| File name: | script.exe |
| Full analysis: | https://app.any.run/tasks/6817994b-cbbc-44ab-a486-3445fe873f60 |
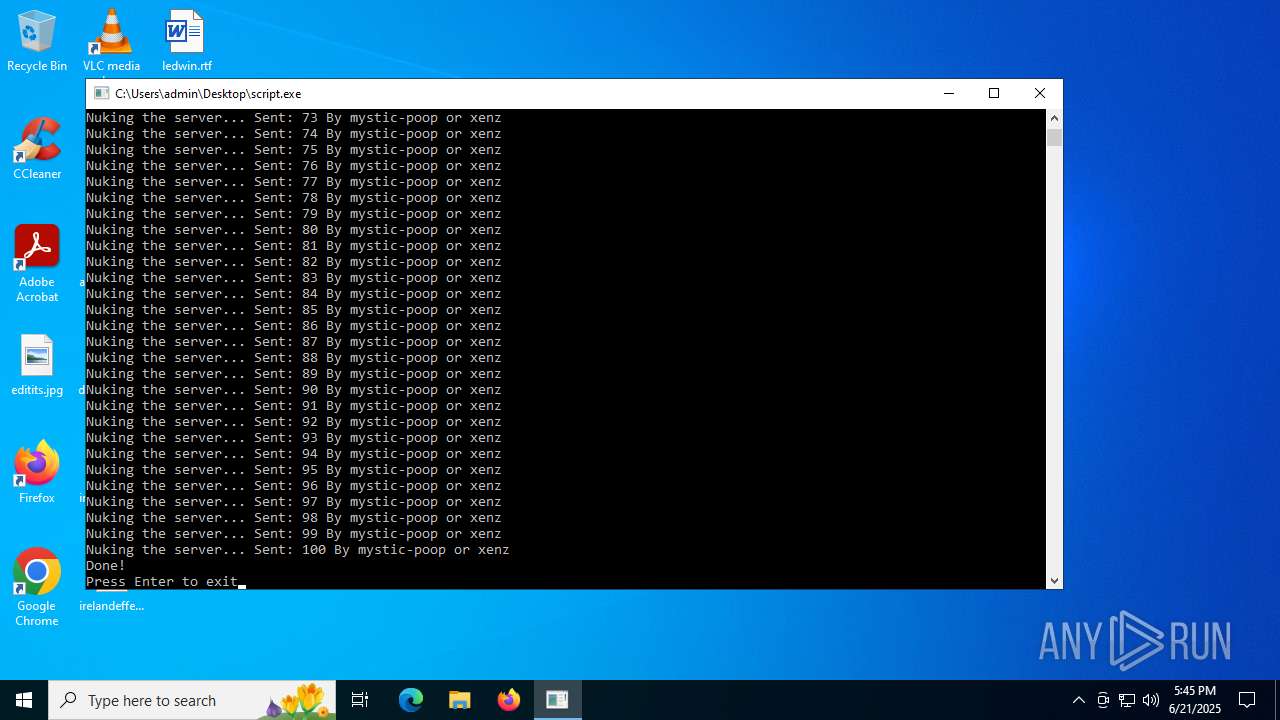
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 17:45:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | D56E877A0CC156C73FFF5426356CD63B |
| SHA1: | BC94D715D610076A54EF3DF815641FED66C6A741 |
| SHA256: | 19AA4EFE80BC11EE17138F5EA3DFEEE05C82096A91210A2C89612109802C7F5C |
| SSDEEP: | 98304:zD/l71vqeLnc1ZaDPHUFK/uXbQx2UfuwiX8PHFC9uDytdK6CXFtrb+heFSf7UJDa:VkKVtKTyMNUfi9W |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- script.exe (PID: 5348)
Process drops legitimate windows executable
- script.exe (PID: 5348)
Process drops python dynamic module
- script.exe (PID: 5348)
Executable content was dropped or overwritten
- script.exe (PID: 5348)
Application launched itself
- script.exe (PID: 5348)
Loads Python modules
- script.exe (PID: 4040)
Starts CMD.EXE for commands execution
- script.exe (PID: 4040)
INFO
Checks supported languages
- script.exe (PID: 5348)
- script.exe (PID: 4040)
Reads the computer name
- script.exe (PID: 5348)
- script.exe (PID: 4040)
The sample compiled with english language support
- script.exe (PID: 5348)
Create files in a temporary directory
- script.exe (PID: 5348)
PyInstaller has been detected (YARA)
- script.exe (PID: 5348)
- script.exe (PID: 4040)
Checks proxy server information
- slui.exe (PID: 3780)
Reads the software policy settings
- slui.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 17:43:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 179712 |
| InitializedDataSize: | 95232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc650 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
140
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | "C:\Users\admin\Desktop\script.exe" | C:\Users\admin\Desktop\script.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3780 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\Desktop\script.exe" | C:\Users\admin\Desktop\script.exe | script.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5008 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | script.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5348 | "C:\Users\admin\Desktop\script.exe" | C:\Users\admin\Desktop\script.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | script.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 809
Read events
3 809
Write events
0
Delete events
0
Modification events
Executable files
50
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\_bz2.pyd | executable | |
MD5:057325E89B4DB46E6B18A52D1A691CAA | SHA256:5BA872CAA7FCEE0F4FB81C6E0201CEED9BD92A3624F16828DD316144D292A869 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\_decimal.pyd | executable | |
MD5:F465C15E7BACEAC920DC58A5FB922C1C | SHA256:F4A486A0CA6A53659159A404614C7E7EDCCB6BFBCDEB844F6CEE544436A826CB | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\_hashlib.pyd | executable | |
MD5:CF4120BAD9A7F77993DD7A95568D83D7 | SHA256:14765E83996FE6D50AEDC11BB41D7C427A3E846A6A6293A4A46F7EA7E3F14148 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:C148A26D3D9D39777DABE28DC08CEE60 | SHA256:085968D938EA924827C4740697713674850218A8FE91DD9982E93B0EFFACC820 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:EE3F0D24E7E32E661AC407C60B84B7DB | SHA256:C86EBC9F48E2DB659E80D9C7AD5F29E6B6C850EEA58813C041BAEFF496AE4F18 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\_socket.pyd | executable | |
MD5:69C4A9A654CF6D1684B73A431949B333 | SHA256:8DAEFAFF53E6956F5AEA5279A7C71F17D8C63E2B0D54031C3B9E82FCB0FB84DB | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:E933CDD91FD5725873F57532F262F815 | SHA256:120C3AFED9CE2A981C61208757FCA0665F43926751EC8D0D13E10EF1096A0D48 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:F90E3B45C7942E3E30ECF1505253B289 | SHA256:7E45A1B997331F4D038F847F205904D6EC703DF7A8C5C660435697E318CED8FC | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:B59D773B0848785A76BABA82D3F775FA | SHA256:0DC1F695BEFDDB8EE52A308801410F2F1D115FC70668131075C2DBCFA0B6F9A0 | |||
| 5348 | script.exe | C:\Users\admin\AppData\Local\Temp\_MEI53482\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:B71C18F8966CEAD654800FF402C6520F | SHA256:A94B80A5111AABEFB1309609ABDD300BB626D861CD8E0938B9735AB711A43C22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
43
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6672 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6672 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.20:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.160.20:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 200 | 40.126.32.74:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6672 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6672 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
tip.neiki.dev |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |