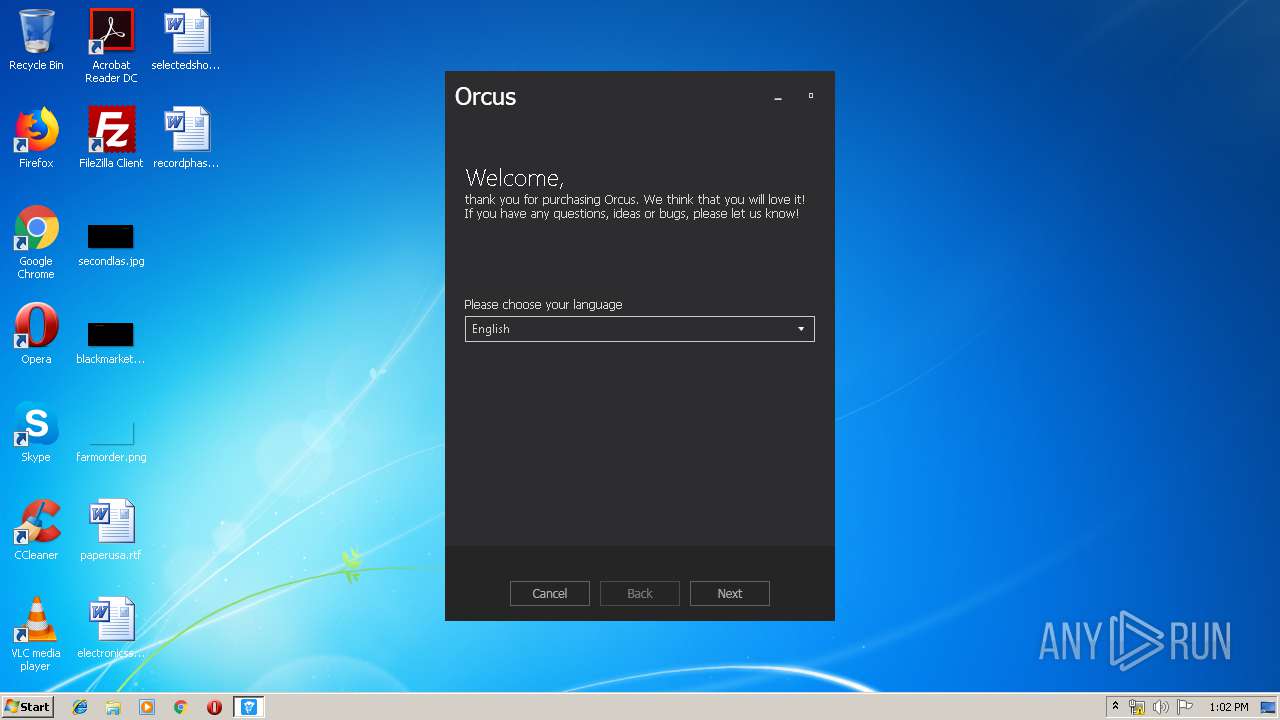
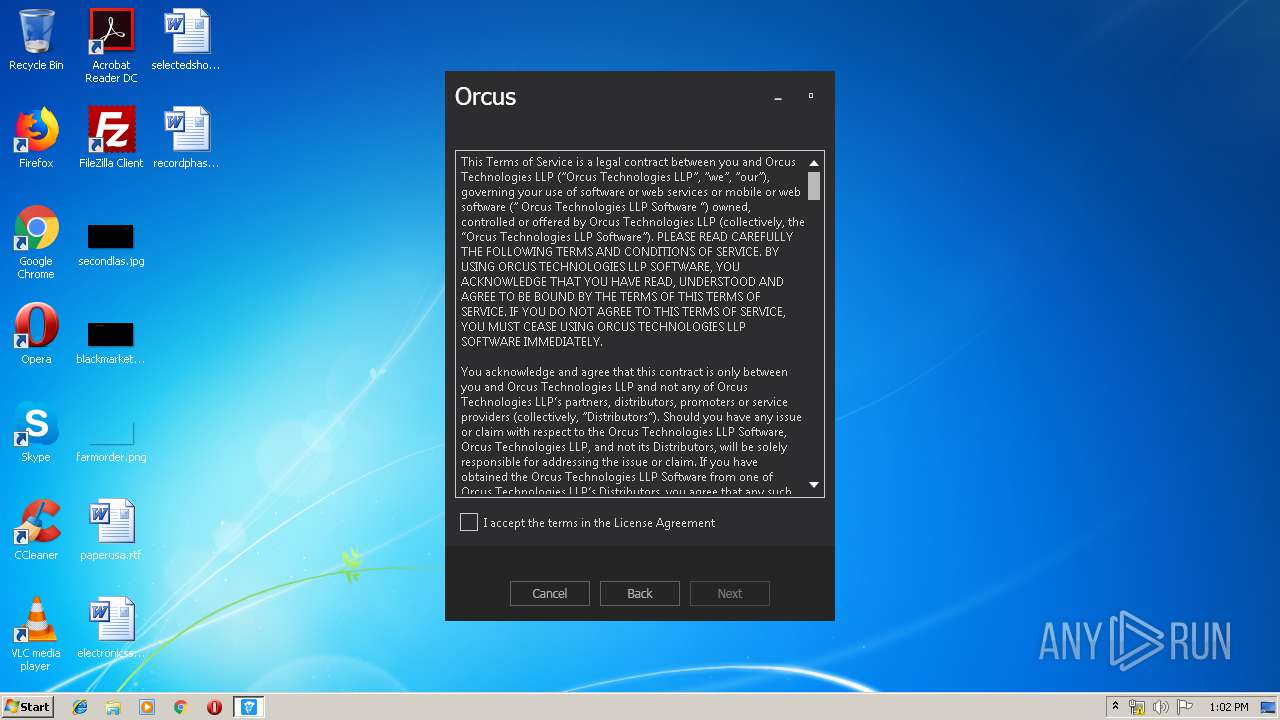
| File name: | Orcus RAT v1.3.1 Cracked by Wardow.exe |
| Full analysis: | https://app.any.run/tasks/8197fd2b-8b57-44ad-9e59-15b48cb1b0cf |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2019, 12:01:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4E47E4FE0868600785B59A0CED05003D |
| SHA1: | 697A72D58EE551C91E7FC58295DE014A158A8AA5 |
| SHA256: | 196E78C9528BA1ACC62A932DCAE1302BF4BB753B93FAFFB87389D1868DCC812B |
| SSDEEP: | 393216:5clChYZDH9iXqOnCa4Yl+pi3ZhJv+D8KMiKdPgjH:icm6qOnKY4oZnpKadYjH |
MALICIOUS
Application was dropped or rewritten from another process
- Orcus.Administration.exe (PID: 1704)
Loads dropped or rewritten executable
- Orcus.Administration.exe (PID: 1704)
SUSPICIOUS
Executable content was dropped or overwritten
- Orcus RAT v1.3.1 Cracked by Wardow.exe (PID: 3220)
Reads Environment values
- Orcus.Administration.exe (PID: 1704)
INFO
Dropped object may contain Bitcoin addresses
- Orcus RAT v1.3.1 Cracked by Wardow.exe (PID: 3220)
Reads settings of System Certificates
- Orcus.Administration.exe (PID: 1704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 242176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d759 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:27 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E854 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69231 |
.rdata | 0x00030000 | 0x00009A9C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13286 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.25381 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.11154 |
.rsrc | 0x0005D000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63679 |
.reloc | 0x0006B000 | 0x00001FCC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64554 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
32
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1704 | "C:\Users\admin\AppData\Local\Temp\Orcus.Administration.exe" | C:\Users\admin\AppData\Local\Temp\Orcus.Administration.exe | Orcus RAT v1.3.1 Cracked by Wardow.exe | ||||||||||||
User: admin Company: Orcus Technologies Integrity Level: MEDIUM Description: Orcus Administration Exit code: 0 Version: 1.3.1 Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Local\Temp\Orcus RAT v1.3.1 Cracked by Wardow.exe" | C:\Users\admin\AppData\Local\Temp\Orcus RAT v1.3.1 Cracked by Wardow.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
417
Read events
386
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3220) Orcus RAT v1.3.1 Cracked by Wardow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3220) Orcus RAT v1.3.1 Cracked by Wardow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Orcus.Administration.exe | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Orcus_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Orcus_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Orcus_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Orcus_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1704) Orcus.Administration.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Orcus_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
34
Suspicious files
0
Text files
20
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\Orcus.Administration.exe.config | xml | |
MD5:2846EC087E67923C130A5B875193C893 | SHA256:148DC241BFA25E5FDA9EBEF2D315AA95121F9468DA29DC167573F32F14733D08 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\CSCore.dll | executable | |
MD5:5E8FE2A84D3076F5D9815B77EB67D4F6 | SHA256:FD3FEEFC62097FF785C7FDD524070E25FCABA7E4CE19F5480ECAD695DD2A5405 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\Orcus.Administration.pdb | pdb | |
MD5:16B3E1C39BC2E62BF1B0A33B1CBD599C | SHA256:19DD178E25A83E34CE3E739B5E86979F662605E3AAE986D50C2653F04DFEC99E | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\Be.Windows.Forms.HexBox.dll | executable | |
MD5:E00907B3D9270D4CCA87C25FF30BCD02 | SHA256:5448E587498C560EF1D8E182344BC340A57CFD3B05C4507C48DA11E139035818 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\Be.Windows.Forms.HexBox.xml | xml | |
MD5:B534569D28458990C1B2F68EAFA60BC3 | SHA256:415EA2D9A22AB58E5F89ECE1CAF45FD61F2579EF0C700C990A997841F284E4E3 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\AlphaChiTech.Virtualization.pdb | pdb | |
MD5:E05045DCF2036739BD51C44EE0BC2141 | SHA256:5843A10C4E7A45BB9794B2C603E5B617A5592B104E5FEA01FF9A5524BBC63F96 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\AlphaChiTech.Virtualization.dll | executable | |
MD5:66C29815E0E824874E69342FE344D460 | SHA256:5A9296146DD3D0DCA9507E59520C29EF9848CBD7599A95EFE09C01FA1C894D8A | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\Exceptionless.Extras.xml | xml | |
MD5:9EB536682CDBC5DD645F3DCBF5504476 | SHA256:043078267F89A151E669FBB34E630E70CFAF4254FD1C8B1985AC73B56B69EFE9 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\Exceptionless.Extras.dll | executable | |
MD5:D3FCD5038079EF42E23ED39A86AF5A31 | SHA256:9D4AB0418D94D3C3D7025ECC1C70CE1762EE12AAA4D35666C2DC7887DF53A537 | |||
| 3220 | Orcus RAT v1.3.1 Cracked by Wardow.exe | C:\Users\admin\AppData\Local\Temp\libraries\Exceptionless.Wpf.dll | executable | |
MD5:609FBFCF1BEA7AC58712764CB9E408F1 | SHA256:C14B8C33F9679CF4CF4F80D91698E3F40ACDBD82D3B700A8B2813322E5E42EC3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | Orcus.Administration.exe | 40.85.179.199:443 | collector.exceptionless.io | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
collector.exceptionless.io |
| unknown |