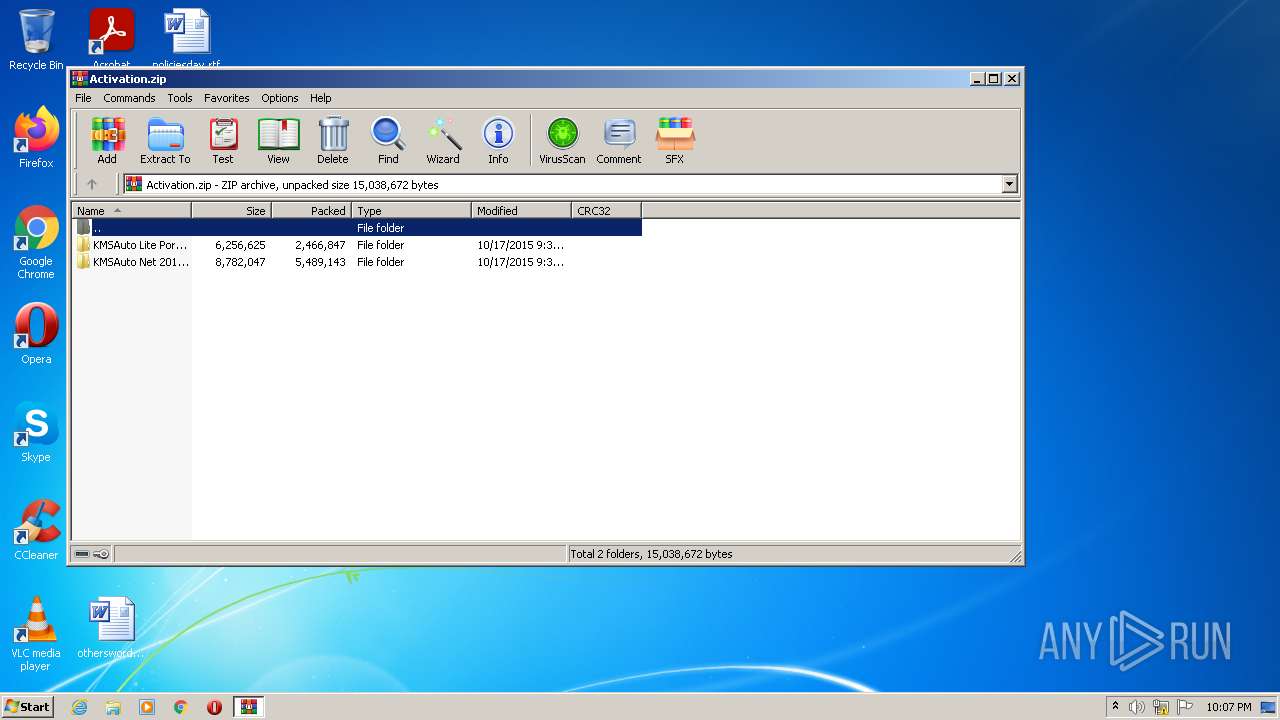
| File name: | Activation.zip |
| Full analysis: | https://app.any.run/tasks/759da05c-e950-4ac8-9e41-499d423bed69 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 22:07:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 4674F2AFCF4ABF39C7C49F38AF75AFB9 |
| SHA1: | 14C572587B8E77663BDECDBC75AE68BC32B3D2E9 |
| SHA256: | 195A48AE157F64294103B83922742F8F16B6EB40F24775B298DF2A8B50081F1F |
| SSDEEP: | 98304:SKK+7pxMlYKZUJd3QgdcAtVf6flFCYRC0j17lKlcWvHhWnPZ5HdLxLDI/s/Yaf/8:0+0BZUJdqAtJ0j17wKwEnPXvIUtSdiC |
MALICIOUS
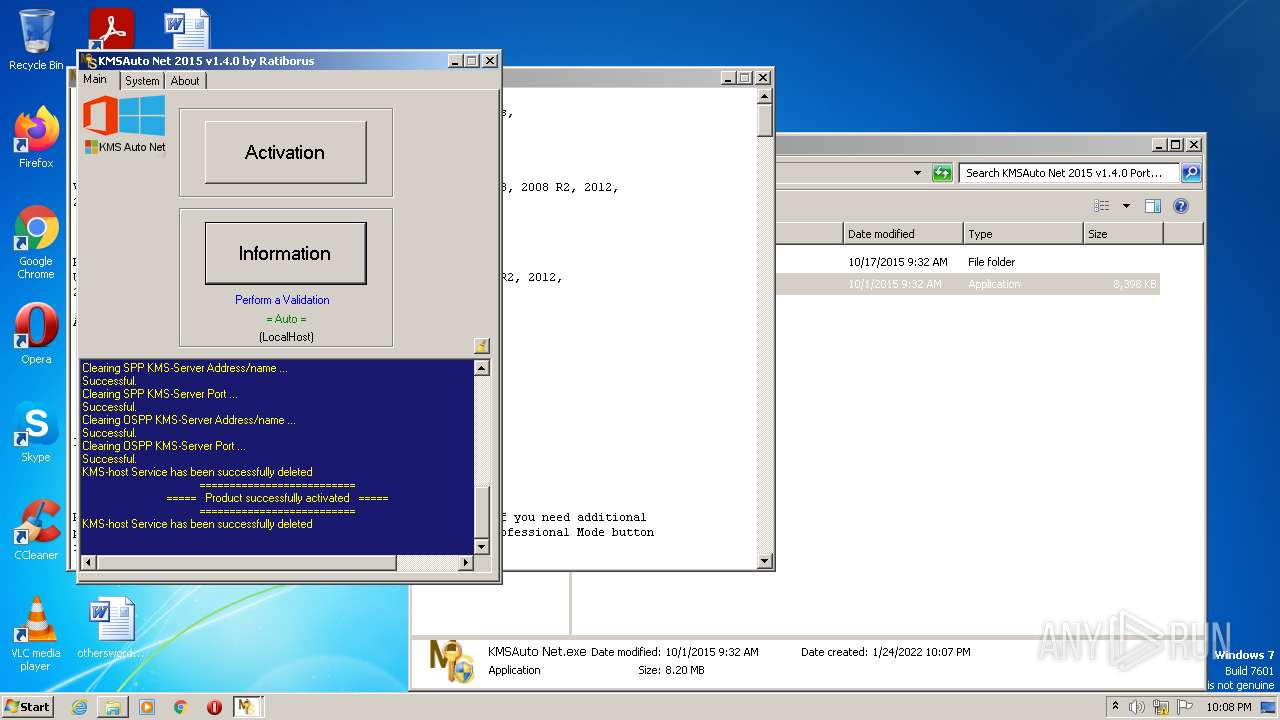
Application was dropped or rewritten from another process
- KMSAuto Net.exe (PID: 276)
- bin_x86.dat (PID: 2484)
- bin.dat (PID: 1620)
- KMSSS.exe (PID: 1076)
- bin.dat (PID: 240)
- bin_x86.dat (PID: 3464)
Drops executable file immediately after starts
- bin_x86.dat (PID: 2484)
- bin.dat (PID: 1620)
- bin.dat (PID: 240)
- bin_x86.dat (PID: 3464)
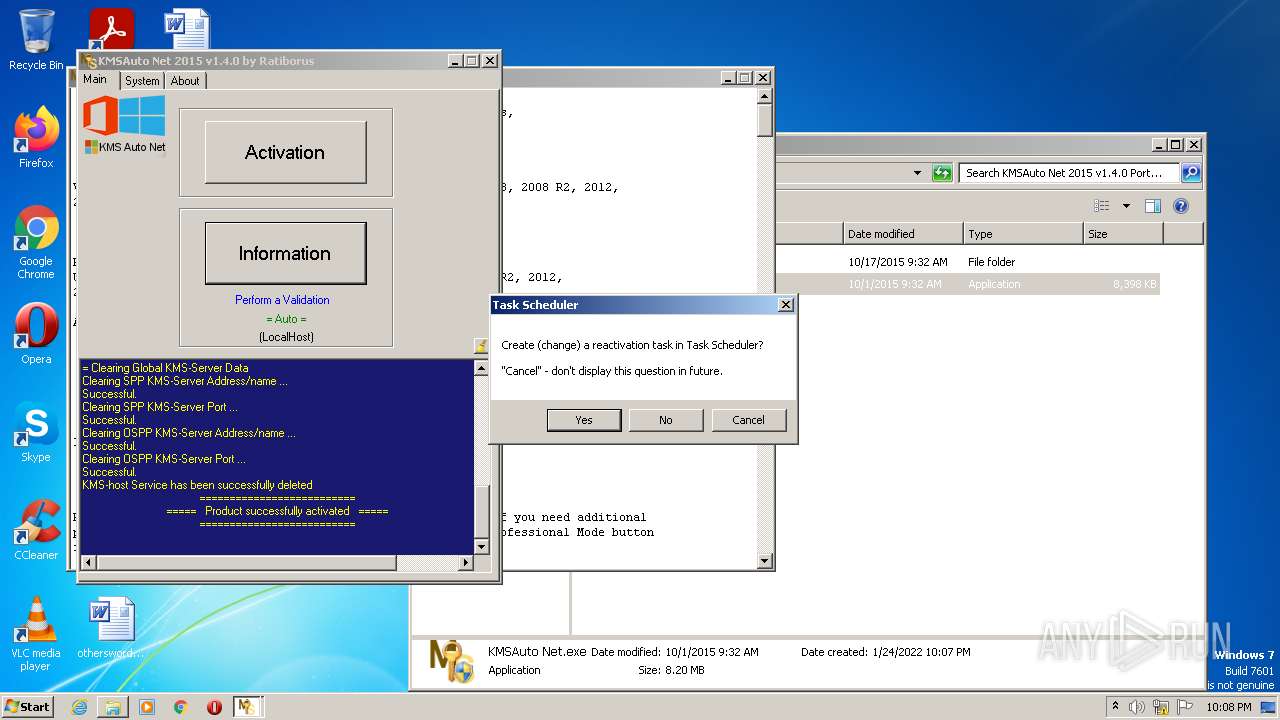
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1992)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 3152)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4084)
- schtasks.exe (PID: 3444)
- schtasks.exe (PID: 3836)
- schtasks.exe (PID: 1808)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1256)
- KMSAuto Net.exe (PID: 276)
- bin.dat (PID: 1620)
- bin_x86.dat (PID: 2484)
- bin.dat (PID: 240)
- bin_x86.dat (PID: 3464)
Reads the computer name
- WinRAR.exe (PID: 1256)
- KMSAuto Net.exe (PID: 276)
- cscript.exe (PID: 3820)
- KMSSS.exe (PID: 1076)
Checks supported languages
- WinRAR.exe (PID: 1256)
- KMSAuto Net.exe (PID: 276)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 1128)
- cmd.exe (PID: 1356)
- cscript.exe (PID: 3820)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 3712)
- bin.dat (PID: 1620)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2792)
- bin_x86.dat (PID: 2484)
- cmd.exe (PID: 2872)
- cmd.exe (PID: 2940)
- KMSSS.exe (PID: 1076)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 1992)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 3916)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 2768)
- bin.dat (PID: 240)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 2960)
- bin_x86.dat (PID: 3464)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 1460)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 3152)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 276)
- cmd.exe (PID: 2792)
Starts CMD.EXE for self-deleting
- KMSAuto Net.exe (PID: 276)
Reads Environment values
- KMSAuto Net.exe (PID: 276)
- Netsh.exe (PID: 2208)
- Netsh.exe (PID: 1368)
- Netsh.exe (PID: 2052)
- Netsh.exe (PID: 320)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 276)
Executes scripts
- KMSAuto Net.exe (PID: 276)
Creates files in the program directory
- KMSAuto Net.exe (PID: 276)
- bin.dat (PID: 1620)
- bin_x86.dat (PID: 2484)
- KMSSS.exe (PID: 1076)
- bin.dat (PID: 240)
- bin_x86.dat (PID: 3464)
Starts application with an unusual extension
- cmd.exe (PID: 3712)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 2168)
Drops a file that was compiled in debug mode
- bin.dat (PID: 1620)
- bin_x86.dat (PID: 2484)
- bin.dat (PID: 240)
- bin_x86.dat (PID: 3464)
Drops a file with too old compile date
- bin_x86.dat (PID: 2484)
- bin_x86.dat (PID: 3464)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 2940)
Uses NETSH.EXE for network configuration
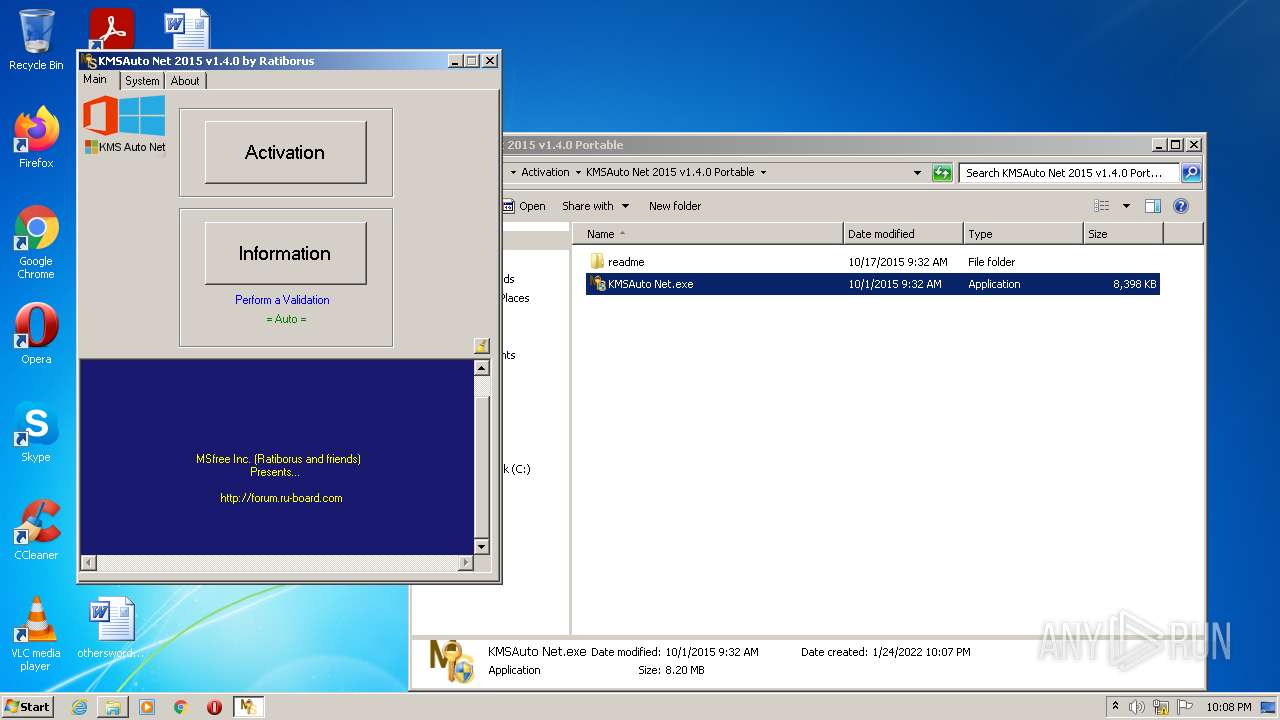
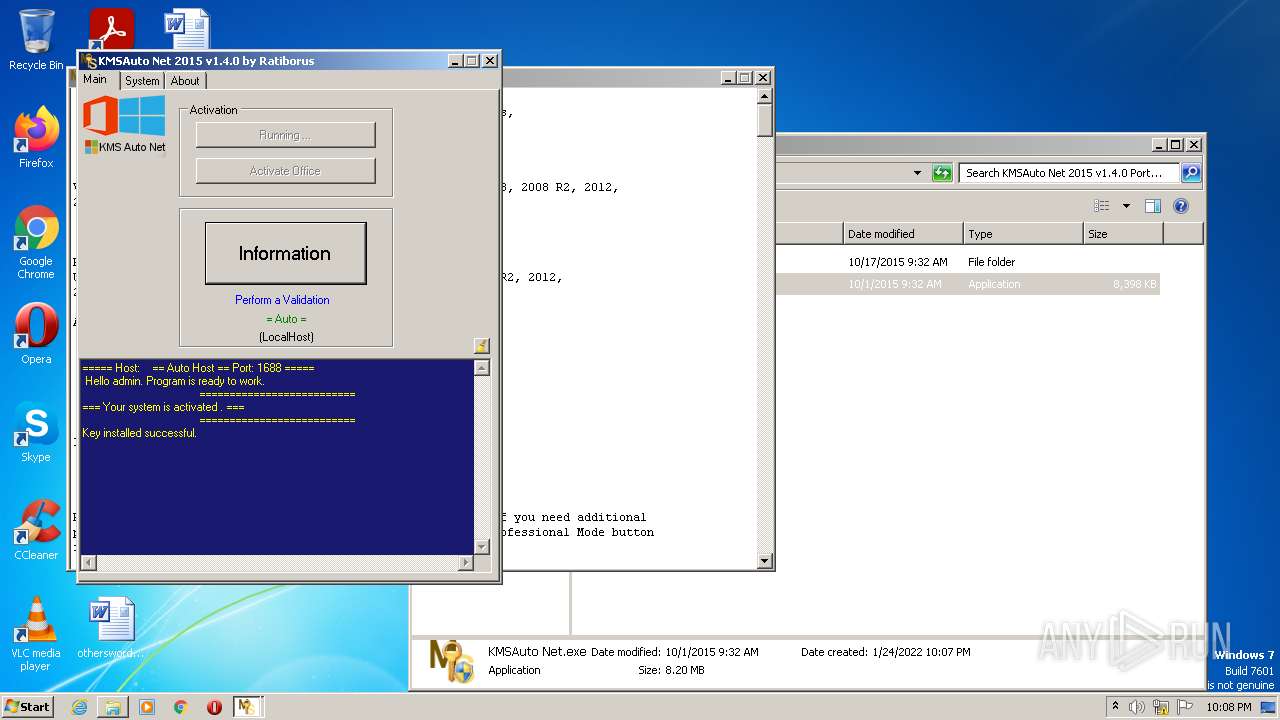
- KMSAuto Net.exe (PID: 276)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 276)
Application launched itself
- cmd.exe (PID: 2792)
Executed as Windows Service
- KMSSS.exe (PID: 1076)
Uses REG.EXE to modify Windows registry
- KMSAuto Net.exe (PID: 276)
- cmd.exe (PID: 3916)
Creates or modifies windows services
- KMSAuto Net.exe (PID: 276)
INFO
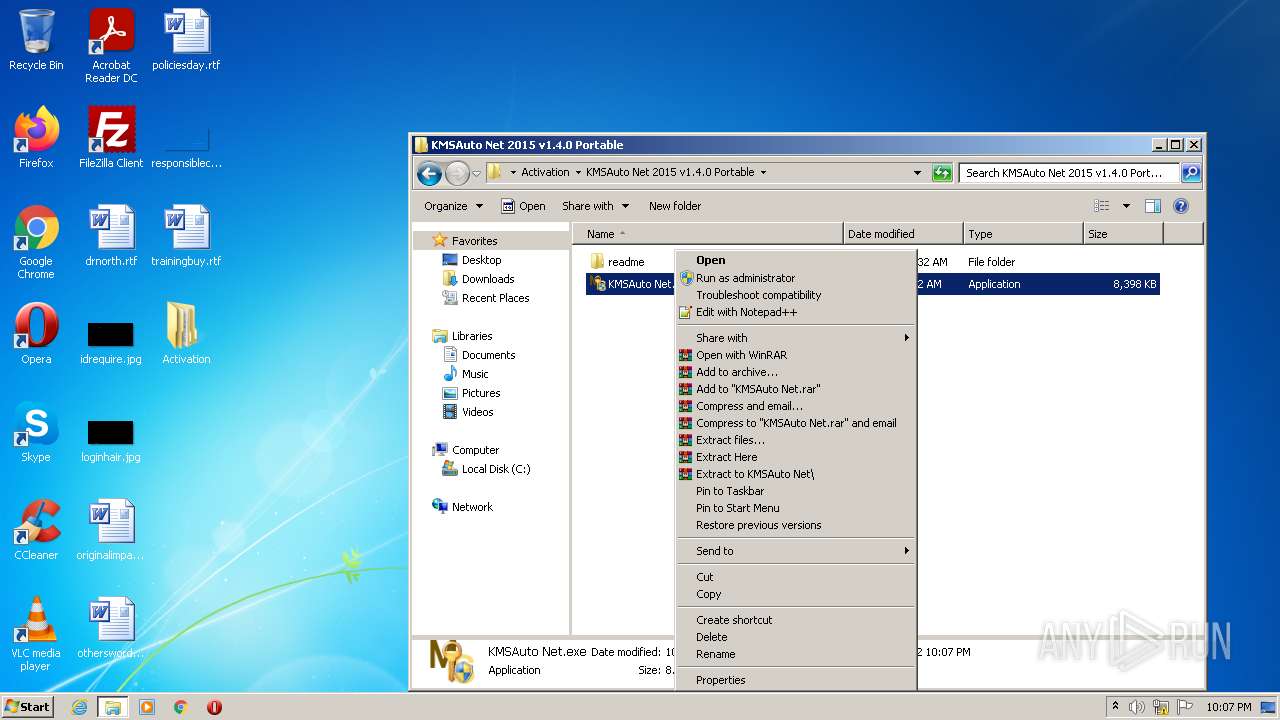
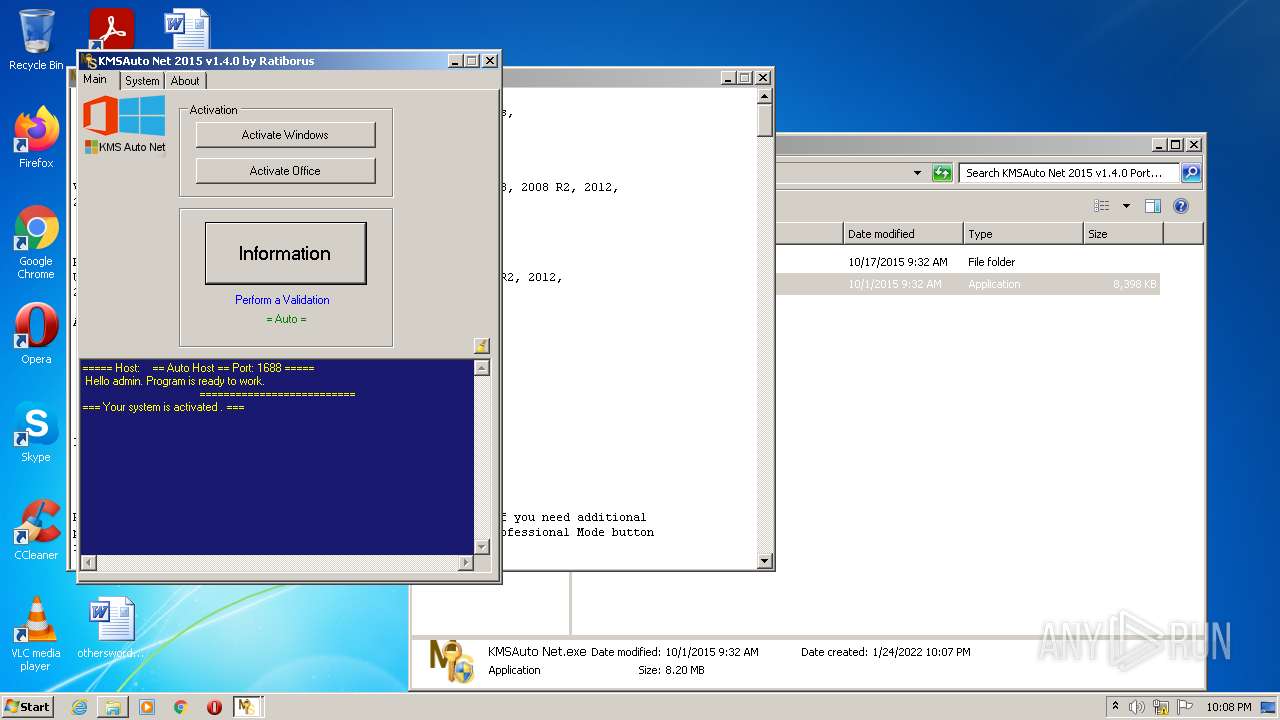
Manual execution by user
- KMSAuto Net.exe (PID: 276)
Checks Windows Trust Settings
- cscript.exe (PID: 3820)
Reads the computer name
- NETSTAT.EXE (PID: 3096)
- sc.exe (PID: 304)
- Netsh.exe (PID: 2208)
- Netsh.exe (PID: 1368)
- sc.exe (PID: 3220)
- sc.exe (PID: 2980)
- sc.exe (PID: 988)
- Netsh.exe (PID: 2052)
- Netsh.exe (PID: 320)
- schtasks.exe (PID: 4084)
- schtasks.exe (PID: 3444)
- schtasks.exe (PID: 3836)
- schtasks.exe (PID: 1808)
Checks supported languages
- NETSTAT.EXE (PID: 3096)
- find.exe (PID: 3040)
- Netsh.exe (PID: 2208)
- Netsh.exe (PID: 1368)
- sc.exe (PID: 304)
- sc.exe (PID: 3220)
- reg.exe (PID: 4036)
- reg.exe (PID: 2992)
- reg.exe (PID: 2072)
- reg.exe (PID: 2664)
- reg.exe (PID: 2828)
- reg.exe (PID: 2640)
- sc.exe (PID: 2980)
- sc.exe (PID: 988)
- Netsh.exe (PID: 2052)
- reg.exe (PID: 3768)
- Netsh.exe (PID: 320)
- schtasks.exe (PID: 4084)
- schtasks.exe (PID: 3444)
- schtasks.exe (PID: 3836)
- schtasks.exe (PID: 1808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
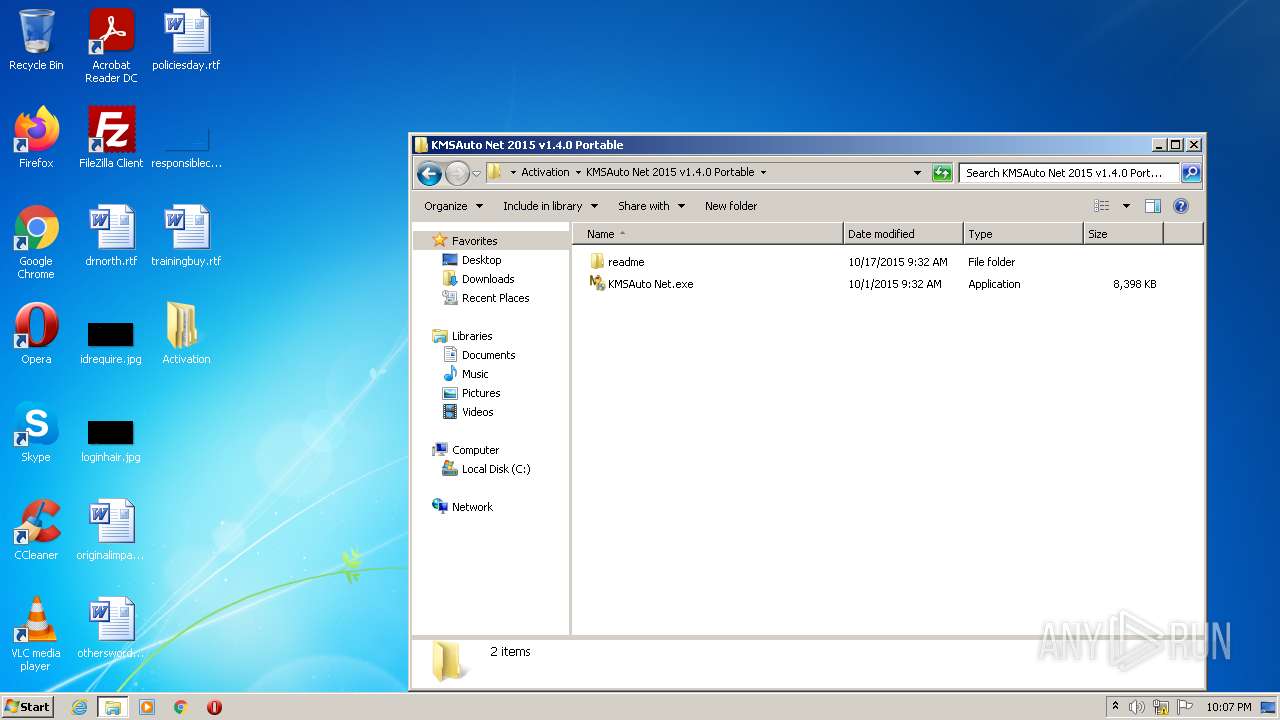
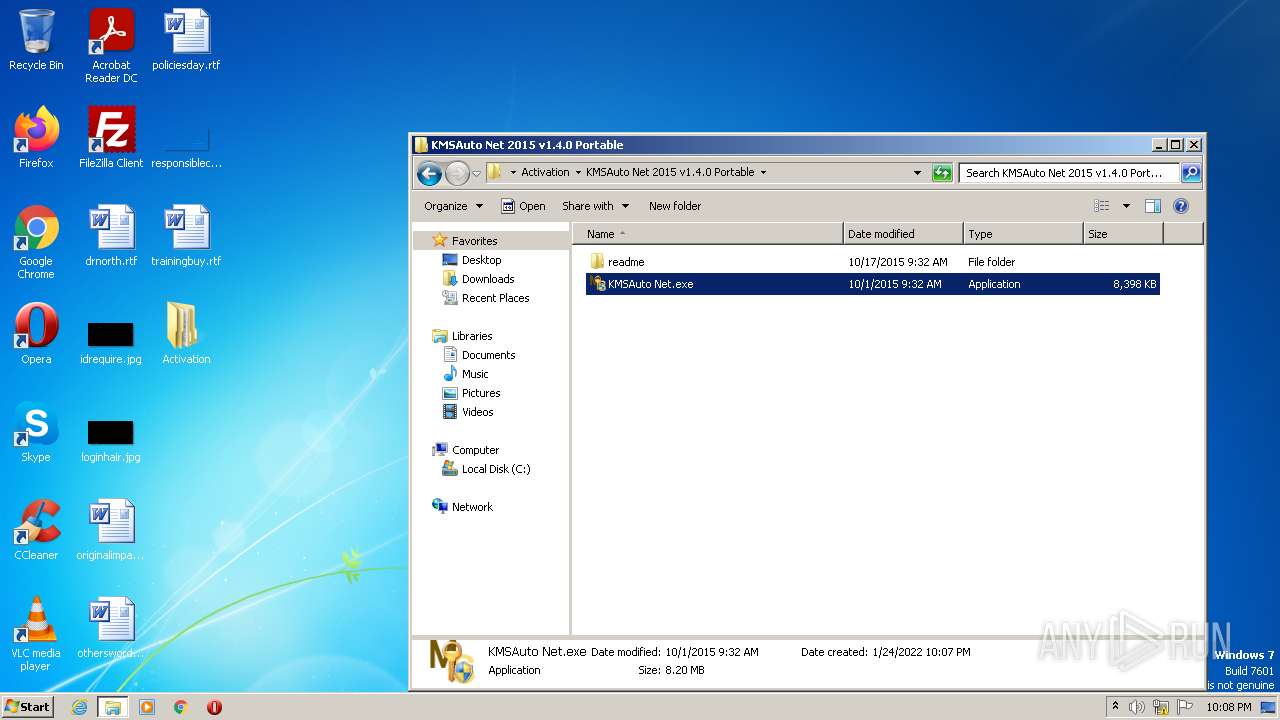
| ZipFileName: | KMSAuto Net 2015 v1.4.0 Portable/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2015:10:17 11:32:20 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
137
Monitored processes
55
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | bin.dat -y -pkmsauto | C:\ProgramData\KMSAutoS\bin.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
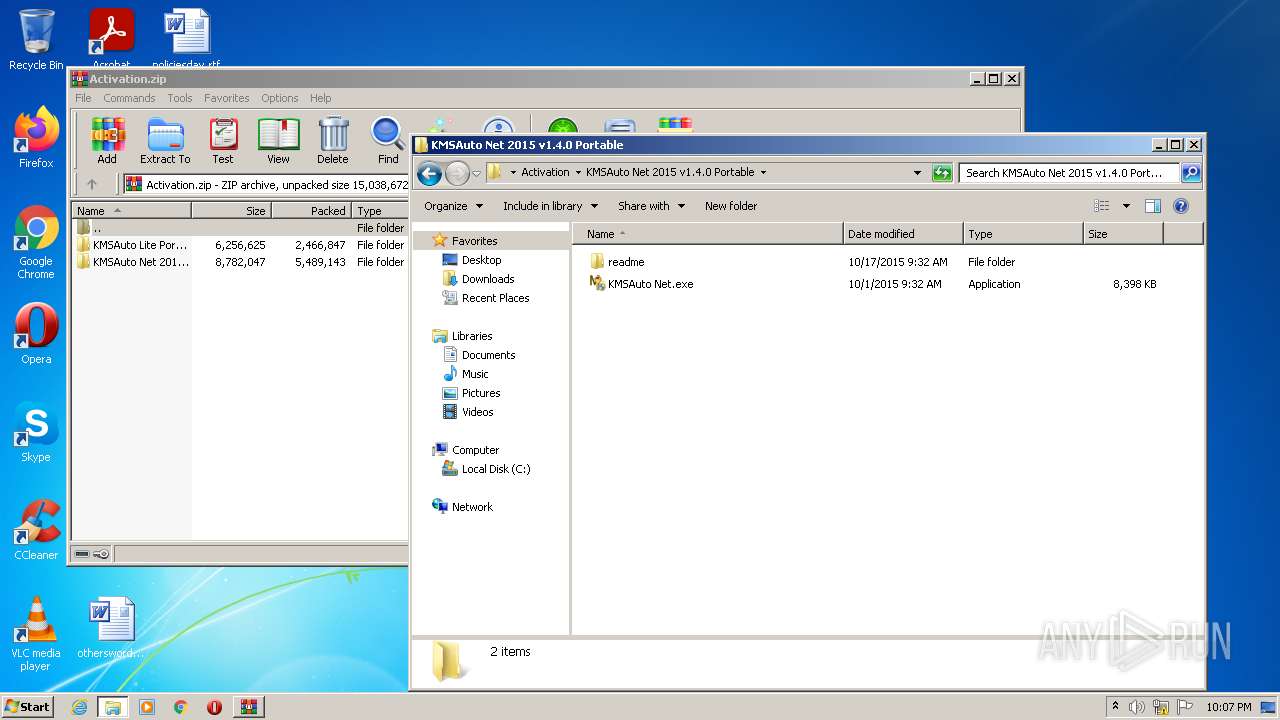
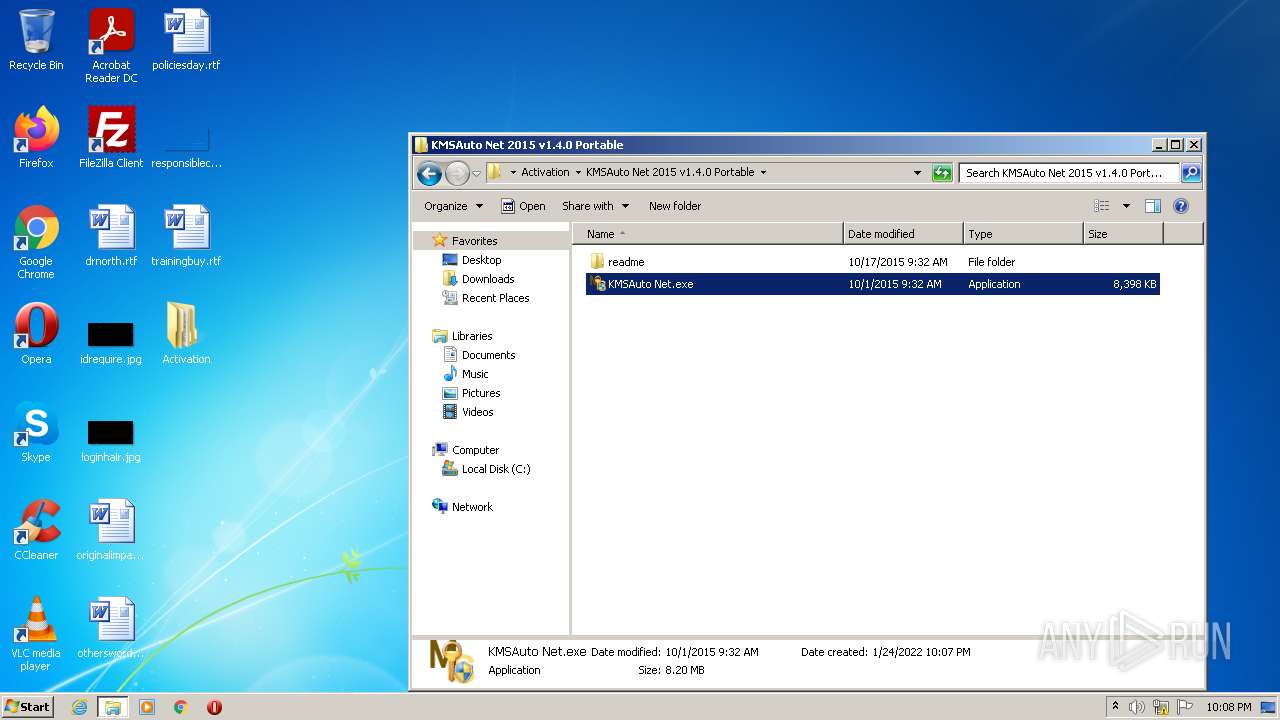
| 276 | "C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\KMSAuto Net.exe" | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\KMSAuto Net.exe | Explorer.EXE | ||||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMSAuto Net Exit code: 3221225547 Version: 1.4.0 Modules
| |||||||||||||||
| 304 | "sc.exe" create KMSEmulator binpath= temp.exe type= own start= auto | C:\Windows\system32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | "sc.exe" delete KMSEmulator | C:\Windows\system32\sc.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | services.exe | ||||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
| 1128 | cmd /c echo test>>"C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\test.test" | C:\Windows\system32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
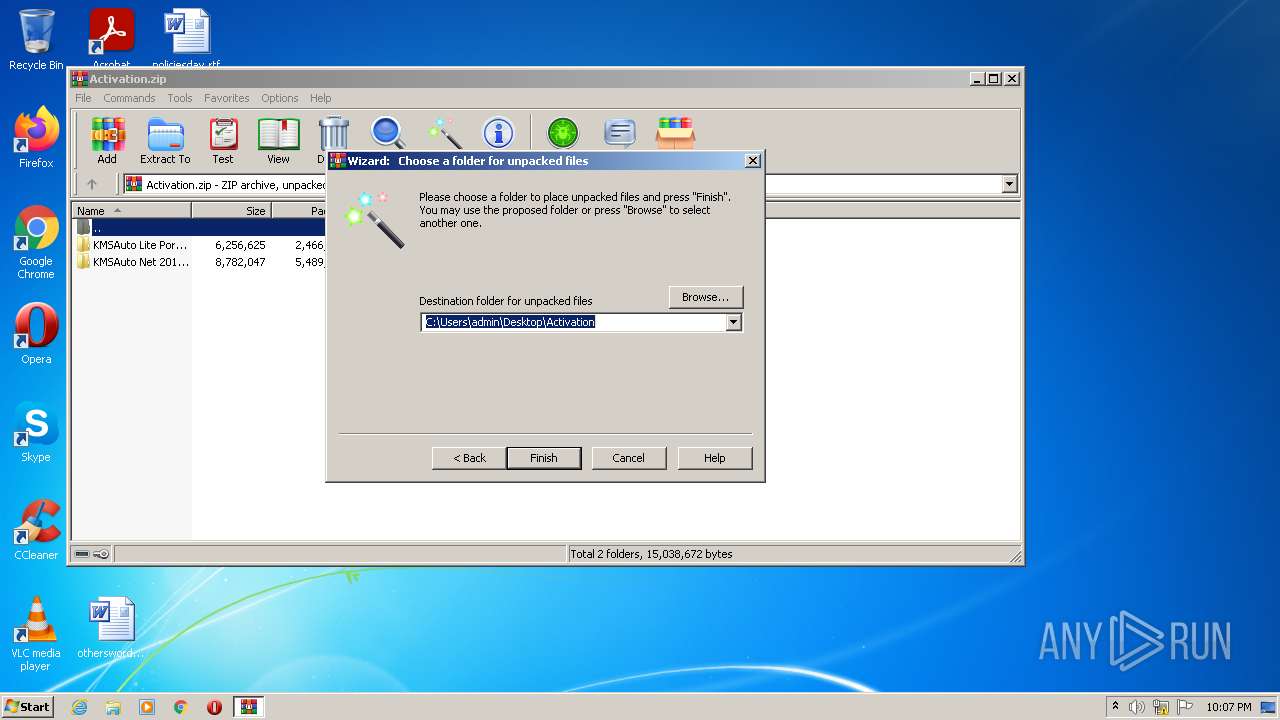
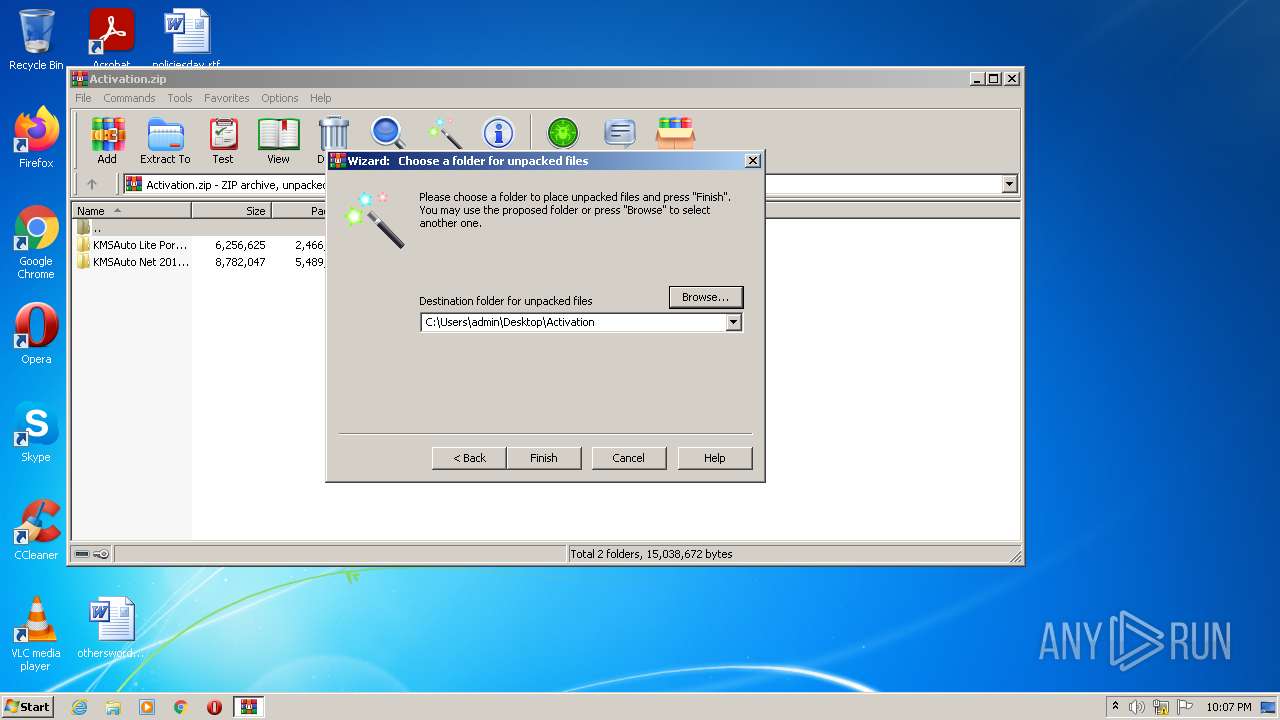
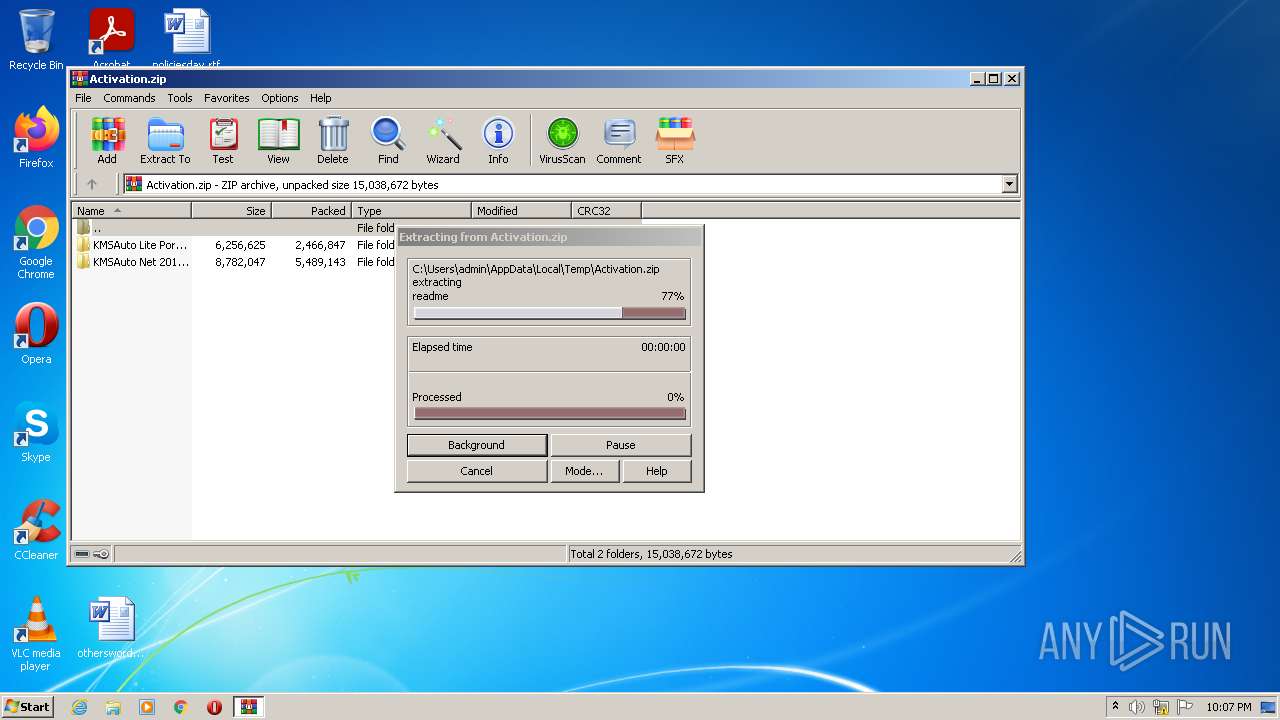
| 1256 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Activation.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1312 | C:\Windows\System32\cmd.exe /D /c del /F /Q "kmsauto.ini" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1356 | C:\Windows\System32\cmd.exe /D /c del /F /Q "test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 323
Read events
4 086
Write events
233
Delete events
4
Modification events
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Activation.zip | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
30
Suspicious files
4
Text files
23
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
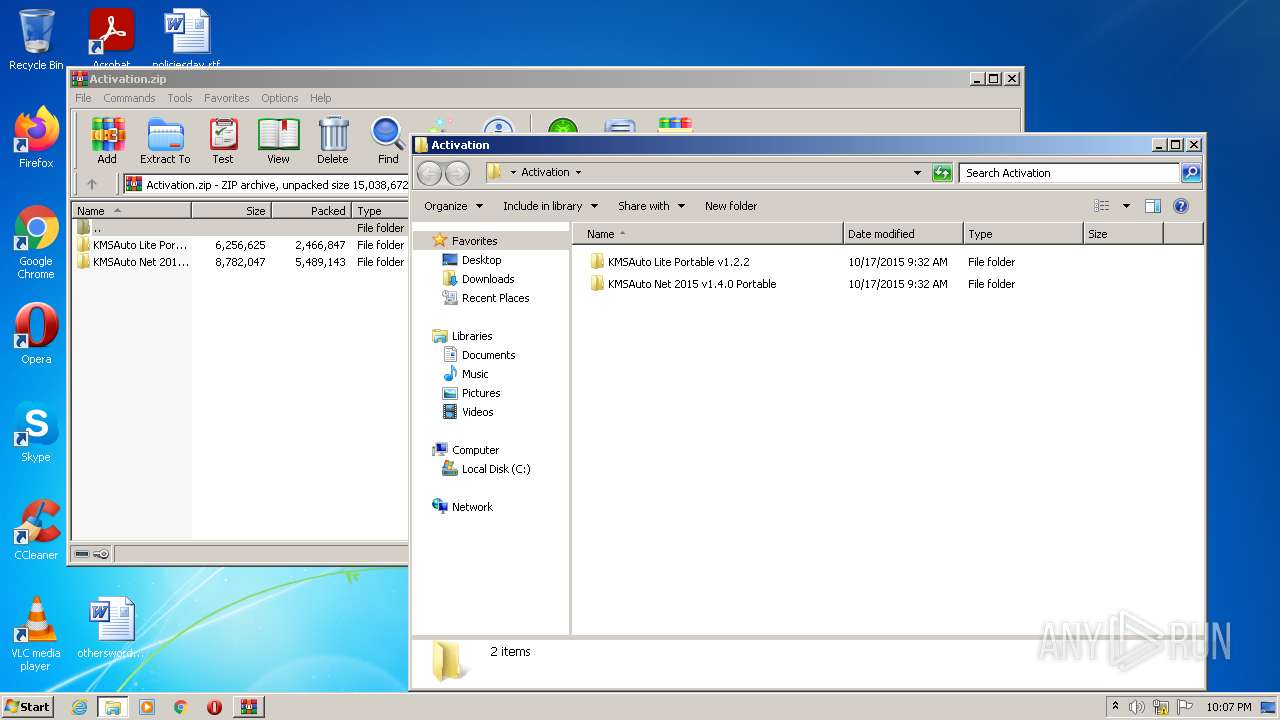
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Lite Portable v1.2.2\KMSAutoLite.ini | text | |
MD5:— | SHA256:— | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Lite Portable v1.2.2\readme_en.txt | text | |
MD5:— | SHA256:— | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\KMSAuto Net.exe | executable | |
MD5:B9D0B1C63D81A546C6CF6FB800F881AB | SHA256:3C56387A047564AB68443D8C2F9F427933D5CAA09354B60EBF1879A3F3862CEB | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_ua.txt | text | |
MD5:A57C260C2BD914D8D29FBBDEFCA1C0B1 | SHA256:59284FBDE0DF5173661AF8AC68D909454C3E85B1DCFBEB0E1035167DB0E95B49 | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_vi.txt | text | |
MD5:02DA567E68D0AC19ACE3034FE521ABDA | SHA256:0C454CA1441D1C23A5D7F2EA2573DE9C580CC7768BAC457A5B2A2A9F4F461770 | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_fr.txt | text | |
MD5:13A127FE54E0C32C685682898F3B9BF0 | SHA256:8D4B747DDB496DBCA93B513F8A850A2421F9699A91BE771D9C17797733BD8381 | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_ru.txt | text | |
MD5:3130279E396F2673AB50F63DA65BA3EC | SHA256:F1F70751B549B4B44DDE66D62259279E0C669BEBA8E9961881C9379F98CD027F | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_es.txt | text | |
MD5:564031DDACC56EDEC05E41786A798CF7 | SHA256:365AE7C998EEED200995322F2BFDAA68EEFC27F3DE81FF6DD8F855509457A74C | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_kms.txt | text | |
MD5:922BFF8450A1F9E5FEF2D130D50F980A | SHA256:D637E76FCED201C2C88CDBF515E8FED0EFD9C12B477776B322164093B02D532B | |||
| 1256 | WinRAR.exe | C:\Users\admin\Desktop\Activation\KMSAuto Net 2015 v1.4.0 Portable\readme\readme_bg.txt | text | |
MD5:BE93068E2139DFFB69831764D37101A4 | SHA256:B1993BBEB8471F544F8B0358918AE240EED4336DD0D98808297B6762F43CA7A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report