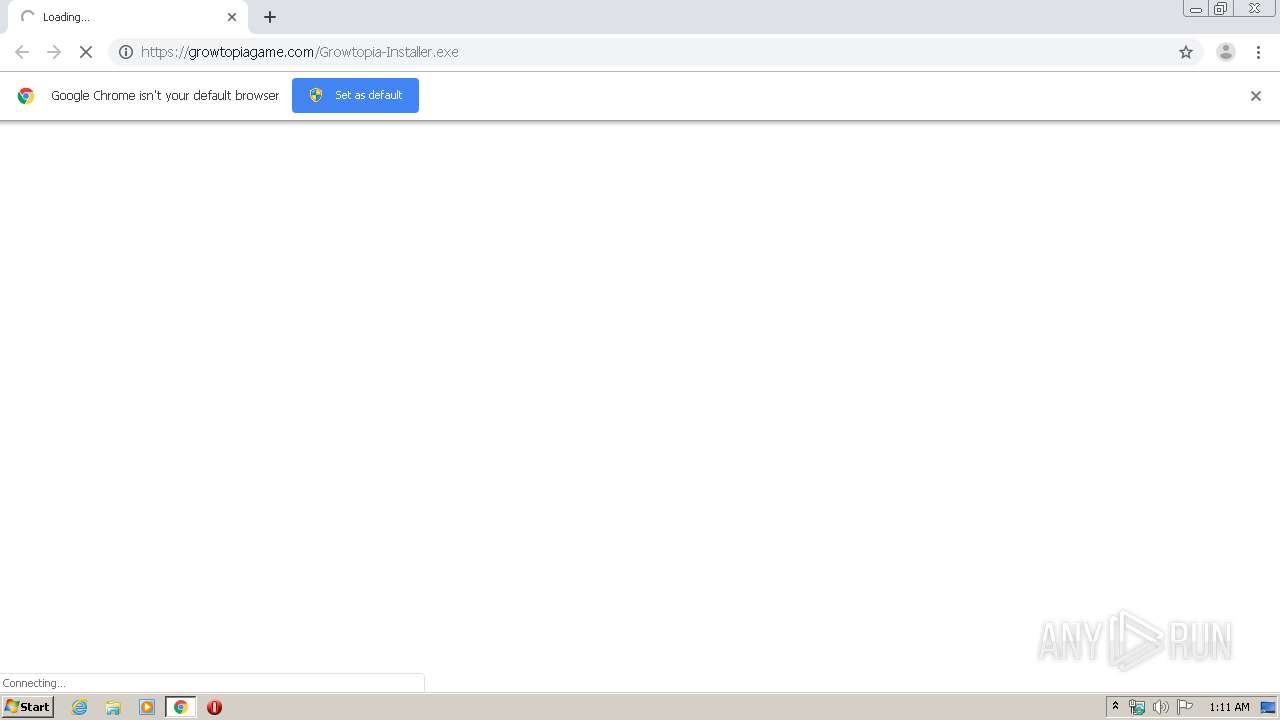
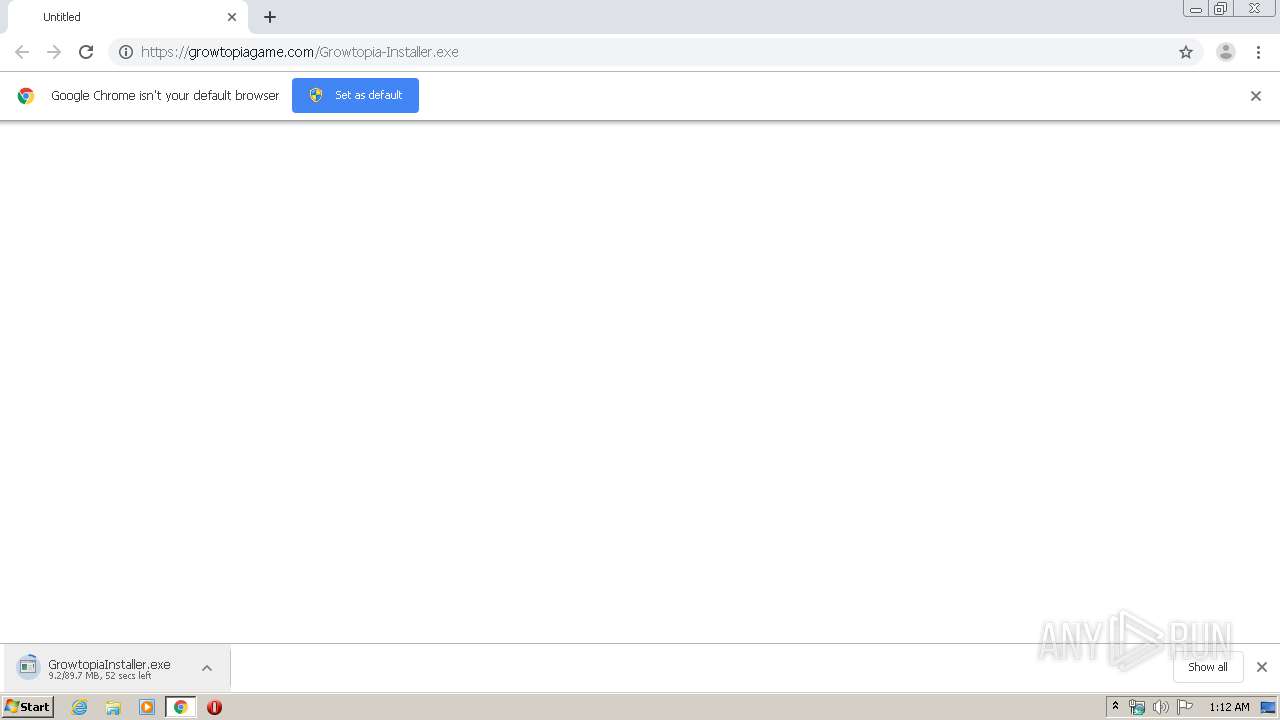
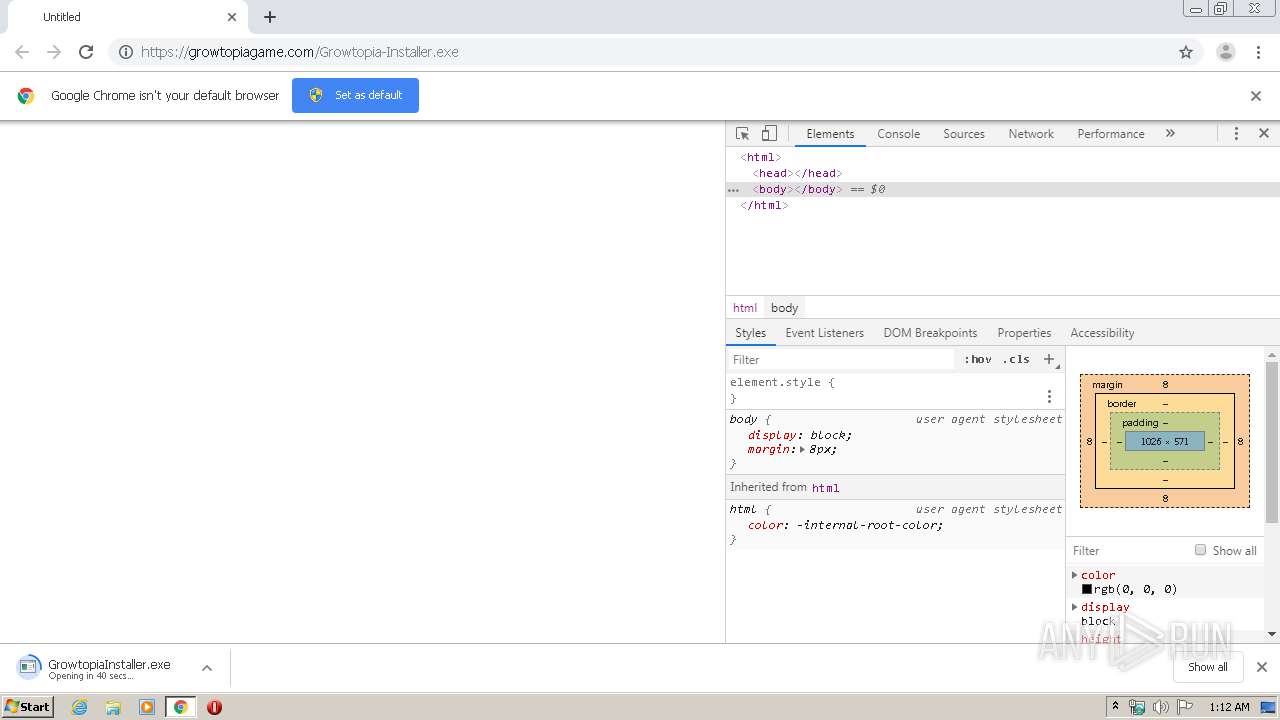
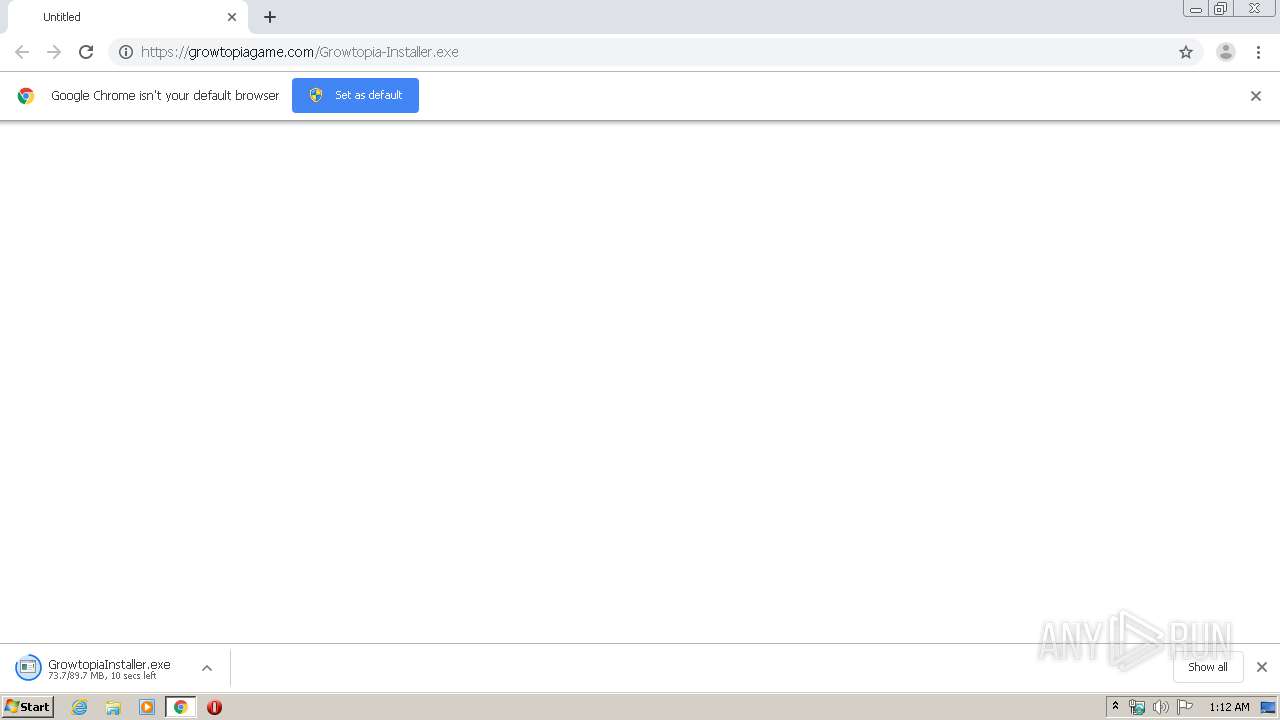
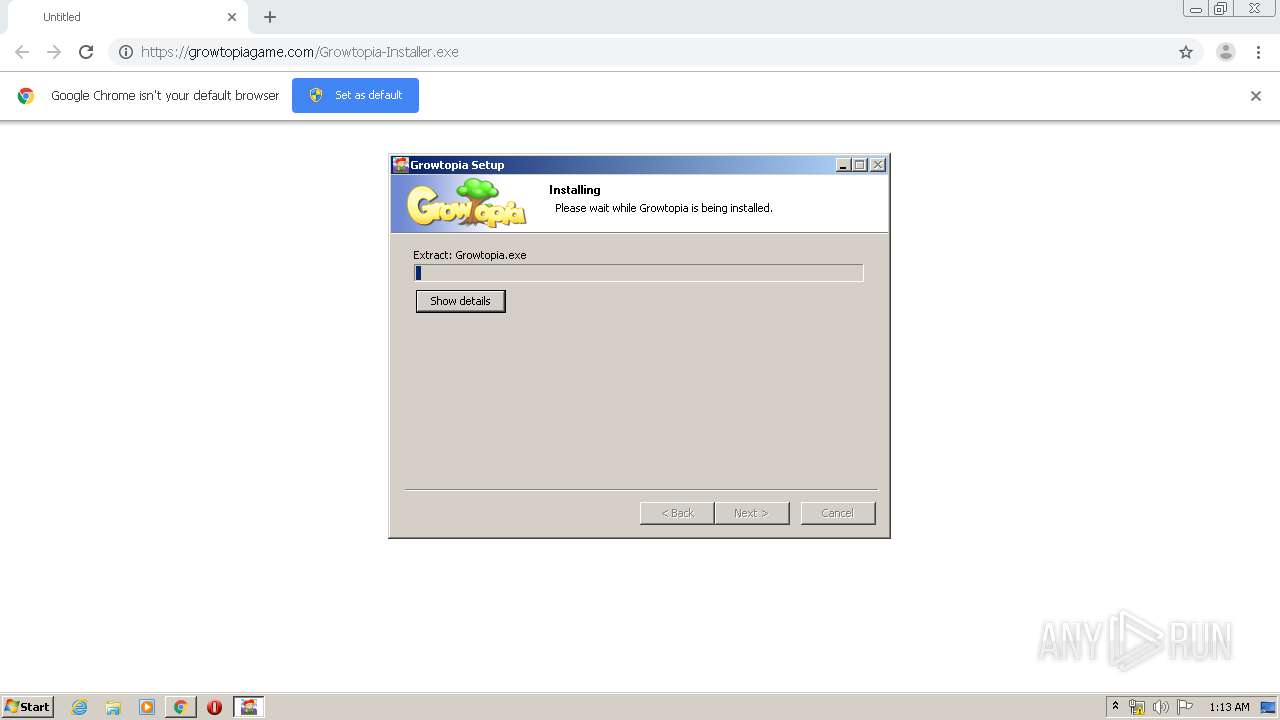
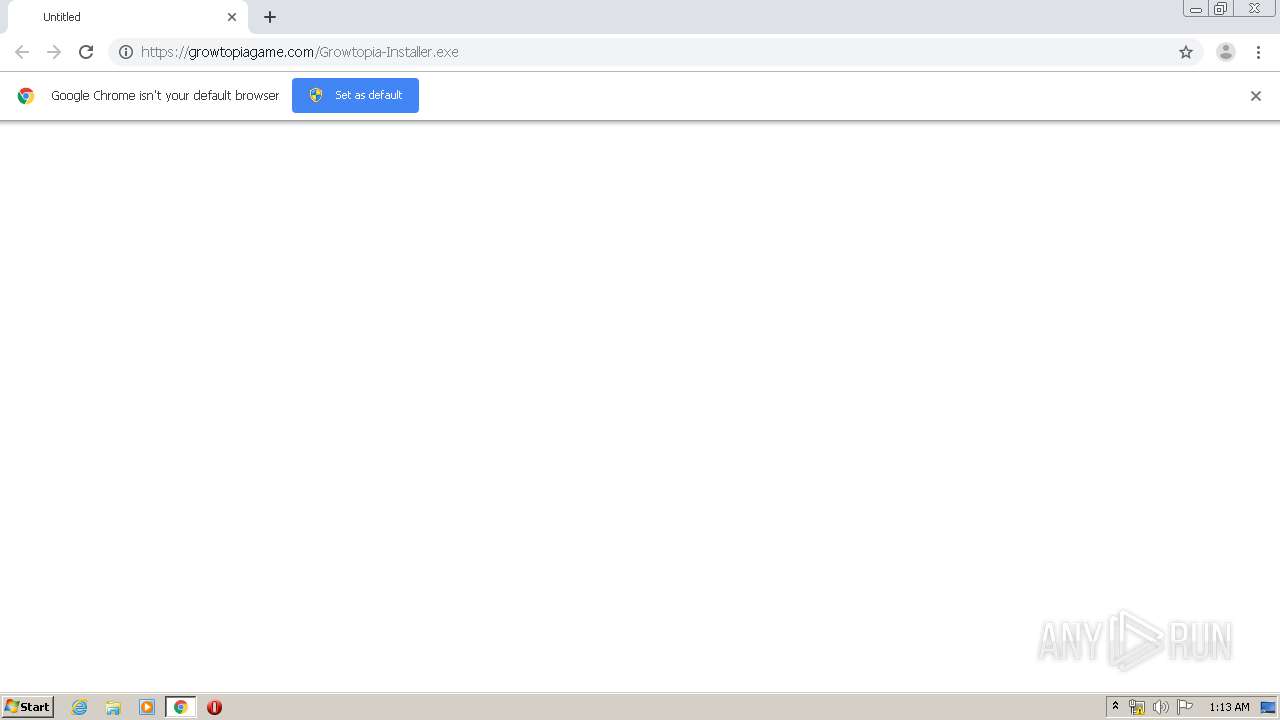
| URL: | https://growtopiagame.com/Growtopia-Installer.exe |
| Full analysis: | https://app.any.run/tasks/c577c746-ce5b-4d34-8361-fe62f64cc2d3 |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2020, 00:11:42 |
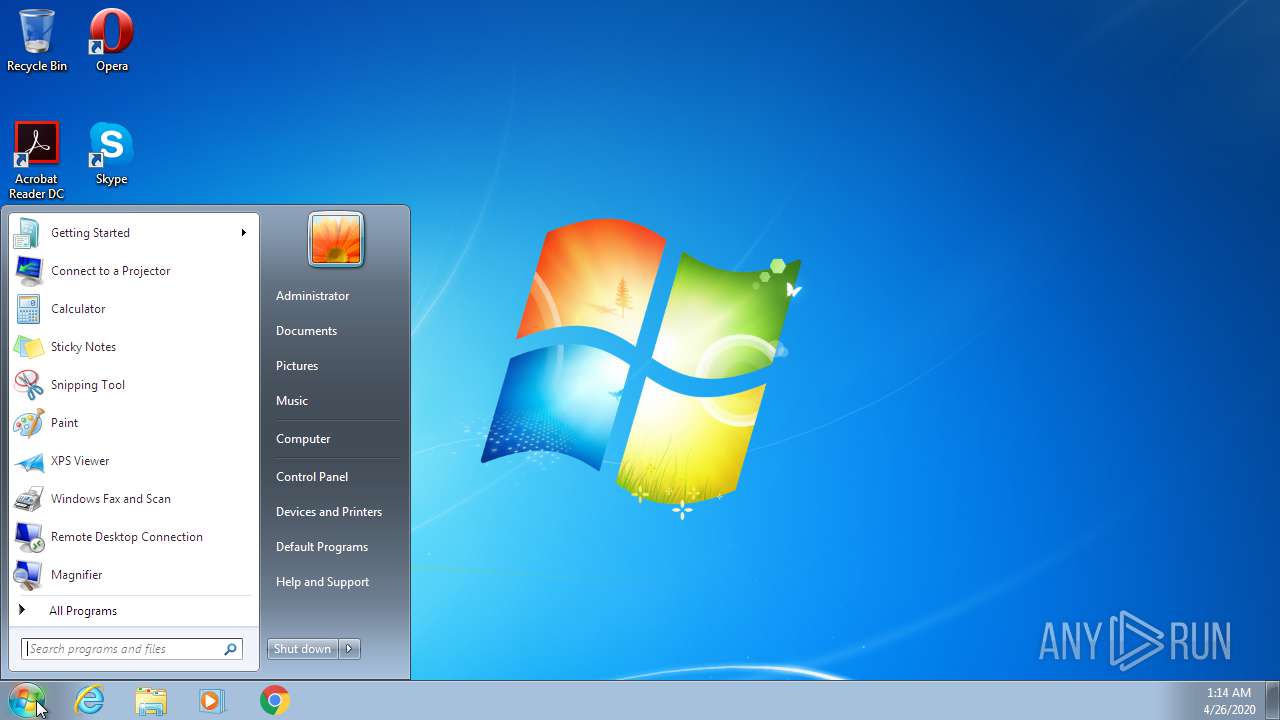
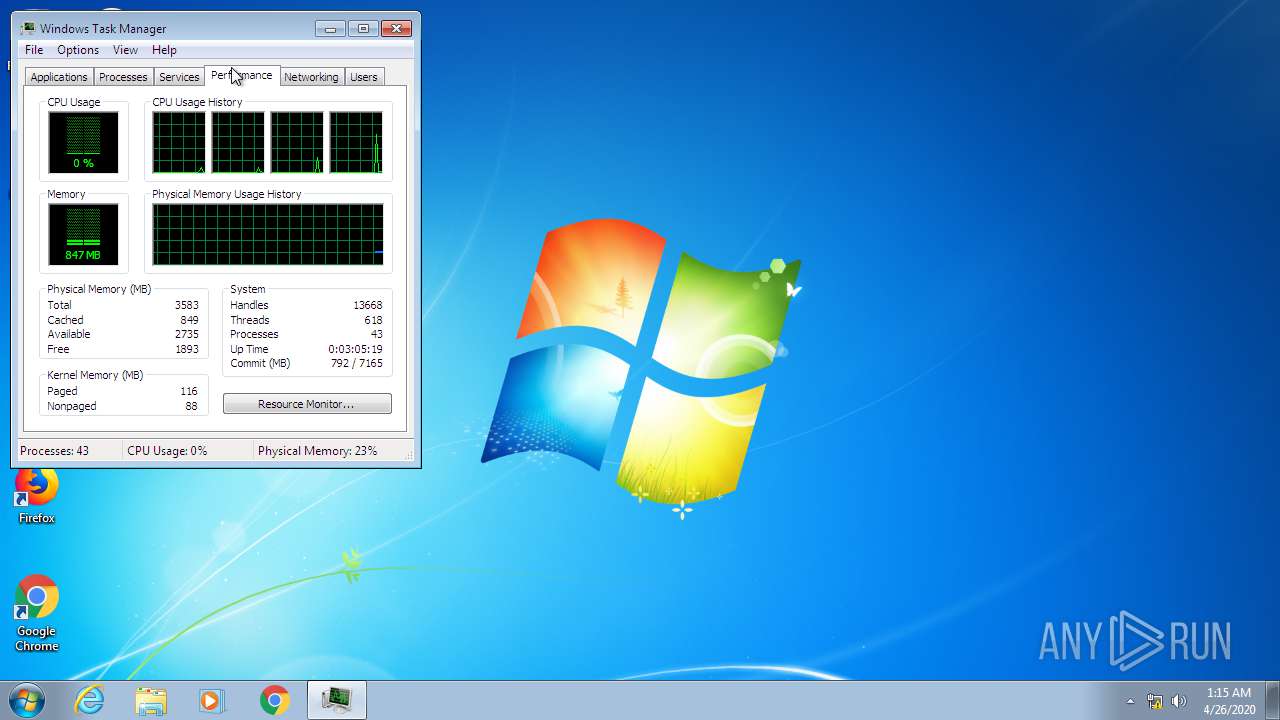
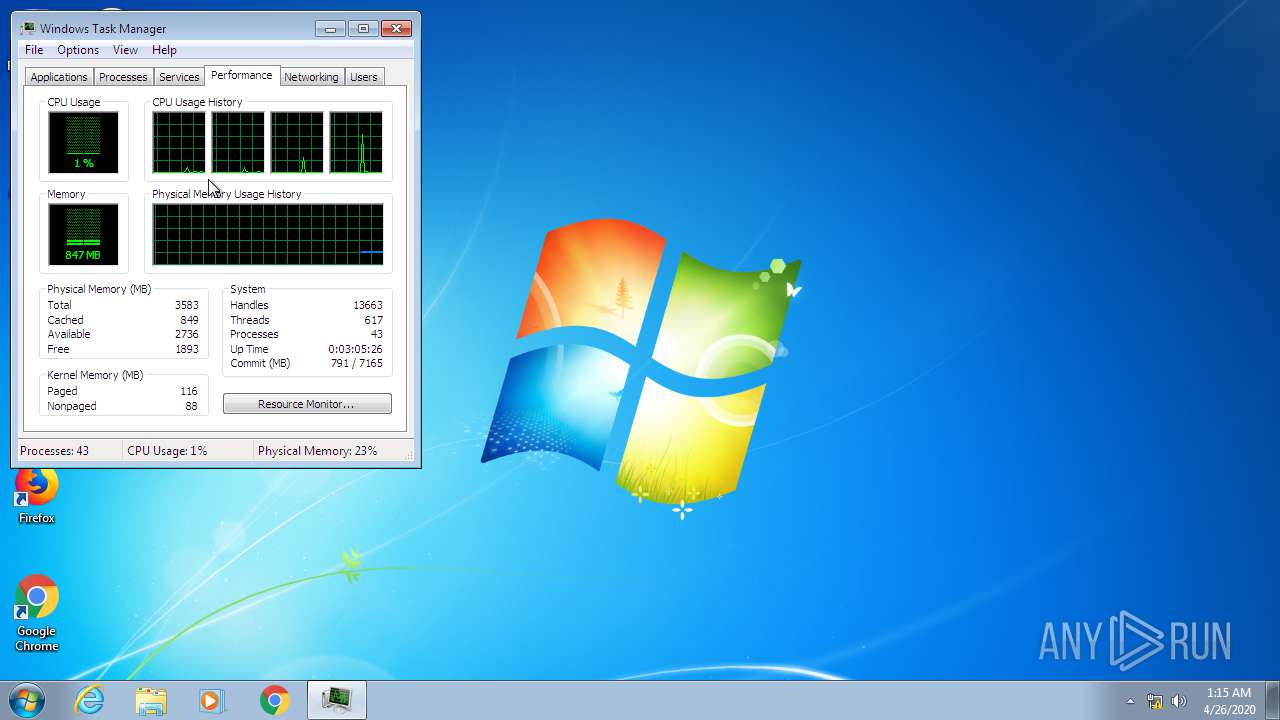
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DD382D3071A99CC93767652C7D47D371 |
| SHA1: | 36597F65683BED2622FA454FF39B1F2DDDDA882C |
| SHA256: | 1974F36BAB006922E15371ED825D12E86E34C4AD7BA1D238276D8EFA48C47532 |
| SSDEEP: | 3:N82KSOeRKztDgXLNn:220yXLN |
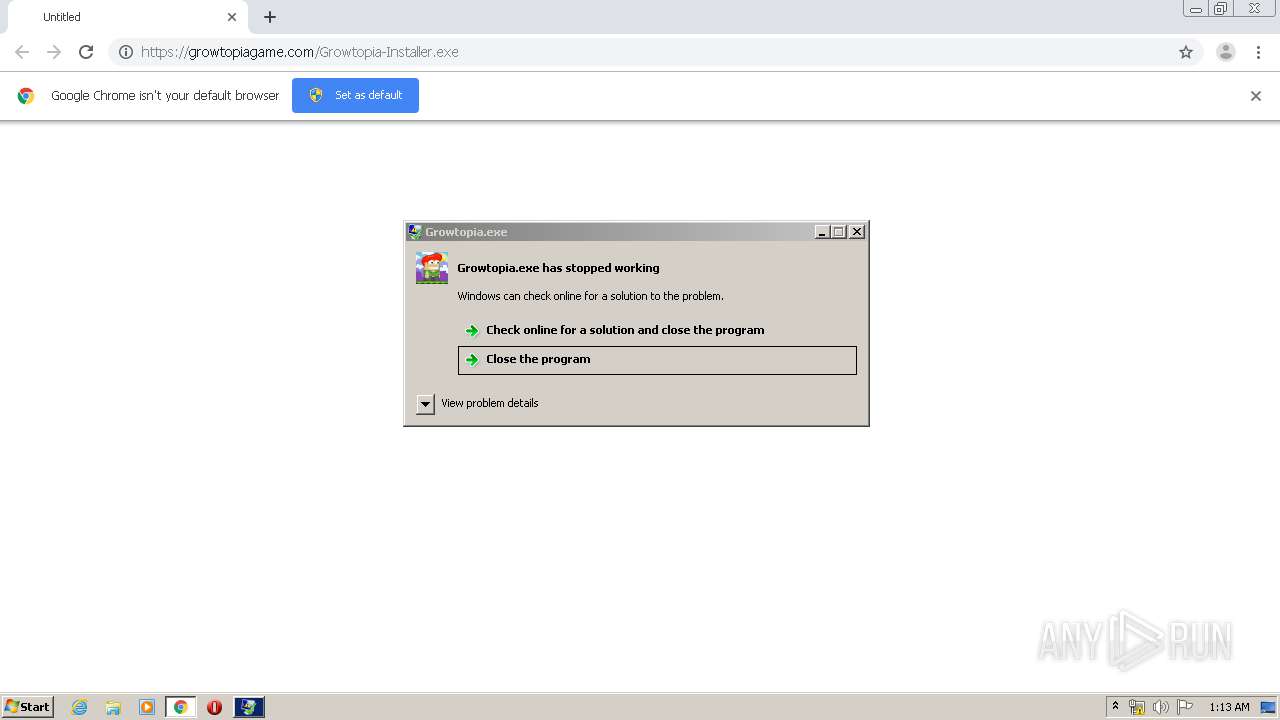
MALICIOUS
Application was dropped or rewritten from another process
- GrowtopiaInstaller.exe (PID: 944)
- Growtopia.exe (PID: 1136)
Loads dropped or rewritten executable
- GrowtopiaInstaller.exe (PID: 944)
- Growtopia.exe (PID: 1136)
- WerFault.exe (PID: 2828)
Changes internet zones settings
- ie4uinit.exe (PID: 2072)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2516)
SUSPICIOUS
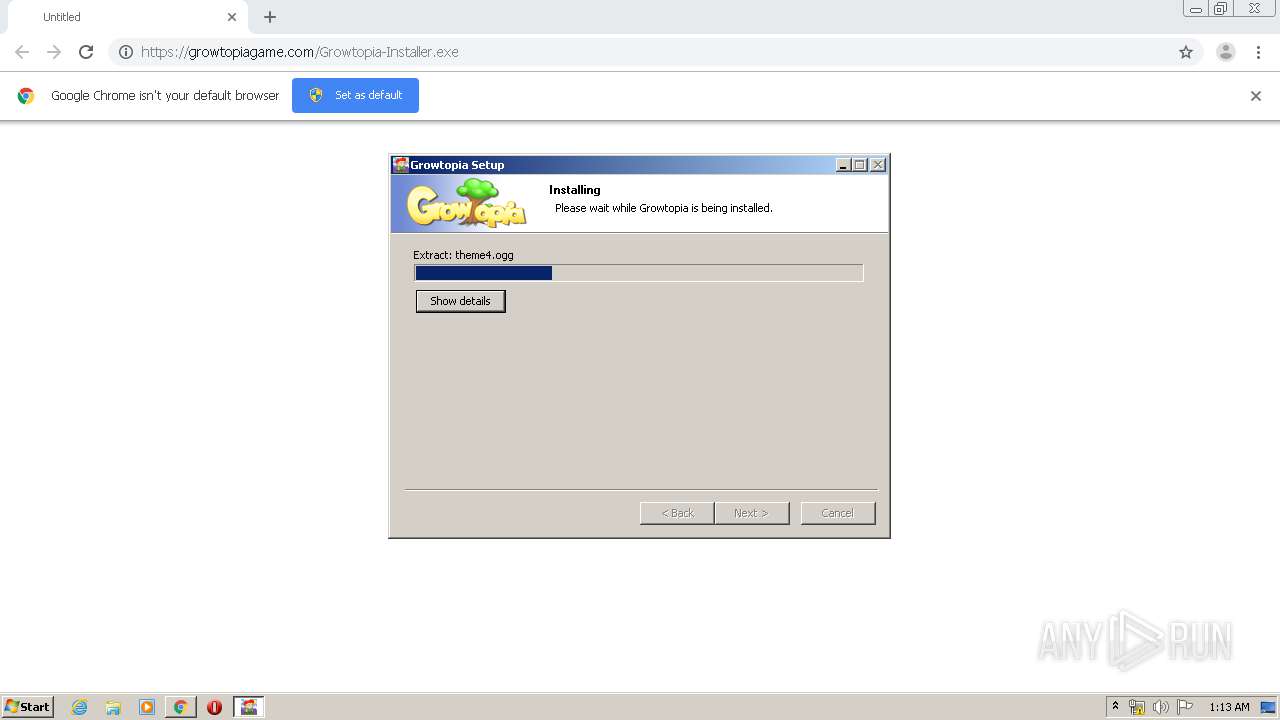
Executable content was dropped or overwritten
- GrowtopiaInstaller.exe (PID: 944)
- chrome.exe (PID: 3312)
Creates a software uninstall entry
- GrowtopiaInstaller.exe (PID: 944)
Creates files in the user directory
- GrowtopiaInstaller.exe (PID: 944)
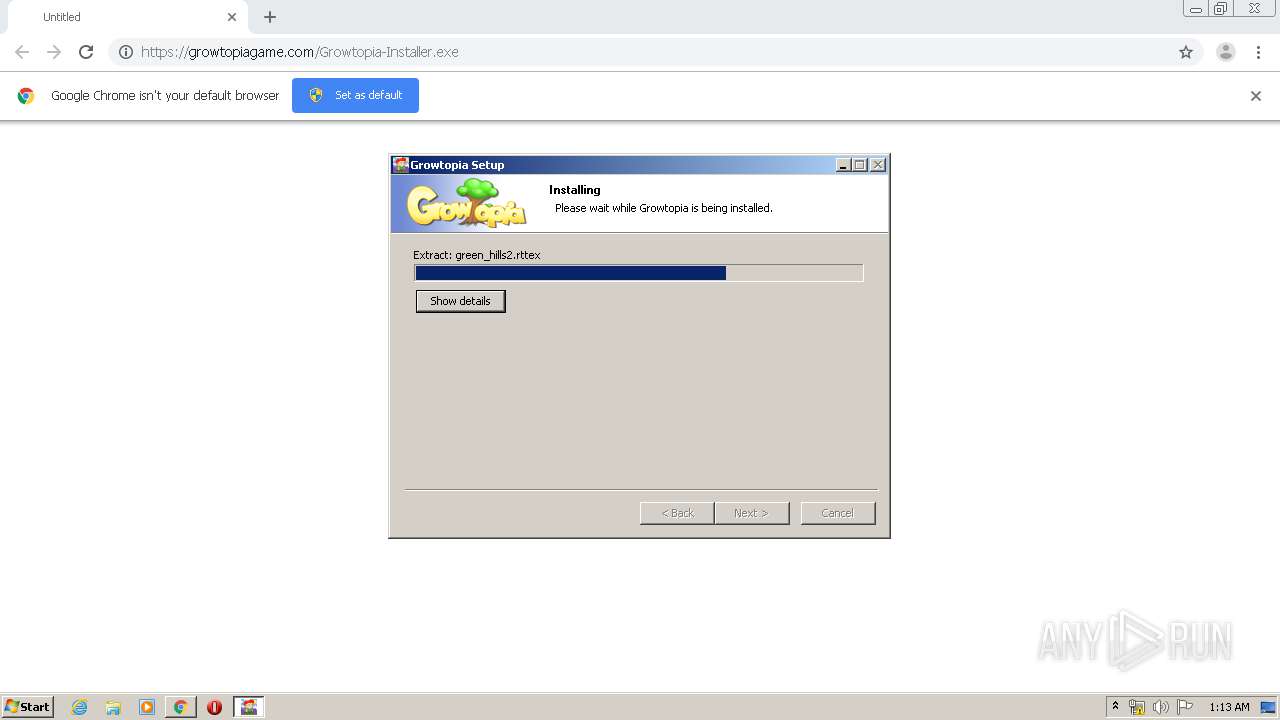
Application launched itself
- rundll32.exe (PID: 2516)
Creates files in the program directory
- ie4uinit.exe (PID: 2072)
- chrmstp.exe (PID: 4000)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 2516)
- ie4uinit.exe (PID: 2072)
Executed as Windows Service
- taskhost.exe (PID: 3988)
Reads Internet Cache Settings
- taskhost.exe (PID: 3988)
- ie4uinit.exe (PID: 2072)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 2072)
INFO
Reads the hosts file
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3312)
Reads Internet Cache Settings
- chrome.exe (PID: 3312)
Dropped object may contain Bitcoin addresses
- GrowtopiaInstaller.exe (PID: 944)
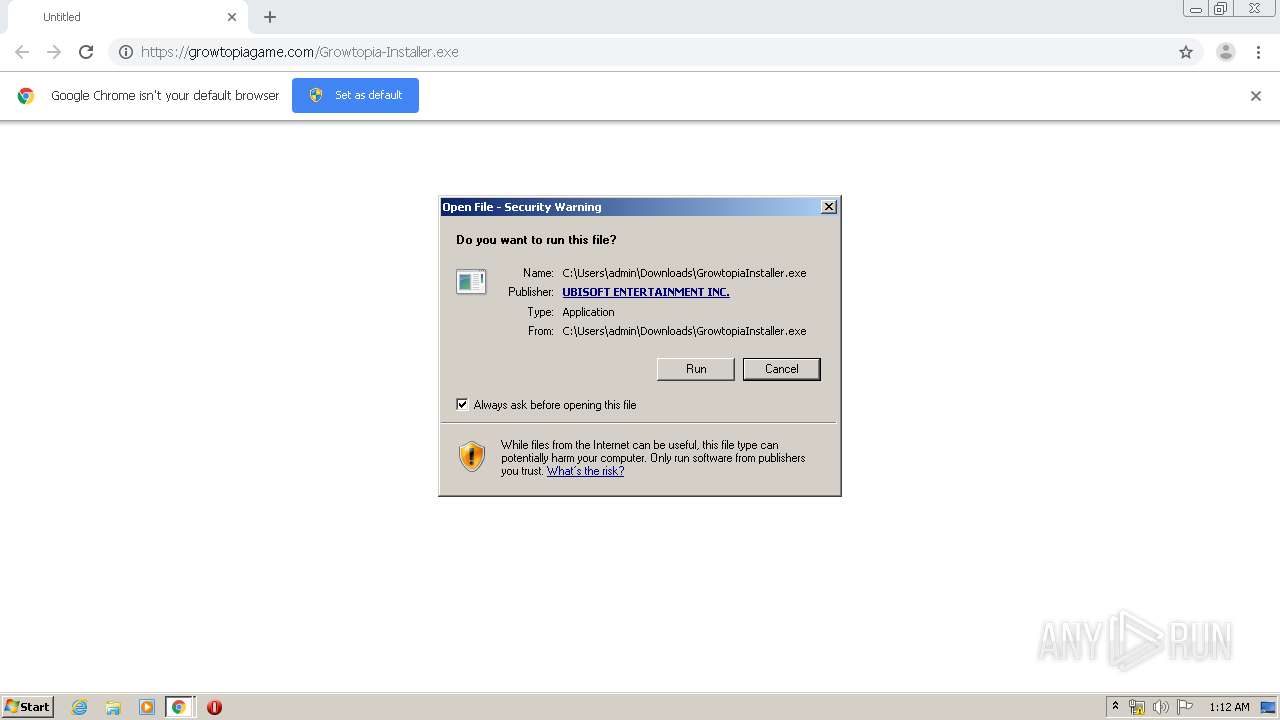
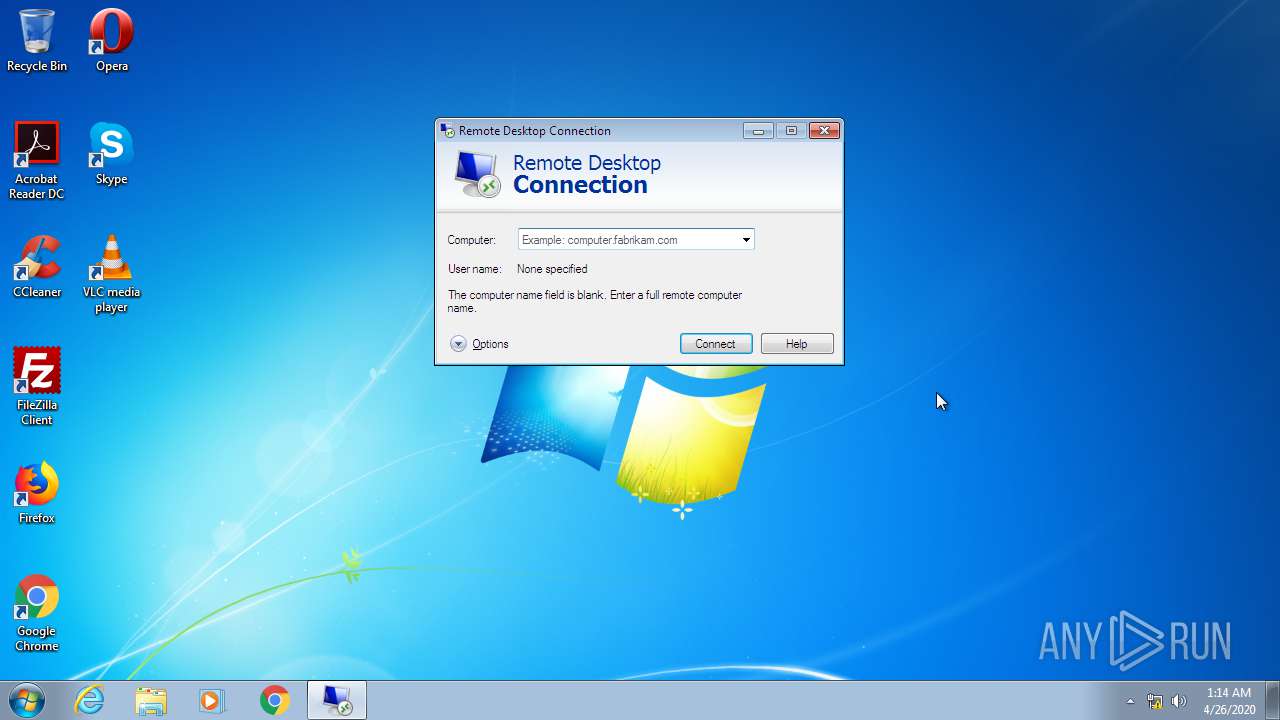
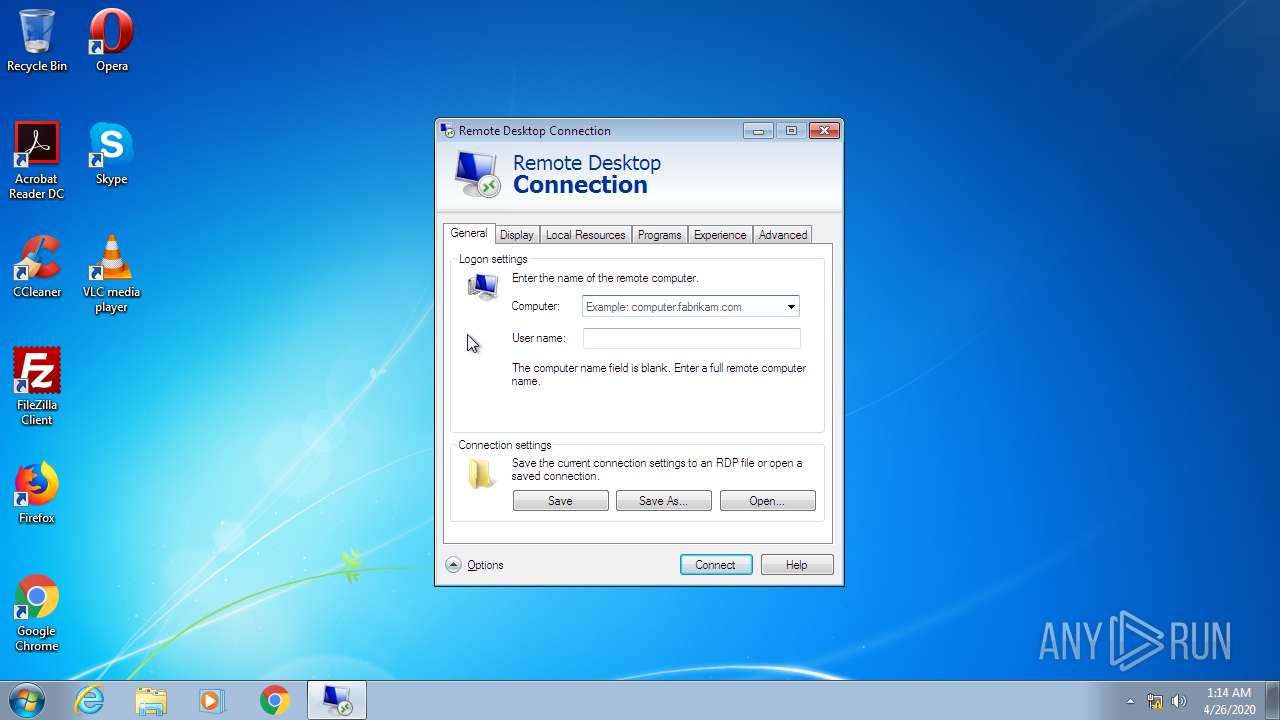
Manual execution by user
- chrmstp.exe (PID: 4000)
- ie4uinit.exe (PID: 2072)
- IMEKLMG.EXE (PID: 1740)
- IMEKLMG.EXE (PID: 2796)
- ie4uinit.exe (PID: 2896)
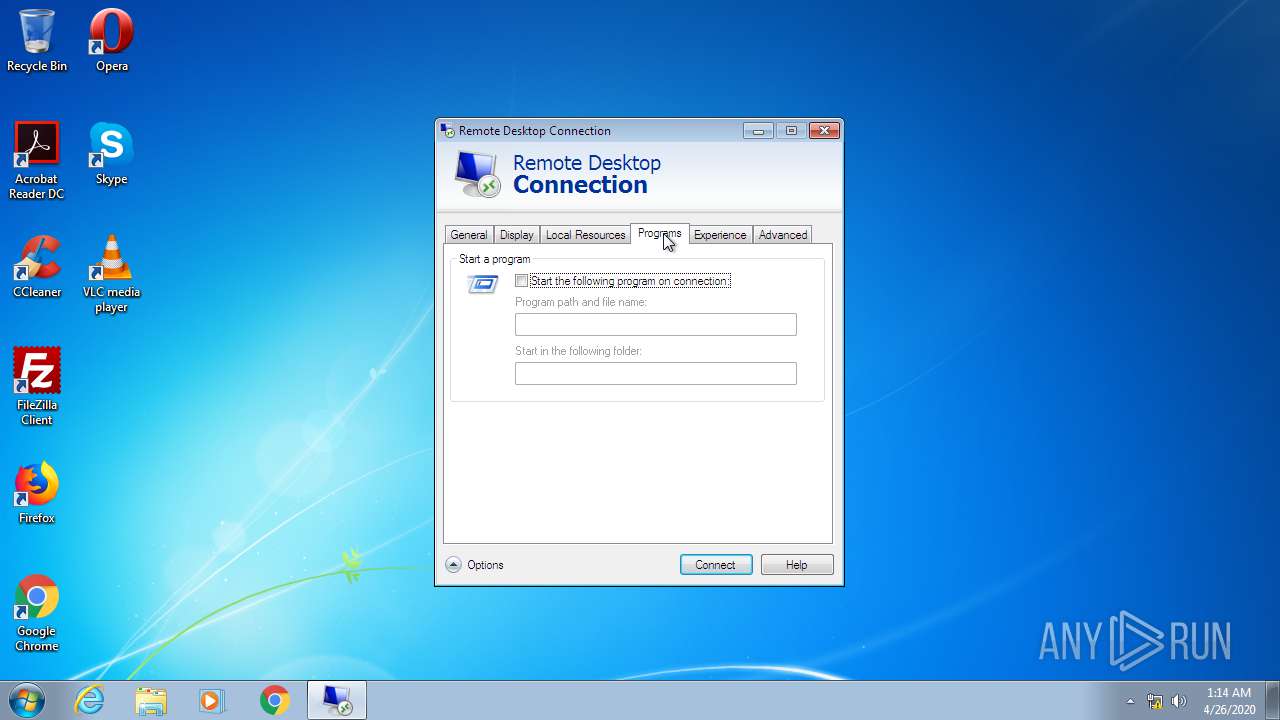
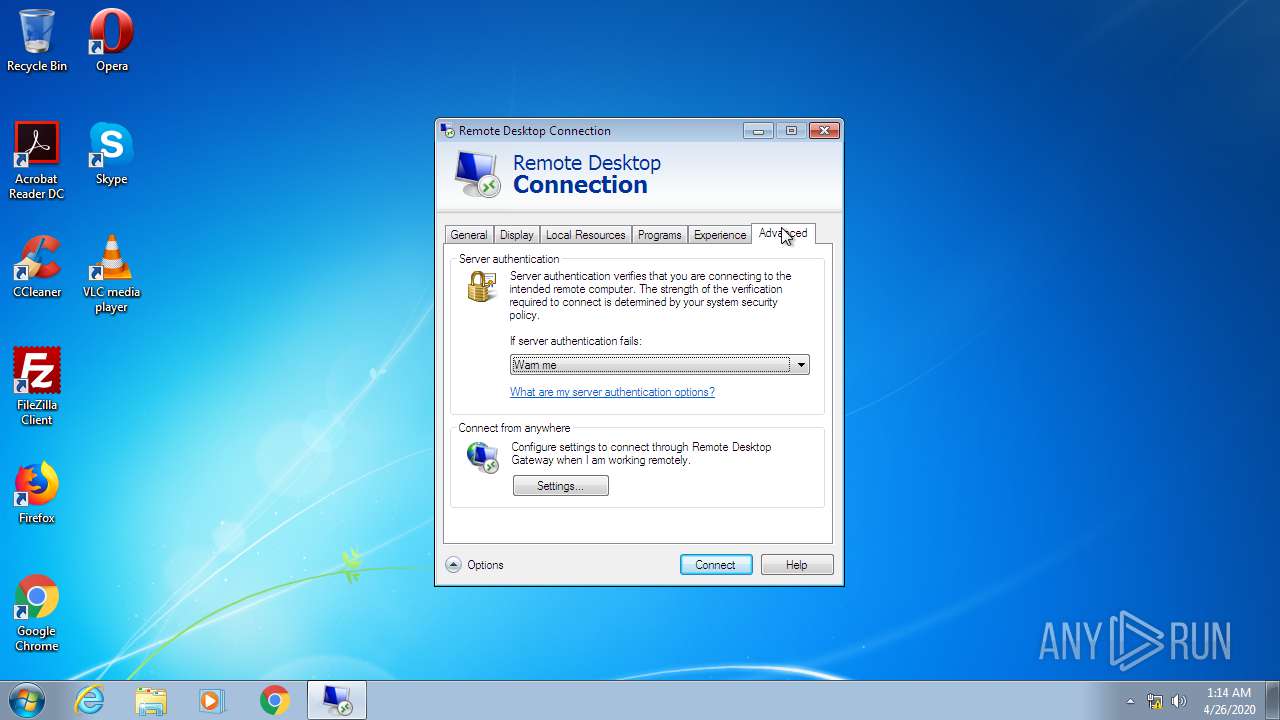
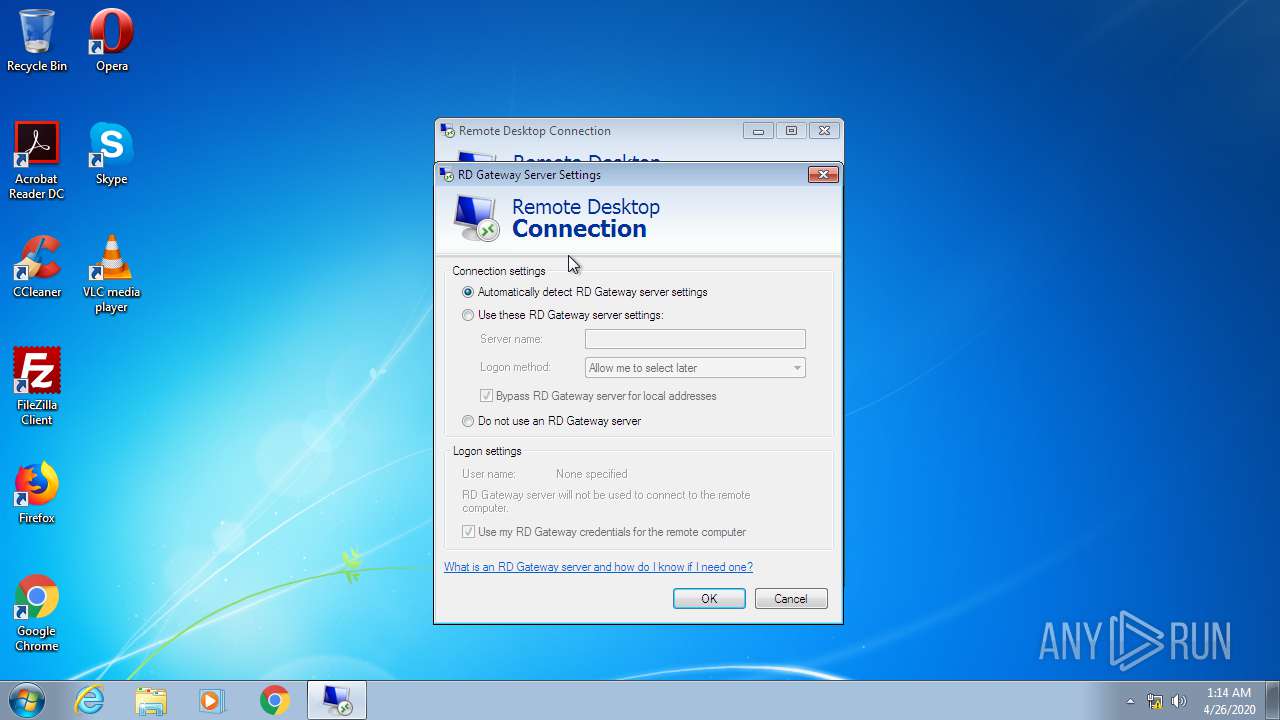
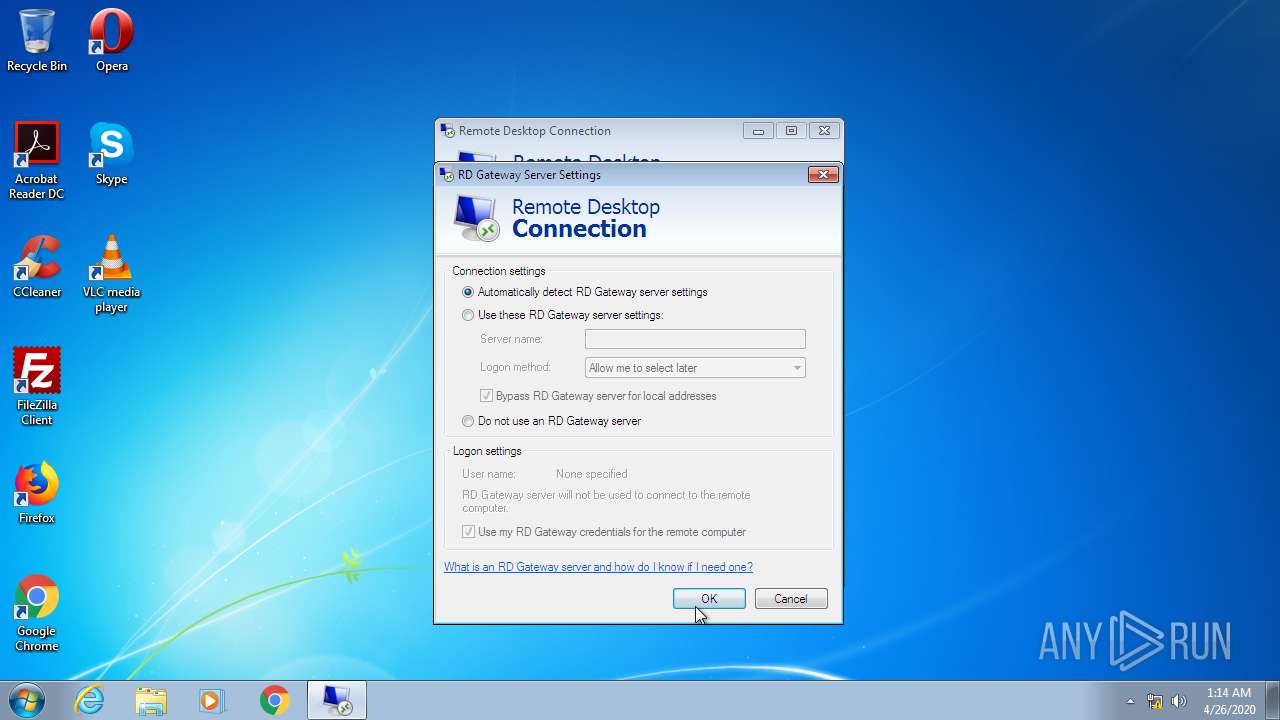
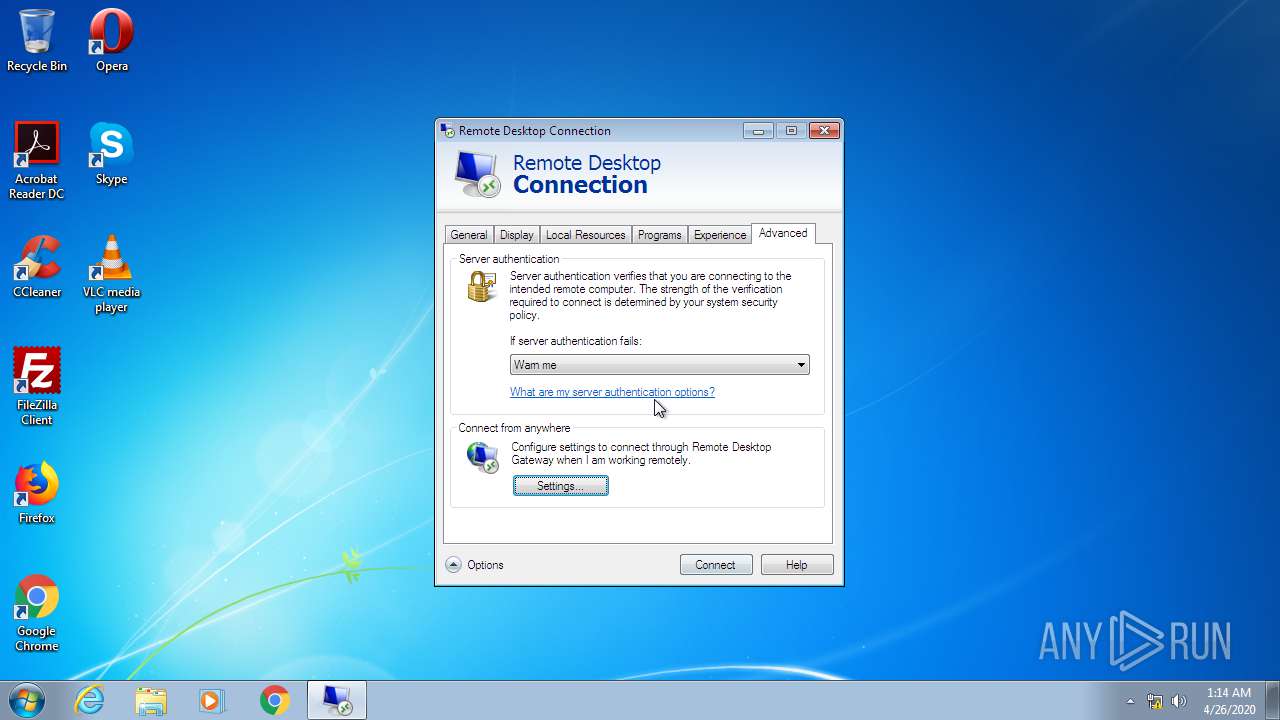
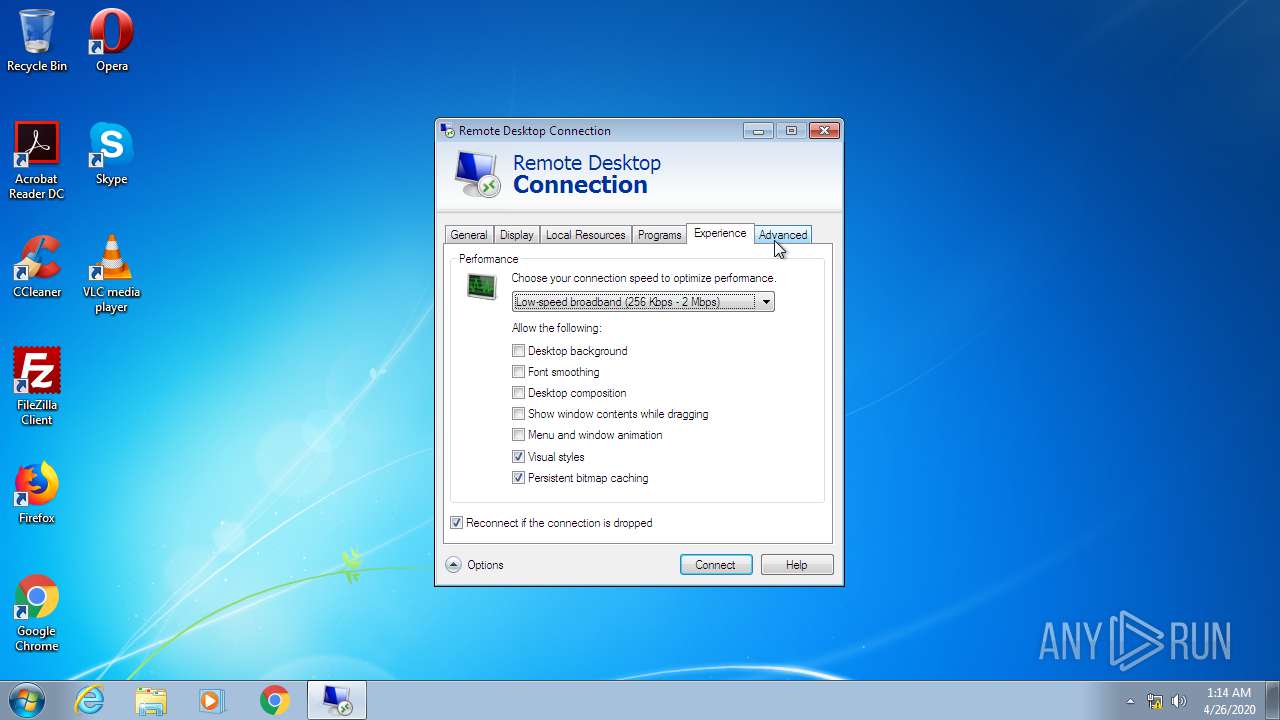
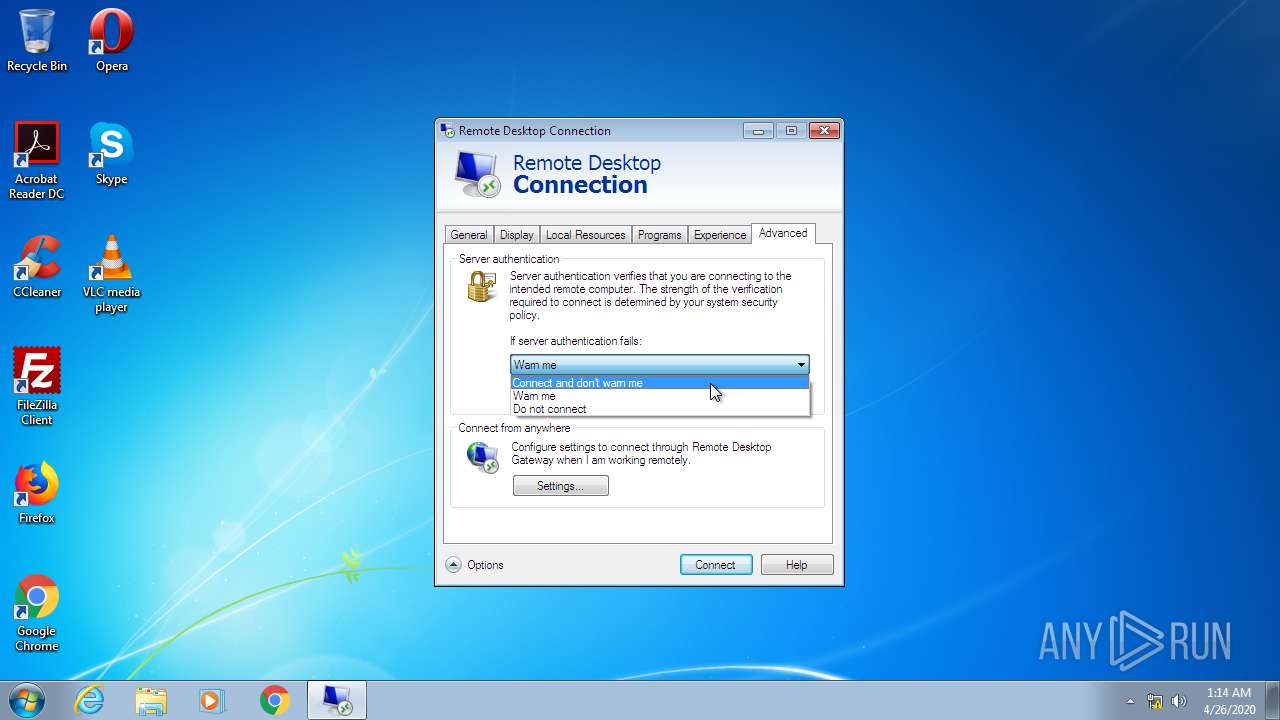
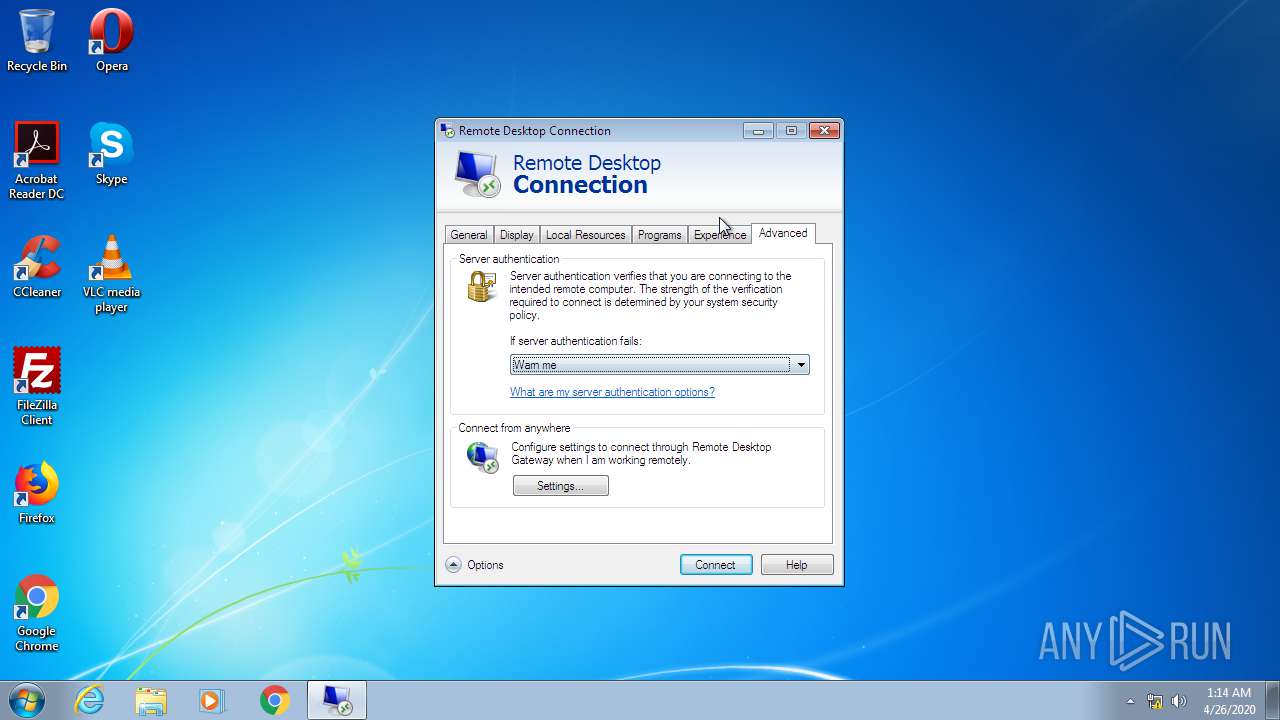
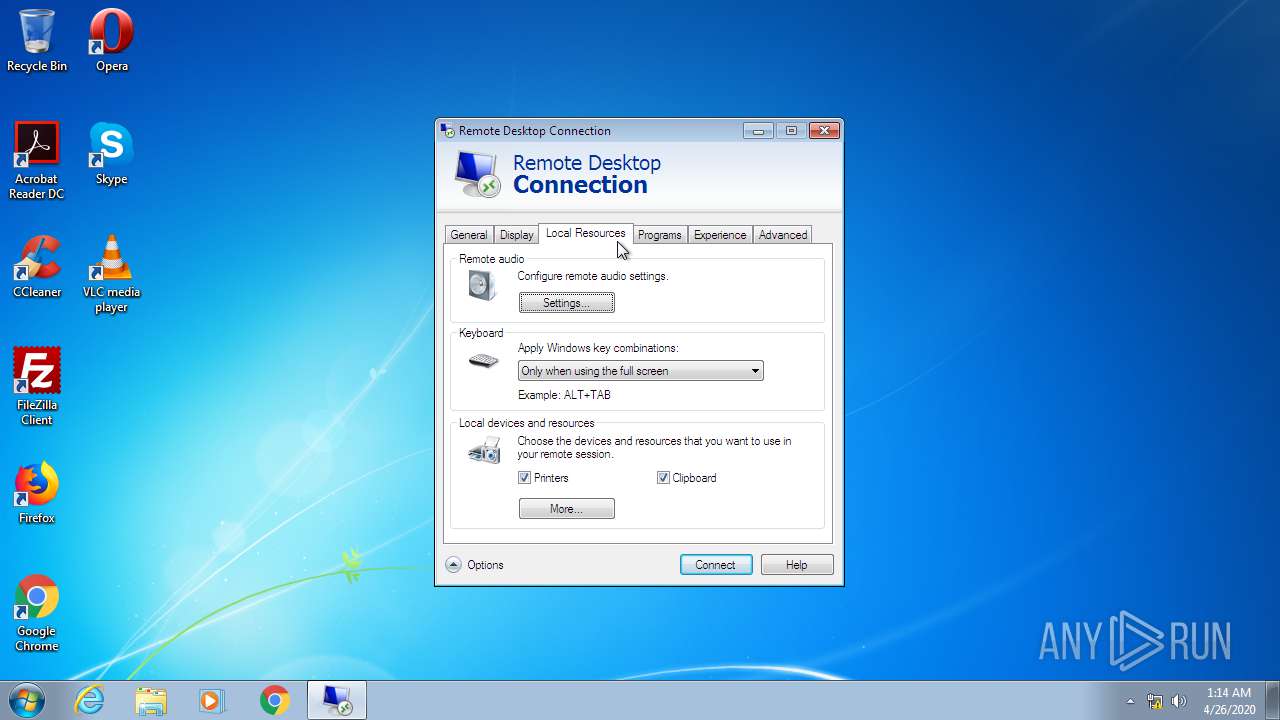
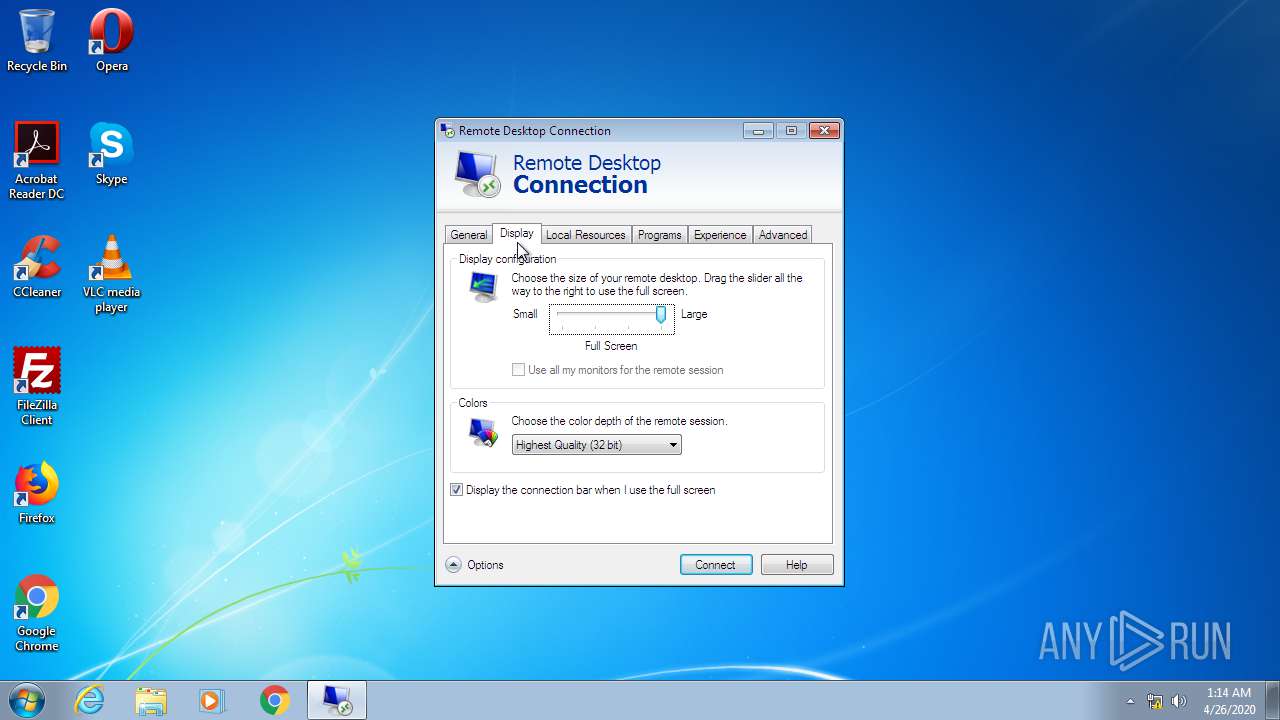
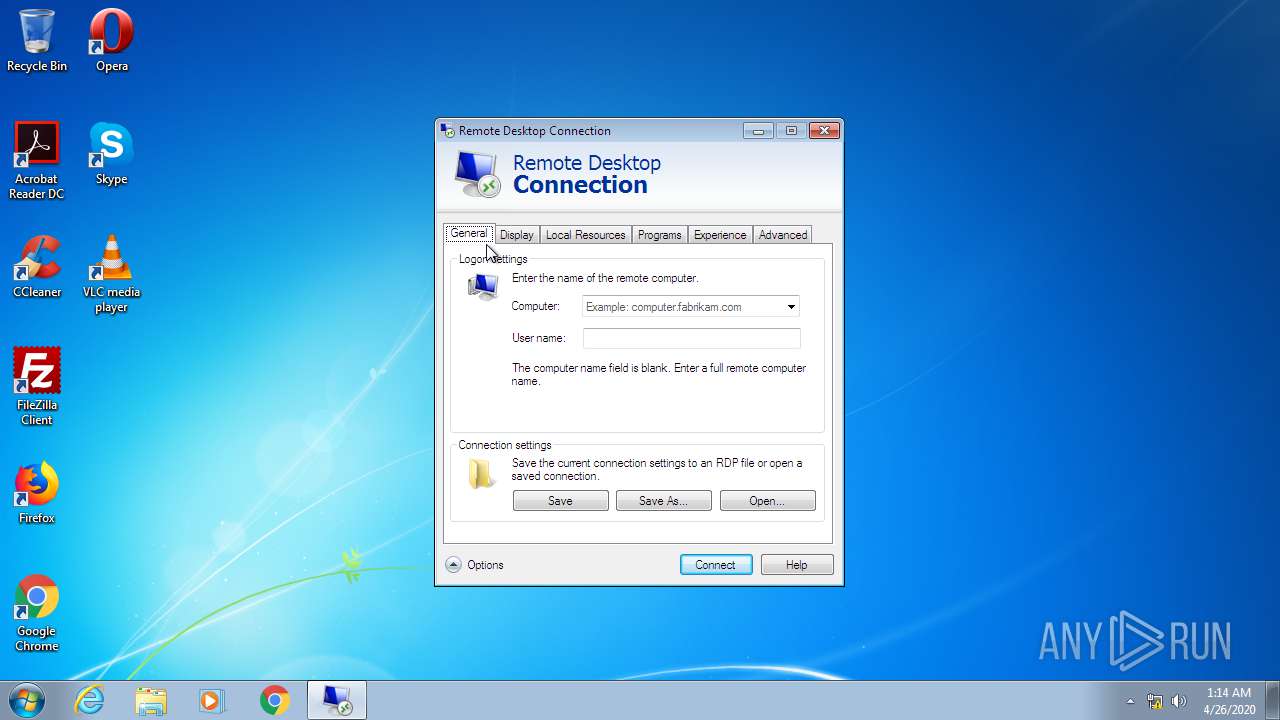
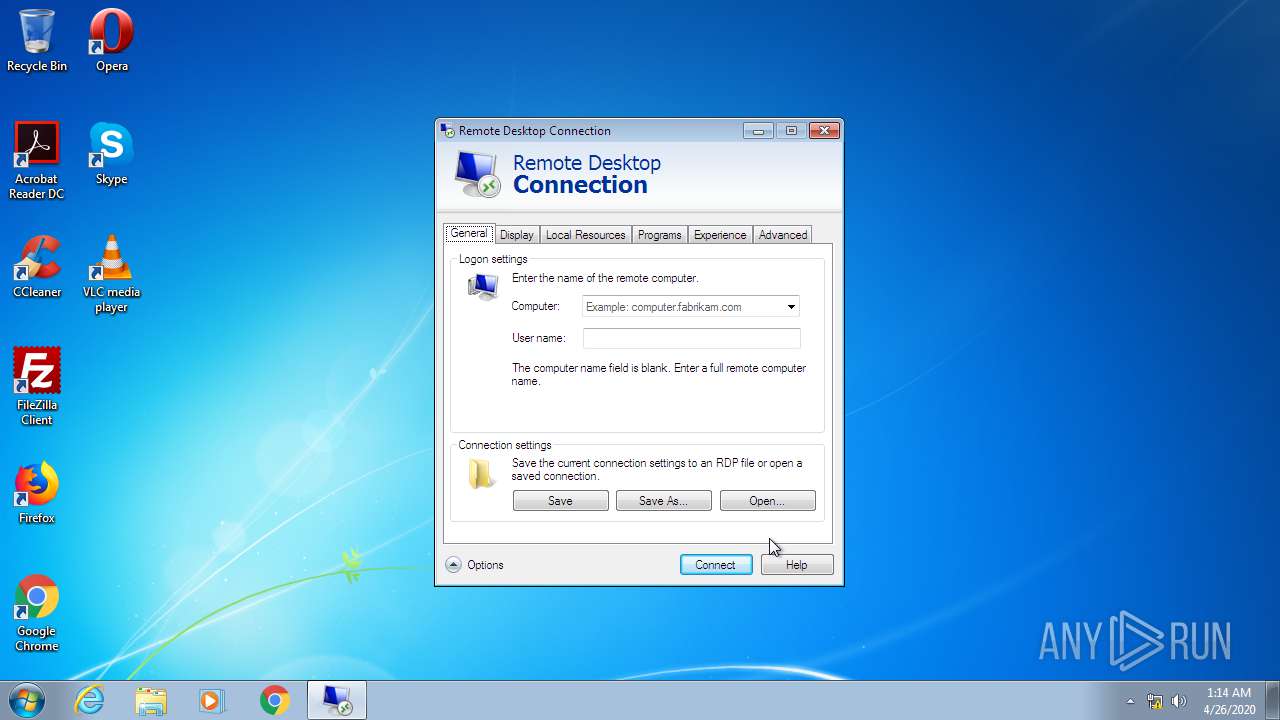
- mstsc.exe (PID: 1716)
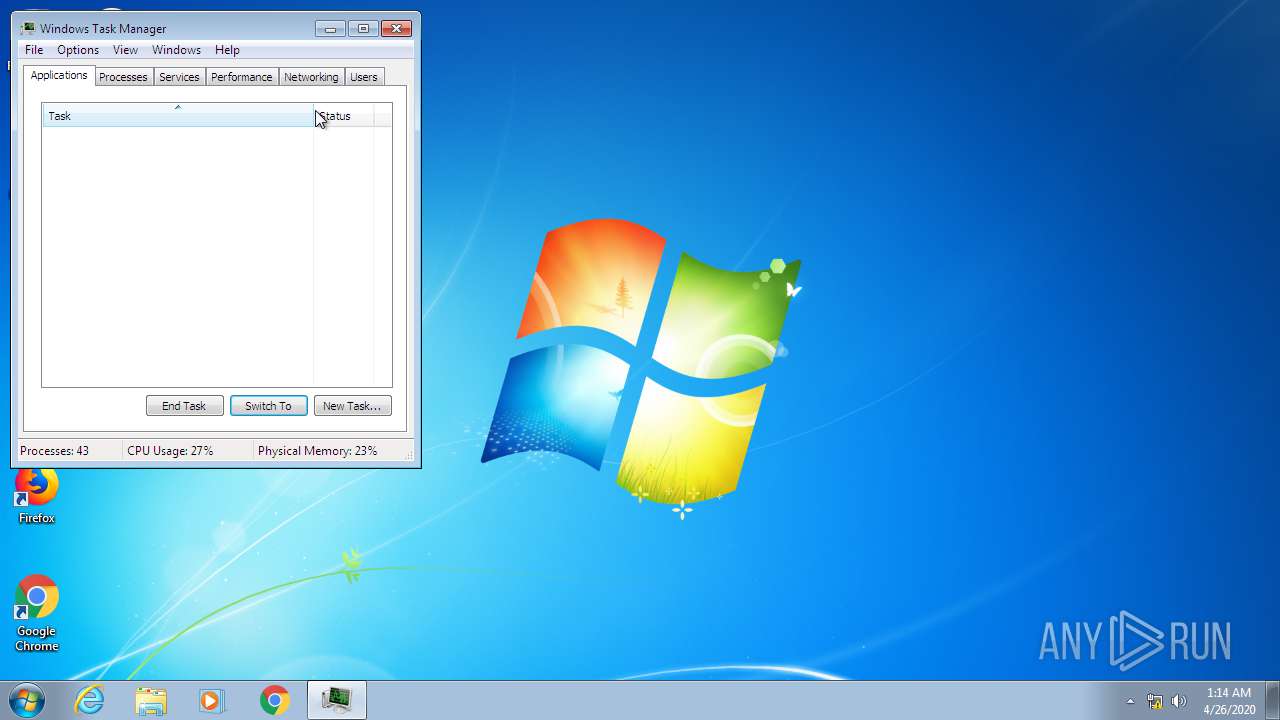
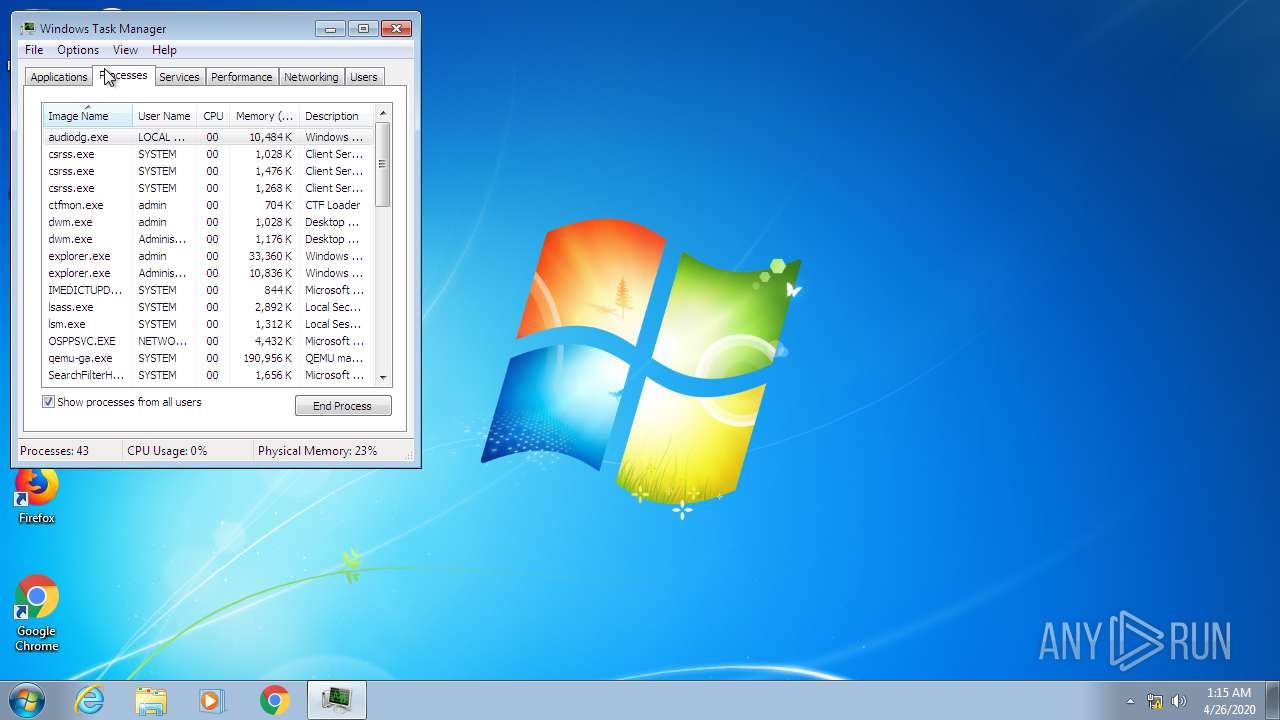
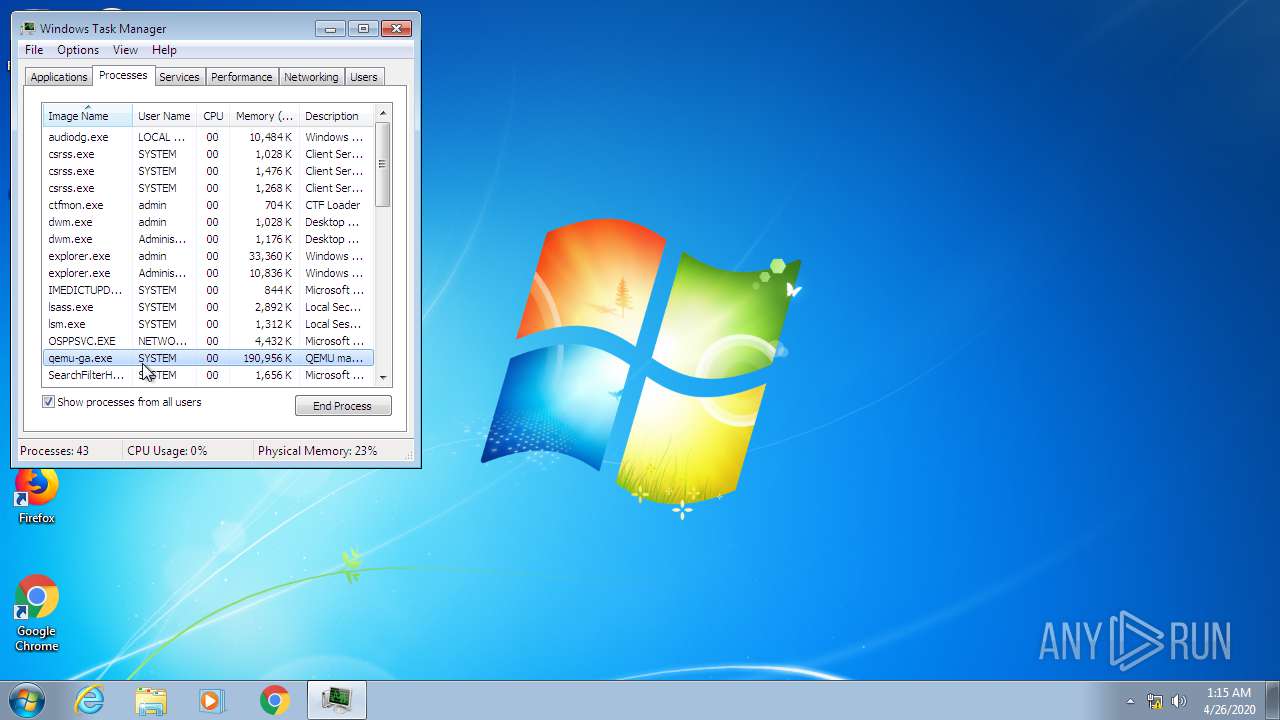
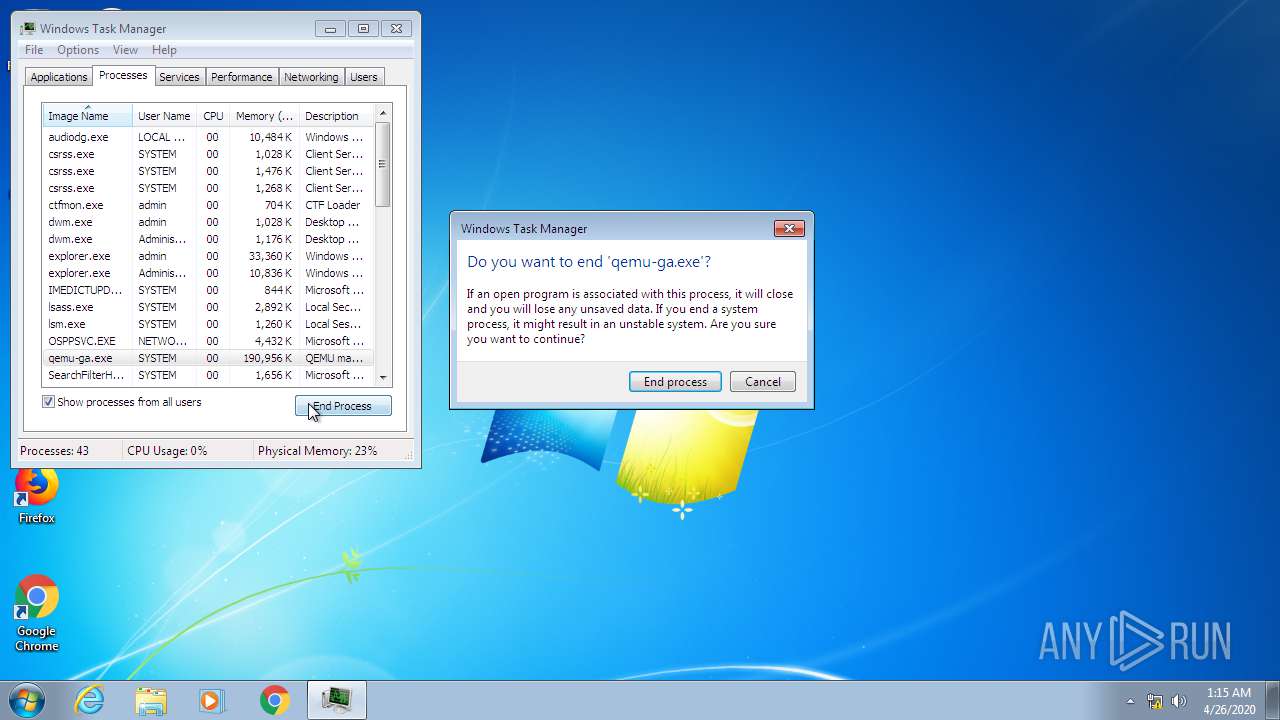
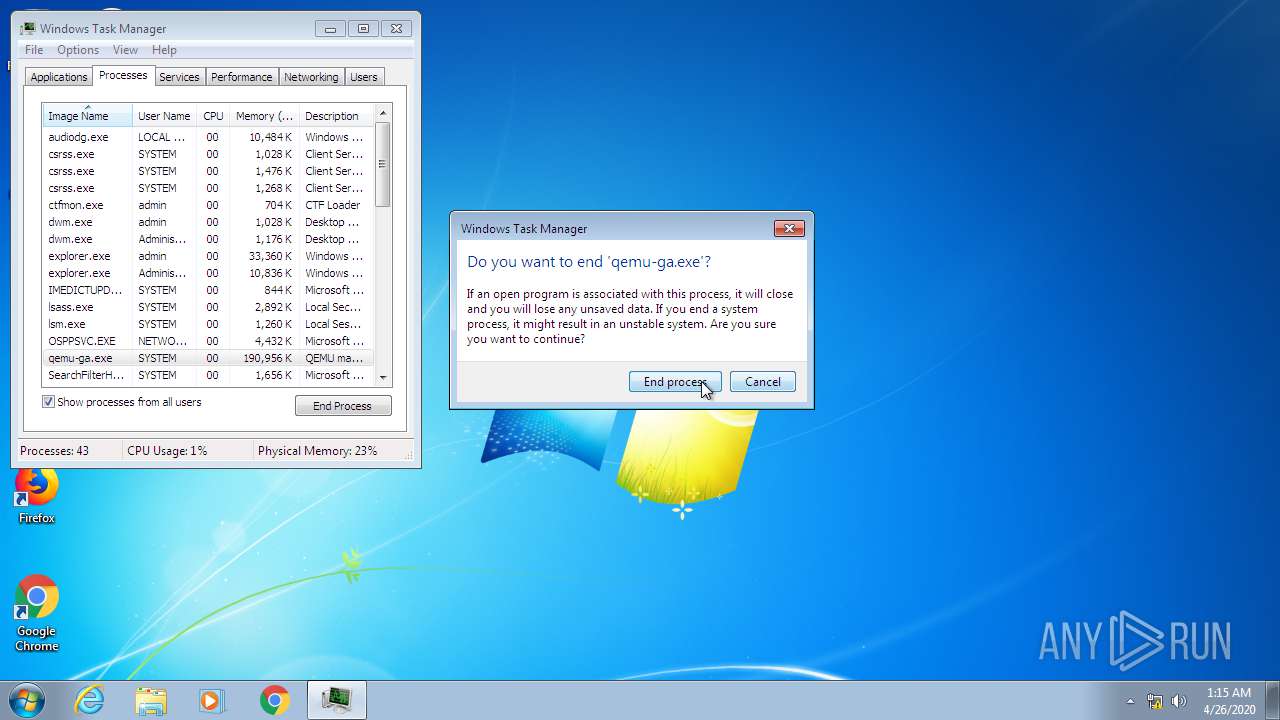
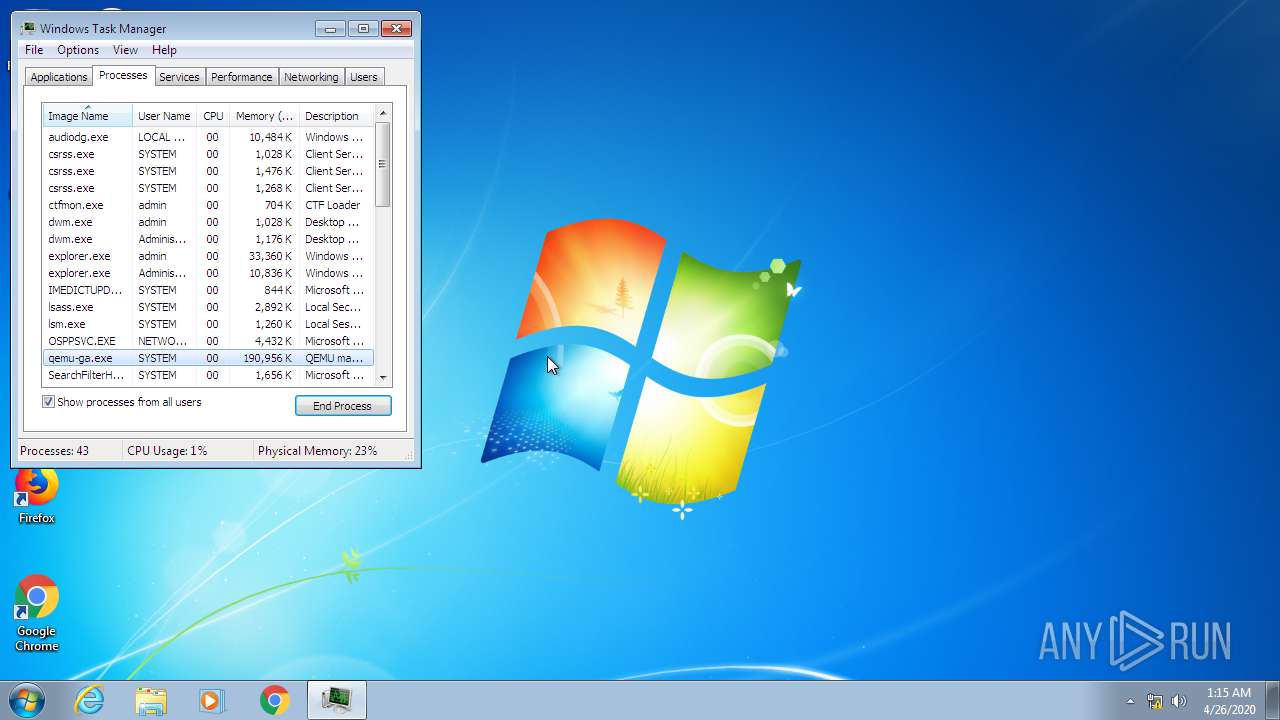
- taskmgr.exe (PID: 3404)
Application launched itself
- chrome.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
81
Monitored processes
31
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Users\admin\Downloads\GrowtopiaInstaller.exe" | C:\Users\admin\Downloads\GrowtopiaInstaller.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
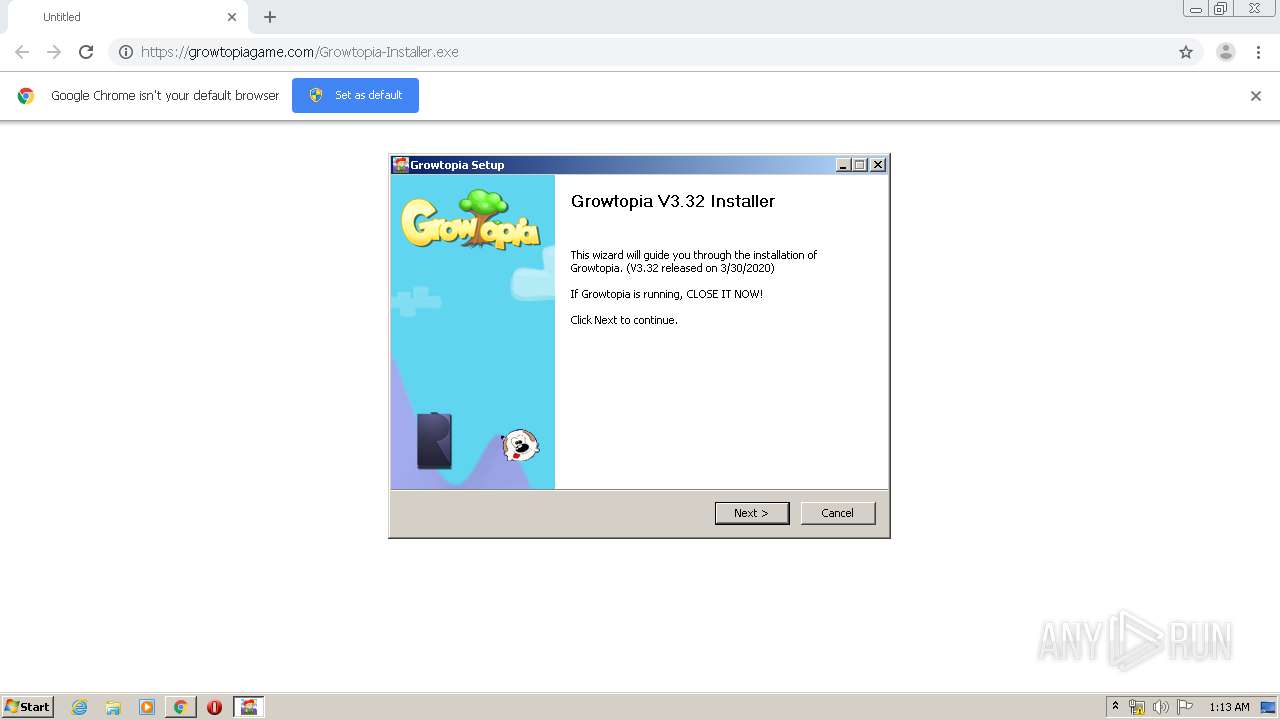
| 1136 | "C:\Users\admin\AppData\Local\Growtopia\Growtopia.exe" | C:\Users\admin\AppData\Local\Growtopia\Growtopia.exe | GrowtopiaInstaller.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=118112989606521677 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1716 | "C:\Windows\system32\mstsc.exe" | C:\Windows\system32\mstsc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\ie4uinit.exe" -UserConfig | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2248 | C:\Windows\System32\ie4uinit.exe -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13440275480388337144 --mojo-platform-channel-handle=3084 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,18099977384310483853,10735150176943137288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10827978163735605483 --mojo-platform-channel-handle=3228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 988
Read events
1 601
Write events
380
Delete events
7
Modification events
| (PID) Process: | (3680) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3312-13232333517480125 |
Value: 259 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3312) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
34
Text files
195
Unknown types
1 563
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EA4D1CD-CF0.pma | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fae56be7-a4c2-4acf-9ff6-98e8a2a6f673.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa6e2e6.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa6e2e6.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e1ec.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e353.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
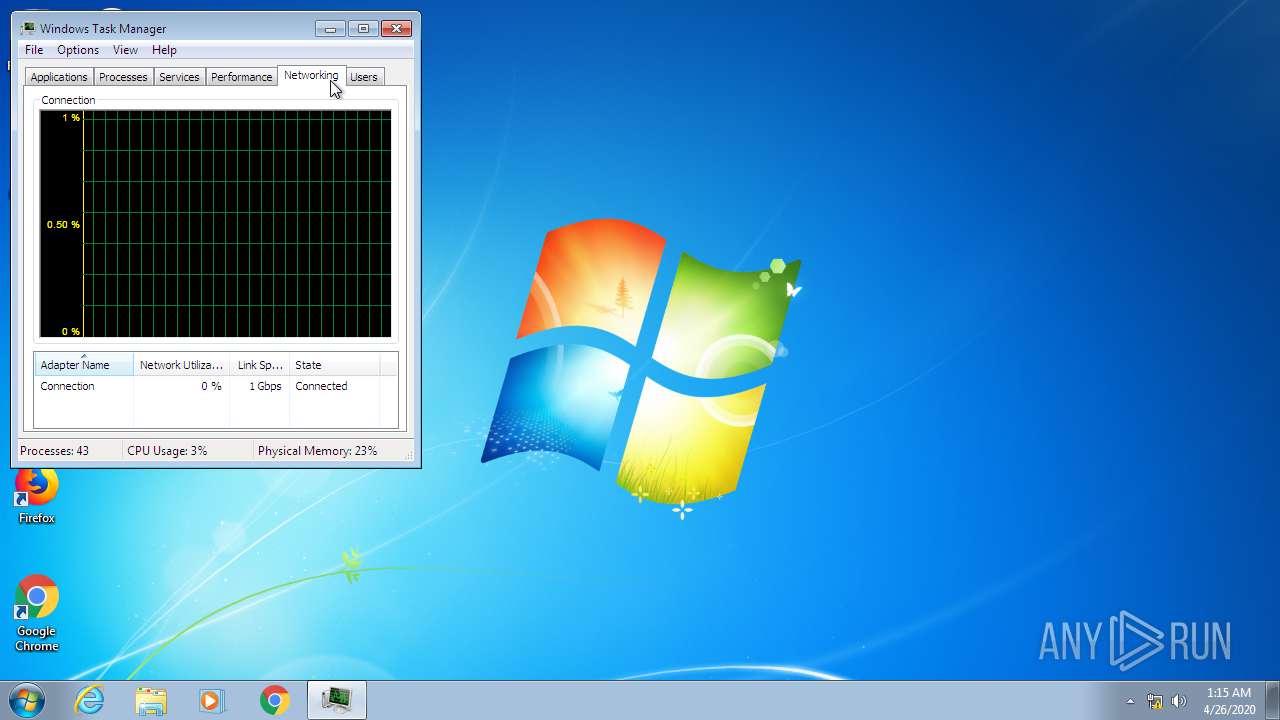
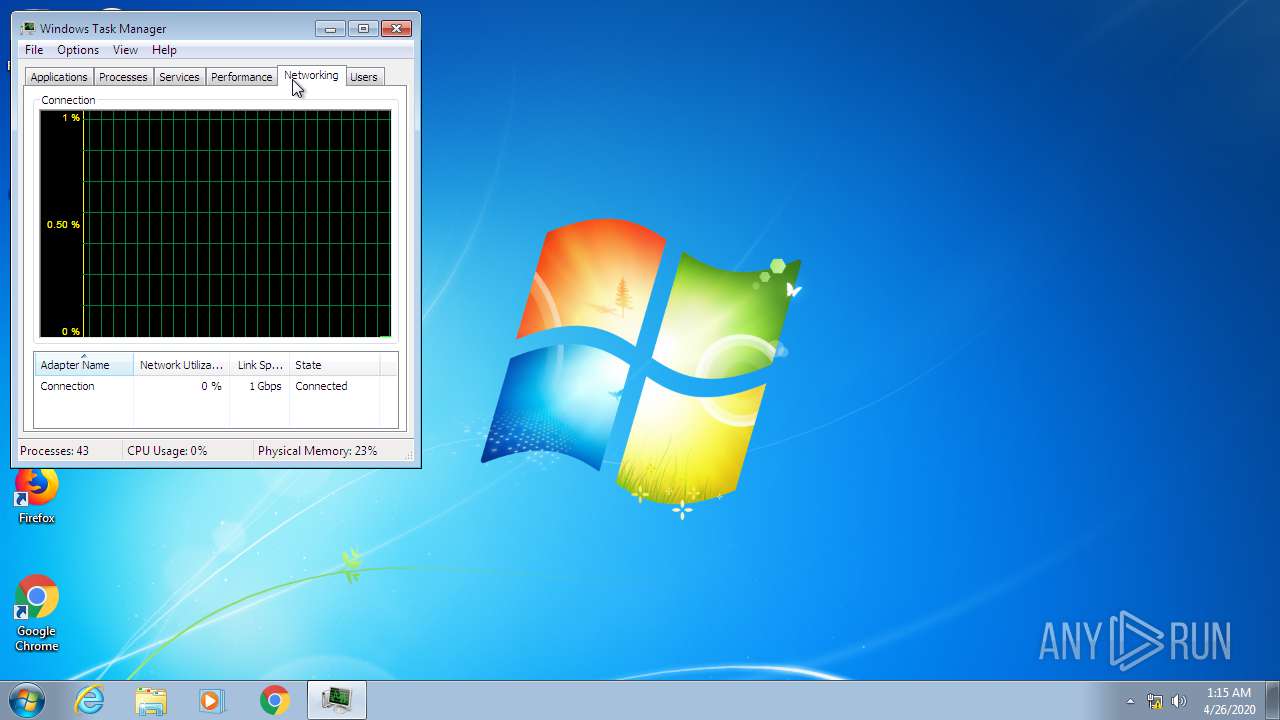
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
9
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2880 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 52.3.29.212:443 | growtopiagame.com | Amazon.com, Inc. | US | unknown |
2880 | chrome.exe | 2.16.186.114:443 | ubistatic-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
2880 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 52.87.110.231:443 | growtopiagame.com | Amazon.com, Inc. | US | unknown |
2880 | chrome.exe | 216.58.207.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2880 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
growtopiagame.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ubistatic-a.akamaihd.net |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Growtopia.exe | (LOG) VideoModeManager::VideoModeManager:698: VideoModeManager |
Growtopia.exe | |
Growtopia.exe | |
Growtopia.exe | |
Growtopia.exe | (ERROR) VideoModeManager::AddVideoMode:333: VideoMode 'Nexus 7B Visible' already exists |
Growtopia.exe | Setting native video mode to 1274, 695 - Fullscreen: 0 Aspect Ratio: 0.00 |