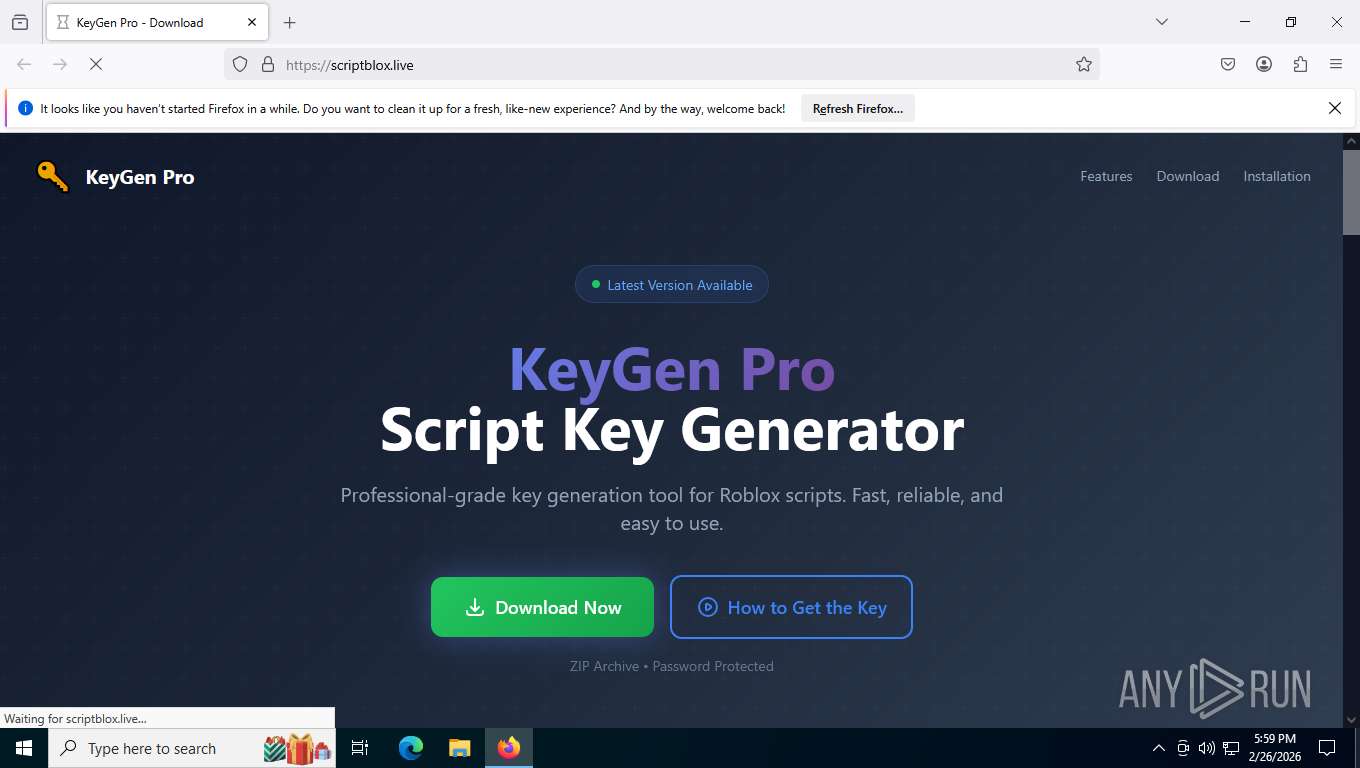
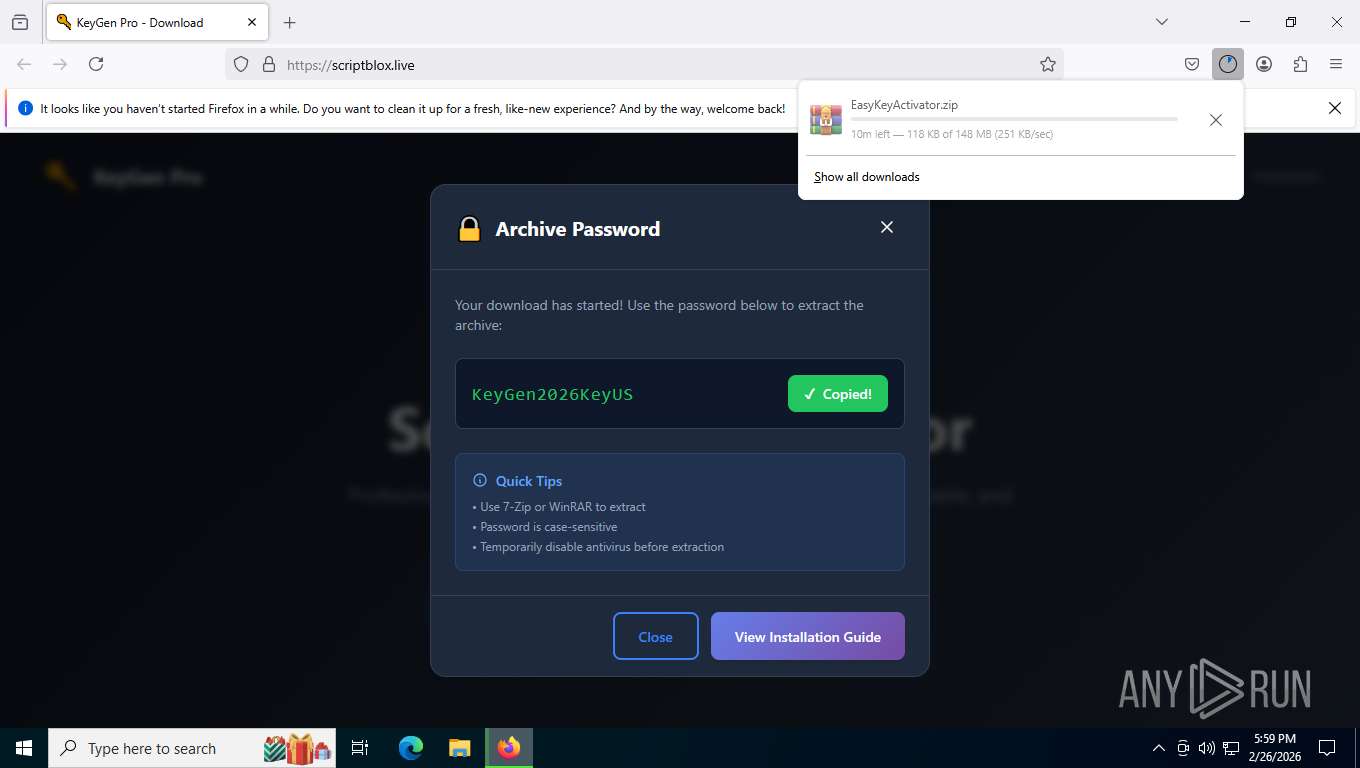
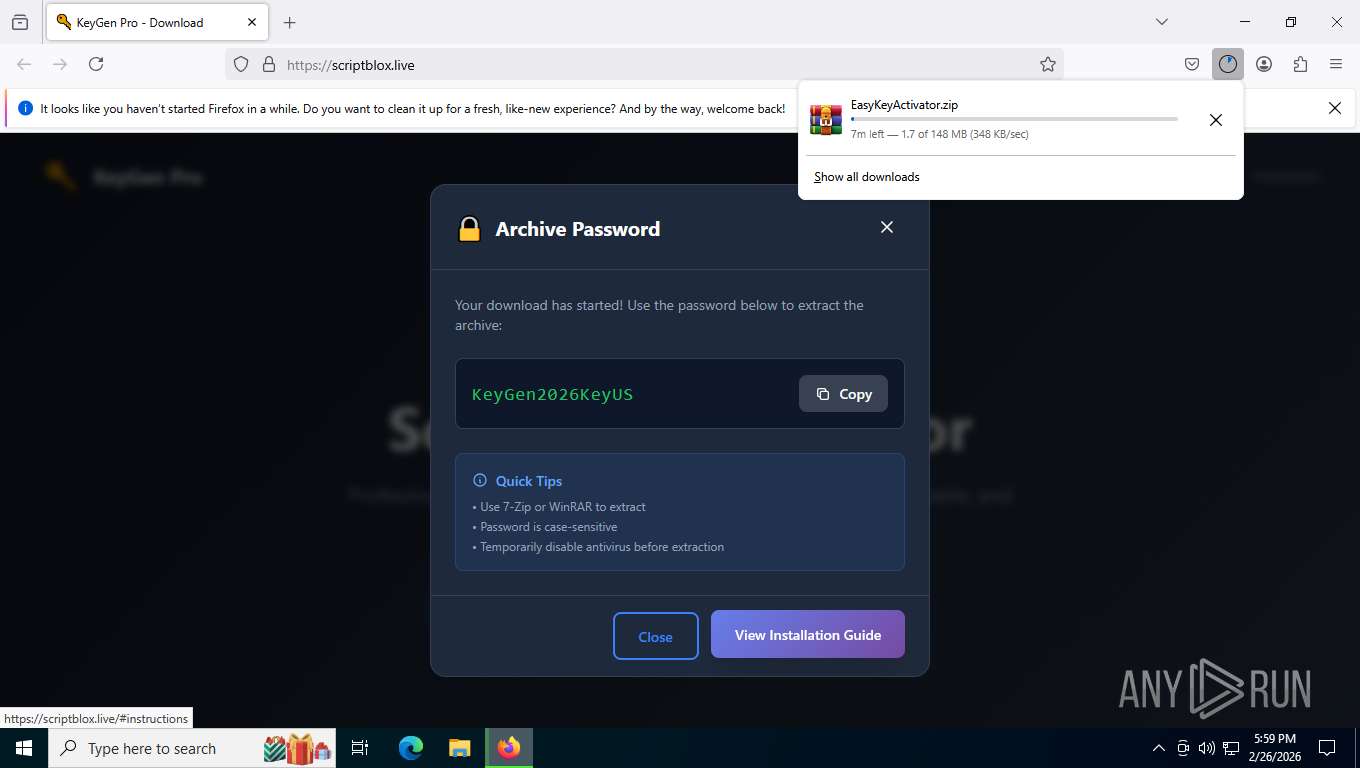
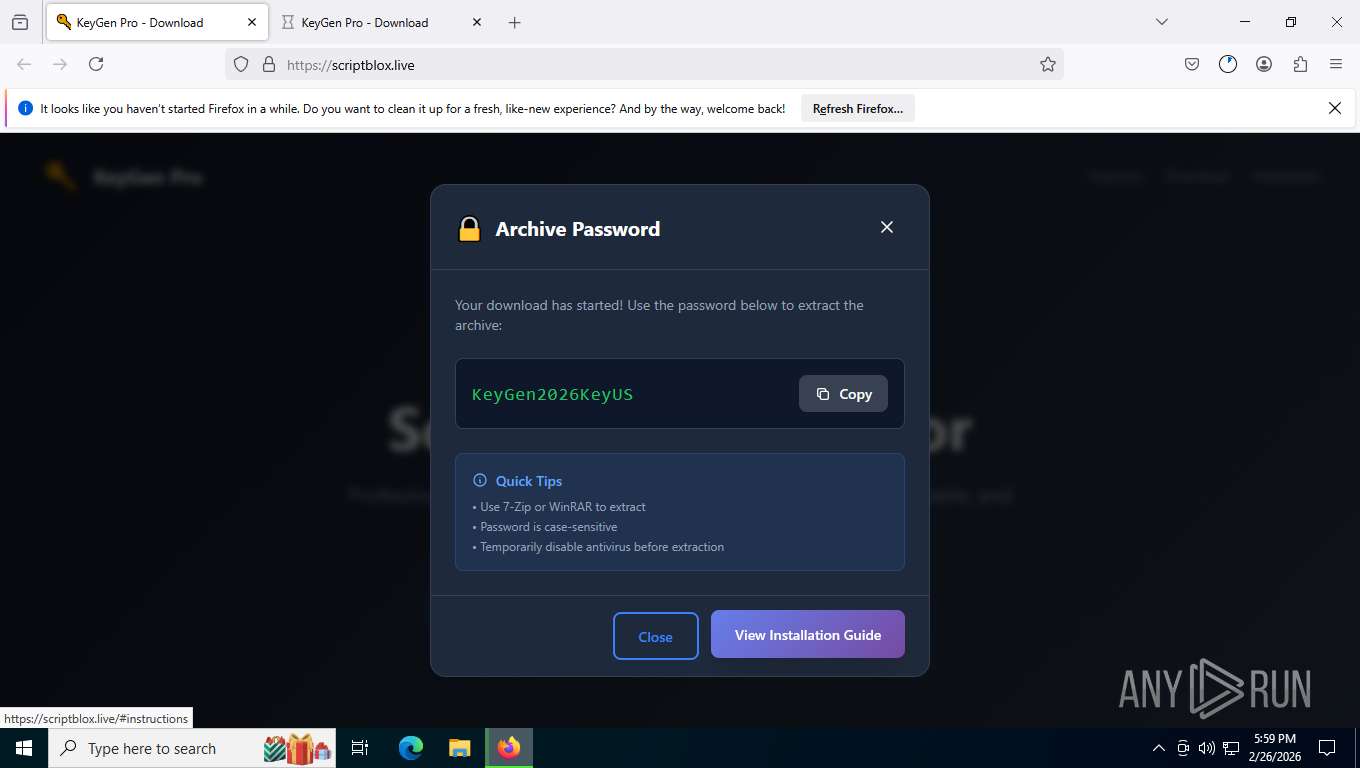
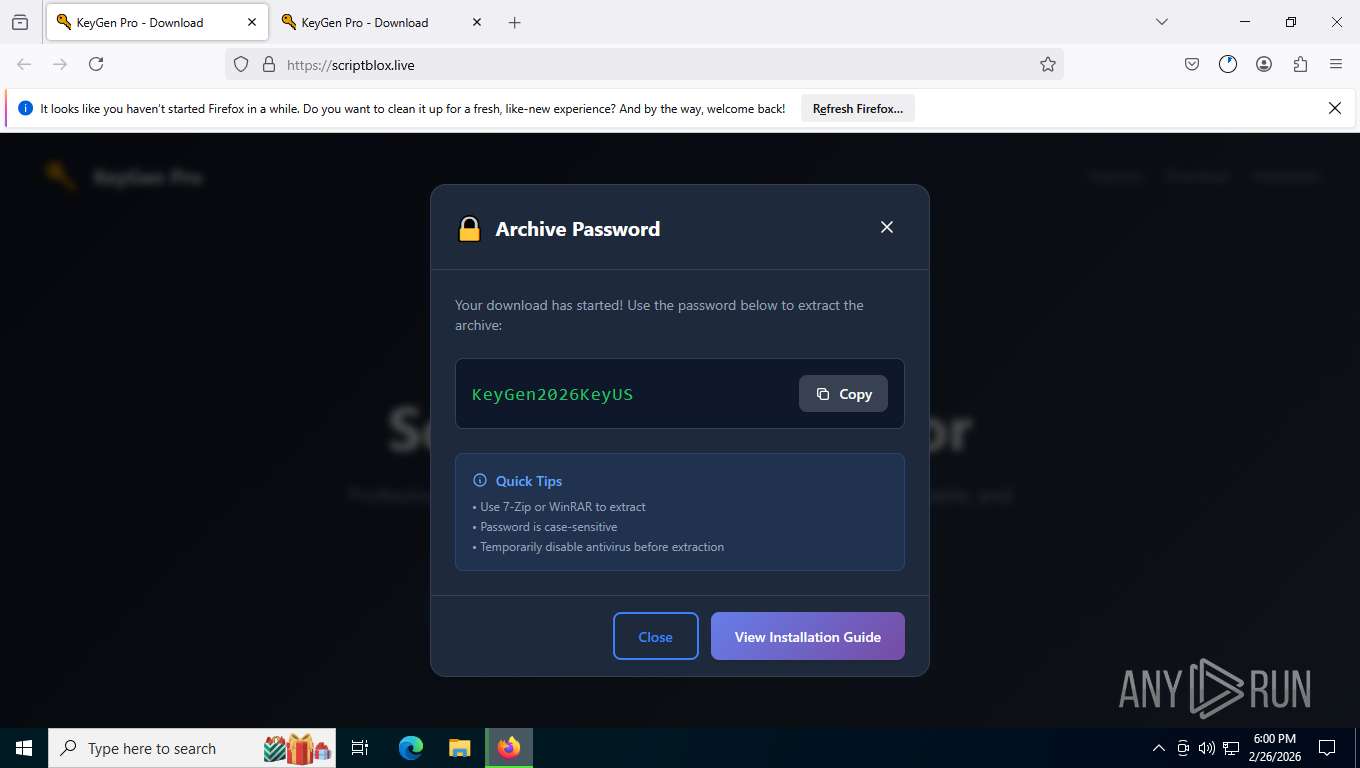
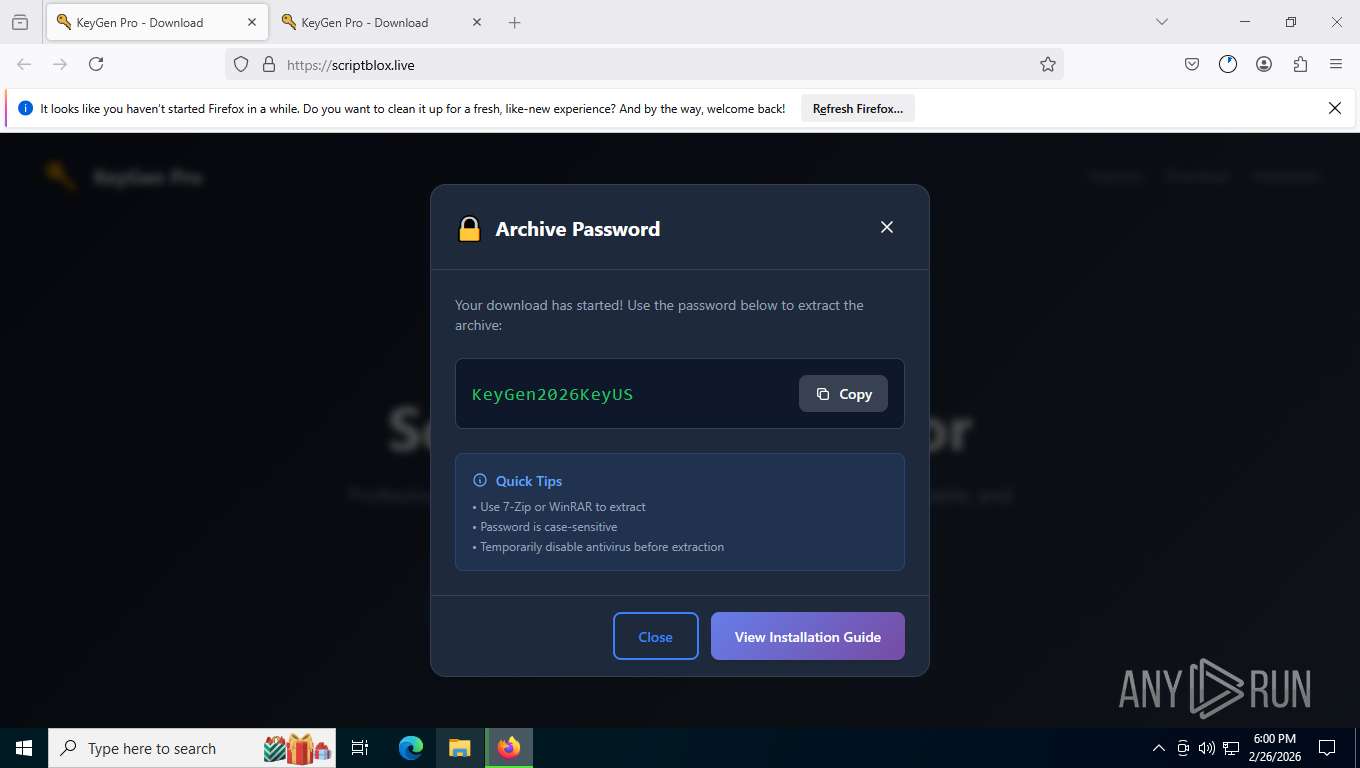
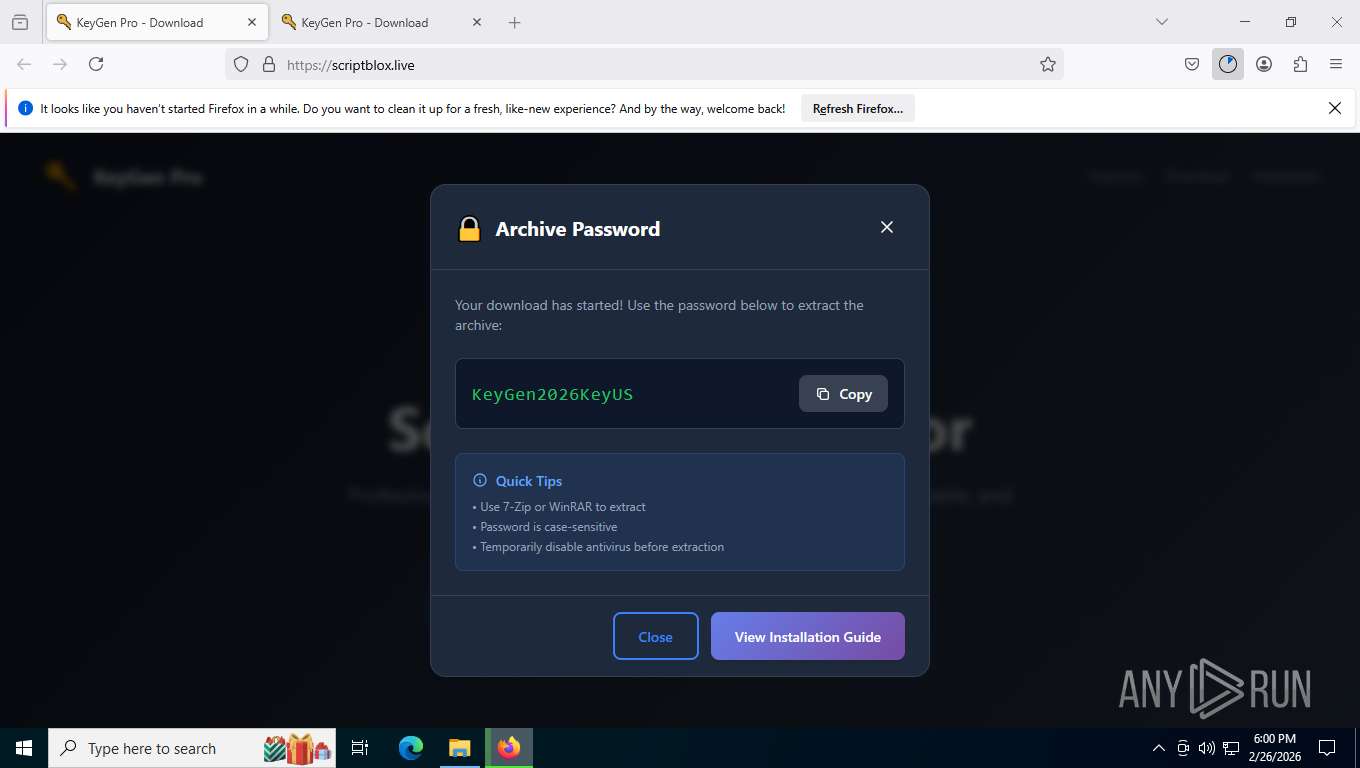
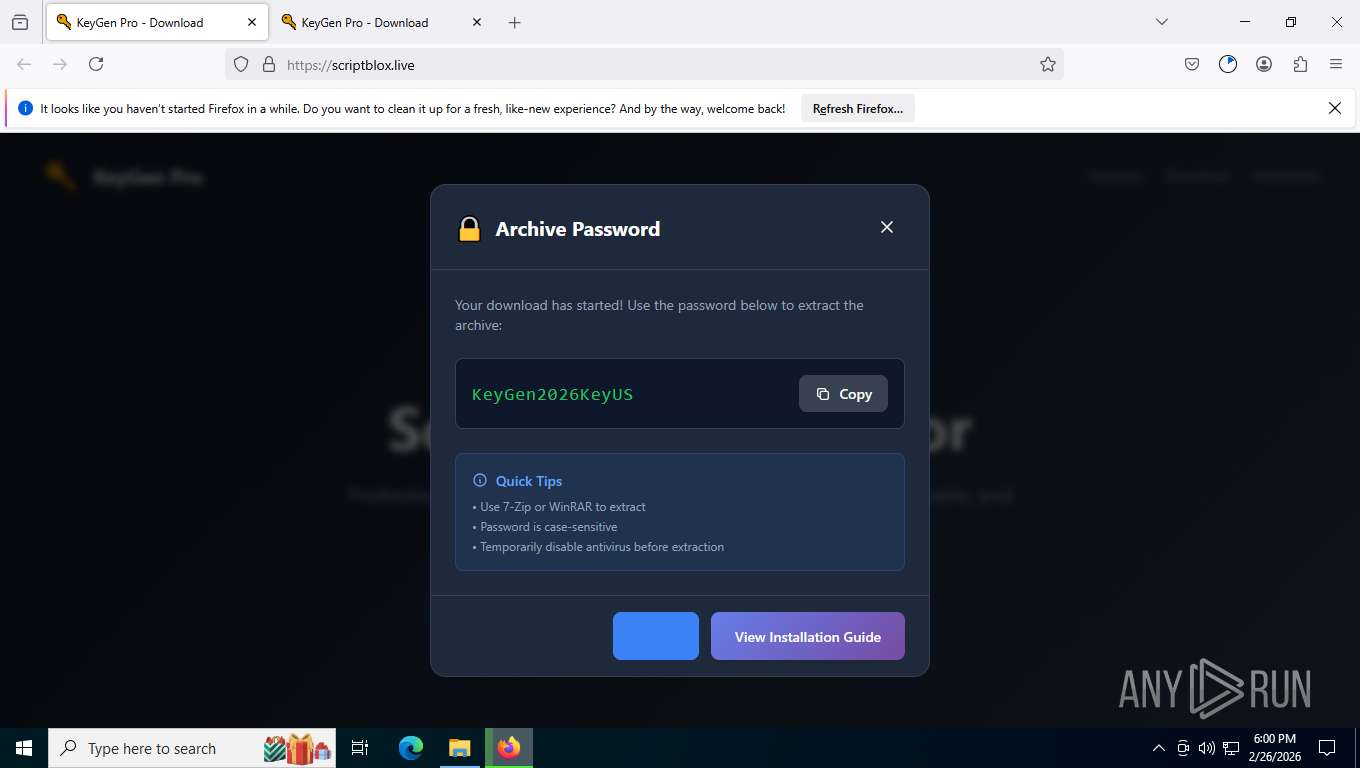
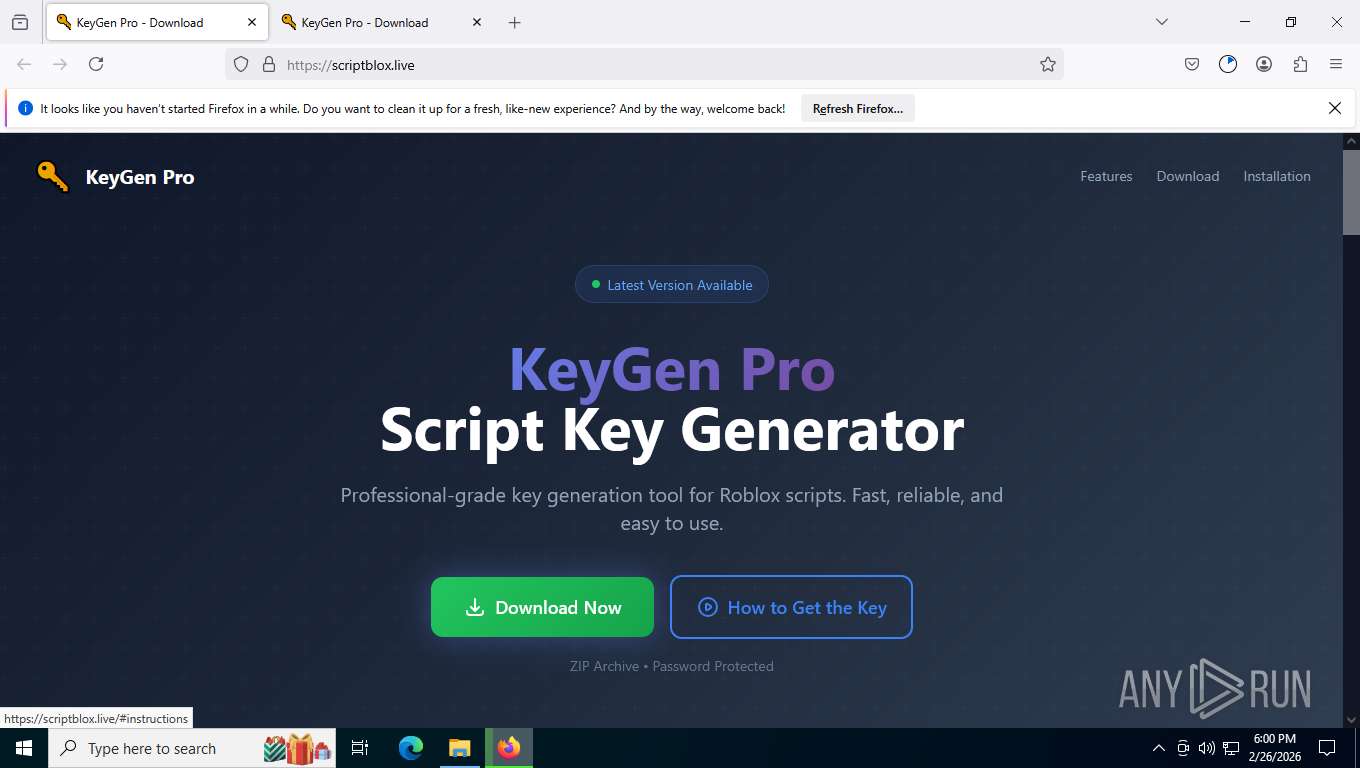
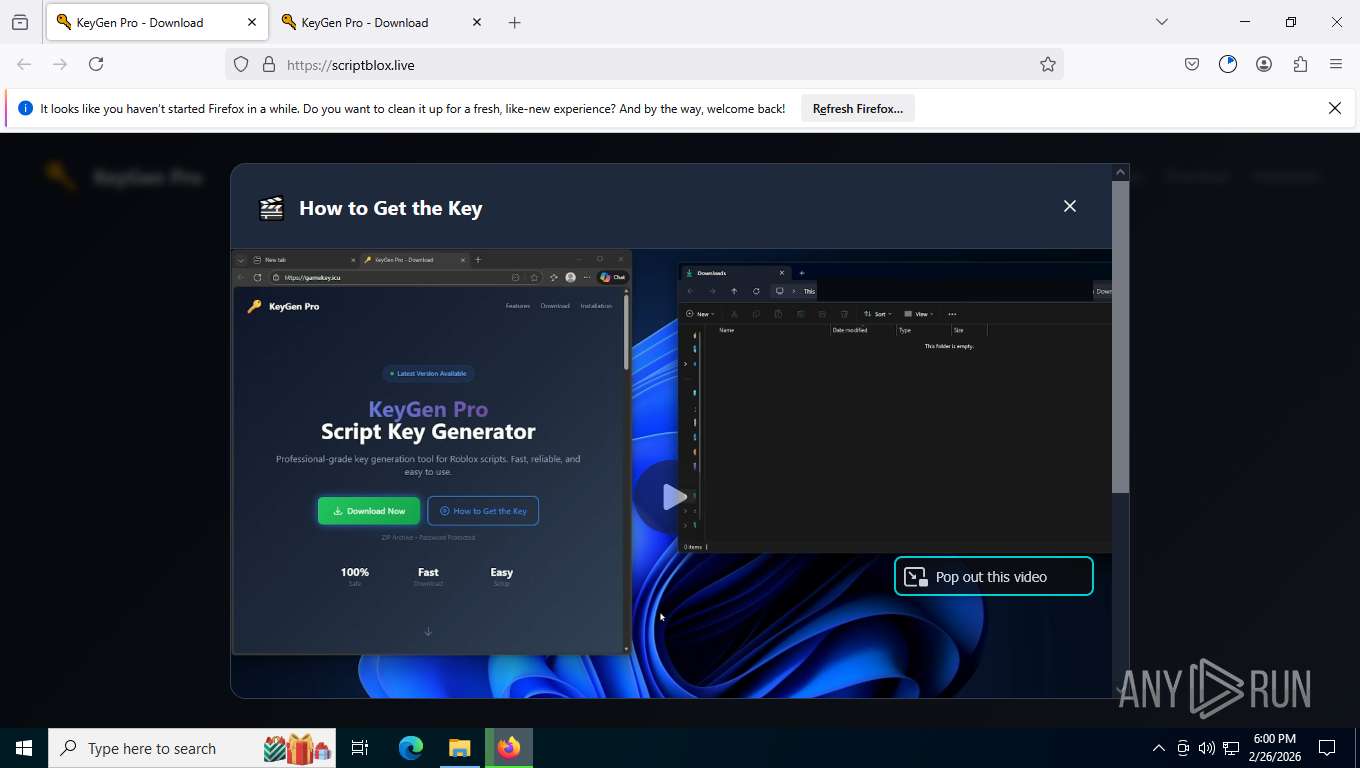
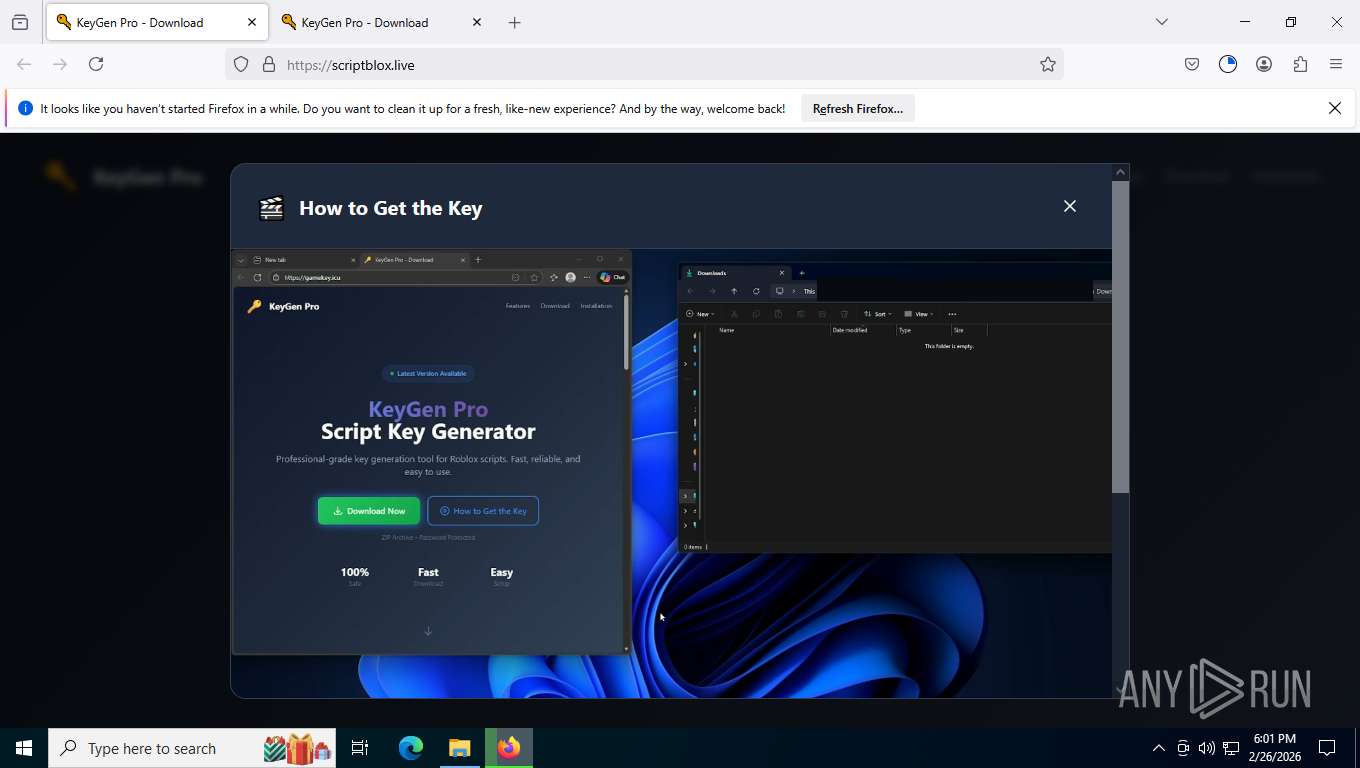
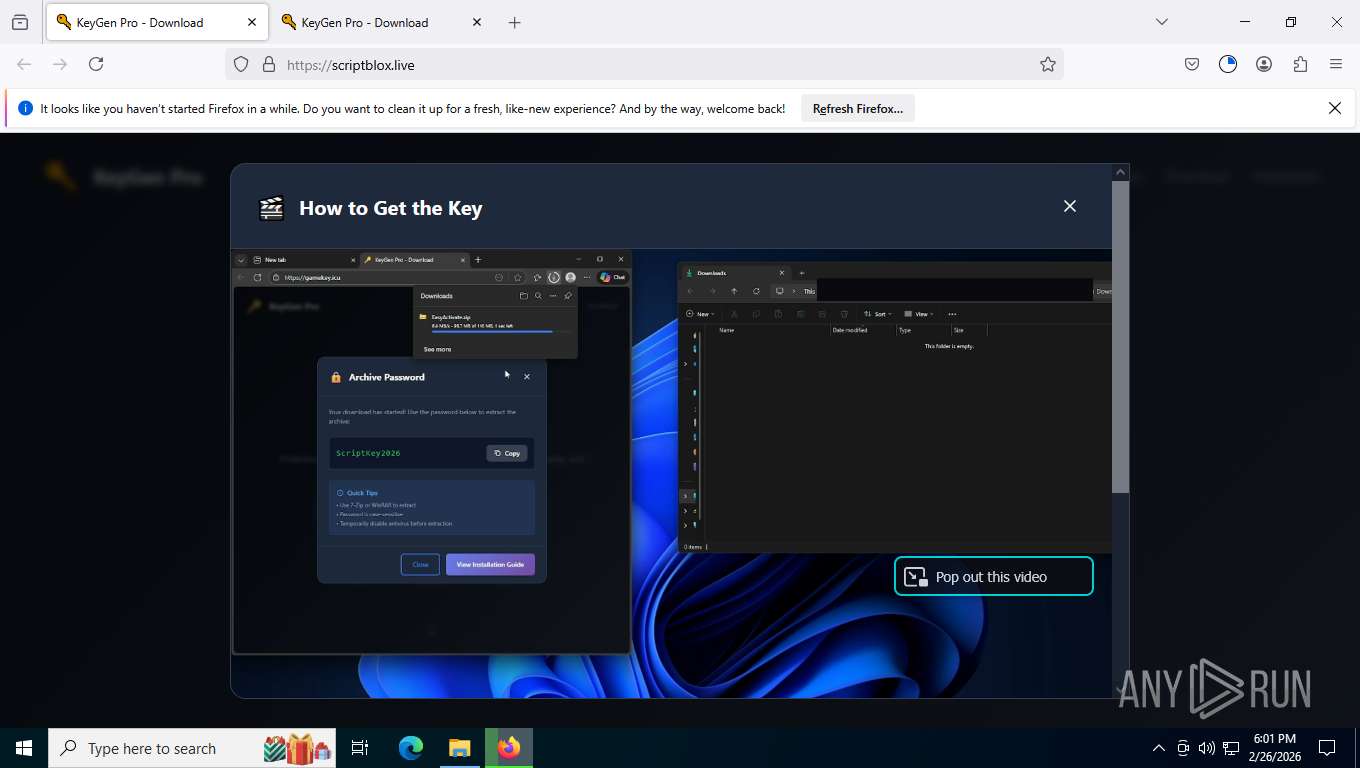
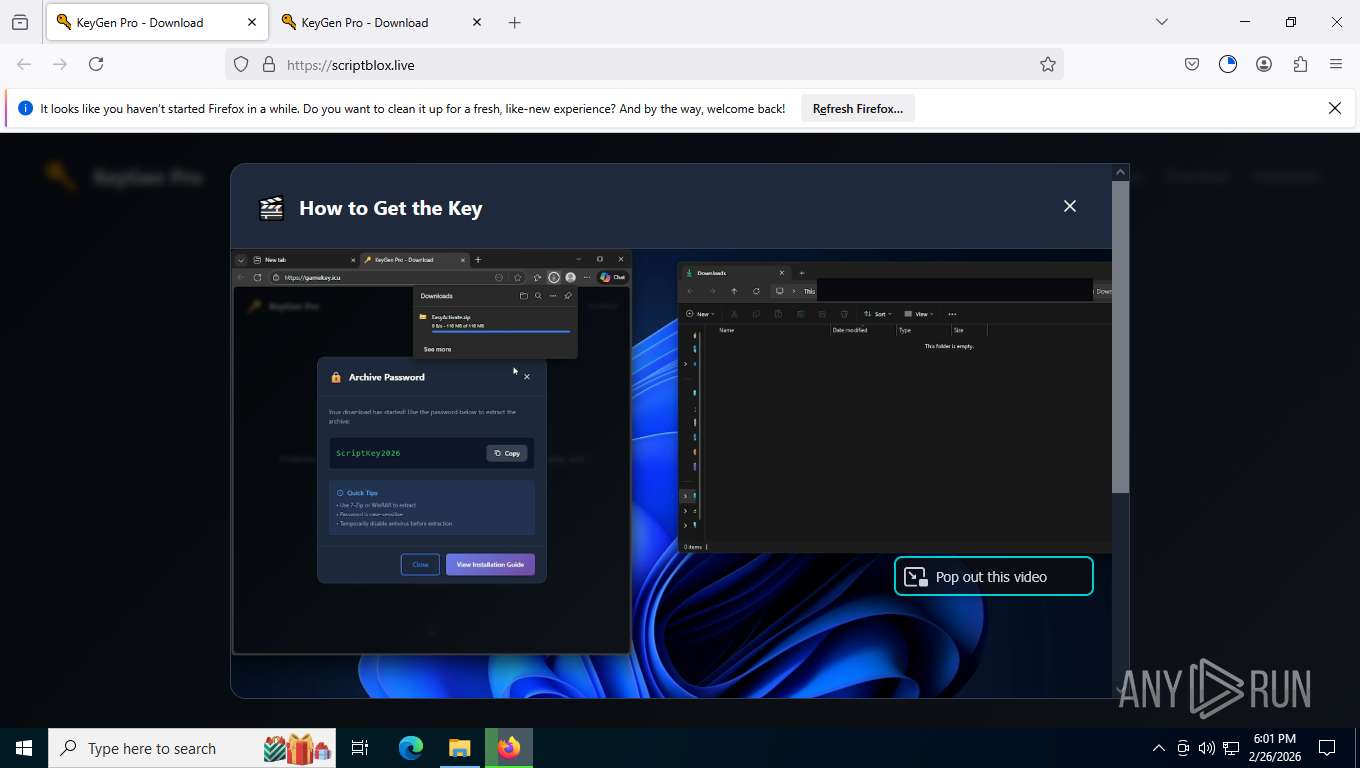
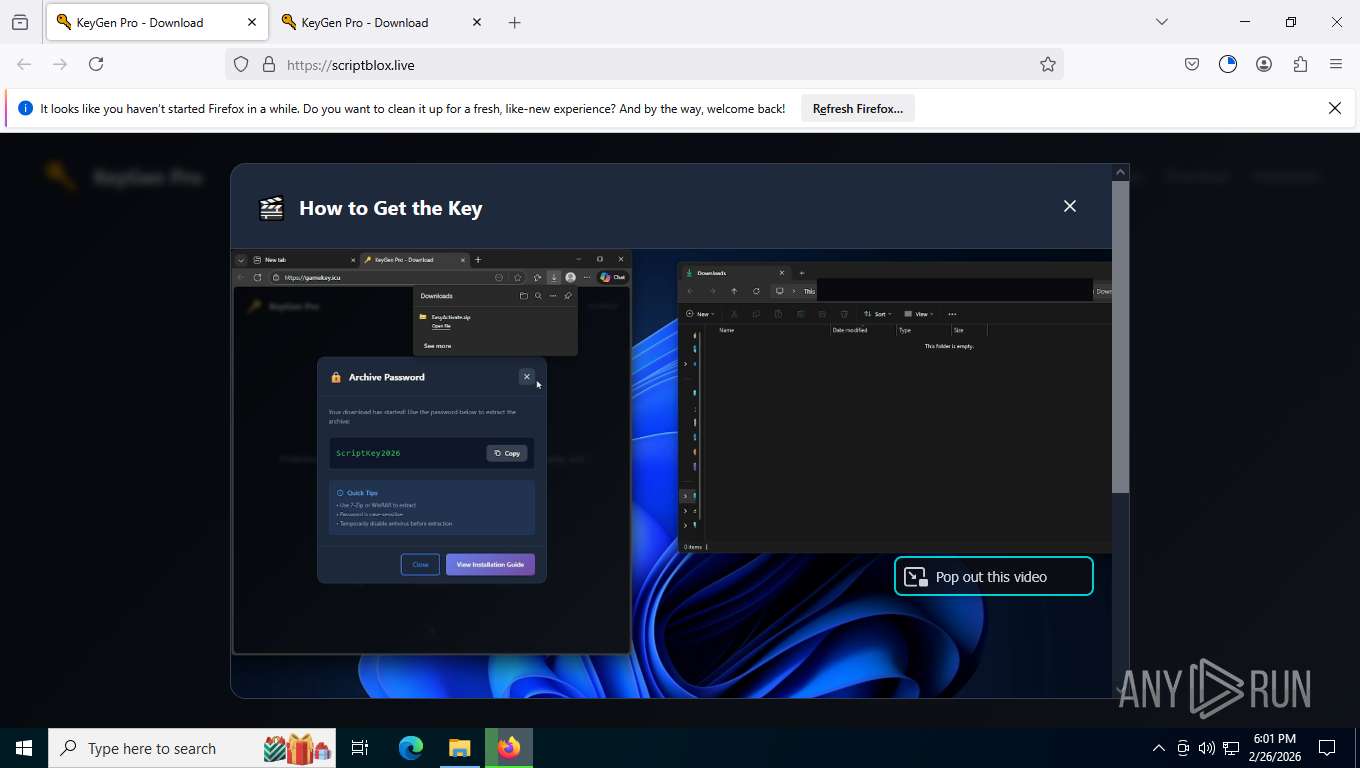
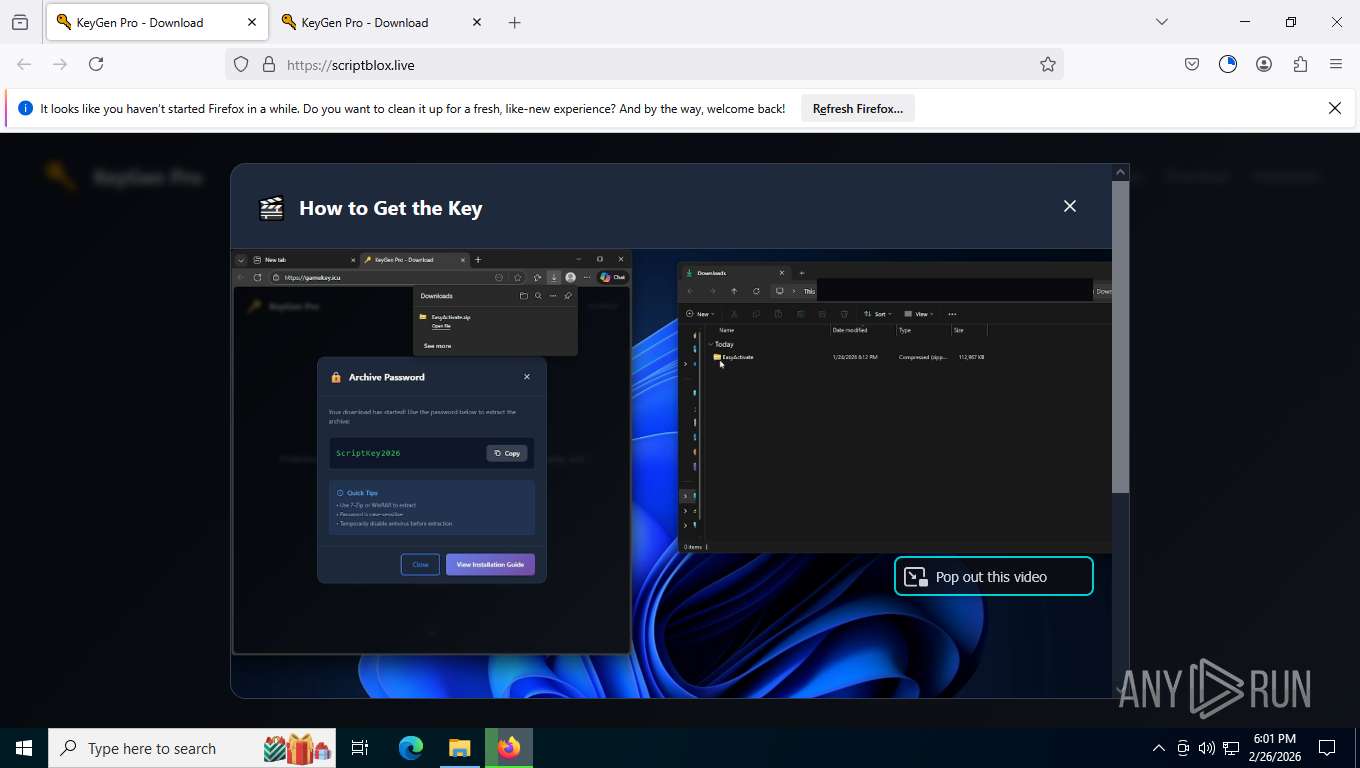
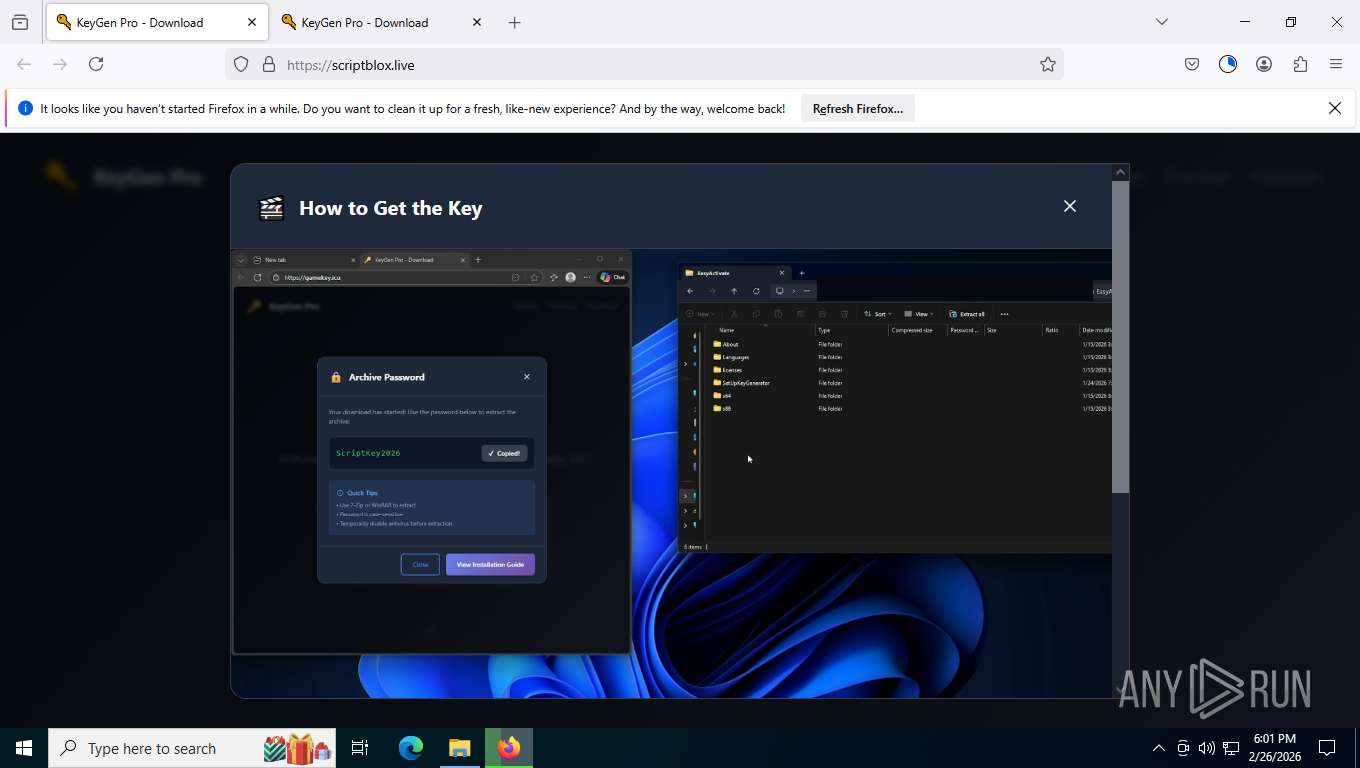
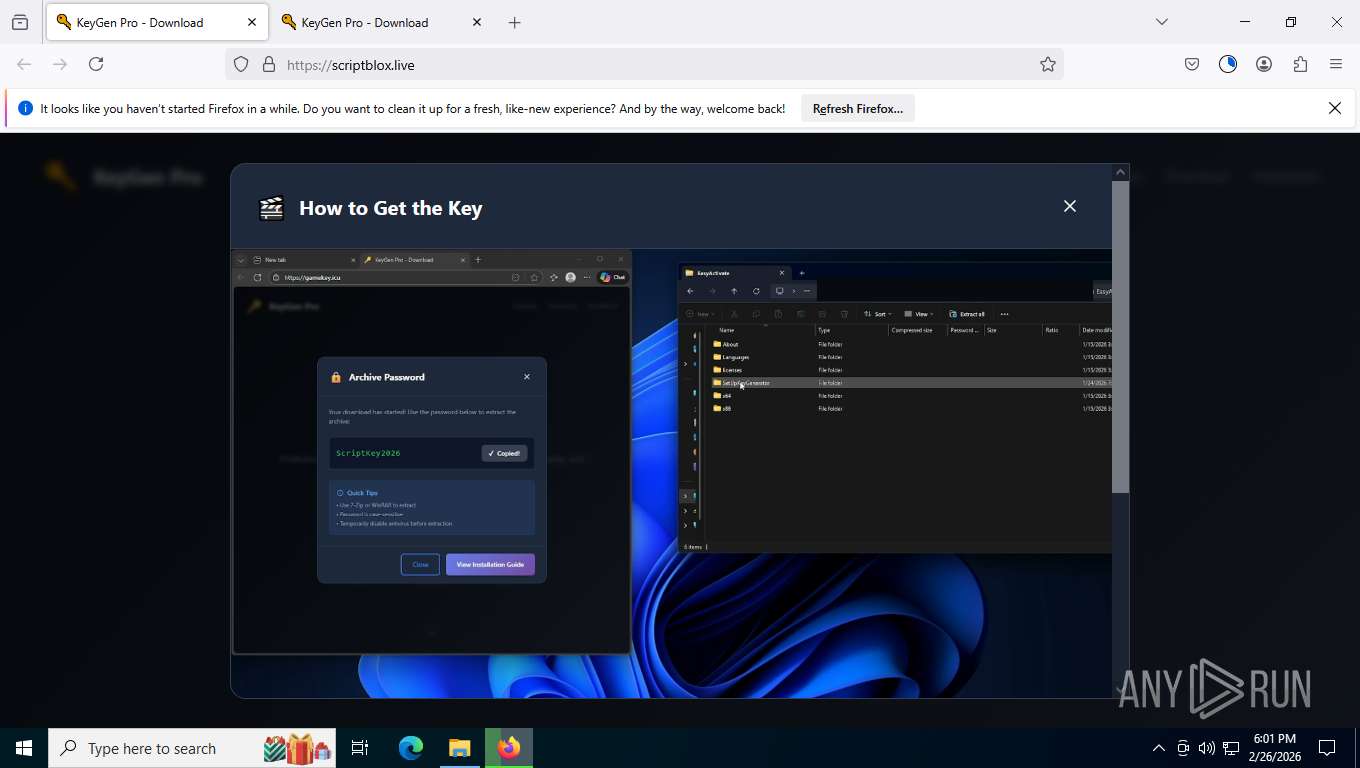
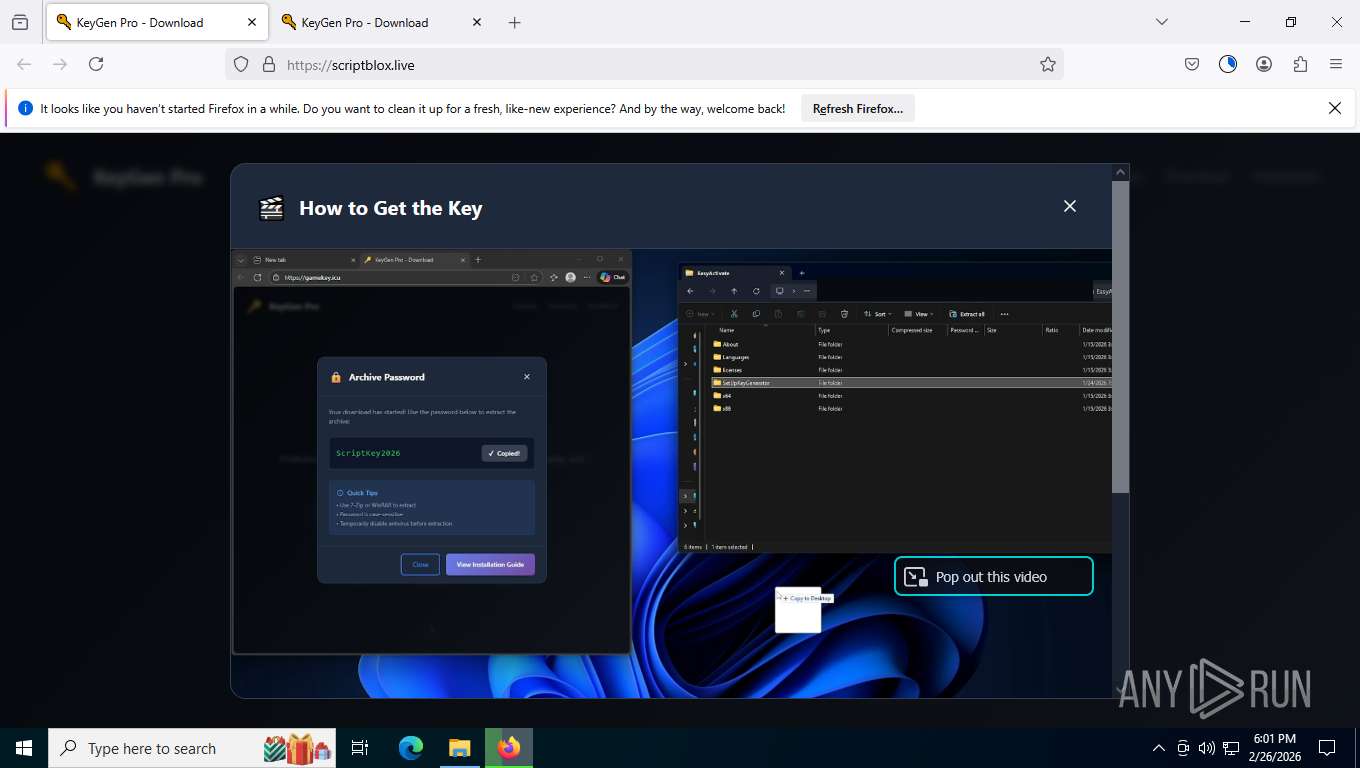
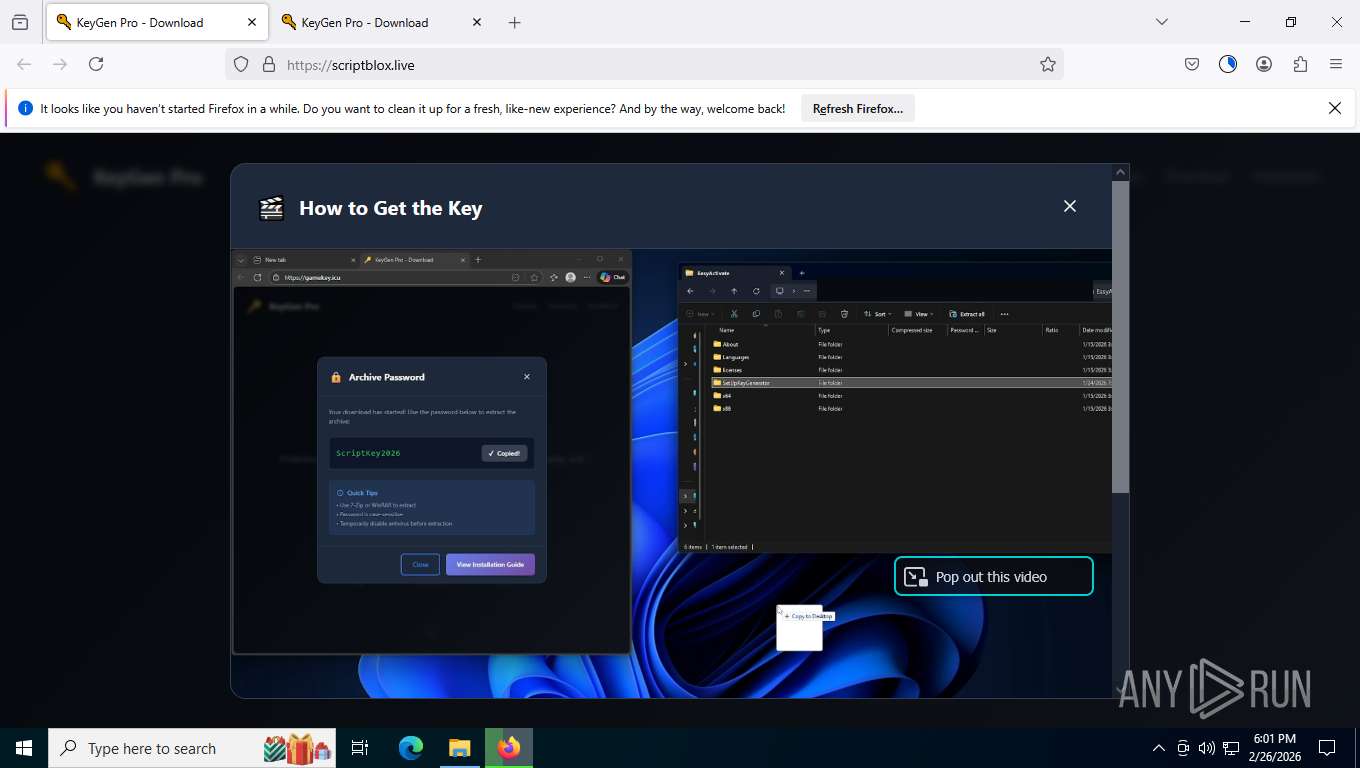
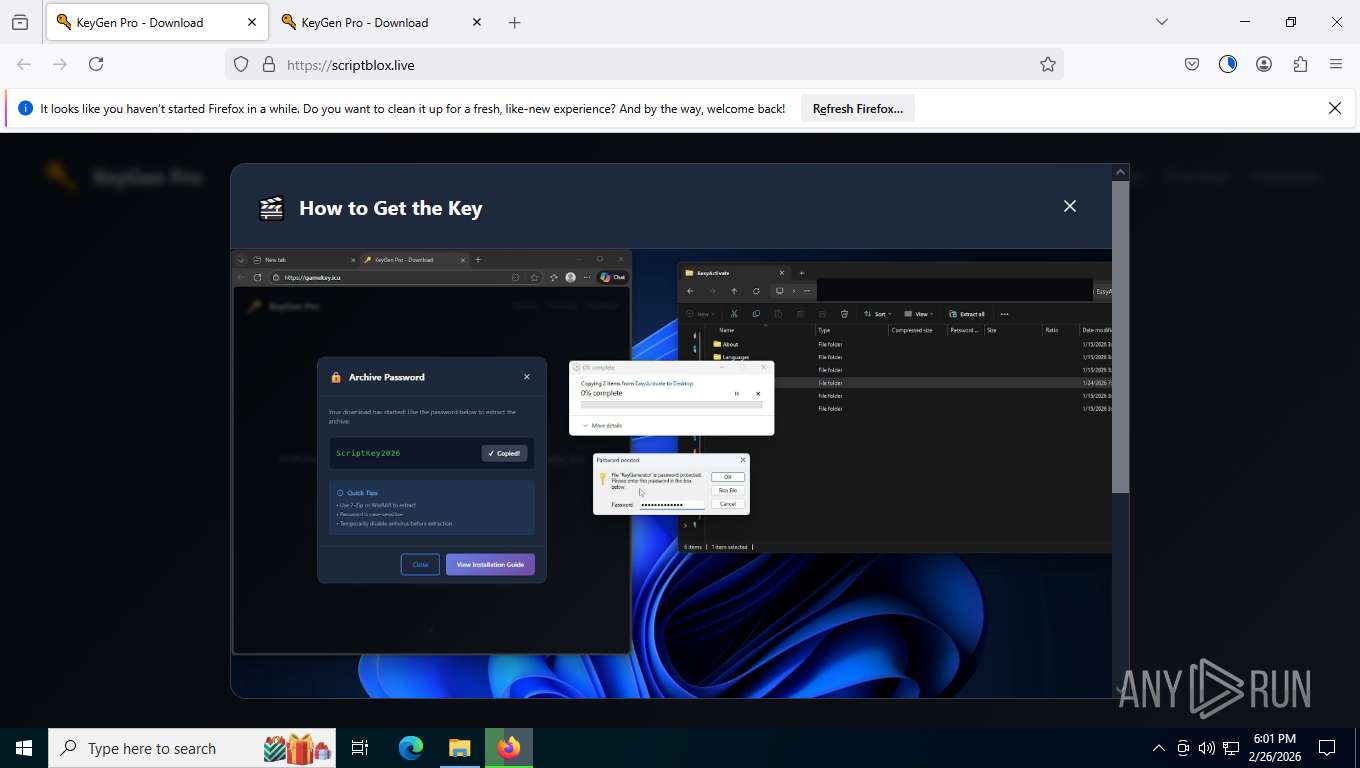
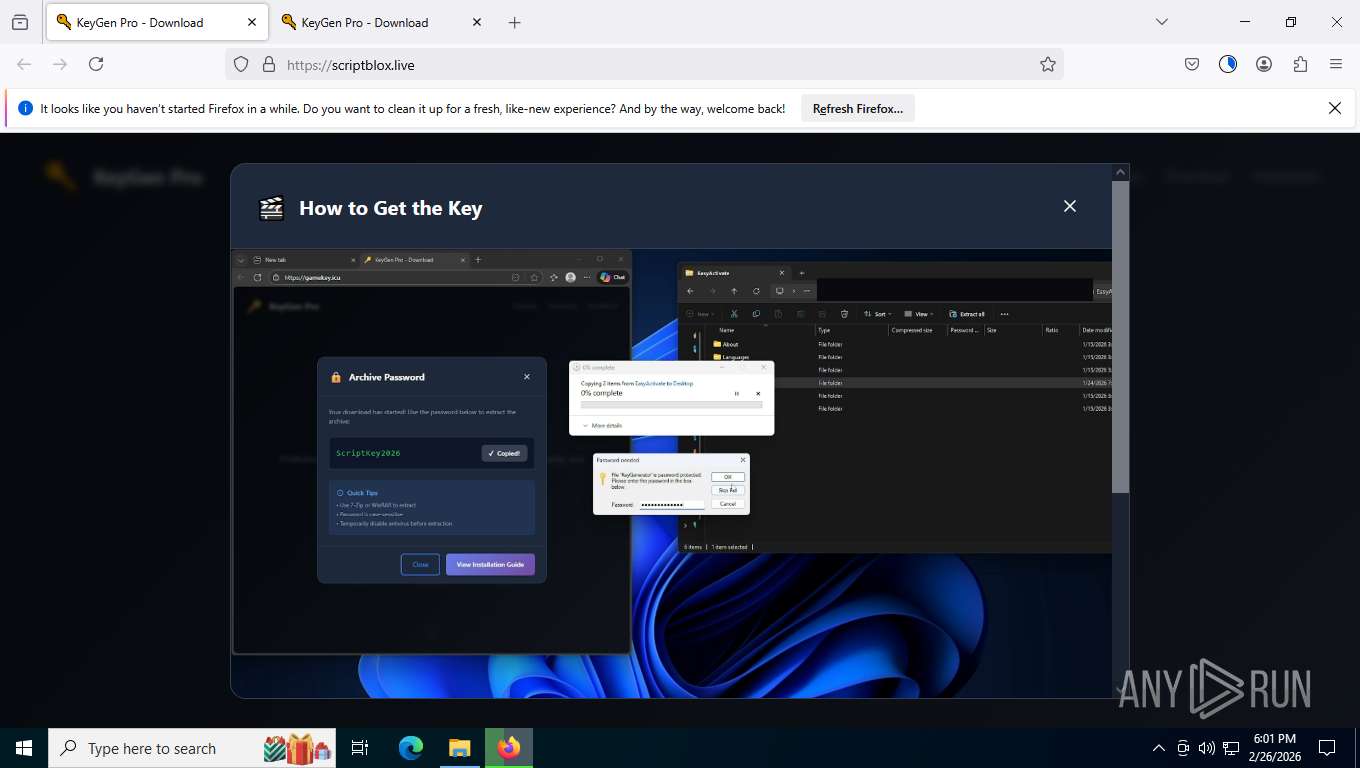
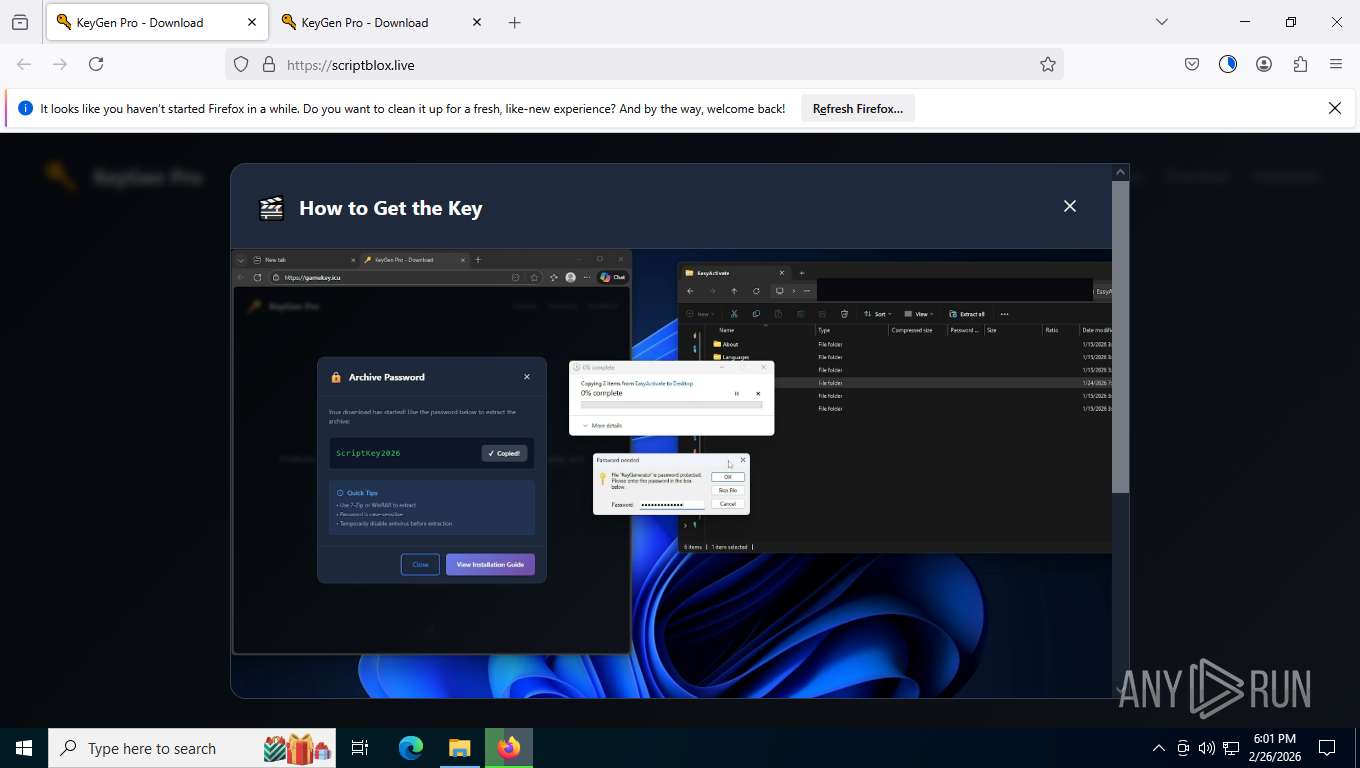
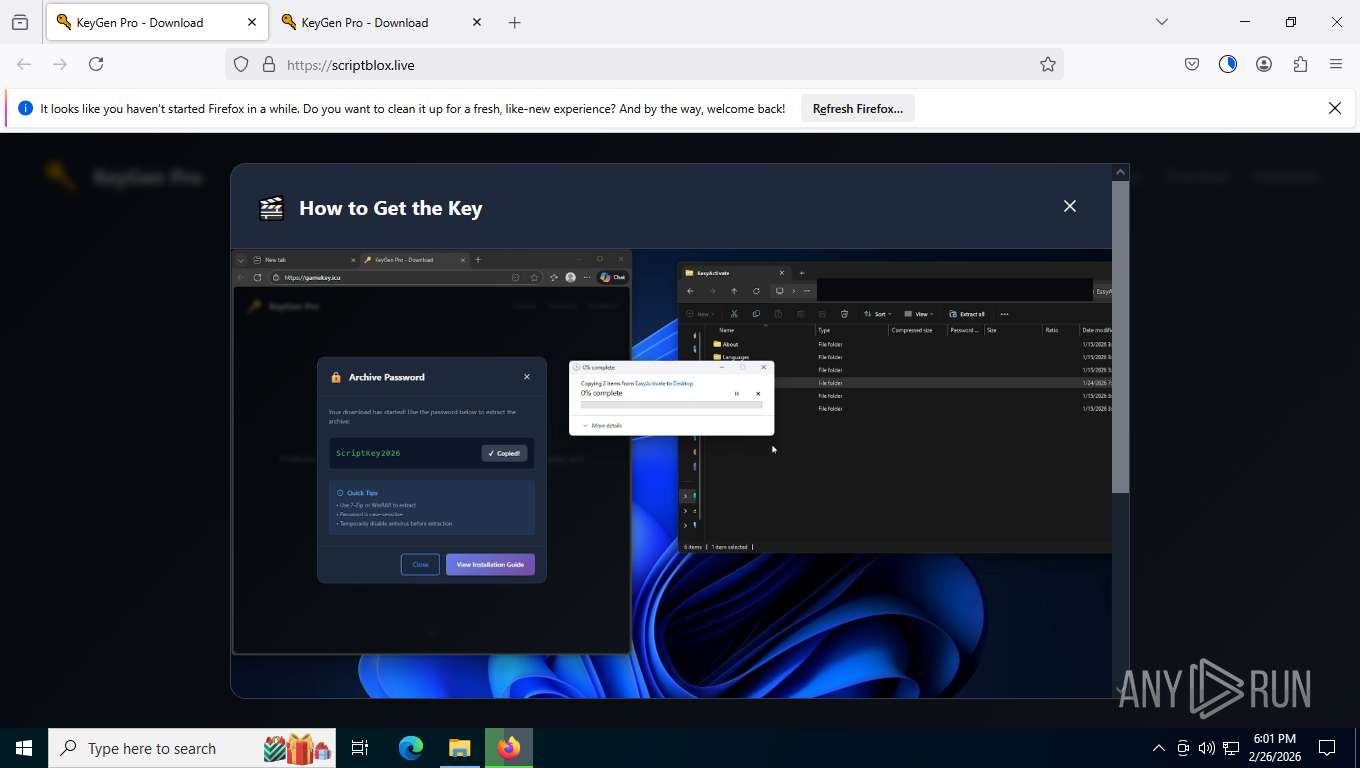
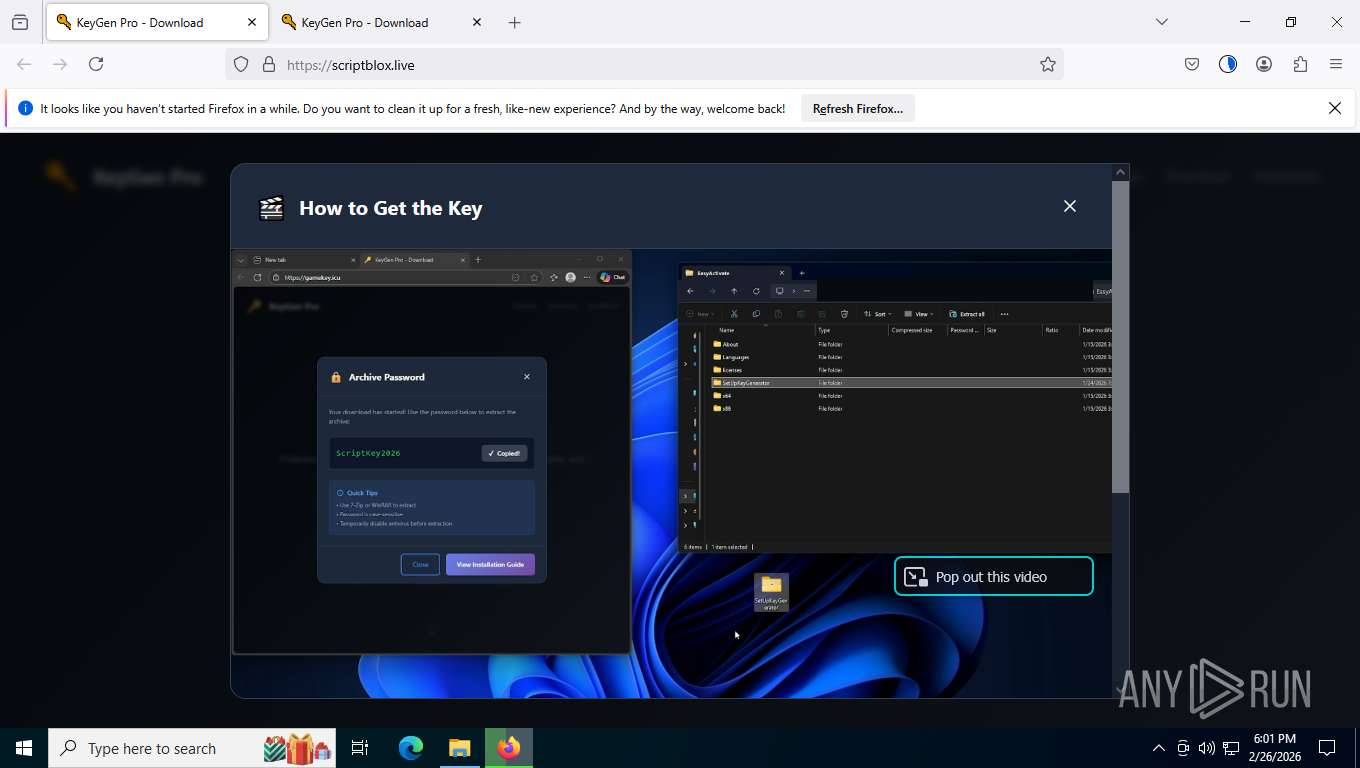
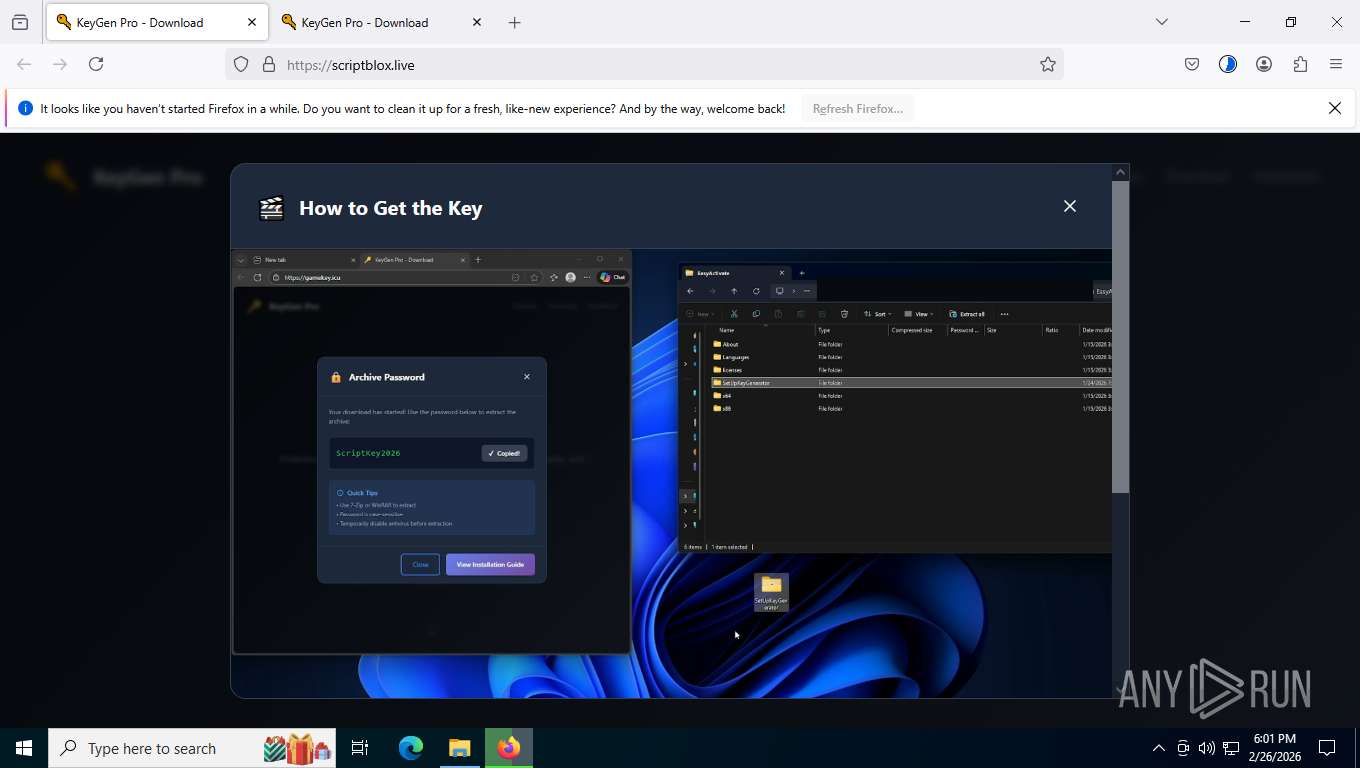
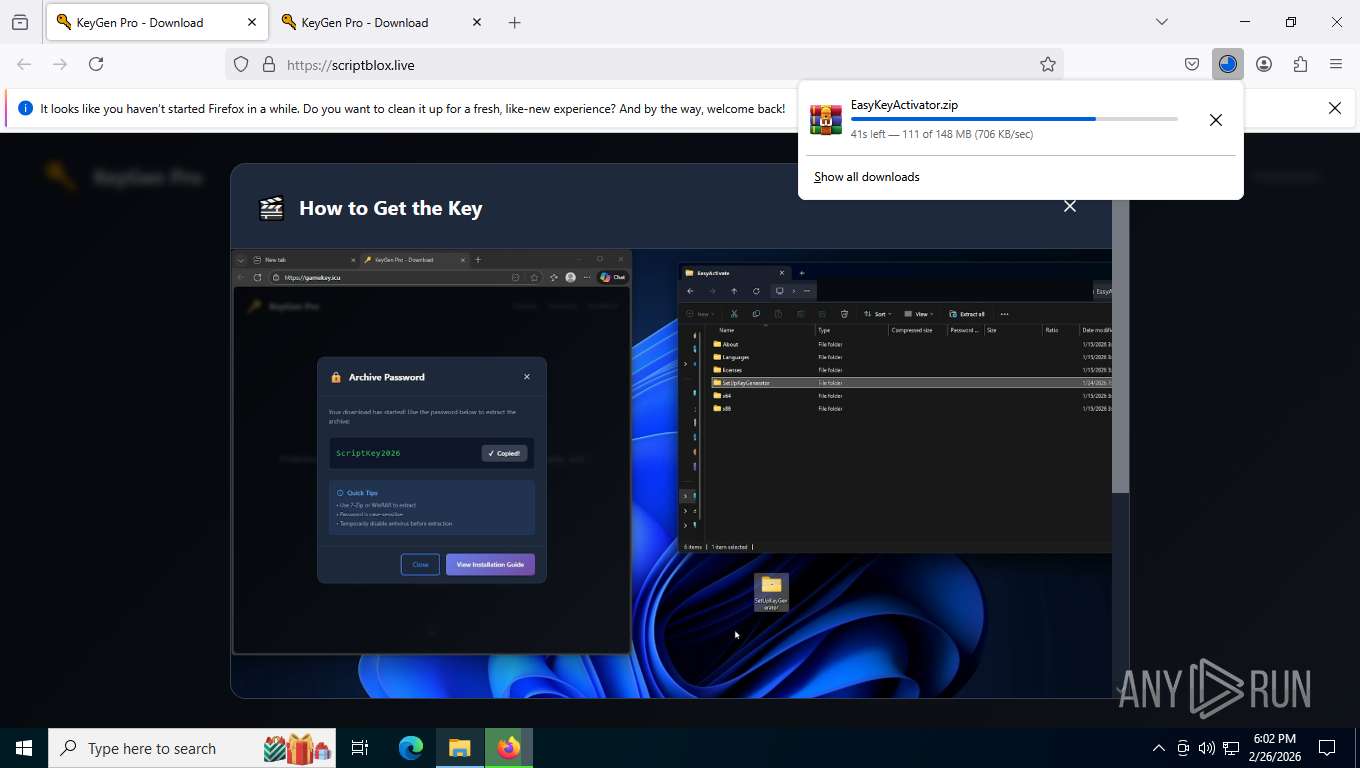
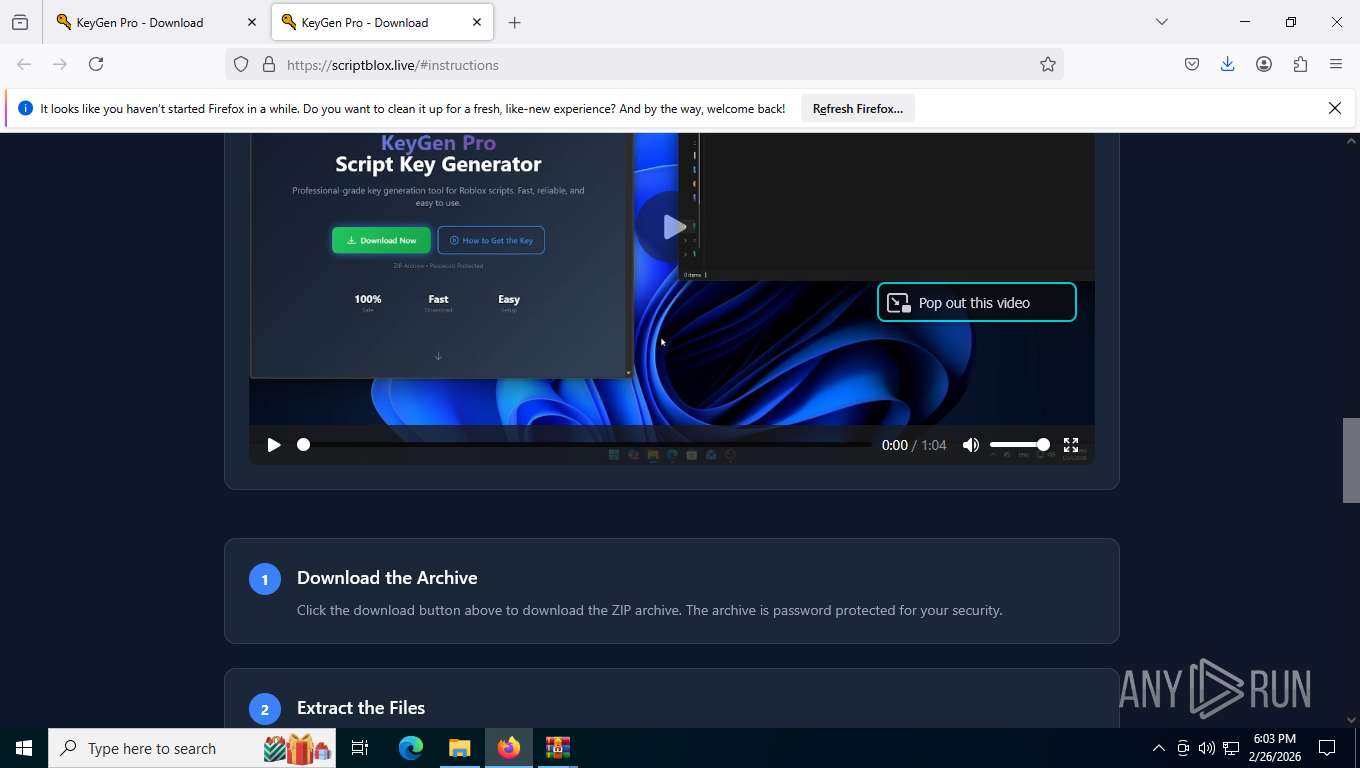
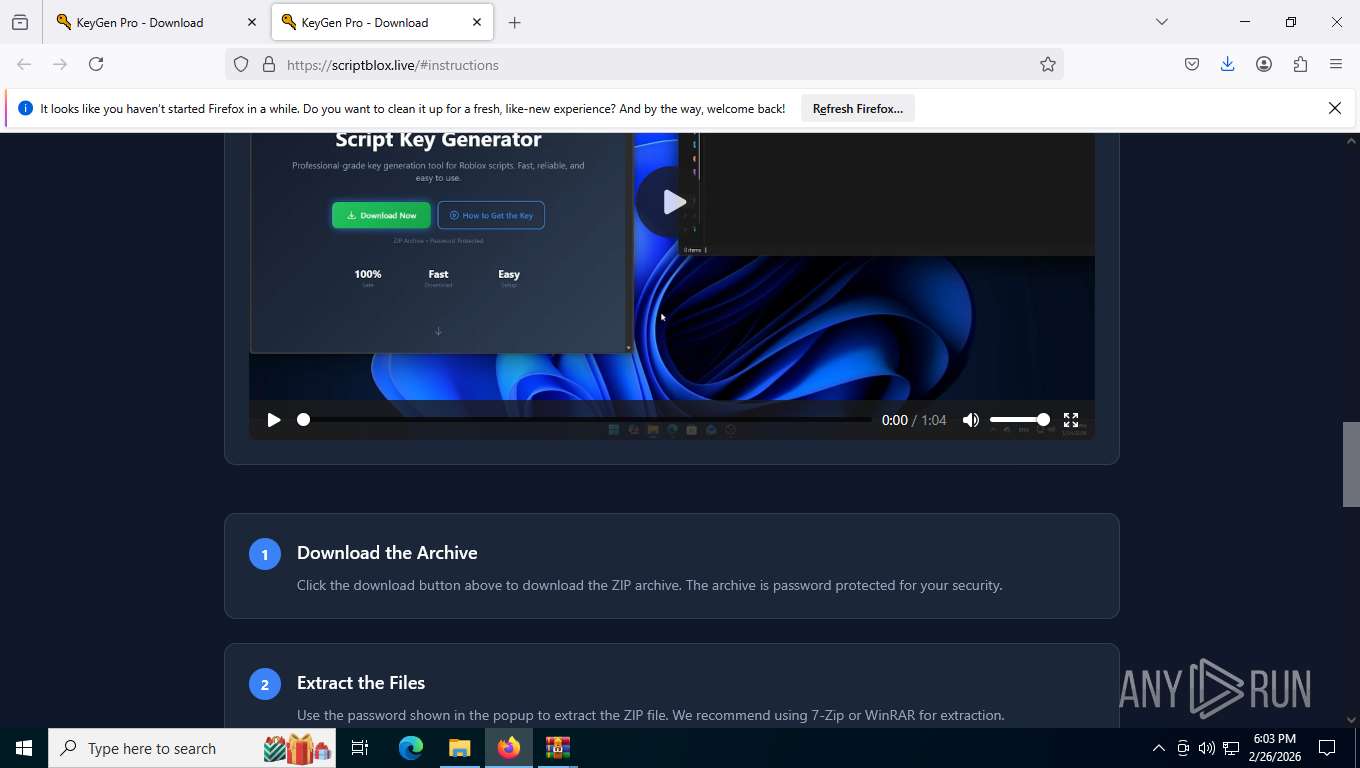
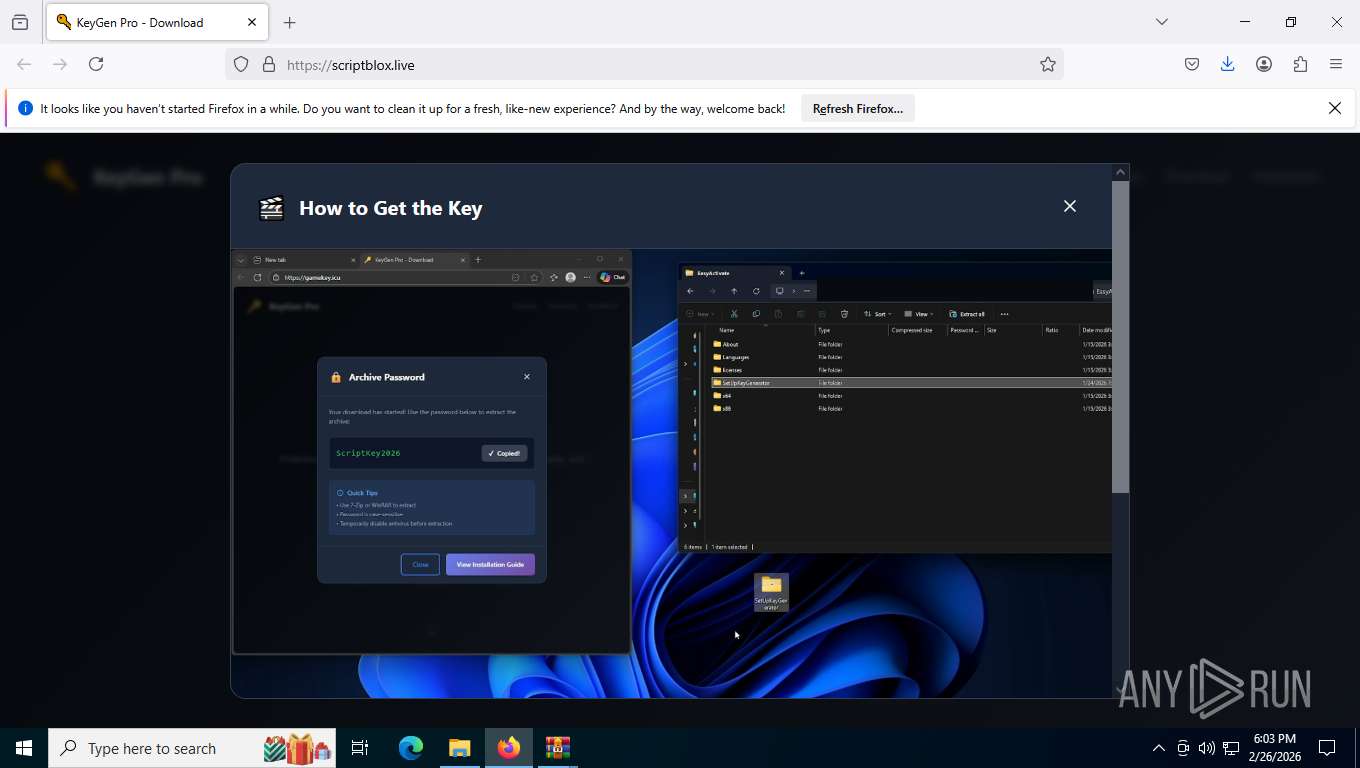
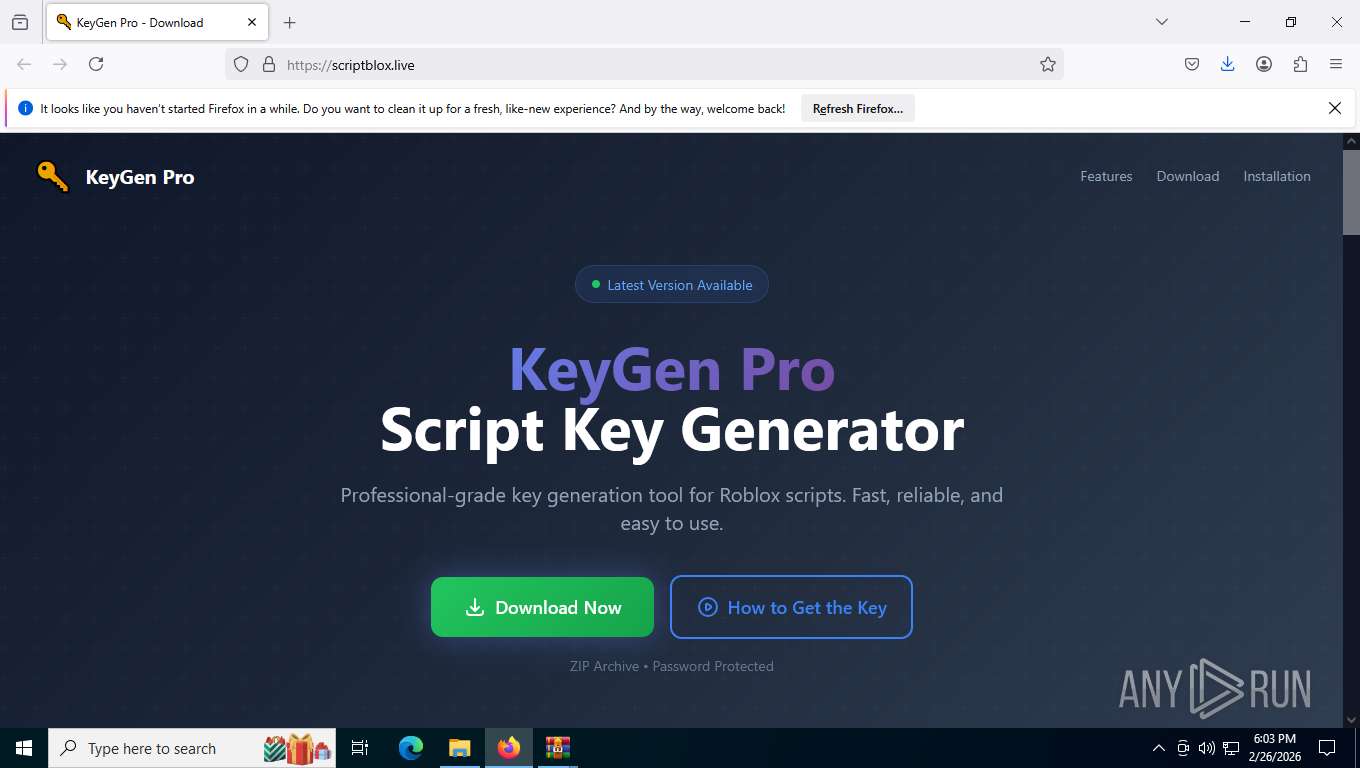
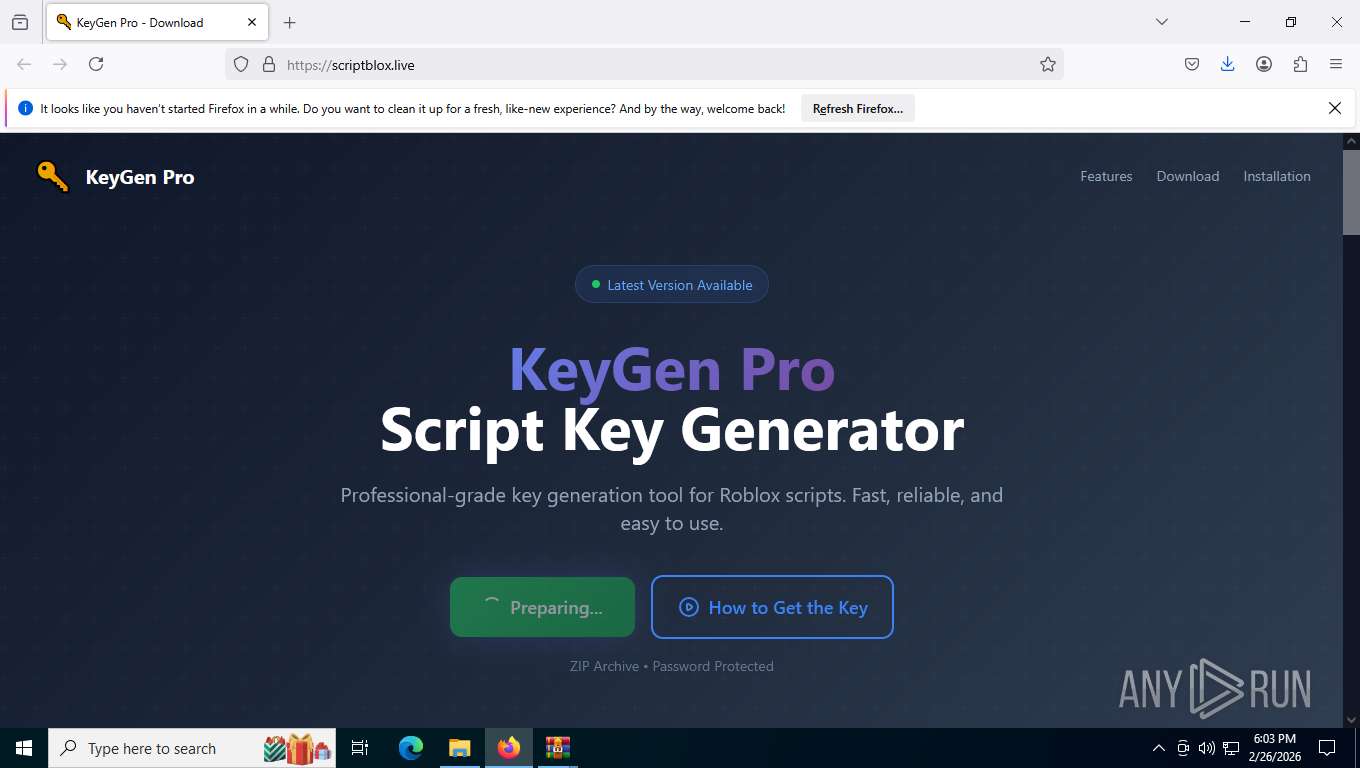
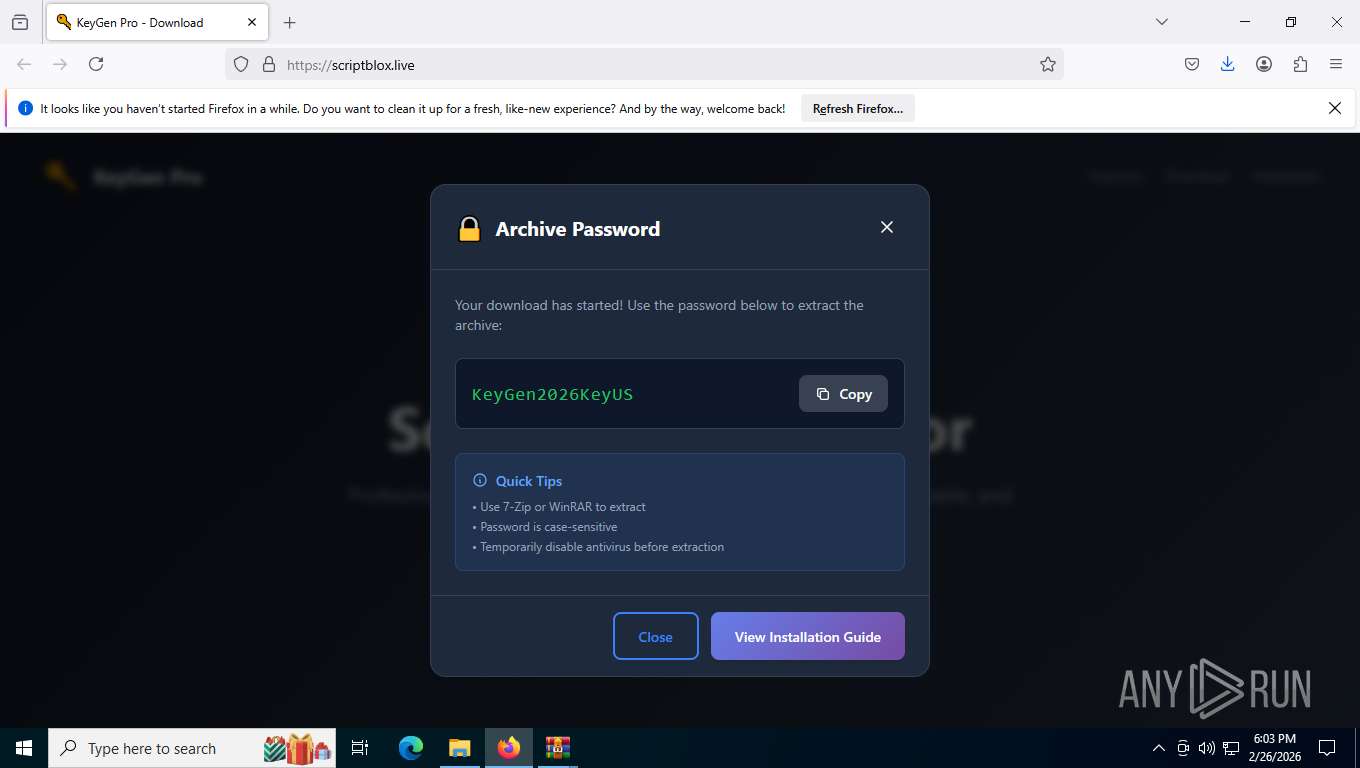
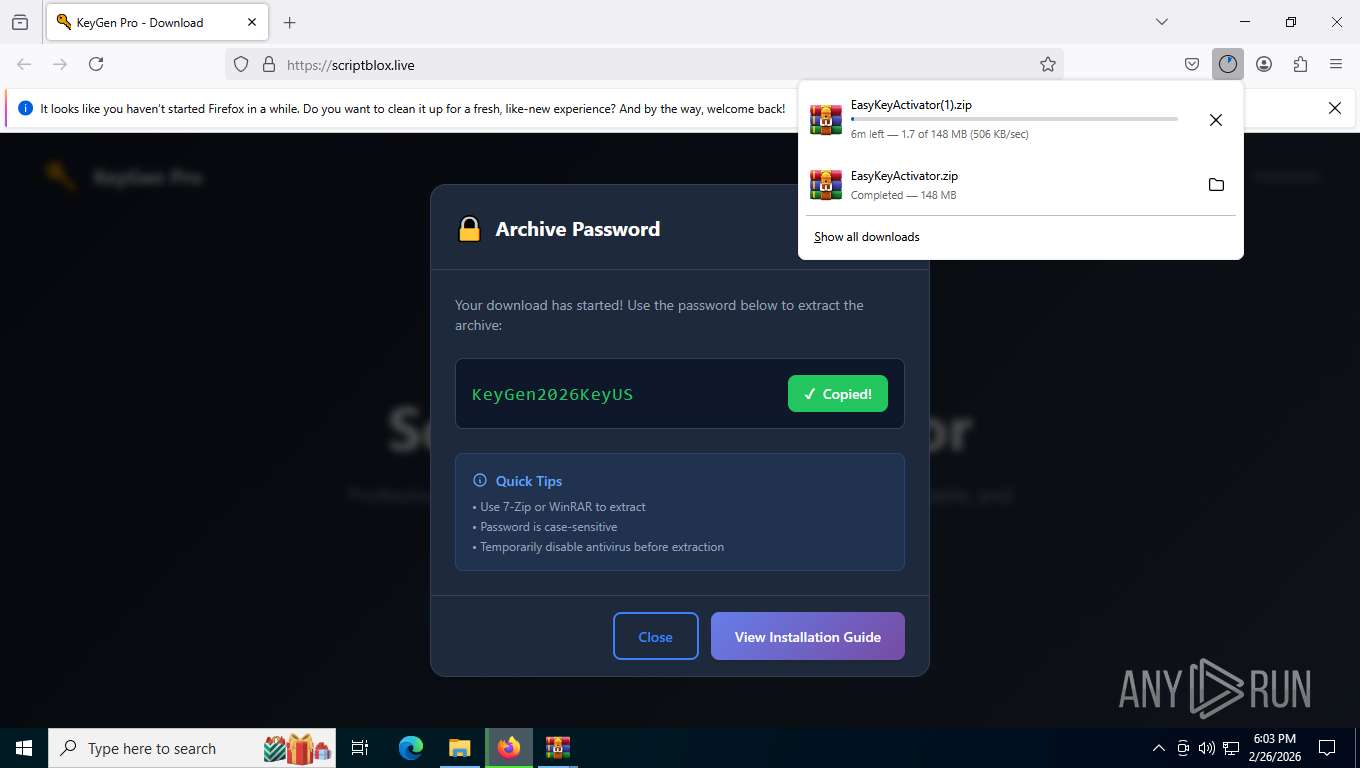
| URL: | https://scriptix.live |
| Full analysis: | https://app.any.run/tasks/ee929d48-cc7d-4896-9901-5ef11ec011f2 |
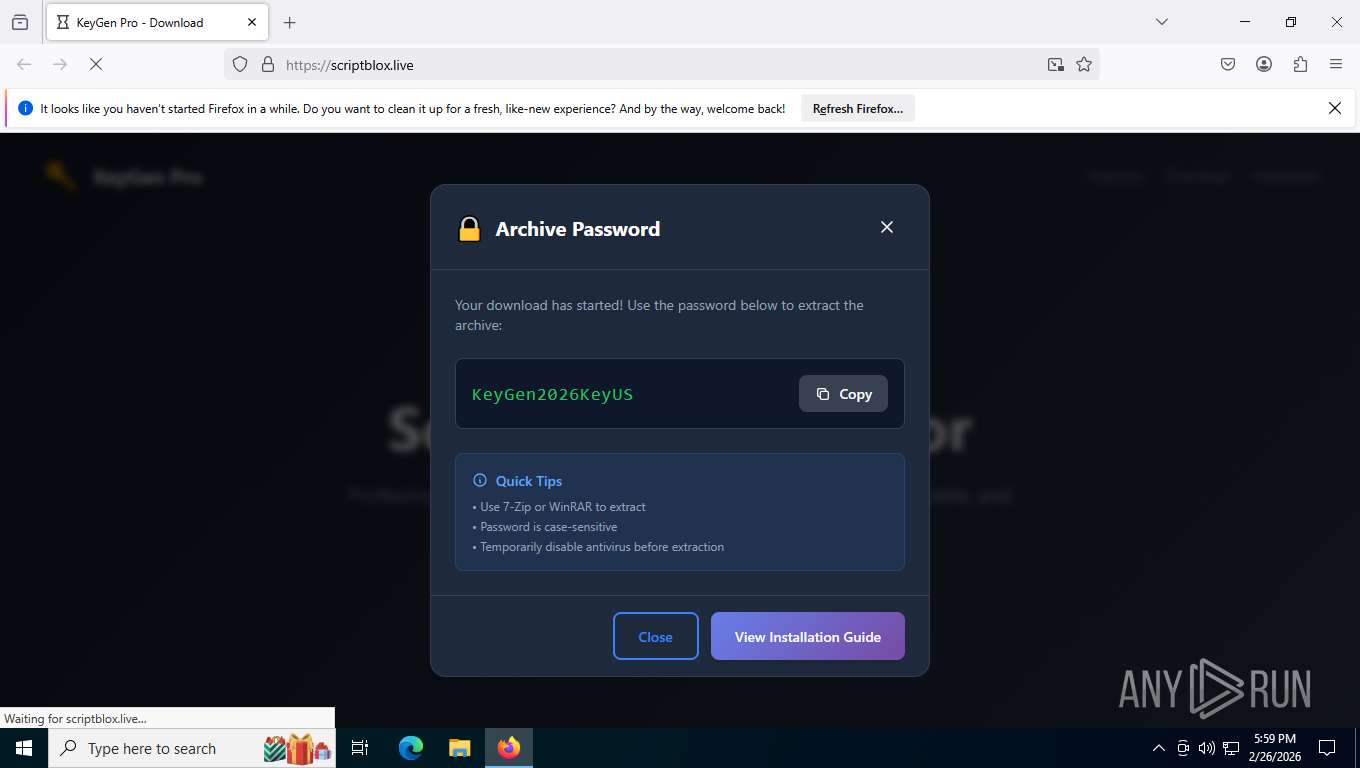
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2026, 22:59:25 |
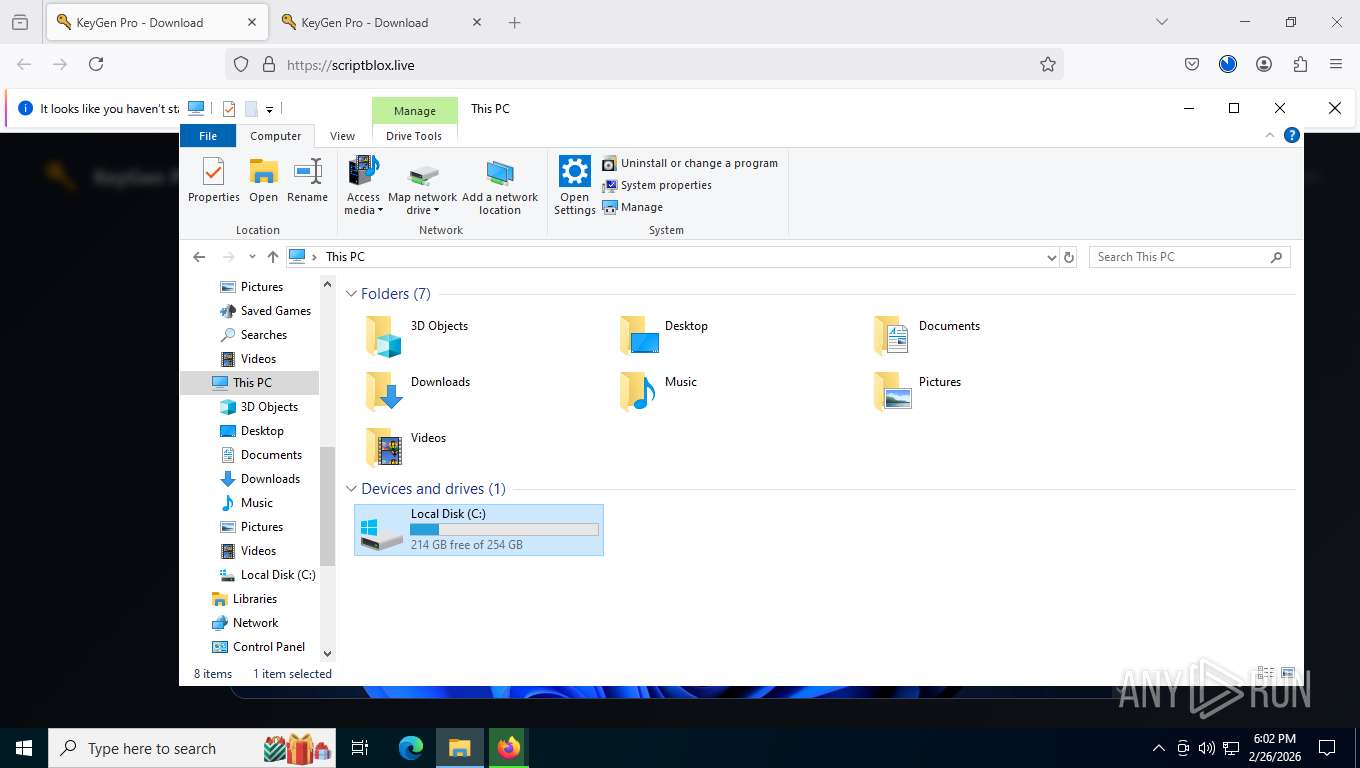
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 7BFAB35B5120951A10B9E93CA77E1668 |
| SHA1: | 536516AED824E382EBF3B8A3DE9B7DF2D842C5A5 |
| SHA256: | 19B599C059611A8C69D361F7DEE32F6AC76ACD257C50F8F0E4786D62EBB81C60 |
| SSDEEP: | 3:N8LY6Jzn:2U6Jzn |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8268)
ETHERHIDING has been detected (SURICATA)
- zyCACcaDQJcSvND.exe (PID: 8772)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8544)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8268)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2292)
Application launched itself
- zyCACcaDQJcSvND.exe (PID: 1488)
INFO
Checks proxy server information
- slui.exe (PID: 7576)
- zyCACcaDQJcSvND.exe (PID: 8772)
Checks supported languages
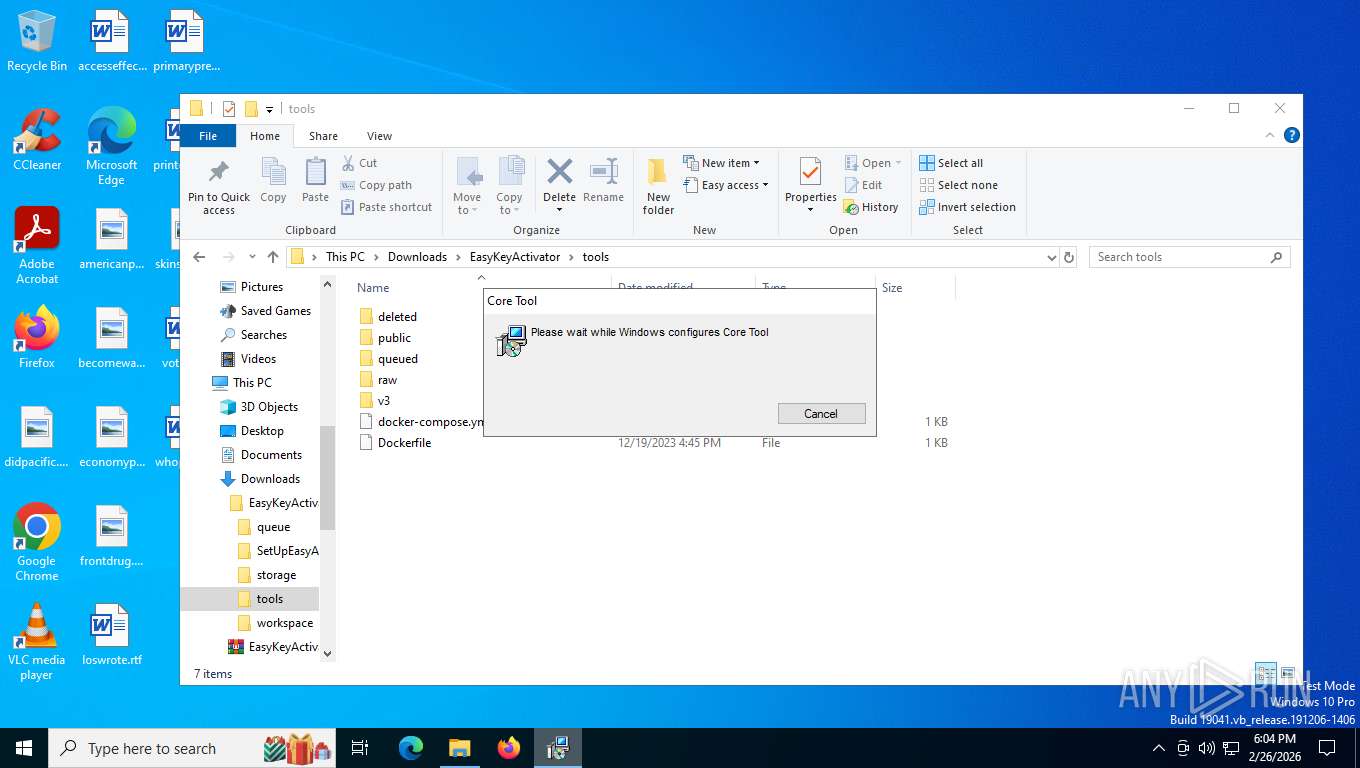
- msiexec.exe (PID: 2260)
- zyCACcaDQJcSvND.exe (PID: 1488)
- zyCACcaDQJcSvND.exe (PID: 8772)
Application launched itself
- firefox.exe (PID: 7452)
- firefox.exe (PID: 8396)
Reads the computer name
- msiexec.exe (PID: 2260)
- zyCACcaDQJcSvND.exe (PID: 1488)
- zyCACcaDQJcSvND.exe (PID: 8772)
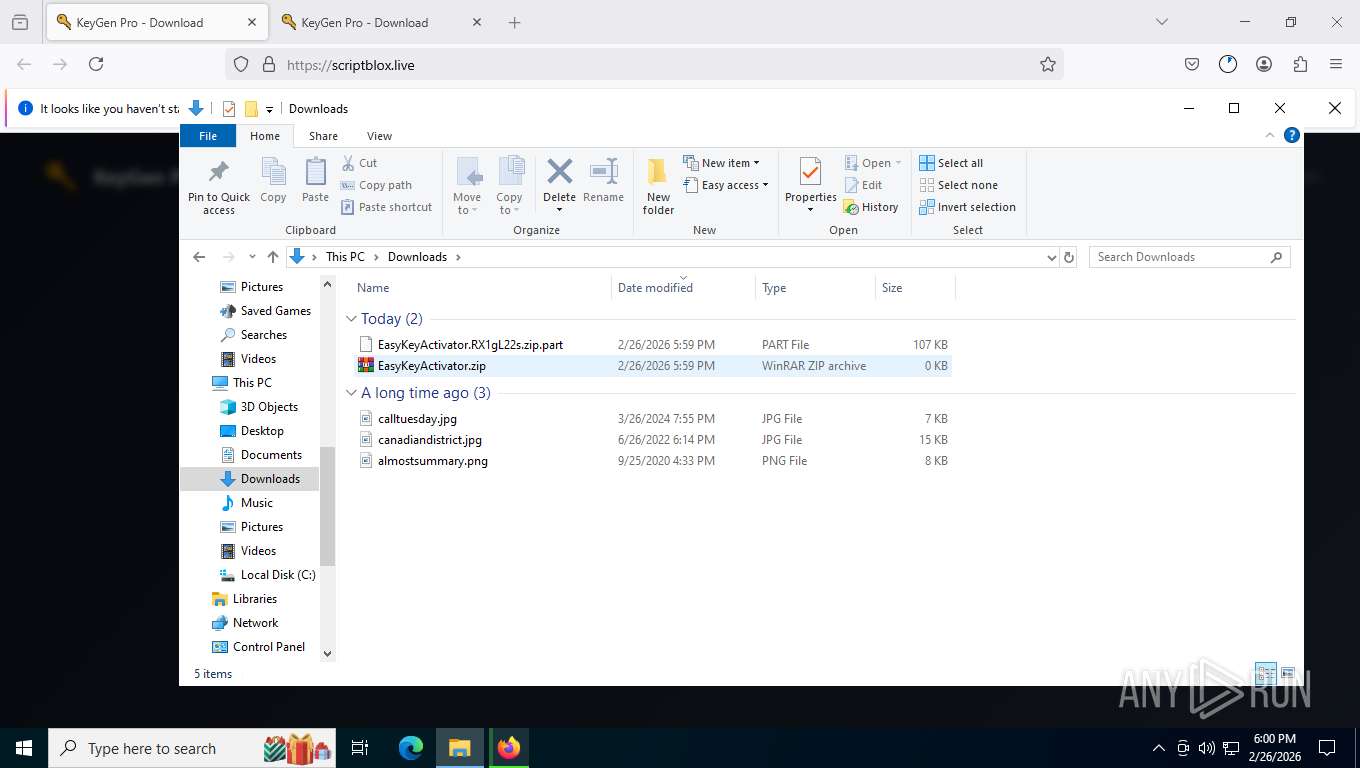
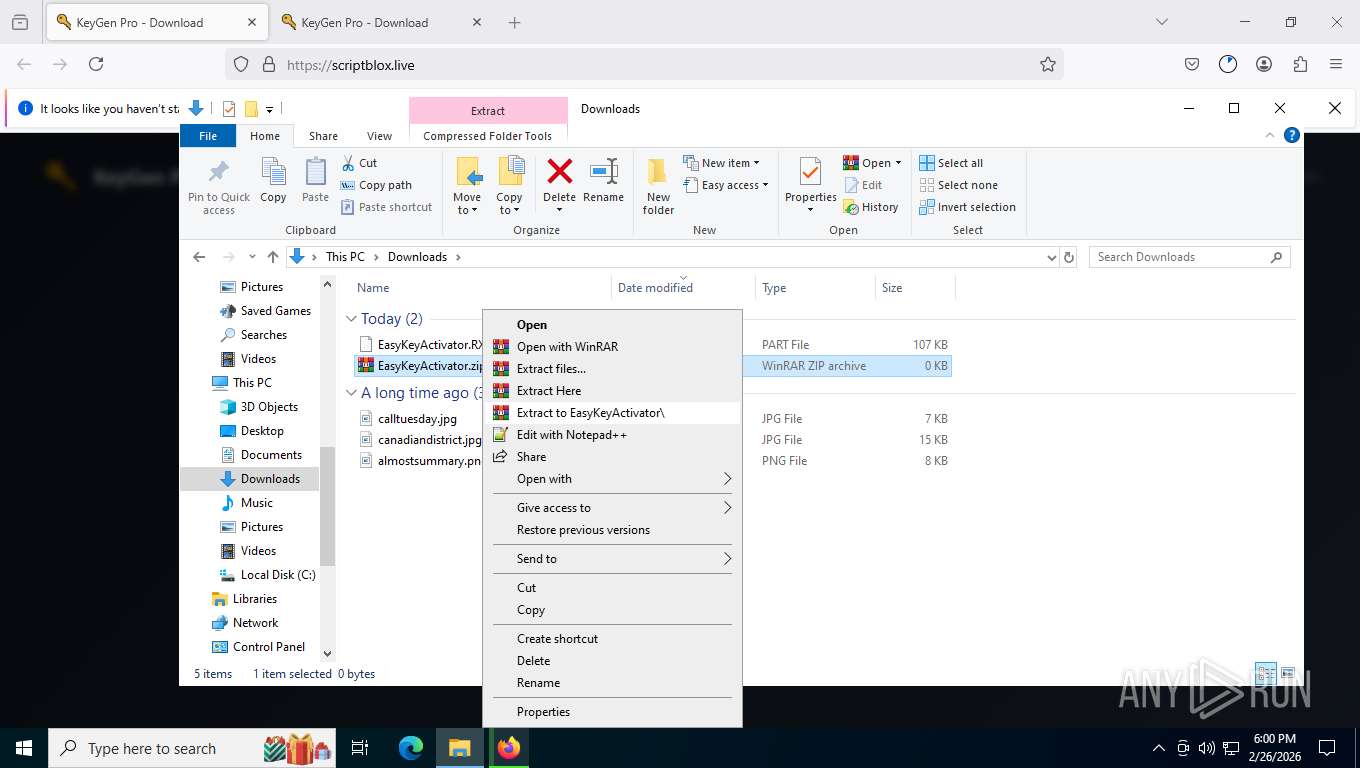
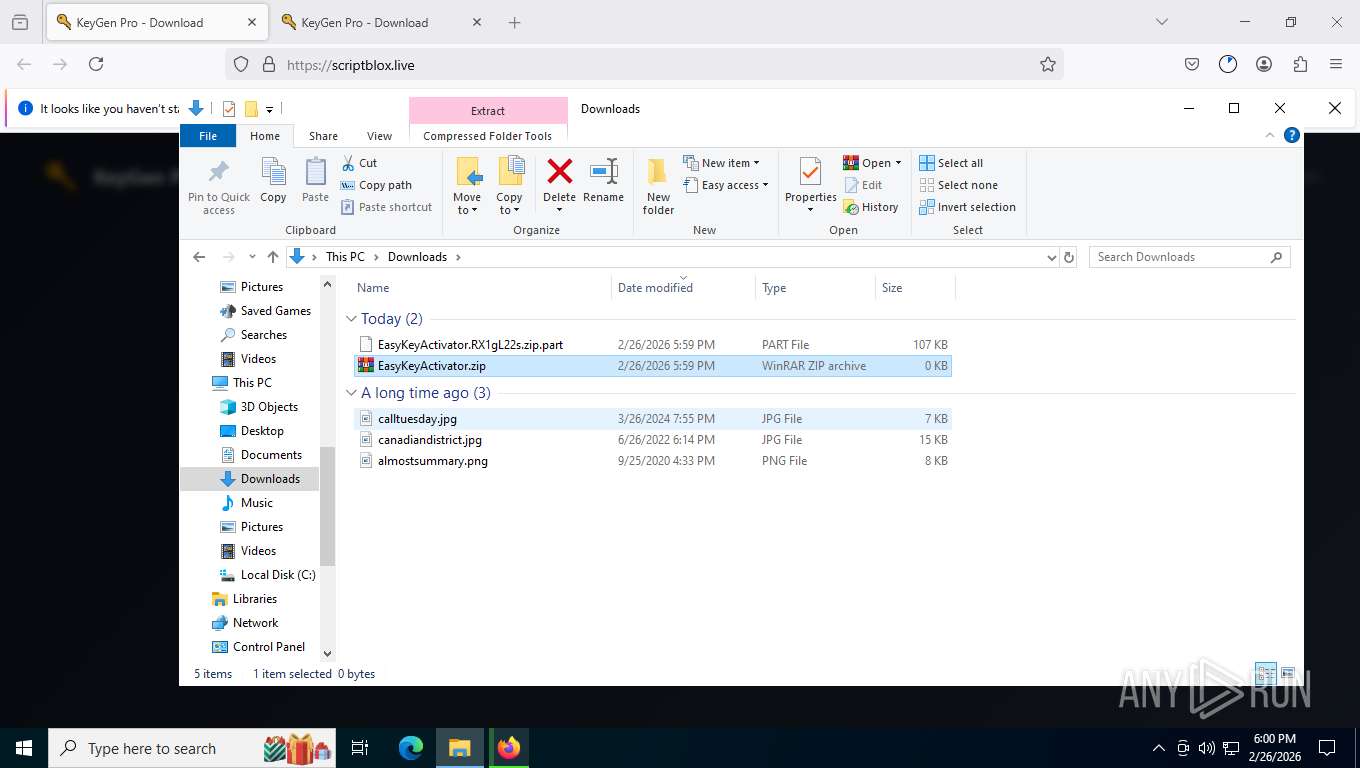
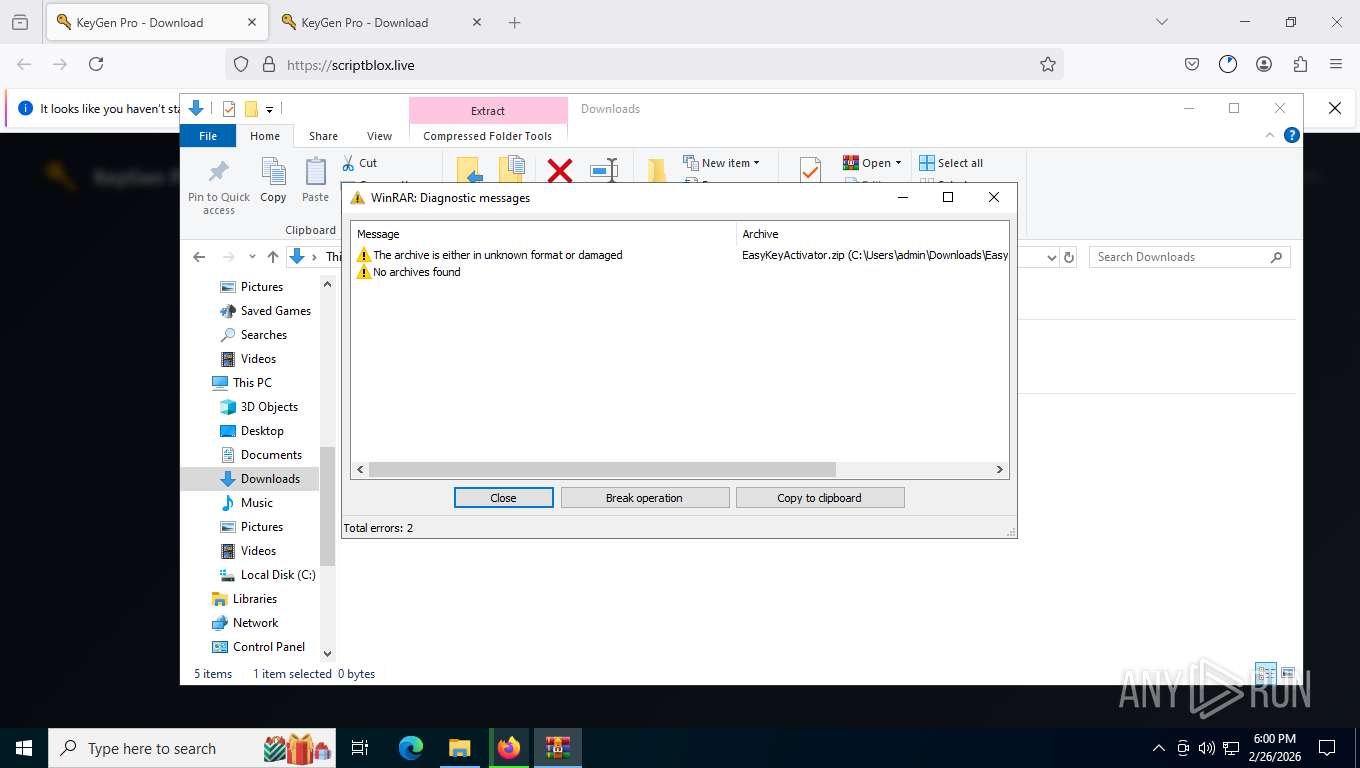
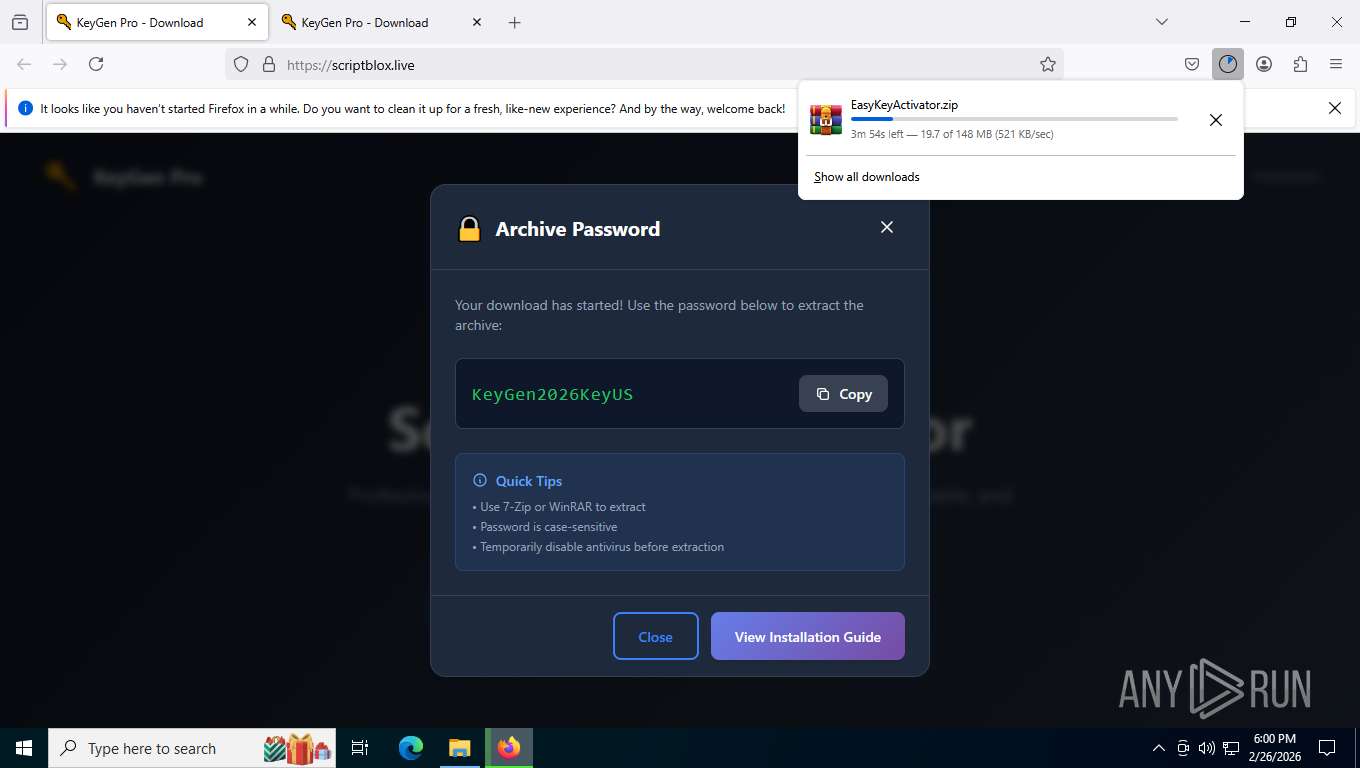
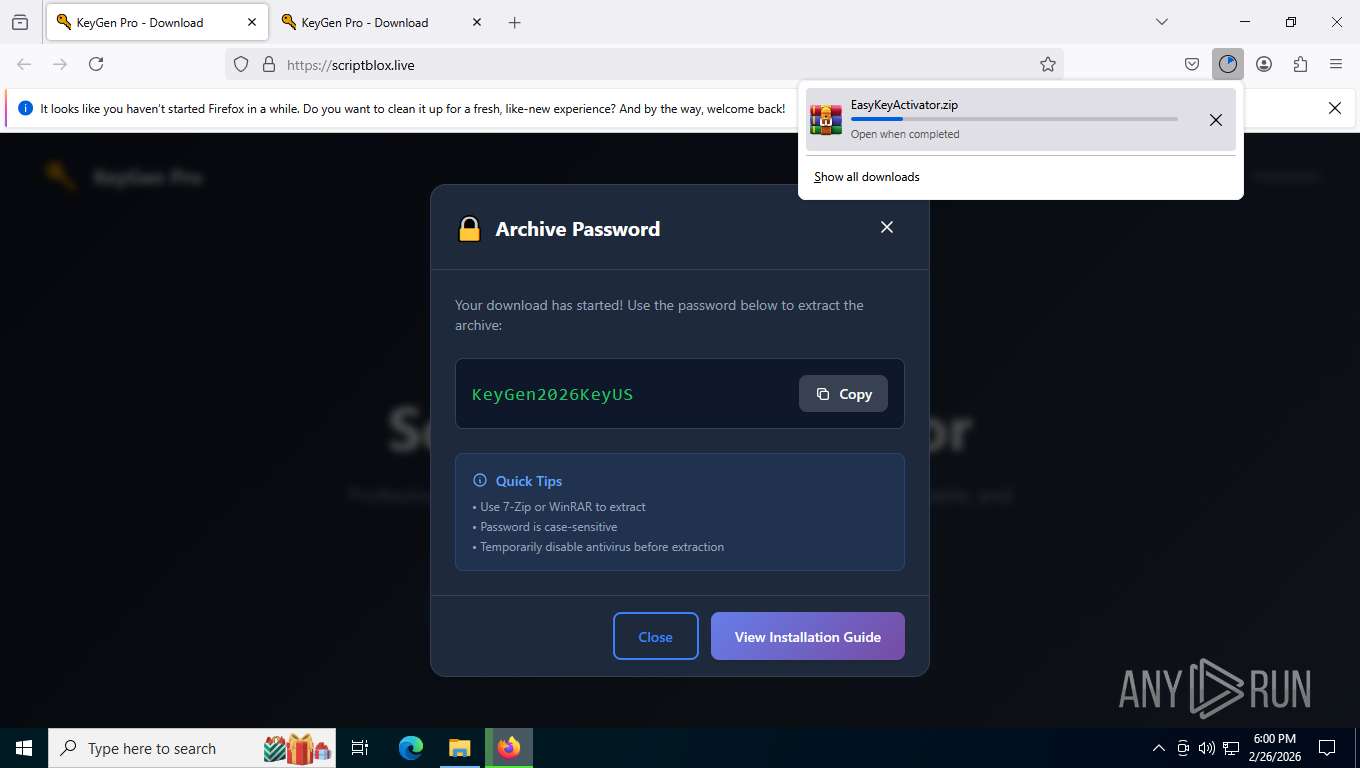
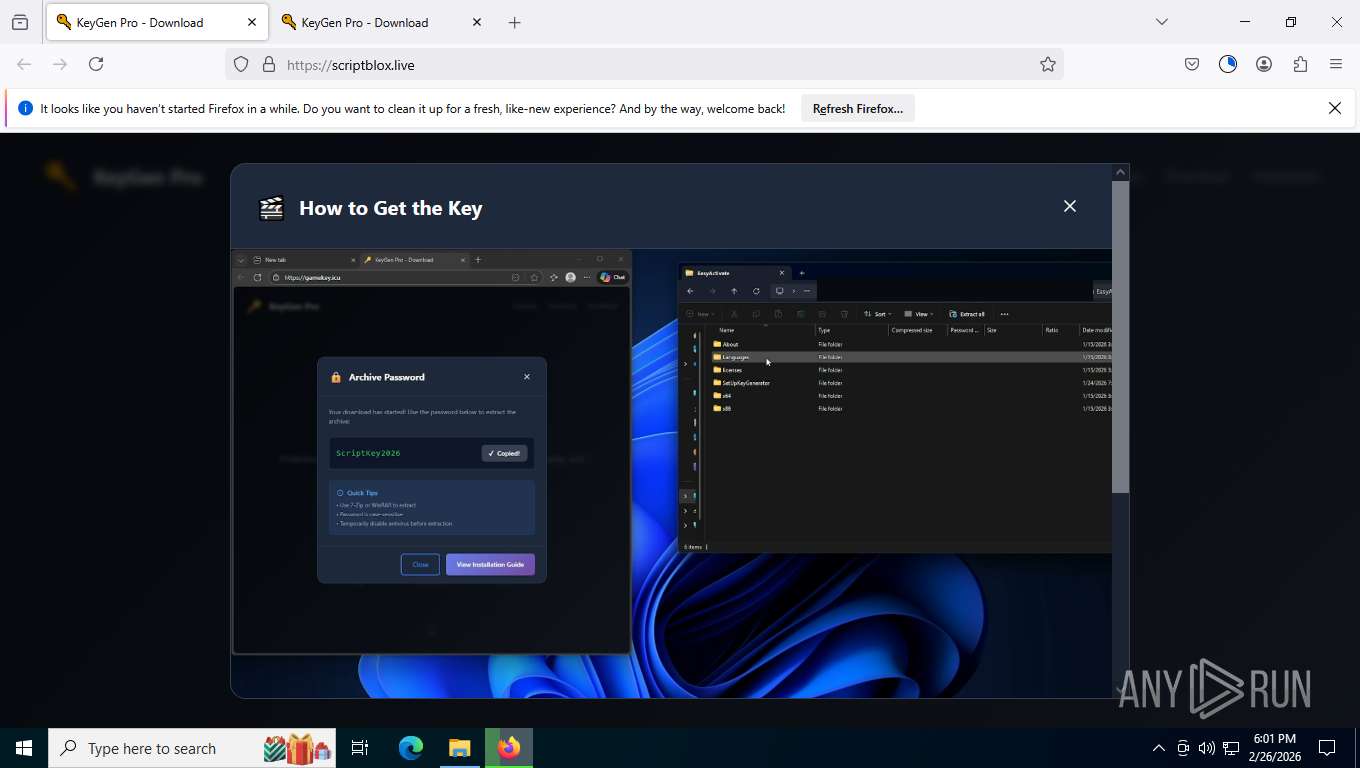
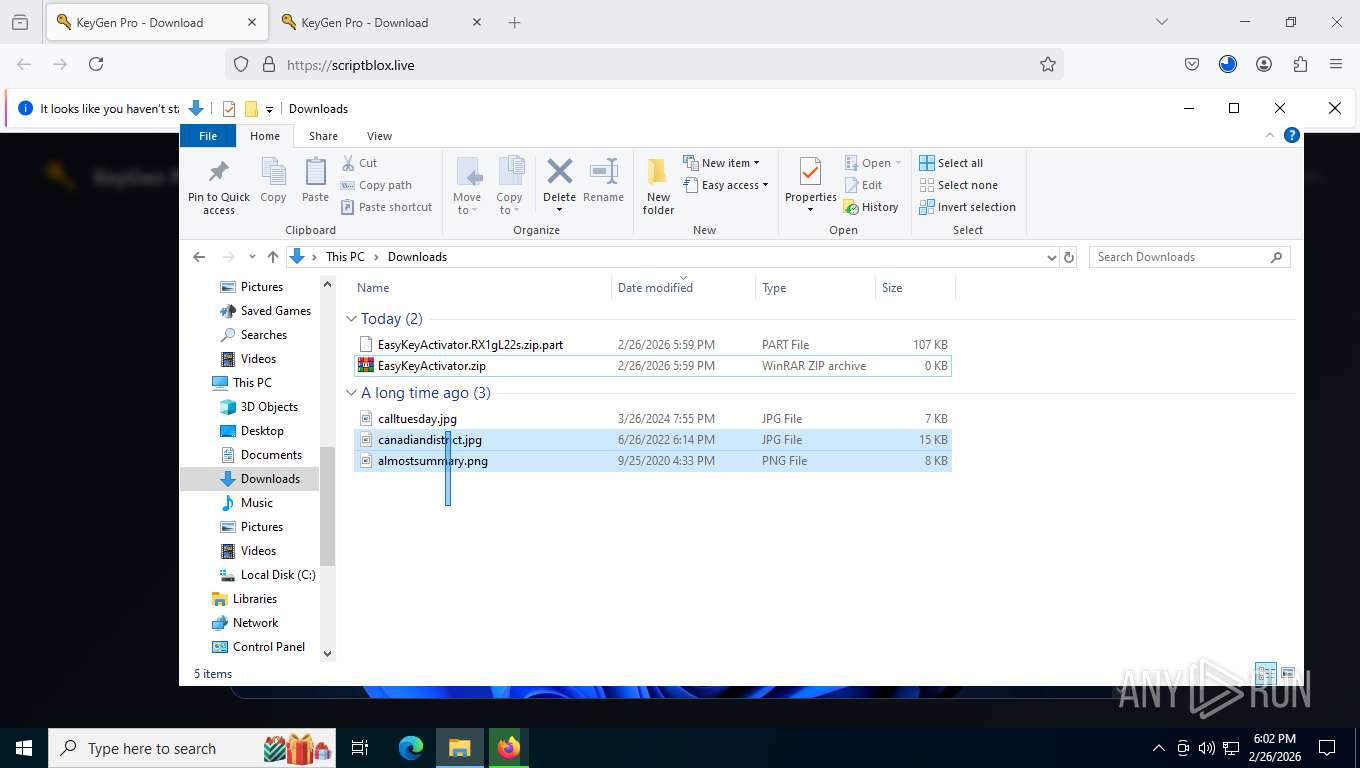
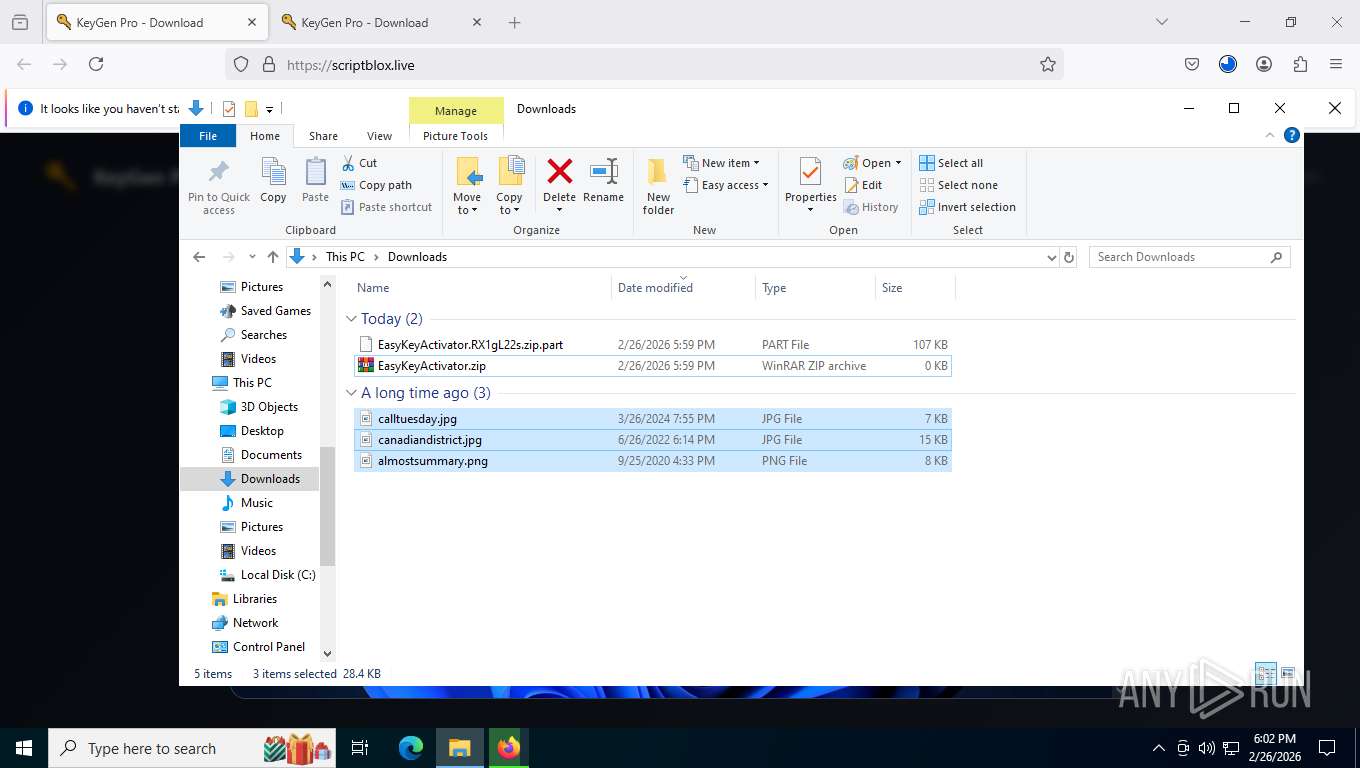
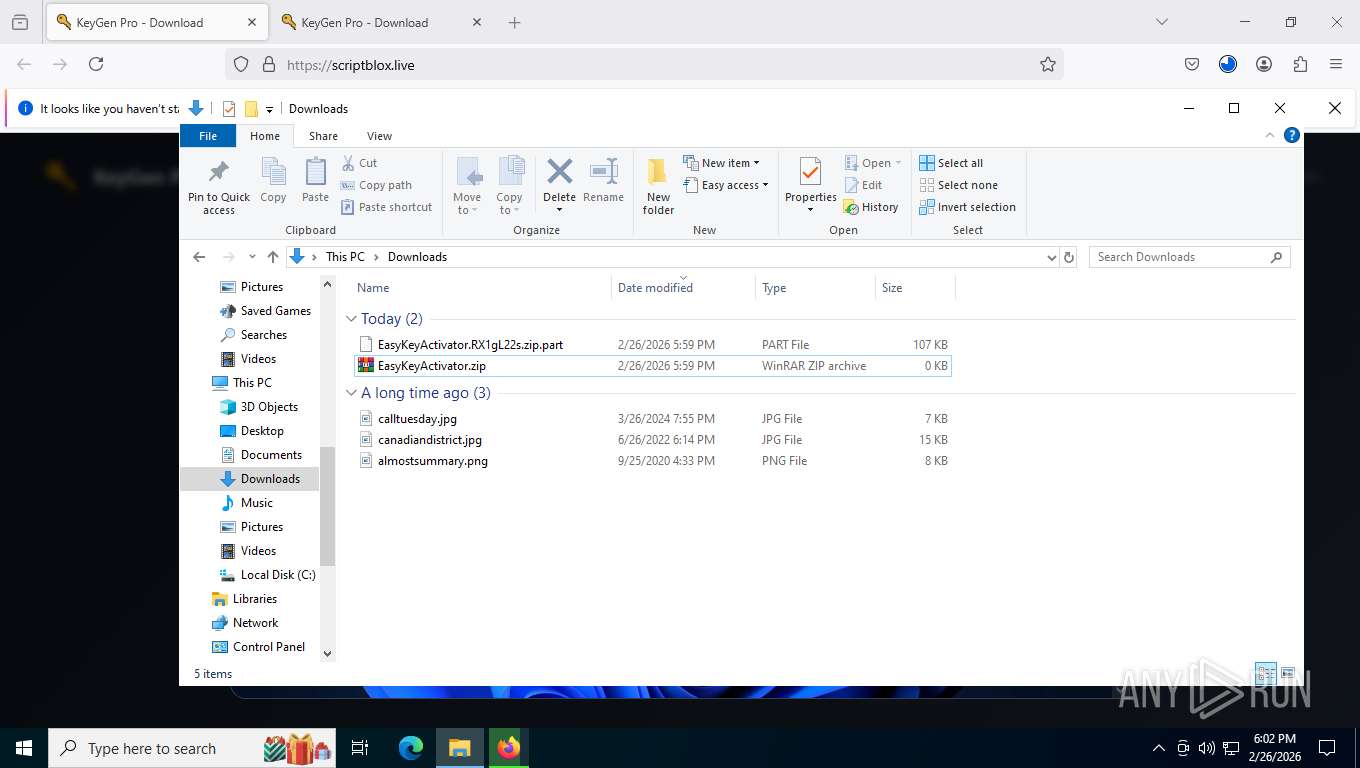
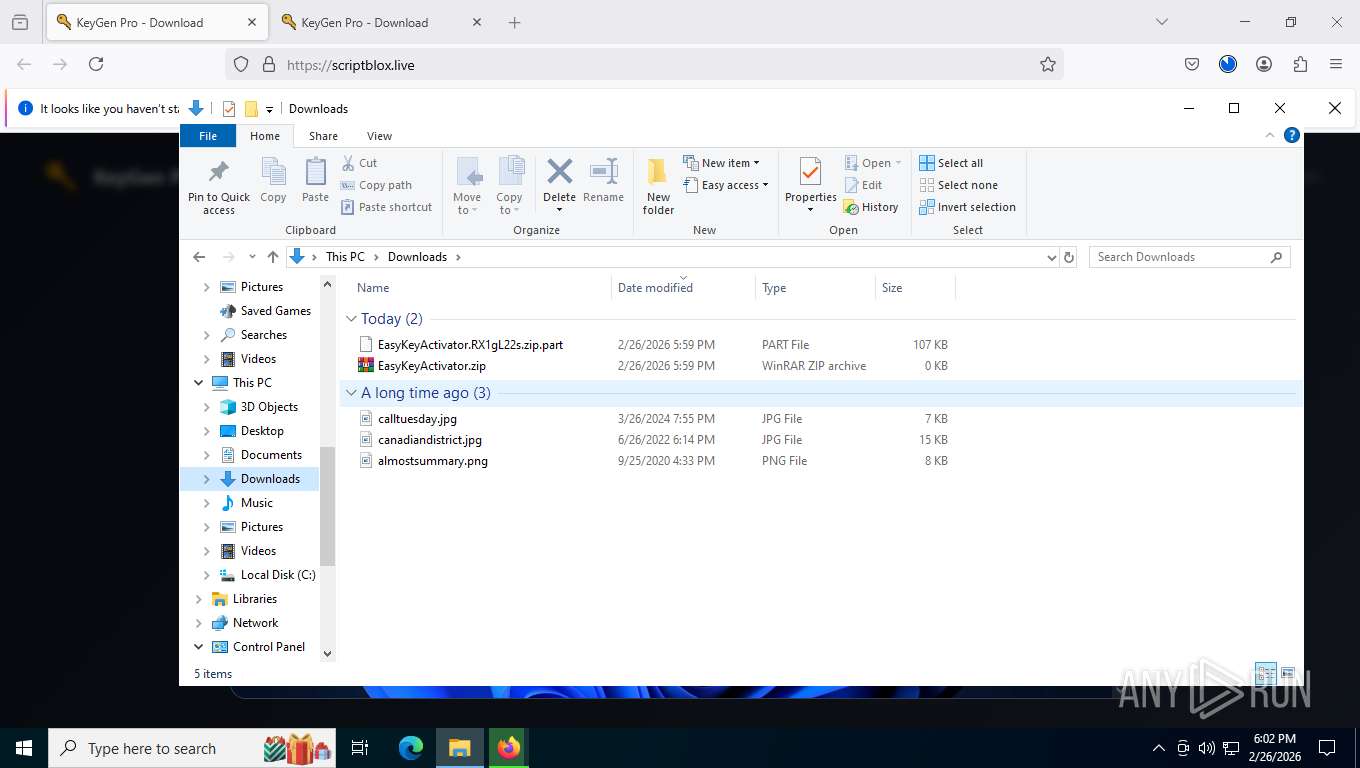
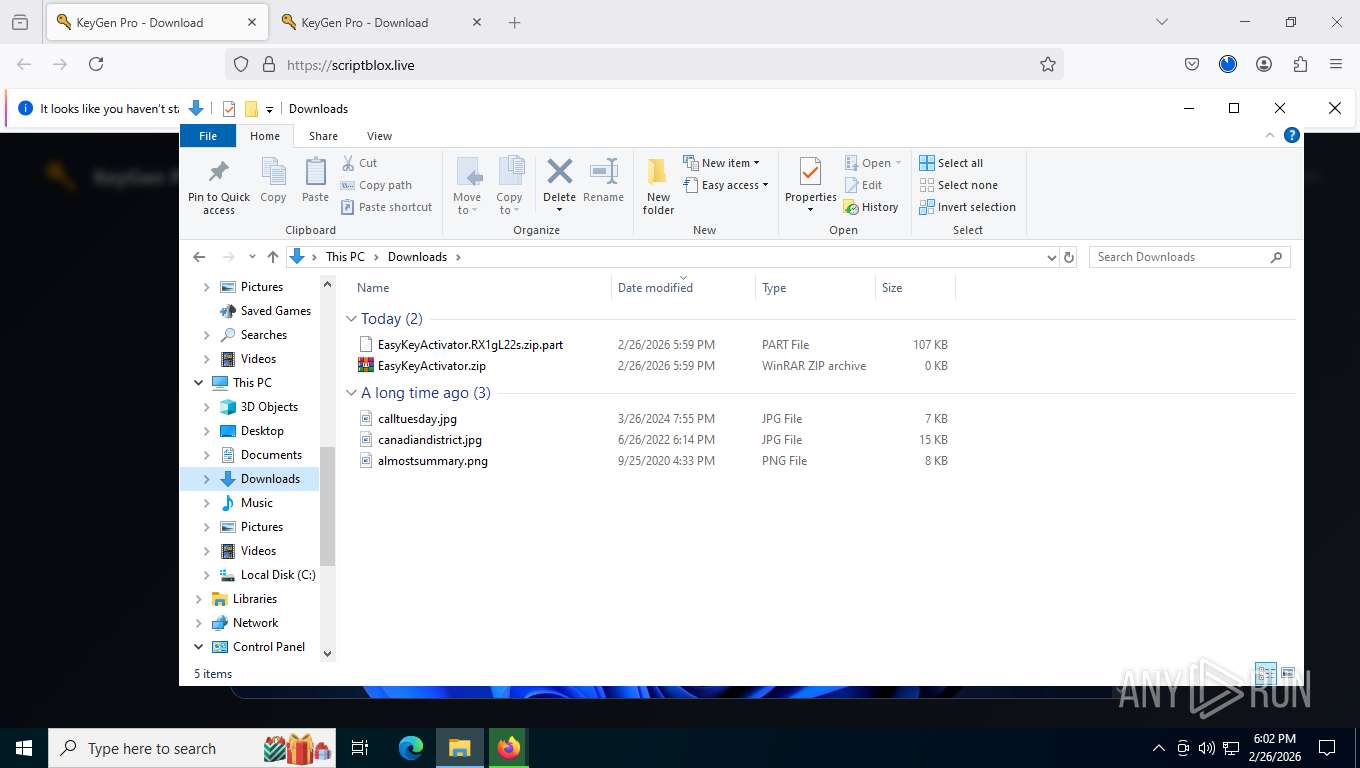
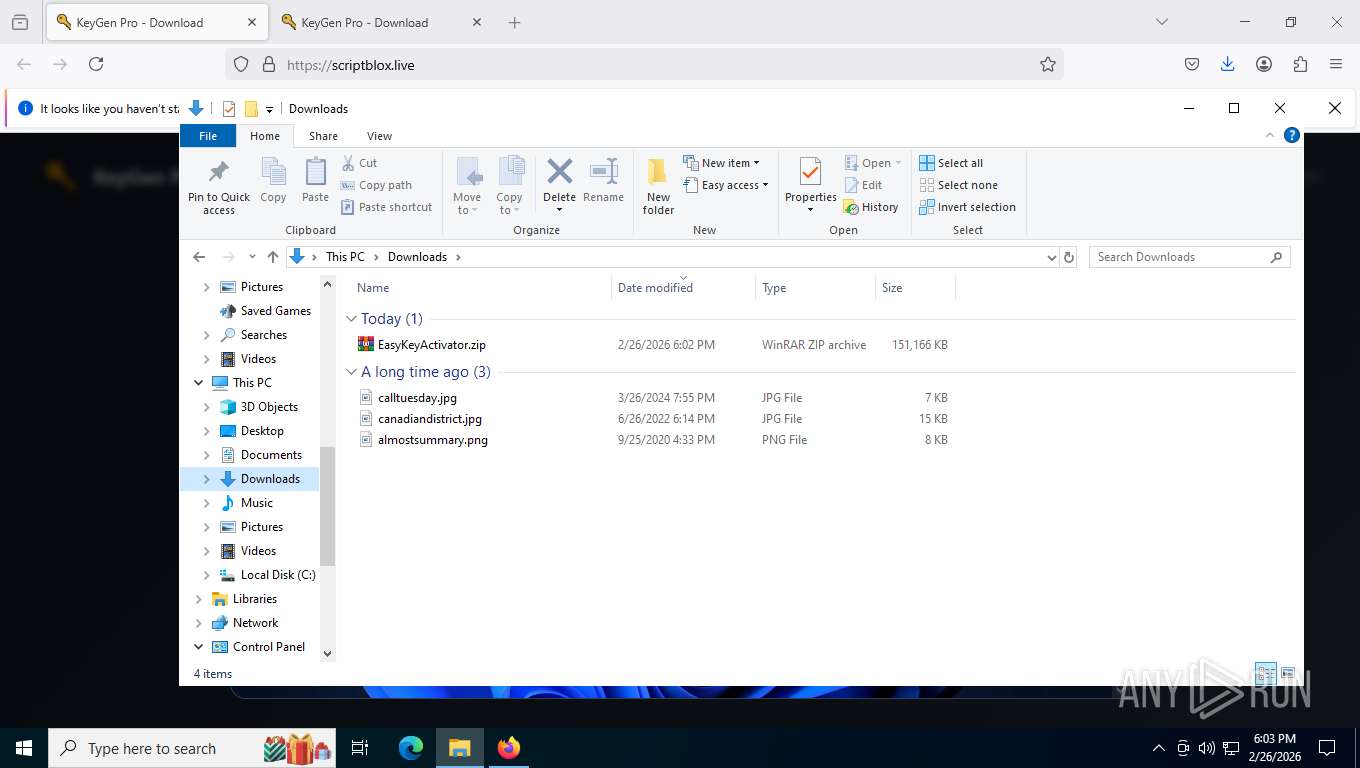
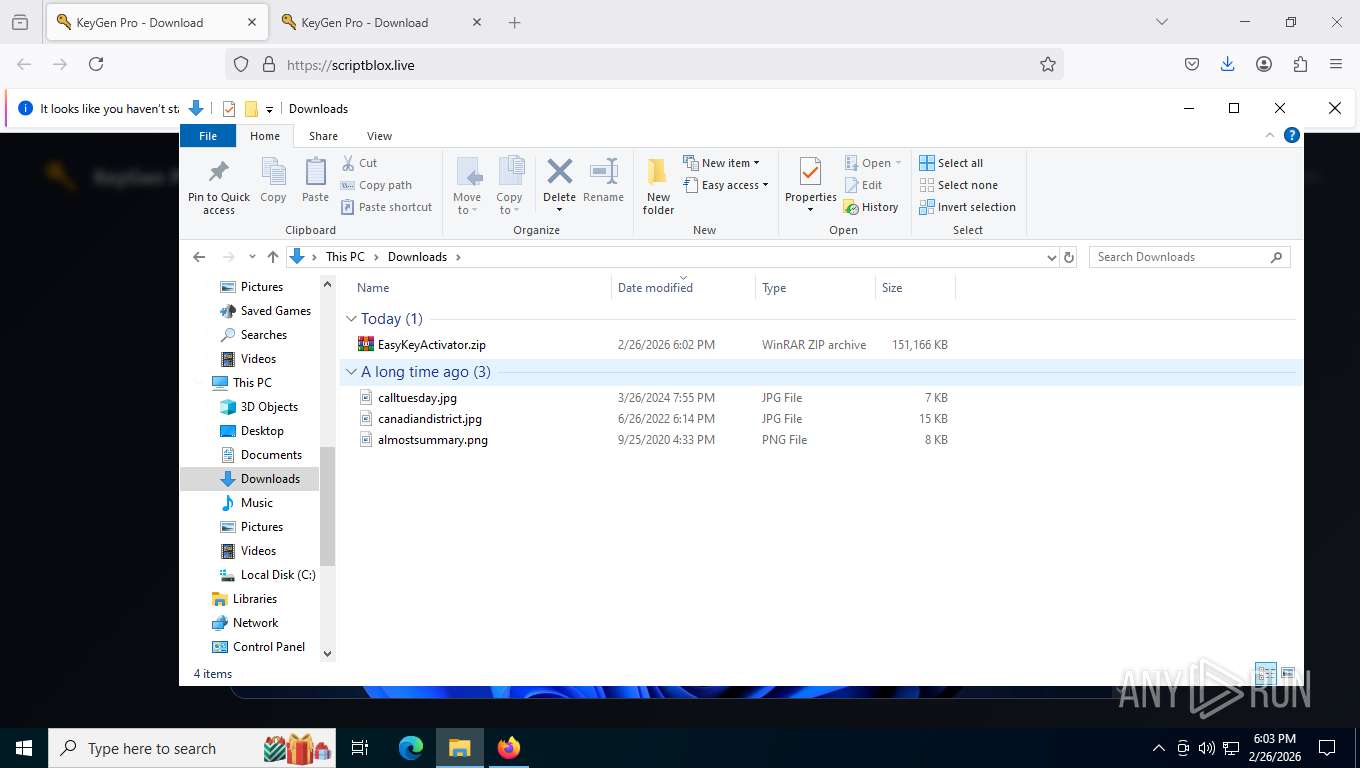
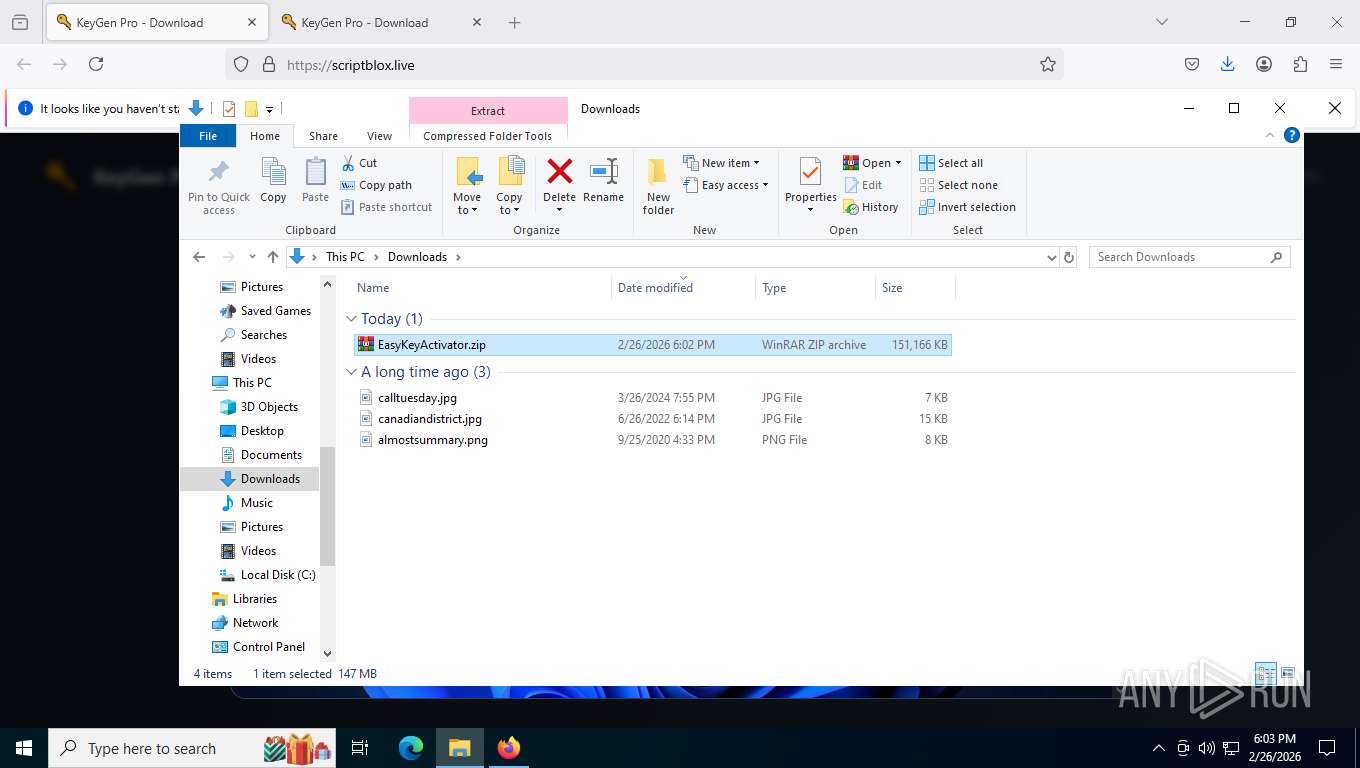
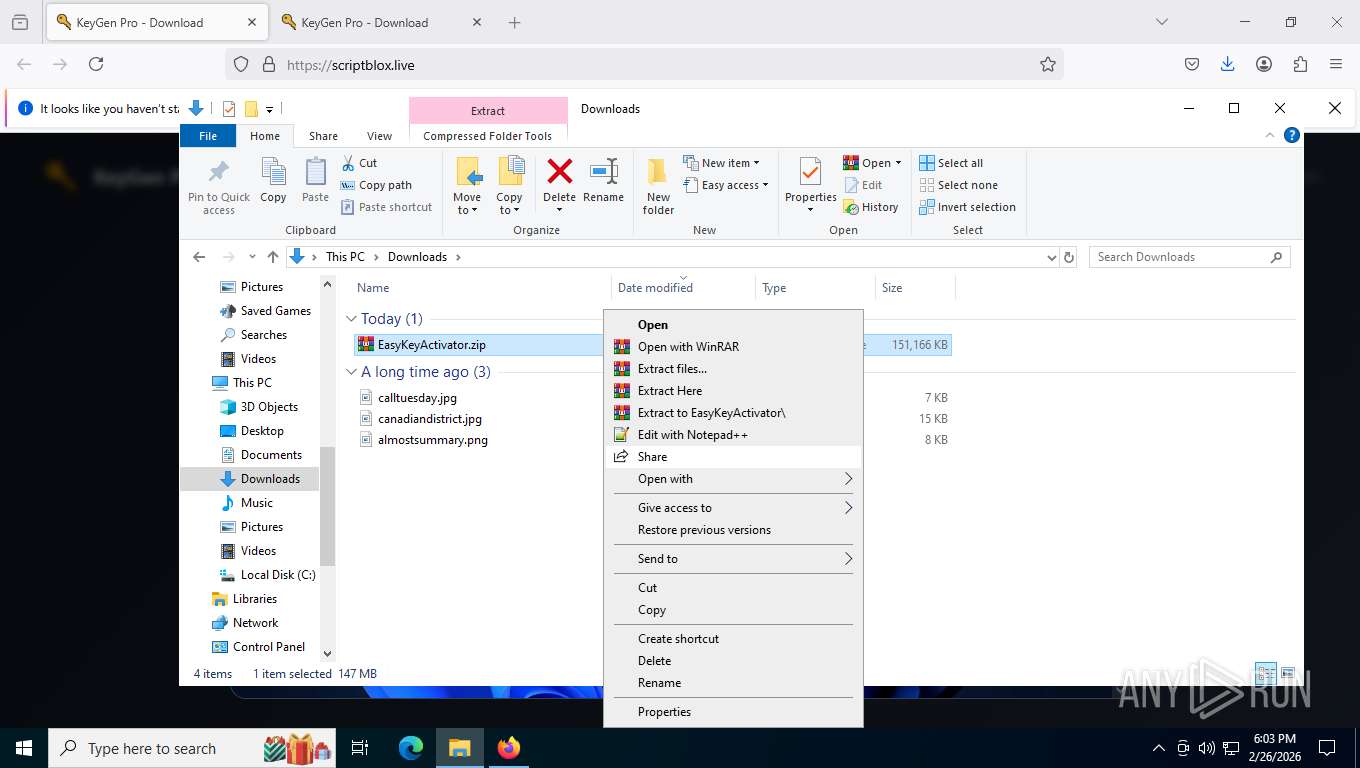
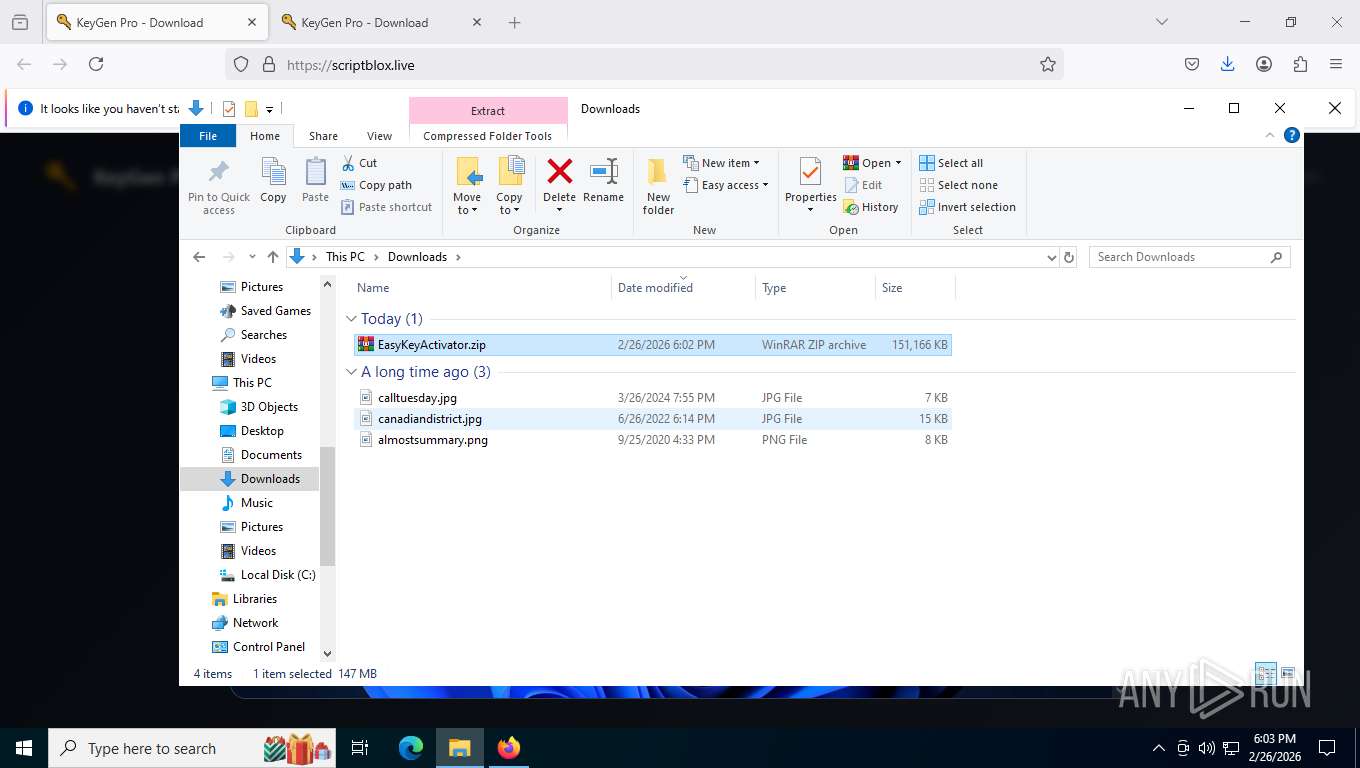
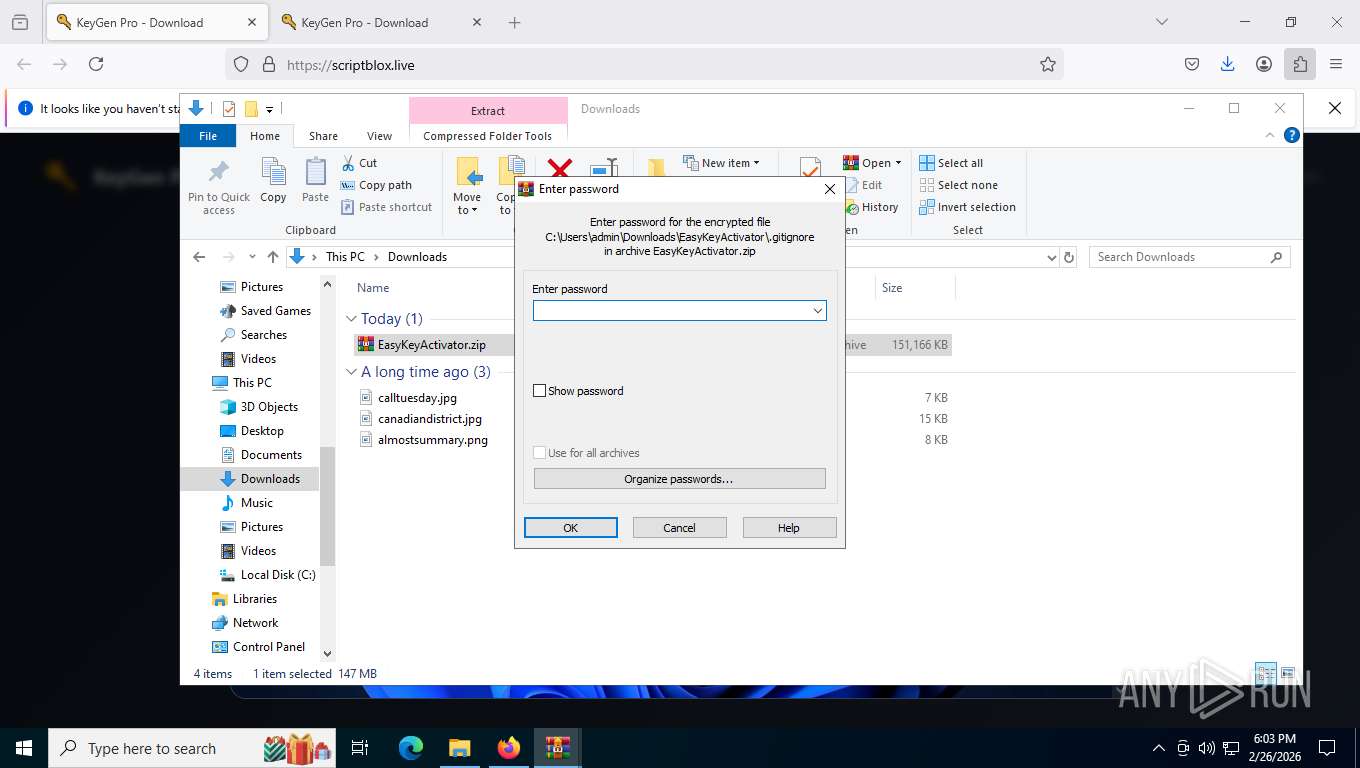
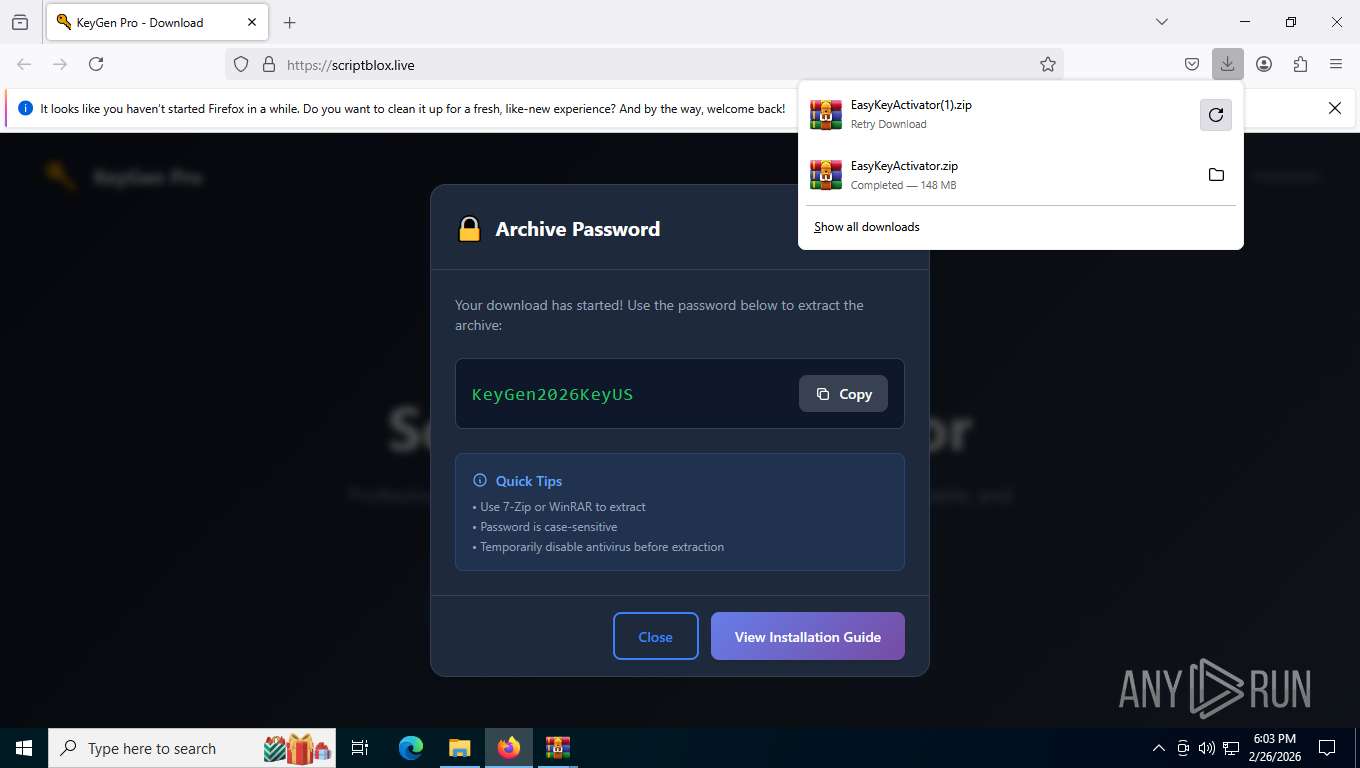
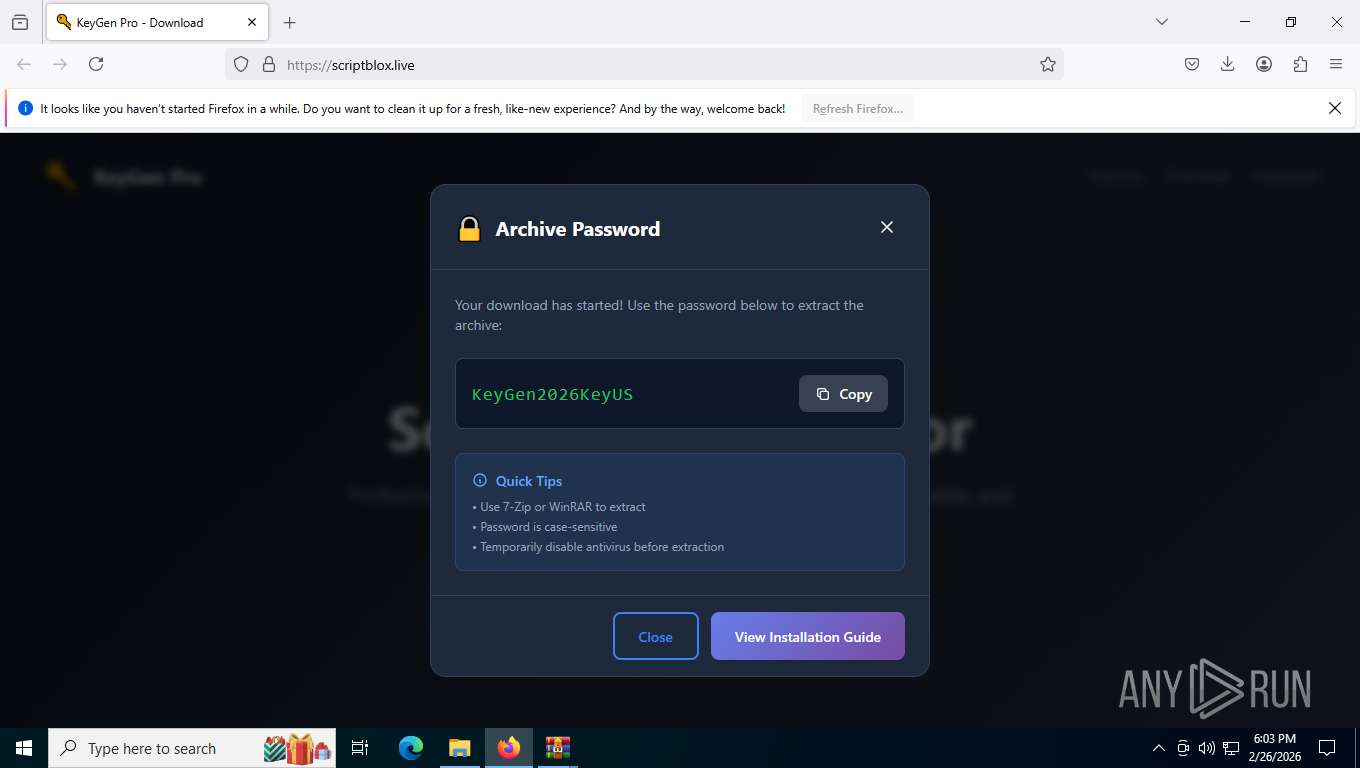
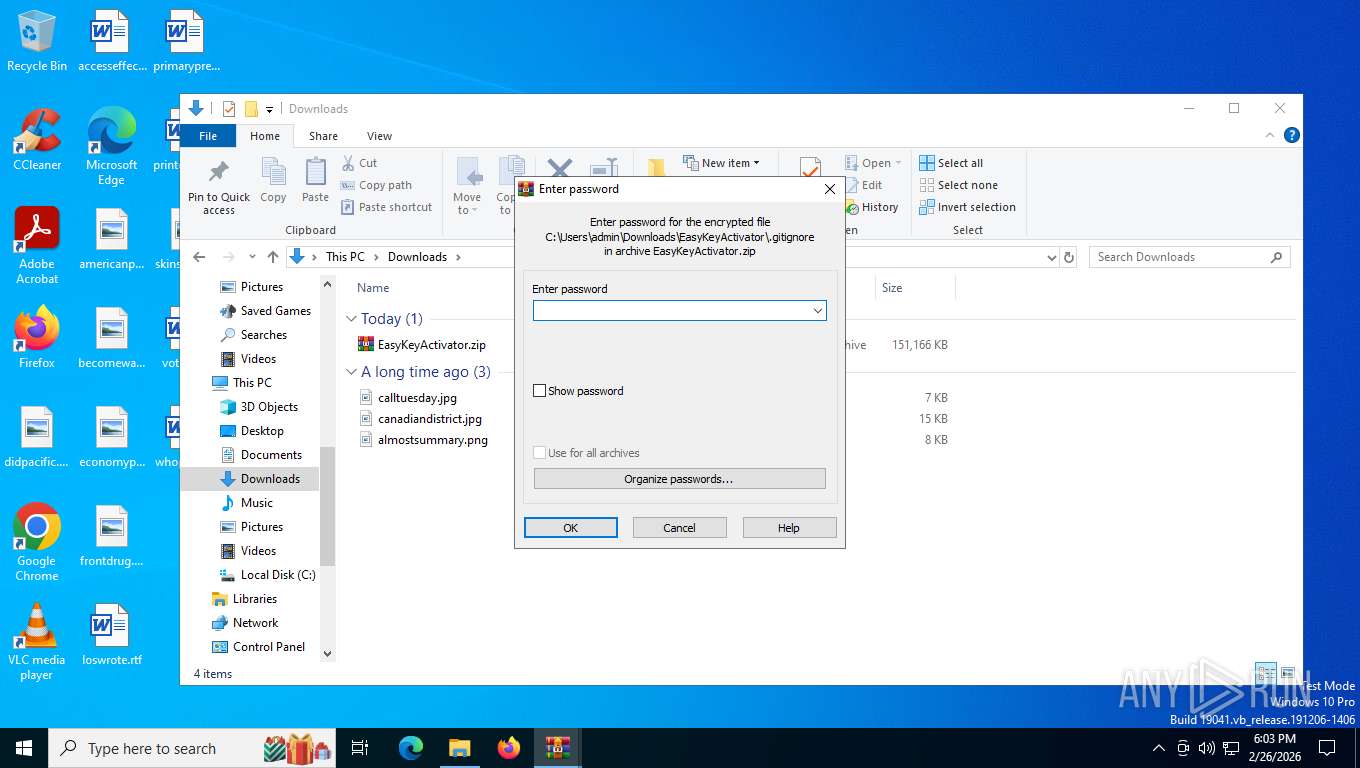
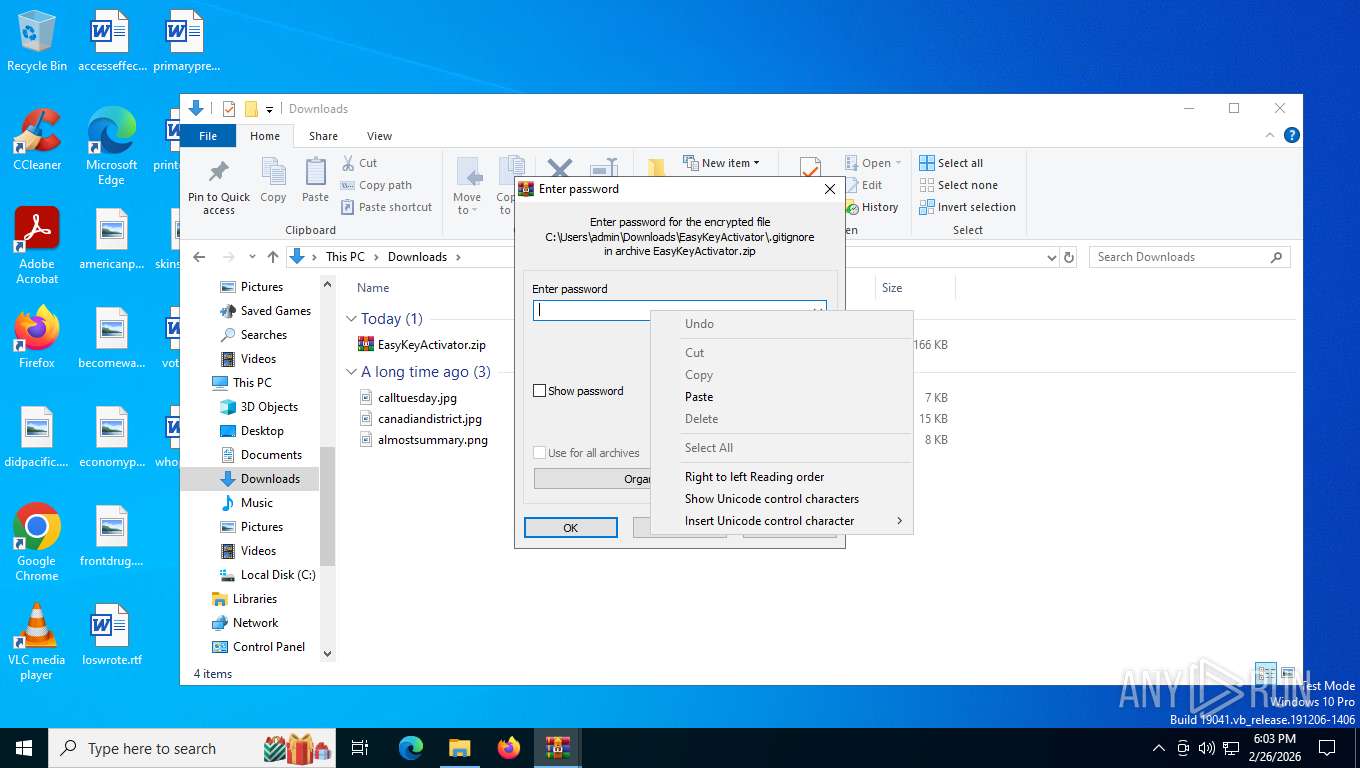
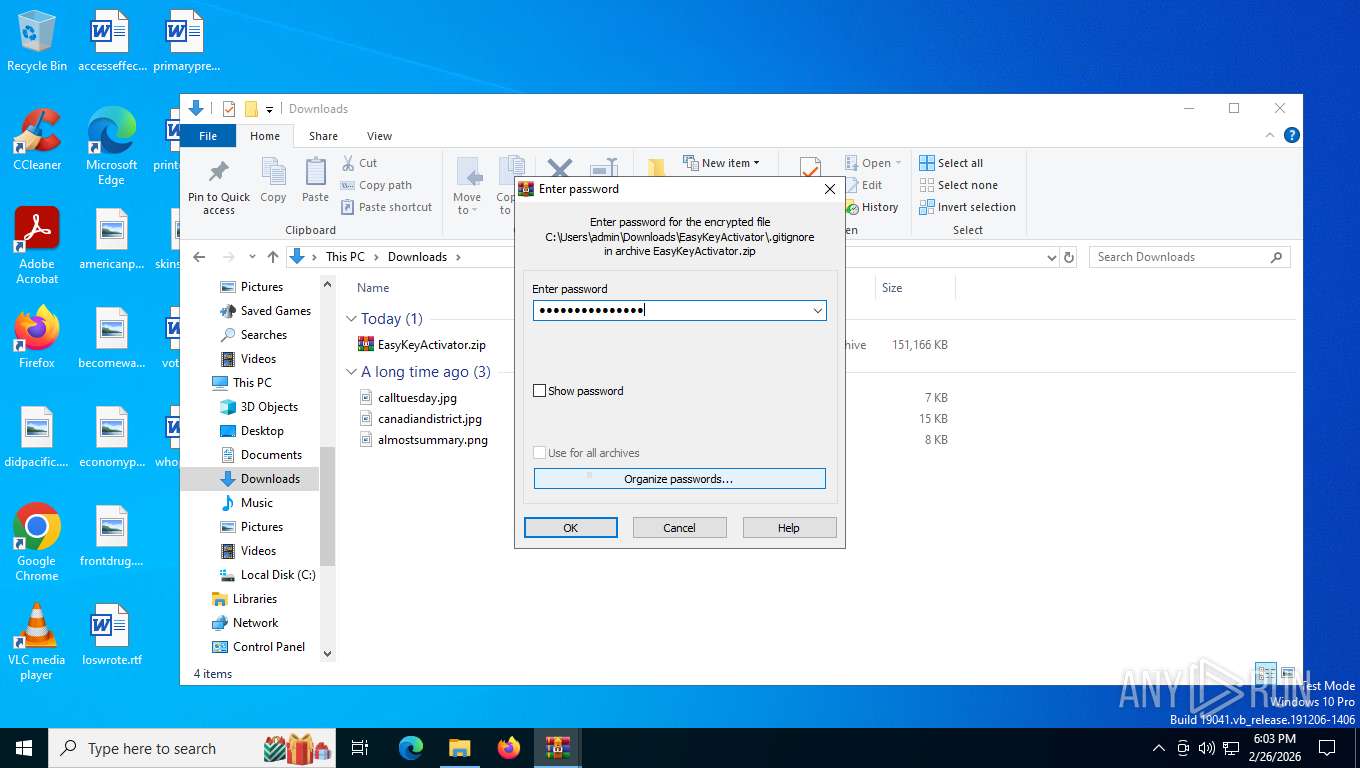
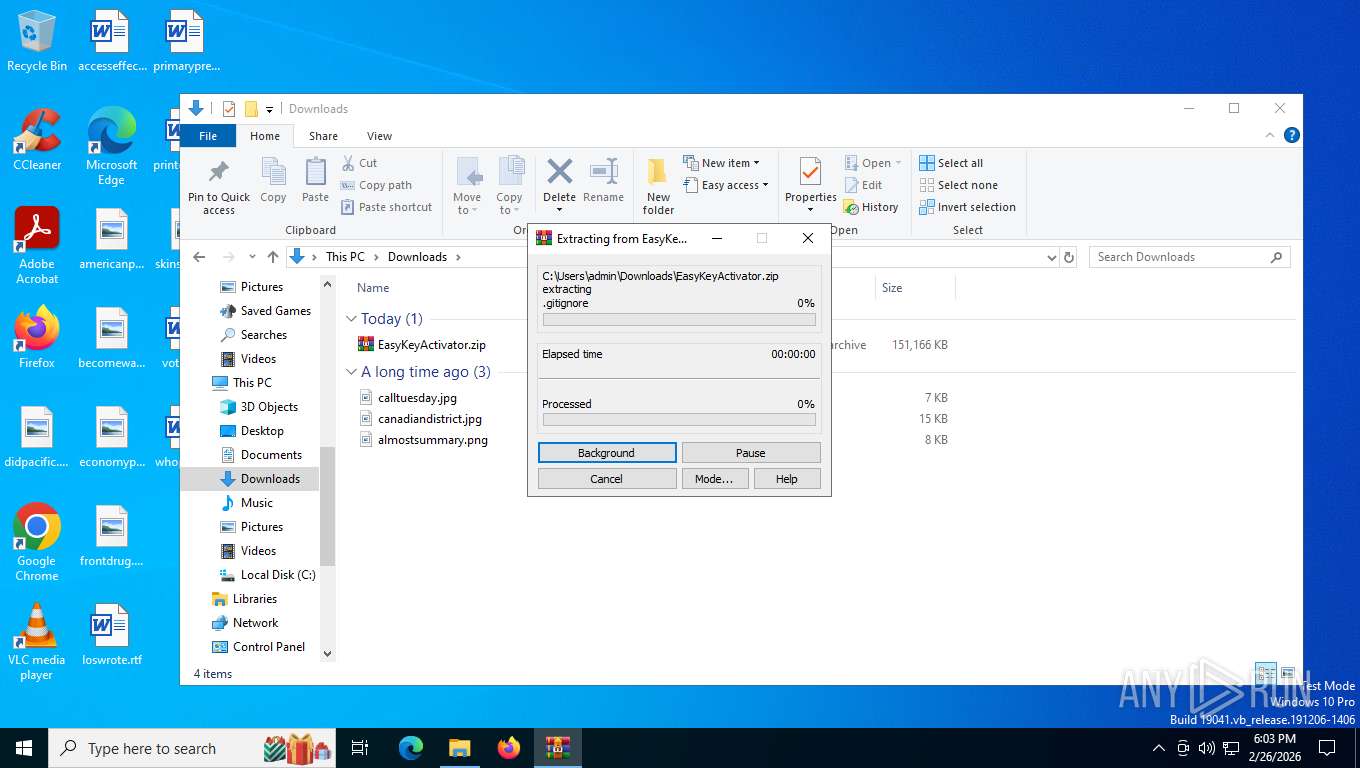
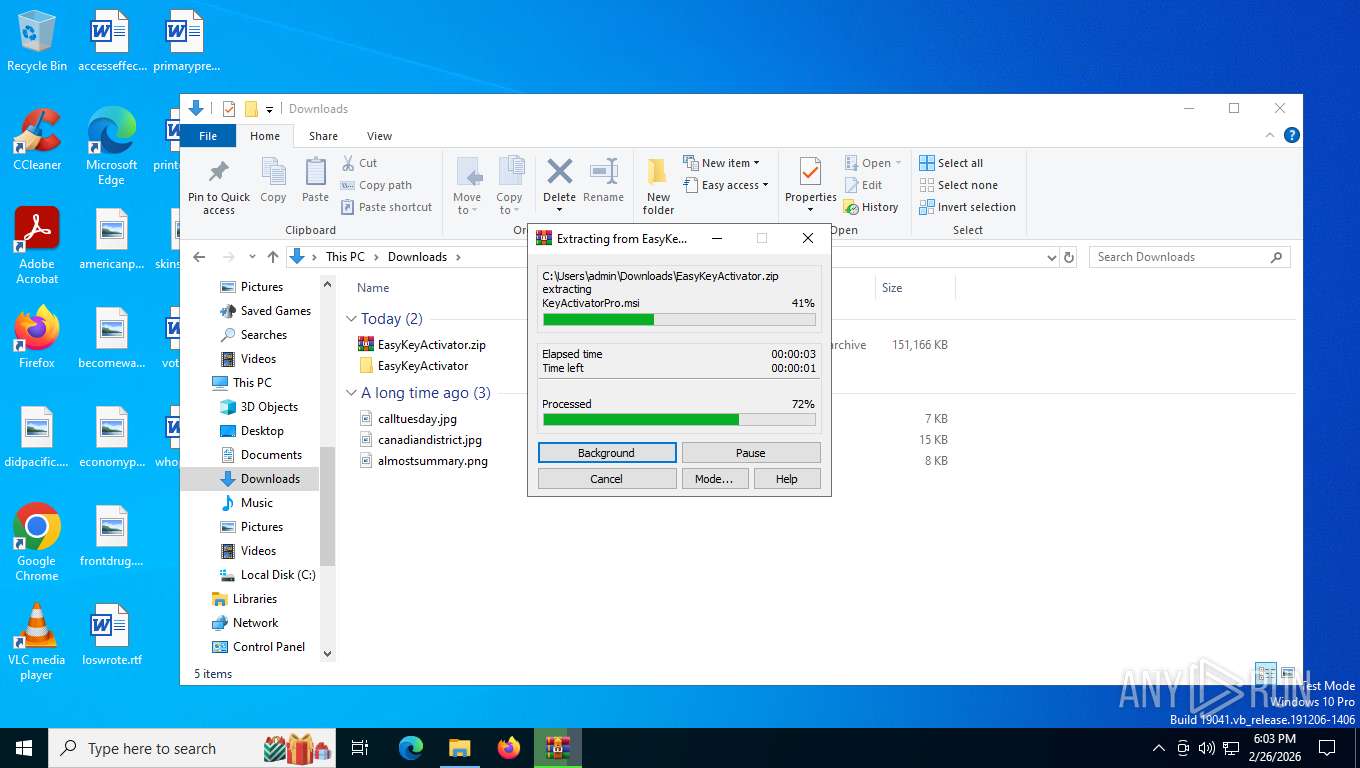
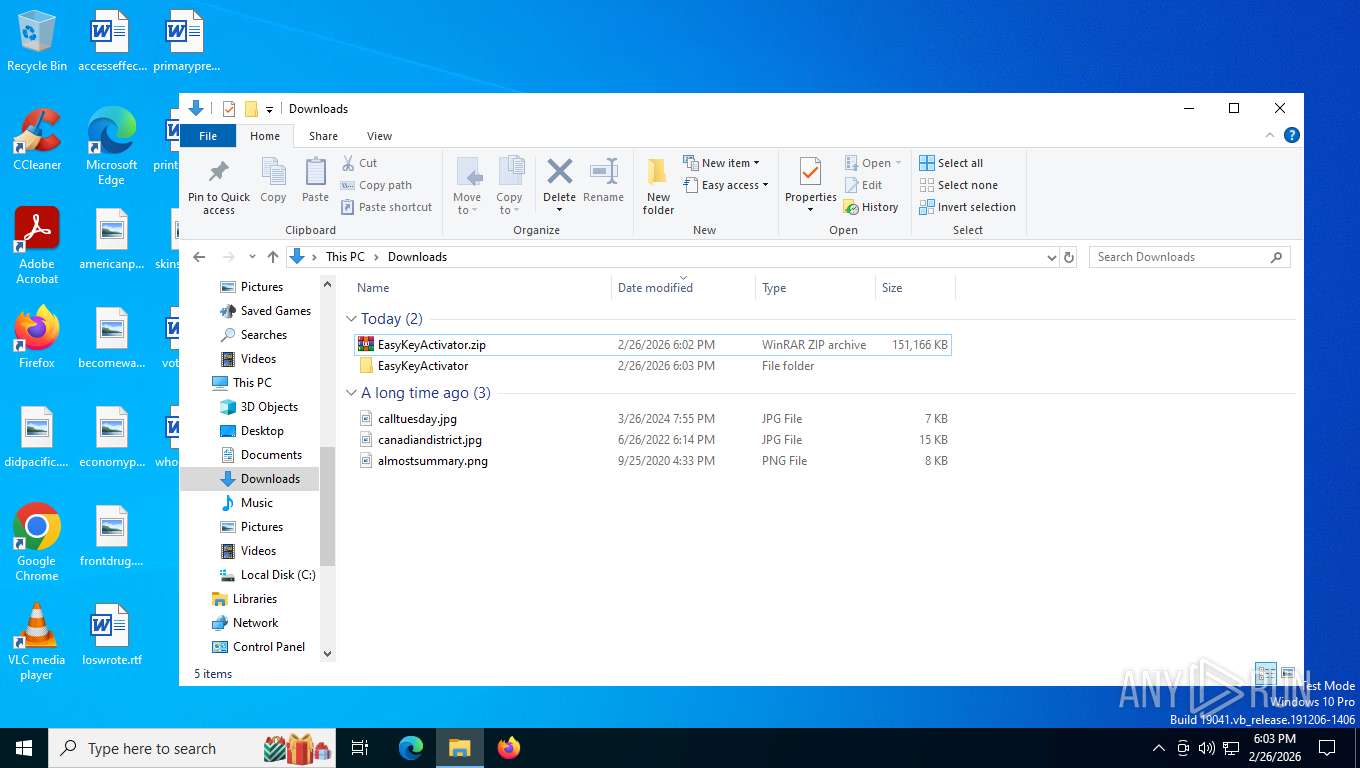
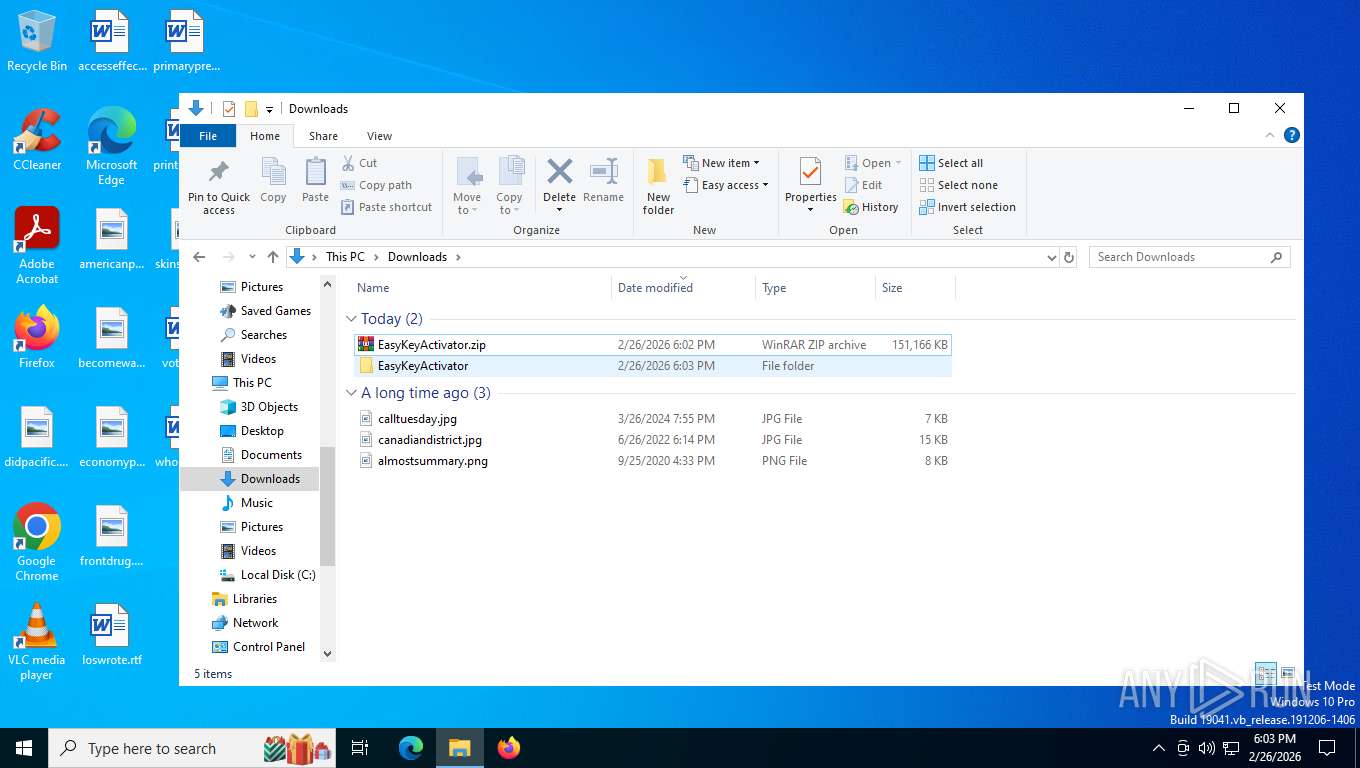
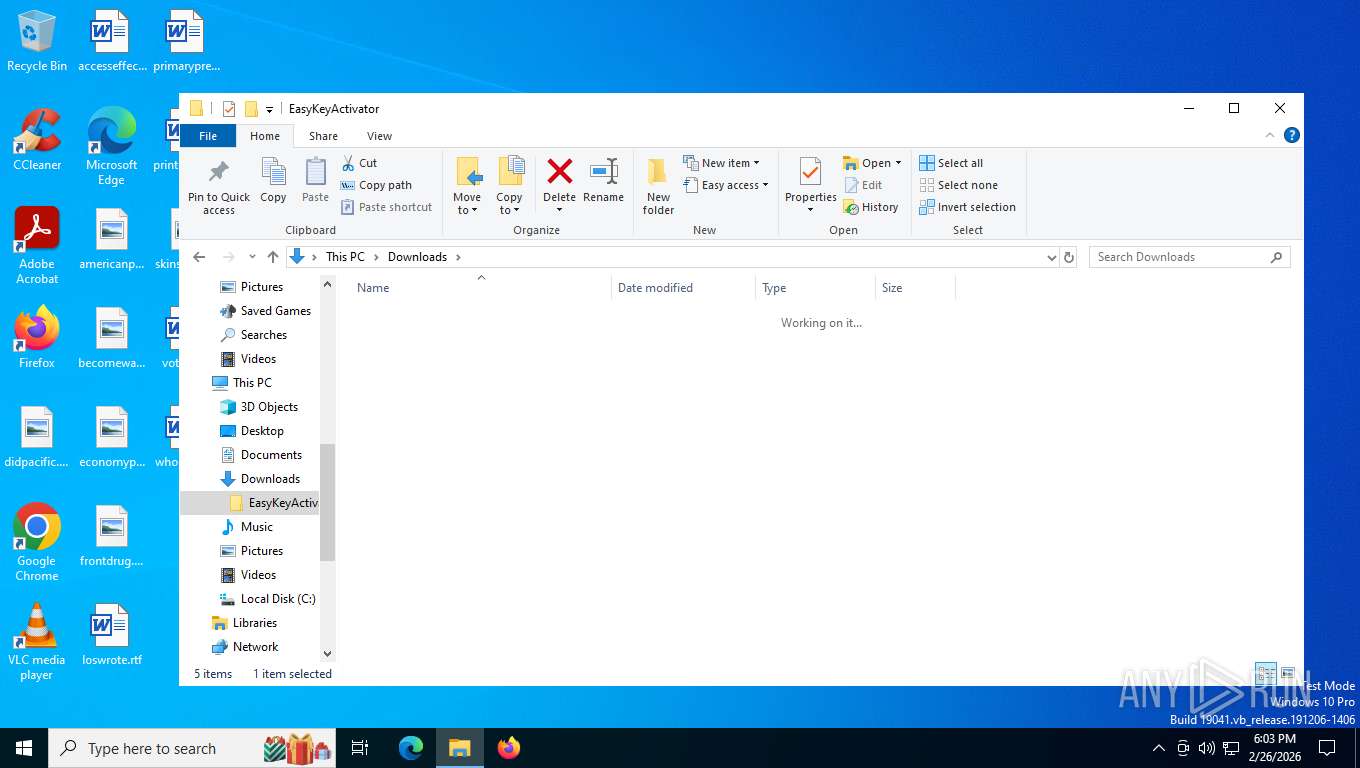
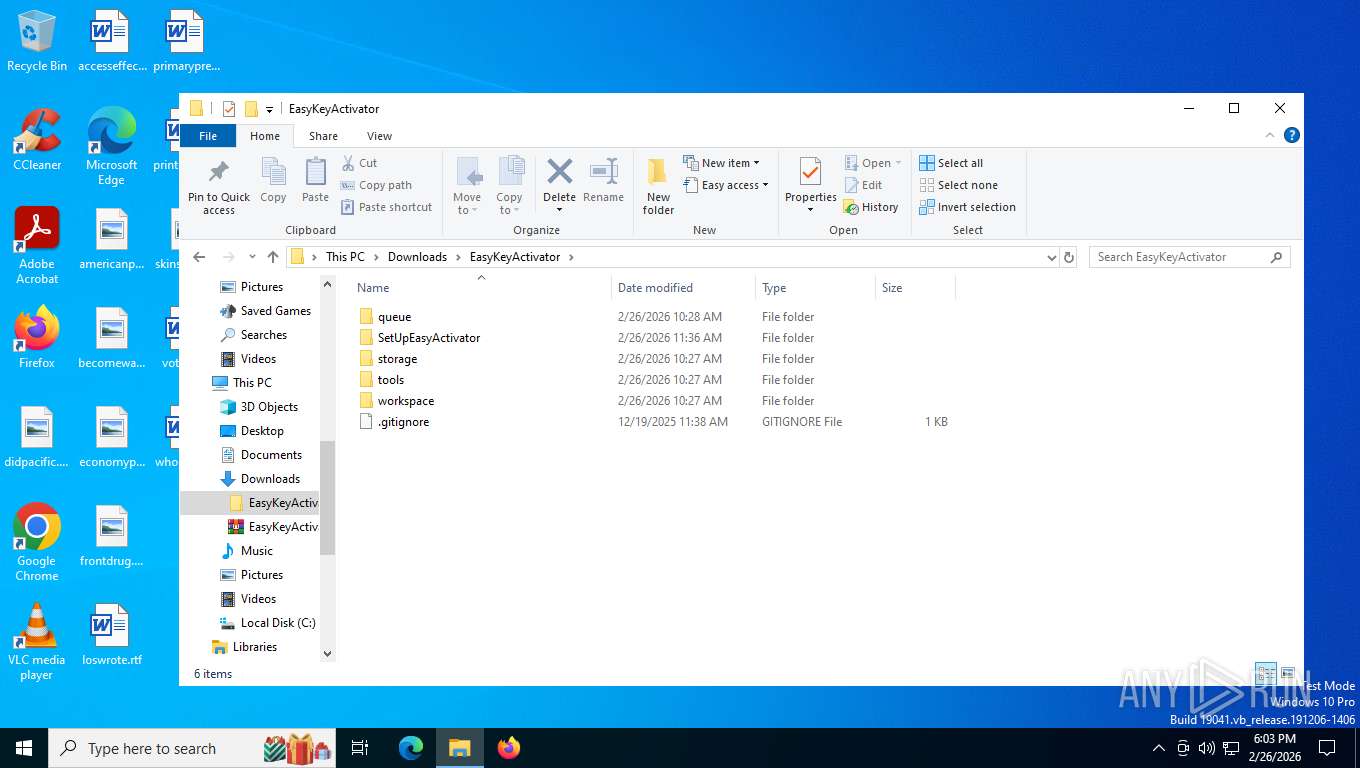
Manual execution by a user
- msiexec.exe (PID: 6360)
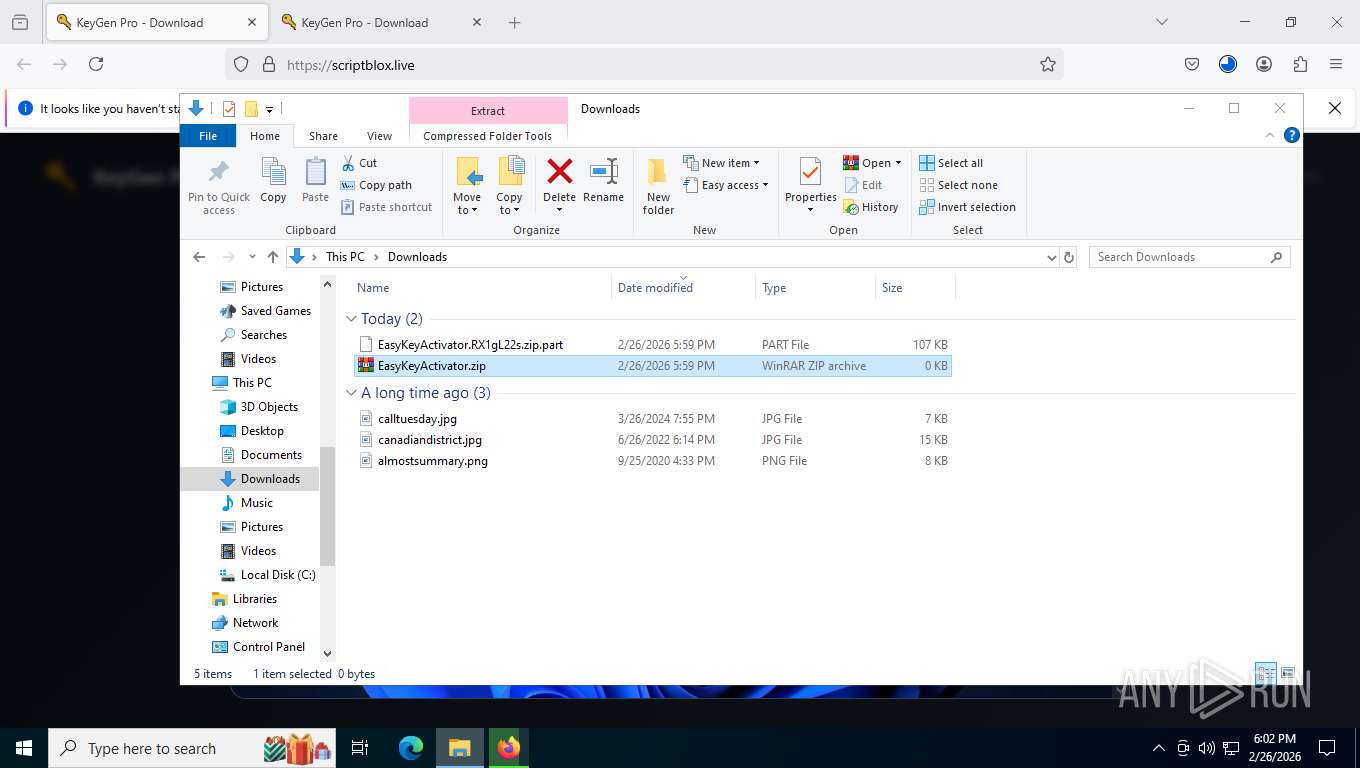
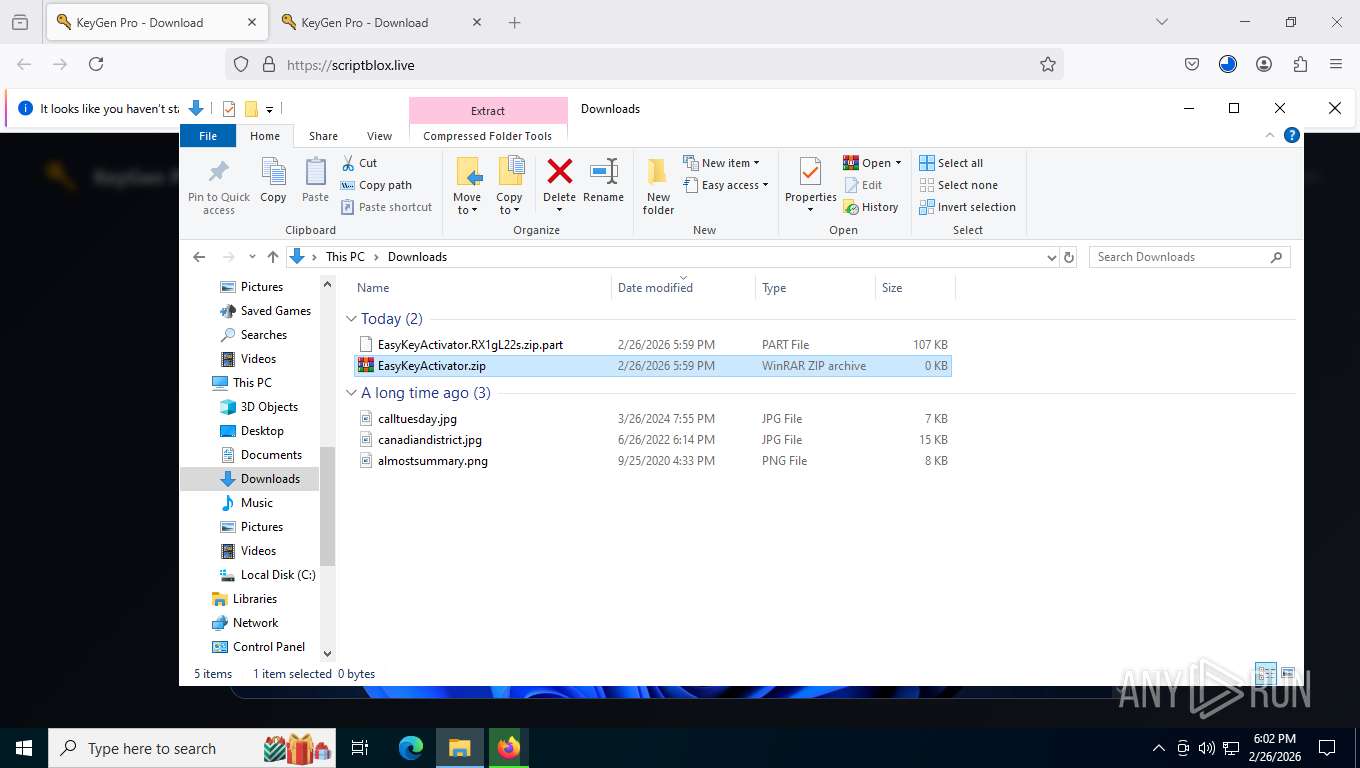
- WinRAR.exe (PID: 8492)
- WinRAR.exe (PID: 4044)
Drops script file
- firefox.exe (PID: 7452)
Manages system restore points
- SrTasks.exe (PID: 6484)
Reads Environment values
- zyCACcaDQJcSvND.exe (PID: 1488)
- zyCACcaDQJcSvND.exe (PID: 8772)
Create files in a temporary directory
- zyCACcaDQJcSvND.exe (PID: 8772)
Reads product name
- zyCACcaDQJcSvND.exe (PID: 8772)
- zyCACcaDQJcSvND.exe (PID: 1488)
Reads CPU info
- zyCACcaDQJcSvND.exe (PID: 1488)
Reads security settings of Internet Explorer
- zyCACcaDQJcSvND.exe (PID: 8772)
Reads the machine GUID from the registry
- zyCACcaDQJcSvND.exe (PID: 8772)
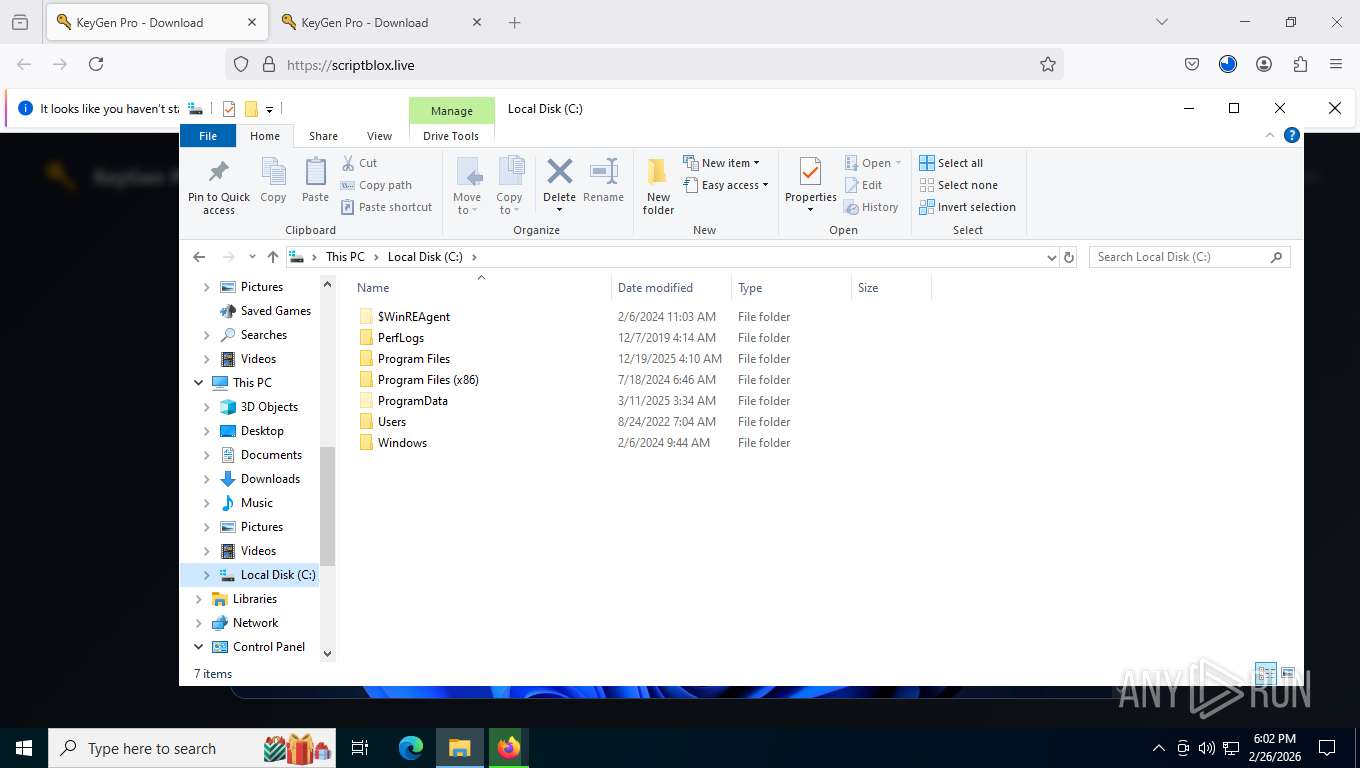
Creates files or folders in the user directory
- zyCACcaDQJcSvND.exe (PID: 8772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
28
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Users\admin\AppData\Local\UXAcMPRuDWwpLpj\zyCACcaDQJcSvND.exe" "GMbKr" | C:\Users\admin\AppData\Local\UXAcMPRuDWwpLpj\zyCACcaDQJcSvND.exe | — | wscript.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 20.19.0 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5872 -prefsLen 39411 -prefMapHandle 5876 -prefMapSize 272981 -jsInitHandle 5880 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5884 -initialChannelId {e3a886a9-ef50-4c11-a87d-441d8c90e015} -parentPid 7452 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7452" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 13 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 2784 -prefsLen 39330 -prefMapHandle 4480 -prefMapSize 272981 -jsInitHandle 5504 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3392 -initialChannelId {0ac1eb33-3dc0-4eb7-acc7-91339556f45d} -parentPid 7452 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7452" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 11 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3864 -prefsLen 45111 -prefMapHandle 3868 -prefMapSize 272981 -jsInitHandle 3872 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3880 -initialChannelId {c21e87d8-55c4-40e6-850c-ffdae7ab5d06} -parentPid 7452 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7452" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
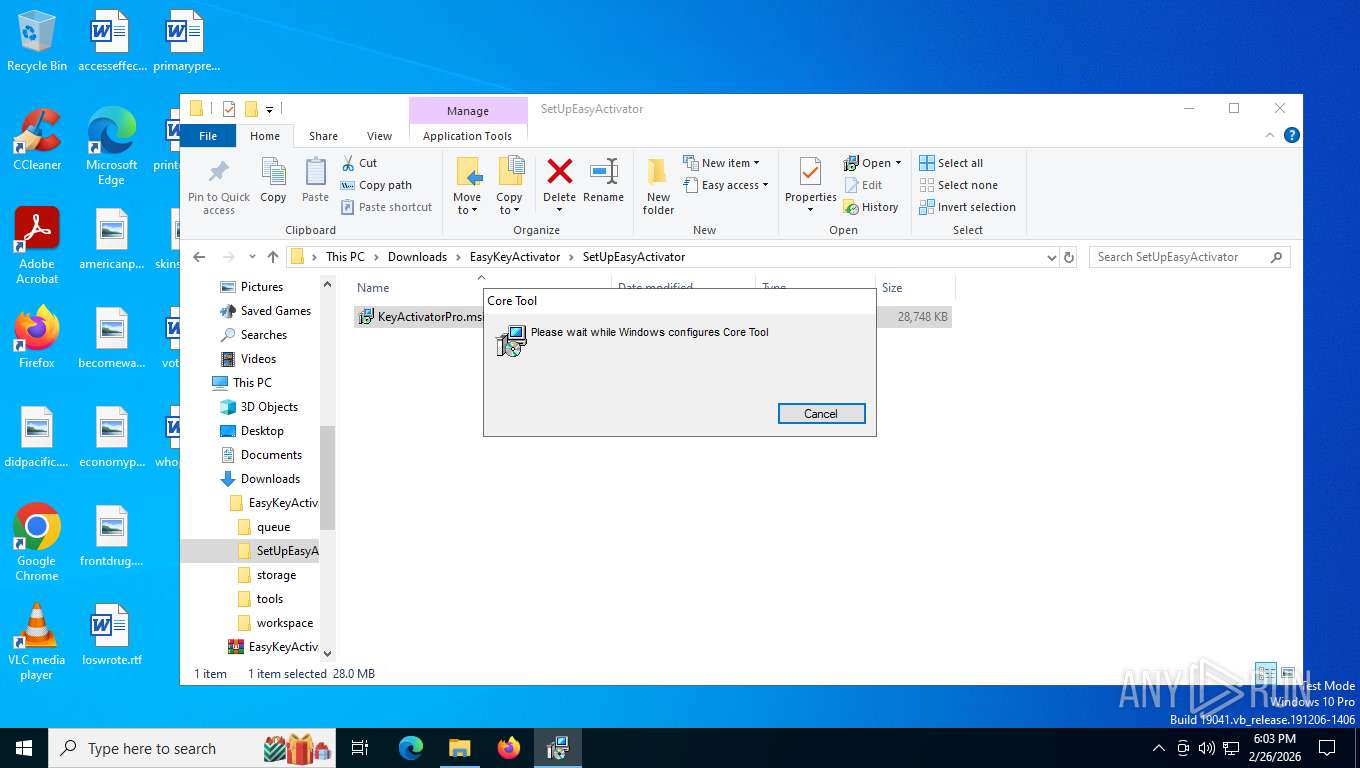
| 2260 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4832 -prefsLen 45212 -prefMapHandle 4836 -prefMapSize 272981 -jsInitHandle 4840 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4844 -initialChannelId {478c9142-3b92-409c-82f9-f6ea8ac53669} -parentPid 7452 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7452" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 1932 -prefsLen 36521 -prefMapHandle 1936 -prefMapSize 272981 -ipcHandle 2004 -initialChannelId {5bfc1623-2a4f-4f2b-bb7b-0cc6891baff5} -parentPid 7452 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7452" -appDir "C:\Program Files\Mozilla Firefox\browser" - 1 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 136.0 Modules
| |||||||||||||||
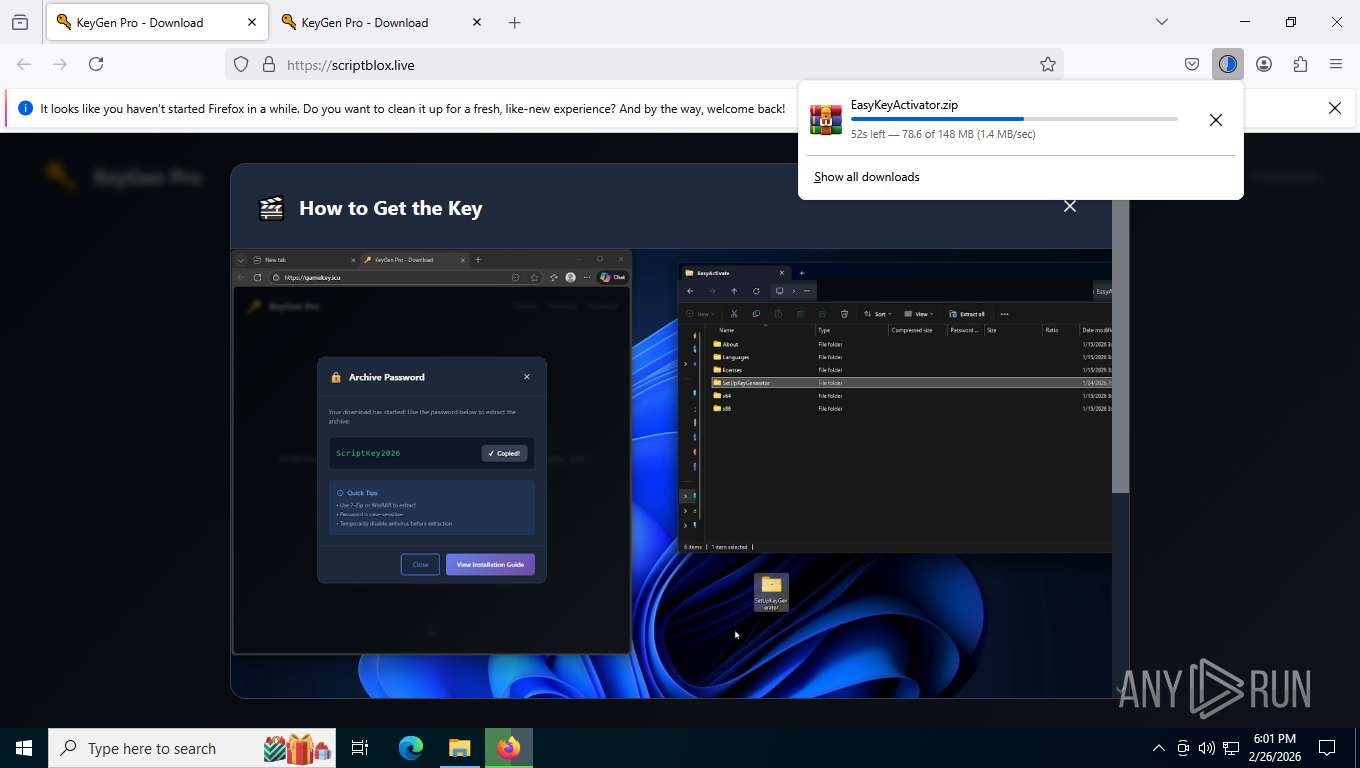
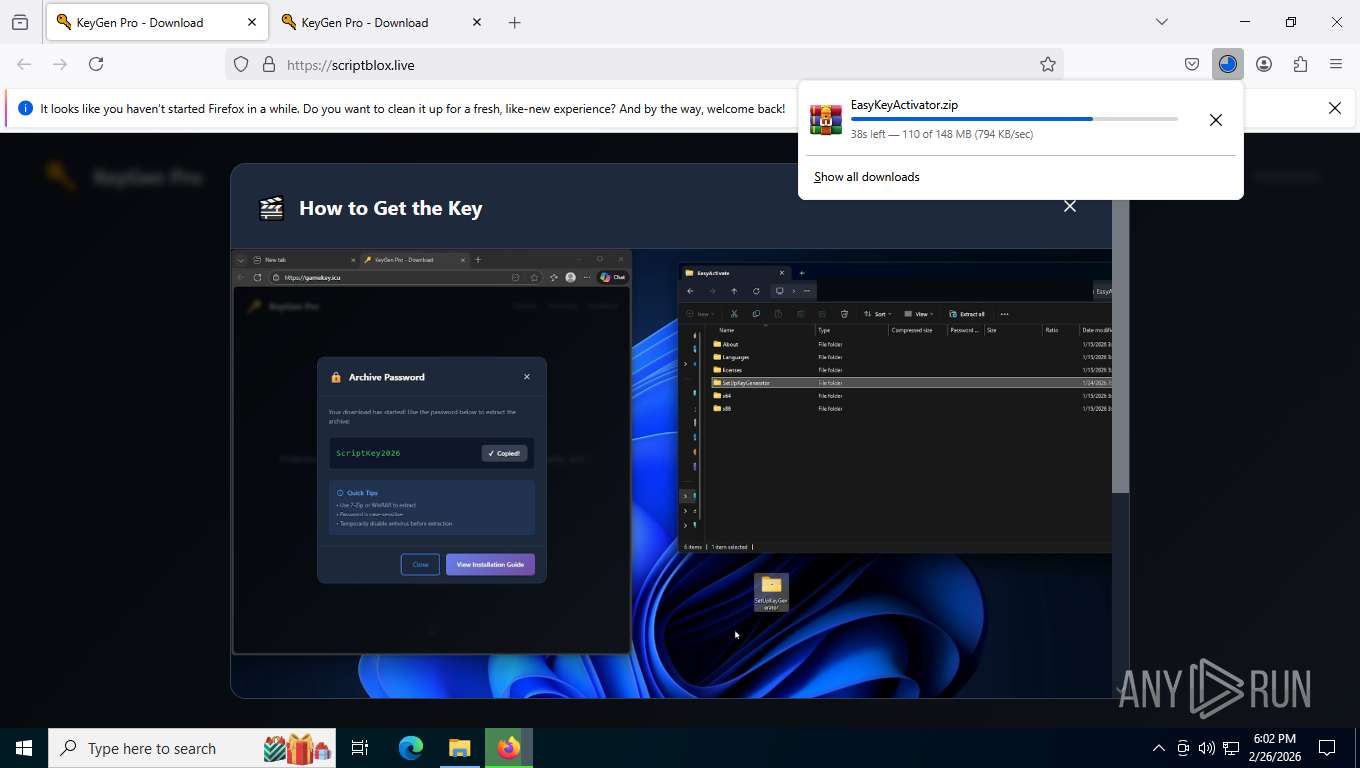
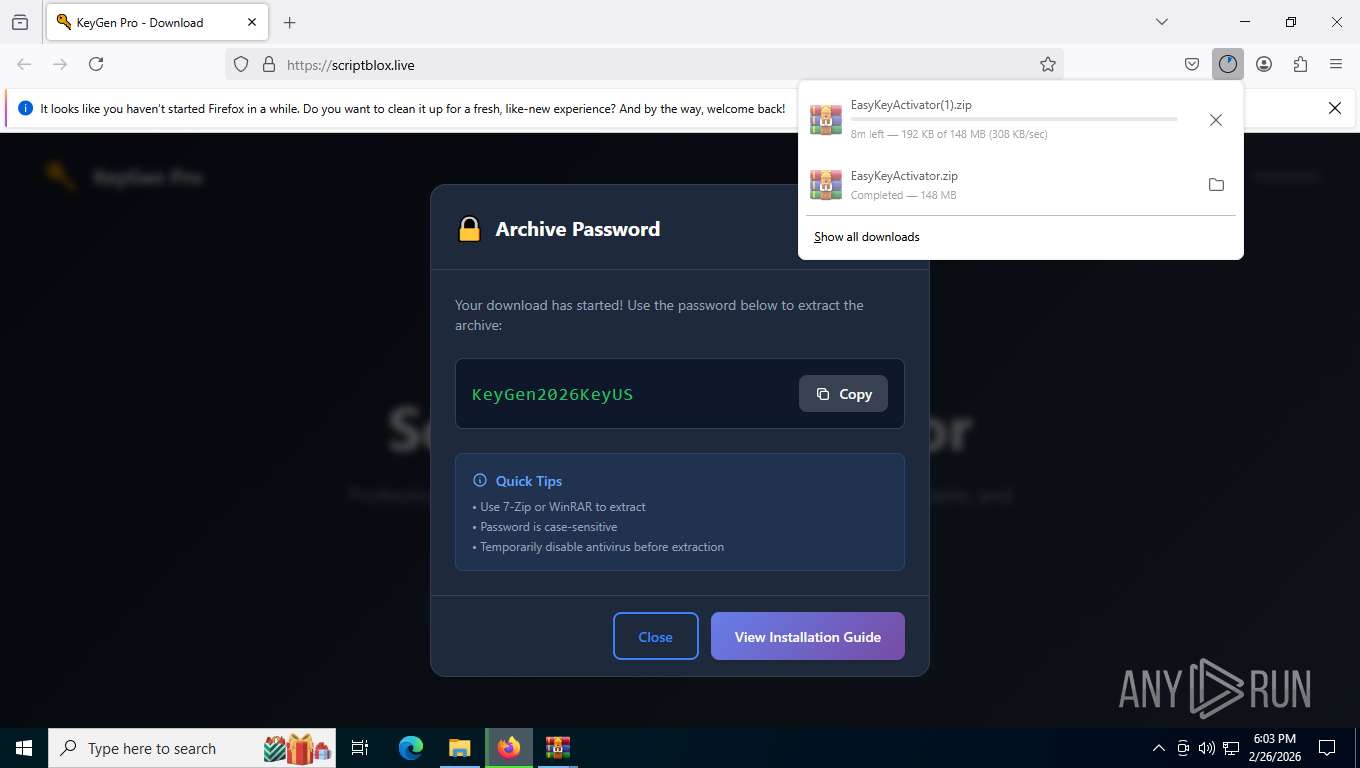
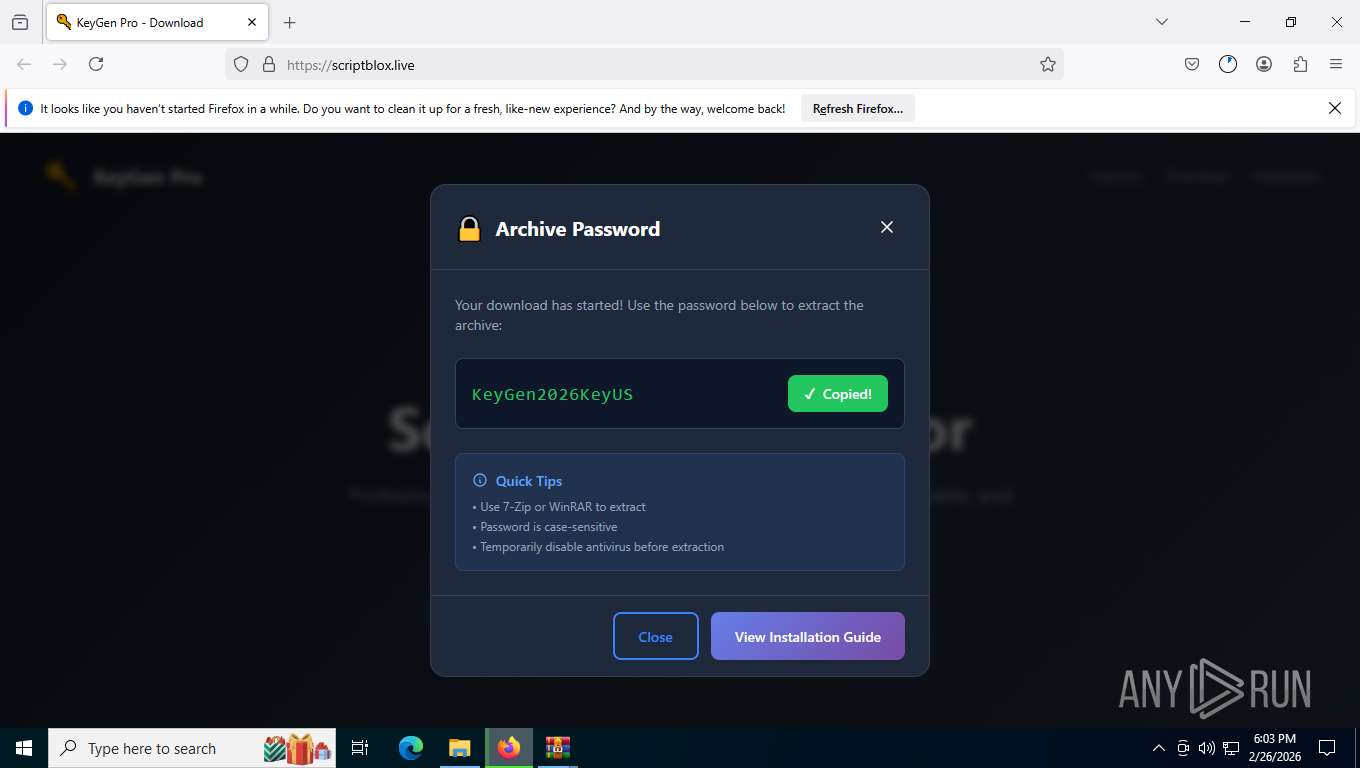
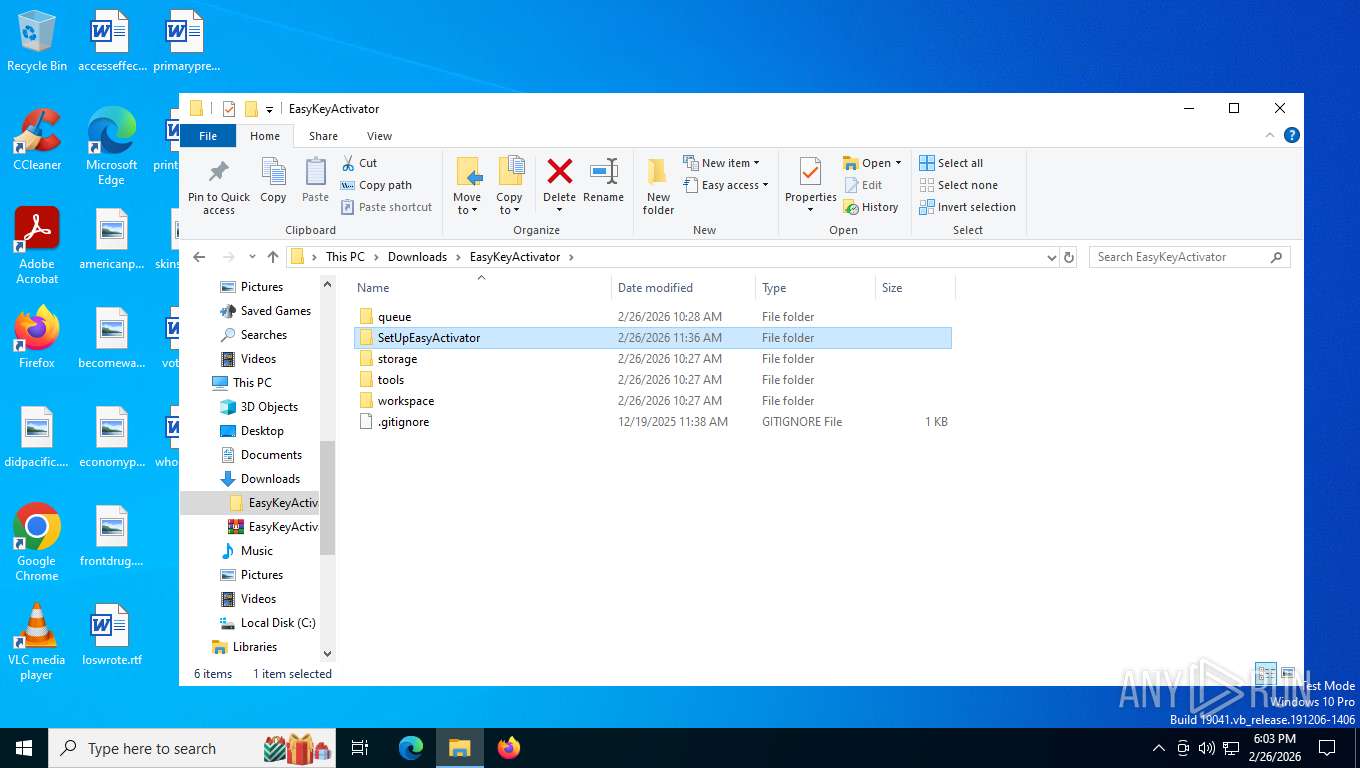
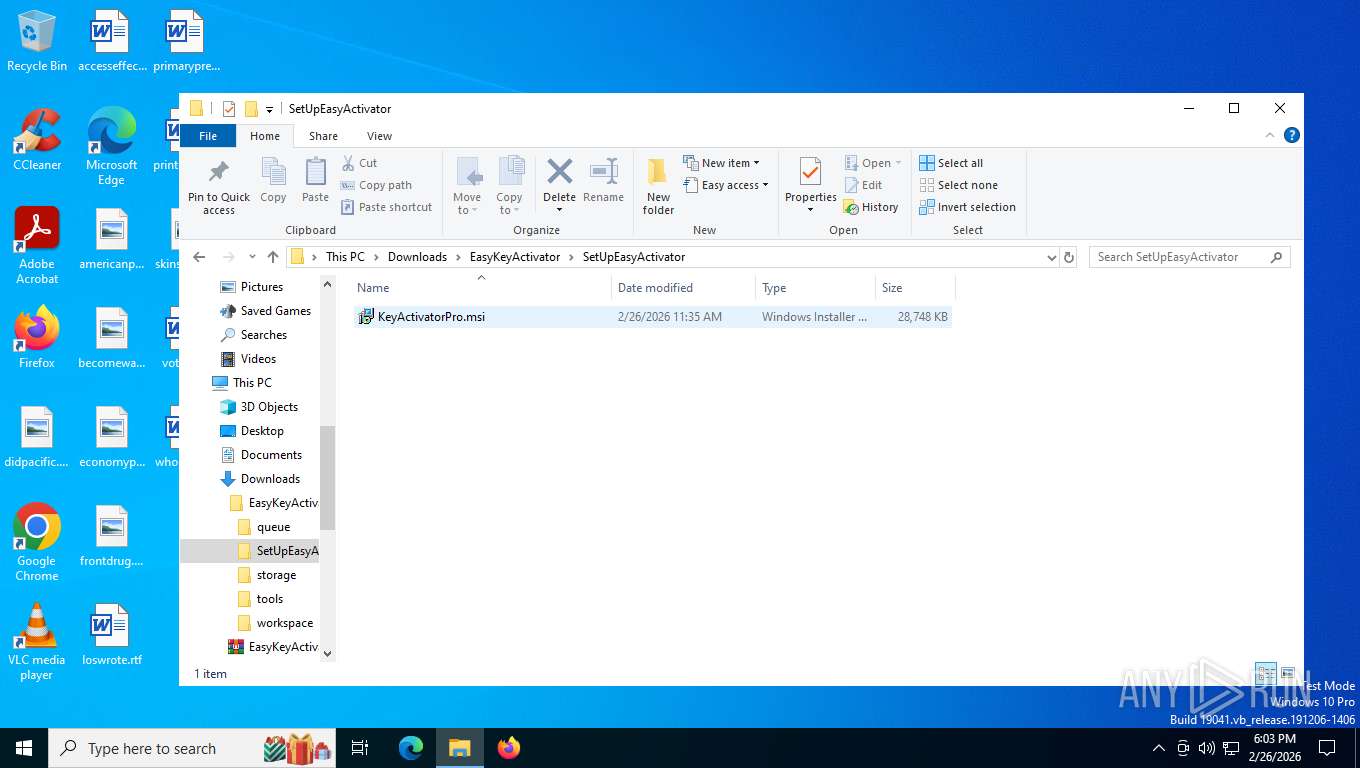
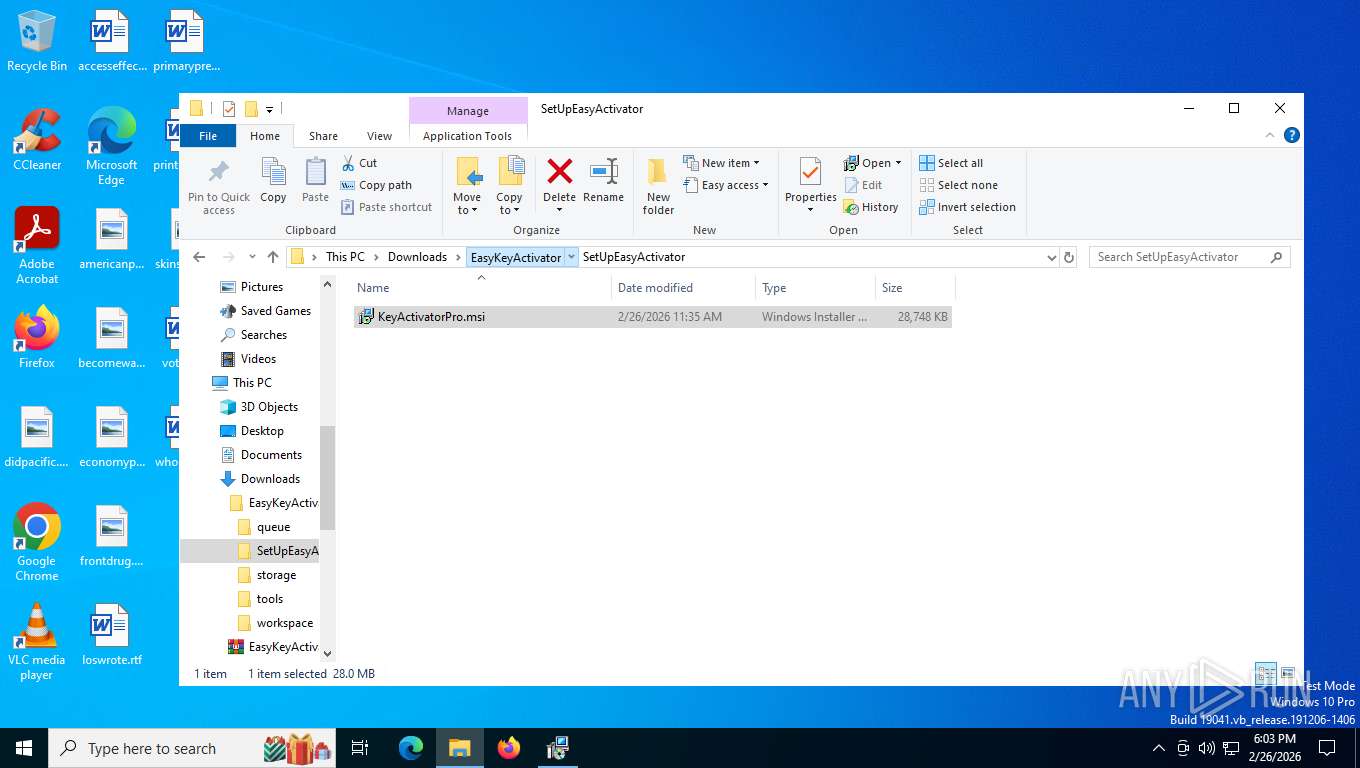
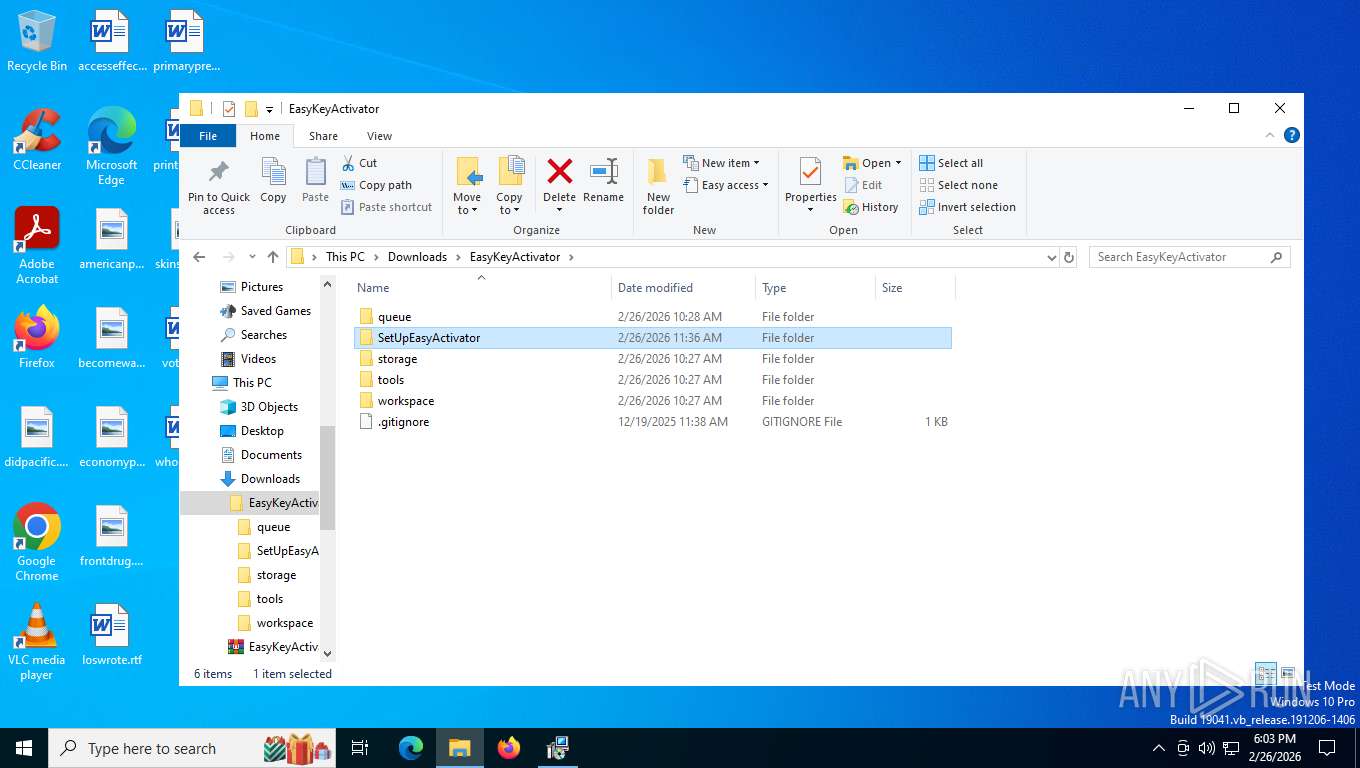
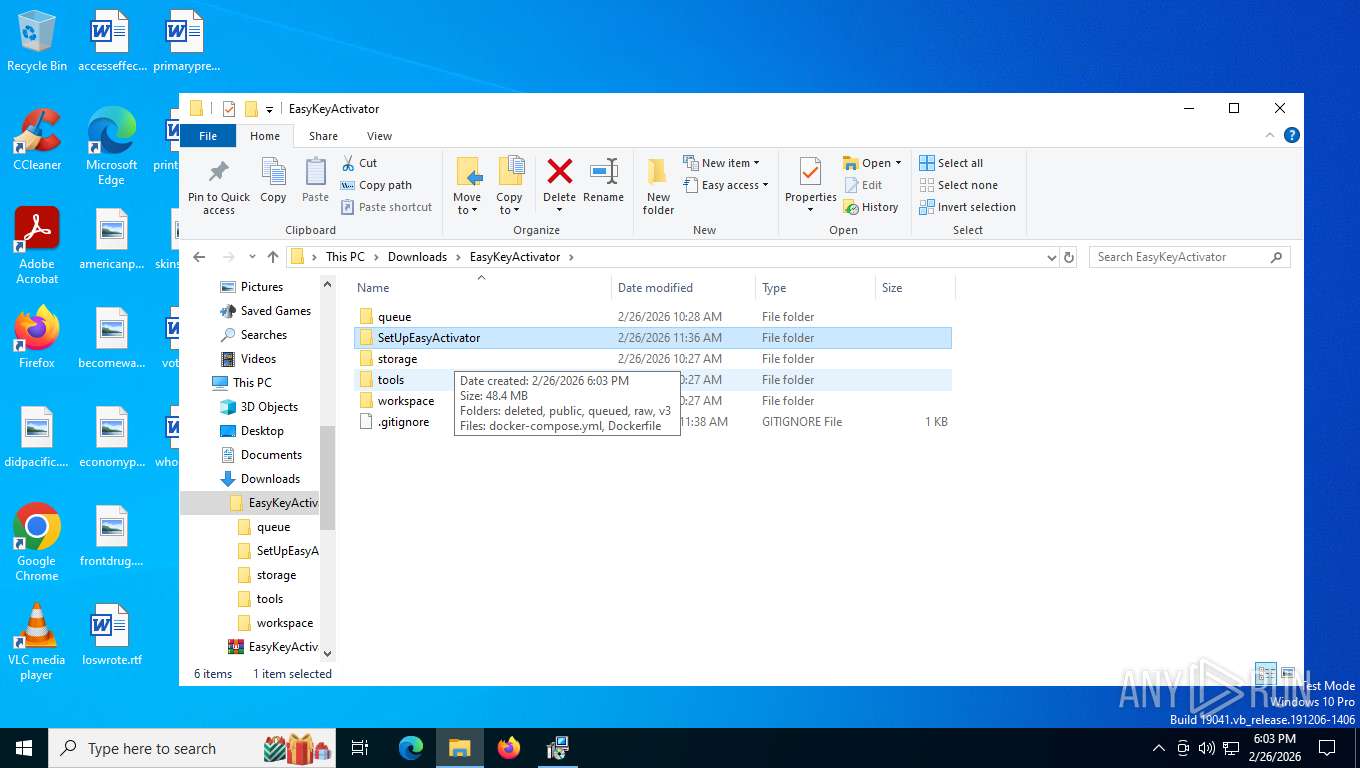
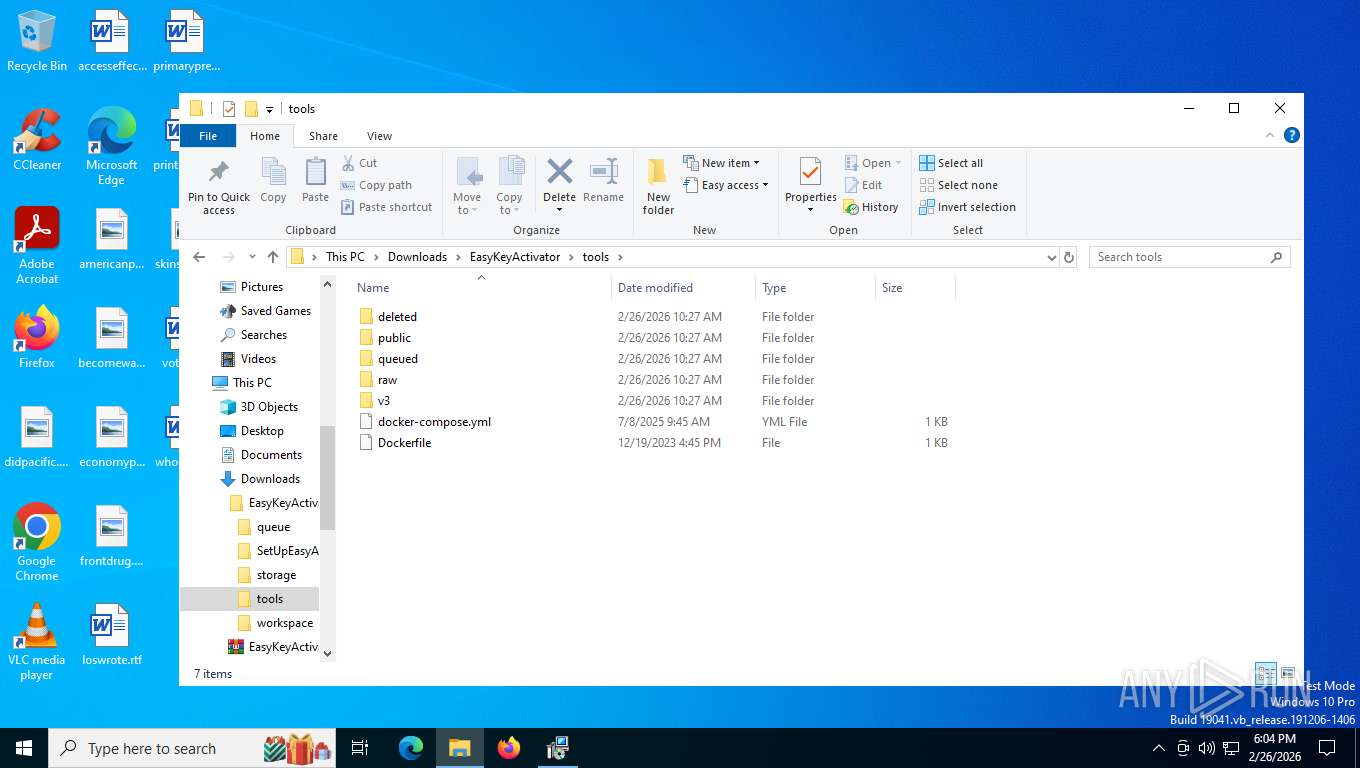
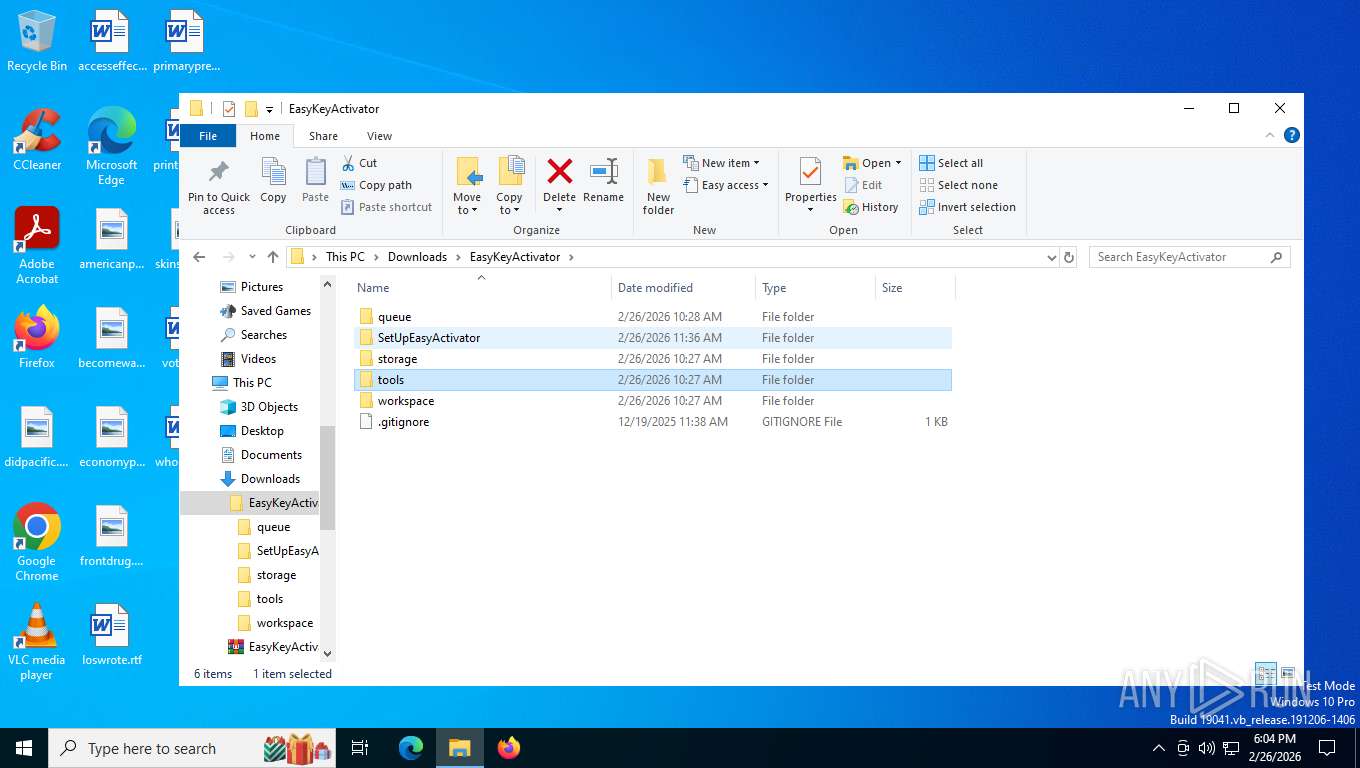
| 4044 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\EasyKeyActivator.zip" C:\Users\admin\Downloads\EasyKeyActivator\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 283
Read events
7 114
Write events
160
Delete events
9
Modification events
| (PID) Process: | (8492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8492) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2260) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000006D5FD32D74A7DC01D4080000C40F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
1 026
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7452 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | binary | |
MD5:0F17F3B6F1D1C36399D1A6EDE7E972B7 | SHA256:23F2C0620DE725F95EDFD1B5C2D39BA4E004790ADBAE950374CE3C2AC634411E | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:A5692178DBDB4F864A31E489F580C428 | SHA256:0569B828DCB748821250B72C0AA1F71EDF7362D49E01EA9659E943EEB95F26D7 | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | binary | |
MD5:0F17F3B6F1D1C36399D1A6EDE7E972B7 | SHA256:23F2C0620DE725F95EDFD1B5C2D39BA4E004790ADBAE950374CE3C2AC634411E | |||
| 7452 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
150
TCP/UDP connections
83
DNS requests
135
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7452 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | binary | 8 b | unknown |
7452 | firefox.exe | GET | — | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | — | — | unknown |
5568 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 958 b | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
7452 | firefox.exe | POST | 200 | 142.251.39.131:80 | http://o.pki.goog/wr2 | US | binary | 471 b | whitelisted |
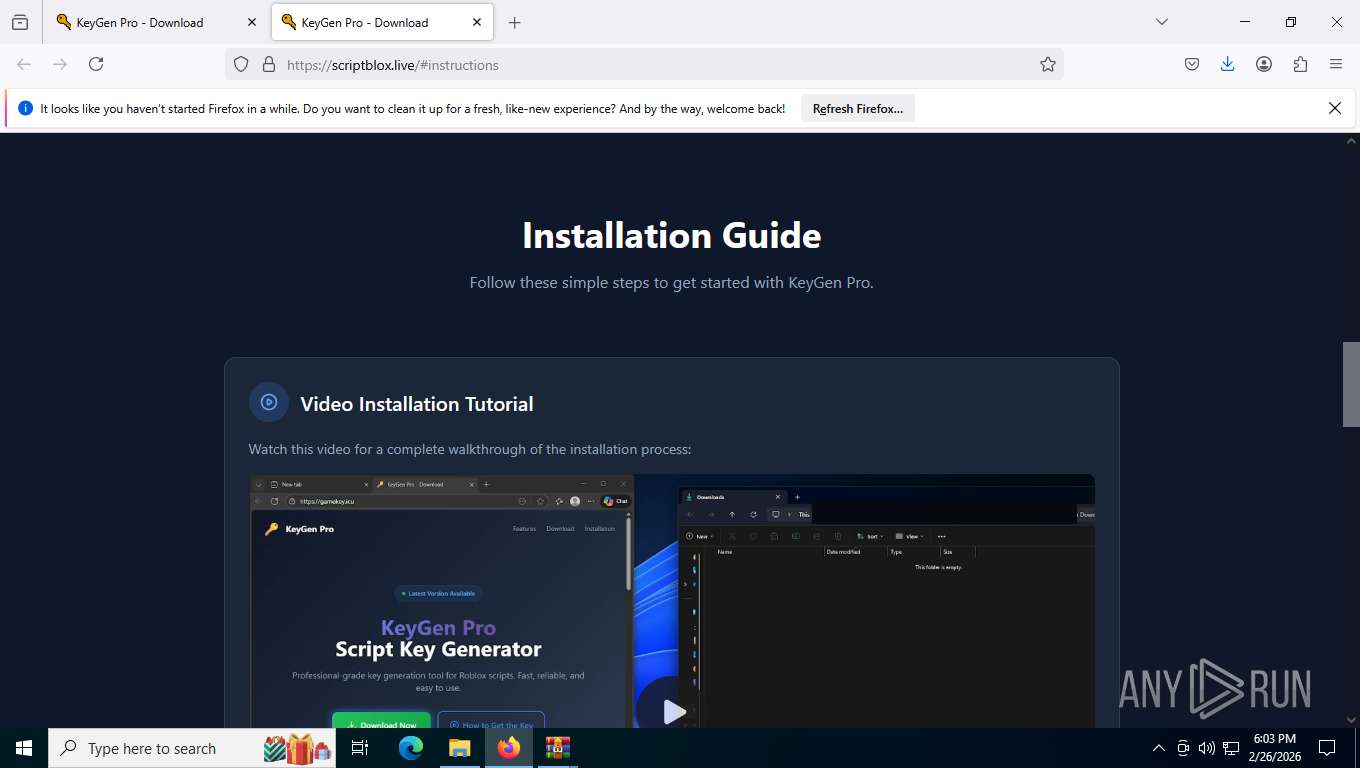
7452 | firefox.exe | GET | 200 | 172.67.170.217:443 | https://scriptix.live/cdn-cgi/scripts/5c5dd728/cloudflare-static/email-decode.min.js | US | — | 1.21 Kb | unknown |
7452 | firefox.exe | GET | 200 | 172.67.170.217:443 | https://scriptix.live/ | US | — | 36.9 Kb | unknown |
7452 | firefox.exe | GET | 200 | 172.67.170.217:443 | https://scriptix.live/js/analytics.min.js | US | — | 29.4 Kb | unknown |
7452 | firefox.exe | POST | 200 | 142.251.39.131:80 | http://o.pki.goog/wr2 | US | binary | 471 b | whitelisted |
7452 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3348 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8860 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.241.218:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 92.123.104.60:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5568 | SearchApp.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7452 | firefox.exe | 151.101.205.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
scriptix.live |
| unknown |
detectportal.firefox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
7452 | firefox.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2292 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |