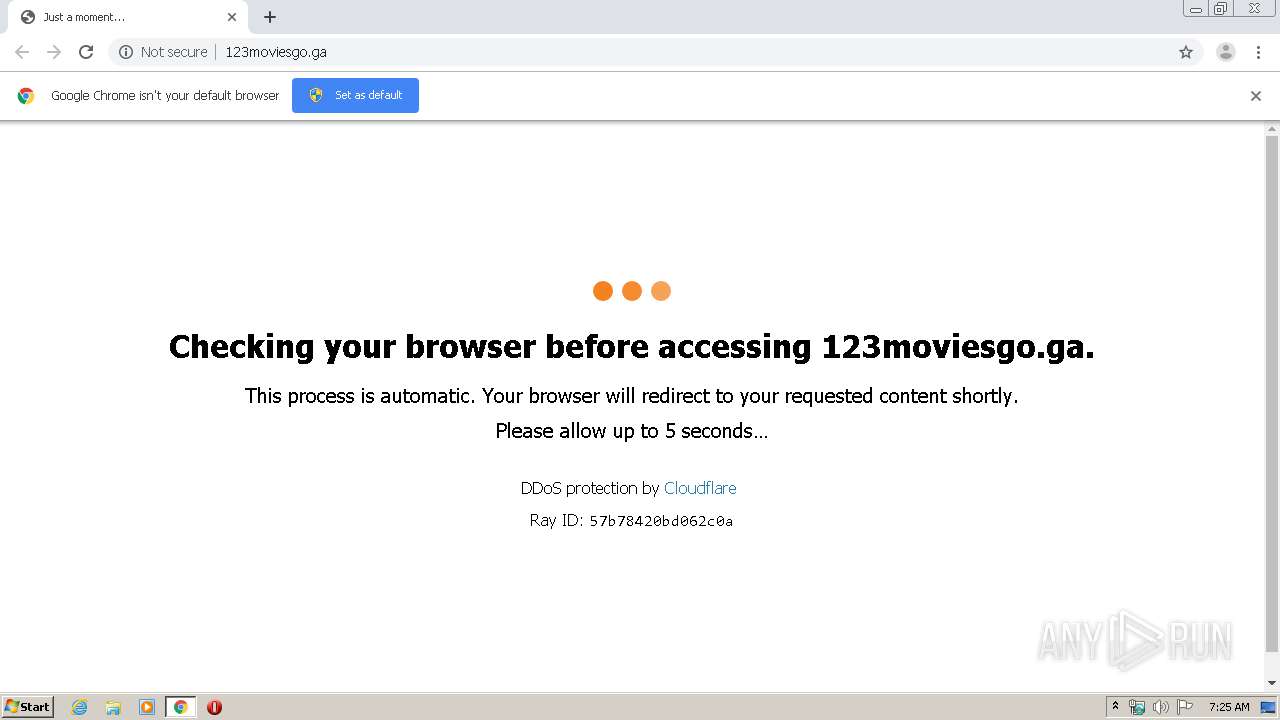
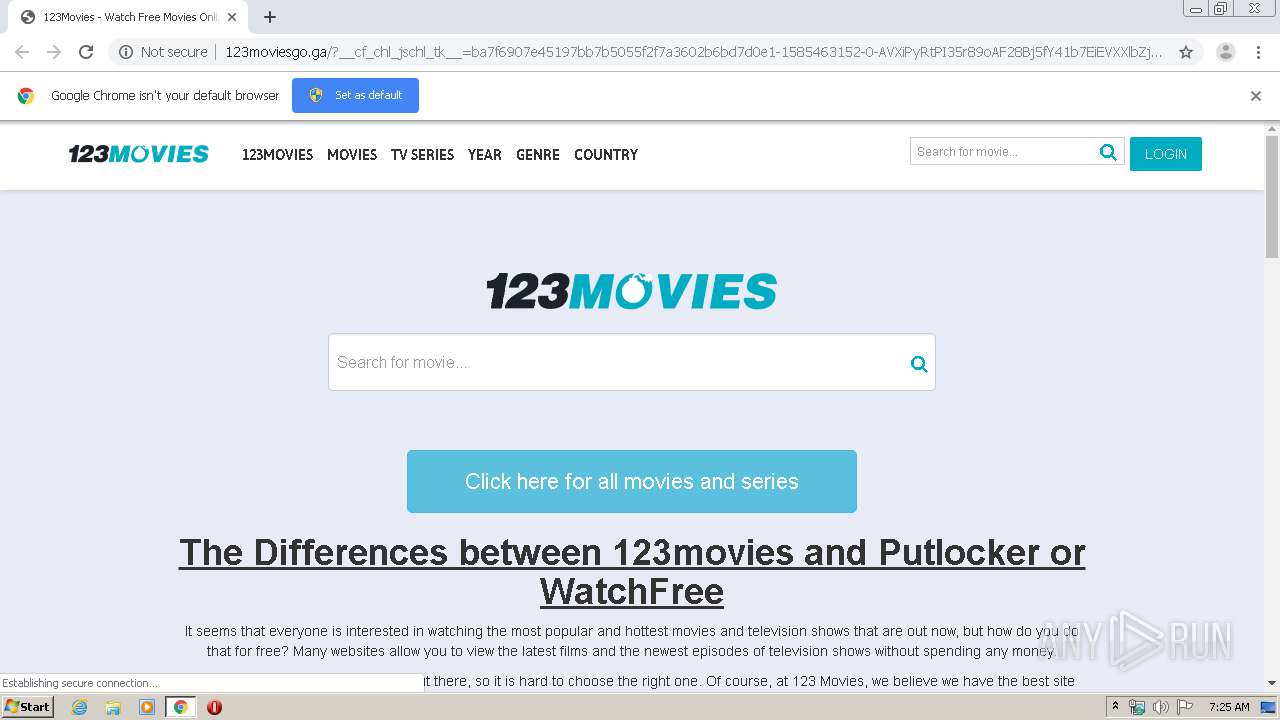
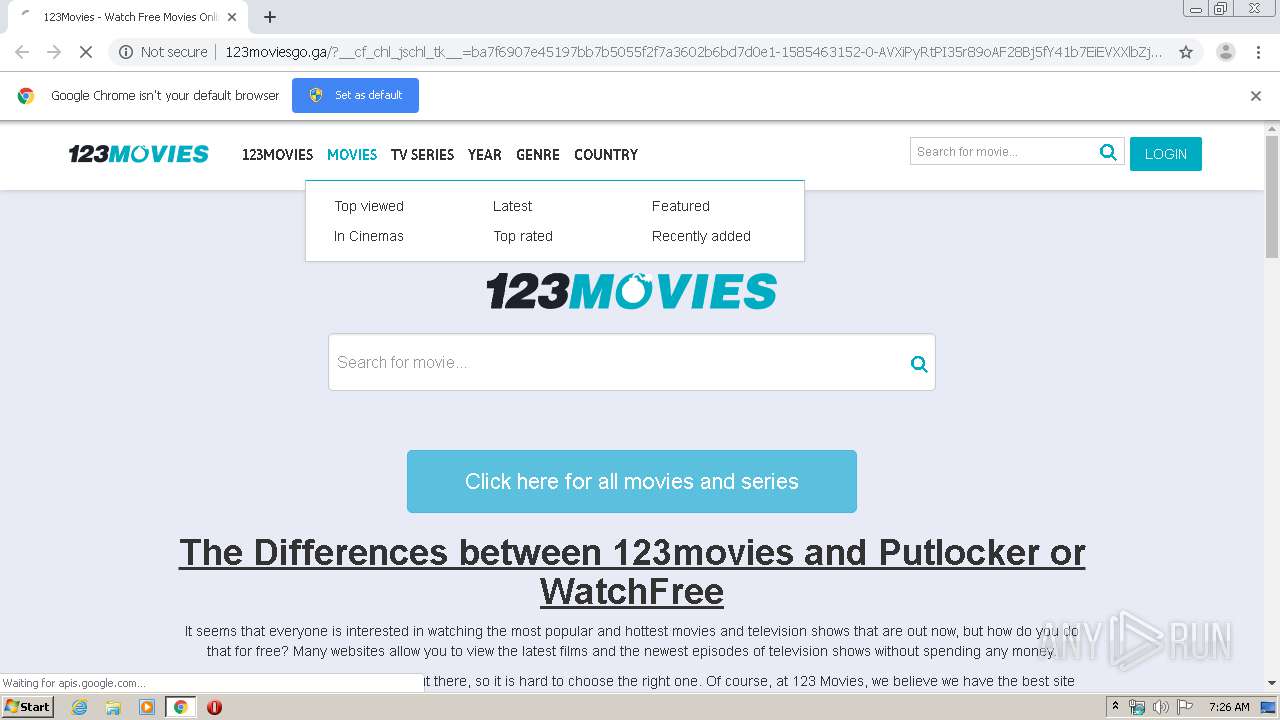
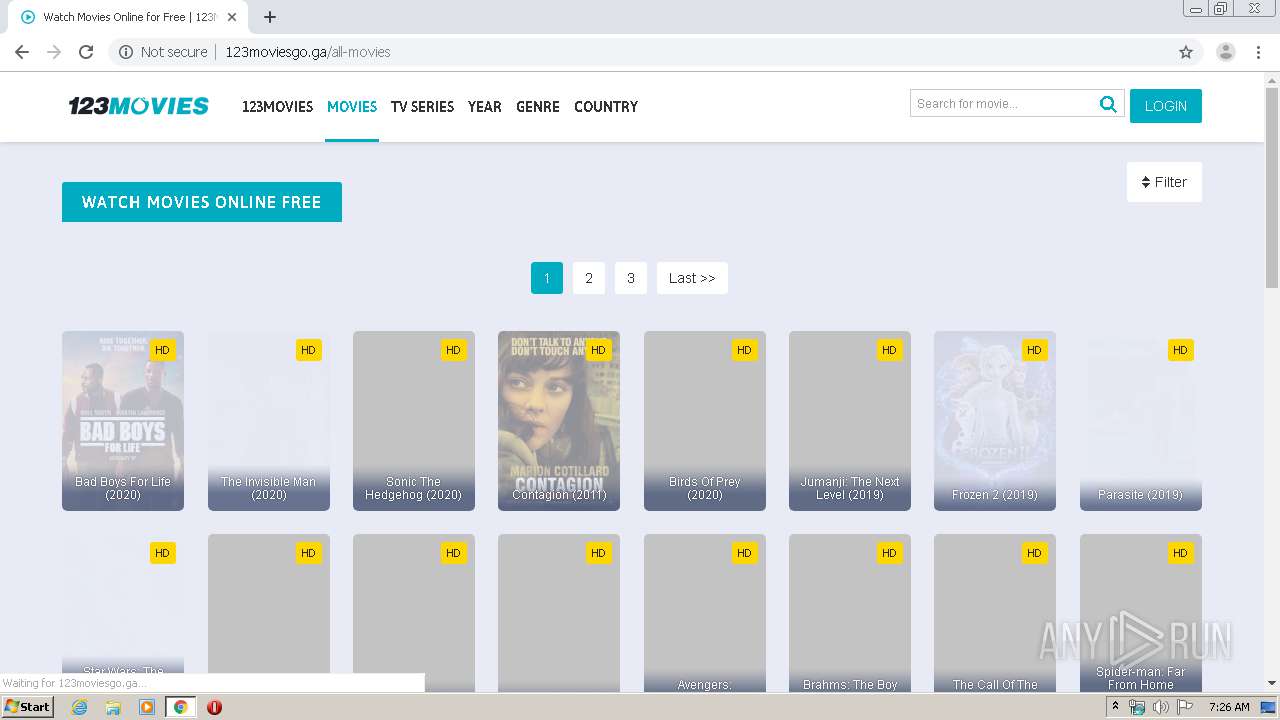
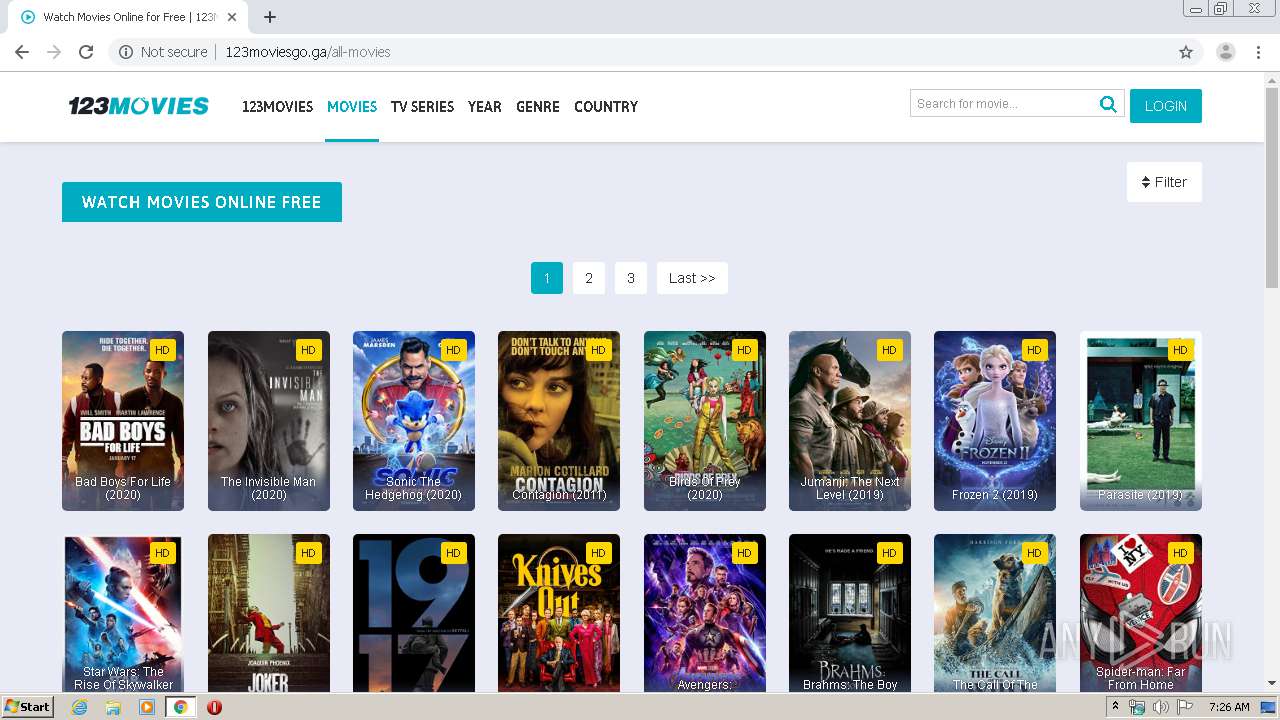
| URL: | http://123moviesgo.ga |
| Full analysis: | https://app.any.run/tasks/bf87e152-5208-4a9a-bf6f-5e4c7c6788e9 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2020, 06:25:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 63280716D3EB35E07ACB9BF97E8231E0 |
| SHA1: | 43ED0B594D53B3976DDDF6D8DF55C99C0B766A45 |
| SHA256: | 1956B4A18A107109362D0B3E839B9B95B5850F10CEF8E8CEBBB9EB046DC19D71 |
| SSDEEP: | 3:N1KvPG+H:CnH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3244)
INFO
Application launched itself
- chrome.exe (PID: 3244)
Reads the hosts file
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16076960529689462443 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15528255244087965612 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3726717447294220923 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5247141843752760963 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa9a9d0,0x6fa9a9e0,0x6fa9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1887314425711934273 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17681897670194208303 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11992703130478721246 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=866443449970549787 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,13403273825571206227,15244553188671100373,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4570887826453894763 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
531
Write events
78
Delete events
5
Modification events
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3244-13229936750626375 |
Value: 259 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3244) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
58
Text files
288
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E803F6F-CAC.pma | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4200488b-276a-4fed-b668-9d5d68cb3d0c.tmp | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFa67fc7.TMP | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RFa67f4a.TMP | text | |
MD5:A9C81BA506E2A0D898698EAF075EBE5C | SHA256:92FB2125FB5A0B877B76C4E3409B250EFF394804C7F24E236FBE162E1054AF90 | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa68025.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
33
DNS requests
26
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
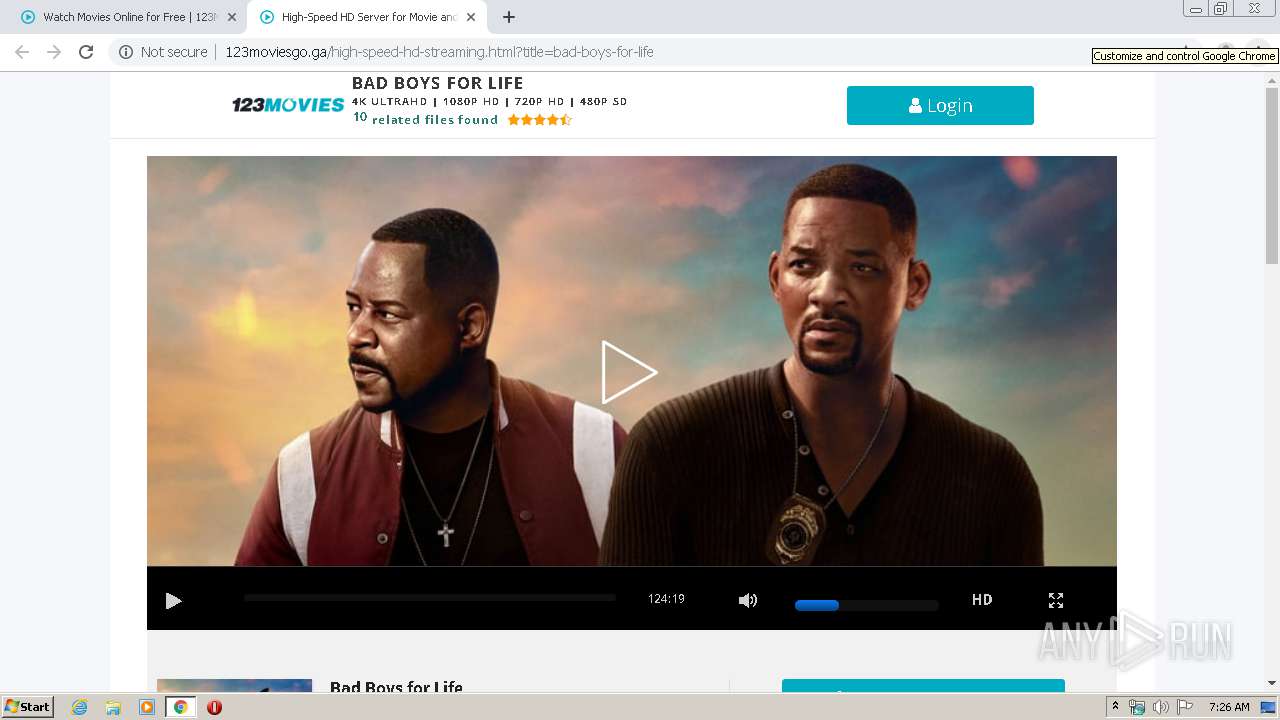
2132 | chrome.exe | GET | 503 | 104.31.88.200:80 | http://123moviesgo.ga/ | US | html | 15.1 Kb | malicious |
2132 | chrome.exe | GET | 404 | 104.31.88.200:80 | http://123moviesgo.ga/favicon.ico | US | html | 435 b | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/cdn-cgi/images/trace/jschal/nojs/transparent.gif?ray=57b78420bd062c0a | US | image | 42 b | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/cdn-cgi/images/trace/jschal/js/transparent.gif?ray=57b78420bd062c0a | US | image | 42 b | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/assets/css/bootstrap.min.css | US | text | 21.4 Kb | malicious |
2132 | chrome.exe | POST | 200 | 104.31.88.200:80 | http://123moviesgo.ga/?__cf_chl_jschl_tk__=ba7f6907e45197bb7b5055f2f7a3602b6bd7d0e1-1585463152-0-AVXiPyRtPI35r89oAF28Bj5fY41b7EiEVXXlbZj75KhlyPQtlVw2hK1eaXVJIsPReZEnDNDjdN3VsdUasxz_eBxnNsNjGHQh7q6UxsRRvCt5EubW9eopcuQwC1f1-m-WIsberkhjg0vE5R61s76tfuuTepwOx_NpwAOKh4HvRuB81SEhe5VvuzJY18ODu3g30tvkOJCO5m95NhIkf-AsULUQeO5oAaf1w3jwP4VGu2iYuQ0lCHfOeIc2zBTEAUqjOh-_nUp3LVevRCYYa8M4xWk | US | html | 7.39 Kb | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/assets/css/jquery.cluetip.css | US | text | 952 b | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/assets/css/main.css?v=0.7 | US | text | 15.4 Kb | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/assets/css/jquery.qtip.min.css | US | text | 2.09 Kb | malicious |
2132 | chrome.exe | GET | 200 | 104.31.88.200:80 | http://123moviesgo.ga/assets/css/custom.css?v=0.1 | US | text | 1.17 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2132 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 104.31.88.200:80 | 123moviesgo.ga | Cloudflare Inc | US | shared |
2132 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2132 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 104.17.64.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
2132 | chrome.exe | 104.17.65.4:443 | ajax.cloudflare.com | Cloudflare Inc | US | unknown |
2132 | chrome.exe | 216.58.208.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2132 | chrome.exe | 74.125.4.203:80 | r5---sn-aigzrner.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
123moviesgo.ga |
| malicious |
accounts.google.com |
| shared |
www.cloudflare.com |
| whitelisted |
yorke-peninsula.net |
| suspicious |
www.google.com |
| malicious |
ajax.cloudflare.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
apis.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
2132 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2132 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.ga Domain |
2132 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] JS obfuscation (obfuscator.io) |