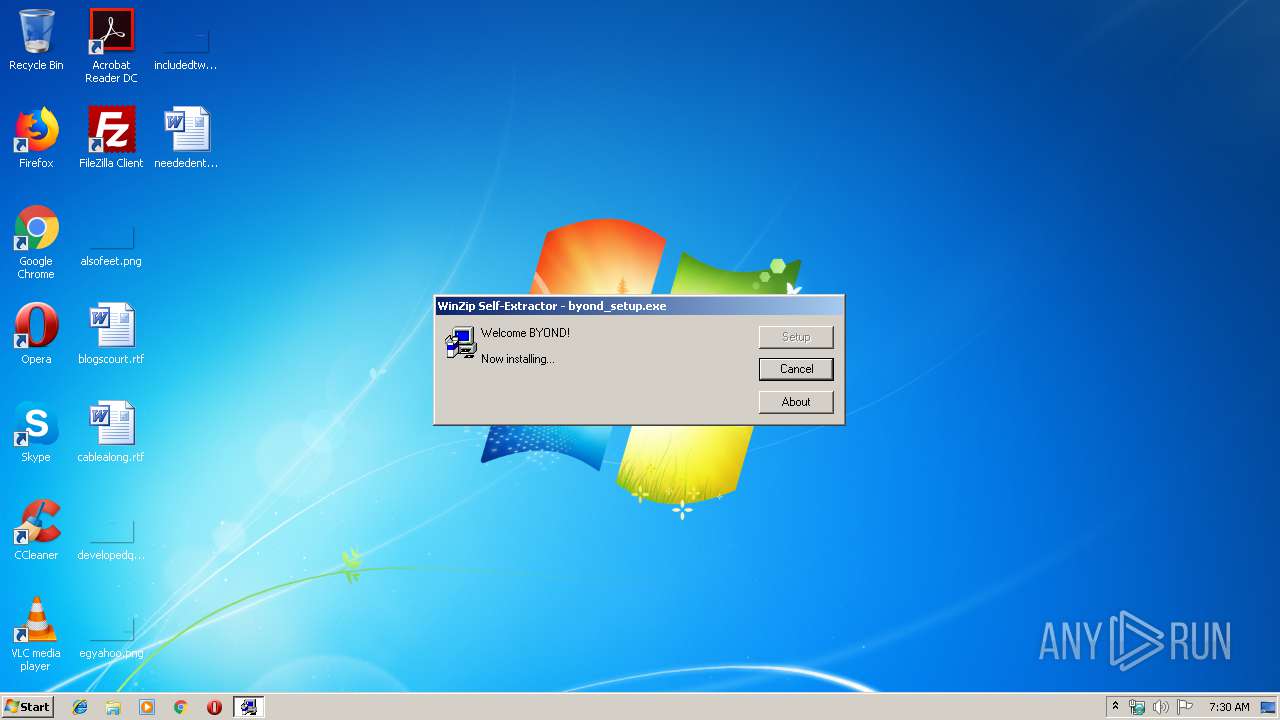
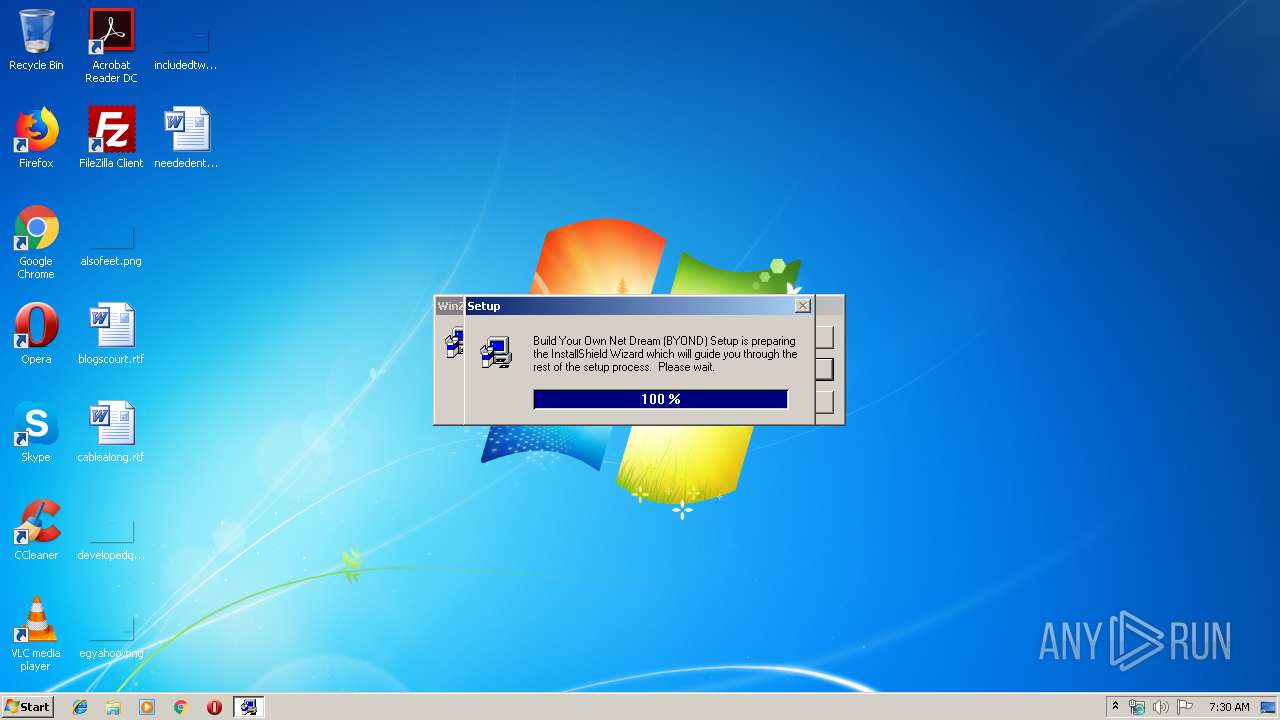
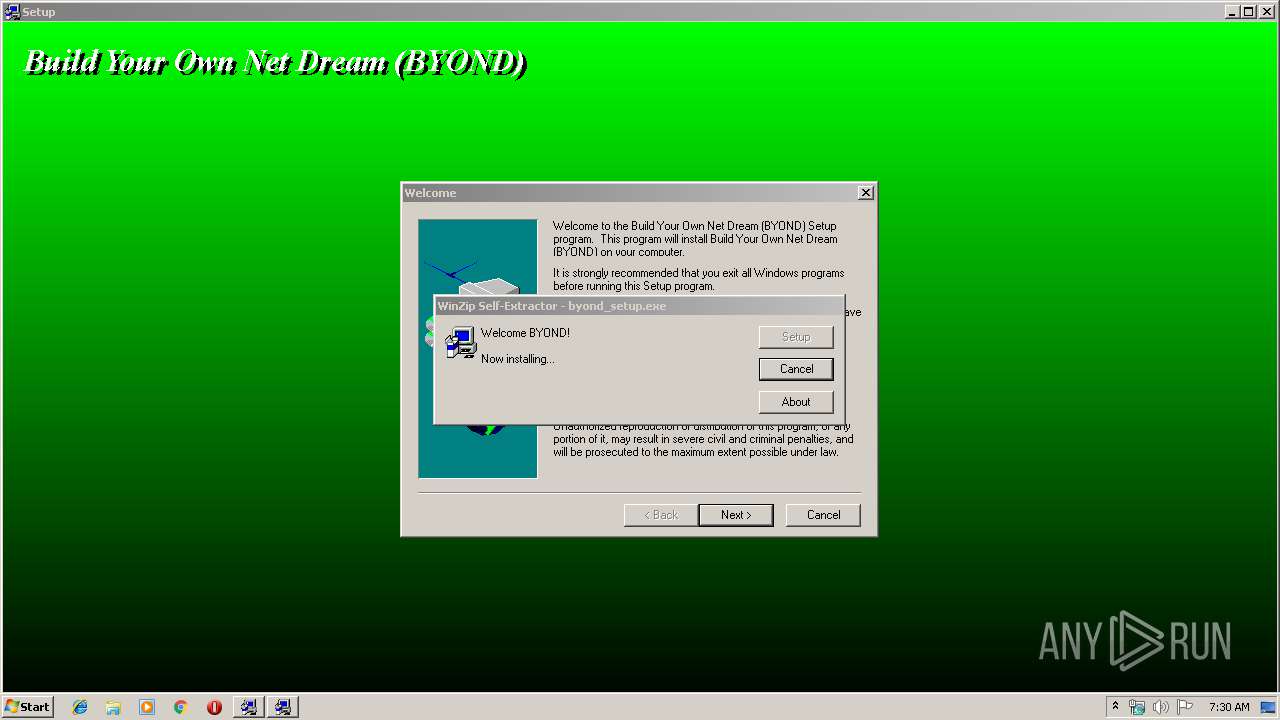
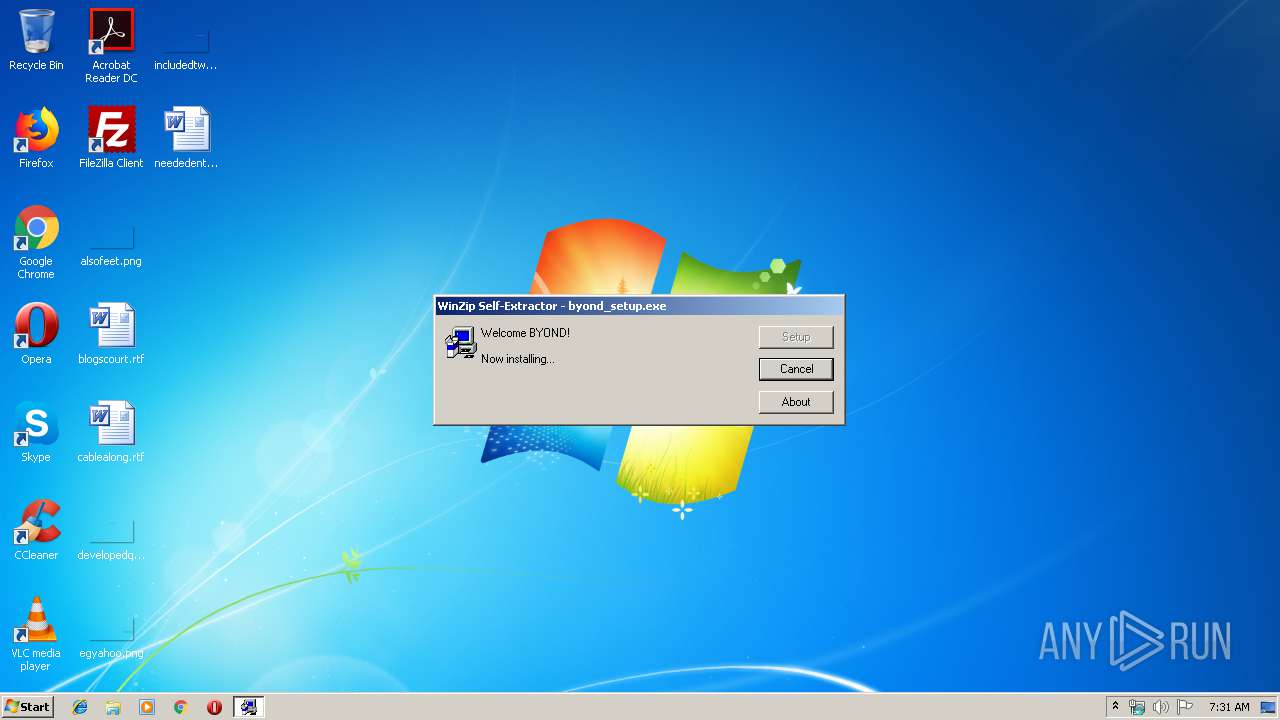
| File name: | byond_setup.exe |
| Full analysis: | https://app.any.run/tasks/395d5e15-1f91-46fe-b280-f6cb1e32a5d6 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2020, 07:29:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5DB8C4FEFFB64A26FDB871EBDEAC7CE3 |
| SHA1: | BB190936AEA9607AED79DB3A5B41C8939C9CE9A7 |
| SHA256: | 19A2574B4B7BE25BFEE42ABF19B8276DC9E7486C2E2F82B07A4DB37BE7D06372 |
| SSDEEP: | 49152:RuGamfQ7od4F/F0qPIleZtnhGjSZeoJHO9kpeG2FXa5xRYis:RuGjQl06IlaASZeo1OCpFsa/RYis |
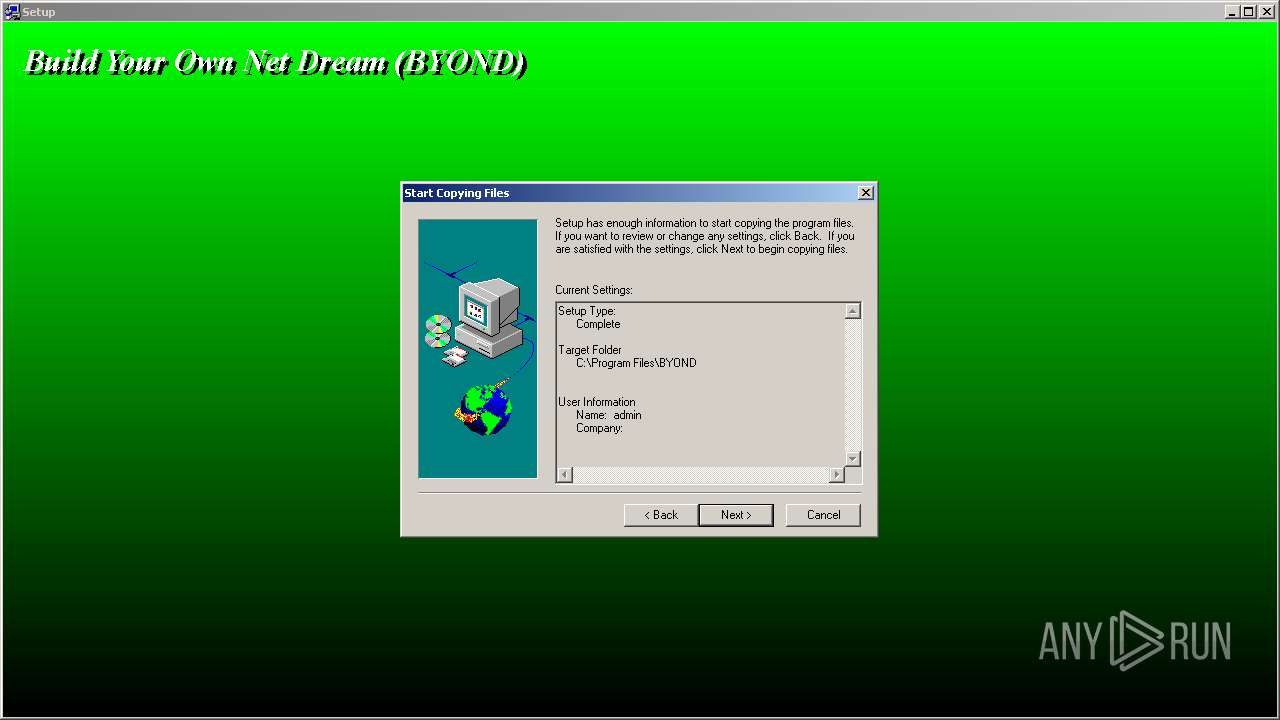
MALICIOUS
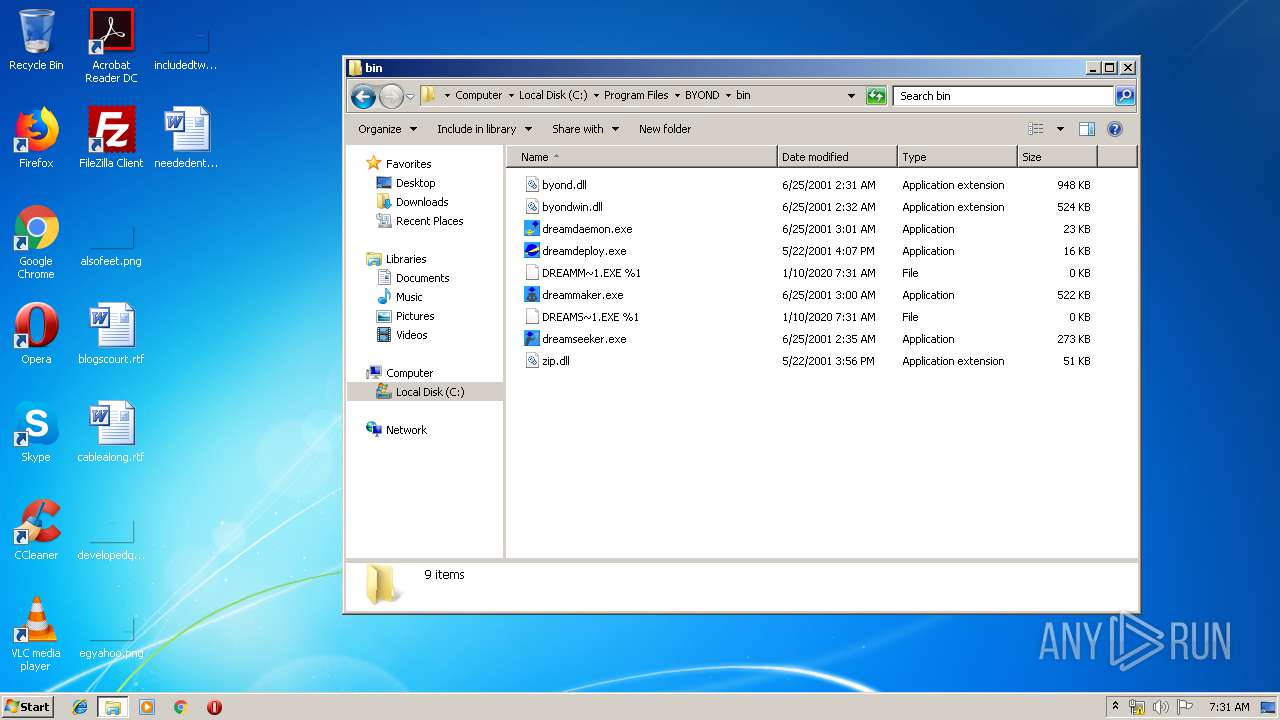
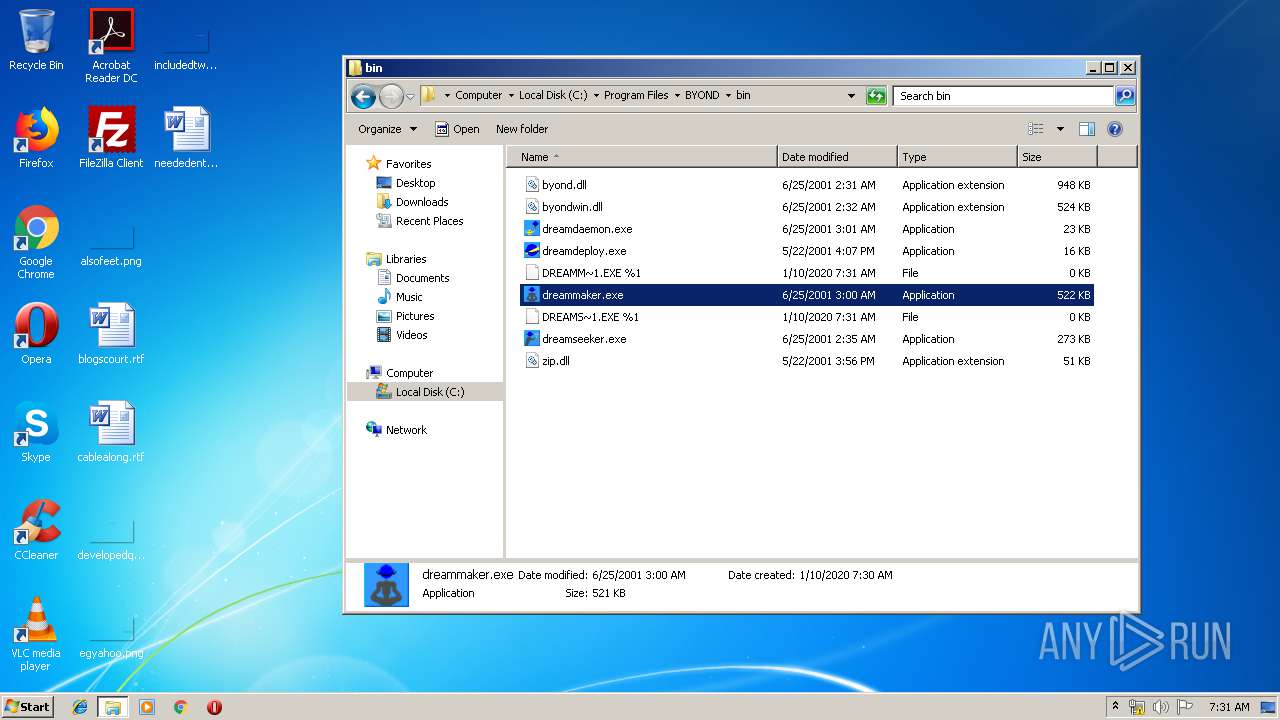
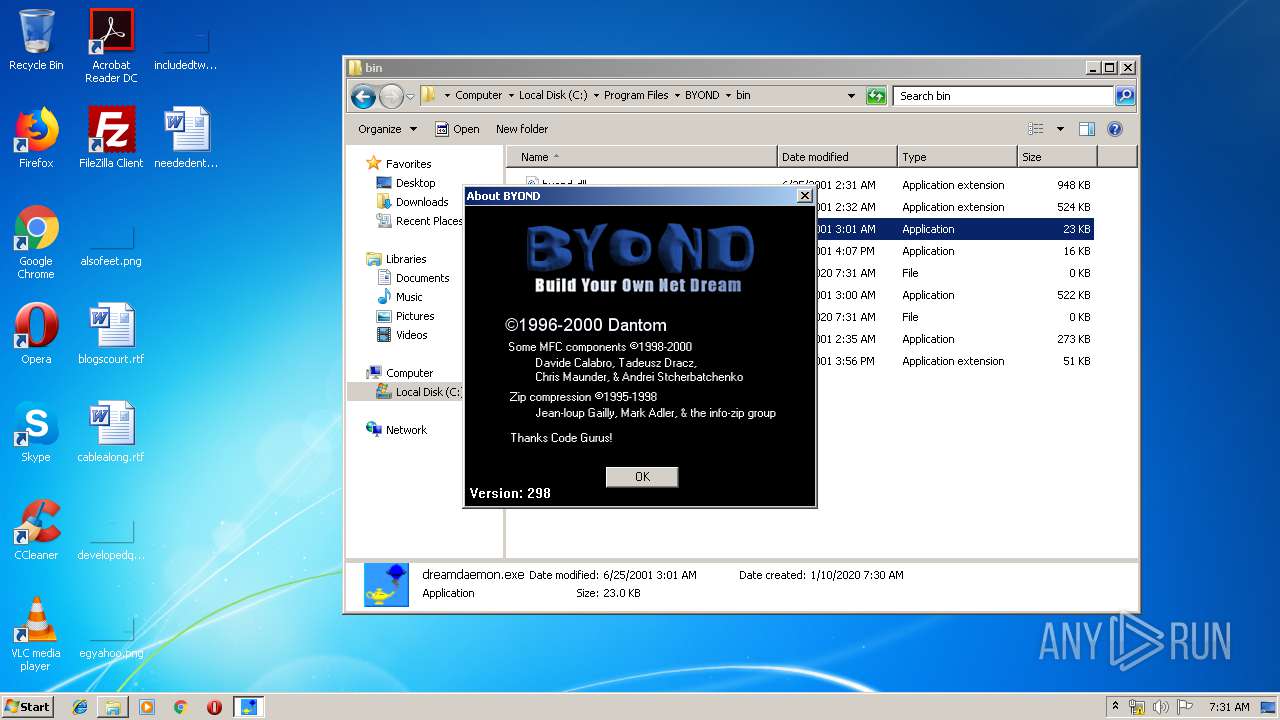
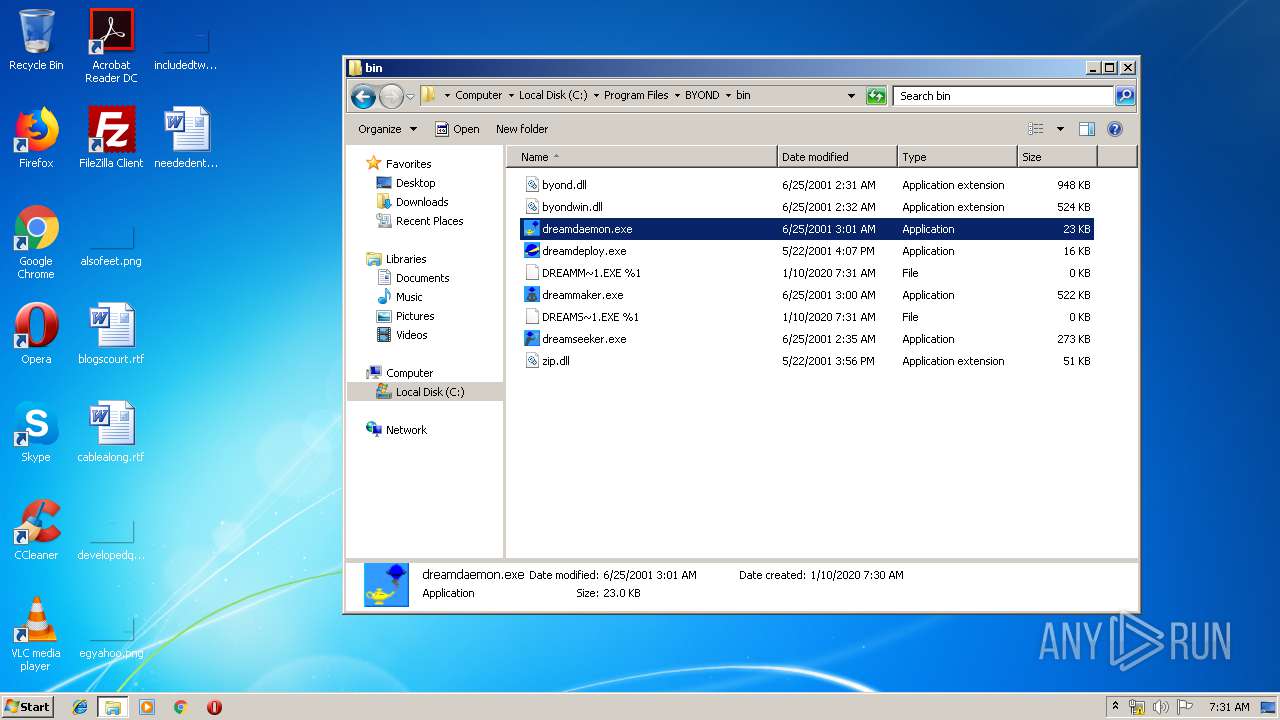
Application was dropped or rewritten from another process
- _INS0432._MP (PID: 2400)
- dreamseeker.exe (PID: 1468)
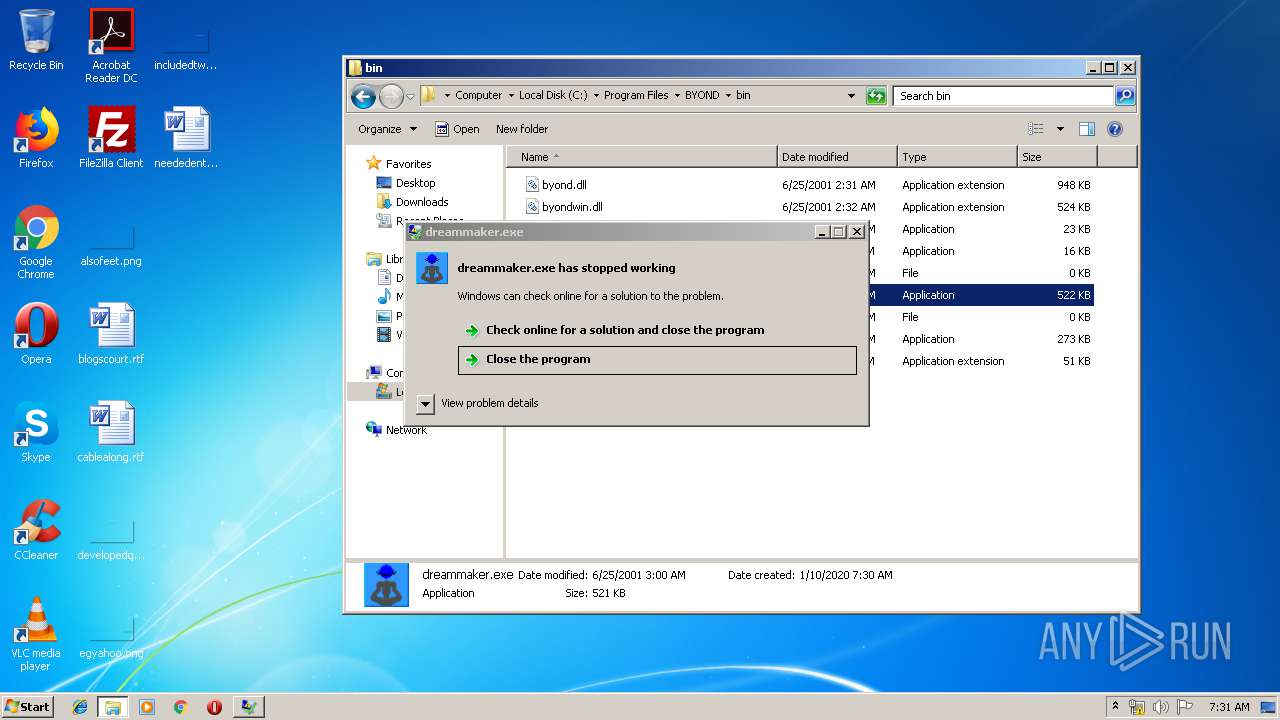
- dreammaker.exe (PID: 3388)
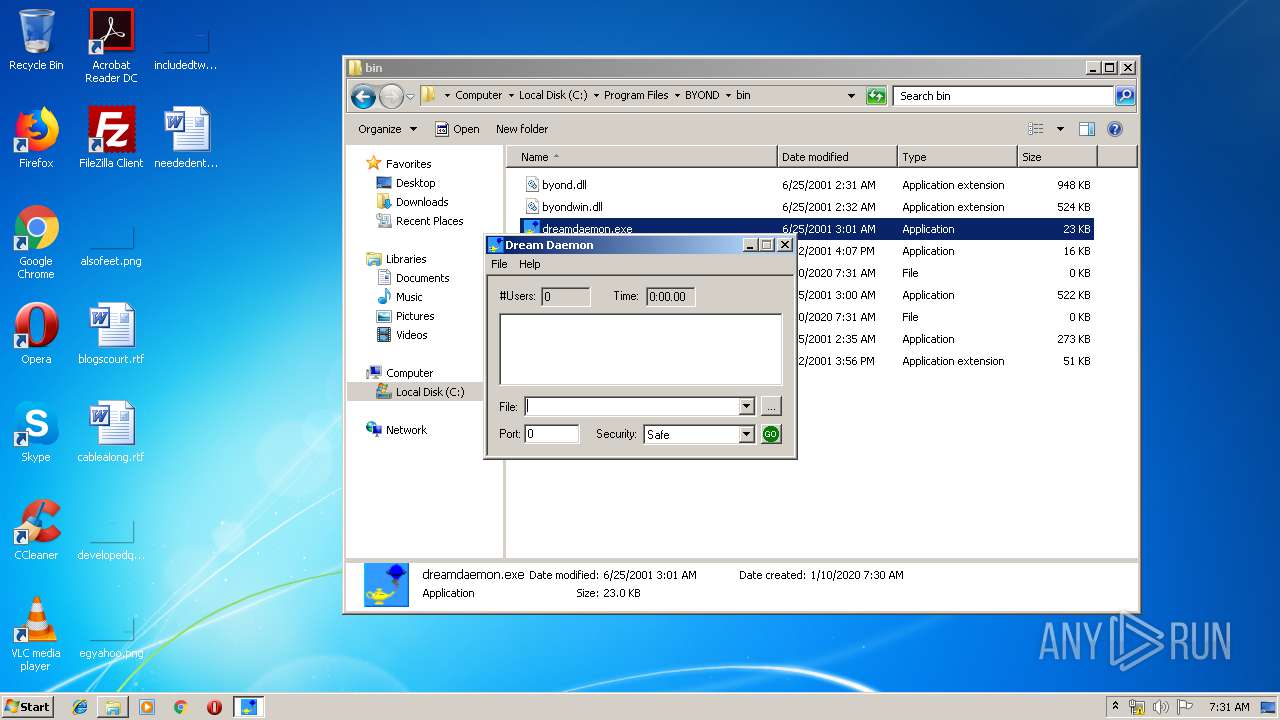
- dreamdaemon.exe (PID: 3596)
Loads dropped or rewritten executable
- _INS0432._MP (PID: 2400)
- WerFault.exe (PID: 3864)
- dreamseeker.exe (PID: 1468)
- WerFault.exe (PID: 2912)
- WerFault.exe (PID: 1812)
- dreamdaemon.exe (PID: 3596)
- dreammaker.exe (PID: 3388)
- explorer.exe (PID: 352)
SUSPICIOUS
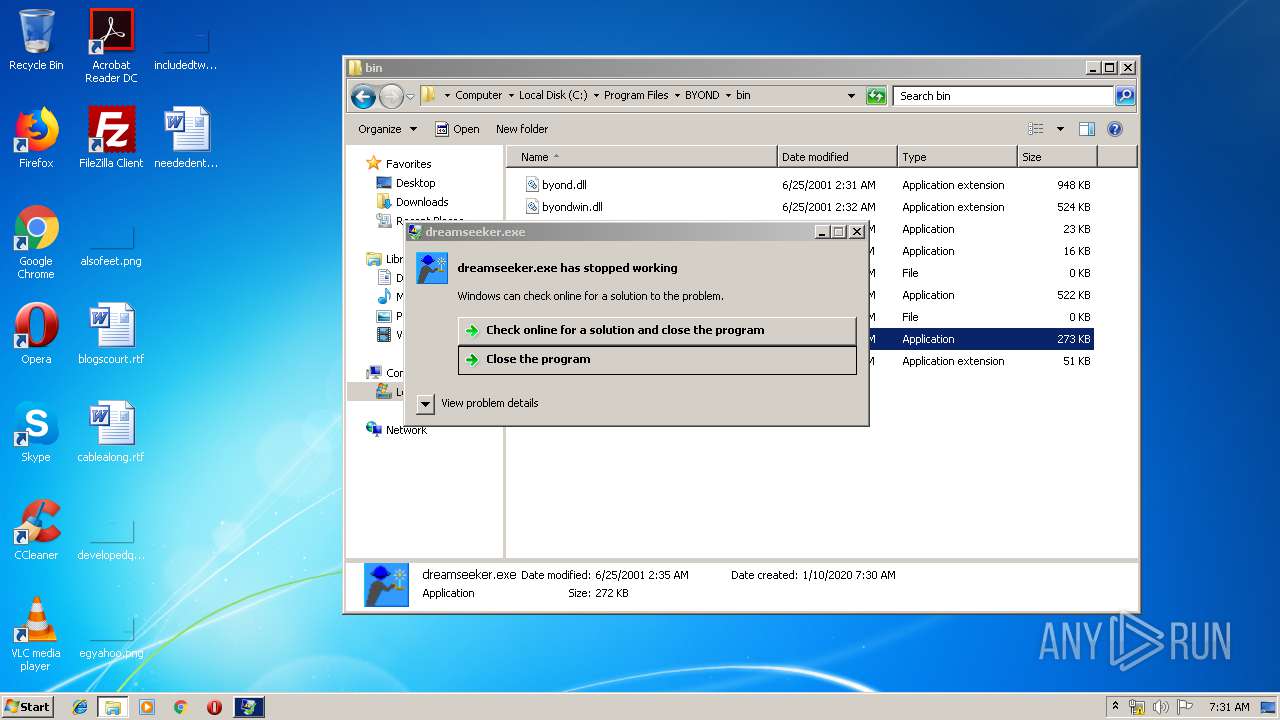
Executes application which crashes
- byond_setup.exe (PID: 1028)
Executable content was dropped or overwritten
- byond_setup.exe (PID: 1028)
- _INS0432._MP (PID: 2400)
- ntvdm.exe (PID: 2476)
Starts application with an unusual extension
- ntvdm.exe (PID: 2476)
Removes files from Windows directory
- ntvdm.exe (PID: 2476)
- _INS0432._MP (PID: 2400)
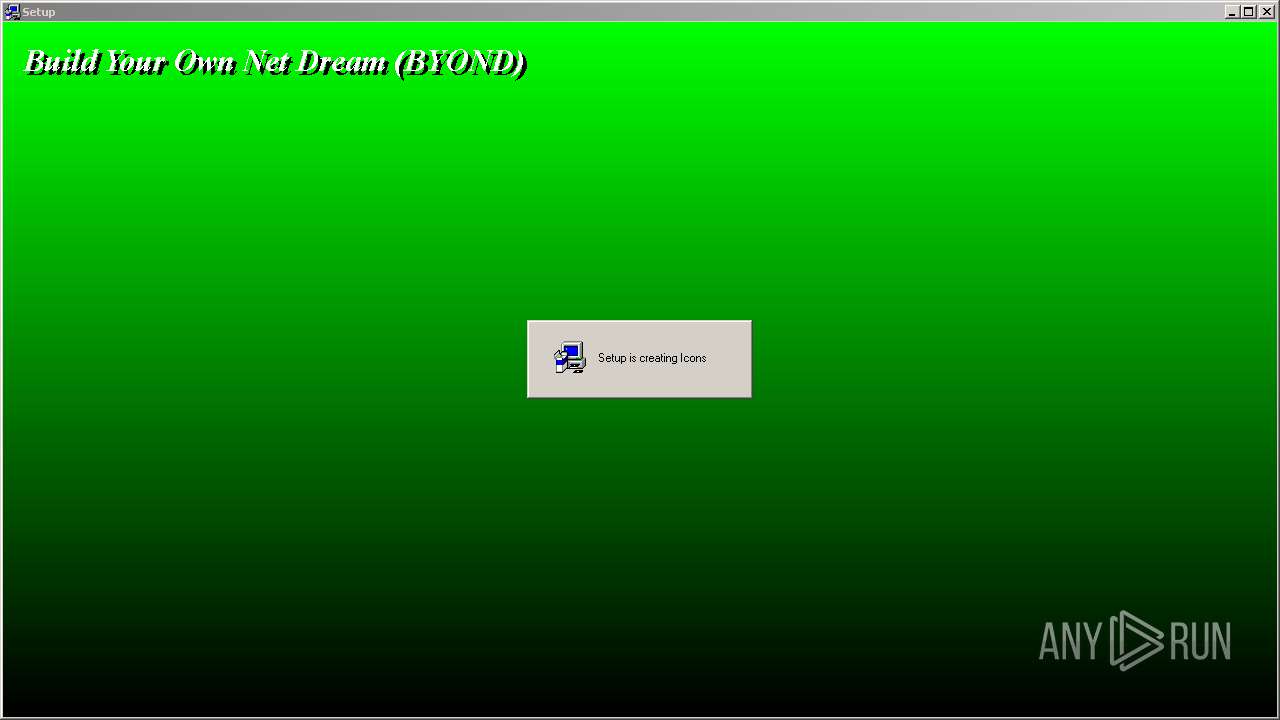
Creates files in the Windows directory
- ntvdm.exe (PID: 2476)
- _INS0432._MP (PID: 2400)
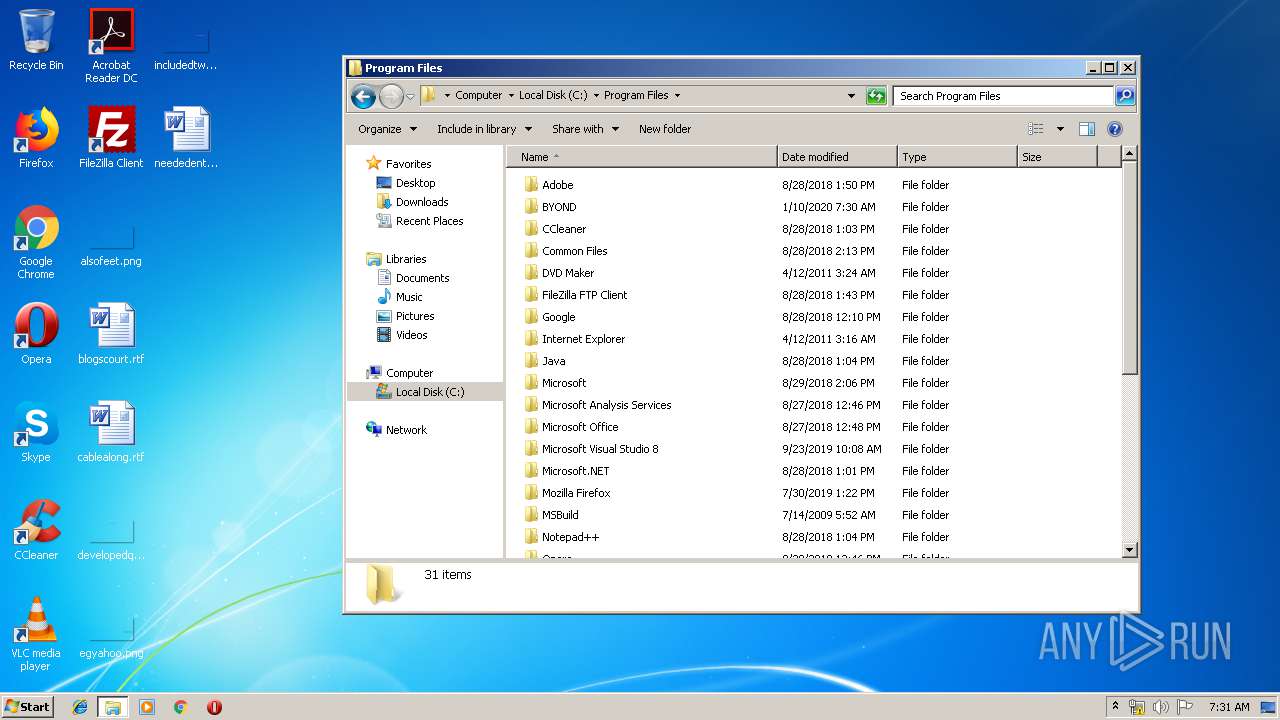
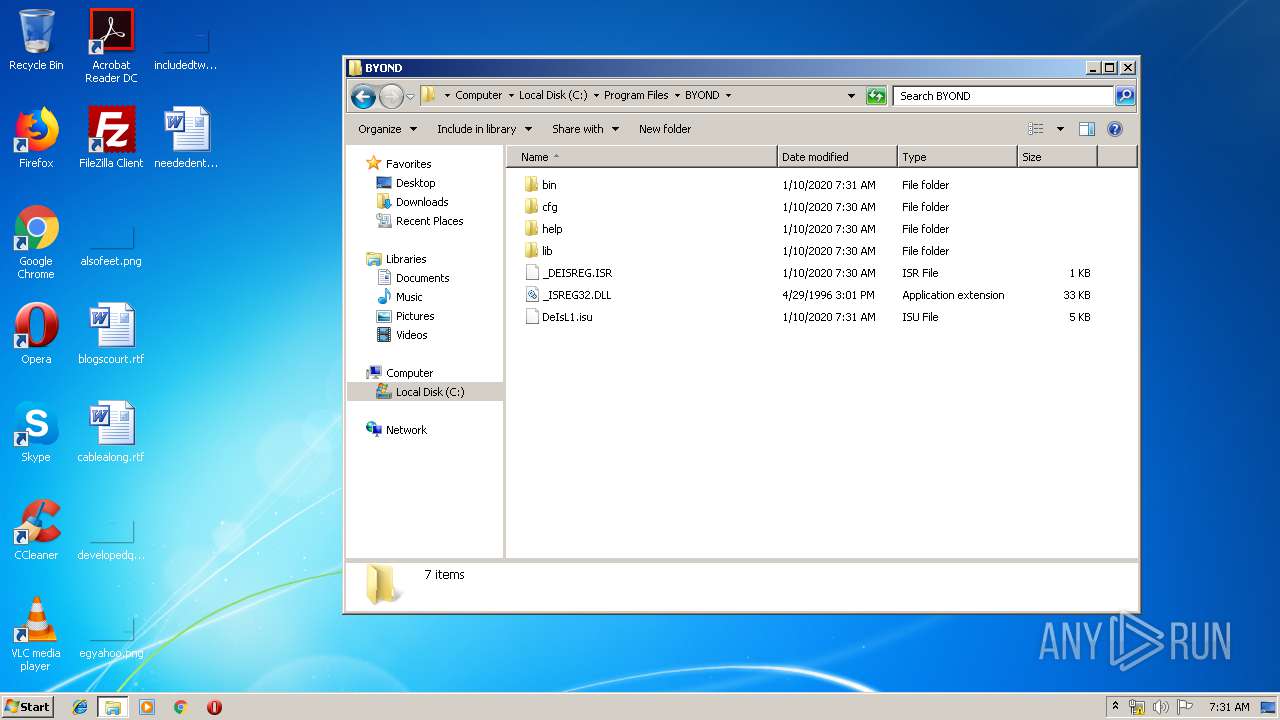
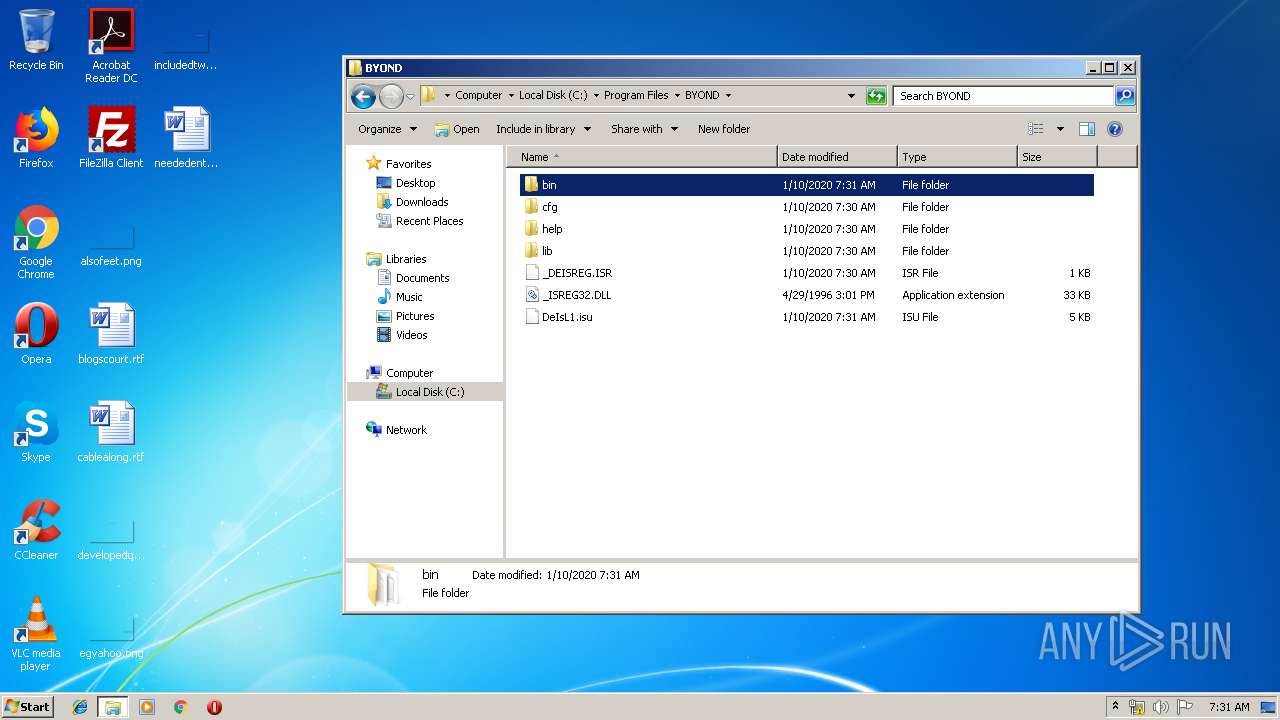
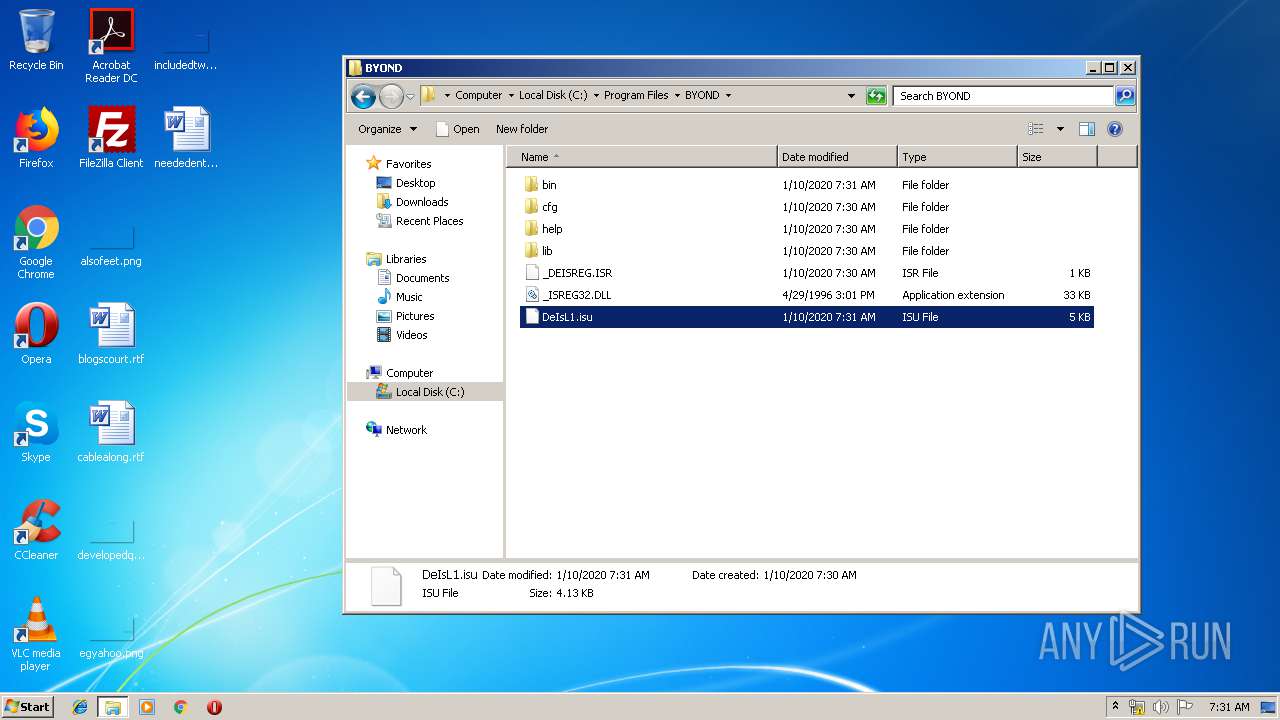
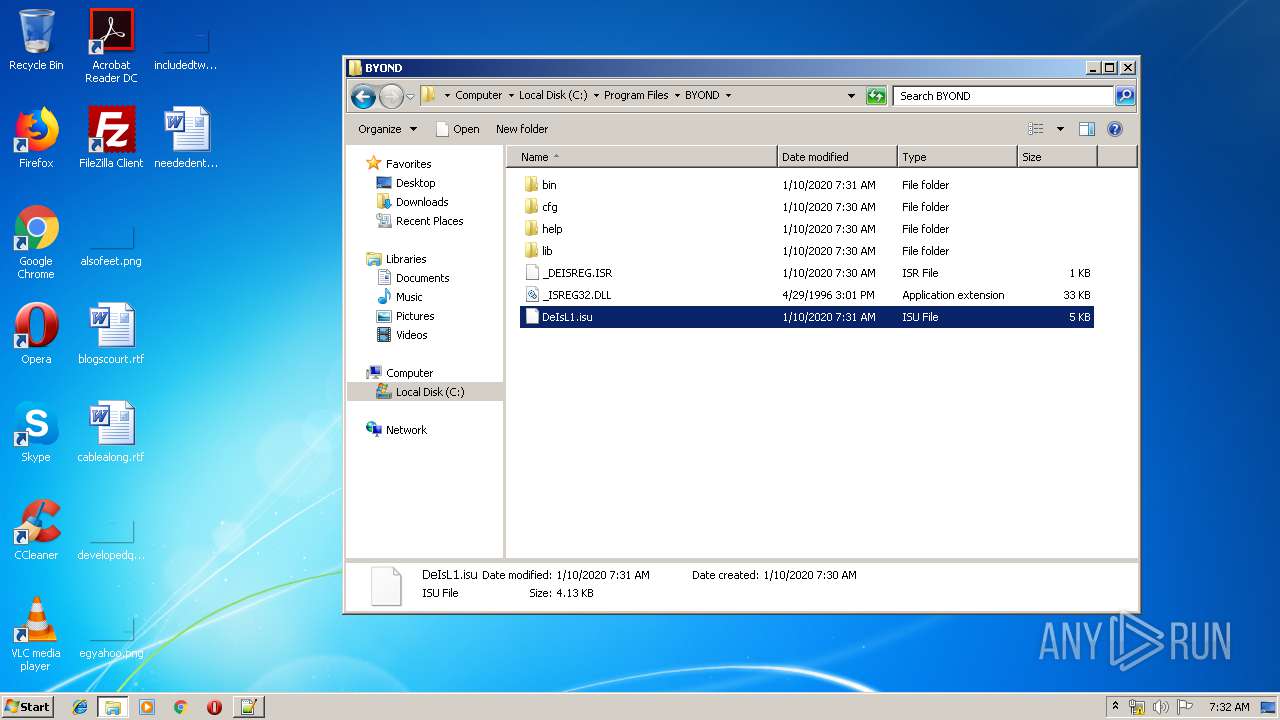
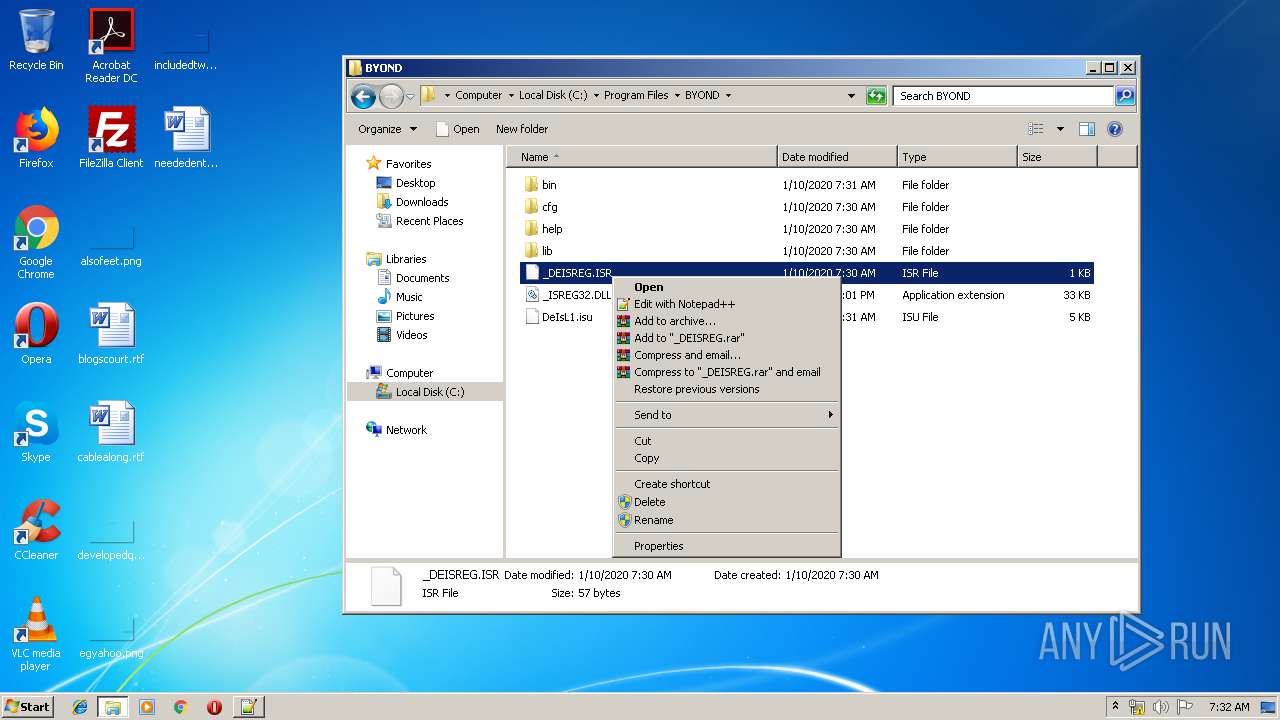
Creates files in the program directory
- _INS0432._MP (PID: 2400)
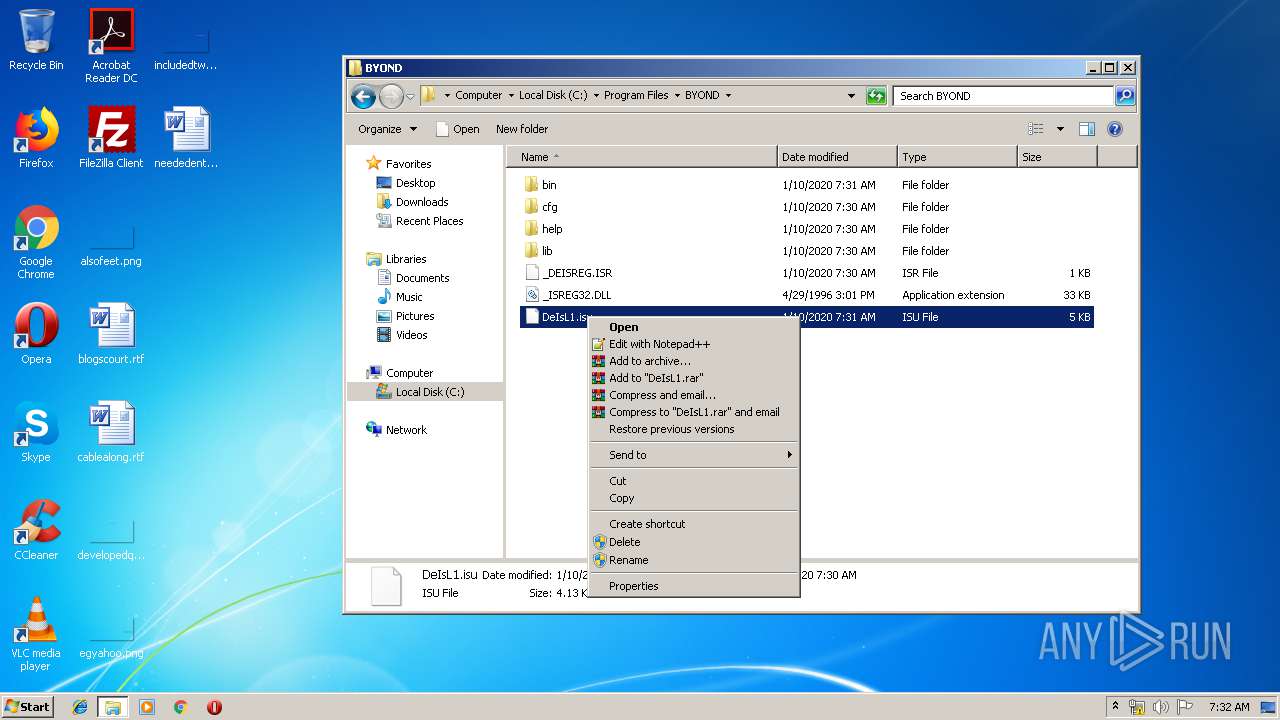
Modifies the open verb of a shell class
- _INS0432._MP (PID: 2400)
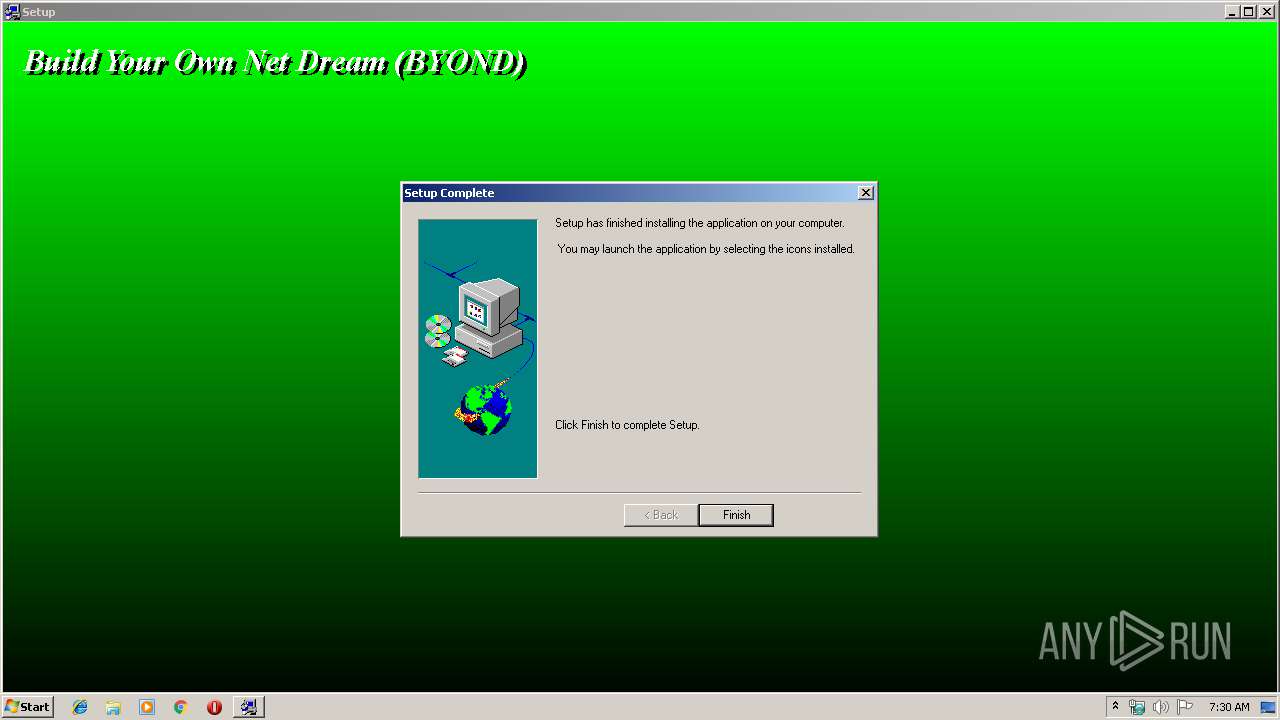
Creates a software uninstall entry
- _INS0432._MP (PID: 2400)
Creates files in the user directory
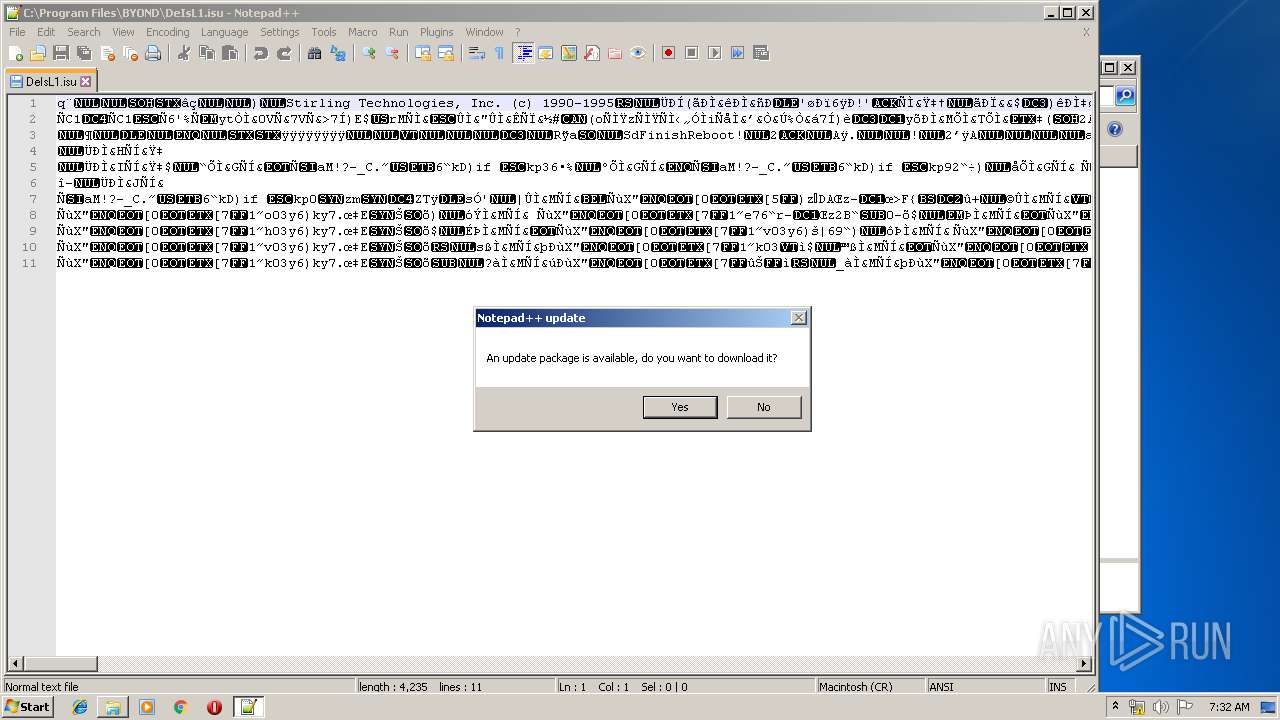
- notepad++.exe (PID: 1400)
INFO
Manual execution by user
- dreamseeker.exe (PID: 1468)
- explorer.exe (PID: 1216)
- dreammaker.exe (PID: 3388)
- dreamdaemon.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:09:13 01:30:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.1 |
| CodeSize: | 22016 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f8f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Sep-2000 23:30:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Sep-2000 23:30:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005486 | 0x00005600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44983 |
.rdata | 0x00007000 | 0x00000BD2 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08356 |
.data | 0x00008000 | 0x00001715 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.77457 |
.rsrc | 0x0000A000 | 0x00000508 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.93173 |
_winzip_ | 0x0000B000 | 0x00244000 | 0x00243C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99884 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
2 | 3.10863 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
55
Monitored processes
15
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\AppData\Local\Temp\byond_setup.exe" | C:\Users\admin\AppData\Local\Temp\byond_setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1216 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
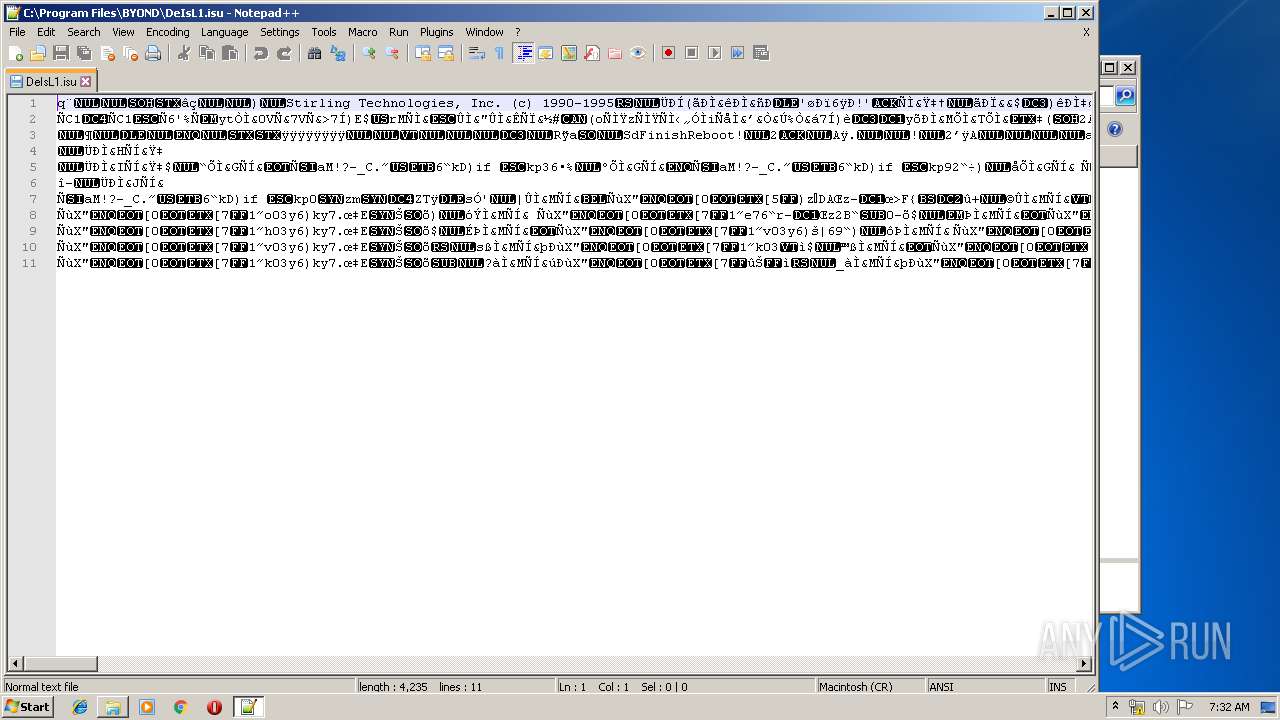
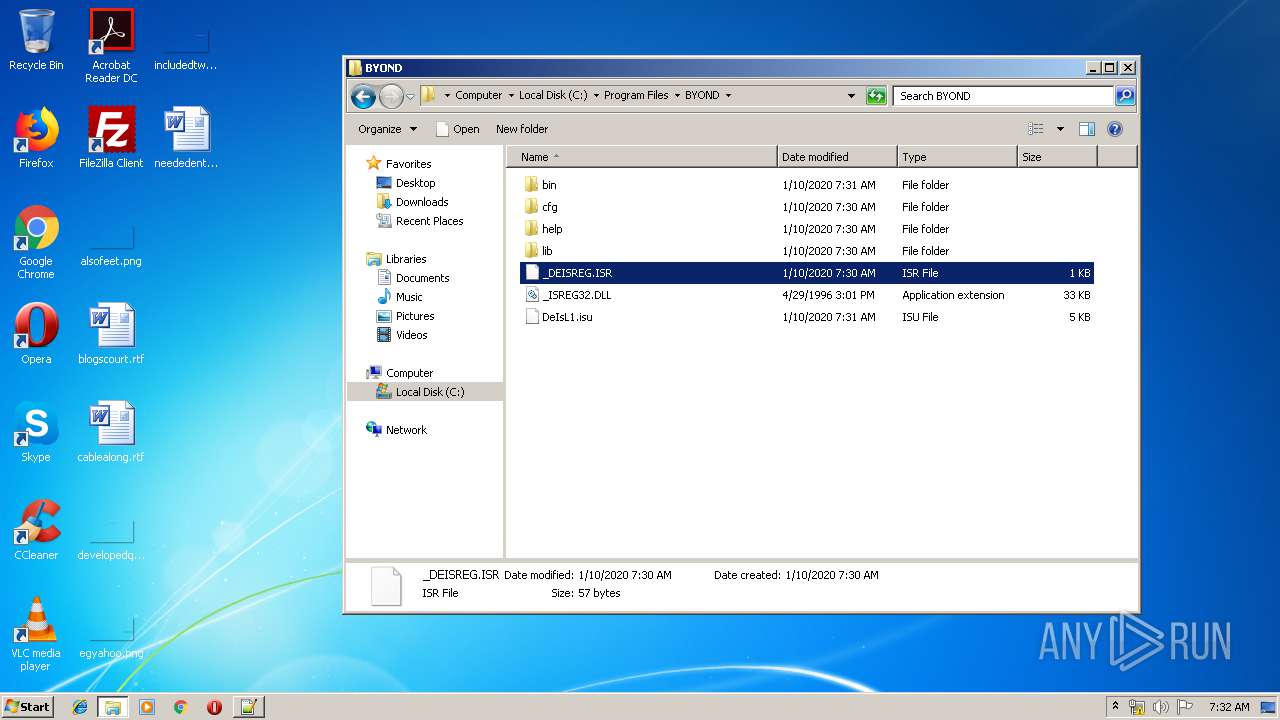
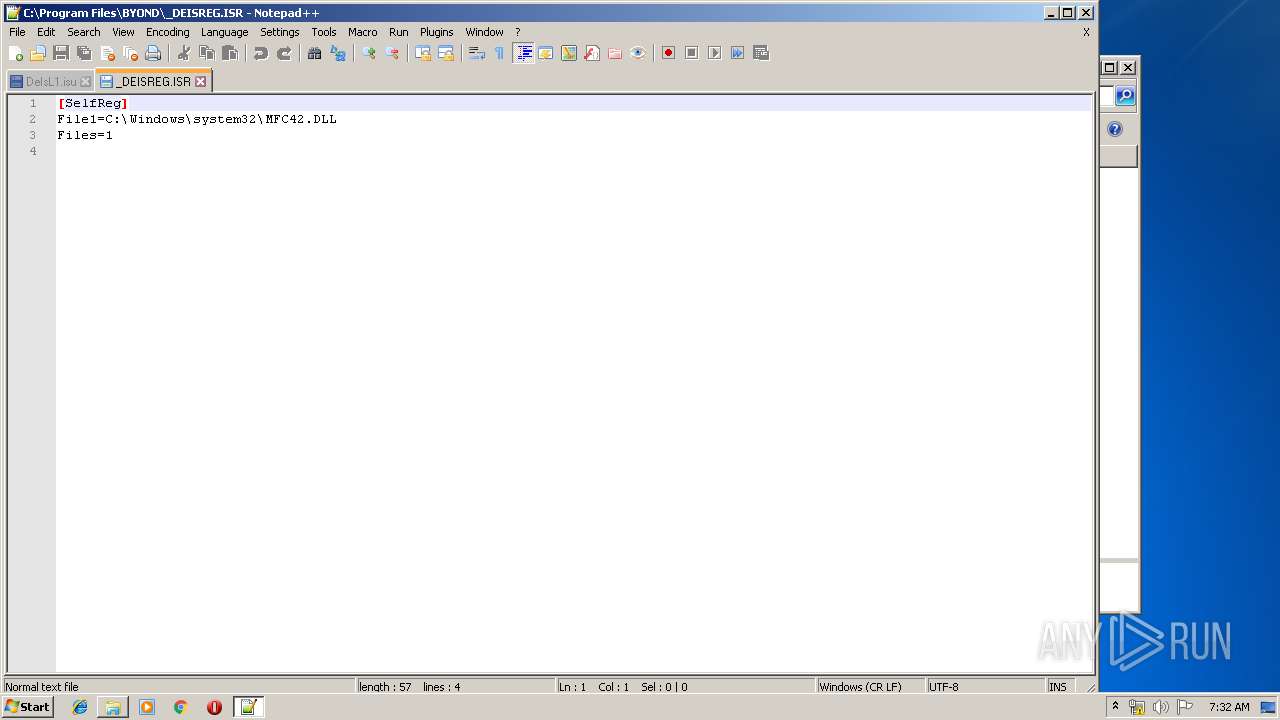
| 1400 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Program Files\BYOND\DeIsL1.isu" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
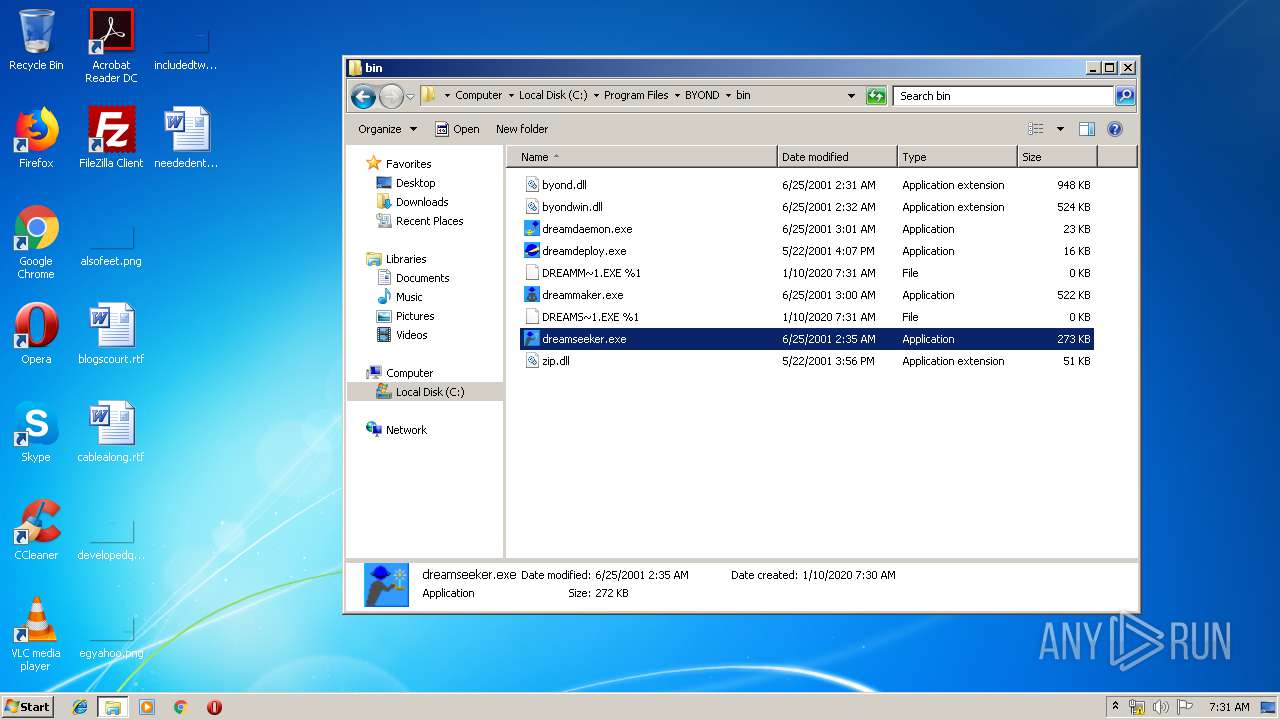
| 1468 | "C:\Program Files\BYOND\bin\dreamseeker.exe" | C:\Program Files\BYOND\bin\dreamseeker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1812 | C:\Windows\system32\WerFault.exe -u -p 3388 -s 216 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\byond_setup.exe" | C:\Users\admin\AppData\Local\Temp\byond_setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2400 | C:\Users\admin\AppData\Local\Temp\_INS0432._MP -fC:\USERS\ADMIN\APPDATA\LOCAL\TEMP\WZSE0.TMP\SETUP.INS -z1 -cx -xC:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\_INS0432._MP | ntvdm.exe | ||||||||||||
User: admin Company: InstallShield Corporation, Inc. Integrity Level: HIGH Description: InstallShield Engine EXE Exit code: 0 Version: 3.00.098.0 Modules
| |||||||||||||||
| 2476 | "C:\Windows\system32\ntvdm.exe" -i1 -ws | C:\Windows\system32\ntvdm.exe | byond_setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | C:\Windows\system32\WerFault.exe -u -p 1468 -s 276 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 450
Read events
823
Write events
622
Delete events
5
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\olbaq_frghc.rkr |
Value: 0000000000000000000000007A320000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000BB131300090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | delete value | Name: | LangID |
Value: 0904 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\StringCacheSettings |
| Operation: | write | Name: | StringCacheGeneration |
Value: 300 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.3g2\OpenWithProgids |
| Operation: | write | Name: | VLC.3g2 |
Value: | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.3gp\OpenWithProgids |
| Operation: | write | Name: | VLC.3gp |
Value: | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.3gp2\OpenWithProgids |
| Operation: | write | Name: | VLC.3gp2 |
Value: | |||
Executable files
23
Suspicious files
8
Text files
31
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsAE4B.tmp | — | |
MD5:— | SHA256:— | |||
| 2476 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsAE5C.tmp | — | |
MD5:— | SHA256:— | |||
| 1028 | byond_setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\SETUP.INI | text | |
MD5:— | SHA256:— | |||
| 1028 | byond_setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\_INST32I.EX_ | ??_ | |
MD5:— | SHA256:— | |||
| 2400 | _INS0432._MP | C:\Users\admin\AppData\Local\Temp\_ISTMP0.DIR\UNINST.728 | — | |
MD5:— | SHA256:— | |||
| 1028 | byond_setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\SETUP.PKG | pkg | |
MD5:— | SHA256:— | |||
| 1028 | byond_setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\_SETUP.1 | compressed | |
MD5:— | SHA256:— | |||
| 2476 | ntvdm.exe | C:\Windows\_delis43.ini | text | |
MD5:— | SHA256:— | |||
| 1028 | byond_setup.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\SETUP.EXE | executable | |
MD5:— | SHA256:— | |||
| 2476 | ntvdm.exe | C:\USERS\ADMIN\APPDATA\LOCAL\TEMP\_INS0432._MP | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAxHWpoyfQpCuYL7zNoKQA4%3D | US | der | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dreamseeker.exe | Invalid parameter passed to C runtime function.
|
dreamseeker.exe | Invalid parameter passed to C runtime function.
|
dreammaker.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|
dreamdaemon.exe | Invalid parameter passed to C runtime function.
|