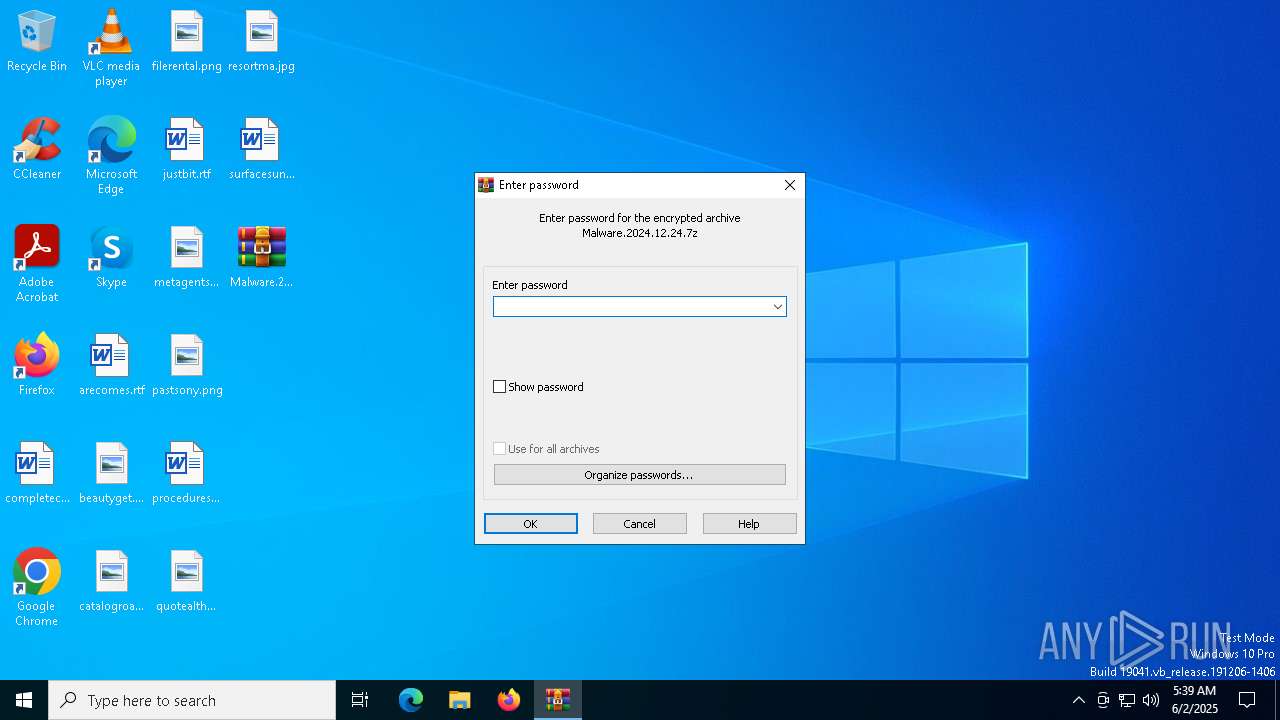
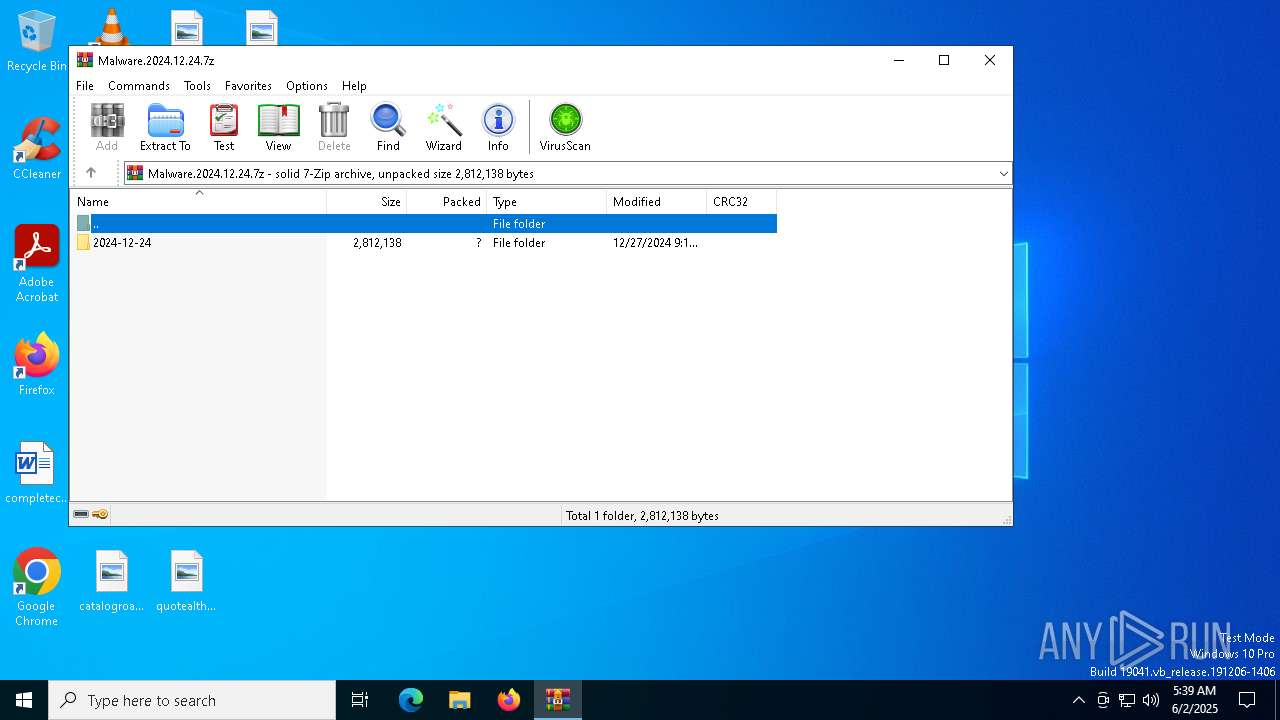
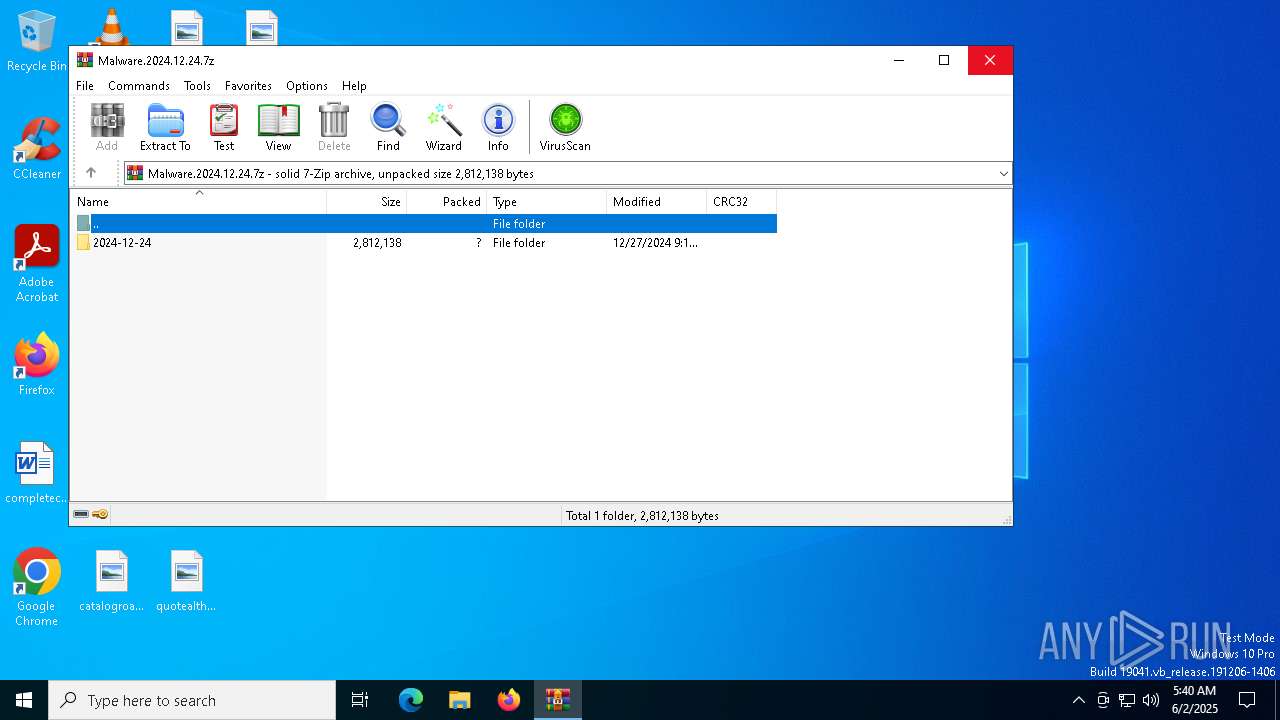
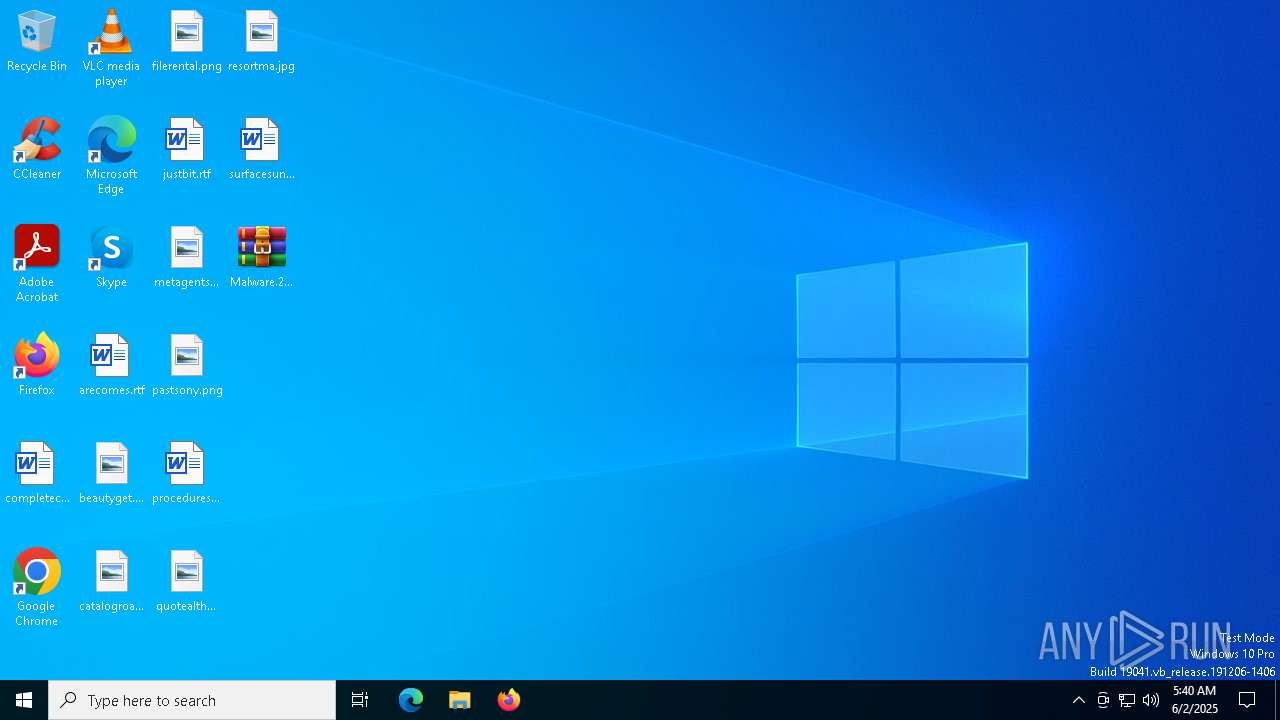
| File name: | Malware.2024.12.24.7z |
| Full analysis: | https://app.any.run/tasks/ab55d07b-4944-4d98-811c-b7a8293c8758 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | June 02, 2025, 05:39:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 5DAAC17067A28DAA7C65449923069387 |
| SHA1: | 9136626E9E75126163A3BE7FEF95DCA7C8E0277D |
| SHA256: | 19B4FA4A282D95E524BFAB06495337C5E0D3A5A3E54B60DEE968923916E2F358 |
| SSDEEP: | 24576:3TwYfpQv9vL/qqdNE6D/UO9JAhEvDltXLoLgvaWCG71pcUgL1UzCvH7Ob:DwYhQv9vL/qqdNE6D/UO9JAhEvDnXLo8 |
MALICIOUS
RAT has been found (auto)
- WinRAR.exe (PID: 5984)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8040)
Adds path to the Windows Defender exclusion list
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
Changes Windows Defender settings
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
SUSPICIOUS
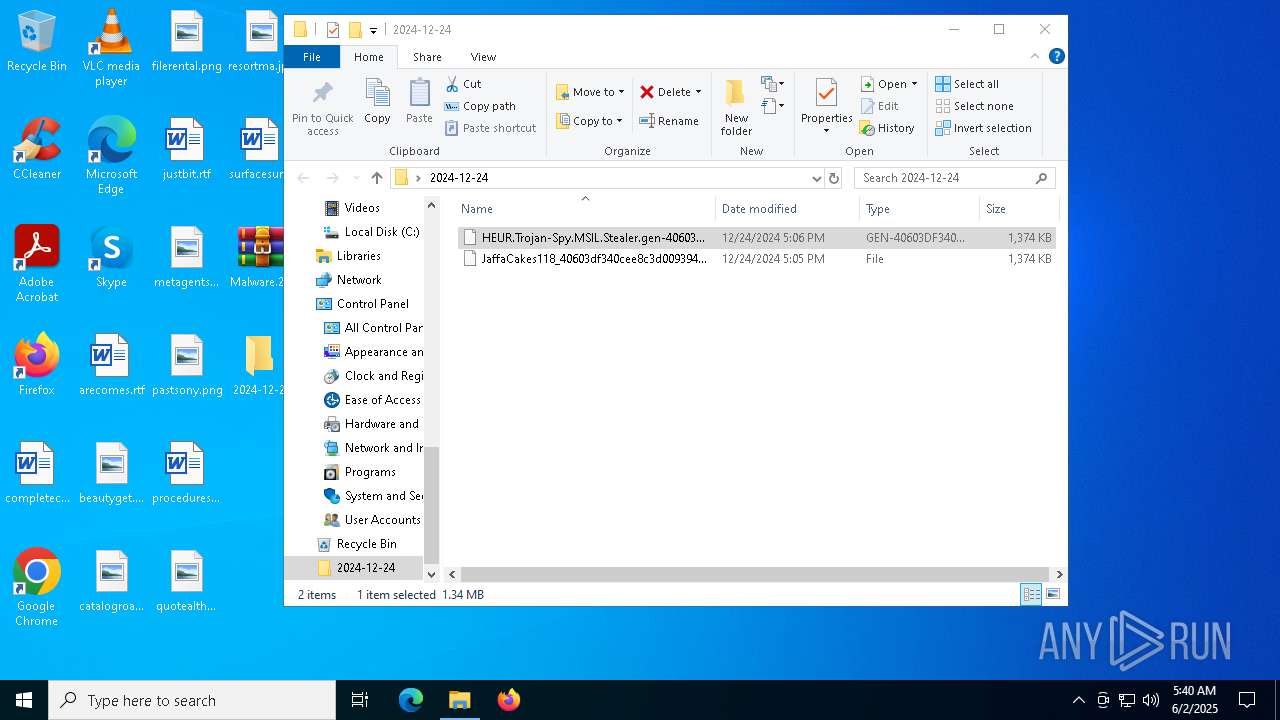
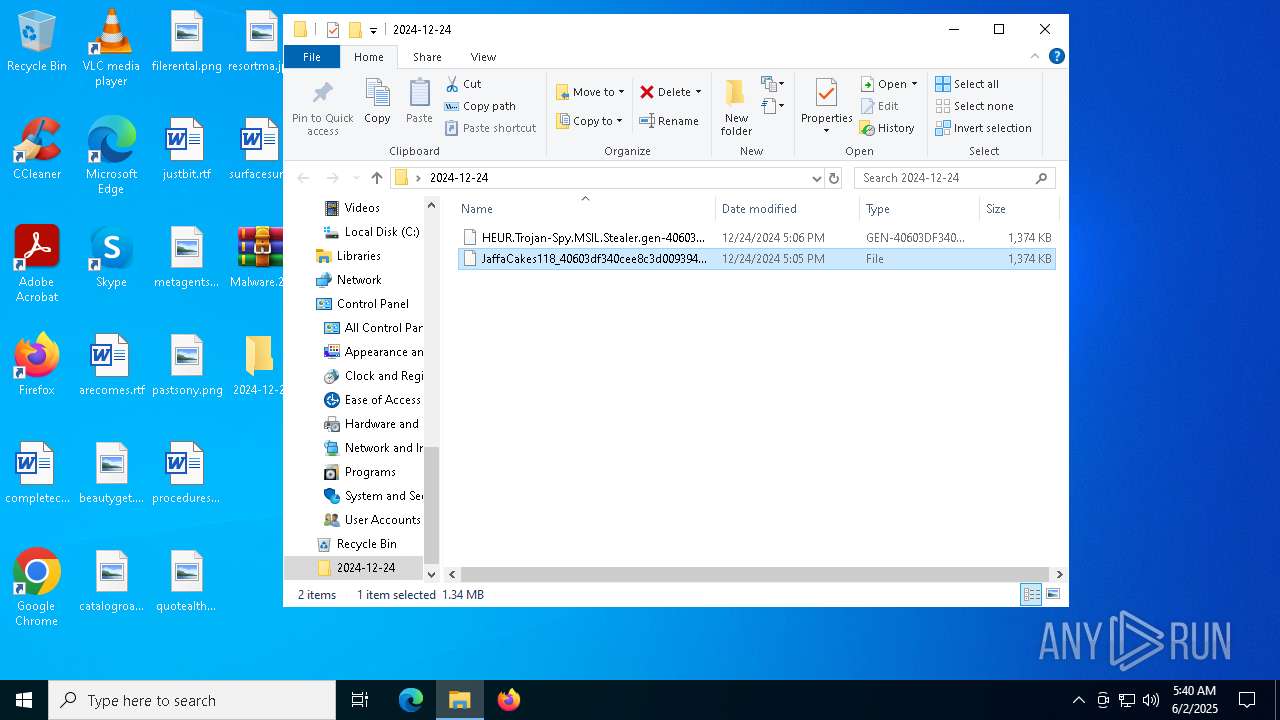
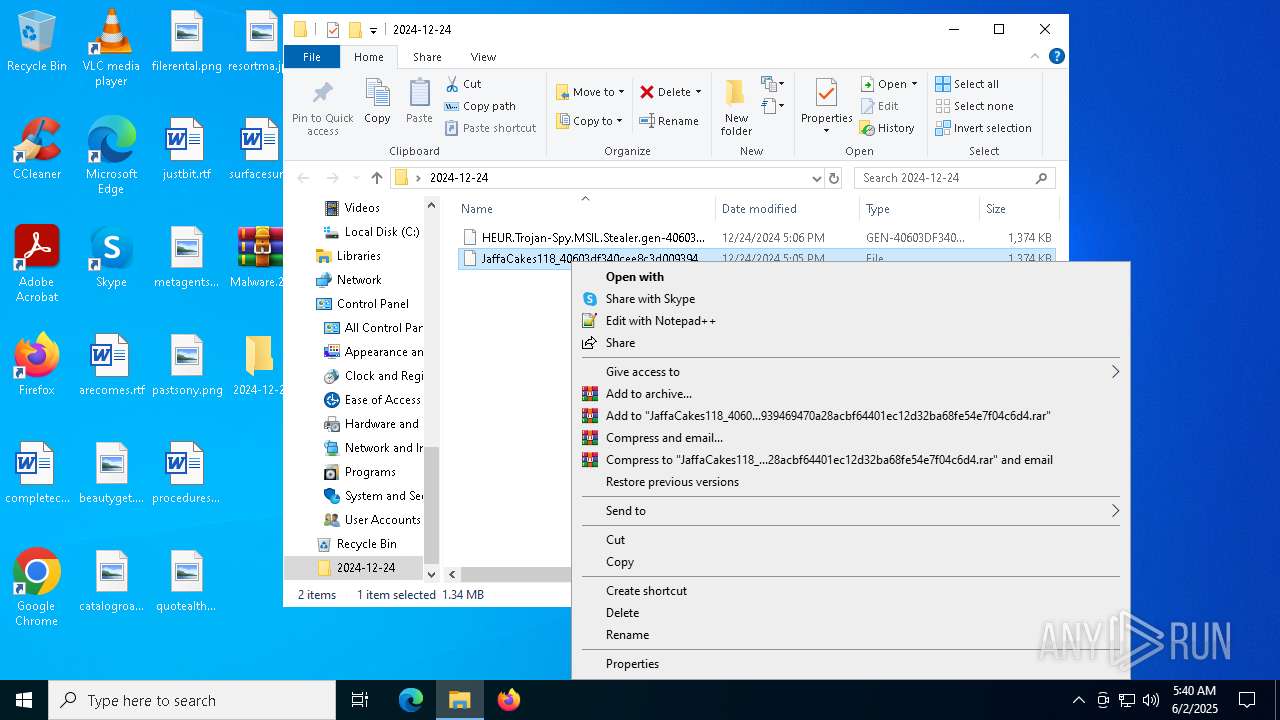
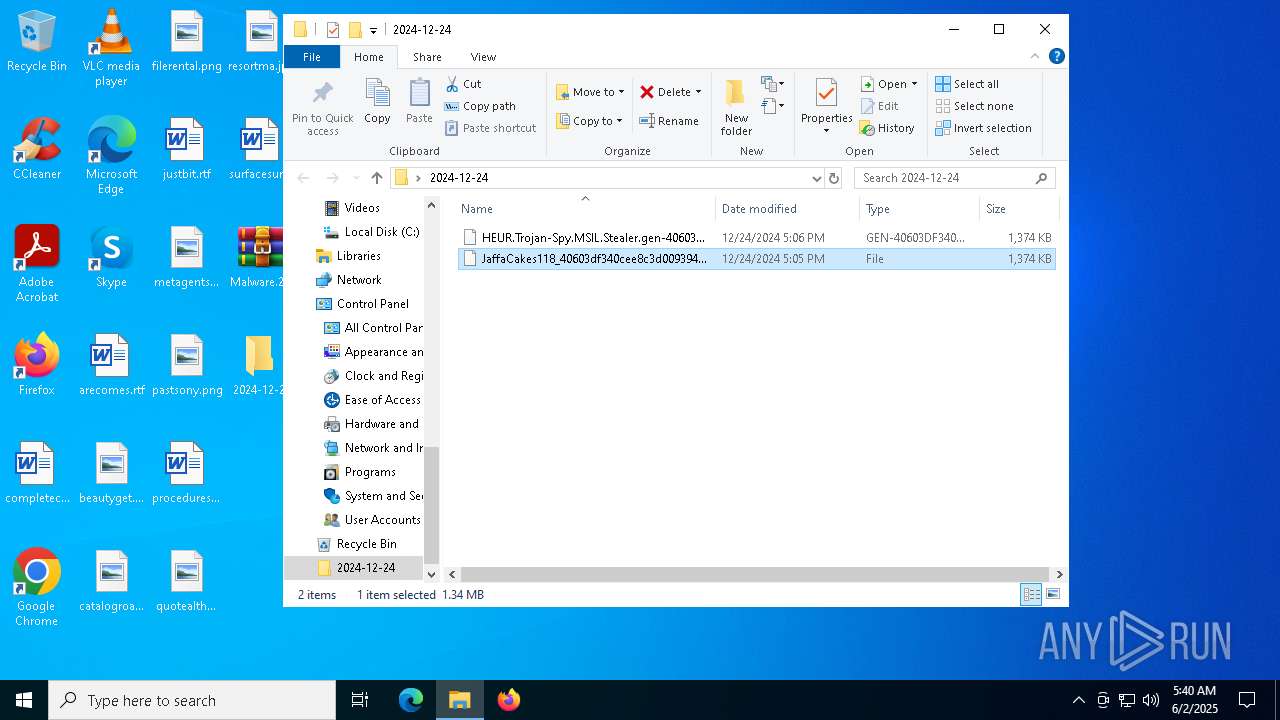
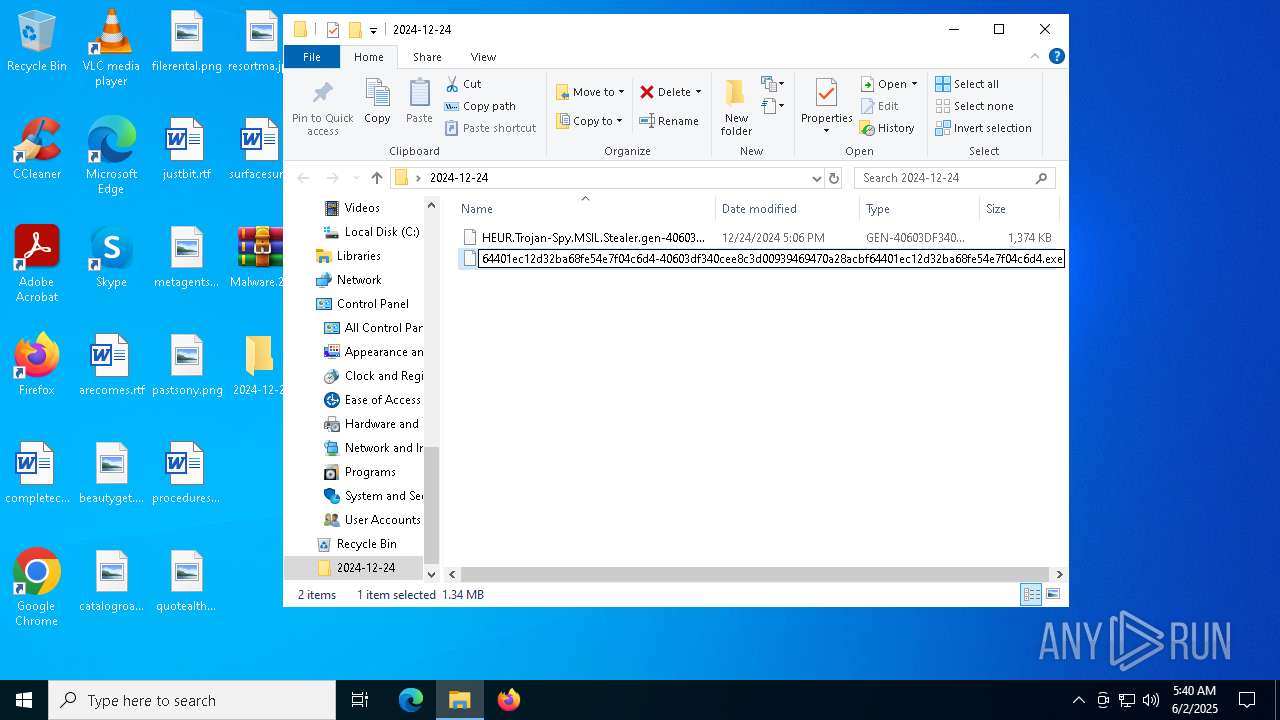
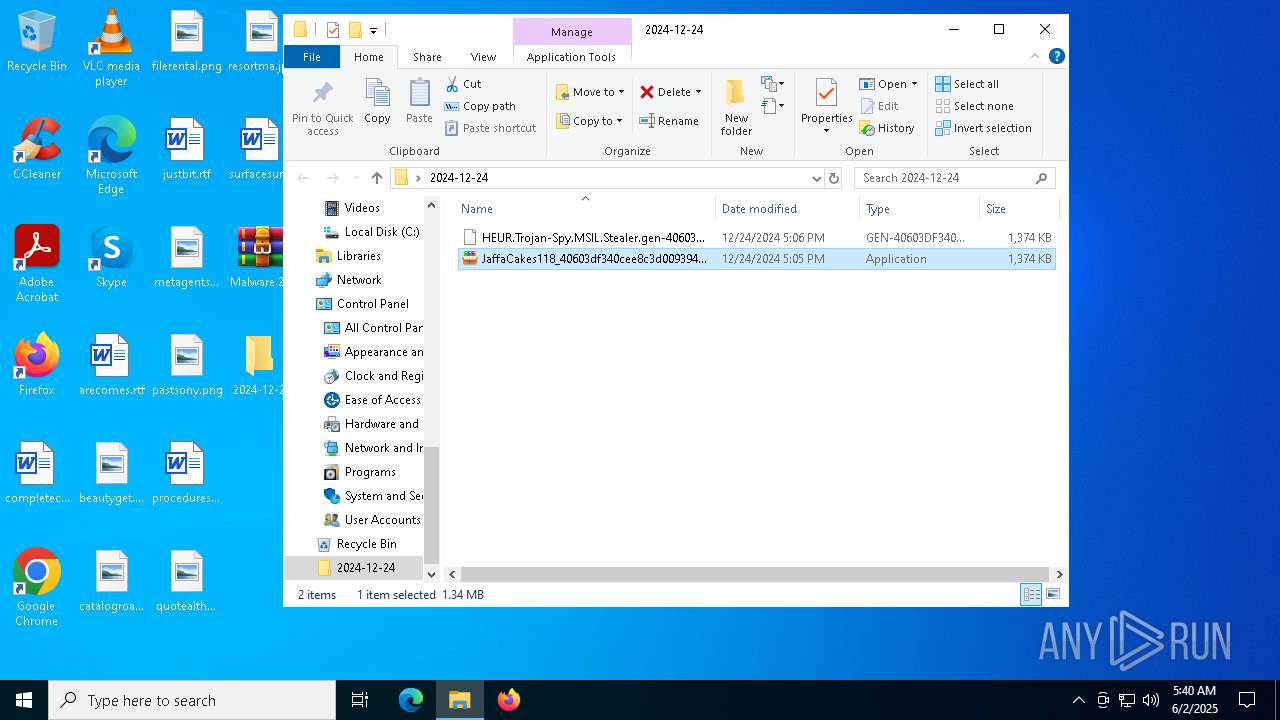
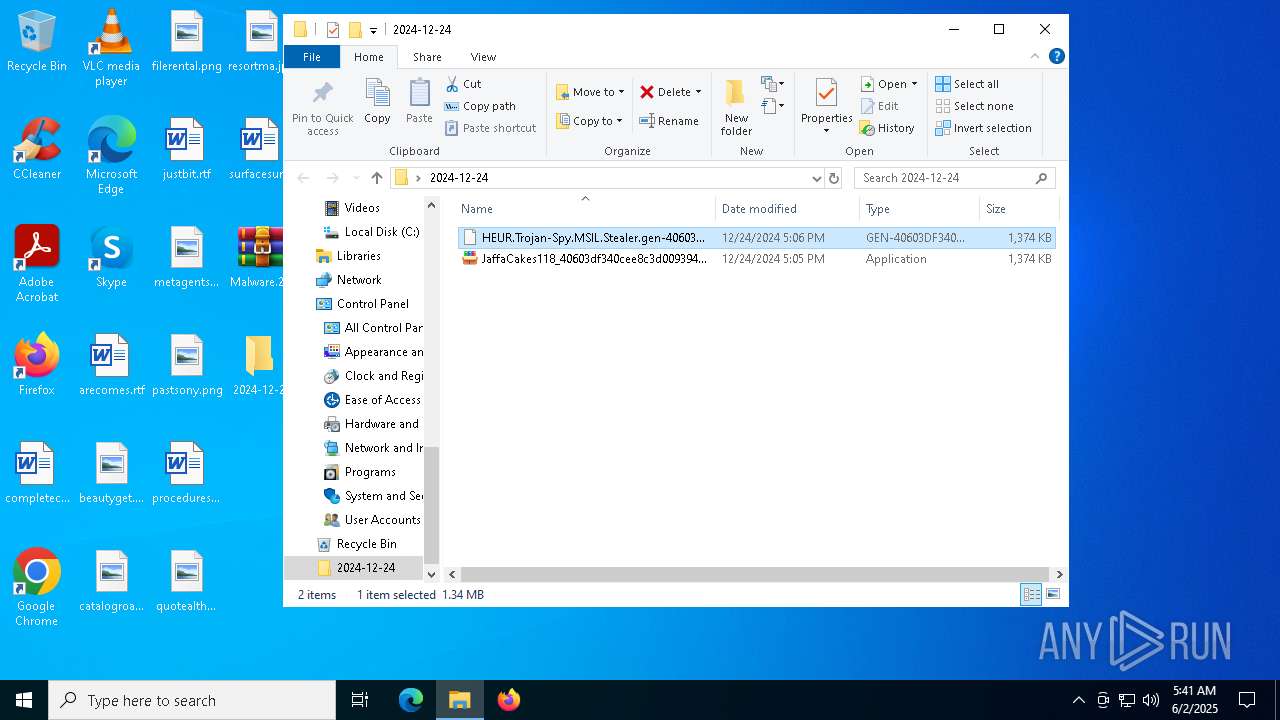
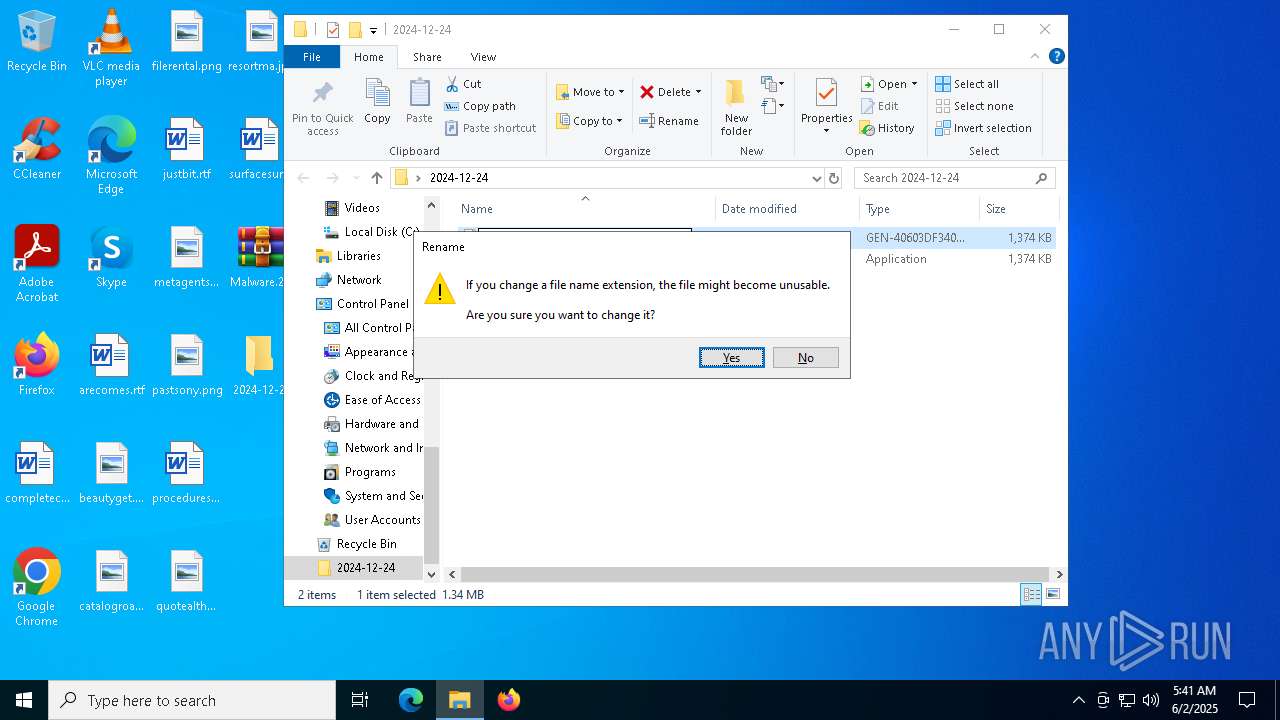
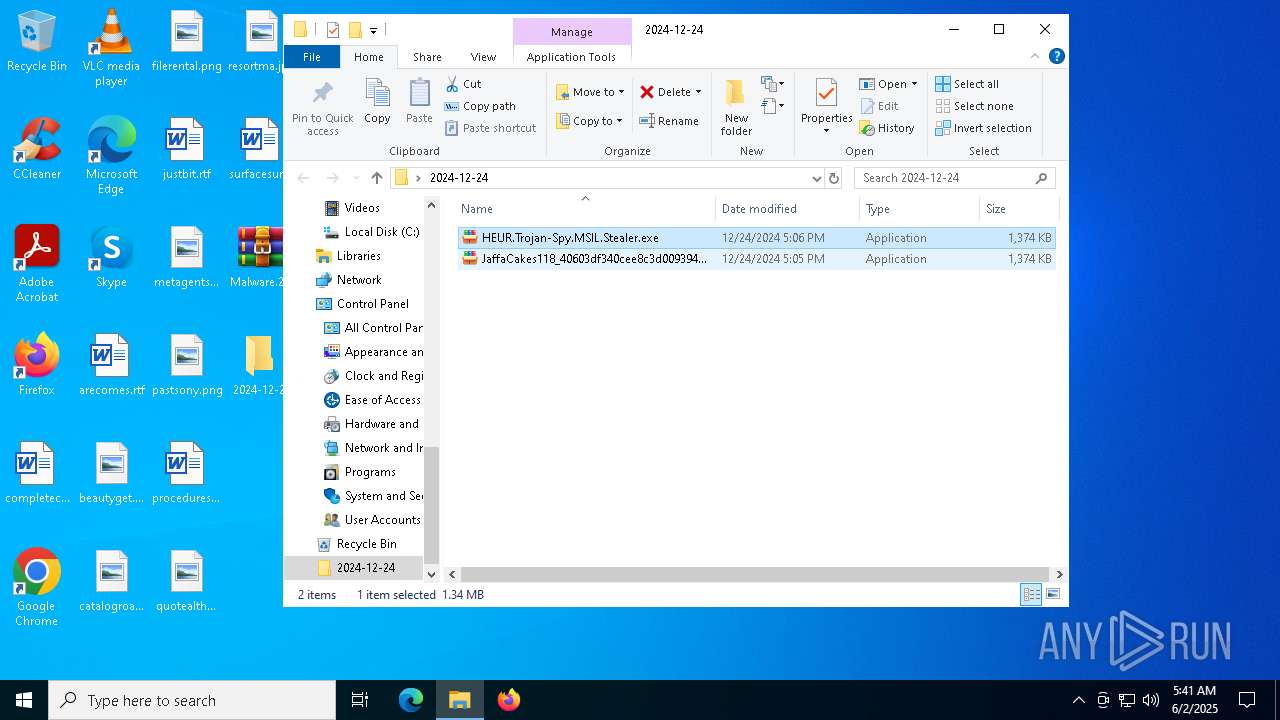
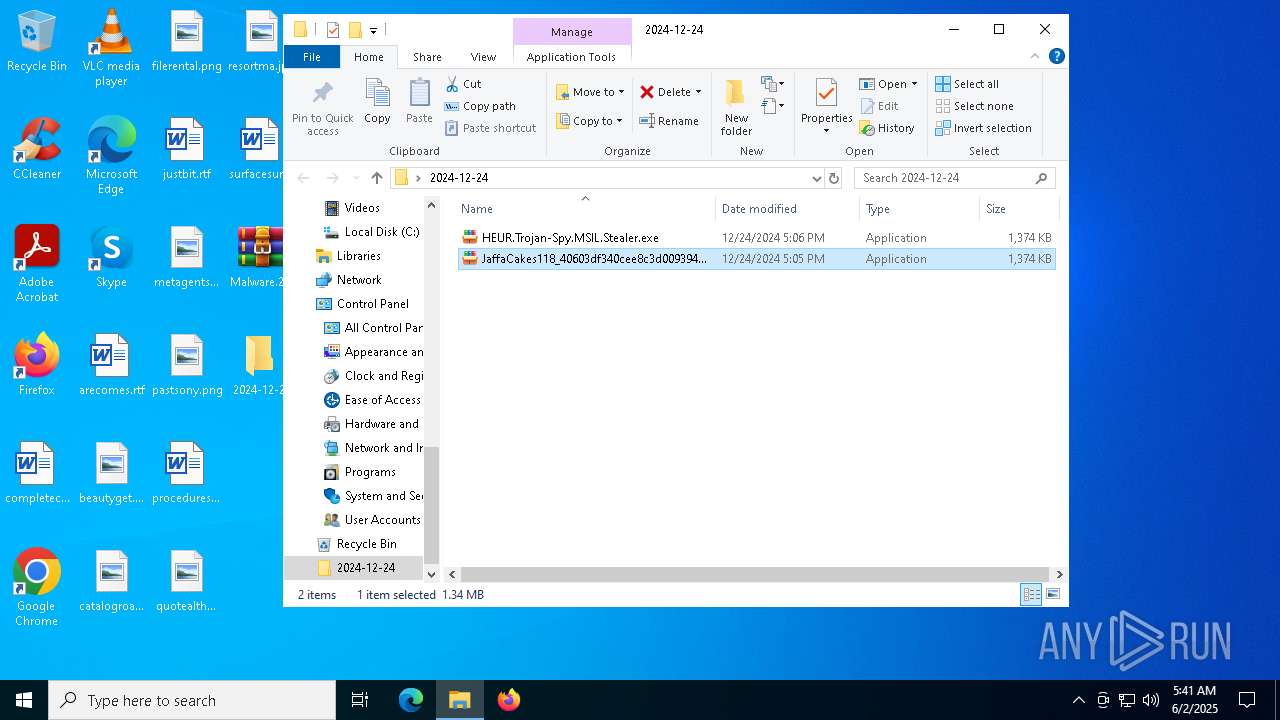
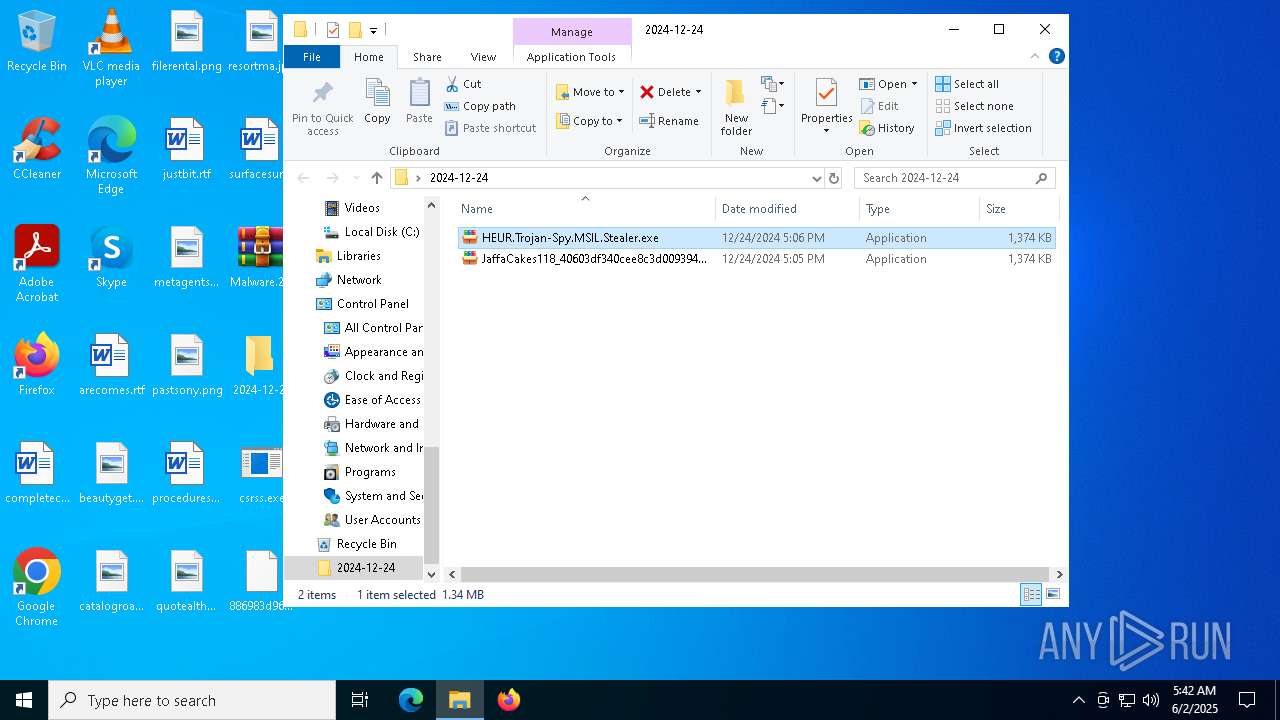
Executable content was dropped or overwritten
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
Reads security settings of Internet Explorer
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8040)
Executing commands from a ".bat" file
- wscript.exe (PID: 8040)
- DllCommonsvc.exe (PID: 7268)
- WmiPrvSE.exe (PID: 5056)
- WmiPrvSE.exe (PID: 9128)
- WmiPrvSE.exe (PID: 8308)
- wscript.exe (PID: 8464)
- wscript.exe (PID: 7736)
- DllCommonsvc.exe (PID: 8508)
- wscript.exe (PID: 7100)
- wscript.exe (PID: 8532)
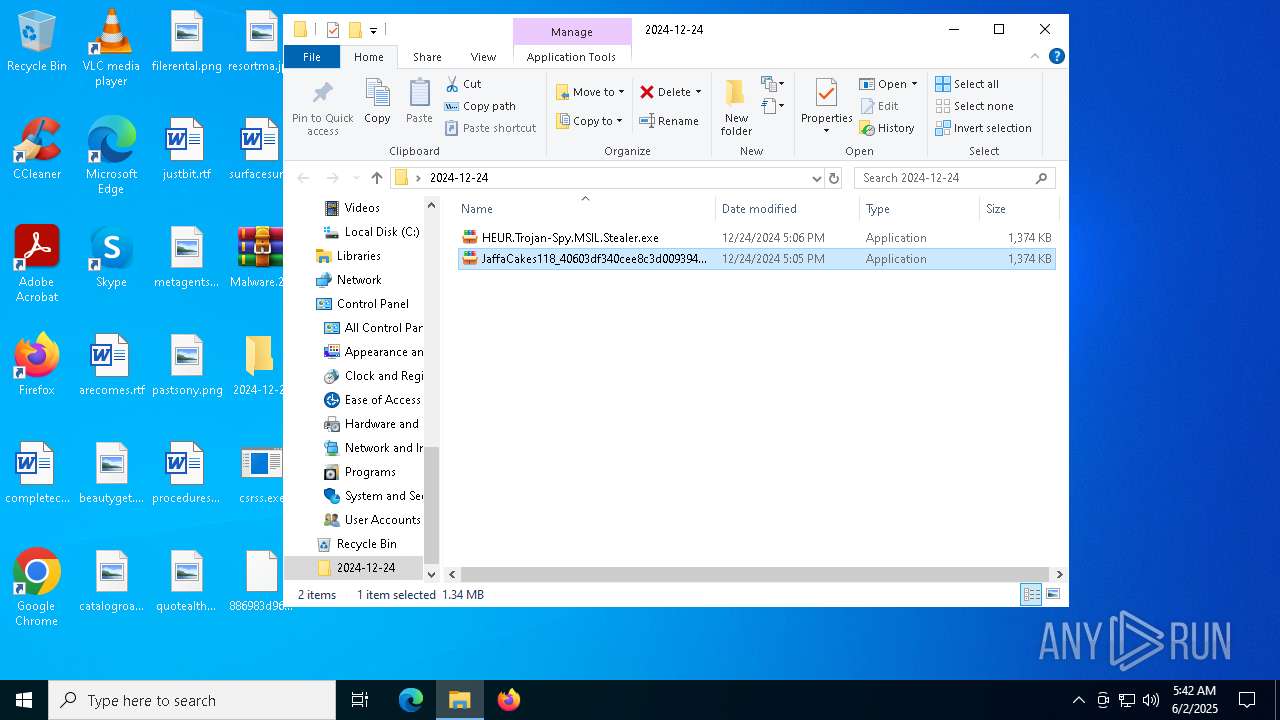
- csrss.exe (PID: 4944)
- DllCommonsvc.exe (PID: 1132)
- csrss.exe (PID: 660)
- wscript.exe (PID: 7364)
- DllCommonsvc.exe (PID: 7612)
- TextInputHost.exe (PID: 8492)
- TextInputHost.exe (PID: 7312)
- TextInputHost.exe (PID: 8932)
- TextInputHost.exe (PID: 8800)
- TextInputHost.exe (PID: 7964)
- TextInputHost.exe (PID: 7972)
- TextInputHost.exe (PID: 6792)
- TextInputHost.exe (PID: 7832)
- TextInputHost.exe (PID: 3684)
- TextInputHost.exe (PID: 7216)
- TextInputHost.exe (PID: 9000)
- TextInputHost.exe (PID: 8444)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8040)
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
- WmiPrvSE.exe (PID: 5056)
- WmiPrvSE.exe (PID: 9128)
- WmiPrvSE.exe (PID: 8308)
- wscript.exe (PID: 8464)
- DllCommonsvc.exe (PID: 6900)
- wscript.exe (PID: 7100)
- wscript.exe (PID: 7736)
- DllCommonsvc.exe (PID: 4628)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- csrss.exe (PID: 660)
- csrss.exe (PID: 4944)
- wscript.exe (PID: 8532)
- DllCommonsvc.exe (PID: 8120)
- wscript.exe (PID: 7364)
- DllCommonsvc.exe (PID: 7612)
- TextInputHost.exe (PID: 8492)
- TextInputHost.exe (PID: 8932)
- TextInputHost.exe (PID: 7312)
- TextInputHost.exe (PID: 6792)
- TextInputHost.exe (PID: 7972)
- TextInputHost.exe (PID: 7832)
- TextInputHost.exe (PID: 8800)
- TextInputHost.exe (PID: 7216)
- TextInputHost.exe (PID: 3684)
- TextInputHost.exe (PID: 7964)
- TextInputHost.exe (PID: 8444)
- TextInputHost.exe (PID: 9000)
Reads the date of Windows installation
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
The process creates files with name similar to system file names
- DllCommonsvc.exe (PID: 7268)
Executed via WMI
- schtasks.exe (PID: 6060)
- schtasks.exe (PID: 5504)
- schtasks.exe (PID: 7272)
- schtasks.exe (PID: 7712)
- schtasks.exe (PID: 7904)
- schtasks.exe (PID: 7764)
- schtasks.exe (PID: 7728)
- schtasks.exe (PID: 8080)
- schtasks.exe (PID: 7596)
- schtasks.exe (PID: 4920)
- schtasks.exe (PID: 2084)
- schtasks.exe (PID: 7524)
- schtasks.exe (PID: 1132)
- schtasks.exe (PID: 7652)
- schtasks.exe (PID: 6480)
- schtasks.exe (PID: 2892)
- schtasks.exe (PID: 656)
- schtasks.exe (PID: 5400)
- schtasks.exe (PID: 5236)
- schtasks.exe (PID: 5548)
- schtasks.exe (PID: 6992)
- schtasks.exe (PID: 1072)
- schtasks.exe (PID: 8152)
- schtasks.exe (PID: 2240)
- schtasks.exe (PID: 4212)
- schtasks.exe (PID: 8092)
- schtasks.exe (PID: 6988)
- schtasks.exe (PID: 4220)
- schtasks.exe (PID: 2840)
- schtasks.exe (PID: 2596)
- schtasks.exe (PID: 7228)
- schtasks.exe (PID: 7380)
- schtasks.exe (PID: 8016)
- schtasks.exe (PID: 6660)
- schtasks.exe (PID: 6920)
- schtasks.exe (PID: 516)
- schtasks.exe (PID: 6892)
- schtasks.exe (PID: 3132)
- schtasks.exe (PID: 1472)
- schtasks.exe (PID: 6576)
- schtasks.exe (PID: 4756)
- schtasks.exe (PID: 7964)
- schtasks.exe (PID: 7784)
- schtasks.exe (PID: 8132)
- schtasks.exe (PID: 7364)
- schtasks.exe (PID: 4528)
- schtasks.exe (PID: 6744)
- schtasks.exe (PID: 6572)
- schtasks.exe (PID: 4724)
- schtasks.exe (PID: 5744)
- schtasks.exe (PID: 8132)
- schtasks.exe (PID: 1168)
- schtasks.exe (PID: 5232)
- schtasks.exe (PID: 4996)
- schtasks.exe (PID: 9160)
- schtasks.exe (PID: 8524)
- schtasks.exe (PID: 7948)
- schtasks.exe (PID: 8364)
- schtasks.exe (PID: 7900)
- schtasks.exe (PID: 7428)
- schtasks.exe (PID: 9196)
- schtasks.exe (PID: 5736)
- schtasks.exe (PID: 6324)
- schtasks.exe (PID: 5156)
- schtasks.exe (PID: 1056)
- schtasks.exe (PID: 8784)
- schtasks.exe (PID: 8736)
- schtasks.exe (PID: 8804)
- schtasks.exe (PID: 8676)
- schtasks.exe (PID: 5596)
- schtasks.exe (PID: 8728)
- schtasks.exe (PID: 7632)
- schtasks.exe (PID: 8392)
- schtasks.exe (PID: 8328)
- schtasks.exe (PID: 5212)
- schtasks.exe (PID: 9156)
- schtasks.exe (PID: 8696)
- schtasks.exe (PID: 8176)
- schtasks.exe (PID: 6560)
- schtasks.exe (PID: 8988)
- schtasks.exe (PID: 5036)
- schtasks.exe (PID: 780)
- schtasks.exe (PID: 8248)
- schtasks.exe (PID: 2088)
- schtasks.exe (PID: 9200)
- schtasks.exe (PID: 5236)
- schtasks.exe (PID: 7568)
- schtasks.exe (PID: 4400)
- schtasks.exe (PID: 7260)
- schtasks.exe (PID: 4212)
- schtasks.exe (PID: 7652)
- schtasks.exe (PID: 2408)
- schtasks.exe (PID: 8040)
- schtasks.exe (PID: 5180)
- schtasks.exe (PID: 1852)
- schtasks.exe (PID: 2332)
- schtasks.exe (PID: 8252)
- schtasks.exe (PID: 8148)
- schtasks.exe (PID: 5608)
- schtasks.exe (PID: 6416)
- schtasks.exe (PID: 7312)
- schtasks.exe (PID: 8180)
- schtasks.exe (PID: 7796)
- schtasks.exe (PID: 4068)
- schtasks.exe (PID: 4776)
- schtasks.exe (PID: 8360)
- schtasks.exe (PID: 8428)
- schtasks.exe (PID: 6640)
- schtasks.exe (PID: 8368)
- schtasks.exe (PID: 5404)
- schtasks.exe (PID: 240)
- schtasks.exe (PID: 7744)
- schtasks.exe (PID: 2596)
- schtasks.exe (PID: 7184)
- schtasks.exe (PID: 9152)
- schtasks.exe (PID: 5512)
- schtasks.exe (PID: 3300)
- schtasks.exe (PID: 4976)
- schtasks.exe (PID: 5260)
- schtasks.exe (PID: 5504)
Starts POWERSHELL.EXE for commands execution
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
Script adds exclusion path to Windows Defender
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 7952)
- cmd.exe (PID: 8236)
- cmd.exe (PID: 8340)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 8988)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 9176)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 9092)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 1616)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 7900)
- schtasks.exe (PID: 7428)
- schtasks.exe (PID: 8364)
- powershell.exe (PID: 7556)
- csrss.exe (PID: 660)
- csrss.exe (PID: 4944)
- csrss.exe (PID: 7372)
Found IP address in command line
- powershell.exe (PID: 5072)
INFO
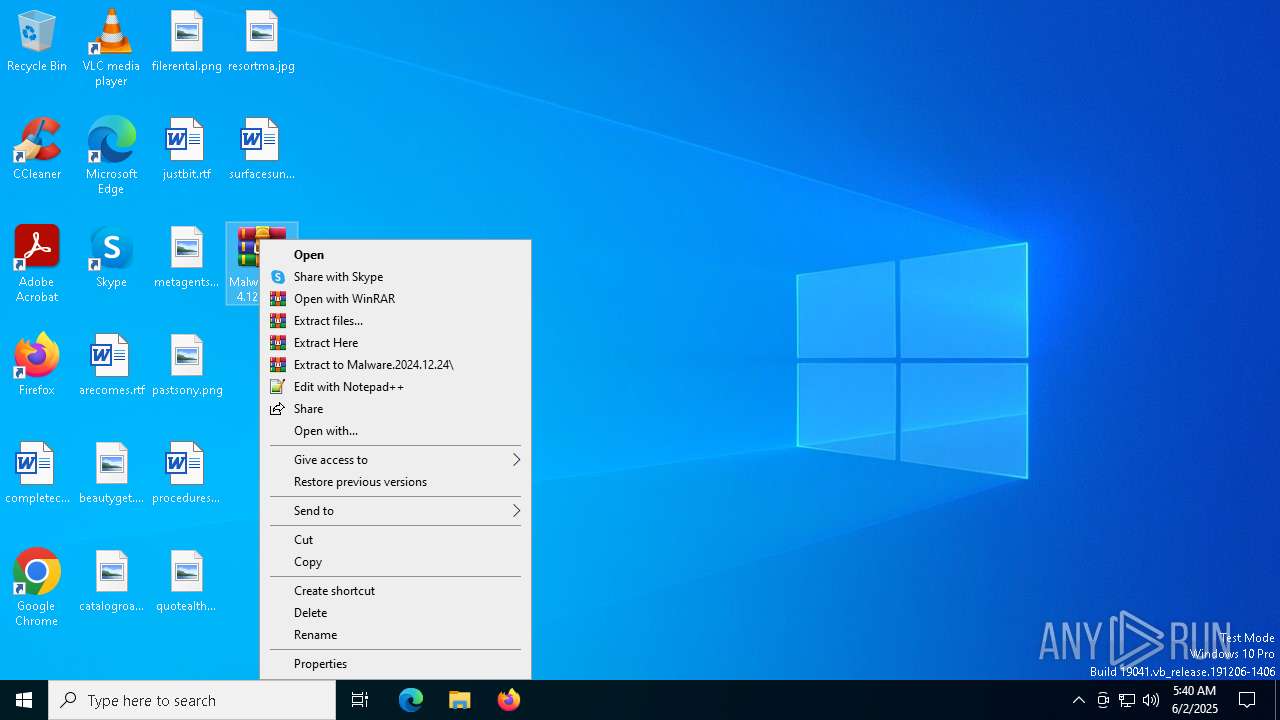
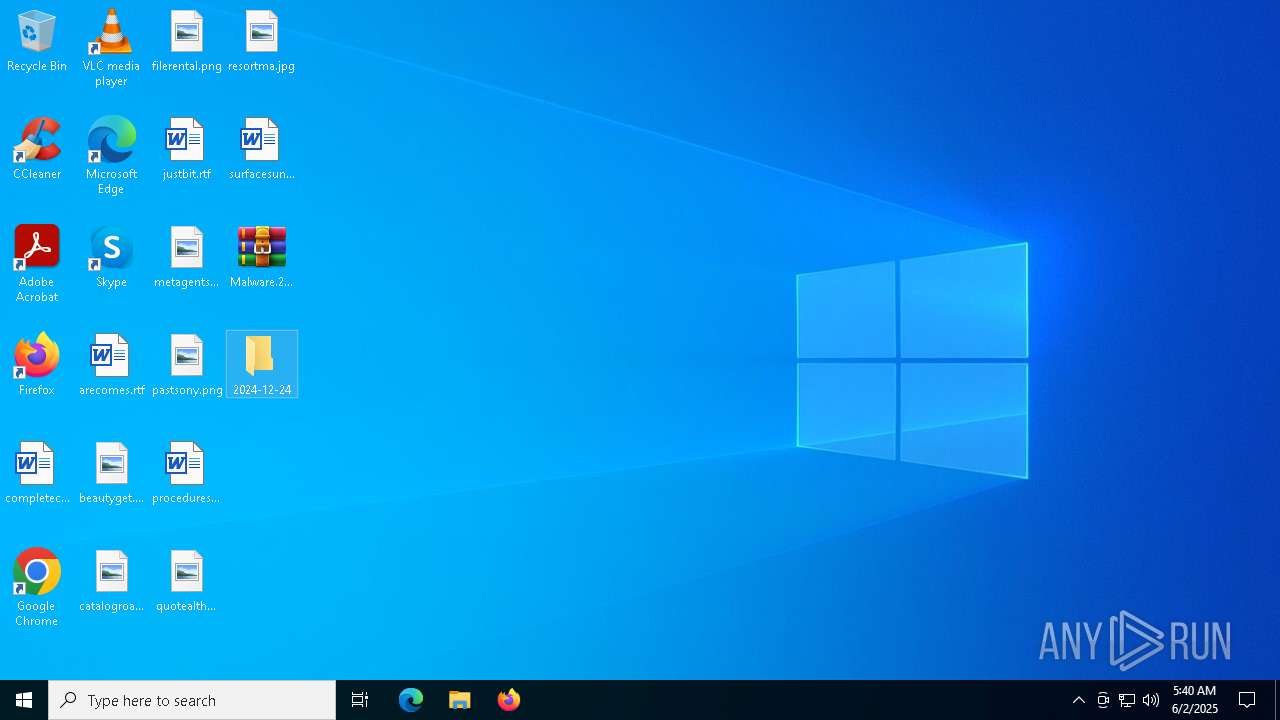
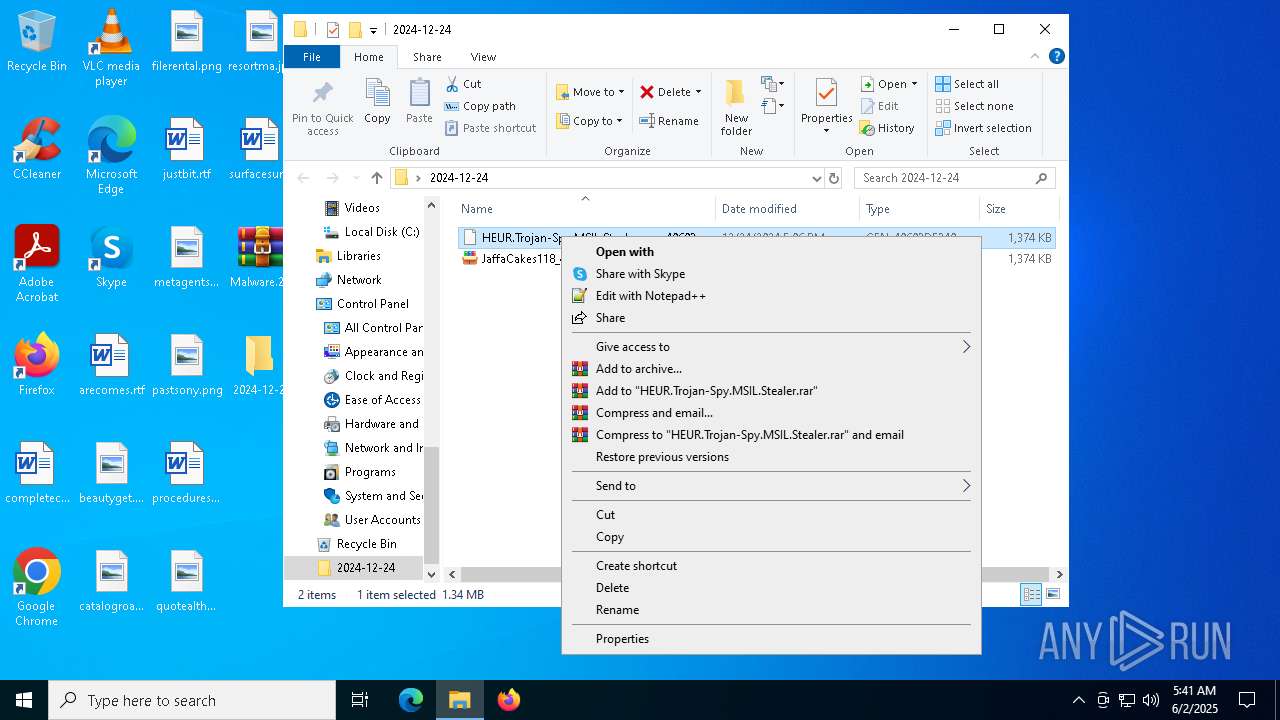
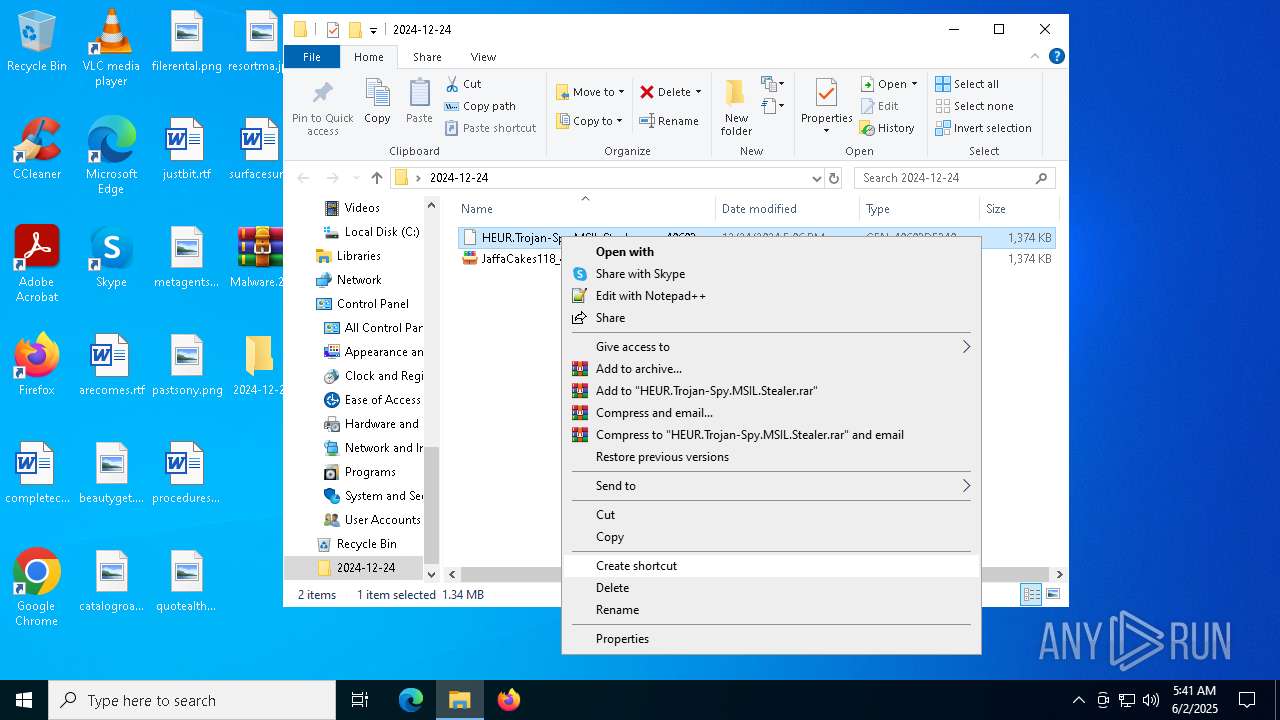
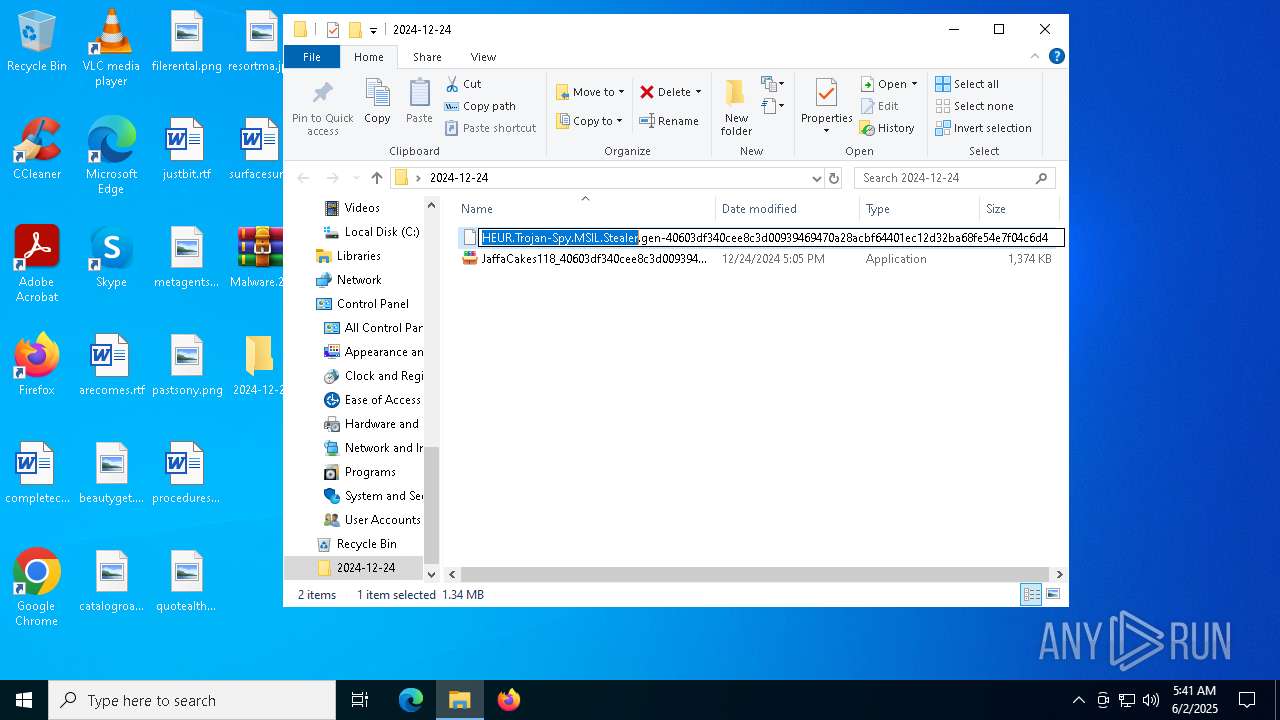
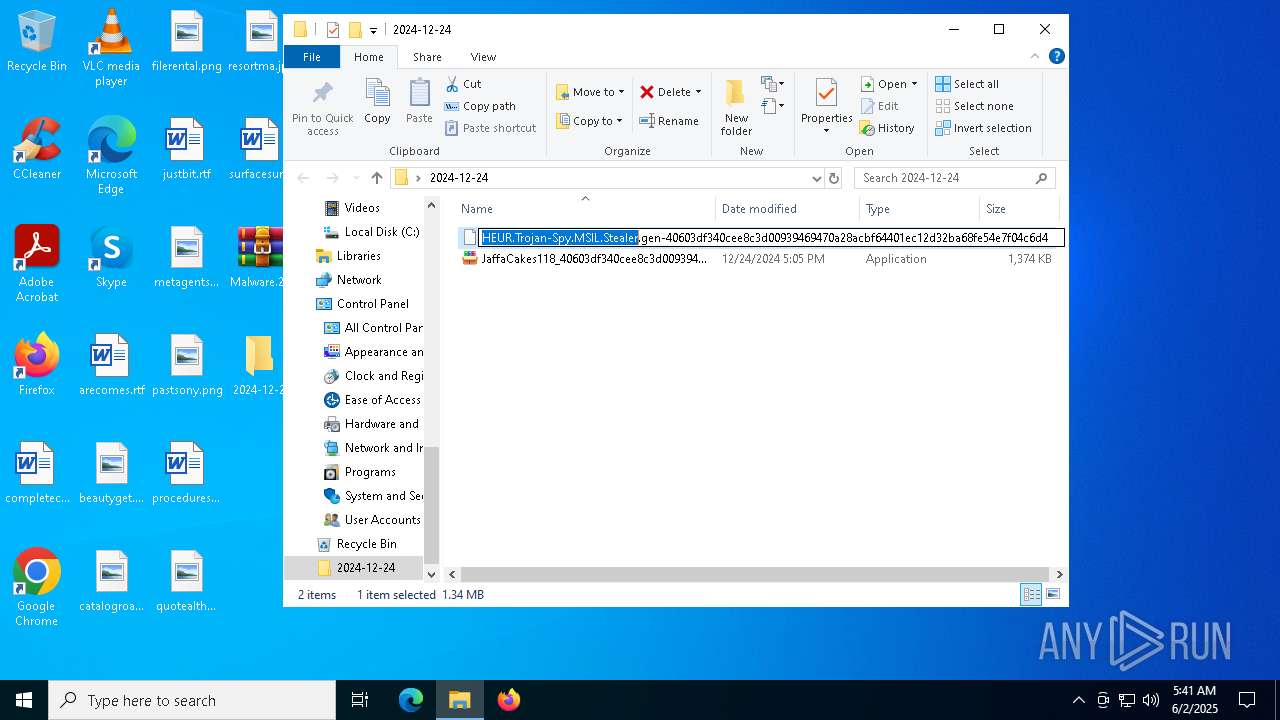
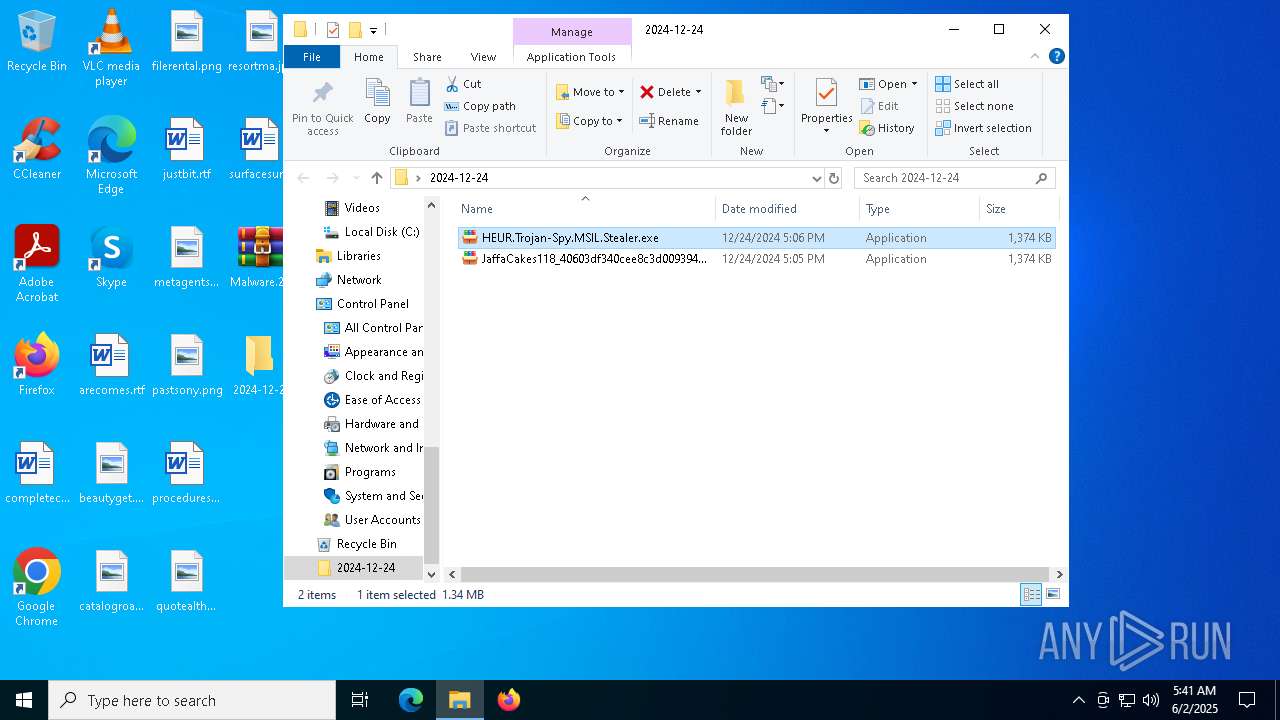
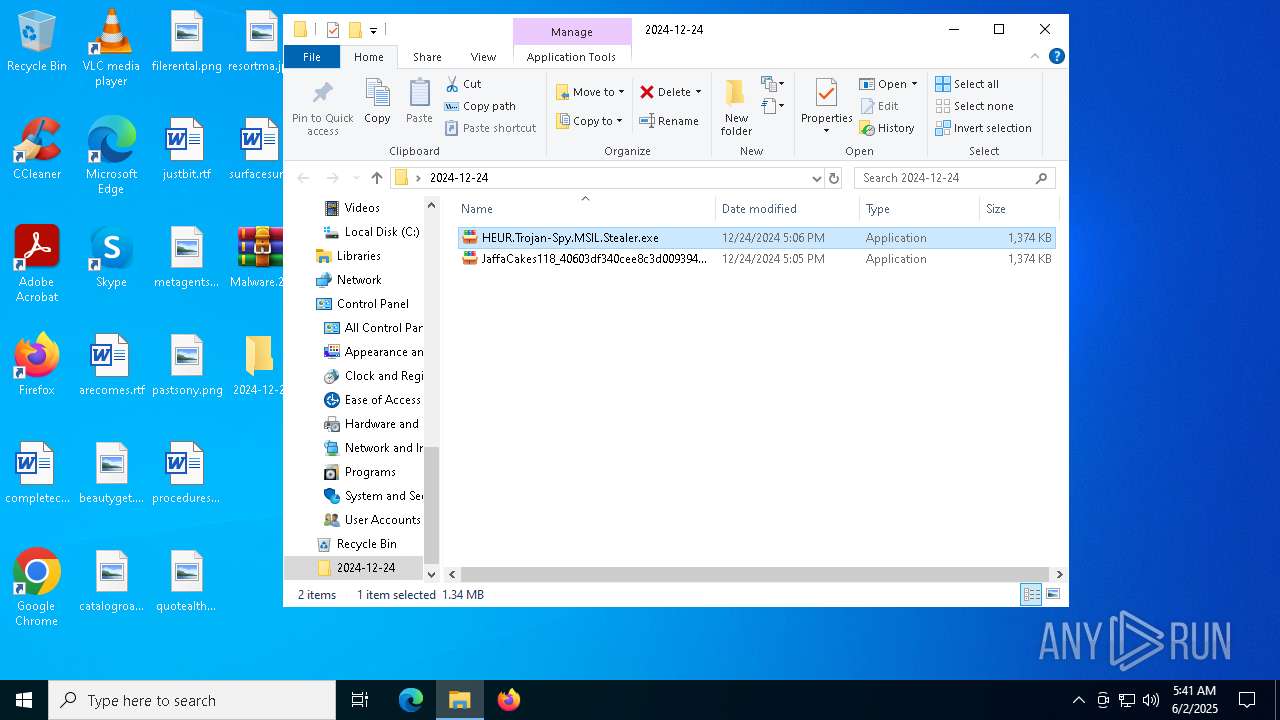
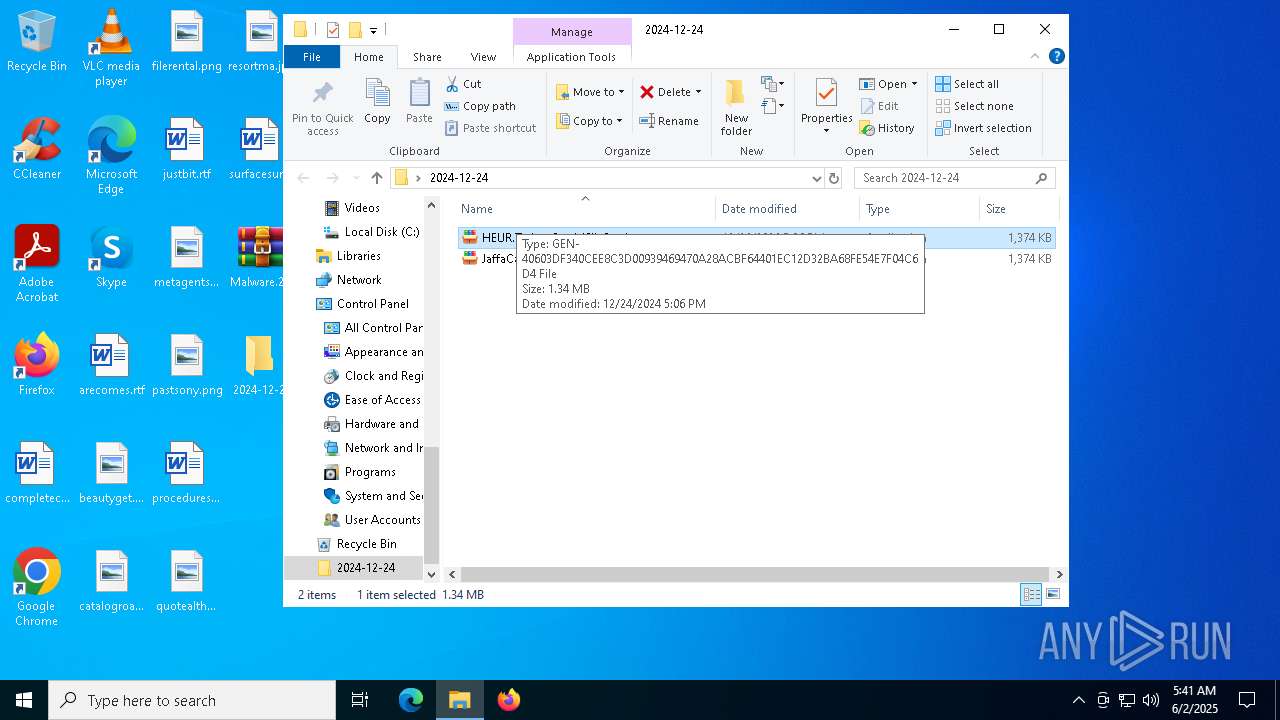
Manual execution by a user
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- WinRAR.exe (PID: 5984)
- HEUR.Trojan-Spy.MSIL.Stealer.exe (PID: 6516)
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 632)
- HEUR.Trojan-Spy.MSIL.Stealer.exe (PID: 7996)
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8020)
- HEUR.Trojan-Spy.MSIL.Stealer.exe (PID: 7264)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5984)
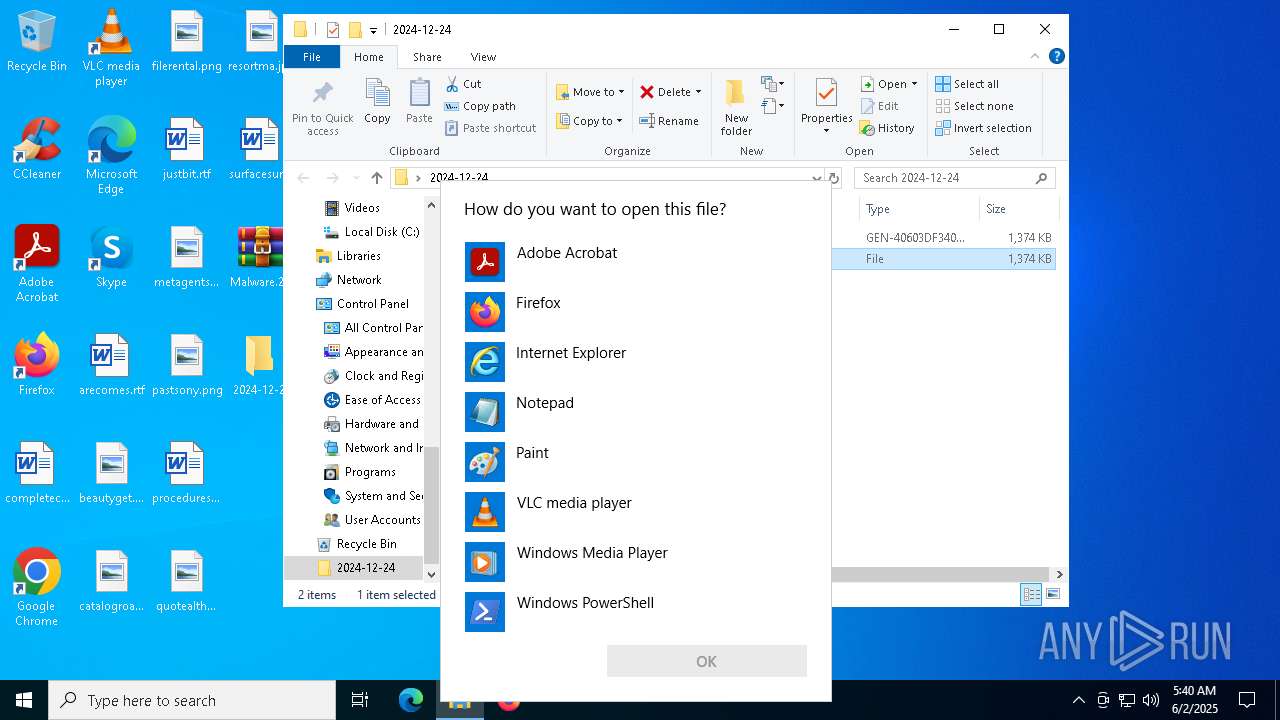
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5260)
- OpenWith.exe (PID: 7864)
Drops encrypted VBS script (Microsoft Script Encoder)
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
The sample compiled with english language support
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 7268)
- DllCommonsvc.exe (PID: 8508)
- DllCommonsvc.exe (PID: 1132)
- DllCommonsvc.exe (PID: 7612)
Reads the computer name
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Checks supported languages
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Process checks computer location settings
- JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe (PID: 8048)
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Reads Environment values
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Reads the machine GUID from the registry
- DllCommonsvc.exe (PID: 4020)
- DllCommonsvc.exe (PID: 7268)
Creates files in the program directory
- DllCommonsvc.exe (PID: 7268)
Create files in a temporary directory
- DllCommonsvc.exe (PID: 7268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
474
Monitored processes
340
Malicious processes
22
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | schtasks.exe /create /tn "dwm" /sc ONLOGON /tr "'C:\found.000\dir_00000002.chk\dwm.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | schtasks.exe /create /tn "WmiPrvSE" /sc ONLOGON /tr "'C:\Recovery\Logs\WmiPrvSE.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Users\admin\Desktop\2024-12-24\JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe" | C:\Users\admin\Desktop\2024-12-24\JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 10 Modules
| |||||||||||||||
| 644 | w32tm /stripchart /computer:localhost /period:5 /dataonly /samples:2 | C:\Windows\System32\w32tm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Time Service Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 656 | schtasks.exe /create /tn "Memory CompressionM" /sc MINUTE /mo 12 /tr "'C:\providercommon\Memory Compression.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Users\Public\Desktop\csrss.exe" | C:\Users\Public\Desktop\csrss.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.1.1o Modules
| |||||||||||||||
| 704 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\providercommon\DllCommonsvc.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | DllCommonsvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | schtasks.exe /create /tn "winlogonw" /sc MINUTE /mo 13 /tr "'C:\Windows\AppReadiness\winlogon.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
305 631
Read events
305 552
Write events
79
Delete events
0
Modification events
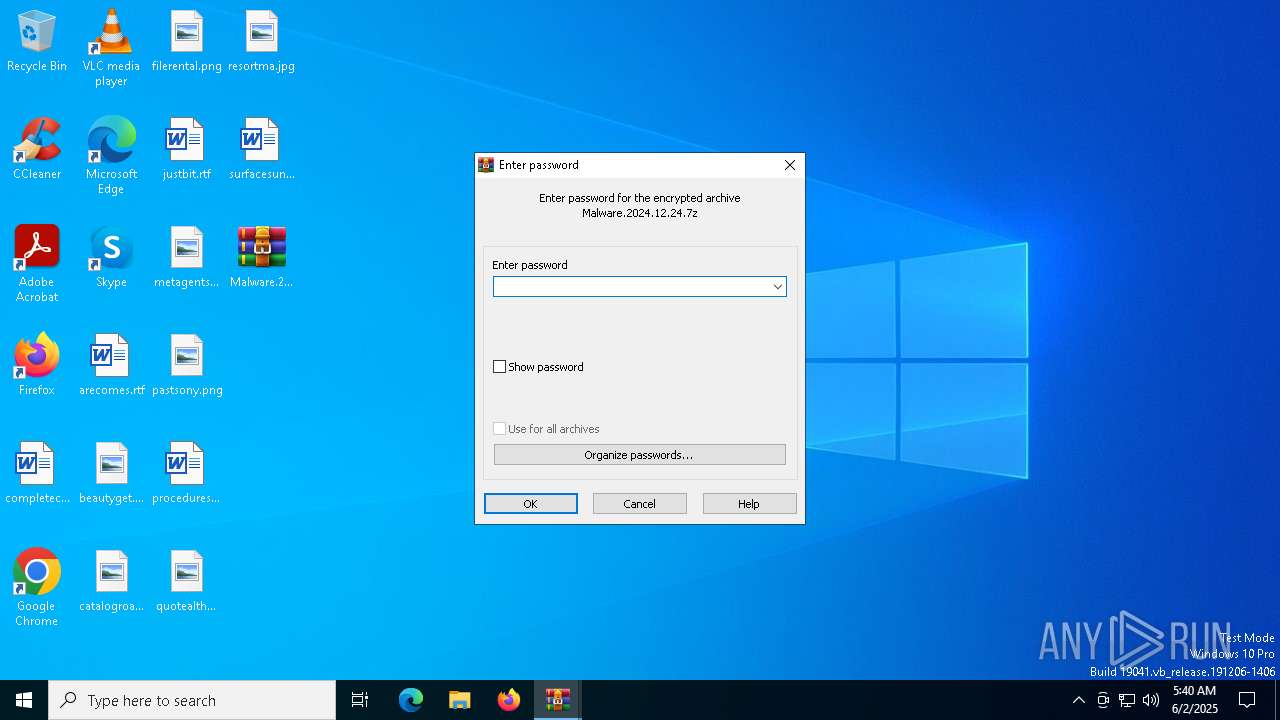
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Malware.2024.12.24.7z | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
42
Suspicious files
2
Text files
171
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7268 | DllCommonsvc.exe | C:\Windows\Installer\{833D52CC-AEFF-3DF3-AE28-372C5BC15088}\c5b4cb5e9653cc | text | |
MD5:9660F6BD524EC243822CC89850F4EE35 | SHA256:E72E860F434D97FFBF9090C3D31A3E72DEC4C93BD90E860D1E76AD98CB29A699 | |||
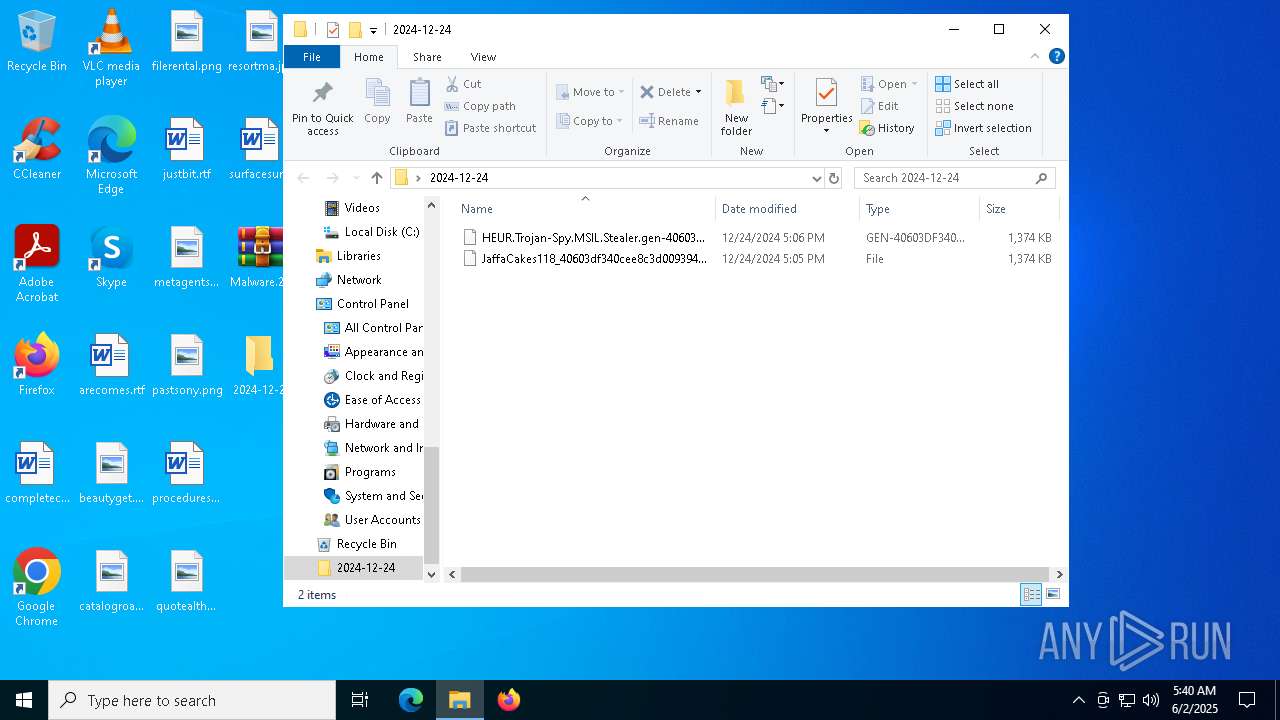
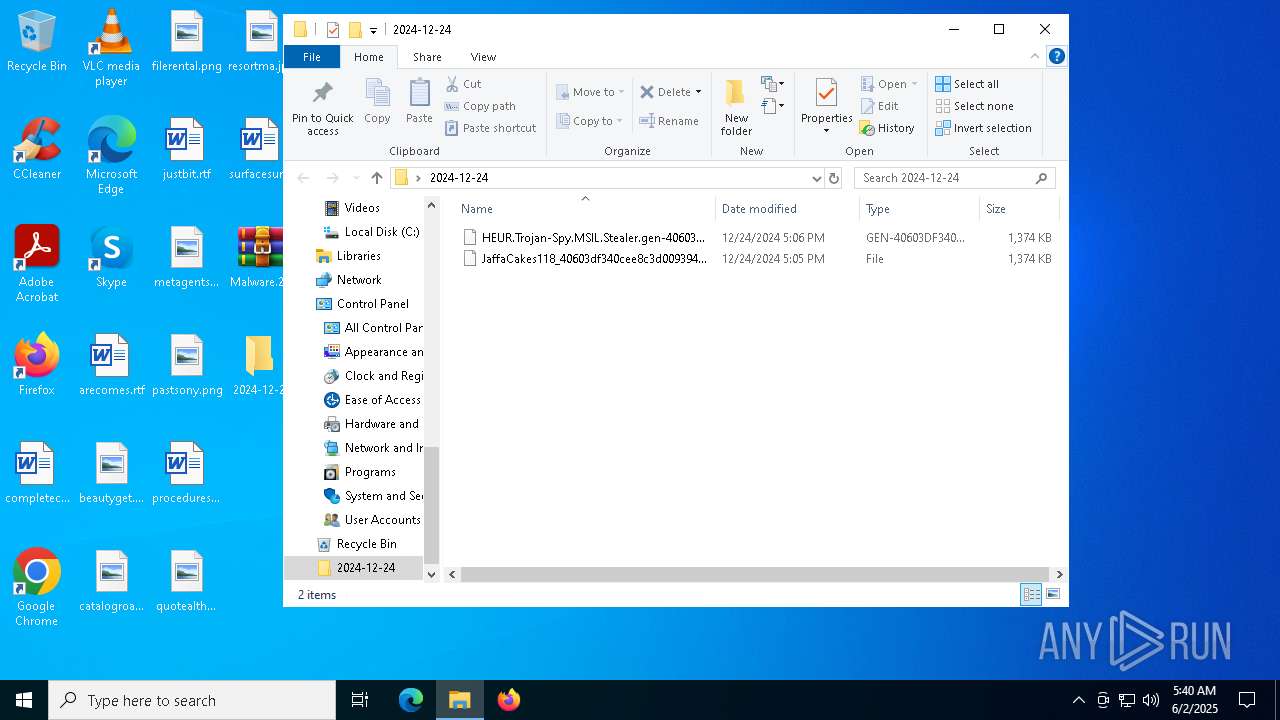
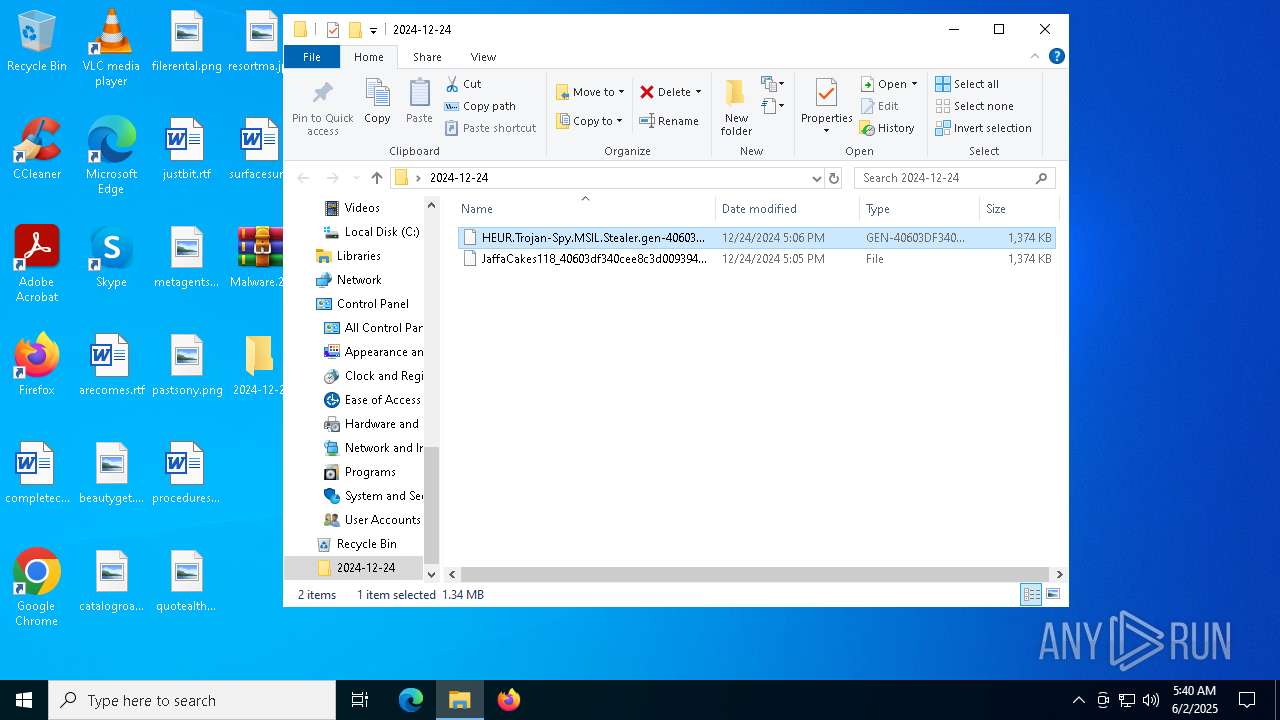
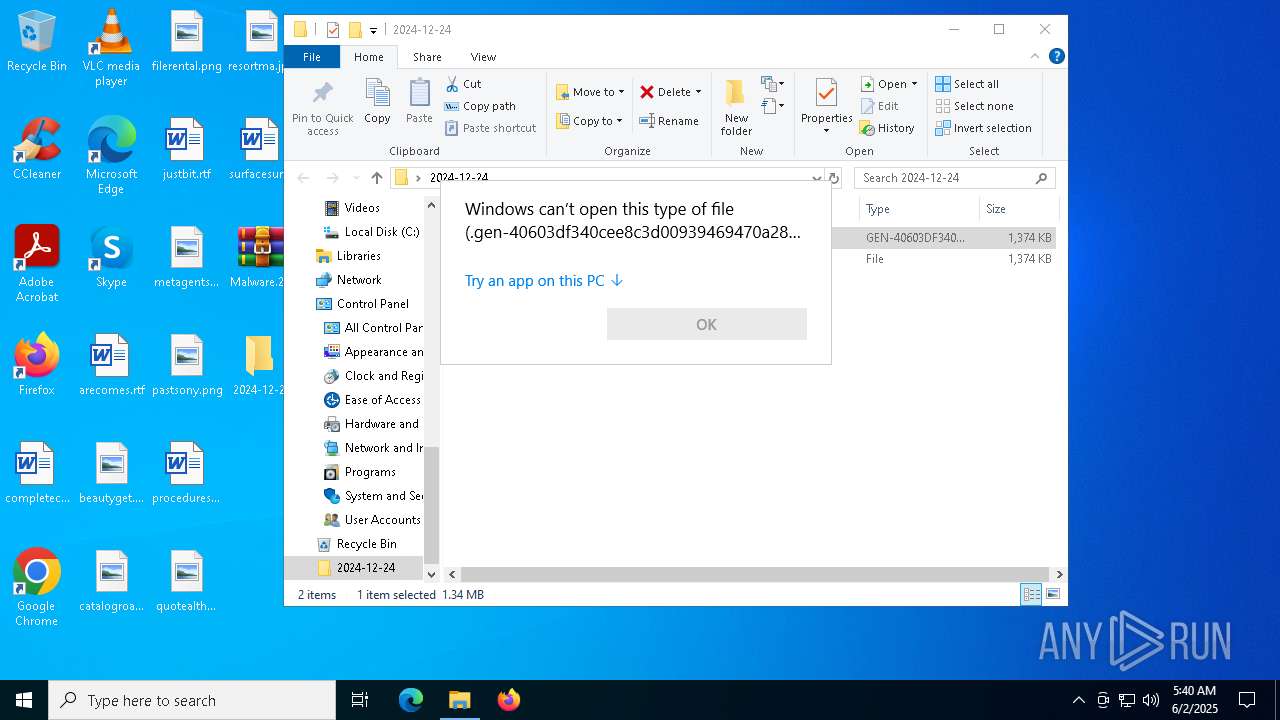
| 5984 | WinRAR.exe | C:\Users\admin\Desktop\2024-12-24\HEUR.Trojan-Spy.MSIL.Stealer.gen-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4 | executable | |
MD5:20043020E5B82CE7E3D69C407A85E50C | SHA256:40603DF340CEE8C3D00939469470A28ACBF64401EC12D32BA68FE54E7F04C6D4 | |||
| 8048 | JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe | C:\providercommon\DllCommonsvc.exe | executable | |
MD5:BD31E94B4143C4CE49C17D3AF46BCAD0 | SHA256:B5199D3EB28E7DE8EC4A5DE66CB339A03D90B297E2292473BADAAB98ADE15C63 | |||
| 7268 | DllCommonsvc.exe | C:\Windows\Installer\{833D52CC-AEFF-3DF3-AE28-372C5BC15088}\services.exe | executable | |
MD5:BD31E94B4143C4CE49C17D3AF46BCAD0 | SHA256:B5199D3EB28E7DE8EC4A5DE66CB339A03D90B297E2292473BADAAB98ADE15C63 | |||
| 8048 | JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe | C:\providercommon\1zu9dW.bat | text | |
MD5:6783C3EE07C7D151CEAC57F1F9C8BED7 | SHA256:8AB782F0F327A2021530E7230D3AEE8ABBECB7EED59482A3A46E78B9E3862322 | |||
| 8048 | JaffaCakes118_40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4-40603df340cee8c3d00939469470a28acbf64401ec12d32ba68fe54e7f04c6d4.exe | C:\providercommon\yTUdeXjbLOhnrN32dgrxVg.vbe | binary | |
MD5:8088241160261560A02C84025D107592 | SHA256:2072CC9A4A3B84D4C5178AB41C5588EEA7D0103E3928E34D64F17BF97F3D1CC1 | |||
| 7268 | DllCommonsvc.exe | C:\Windows\ImmersiveControlPanel\SystemSettings\View\sppsvc.exe | executable | |
MD5:BD31E94B4143C4CE49C17D3AF46BCAD0 | SHA256:B5199D3EB28E7DE8EC4A5DE66CB339A03D90B297E2292473BADAAB98ADE15C63 | |||
| 7268 | DllCommonsvc.exe | C:\found.000\dir_00000002.chk\9e60a5f7a3bd80 | text | |
MD5:98BC68F1E886206900DE317F44E0E2CD | SHA256:4B71BC9B2DA4305090BD5DF52FB88B30D81CE9777464A84F36FA2FB43CD531B0 | |||
| 7268 | DllCommonsvc.exe | C:\Windows\Microsoft.NET\Framework\v1.0.3705\spoolsv.exe | executable | |
MD5:BD31E94B4143C4CE49C17D3AF46BCAD0 | SHA256:B5199D3EB28E7DE8EC4A5DE66CB339A03D90B297E2292473BADAAB98ADE15C63 | |||
| 7268 | DllCommonsvc.exe | C:\providercommon\1a5d5b8dcee3d8 | text | |
MD5:BB7880495CB2EE6516E7D99B78C09DA1 | SHA256:DD458F745A3B3603248D3B4779B184A6B2CE9B183C8275991E798028CD12559B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
39
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1812 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6208 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3760 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3760 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |