| File name: | HyperTerminal.exe |
| Full analysis: | https://app.any.run/tasks/356da421-70b9-4710-9d59-b28a751fc3ed |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 06:27:57 |
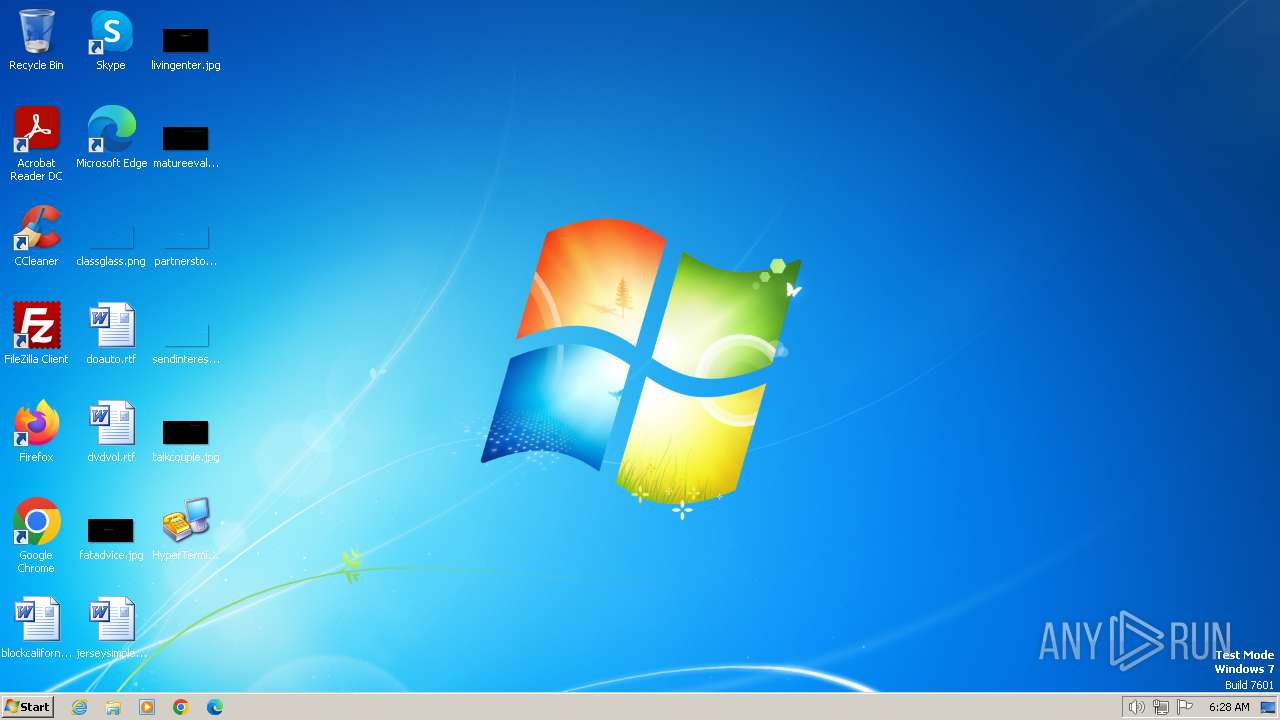
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E8222DD1EBE47386242BDC92CB857BDD |
| SHA1: | 6ECA84EF8A45EFBF26D950786105ADF83A3CFBE2 |
| SHA256: | 19884C82DB92AC9797D3DC54B81BB4A22ED5B2FCD0FFA8B89942A8DDF0097EB6 |
| SSDEEP: | 98304:d+yKHaZ6rVJPWGHWrKq+7nl4rwB2GK4pq5J6kANpjB0fVBiDBwszqyagJZtsixvS:29e52i |
MALICIOUS
Drops the executable file immediately after the start
- HyperTerminal.exe (PID: 2044)
- rdmmgud.exe (PID: 864)
- rdmmgud.exe (PID: 1496)
Changes the AppInit_DLLs value (autorun option)
- rdmmgud.exe (PID: 1496)
SUSPICIOUS
Reads the BIOS version
- HyperTerminal.exe (PID: 2044)
- rdmmgud.exe (PID: 864)
- java_update_xuuacaa.exe (PID: 1652)
- rdmmgud.exe (PID: 1496)
The process executes via Task Scheduler
- rdmmgud.exe (PID: 864)
- rdmmgud.exe (PID: 1496)
Starts itself from another location
- rdmmgud.exe (PID: 864)
Reads the Internet Settings
- rdmmgud.exe (PID: 864)
INFO
Reads the computer name
- HyperTerminal.exe (PID: 2044)
- rdmmgud.exe (PID: 864)
- java_update_xuuacaa.exe (PID: 1652)
Checks supported languages
- HyperTerminal.exe (PID: 2044)
- rdmmgud.exe (PID: 864)
- java_update_xuuacaa.exe (PID: 1652)
- rdmmgud.exe (PID: 1496)
Reads the machine GUID from the registry
- HyperTerminal.exe (PID: 2044)
- rdmmgud.exe (PID: 864)
- rdmmgud.exe (PID: 1496)
- java_update_xuuacaa.exe (PID: 1652)
Creates files in the program directory
- HyperTerminal.exe (PID: 2044)
Create files in a temporary directory
- rdmmgud.exe (PID: 864)
Process checks are UAC notifies on
- java_update_xuuacaa.exe (PID: 1652)
- rdmmgud.exe (PID: 1496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:29 19:00:20+02:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 24576 |
| InitializedDataSize: | 252416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x418058 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.2600.0 |
| ProductVersionNumber: | 5.1.2600.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Hilgraeve, Inc. |
| FileDescription: | HyperTerminal Applet |
| FileVersion: | 5.1.2600.0 |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | C:\PROGRA~2\Mozilla\rdmmgud.exe -ewjeepd | C:\ProgramData\Mozilla\rdmmgud.exe | — | taskeng.exe | |||||||||||
User: admin Company: Hilgraeve, Inc. Integrity Level: MEDIUM Description: HyperTerminal Applet Exit code: 0 Version: 5.1.2600.0 Modules
| |||||||||||||||
| 1496 | C:\PROGRA~2\Mozilla\rdmmgud.exe -ewjeepd | C:\ProgramData\Mozilla\rdmmgud.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Hilgraeve, Inc. Integrity Level: SYSTEM Description: HyperTerminal Applet Exit code: 0 Version: 5.1.2600.0 Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\AppData\Local\Temp\java_update_xuuacaa.exe" | C:\Users\admin\AppData\Local\Temp\java_update_xuuacaa.exe | rdmmgud.exe | ||||||||||||
User: admin Company: Hilgraeve, Inc. Integrity Level: HIGH Description: HyperTerminal Applet Exit code: 0 Version: 5.1.2600.0 Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\Desktop\HyperTerminal.exe" | C:\Users\admin\Desktop\HyperTerminal.exe | — | explorer.exe | |||||||||||
User: admin Company: Hilgraeve, Inc. Integrity Level: MEDIUM Description: HyperTerminal Applet Exit code: 0 Version: 5.1.2600.0 Modules
| |||||||||||||||
Total events
787
Read events
778
Write events
9
Delete events
0
Modification events
| (PID) Process: | (864) rdmmgud.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (864) rdmmgud.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (864) rdmmgud.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (864) rdmmgud.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1496) rdmmgud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows |
| Operation: | write | Name: | LoadAppInit_DLLs |
Value: 0 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1496 | rdmmgud.exe | C:\PROGRA~2\Mozilla\xciqtha.dll | executable | |
MD5:FDAB107849555AA98F46DDB284EC86AF | SHA256:1B3451C6309DBC61B3A3DED42C6277C8F4244DB20B20ADC304A8FDF33C6443AD | |||
| 864 | rdmmgud.exe | C:\Users\admin\AppData\Local\Temp\java_update_xuuacaa.exe | executable | |
MD5:B0A91BD9B29F7AD30DF95E20FE4C2EA7 | SHA256:81859D8B2BC4EA32288B5794204EA4A0FF9E9CC987C571A7251EC0EE97FEDFCE | |||
| 2044 | HyperTerminal.exe | C:\PROGRA~2\Mozilla\rdmmgud.exe | executable | |
MD5:BD9202038EA12CDFAFFF3AB7DD83D8E5 | SHA256:F04D7B0C1B6AB1F2D7E47EF2067B1534C70974025245C04D4DFF905B38830CF4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |