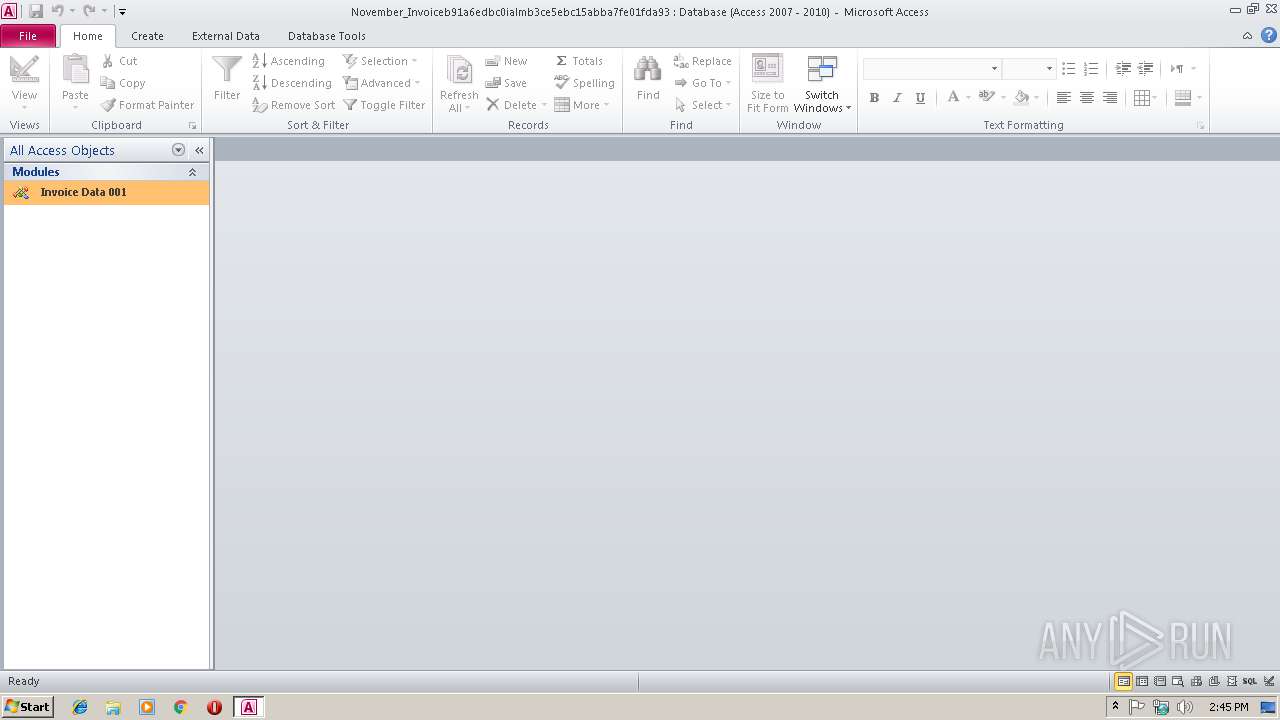
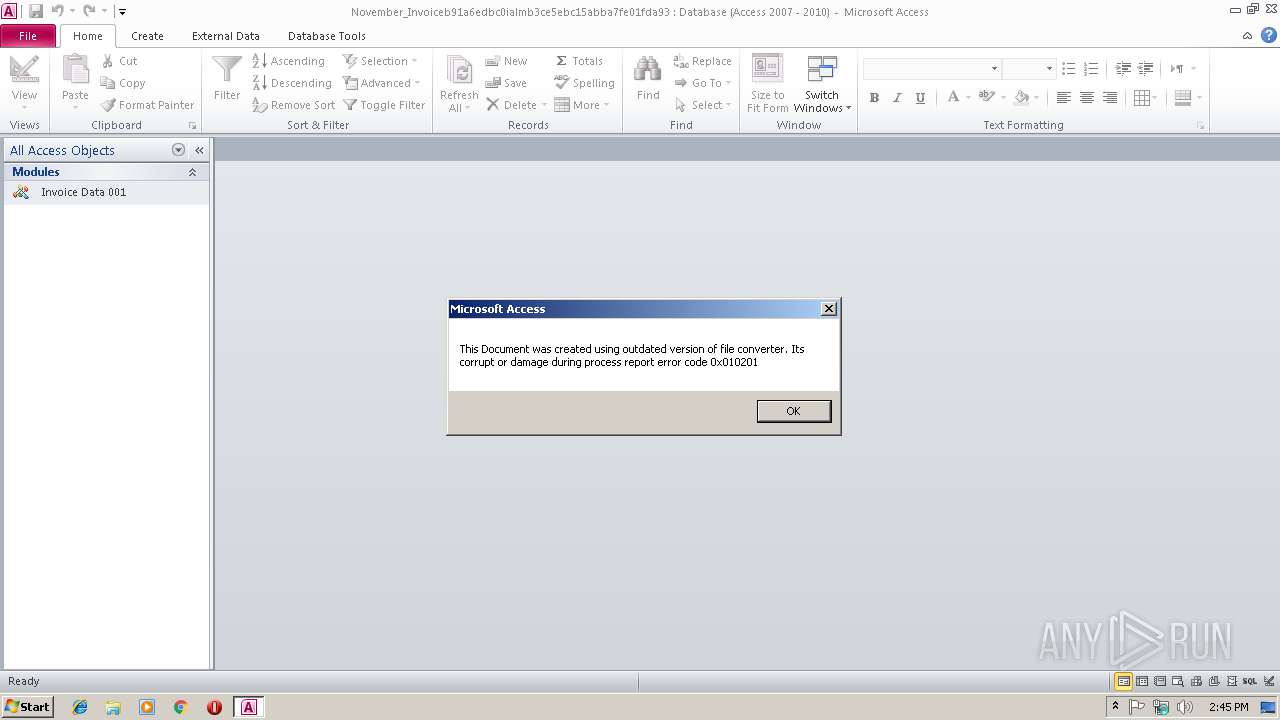
| File name: | November_Invoiceb91a6edbc0ialmb3ce5ebc15abba7fe01fda93.accde |
| Full analysis: | https://app.any.run/tasks/02d908db-9992-495a-beb3-4473113dd009 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 14:45:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msaccess |
| File info: | Microsoft Access Database |
| MD5: | 2601895CFE5909F5F66E98524BCD2AAF |
| SHA1: | C81A4306207D6AEDD9D4EC5B6E4B828BCA8E20AB |
| SHA256: | 18F0B09725C3F4CEA286AAE7FCEAEC0CD6E49F90C9AA72DCC9C6D748BFE716CD |
| SSDEEP: | 768:JlRTCFe+9BdQBrZ4oq03yfXwfksidQpcjEAZrsbVzoFrROlK0GLxt7kzRM/dw/d8:Jl5CArZ4vI0dN+z0lI6L34uSy |
MALICIOUS
Uses Microsoft Installer as loader
- MSACCESS.EXE (PID: 2864)
Unusual execution from Microsoft Office
- MSACCESS.EXE (PID: 2864)
Application was dropped or rewritten from another process
- 016ventdat.exe (PID: 3728)
- igfxCUIService.exe (PID: 3068)
- igfxCUIService.exe (PID: 2924)
SUSPICIOUS
Creates files in the user directory
- MSACCESS.EXE (PID: 2864)
- cmd.exe (PID: 3580)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3164)
- expand.exe (PID: 2444)
- 016ventdat.exe (PID: 3728)
- cmd.exe (PID: 3580)
Starts CMD.EXE for commands execution
- 016ventdat.exe (PID: 3728)
- igfxCUIService.exe (PID: 3068)
INFO
Reads Microsoft Office registry keys
- MSACCESS.EXE (PID: 2864)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3164)
- expand.exe (PID: 2444)
- 016ventdat.exe (PID: 3728)
- cmd.exe (PID: 3580)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 3164)
Application launched itself
- msiexec.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .accdb | | | Microsoft Access 2007 Database (90.4) |
|---|---|---|
| .pi2 | | | DEGAS med-res bitmap (9.5) |
Total processes
44
Monitored processes
11
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Local\Temp\igfxCUIService.exe" | C:\Windows\System32\cmd.exe | — | 016ventdat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2444 | "C:\Windows\System32\expand.exe" -R files.cab -F:* files | C:\Windows\System32\expand.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Microsoft Office\Office14\MSACCESS.EXE" /NOSTARTUP "C:\Users\admin\AppData\Local\Temp\November_Invoiceb91a6edbc0ialmb3ce5ebc15abba7fe01fda93.accde" %2 %3 %4 %5 %6 %7 %8 %9 | C:\Program Files\Microsoft Office\Office14\MSACCESS.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Access Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2924 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\igfxCUIService.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\igfxCUIService.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 10.0.14393.0 Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\AppData\Local\Temp\igfxCUIService.exe" | C:\Users\admin\AppData\Local\Temp\igfxCUIService.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 10.0.14393.0 Modules
| |||||||||||||||
| 3164 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | C:\Windows\system32\MsiExec.exe -Embedding D9DC2E03A557C75124DE54B2479FD4A8 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3580 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\AppData\Local\Temp\igfxCUIService.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\igfxCUIService.exe" | C:\Windows\System32\cmd.exe | igfxCUIService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\MW-4fdf10e9-c43d-4760-a7cb-715ebc7cc196\files\016ventdat.exe" | C:\Users\admin\AppData\Local\Temp\MW-4fdf10e9-c43d-4760-a7cb-715ebc7cc196\files\016ventdat.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Xde.exe Exit code: 0 Version: 10.0.14393.0 Modules
| |||||||||||||||
| 4080 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\igfxCUIService.exe" | C:\Windows\System32\cmd.exe | — | igfxCUIService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 361
Read events
1 269
Write events
72
Delete events
20
Modification events
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Resiliency\StartupItems |
| Operation: | write | Name: | j=$ |
Value: 6A3D2400300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ACCESSFiles |
Value: 1301413891 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | AceFiles |
Value: 1301413890 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access |
| Operation: | write | Name: | MTTT |
Value: 300B00006AA9BF57E096D40100000000 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\AccessParts\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: 6078E9659355D401 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Resiliency\StartupItems |
| Operation: | delete value | Name: | j=$ |
Value: 6A3D2400300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2864) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
5
Suspicious files
2
Text files
19
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Temp\CVR894A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3164 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFD4FF1D9DD86F84CB.TMP | — | |
MD5:— | SHA256:— | |||
| 2444 | expand.exe | C:\Users\admin\AppData\Local\Temp\MW-4fdf10e9-c43d-4760-a7cb-715ebc7cc196\files\$dpx$.tmp\8aa314bd6e02a9478eaba537e98fb24d.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | msiexec.exe | C:\Windows\Installer\MSIB2AE.tmp | — | |
MD5:— | SHA256:— | |||
| 3164 | msiexec.exe | C:\Config.Msi\1996f8.rbs | — | |
MD5:— | SHA256:— | |||
| 3164 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF8F6960F4198BA784.TMP | — | |
MD5:— | SHA256:— | |||
| 2864 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Temp\November_Invoiceb91a6edbc0ialmb3ce5ebc15abba7fe01fda93.laccdb | — | |
MD5:— | SHA256:— | |||
| 2864 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.ldb | — | |
MD5:— | SHA256:— | |||
| 2864 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.mdw | mdw | |
MD5:— | SHA256:— | |||
| 3164 | msiexec.exe | C:\Windows\Installer\MSI910B.tmp | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | msiexec.exe | 94.138.205.138:443 | jplymell.com | IHS Telekomunikasyon Ltd | TR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jplymell.com |
| malicious |
Threats
Process | Message |
|---|---|
MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Access\System.mdw |