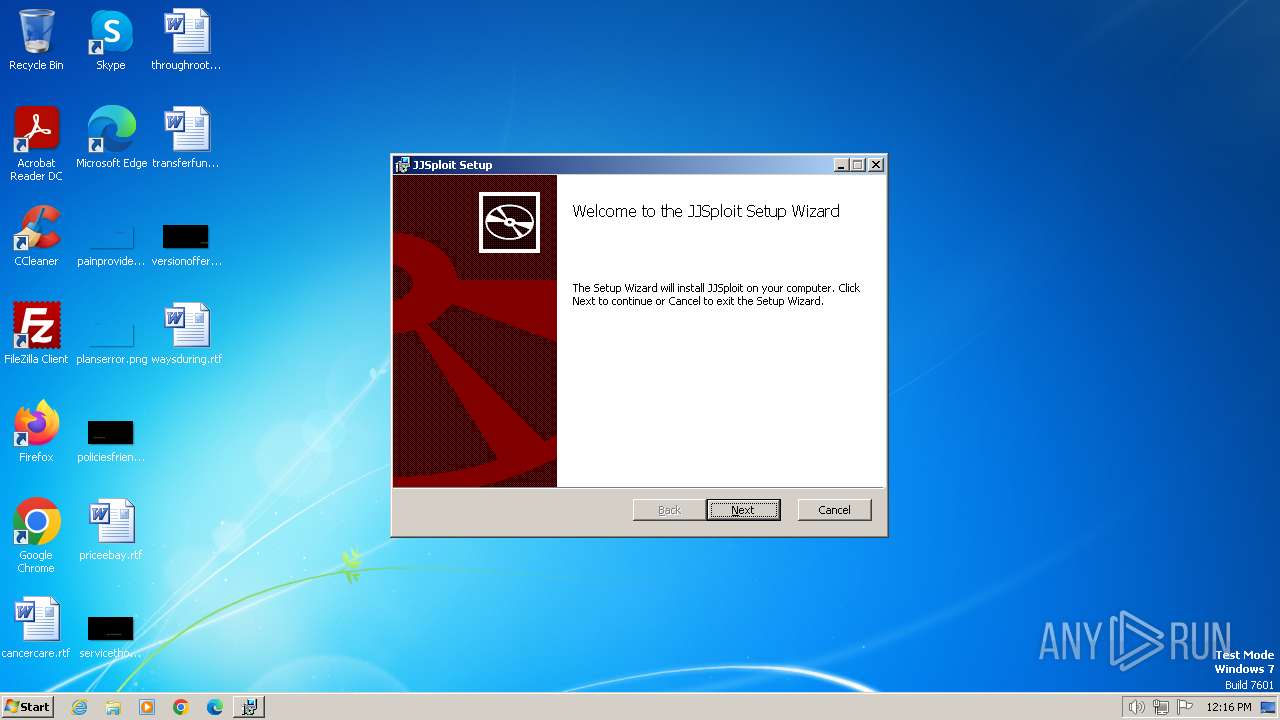
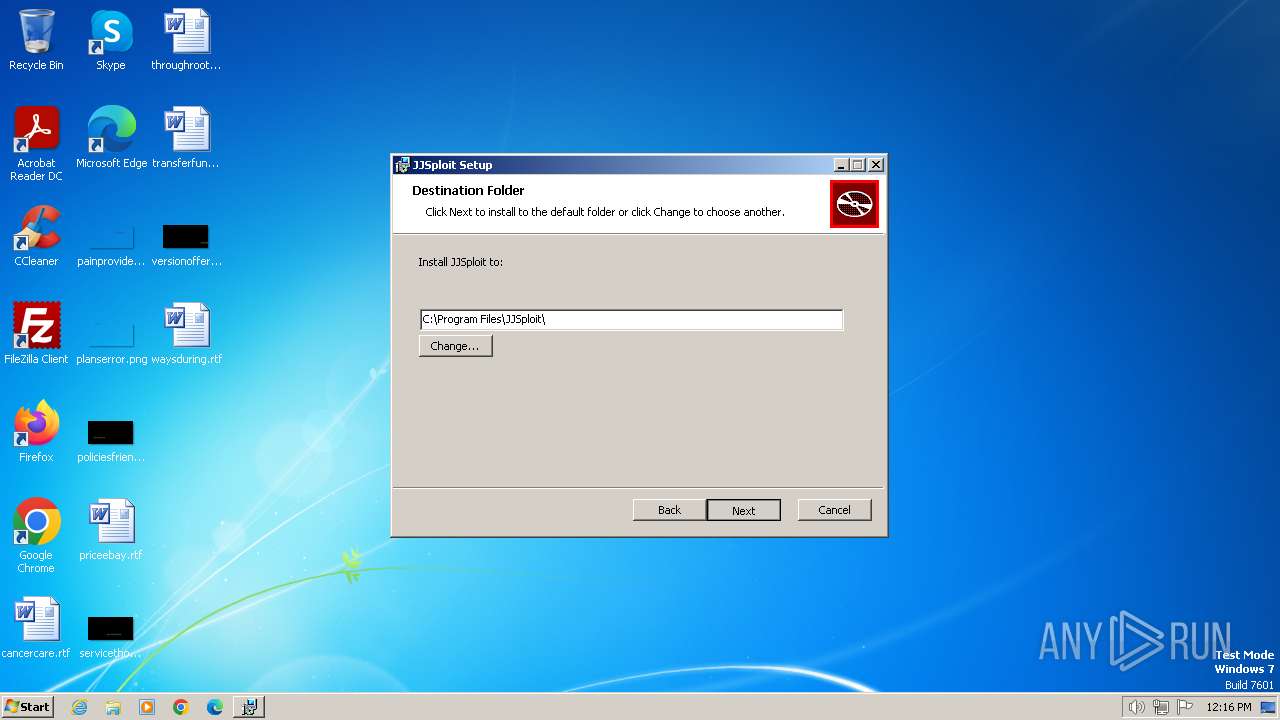
| File name: | JJSploit_7.3.0_x86_en-US.msi |
| Full analysis: | https://app.any.run/tasks/414b4f04-b461-44ac-959d-7b7d21a6a413 |
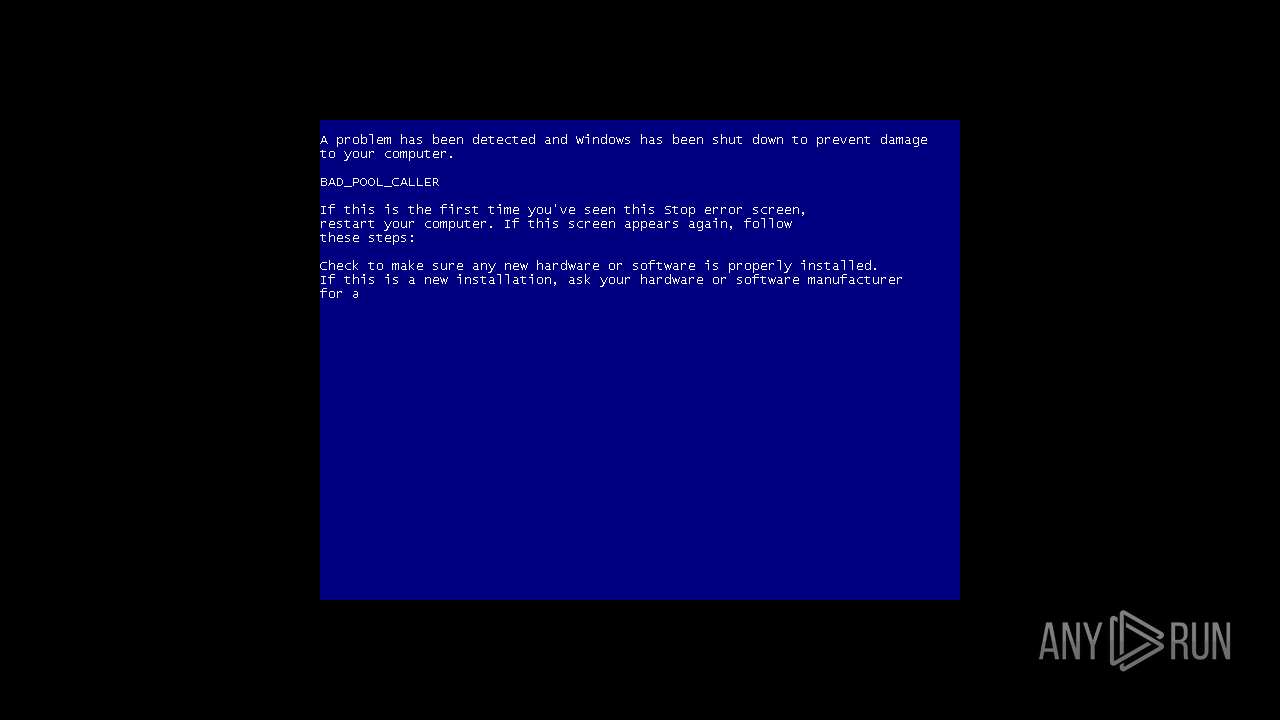
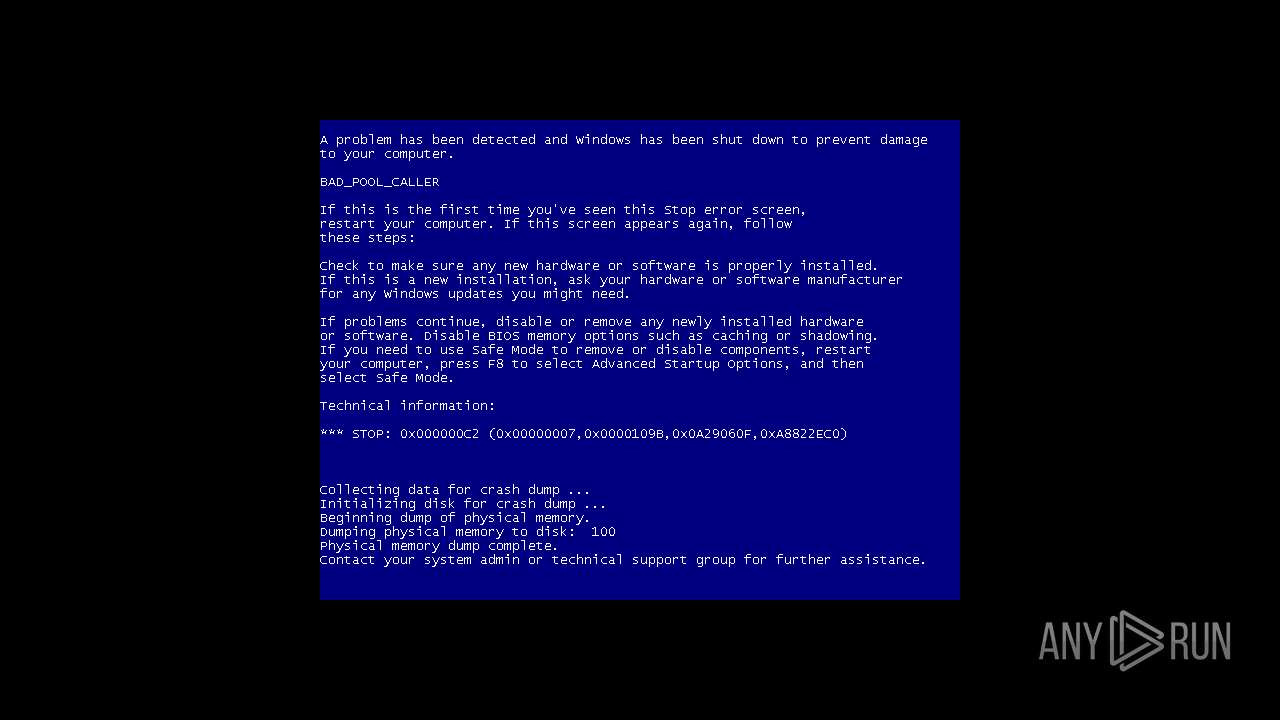
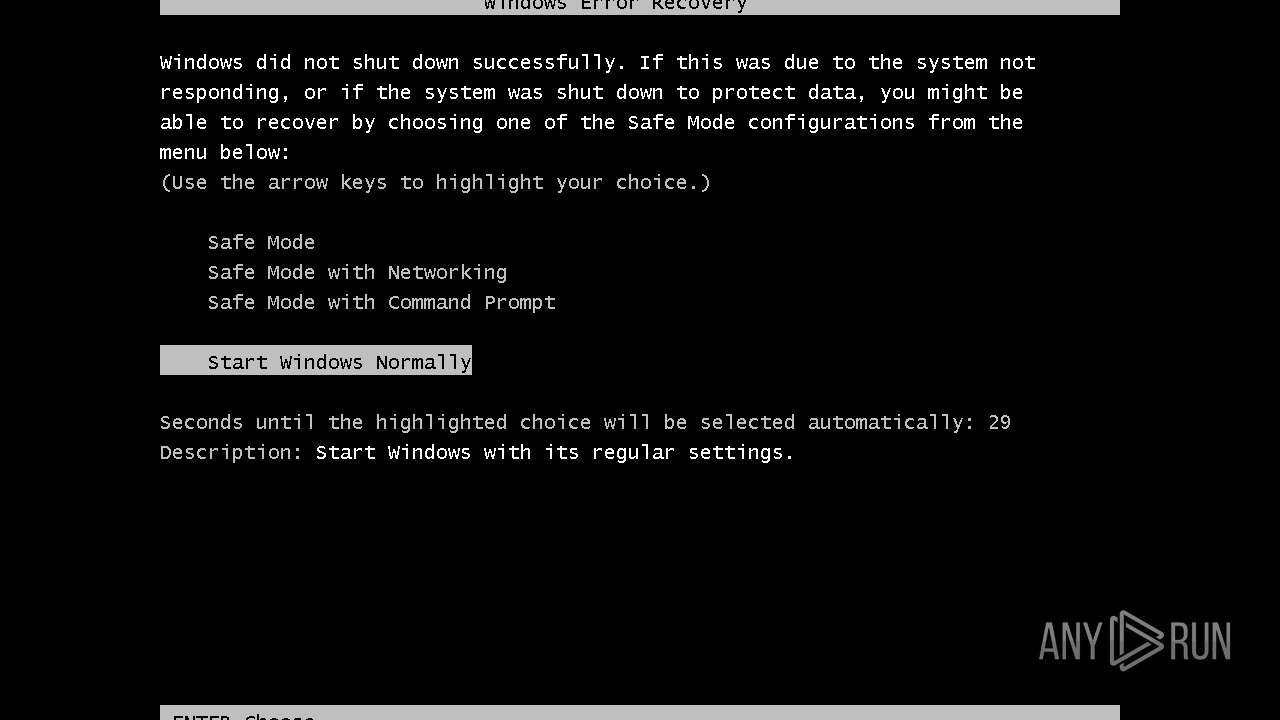
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2023, 12:16:20 |
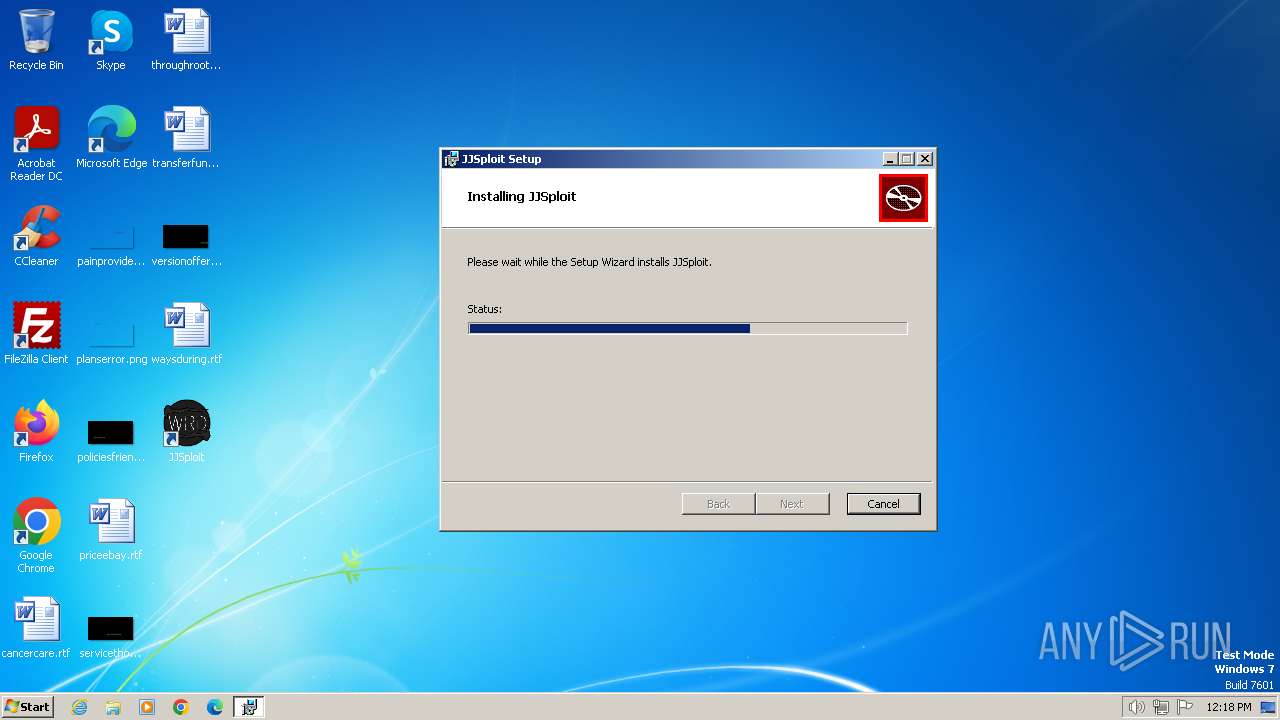
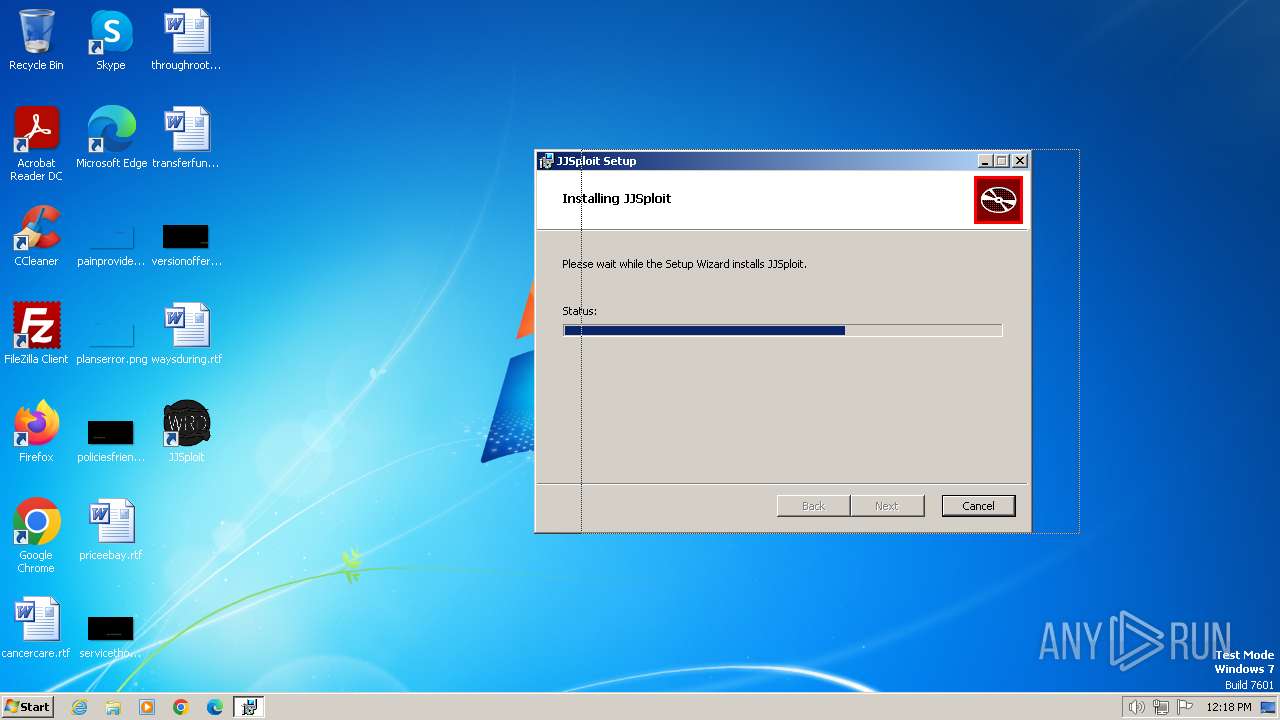
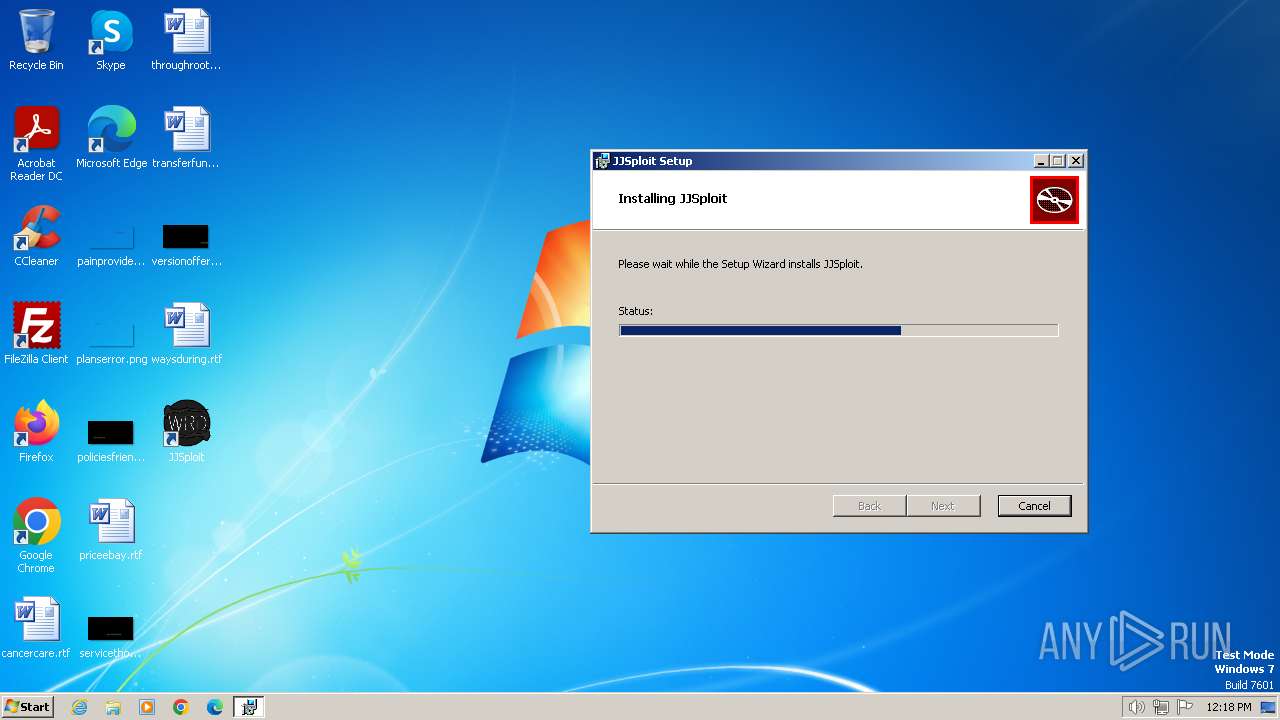
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: JJSploit, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install JJSploit., Template: Intel;0, Revision Number: {36D30491-2DCB-4793-81F4-D1C07F51C1FB}, Create Time/Date: Wed Sep 13 00:53:30 2023, Last Saved Time/Date: Wed Sep 13 00:53:30 2023, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 9C232FE2EDE51929244AFC5C67E53B51 |
| SHA1: | 8E8BB0EDA09D25C1F44B8ABD66A7E15A414B76F5 |
| SHA256: | 1985FDBEC700334FBB2C907F37A102930744E6B3E9198C25F516EAE9F6854E9B |
| SSDEEP: | 98304:S0yJkPPCA1o7IW+9Nh8Jg+y6RuRfhmM9DnNUTresAL2+x7SoEXt5xN6Z30rYNw+u:SPMWdFB/ |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1560)
SUSPICIOUS
Powershell scripting: start process
- msiexec.exe (PID: 1308)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1308)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1308)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 1308)
Reads the Internet Settings
- powershell.exe (PID: 1560)
- MicrosoftEdgeUpdate.exe (PID: 680)
- MicrosoftEdgeUpdate.exe (PID: 2052)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 2648)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 2560)
Unusual connection from system programs
- powershell.exe (PID: 1560)
The Powershell connects to the Internet
- powershell.exe (PID: 1560)
Checks Windows Trust Settings
- MicrosoftEdgeUpdate.exe (PID: 2052)
Reads settings of System Certificates
- MicrosoftEdgeUpdate.exe (PID: 2052)
- MicrosoftEdgeUpdate.exe (PID: 680)
Starts CMD.EXE for commands execution
- JJSploit.exe (PID: 3212)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 2052)
INFO
Reads the computer name
- msiexec.exe (PID: 1308)
- msiexec.exe (PID: 2076)
- MicrosoftEdgeUpdate.exe (PID: 1768)
- MicrosoftEdgeUpdate.exe (PID: 2560)
- MicrosoftEdgeUpdate.exe (PID: 680)
- MicrosoftEdgeUpdate.exe (PID: 1556)
- MicrosoftEdgeUpdate.exe (PID: 2052)
- JJSploit.exe (PID: 3212)
Checks supported languages
- msiexec.exe (PID: 1308)
- msiexec.exe (PID: 2076)
- MicrosoftEdgeWebview2Setup.exe (PID: 2472)
- MicrosoftEdgeUpdate.exe (PID: 2052)
- MicrosoftEdgeUpdate.exe (PID: 1768)
- MicrosoftEdgeUpdate.exe (PID: 2560)
- MicrosoftEdgeUpdate.exe (PID: 1556)
- MicrosoftEdgeUpdate.exe (PID: 680)
- JJSploit.exe (PID: 3212)
Drops the executable file immediately after the start
- msiexec.exe (PID: 128)
- msiexec.exe (PID: 1308)
- powershell.exe (PID: 1560)
- MicrosoftEdgeWebview2Setup.exe (PID: 2472)
- MicrosoftEdgeUpdate.exe (PID: 1768)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1308)
- msiexec.exe (PID: 2076)
- MicrosoftEdgeUpdate.exe (PID: 1768)
- MicrosoftEdgeUpdate.exe (PID: 680)
- MicrosoftEdgeUpdate.exe (PID: 1556)
- MicrosoftEdgeUpdate.exe (PID: 2052)
Application launched itself
- msiexec.exe (PID: 1308)
- msedge.exe (PID: 2988)
- msedge.exe (PID: 2460)
Executes as Windows Service
- VSSVC.exe (PID: 2416)
Create files in a temporary directory
- msiexec.exe (PID: 1308)
- MicrosoftEdgeWebview2Setup.exe (PID: 2472)
- MicrosoftEdgeUpdate.exe (PID: 1768)
- MicrosoftEdgeUpdate.exe (PID: 2052)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 2472)
Process drops legitimate windows executable
- powershell.exe (PID: 1560)
- MicrosoftEdgeWebview2Setup.exe (PID: 2472)
- MicrosoftEdgeUpdate.exe (PID: 1768)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 1768)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 1768)
- MicrosoftEdgeUpdate.exe (PID: 2052)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 2052)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 2052)
Manual execution by a user
- JJSploit.exe (PID: 3212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | JJSploit |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install JJSploit. |
| Template: | Intel;0 |
| RevisionNumber: | {36D30491-2DCB-4793-81F4-D1C07F51C1FB} |
| CreateDate: | 2023:09:12 23:53:30 |
| ModifyDate: | 2023:09:12 23:53:30 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
58
Monitored processes
18
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\JJSploit_7.3.0_x86_en-US.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.181.5 Modules
| |||||||||||||||
| 1308 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{3977F5E5-3C86-4E7C-B88D-E9AA687F1082}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.181.5 Modules
| |||||||||||||||
| 1560 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1768 | C:\Users\admin\AppData\Local\Temp\EU5B6A.tmp\MicrosoftEdgeUpdate.exe /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EU5B6A.tmp\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeWebview2Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.181.5 Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xODEuNSIgc2hlbGxfdmVyc2lvbj0iMS4zLjE4MS41IiBpc21hY2hpbmU9IjAiIHNlc3Npb25pZD0iezM5NzdGNUU1LTNDODYtNEU3Qy1CODhELUU5QUE2ODdGMTA4Mn0iIGluc3RhbGxzb3VyY2U9Im90aGVyaW5zdGFsbGNtZCIgcmVxdWVzdGlkPSJ7NkQ1RUNCMTItMTAwNC00RUI5LUEwOTEtQzMwMDgyMjMwRkJDfSIgZGVkdXA9ImNyIiBkb21haW5qb2luZWQ9IjAiPjxodyBsb2dpY2FsX2NwdXM9IjQiIHBoeXNtZW1vcnk9IjMiIGRpc2tfdHlwZT0iMCIgc3NlPSIxIiBzc2UyPSIxIiBzc2UzPSIxIiBzc3NlMz0iMSIgc3NlNDE9IjEiIHNzZTQyPSIxIiBhdng9IjEiLz48b3MgcGxhdGZvcm09IndpbiIgdmVyc2lvbj0iNi4xLjc2MDEuMjQ1NDYiIHNwPSJTZXJ2aWNlIFBhY2sgMSIgYXJjaD0ieDg2IiBwcm9kdWN0X3R5cGU9IjQ4IiBpc193aXA9IjAiIGlzX2luX2xvY2tkb3duX21vZGU9IjAiLz48b2VtIHByb2R1Y3RfbWFudWZhY3R1cmVyPSJERUxMIiBwcm9kdWN0X25hbWU9IkRFTEwiLz48ZXhwIGV0YWc9IiIvPjxhcHAgYXBwaWQ9IntGM0M0RkUwMC1FRkQ1LTQwM0ItOTU2OS0zOThBMjBGMUJBNEF9IiB2ZXJzaW9uPSIiIG5leHR2ZXJzaW9uPSIxLjMuMTgxLjUiIGxhbmc9IiIgYnJhbmQ9IiIgY2xpZW50PSIiPjxldmVudCBldmVudHR5cGU9IjIiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIHN5c3RlbV91cHRpbWVfdGlja3M9Ijk0MTU1MjczNDMiIGluc3RhbGxfdGltZV9tcz0iNjU2Ii8-PC9hcHA-PC9yZXF1ZXN0Pg | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.181.5 Modules
| |||||||||||||||
| 2076 | C:\Windows\system32\MsiExec.exe -Embedding 002763C2DBAAE1292731715E714EA027 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.youtube.com/@WeAreDevsExploits | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
17 330
Read events
14 979
Write events
2 337
Delete events
14
Modification events
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009F5A7BD72FB0D90164030000840D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 73 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008543C5D72FB0D90164030000840D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 4000000000000000D1ABF1D82FB0D90164030000840D0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 4000000000000000475C02D92FB0D90164030000840D0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000E57701DA2FB0D90164030000840D0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1308) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | FirstRun |
Value: 0 | |||
Executable files
204
Suspicious files
19
Text files
25
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1308 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1308 | msiexec.exe | C:\Windows\Installer\e3748.msi | — | |
MD5:— | SHA256:— | |||
| 1308 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:9CD769E4F82D6321827C090C4E5AB0AE | SHA256:488AF85386971969BCA35709C7AC879833611DA49A373186CCBD40677F4A3132 | |||
| 1308 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\noclip.lua | text | |
MD5:F41312C46F3B932B0B6005907ECA2D83 | SHA256:E61471834F3A99B8B2EBFA166DB499EDF871FFE68FCB9FFF6F113428291D4ABB | |||
| 128 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI170E.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 1308 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFAAB986E9CF9ED905.TMP | binary | |
MD5:DBC711C400E1BDE0FF9EDE603D571BA9 | SHA256:4C6C69F1EAE49CE96E426E7D1D6A6DF7F90B6DCBDA50919E40CACB1B605570A9 | |||
| 1308 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\animations\levitate.lua | text | |
MD5:648E324C30233817A5E8BEBA883EC83B | SHA256:0F471CB5527E96ED48ED21F59714B78C64C944D528D65109946D8F91E0D76792 | |||
| 1308 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\teleportto.lua | text | |
MD5:CD719CA0E57C68FACFACEF67C2AAFE90 | SHA256:A22A6EF7A55035961C0A6F529C77D1100A333EC7A4CAA6384962E273C76CBA33 | |||
| 1308 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\infinitejump.lua | text | |
MD5:BC3B3ADE9D29745D015F532903112DF7 | SHA256:496AF192B1A41C54F22257ED174F75DE2F722CA18C7A98BC9CEF58E45ACFA880 | |||
| 1308 | msiexec.exe | C:\Windows\Installer\MSI3BFB.tmp | binary | |
MD5:110BD196FF52563FCEDF16BDEDEE4EE3 | SHA256:B86C37E0EF19D2D9BB711691B02A4FE911E1B135C1A91134101C0568B616CEB5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2052 | MicrosoftEdgeUpdate.exe | GET | 200 | 72.247.153.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a345e775e21c7c65 | unknown | compressed | 4.66 Kb | unknown |
2052 | MicrosoftEdgeUpdate.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | binary | 471 b | unknown |
856 | svchost.exe | HEAD | 200 | 2.22.242.227:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d87a3bbd-7fe5-4ec3-b806-293cca78b363?P1=1704025019&P2=404&P3=2&P4=N58Z8oEkQH%2fzwj3lt%2fOzhj5exZZdqVxnjJVSmrOWOcaFXUaa%2fmnum68SujvPh2OqPyUXuYljIp74gtidXmlTtw%3d%3d | unknown | — | — | unknown |
856 | svchost.exe | GET | — | 2.22.242.227:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d87a3bbd-7fe5-4ec3-b806-293cca78b363?P1=1704025019&P2=404&P3=2&P4=N58Z8oEkQH%2fzwj3lt%2fOzhj5exZZdqVxnjJVSmrOWOcaFXUaa%2fmnum68SujvPh2OqPyUXuYljIp74gtidXmlTtw%3d%3d | unknown | — | — | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e412f7b4eff0943 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1560 | powershell.exe | 23.43.62.58:443 | go.microsoft.com | Akamai International B.V. | US | unknown |
1560 | powershell.exe | 2.16.164.32:443 | msedge.sf.dl.delivery.mp.microsoft.com | Akamai International B.V. | NL | unknown |
2052 | MicrosoftEdgeUpdate.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
680 | MicrosoftEdgeUpdate.exe | 20.114.58.89:443 | msedge.api.cdp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2052 | MicrosoftEdgeUpdate.exe | 104.46.162.224:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
2052 | MicrosoftEdgeUpdate.exe | 72.247.153.178:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
2896 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
msedge.f.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
856 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
JJSploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|