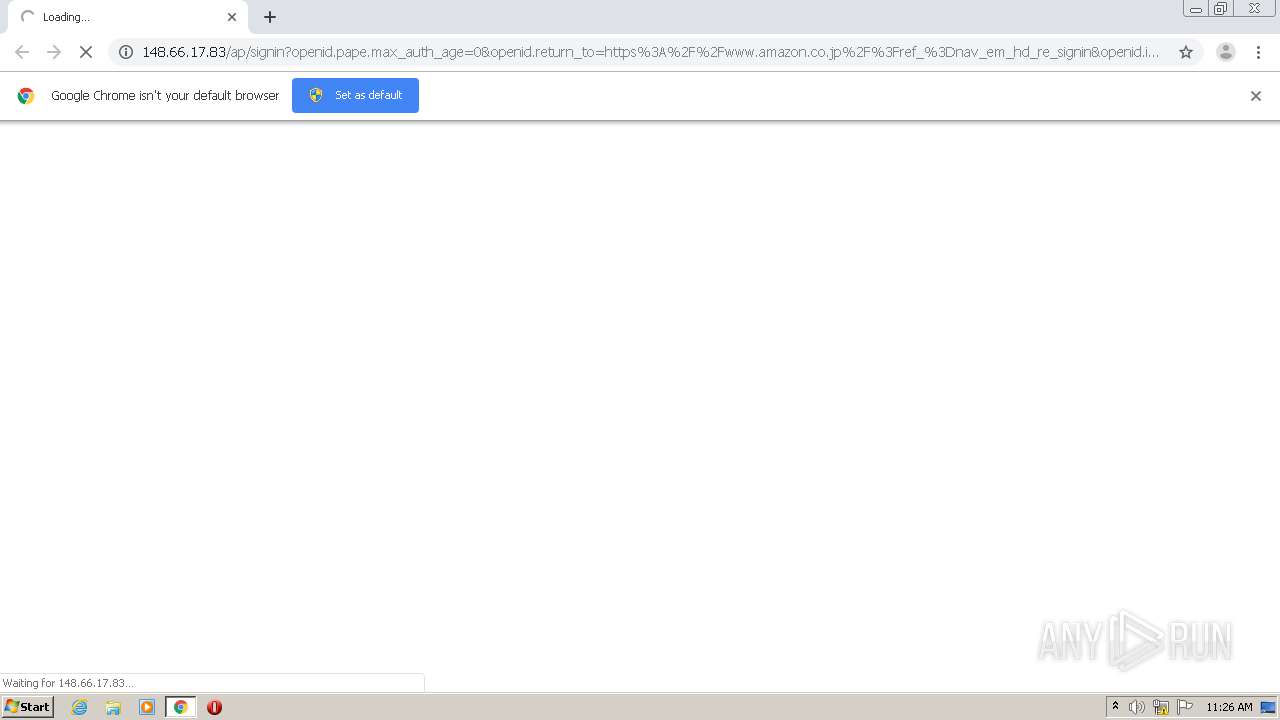
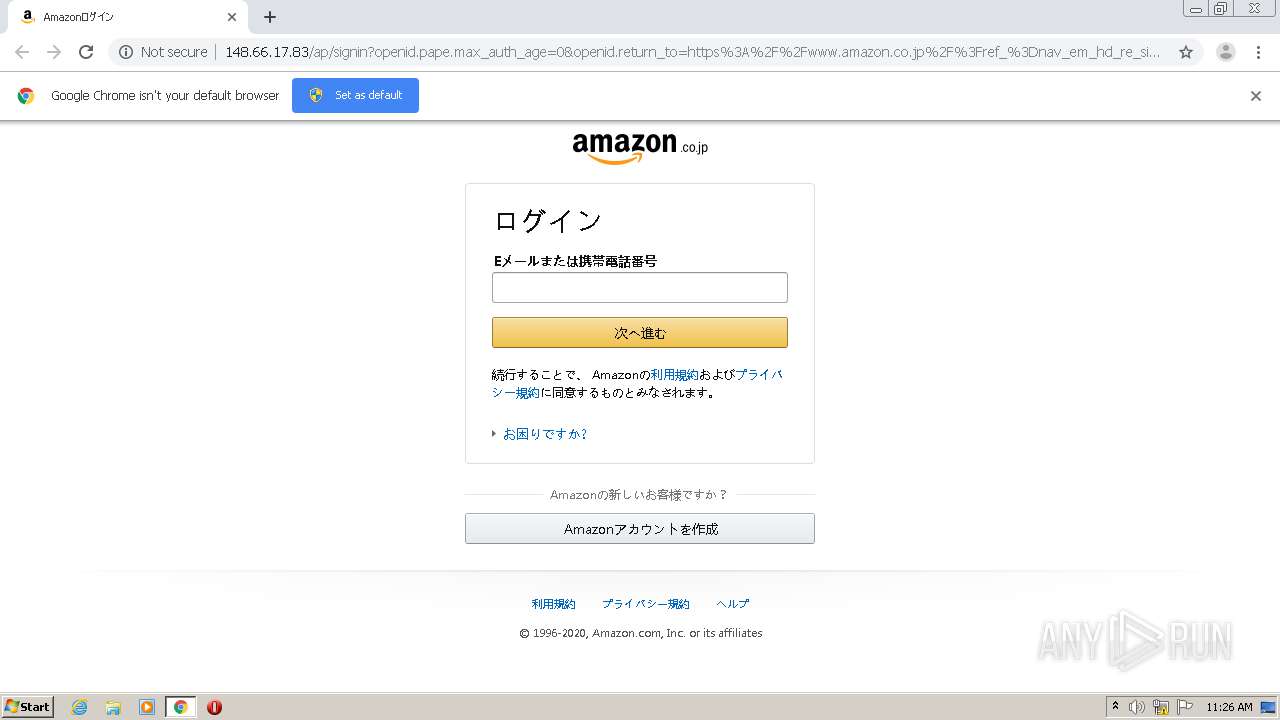
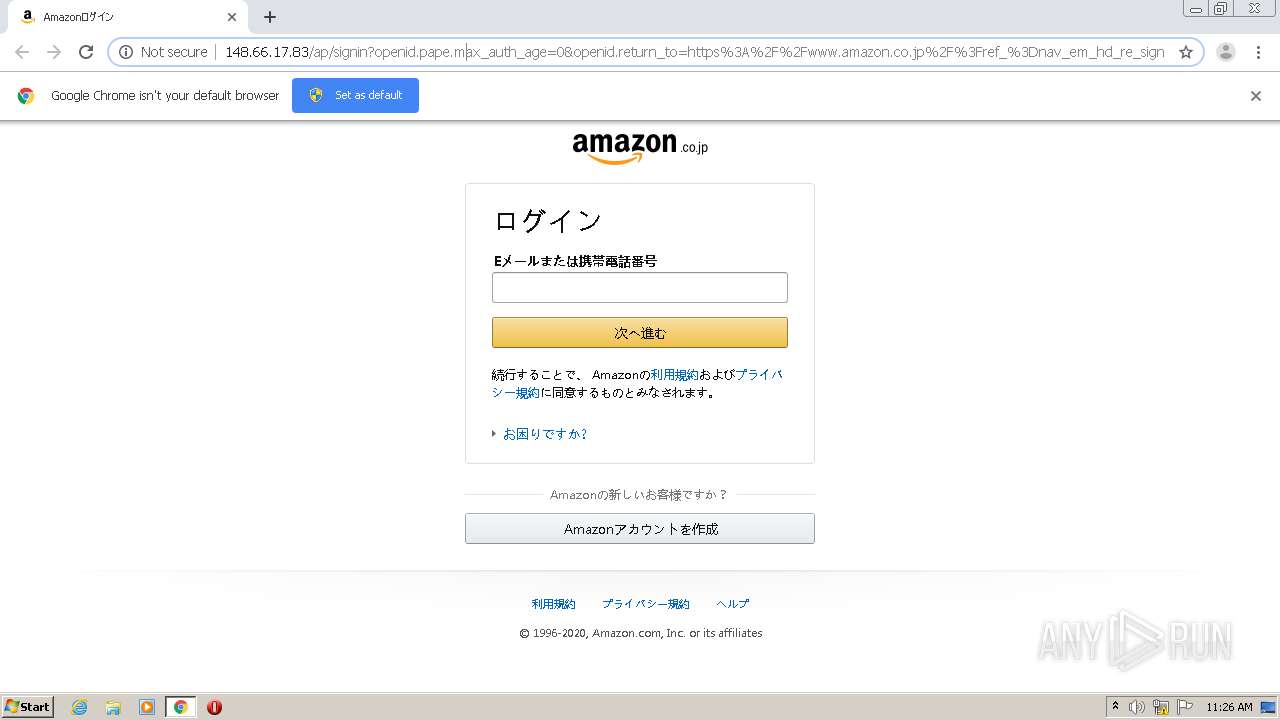
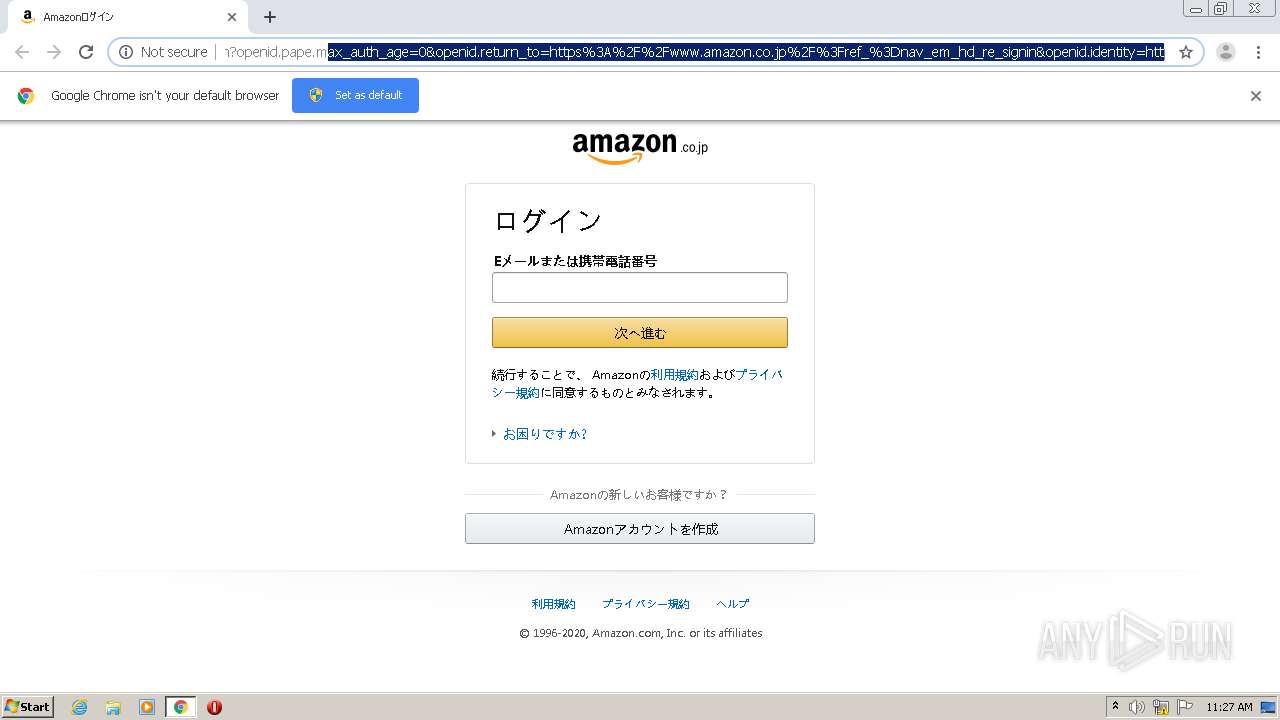
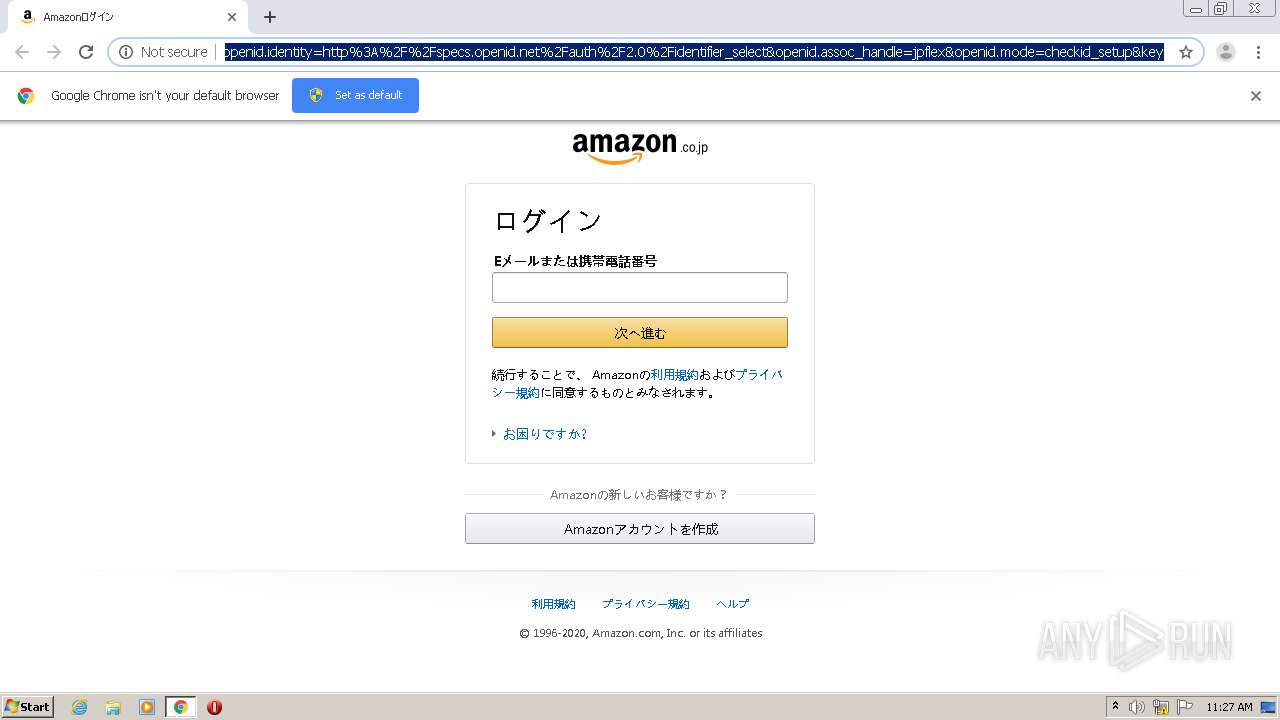
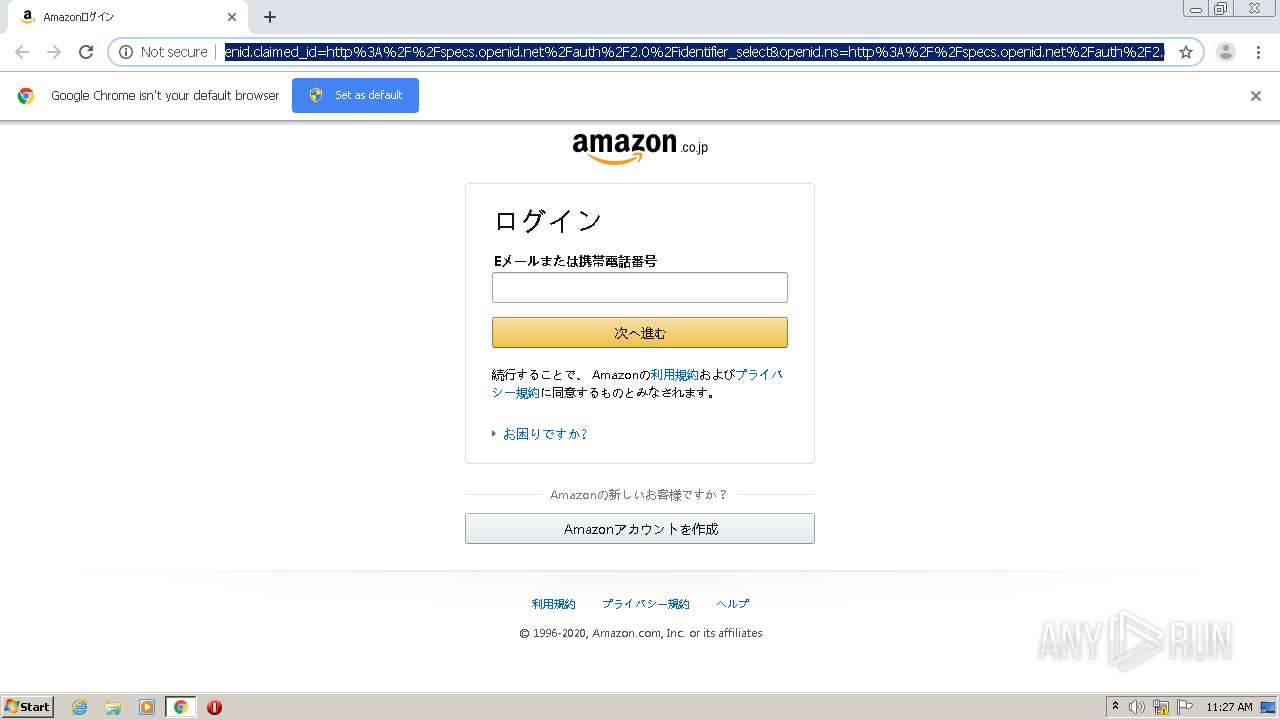
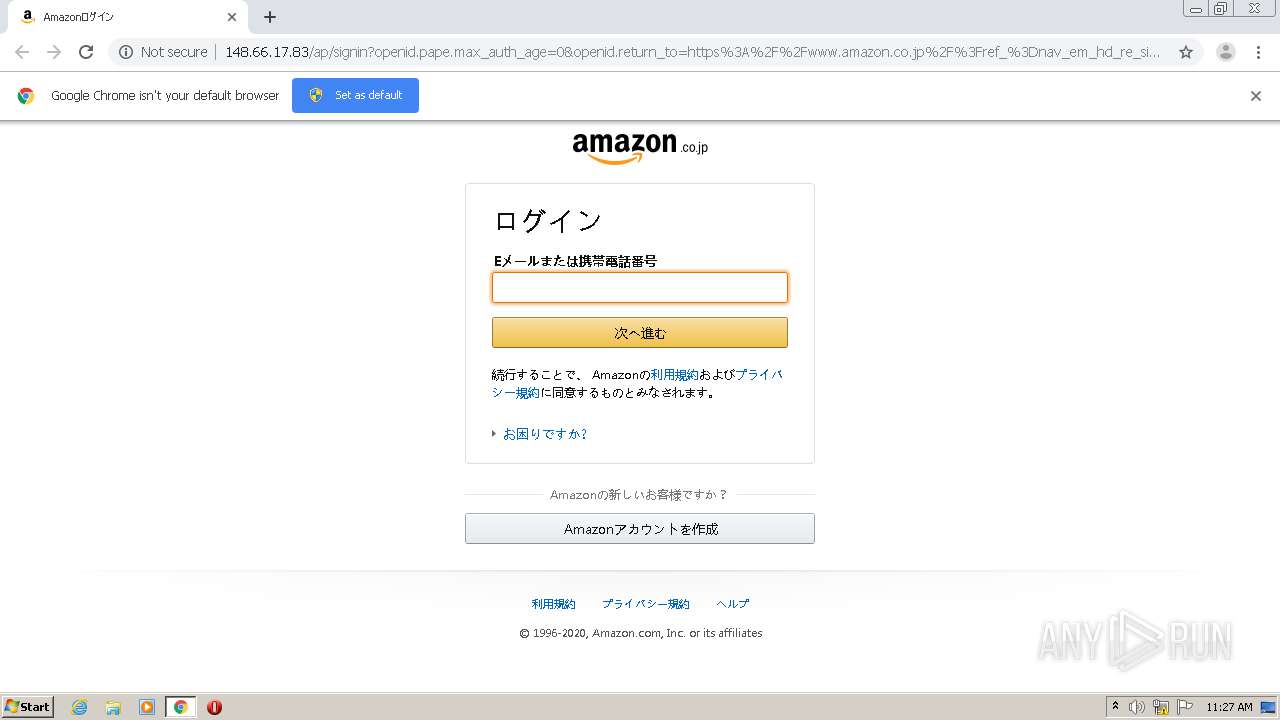
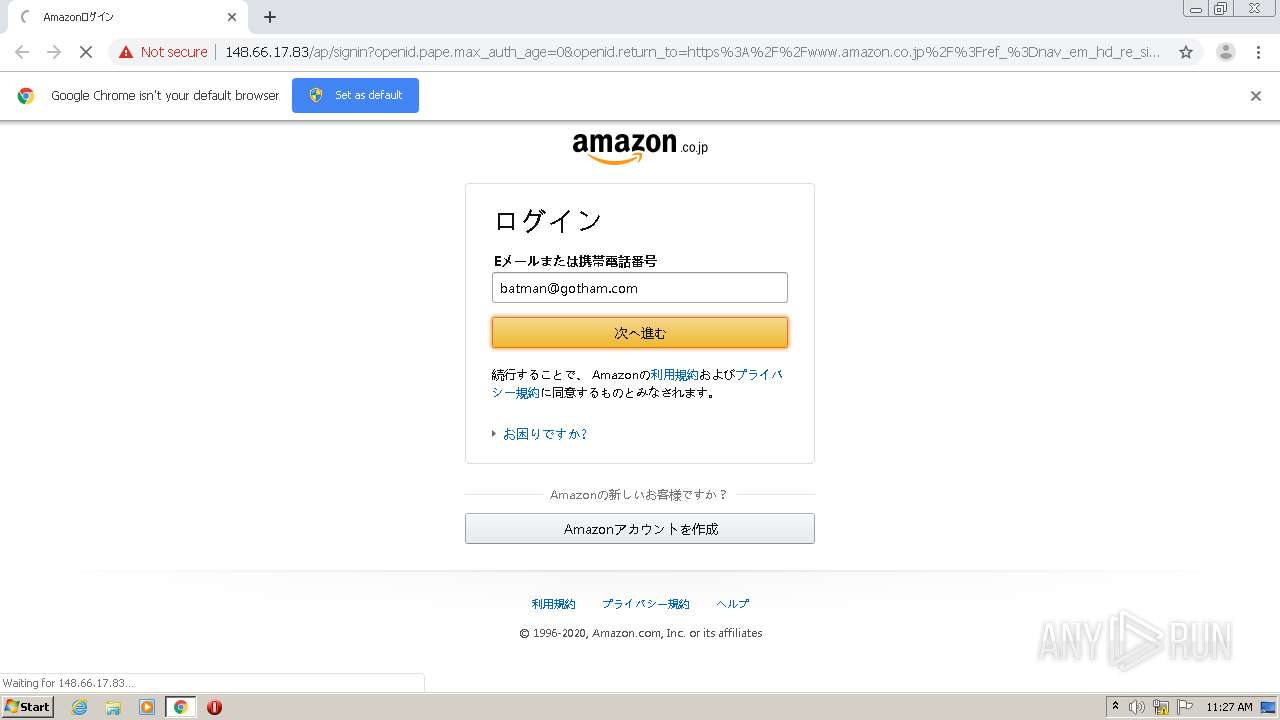
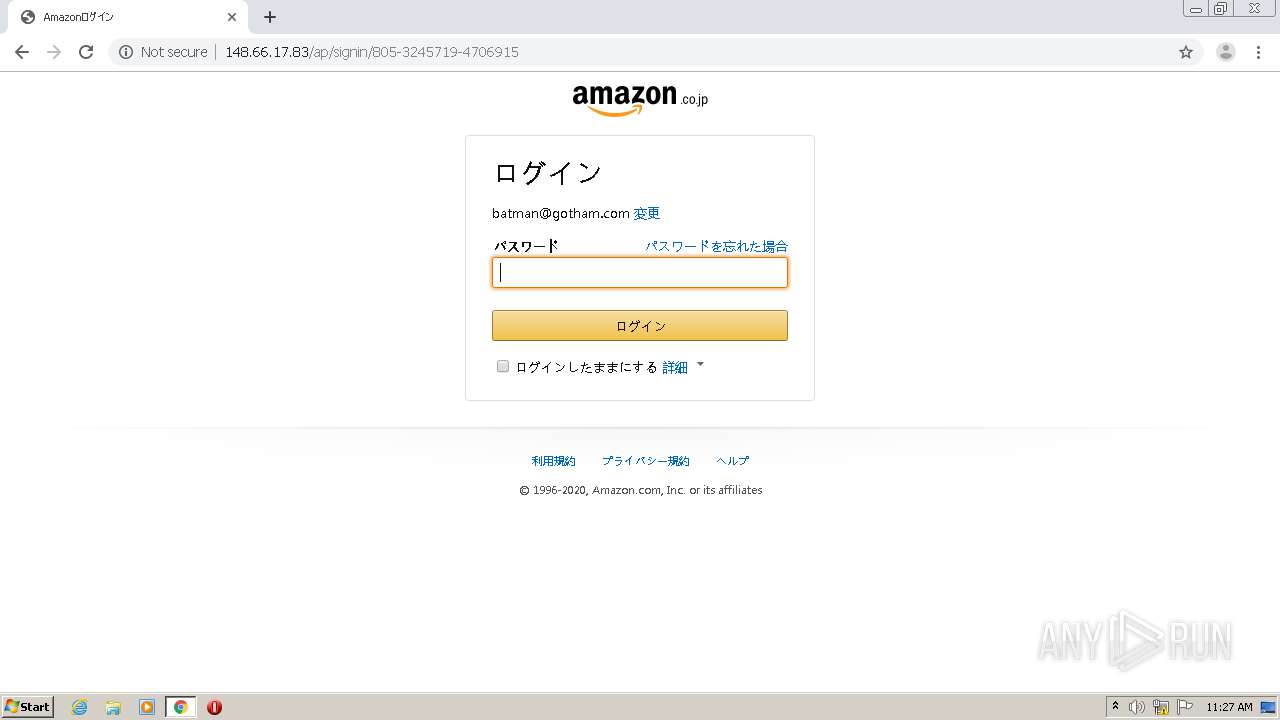
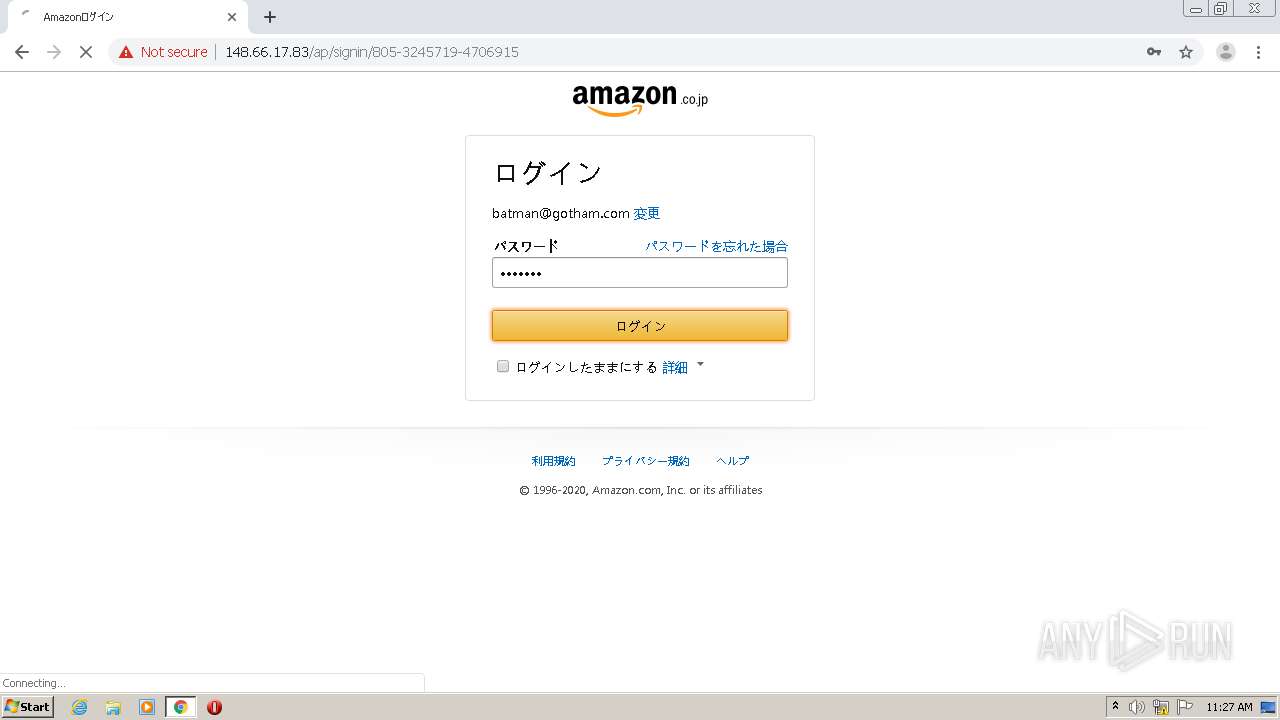
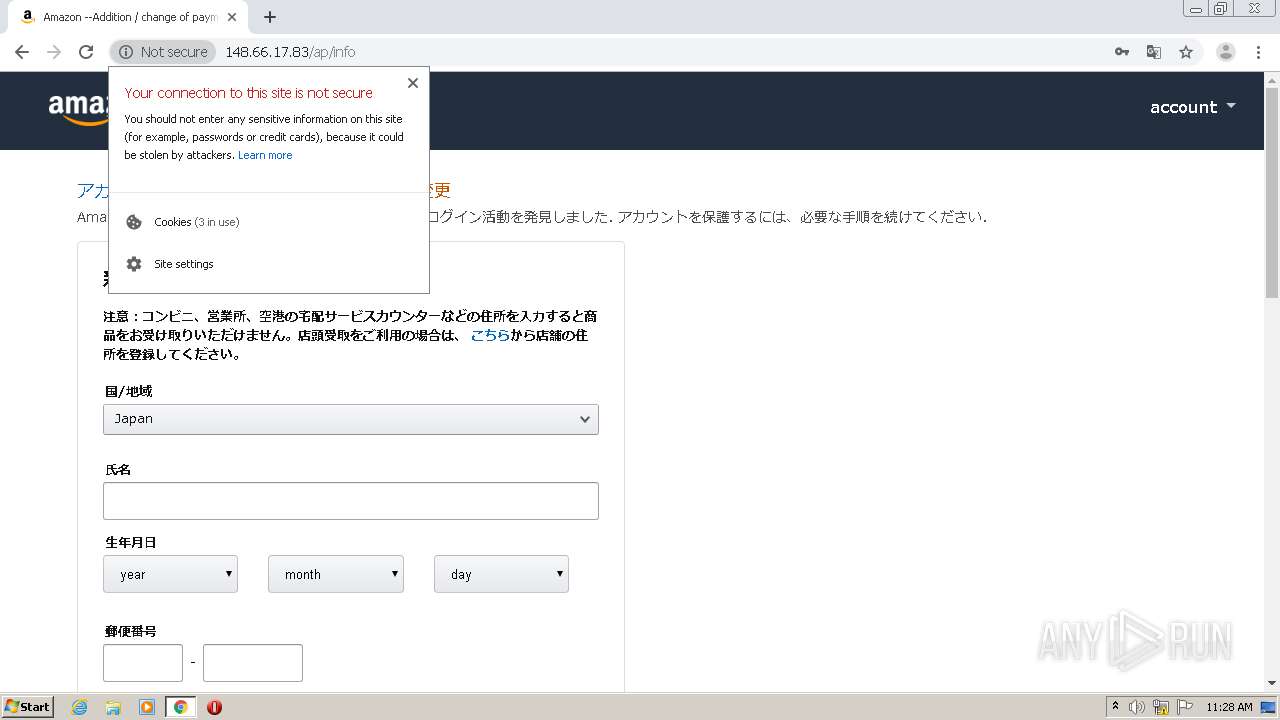
| URL: | http://148.66.17.83/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin |
| Full analysis: | https://app.any.run/tasks/ffeaee7b-c765-4de5-a9f6-b288c8bc95d0 |
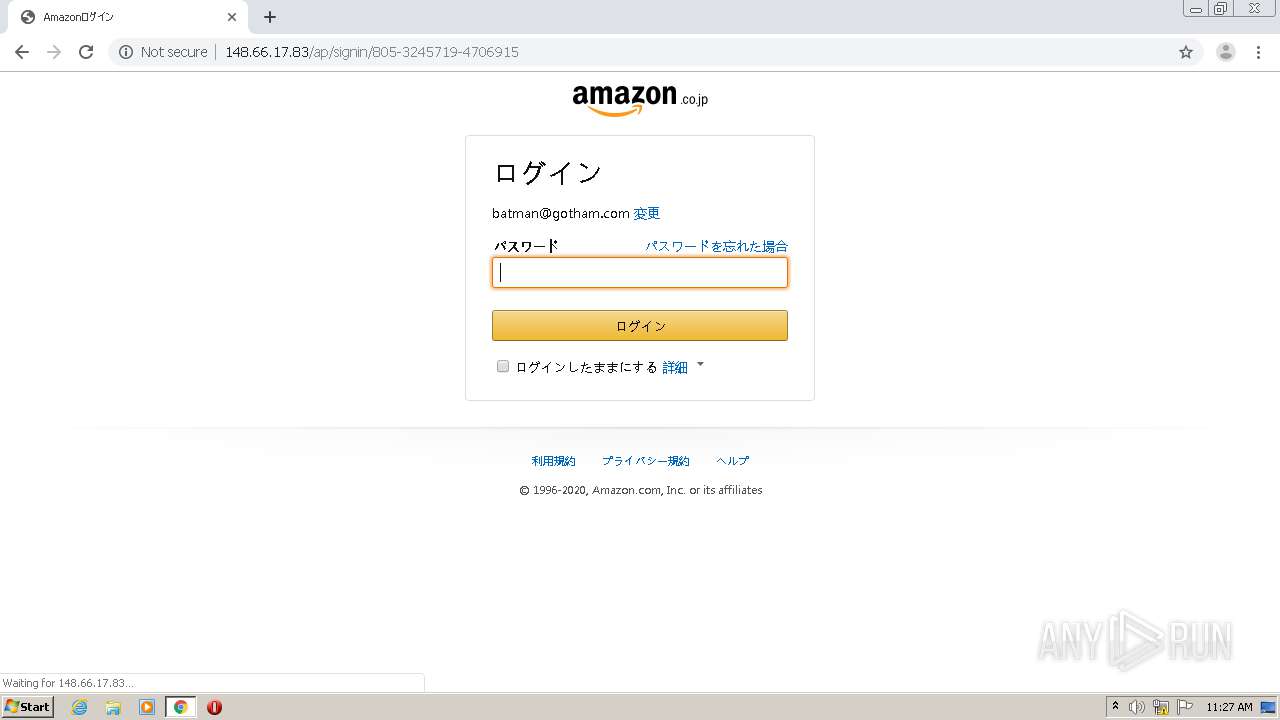
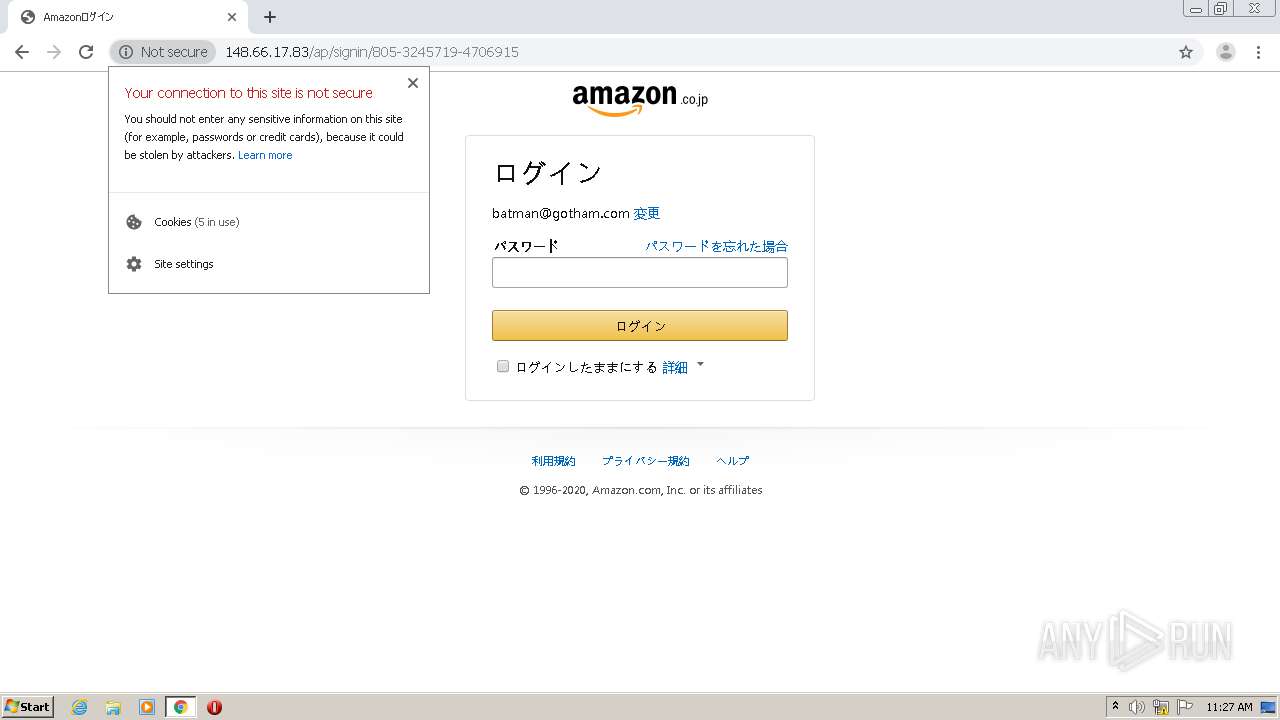
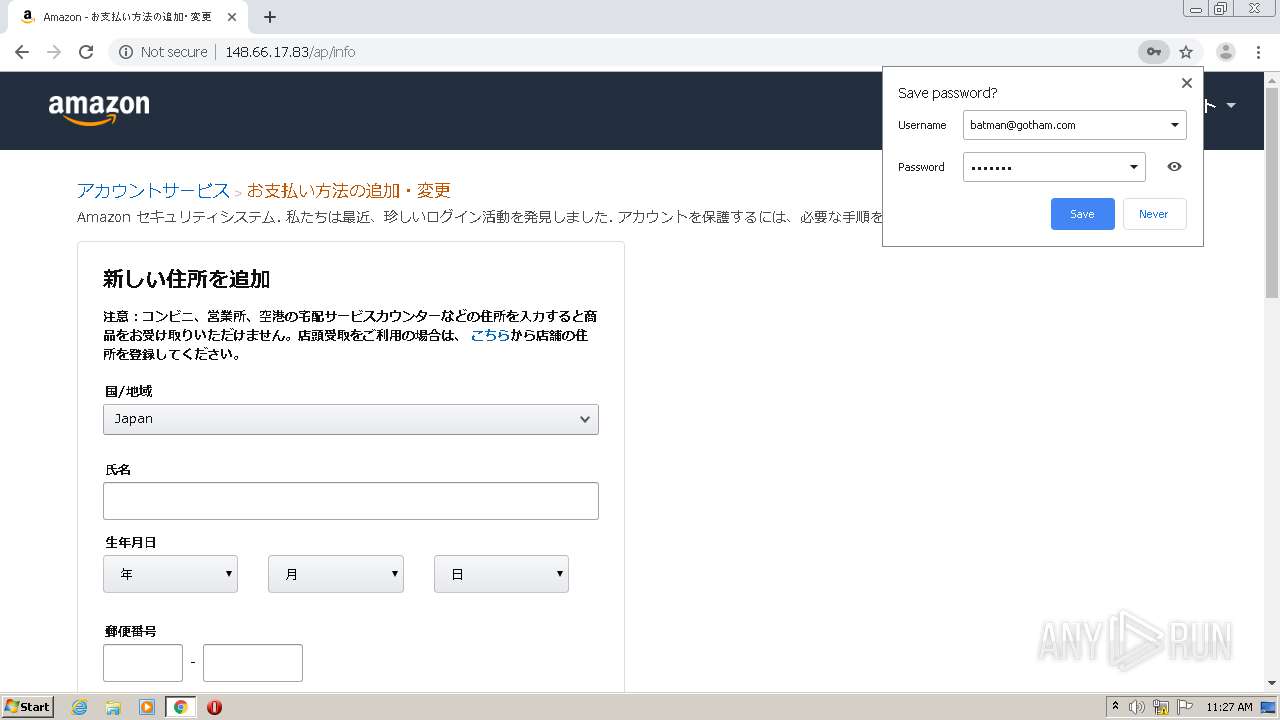
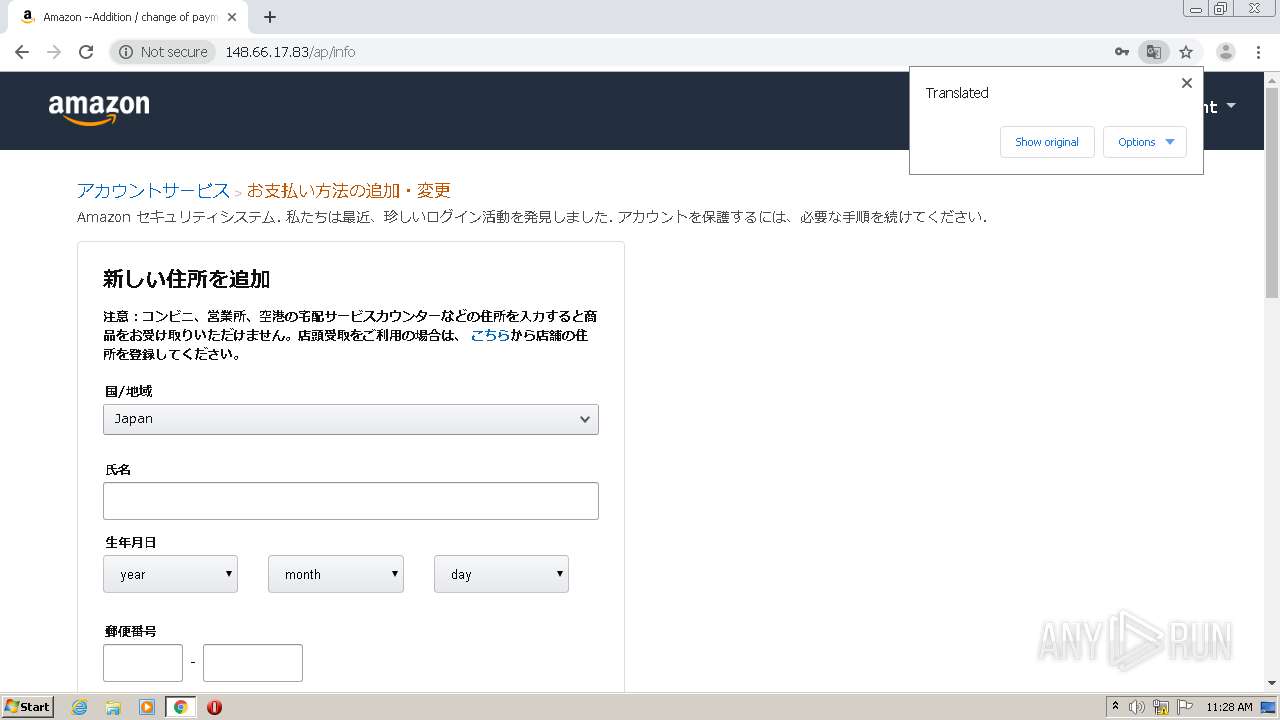
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2020, 11:26:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0E2652C7B73E0465FEC91EEC19353B8C |
| SHA1: | 06F44D36E516D4A518455BC2BBA10B1920D0E738 |
| SHA256: | 18FE44136DADFB136747D4C34EA26DD9513D65967102EEEE494E4699409ED4EB |
| SSDEEP: | 12:STNnt3Oc8Q2LKS4HsQupmokihAtUs3QxysQupmokihAtUVdsQupmokihoOW6n:4Ntr8Q5SU6oilsP6oilD6oiqUn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Connects to server without host name
- chrome.exe (PID: 1352)
INFO
Application launched itself
- chrome.exe (PID: 2672)
Reads the hosts file
- chrome.exe (PID: 2672)
- chrome.exe (PID: 1352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15227274036089033176 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15151623379788238859 --mojo-platform-channel-handle=3312 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9368270246244186999 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18142562416033176239 --mojo-platform-channel-handle=1484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10914408820931173027 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://148.66.17.83/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2364 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16477638402259209018 --mojo-platform-channel-handle=916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,17107673382752760653,10900108974260601529,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10894538407466479000 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bf5a9d0,0x6bf5a9e0,0x6bf5a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
581
Read events
528
Write events
50
Delete events
3
Modification events
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2672-13250258799347000 |
Value: 259 | |||
Executable files
0
Suspicious files
31
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FB6566F-A70.pma | — | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7b958ecc-4d31-4ad4-87c3-5f4f7fc66e32.tmp | — | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18d27e.TMP | text | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d443.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
25
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/ap/uedata?at&v=0.207204.0&id=8HSX8GW2CMQHB2HJV2G6&m=1&sc=adblk_no&pc=581&at=581&t=1605785206744&csmtags=adblk_no&pty=AuthenticationPortal&spty=SignInClaimCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1 | HK | — | — | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/ap/uedata?ld&v=0.207204.0&id=8HSX8GW2CMQHB2HJV2G6&sw=1280&sh=720&vw=1280&vh=572&m=1&sc=8HSX8GW2CMQHB2HJV2G6&ue=2&bb=138&cf=204&be=207&fp=200&fcp=200&pc=456&tc=-5805&na_=-5805&ul_=-1605785206163&_ul=-1605785206163&rd_=-1605785206163&_rd=-1605785206163&fe_=-5789&lk_=-5789&_lk=-5789&co_=-5789&_co=-5789&sc_=-1605785206163&rq_=-5014&rs_=-14&_rs=190&dl_=-8&di_=243&de_=243&_de=244&_dc=456&ld_=456&_ld=-1605785206163&ntd=0&ty=0&rc=0&hob=1&hoe=2&ld=456&t=1605785206619&ctb=1&rt=cf:3-0-3-0-1-0-0__ld:10-5-3-0-2-0-0&csmtags=aui|aui:aui_build_date:3.19.8-2020-01-19|www-amazon-co-jp-2sc54kya23e65bcefd2kynmpjecdb2b5-com|csm-feature-touch-enabled:false&viz=visible:2&pty=AuthenticationPortal&spty=SignInClaimCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1&ui=2 | HK | compressed | 35.1 Kb | suspicious |
1352 | chrome.exe | POST | 302 | 148.66.17.83:80 | http://148.66.17.83/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin | HK | html | 267 b | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/ap/signin?openid.pape.max_auth_age=0&openid.return_to=https%3A%2F%2Fwww.amazon.co.jp%2F%3Fref_%3Dnav_em_hd_re_signin&openid.identity=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.assoc_handle=jpflex&openid.mode=checkid_setup&key=a@b.c&openid.claimed_id=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0%2Fidentifier_select&openid.ns=http%3A%2F%2Fspecs.openid.net%2Fauth%2F2.0&&ref_=nav_em_hd_clc_signin | HK | html | 35.1 Kb | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/ap/uedata?at&v=0.207204.0&id=BX2YNWXH6WZ5GBNEG08W&m=1&sc=adblk_no&pc=223&at=223&t=1605785240446&csmtags=adblk_no&pty=AuthenticationPortal&spty=SignInPwdCollect&pti=undefined&tid=8HSX8GW2CMQHB2HJV2G6&aftb=1 | HK | compressed | 35.1 Kb | suspicious |
1352 | chrome.exe | POST | 302 | 148.66.17.83:80 | http://148.66.17.83/ap/signin/805-3245719-4706915 | HK | html | 223 b | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/static/sheets/accbilling.css | HK | text | 665 b | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/static/css/warning/SheDin.css | HK | text | 58 b | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/static/aa/41+819VXLqL.css | HK | text | 24.4 Kb | suspicious |
1352 | chrome.exe | GET | 200 | 148.66.17.83:80 | http://148.66.17.83/static/css/warning/QieHu.css | HK | text | 290 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | chrome.exe | 52.33.196.198:80 | fls-fe.amazon.co.jp | Amazon.com, Inc. | US | unknown |
1352 | chrome.exe | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 148.66.17.83:80 | — | NETSEC NOC | HK | suspicious |
1352 | chrome.exe | 99.86.237.144:443 | images-cn.ssl-images-amazon.com | AT&T Services, Inc. | US | unknown |
1352 | chrome.exe | 172.217.195.84:443 | accounts.google.com | Google Inc. | US | unknown |
1352 | chrome.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 151.101.129.16:443 | images-na.ssl-images-amazon.com | Fastly | US | unknown |
1352 | chrome.exe | 172.217.16.142:80 | translate.google.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 172.217.22.106:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1352 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
images-na.ssl-images-amazon.com |
| shared |
images-cn.ssl-images-amazon.com |
| unknown |
www.amazon.co.jp |
| whitelisted |
clients1.google.com |
| whitelisted |
www.amazon.co.jp.2sc54kya23e65bcefd2kynmpjecdb2b5.com |
| unknown |
m.media-amazon.com |
| whitelisted |
images-fe.ssl-images-amazon.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
codexperience.net |
| malicious |
Threats
2 ETPRO signatures available at the full report