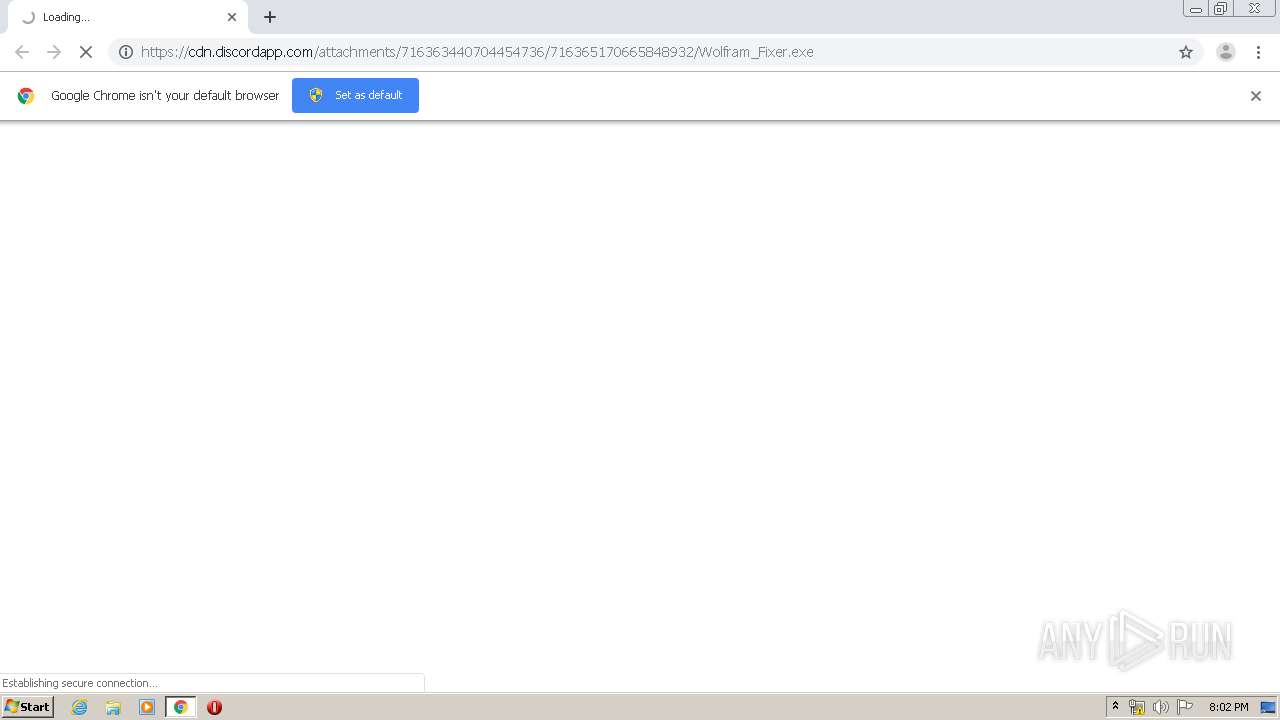
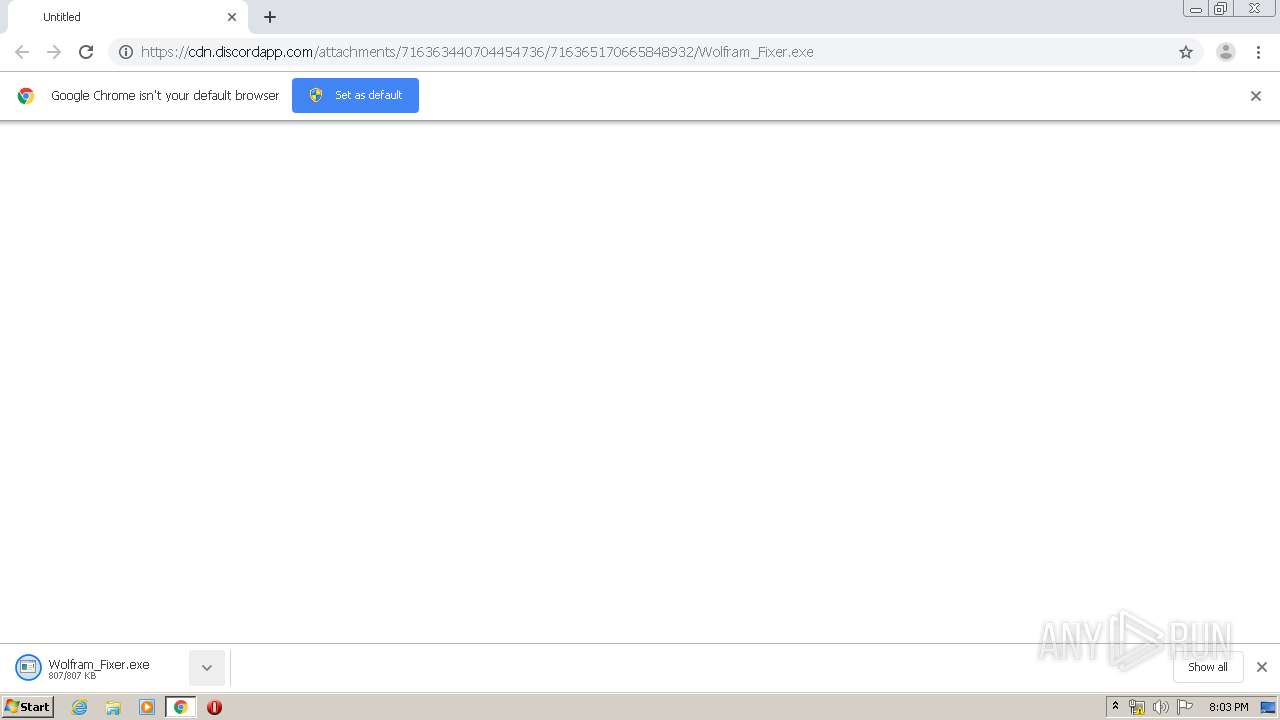
| URL: | https://cdn.discordapp.com/attachments/716363440704454736/716365170665848932/Wolfram_Fixer.exe |
| Full analysis: | https://app.any.run/tasks/02eb4f7d-8363-48a6-a4c7-c747d37949a5 |
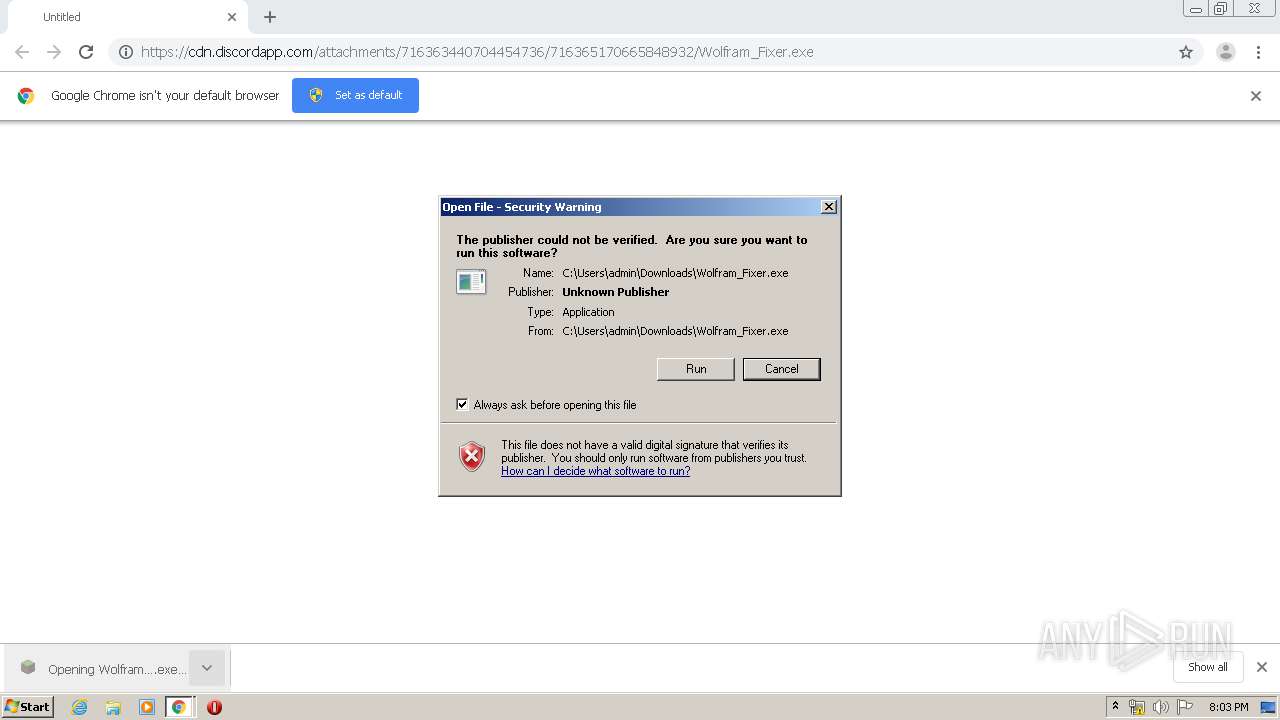
| Verdict: | Malicious activity |
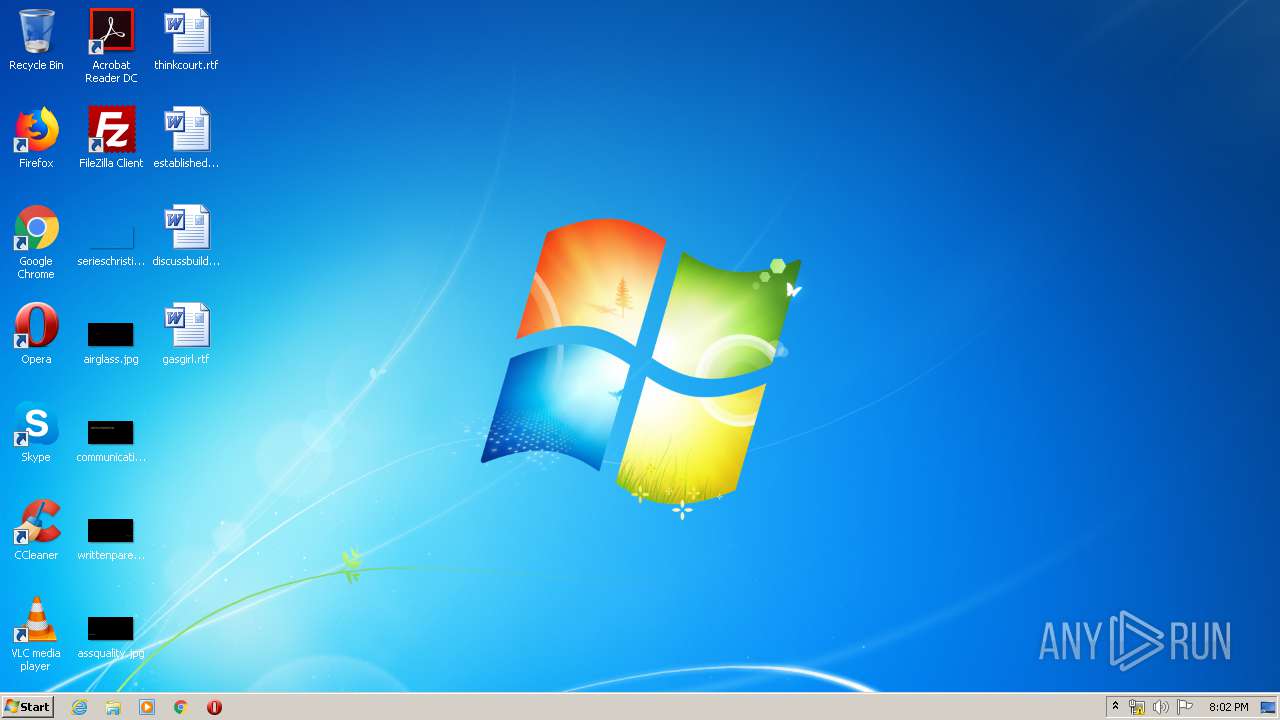
| Analysis date: | May 30, 2020, 19:02:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 02DF2C49179C73A70D680BEB223F8378 |
| SHA1: | 482B36E9ED0C8A83DD3F6C17863FF2477A88A121 |
| SHA256: | 19618F0D70D5C6693D6627A22462FD759E36E397FA1C270D9ADFDFF682AF88BE |
| SSDEEP: | 3:N8cCWdy6//nTUWFlTKalkTEXADR6jMGn:2cry6XnYWLTK7gXADR8 |
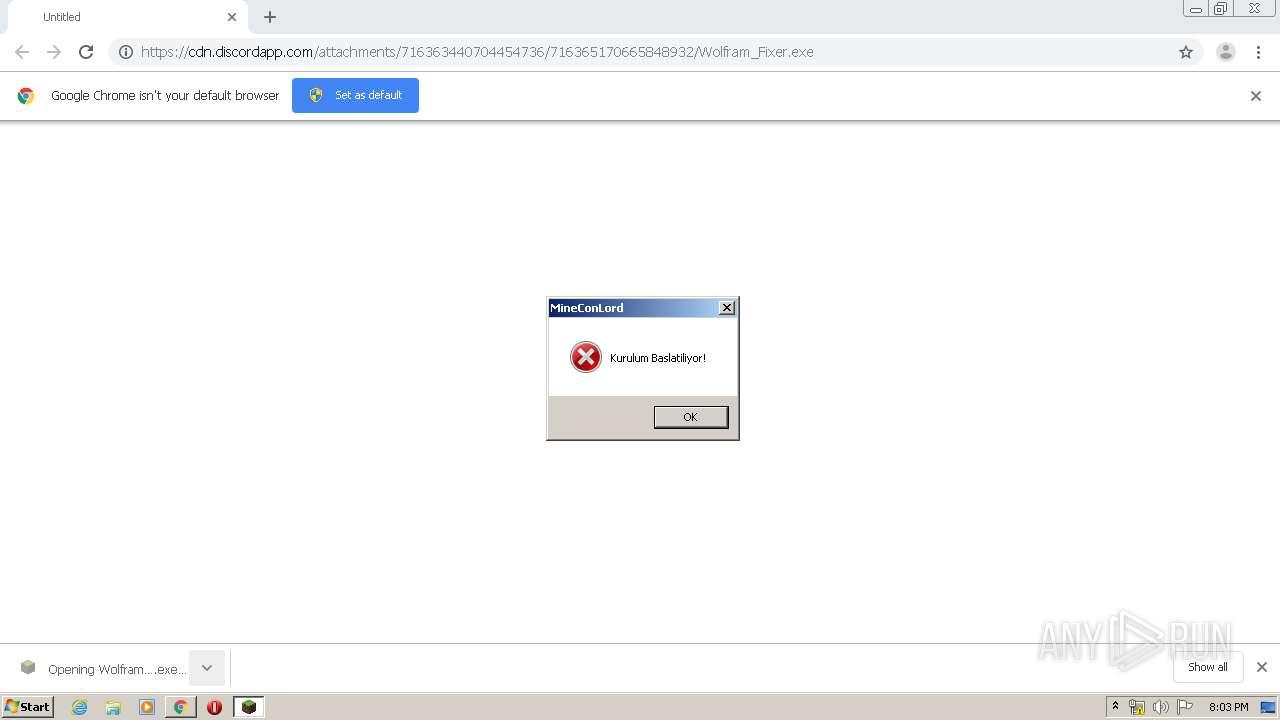
MALICIOUS
Changes Security Center notification settings
- msdcsc.exe (PID: 2264)
Application was dropped or rewritten from another process
- Wolfram_Fixer.exe (PID: 3580)
- msdcsc.exe (PID: 2264)
Changes the autorun value in the registry
- Wolfram_Fixer.exe (PID: 3580)
- msdcsc.exe (PID: 2264)
- explorer.exe (PID: 1936)
Changes the login/logoff helper path in the registry
- Wolfram_Fixer.exe (PID: 3580)
SUSPICIOUS
Starts Internet Explorer
- msdcsc.exe (PID: 2264)
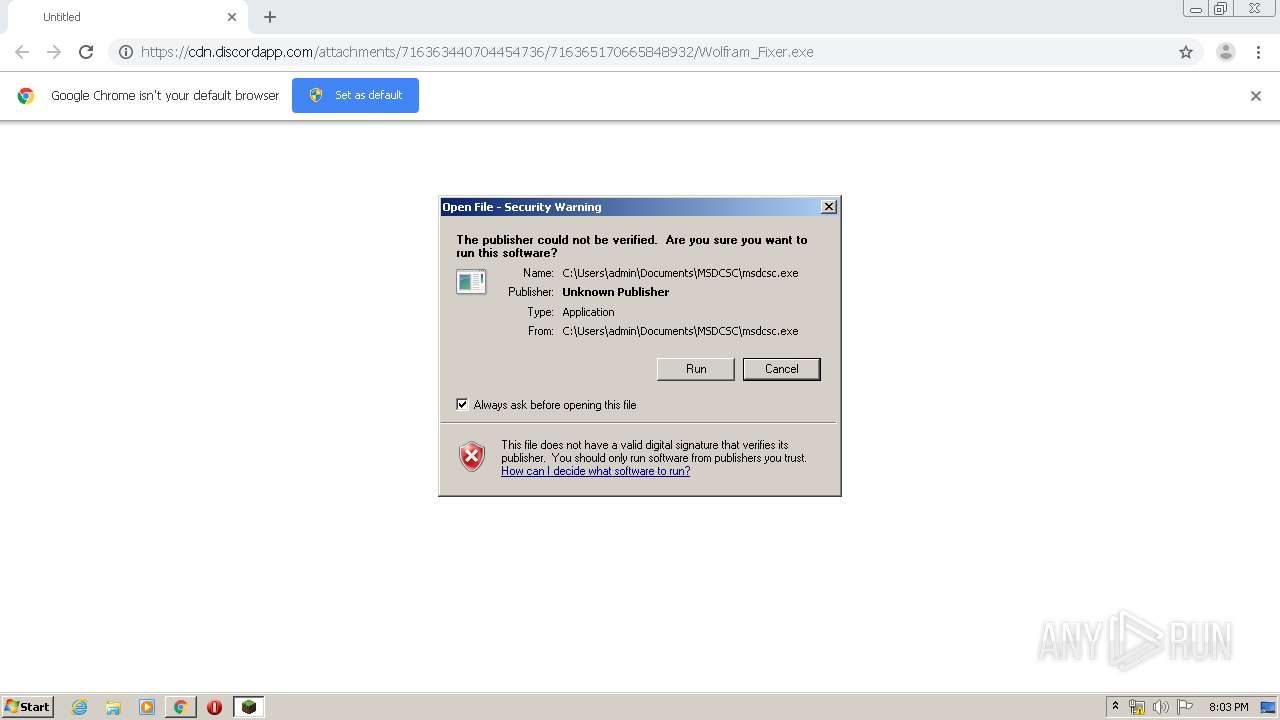
Executable content was dropped or overwritten
- chrome.exe (PID: 1196)
- chrome.exe (PID: 1160)
- Wolfram_Fixer.exe (PID: 3580)
Starts CMD.EXE for commands execution
- Wolfram_Fixer.exe (PID: 3580)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2080)
- cmd.exe (PID: 2300)
Starts itself from another location
- Wolfram_Fixer.exe (PID: 3580)
INFO
Application launched itself
- chrome.exe (PID: 1196)
Reads the hosts file
- chrome.exe (PID: 1196)
- chrome.exe (PID: 1160)
Reads Internet Cache Settings
- chrome.exe (PID: 1196)
Reads settings of System Certificates
- chrome.exe (PID: 1160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
20
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2136 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | notepad | C:\Windows\system32\notepad.exe | — | Wolfram_Fixer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9170087251852807215,4620695401133829337,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6661044698332534990 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://cdn.discordapp.com/attachments/716363440704454736/716365170665848932/Wolfram_Fixer.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,9170087251852807215,4620695401133829337,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8812852998149607453 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | msdcsc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Downloads\Wolfram_Fixer.exe" +s +h | C:\Windows\System32\cmd.exe | — | Wolfram_Fixer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,9170087251852807215,4620695401133829337,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1581176983507380329 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | msdcsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | Wolfram_Fixer.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 674
Read events
1 547
Write events
124
Delete events
3
Modification events
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1196-13235338977990625 |
Value: 259 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1196) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
10
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5ED2ADE2-4AC.pma | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0e38b451-ea55-4fee-9d35-c80fb051a1da.tmp | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12abd8.TMP | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12addc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
8
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1160 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1160 | chrome.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
1160 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1160 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1160 | chrome.exe | 216.58.212.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1160 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1160 | chrome.exe | 216.58.206.14:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
1936 | explorer.exe | 88.230.228.134:1604 | gamerofsultan.duckdns.org | Turk Telekom | TR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
gamerofsultan.duckdns.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |