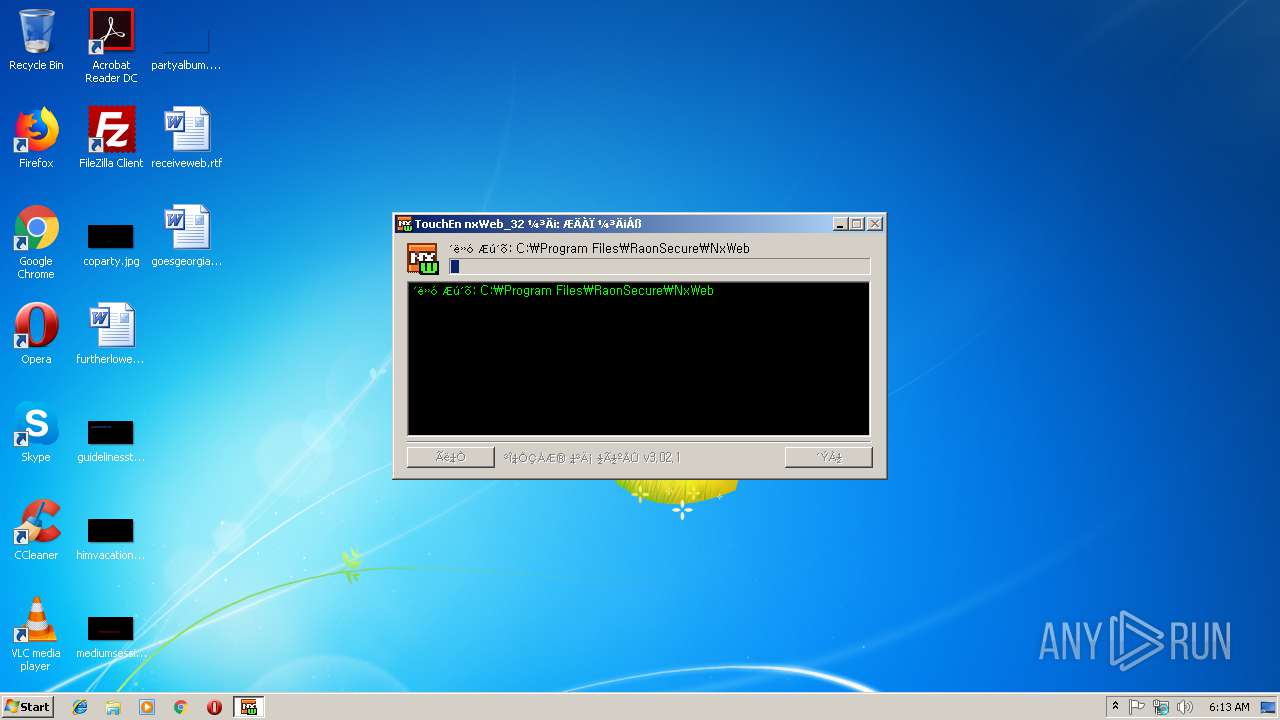
| File name: | TouchEn_nxWeb_Installer32.exe |
| Full analysis: | https://app.any.run/tasks/41e9aadd-95df-413e-94e1-95e642e90f04 |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2019, 06:13:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 53A131915AA83EAE3AD751776773C706 |
| SHA1: | AE113AB7CA3945BD6FD425507FADD165F2BDDDDF |
| SHA256: | 18DDC24F83C6AE89882201B73D8AA7B2B122FF43F3724309DF6DCC67940B24E8 |
| SSDEEP: | 98304:p9TIa85JeRwF6Q0J4u9oHD+wdInzmP0b6RR9iCXxEuCLBO3Gt9/2wCPJAB:p9krQRwK9qTIzmPhbECXhCtOWttwC |
MALICIOUS
Changes the autorun value in the registry
- CrossEX_LocalService_Install.exe (PID: 3624)
Loads dropped or rewritten executable
- TouchEn_nxWeb_Installer32.exe (PID: 3572)
- raon_touchenex_Install.exe (PID: 2592)
- TEWebP.exe (PID: 3548)
- explorer.exe (PID: 116)
- CrossEX_LocalService_Install.exe (PID: 3624)
- TEWeb.exe (PID: 4028)
Changes settings of System certificates
- CrossEX_LocalService_Install.exe (PID: 3624)
Application was dropped or rewritten from another process
- TENXW_SVR.exe (PID: 3724)
- TENXW_SVR.exe (PID: 2404)
- nsB790.tmp (PID: 2828)
- nsB8F9.tmp (PID: 1416)
- nsB9E4.tmp (PID: 3084)
- CrossEXService.exe (PID: 2560)
- CrossEX_LocalService_Install.exe (PID: 3624)
- TENXW_SVR.exe (PID: 2992)
- TEWebP.exe (PID: 3548)
- TEWeb.exe (PID: 3356)
- ObCrossEXService.exe (PID: 3856)
- raon_touchenex_Install.exe (PID: 2592)
- TEWeb.exe (PID: 3936)
- TEWeb.exe (PID: 4028)
SUSPICIOUS
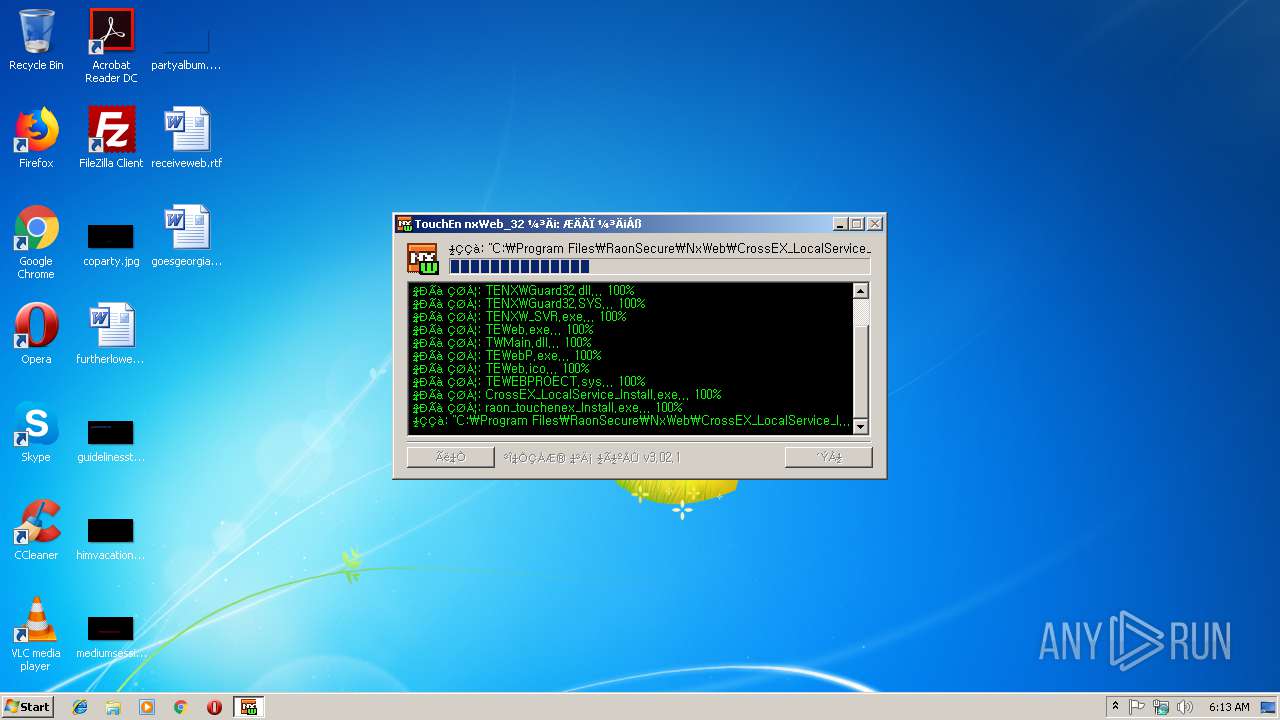
Creates files in the program directory
- TouchEn_nxWeb_Installer32.exe (PID: 3572)
- CrossEX_LocalService_Install.exe (PID: 3624)
- raon_touchenex_Install.exe (PID: 2592)
Executable content was dropped or overwritten
- TouchEn_nxWeb_Installer32.exe (PID: 3572)
- CrossEX_LocalService_Install.exe (PID: 3624)
- raon_touchenex_Install.exe (PID: 2592)
Starts application with an unusual extension
- CrossEX_LocalService_Install.exe (PID: 3624)
Starts SC.EXE for service management
- nsB9E4.tmp (PID: 3084)
- nsB8F9.tmp (PID: 1416)
- nsB790.tmp (PID: 2828)
Creates a software uninstall entry
- CrossEX_LocalService_Install.exe (PID: 3624)
- TouchEn_nxWeb_Installer32.exe (PID: 3572)
Creates COM task schedule object
- raon_touchenex_Install.exe (PID: 2592)
Creates or modifies windows services
- TENXW_SVR.exe (PID: 2404)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:34:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31f1 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.7 |
| ProductVersionNumber: | 1.0.0.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| CompanyName: | Copyright(C)2013 Raonsecure Co., Ltd. |
| FileDescription: | TouchEn nxWeb Installer_32 |
| FileVersion: | 1.0.0.7 |
| LegalCopyright: | Copyright(C)2013 Raonsecure Co., Ltd. |
| ProductName: | Application |
| ProductVersion: | 1, 0, 0, 7 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:34:02 |
| Detected languages: |
|
| CompanyName: | Copyright(C)2013 Raonsecure Co., Ltd. |
| FileDescription: | TouchEn nxWeb Installer_32 |
| FileVersion: | 1.0.0.7 |
| LegalCopyright: | Copyright(C)2013 Raonsecure Co., Ltd. |
| ProductName: | Application |
| ProductVersion: | 1, 0, 0, 7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:34:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006254 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43386 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04463 |
.ndata | 0x00030000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00003DE0 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.50273 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28995 | 843 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.63789 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.6301 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.64979 | 1384 | UNKNOWN | English - United States | RT_ICON |
103 | 2.74259 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.55952 | 236 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.8423 | 264 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.36476 | 76 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
20
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1416 | "C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB8F9.tmp" sc description "CrossEX Live Checker" "checking live status of CrossEXService" | C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB8F9.tmp | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\RaonSecure\NxWeb\TENXW_SVR.exe" | C:\Program Files\RaonSecure\NxWeb\TENXW_SVR.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: TouchEn nxWeb Exit code: 0 Version: 1, 0, 0, 5 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe" | C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe | CrossEX_LocalService_Install.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: CrossEX Service Exit code: 0 Version: 1.0.2.4 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\RaonSecure\NxWeb\raon_touchenex_Install.exe" /S | C:\Program Files\RaonSecure\NxWeb\raon_touchenex_Install.exe | TouchEn_nxWeb_Installer32.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: iniLINE CrossEX 32bit Exit code: 0 Version: 1.0.1.1091 Modules
| |||||||||||||||
| 2708 | sc description "CrossEX Live Checker" "checking live status of CrossEXService" | C:\Windows\system32\sc.exe | — | nsB8F9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB790.tmp" sc create "CrossEX Live Checker" binpath= "C:\Program Files\iniLINE\CrossEX\crossex\ObCrossEXService.exe" start= auto | C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB790.tmp | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\RaonSecure\NxWeb\TENXW_SVR.exe" i | C:\Program Files\RaonSecure\NxWeb\TENXW_SVR.exe | — | TouchEn_nxWeb_Installer32.exe | |||||||||||
User: admin Integrity Level: HIGH Description: TouchEn nxWeb Exit code: 2 Version: 1, 0, 0, 5 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB9E4.tmp" sc start "CrossEX Live Checker" | C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB9E4.tmp | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\TouchEn_nxWeb_Installer32.exe" | C:\Users\admin\AppData\Local\Temp\TouchEn_nxWeb_Installer32.exe | — | explorer.exe | |||||||||||
User: admin Company: Copyright(C)2013 Raonsecure Co., Ltd. Integrity Level: MEDIUM Description: TouchEn nxWeb Installer_32 Exit code: 3221226540 Version: 1.0.0.7 Modules
| |||||||||||||||
Total events
446
Read events
389
Write events
55
Delete events
2
Modification events
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | write | Name: | CrossEXService |
Value: 020000000000000000000000 | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\iniLINE_CrossEX |
| Operation: | write | Name: | DisplayName |
Value: iniLINE CrossEX Service | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\iniLINE_CrossEX |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\iniLINE\CrossEX\crossex\UnInstallCrossEXLocal.exe | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\iniLINE_CrossEX |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.2.4 | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\iniLINE_CrossEX |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.iniline.co.kr | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\iniLINE_CrossEX |
| Operation: | write | Name: | Publisher |
Value: iniLINE Co., Ltd. | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3D362BDF73E5A3EDF54768CCF30D77B858809BAC |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000003D362BDF73E5A3EDF54768CCF30D77B858809BAC2000000001000000B1040000308204AD30820395A003020102020900A3E9A7E5BCCFFF5A300D06092A864886F70D01010B0500308195310B3009060355040613024B52311330110603550408130A536F6D652D5374617465310E300C0603550407130553656F756C311A3018060355040A1311696E694C494E4520436F2E2C204C74642E311F301D06035504031316696E694C494E452043726F7373455820526F6F7443413124302206092A864886F70D0109011615737570706F727440696E696C696E652E636F2E6B72301E170D3135313131313037313932305A170D3235313131313037313932305A308195310B3009060355040613024B52311330110603550408130A536F6D652D5374617465310E300C0603550407130553656F756C311A3018060355040A1311696E694C494E4520436F2E2C204C74642E311F301D06035504031316696E694C494E452043726F7373455820526F6F7443413124302206092A864886F70D0109011615737570706F727440696E696C696E652E636F2E6B7230820122300D06092A864886F70D01010105000382010F003082010A0282010100B652D1FDC8391A8E3ED30E4DC7D19CB964345963936289104515077F4D7203665001B36DFE42CE0C78F0FFF71504C542071AD95E69958CD914BD23D520A216D7AFC5CBD7FA0AAE9DB93446D68E55F390346A097C71B5EF1E4C54E8C8D6E82C2BC0A91E80D20795D8AE67B9A8D6C2B5B2C698B5EF7D9BDAB41877E6A29B1F645C6F8C70FA82E11FB0EE19F62379EF468C8AD704B8A38F1BAE717531713105FDBE6154F707AB81A524FB6A12A37C99D695327B555566D3ADA6DC9310DF75D9813D167A80167AD930D1D4F6C7D00EEDDBB0B15B7FBAEE876AF2AEC609F679649EA004DAE6C8BBE8027673AA9F913FAC833D3E0D3DB0DF5C6D9876D84F48384391150203010001A381FD3081FA301D0603551D0E041604147C6A6A1E808F4C6C1A5B26D443946E8C2ECEE67E3081CA0603551D230481C23081BF80147C6A6A1E808F4C6C1A5B26D443946E8C2ECEE67EA1819BA48198308195310B3009060355040613024B52311330110603550408130A536F6D652D5374617465310E300C0603550407130553656F756C311A3018060355040A1311696E694C494E4520436F2E2C204C74642E311F301D06035504031316696E694C494E452043726F7373455820526F6F7443413124302206092A864886F70D0109011615737570706F727440696E696C696E652E636F2E6B72820900A3E9A7E5BCCFFF5A300C0603551D13040530030101FF300D06092A864886F70D01010B0500038201010001DF83E8698B5001A22192C954F03ADB78718D9CEDC13C99A4BEC38211BF7643EF639C61A5BDD5B568F8052945C2A896F2EE0BE047D83DED64078395E2B3356E10E19708961DB18FDC5AFC383FDED0F21E594A29CB2062829B7F6B498871BA307CDC8C5E9DBA2E4B97E0E56994F7AB164534771C604CFC971A8CA3A10FE69E5AEBC7ED7AAF721D75273008370073E2CE1FCFA773F2A9701E1B759137D82ECC1C34680FC8DEA44F2FDDDD18D4AB76E6BFB12EE0935342E75F3D6ADAACF81A35EF3B64A720F63BA1B1AADAD7ACCFA47DEE57811AF050F9D7D52A7E5CA91CA6E4A34C54E75FC3009ABDD958E21B758A617557DA29EDD4BDEDECF761D1EE9B5B059E | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CrossEXService |
Value: C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe | |||
| (PID) Process: | (3624) CrossEX_LocalService_Install.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | CrossEXService |
Value: C:\Program Files\iniLINE\CrossEX\crossex\CrossEXService.exe | |||
| (PID) Process: | (2404) TENXW_SVR.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\TENXWGuard |
| Operation: | write | Name: | Type |
Value: 1 | |||
Executable files
23
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3624 | CrossEX_LocalService_Install.exe | C:\Users\admin\AppData\Local\Temp\nscB731.tmp\nsB8F9.tmp | — | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TENXWGuard32.SYS | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TENXW_SVR.exe | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TWMain.dll | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TEWeb.exe | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TEWeb.ico | image | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TEWebP.exe | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TENXWGuard32.dll | executable | |
MD5:— | SHA256:— | |||
| 3572 | TouchEn_nxWeb_Installer32.exe | C:\Program Files\RaonSecure\NxWeb\TEWEBPROECT.sys | executable | |
MD5:— | SHA256:— | |||
| 3624 | CrossEX_LocalService_Install.exe | C:\Users\admin\AppData\Local\Temp\nscB731.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
TENXW_SVR.exe | C:\Program Files\RaonSecure\NxWeb\TEWEBPROECT.sys |
TENXW_SVR.exe | err : 193 |
TENXW_SVR.exe | [TENXW_SVR.exe] - Failed to StartDriver. |
TEWebP.exe | [ZDSGuard] 32 DllMain hook strProductName2 : C:\Program Files\RaonSecure\NxWeb\TEWebP.exe-1 |
explorer.exe | [ZDSGuard] 32 DllMain hook strProductName2 : C:\Windows\Explorer.EXE-1 |
TEWebP.exe | LaunchAppIntoDifferentSession |
TEWebP.exe | LaunchAppIntoDifferentSession |
TEWebP.exe | CreateProcessAsUser : error:740 - C:\Program Files\RaonSecure\NxWeb\TEWeb.exe |
TEWeb.exe | [ZDSGuard] 32 DllMain hook strProductName2 : C:\Program Files\RaonSecure\NxWeb\TEWeb.exe-1 |
TEWeb.exe | [TEWeb.exe] 0 Execute2ndModule : bRet:1, path:C:\Program Files\RaonSecure\NxWeb\TEWeb64.exe |