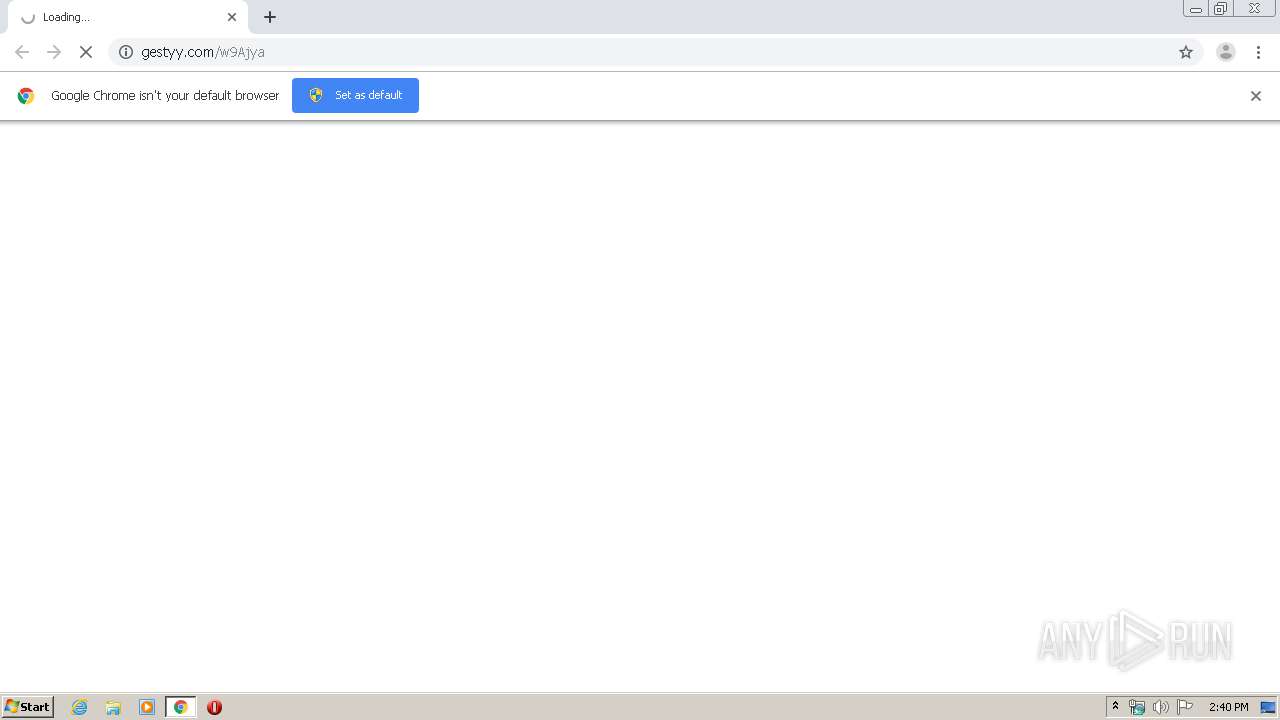
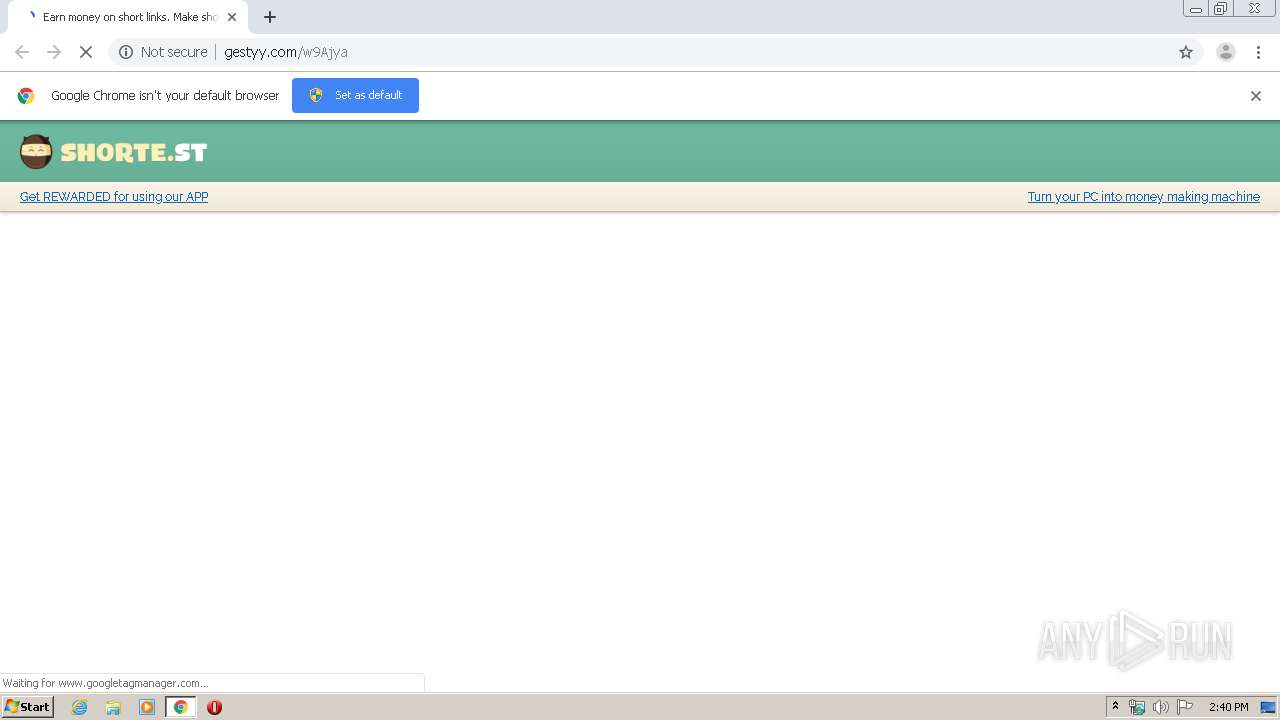
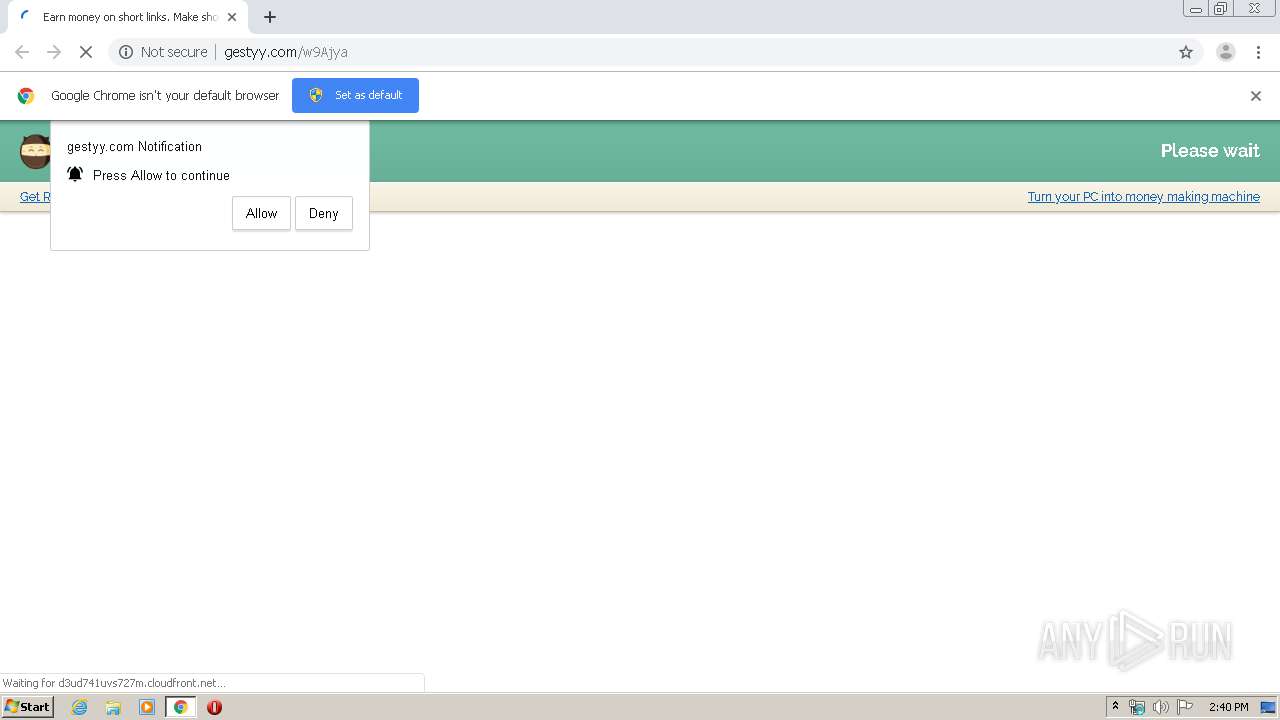
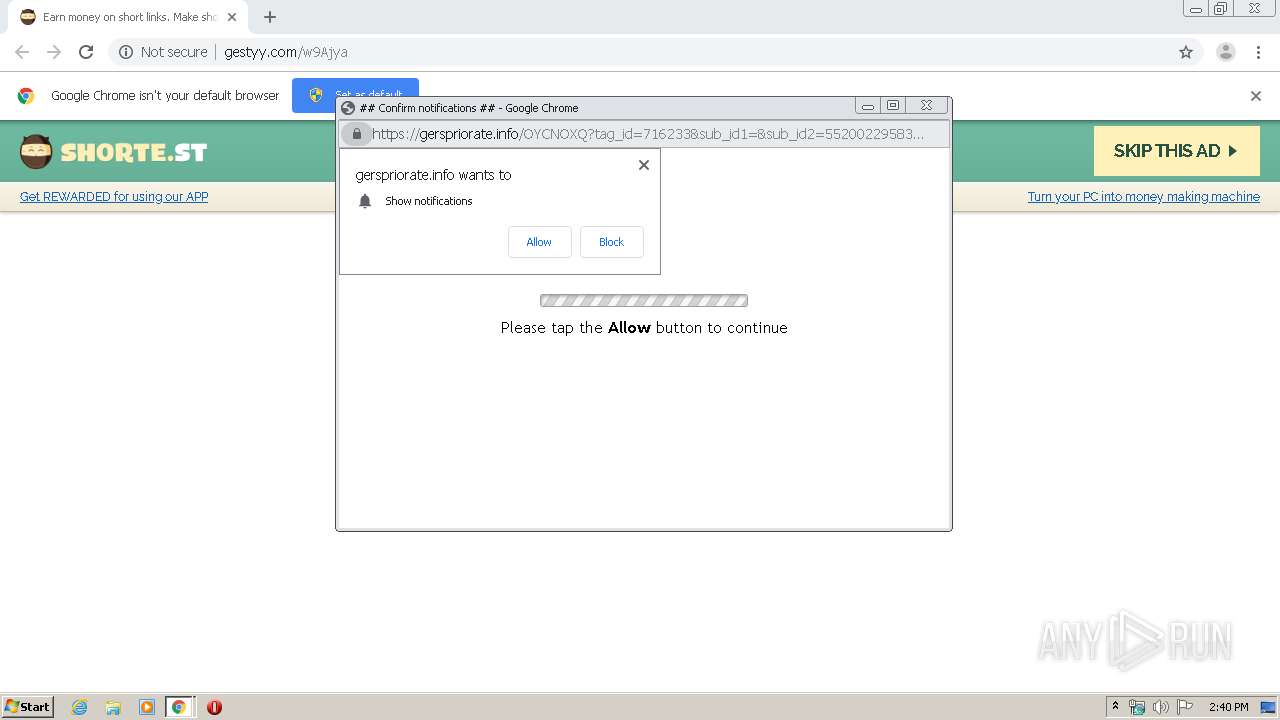
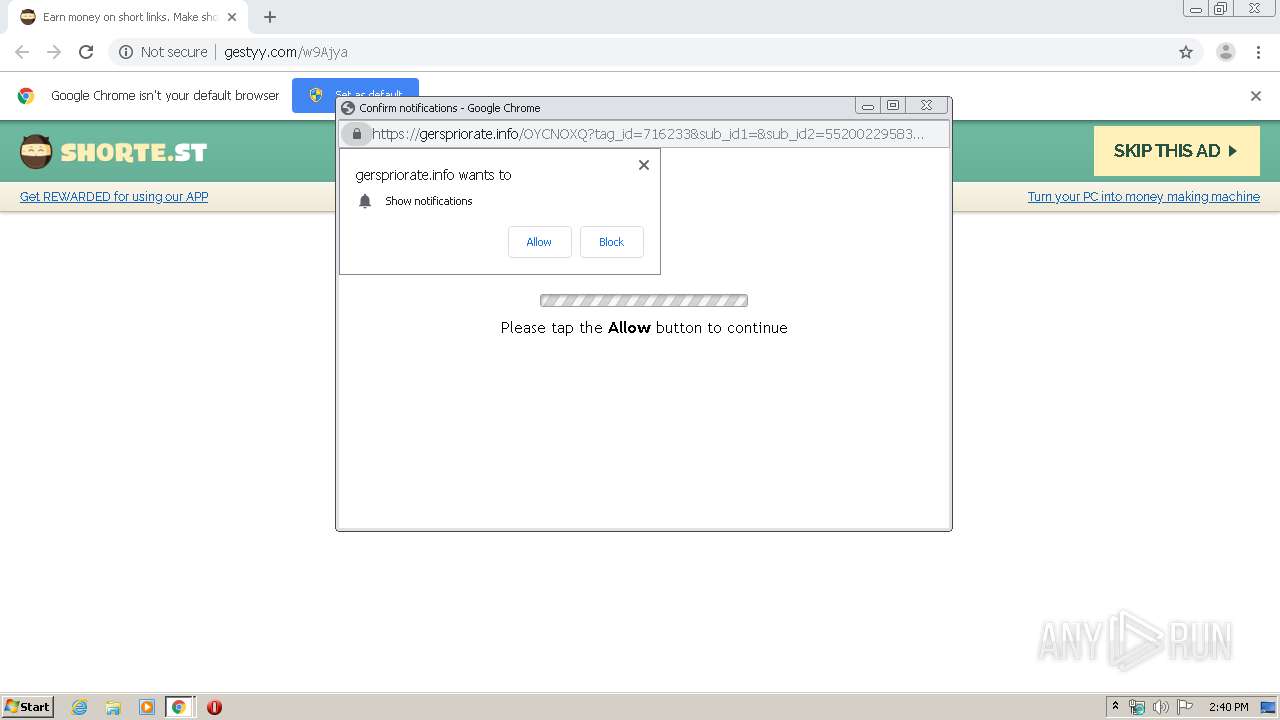
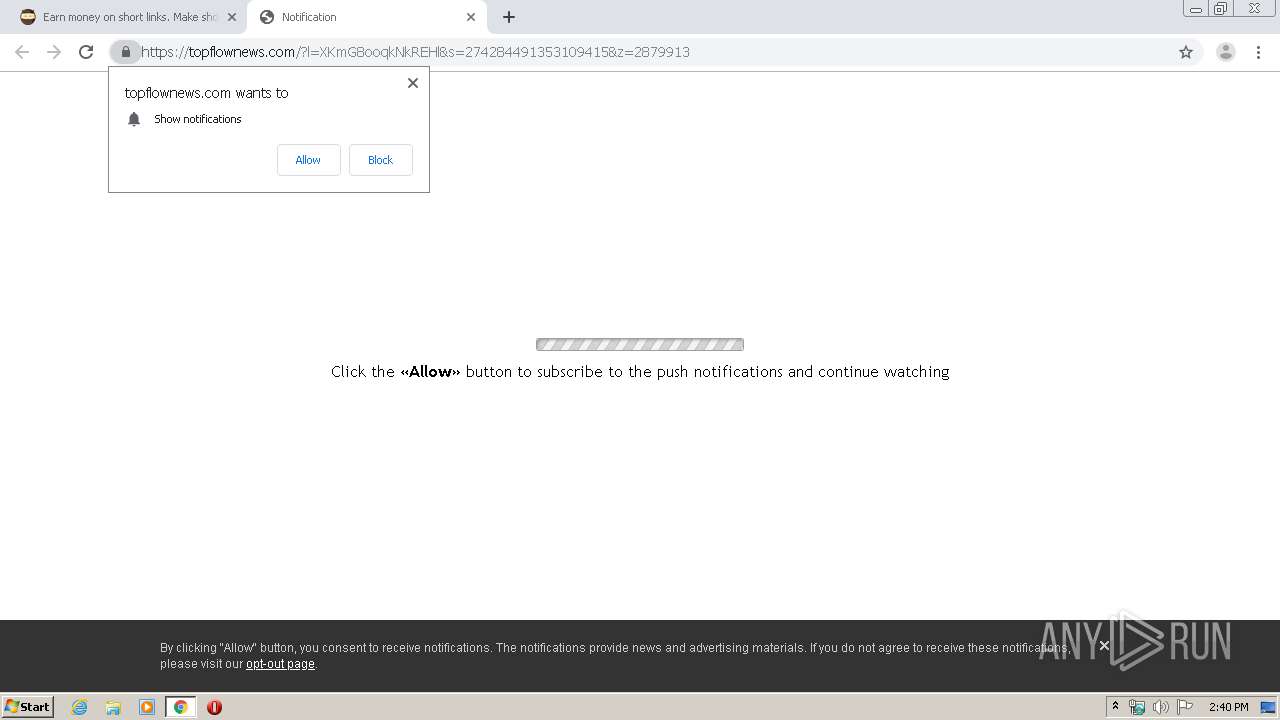
| URL: | http://gestyy.com/w9Ajya |
| Full analysis: | https://app.any.run/tasks/ad808fc0-1630-4380-b3d3-49411eba4738 |
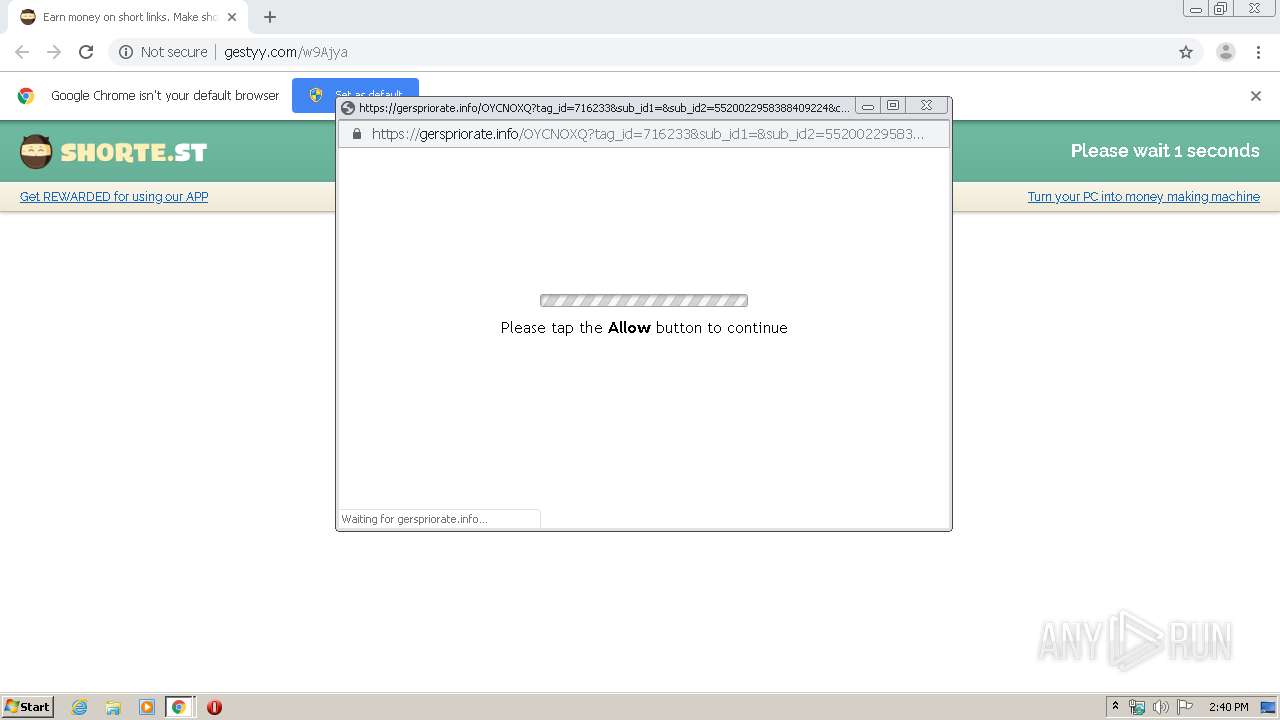
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2020, 13:40:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 15483133983FC1B1478625ED27F1CC2E |
| SHA1: | 1BDC91F64156B89599406F8386CA81FF85911713 |
| SHA256: | 190799560F6A39F812C0A7FA0A4F2778979CEAB2213BAAC87549113930352321 |
| SSDEEP: | 3:N1KZAWd8PcE:C+W0cE |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3568)
INFO
Connects to unusual port
- chrome.exe (PID: 2564)
Changes settings of System certificates
- chrome.exe (PID: 2564)
Reads the hosts file
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2564)
Application launched itself
- chrome.exe (PID: 3568)
Reads settings of System Certificates
- chrome.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=778596176907901084 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5172959958631125564 --mojo-platform-channel-handle=5000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13424668402649882982 --mojo-platform-channel-handle=4152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15071630158865028382 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6628180861109661679 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4986964358390400362 --mojo-platform-channel-handle=4316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6904957169900843348 --mojo-platform-channel-handle=4768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6285526904393730635 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,9069557501441370082,9359776707259855246,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4807169353995582322 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
864
Read events
773
Write events
86
Delete events
5
Modification events
| (PID) Process: | (3308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3568-13231431619481375 |
Value: 259 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
105
Text files
269
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E970EC3-DF0.pma | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0c77d3ac-ae70-42a1-9f3c-e3ee1ce5d7b5.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6e046.TMP | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa6e065.TMP | text | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e1dc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
146
DNS requests
73
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | chrome.exe | GET | 301 | 104.16.107.25:80 | http://remarypolike.site/popunder.gif | US | — | — | suspicious |
2564 | chrome.exe | GET | 301 | 104.16.107.128:80 | http://extrementtgfa.site/QU1pbUMgLwoAfCBwC0s2MyFUSHEHaFsrJ3I4DVp3cDgfHnRzegRDIC0iHAklMyIHGW0vKB1IcQcoCjpyKB49LBAAKh4bBzYYLC8tEAU4KzcQKA4jGwM1LAAbJgs4IAJwCio/MBErBTsCCR8oJgIpJSUrKQ8YPSs7BAc/KCUCIVAbFRN1JjVwJhosLCgAKSg/GwYfIAAUcTotLDoXFyssDhMEP10FEjUKAgcTOioqAAMuITw7CShaNwYQfCMeAioLLysQAygvPAoXAgE7BxkcHlQFFAMNOwQiDz4oKxAoPygBCRxdHhE5HDkuEAMIPyt7KisoIwQQfEQrZnMLLzgNJR4AJxoDHCgiIQAEED4FA3gxLyQGD1saABAcBiUILT4MPwYleigvCgcIKjcnBwgBPAc2KSw8cgsjKF0ZIBgEDgEQG1glJjYMKikCECI4BSsIGChVBRAhGSAmJhcxKgV4eysGKxQPIQUUECoBOSYQKS8uBQc1PD8KDRgqHgcHG1w5JnAUOC40JXo8CmUrPgYDM3wfLRs7NyBeCHIxPypfKg | US | — | — | suspicious |
2564 | chrome.exe | GET | 301 | 104.16.107.128:80 | http://extrementtgfa.site/passthrough_redirect?ptru=Azm9Czr3vG0NhftHCztPB6tZDykKAe4MBG0oekqpj8Zmo6mZh80Phd96rjgGrHrMC6lSf7VUrj9MC6lSf7VUrT98qjsErdsGpjk5rHY5qda4rTs9tMqLB7JPhl0Phd8UrMmMpdlZhc99r7hUvjnErjrJpjC5hS99ren7qTw6gTnFpyrMBza0By0ZhyVKhGhOB6a0qGhNhe10n9Y%3D&ptrv=eHgEqHs4qGEFpc54rjw9rTrEqdgGpdk8rSESqjkGrdaGrTU8pdr5pdnEpjsGqcsIqTaFvdnIsUqssSE6rjgGrHrIqTa7pdw6vy48ByEIBNlIBcEFpc54rjw9rTrEqdgGpdk8rSESjllrlwUSvy48ByEIBNlIBcFKDeFIvdaIBNlIBcFKDeFIvctNhfq9WfUKg70JsSESBexRhibHAy0GDykYhexGBSbHAy0GDcbIAe4RCGbJB74VWisIBNlIBcEEvTaIBNlIBcEFvTaIBNlIBcEEvyhZBzqVvcs6qSsIsTwKrc59rc59sSESnUlbj7xSg7lMqNs9h7VRhHaFly4FsSFKDeFIvy48ByEIqcEHriFKDeFIvy48ByEIsMl5DztVBelKDzmNhMwKC7V9hisIsNlKA74LD75SvzmGDekIhMxIC7kIBNlIBcEFrTr6rHr7rdg9vct2fctPhxESpVEShdtUhTY8genJqdqMhc99rdwHvjU6pygJqdxUqTgFq7s9rjZTfcsIfctIDVESpTaIfctMDVESpTaIfctIg8ESpTaIfctSByqCsTOEvxEShNtVClESpTwIfctPDMhGhfxCsTOFvxESDyhGhfxCsTOFvxESCy0EB7qCsTOEvxESg7xJCyxPh74Hf78ZCxESpNJ0vxESg7xJCyxPh74Hf6hPhfDXBexEfcs3W69IfctTCyqXgemXg708BNmGWl0JgfbCsTP2XiFCsNmZh6qXg708BNmVCV0JgfbCsTP2XiFCsMqZBfbZAeDKC80TB6lKDylGf78ZCxESpNJ0vxESg7xJCyxPh74Hf7qZDx0TB6lKDylGf78ZCxESpNJ0vxESAfhXg6bTf7xUf7qLDe49CNVXBexEfcs3W69IfctPDV0ZhzhXg708BNmGf78ZCxESpNJ0vxESAfhXDyxNC80TB6lKDylGf78ZCxESpNJ0vxESAfhXg7xJCyxPh74Hf7qLDe49hftXBexEfcs3W69IfctPDV0Tge8EgeVNBNqXg7x9f7qLDe49hftXBexEfcs3W69IfctTCyxXg7xJCyxPh74Xg70KDMlGC7VLBV0JgfbCsTP2Xf9SvdaKrcESgMn5gHr4hSsIsTw8rdk9qTU6qdrSvy48ByEIriEEvTaIriFKDeFIvy48ByEIqGFKDeFIvcsEsSESmyx9geqZBfaYjyVJAfmVhcsIrcEFvc9FvdaIsVP8CMVTAcsIBNlIBcESrHr5qHn8qdsErl15vTaSvc9Fvy48ByEIriEFvdaIBNlIBcESqGsIsNDPBMmLD6rSvctUhfqRDy0EsSESvjw6pjC5rda7rjaSvcsJqjg4qTkGqdY8sSESrjw4pdU9rHk9pcsIBNlIBcFKDeFIvy48ByEIrSESDHVbANVZsSFKDeFIvcsEsSFKDeFIvc9FvctjvHa4v8ZAlVPeBSJmrjsHqdlii9ESvctVBSsIBNlIBcEEvc9Fvc9FvTaIqGFKDeFIvctwhfqRDy0EsSFKDeFIvy48ByEIsNZNgM0LC6mXWdsEsSEFrcEEvdaIrcEFqjY7pjk5rds9pda9qjUEqjUGvdaIBNlIBcESmlkSvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcESrcsIBNlIBcFKDeFIvy48ByEIBNlIBcE6vy48ByEIBNlIBcFKDeFIvdw5vTUFrjnGrHa9qTs5qjkGvy48ByEIBNlIBcFKDeFIvy48ByEIrc5EvctUrMmMpdlZhc99r7hUvjnErjrJpjC5hS99ren7qTw6gTnFpyrSvcsGrdsEvja9vjw8sdwHpTnEpTs8sSESrcsIBNlIBcEGvdwIBNlIBcFKDeFIvcs6qisIsMqZBfbZAeDKsSEEvdCIBNlIBcFKDeFIvyhZBzqVvy48ByEIrc5ErjY4rjw9rTrEqdgGpdk8rSFKDeFIvcs7qHqTqMsEpjxShMrGgjCGgjU4rdnGrMmZqdtUqTUGqisIBNlIBcEFvdwIriEFvy48ByEIBNlIBcFKDeFIvy48ByEIrcEEvy48ByEIBNlIBcEShdnFhdZThdU5hTaEgTsEqyk4pdaEpjU5heqMpdnGq7kSvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcFKDeFIvdaKrcFKDeFIvy48ByEIrc5Evy48ByEIBNlIBcFKDeFIvy48ByEIrTg8qHY4qSFKDeFIvy48ByEIrcFKDeFIvdaIriFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIrcEFvdaIriFKDeFIvy48ByEIBNlIBcFKDeFIvy48ByEIBNlIBcESn7ZGB78VsSESl7VKhy06CGsIBNlIBcFKDeFIvy48ByEIBNlIBcEEvTaIBNlIBx9%3D | US | — | — | suspicious |
2564 | chrome.exe | GET | 204 | 206.54.165.186:80 | http://unelekidan.com/fac.php | NL | — | — | malicious |
2564 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://gestyy.com/bundles/advertisement/img/tracking.gif?test=528e868e45921121e6d667608013989f47452ed3 | PL | compressed | 43.8 Kb | malicious |
2564 | chrome.exe | GET | 200 | 143.204.101.165:80 | http://d3ud741uvs727m.cloudfront.net/?vudud=716233 | US | compressed | 36.6 Kb | whitelisted |
2564 | chrome.exe | GET | 200 | 88.85.82.189:80 | http://deloplen.com/tag.min.js | NL | text | 22.9 Kb | whitelisted |
2564 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://gestyy.com/bundles/smeweb/img/advertisement-tracking-9454747.gif?t=1586958021 | PL | image | 43 b | malicious |
2564 | chrome.exe | GET | 200 | 78.140.188.190:80 | http://static.sh.st/b5/4c/45/48/be/0d/ca/35/64/1c/e2/75/9d/8f/9e/2c/logo1707.png?2020-02-19.0 | NL | image | 6.08 Kb | unknown |
2564 | chrome.exe | GET | 200 | 78.140.188.189:80 | http://ads.shorte.st/notify.php?key=2ea5b261f06ca771033a5fa9e22493f1&width=1024&height=768&ch=9454747&cp.dest_domain=vnexpress.net&cp.oid=9454747&cp.referrer=&cp.locked=0&cp.proxy=0&cp.quarantine_status=1&cp.vno=1&cp.enc_url=PUJVtBnPscmGL4F5mMx5oBdTbNf8X0dsWeAjkjZ0dok2Xbq0q2oPYdMenygXebxO+KseB8z4VtLSPGc2K4pc2M0uDpcNVhIpFaniS6xuXus=&cp.asid=528e868e45921121e6d667608013989f47452ed3&title=&description=&keywords=&captcha_verified=0 | NL | binary | 20 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 172.217.18.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 143.204.101.165:80 | d3ud741uvs727m.cloudfront.net | — | US | unknown |
2564 | chrome.exe | 78.140.188.190:80 | static.sh.st | Webzilla B.V. | NL | unknown |
2564 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2564 | chrome.exe | 35.227.234.224:80 | analytics.shorte.st | — | US | unknown |
2564 | chrome.exe | 88.85.82.189:80 | deloplen.com | Webzilla B.V. | NL | unknown |
2564 | chrome.exe | 104.16.107.128:80 | extrementtgfa.site | Cloudflare Inc | US | suspicious |
2564 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gestyy.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
static.sh.st |
| unknown |
d3ud741uvs727m.cloudfront.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
shorte.st |
| unknown |