| File name: | Activator.exe |
| Full analysis: | https://app.any.run/tasks/61171519-471a-4eff-bff6-6ebef0279140 |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2024, 19:29:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B907E800BF12F6DD675EF118743CF1B2 |
| SHA1: | 83B96285F2D8427F2F050544CB7010D8965C8ADB |
| SHA256: | 19C5287B4F8CE60C8739C868CB343F5B79F5FD15F179E83DD097B858140FB38C |
| SSDEEP: | 98304:7lE1aDa0lGbsGuKPkROJXPJOU2siDpAR68jqHSsemZEtfE9MMyINMdlOo5osmDVi:ofGvuiy |
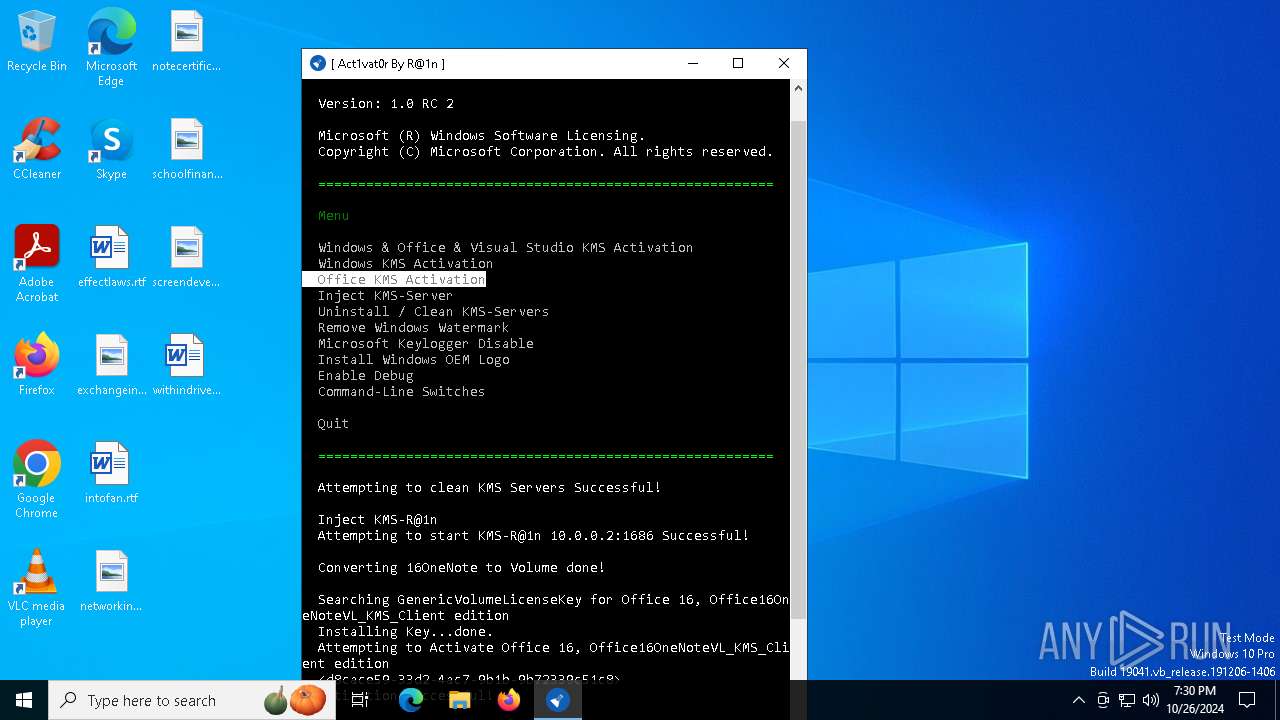
MALICIOUS
Changes image file execution options
- Activator.exe (PID: 6216)
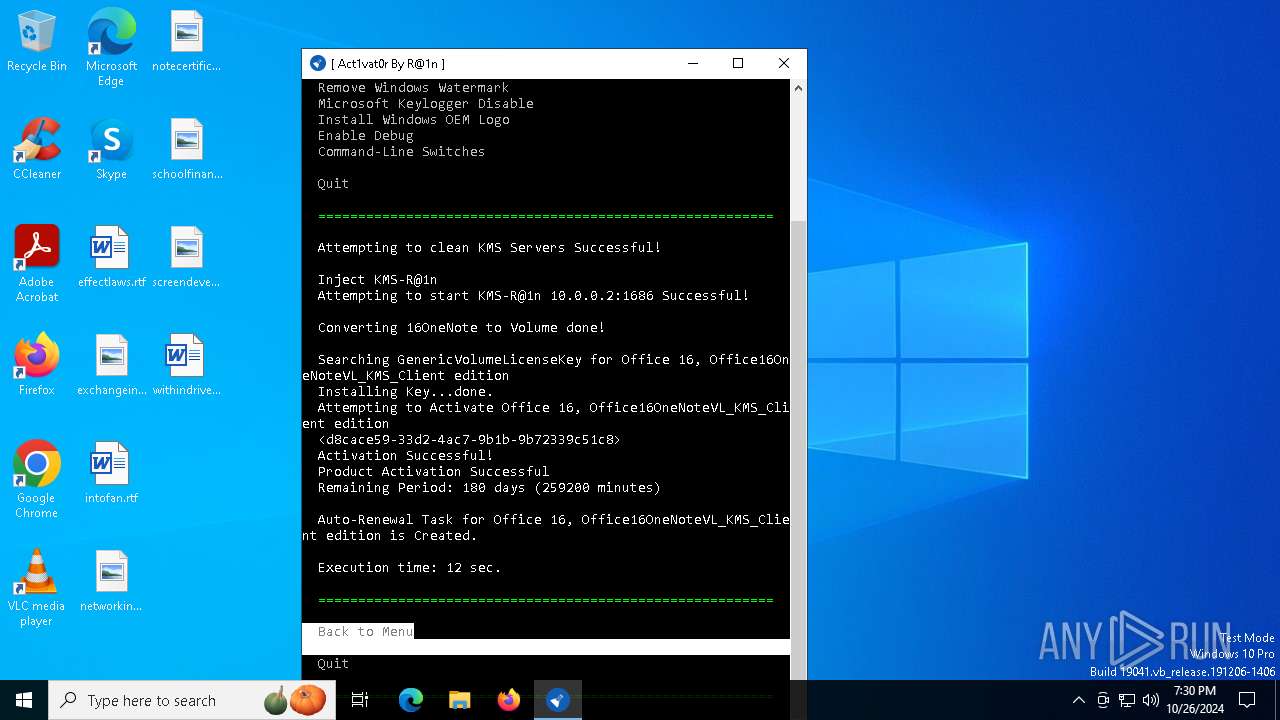
Uses Task Scheduler to run other applications
- Activator.exe (PID: 6216)
SUSPICIOUS
Reads security settings of Internet Explorer
- Activator.exe (PID: 6216)
Searches for installed software
- Activator.exe (PID: 6216)
Uses TASKKILL.EXE to kill process
- Activator.exe (PID: 6216)
Starts SC.EXE for service management
- Activator.exe (PID: 6216)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- Activator.exe (PID: 6216)
Executable content was dropped or overwritten
- Activator.exe (PID: 6216)
Executes as Windows Service
- KMS-R@1n.exe (PID: 1552)
INFO
Reads the machine GUID from the registry
- Activator.exe (PID: 6216)
- KMS-R@1n.exe (PID: 1552)
Checks supported languages
- Activator.exe (PID: 6216)
- KMS-R@1n.exe (PID: 1552)
- KMS-R@1nHook.exe (PID: 1700)
Reads the computer name
- Activator.exe (PID: 6216)
- KMS-R@1n.exe (PID: 1552)
Reads Environment values
- Activator.exe (PID: 6216)
Creates files or folders in the user directory
- Activator.exe (PID: 6216)
The process uses the downloaded file
- Activator.exe (PID: 6216)
Create files in a temporary directory
- Activator.exe (PID: 6216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:05 07:50:21+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 3122688 |
| InitializedDataSize: | 3160064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2fc53e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2.2 |
| ProductVersionNumber: | 1.0.2.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
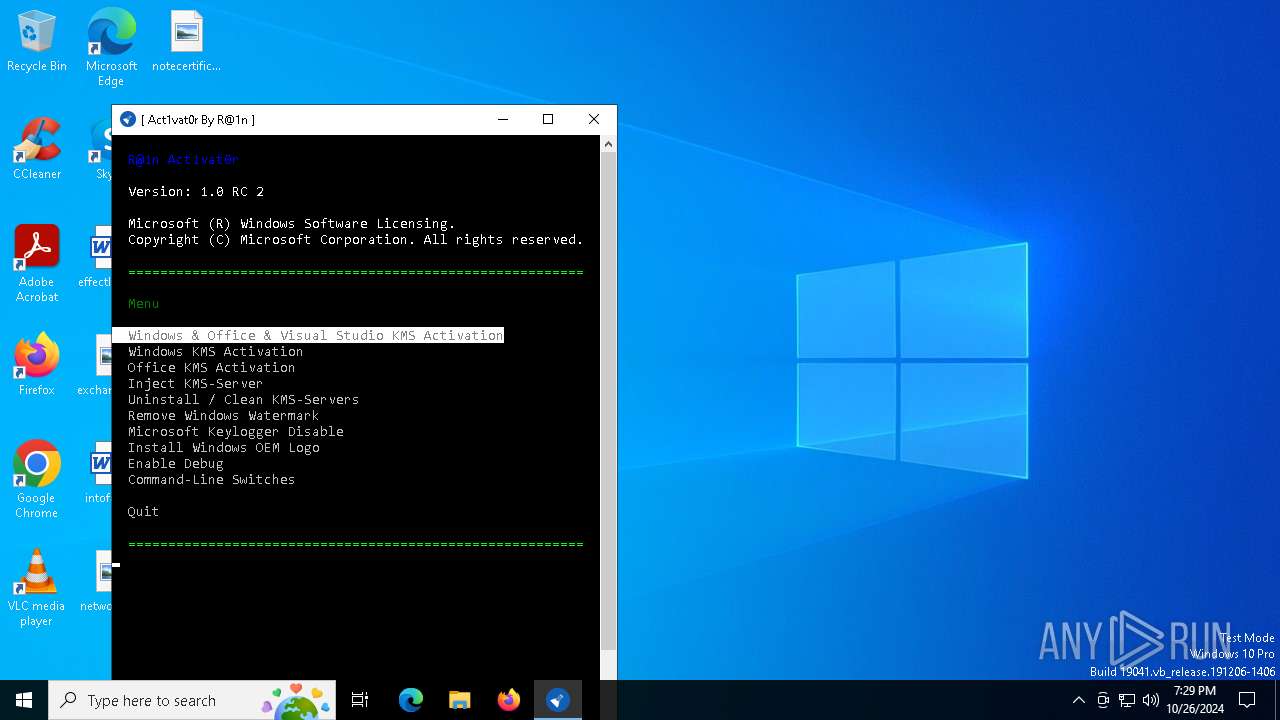
| FileDescription: | R@1n Activator |
| FileVersion: | 1.0.2.2 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | R@1n Activator |
| ProductVersion: | 1.0.2.2 |
| AssemblyVersion: | 1.0.2.2 |
Total processes
152
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Users\admin\AppData\Local\Temp\Activator.exe" | C:\Users\admin\AppData\Local\Temp\Activator.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: R@1n Activator Exit code: 3221226540 Version: 1.0.2.2 Modules
| |||||||||||||||
| 1552 | C:\Windows\KMS-R@1n.exe | C:\Windows\KMS-R@1n.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Modules
| |||||||||||||||
| 1700 | KMS-R@1nHook.exe C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\KMS-R@1nHook.exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Modules
| |||||||||||||||
| 2692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | "C:\Windows\System32\sc.exe" create "KMS-R@1n" DisplayName= KMS-R@1n binPath= "C:\Windows\KMS-R@1n.exe" obj= "NT Authority\NetworkService" type= "own" error= "normal" start= "auto" depend= "RpcSs/tcpip" | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1073 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3964 | "C:\Windows\System32\sc.exe" create "KMS-R@1n" DisplayName= KMS-R@1n binPath= "C:\Windows\KMS-R@1n.exe" obj= "NT Authority\NetworkService" type= "own" error= "normal" start= "auto" depend= "RpcSs/tcpip" | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4228 | "C:\Windows\System32\sc.exe" delete KMS-R@1n | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | "C:\Windows\System32\sc.exe" description "KMS-R@1n" "v0.2" | C:\Windows\System32\sc.exe | — | Activator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 983
Read events
1 970
Write events
9
Delete events
4
Modification events
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options |
| Operation: | delete value | Name: | SppExtComObj.exe |
Value: | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options |
| Operation: | delete value | Name: | OsppSvc.exe |
Value: | |||
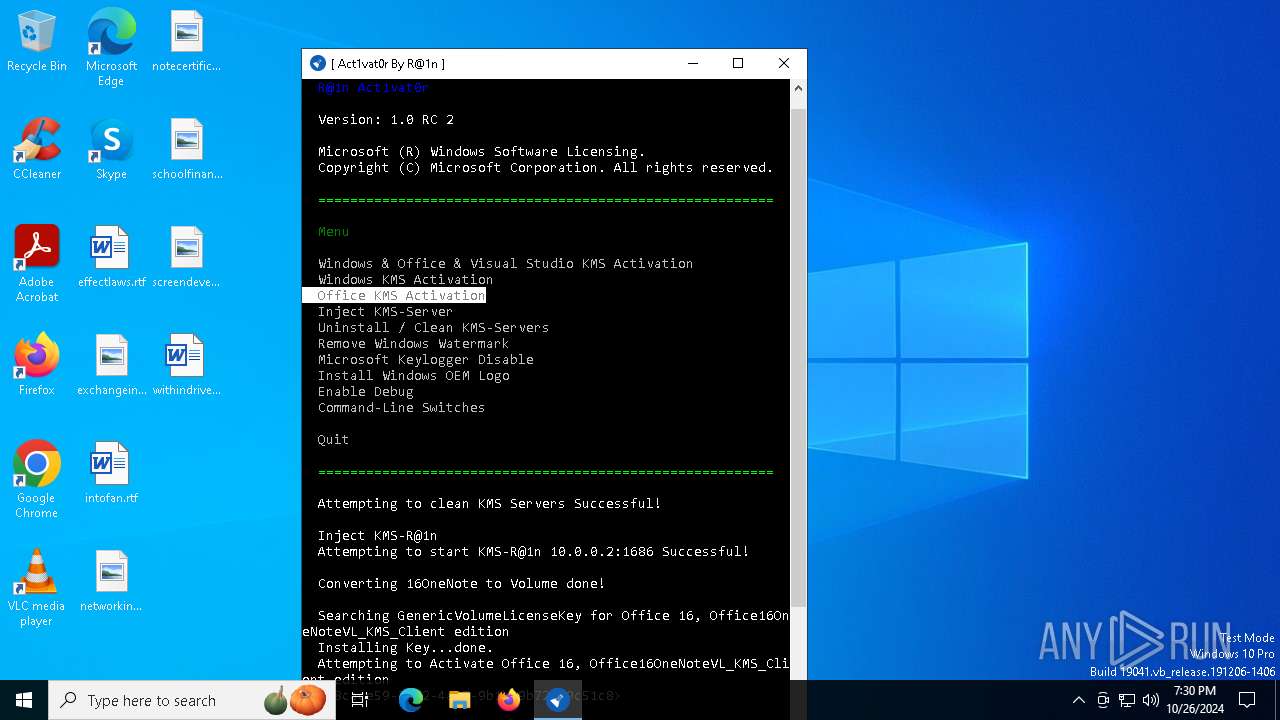
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | Debugger |
Value: KMS-R@1nHook.exe | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | KMS_Emulation |
Value: 0 | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\OSppSvc.exe |
| Operation: | write | Name: | Debugger |
Value: KMS-R@1nHook.exe | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\OSppSvc.exe |
| Operation: | write | Name: | KMS_Emulation |
Value: 0 | |||
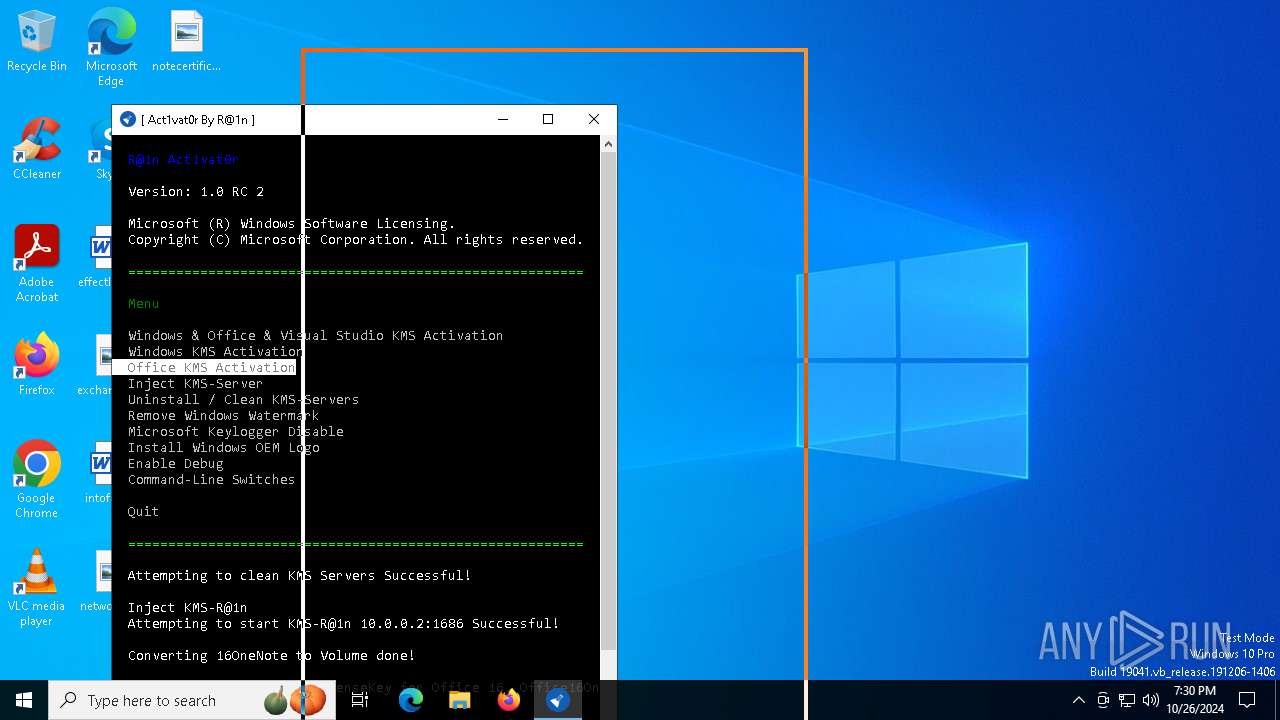
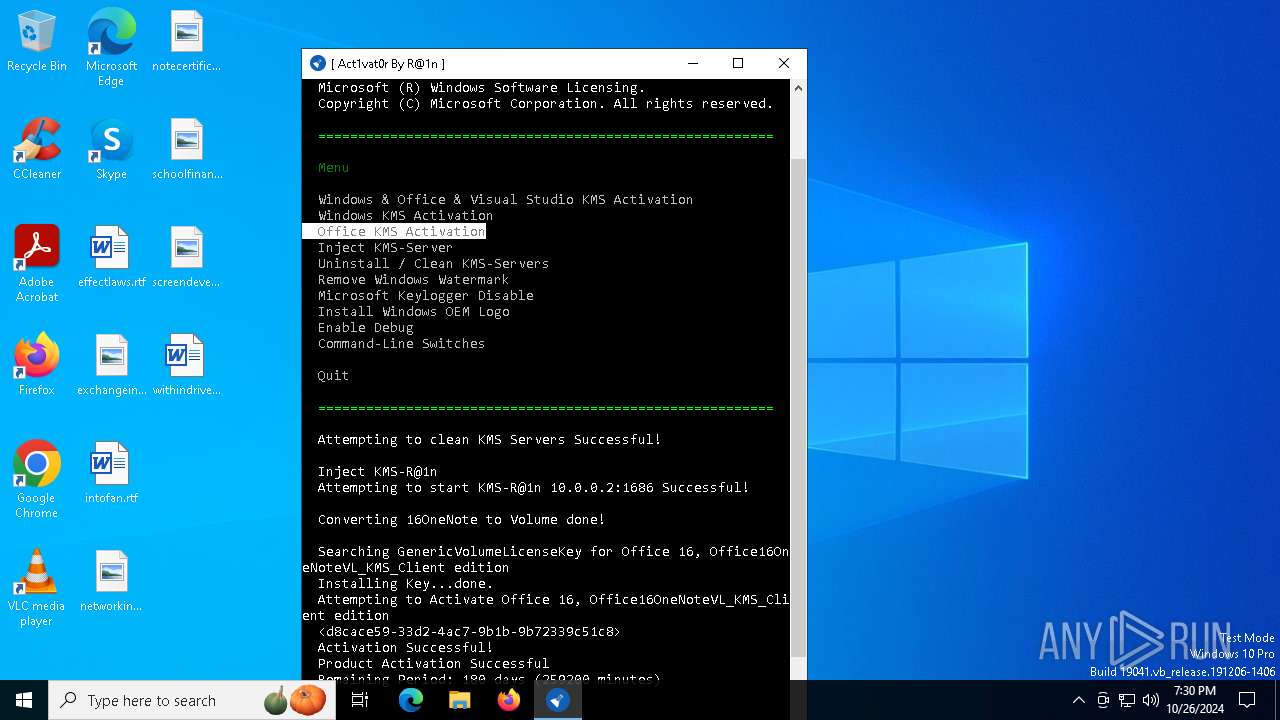
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServiceName |
Value: 10.0.0.2 | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform |
| Operation: | write | Name: | KeyManagementServicePort |
Value: 1686 | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform |
| Operation: | delete value | Name: | 59a52881-a989-479d-af46-f275c6370663 |
Value: | |||
| (PID) Process: | (6216) Activator.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\CurrentVersion\Software Protection Platform |
| Operation: | write | Name: | NoGenTicket |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
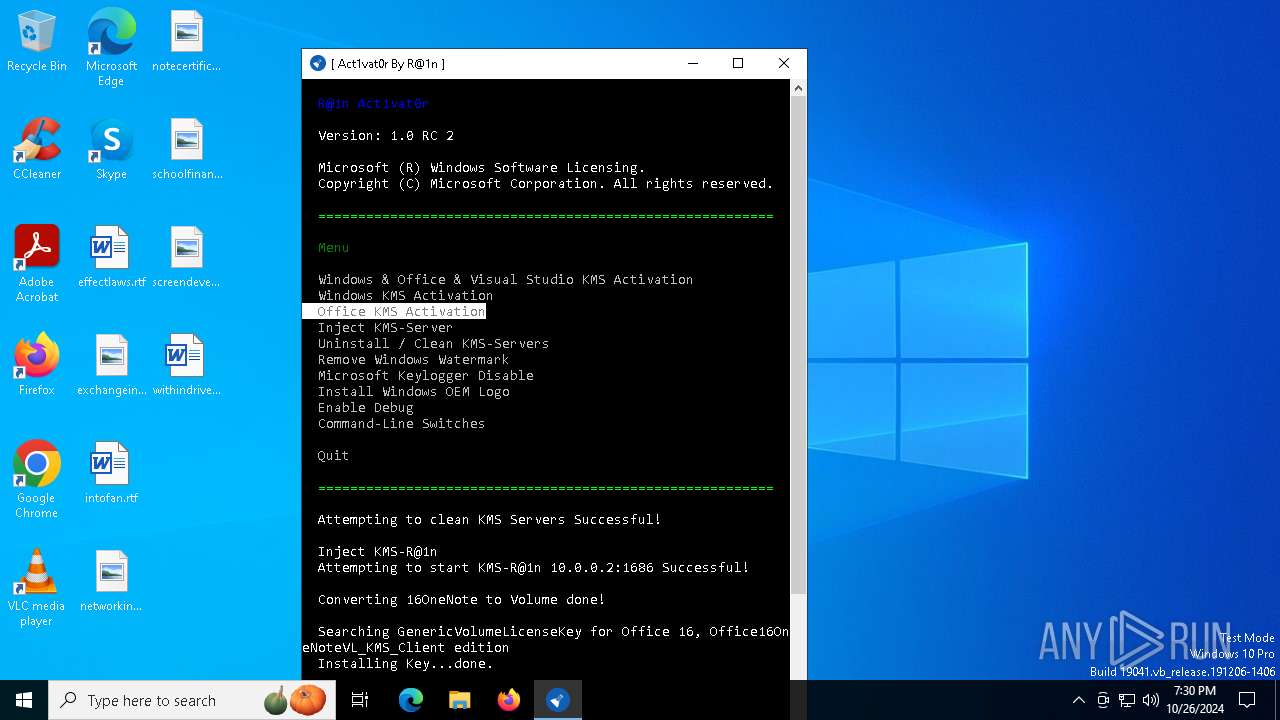
| 6216 | Activator.exe | C:\Windows\KMS-R@1nHook.dll | executable | |
MD5:A2F93B21413115C31260975C35EC4E4C | SHA256:5197323DDEE0141CA9C433D3860E5E7B0193C0821D9E5278D8E5F6EA0523C322 | |||
| 6216 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\CERT\16OneNote1.xrm-ms | xml | |
MD5:DD33A38221AEC229289F3E0514BB8FFE | SHA256:AC76BEFBAC5715F1477AA95CE959EFAE86EFA84FF076D41C476D3C75DF2625AB | |||
| 6216 | Activator.exe | C:\Windows\KMS-R@1nHook.exe | executable | |
MD5:DC30CFD21BBB742C10E3621D5B506780 | SHA256:484C74D529EB1551FC2DDFE3C821A7A87113CE927CF22D79241030C2B4A4AA74 | |||
| 6216 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\CERT\16OneNote2.xrm-ms | xml | |
MD5:72DA7CF159C77D5F8157C594080715D0 | SHA256:8AC62912BE250279AC147B750DA7777E8432CAA9EF07FE50CACF04465719BA96 | |||
| 6216 | Activator.exe | C:\Windows\KMS-R@1n.exe | executable | |
MD5:0F9FD9565E6EB157FA9BE11ED9C1DC9F | SHA256:7565255F0A28D065F8F30F876E7DF3E46EF2E6FEDF420ECA7D454CF49887B2DE | |||
| 6216 | Activator.exe | C:\Users\admin\AppData\Local\Temp\Ra1n\CERT\16OneNote0.xrm-ms | xml | |
MD5:8EDE9E02D8D50E1D903A41C922C0B2D0 | SHA256:8C0E68BC398F777ADA66F65B0F89614ECDDB69E430E7A2D71704F4CE310157FC | |||
| 6216 | Activator.exe | C:\Users\admin\AppData\Local\A\Activator.exe_StrongName_l3aknjskewujmzuvhm2boapxs5tu1yjk\1.0.2.2\user.config | xml | |
MD5:B4665D173842909296DEC849F4005A0D | SHA256:FB762B6D33D0A090D055B5634994F41C8B5970DC28D1CC16672A5E15A337733C | |||
| 6216 | Activator.exe | C:\Users\admin\AppData\Local\A\Activator.exe_StrongName_l3aknjskewujmzuvhm2boapxs5tu1yjk\1.0.2.2\5euenig1.newcfg | xml | |
MD5:B4665D173842909296DEC849F4005A0D | SHA256:FB762B6D33D0A090D055B5634994F41C8B5970DC28D1CC16672A5E15A337733C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
38
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.86.251.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2724 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.76.201.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6128 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6128 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.86.251.134:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.76.201.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2724 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |