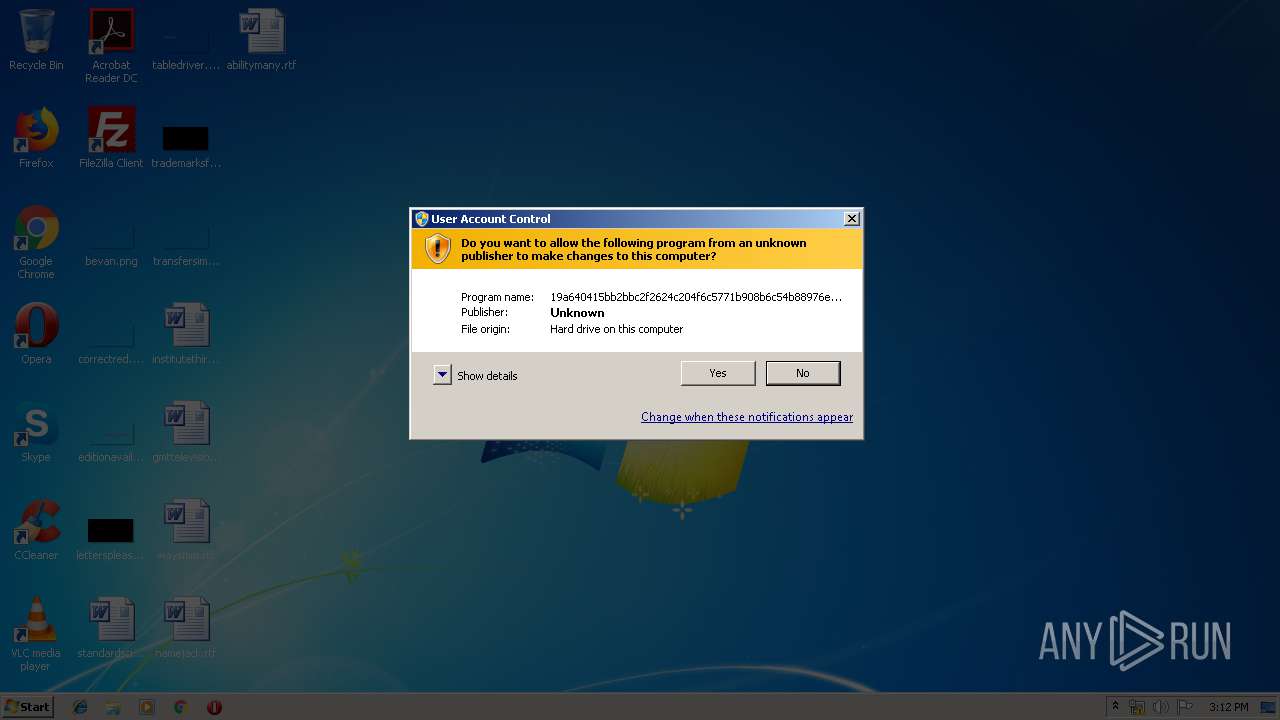
| File name: | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin |
| Full analysis: | https://app.any.run/tasks/3664e175-08c6-4007-a3e9-ed6975a65932 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 14:12:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FD946BA0CA811F8F5CDDBA5C4634FD64 |
| SHA1: | 02536E5089857FD7421A50ADB07FE871593D5B9F |
| SHA256: | 19A640415BB2BBC2F2624C204F6C5771B908B6C54B88976EB0DAA76A29AF255C |
| SSDEEP: | 3072:Tv/FR9m6kfHpVC1pY8iblkCIax6CdAje+QlLC+Q/eJRhz8Jmu+X:j/f9m6g42xqQVSD |
MALICIOUS
Writes to a start menu file
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Dropped file may contain instructions of ransomware
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Changes the autorun value in the registry
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Renames files like Ransomware
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Actions looks like stealing of personal data
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Modifies files in Chrome extension folder
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
SUSPICIOUS
Executable content was dropped or overwritten
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Creates files in the user directory
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Starts MSHTA.EXE for opening HTA or HTMLS files
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
Creates files in the program directory
- 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe (PID: 3172)
INFO
Writes to a desktop.ini file (may be used to cloak folders)
- mshta.exe (PID: 2420)
Reads internet explorer settings
- mshta.exe (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:16 08:01:06+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 98816 |
| InitializedDataSize: | 635904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x148c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40444) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (5685) |
| CharacterSet: | Unknown (684B0) |
| FileVersion: | 1.0.0.11 |
| InternalName: | sfhdtyjdtsc.ixe |
| LegalCopyright: | Copyright (C) 2019, mfuyliogui |
| ProductVersion: | 1.0.0.11 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Feb-2018 07:01:06 |
| FileVersion: | 1.0.0.11 |
| InternalName: | sfhdtyjdtsc.ixe |
| LegalCopyright: | Copyright (C) 2019, mfuyliogui |
| ProductVersion: | 1.0.0.11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Feb-2018 07:01:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000180C0 | 0x00018200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.82323 |
.rdata | 0x0001A000 | 0x00001C80 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.40863 |
.data | 0x0001C000 | 0x0009191C | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.5696 |
.rsrc | 0x000AE000 | 0x00007340 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25484 |
.reloc | 0x000B6000 | 0x00001422 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.27538 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32464 | 496 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 5.31453 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.95818 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.06004 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.21977 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.20897 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.10616 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.23617 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
12 | 3.28109 | 1684 | UNKNOWN | UNKNOWN | RT_STRING |
120 | 2.85812 | 118 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2420 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\info.hta" | C:\Windows\System32\mshta.exe | — | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3172 | "C:\Users\admin\AppData\Local\Temp\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe" | C:\Users\admin\AppData\Local\Temp\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
396
Read events
382
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3172) 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3172) 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3172) 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin |
Value: C:\Users\admin\AppData\Local\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | |||
| (PID) Process: | (3172) 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin |
Value: C:\Users\admin\AppData\Local\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\CpMRU |
| Operation: | write | Name: | Enable |
Value: 1 | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\CpMRU |
| Operation: | write | Name: | Size |
Value: 10 | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\CpMRU |
| Operation: | write | Name: | InitHits |
Value: 100 | |||
| (PID) Process: | (2420) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\CpMRU |
| Operation: | write | Name: | Factor |
Value: 20 | |||
Executable files
2
Suspicious files
1 873
Text files
13
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | executable | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Liesmich.htm.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\snapshot_blob.bin.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\natives_blob.bin.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Llegiu-me.htm.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leggimi.htm.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\COPYING.LGPLv2.1.txt.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\users\admin\appdata\roaming\microsoft\windows\start menu\programs\startup\19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | executable | |
MD5:— | SHA256:— | |||
| 3172 | 19a640415bb2bbc2f2624c204f6c5771b908b6c54b88976eb0daa76a29af255c.bin.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LueMinut.htm.id[C4BA3647-1130].[fileb@protonmail.com].mamba | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report