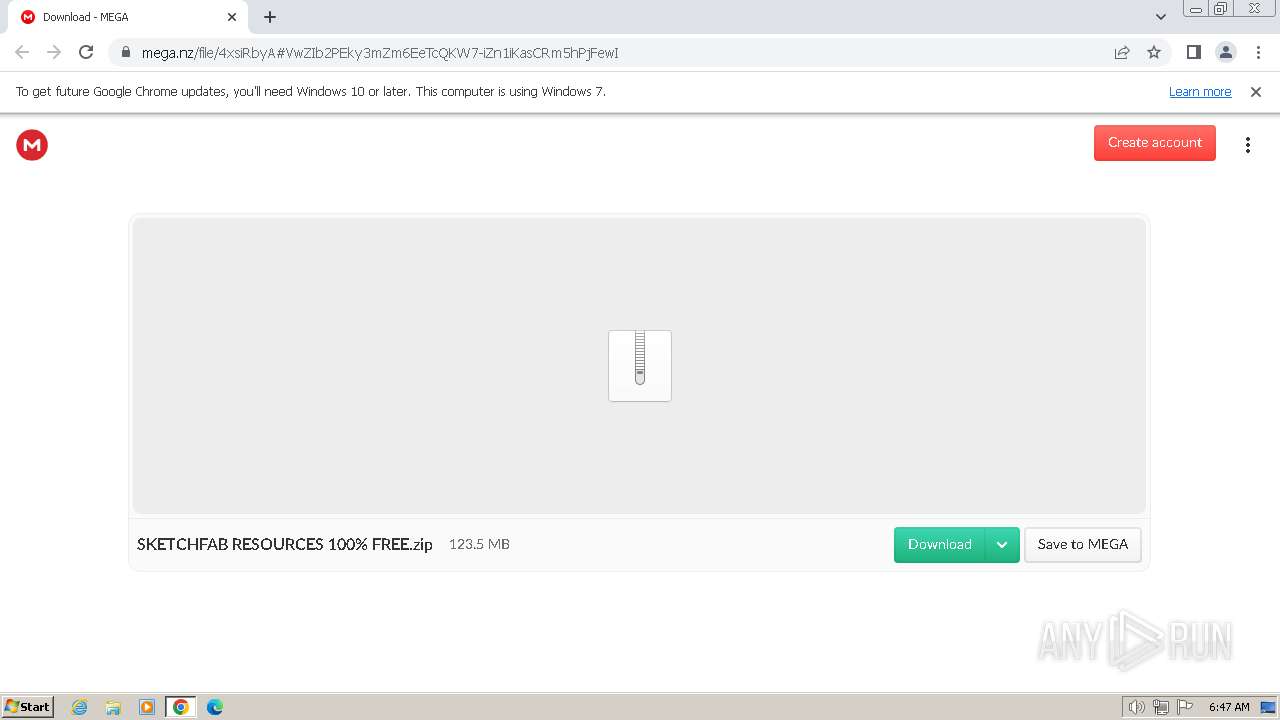
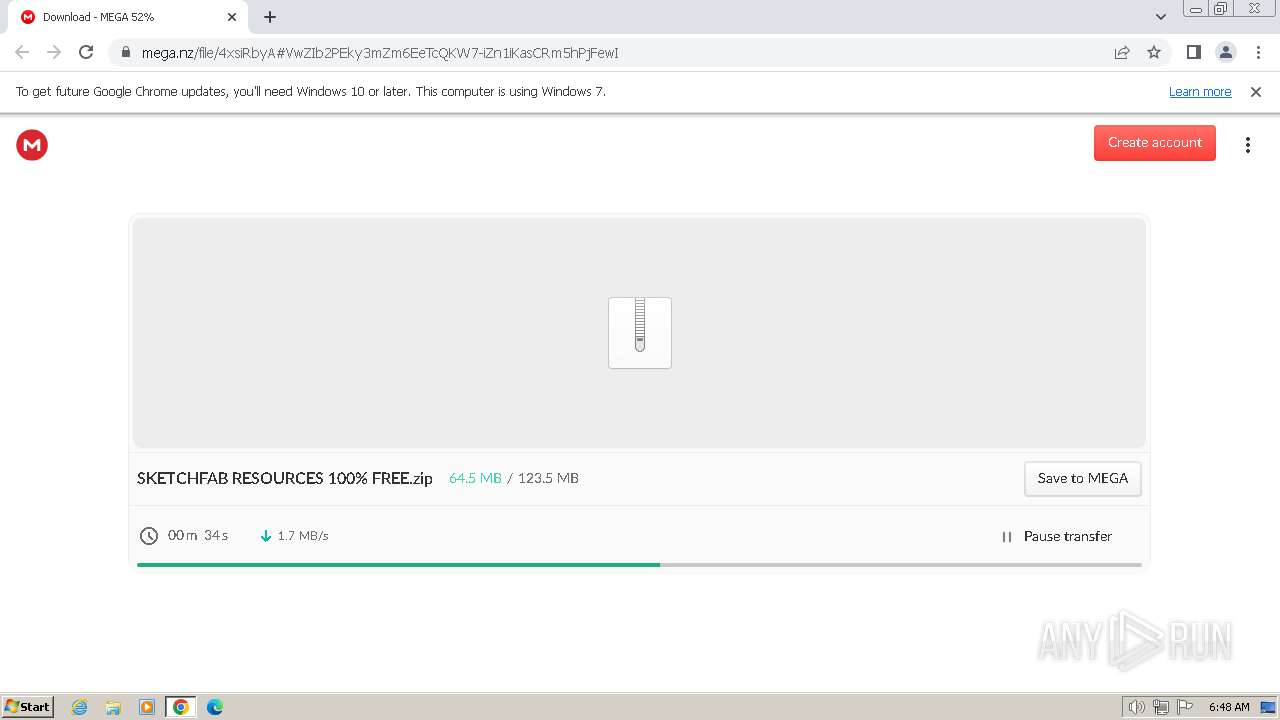
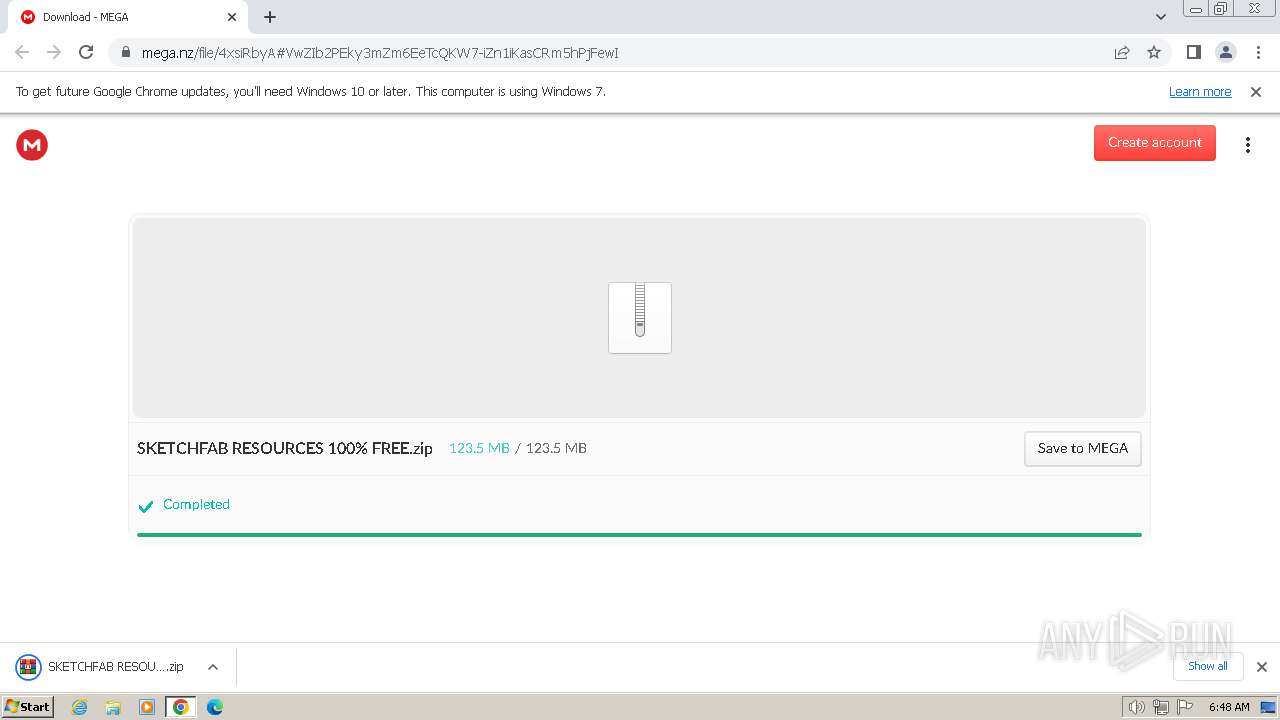
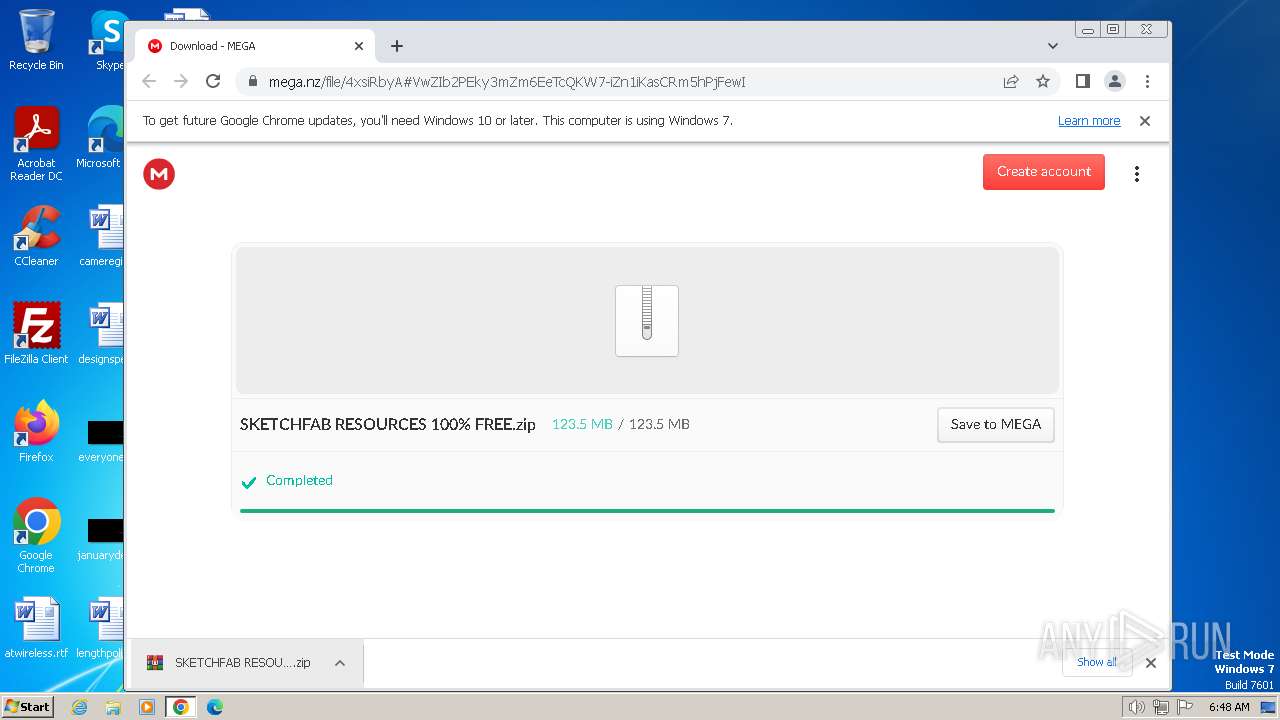
| URL: | https://mega.nz/file/4xsiRbyA#VwZIb2PEky3mZm6EeTcQKW7-iZn1iKasCRm5hPjFewI |
| Full analysis: | https://app.any.run/tasks/abf94445-3d9f-40d3-b705-4a294766dae6 |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2024, 06:46:48 |
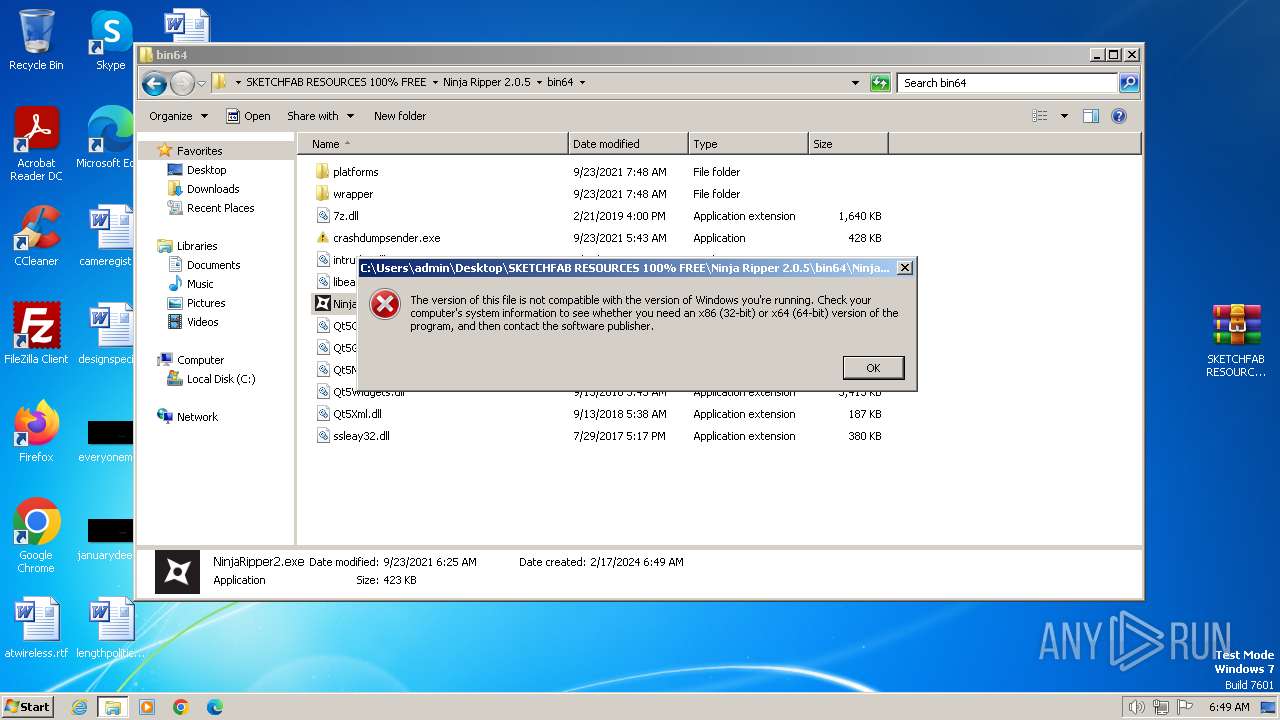
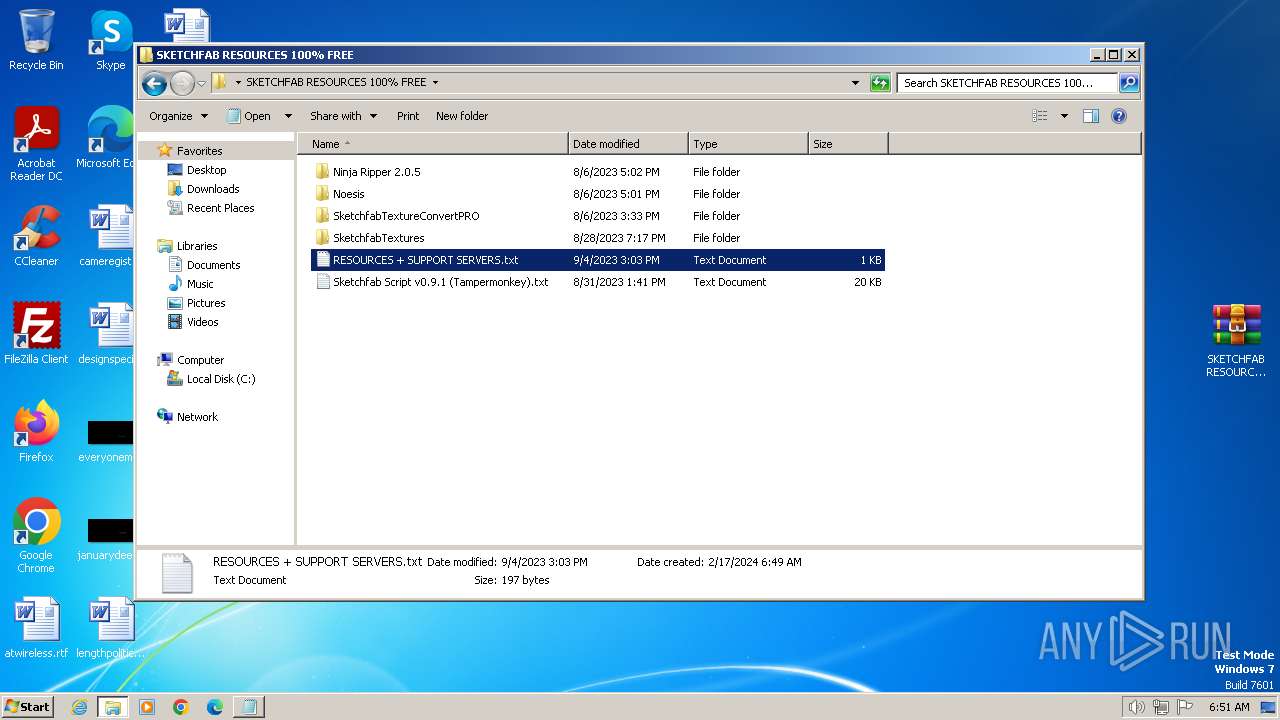
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D223DE45241DEB61AFDE1D7C9370A1A9 |
| SHA1: | F1AD9DBD50FBCFC3394C490FA220B162079B1CF2 |
| SHA256: | 19652F886A77346482E2D7CE2DFD692A721E762AA22276583A949CD0C09DCA26 |
| SSDEEP: | 3:N8X/iQmkbs3WPAhAiSItv4/1bAf:2hTbZAGx+v4Rc |
MALICIOUS
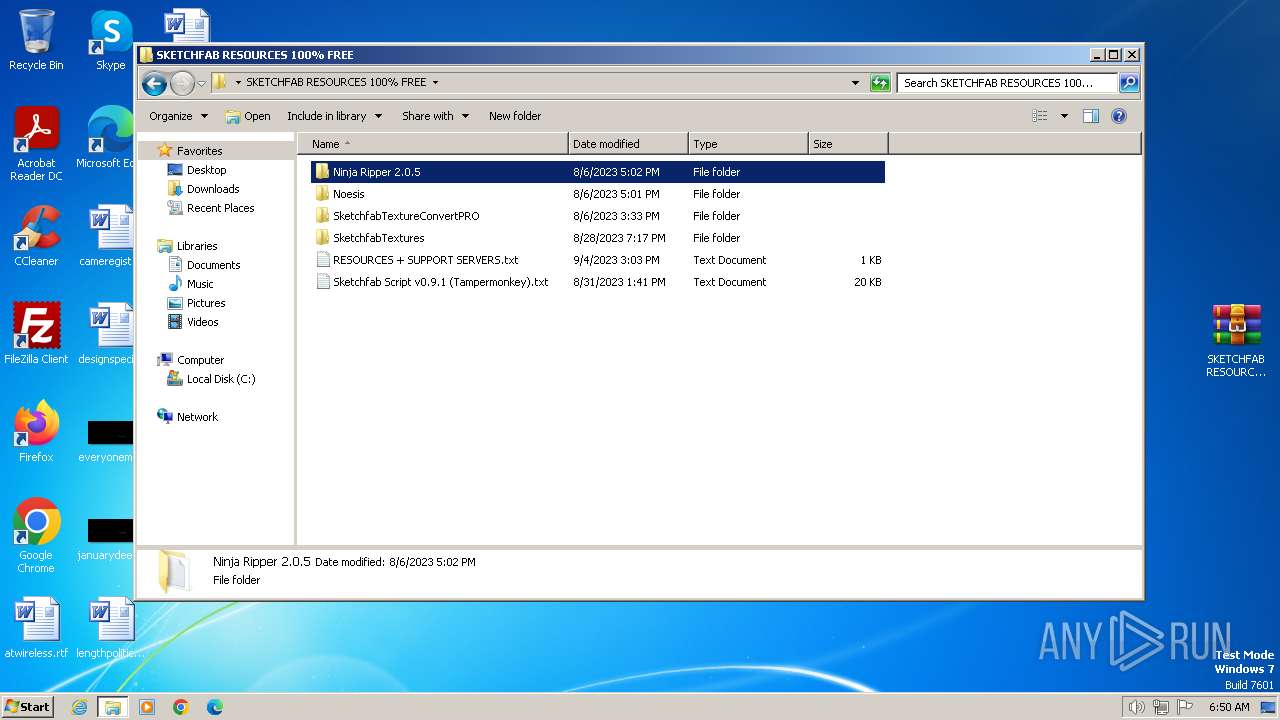
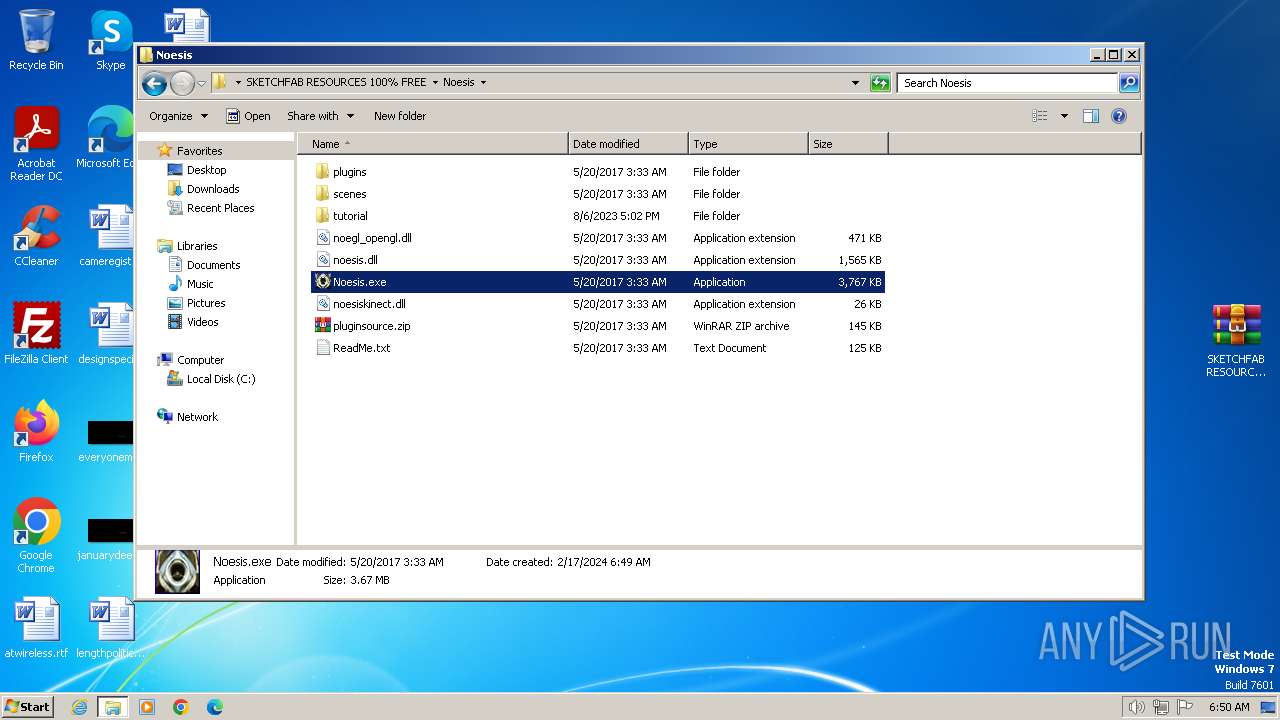
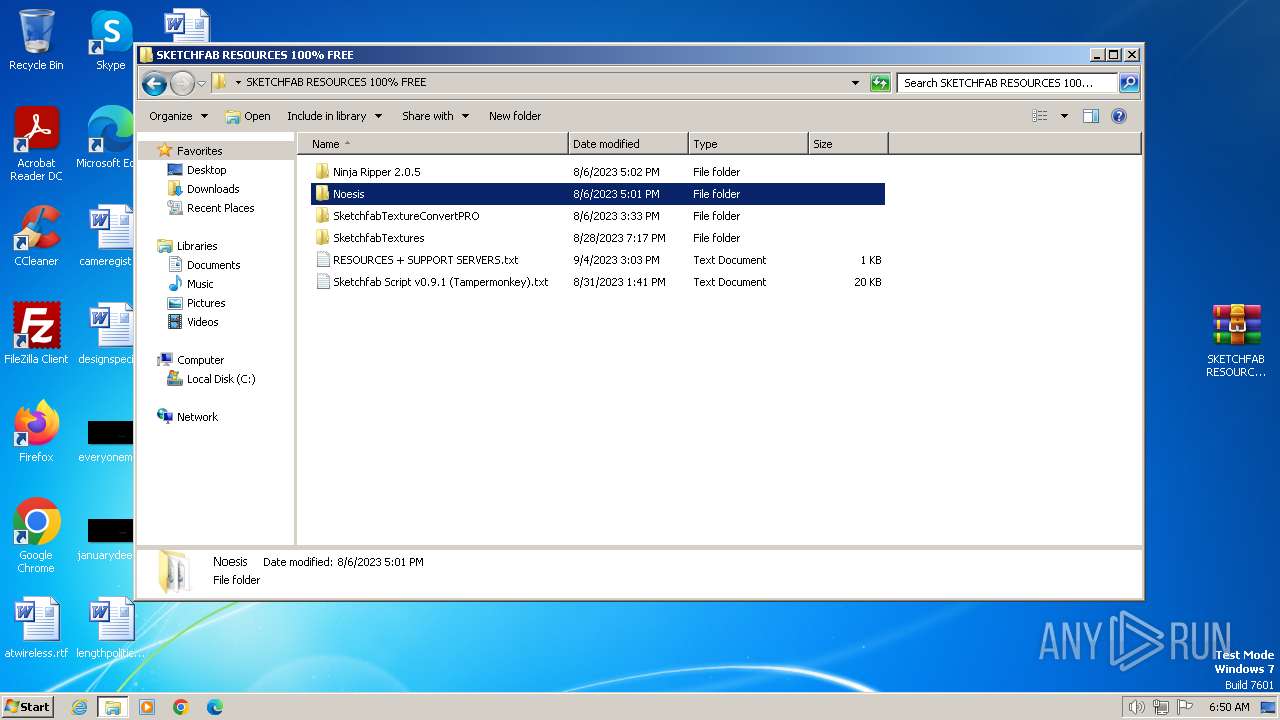
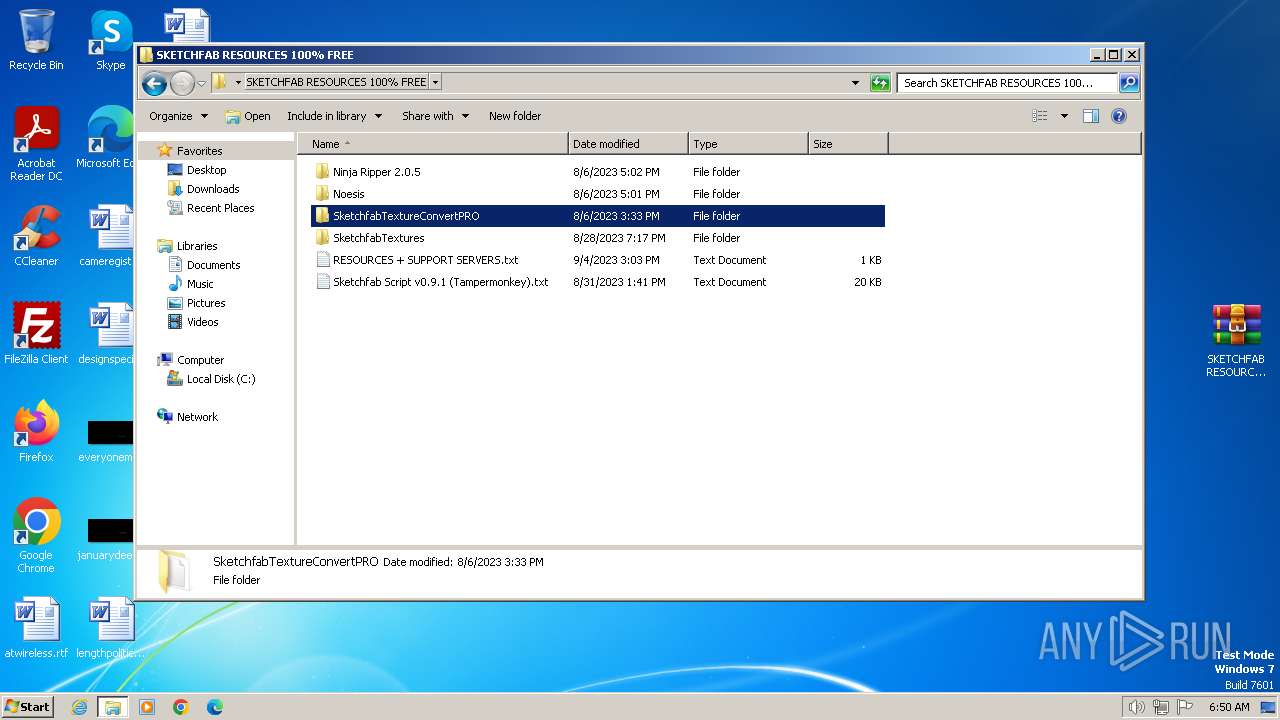
Drops the executable file immediately after the start
- Noesis.exe (PID: 2520)
SUSPICIOUS
Reads settings of System Certificates
- NinjaRipper2.exe (PID: 2228)
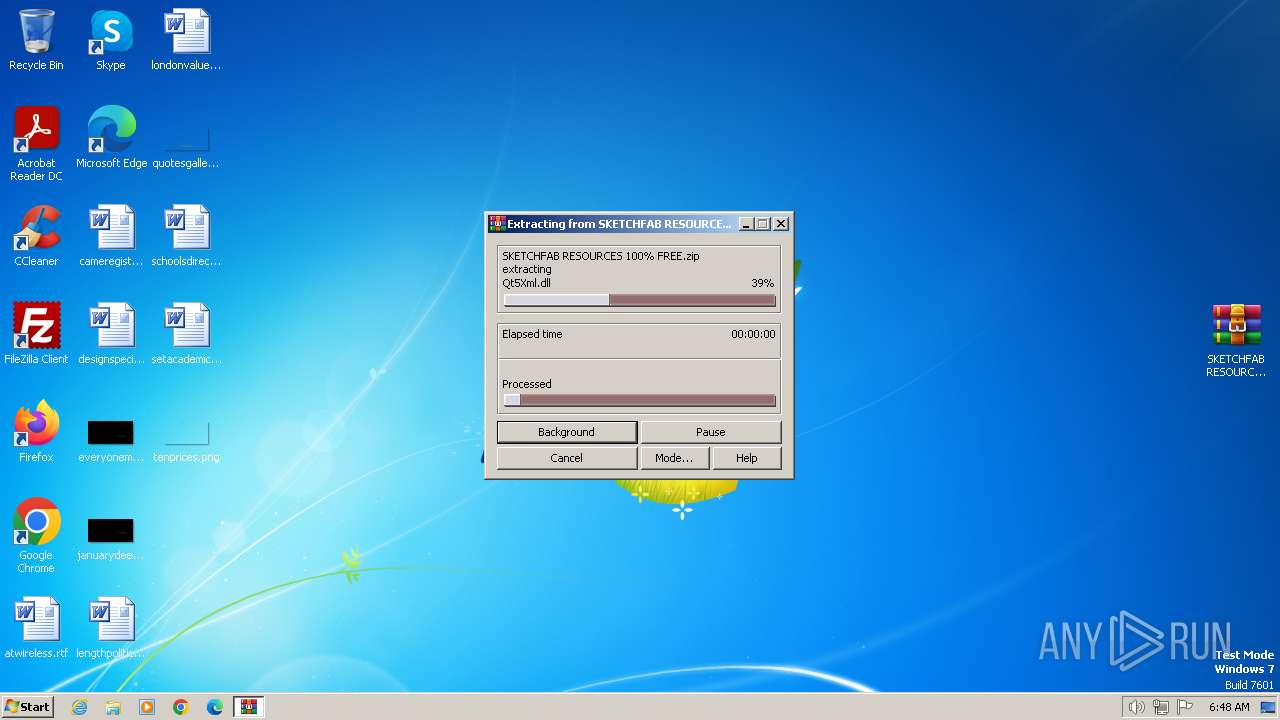
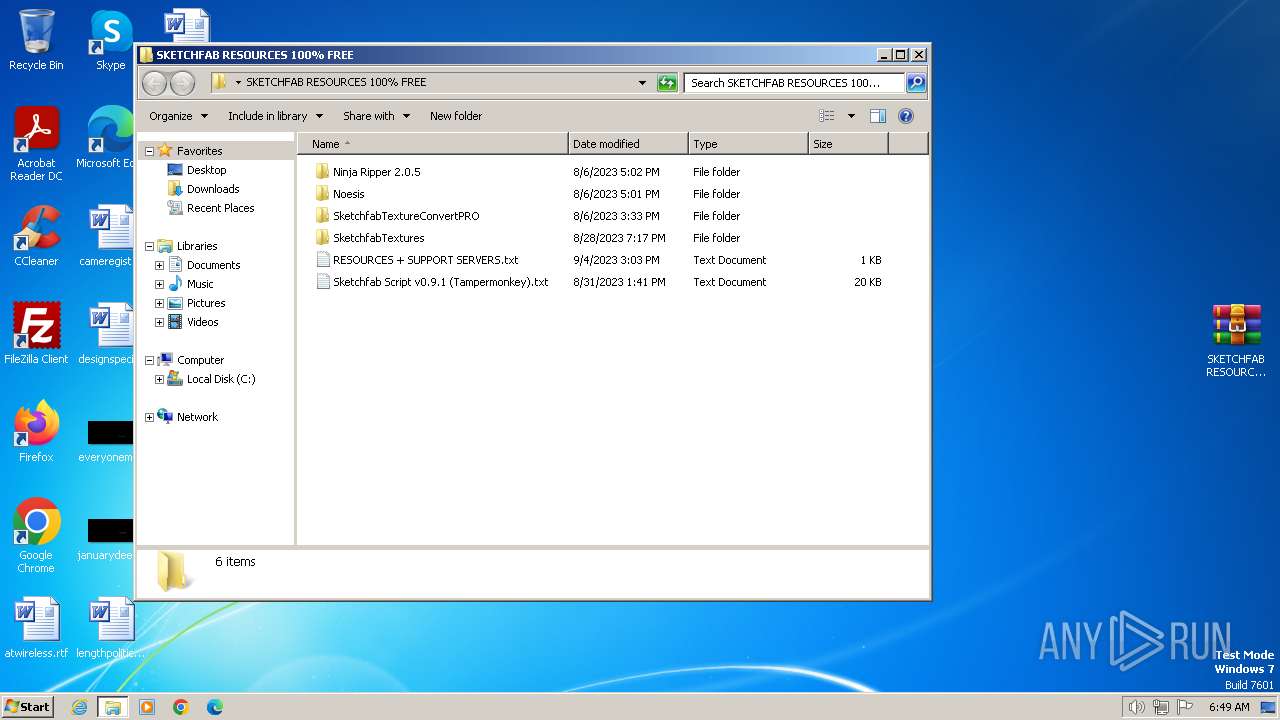
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 2612)
Reads the Internet Settings
- NinjaRipper2.exe (PID: 2228)
Executable content was dropped or overwritten
- Noesis.exe (PID: 2520)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2612)
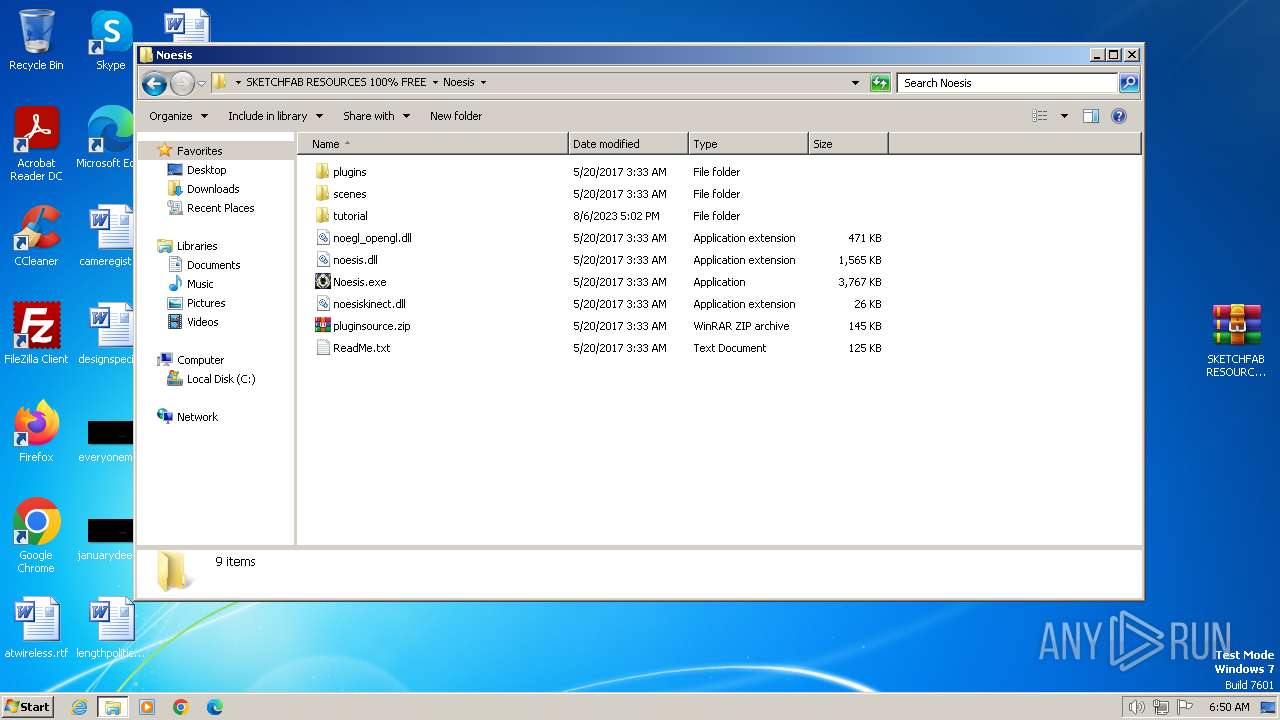
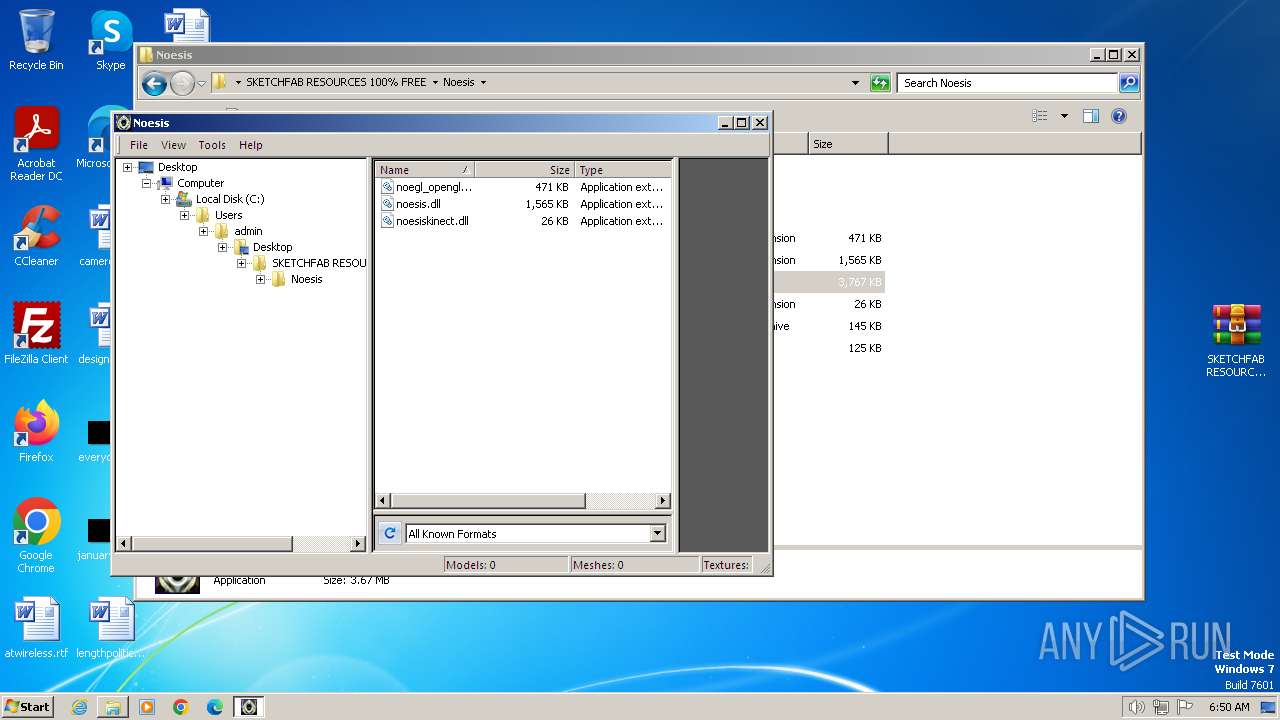
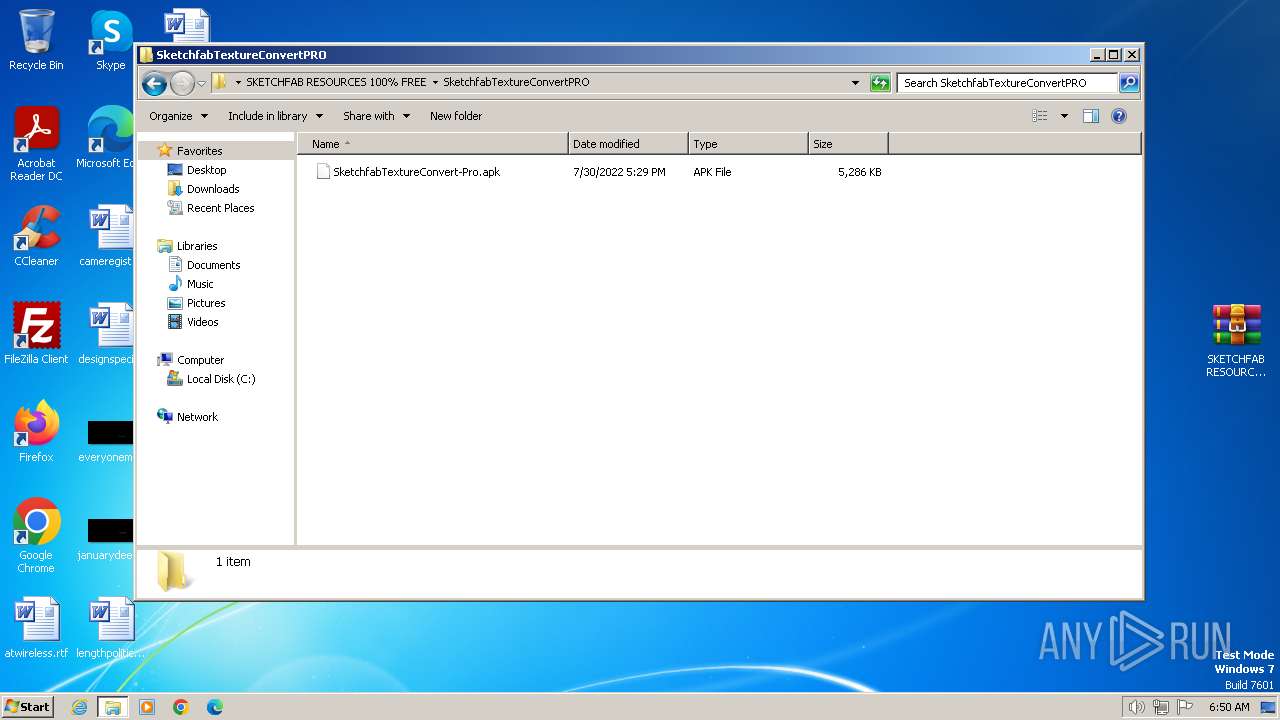
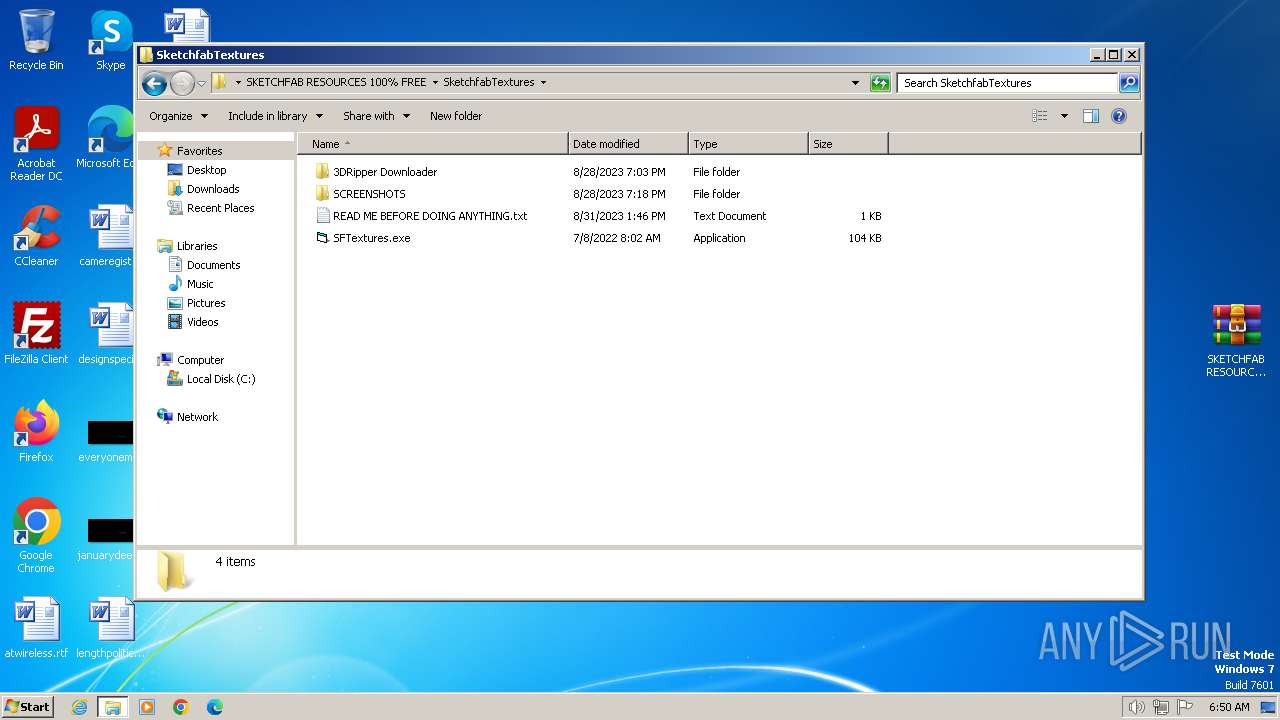
Manual execution by a user
- WinRAR.exe (PID: 1196)
- WinRAR.exe (PID: 2612)
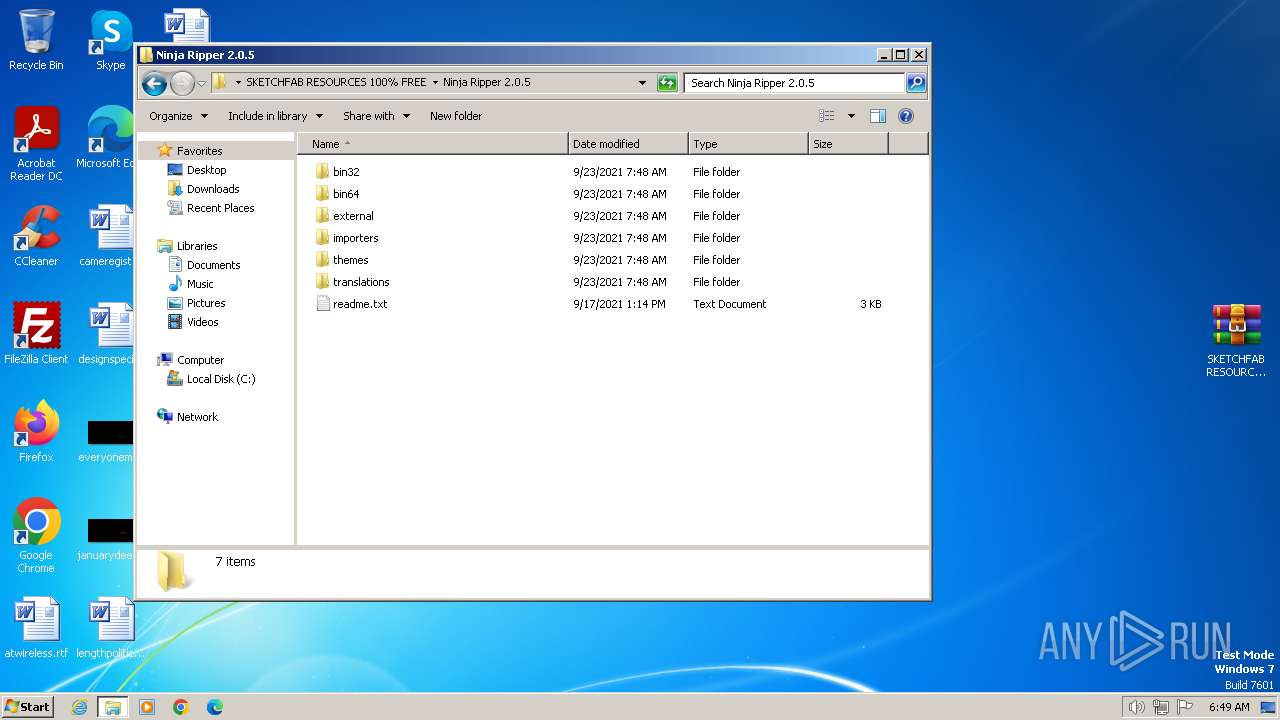
- NinjaRipper2.exe (PID: 2228)
- Noesis.exe (PID: 2520)
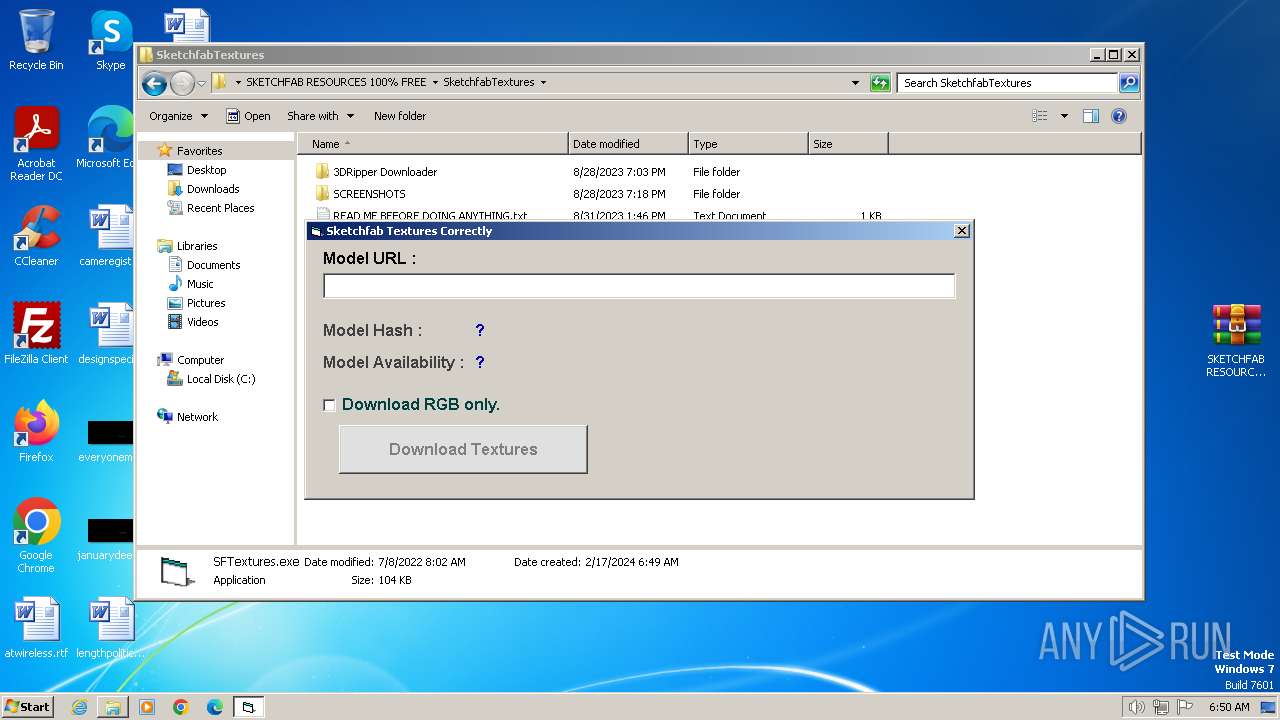
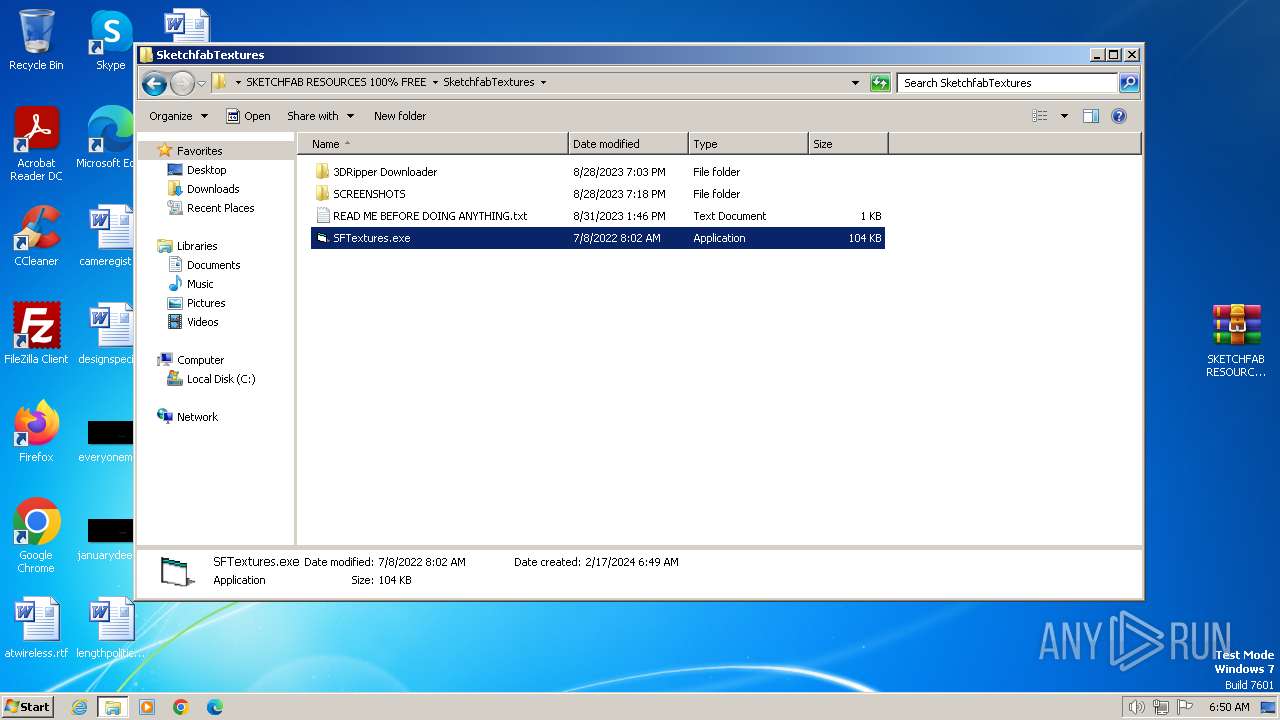
- SFTextures.exe (PID: 2000)
- notepad.exe (PID: 1288)
- notepad.exe (PID: 3524)
- notepad.exe (PID: 2852)
The process uses the downloaded file
- chrome.exe (PID: 3252)
Application launched itself
- chrome.exe (PID: 3864)
Checks supported languages
- NinjaRipper2.exe (PID: 2228)
- Noesis.exe (PID: 2520)
- SFTextures.exe (PID: 2000)
Reads the computer name
- NinjaRipper2.exe (PID: 2228)
- Noesis.exe (PID: 2520)
Reads the machine GUID from the registry
- NinjaRipper2.exe (PID: 2228)
- Noesis.exe (PID: 2520)
Create files in a temporary directory
- Noesis.exe (PID: 2520)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
24
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3380 --field-trial-handle=1124,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
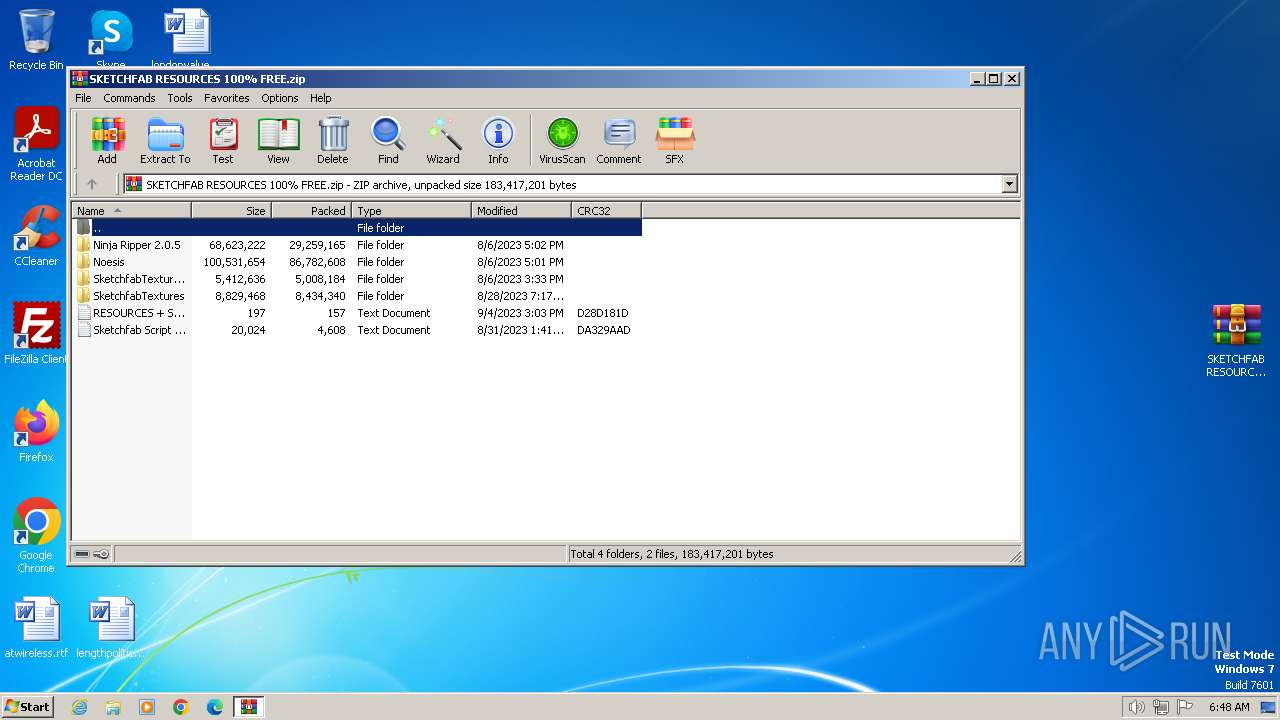
| 1196 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3044 --field-trial-handle=1124,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
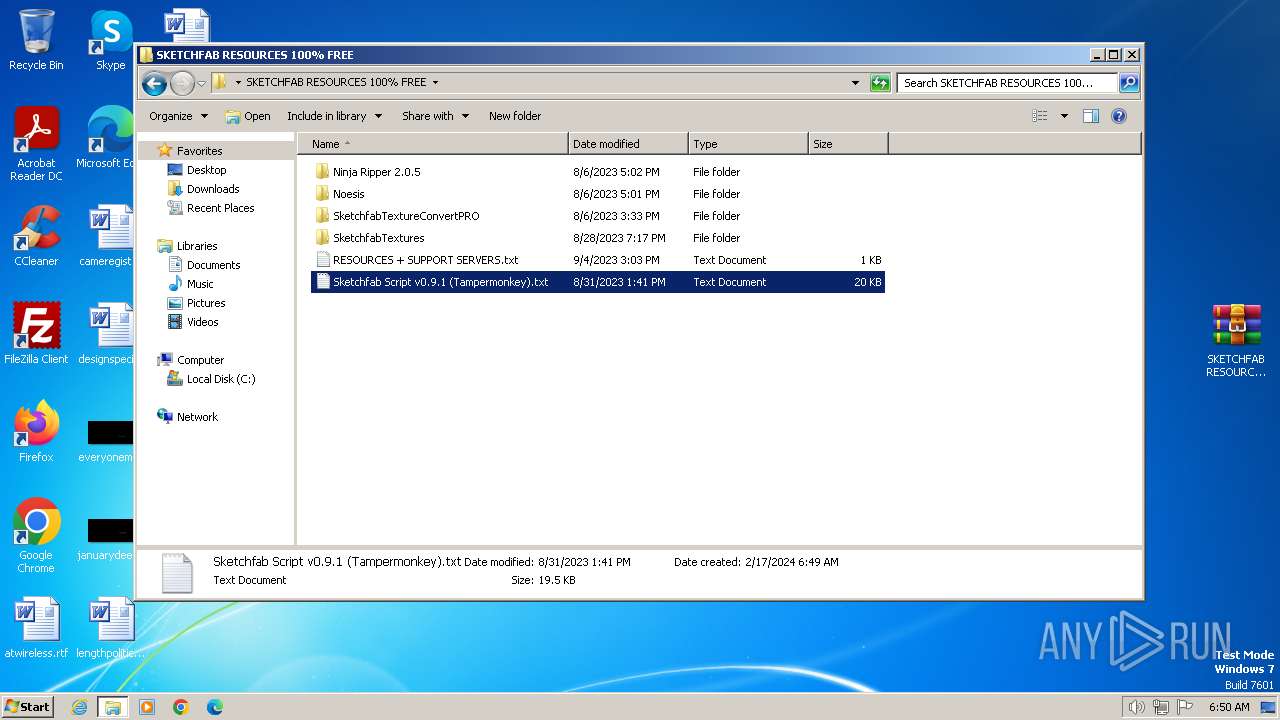
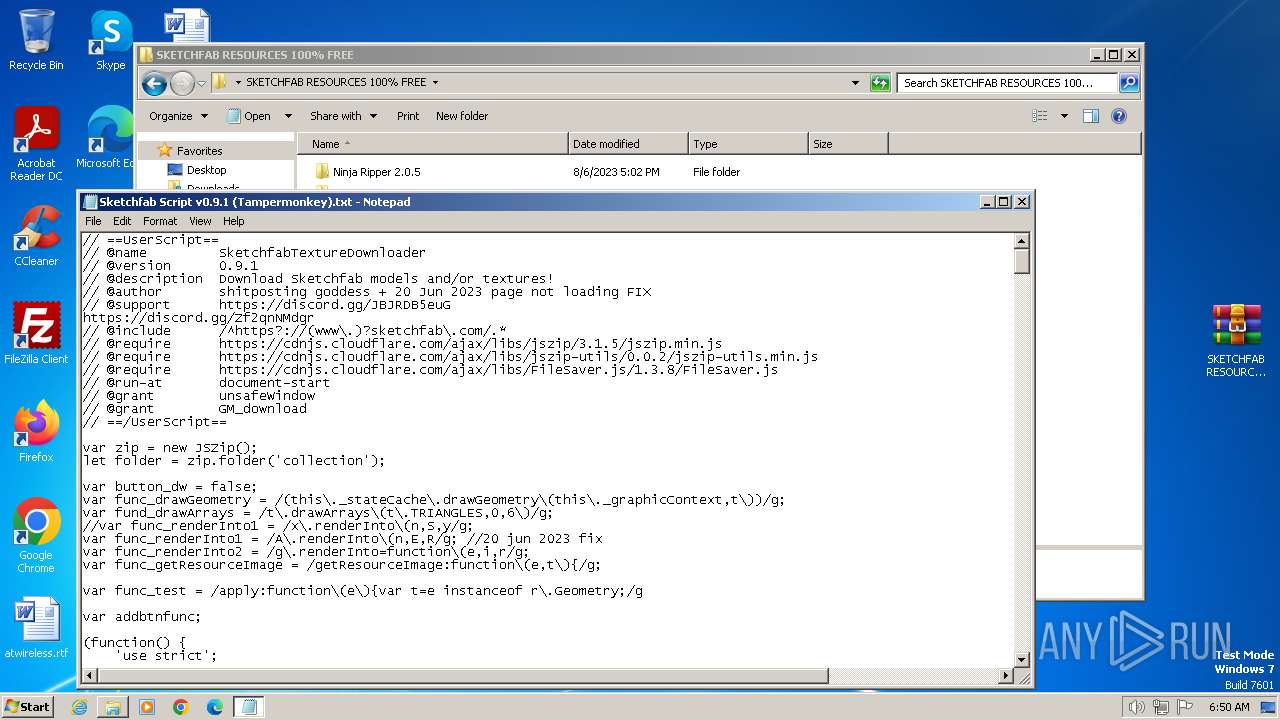
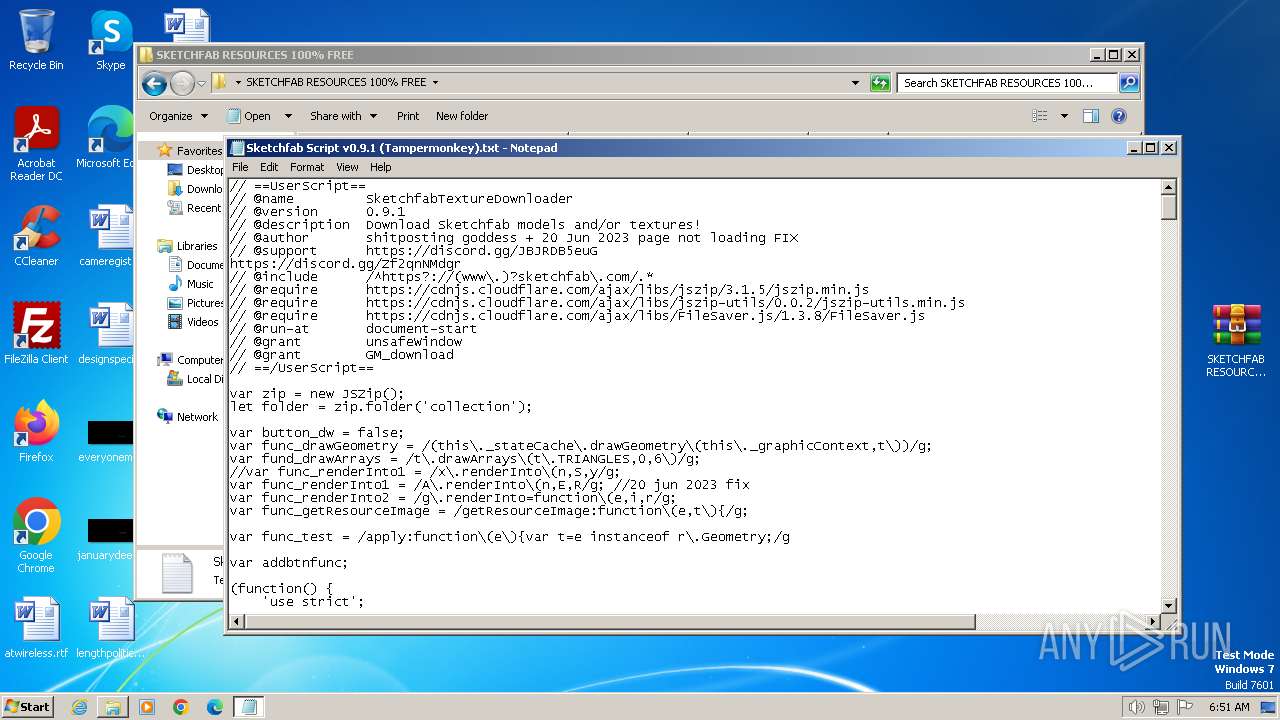
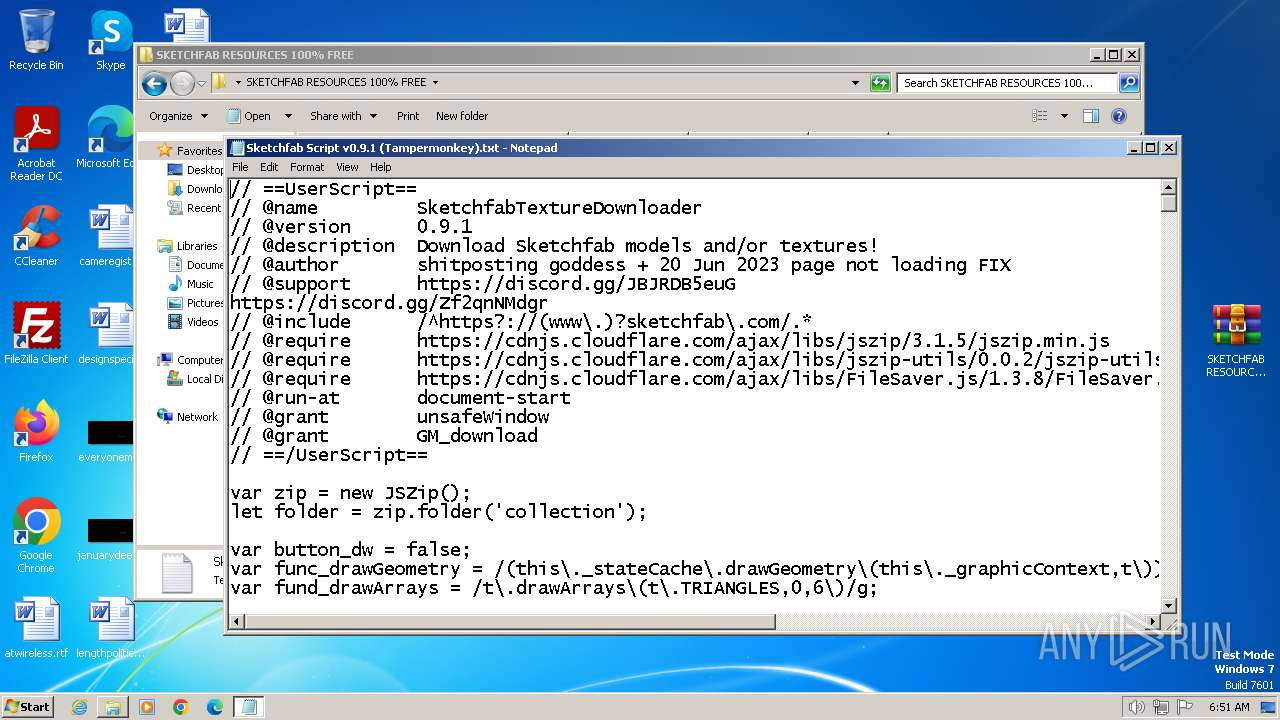
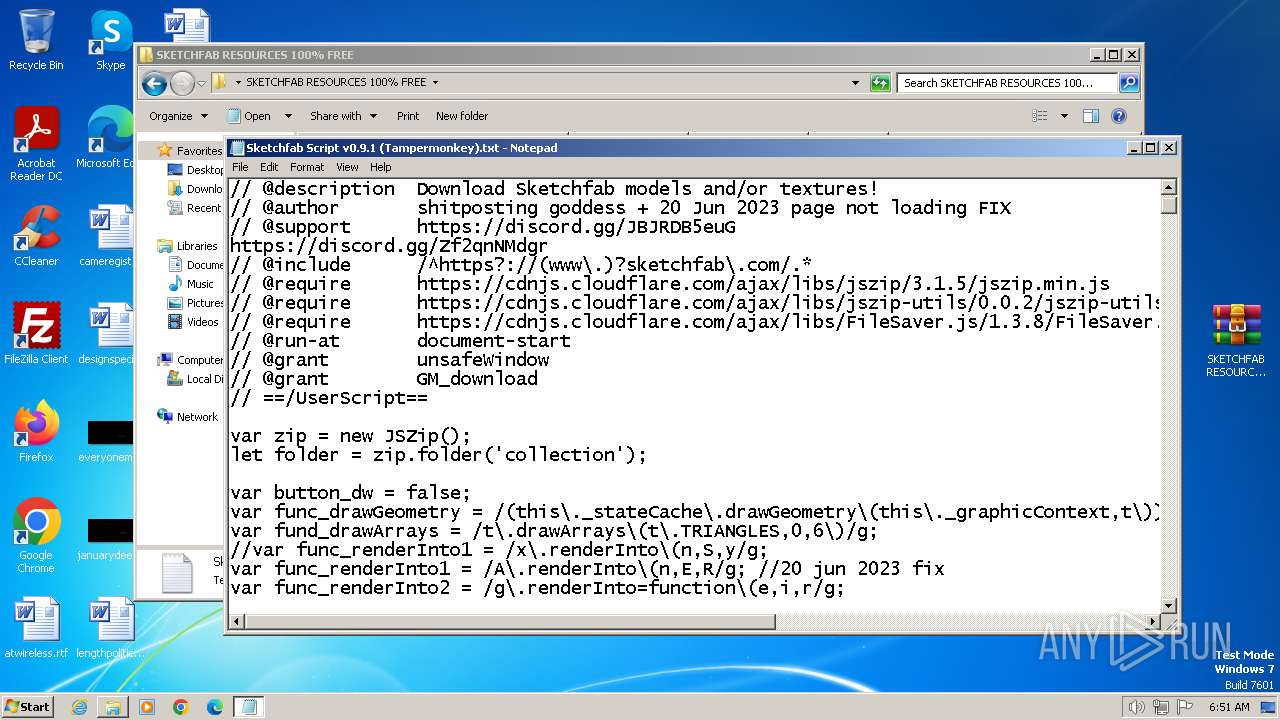
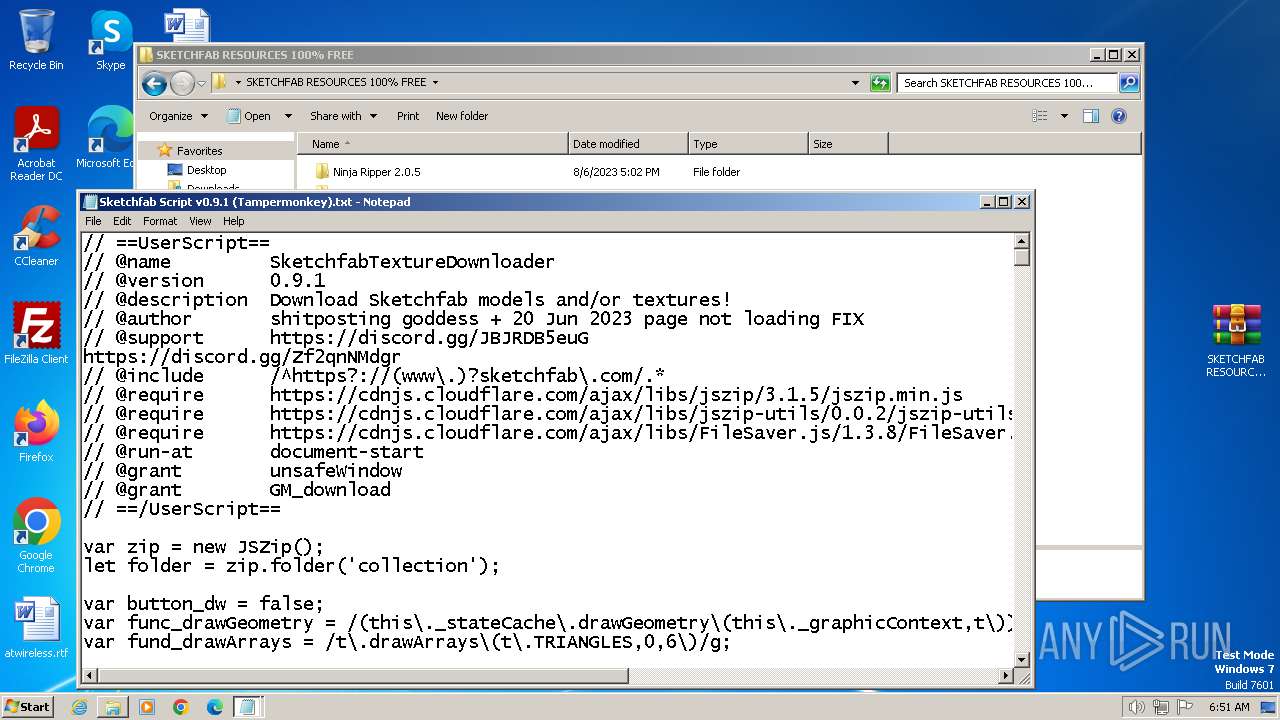
| 1288 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Sketchfab Script v0.9.1 (Tampermonkey).txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3772 --field-trial-handle=1124,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2000 | "C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\SketchfabTextures\SFTextures.exe" | C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\SketchfabTextures\SFTextures.exe | — | explorer.exe | |||||||||||
User: admin Company: SFTextures Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1376 --field-trial-handle=1124,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
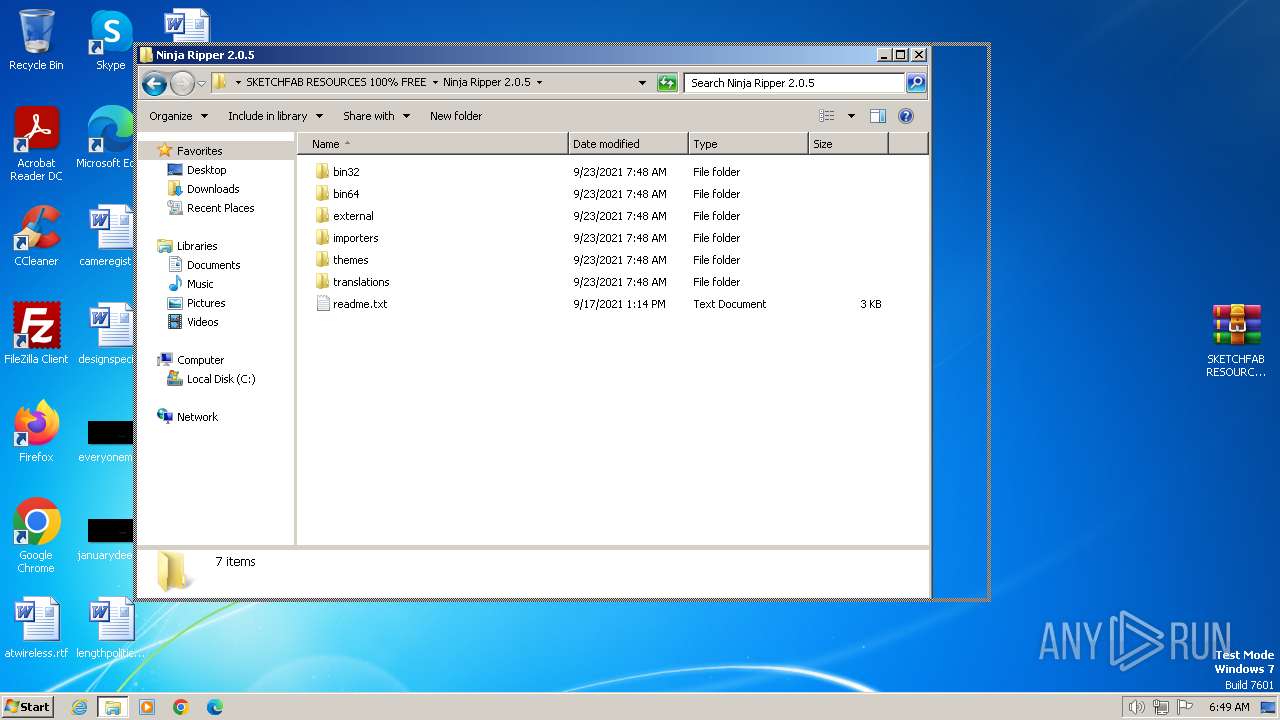
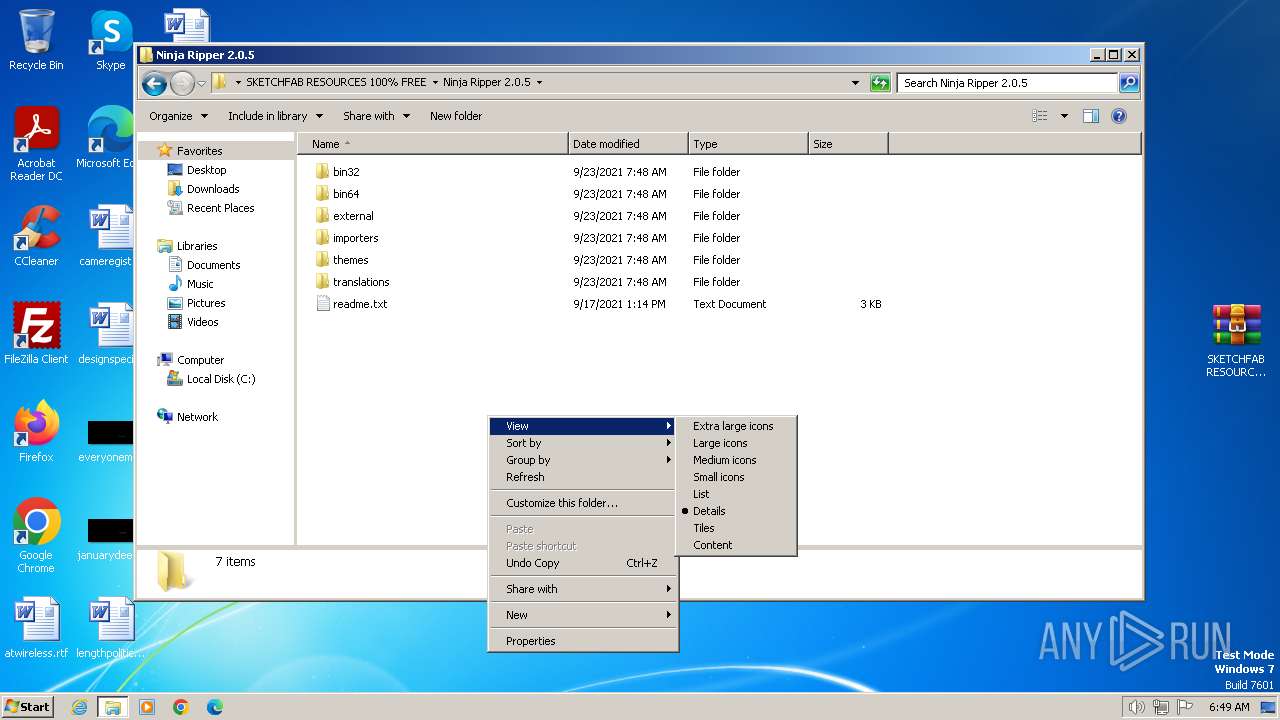
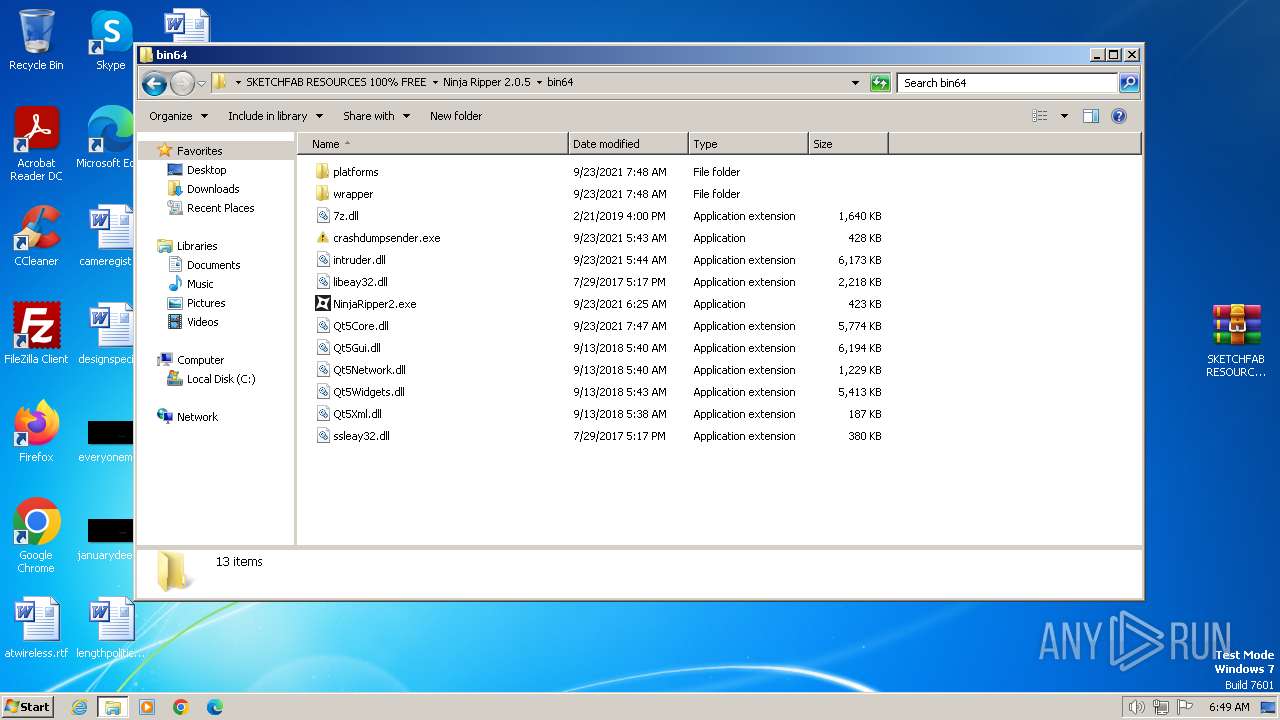
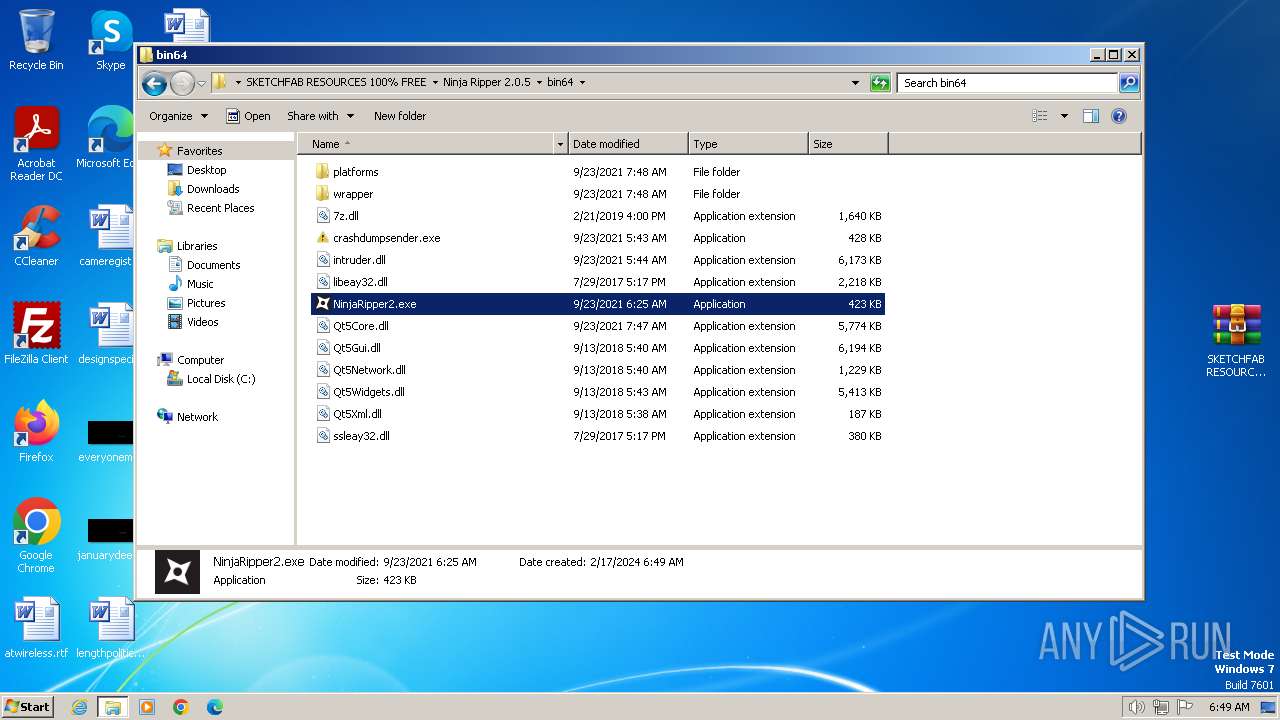
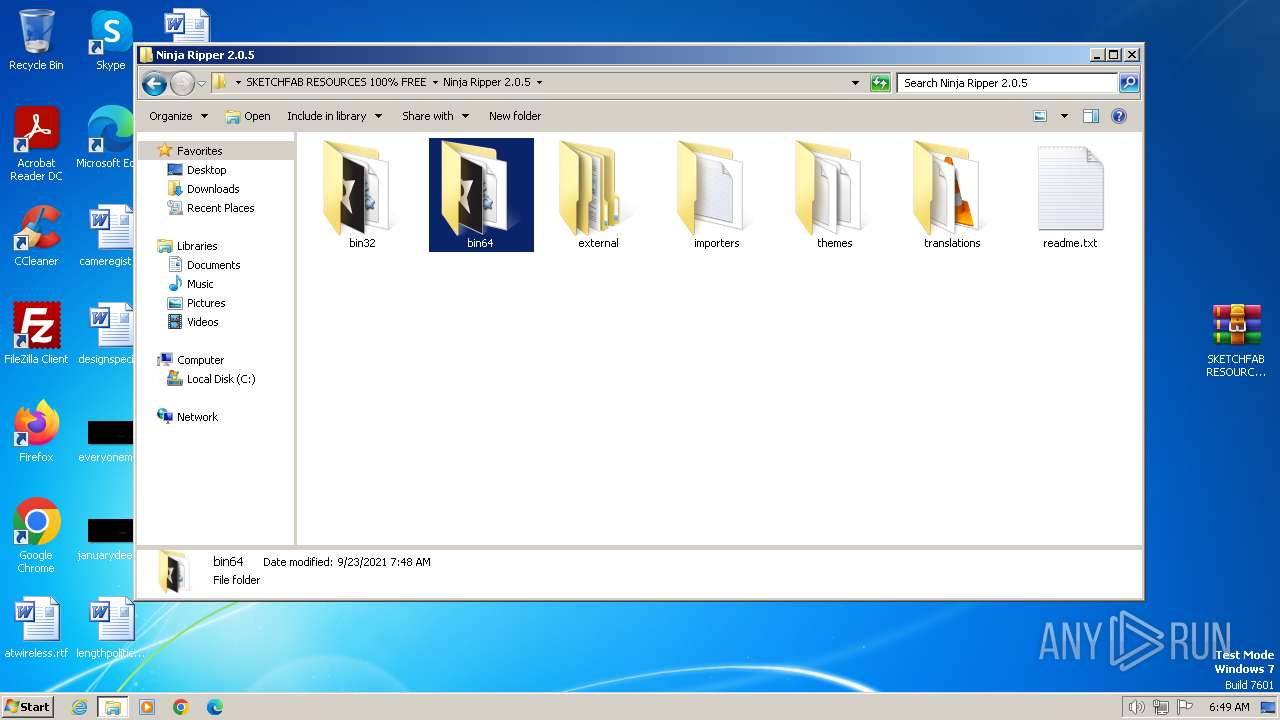
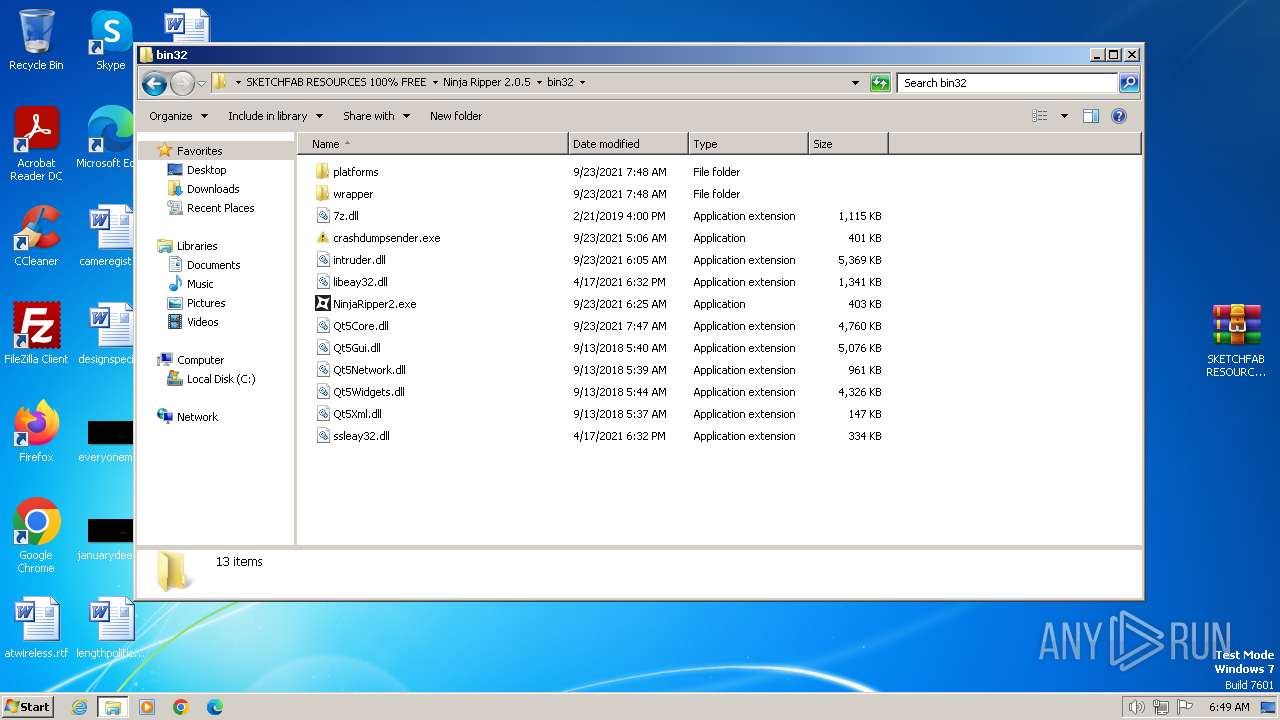
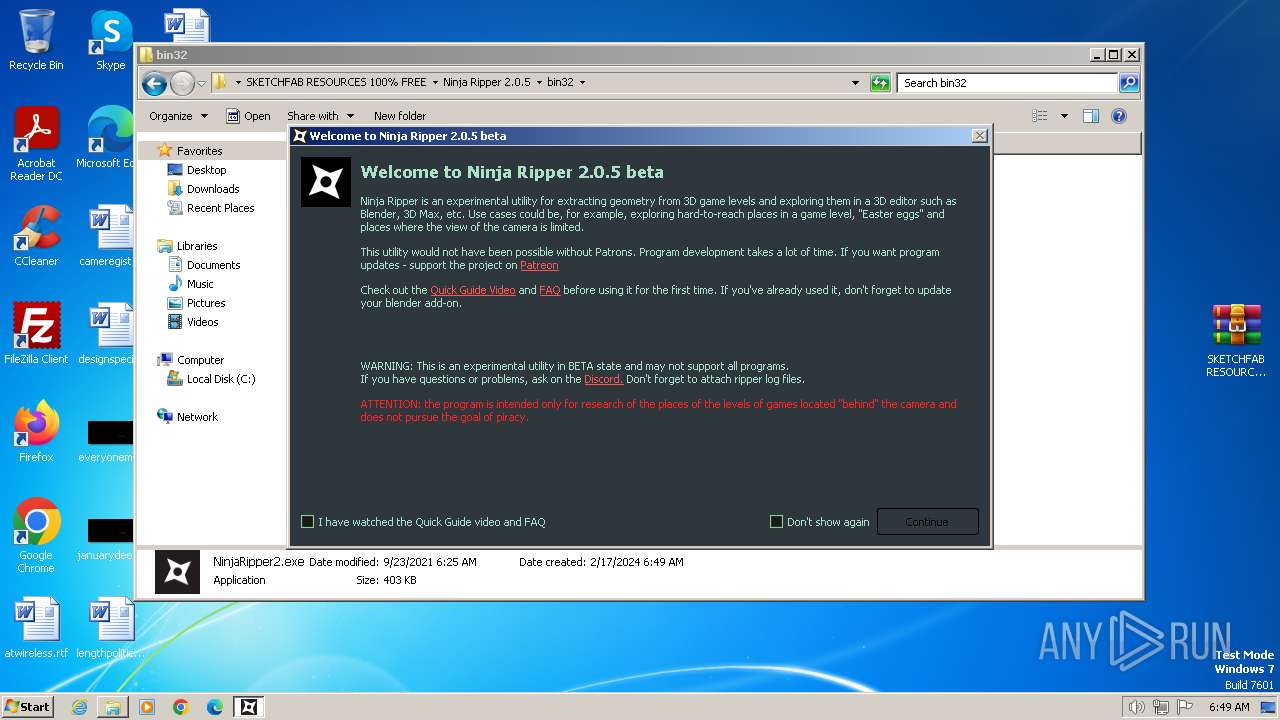
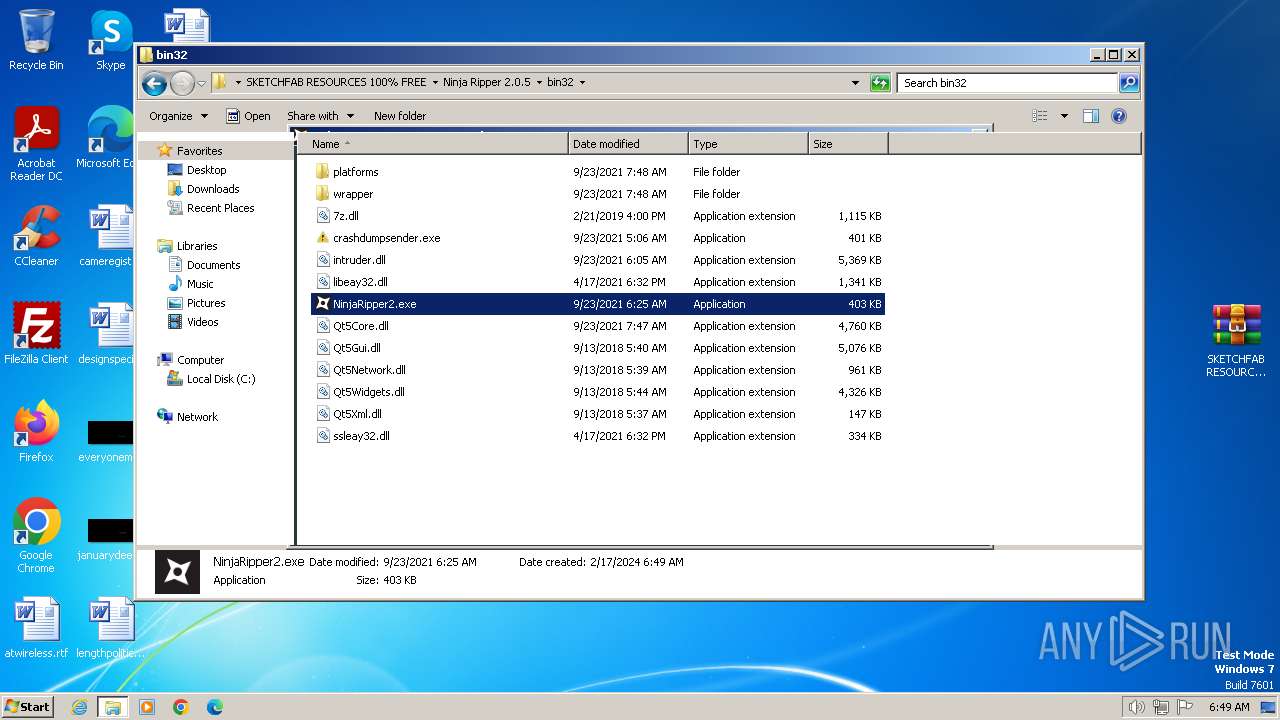
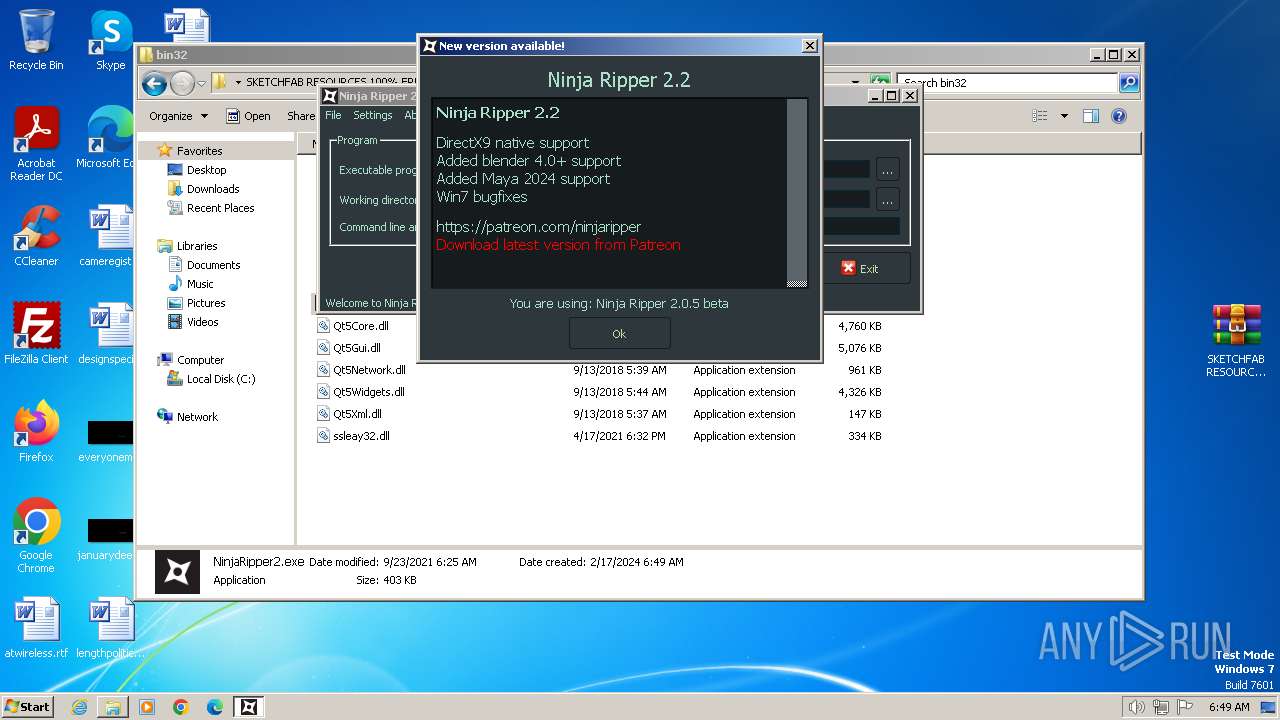
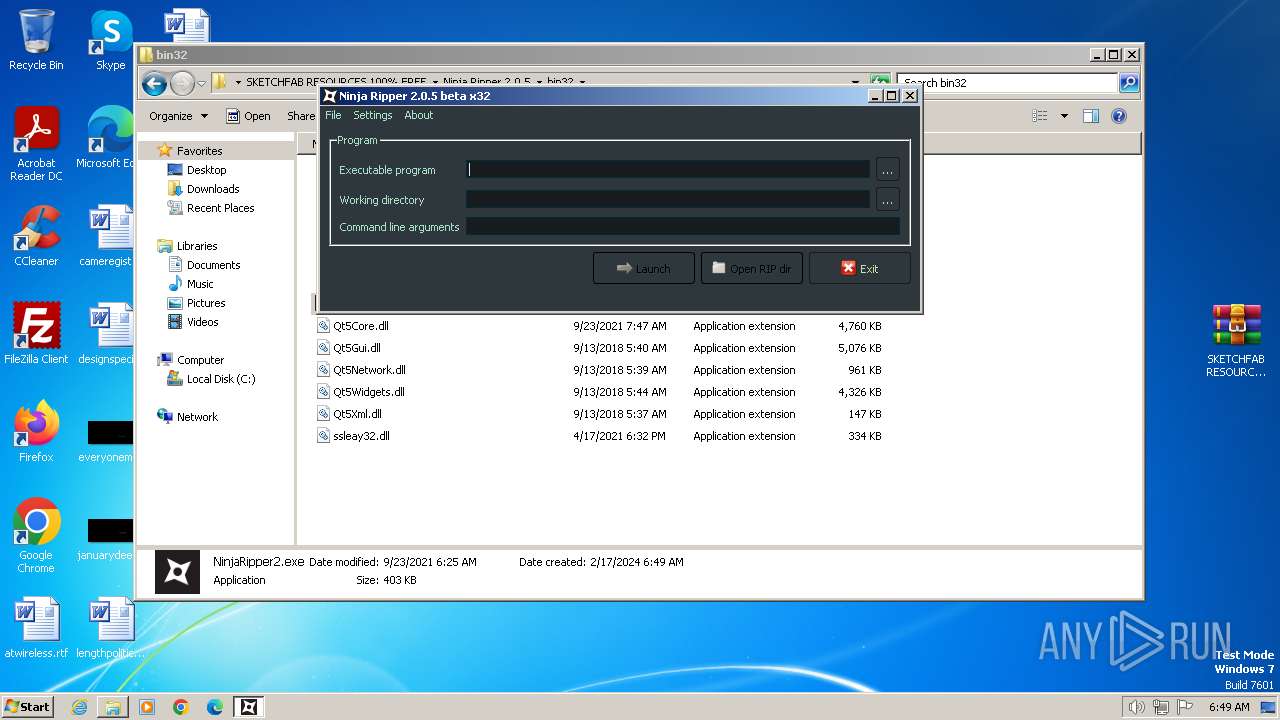
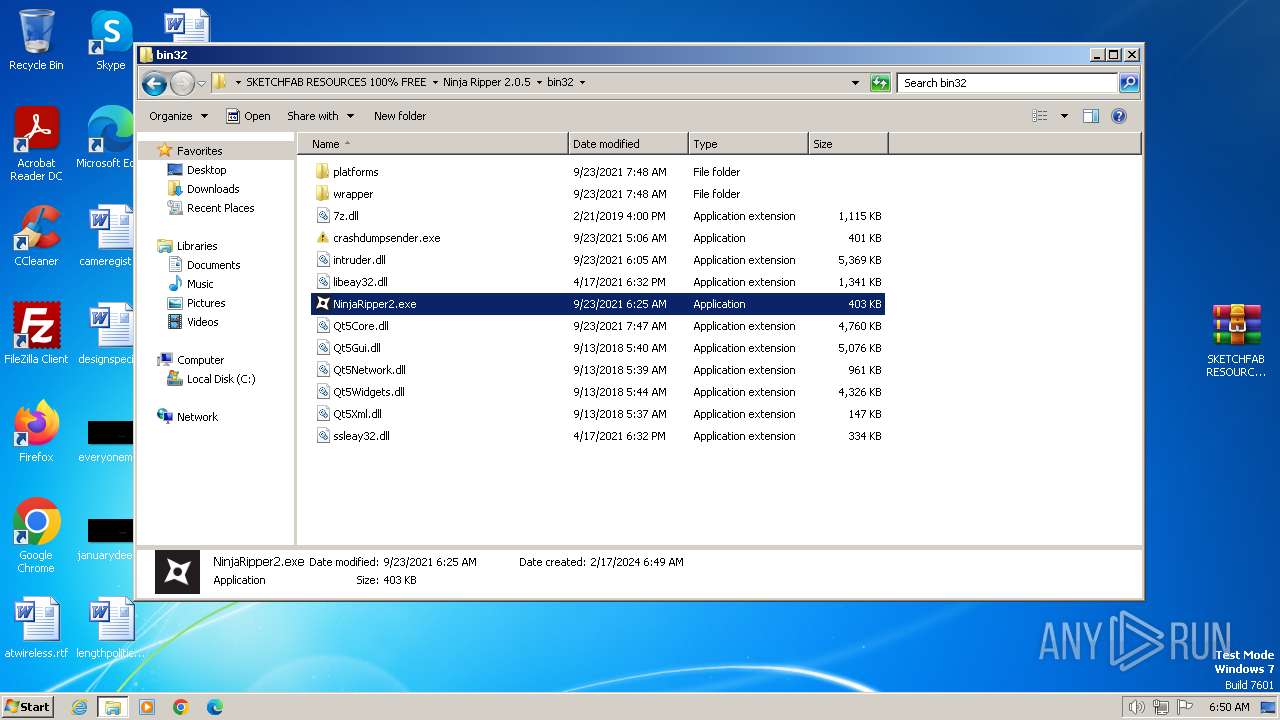
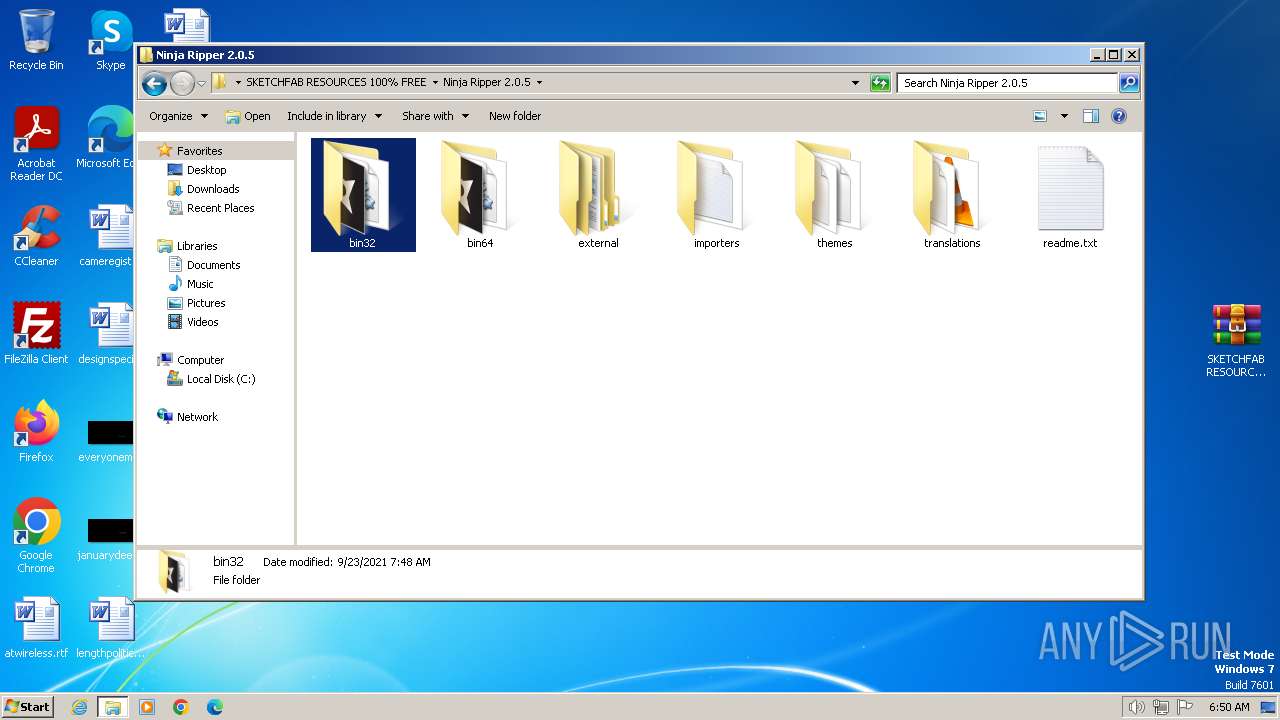
| 2228 | "C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\NinjaRipper2.exe" | C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\NinjaRipper2.exe | explorer.exe | ||||||||||||
User: admin Company: blackninja Integrity Level: MEDIUM Description: Ninja Ripper Injector Exit code: 0 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3368 --field-trial-handle=1124,i,6103960125240165427,14342743250369415756,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
16 209
Read events
15 957
Write events
244
Delete events
8
Modification events
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
78
Suspicious files
97
Text files
138
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f2dc.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f2cc.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f339.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF17f983.TMP | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF17f4b0.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:4755704EAEB72509F8E78594142D80D6 | SHA256:52D45B3A4947B8B5B8C48F83F83BA6758CFB7C4434FC574124378F5B01E15999 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
50
DNS requests
36
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 5.78 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 10.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 13.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 17.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 13.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 28.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 57.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 117 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6eob6nunr64xlqs3i7jpbbwlqa_20230923.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230923.567854667.14_all_ENUS500000_ace7f54yxy3vtmc2mjkr5yii7sta.crx3 | unknown | binary | 210 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3864 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3948 | chrome.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
3948 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3948 | chrome.exe | 172.217.16.202:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
3948 | chrome.exe | 66.203.124.37:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
3948 | chrome.exe | 216.58.206.42:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
3948 | chrome.exe | 66.203.125.15:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
g.api.mega.co.nz |
| shared |
www.google.com |
| whitelisted |
gfs206n181.userstorage.mega.co.nz |
| unknown |
gfs208n114.userstorage.mega.co.nz |
| unknown |
gfs204n124.userstorage.mega.co.nz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3948 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
3948 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
Process | Message |
|---|---|
NinjaRipper2.exe | NR[3632]: ****NinjaRipper2****
|
NinjaRipper2.exe | NR[3632]: Exe: C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\NinjaRipper2.exe
|
NinjaRipper2.exe | NR[3632]: Pid=2228
|
NinjaRipper2.exe | NR[3632]: CmdLine: "C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\NinjaRipper2.exe"
|
NinjaRipper2.exe | NR[3632]: WorkDir: C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32
|
NinjaRipper2.exe | NR[3632]: New QtPlugin dir=C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\
|
NinjaRipper2.exe | NR[3632]: New QtPlugin dir=C:\Users\admin\Desktop\SKETCHFAB RESOURCES 100% FREE\Ninja Ripper 2.0.5\bin32\platforms
|