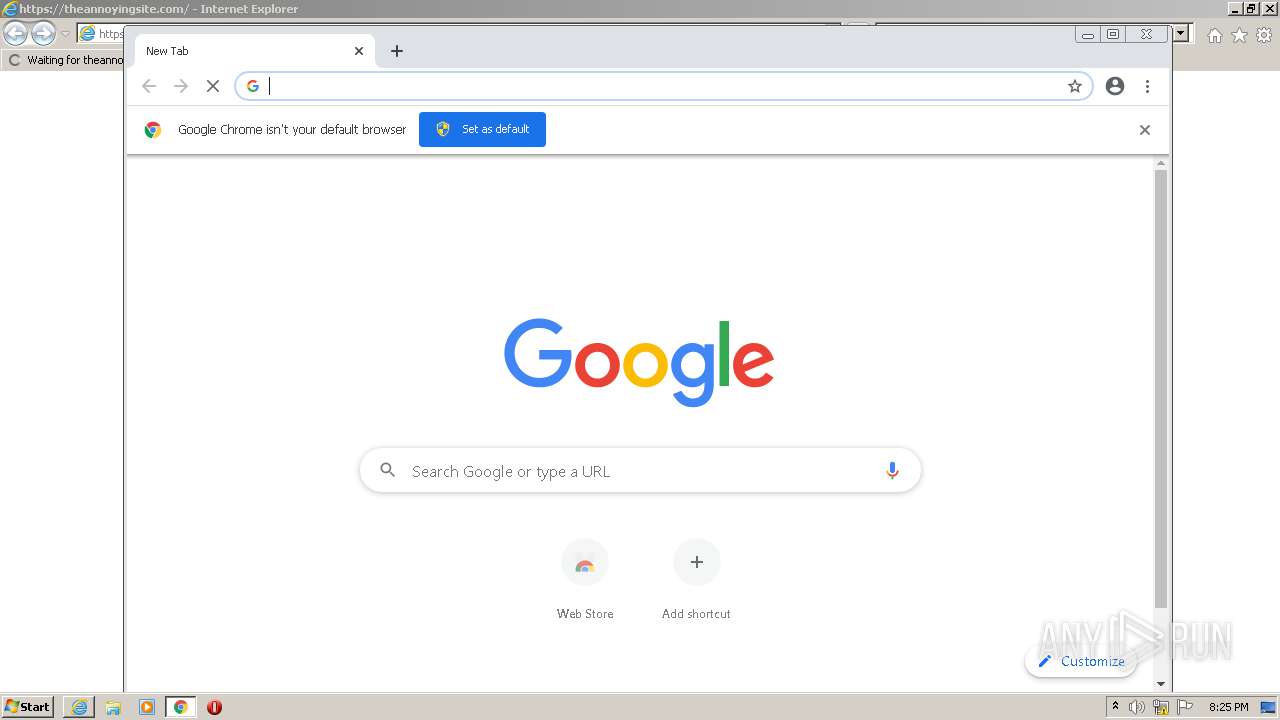
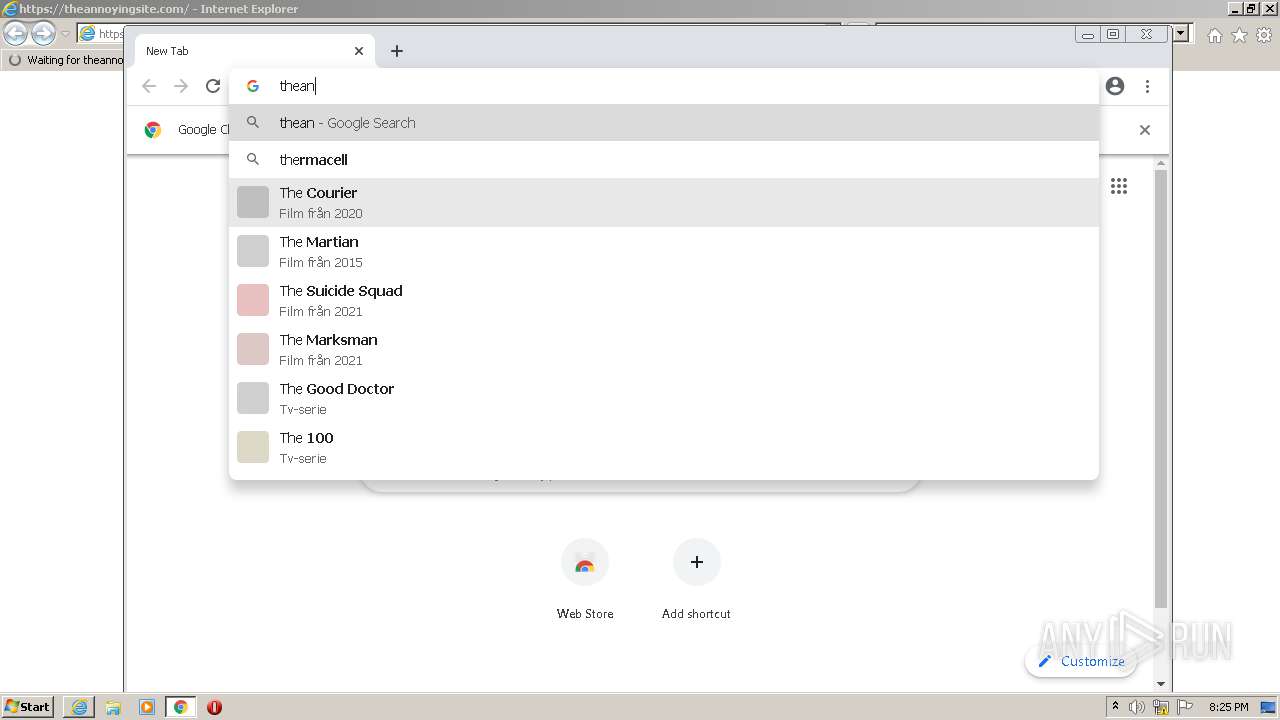
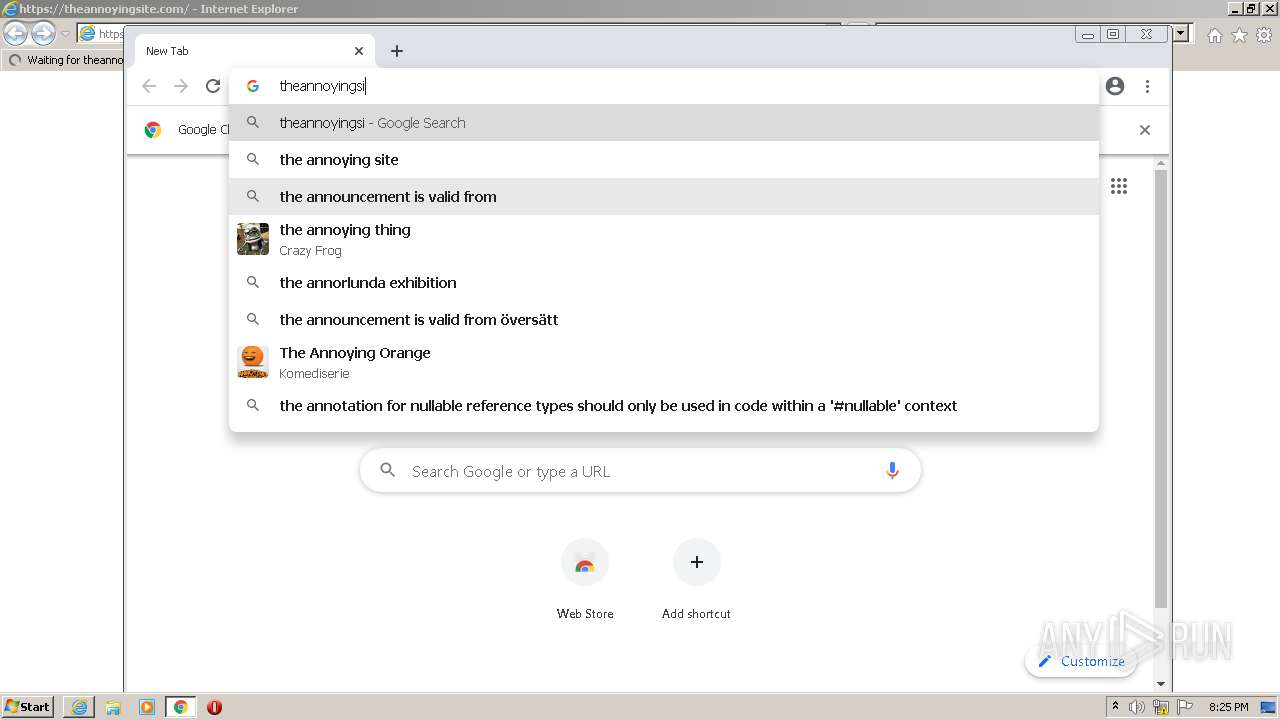
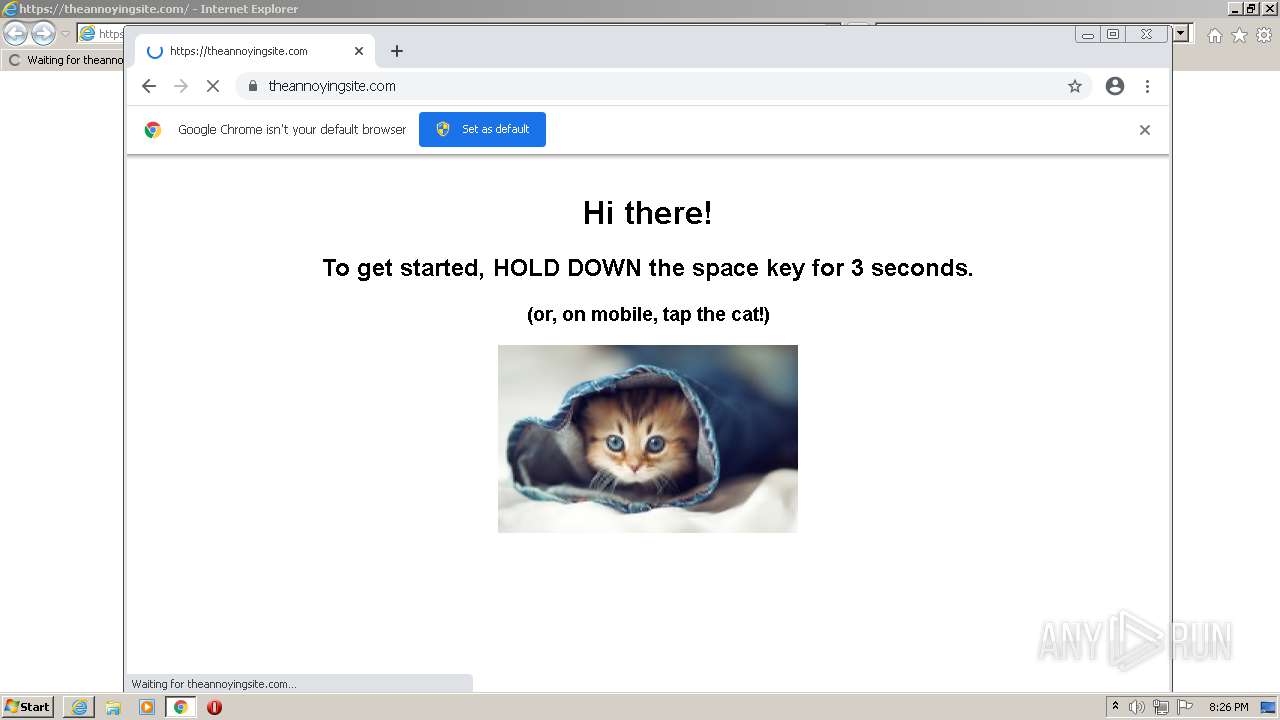
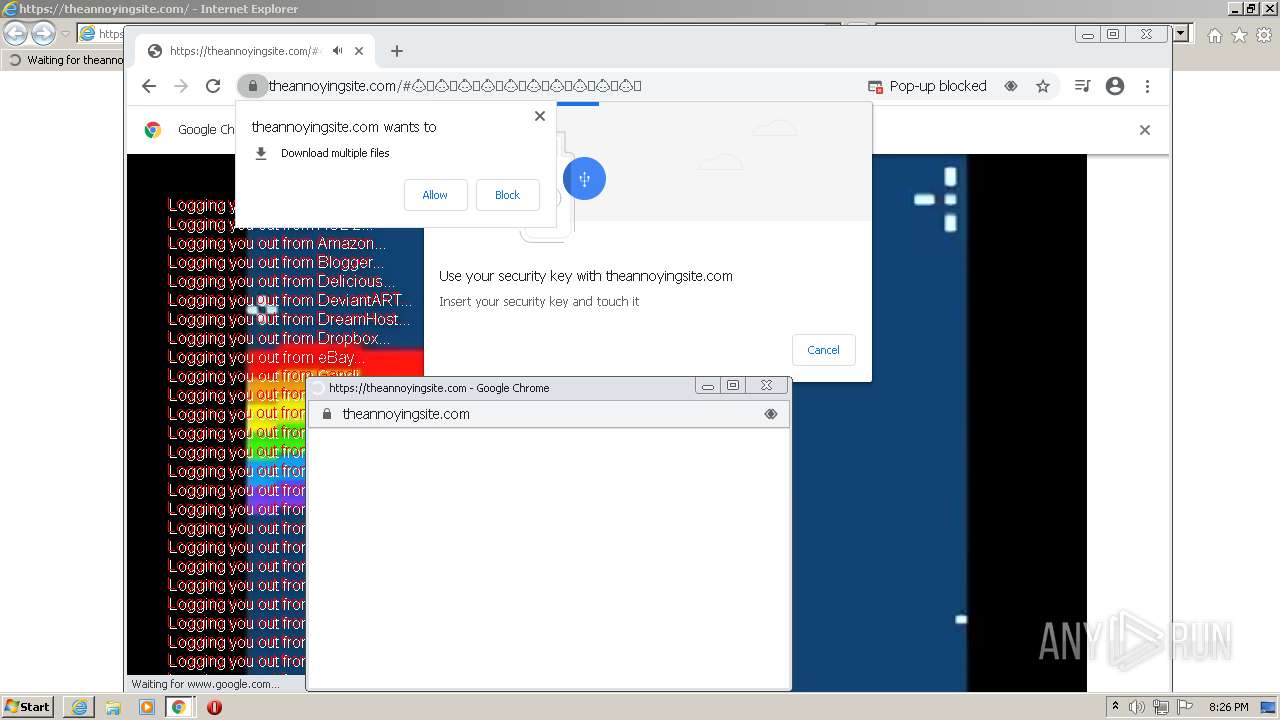
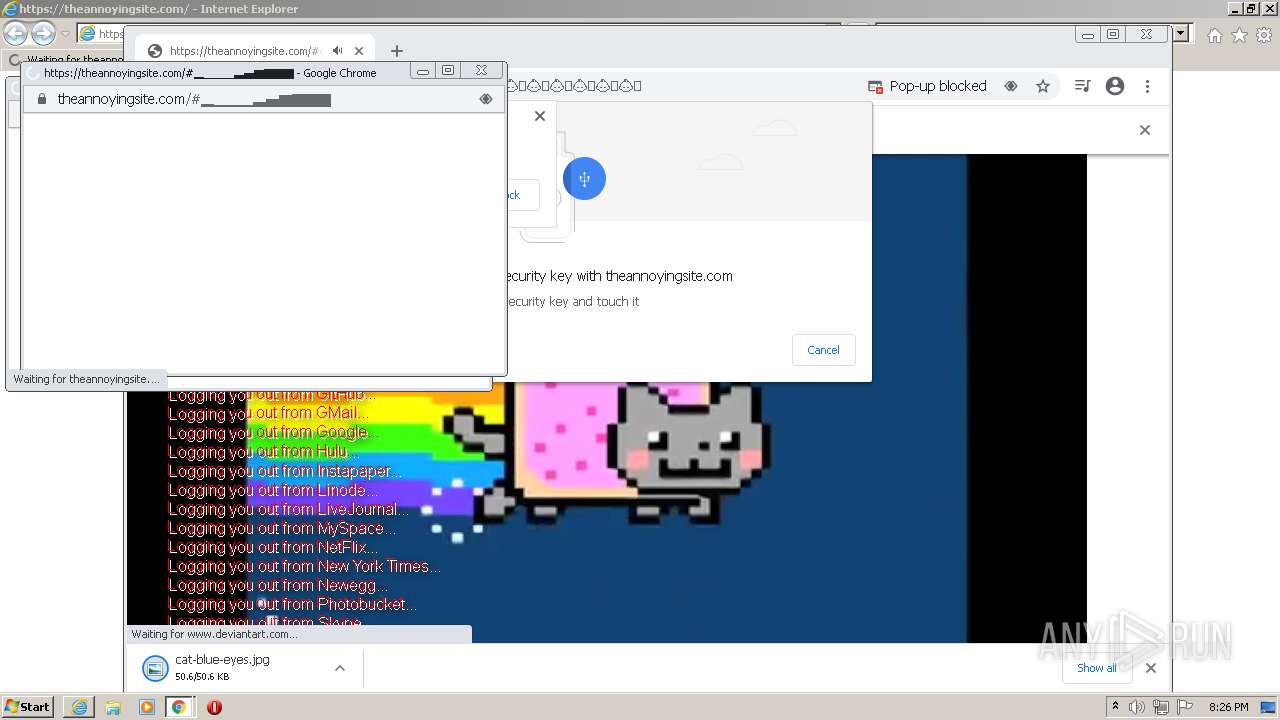
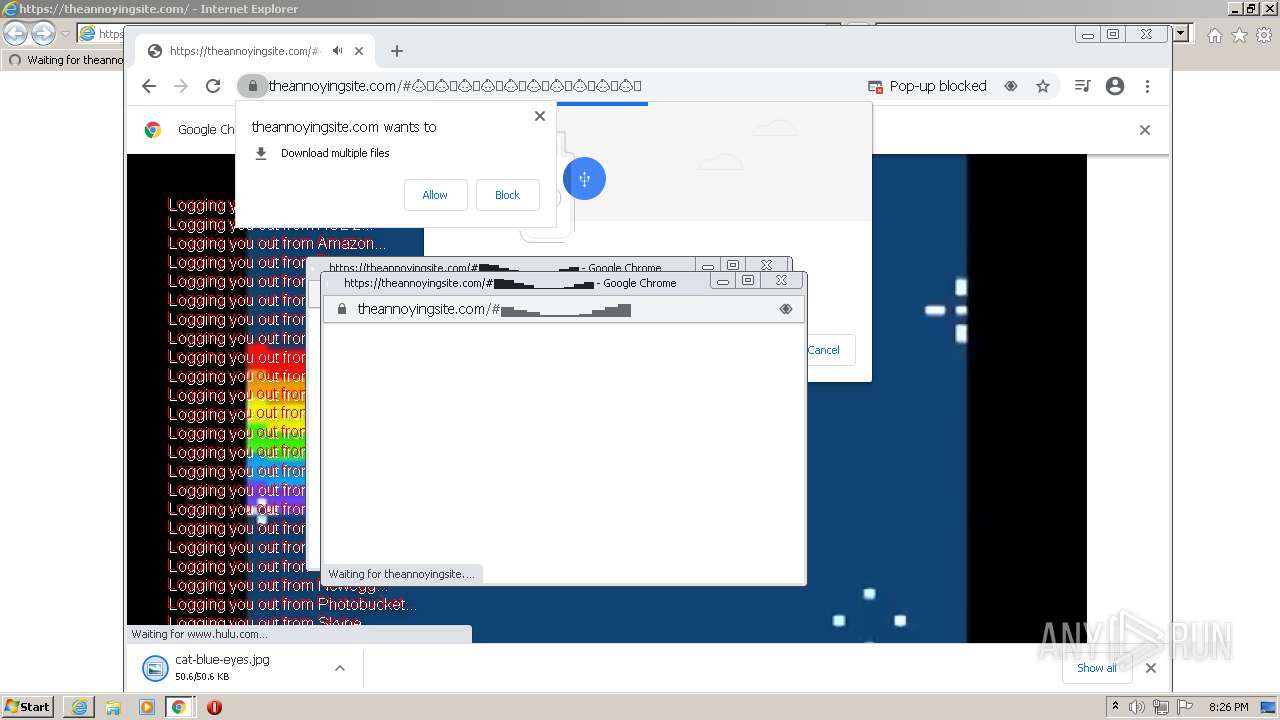
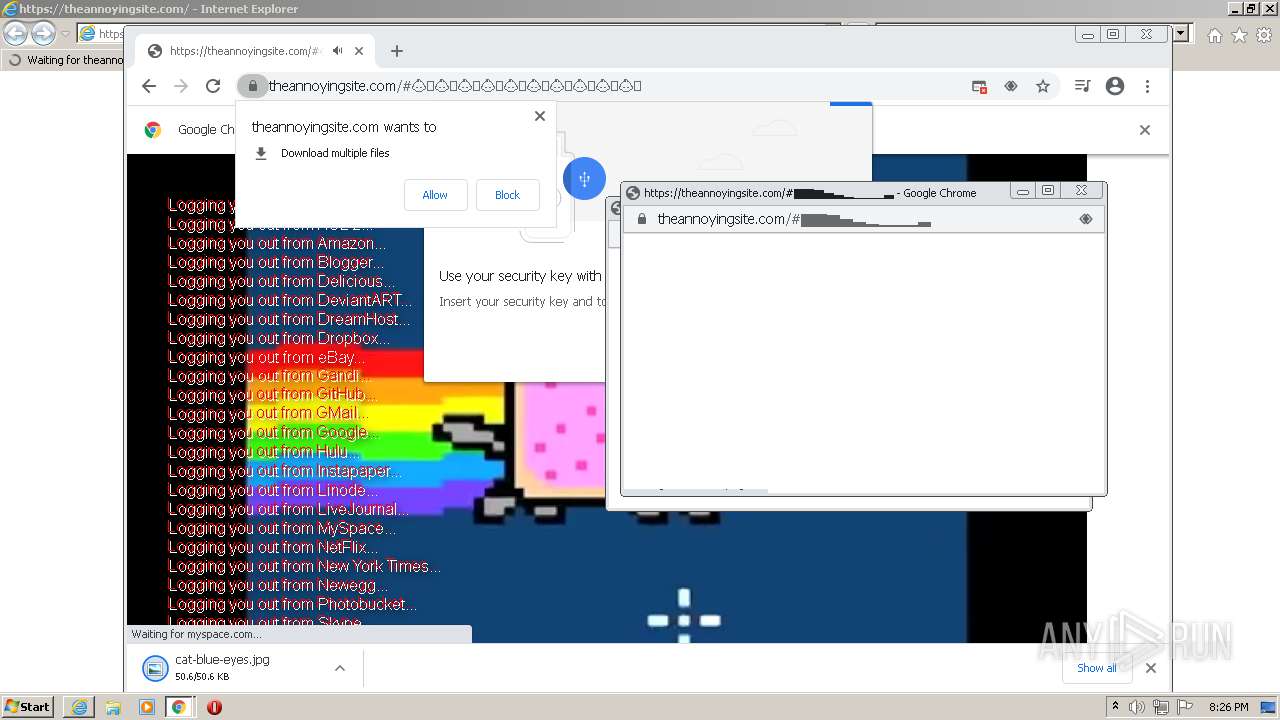
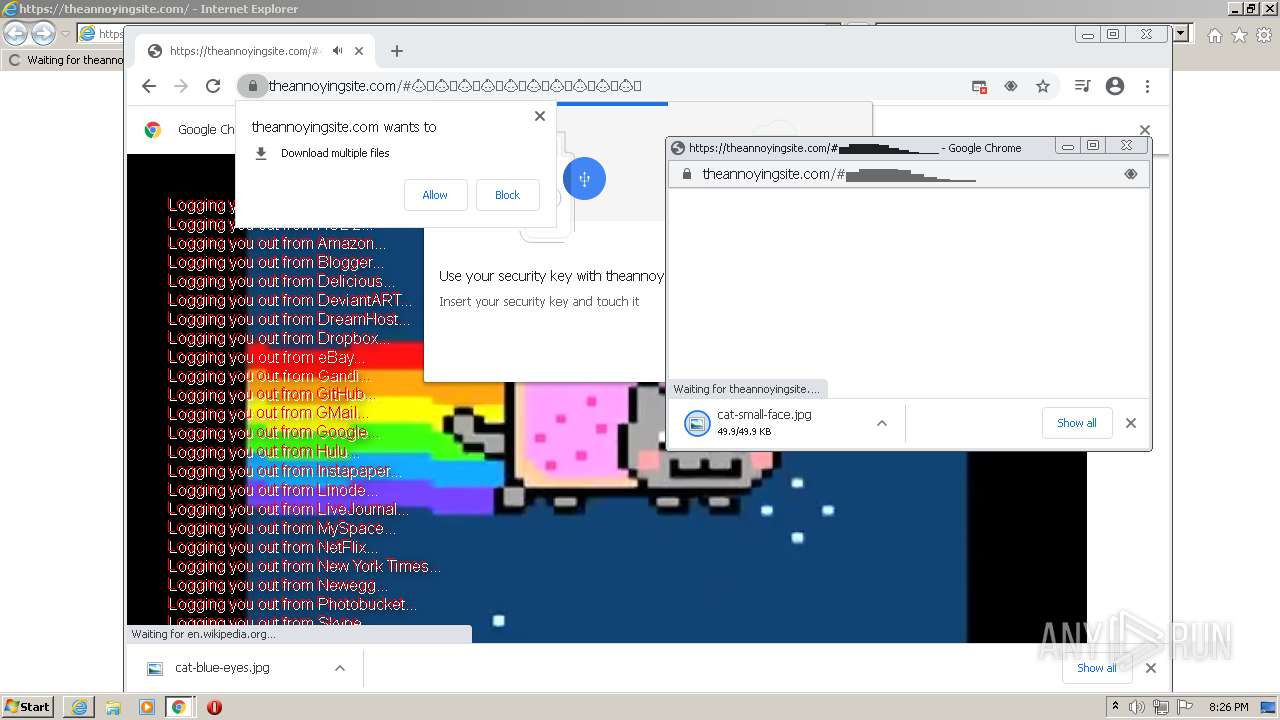
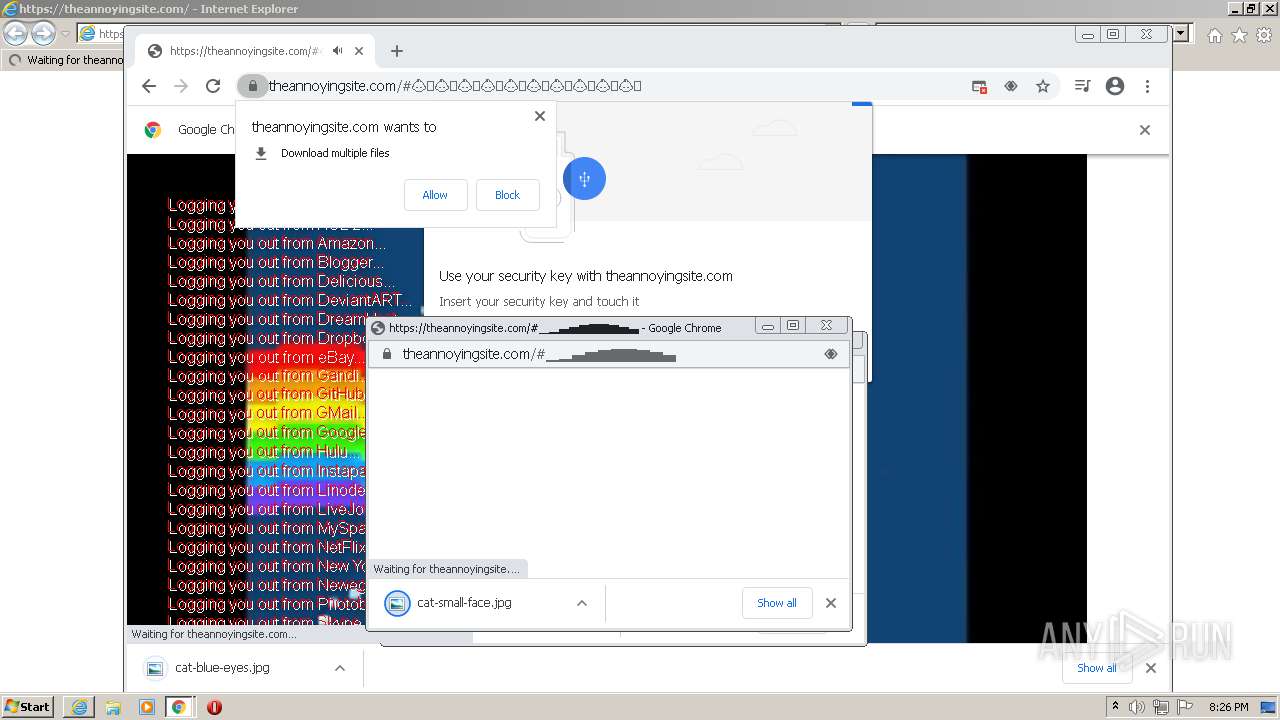
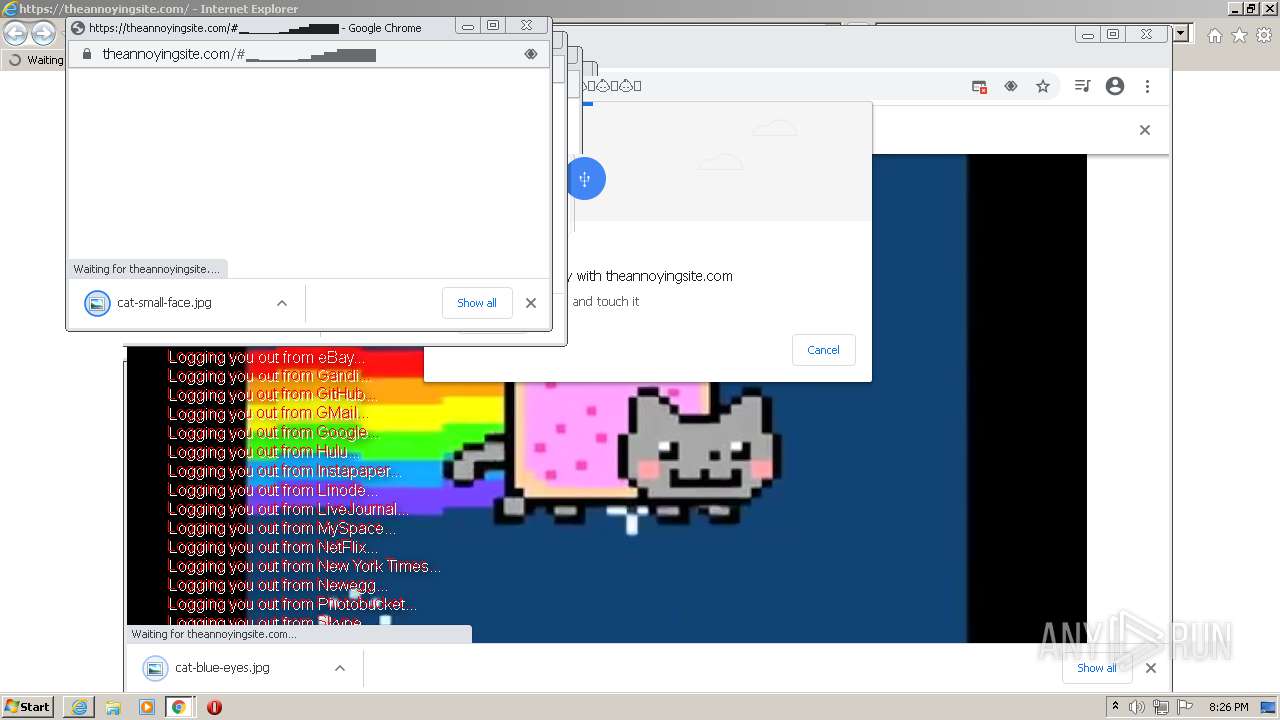
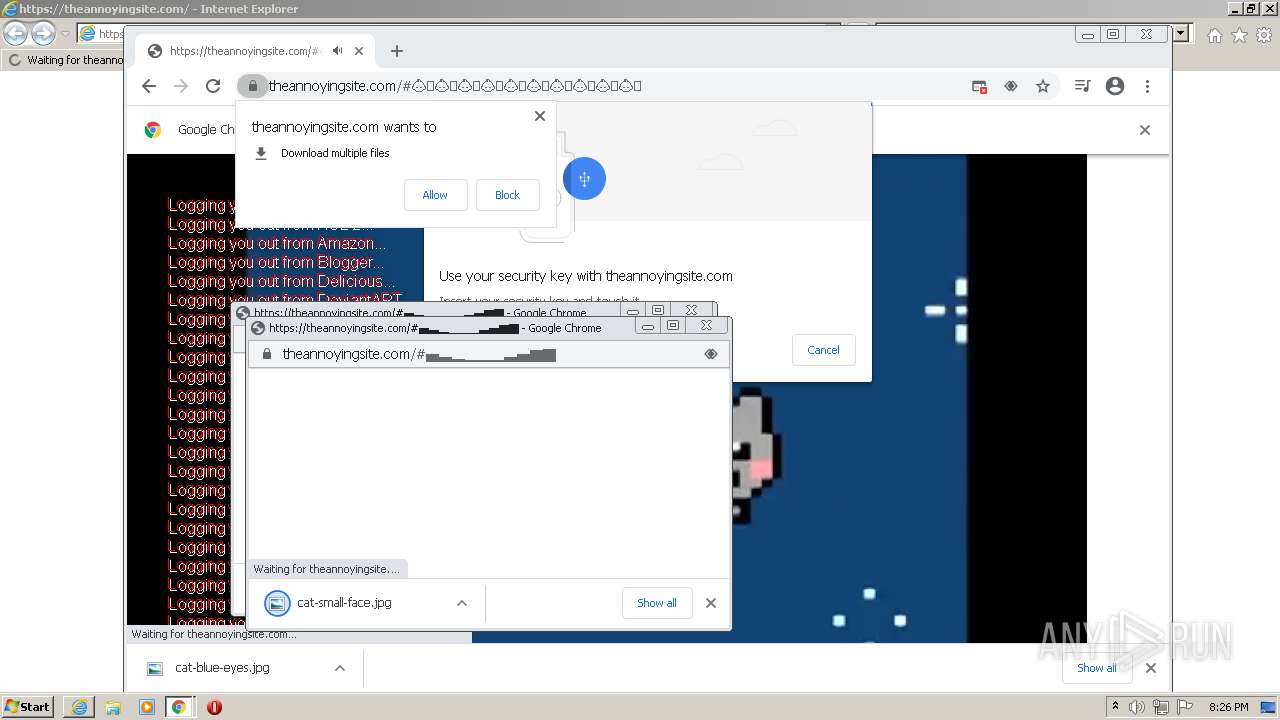
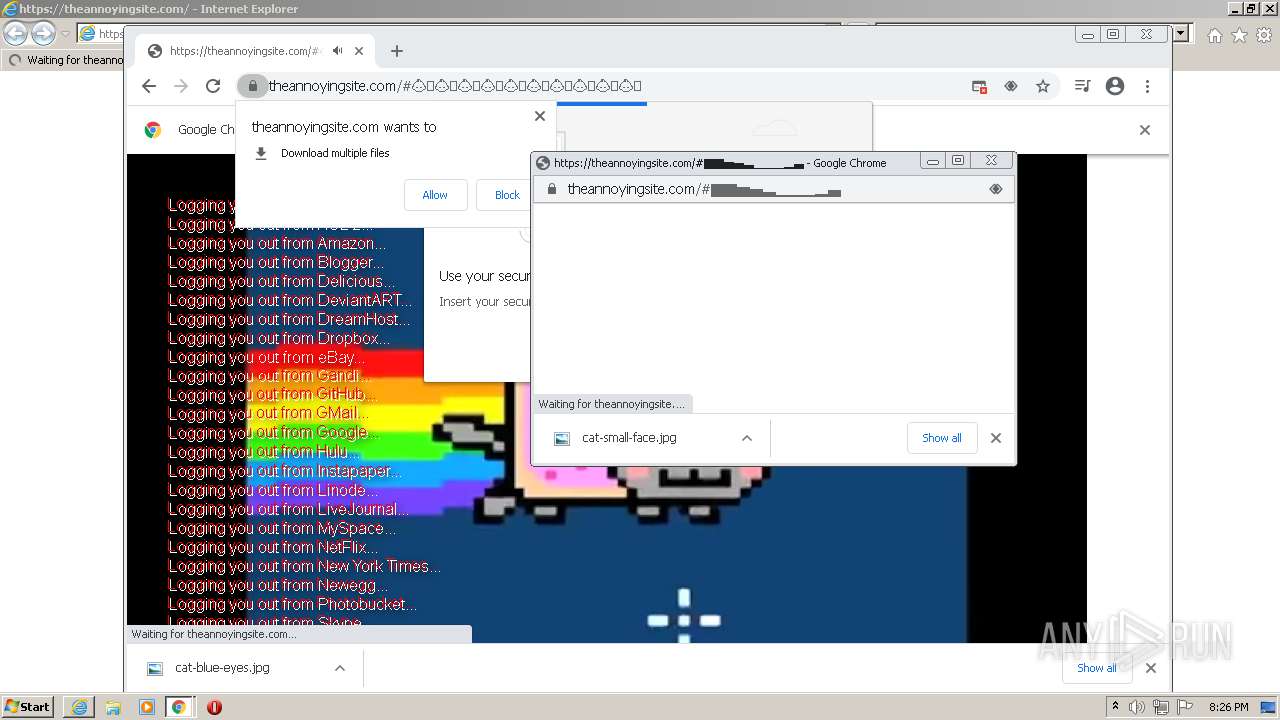
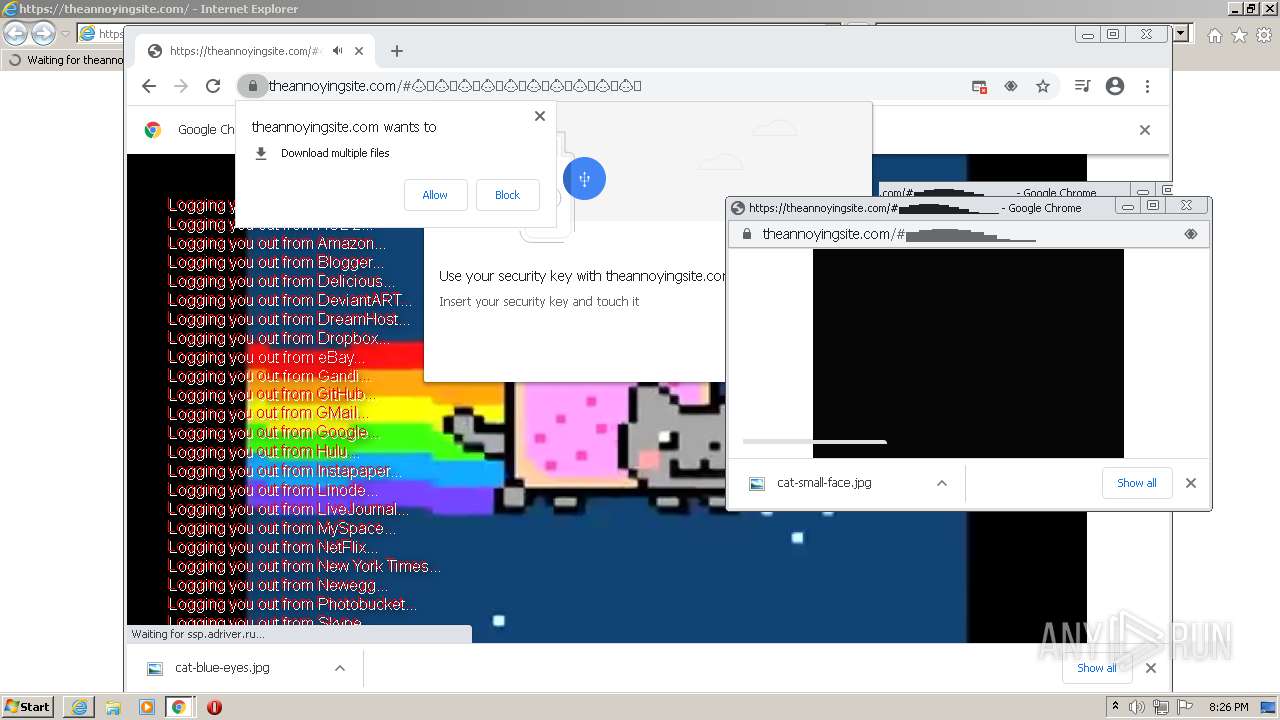
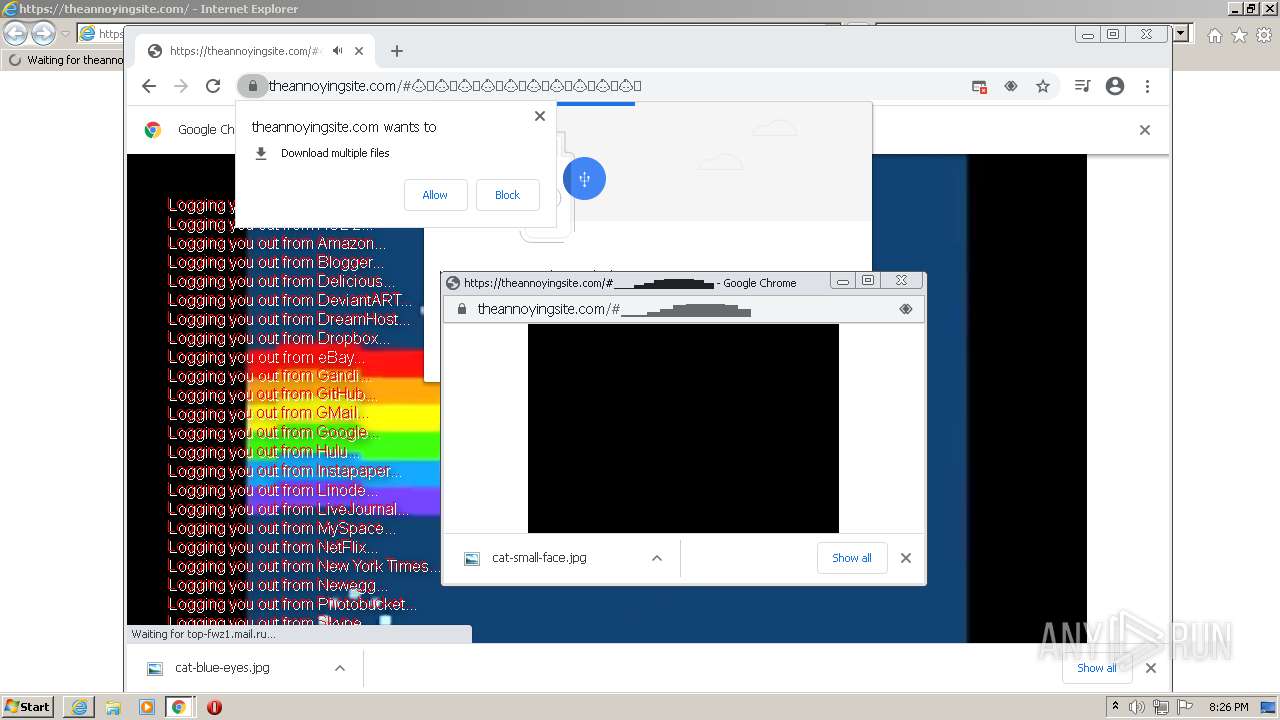
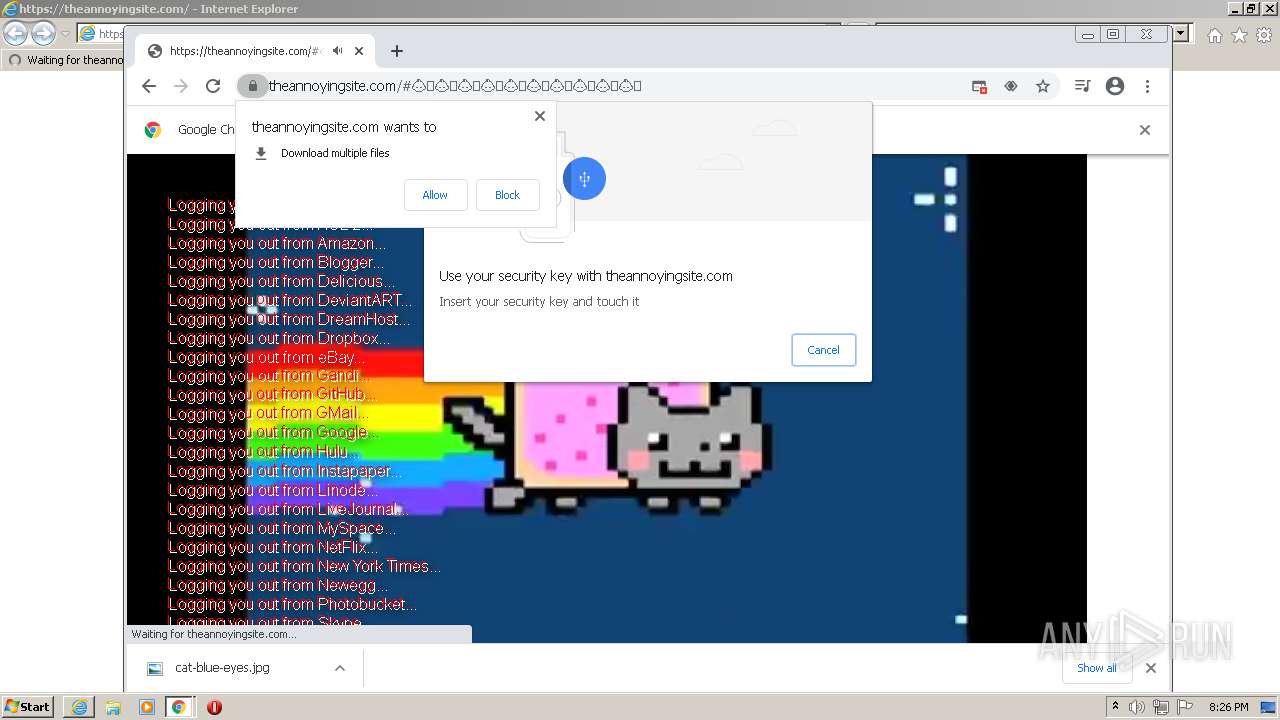
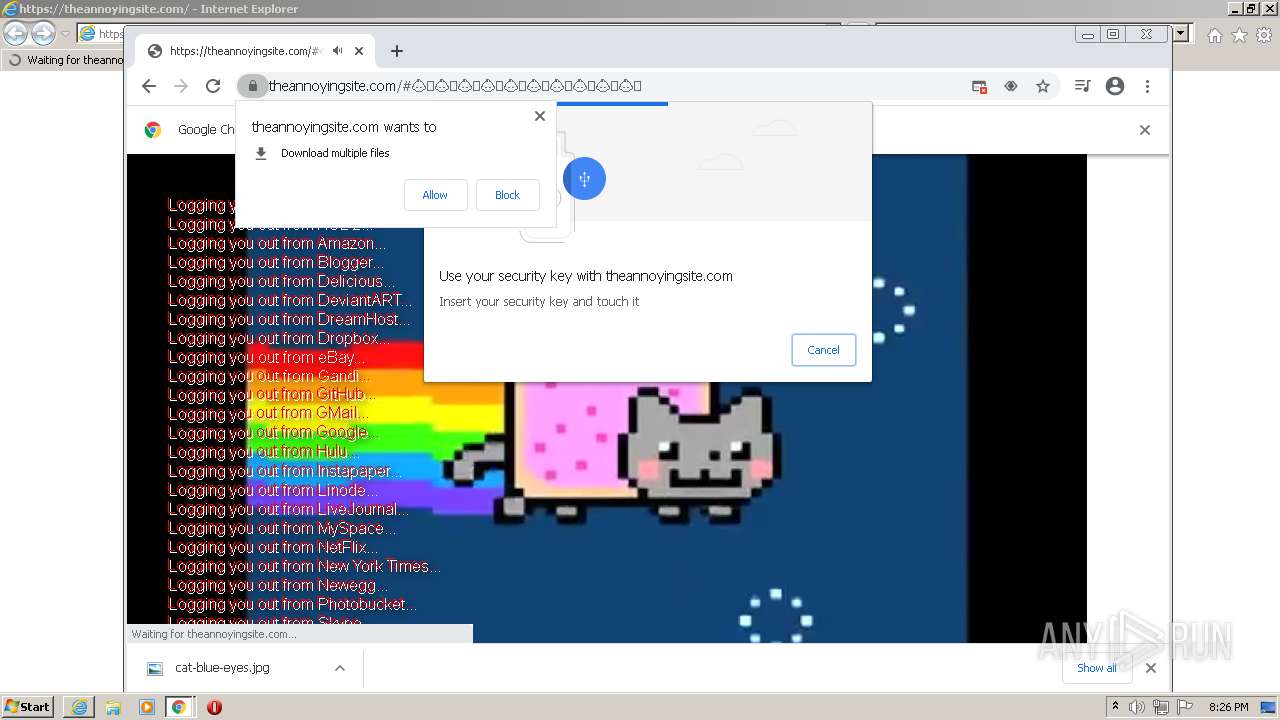
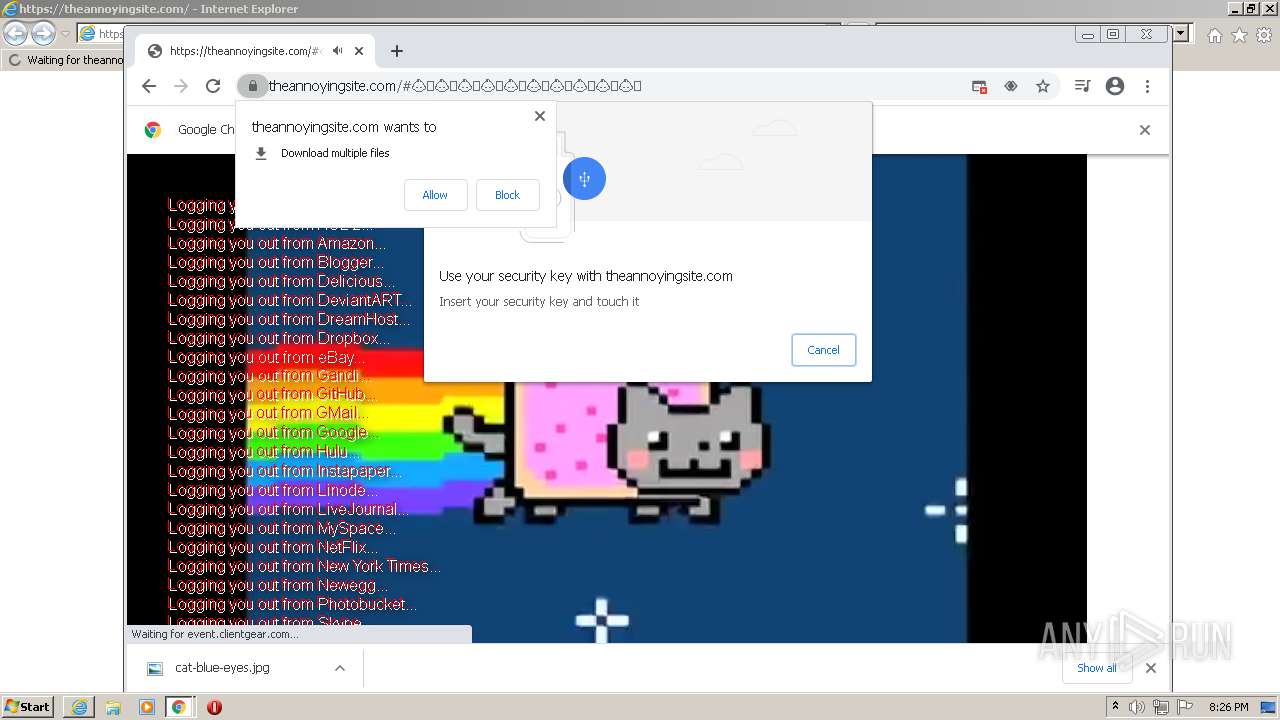
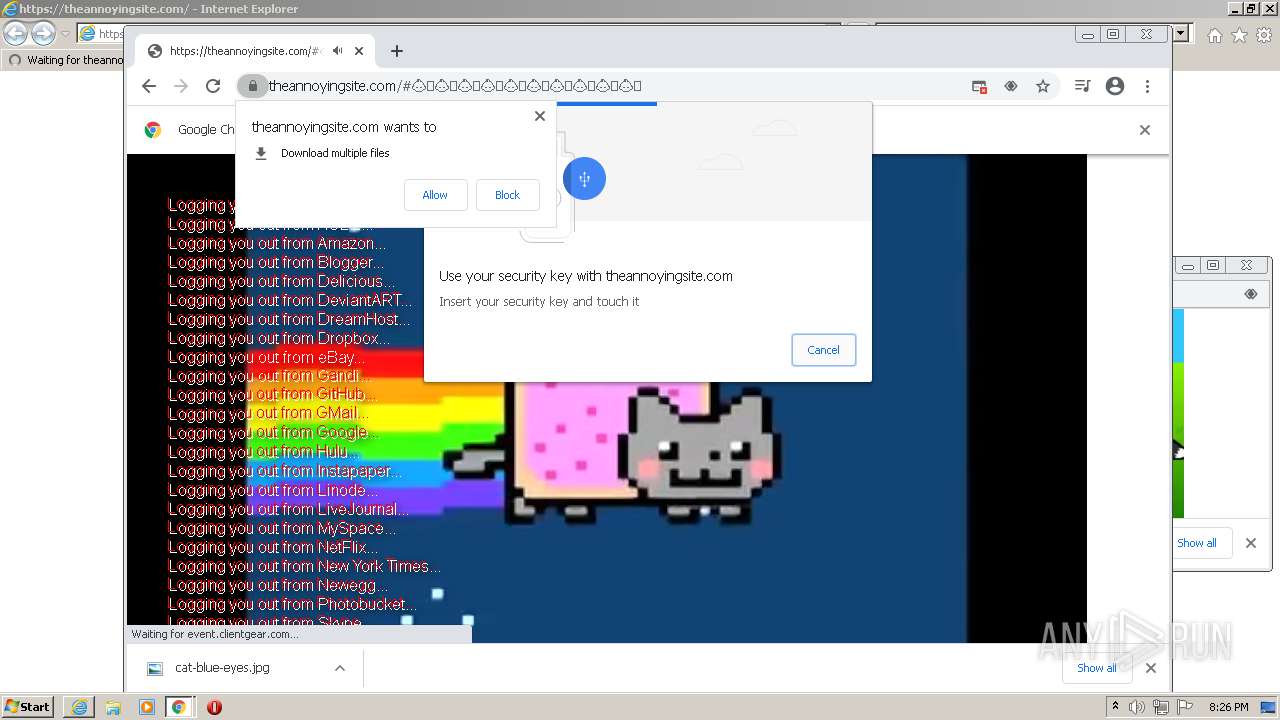
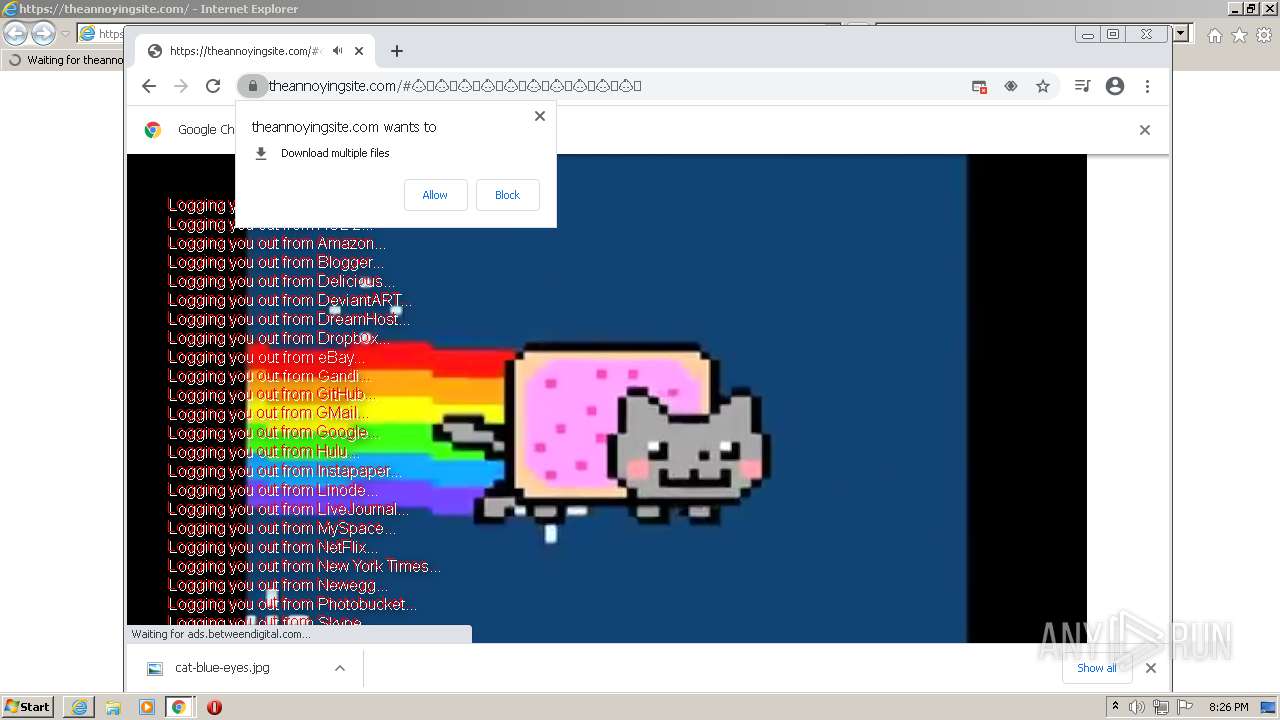
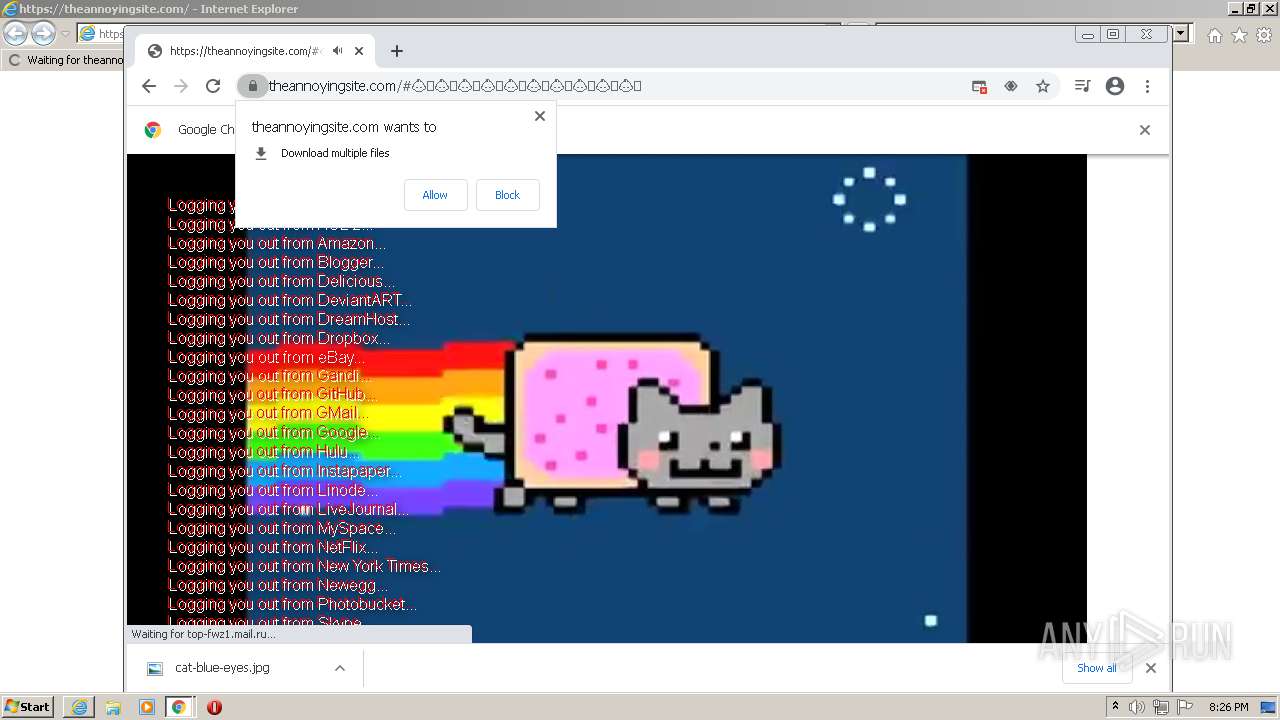
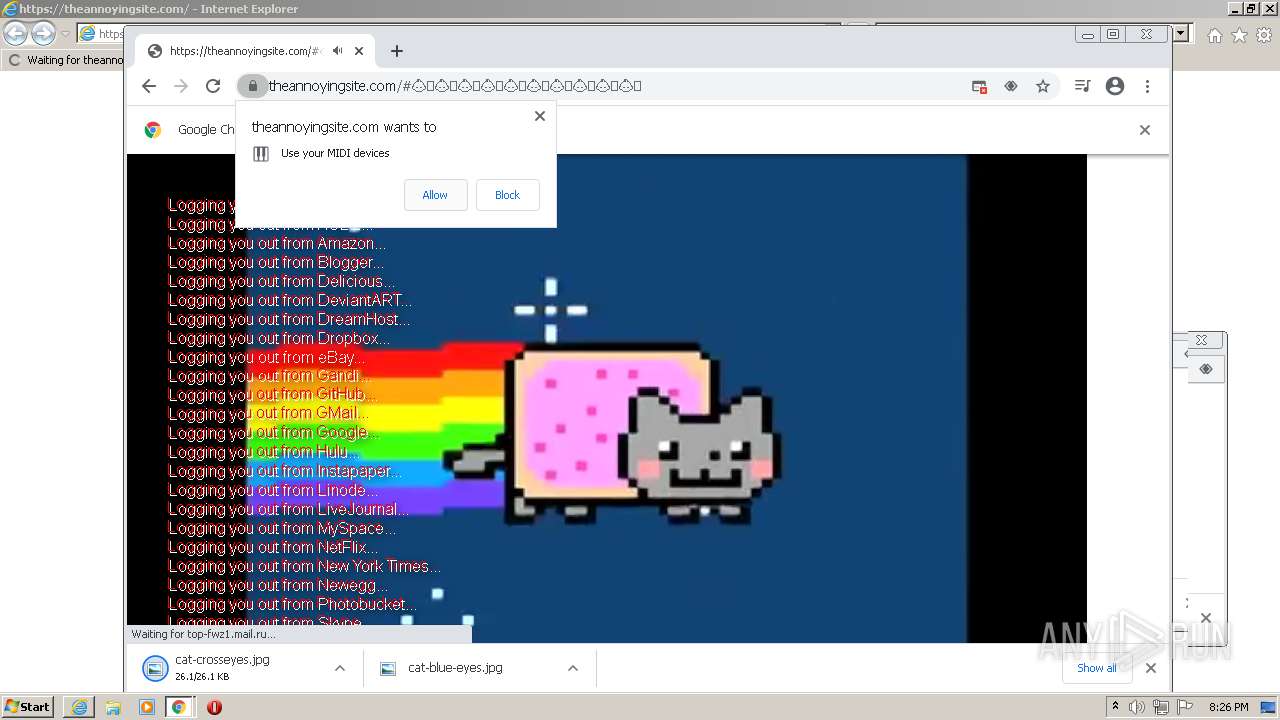
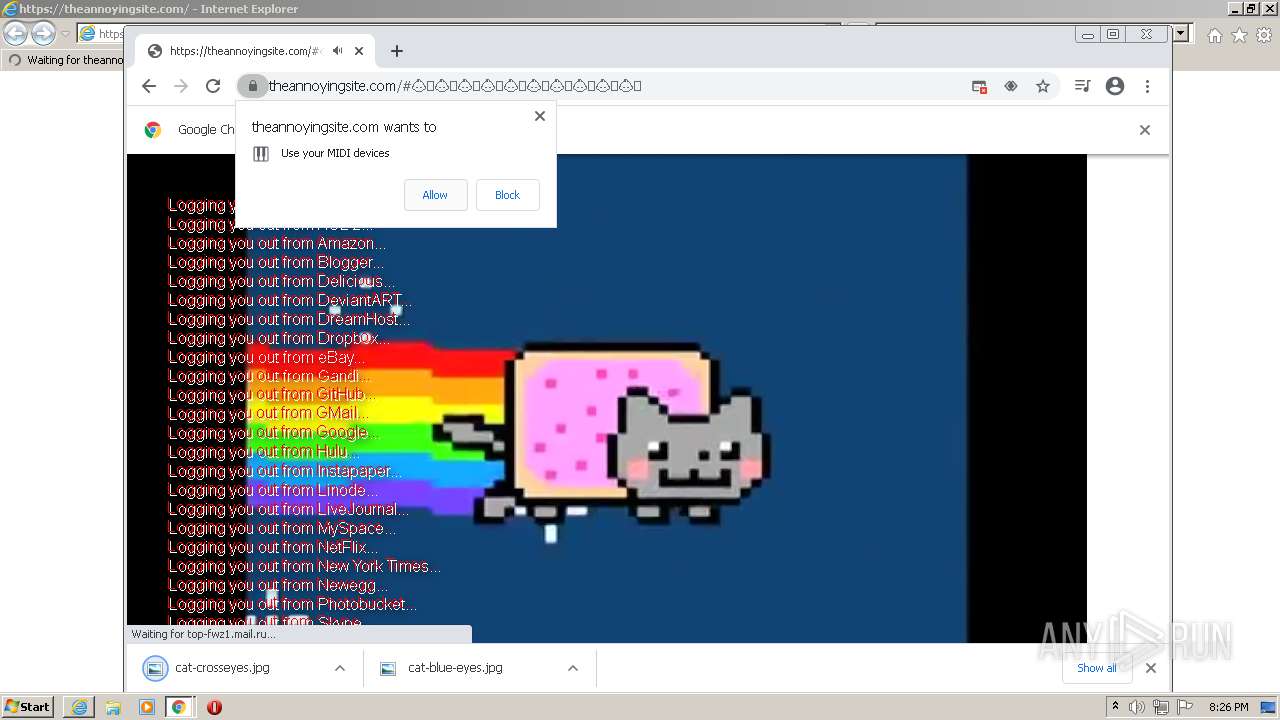
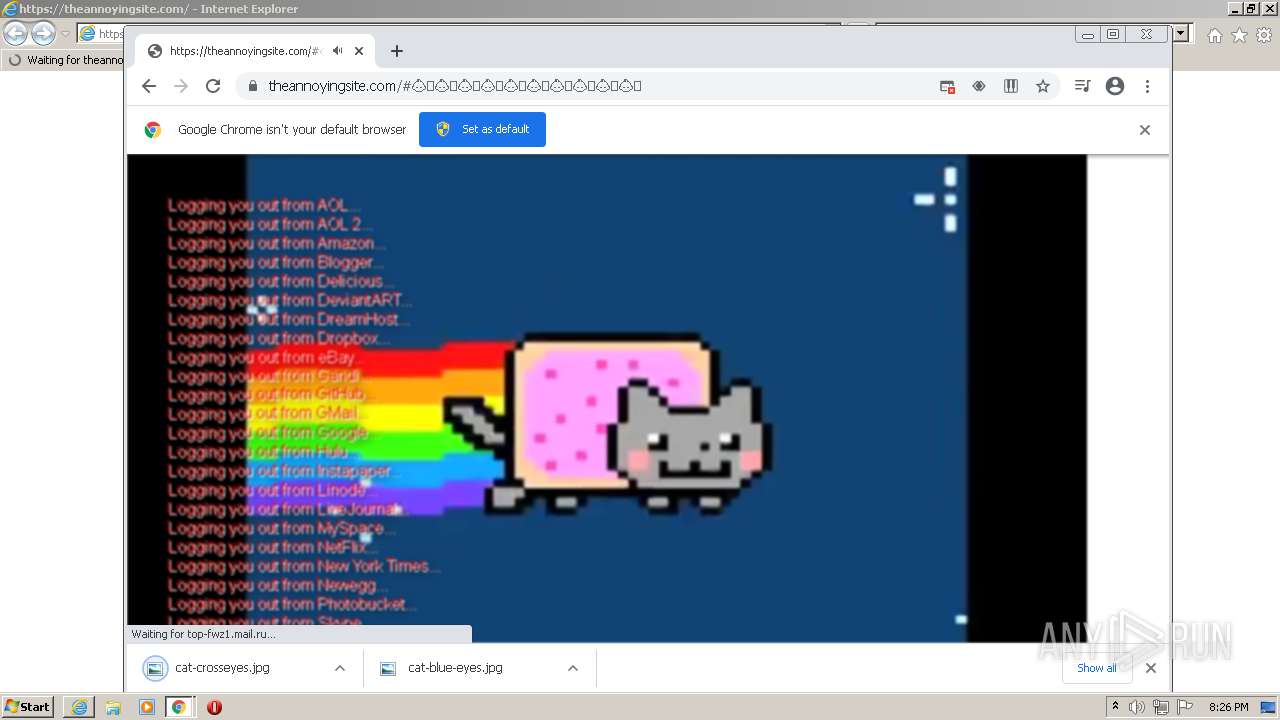
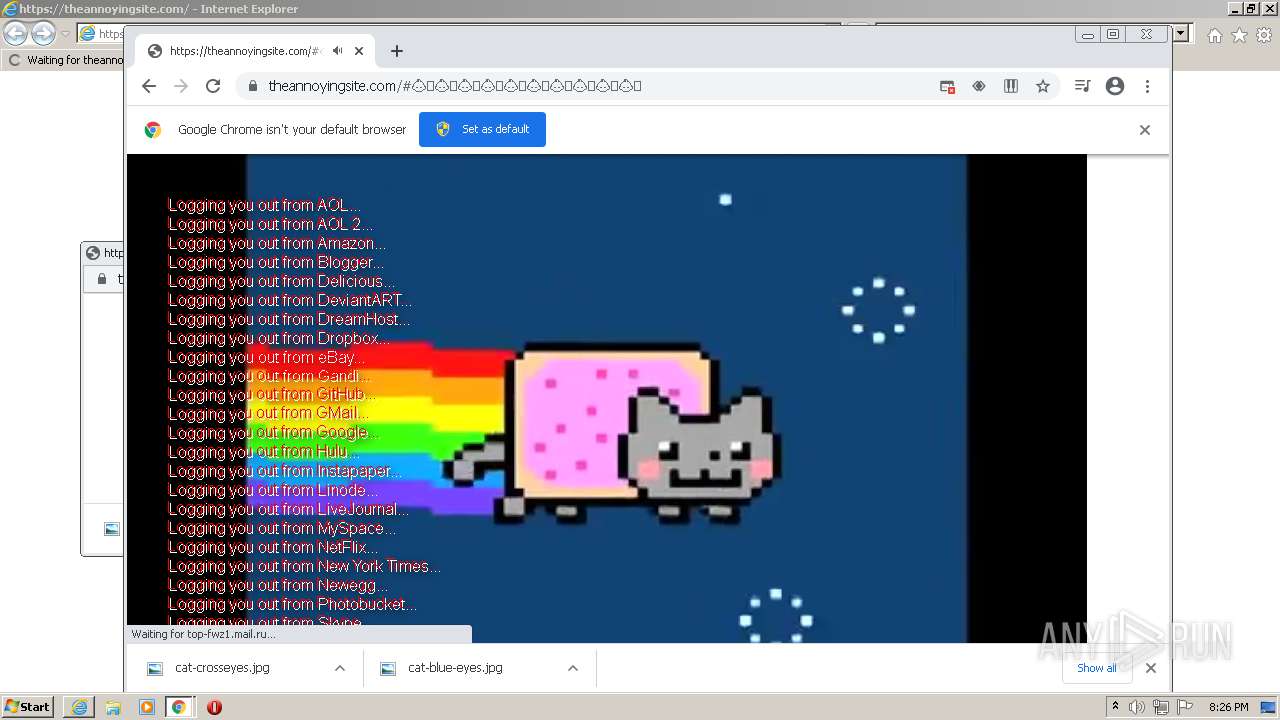
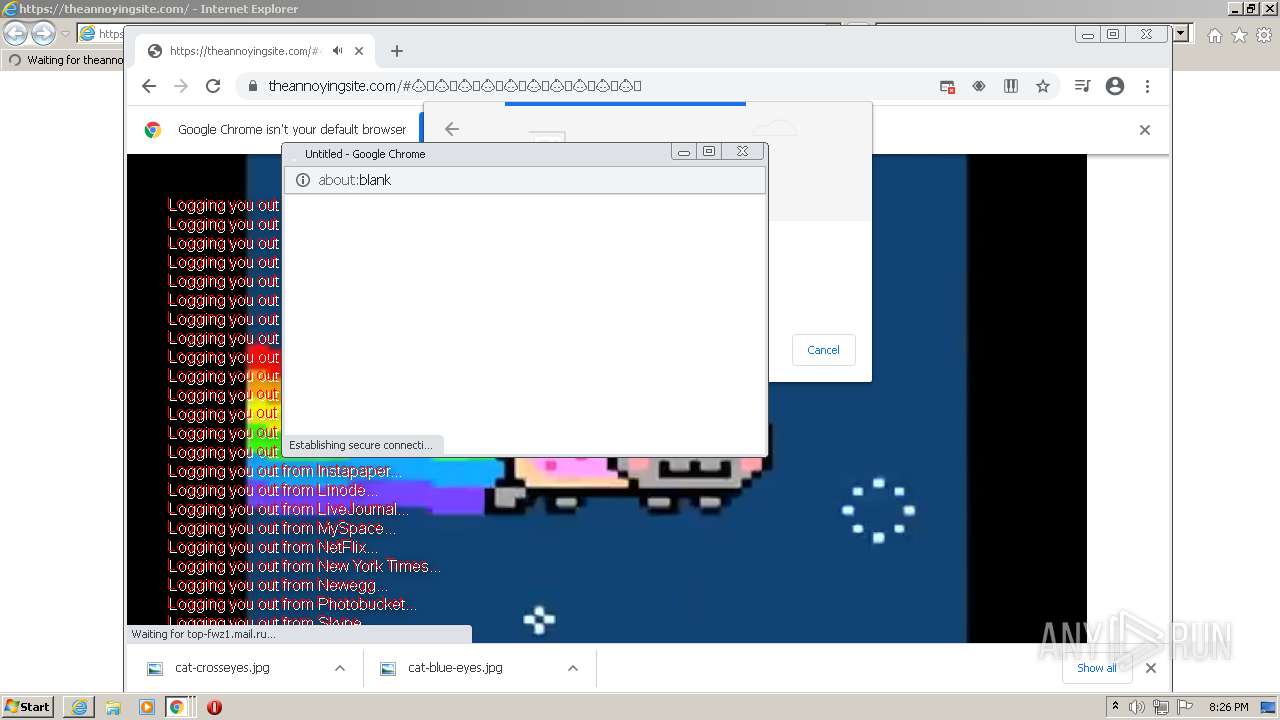
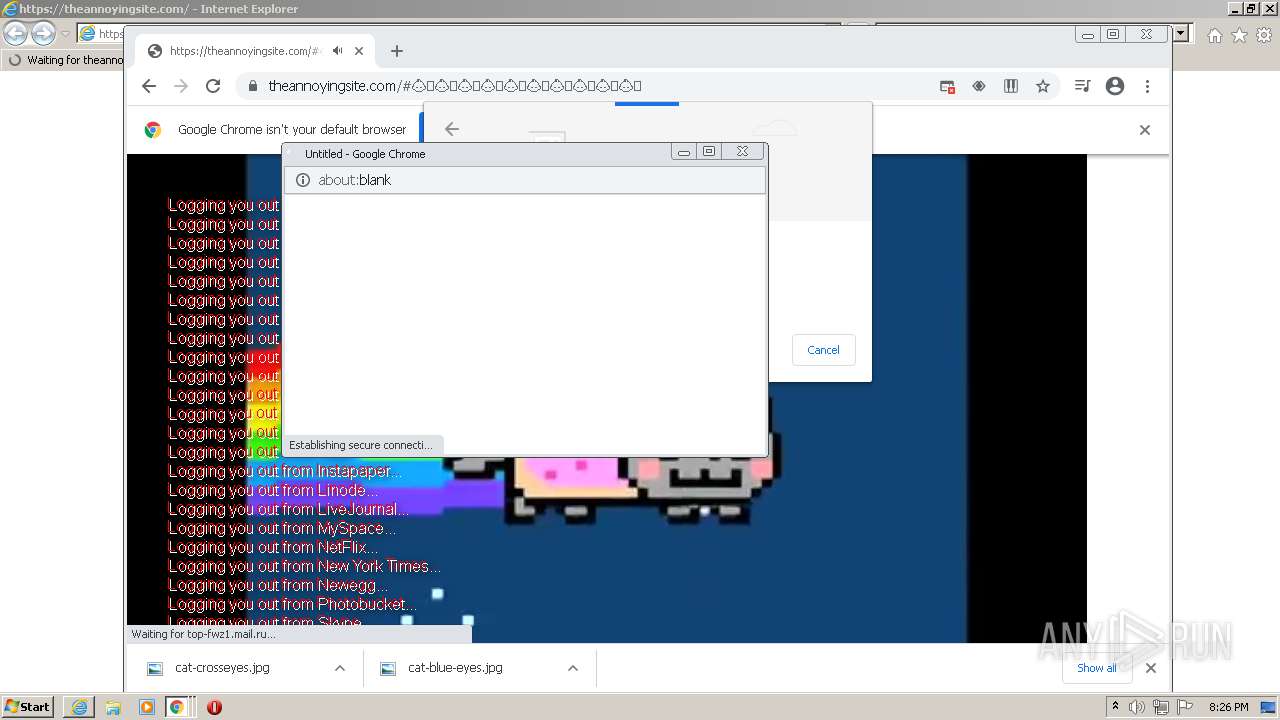
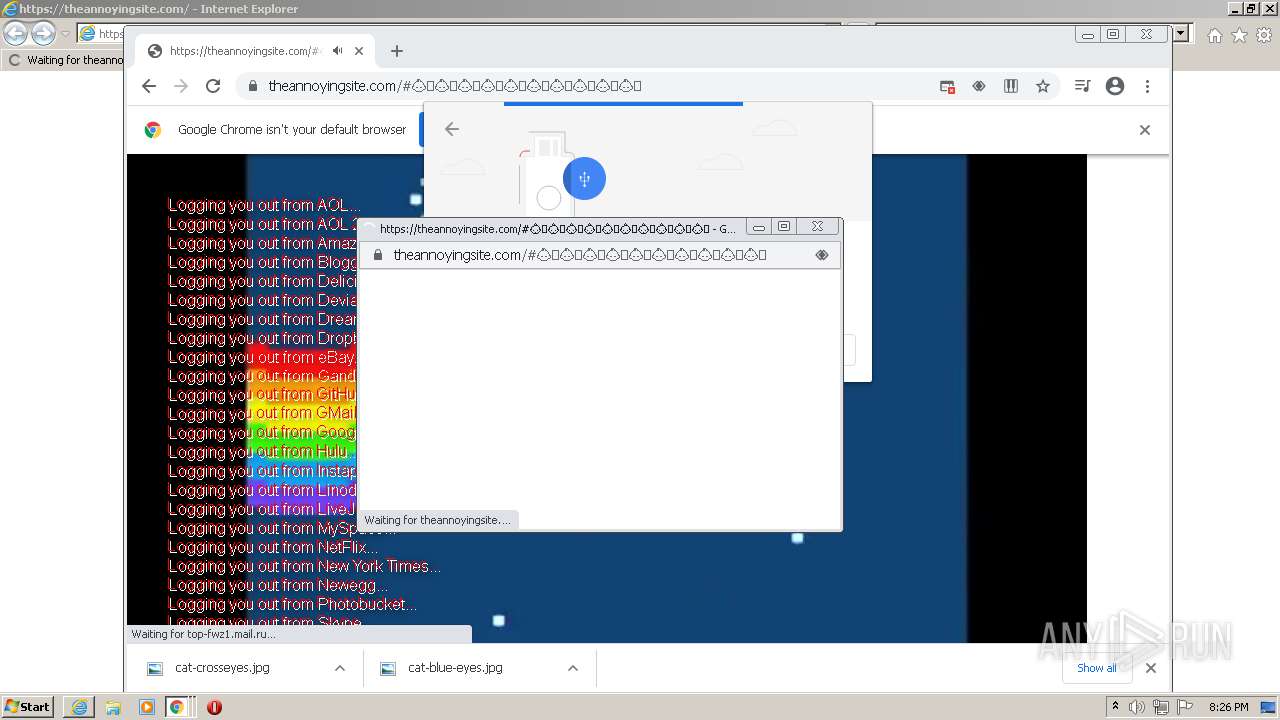
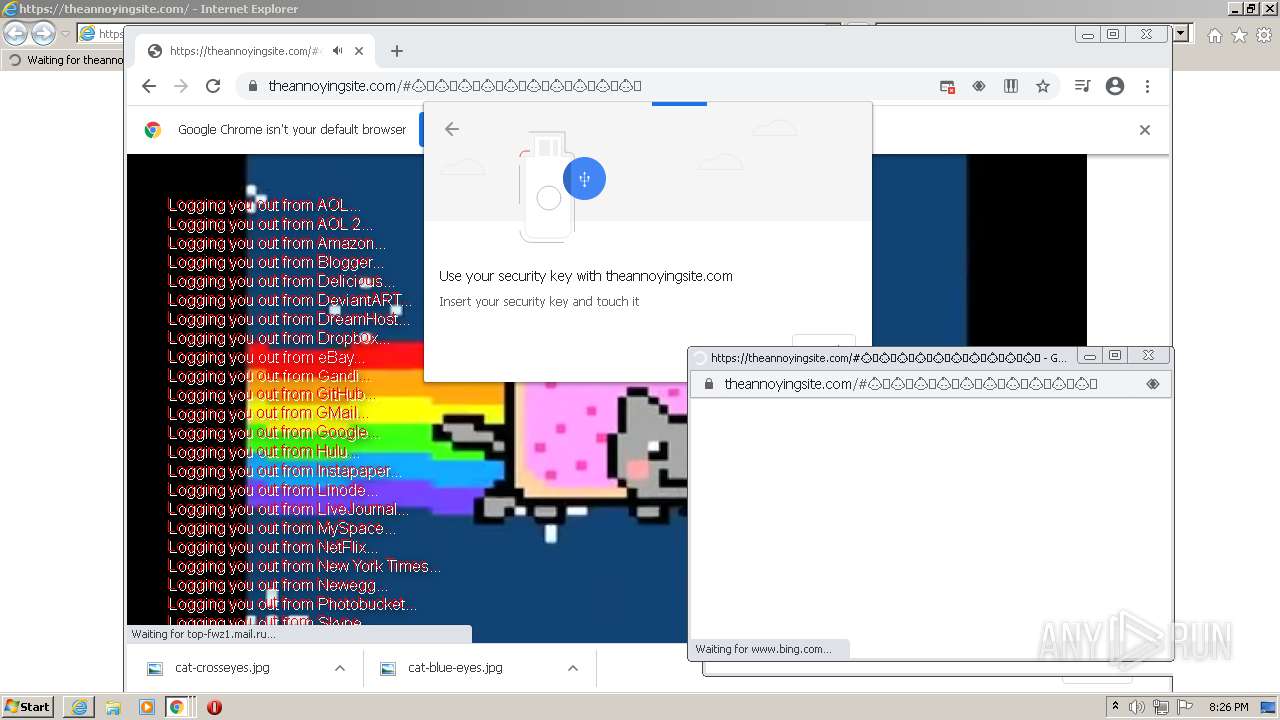
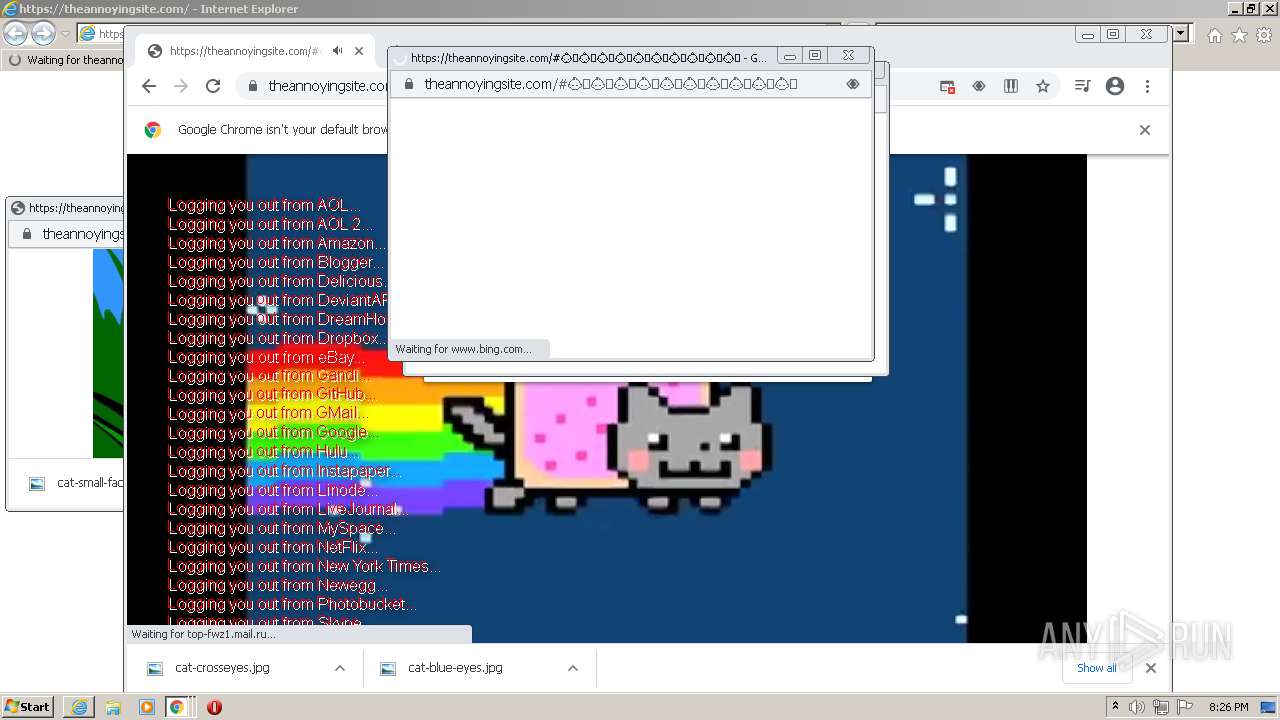
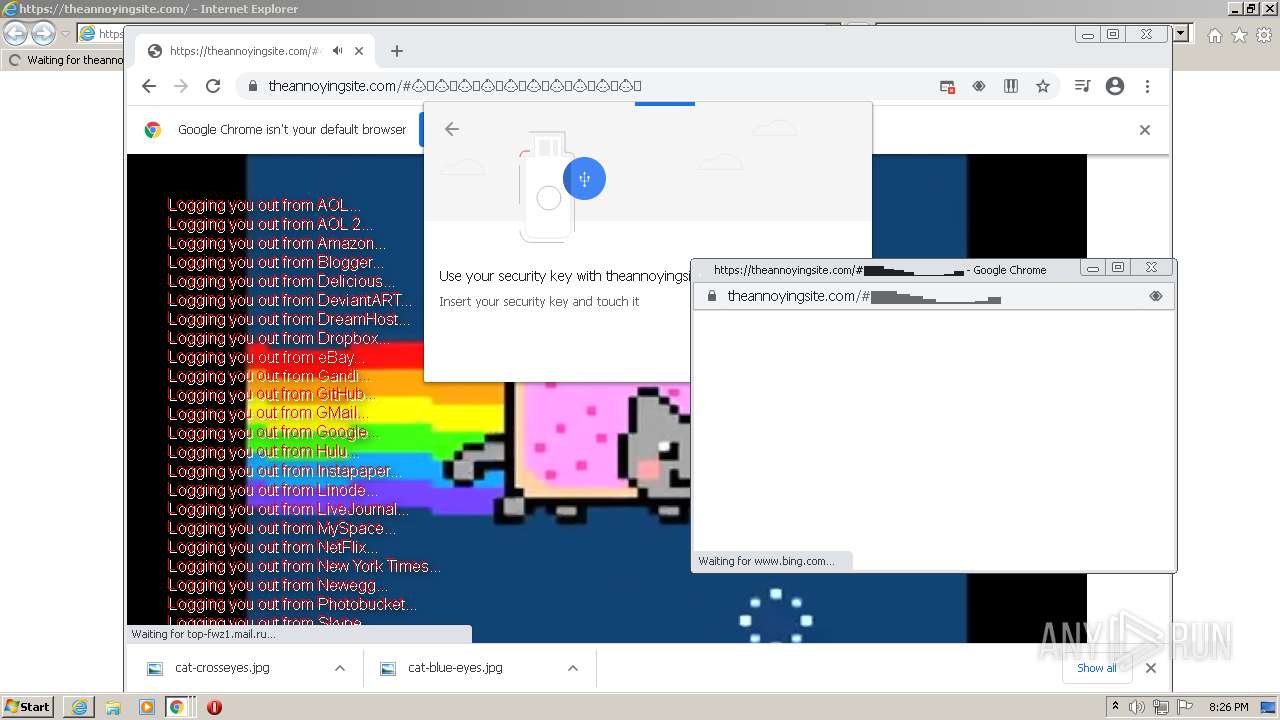
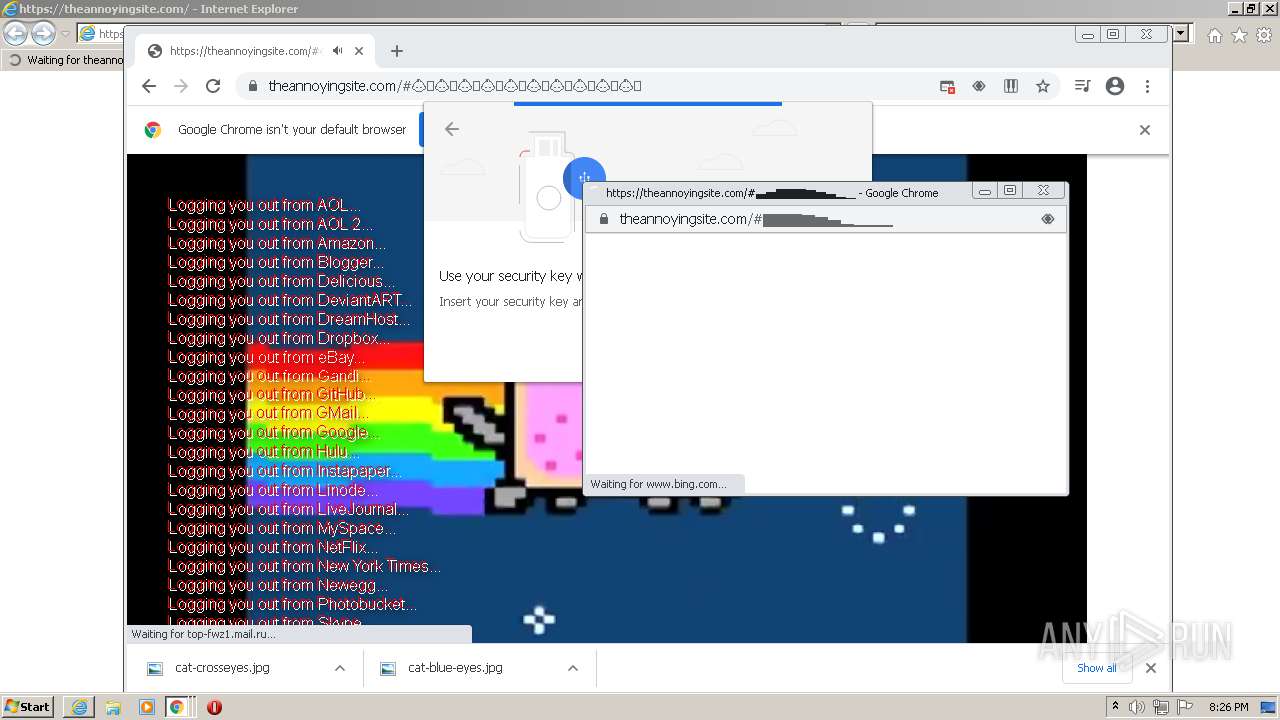
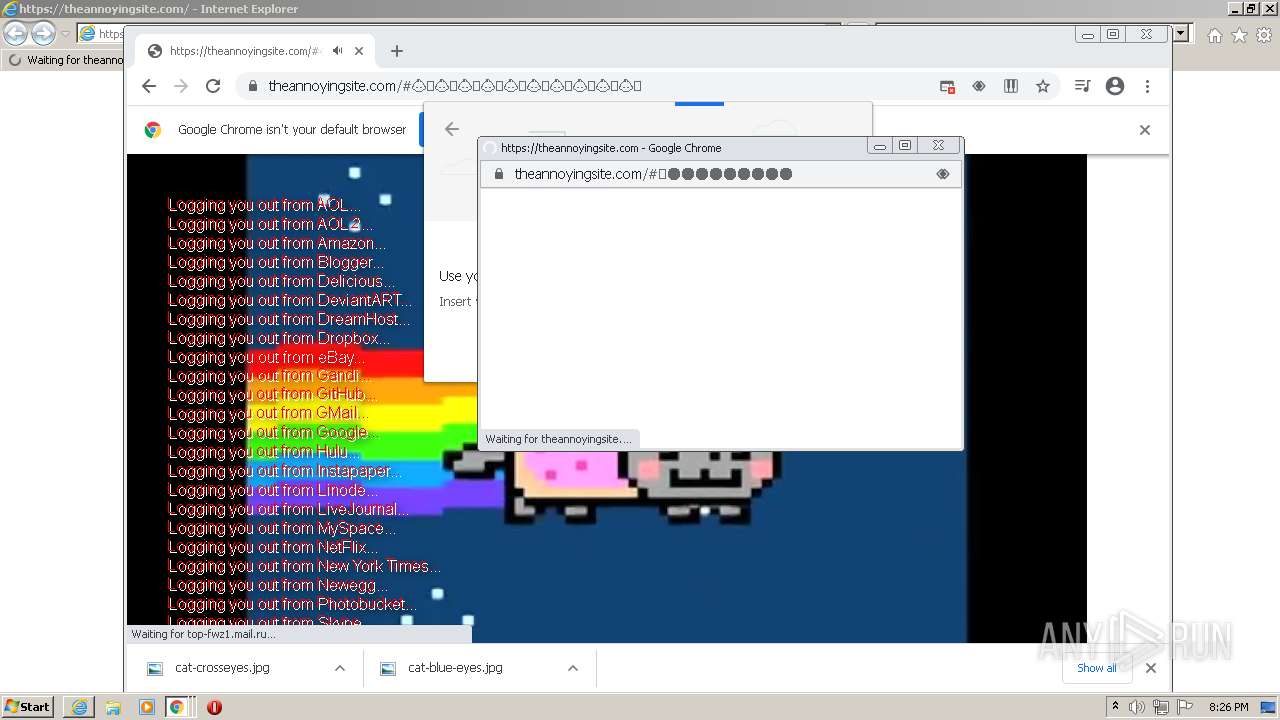
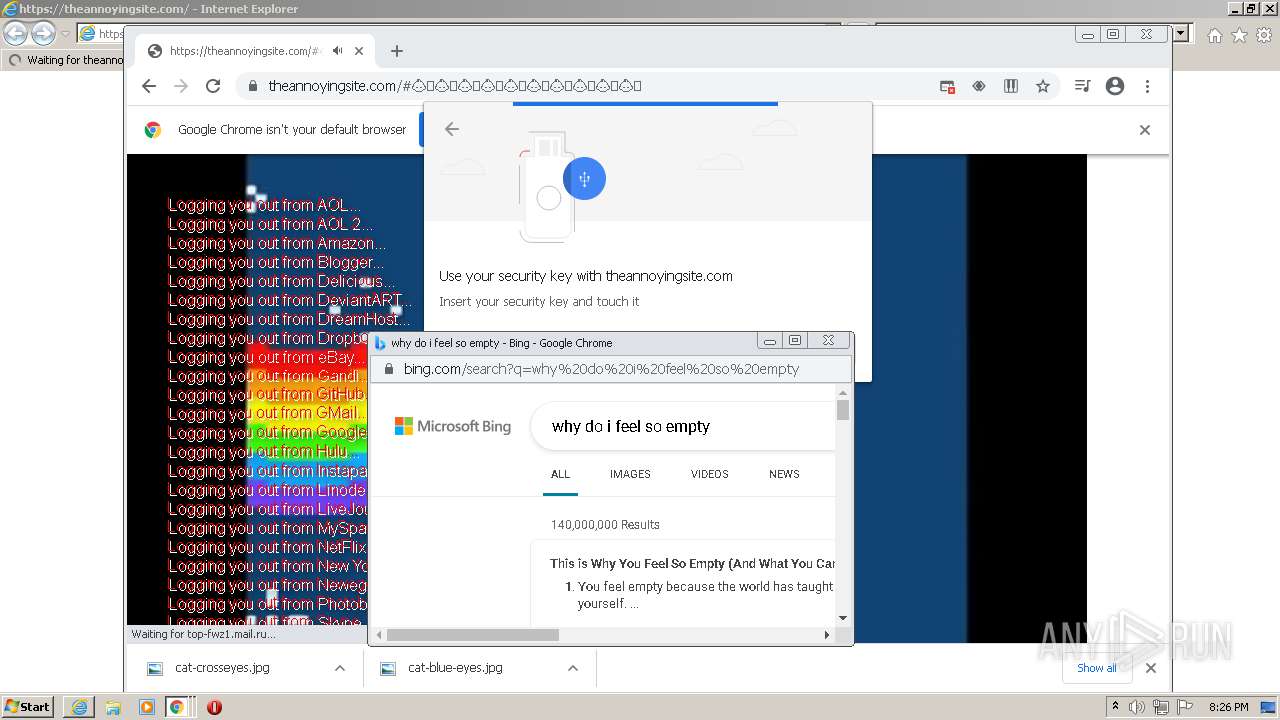
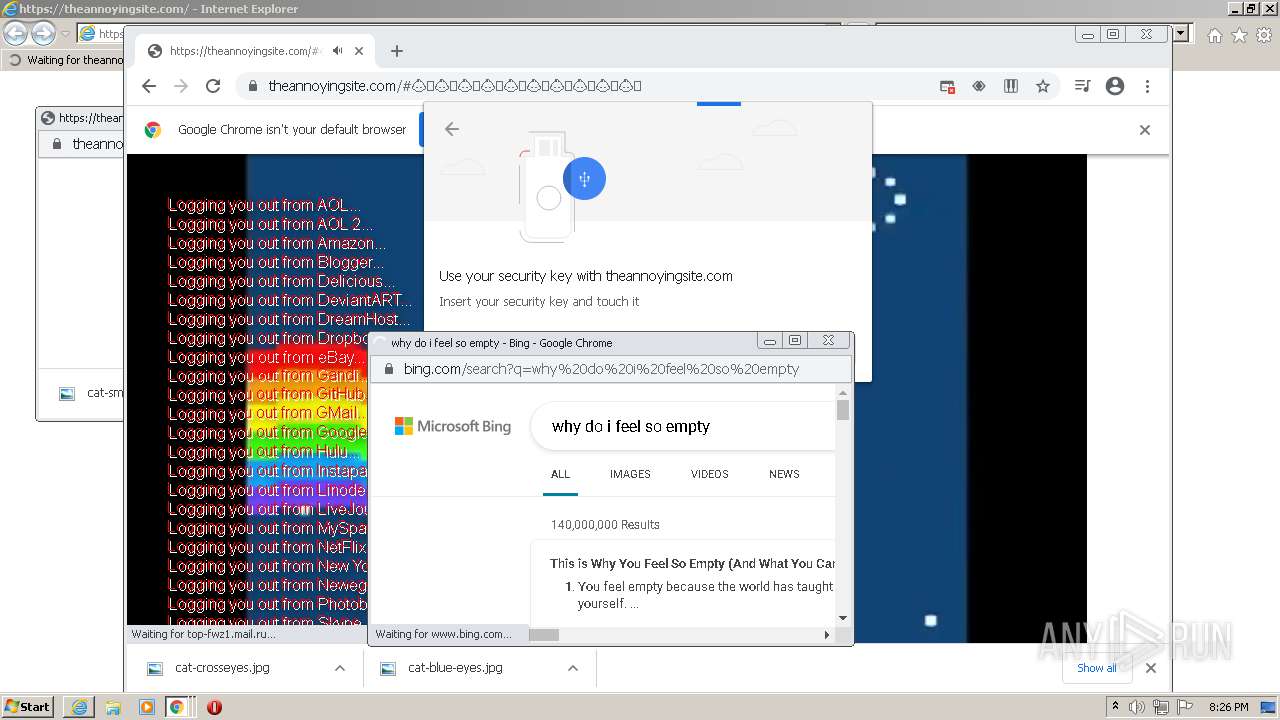
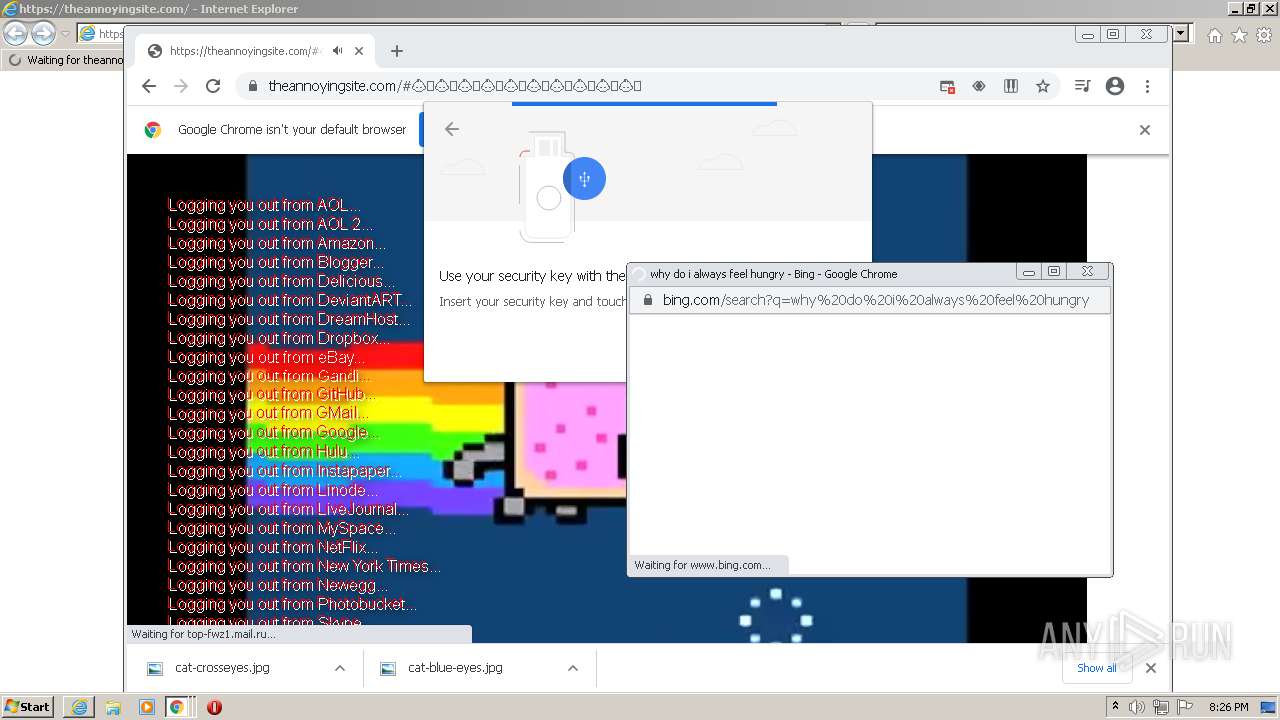
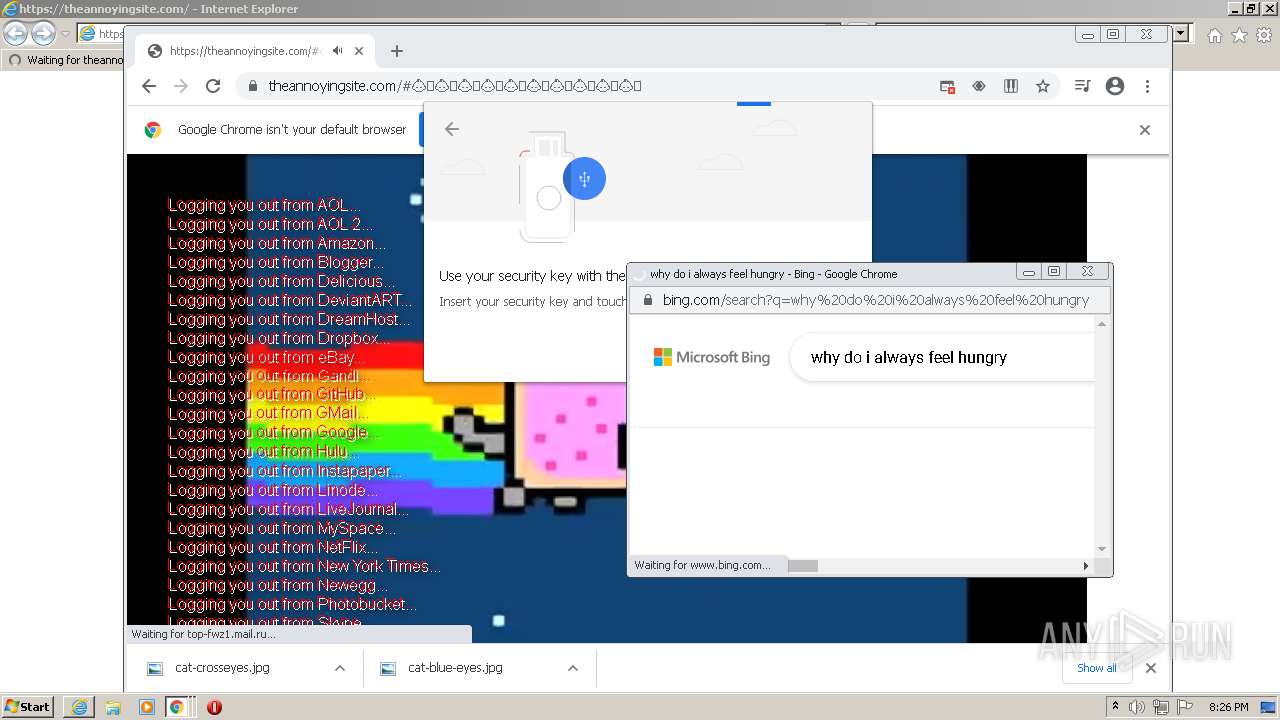
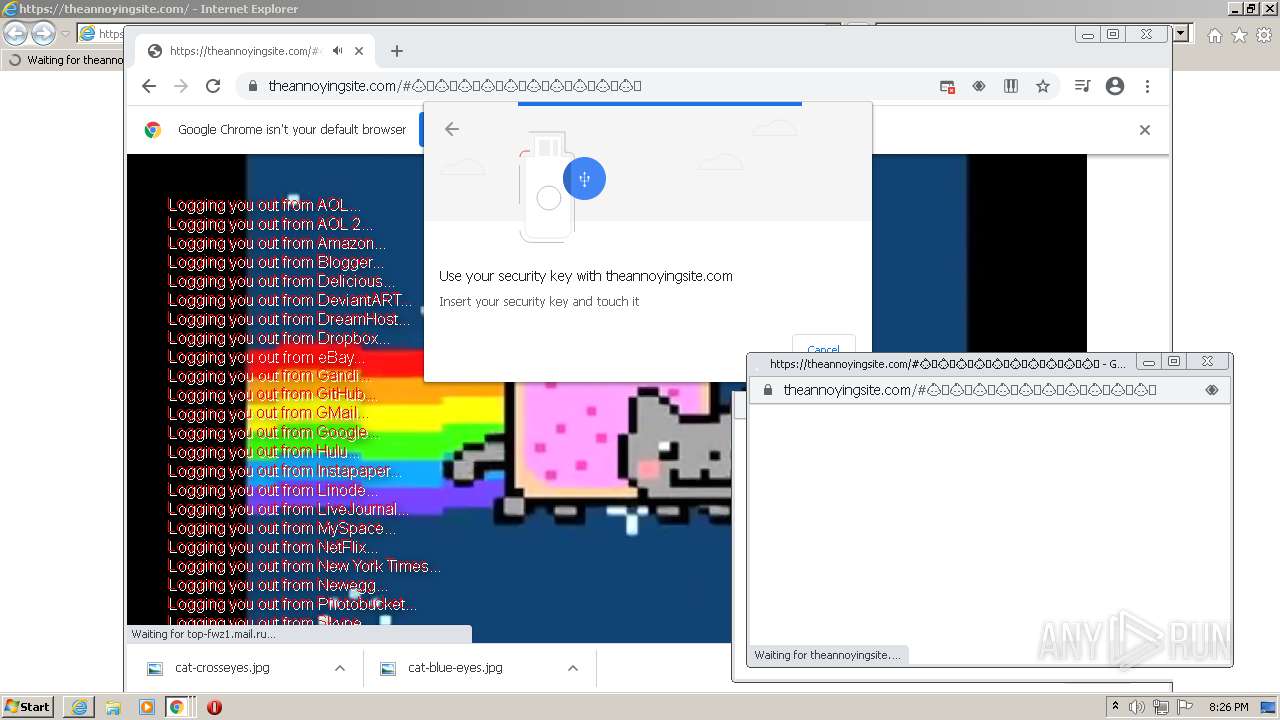
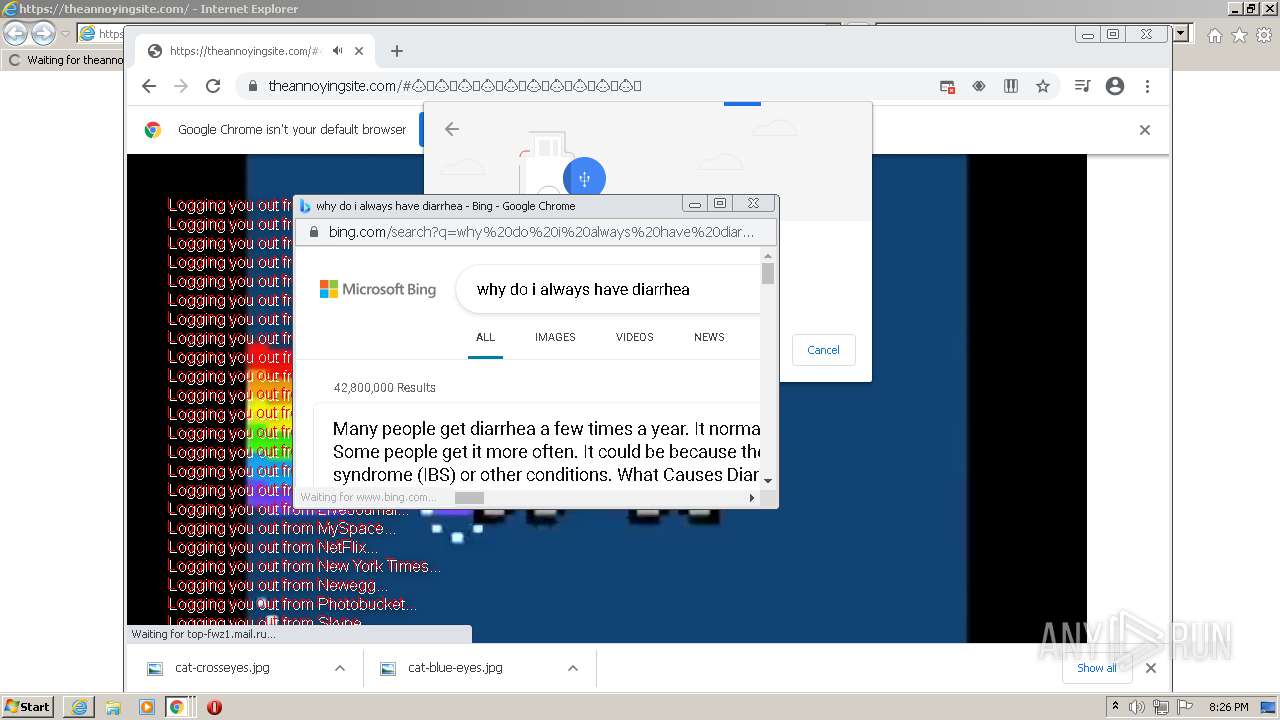
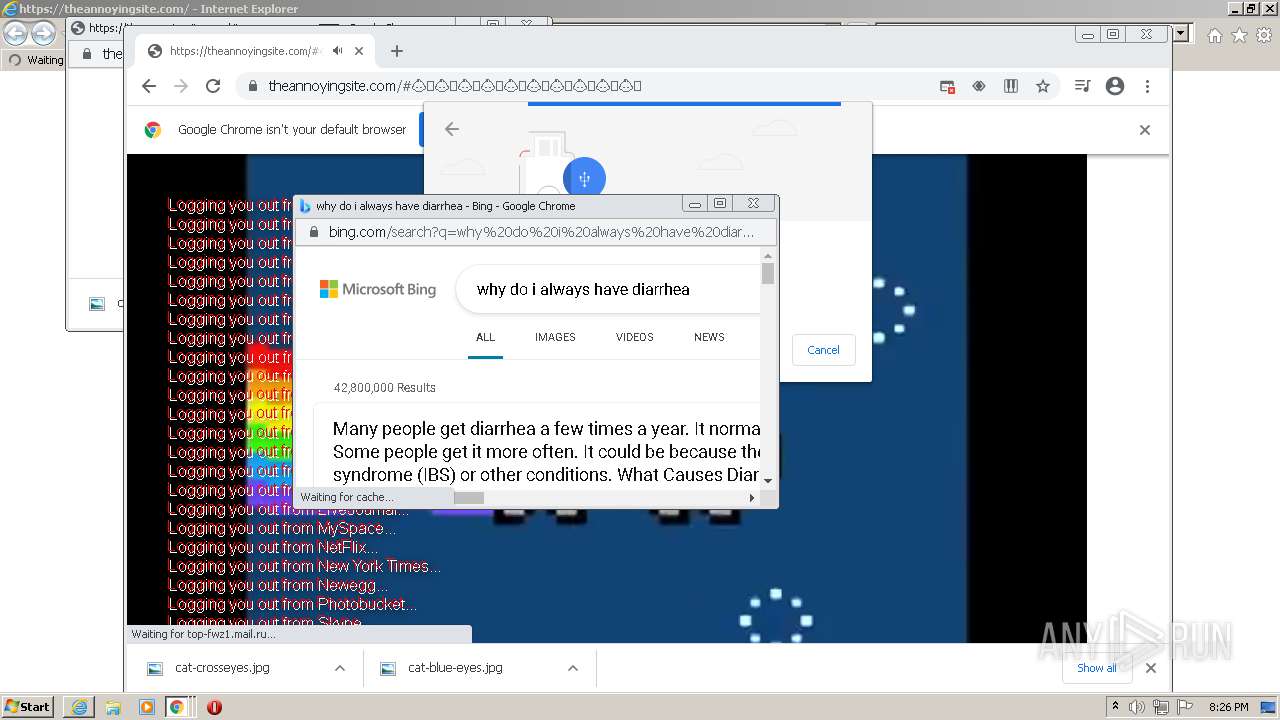
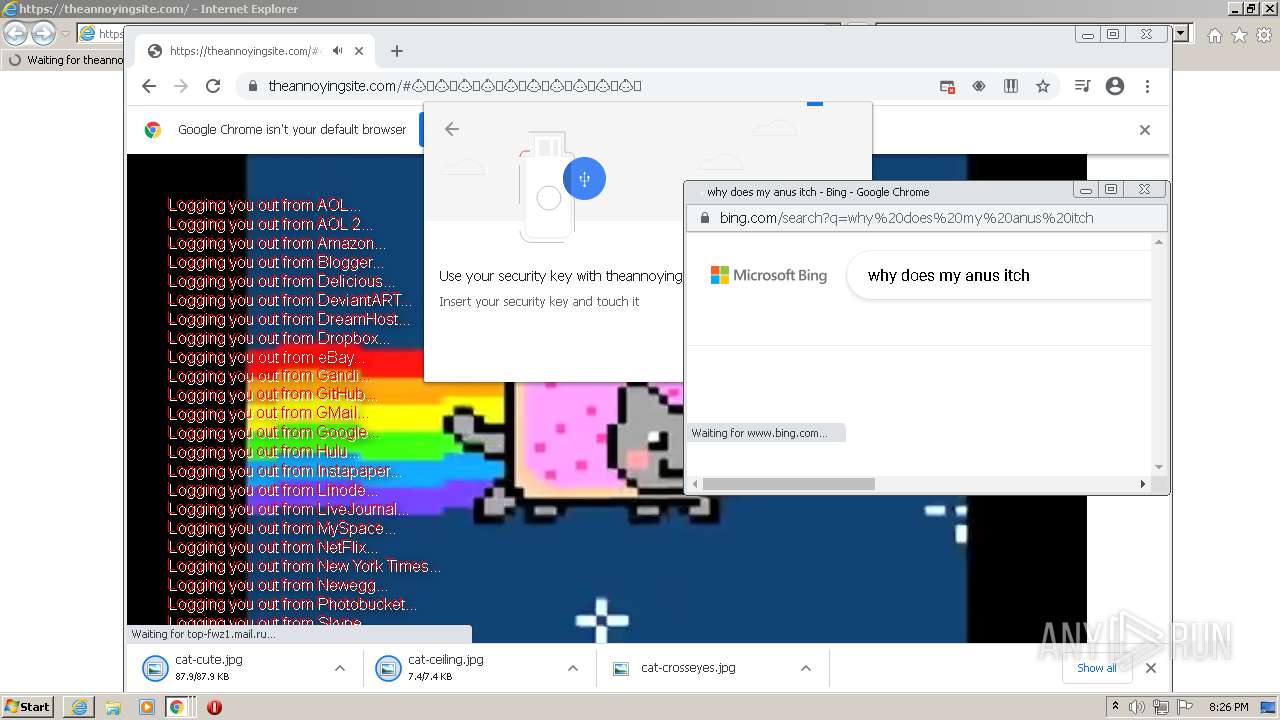
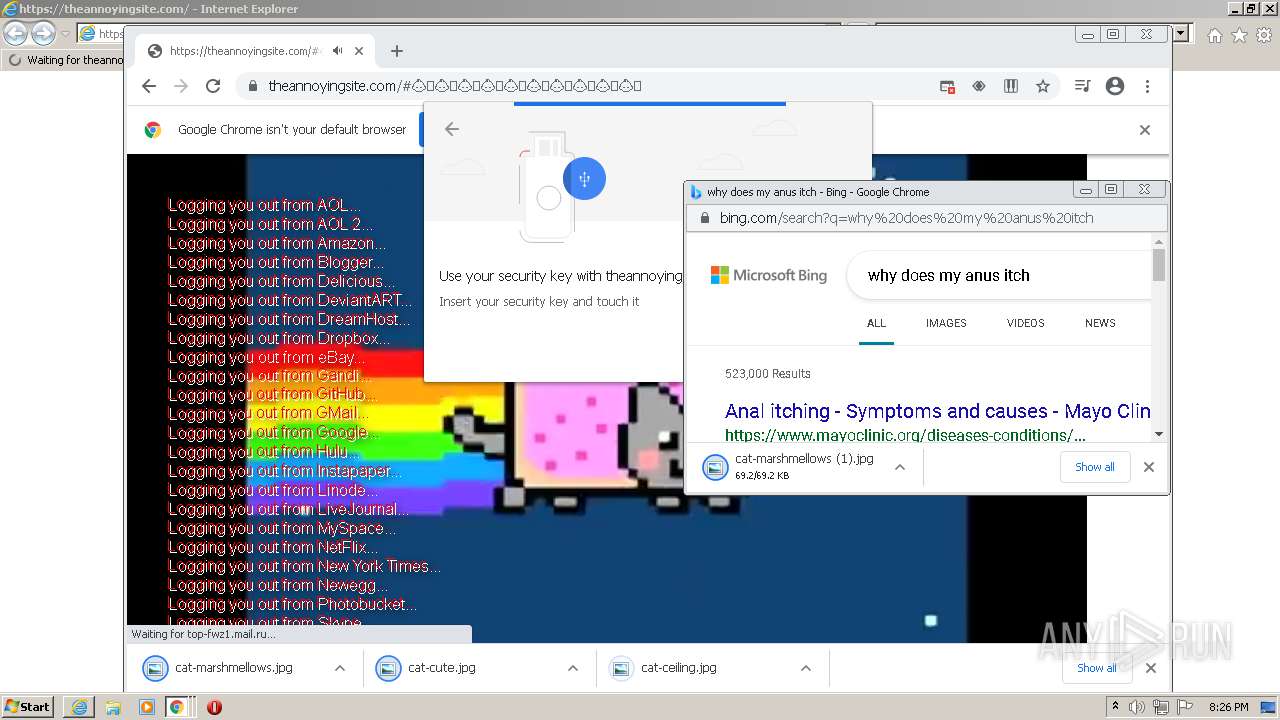
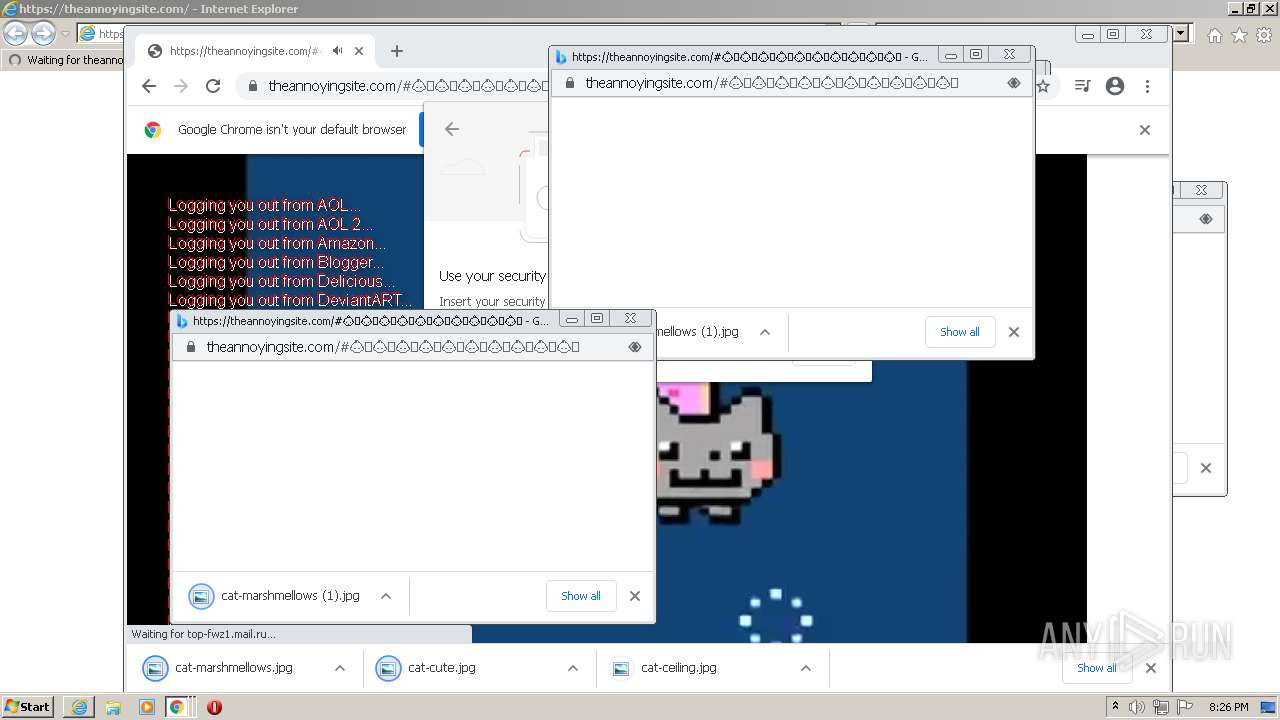
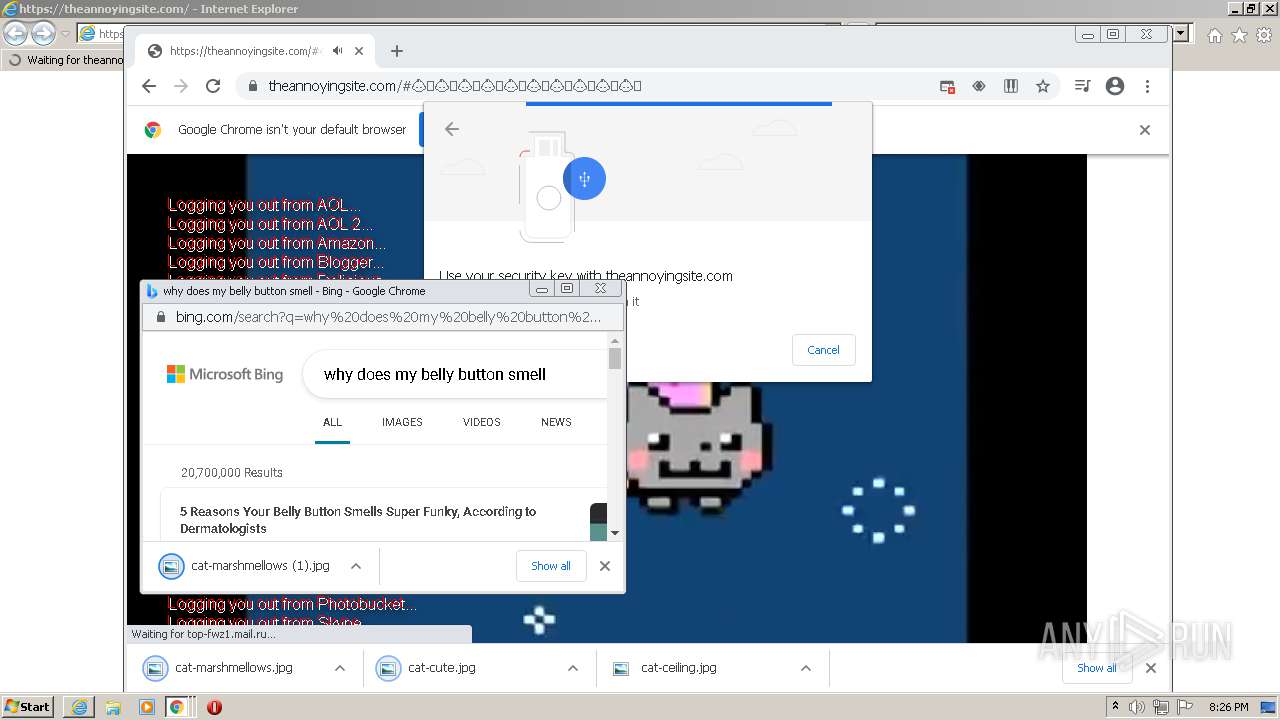
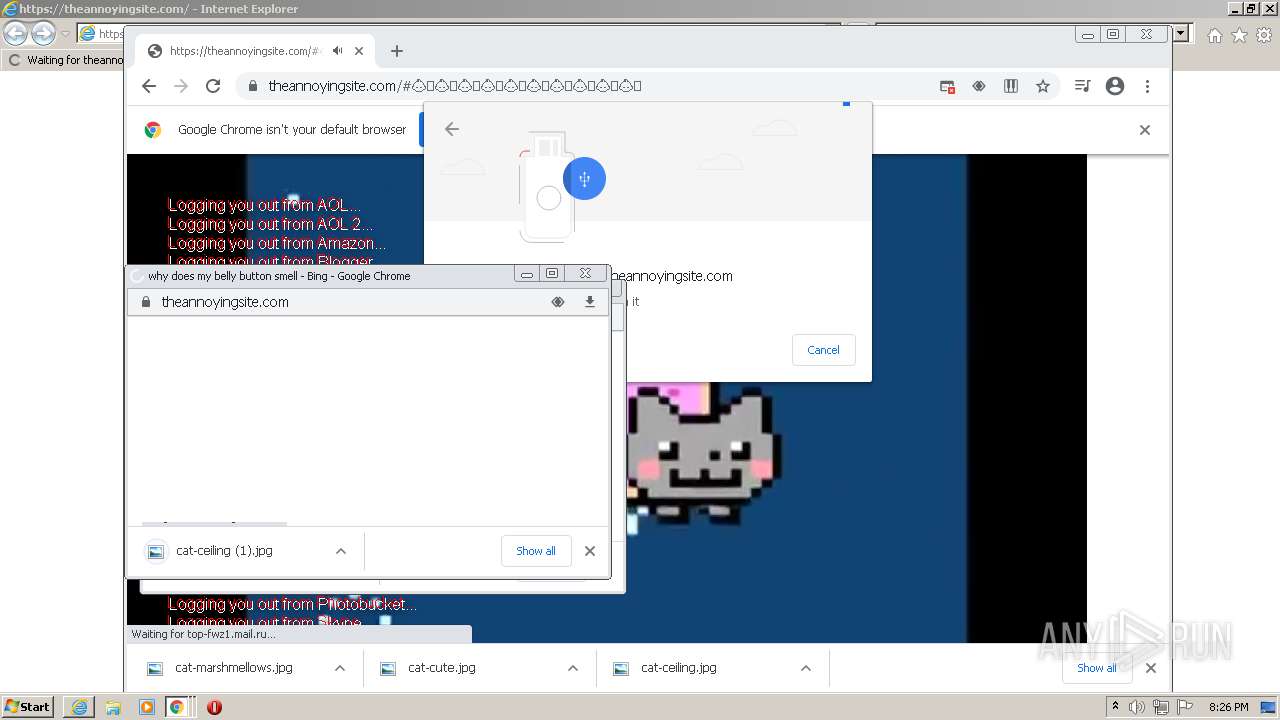
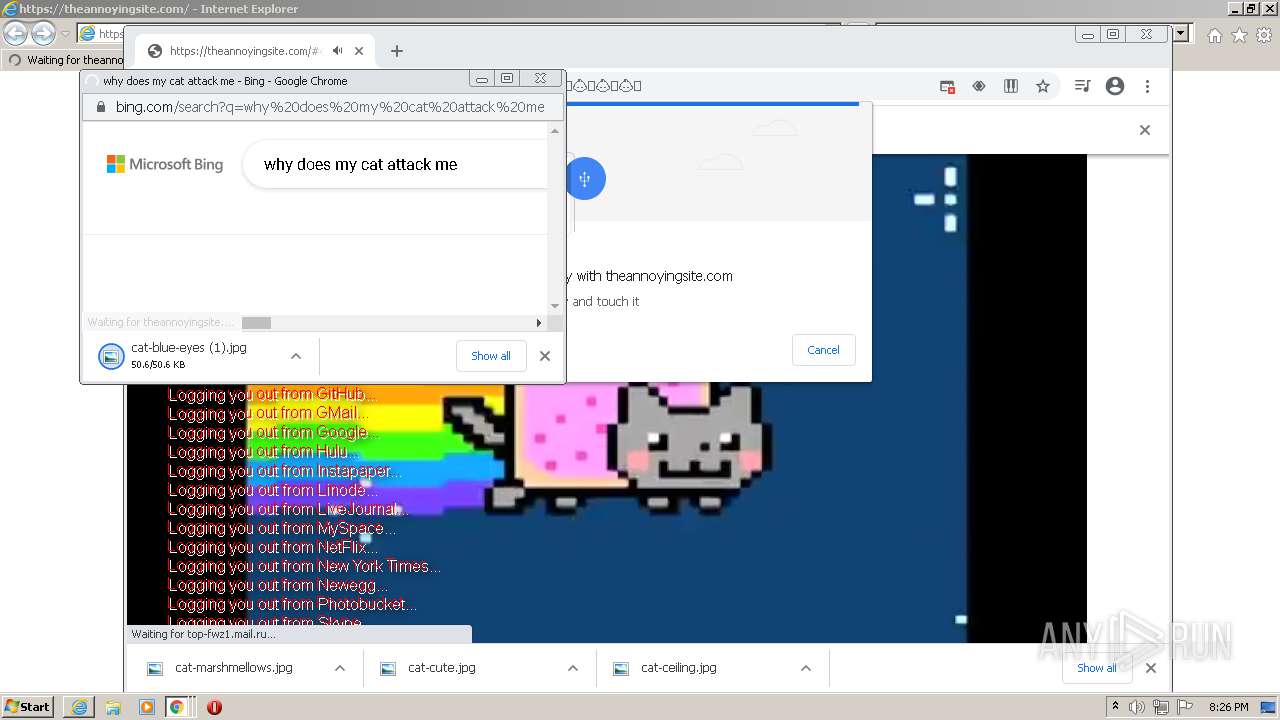
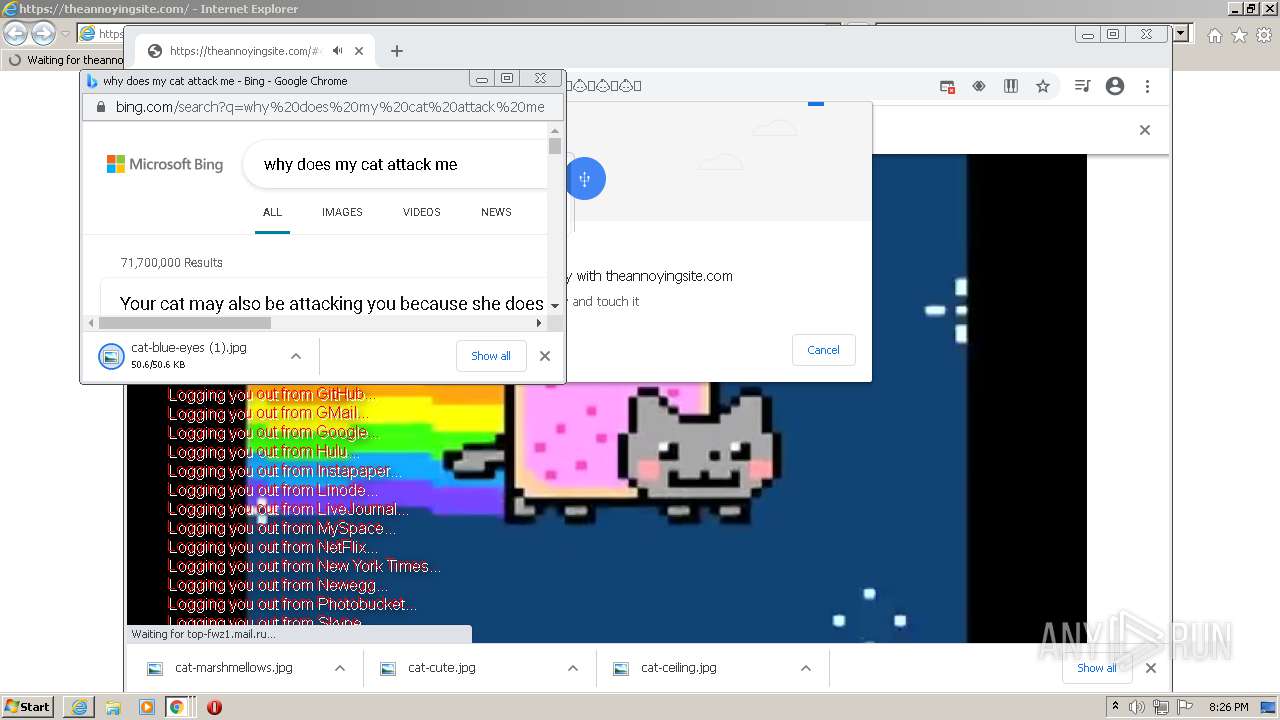
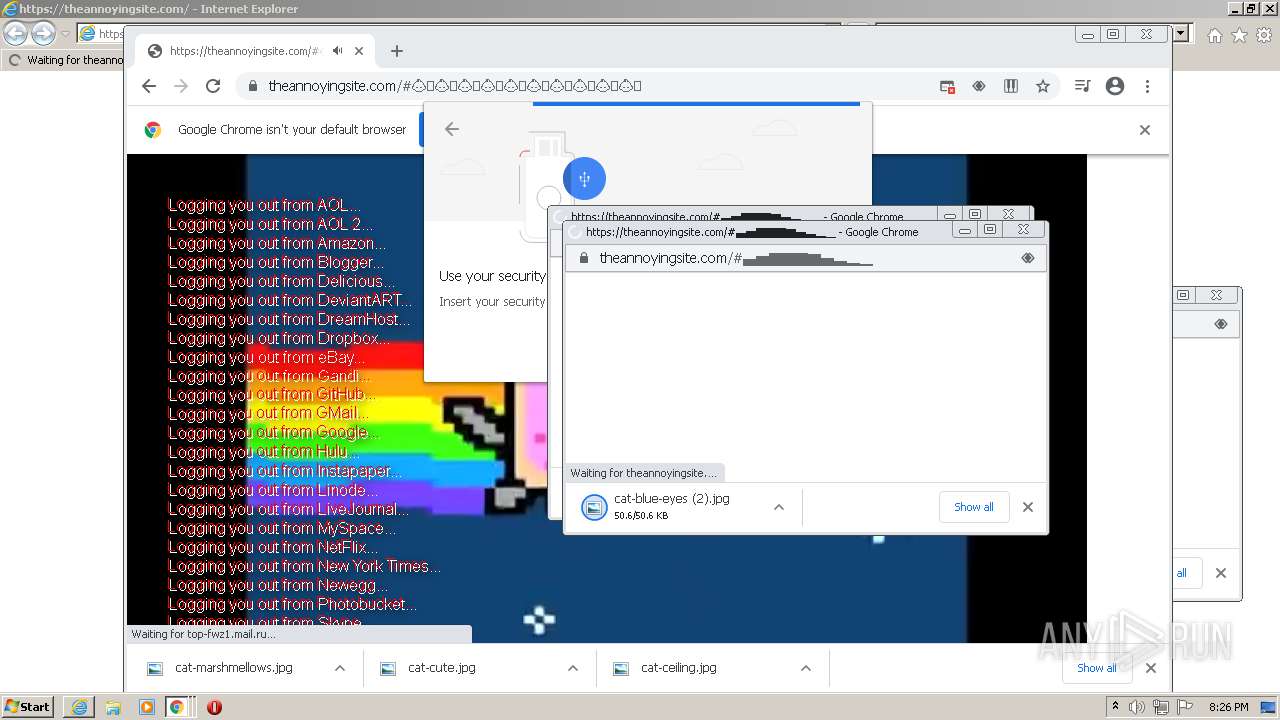
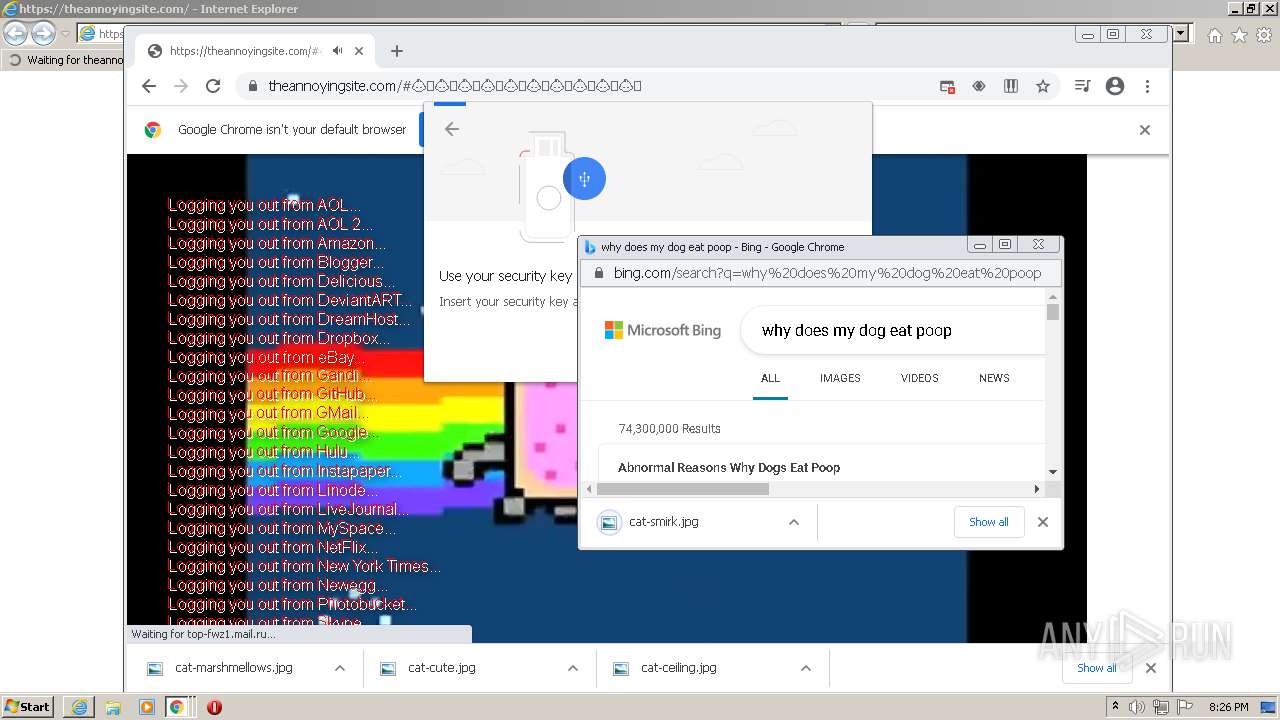
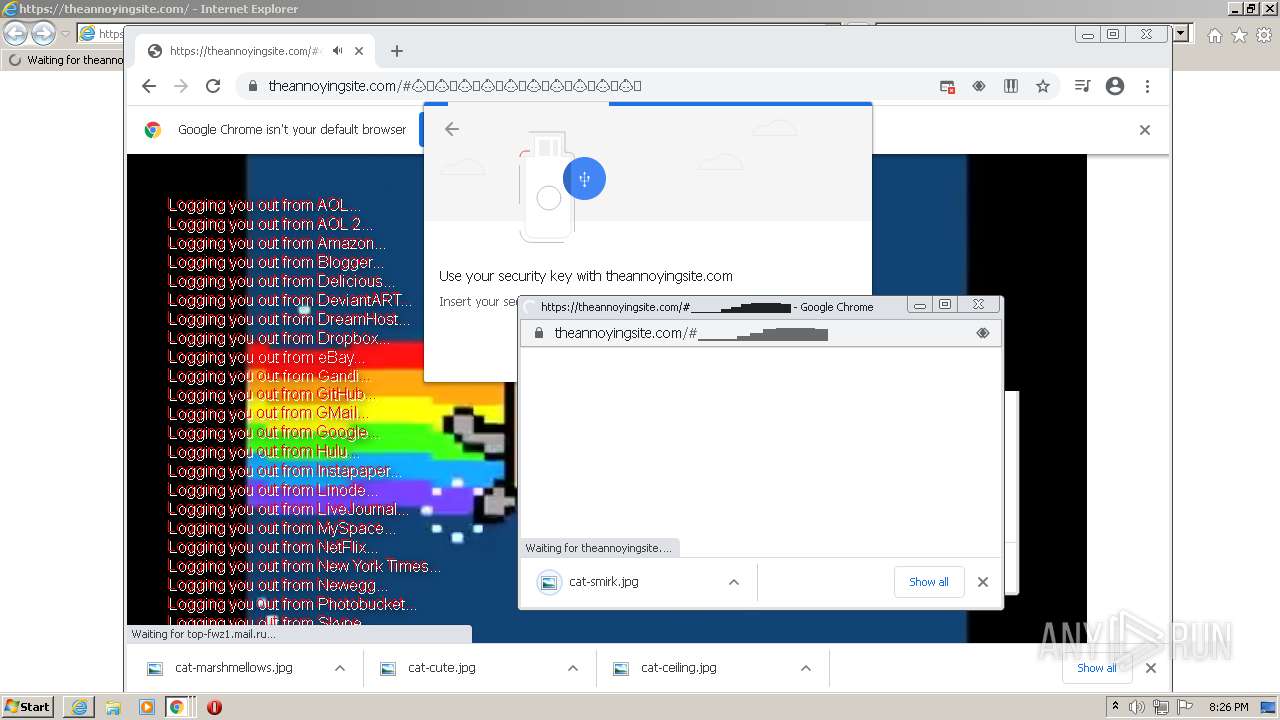
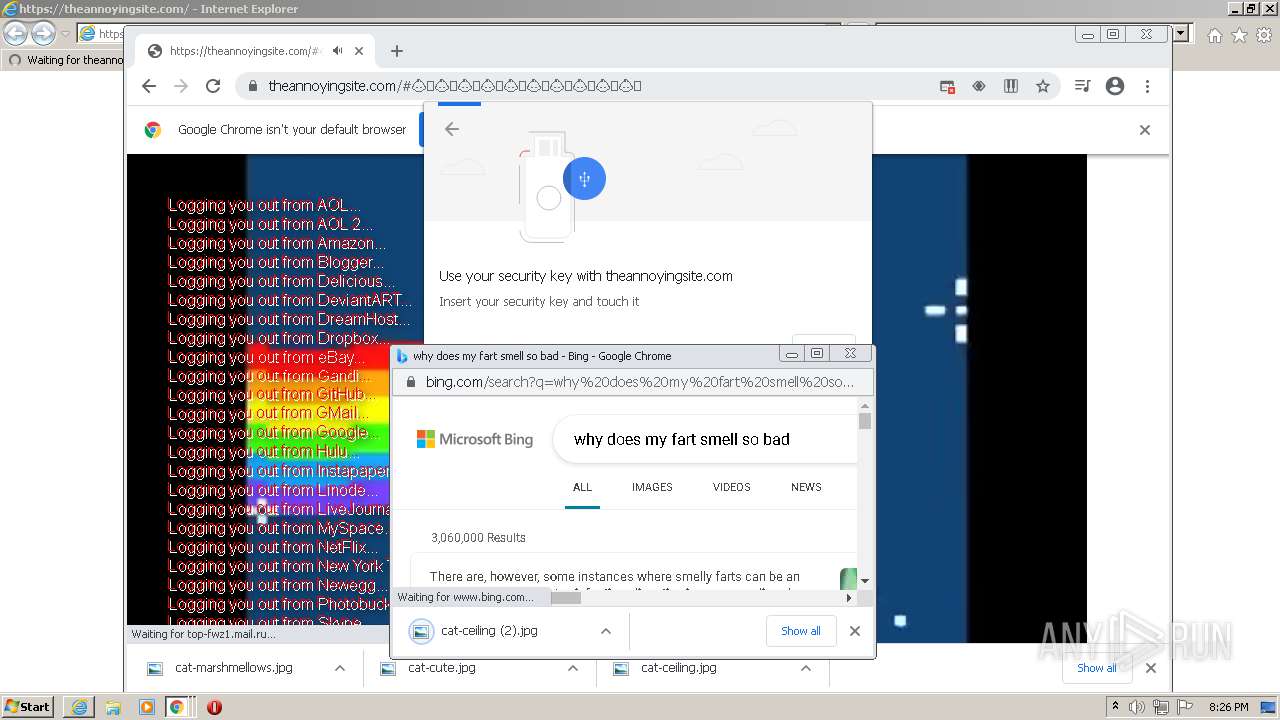
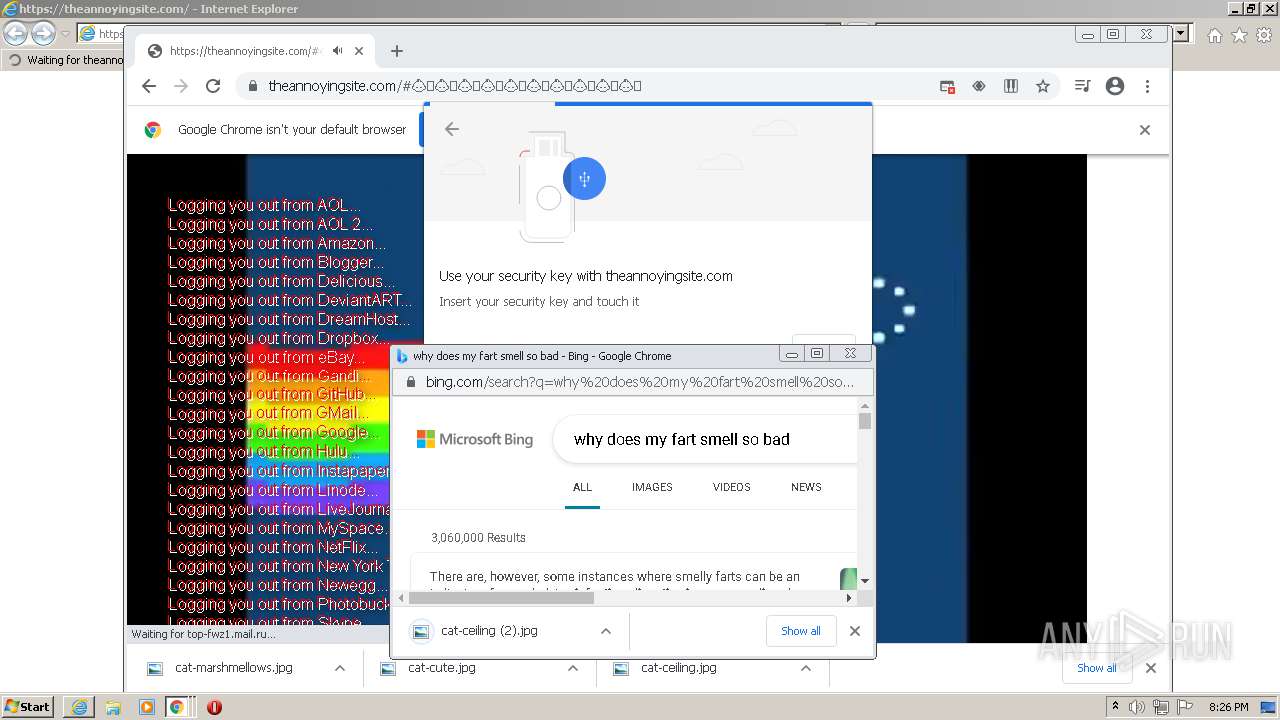
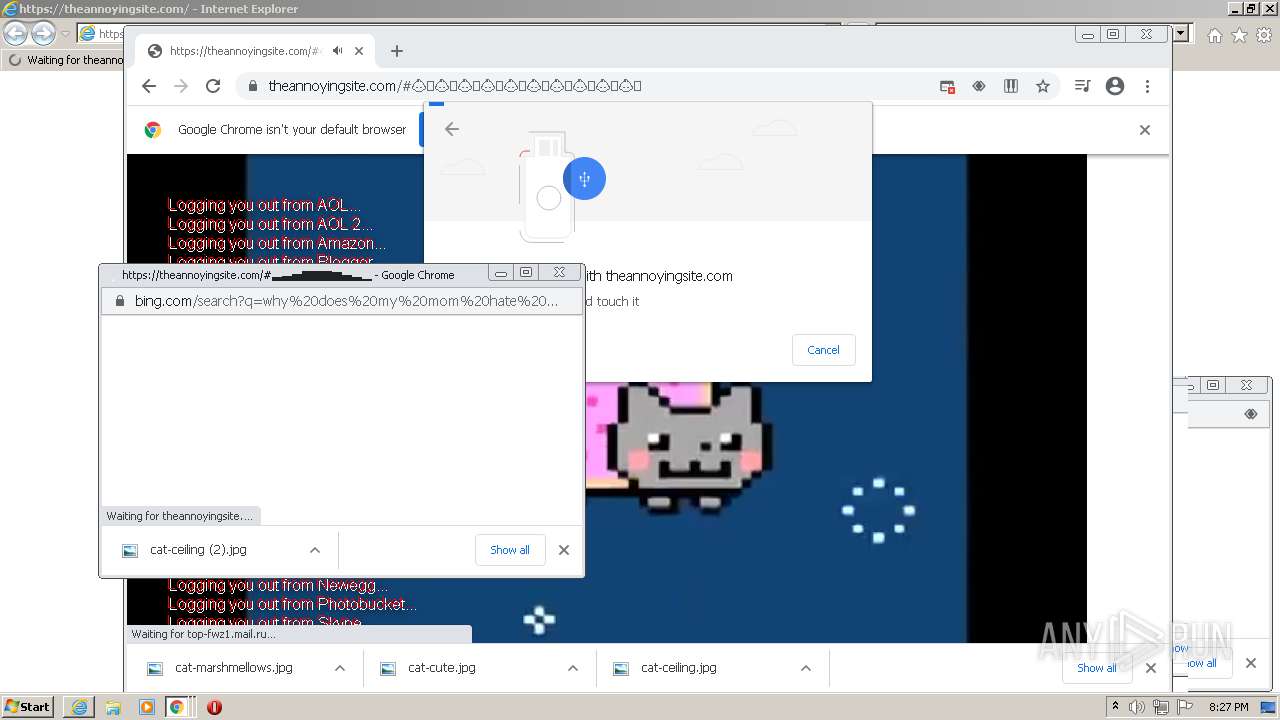
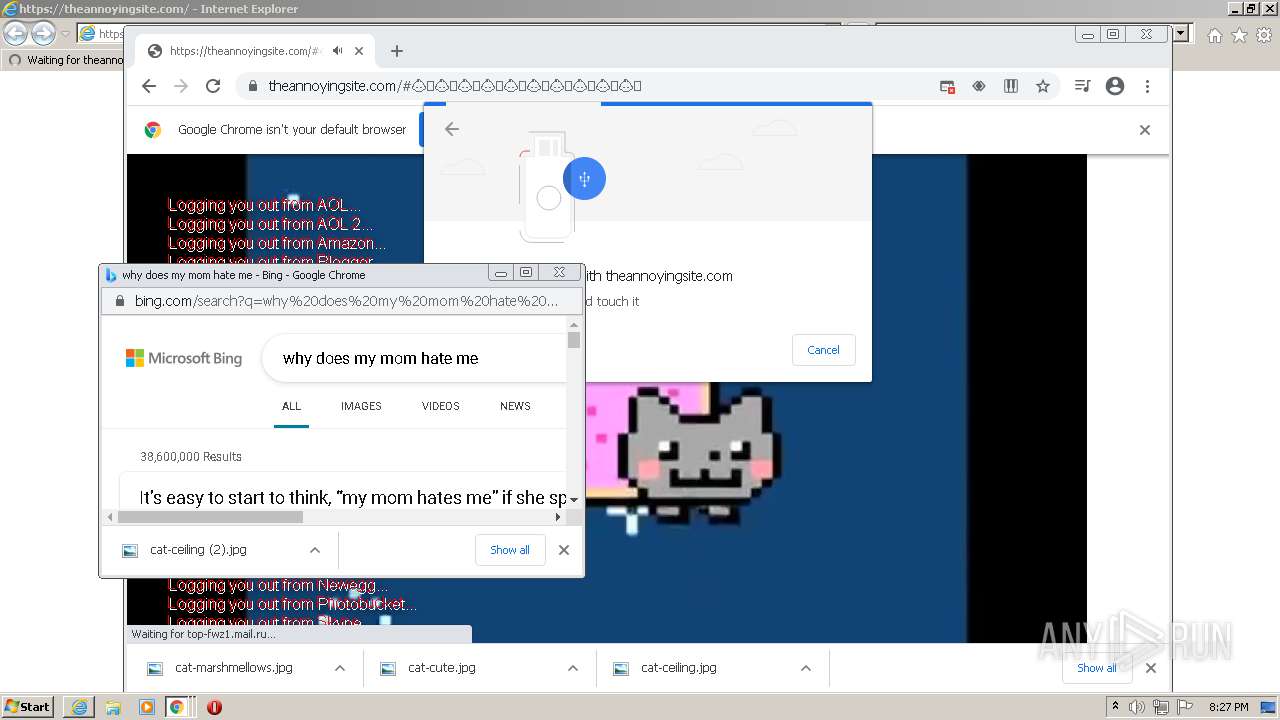
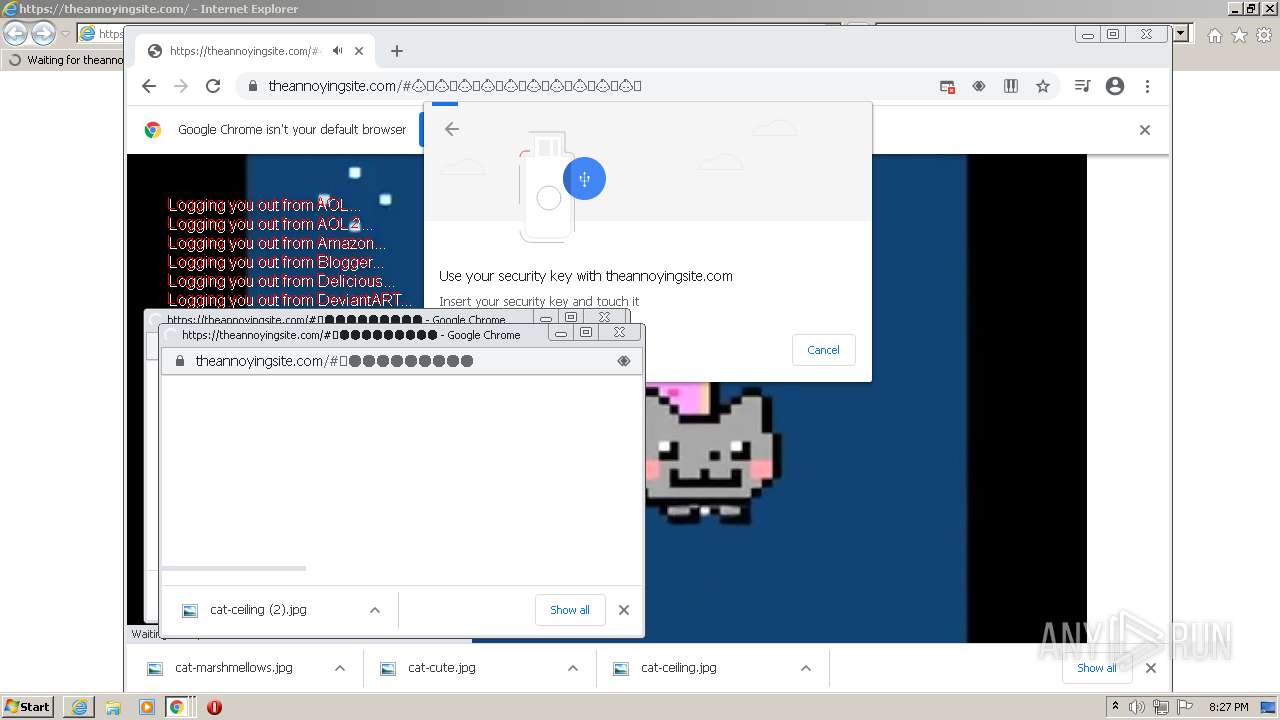
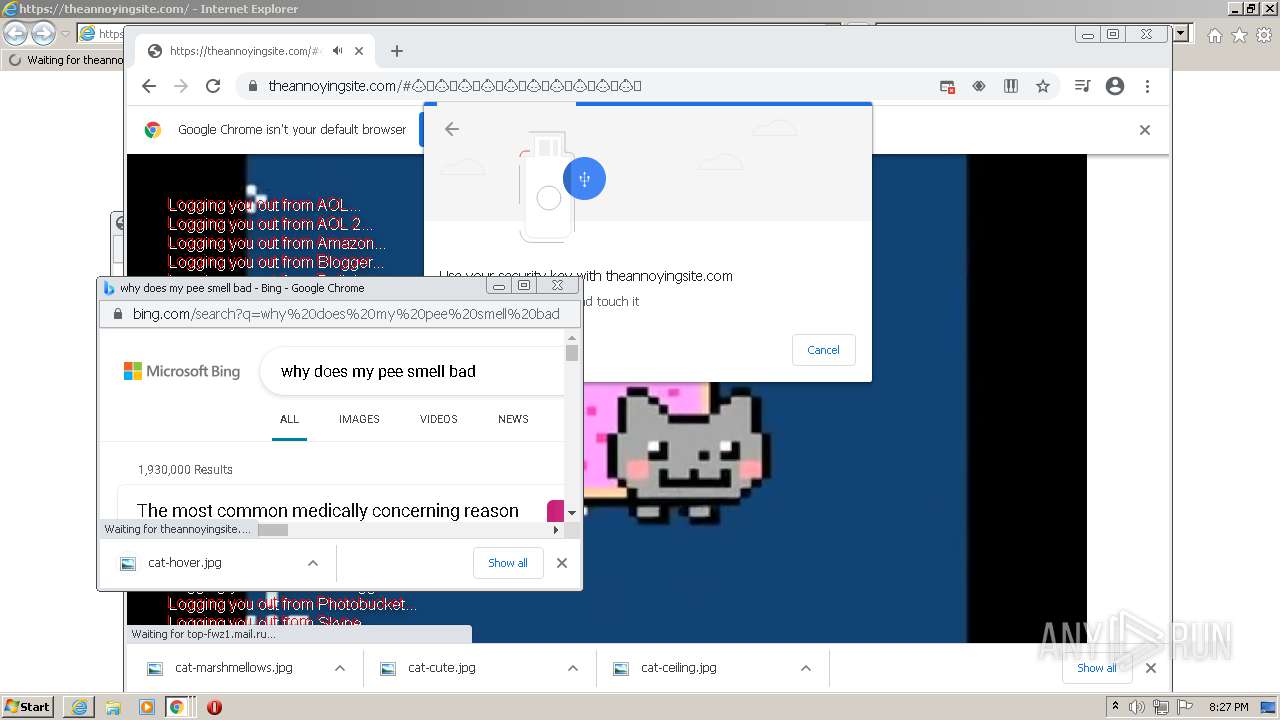
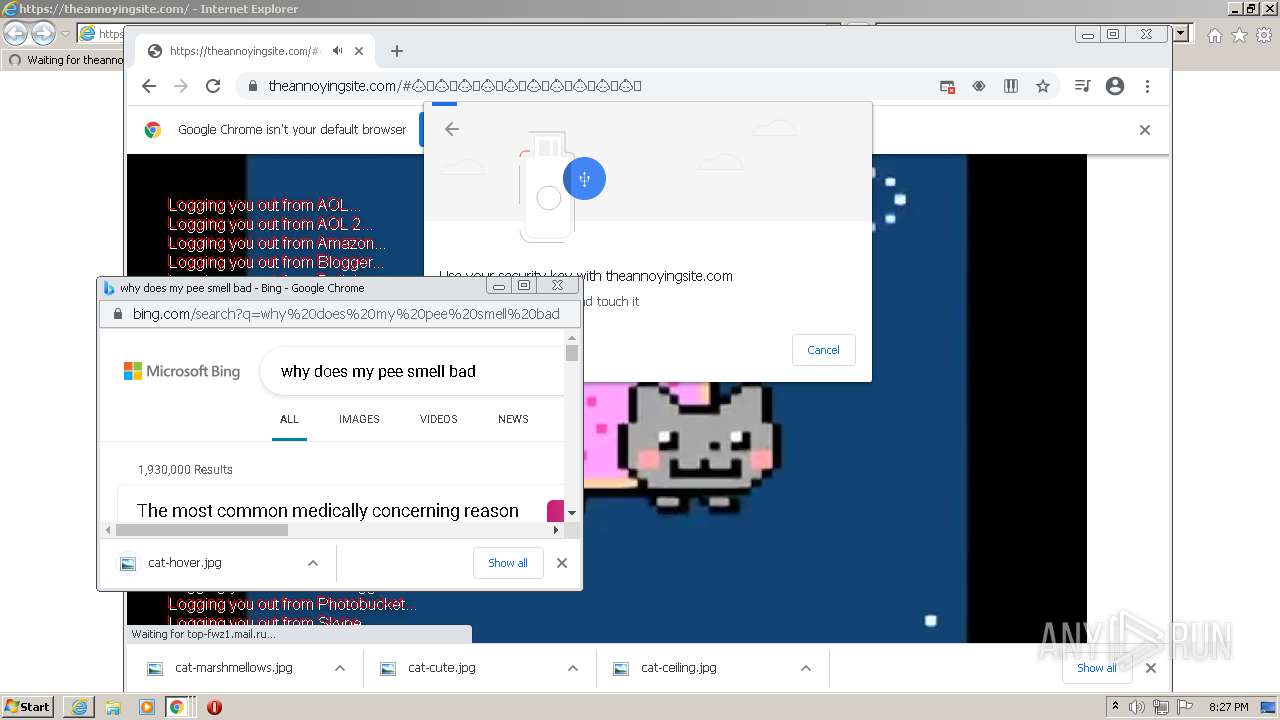
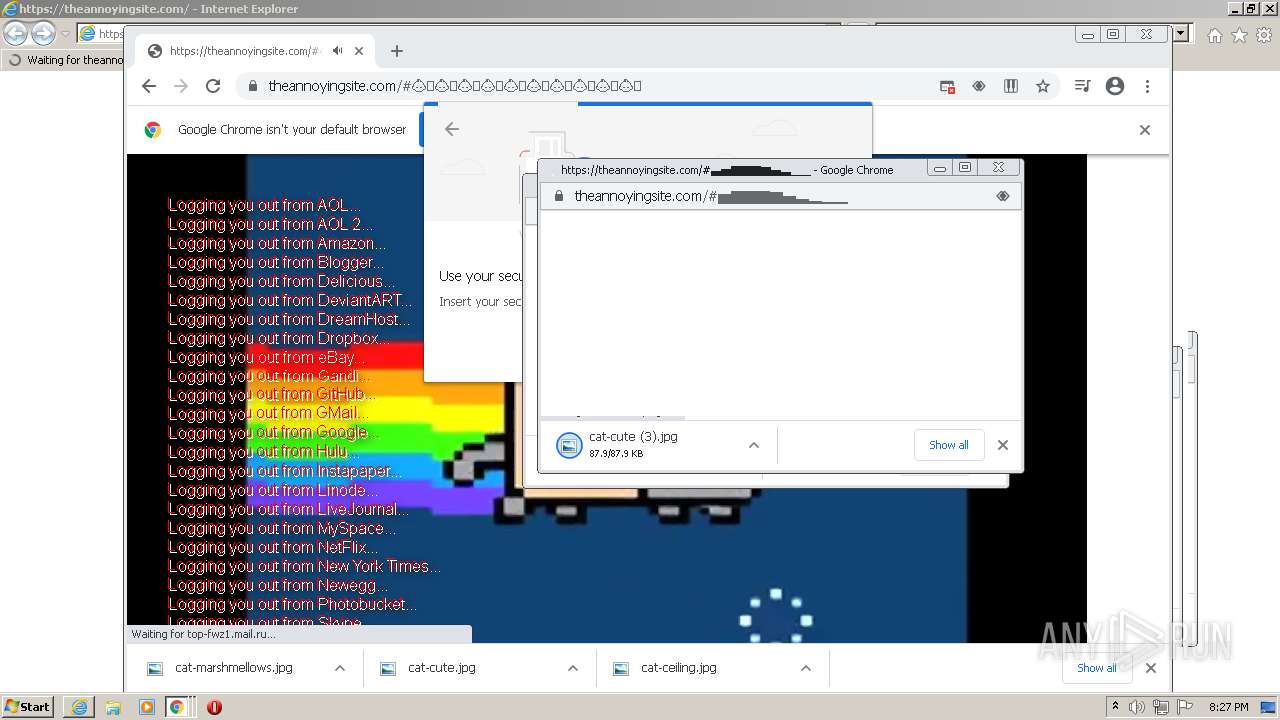
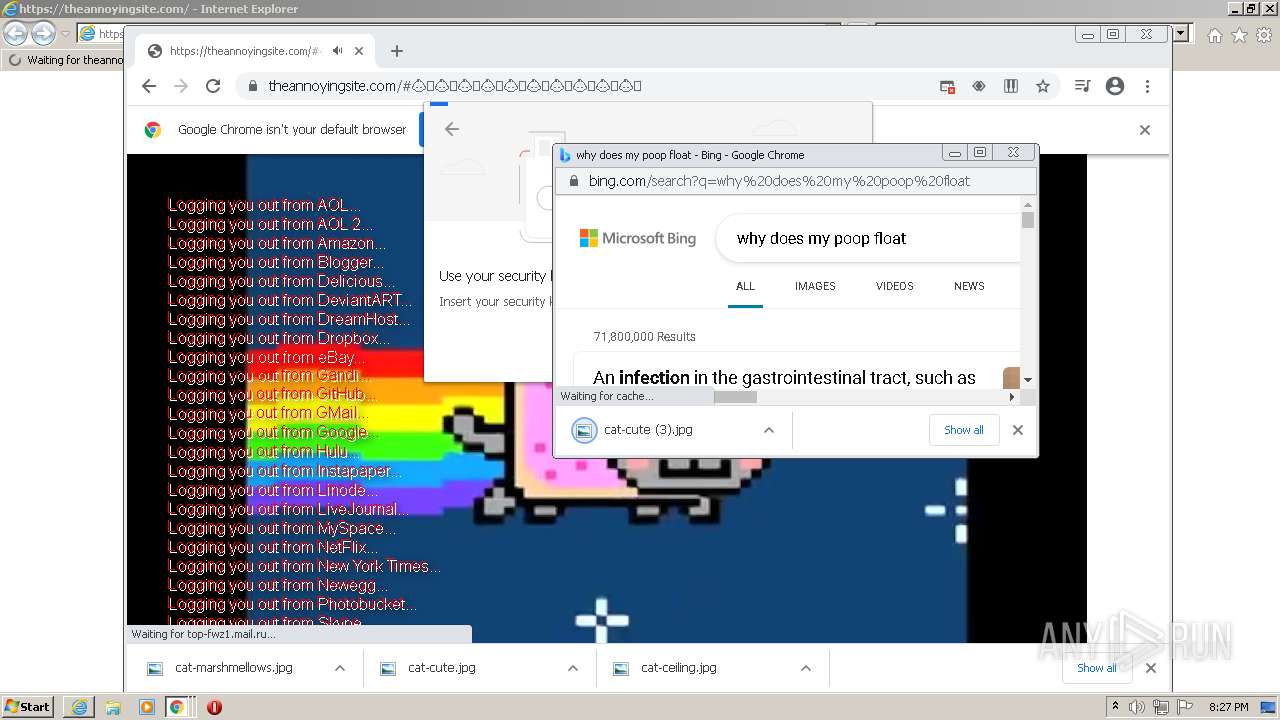
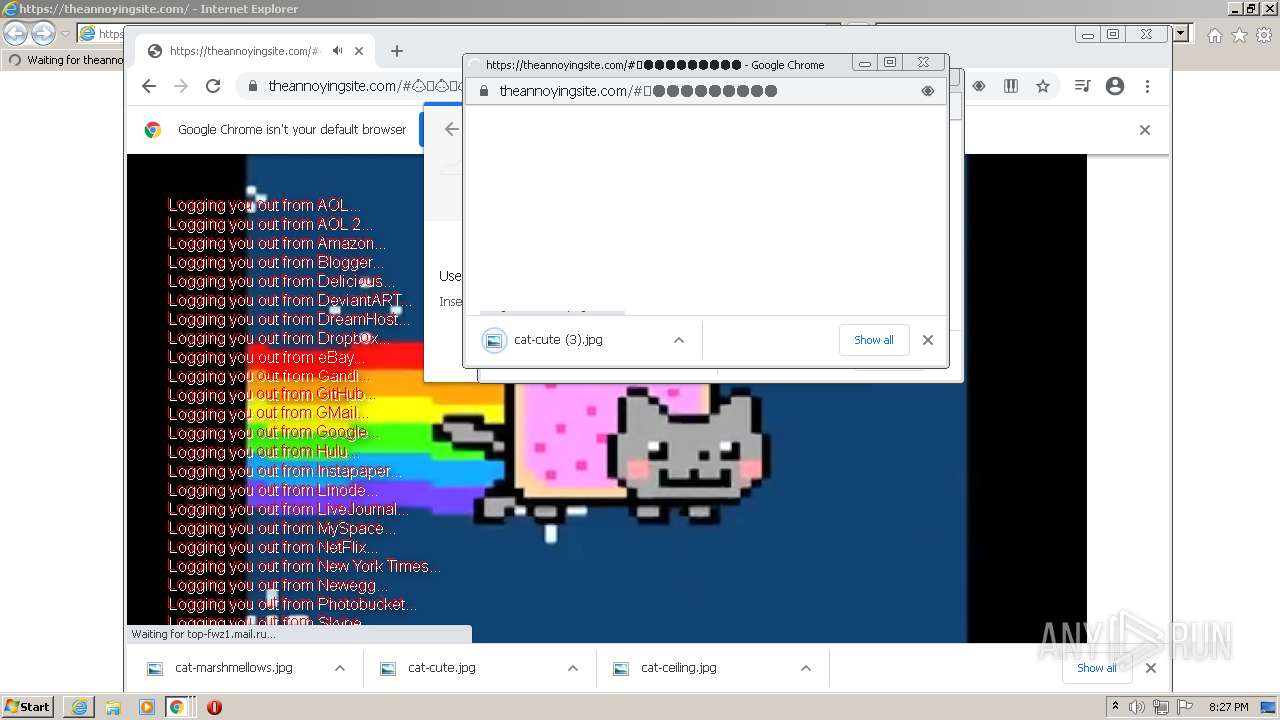
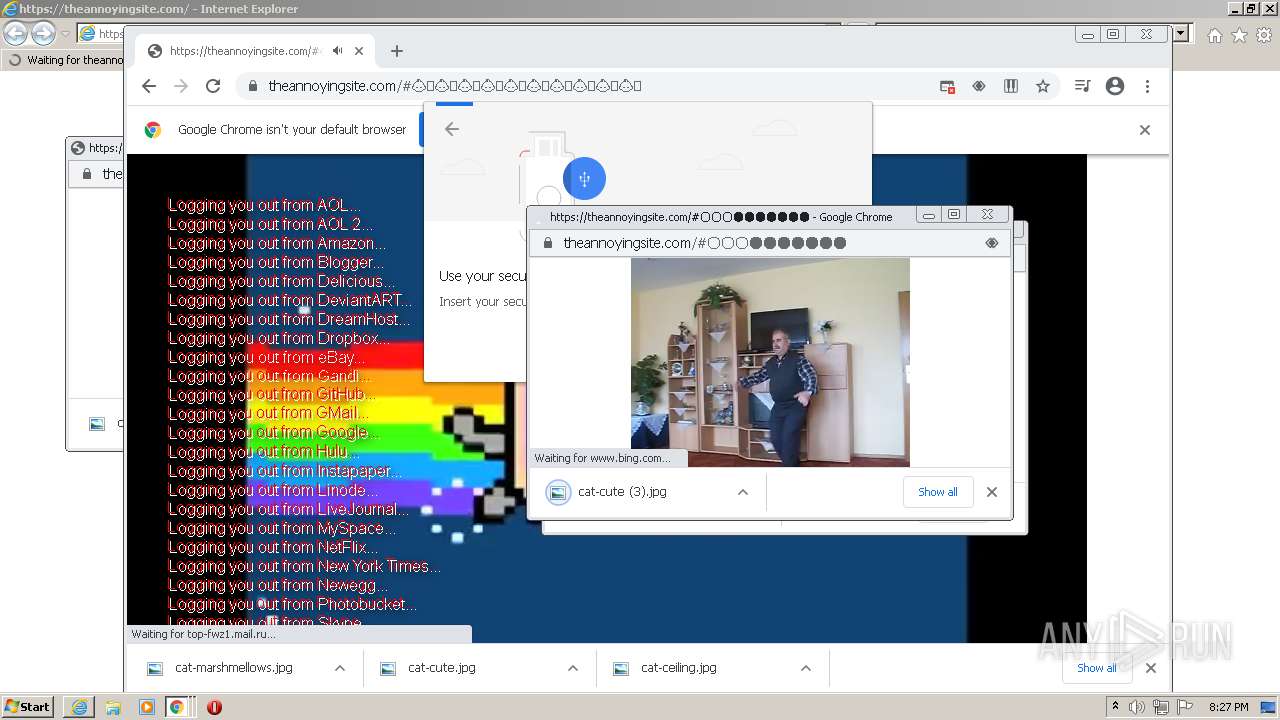
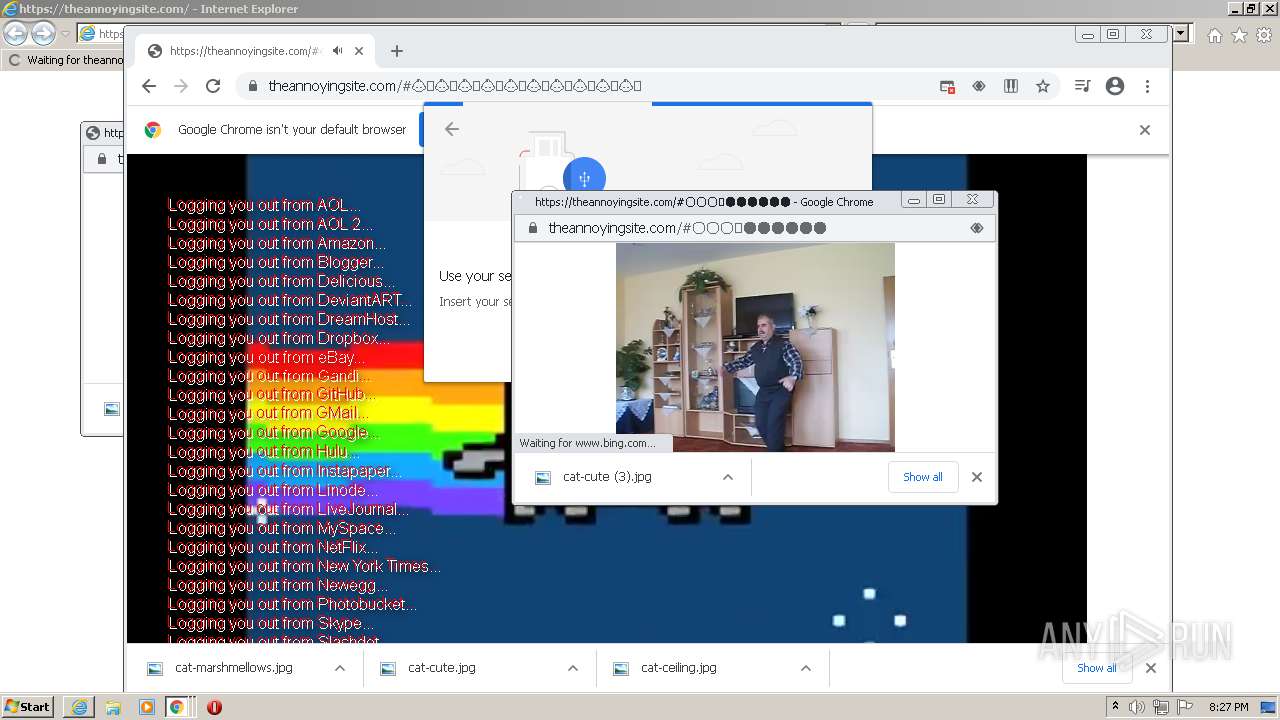
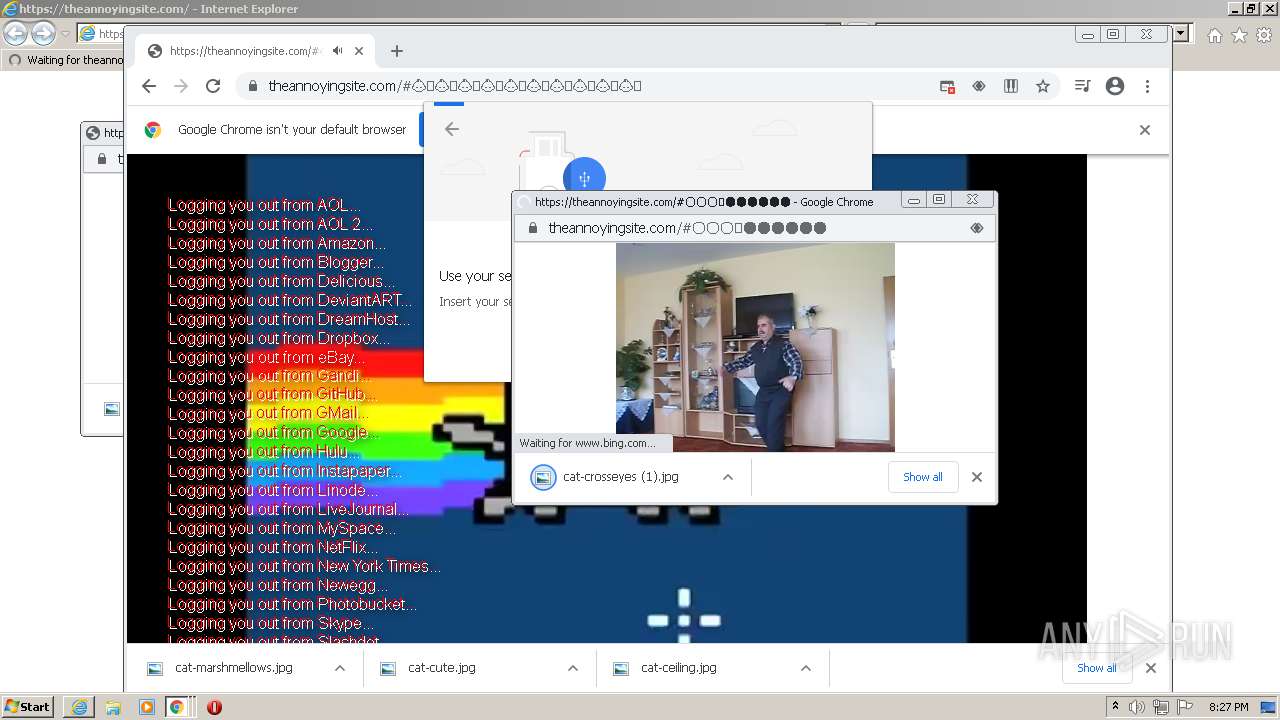
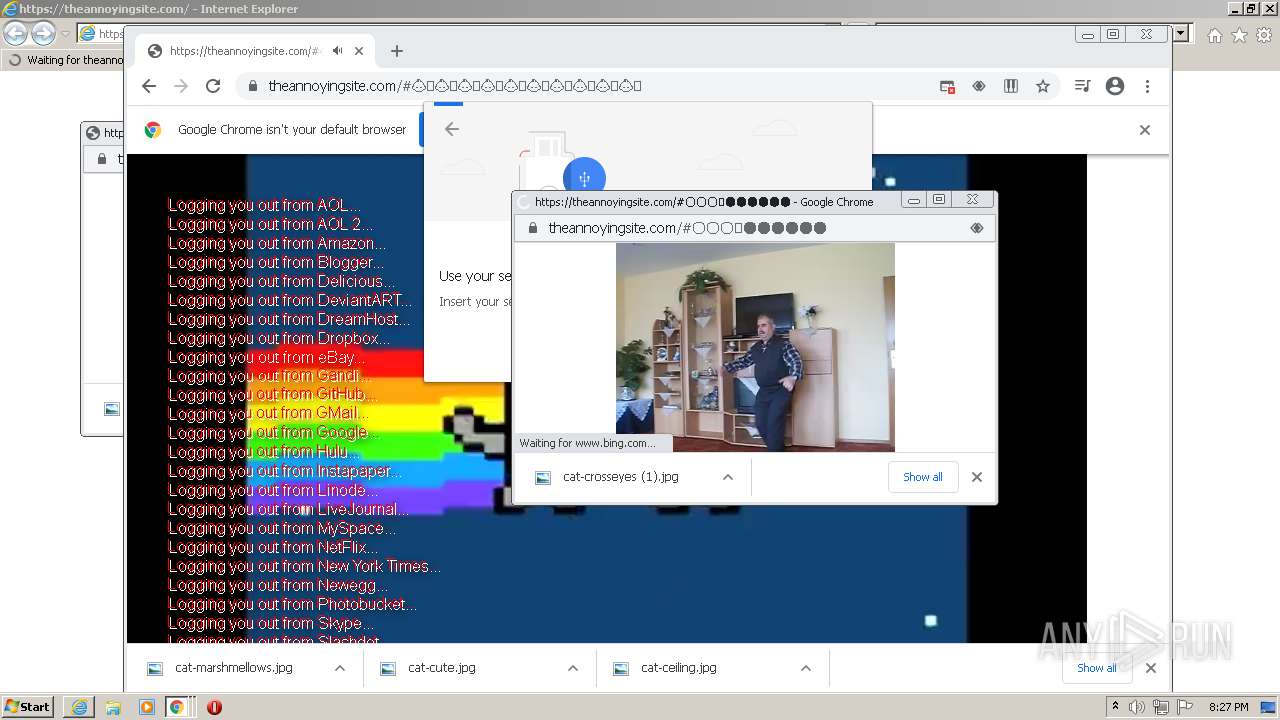
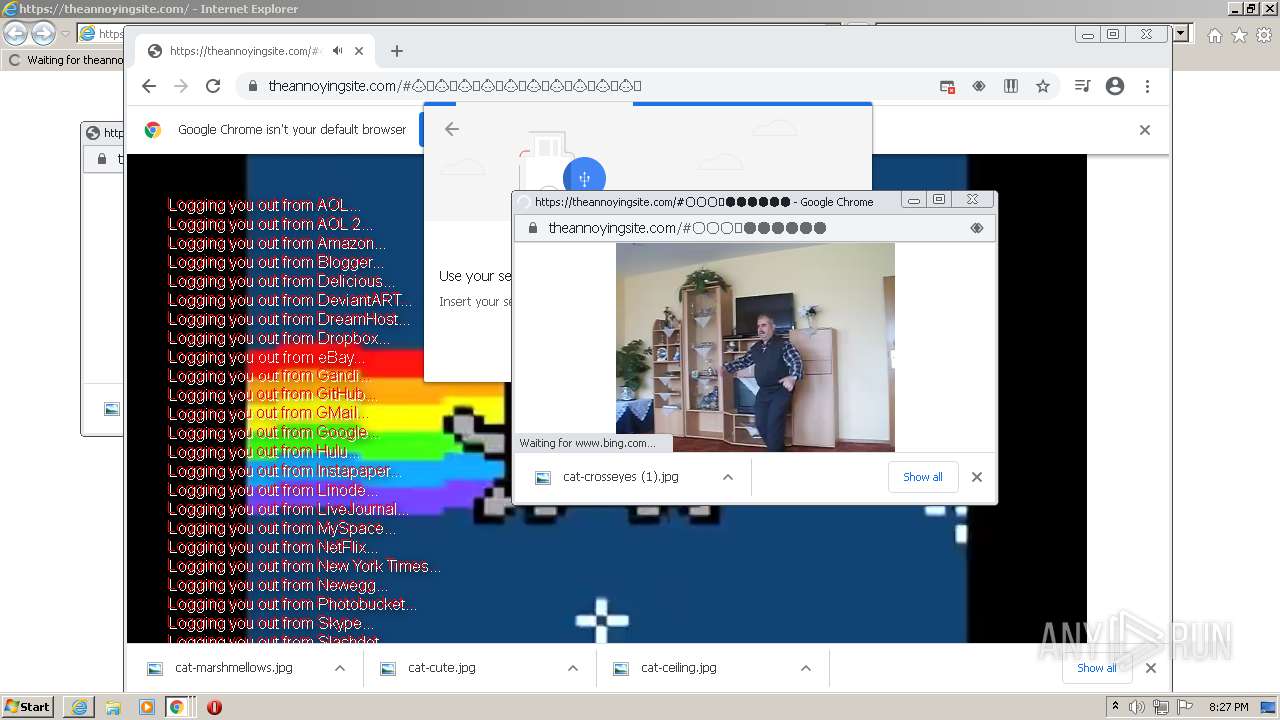
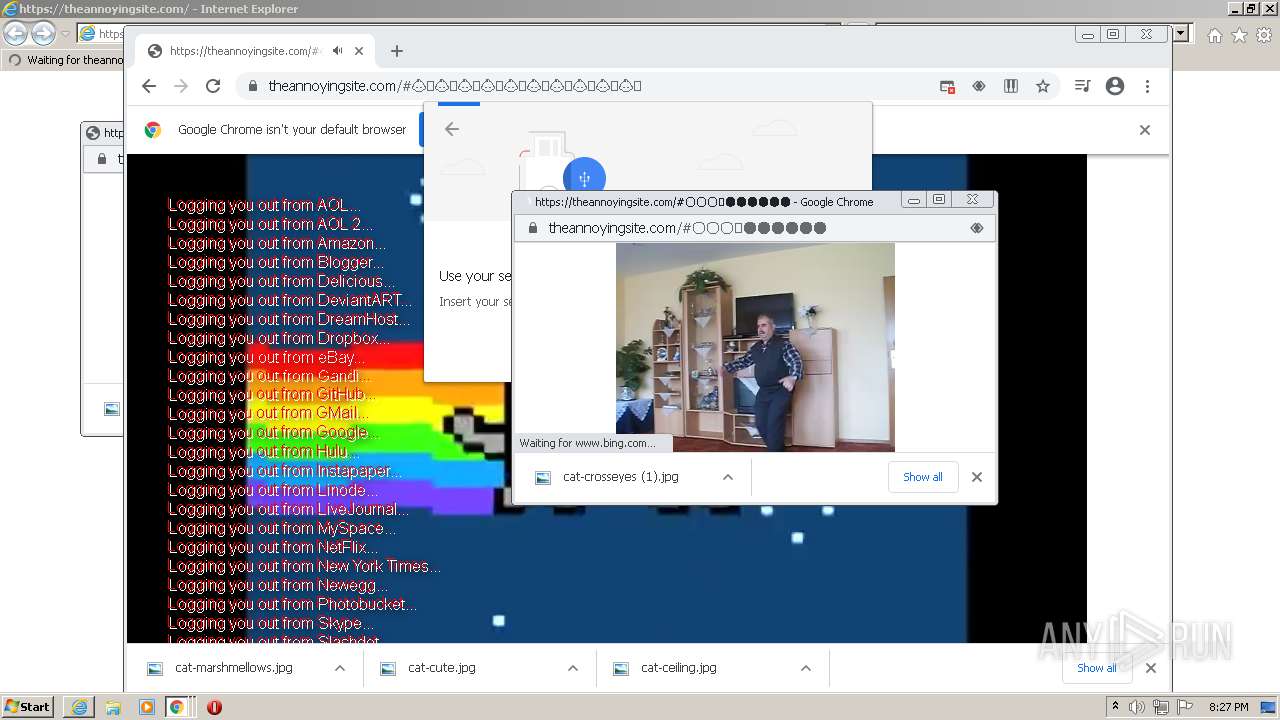
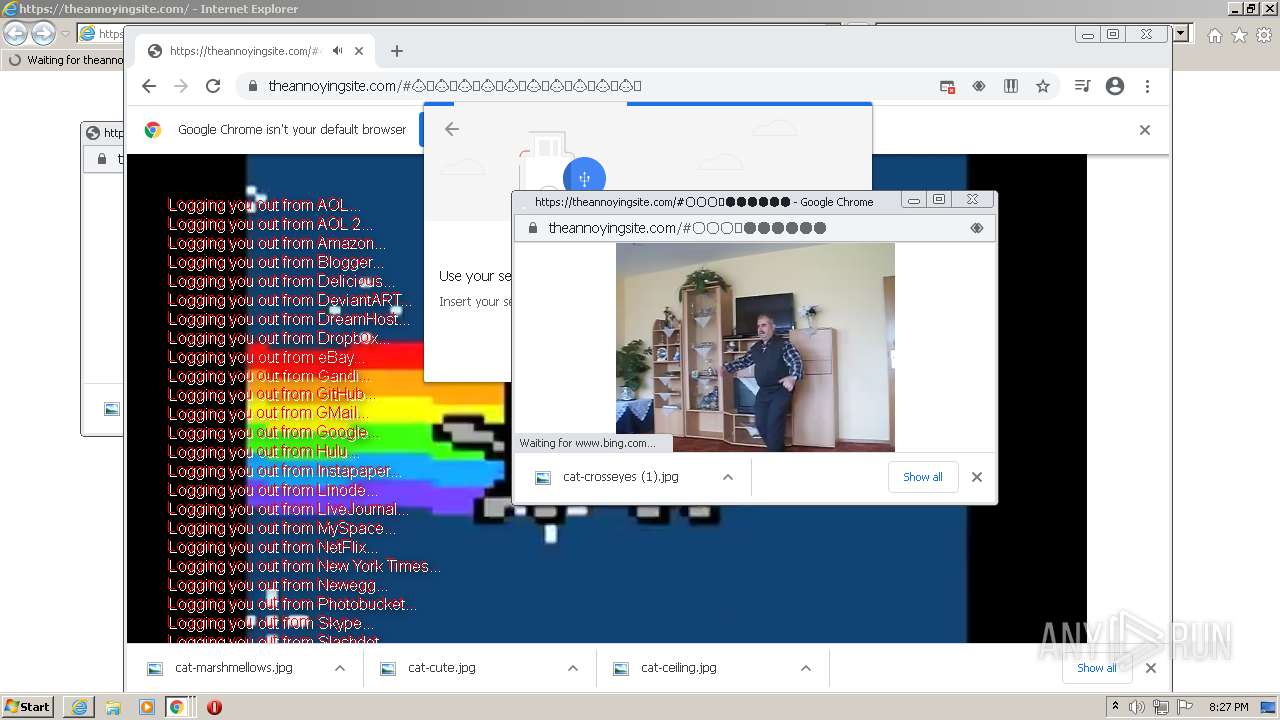
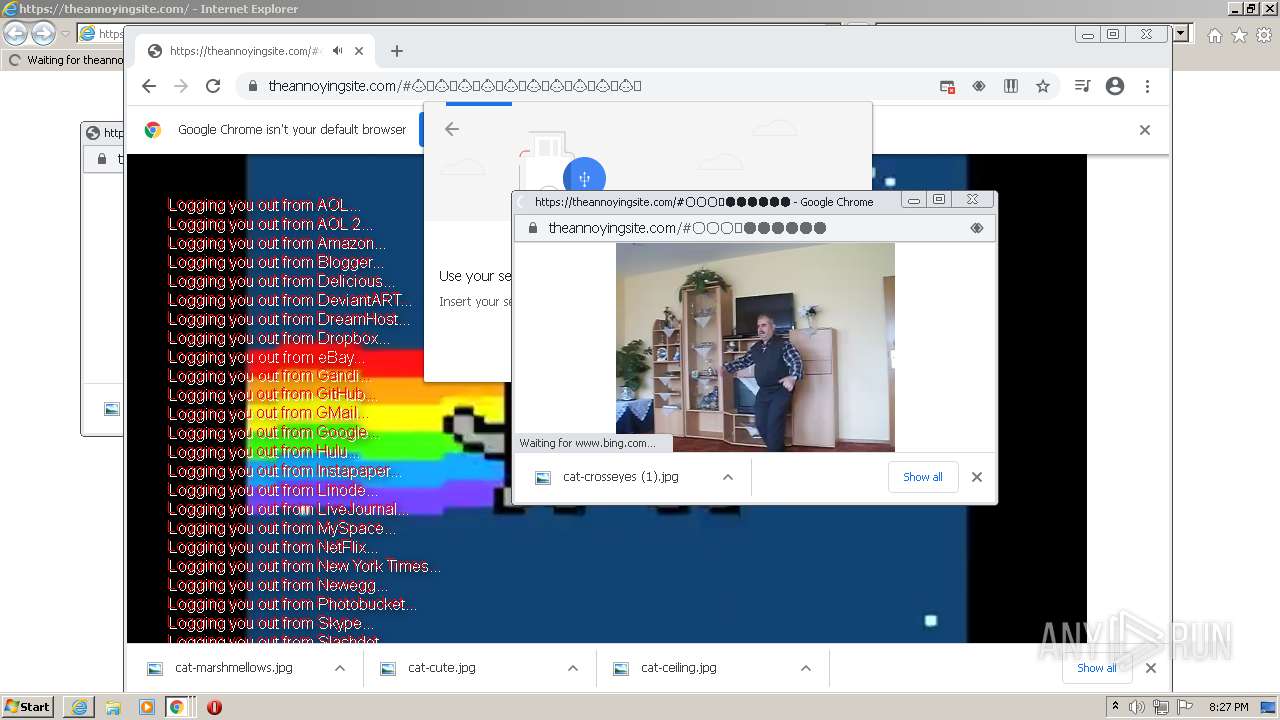
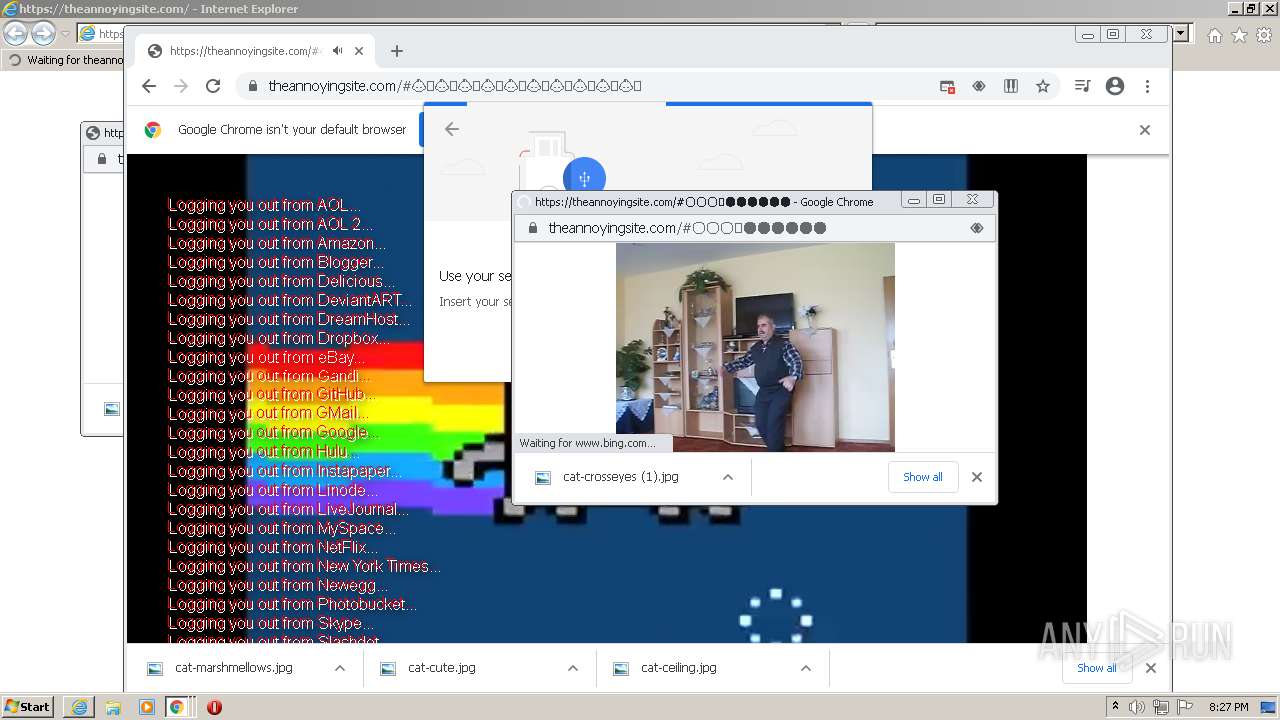
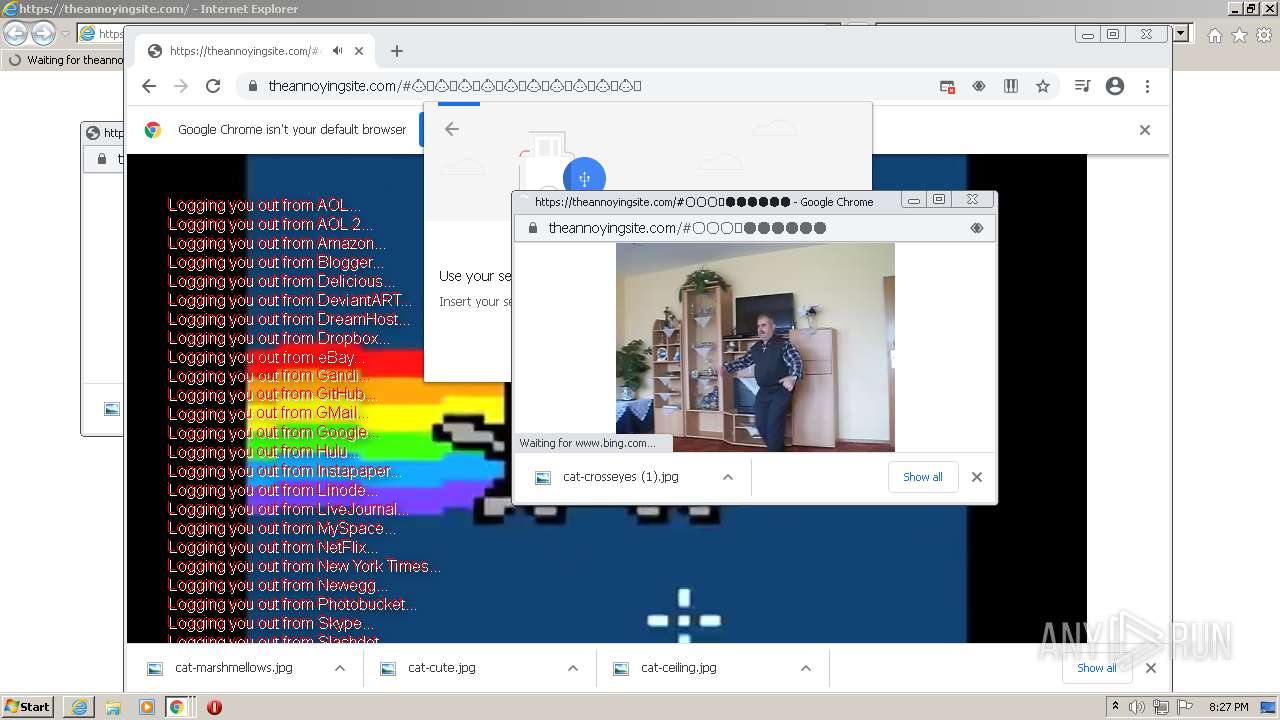
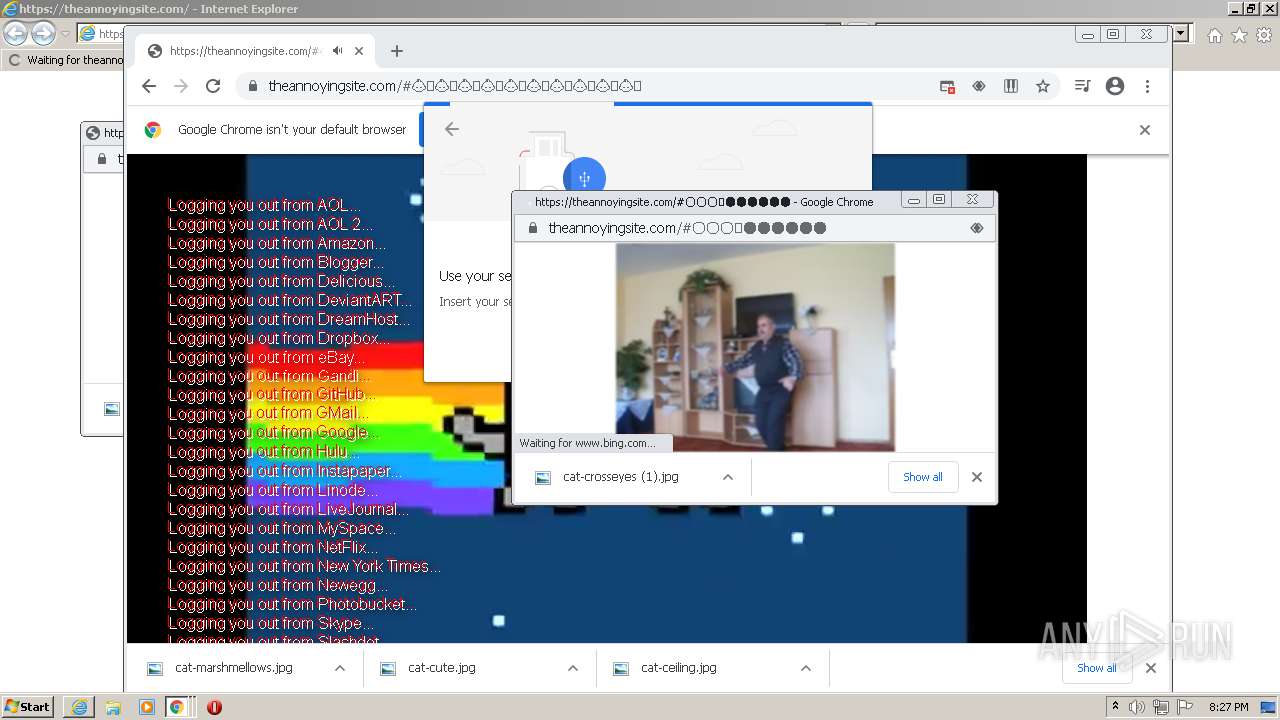
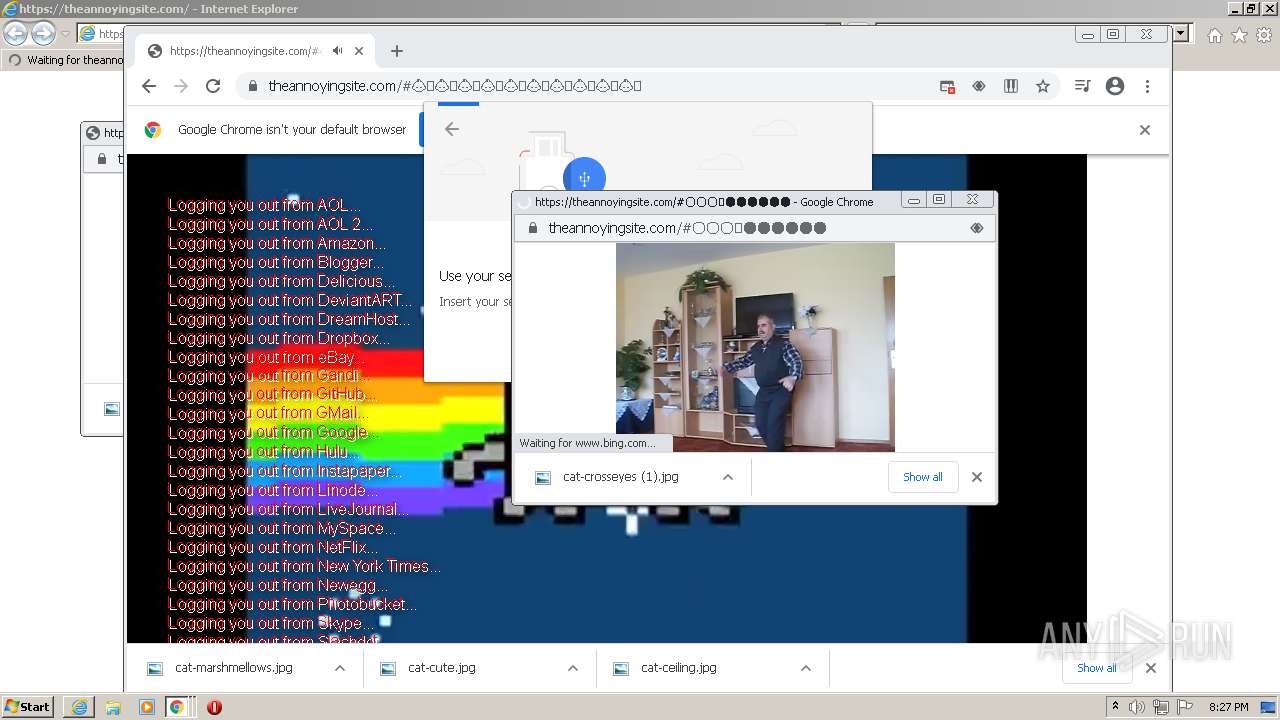
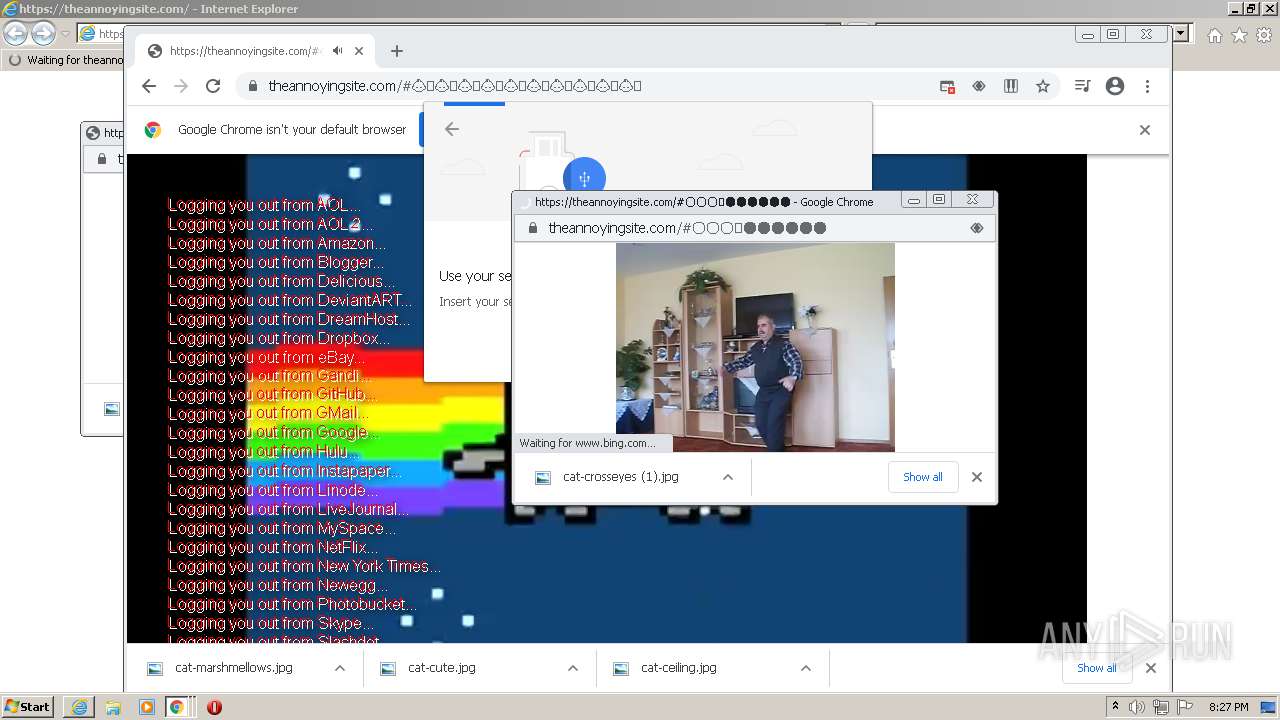
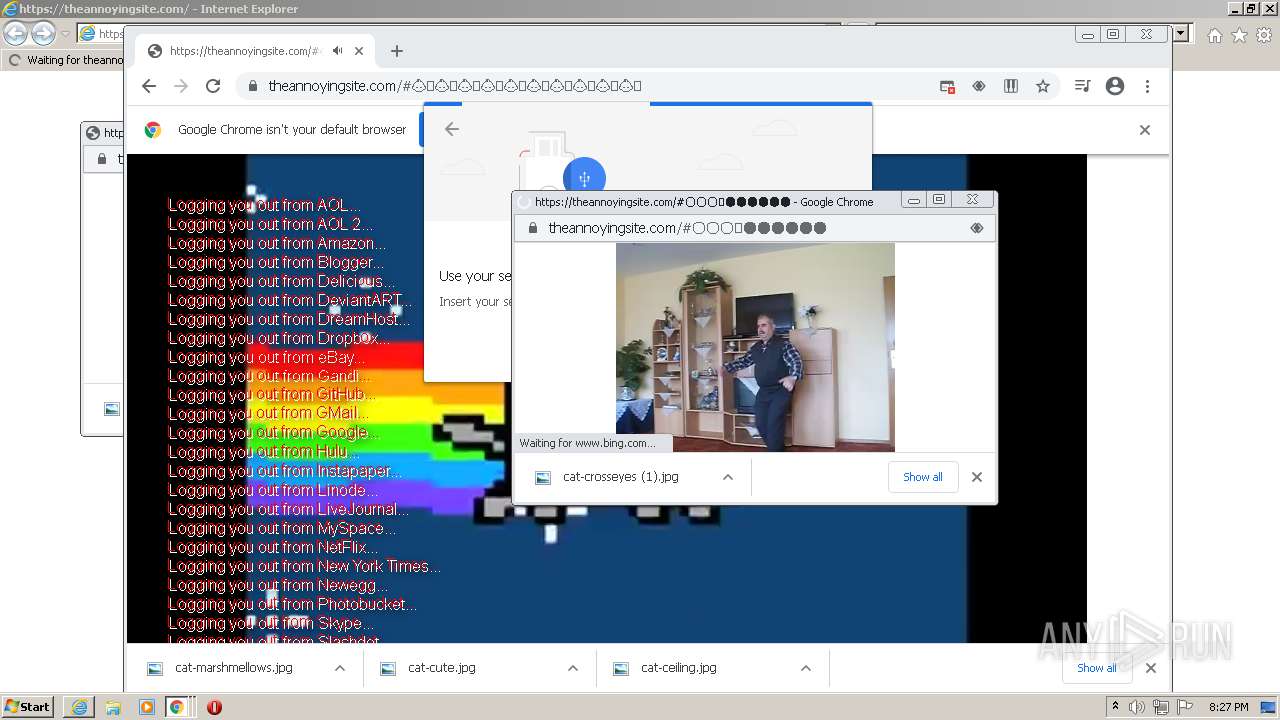
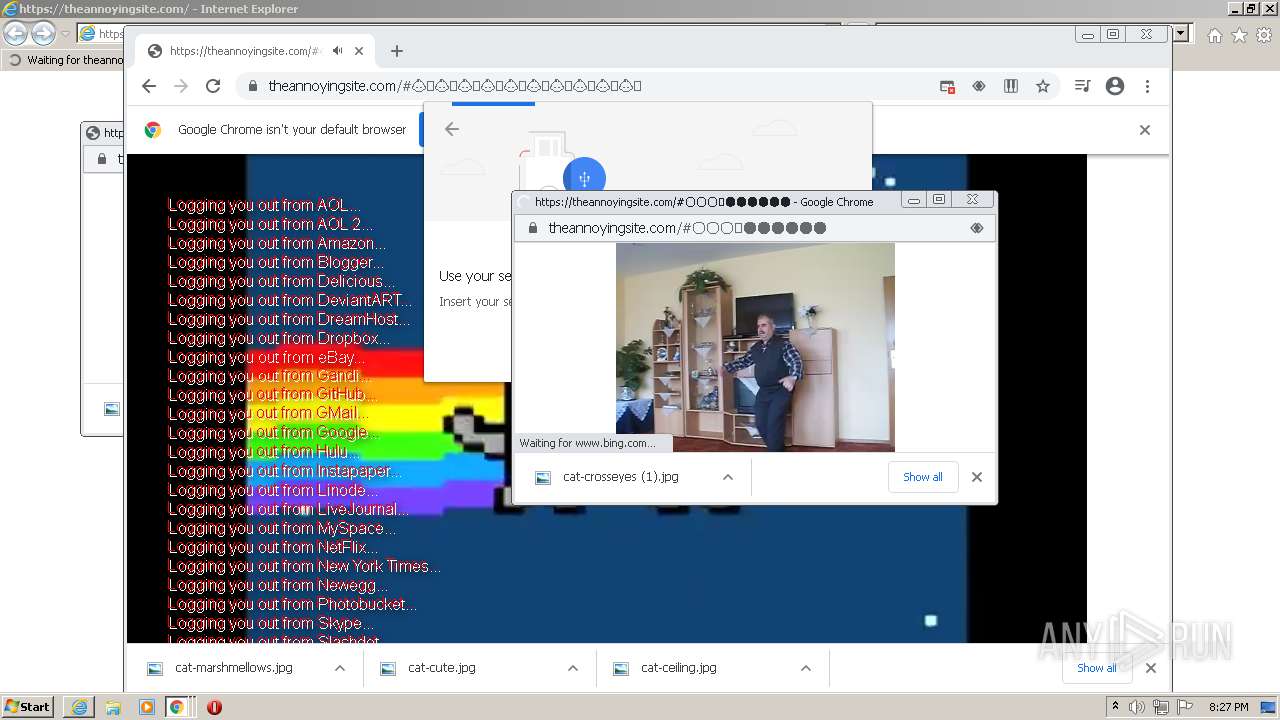
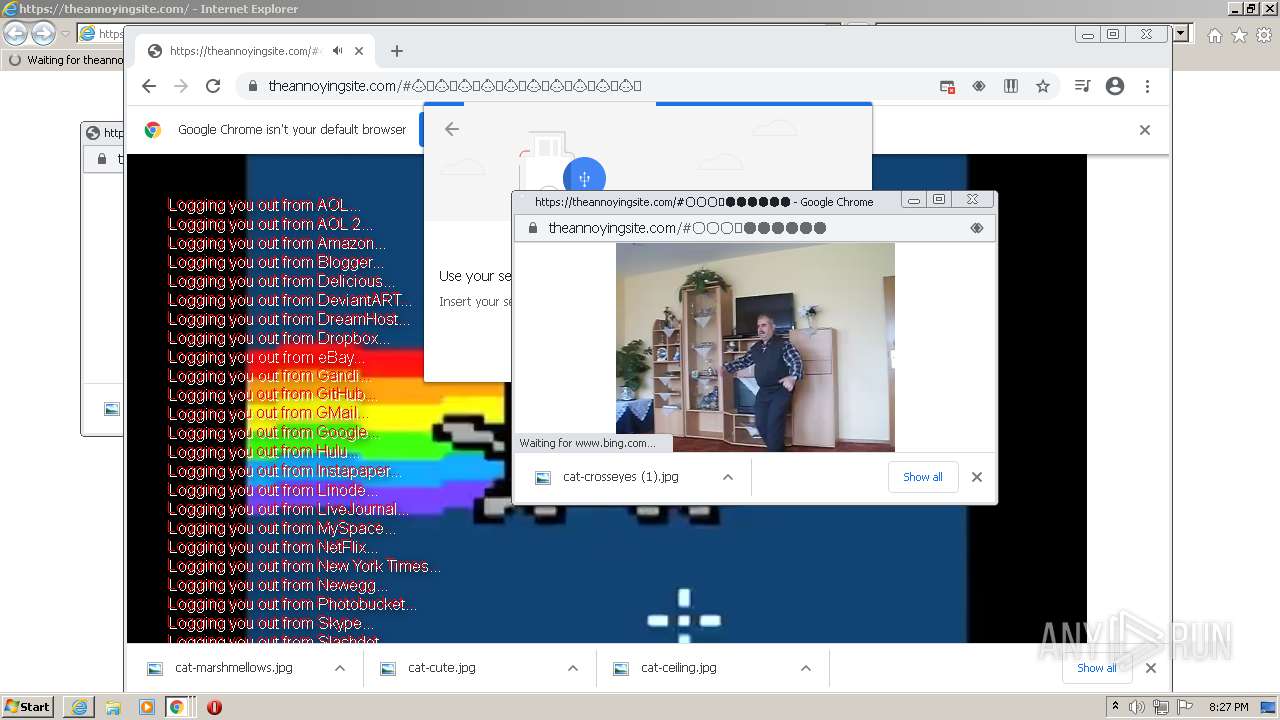
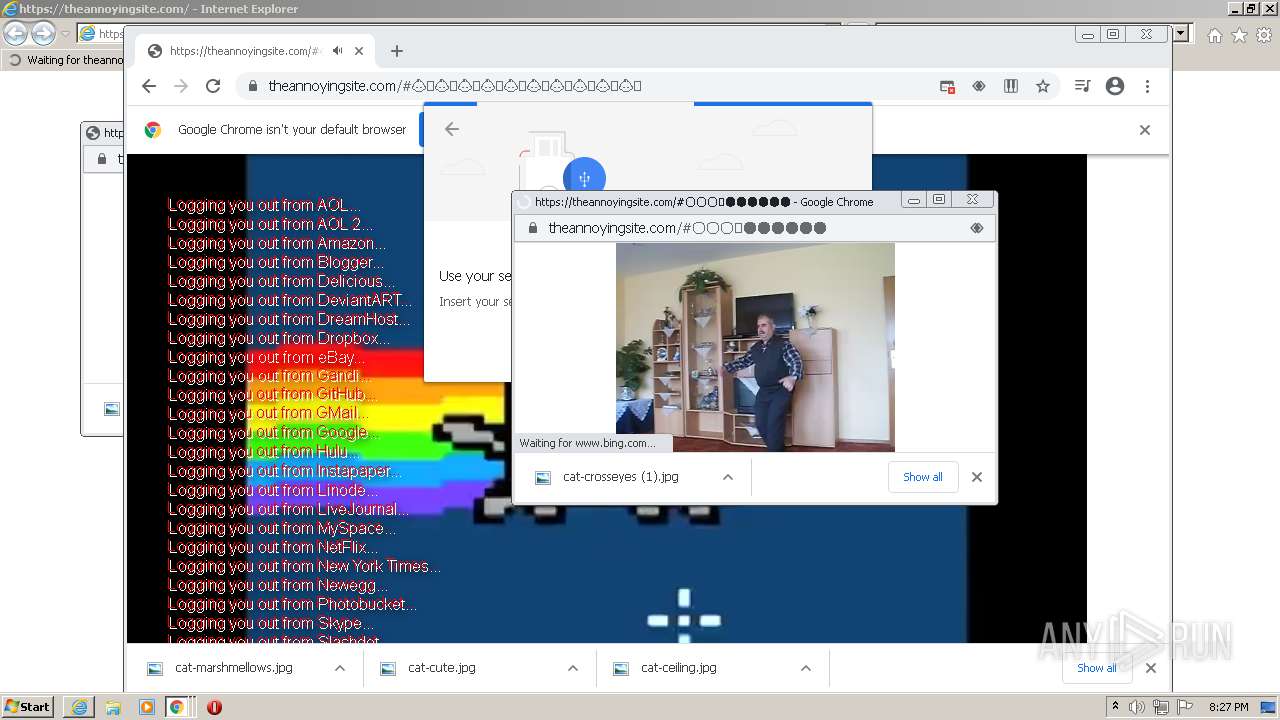
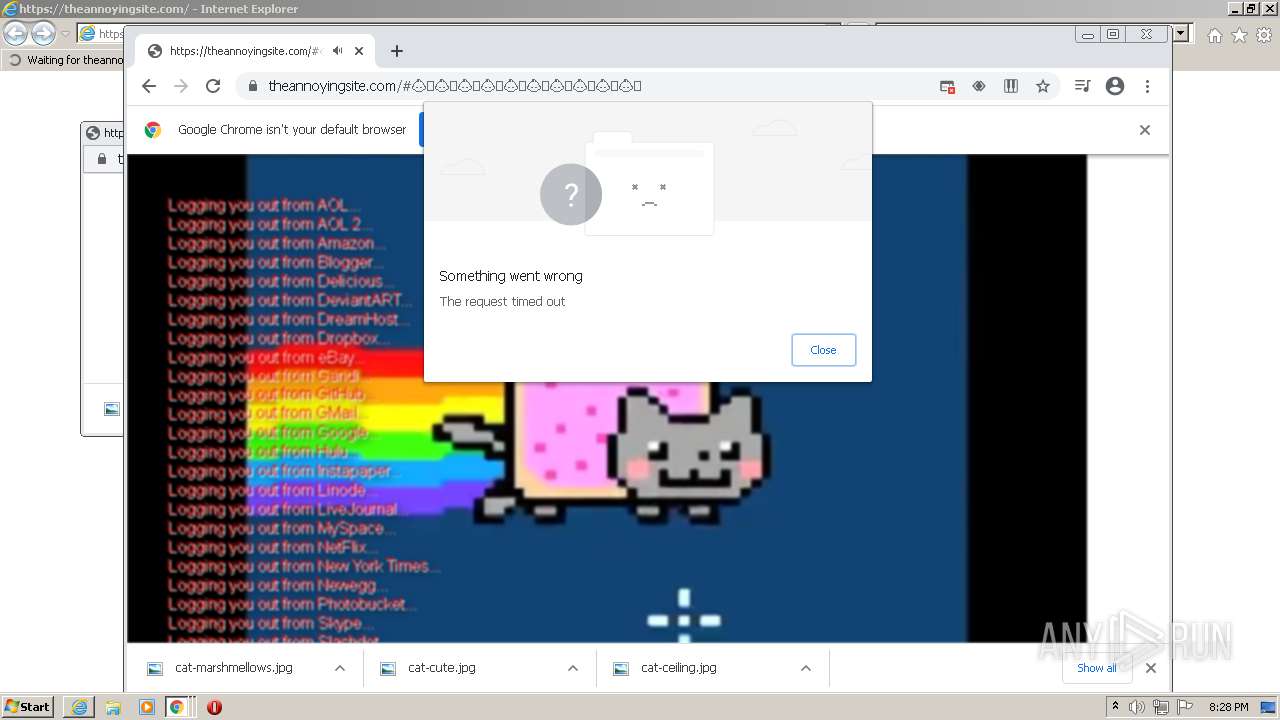
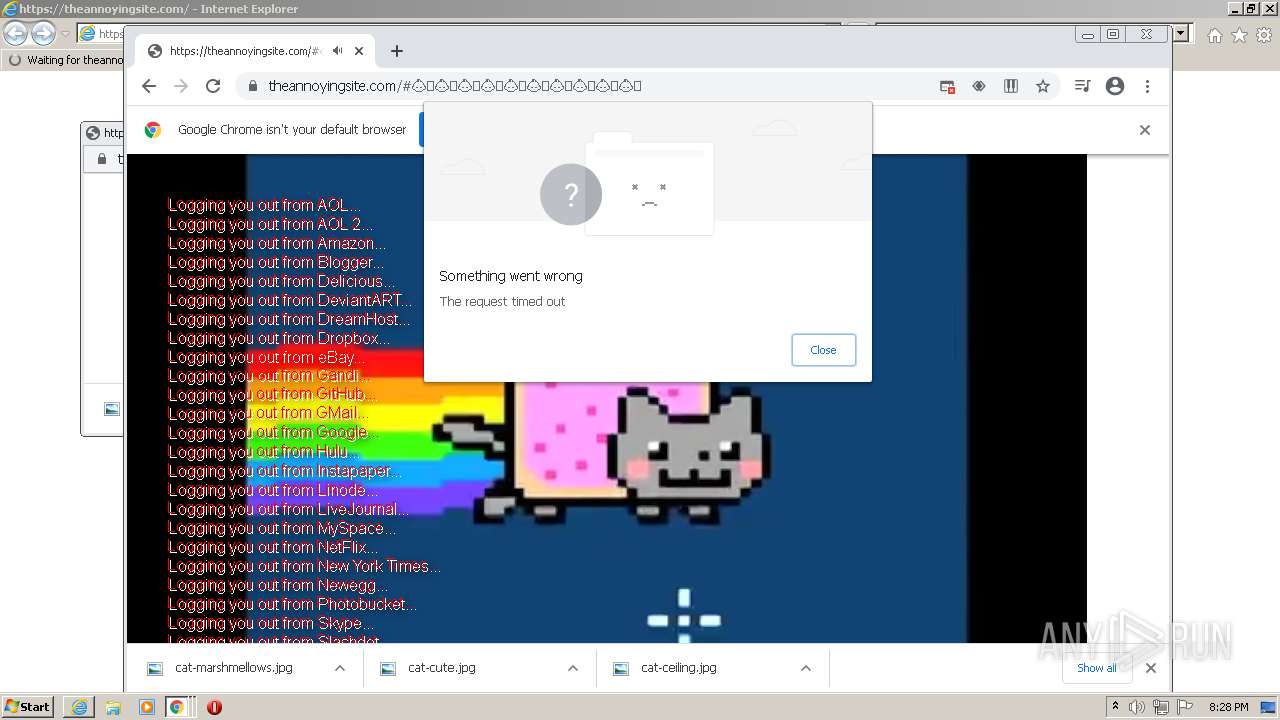
| URL: | https://theannoyingsite.com |
| Full analysis: | https://app.any.run/tasks/6e4f1bb8-dfa7-4532-aba5-1985d70fe69c |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2021, 19:24:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DF8B5A78E1EF8F6C59C1AF036894E0E3 |
| SHA1: | 057824B5D89FF8CC6D6B397D41AFD01FC042406F |
| SHA256: | 192B6241C3D4D25EC551A4FEB4CCEB52E9A690407472A30AA796730727835A0E |
| SSDEEP: | 3:N8FAELjoVyT:2vfR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 724)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3540)
INFO
Checks supported languages
- iexplore.exe (PID: 4036)
- iexplore.exe (PID: 724)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 2884)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 2272)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 464)
- chrome.exe (PID: 356)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 1428)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 732)
- chrome.exe (PID: 356)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 1448)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 1472)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 1204)
- chrome.exe (PID: 3884)
Changes internet zones settings
- iexplore.exe (PID: 4036)
Reads the computer name
- iexplore.exe (PID: 724)
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 356)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 1212)
- chrome.exe (PID: 2520)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 356)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 344)
- chrome.exe (PID: 3816)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 1204)
Reads settings of System Certificates
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 2708)
Creates files in the user directory
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 3540)
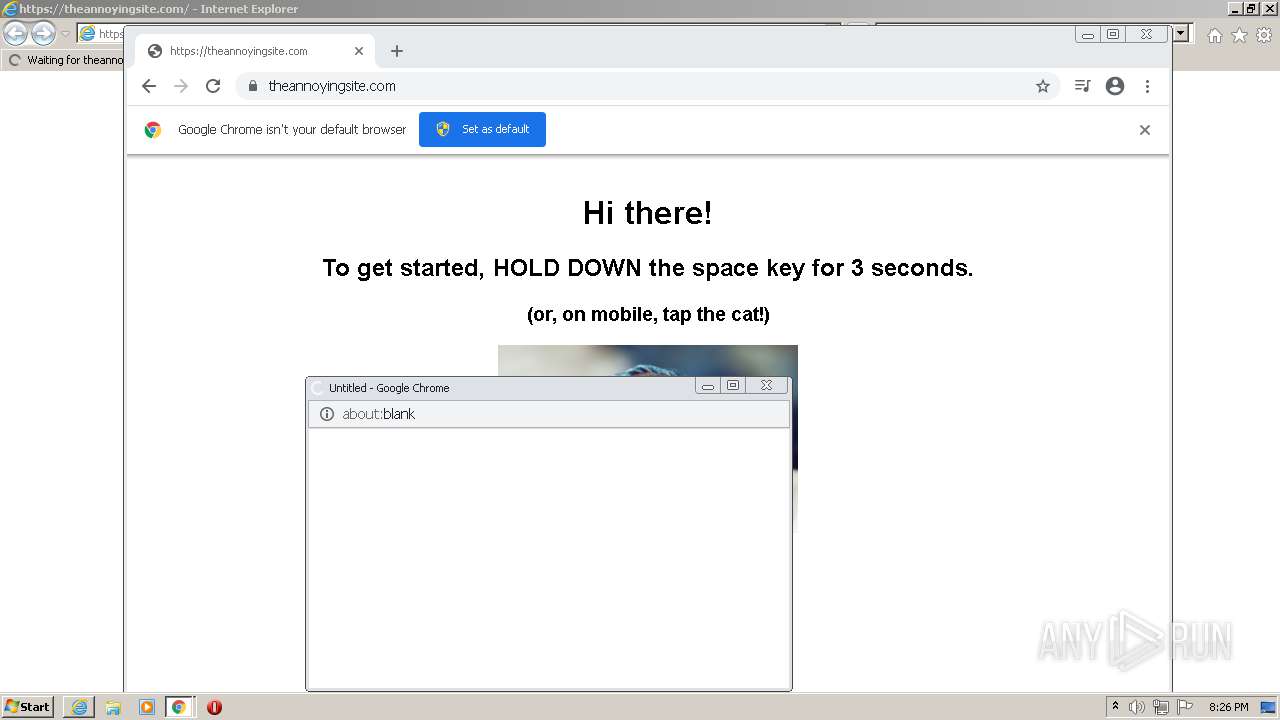
Application launched itself
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 3540)
Checks Windows Trust Settings
- iexplore.exe (PID: 4036)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4036)
Manual execution by user
- chrome.exe (PID: 3540)
Reads internet explorer settings
- iexplore.exe (PID: 724)
Changes settings of System certificates
- iexplore.exe (PID: 4036)
- chrome.exe (PID: 2708)
Reads the hosts file
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2708)
Reads the date of Windows installation
- chrome.exe (PID: 356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
80
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2064 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4036 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=5772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1804 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,3629989662234539370,5336483141080909955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3132 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
54 627
Read events
54 061
Write events
562
Delete events
4
Modification events
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902831 | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902831 | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4036) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
171
Text files
347
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\WF6QO6LH.txt | text | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-610C3B42-DD4.pma | — | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6C53.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
182
DNS requests
148
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
896 | svchost.exe | HEAD | 200 | 173.194.150.220:80 | http://r6---sn-5goeen7r.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=157.97.120.10&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1628191458&mv=m&mvi=6&pl=24&rmhost=r2---sn-5goeen7r.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
896 | svchost.exe | HEAD | 200 | 173.194.150.186:80 | http://r4---sn-5goeen7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=Yu&mip=157.97.120.10&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1628191458&mv=m&mvi=4&pl=24&rmhost=r3---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r3---sn-5goeen7r.gvt1.com | US | — | — | whitelisted |
896 | svchost.exe | HEAD | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
4036 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2708 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
4036 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
4036 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
896 | svchost.exe | GET | 200 | 173.194.150.186:80 | http://r4---sn-5goeen7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx?cms_redirect=yes&mh=Yu&mip=157.97.120.10&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1628190981&mv=m&mvi=4&pl=24&rmhost=r3---sn-5goeen7d.gvt1.com&shardbypass=yes&smhost=r3---sn-5goeen7r.gvt1.com | US | crx | 2.85 Kb | whitelisted |
2708 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
4036 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
724 | iexplore.exe | 50.116.11.184:443 | theannoyingsite.com | Linode, LLC | US | suspicious |
4036 | iexplore.exe | 205.185.216.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
4036 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
4036 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4036 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
4036 | iexplore.exe | 205.185.216.10:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2708 | chrome.exe | 142.250.185.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4036 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
4036 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4036 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
theannoyingsite.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2708 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2708 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM bad window update |
2708 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |