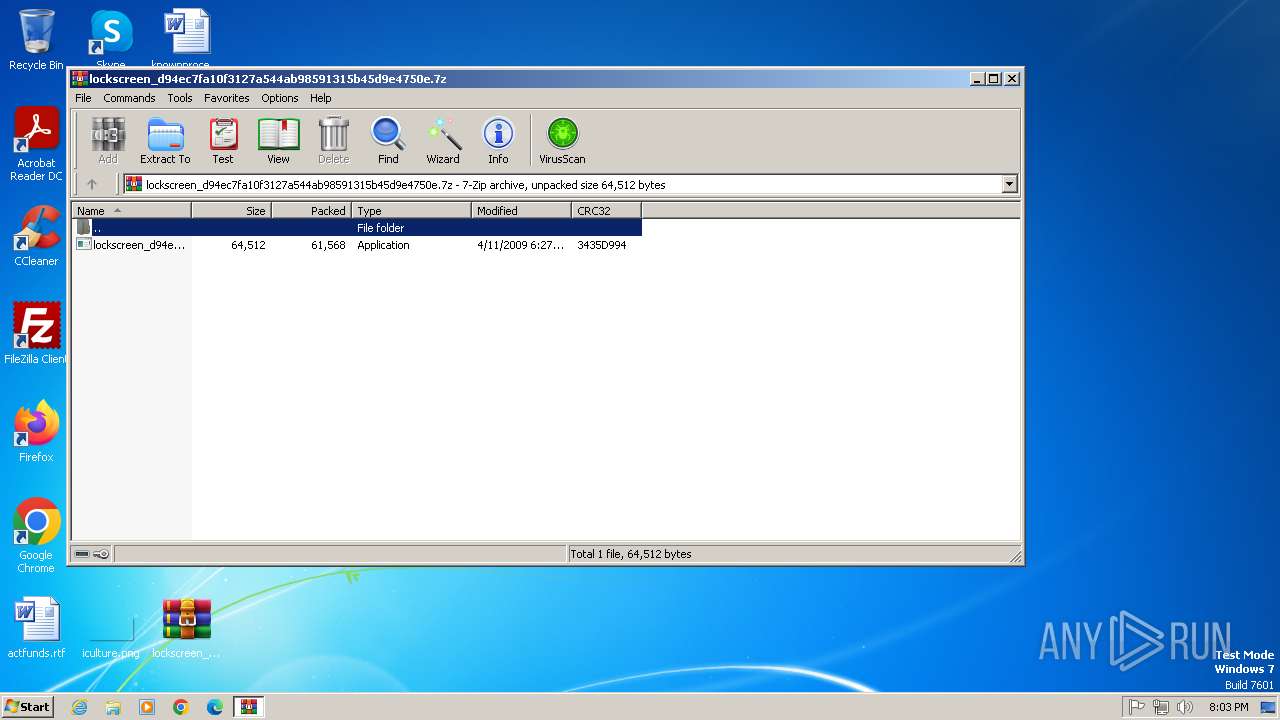
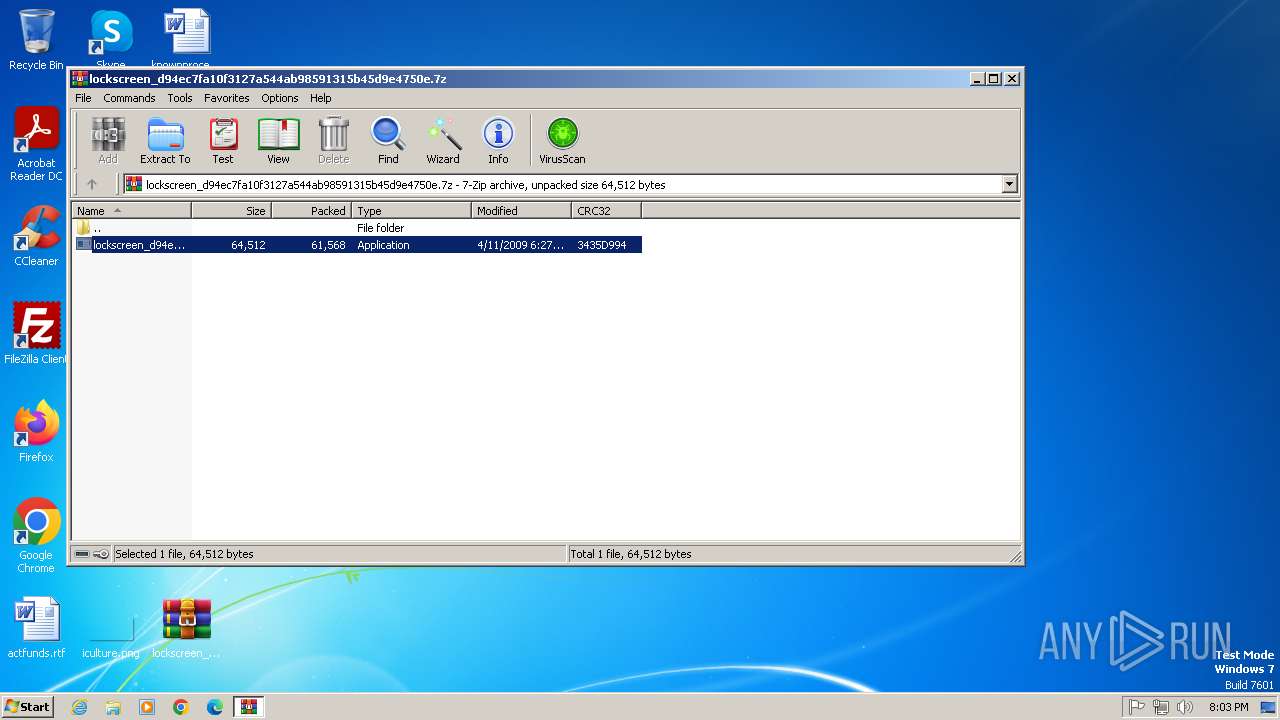
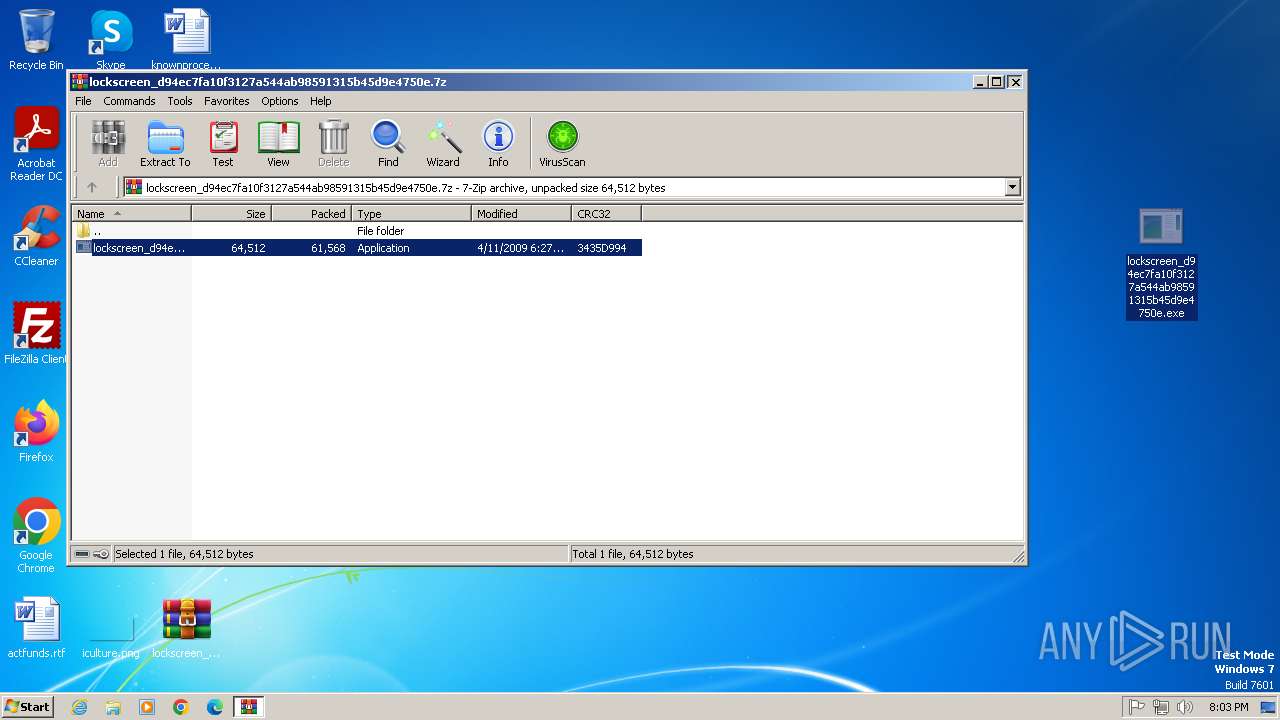
| File name: | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.7z |
| Full analysis: | https://app.any.run/tasks/1455d36d-16b9-4f19-b2a2-2802e78dbce9 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 19:03:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | FF5352BF8C5C67FE02F9141EEB48F296 |
| SHA1: | 0BBB965A7F25923450E81AA3B71438BE1D550DFE |
| SHA256: | 19650C5A7D19087F2AC8133F521F2855246103EF38D6C01D4041DFCB5823F71D |
| SSDEEP: | 1536:5HyKQYhttArOD3NJ1+8cRZL/jADKzuDe2FNPGKvTbOzP:gm/ArOv1+zBADK6De2FNGKs |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2812)
Changes the autorun value in the registry
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
SUSPICIOUS
Executable content was dropped or overwritten
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
Reads the Internet Settings
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
- svhcost.exe (PID: 2944)
Executing commands from a ".bat" file
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
Starts CMD.EXE for commands execution
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
Reads security settings of Internet Explorer
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
- svhcost.exe (PID: 2944)
Starts itself from another location
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
There is functionality for taking screenshot (YARA)
- svhcost.exe (PID: 2944)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2812)
The sample compiled with english language support
- WinRAR.exe (PID: 2812)
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
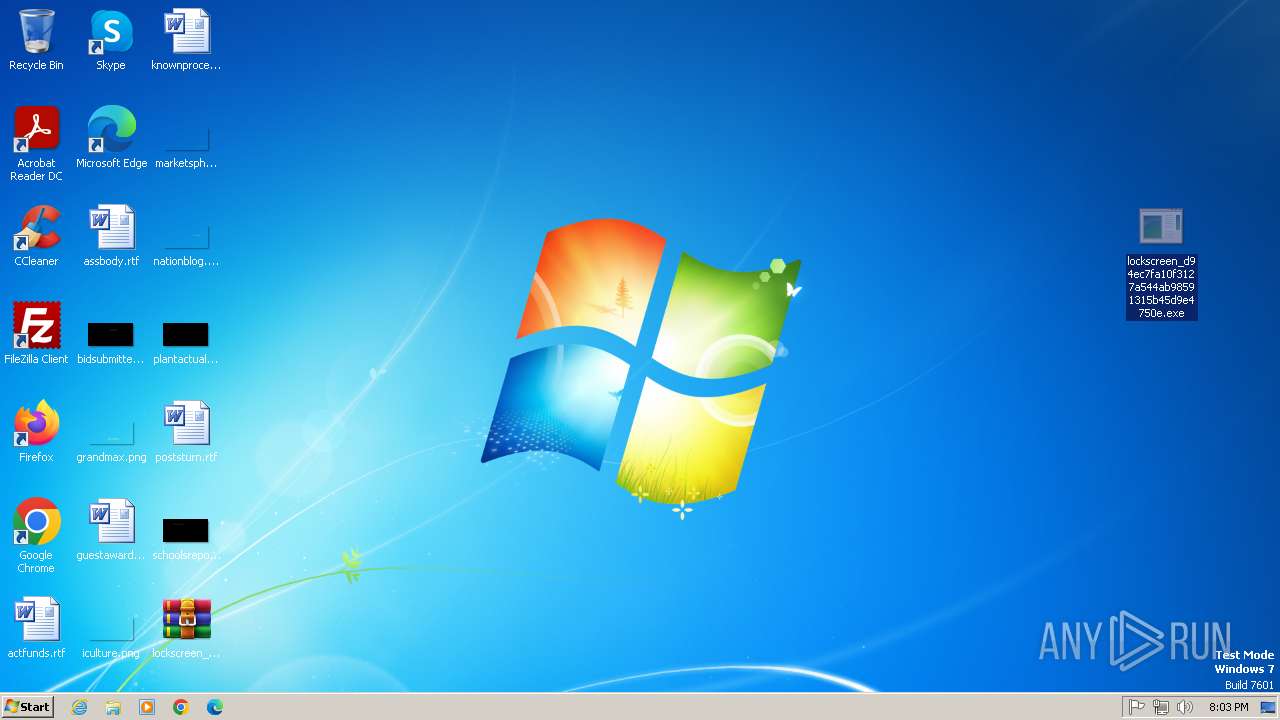
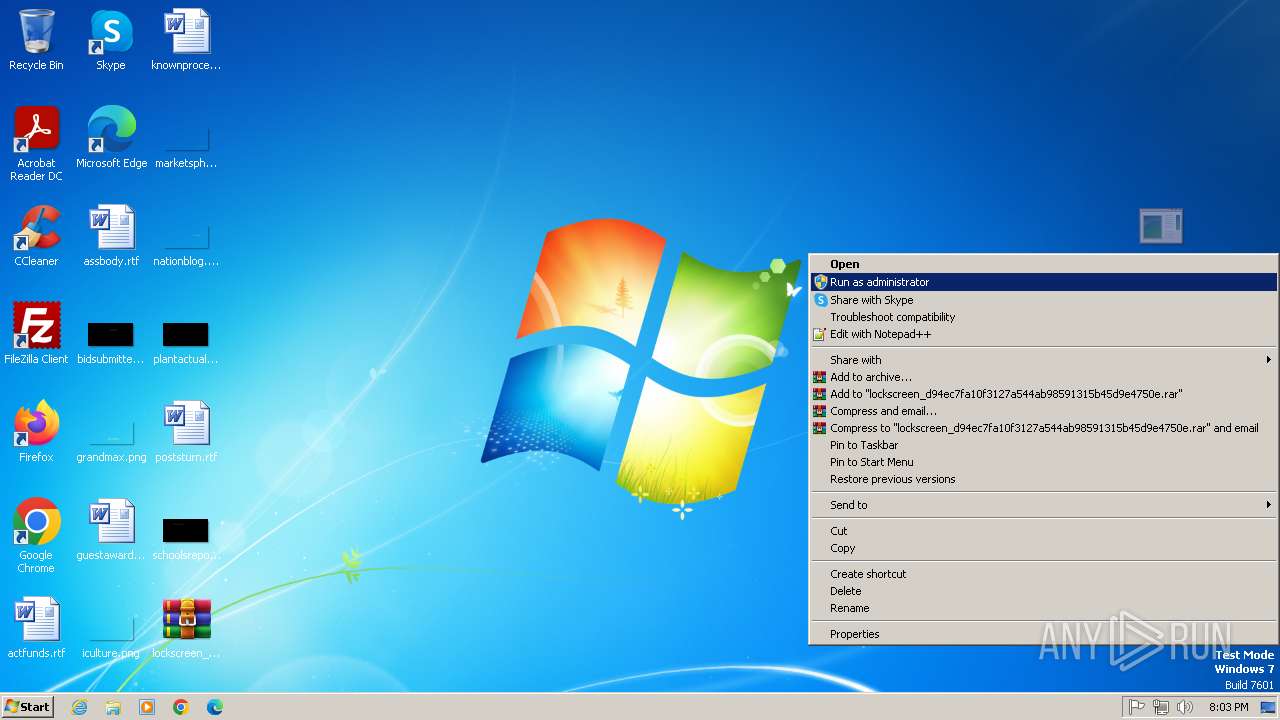
Manual execution by a user
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
Creates files or folders in the user directory
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
Checks supported languages
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
- svhcost.exe (PID: 2944)
Reads the computer name
- lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe (PID: 2612)
- svhcost.exe (PID: 2944)
Checks proxy server information
- svhcost.exe (PID: 2944)
Reads the machine GUID from the registry
- svhcost.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2009:04:11 05:27:38+00:00 |
| ArchivedFileName: | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 972 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\clean.bat" " | C:\Windows\System32\cmd.exe | — | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\Desktop\lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe" | C:\Users\admin\Desktop\lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
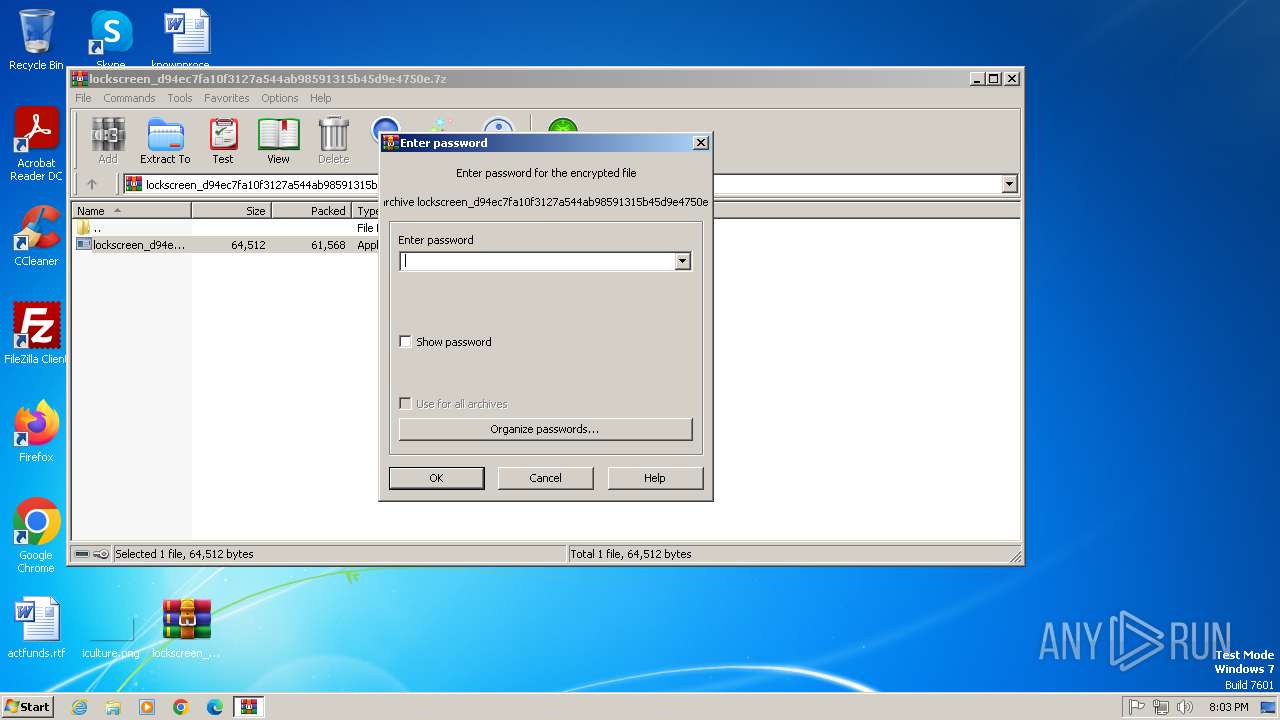
| 2812 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\AppData\Roaming\Microsoft\svhcost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\svhcost.exe | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 140
Read events
3 082
Write events
52
Delete events
6
Modification events
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.7z | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2812) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2812.11289\lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | executable | |
MD5:369CE141D3D15186650367B74EC397B4 | SHA256:584EA11AA614D7BEFBE6403E8C8291715A465F9C5B82669C2711BEF732D6CD6E | |||
| 2612 | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | C:\Users\admin\AppData\Roaming\Microsoft\svhcost.exe | executable | |
MD5:369CE141D3D15186650367B74EC397B4 | SHA256:584EA11AA614D7BEFBE6403E8C8291715A465F9C5B82669C2711BEF732D6CD6E | |||
| 2612 | lockscreen_d94ec7fa10f3127a544ab98591315b45d9e4750e.exe | C:\Users\admin\Desktop\clean.bat | text | |
MD5:4FEAA73BEC8EC6B8E50B4ACCF38792A8 | SHA256:A36D6EDD307477176C3E7D59B6E18279439C612A927E7A09CE1781768841FE40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | svhcost.exe | POST | 404 | 49.13.77.253:80 | http://cutsomd.com/index.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2944 | svhcost.exe | 49.13.77.253:80 | cutsomd.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
cutsomd.com |
| unknown |