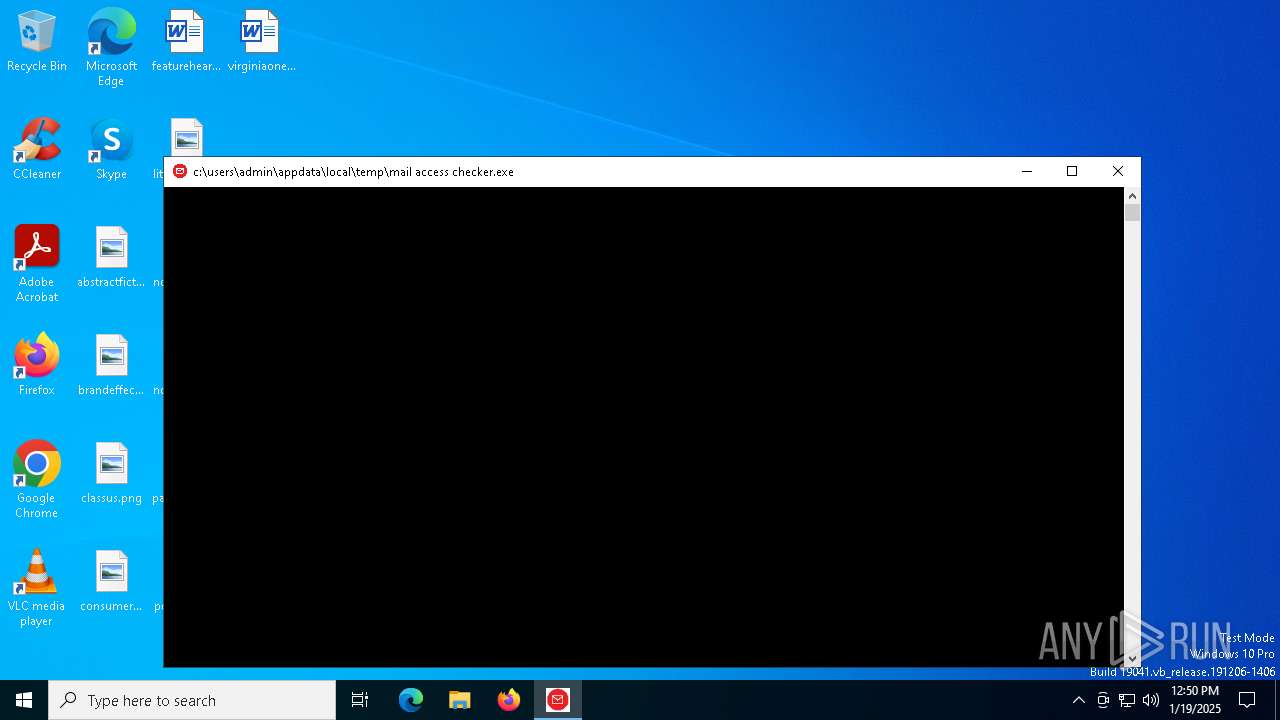
| File name: | mail access checker.exe |
| Full analysis: | https://app.any.run/tasks/23ed8c6f-1290-4ad0-a2cb-4922390bf5f4 |
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2025, 12:50:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 672EFD88A59E4E1FA3FE9F18ADE72D09 |
| SHA1: | 60998A69B9D83598FF9B66C22013ECDB25EEE68E |
| SHA256: | 18A95984FE80BCC9318CAA42AE5C2BDFAC6E4747B747253381391B2B13FA5FC5 |
| SSDEEP: | 98304:etfGrRCpfAbLUnj4Aq4lrYJhhDvsU2oL8nBMqdPfzKeJQJHOGh9wv2WsUbUdw35k:0Abv9y0SCZ/dbpNb1Ou |
MALICIOUS
No malicious indicators.SUSPICIOUS
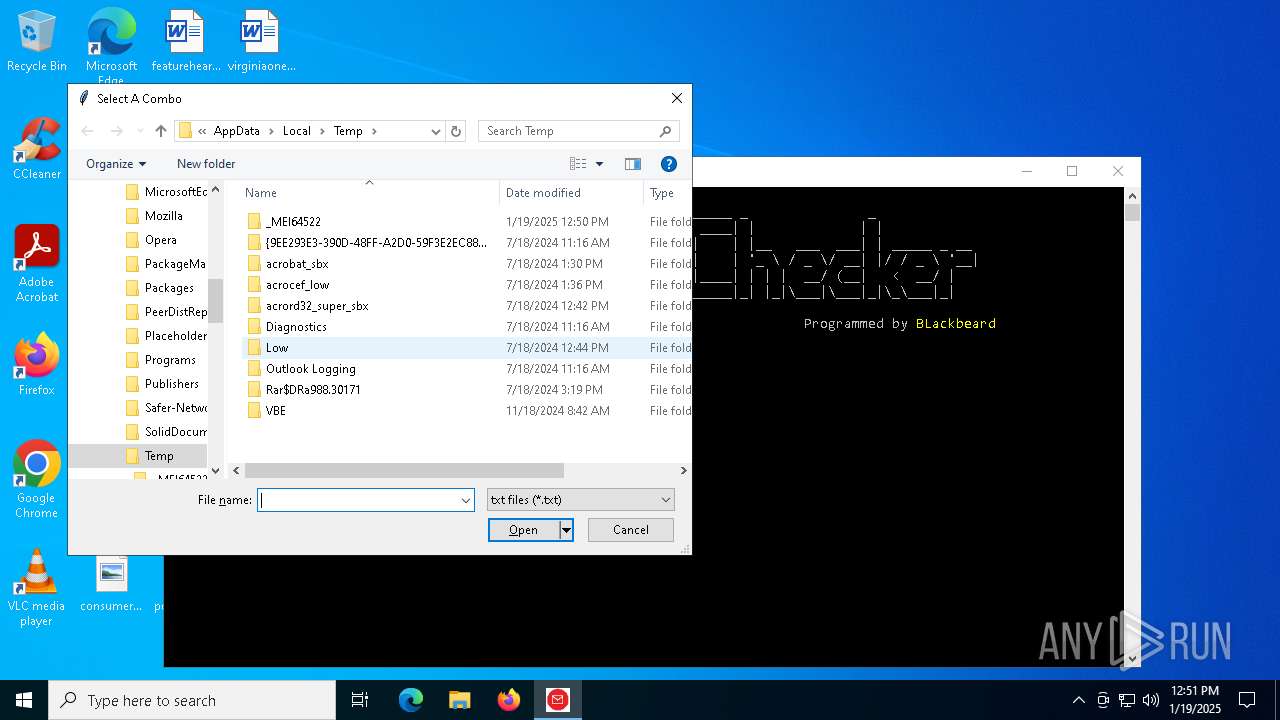
Starts application with an unusual extension
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 6452)
Executable content was dropped or overwritten
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 6452)
Starts itself from another location
- mail access checker.exe (PID: 6296)
Process drops legitimate windows executable
- mail access checker.exe (PID: 6452)
The process drops C-runtime libraries
- mail access checker.exe (PID: 6452)
Process drops python dynamic module
- mail access checker.exe (PID: 6452)
Application launched itself
- mail access checker.exe (PID: 6452)
Reads security settings of Internet Explorer
- mail access checker.exe (PID: 2216)
Loads Python modules
- mail access checker.exe (PID: 2216)
INFO
Creates files or folders in the user directory
- mail access checker.exe (PID: 6296)
Checks supported languages
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 6452)
- icsys.icn.exe (PID: 6460)
- mail access checker.exe (PID: 2216)
Reads the computer name
- mail access checker.exe (PID: 6452)
- icsys.icn.exe (PID: 6460)
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 2216)
The sample compiled with english language support
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 6452)
Create files in a temporary directory
- icsys.icn.exe (PID: 6460)
- mail access checker.exe (PID: 6296)
- mail access checker.exe (PID: 6452)
Failed to create an executable file in Windows directory
- icsys.icn.exe (PID: 6460)
PyInstaller has been detected (YARA)
- mail access checker.exe (PID: 6452)
Reads the machine GUID from the registry
- mail access checker.exe (PID: 2216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (42.6) |
|---|---|---|
| .exe | | | InstallShield setup (22.3) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.2) |
| .exe | | | Win64 Executable (generic) (14.3) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:06:14 19:01:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 176128 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3670 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| ProductName: | Win |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Win |
| OriginalFileName: | Win.exe |
Total processes
132
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2216 | "c:\users\admin\appdata\local\temp\mail access checker.exe " | C:\Users\admin\AppData\Local\Temp\mail access checker.exe | — | mail access checker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6296 | "C:\Users\admin\AppData\Local\Temp\mail access checker.exe" | C:\Users\admin\AppData\Local\Temp\mail access checker.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6452 | "c:\users\admin\appdata\local\temp\mail access checker.exe " | C:\Users\admin\AppData\Local\Temp\mail access checker.exe | mail access checker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6460 | C:\Users\admin\AppData\Local\icsys.icn.exe | C:\Users\admin\AppData\Local\icsys.icn.exe | — | mail access checker.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | mail access checker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 410
Read events
3 389
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6460) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (6296) mail access checker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E000000040000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000020000000300000001000000FFFFFFFF | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\209\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (2216) mail access checker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 49F58C6700000000 | |||
Executable files
26
Suspicious files
7
Text files
915
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_asyncio.pyd | executable | |
MD5:4E406CBFBFB77D6155B814E9F344165C | SHA256:47998CDEC5D134DD351947D94AD5CA5A234130D22DFF7DAE1A12B8C06DAF2891 | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_bz2.pyd | executable | |
MD5:1C7F3F37A067019B7926C0F92F3A3AA7 | SHA256:BBC7F102B547180EA8CA5FF496F1BD419BFEFD360BE15610AE6B08837076F5DC | |||
| 6296 | mail access checker.exe | C:\Users\admin\AppData\Local\icsys.icn.exe | executable | |
MD5:D09C3F1C2BD7BDABD474D272BB1F6B42 | SHA256:067BE26B41A52DDBCADA5CE393C91FD1555812BB6722B9CE0B892A2DDB17043B | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_lzma.pyd | executable | |
MD5:280C3A7C8C5E5282EC8E746AE685FF54 | SHA256:C6E30F1139D4F2B1EC7A5ACA8563D6F946EE6FFA6A90A4EB066CD867D3384C39 | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_tkinter.pyd | executable | |
MD5:1B81683BE893967C0300BA93D65626F2 | SHA256:DF2C5E49D13DAA417CD599C0955AEEA0679543766E5F30F1814B1F8BF9C6435D | |||
| 6296 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\mail access checker.exe | executable | |
MD5:485AC6CDC8BB8CD5C3621A2772482B47 | SHA256:974737403125B78C57DB8126B28D8B80686B0447CC12D1BD141EE6E89E55FC26 | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_overlapped.pyd | executable | |
MD5:54C6149AB1C0A621B22BE4F4046386B6 | SHA256:44D896E8AA8887BAD398B03DFDB8CF72AA3C0D87730A2AC0D92763722A426A7F | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\libffi-7.dll | executable | |
MD5:BC20614744EBF4C2B8ACD28D1FE54174 | SHA256:0C7EC6DE19C246A23756B8550E6178AC2394B1093E96D0F43789124149486F57 | |||
| 6452 | mail access checker.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_ctypes.pyd | executable | |
MD5:ADAD459A275B619F700D52A0F9470131 | SHA256:2695A7635FA2BEBB6BD720146916F21676E846EA5F39288886BBB27CE2AF92F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
27
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6192 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2072 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6192 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2536 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2072 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |