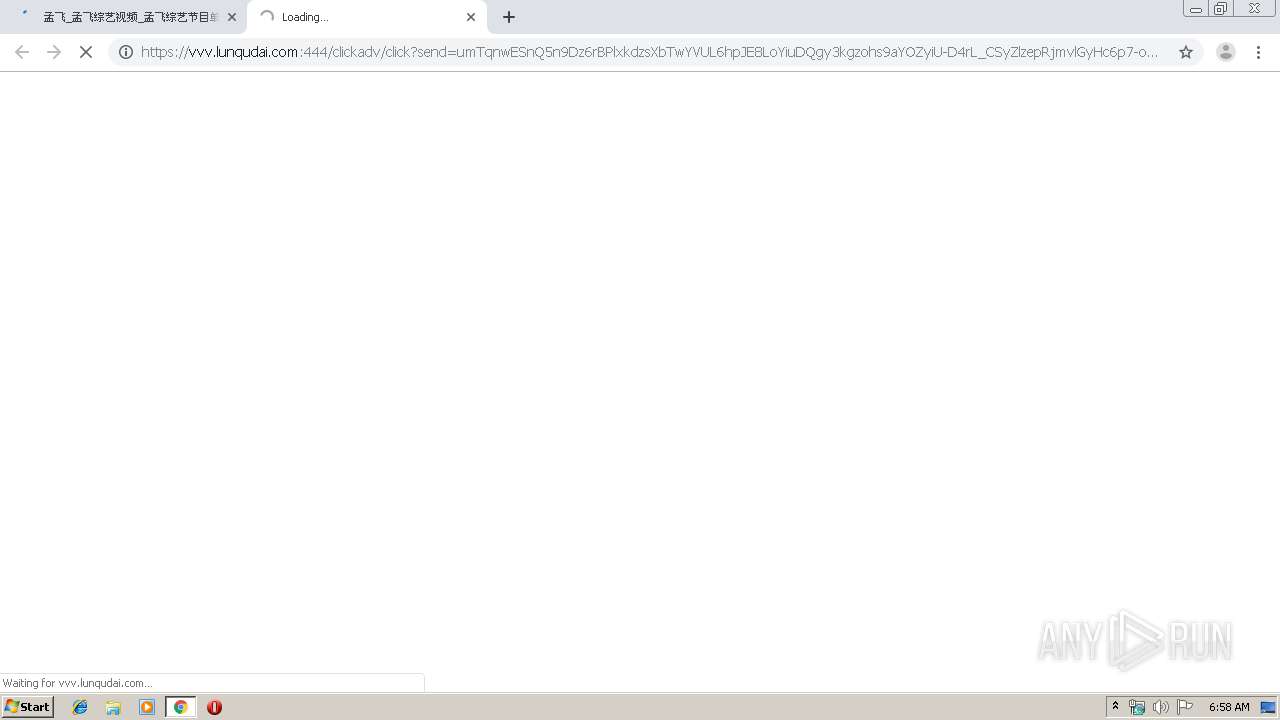
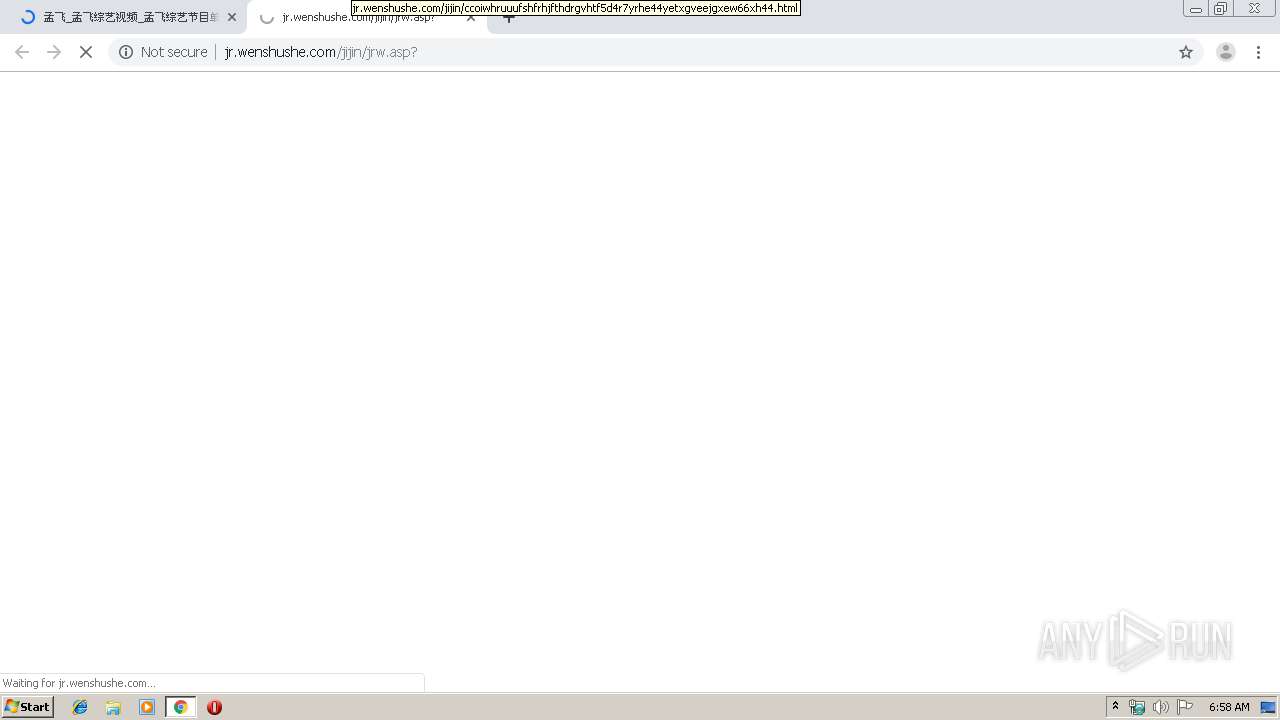
| URL: | http://www.zy84.cc/artist/53513670/ |
| Full analysis: | https://app.any.run/tasks/6b71be2e-faca-4ccc-8bf3-fc138656282a |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 05:58:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3D9D88980E7887C0E002E1A8E2525377 |
| SHA1: | 796B7BCB01B5FDA99D90B603C5099E0E416D68E0 |
| SHA256: | 19084ACA9773B5C1CC8B4F8A96A4CAA6CDE7F8151F7A4ACB645848035AE76C2F |
| SSDEEP: | 3:N1KJS40xKEXqCXrSVK:Cc40xf6CbSVK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3440)
INFO
Reads the hosts file
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2960)
Creates files in the user directory
- chrome.exe (PID: 3440)
Reads settings of System Certificates
- chrome.exe (PID: 2960)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3440)
Application launched itself
- chrome.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
55
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6945333097527472549 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3372 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13416485536266658294 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=306730191904303886 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11105941119200736301 --mojo-platform-channel-handle=8276 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2738502525447289794 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6468467013490489262 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6627071294562979646 --mojo-platform-channel-handle=8588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17602105136788260978 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18427199864753977657,3076804926658334403,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2281584964837596269 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
625
Read events
540
Write events
82
Delete events
3
Modification events
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3440-13212655103078500 |
Value: 259 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3440) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
193
Text files
187
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\604263f6-96da-4c37-bc68-b4626cae7d3e.tmp | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169e77.TMP | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169e96.TMP | text | |
MD5:— | SHA256:— | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
290
TCP/UDP connections
293
DNS requests
181
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/images/logo.png | HK | image | 5.11 Kb | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/artist/53513670/ | HK | html | 5.83 Kb | unknown |
2960 | chrome.exe | GET | 200 | 222.186.61.189:80 | http://vj.tianji520.cn/o7_l.js | CN | html | 1.79 Kb | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/js/webaction.js | HK | text | 804 b | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/css/webstyle.css | HK | text | 2.36 Kb | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/images/search.png | HK | image | 1.46 Kb | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/js/bus.js | HK | html | 1013 b | unknown |
2960 | chrome.exe | GET | 200 | 47.106.29.0:80 | http://adx.dlads.cn/v.php?id=2035&p=aj0wJnBsPTMmbT00JmY9MCZyPSZ1PWh0dHAlM0ElMkYlMkZ3d3cuenk4NC5jYyUyRmFydGlzdCUyRjUzNTEzNjcwJTJGJnJlcz0xMjgweDcyMCZ0PSVFNSVBRCU5RiVFOSVBMyU5RV8lRTUlQUQlOUYlRTklQTMlOUUlRTclQkIlQkMlRTglODklQkElRTglQTclODYlRTklQTIlOTFfJUU1JUFEJTlGJUU5JUEzJTlFJUU3JUJCJUJDJUU4JTg5JUJBJUU4JThBJTgyJUU3JTlCJUFFJUU1JThEJTk1XyVFNyVCQiVCQyVFOCU4OSVCQSVFNSVCNyVCNCVFNSVBMyVBQiZsPWVuLVVTJmM9MSZoPTE1NTgmc2U9Mg==&l=d3d3Lnp5ODQuY2M=&t=1568181534 | CN | html | 6.75 Kb | unknown |
2960 | chrome.exe | GET | 200 | 47.52.43.156:80 | http://www.zy84.cc/images/live.gif | HK | image | 1.58 Kb | unknown |
2960 | chrome.exe | GET | 200 | 14.18.204.179:80 | http://j.sdqoi2d.com/r/er_18203_7798.js | CN | text | 1.73 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2960 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 47.52.43.156:80 | www.zy84.cc | Alibaba (China) Technology Co., Ltd. | HK | unknown |
2960 | chrome.exe | 222.186.61.189:80 | vj.tianji520.cn | AS Number for CHINANET jiangsu province backbone | CN | unknown |
2960 | chrome.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
2960 | chrome.exe | 119.23.94.67:443 | 594.dlads.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2960 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2960 | chrome.exe | 47.106.29.0:443 | adx.dlads.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2960 | chrome.exe | 61.135.185.248:80 | push.zhanzhang.baidu.com | China Unicom Beijing Province Network | CN | unknown |
2960 | chrome.exe | 47.106.29.0:80 | adx.dlads.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.zy84.cc |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
hm.baidu.com |
| whitelisted |
push.zhanzhang.baidu.com |
| whitelisted |
594.dlads.cn |
| unknown |
vj.tianji520.cn |
| unknown |
www.google.com |
| malicious |
api.share.baidu.com |
| whitelisted |
adx.dlads.cn |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |