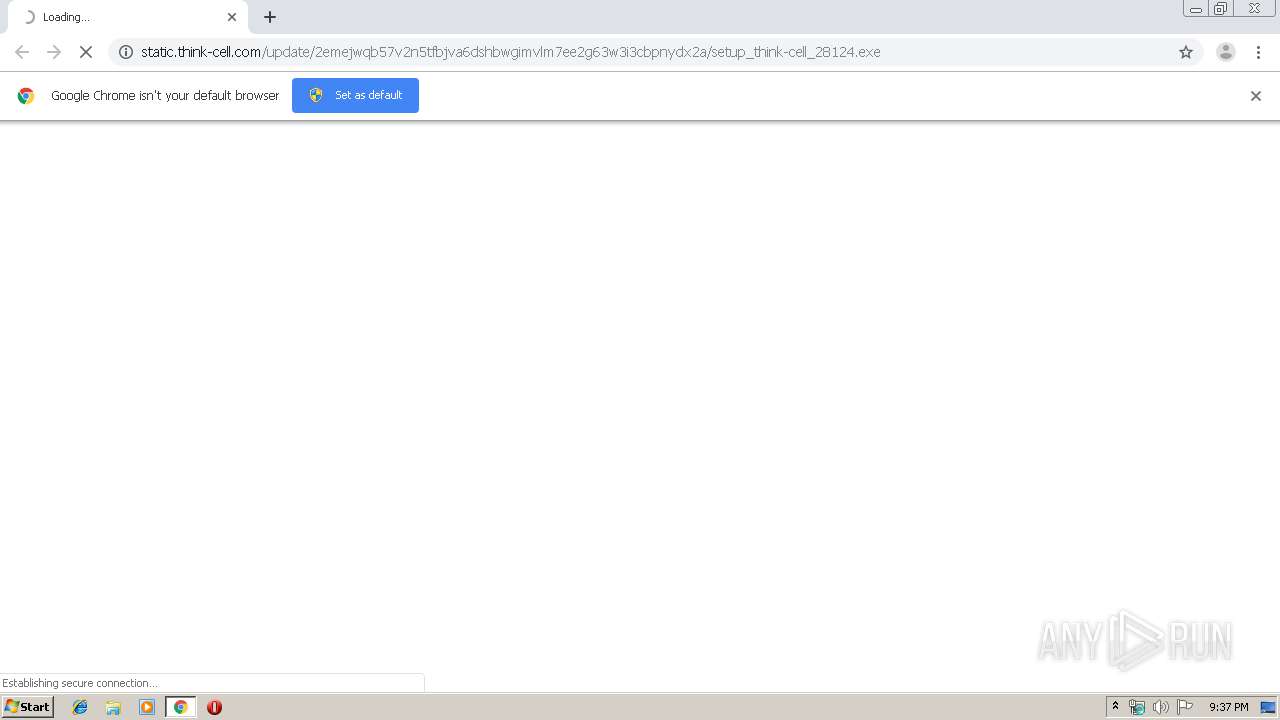
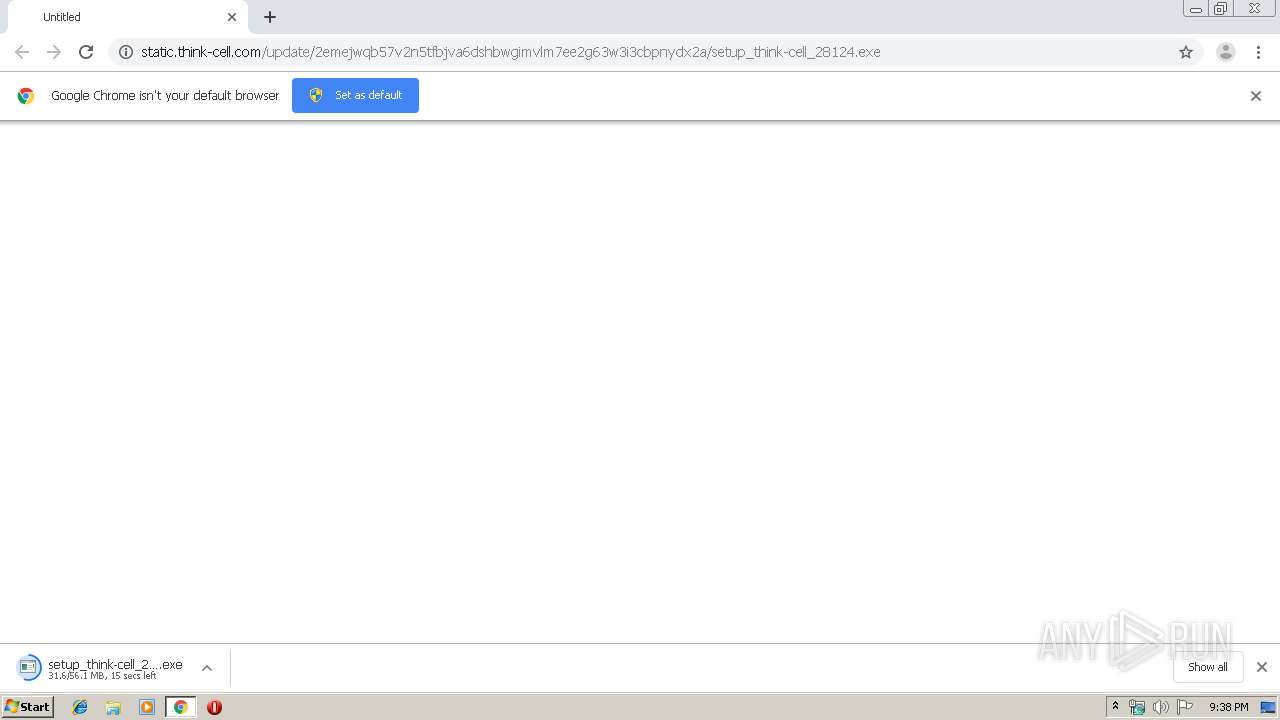
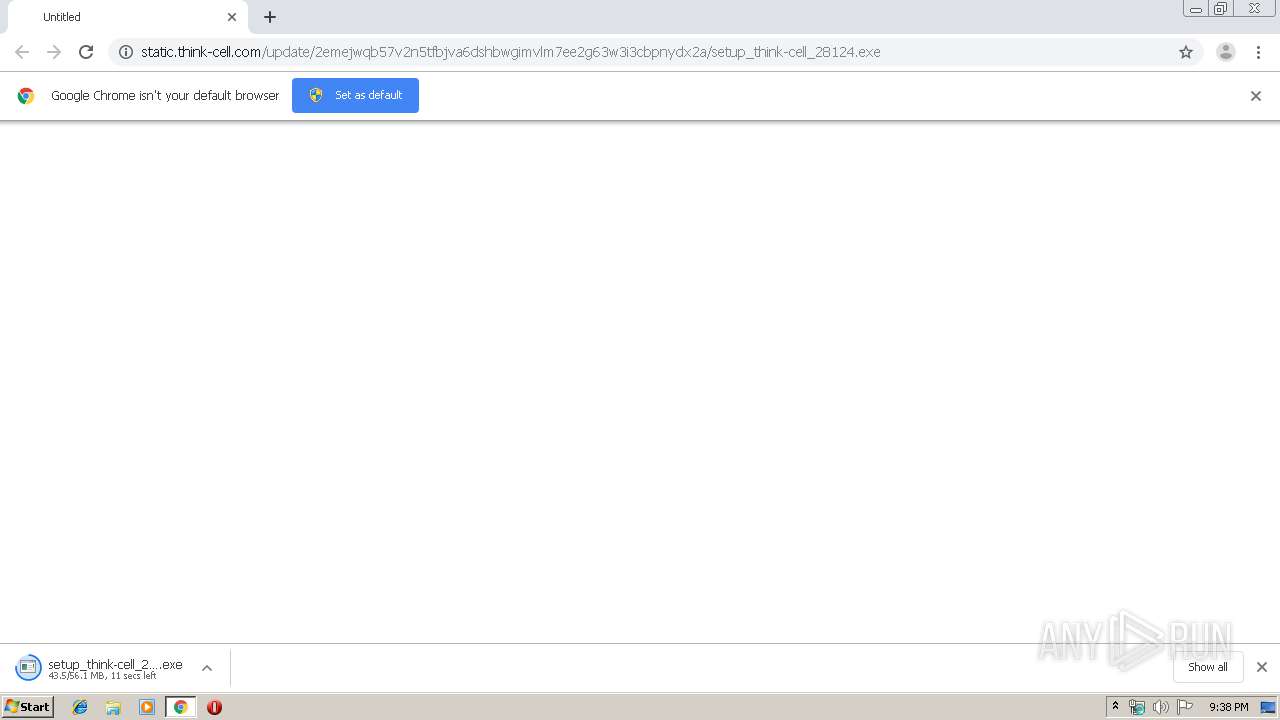
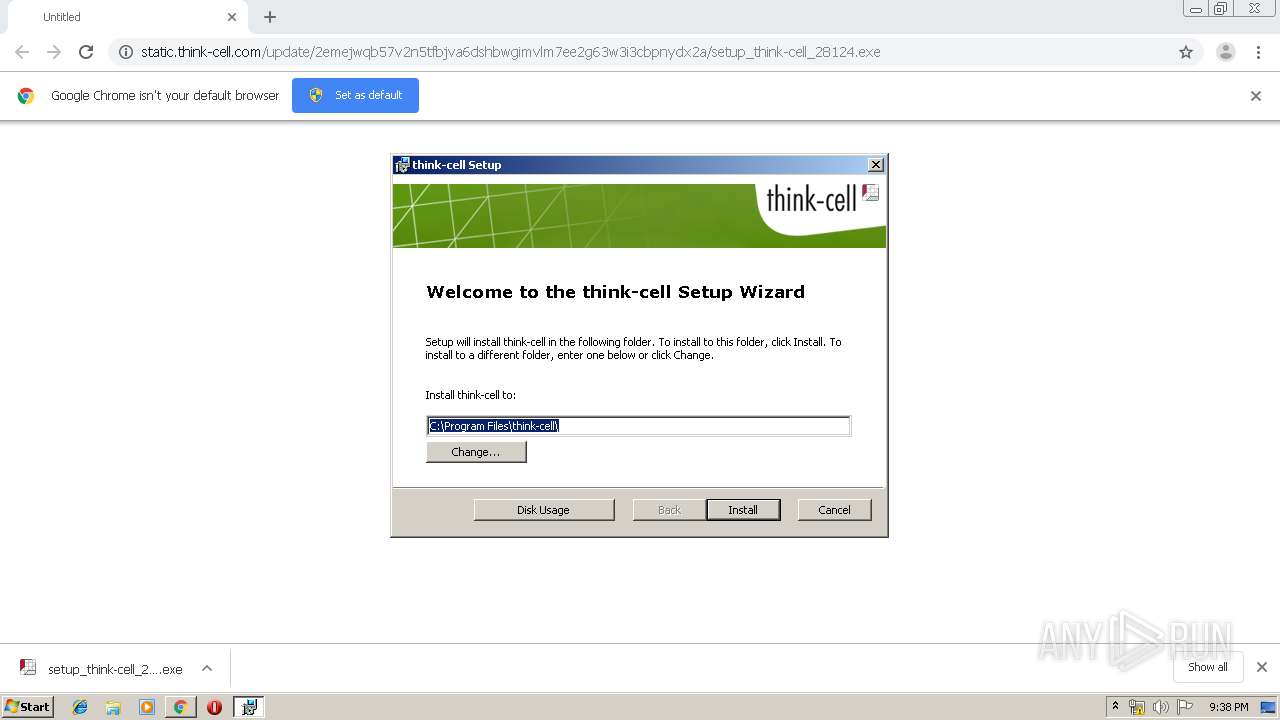
| URL: | http://static.think-cell.com/update/2emejwqb57v2n5tfbjva6dshbwgimvlm7ee2g63w3i3cbpnydx2a/setup_think-cell_28124.exe |
| Full analysis: | https://app.any.run/tasks/a2aed7eb-4249-4475-94c4-0b5e958b3147 |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 21:37:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D0F19C4E53AC97199C9632E0C3CA5690 |
| SHA1: | 48DB4551A438510F51B4BB34CF643209F01DF5D0 |
| SHA256: | 19272416181E39EF7BC62783B7CE507E168EACBADC48600AC3CDEDECFD16D28D |
| SSDEEP: | 3:N1KNRwLrMLGArGTLQmMtAPTobRNHSCJTFQzHQjWpQrKOIGAaAR0C:CirzQ1tAPkrHTBQrQjWxnKAR0C |
MALICIOUS
Application was dropped or rewritten from another process
- setup_think-cell_28124.exe (PID: 2492)
- setup_think-cell_28124.exe (PID: 3356)
- tcupdate.exe (PID: 2768)
- tcasr.exe (PID: 3524)
- tcupdate.exe (PID: 2648)
- tcupdate.exe (PID: 2376)
Changes settings of System certificates
- MSIEXEC.EXE (PID: 2996)
Loads dropped or rewritten executable
- POWERPNT.EXE (PID: 2880)
SUSPICIOUS
Application launched itself
- setup_think-cell_28124.exe (PID: 2492)
Executable content was dropped or overwritten
- chrome.exe (PID: 2040)
- msiexec.exe (PID: 2576)
Adds / modifies Windows certificates
- MSIEXEC.EXE (PID: 2996)
Executed as Windows Service
- vssvc.exe (PID: 3368)
- tcupdate.exe (PID: 2768)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2576)
Creates COM task schedule object
- msiexec.exe (PID: 2576)
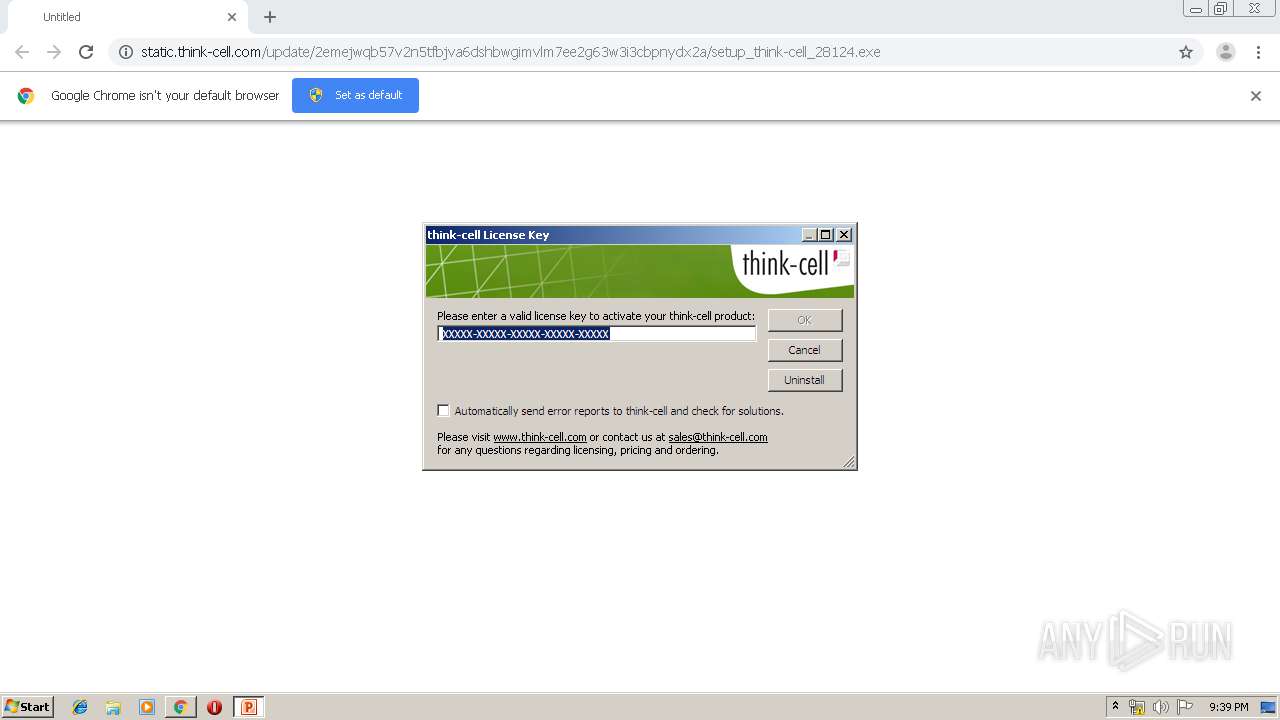
Starts Microsoft Office Application
- setup_think-cell_28124.exe (PID: 2492)
Checks supported languages
- POWERPNT.EXE (PID: 2880)
Executed via COM
- tcasr.exe (PID: 3524)
Starts Microsoft Installer
- setup_think-cell_28124.exe (PID: 3356)
Creates files in the Windows directory
- tcupdate.exe (PID: 2376)
INFO
Reads the hosts file
- chrome.exe (PID: 2040)
- chrome.exe (PID: 4016)
Application launched itself
- chrome.exe (PID: 2040)
- msiexec.exe (PID: 2576)
Reads Internet Cache Settings
- chrome.exe (PID: 2040)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3368)
Creates a software uninstall entry
- msiexec.exe (PID: 2576)
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2880)
Searches for installed software
- msiexec.exe (PID: 2576)
Creates files in the program directory
- msiexec.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
23
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11387300869567014142 --mojo-platform-channel-handle=3460 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16114352841465016934 --mojo-platform-channel-handle=2968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=896 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://static.think-cell.com/update/2emejwqb57v2n5tfbjva6dshbwgimvlm7ee2g63w3i3cbpnydx2a/setup_think-cell_28124.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | C:\Windows\system32\MsiExec.exe -Embedding 38D049BBBAC757D9765382A72252DBF3 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8505653349555599295 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3827487132798772863 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\think-cell\tcupdate.exe" "BHZQLP5T7ZX7H3FIFENEF5WQAM" | C:\Program Files\think-cell\tcupdate.exe | tcupdate.exe | ||||||||||||
User: SYSTEM Company: think-cell Operations GmbH Integrity Level: SYSTEM Description: think-cell component Exit code: 0 Version: 10.0.28.124 Modules
| |||||||||||||||
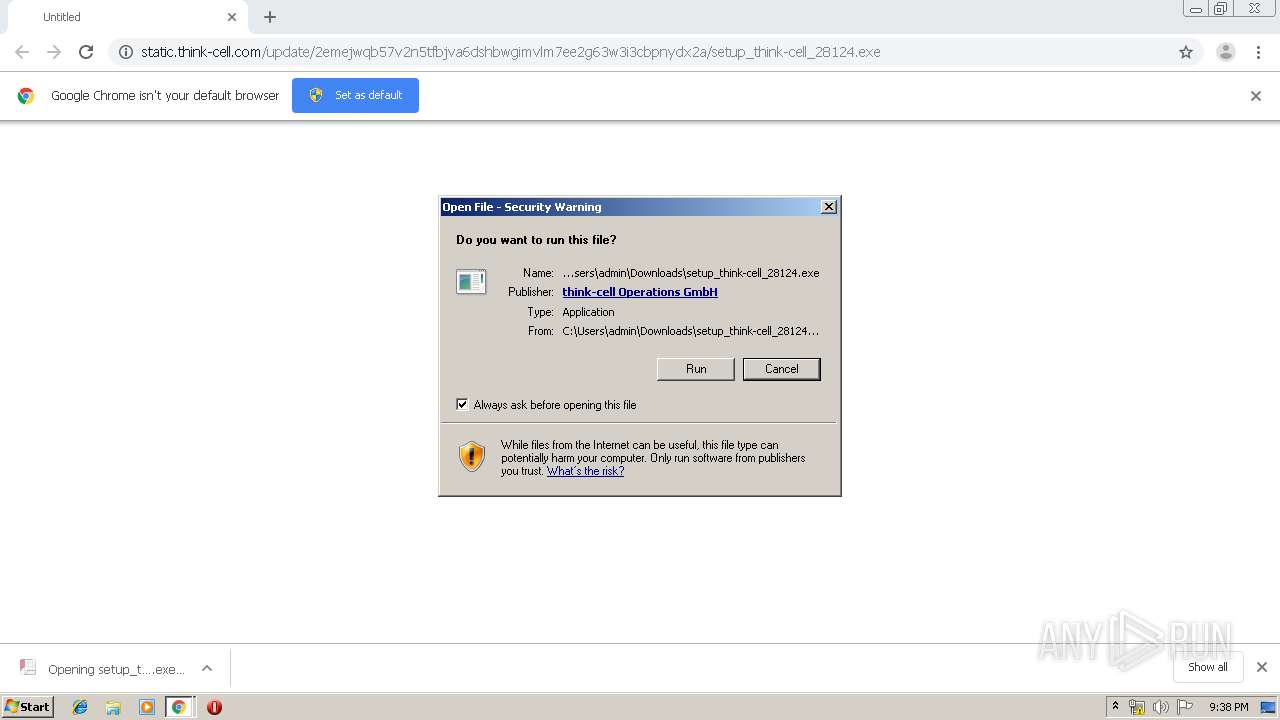
| 2492 | "C:\Users\admin\Downloads\setup_think-cell_28124.exe" | C:\Users\admin\Downloads\setup_think-cell_28124.exe | — | chrome.exe | |||||||||||
User: admin Company: think-cell Operations GmbH Integrity Level: MEDIUM Description: think-cell setup Exit code: 0 Version: 10.0.28.124 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,2822993343566949409,16240473352529002159,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3615767360305071011 --mojo-platform-channel-handle=3724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 738
Read events
2 165
Write events
551
Delete events
22
Modification events
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2040-13218413864110375 |
Value: 259 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2040) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
17
Suspicious files
16
Text files
88
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ff814c22-f55b-4cd7-9df6-64cc5caafd95.tmp | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a9a8.TMP | text | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a9a8.TMP | text | |
MD5:— | SHA256:— | |||
| 2040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
15
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4016 | chrome.exe | GET | 301 | 46.101.73.231:80 | http://static.think-cell.com/update/2emejwqb57v2n5tfbjva6dshbwgimvlm7ee2g63w3i3cbpnydx2a/setup_think-cell_28124.exe | GB | html | 185 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 46.101.73.231:80 | static.think-cell.com | Digital Ocean, Inc. | GB | unknown |
4016 | chrome.exe | 46.101.73.231:443 | static.think-cell.com | Digital Ocean, Inc. | GB | unknown |
4016 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
4016 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.21.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.16.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2376 | tcupdate.exe | 213.61.229.130:443 | update.appcom.think-cell.com | COLT Technology Services Group Limited | DE | unknown |
4016 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
static.think-cell.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
update.appcom.think-cell.com |
| unknown |