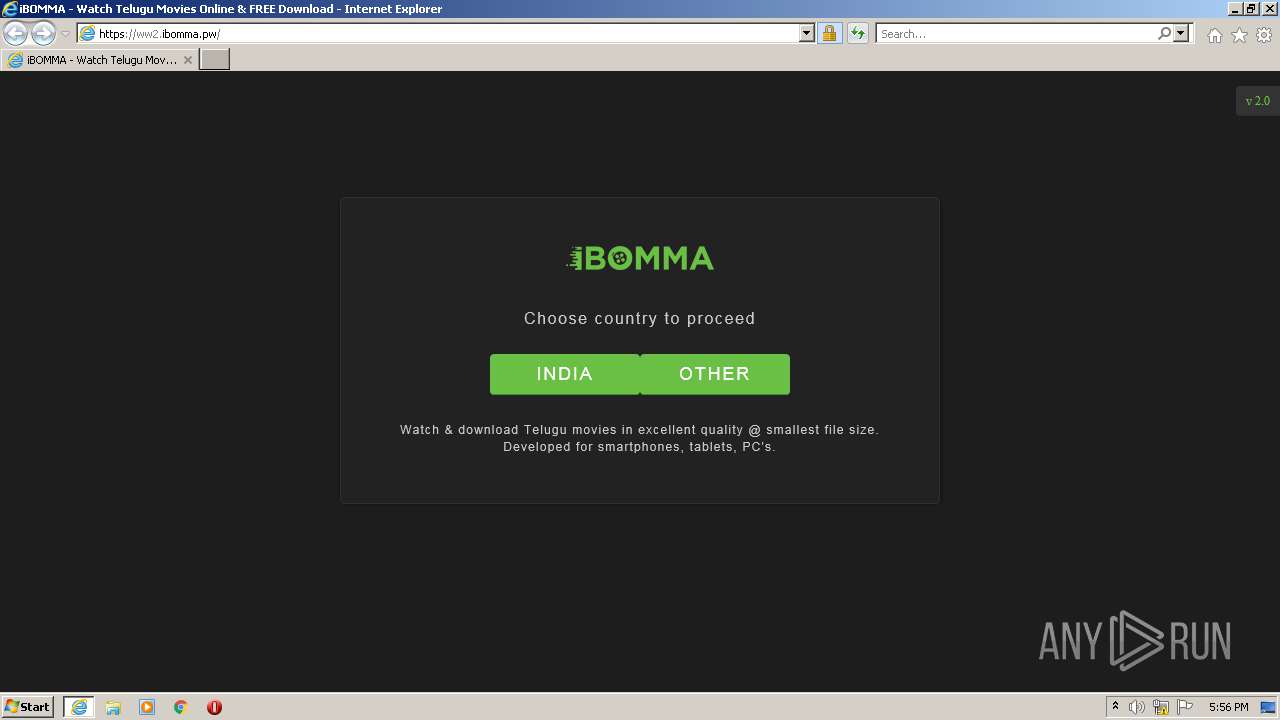
| URL: | https://ww2.ibomma.pw/ |
| Full analysis: | https://app.any.run/tasks/bbcf298d-e07e-42d1-bb1e-dd51f1052036 |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2021, 17:55:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 631570E48B70F64E9C8FD35BC0E81225 |
| SHA1: | AF351904990D4701015543C5CDB6720CC503FFA4 |
| SHA256: | 190531A15105A4A8D3CE586E433AA79E35B3EDC6C6DF5696D4F4B927F9819A67 |
| SSDEEP: | 3:N8DoH5V5:2Ed |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3696)
INFO
Reads the computer name
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 3696)
Reads internet explorer settings
- iexplore.exe (PID: 3696)
Reads settings of System Certificates
- iexplore.exe (PID: 3696)
- iexplore.exe (PID: 2812)
Checks Windows Trust Settings
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 3696)
Checks supported languages
- iexplore.exe (PID: 3696)
- iexplore.exe (PID: 2812)
Changes internet zones settings
- iexplore.exe (PID: 2812)
Application launched itself
- iexplore.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2812 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ww2.ibomma.pw/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3696 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2812 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 031
Read events
19 915
Write events
116
Delete events
0
Modification events
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 262539680 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30924545 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 562543430 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30924545 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2812) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
90
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:7394E4417F92C2AE5EB2787CE676047E | SHA256:BCB46261F8D8F04579541BEA7F3B138BFD1A05277969D539B7667A4821C64498 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:DF81576F611329E1C1AF207BE6CCDD37 | SHA256:841A636A3DC4EA5F052533E244A9EF3A99DD301E55F15559A1F19504FE25AC54 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4D18DE4674820A8F7862323651BF6219 | SHA256:D8C0FE545C2889284A192CDDB9BC222999812FA089453BF6948F698EF7DED82F | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\03533B31AAB1D1912D10B6872B9D98BA | der | |
MD5:6A05502EAC3A58427C2AC672F7D7FD64 | SHA256:749BBC760F41188372FCA86E9EFF1972C78EDED6A9F73DA9951949026D1CAE89 | |||
| 2812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:E19C7CB9D5BDDEB3CA7042622FAF7061 | SHA256:C86C4A4EAE3E2A08A0A0A2DBBA46BF1533B23B8D741B533A451A9BC72C435175 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\03533B31AAB1D1912D10B6872B9D98BA | binary | |
MD5:9491D1F546454C205E1EB7415EE69C70 | SHA256:C90B1012CB8A871D7FBDB8C887E202654BA0263D0F26AFF0799CE6A094CCF4F7 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\KK932QD7.htm | html | |
MD5:2E61C10CA88F2EE4BBADFF830431D911 | SHA256:3954826587CAE4C30126D9BE52A1BC21130AE7EAC71FAC4BAAFF31D100DBADC4 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:B395E885A5A78E19FC5648CF735D9FCD | SHA256:923A7F83645CC7AF03B56EB491A5770B7393CF406B1D3A214D2EA2004D957475 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\0meOCEUoKgo14MKOaenxF7MWpbk[1].js | text | |
MD5:807F6567D104B5F5D8C8BAAB7FEE8711 | SHA256:2183F7D1AD4851A144F3EFD16C836488D4BA82F40DD65B2A7159FCB04D3D5CE8 | |||
| 3696 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:09B8543D3C8C6AEA4C4FE3C047F362DF | SHA256:B11D44C7049297F3359CCEB85A6D71A09D2BF1936A08AA53C8C3C7A014BE77DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
33
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3696 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 23.32.238.26:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTJFyfMheGl%2BHWWzCZYbG29oQ%3D%3D | US | der | 503 b | shared |
3696 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.40 Kb | whitelisted |
2812 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2812 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3696 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f4f7152d0870c8cb | US | compressed | 4.70 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?96703f3b2718fa57 | US | compressed | 59.9 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a985983c38adb1da | US | compressed | 59.9 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3696 | iexplore.exe | GET | 200 | 8.248.141.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?588f186eccf412d6 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3696 | iexplore.exe | 172.64.166.21:443 | ww2.ibomma.pw | Cloudflare Inc | US | unknown |
3696 | iexplore.exe | 8.248.141.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3696 | iexplore.exe | 23.37.41.57:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3696 | iexplore.exe | 23.32.238.26:80 | r3.o.lencr.org | XO Communications | US | suspicious |
3696 | iexplore.exe | 104.21.67.2:443 | my-bucket-s3-ap-east-amazonaws.lokicdn.com | Cloudflare Inc | US | unknown |
2812 | iexplore.exe | 104.21.67.2:443 | my-bucket-s3-ap-east-amazonaws.lokicdn.com | Cloudflare Inc | US | unknown |
3696 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2812 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2812 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3696 | iexplore.exe | 151.101.2.114:443 | ssl.p.jwpcdn.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww2.ibomma.pw |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
my-bucket-s3-ap-east-amazonaws.lokicdn.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ww4.ibomma.pw |
| suspicious |
ssl.p.jwpcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |