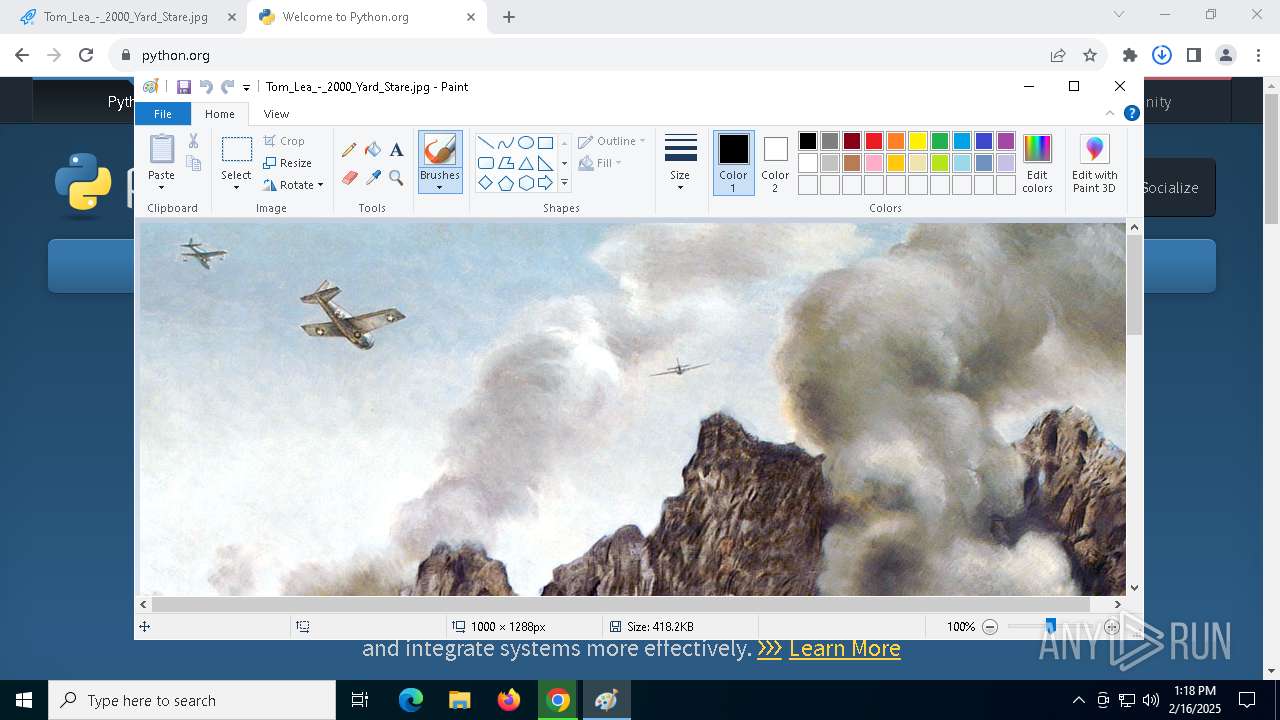
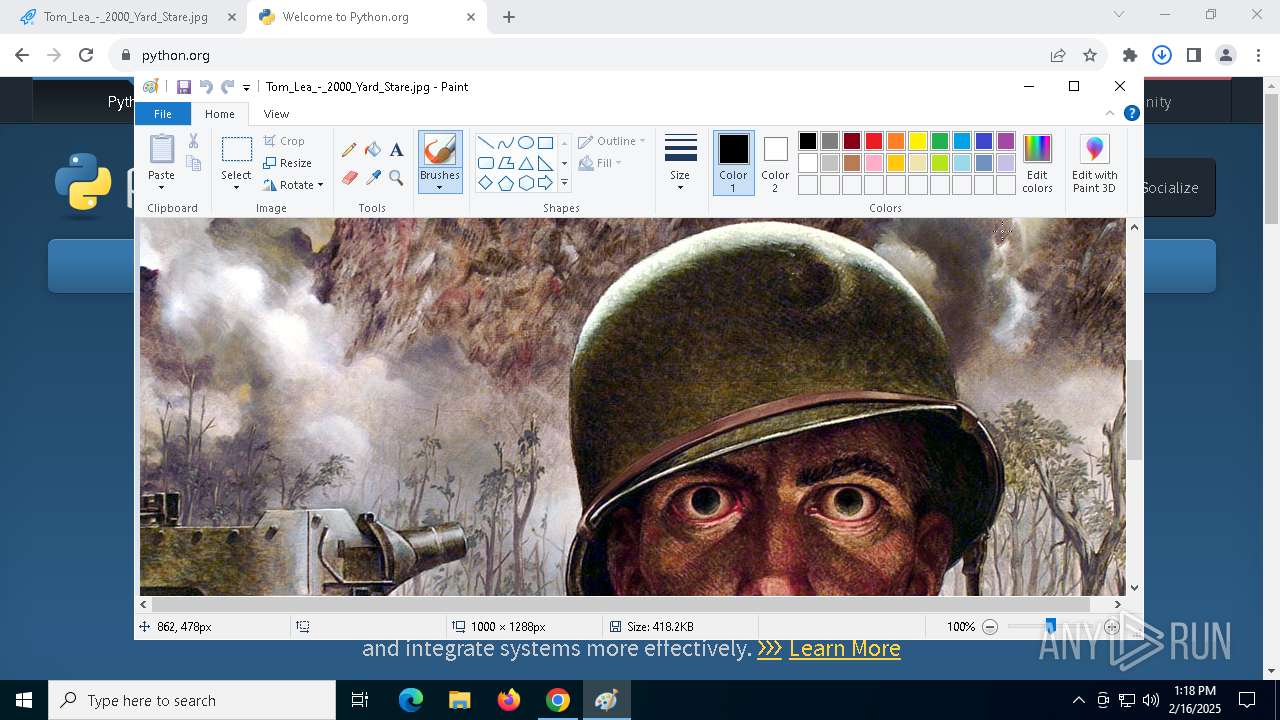
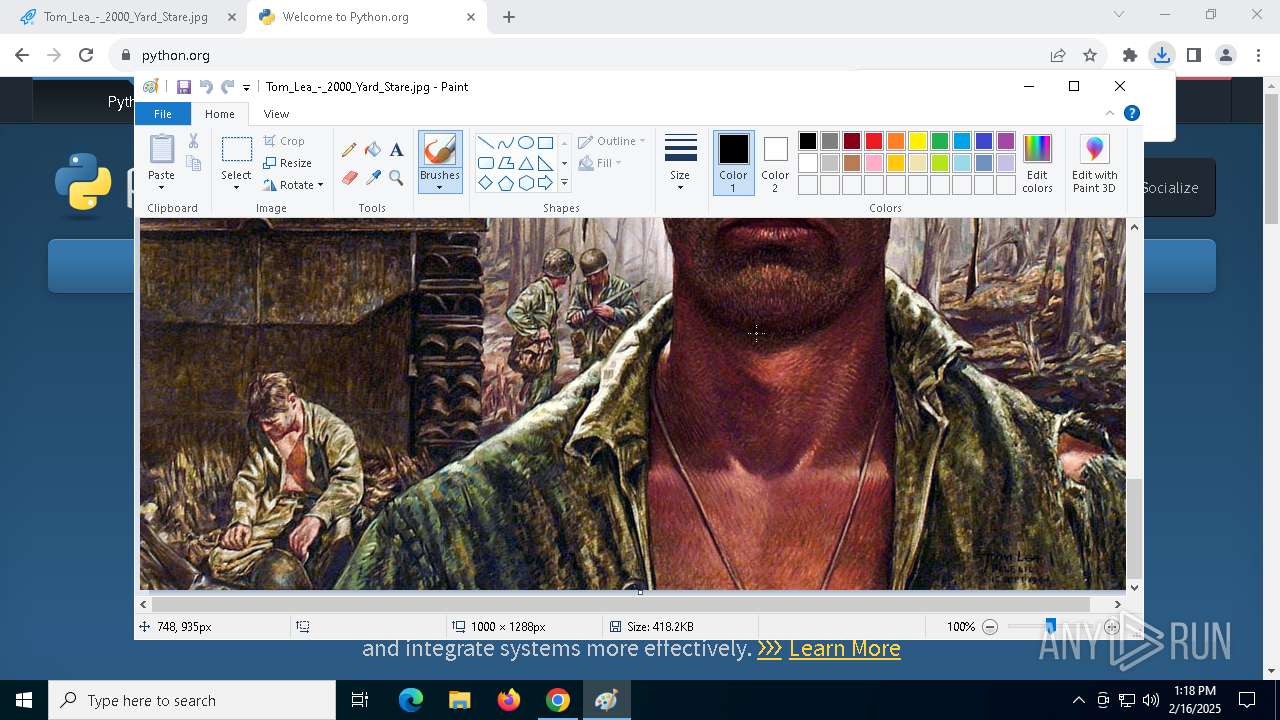
| 3568 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Downloads\Tom_Lea_-_2000_Yard_Stare.jpg" | C:\Windows\System32\mspaint.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 064
Read events
30 897
Write events
3 115
Delete events
52
Modification events
| (PID) Process: | (3688) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000EE451D3A7580DB01 | |||
| (PID) Process: | (6324) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (6324) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpg\OpenWithProgids |
| Operation: | write | Name: | jpegfile |
Value: | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF7F000000470000007F04000087020000 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowThumbnail |
Value: 0 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPWidth |
Value: 0 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPHeight |
Value: 0 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbXPos |
Value: 0 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbYPos |
Value: 0 | |||
| (PID) Process: | (3568) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbWidth |
Value: 0 | |||
Executable files
85
Suspicious files
505
Text files
1 986
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF139994.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF139994.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF139994.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF139994.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1399d2.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
107
DNS requests
85
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
68 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5464 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6536 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1400 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
5464 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1400 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
1400 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
1400 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
1400 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
68 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
68 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.96.120:443 | — | Akamai International B.V. | DE | unknown |
— | — | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 23.88.72.235:443 | f74.workupload.com | Hetzner Online GmbH | DE | whitelisted |
— | — | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
f74.workupload.com |
| whitelisted |
accounts.google.com |
| whitelisted |
workupload.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
t.workupload.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6708 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6708 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6708 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |