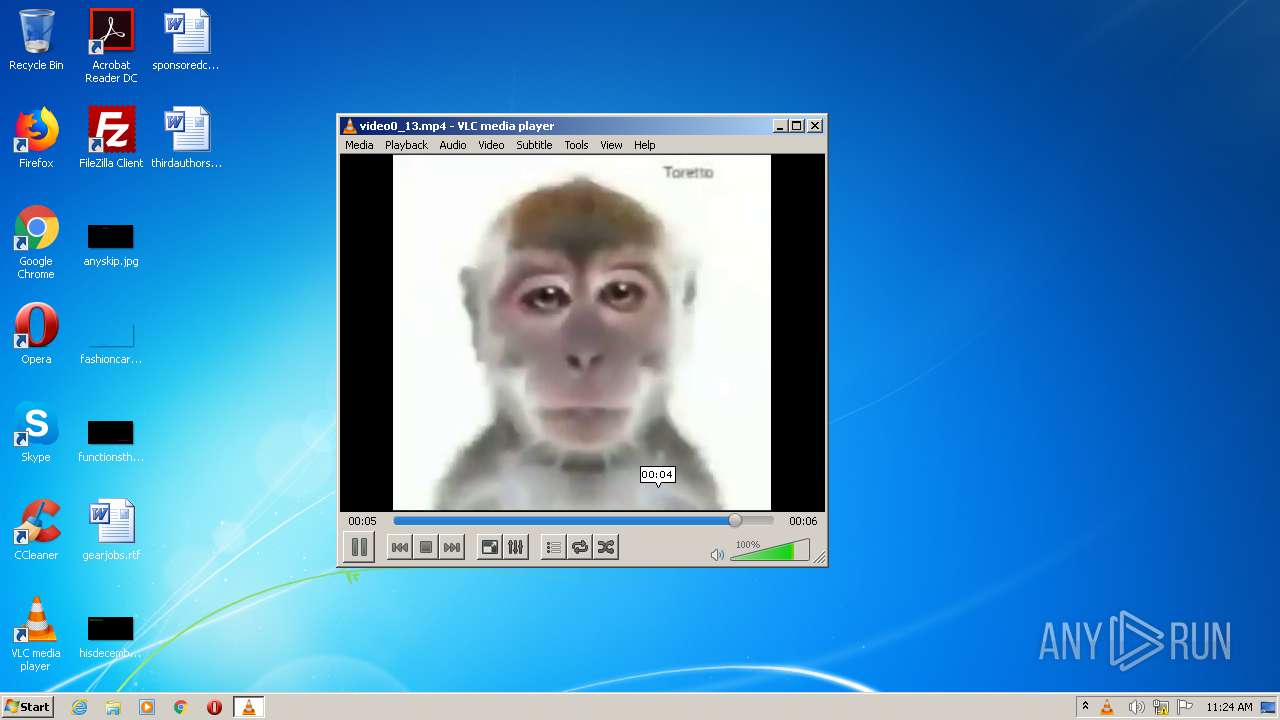
| File name: | video0_13.mp4 |
| Full analysis: | https://app.any.run/tasks/50824b6b-2416-42e5-82d2-3c367c345a23 |
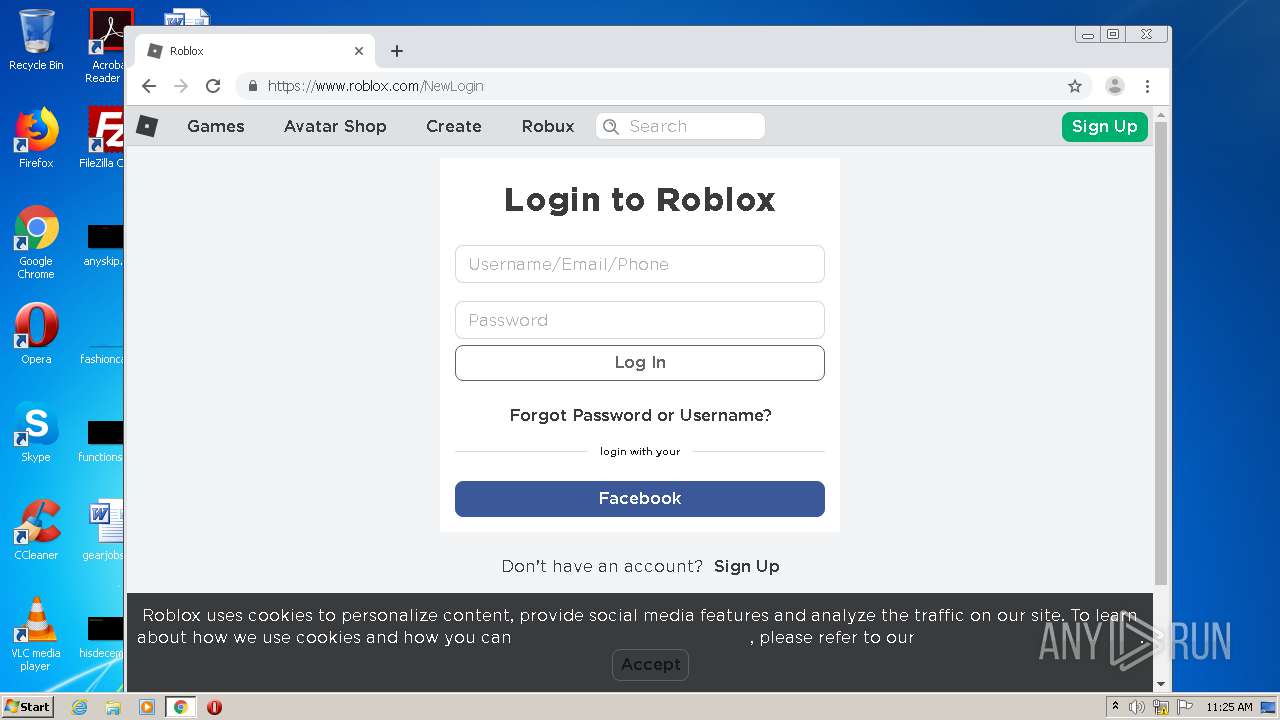
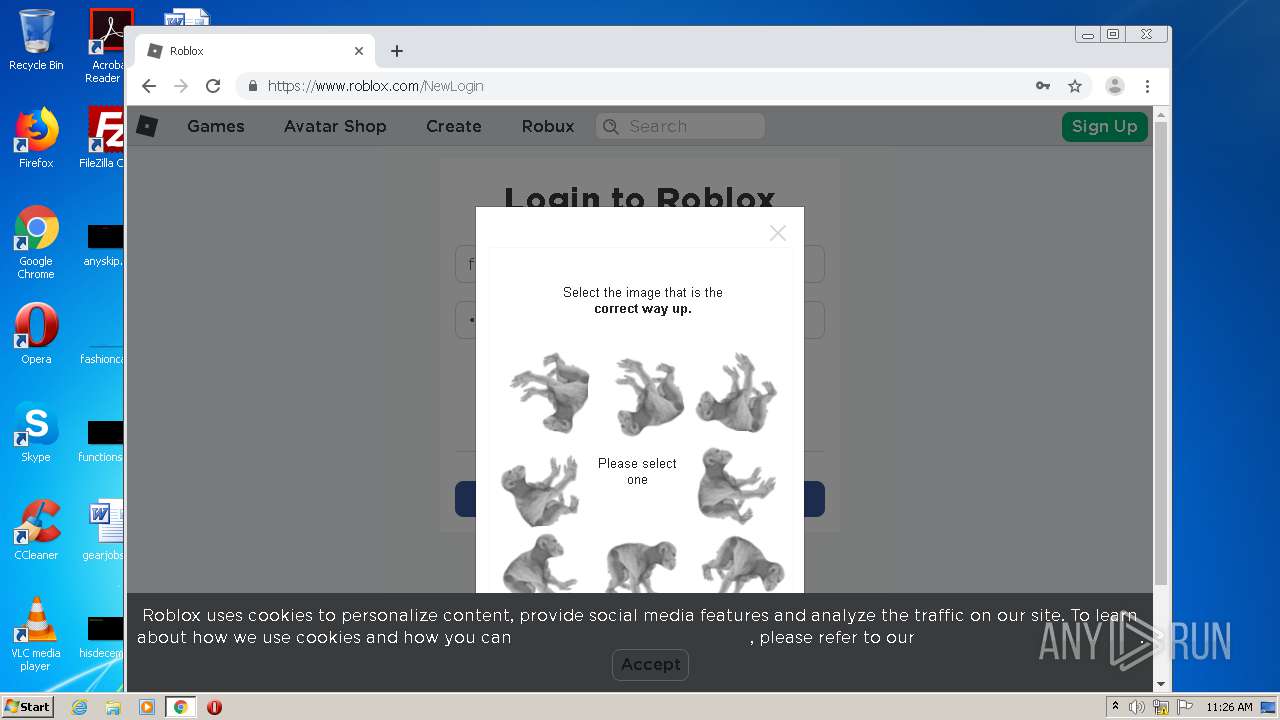
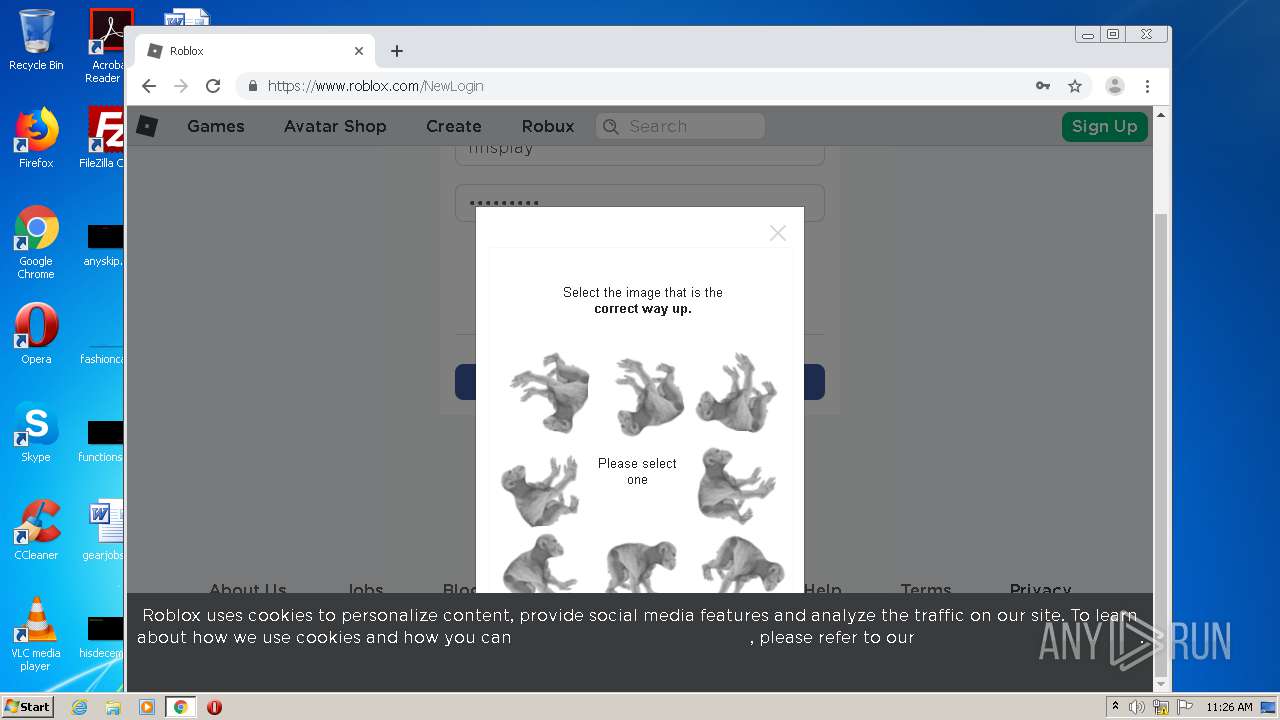
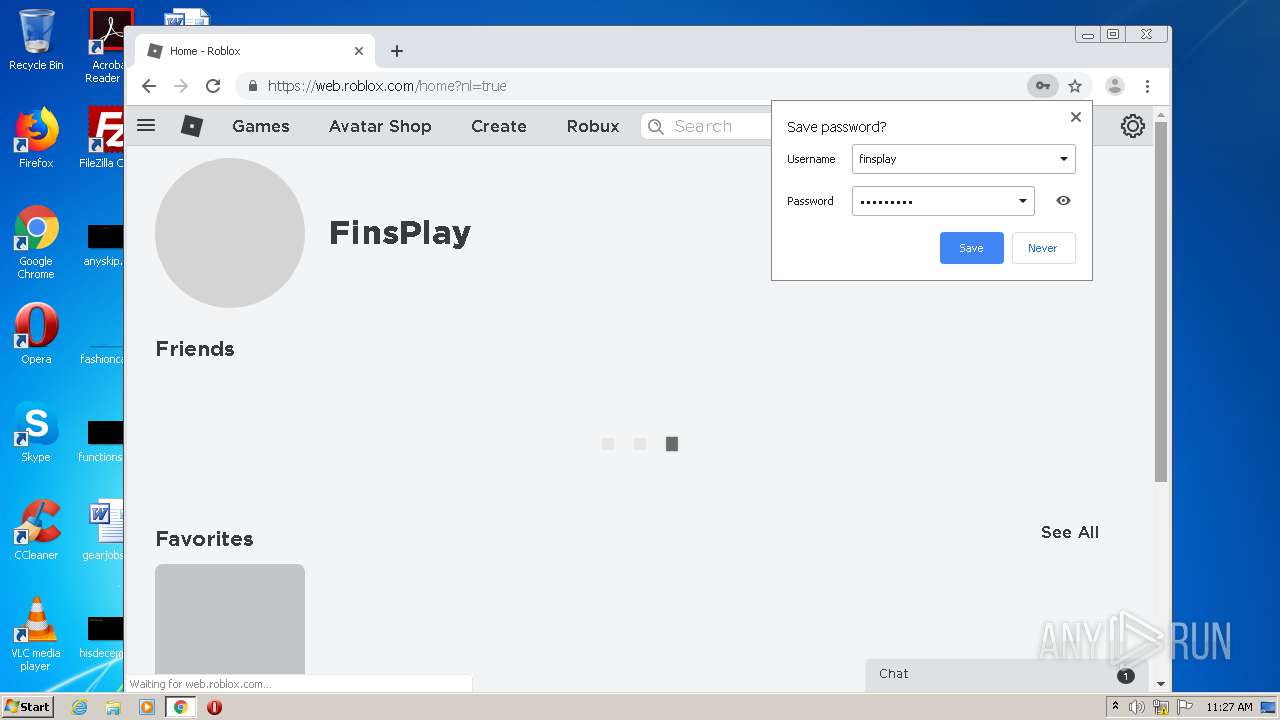
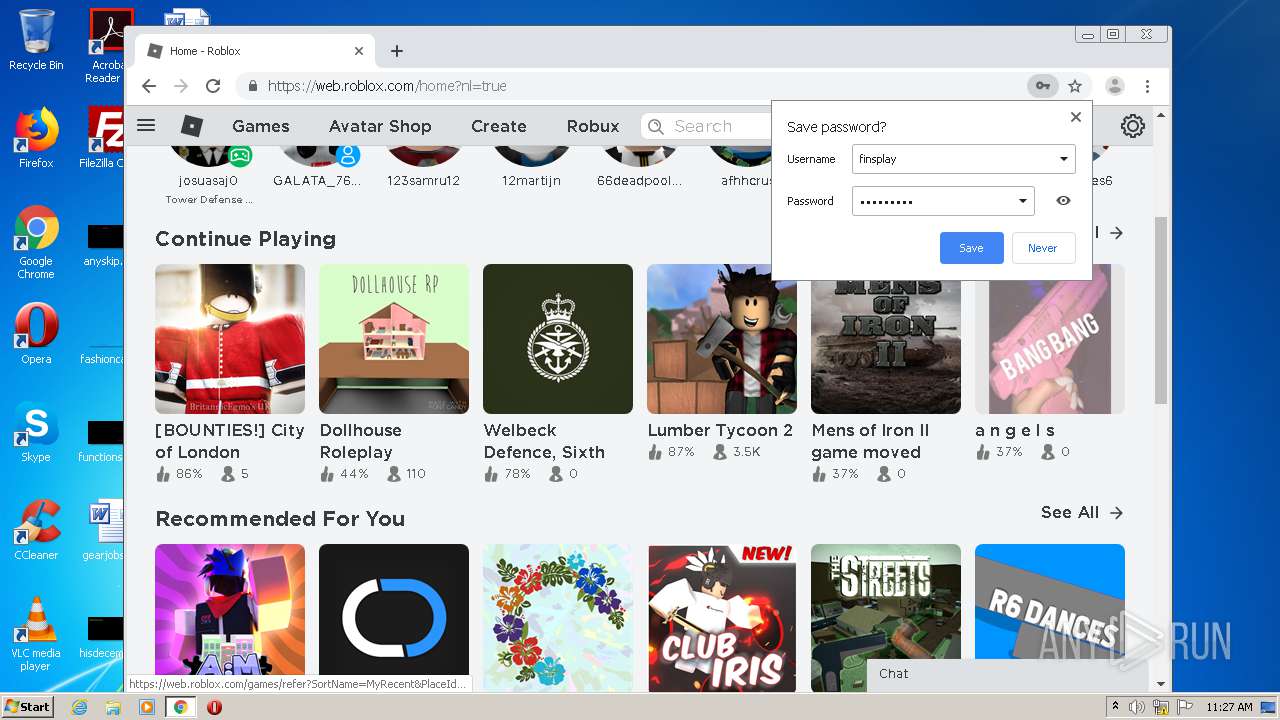
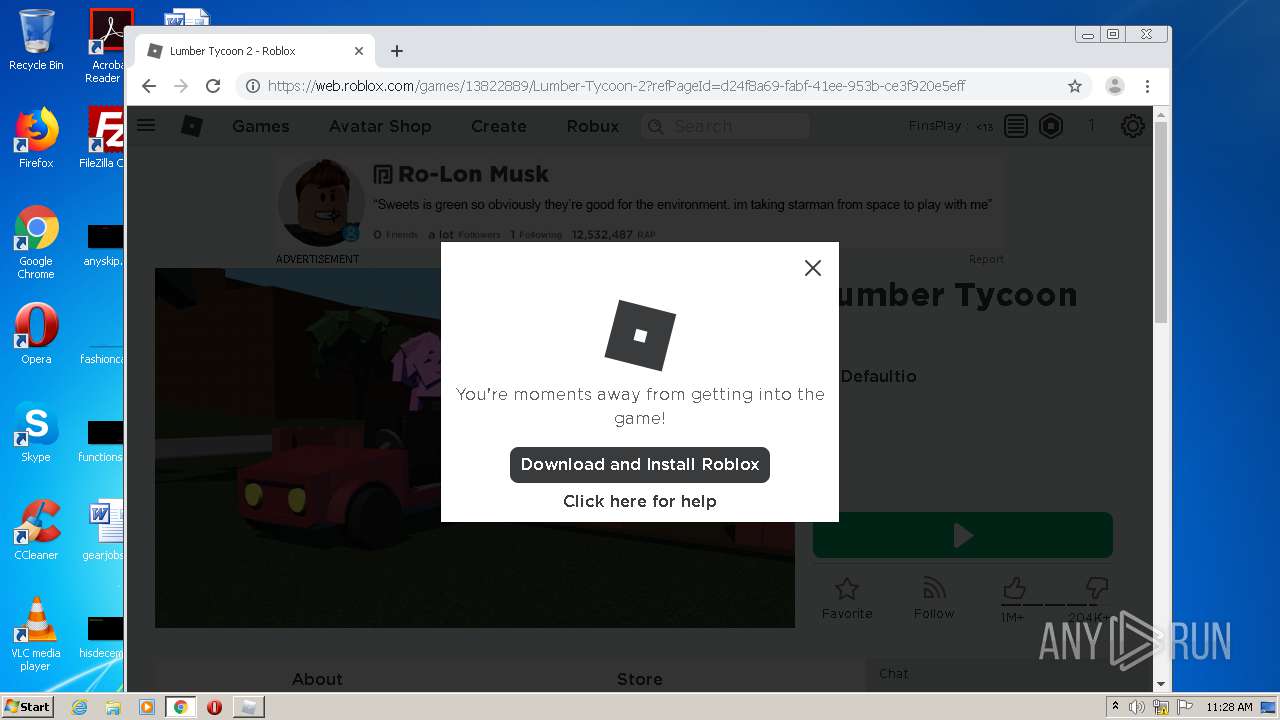
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 10:24:14 |
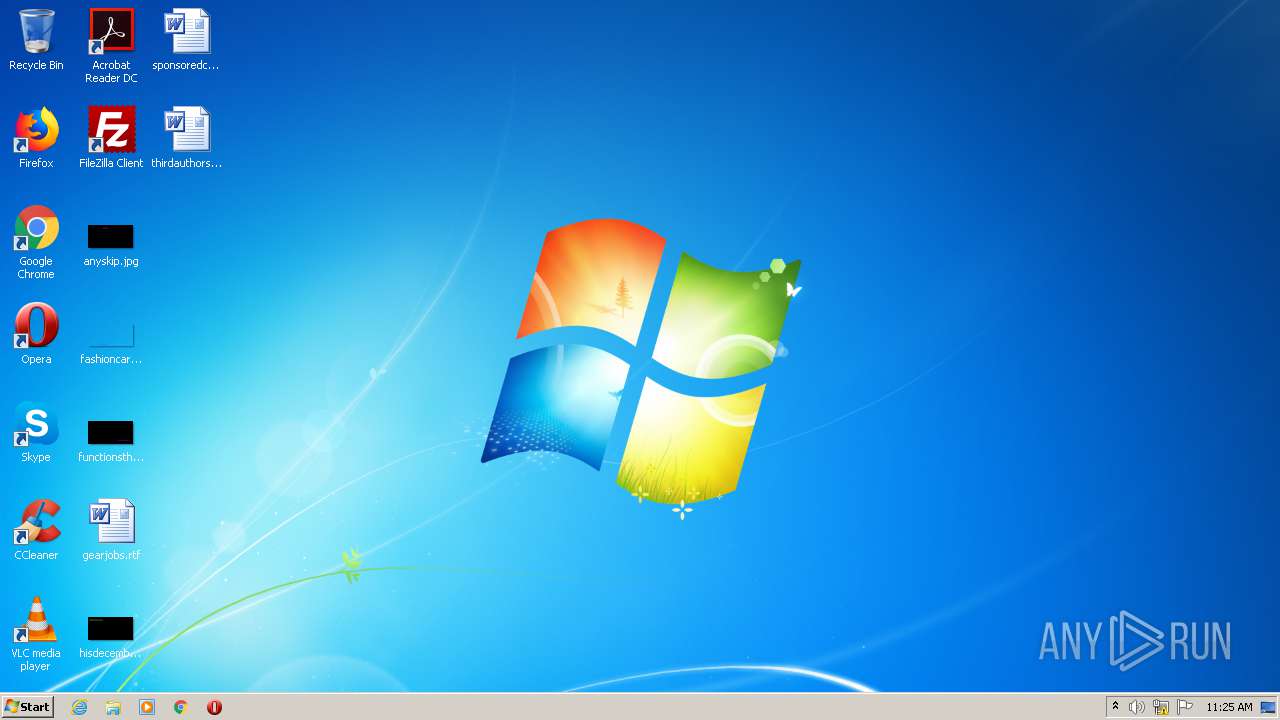
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | video/mp4 |
| File info: | ISO Media, MP4 v2 [ISO 14496-14] |
| MD5: | B940B684D8D53C58B835DCFD48FE0D93 |
| SHA1: | 9B3EF0D69F9CA0A86BA787B139C441541F5A41B0 |
| SHA256: | 190CE2AD6DC6F9086BBAA25866DEE5ACDAF1109C0EC39C473D8CBD04AC532A66 |
| SSDEEP: | 1536:HyIWWdEky/rnFSLBg/CB1Ua5DuhGnnp1BibEmdIV/awwxjV5:HyIVdEfrnFSLB2CjU/Vo1ijV5 |
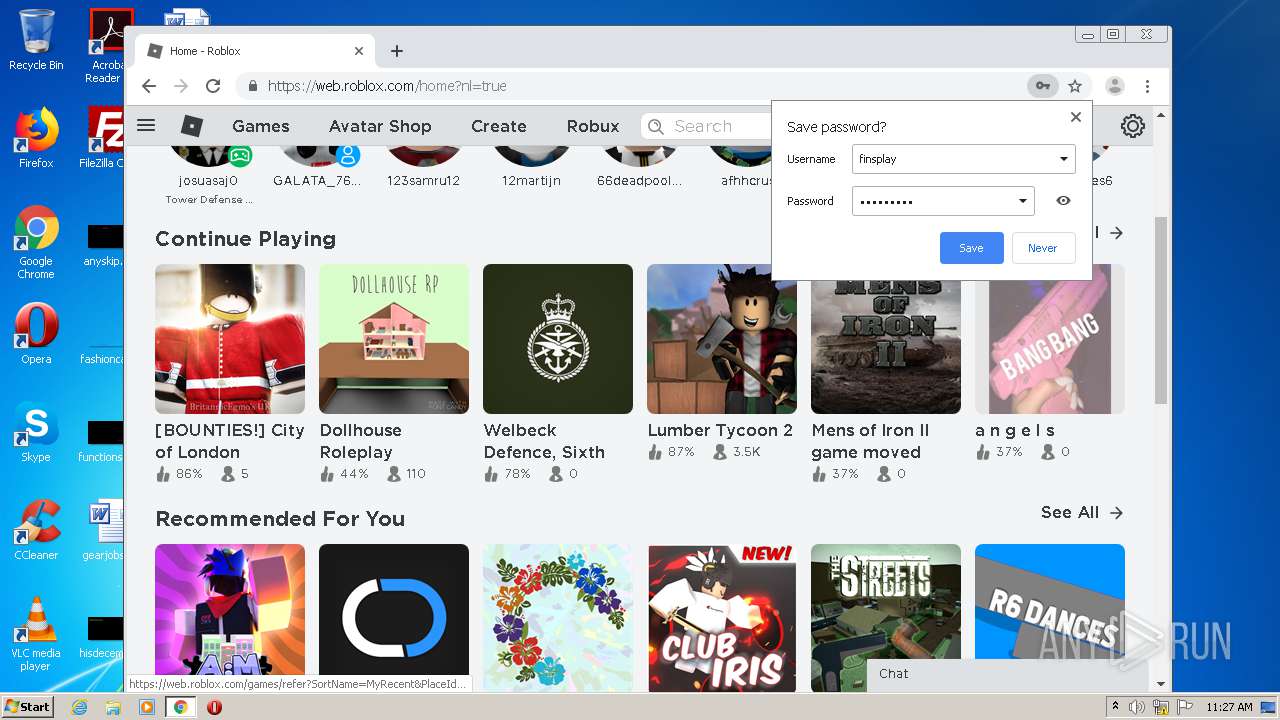
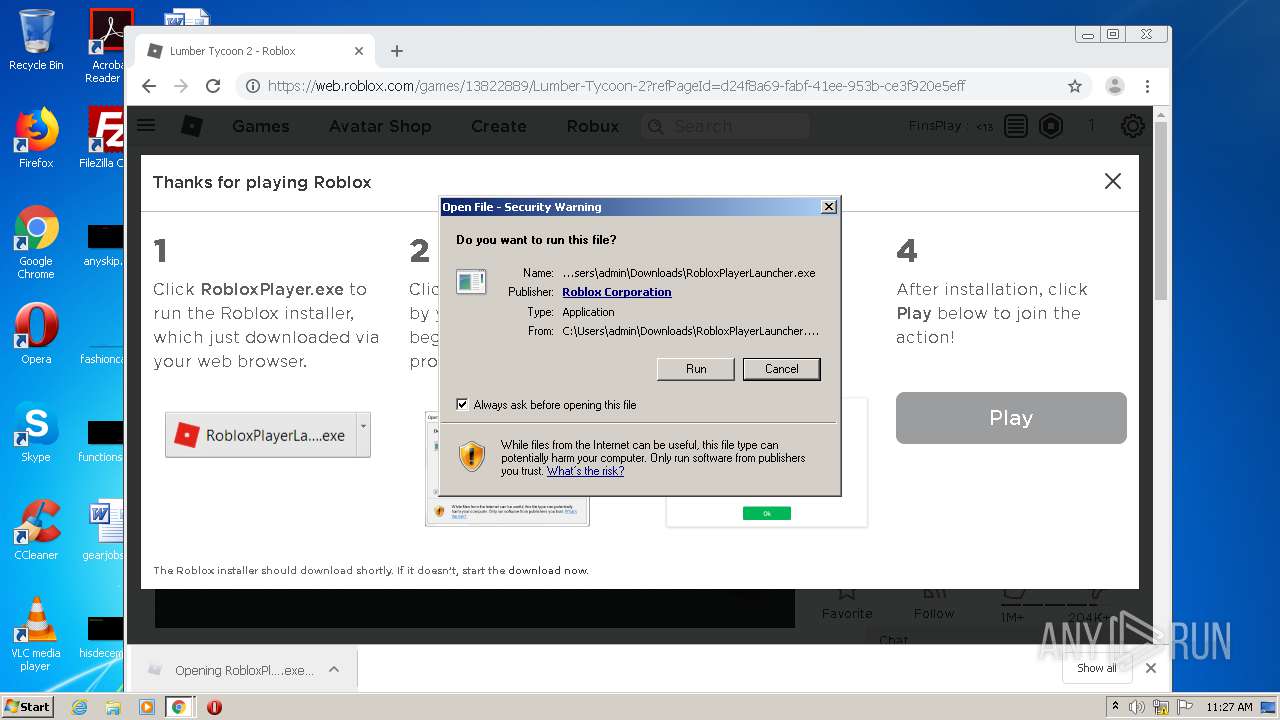
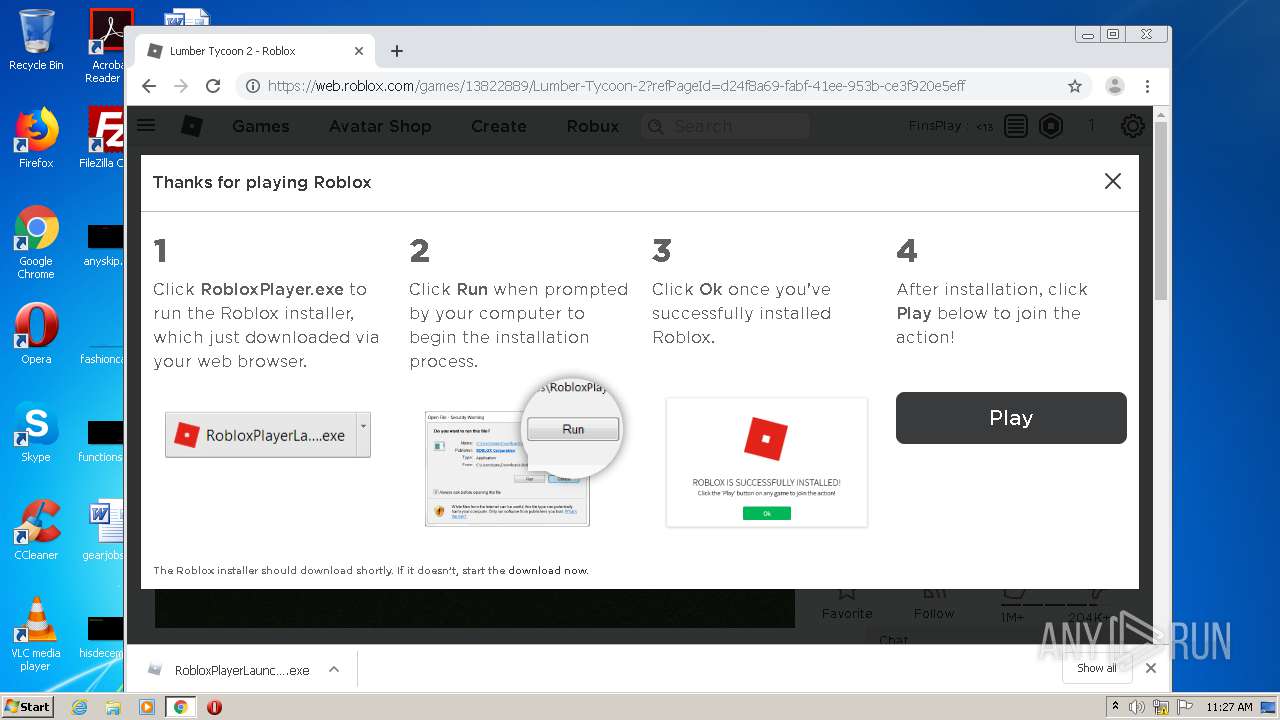
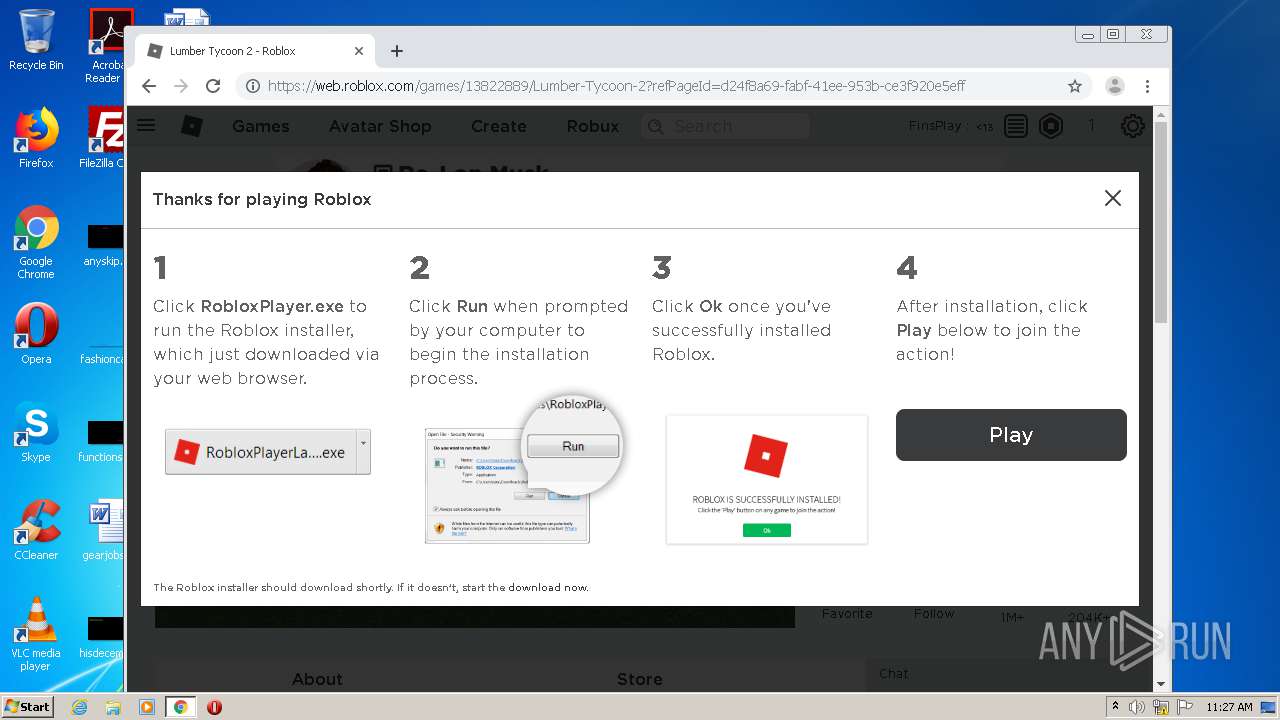
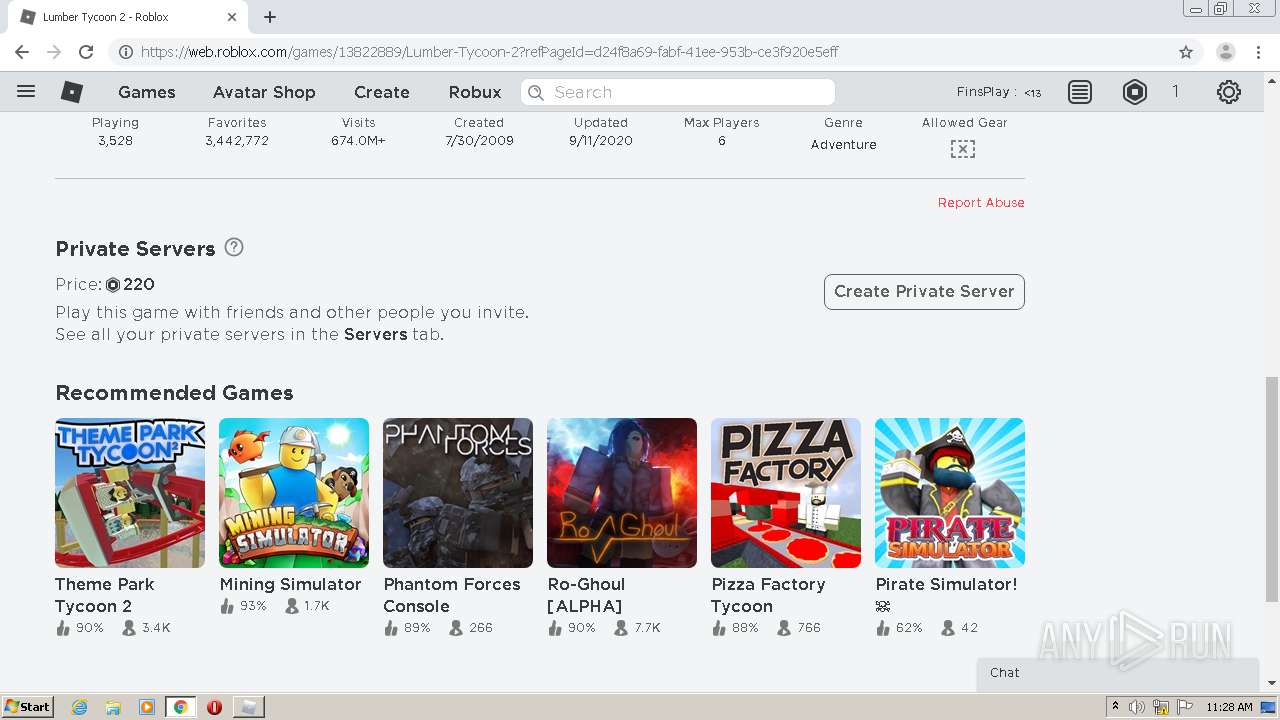
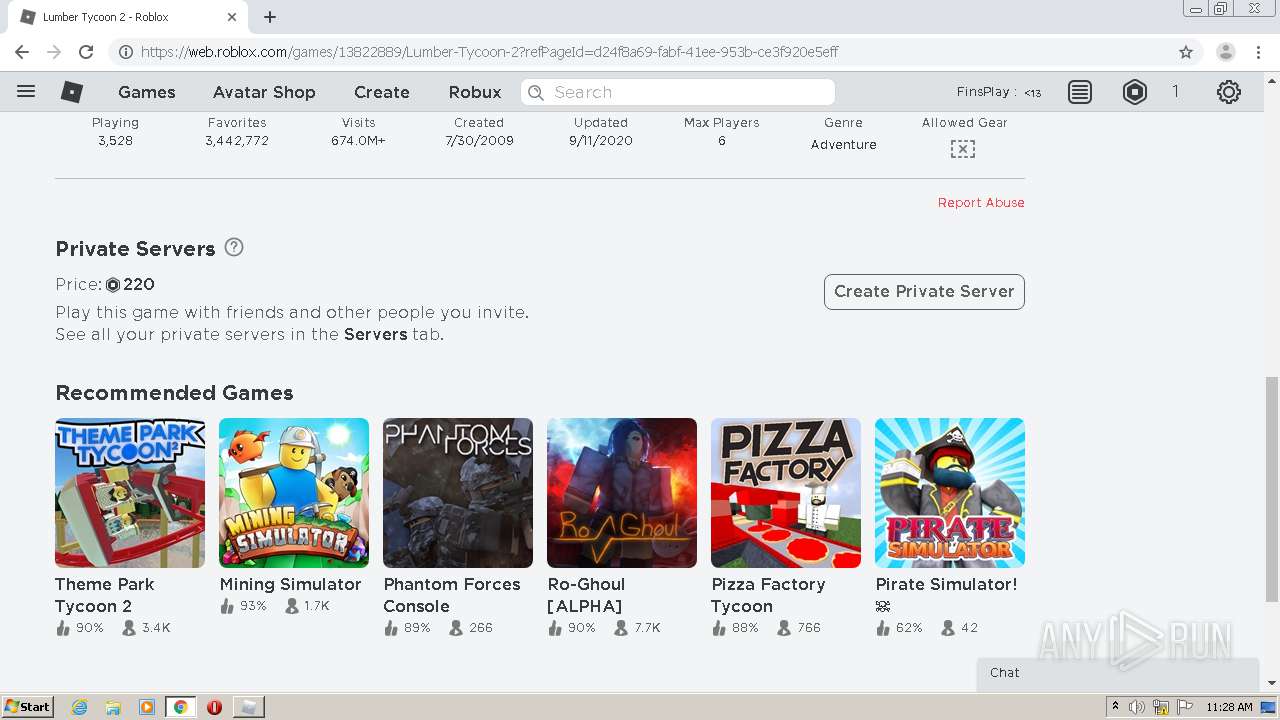
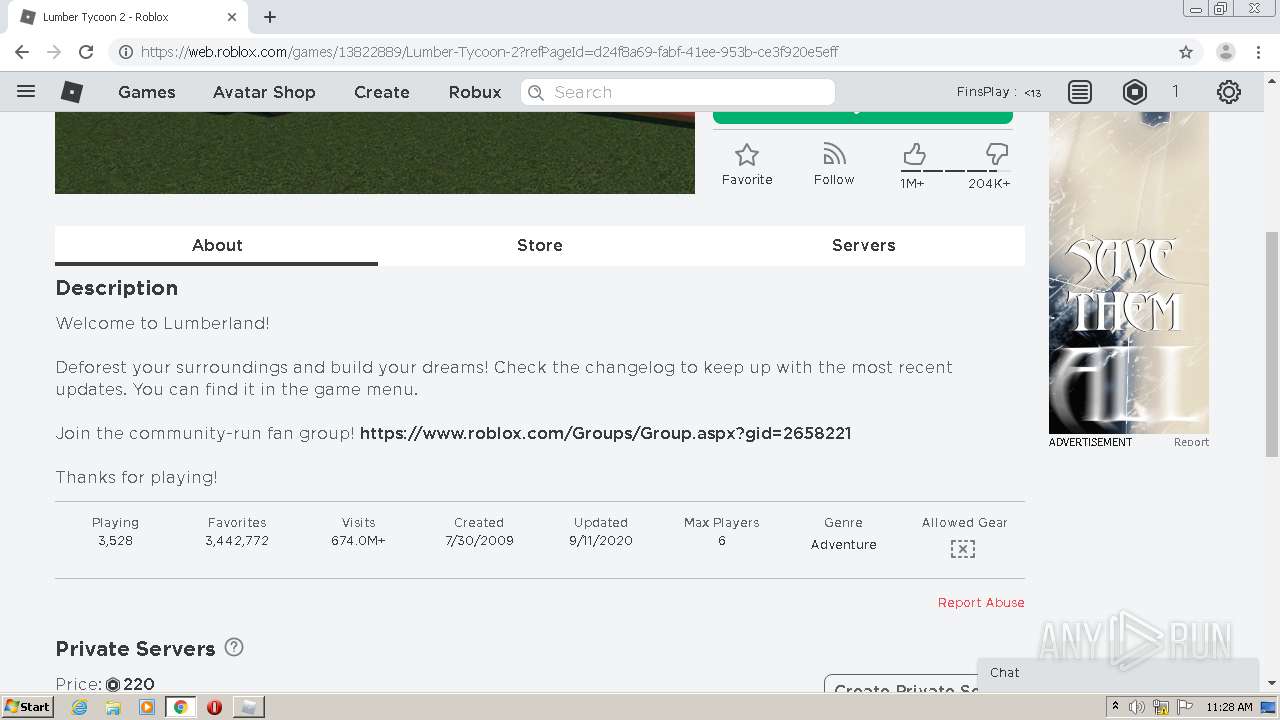
MALICIOUS
Application was dropped or rewritten from another process
- RobloxPlayerLauncher.exe (PID: 1504)
- RobloxPlayerLauncher.exe (PID: 3276)
SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 3088)
- RobloxPlayerLauncher.exe (PID: 1504)
Reads Internet Cache Settings
- RobloxPlayerLauncher.exe (PID: 1504)
- RobloxPlayerLauncher.exe (PID: 3276)
Executable content was dropped or overwritten
- chrome.exe (PID: 3004)
- RobloxPlayerLauncher.exe (PID: 1504)
Application launched itself
- RobloxPlayerLauncher.exe (PID: 1504)
Modifies the open verb of a shell class
- RobloxPlayerLauncher.exe (PID: 1504)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2248)
- chrome.exe (PID: 1876)
Reads the hosts file
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 3004)
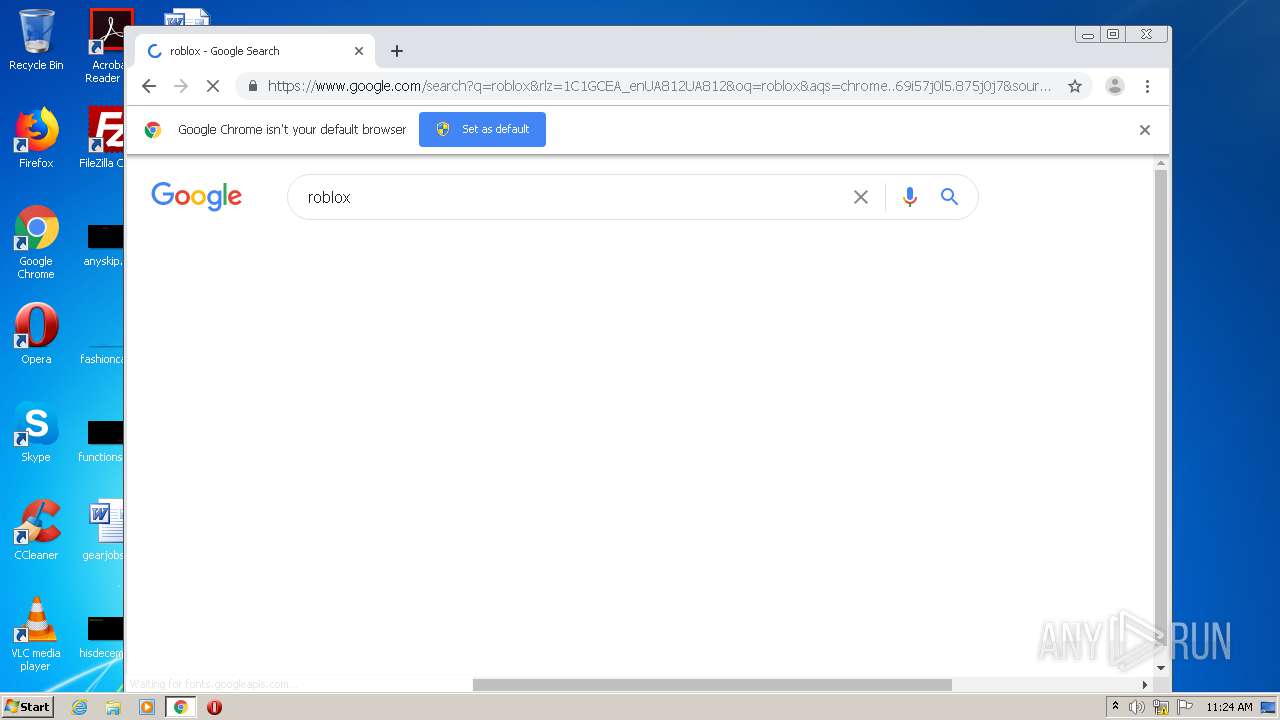
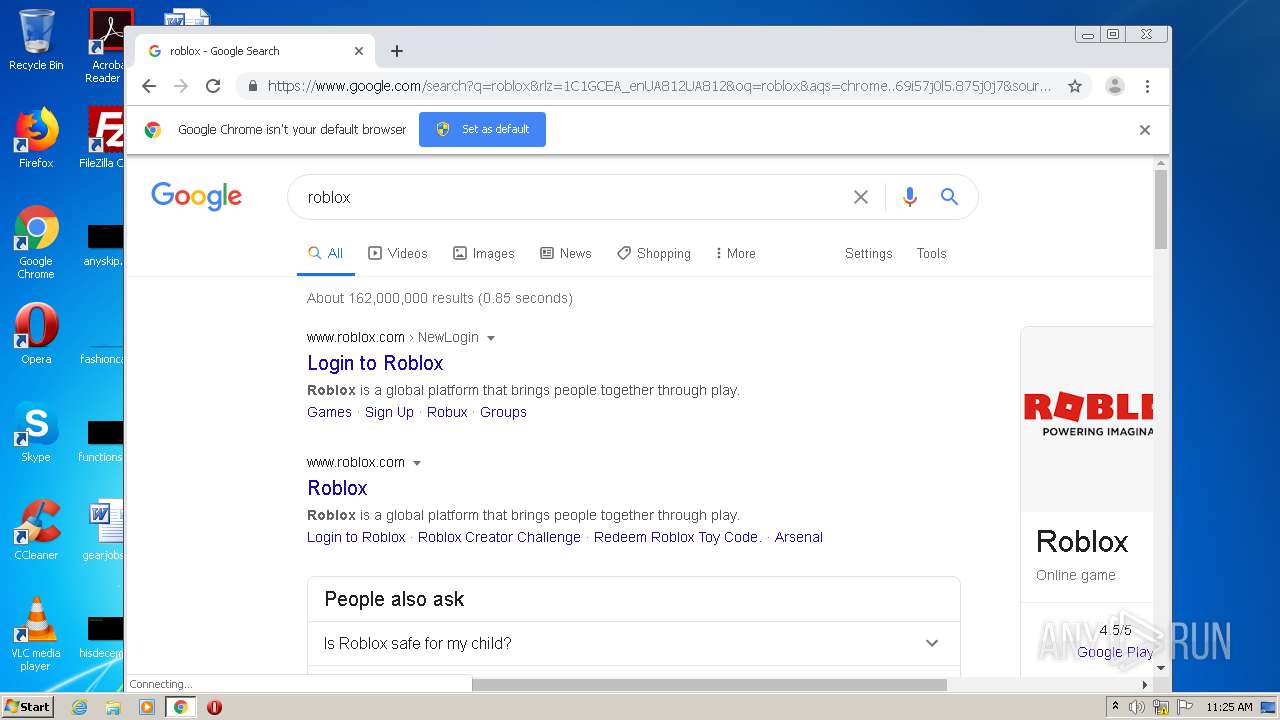
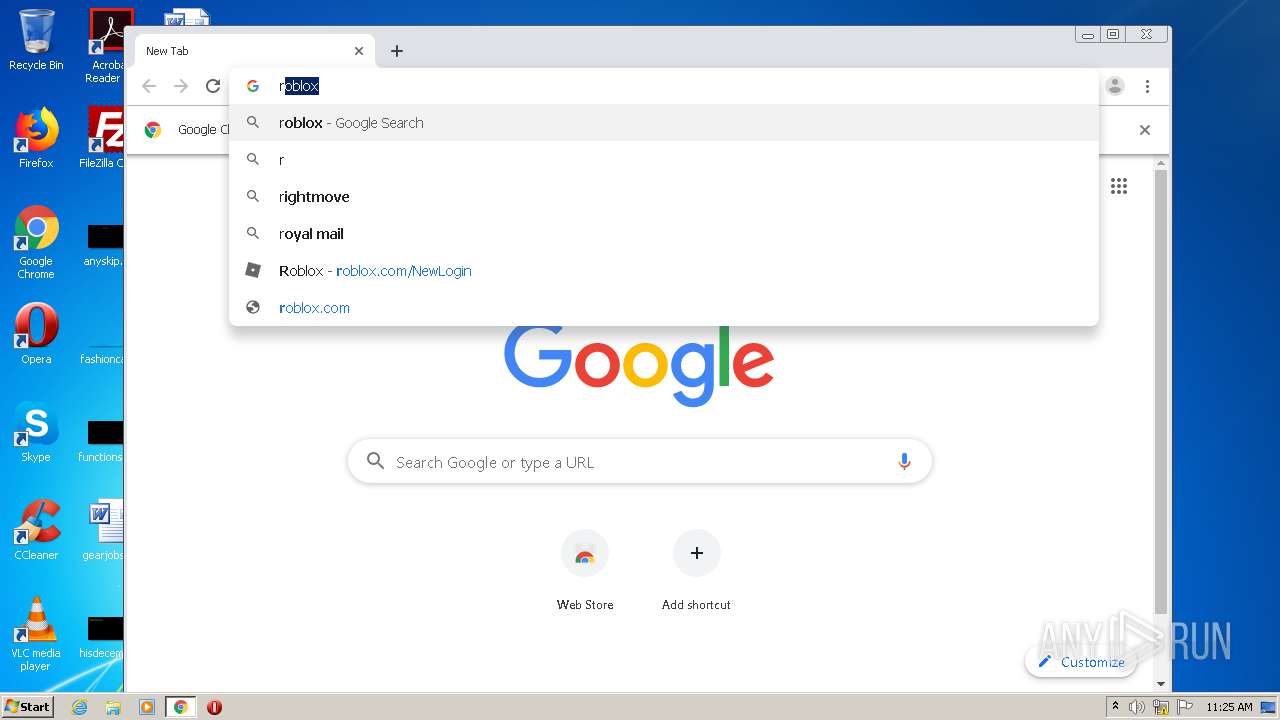
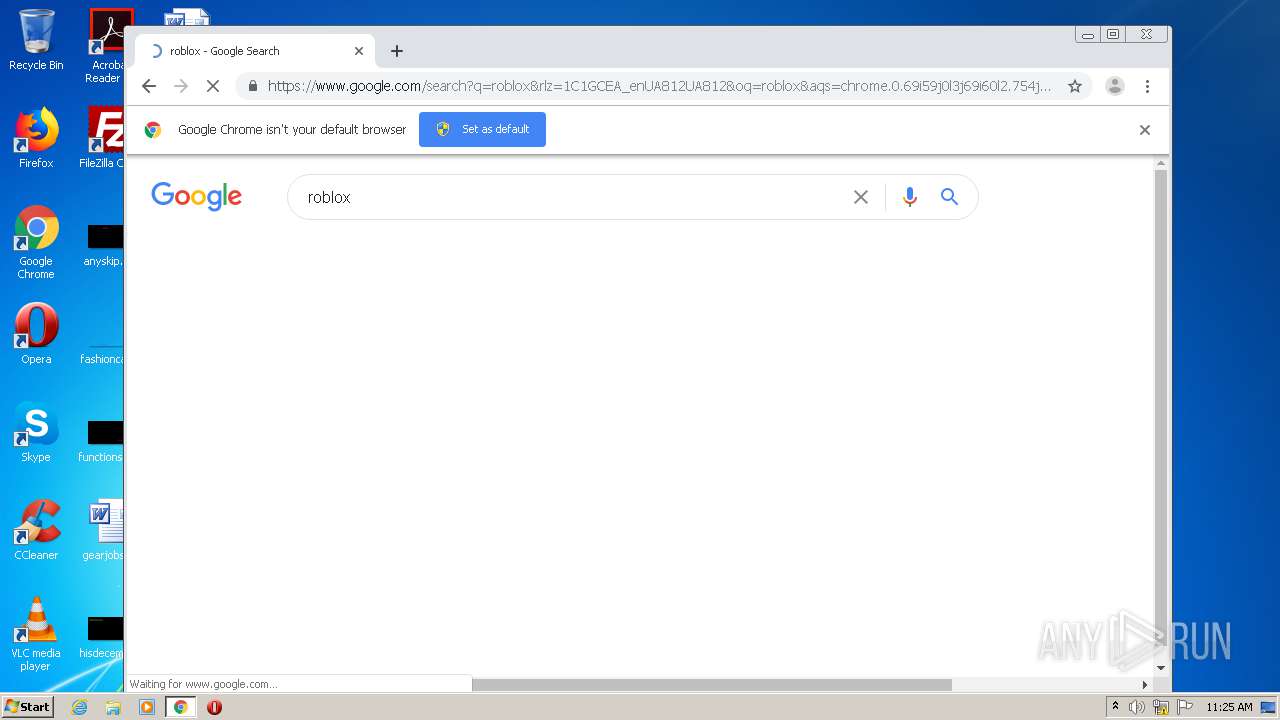
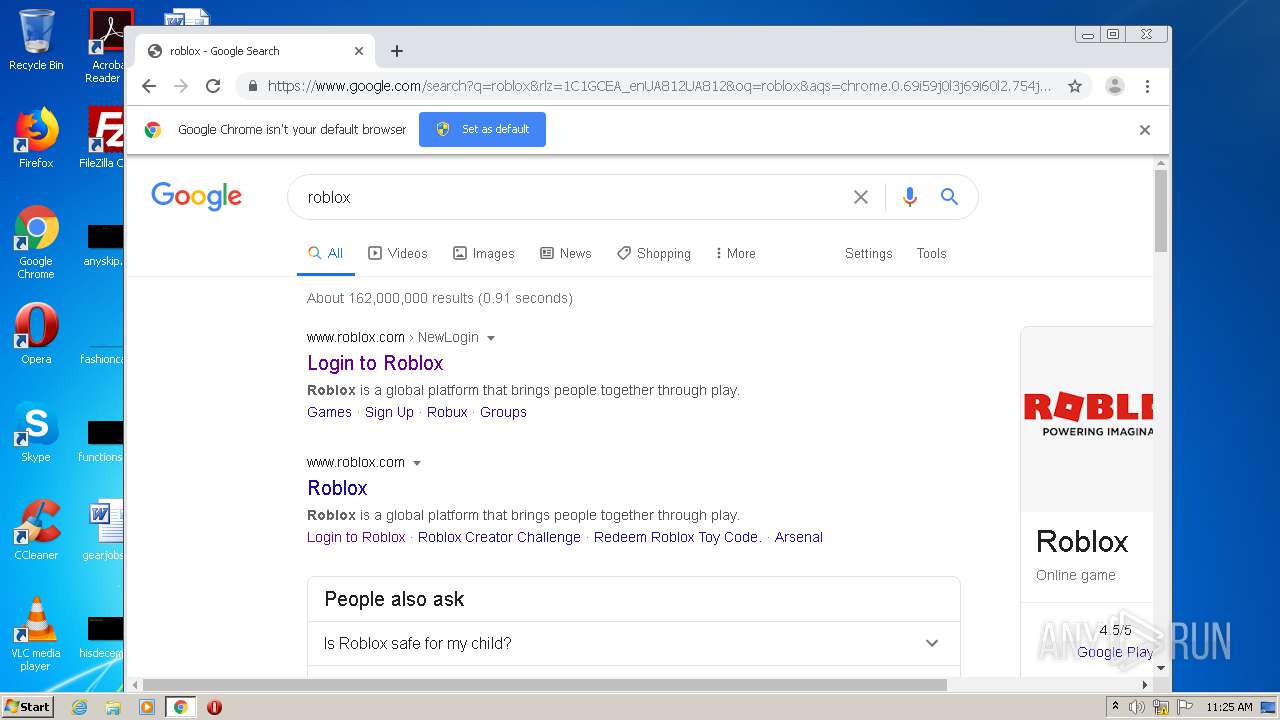
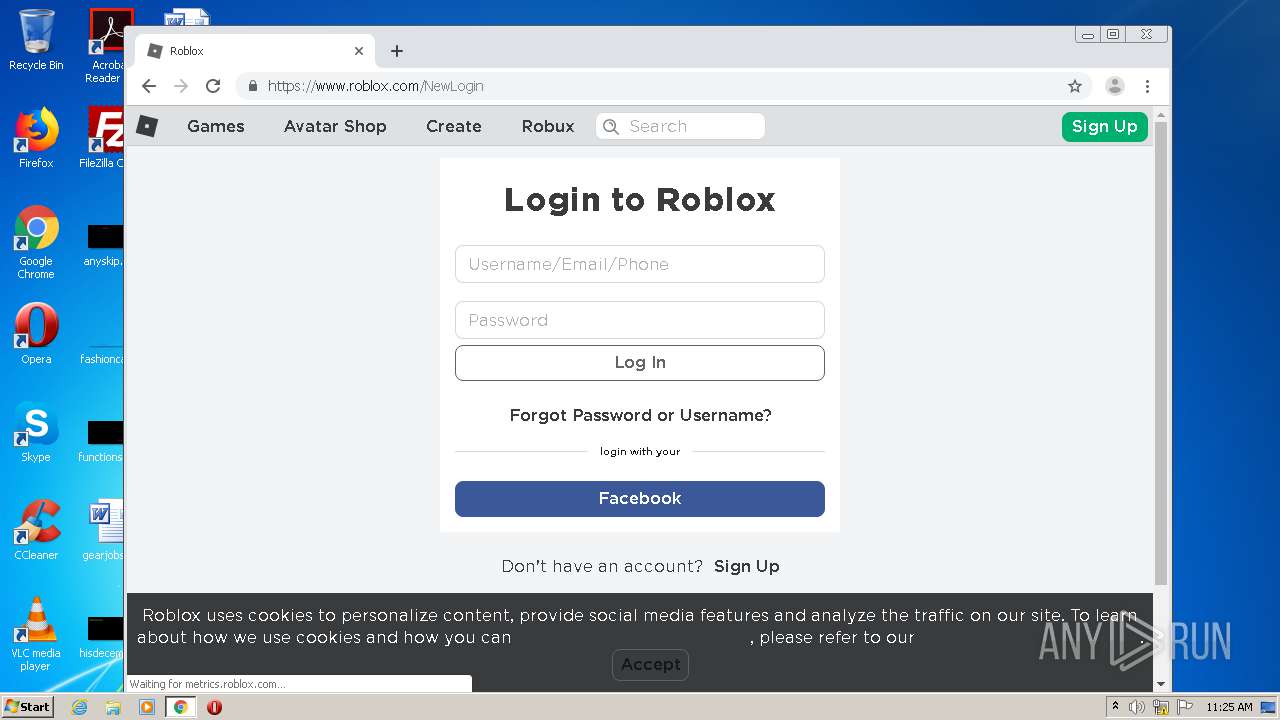
Manual execution by user
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3004)
Application launched itself
- chrome.exe (PID: 3692)
- chrome.exe (PID: 3004)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3004)
Reads Internet Cache Settings
- chrome.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .m4v | | | MPEG-4 Video (54.4) |
|---|---|---|
| .3g2 | | | 3GPP2 multimedia audio/video (37.7) |
| .mov | | | QuickTime Movie (3.8) |
| .mp4 | | | Generic MP4 container (2.3) |
| .abr | | | Adobe PhotoShop Brush (0.7) |
EXIF
QuickTime
| MajorBrand: | MP4 v2 [ISO 14496-14] |
|---|---|
| MinorVersion: | 0.0.0 |
| CompatibleBrands: |
|
| MovieHeaderVersion: | - |
| CreateDate: | 2020:01:16 21:17:14 |
| ModifyDate: | 2020:01:16 21:17:14 |
| TimeScale: | 48000 |
| Duration: | 6.34 s |
| PreferredRate: | 1 |
| PreferredVolume: | 100.00% |
| PreviewTime: | 0 s |
| PreviewDuration: | 0 s |
| PosterTime: | 0 s |
| SelectionTime: | 0 s |
| SelectionDuration: | 0 s |
| CurrentTime: | 0 s |
| NextTrackID: | 3 |
| TrackHeaderVersion: | - |
| TrackCreateDate: | 2020:01:16 21:17:14 |
| TrackModifyDate: | 2020:01:16 21:17:14 |
| TrackID: | 1 |
| TrackDuration: | 6.30 s |
| TrackLayer: | - |
| TrackVolume: | 0.00% |
| ImageWidth: | 378 |
| ImageHeight: | 358 |
| GraphicsMode: | srcCopy |
| OpColor: | 0 0 0 |
| CompressorID: | avc1 |
| SourceImageWidth: | 378 |
| SourceImageHeight: | 358 |
| XResolution: | 72 |
| YResolution: | 72 |
| CompressorName: | AVC Coding |
| BitDepth: | - |
| BufferSize: | 4213 |
| MaxBitrate: | 107024 |
| AverageBitrate: | 49760 |
| VideoFrameRate: | 30 |
| MatrixStructure: | 1 0 0 0 1 0 0 0 1 |
| MediaHeaderVersion: | - |
| MediaCreateDate: | 2020:01:16 21:17:14 |
| MediaModifyDate: | 2020:01:16 21:17:14 |
| MediaTimeScale: | 48000 |
| MediaDuration: | 6.34 s |
| MediaLanguageCode: | und |
| HandlerType: | Audio Track |
| HandlerDescription: | Vireo Ears v2.5.3 |
| Balance: | - |
| AudioFormat: | mp4a |
| AudioChannels: | 2 |
| AudioBitsPerSample: | 16 |
| AudioSampleRate: | 48000 |
| MovieDataSize: | 90695 |
| MovieDataOffset: | 4782 |
Composite
| AvgBitrate: | 115 kbps |
|---|---|
| ImageSize: | 378x358 |
| Megapixels: | 0.135 |
| Rotation: | - |
Total processes
83
Monitored processes
44
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6648706371620057568,13614383322614982790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3340679236989910295 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16922319955364748980,8380959670058781382,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16809442001489192218 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16922319955364748980,8380959670058781382,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=655754094302789003 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d07a9d0,0x6d07a9e0,0x6d07a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3548 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16922319955364748980,8380959670058781382,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14113255525936690507 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16922319955364748980,8380959670058781382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6455265982364158965 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6648706371620057568,13614383322614982790,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11288907143452957939 --mojo-platform-channel-handle=3588 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16922319955364748980,8380959670058781382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=393922963568173261 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,6648706371620057568,13614383322614982790,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=453278158027867449 --mojo-platform-channel-handle=2284 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 317
Read events
2 073
Write events
237
Delete events
7
Modification events
| (PID) Process: | (3088) vlc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: vlc.exe | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
7
Suspicious files
269
Text files
296
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC7763.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78CB.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78CC.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78CD.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78CE.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78CF.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78D0.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78D1.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78D2.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLC78D3.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
132
DNS requests
101
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | RobloxPlayerLauncher.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr5/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQiD0S5cIHyfrLTJ1fvAkJWflH%2B2QQUPeYpSJvqB8ohREom3m7e0oPQn1kCDQHuXyKVQkkF%2BQGRqNw%3D | US | der | 1.34 Kb | whitelisted |
1504 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1504 | RobloxPlayerLauncher.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gseccovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBSTMjK03nNiYoQYvu4Izyfn9OJNdAQUWHuOdSr%2BYYCqkEABrtboB0ZuP0gCDGbM6PQ9Yanr1EKr1g%3D%3D | US | der | 1.01 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 23.210.249.93:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | NL | der | 813 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
1504 | RobloxPlayerLauncher.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1504 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
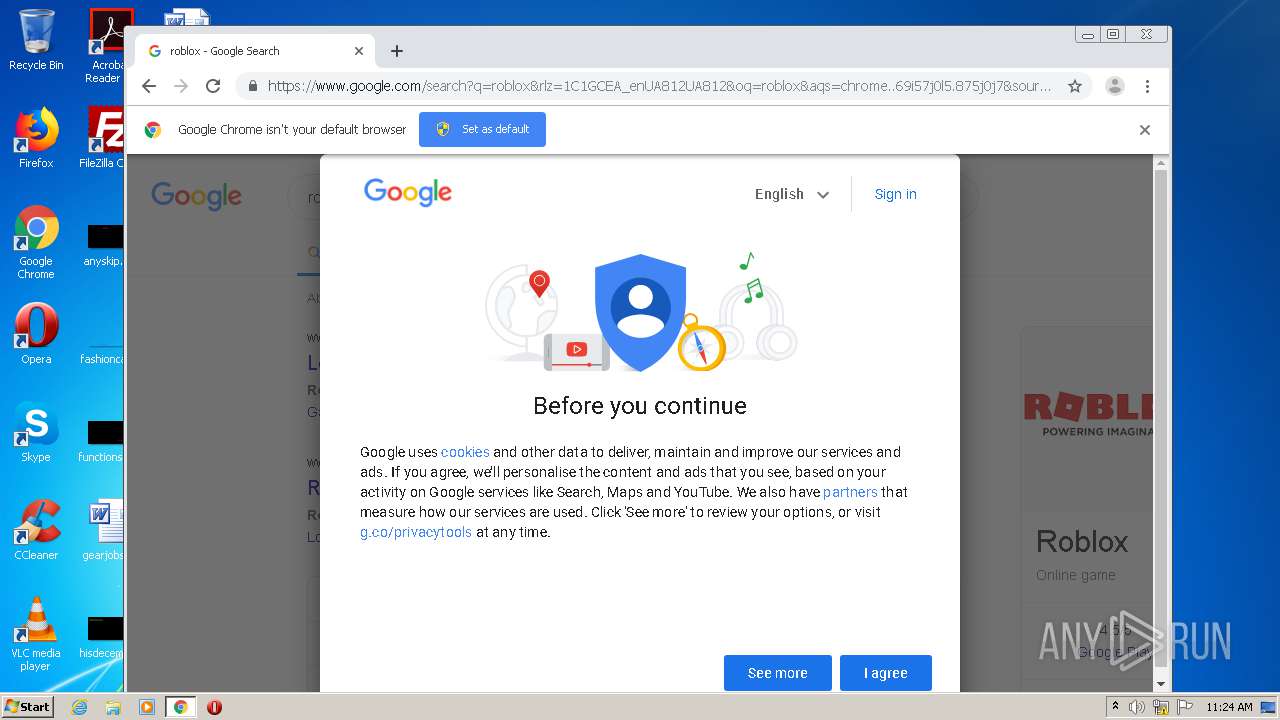
2248 | chrome.exe | 172.217.23.110:443 | consent.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.207.46:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
encrypted-tbn0.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|
vlc.exe | core input error: ES_OUT_SET_(GROUP_)PCR is called too late (pts_delay increased to 300 ms)
|
vlc.exe | core input error: ES_OUT_RESET_PCR called
|